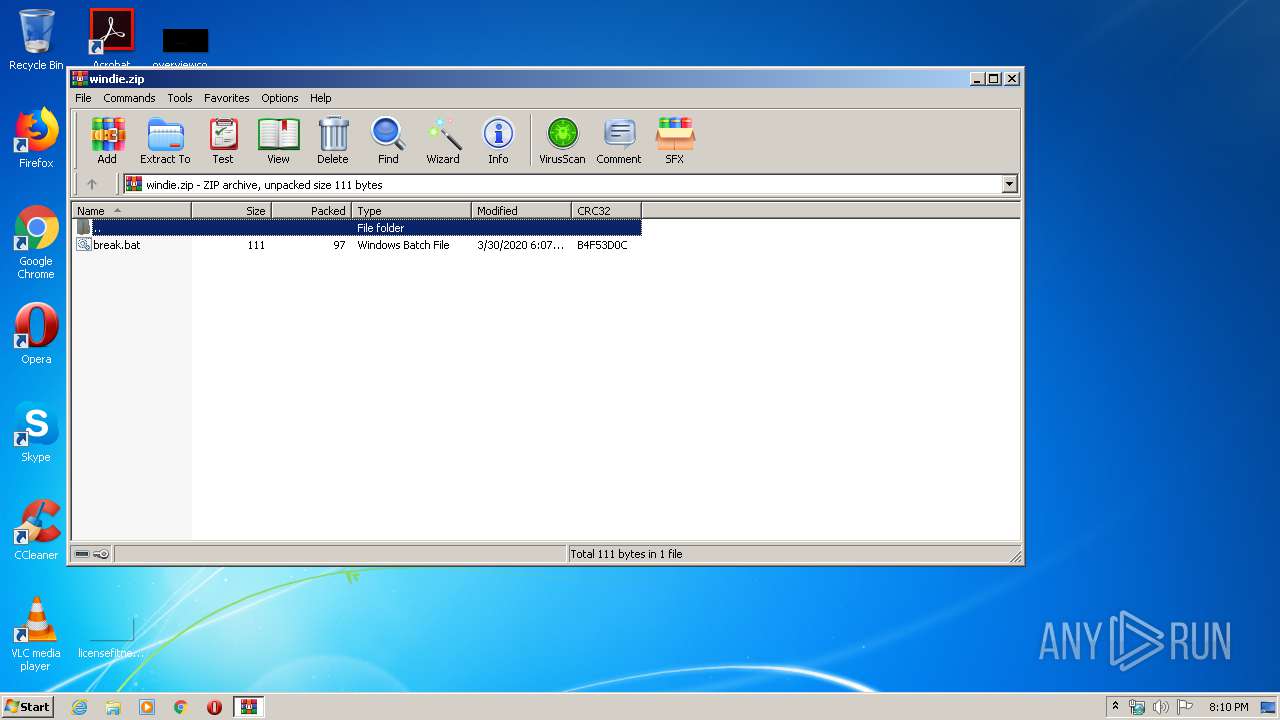
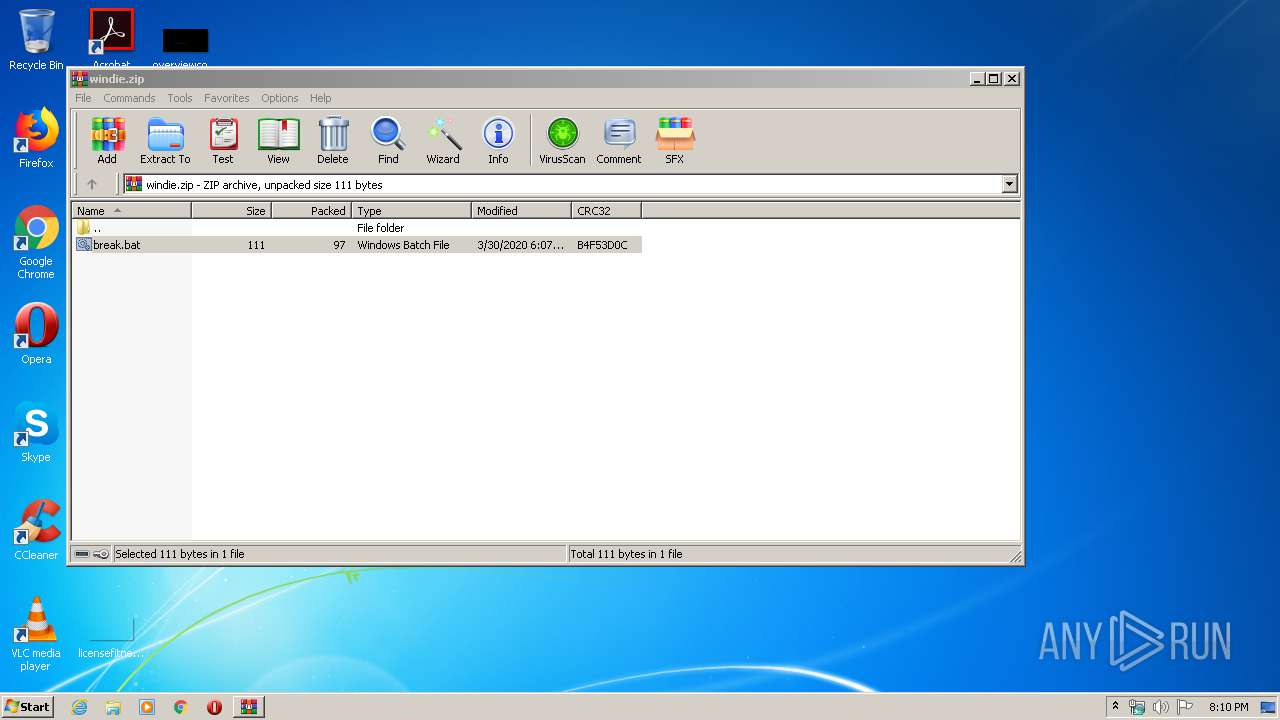
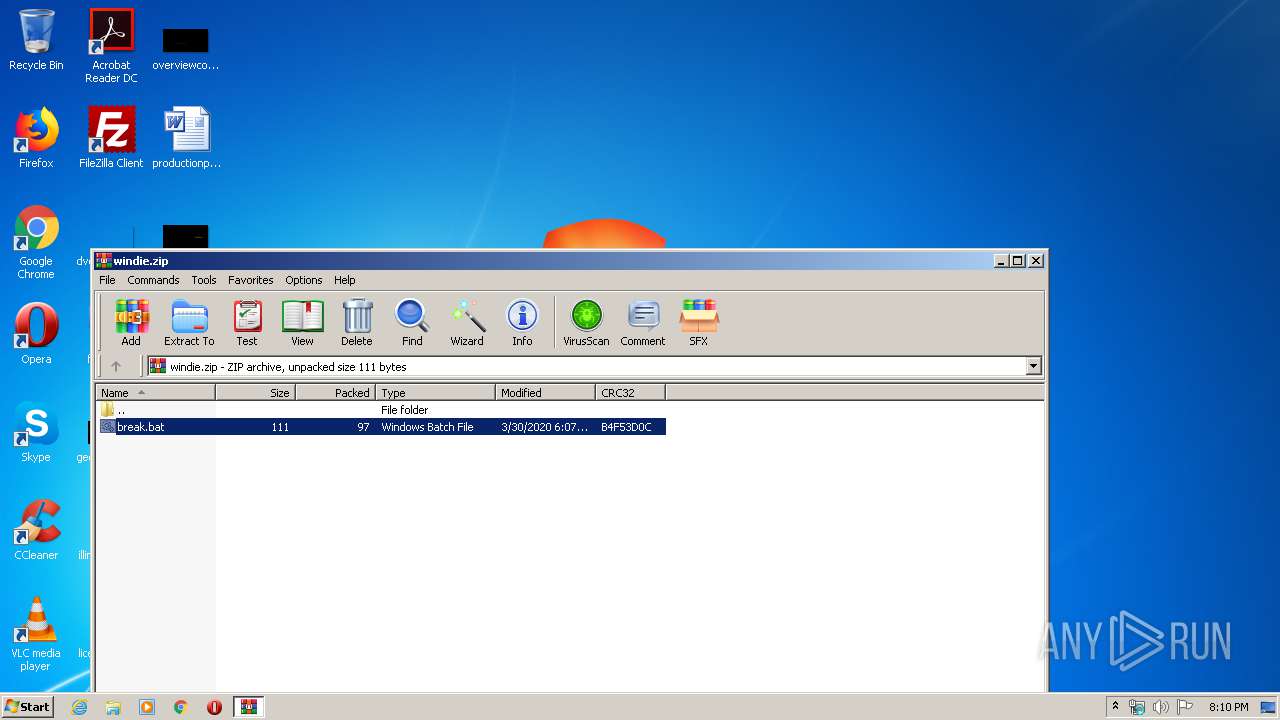
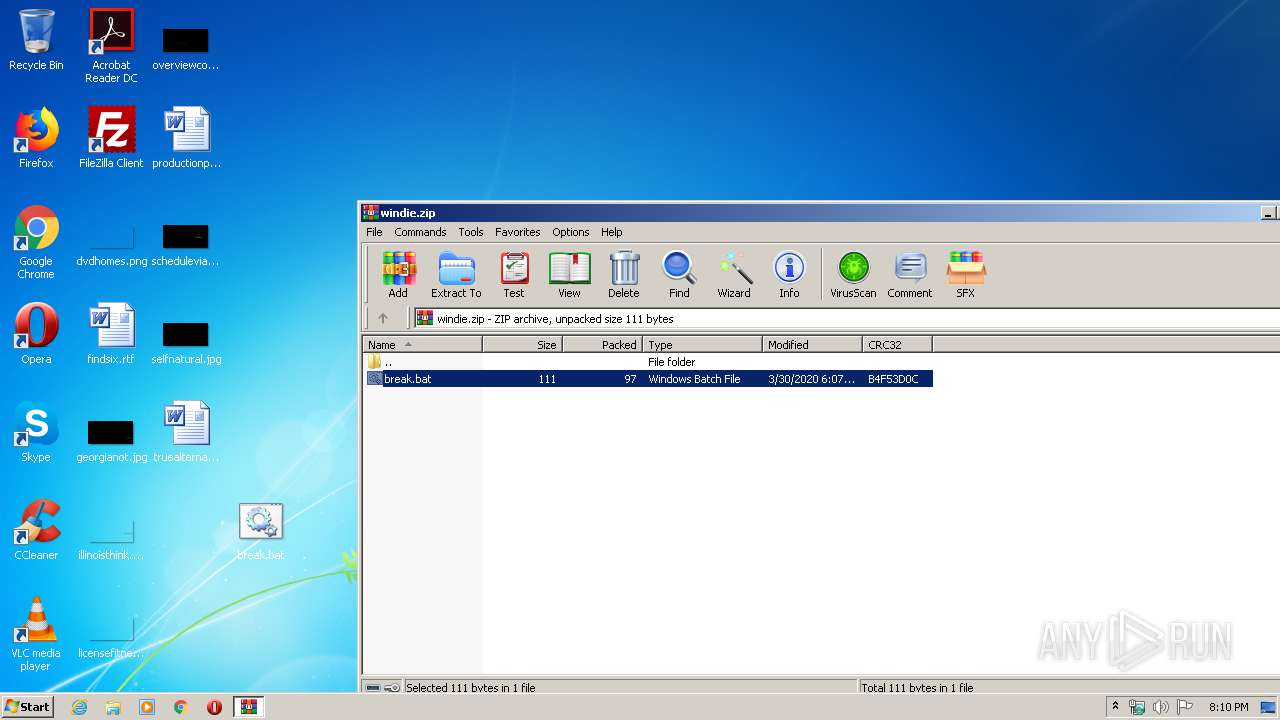
| File name: | windie.zip |
| Full analysis: | https://app.any.run/tasks/e268ced5-74af-4db6-861f-2084cd8ae5a8 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 19:10:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A58B66A797906EA265BBB410180AE932 |
| SHA1: | 053C9620F840CC9737B8B6CB88D70005FA9C7342 |
| SHA256: | E85CAEF8354524650B774662B34A233A9AAA010ED96AD0E3701172EAB227A06E |
| SSDEEP: | 6:5jEhFlxYbX8LvLfDAHQVLV6KaPHLB+lFX:5jKTviA0HLBaV |
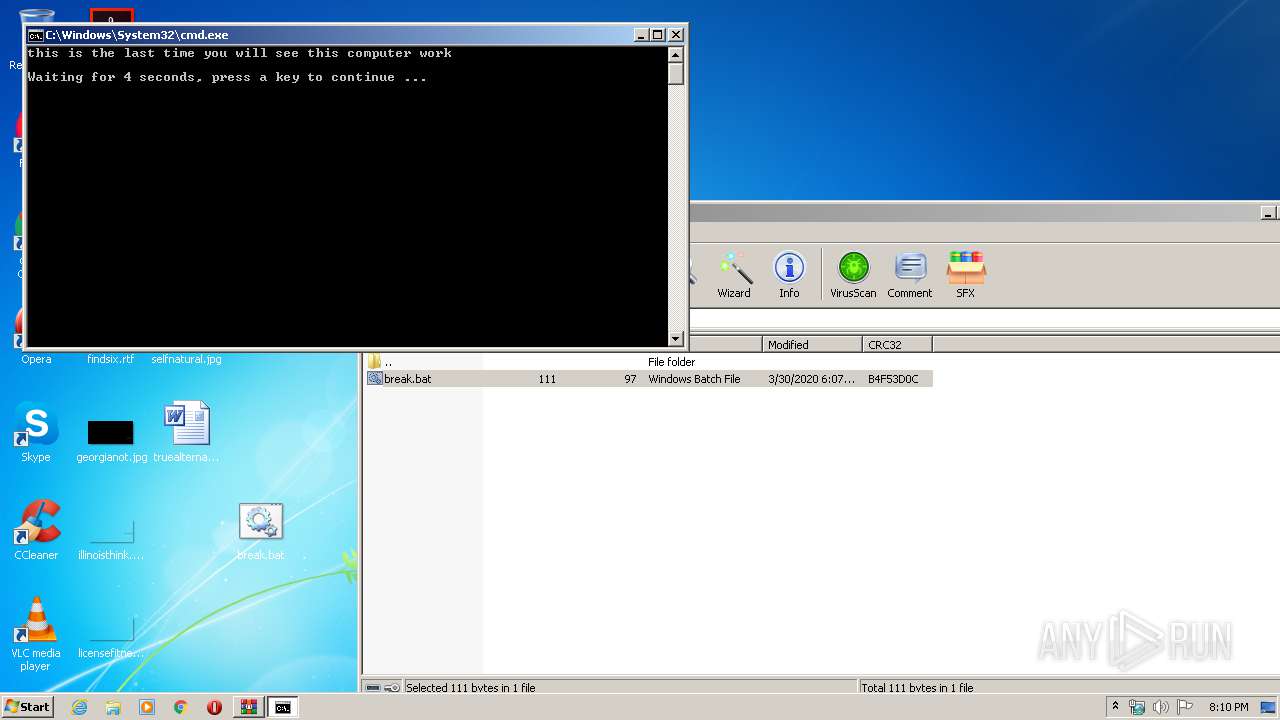
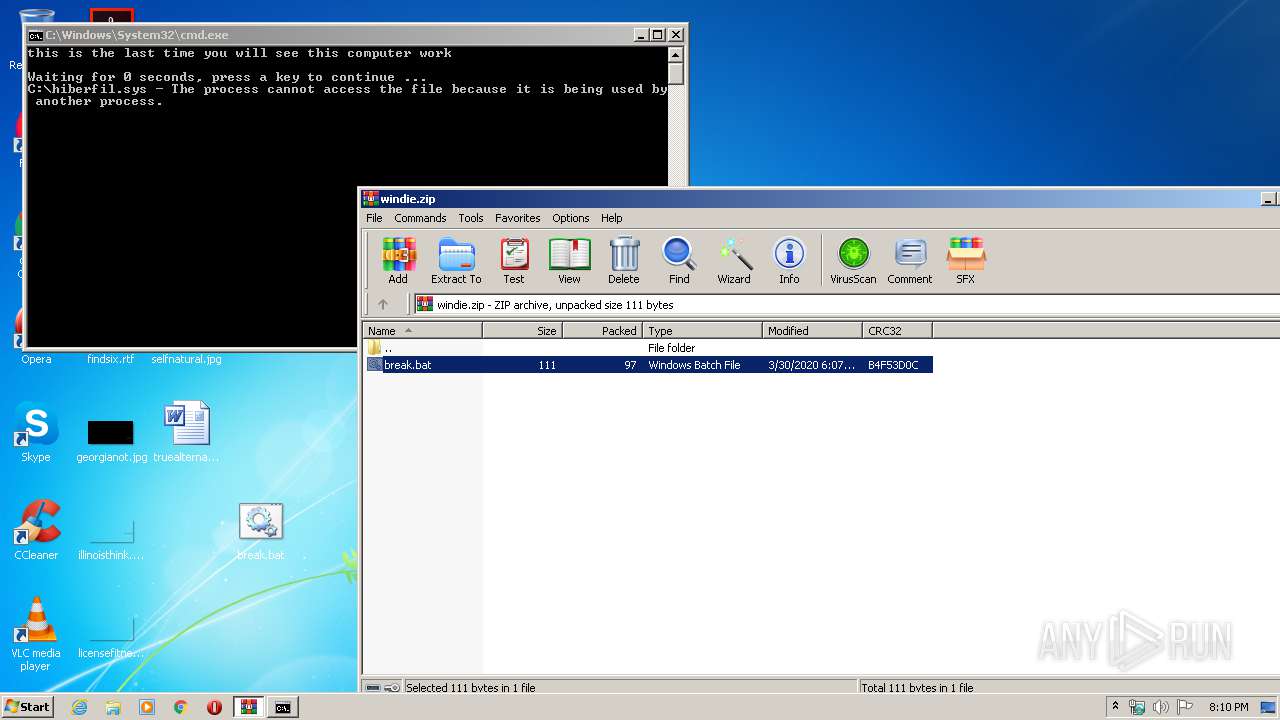
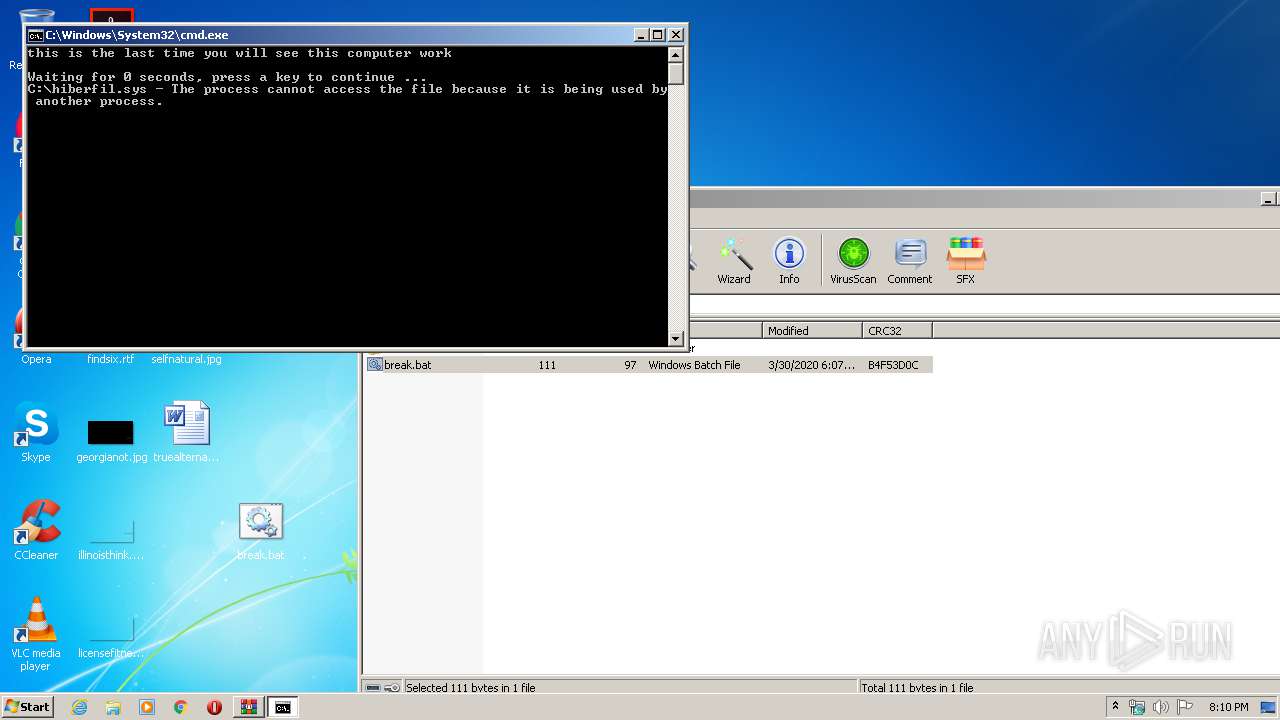
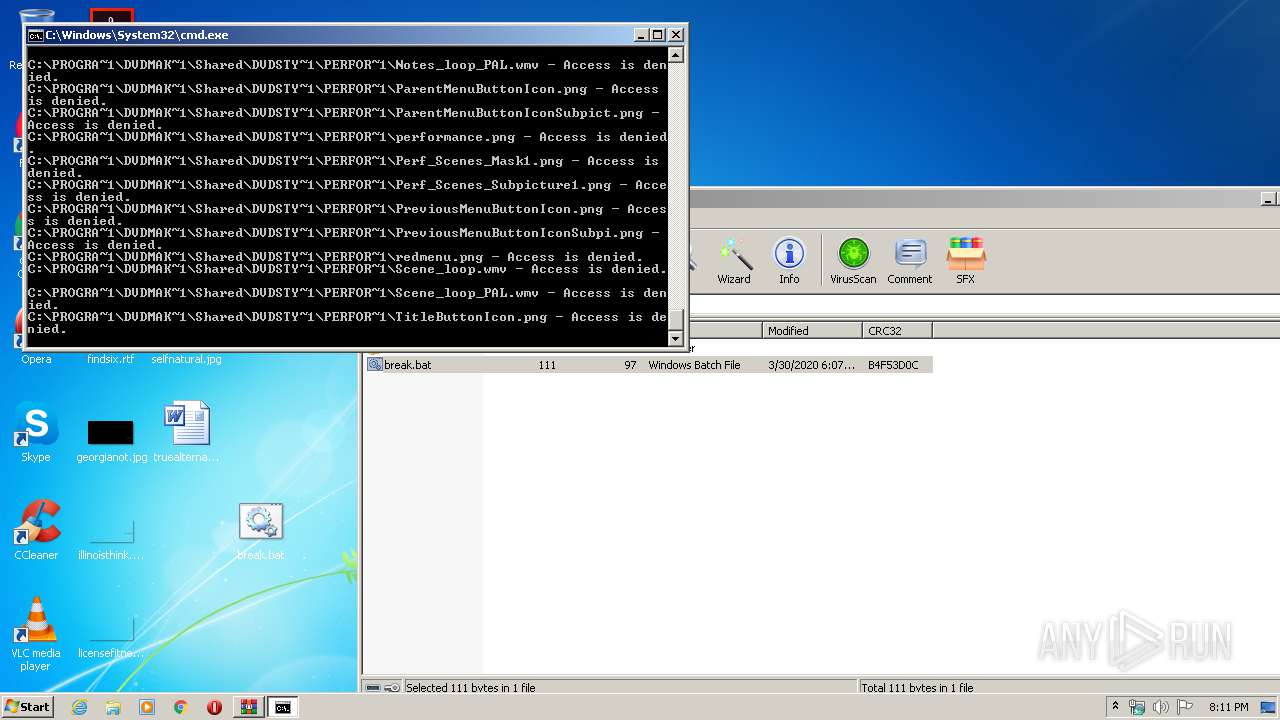
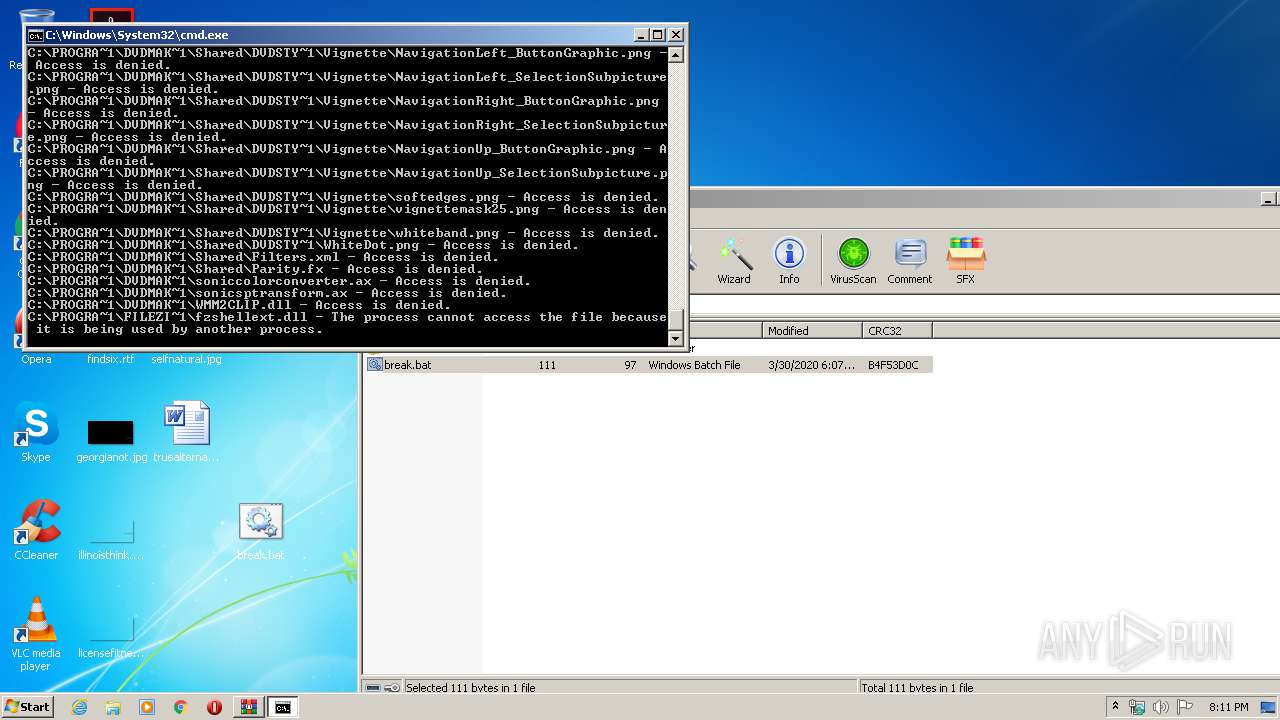
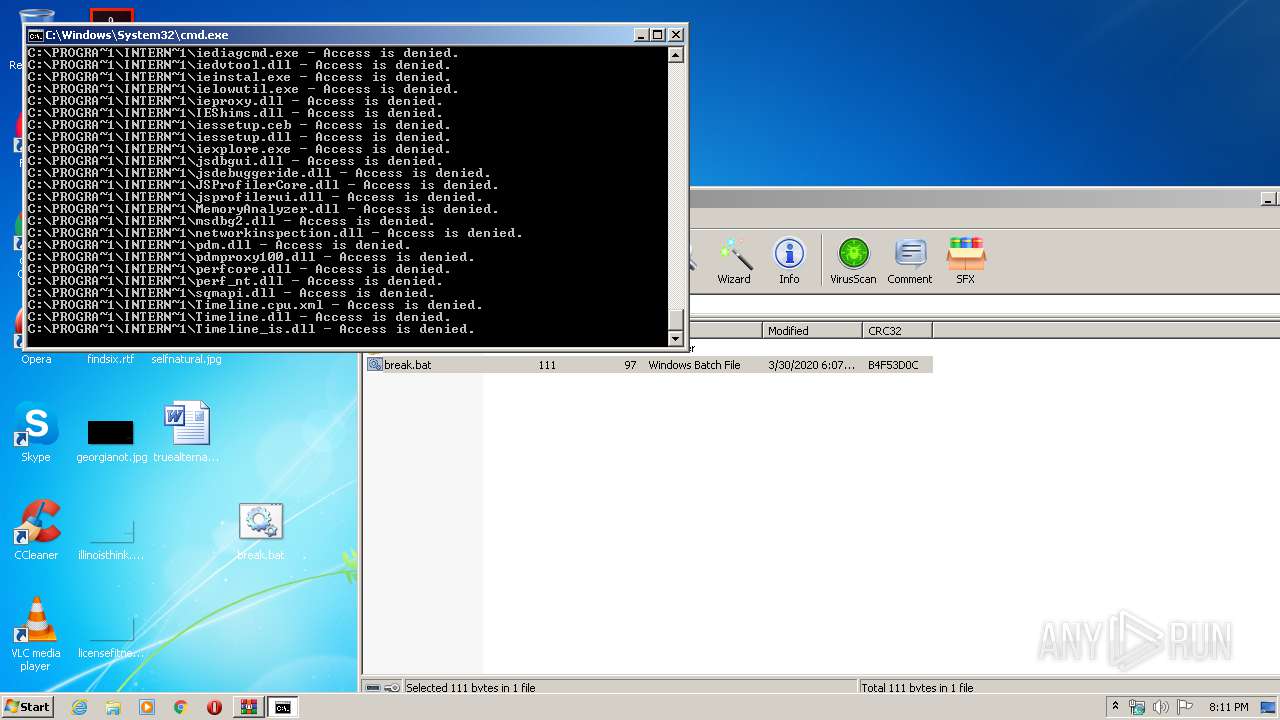
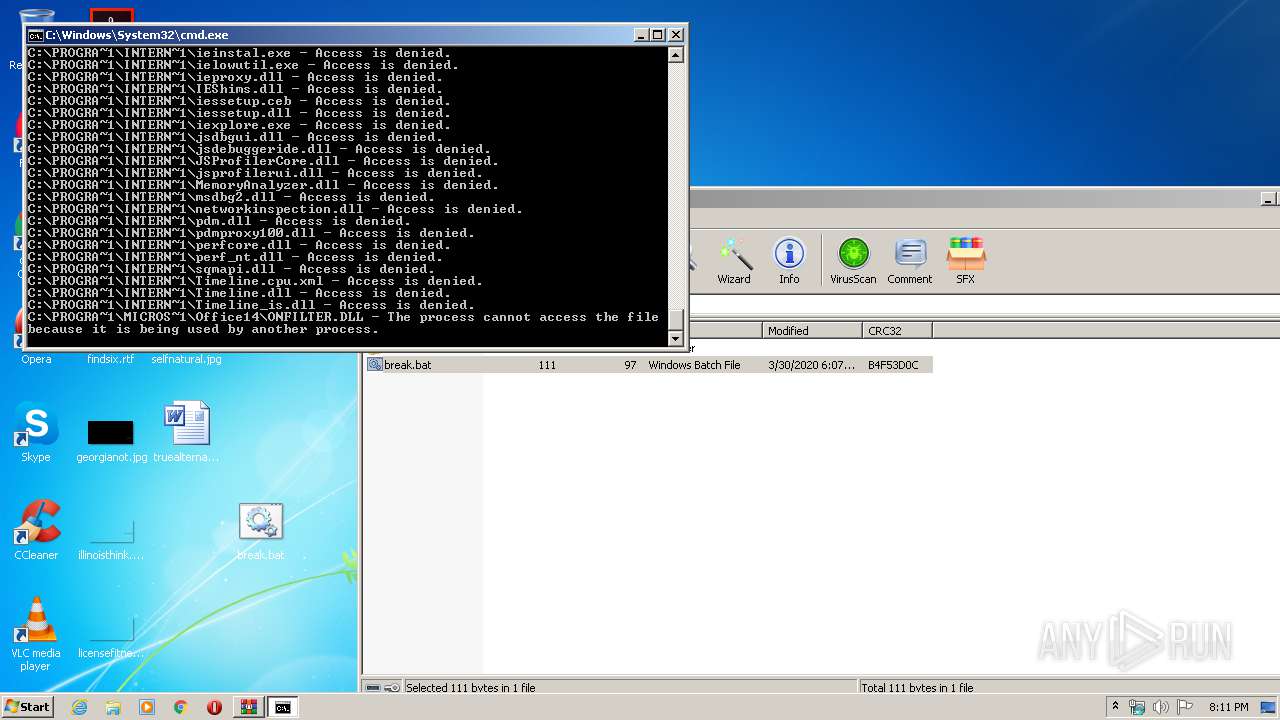
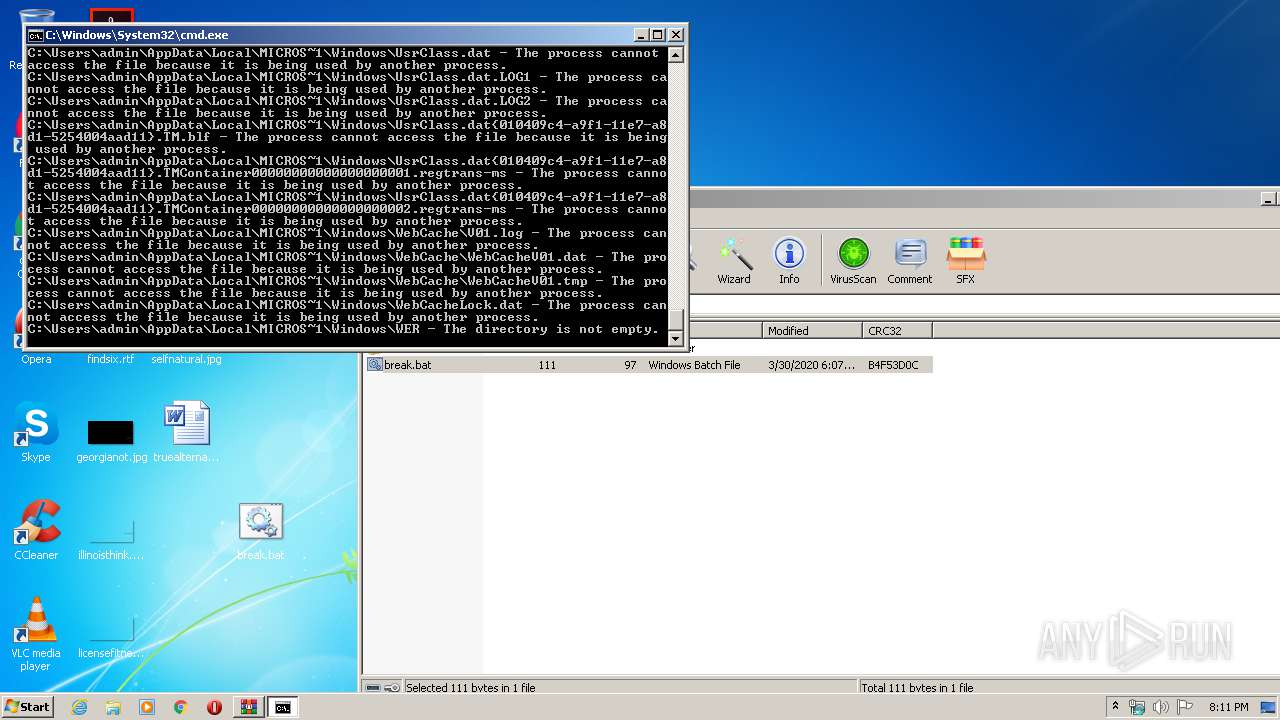
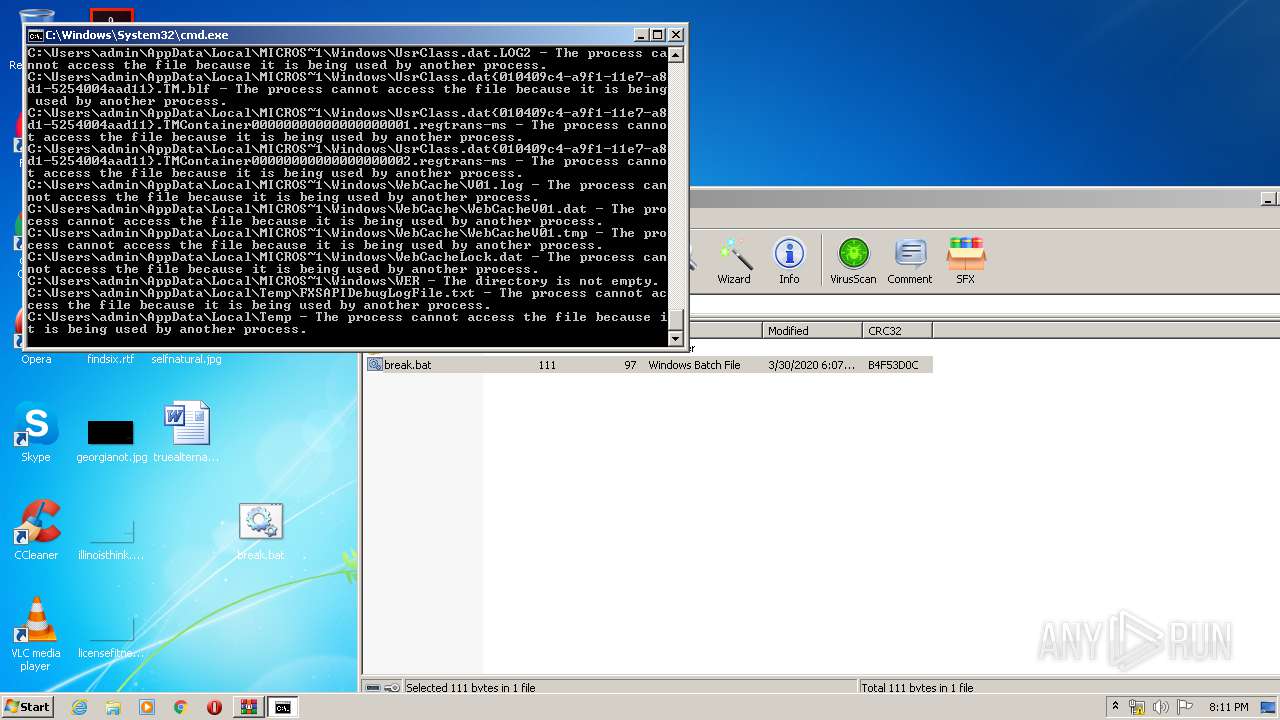
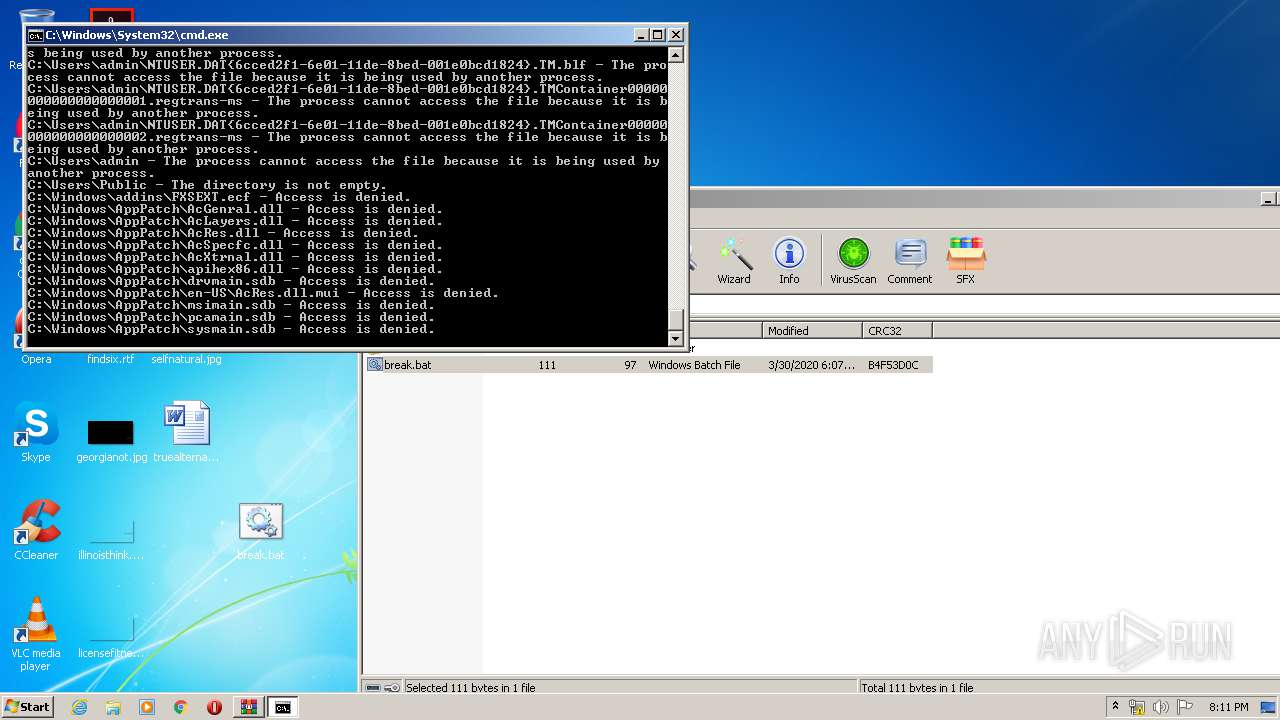
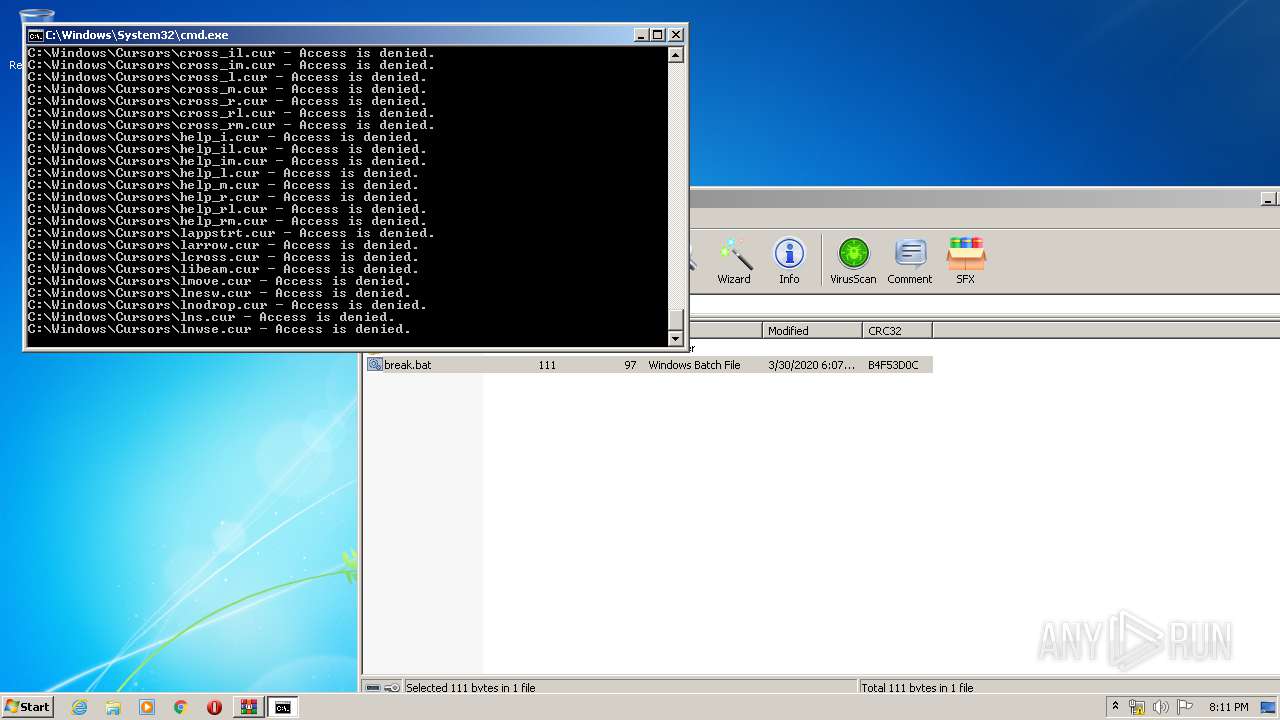
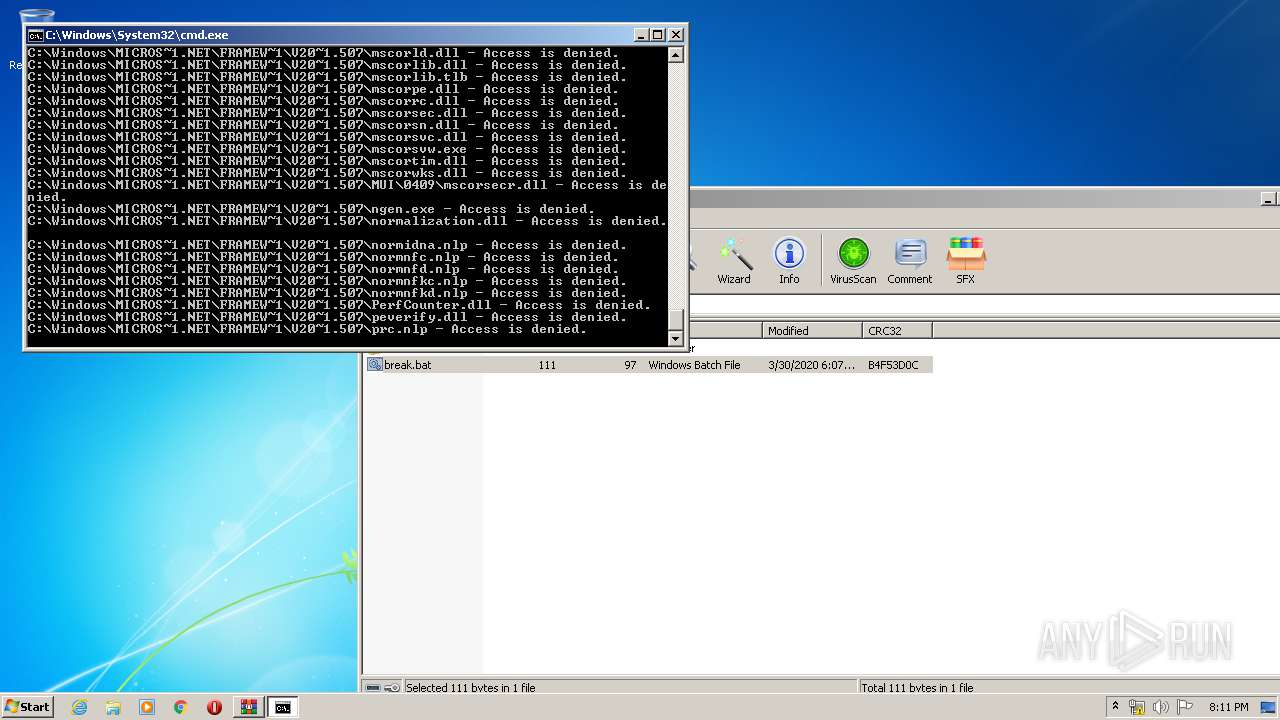
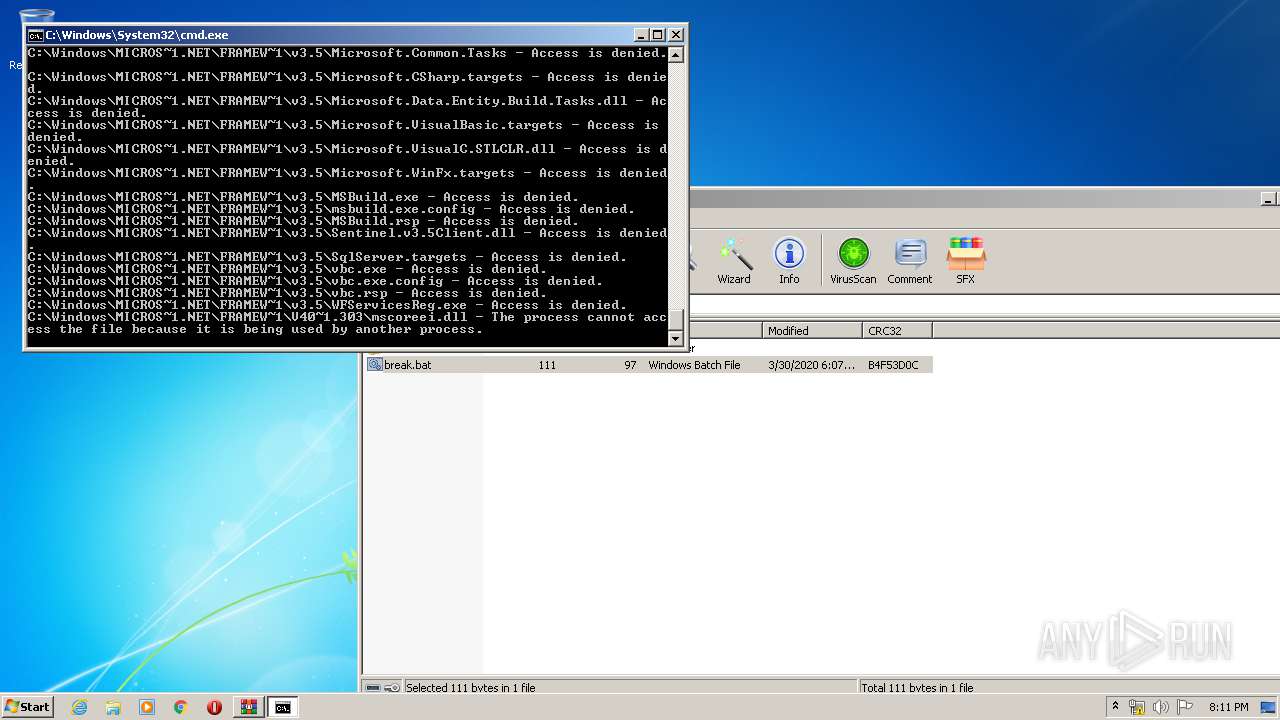
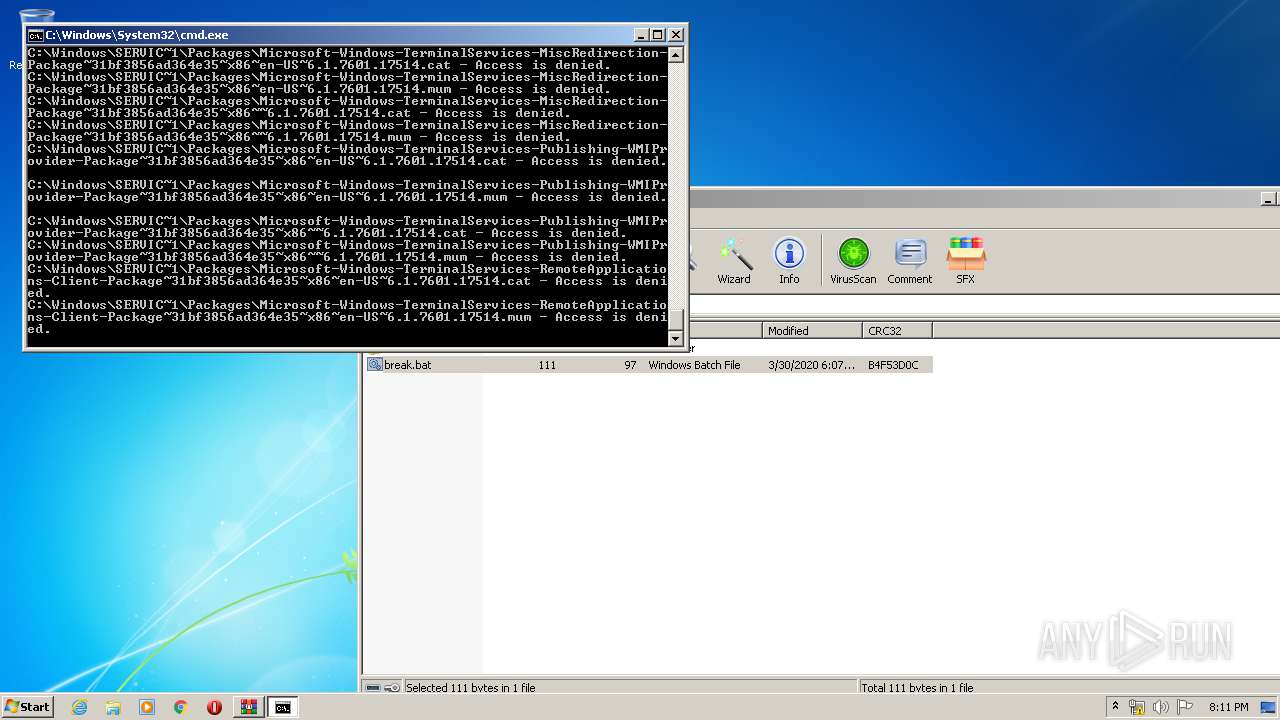
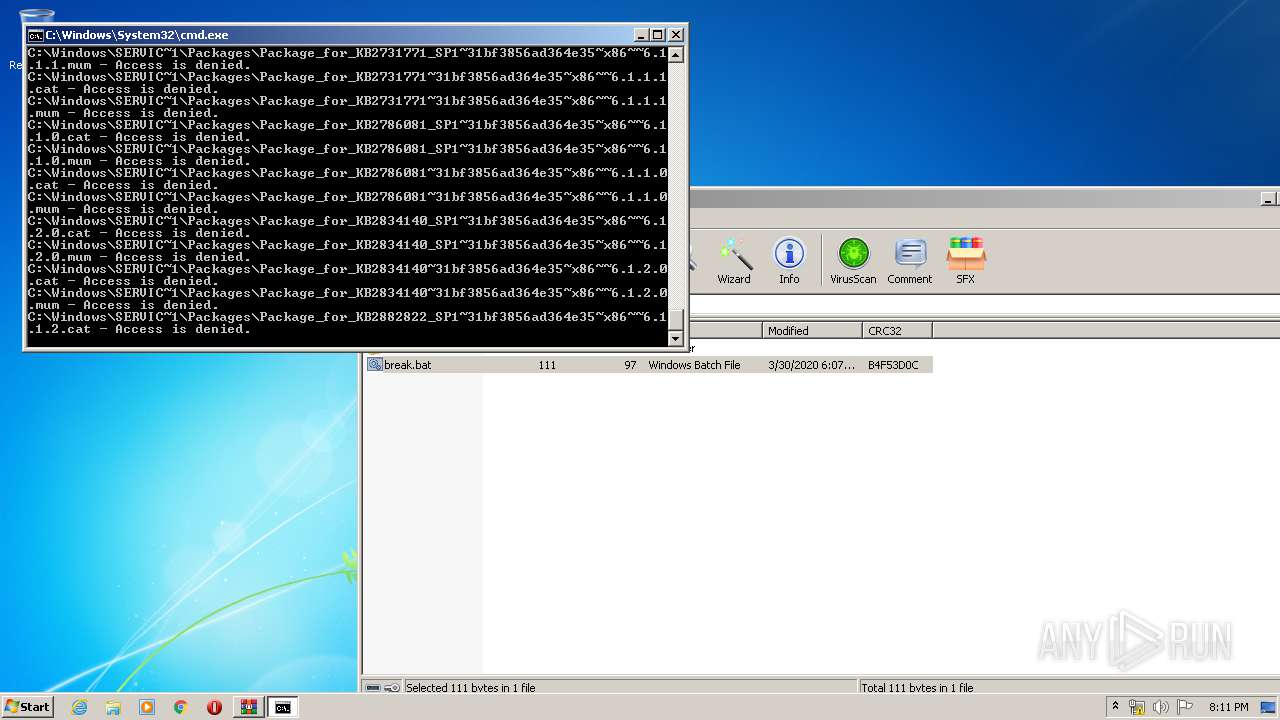
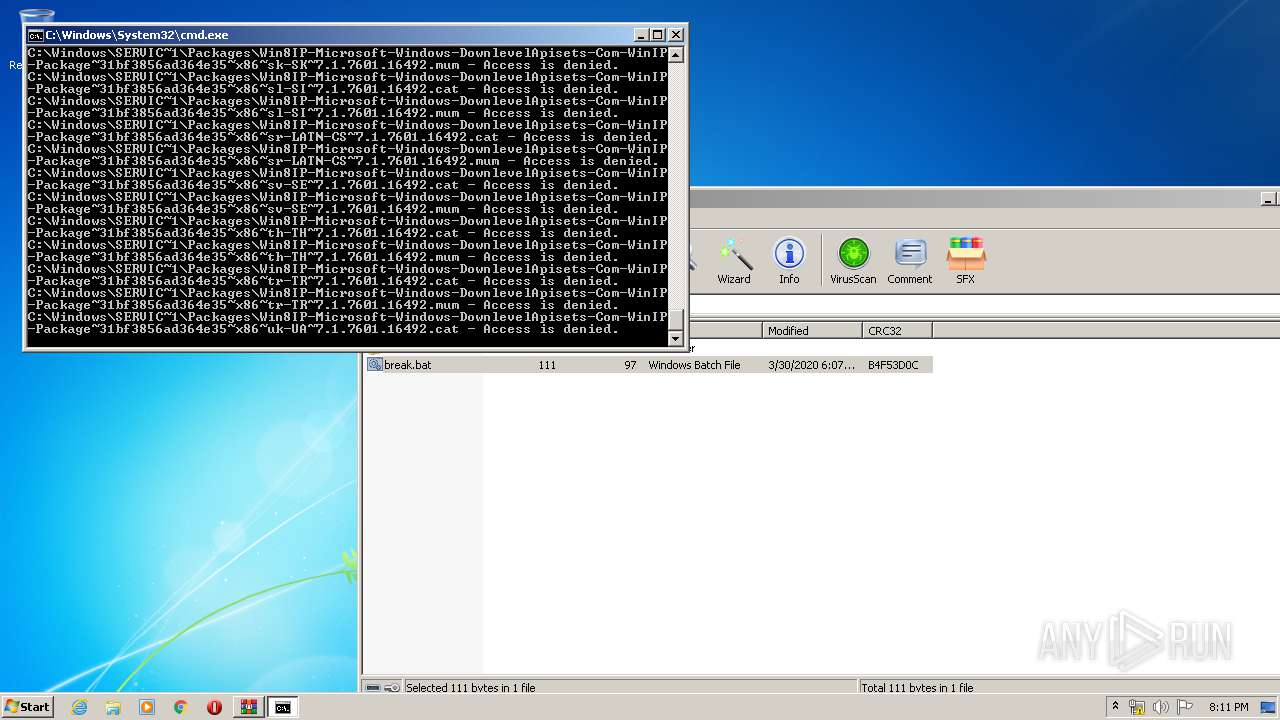
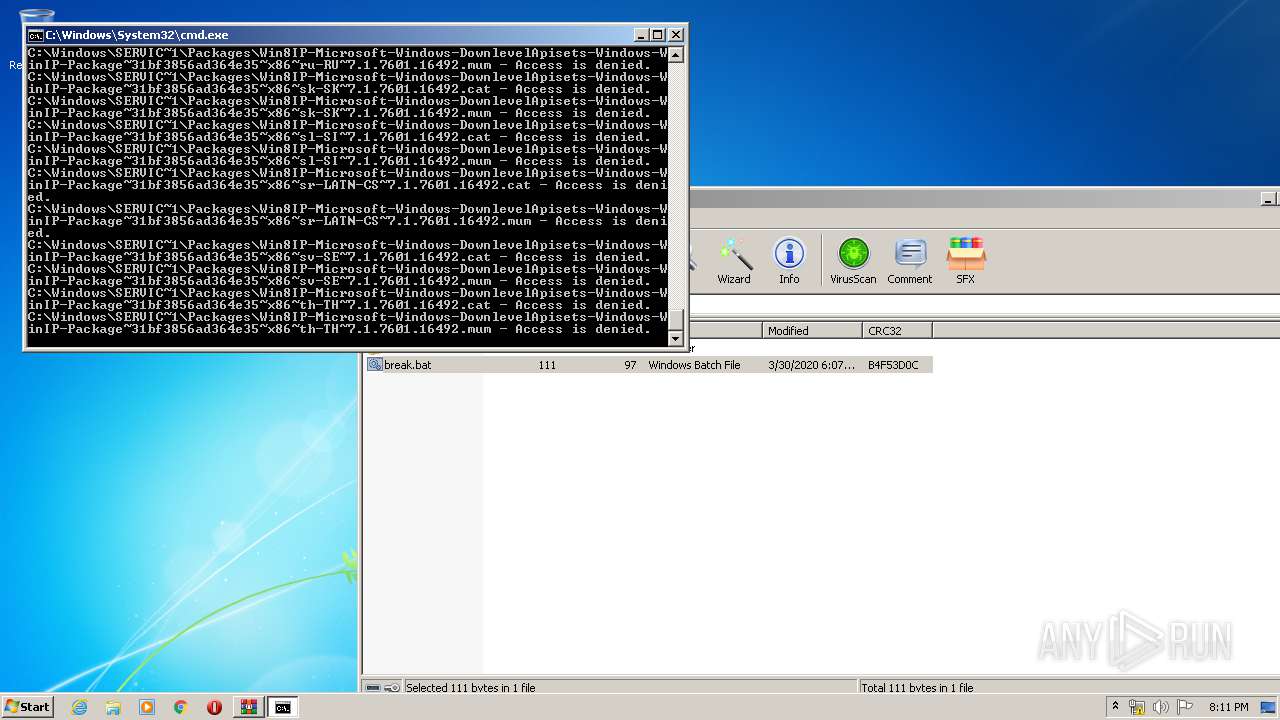
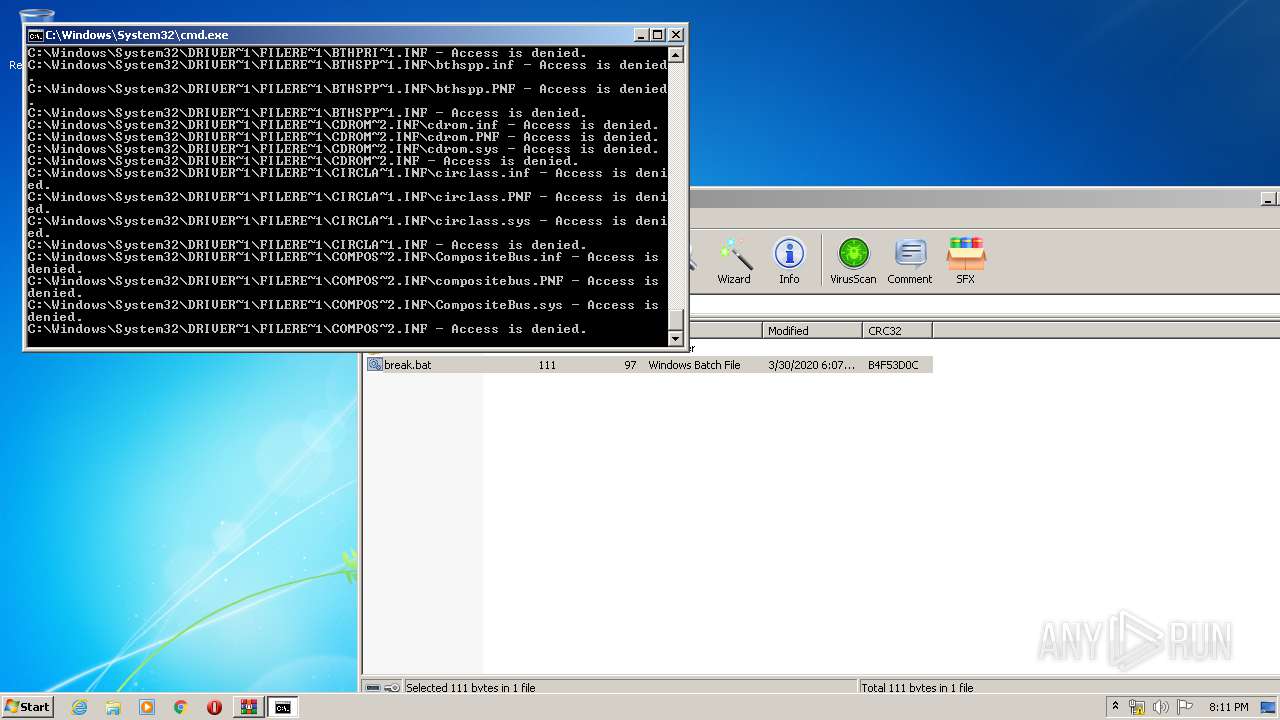
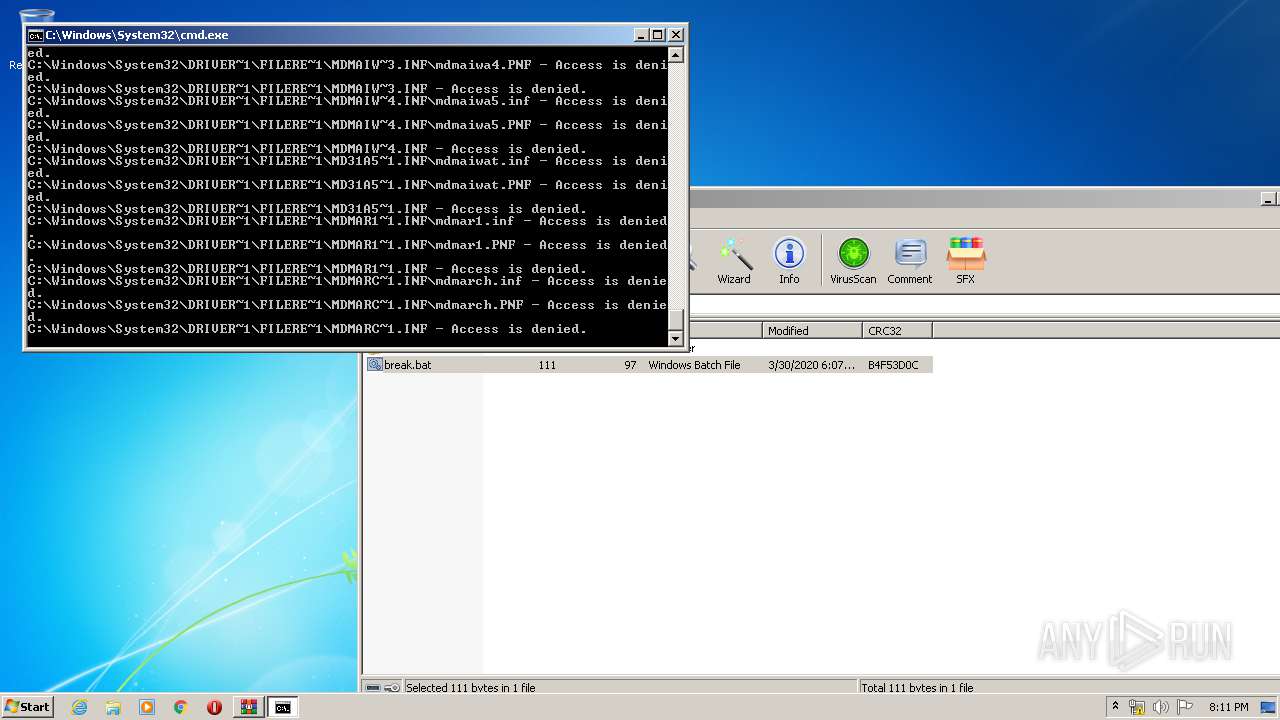
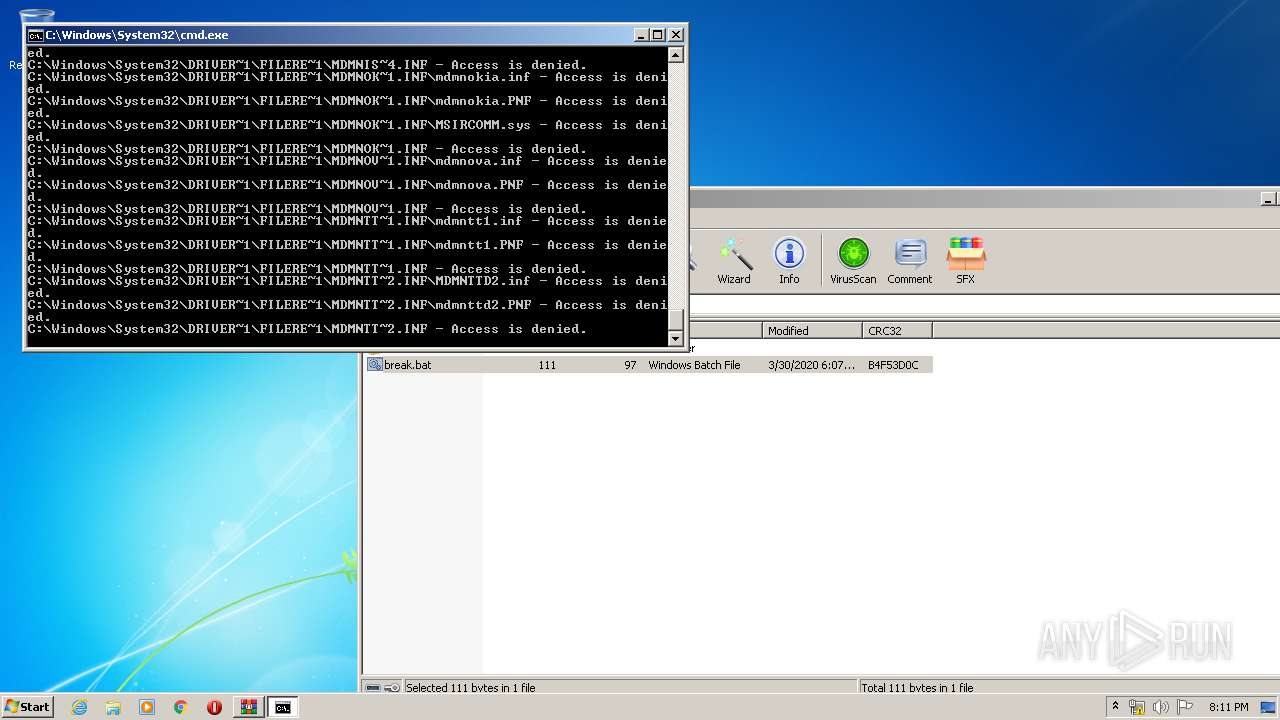
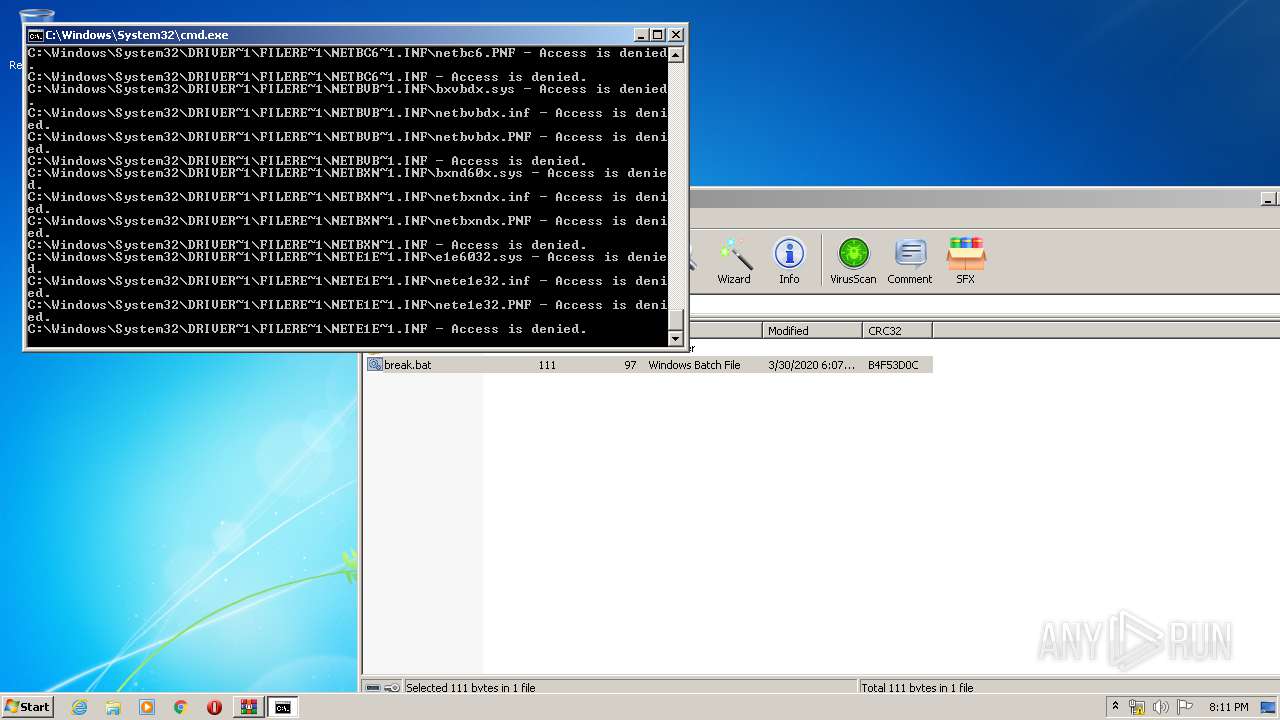
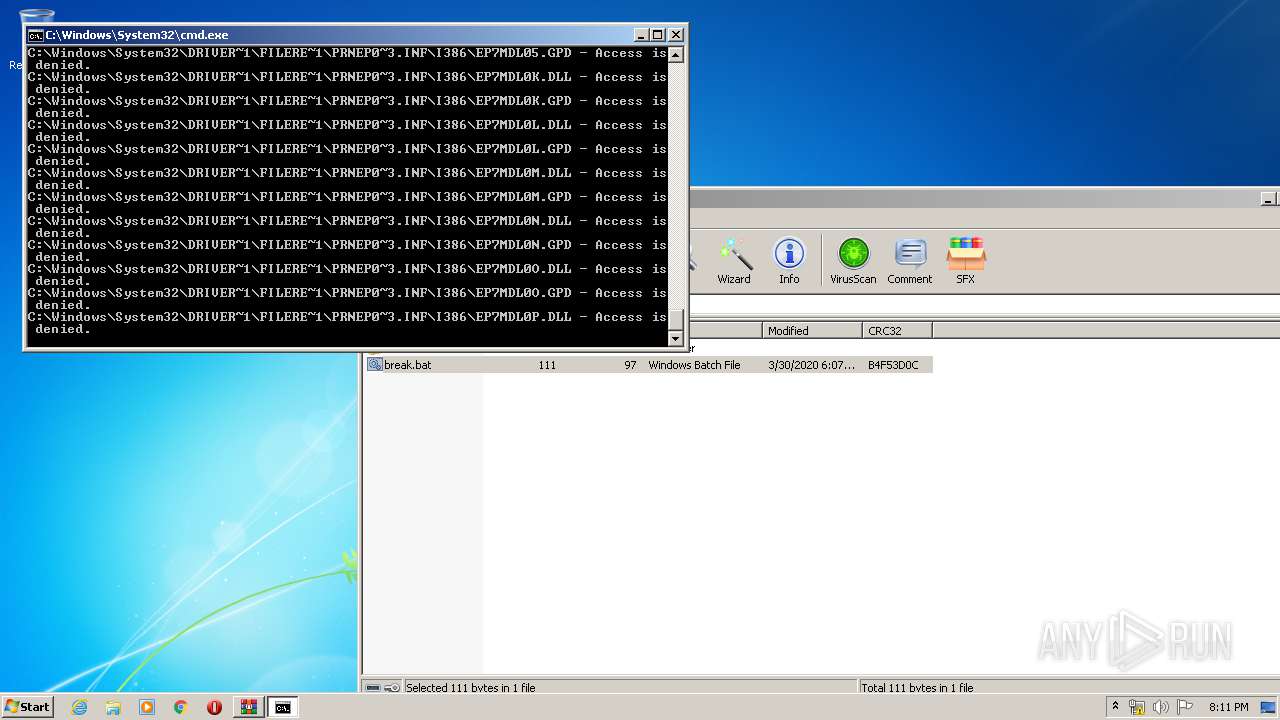
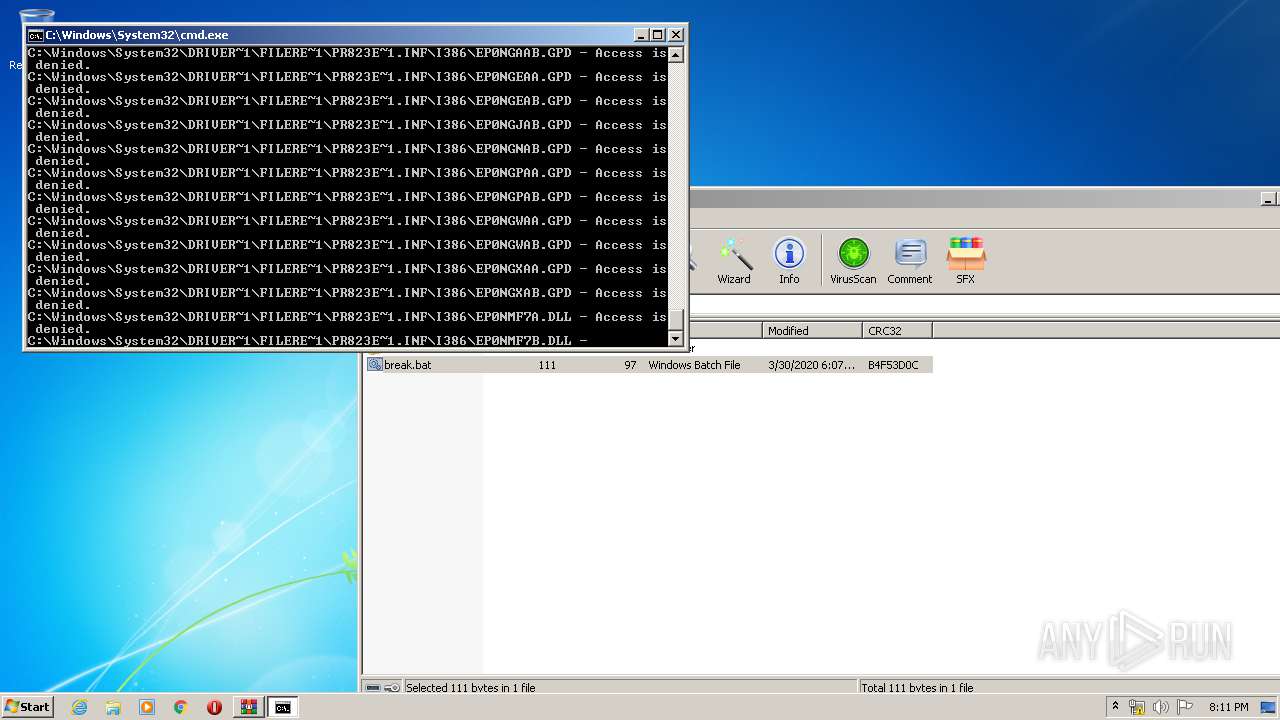
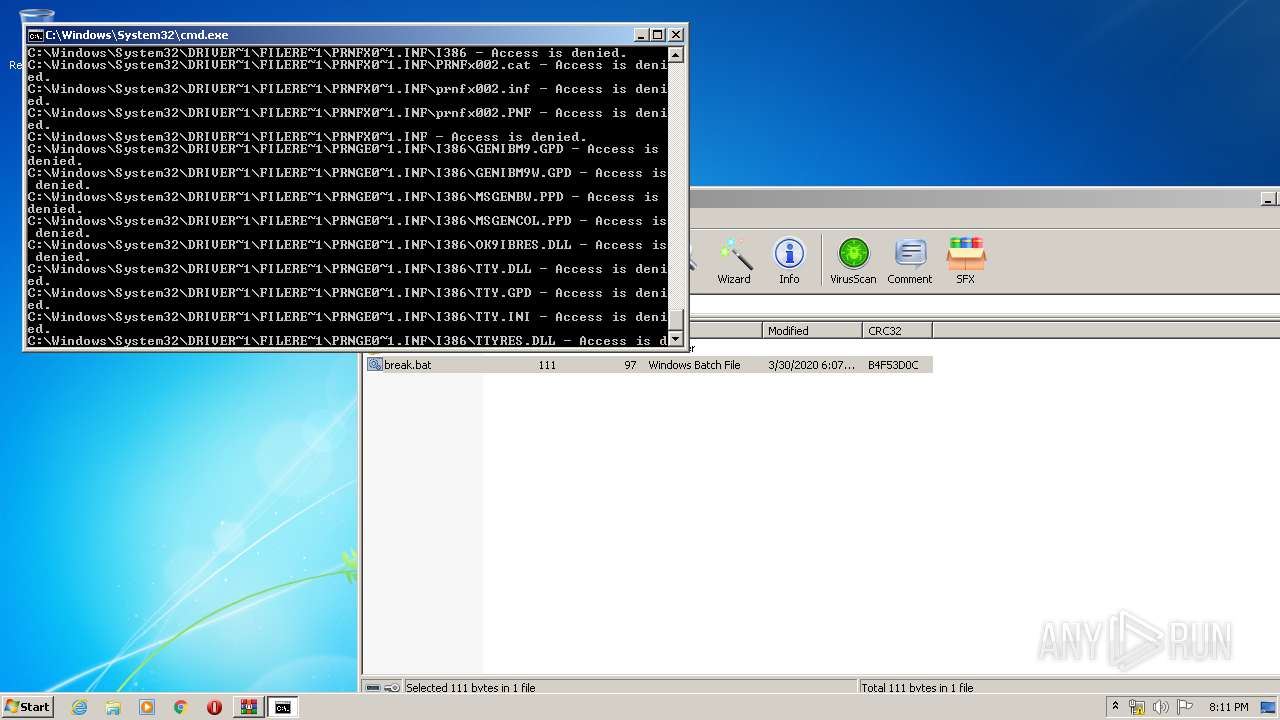
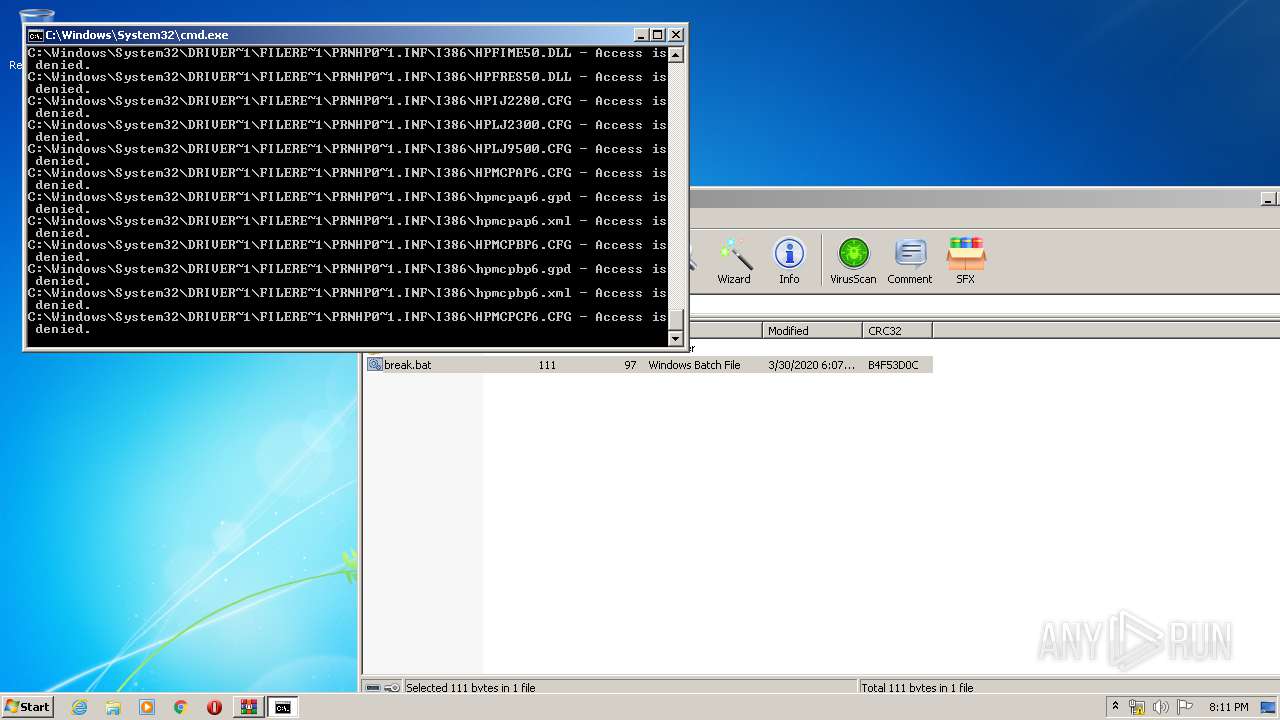
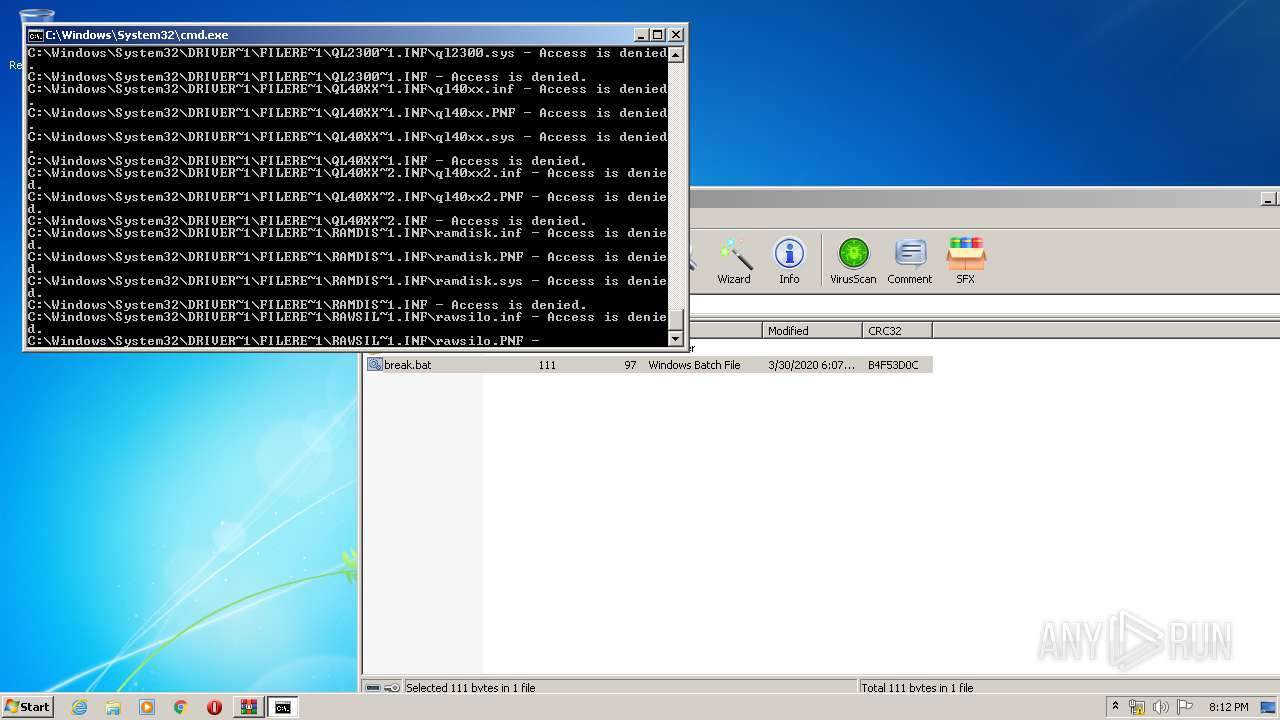
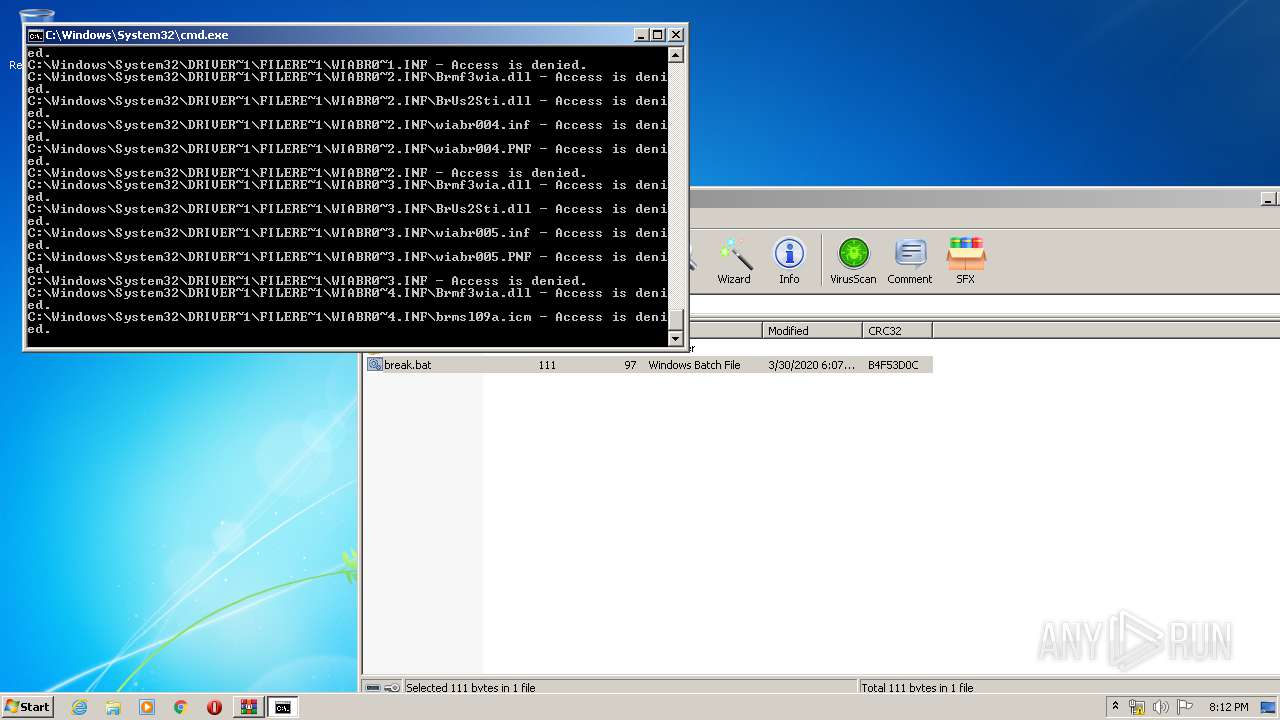
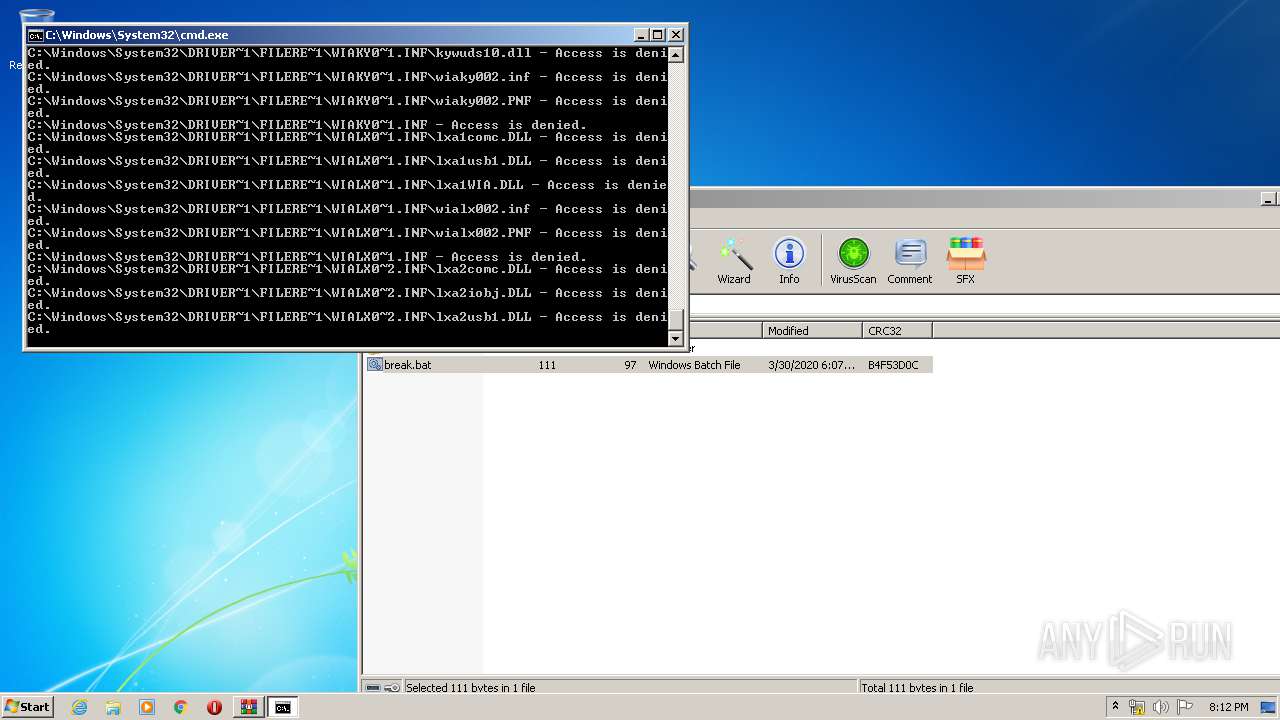
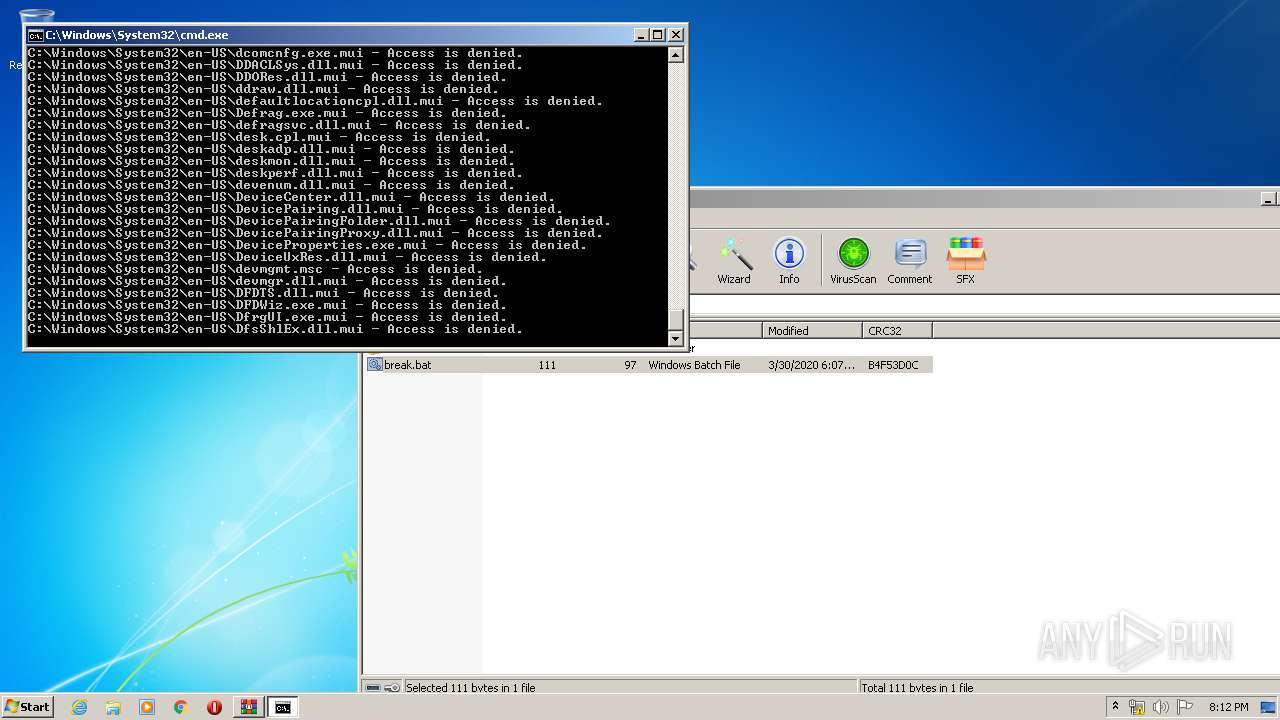
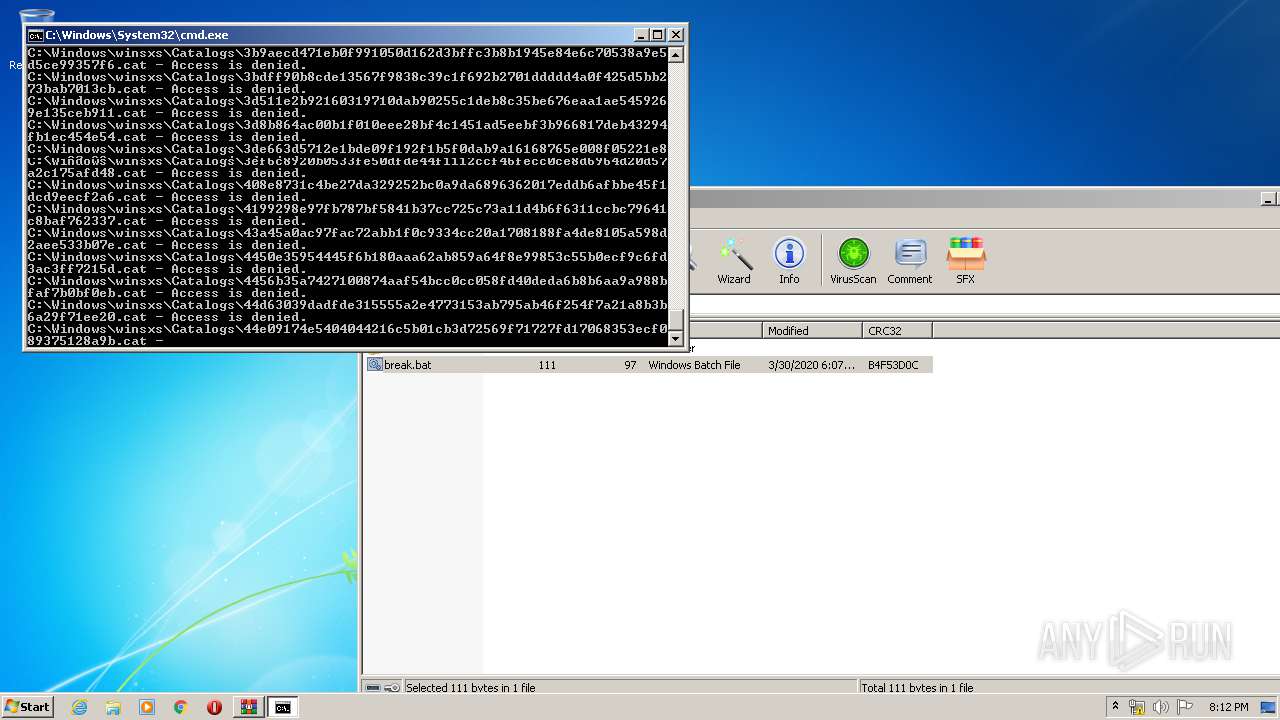
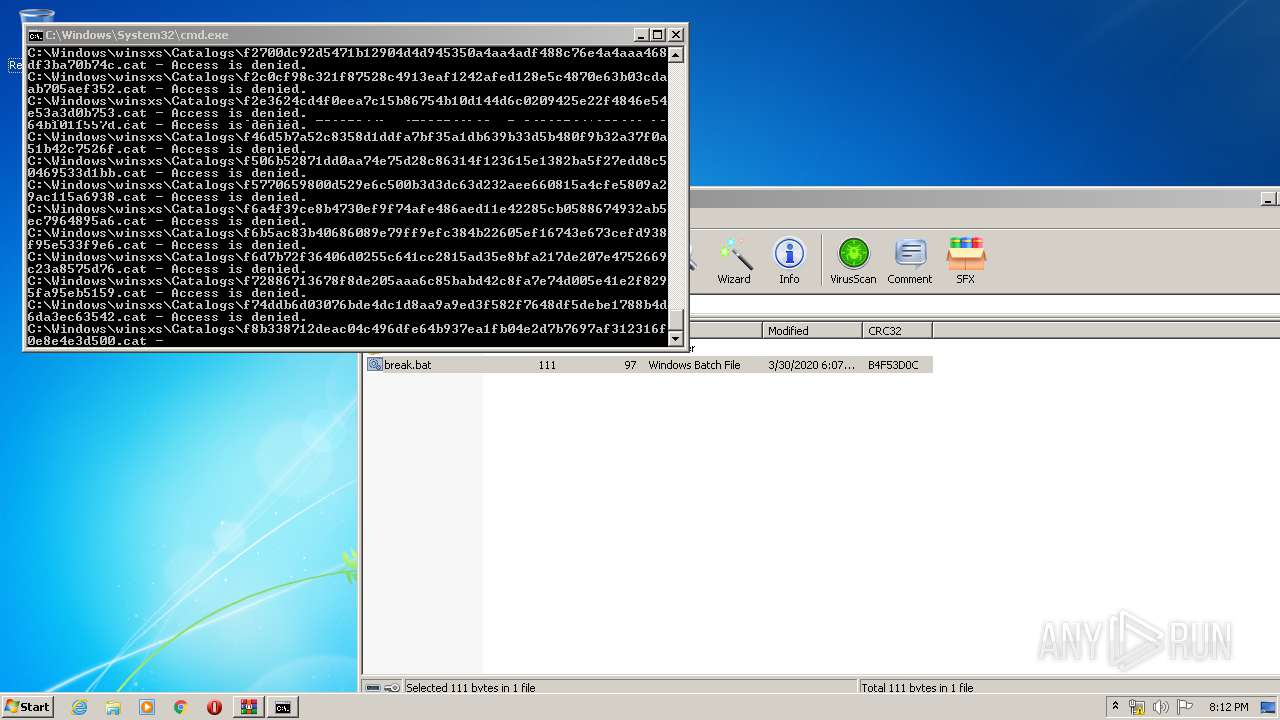
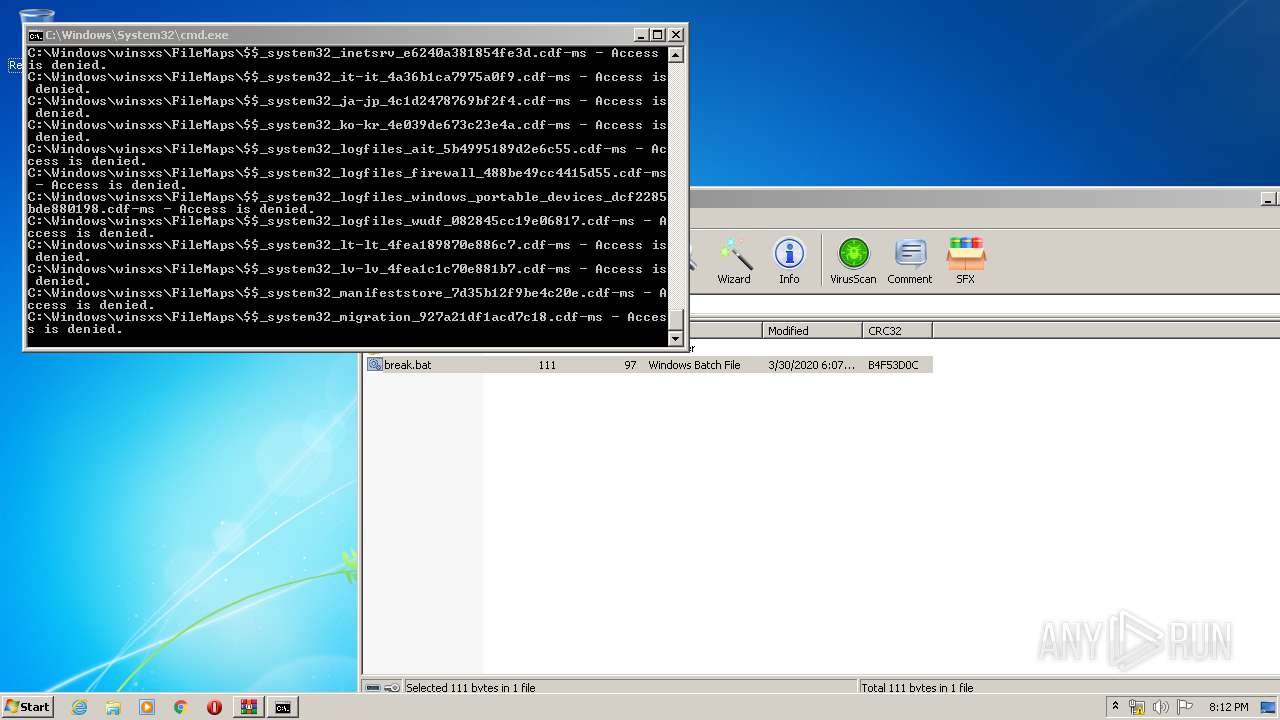
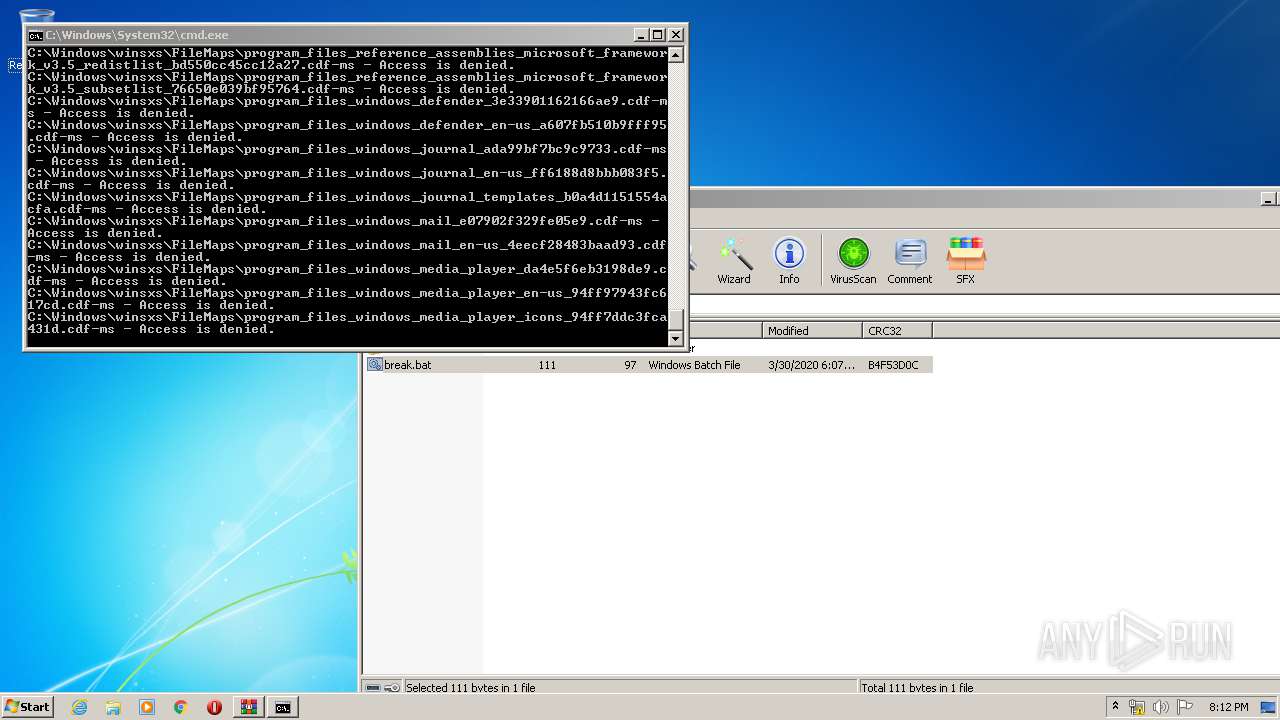
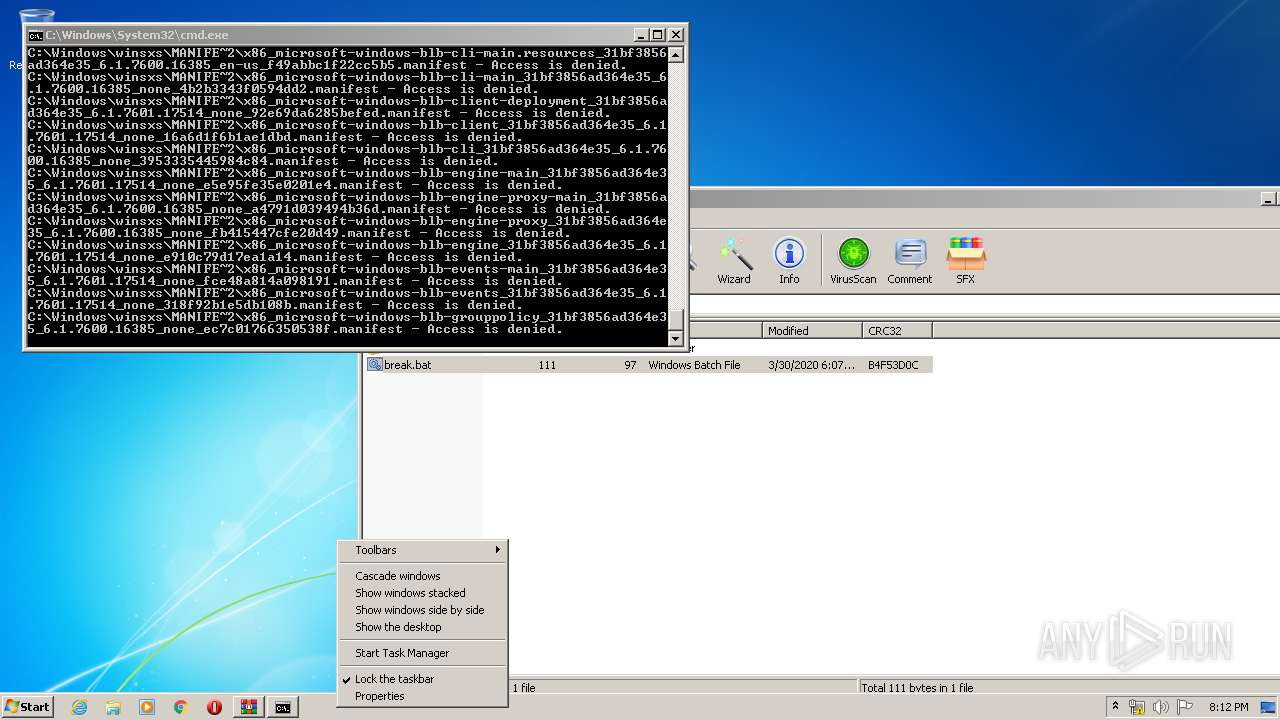
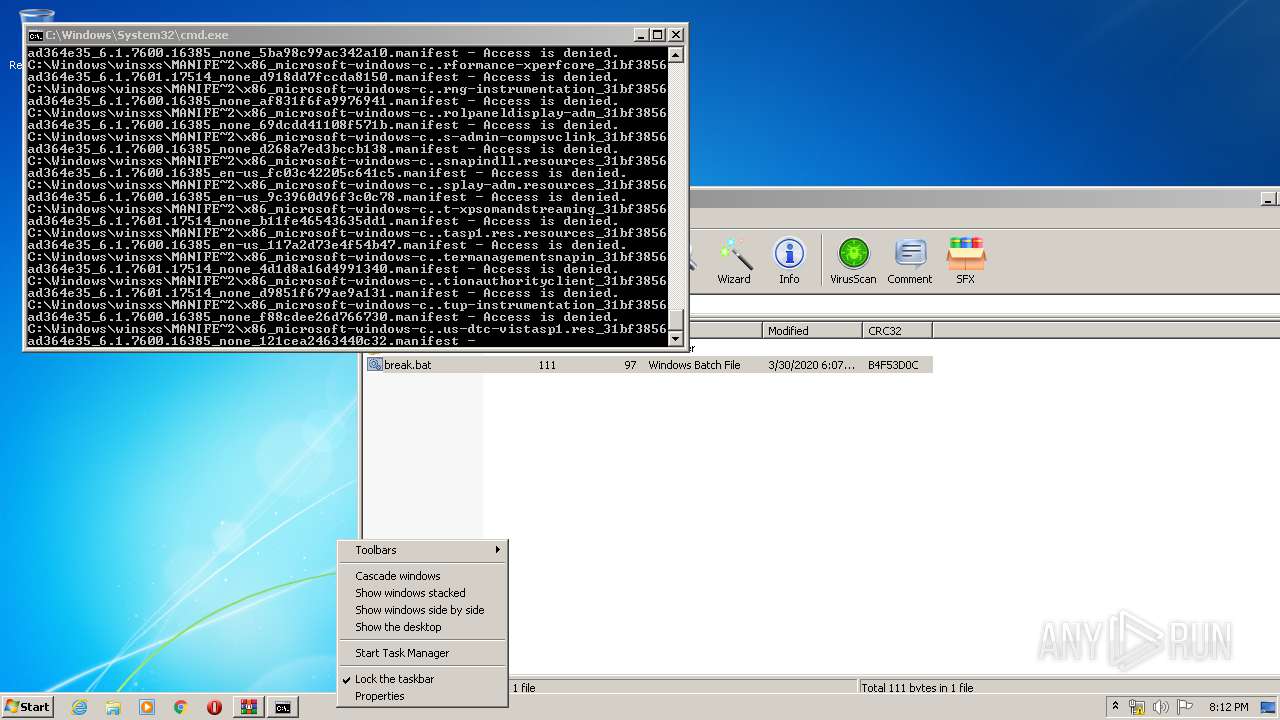
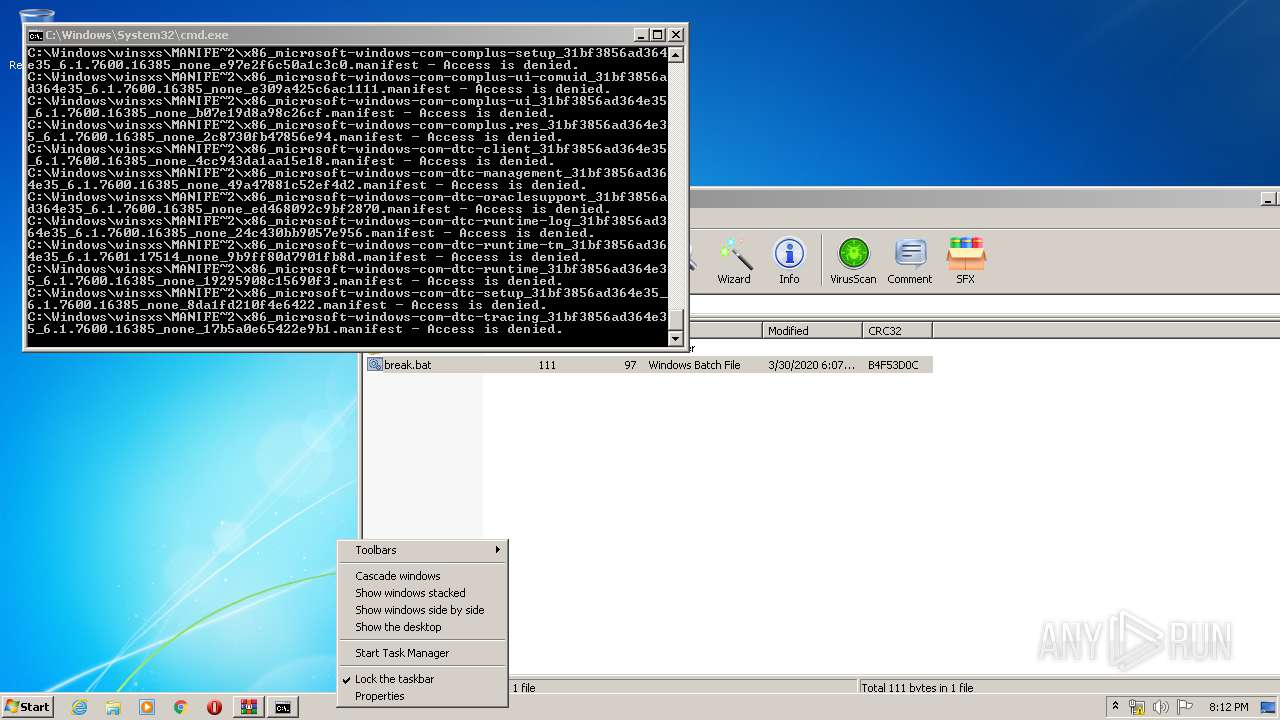
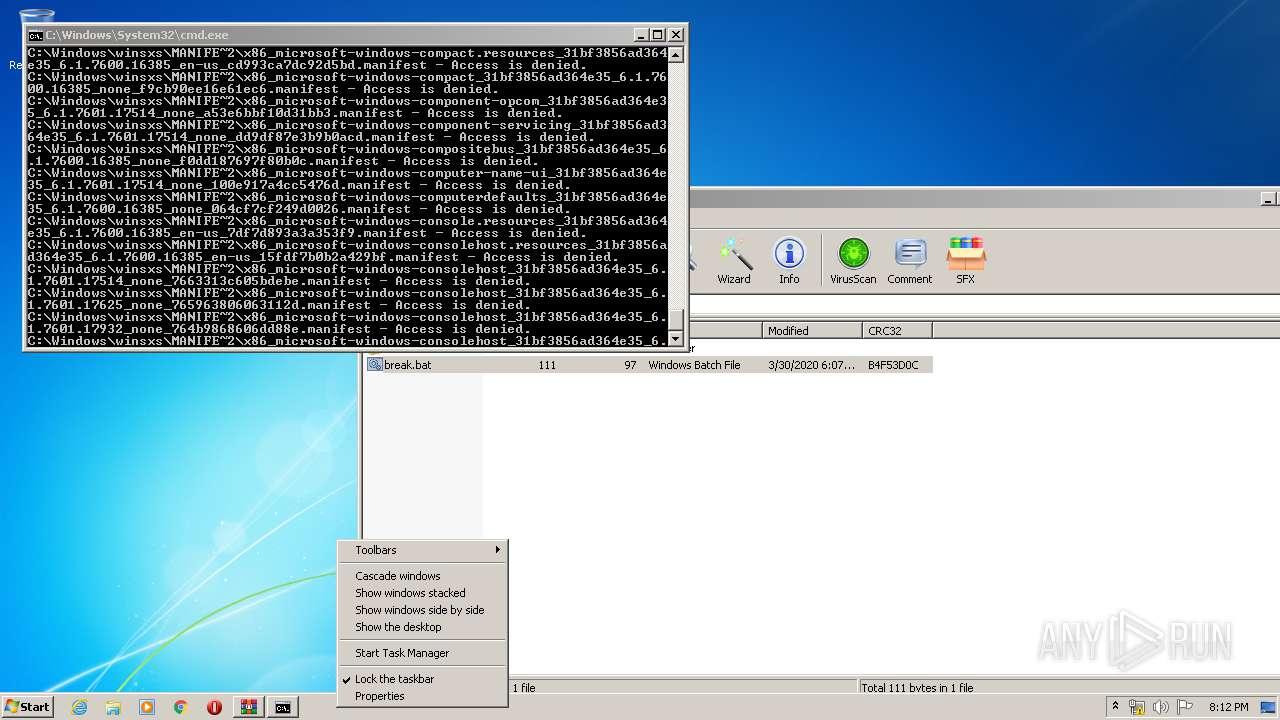
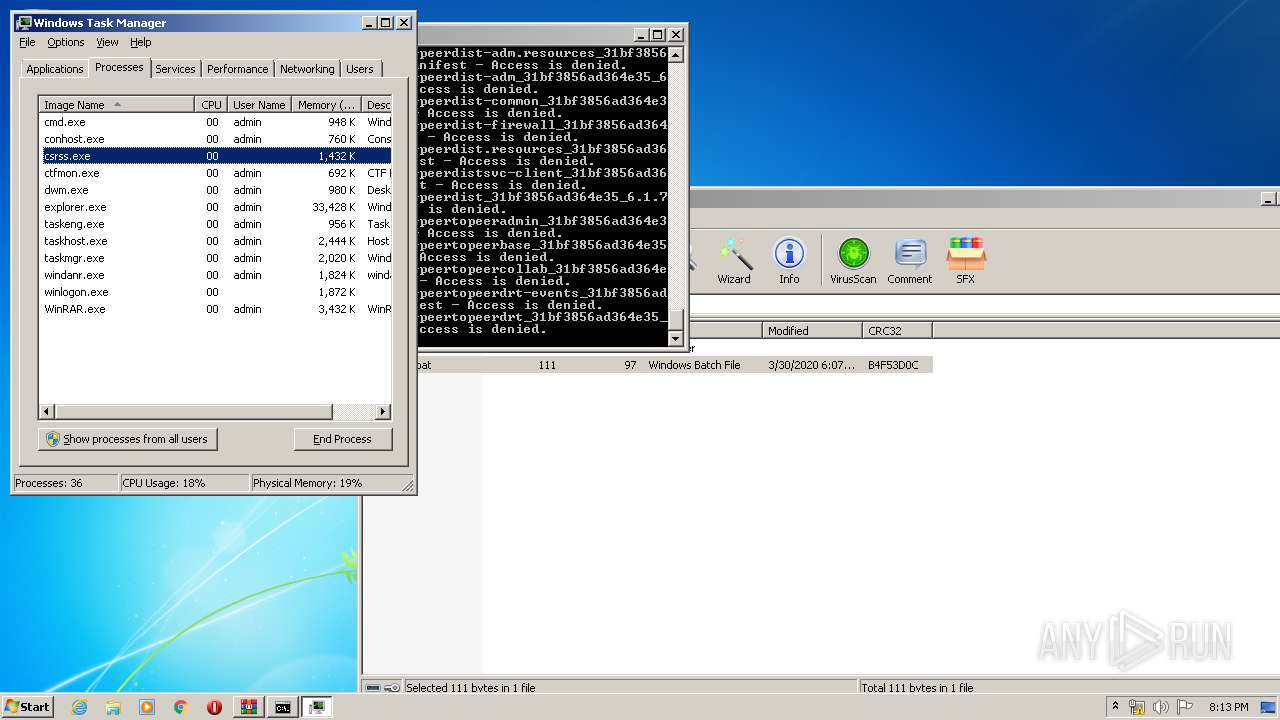
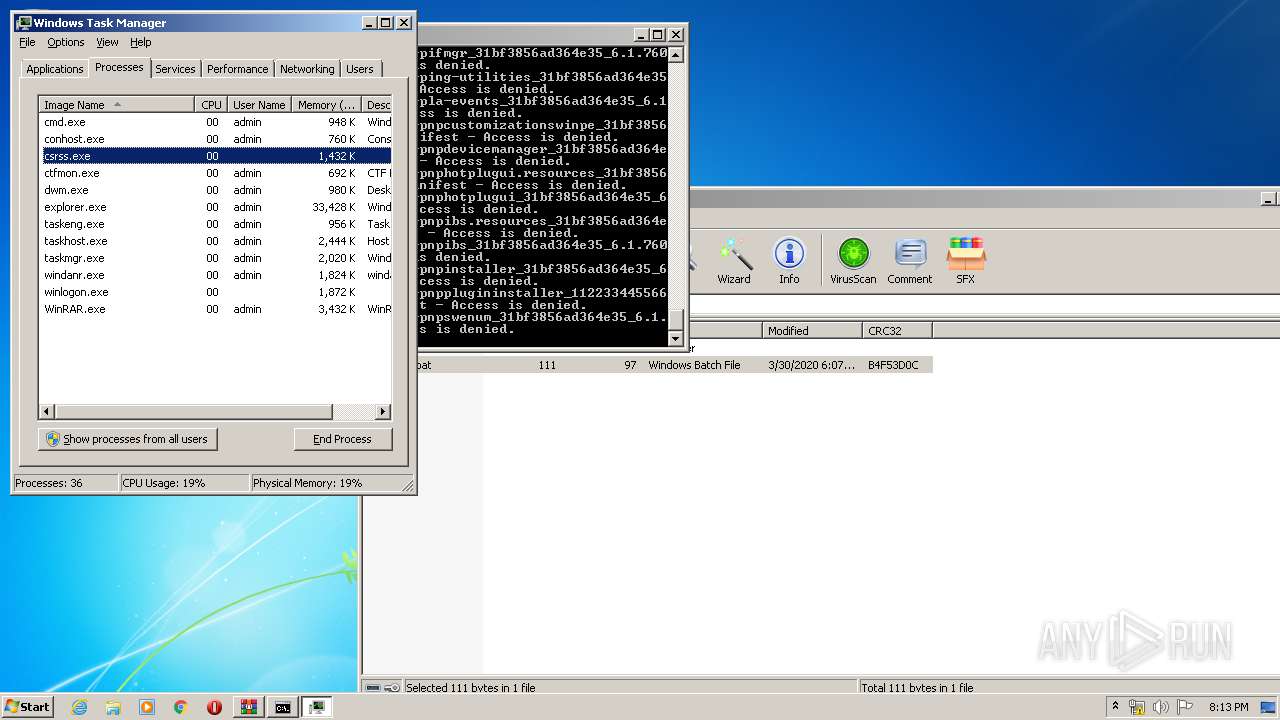
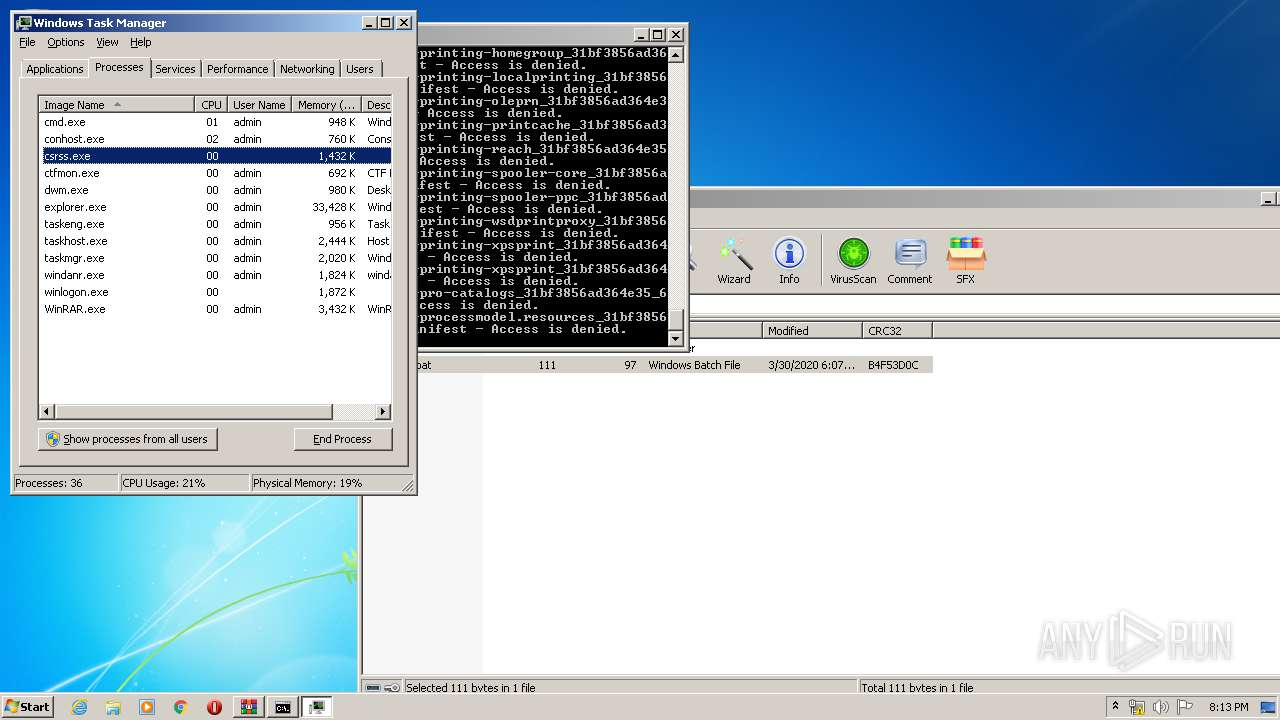
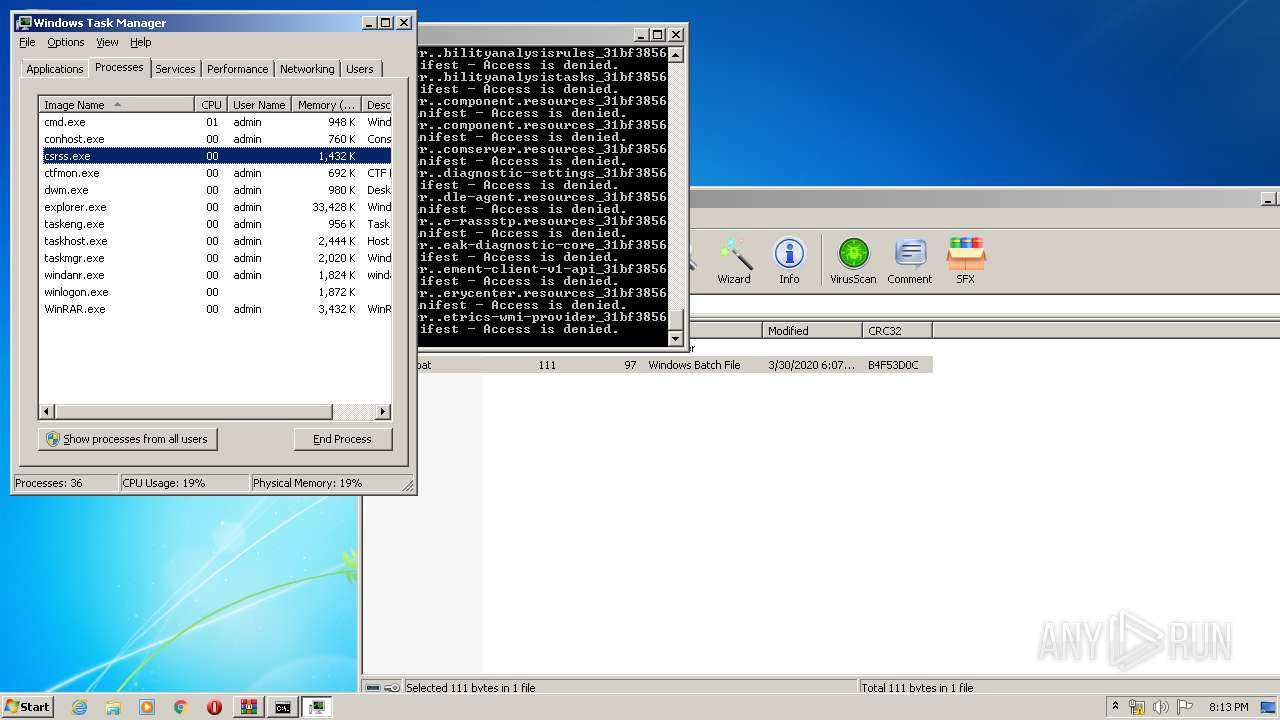
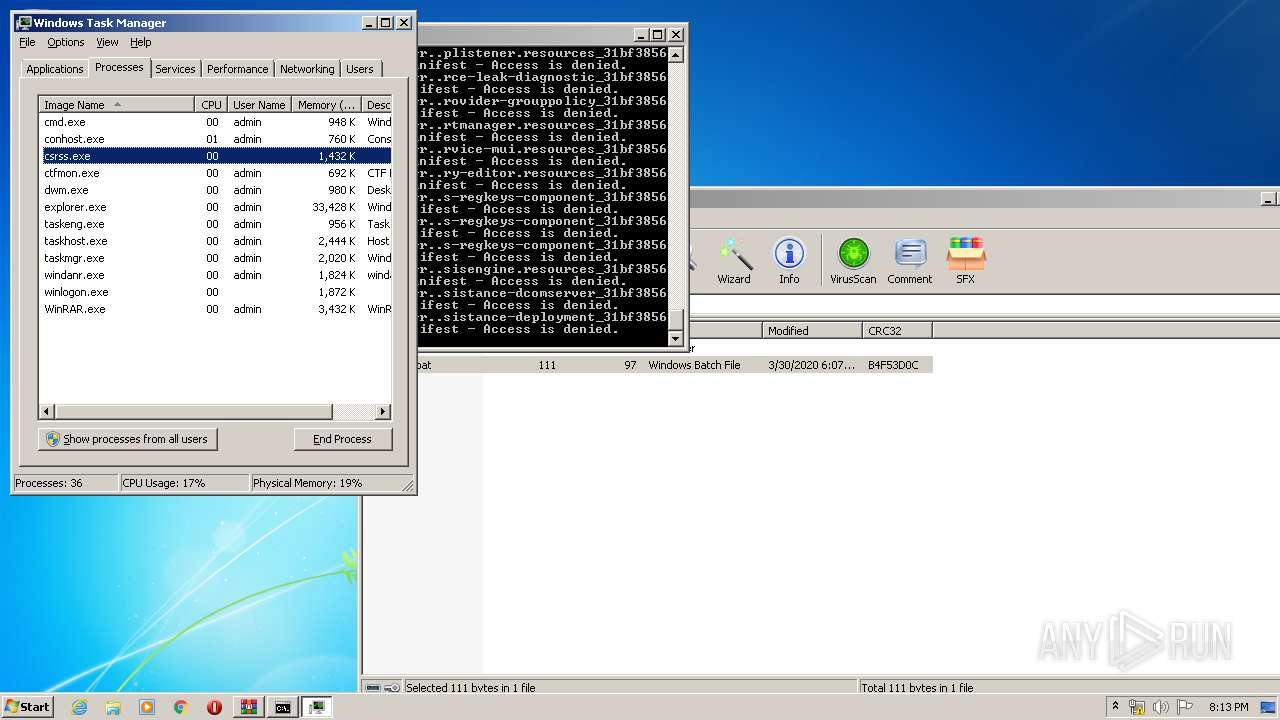
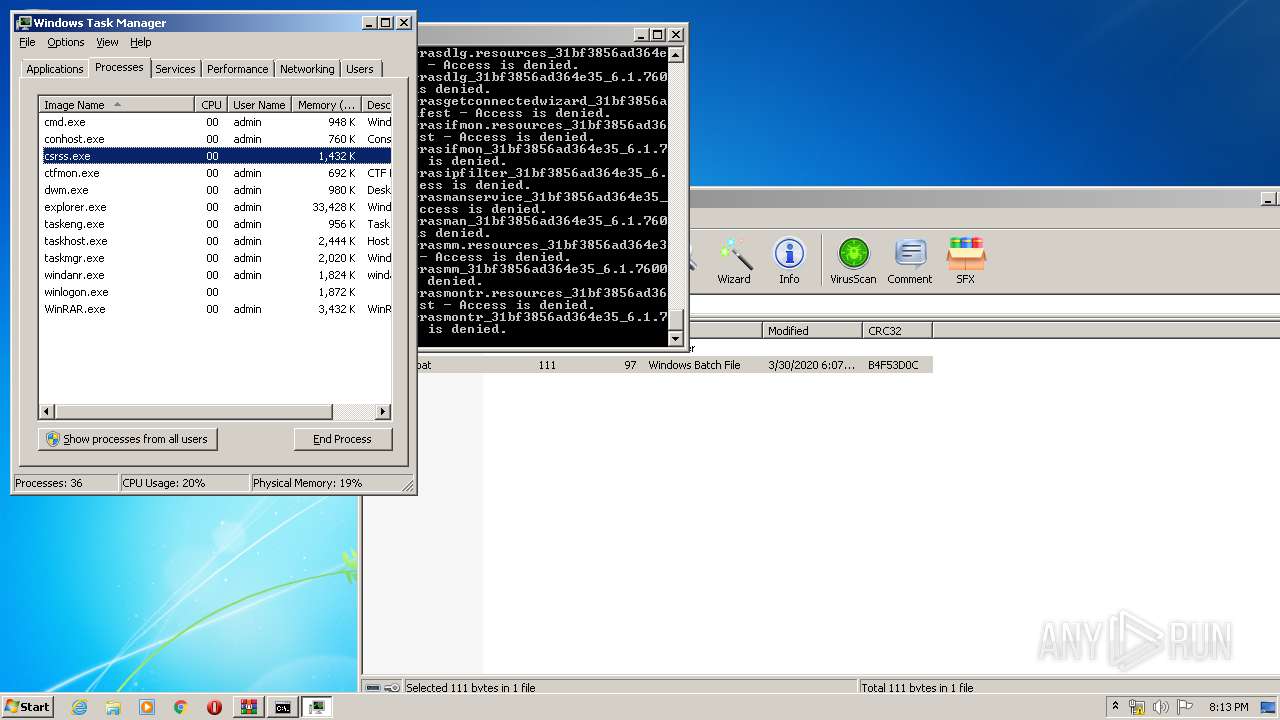
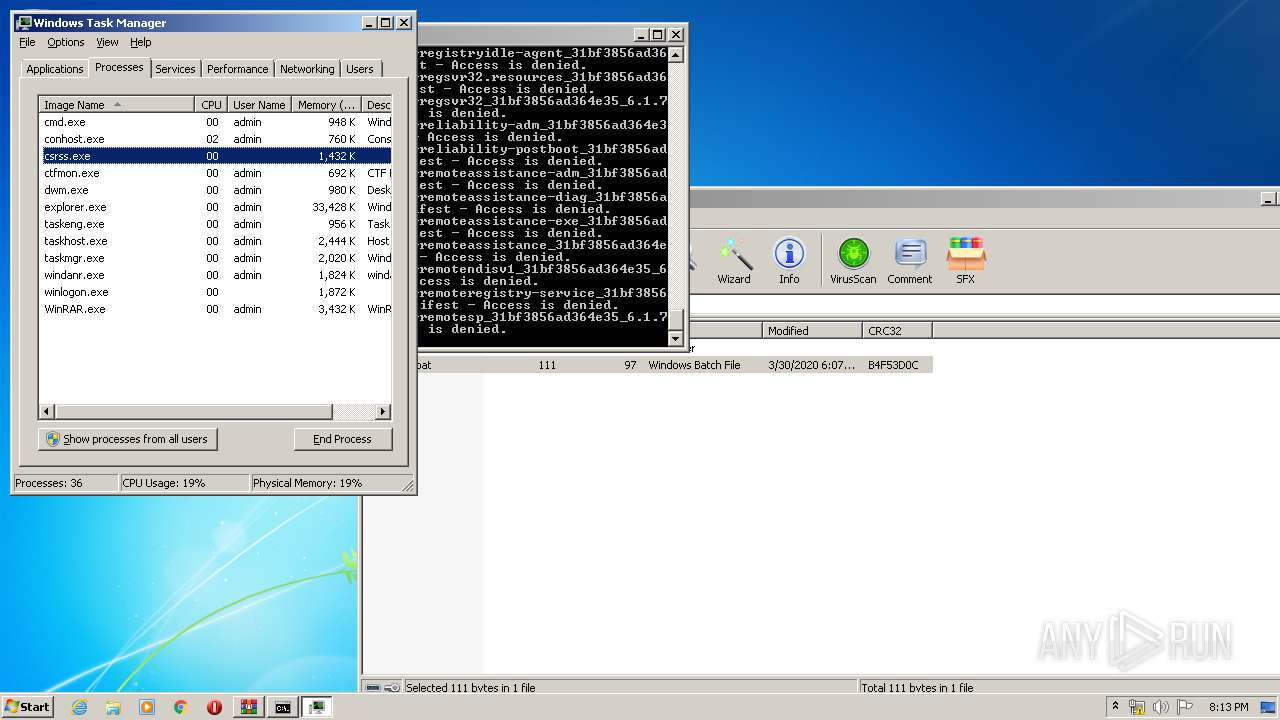
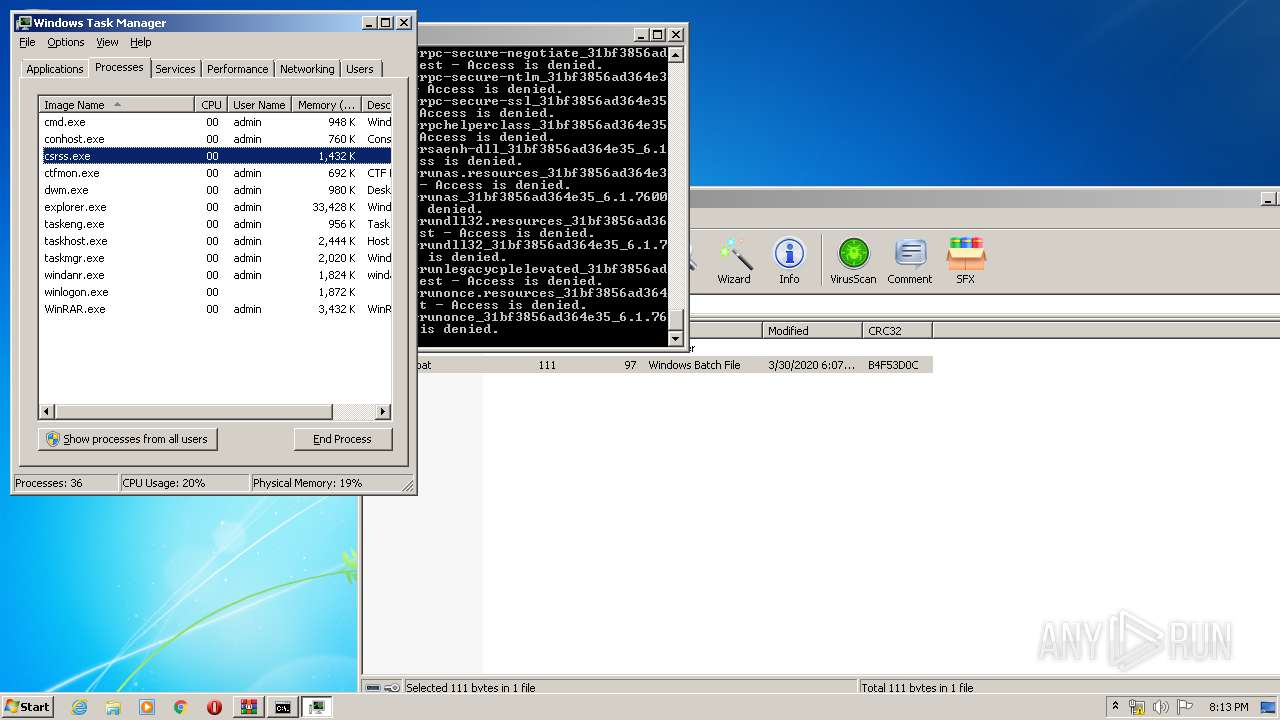
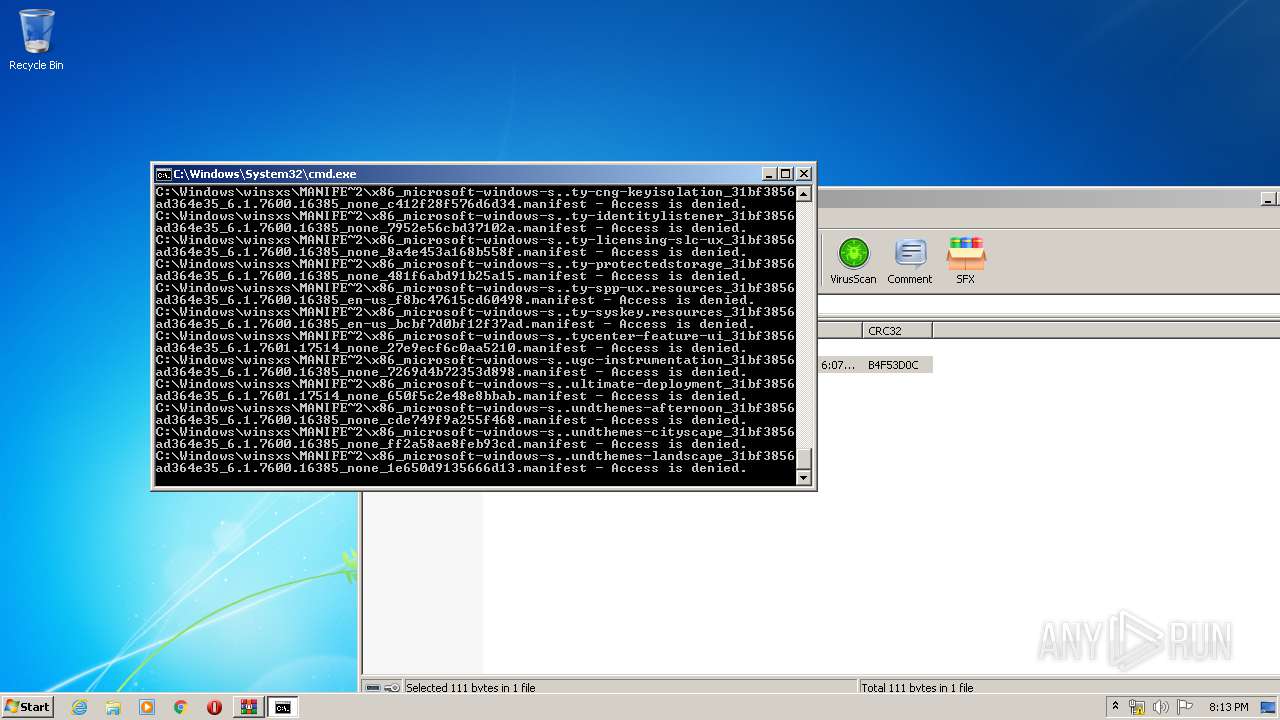
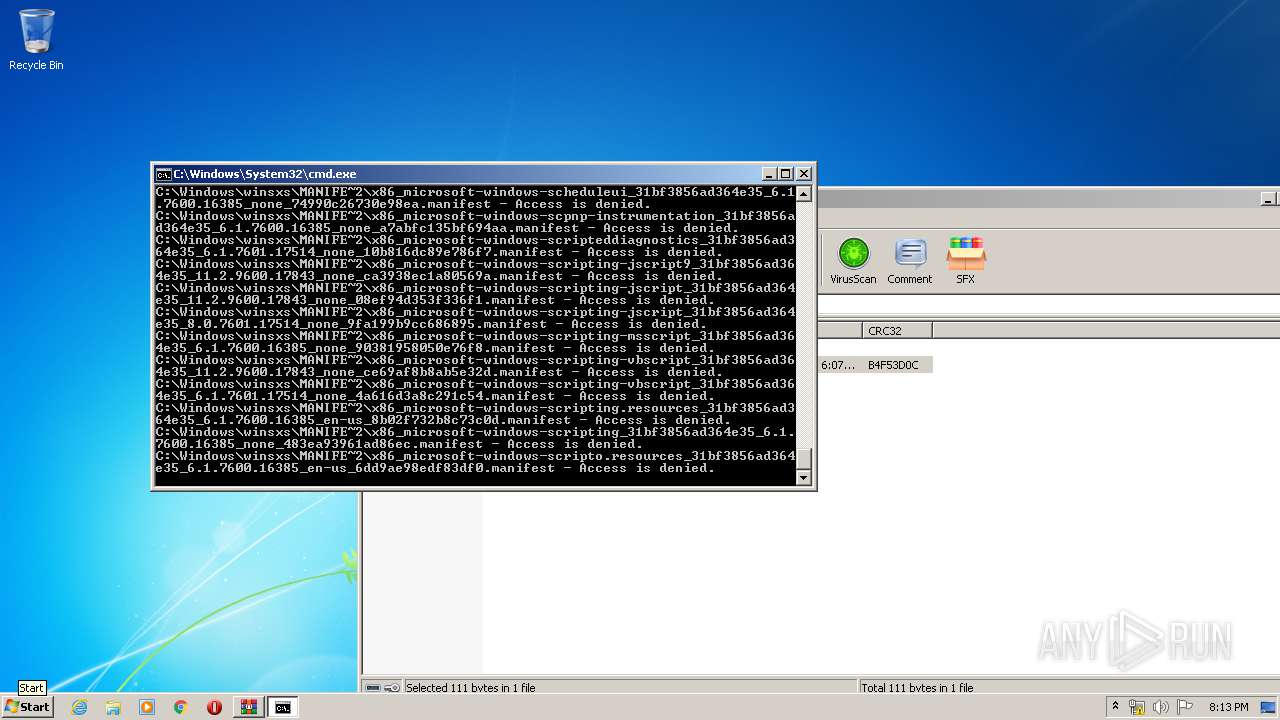
MALICIOUS
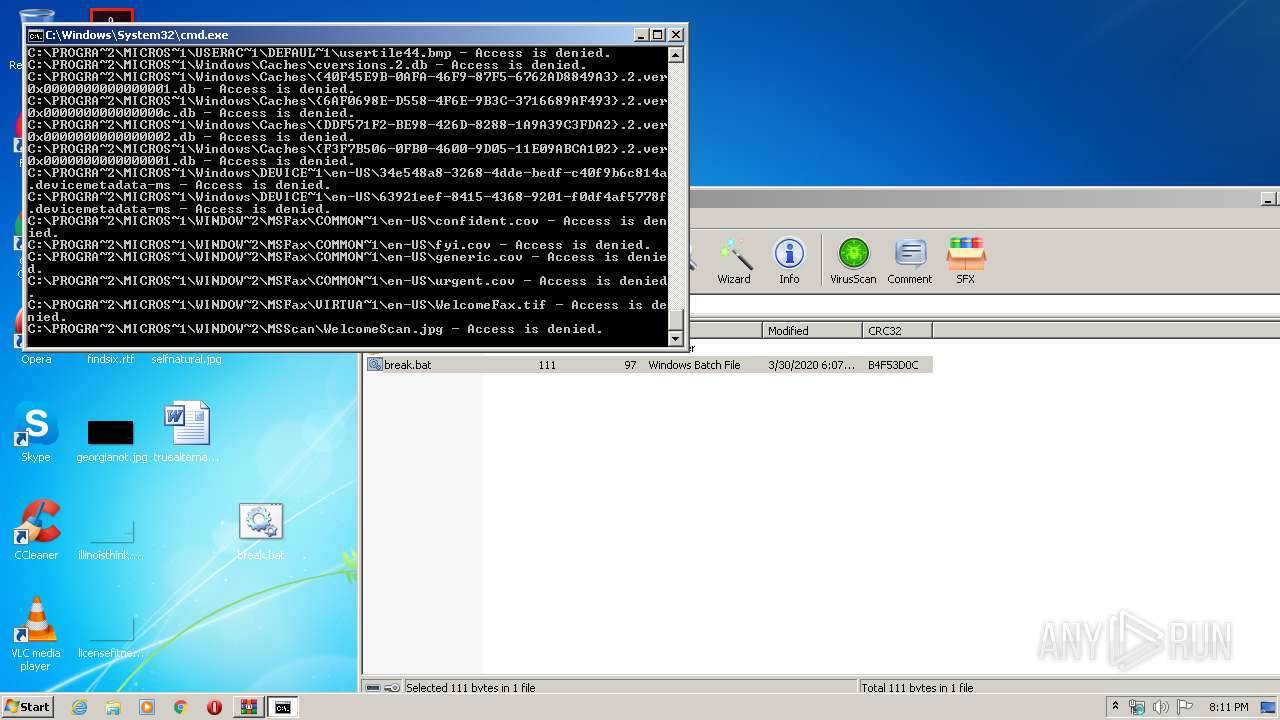
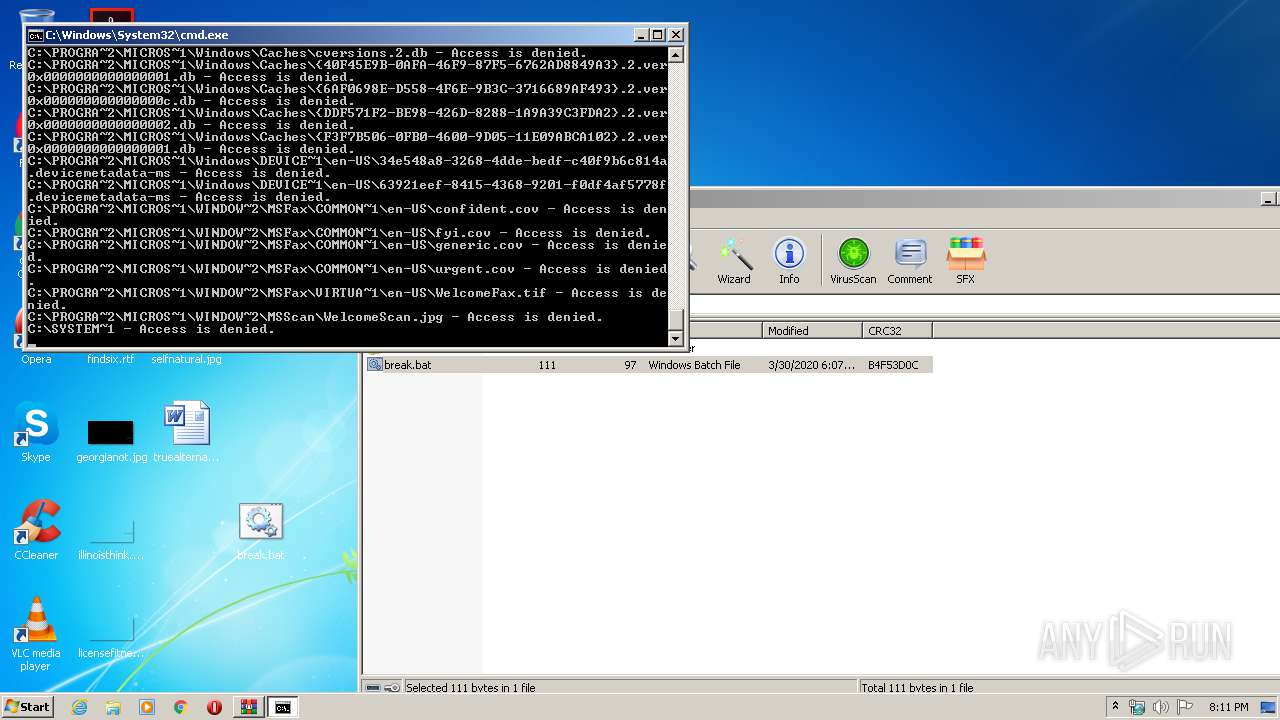
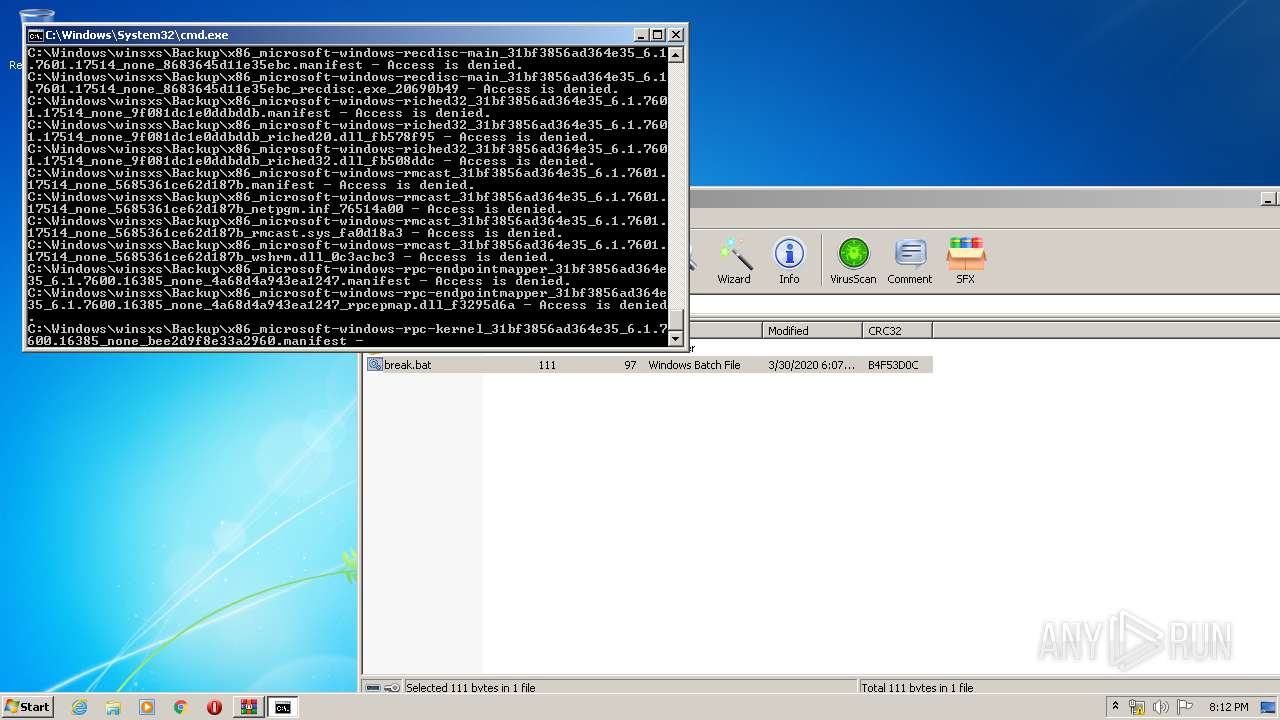
Actions looks like stealing of personal data
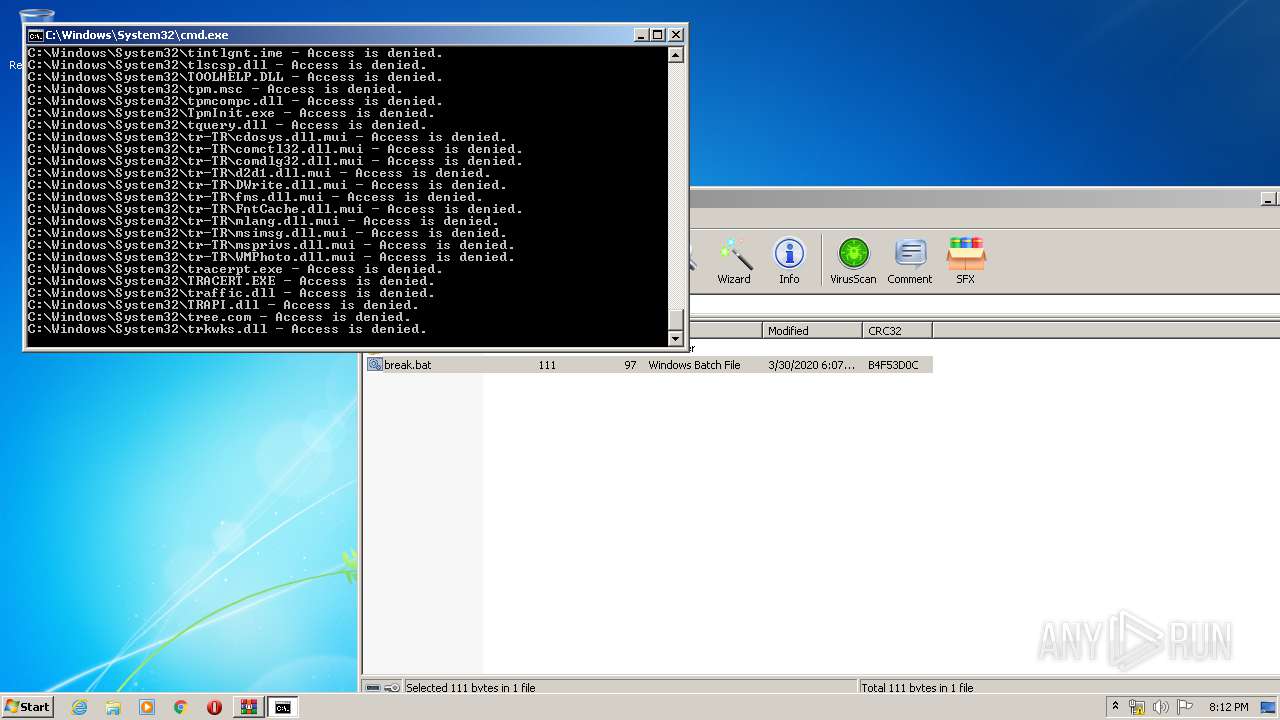
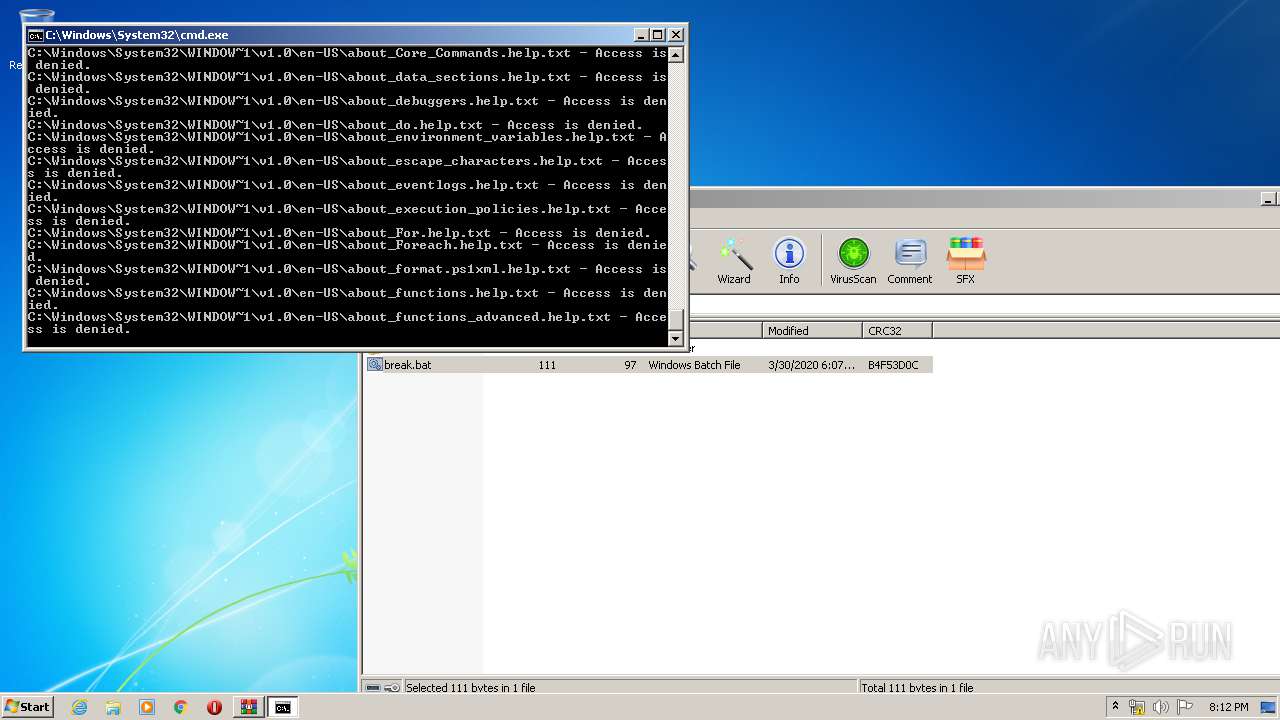
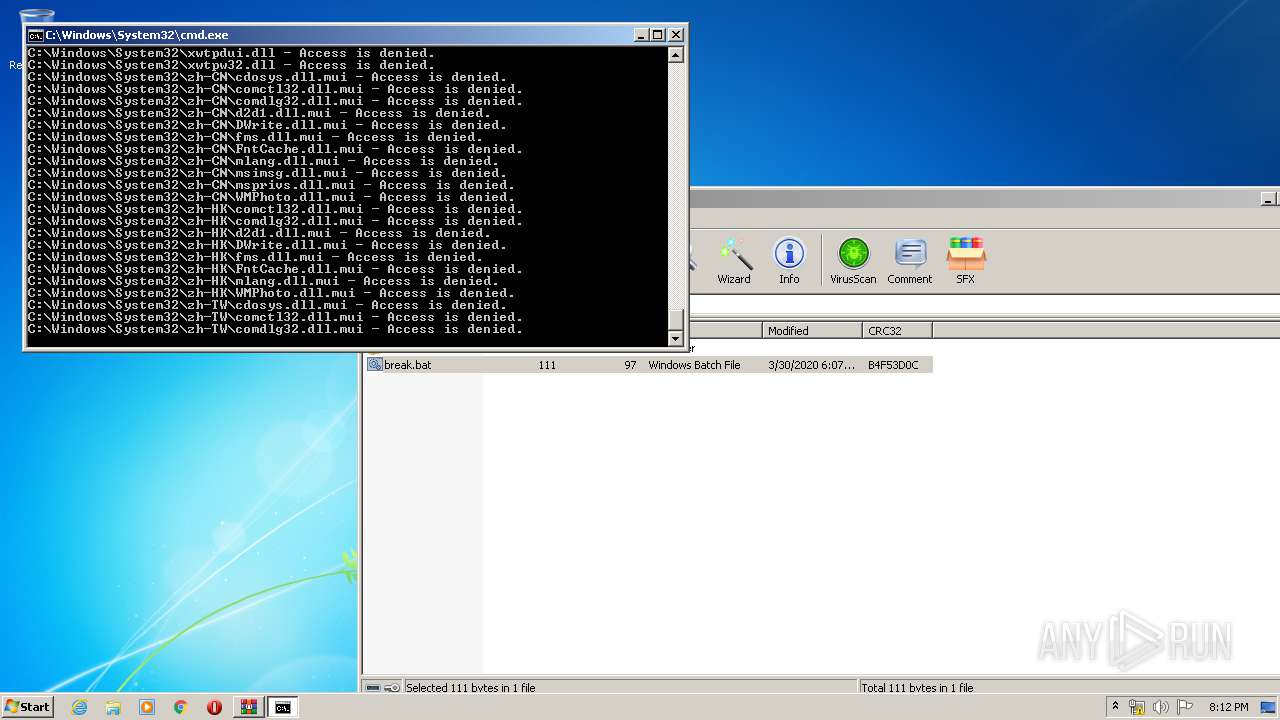
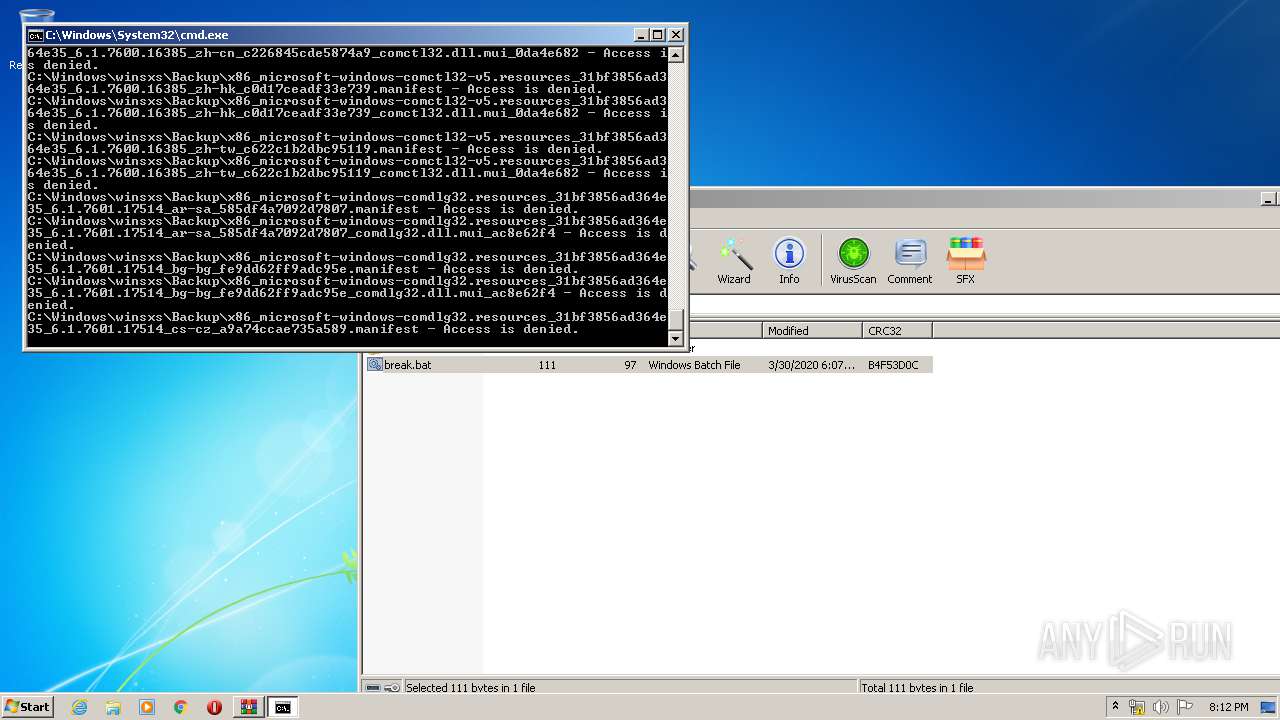
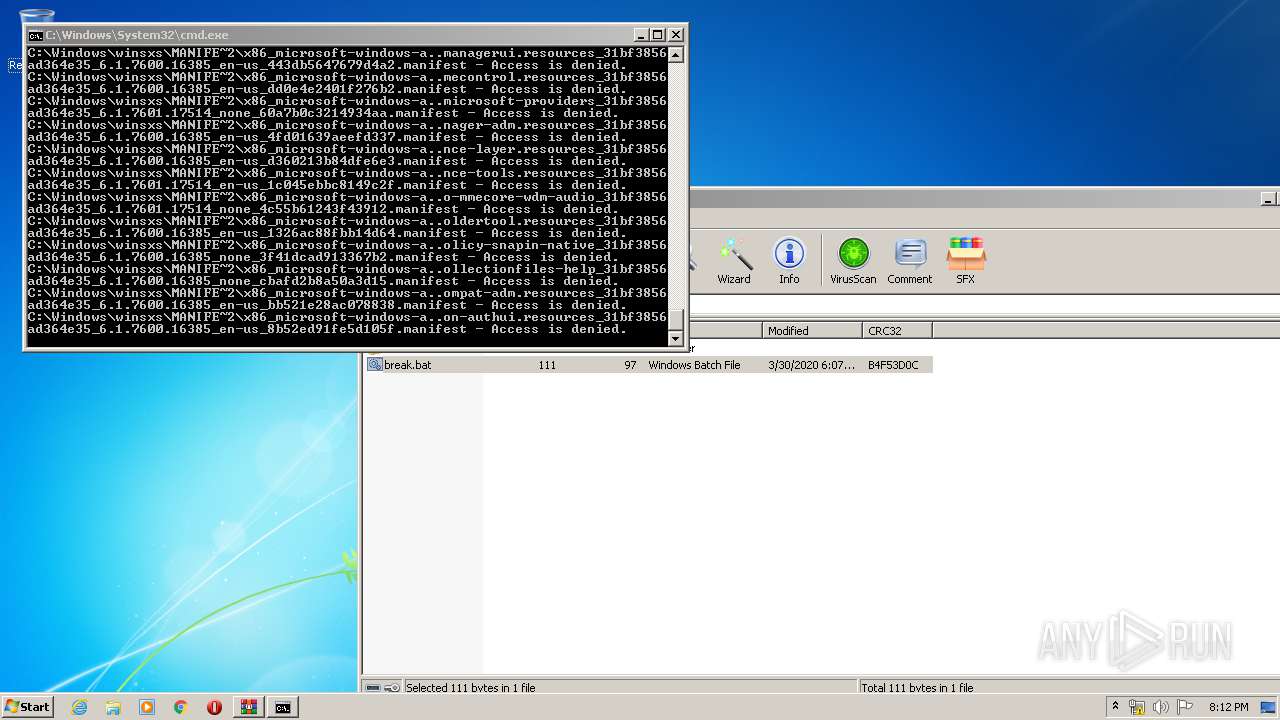
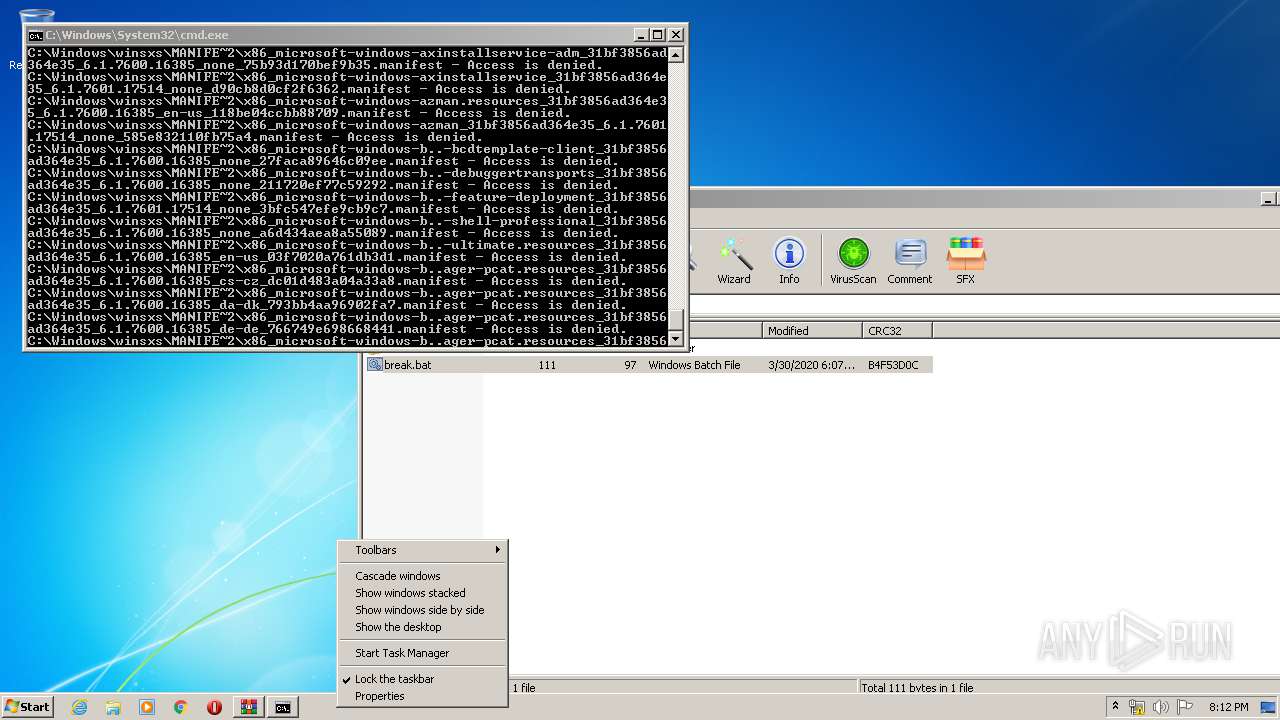
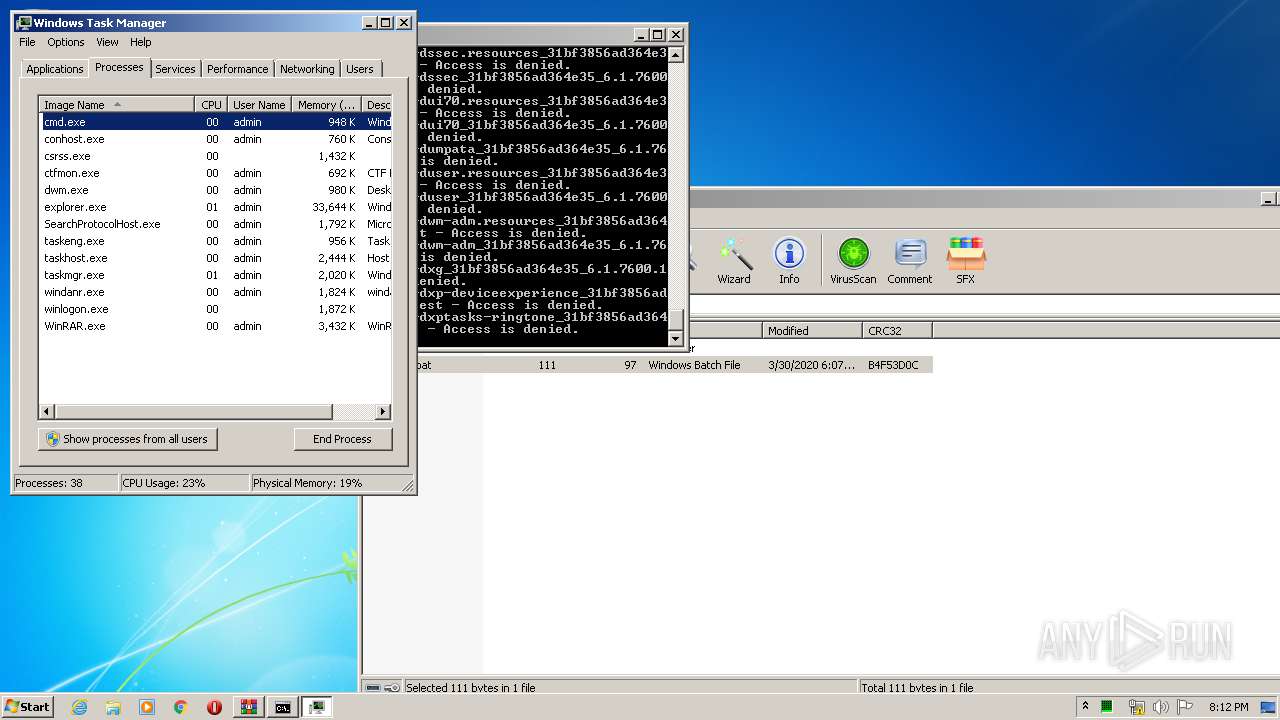
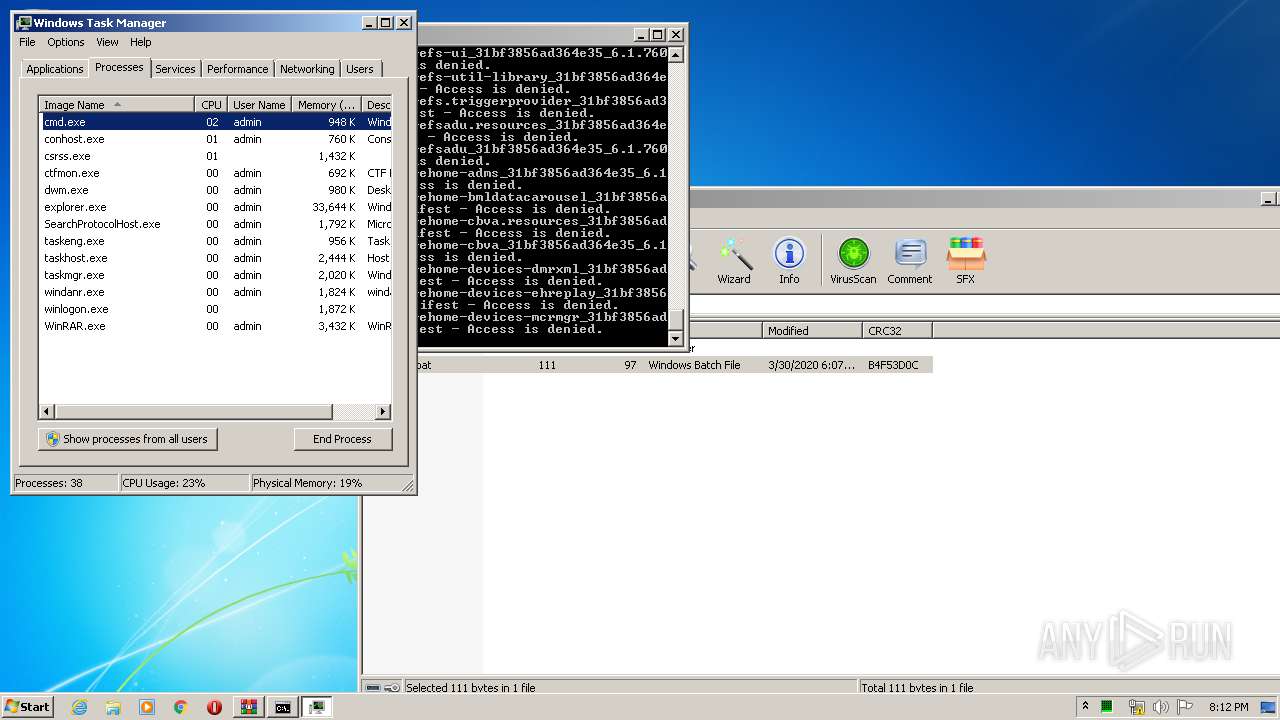
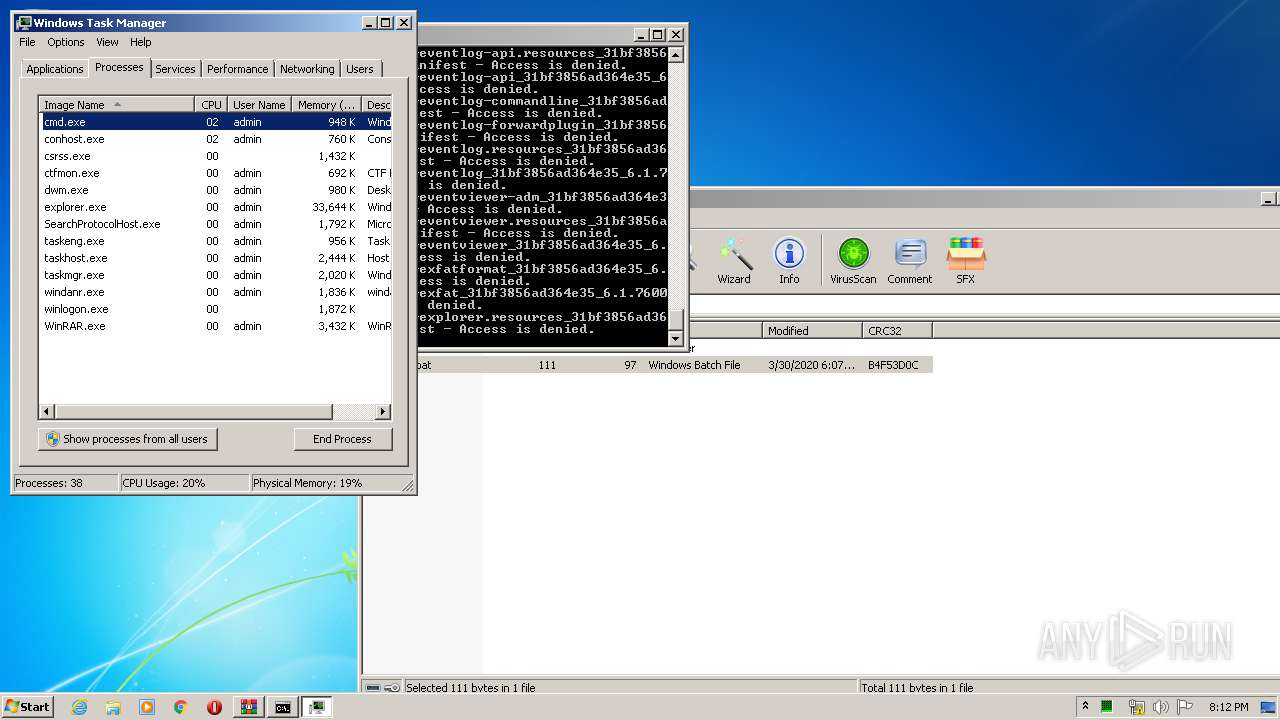
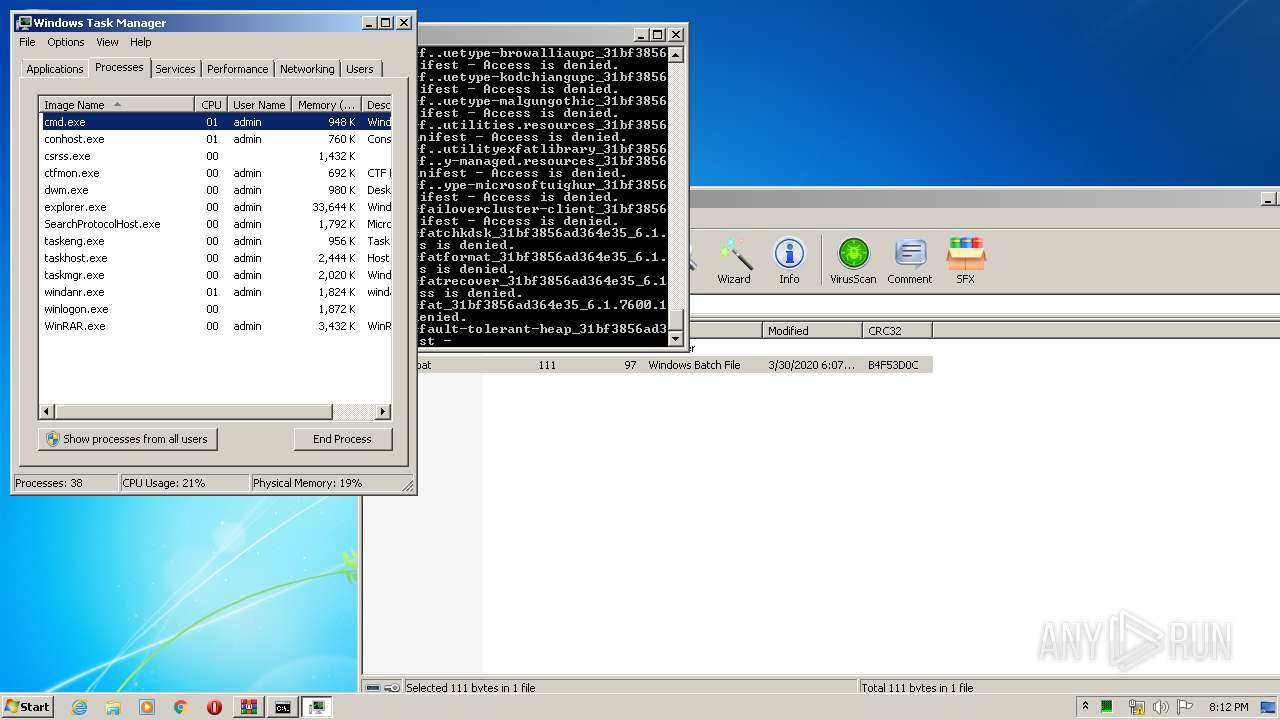
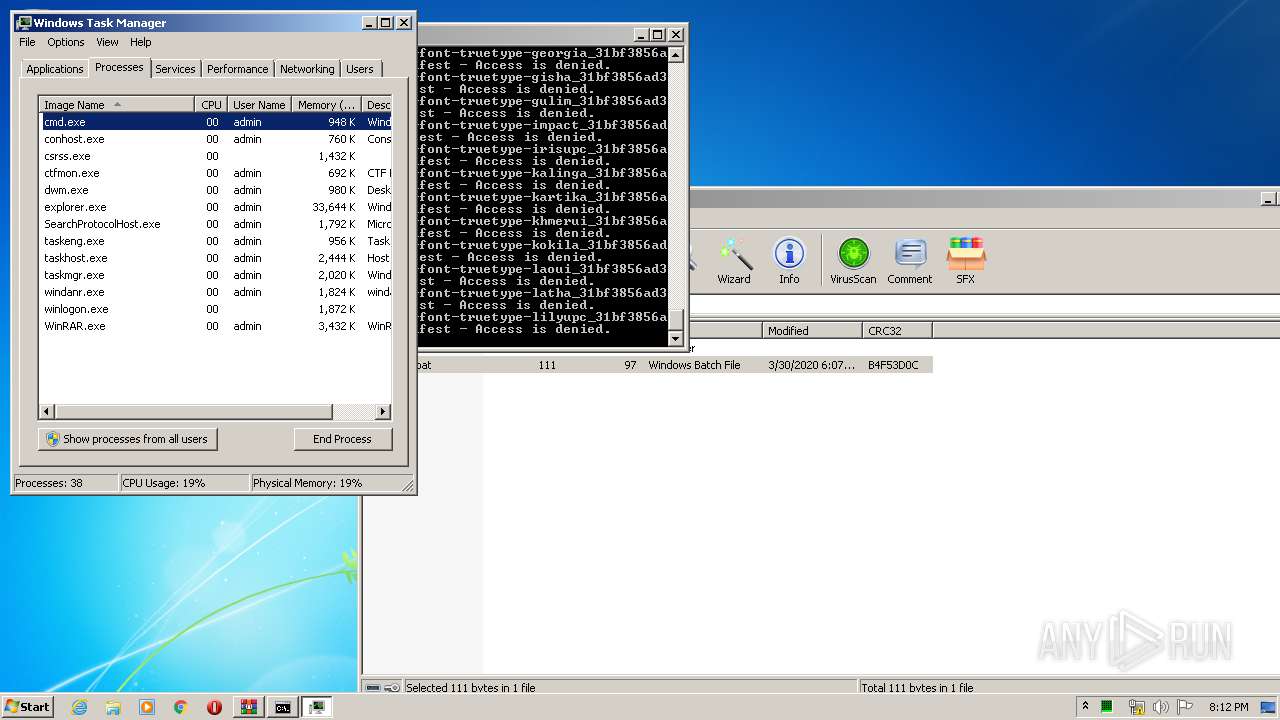
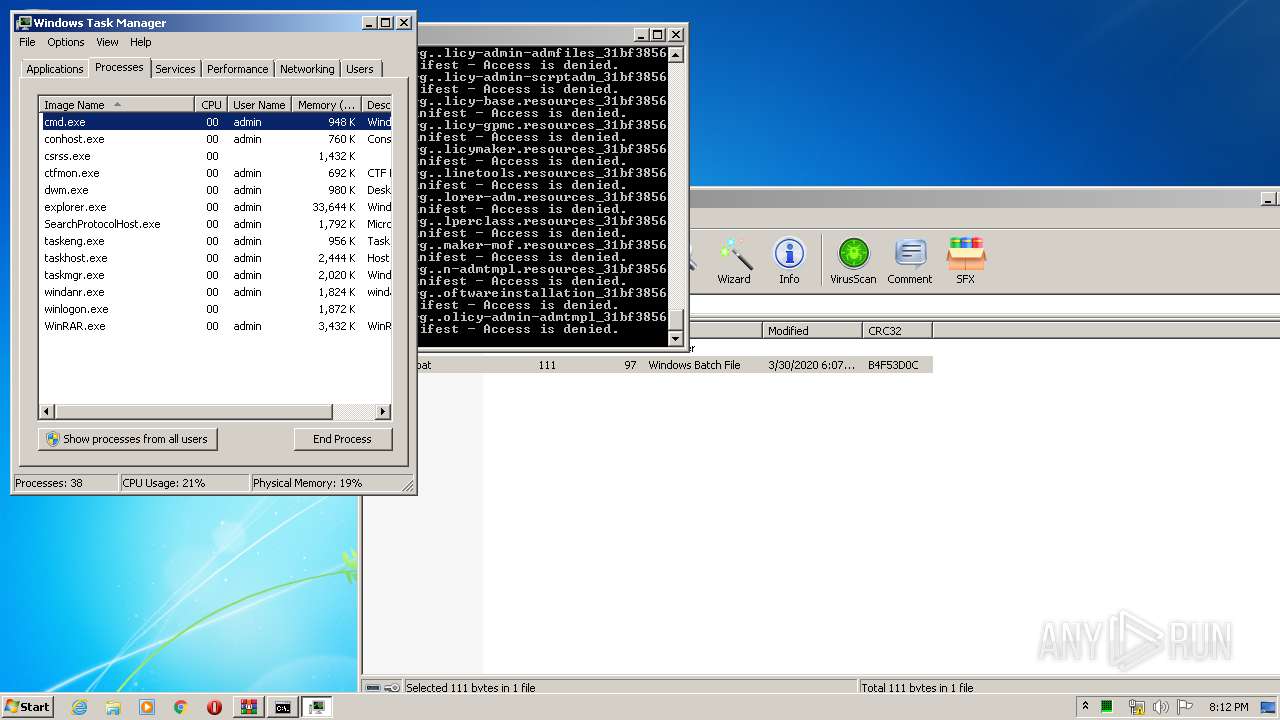
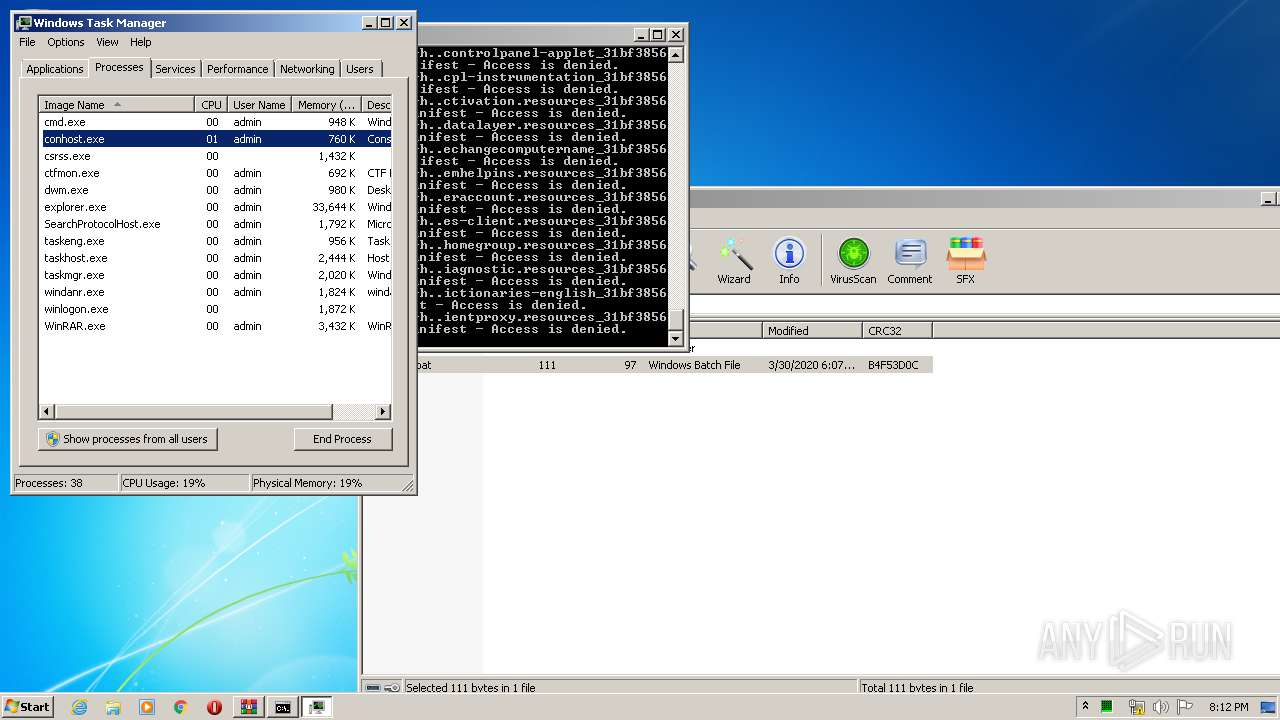
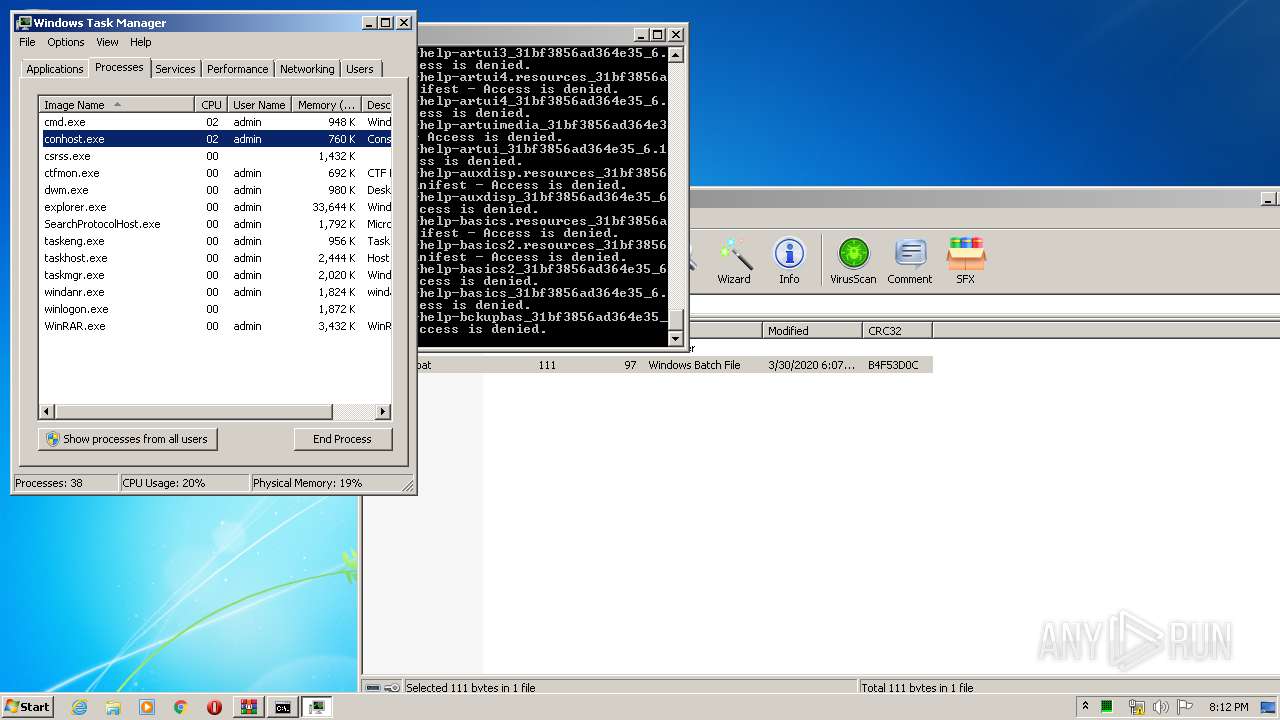
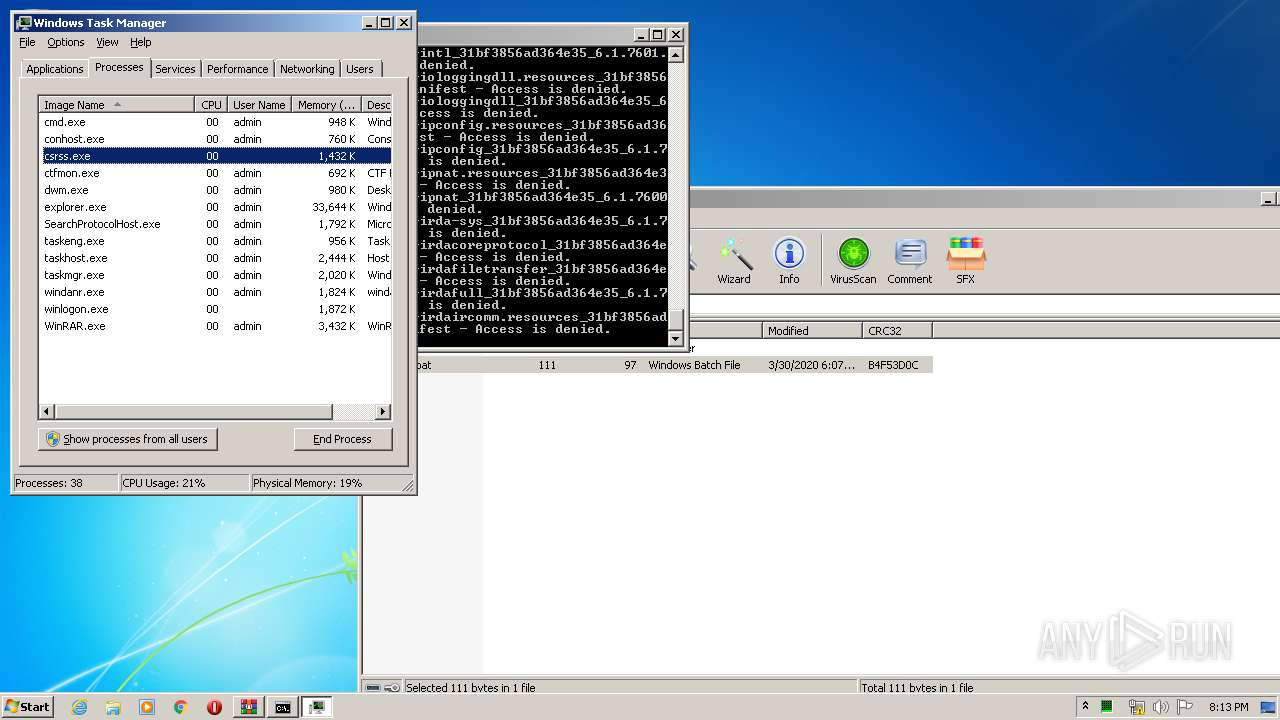
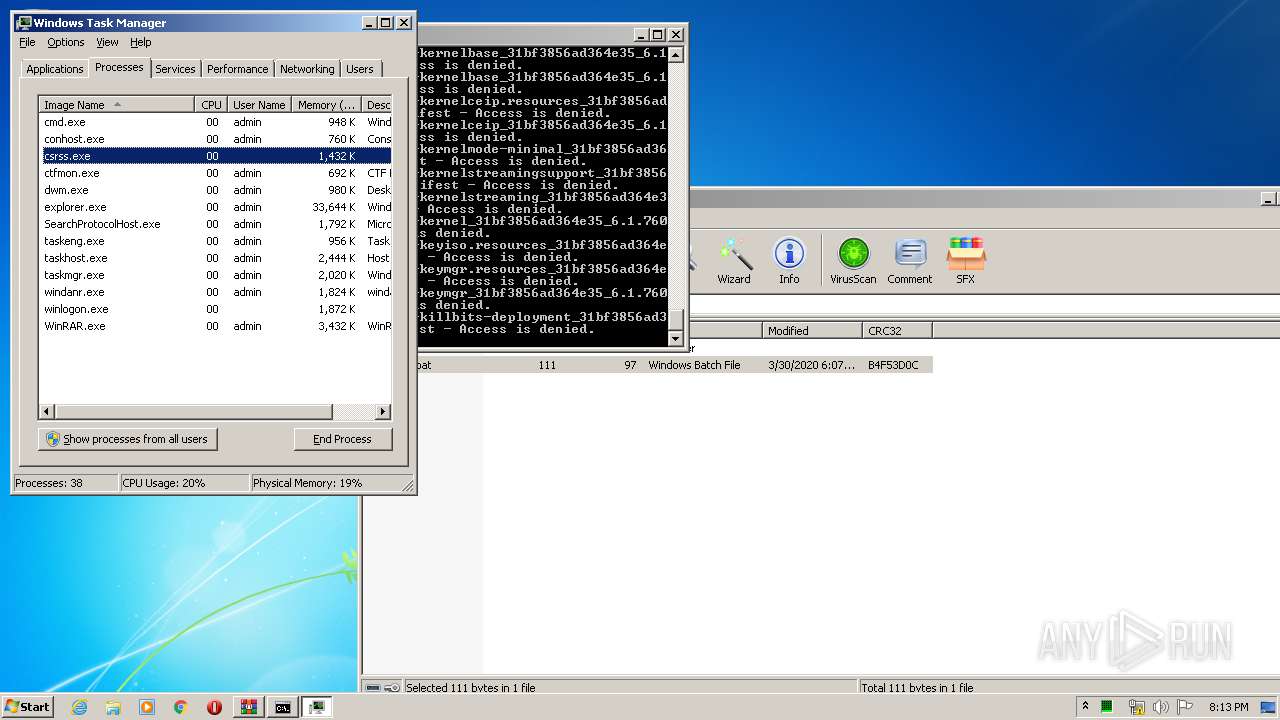
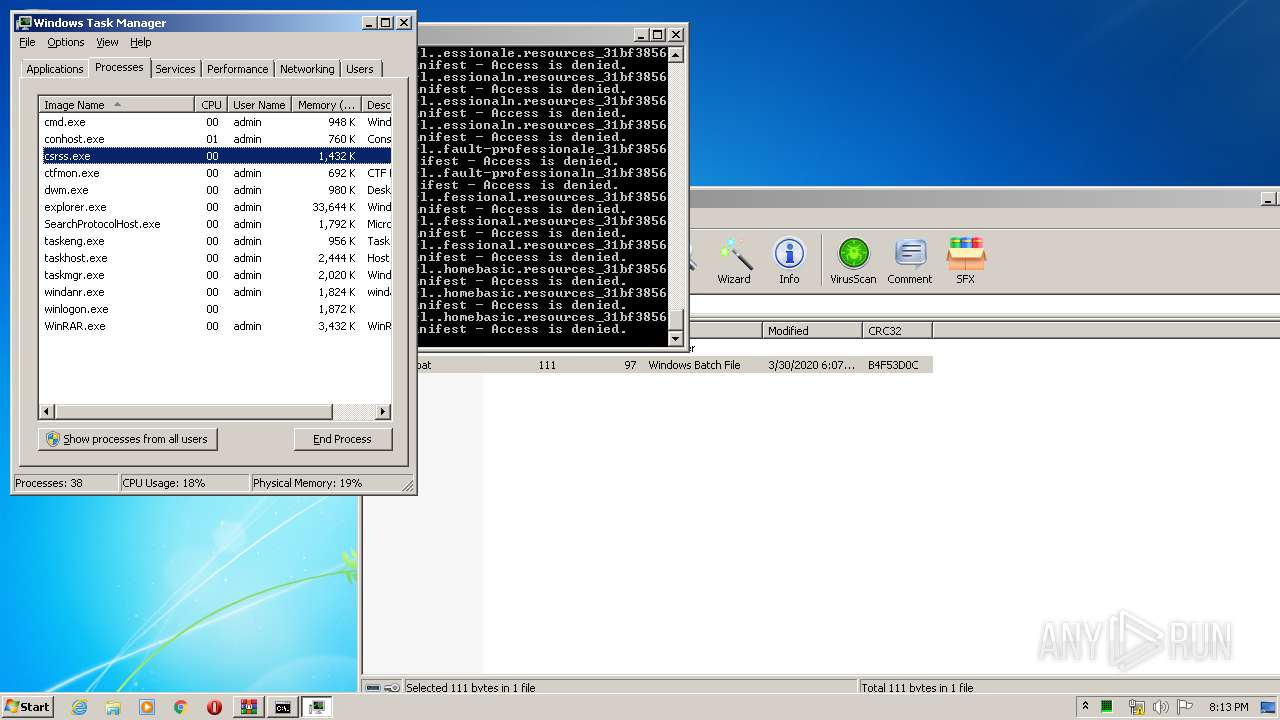
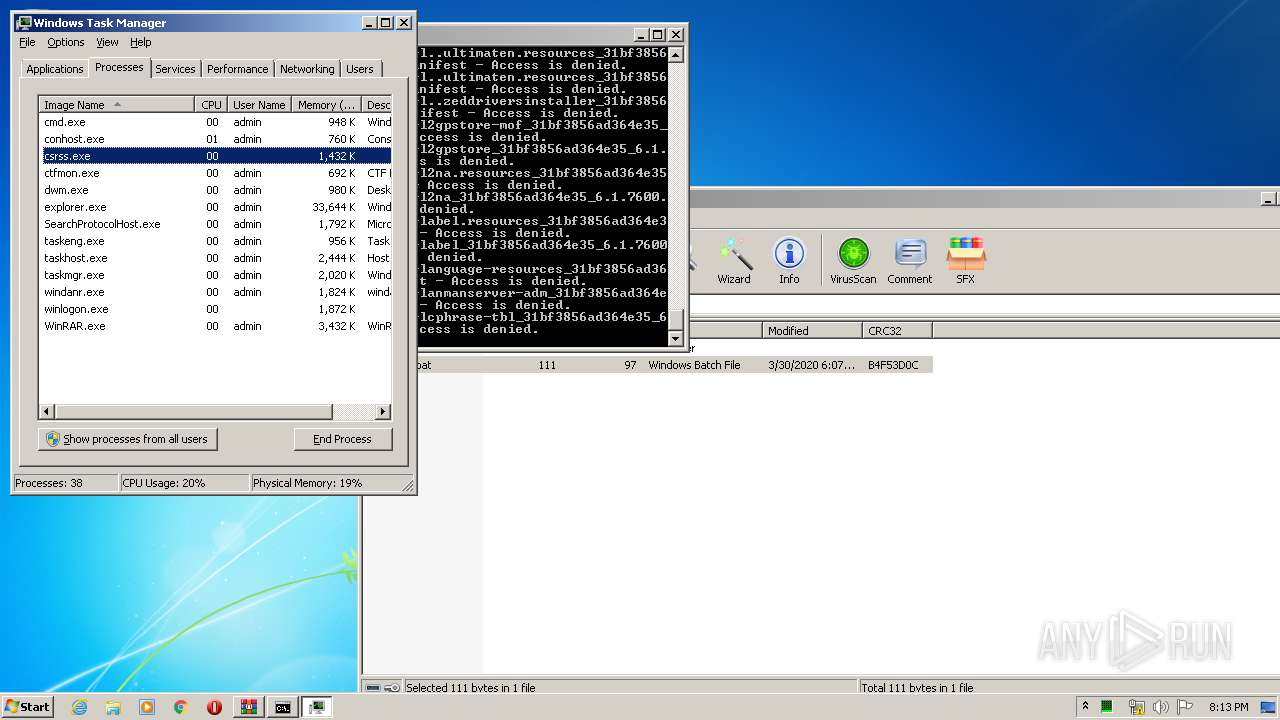
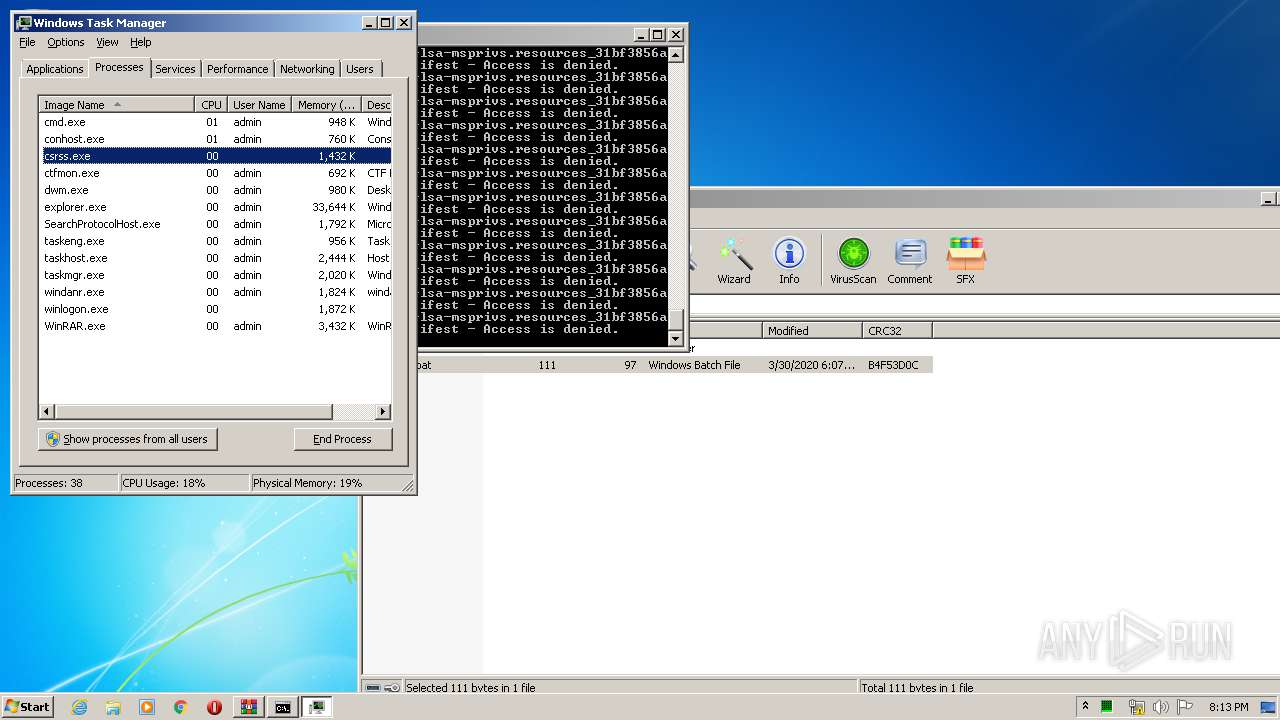
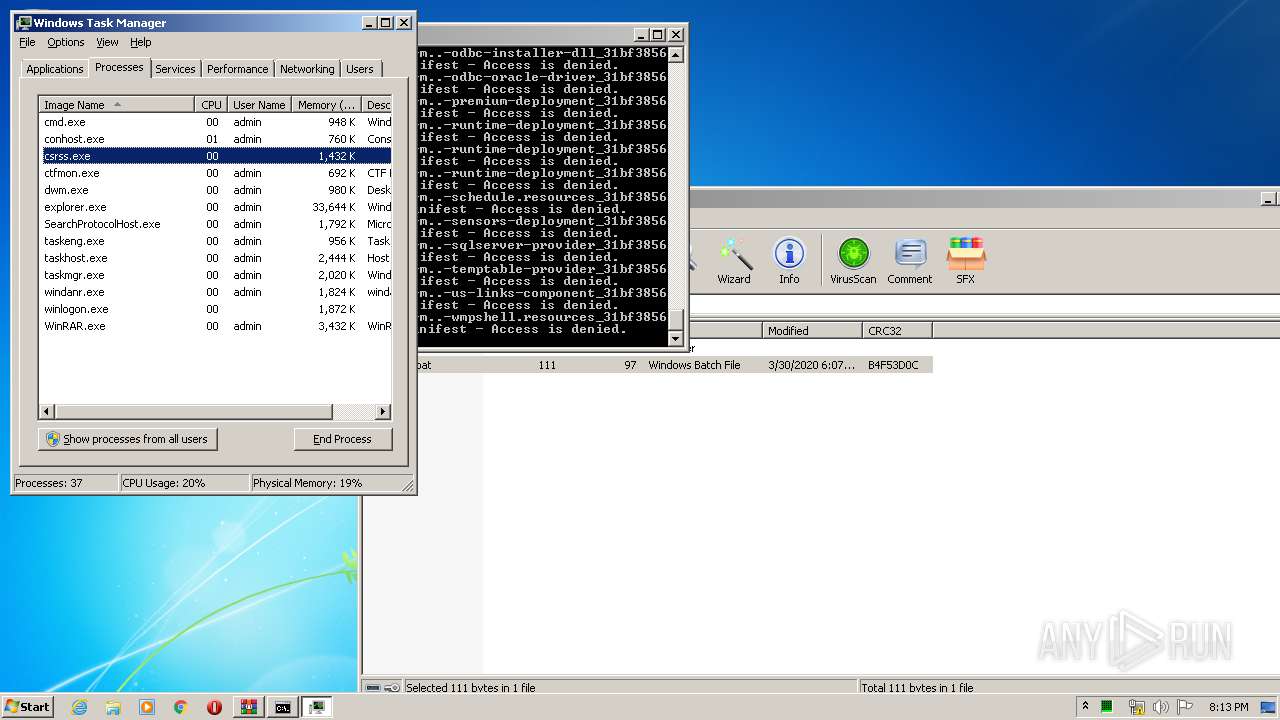
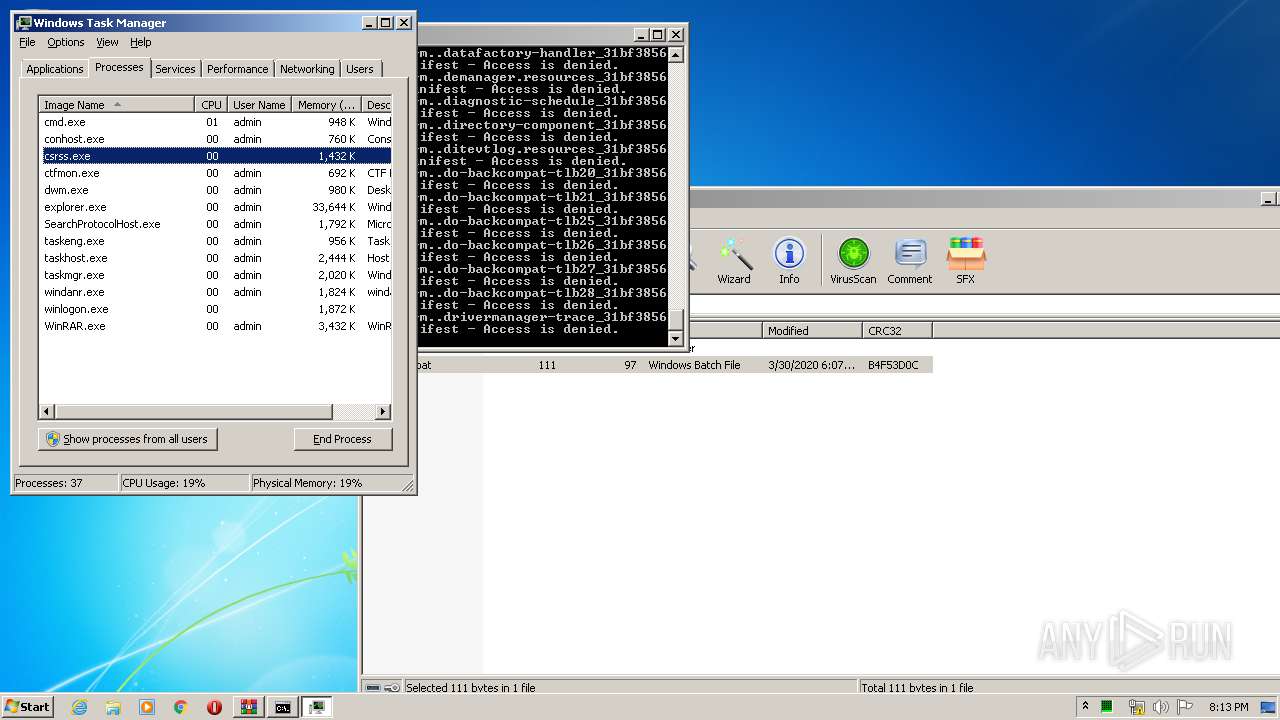
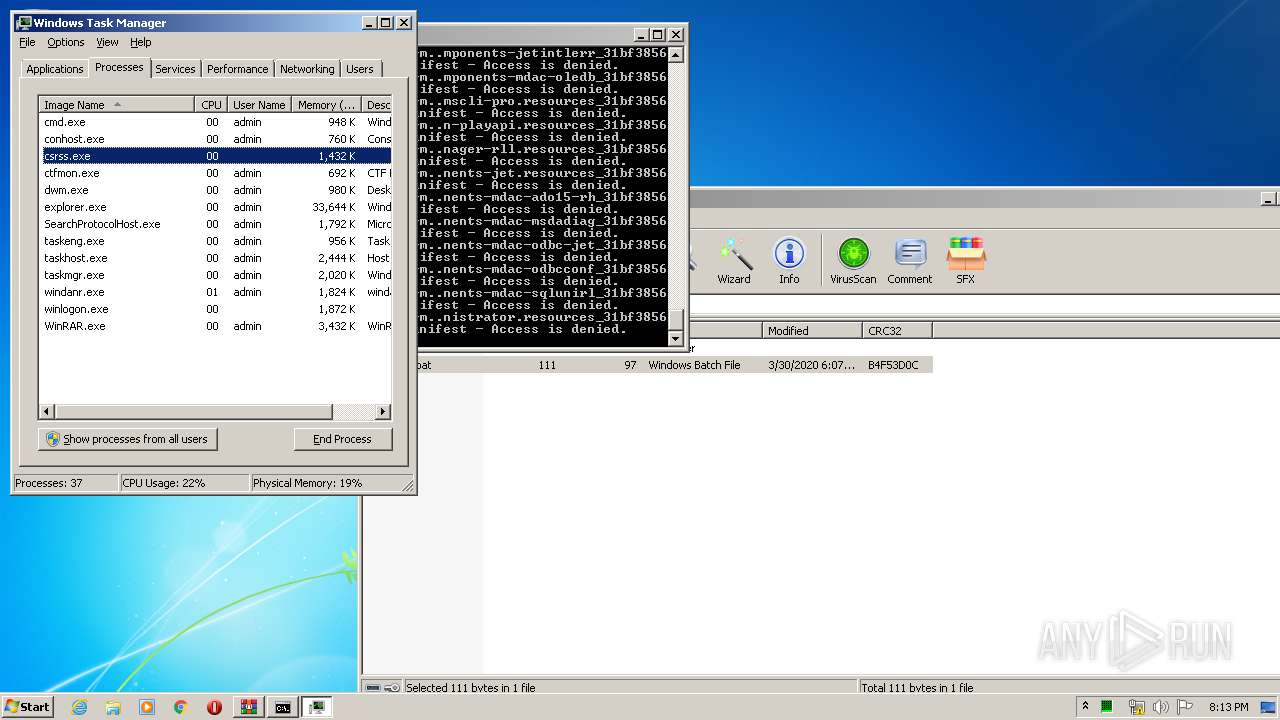
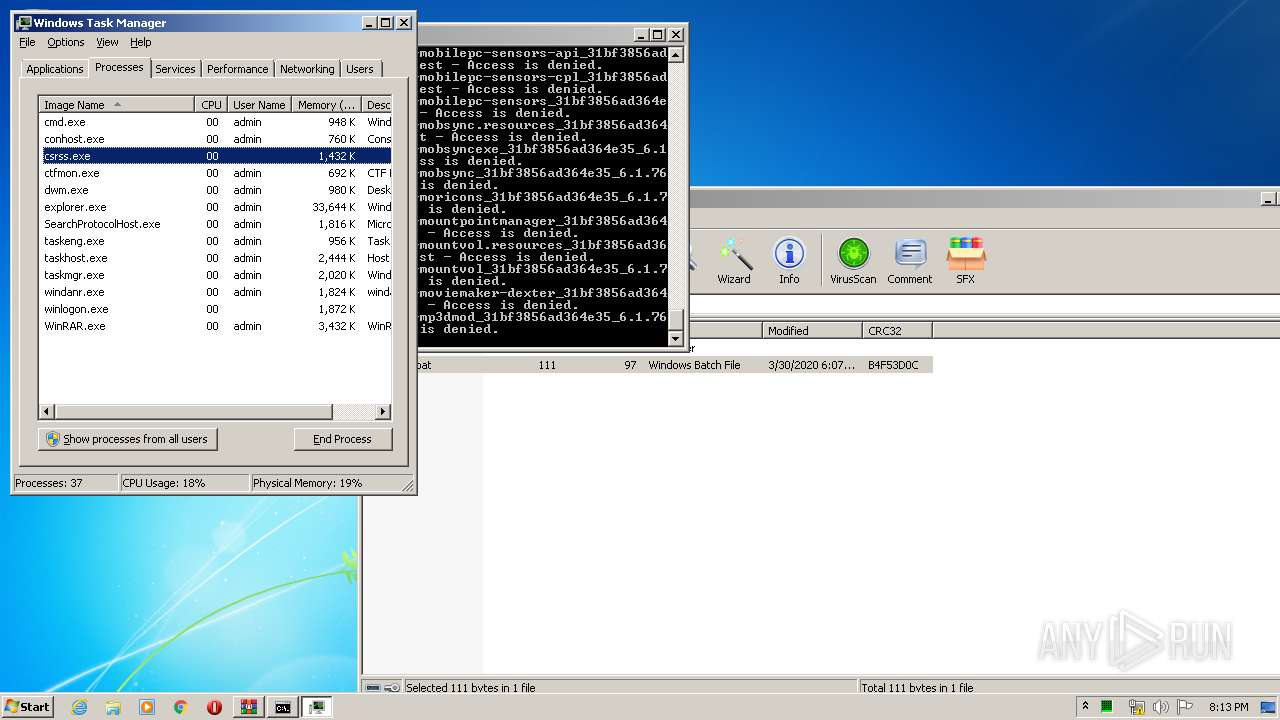
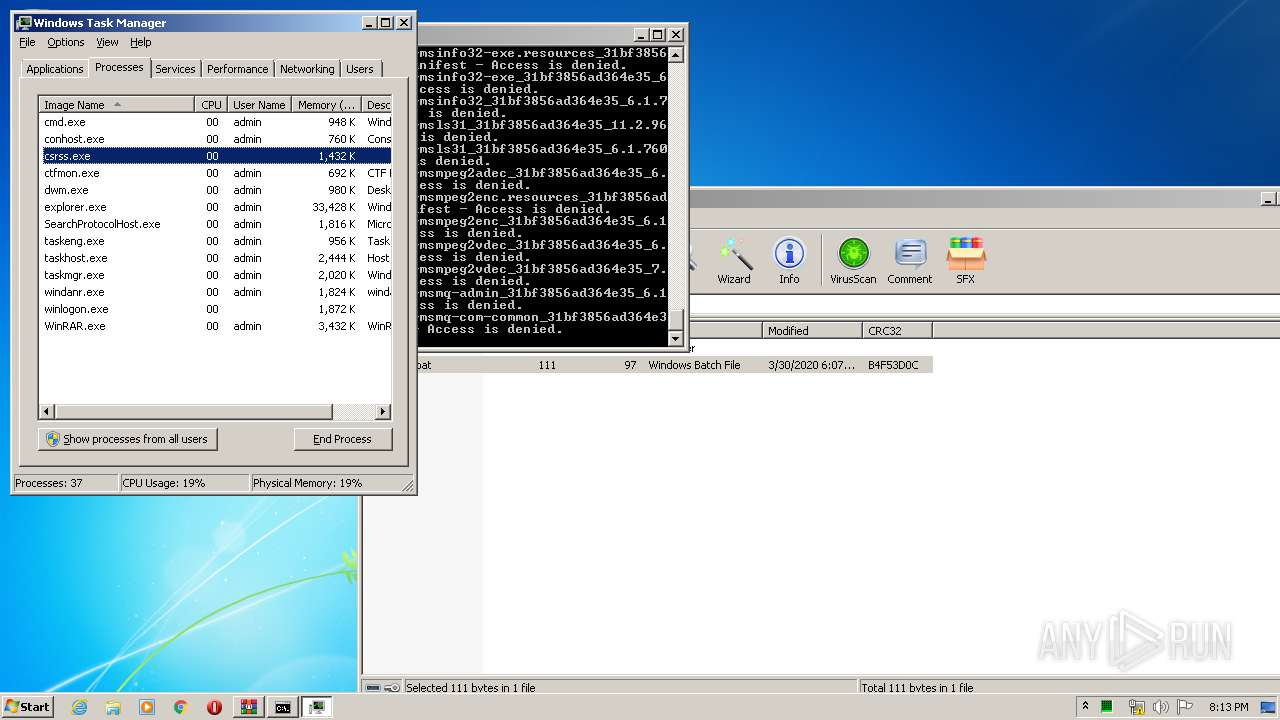
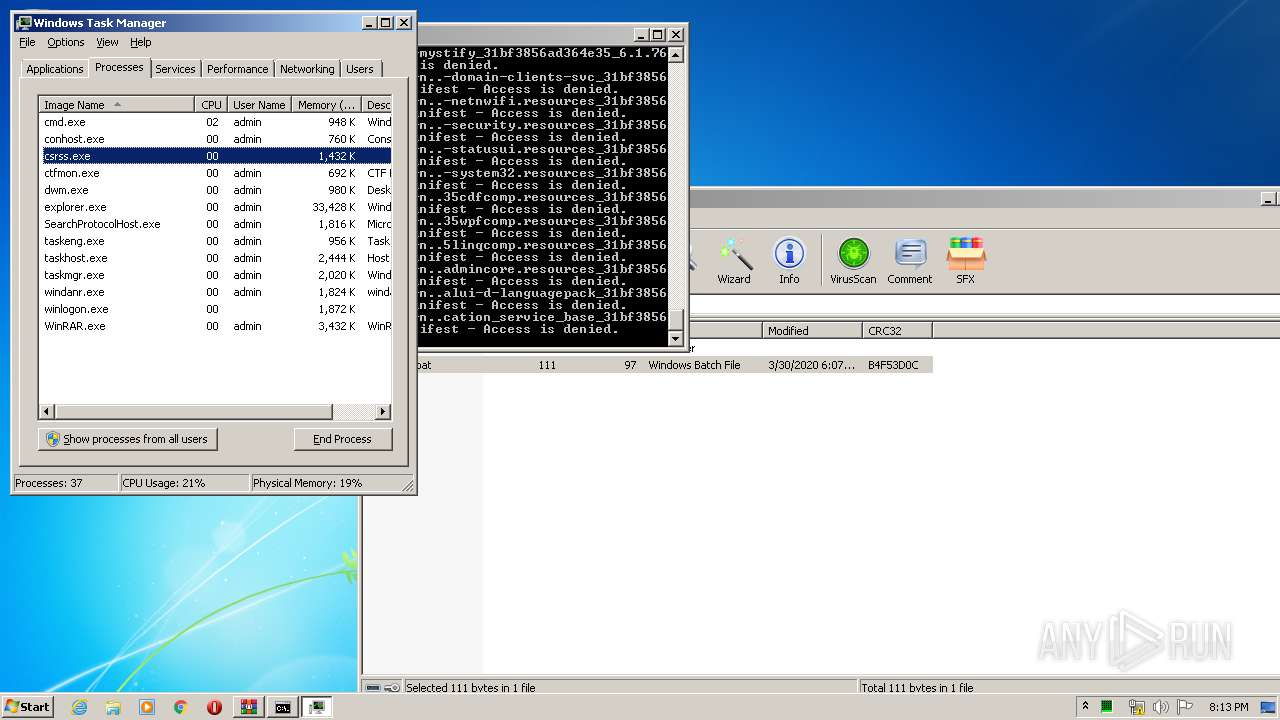
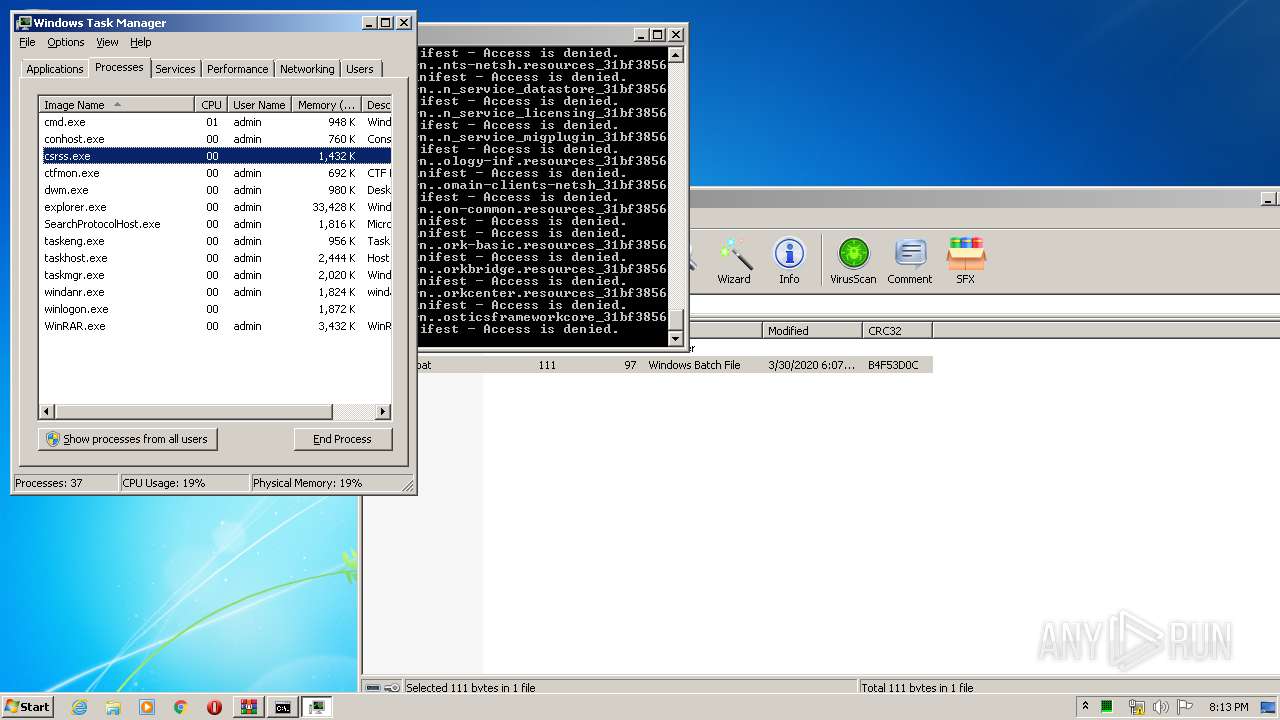
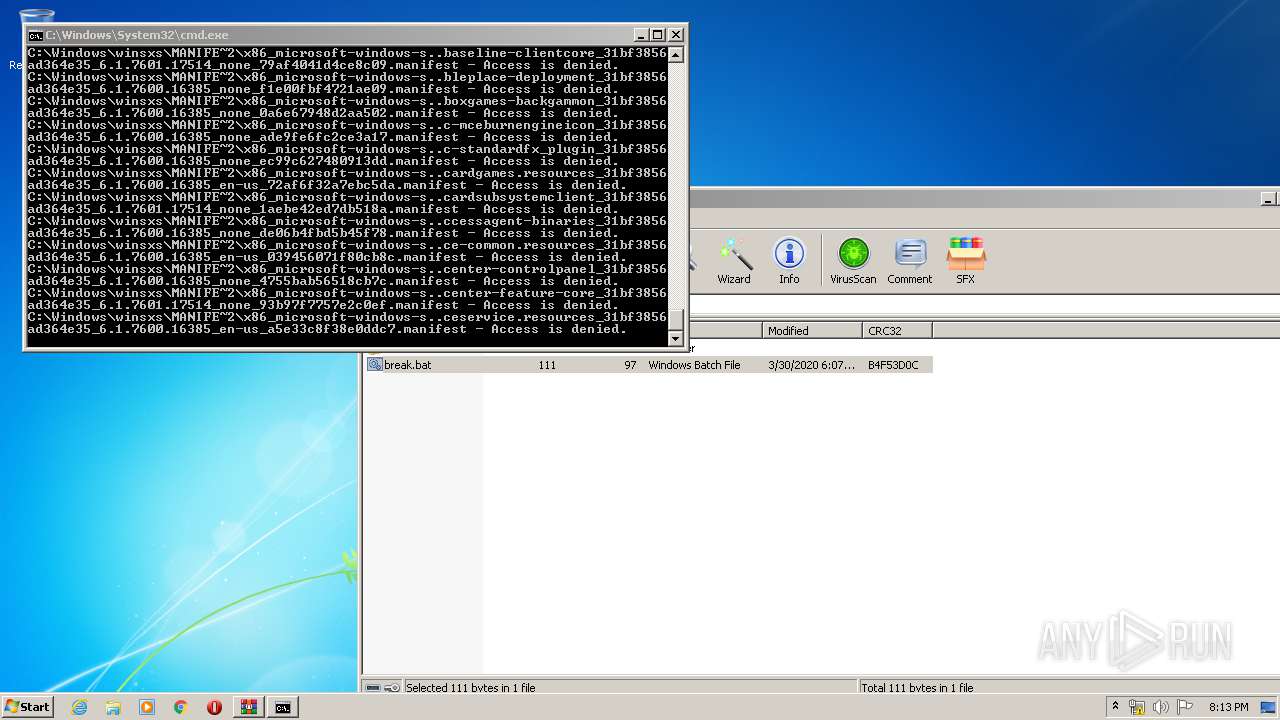
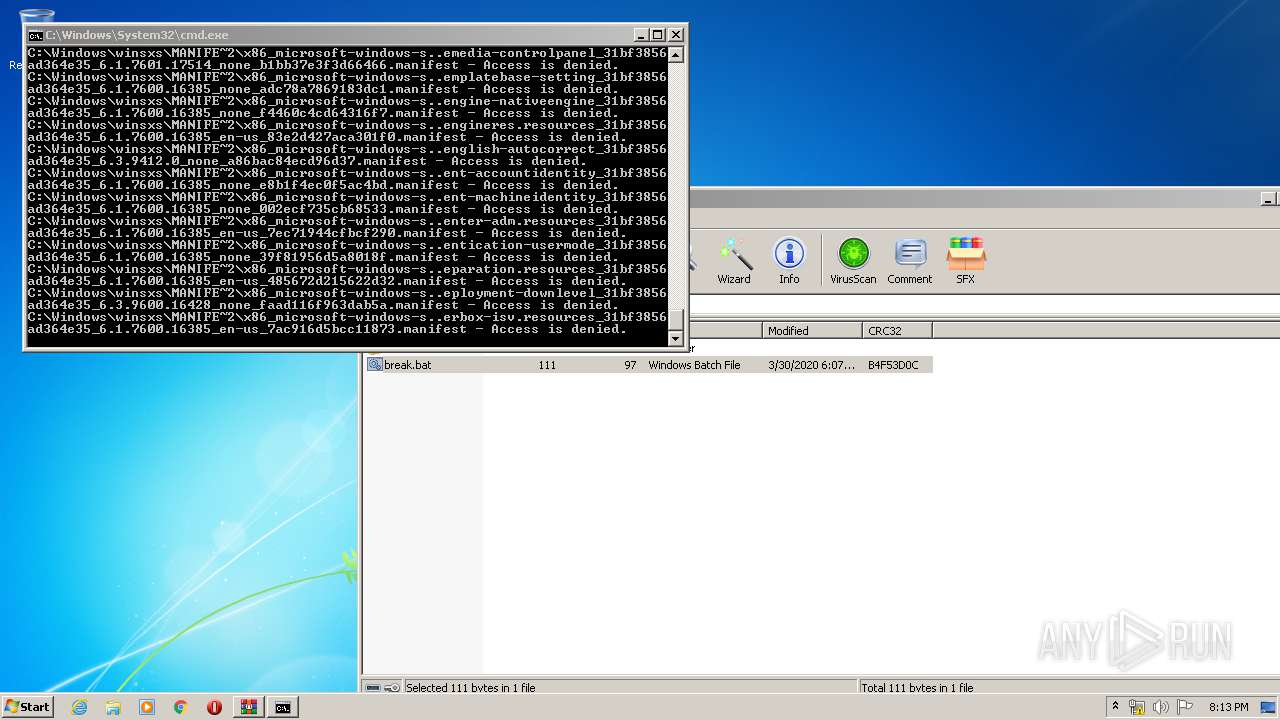
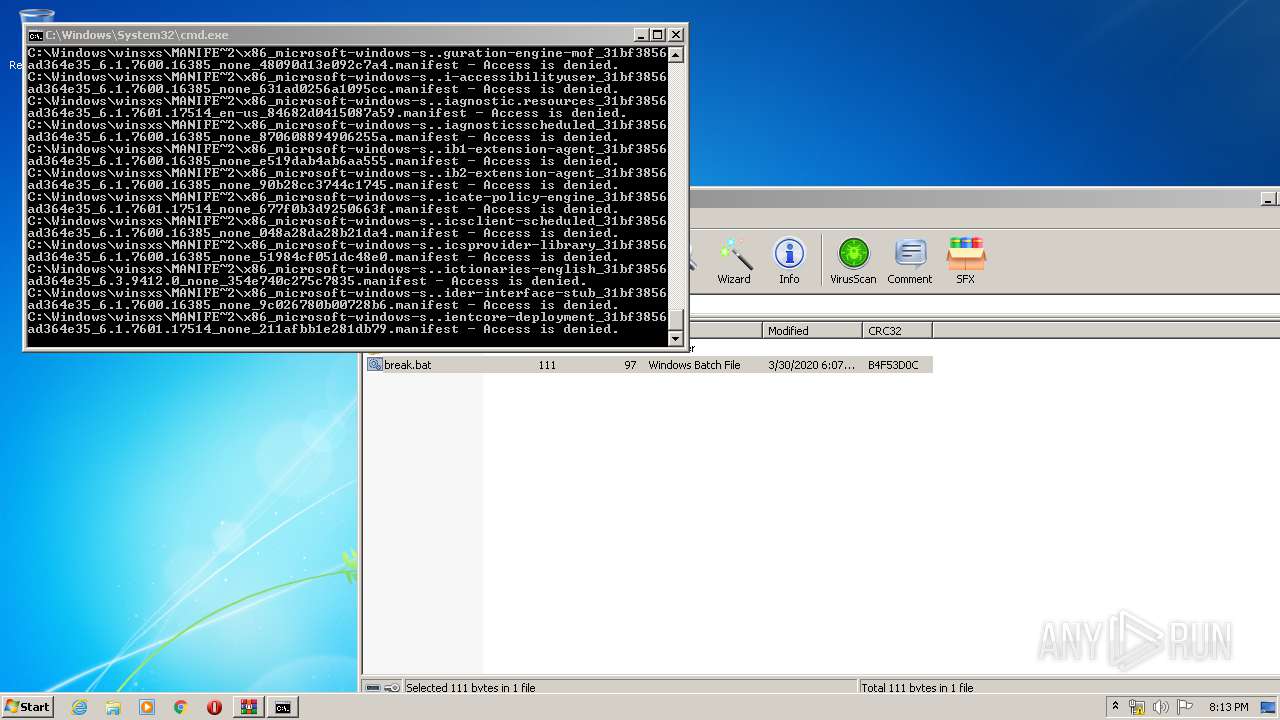
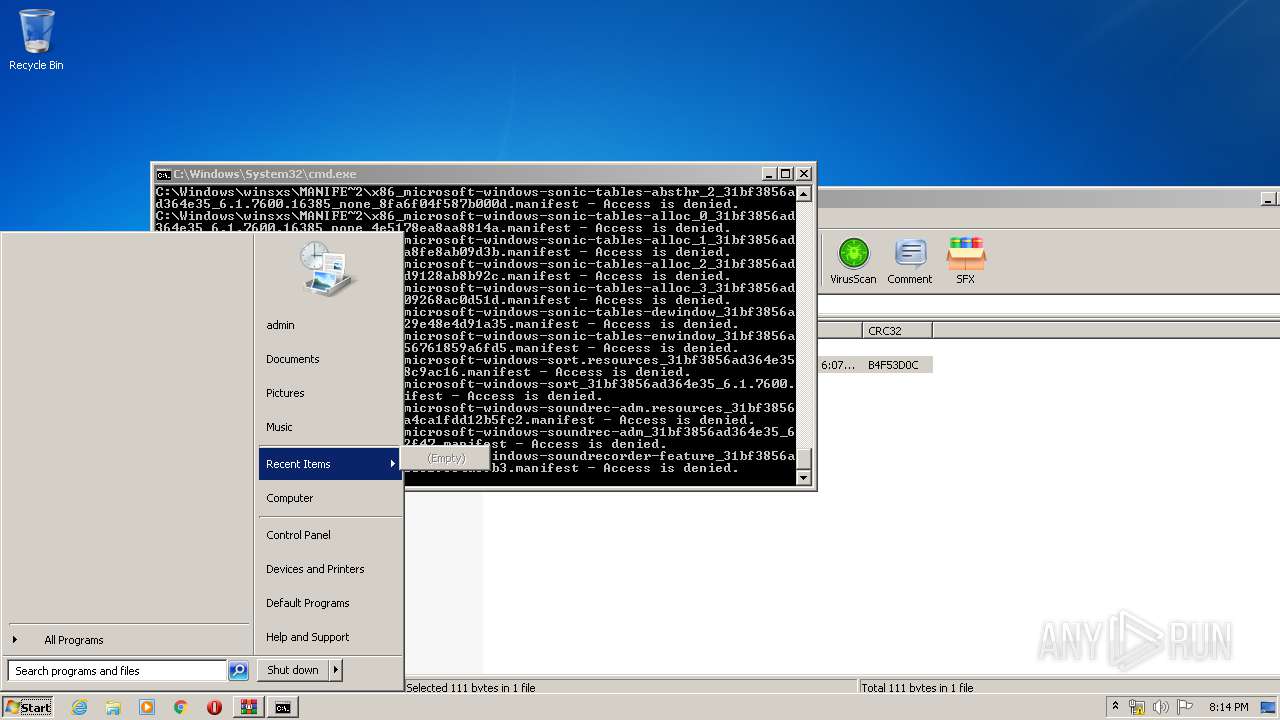
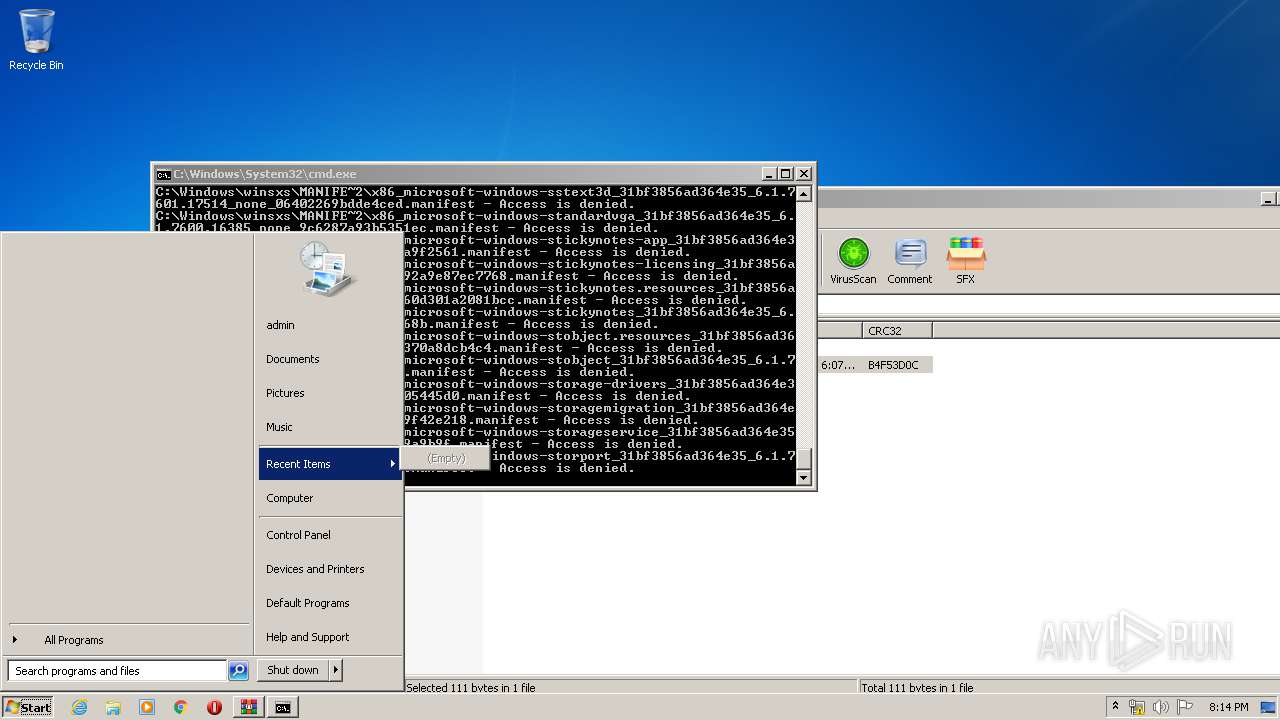
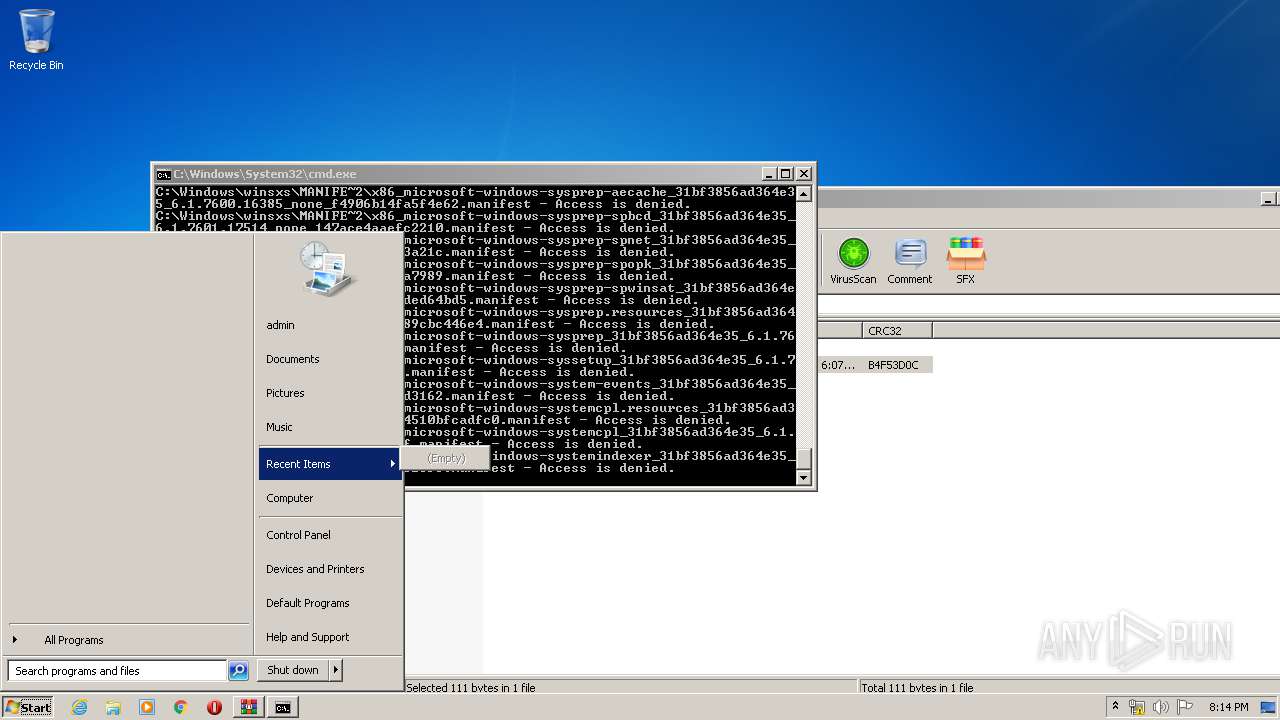
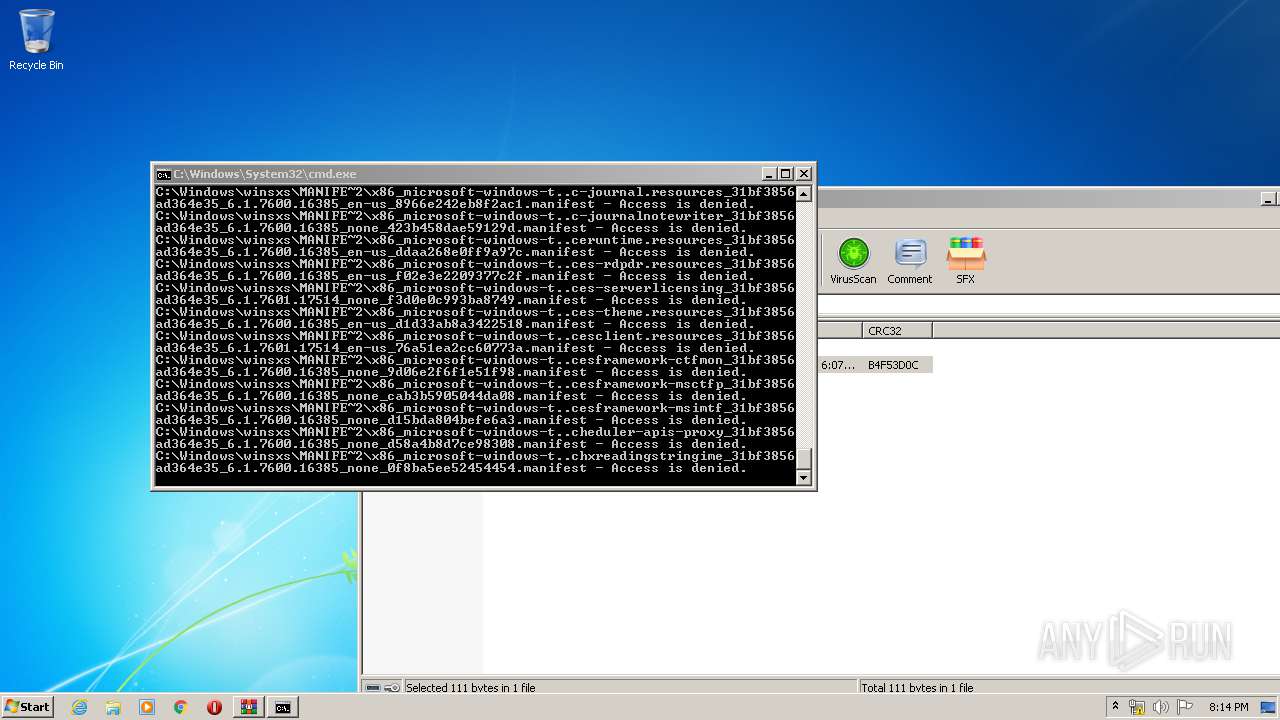
- cmd.exe (PID: 2816)
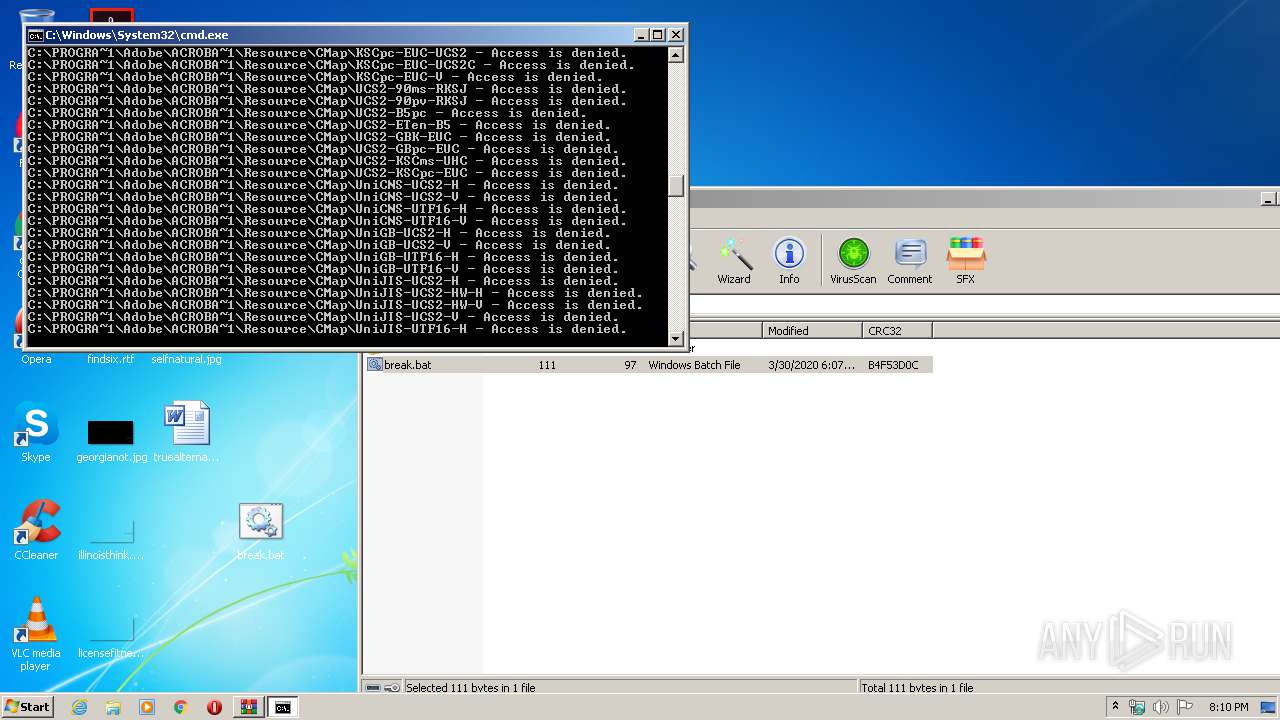
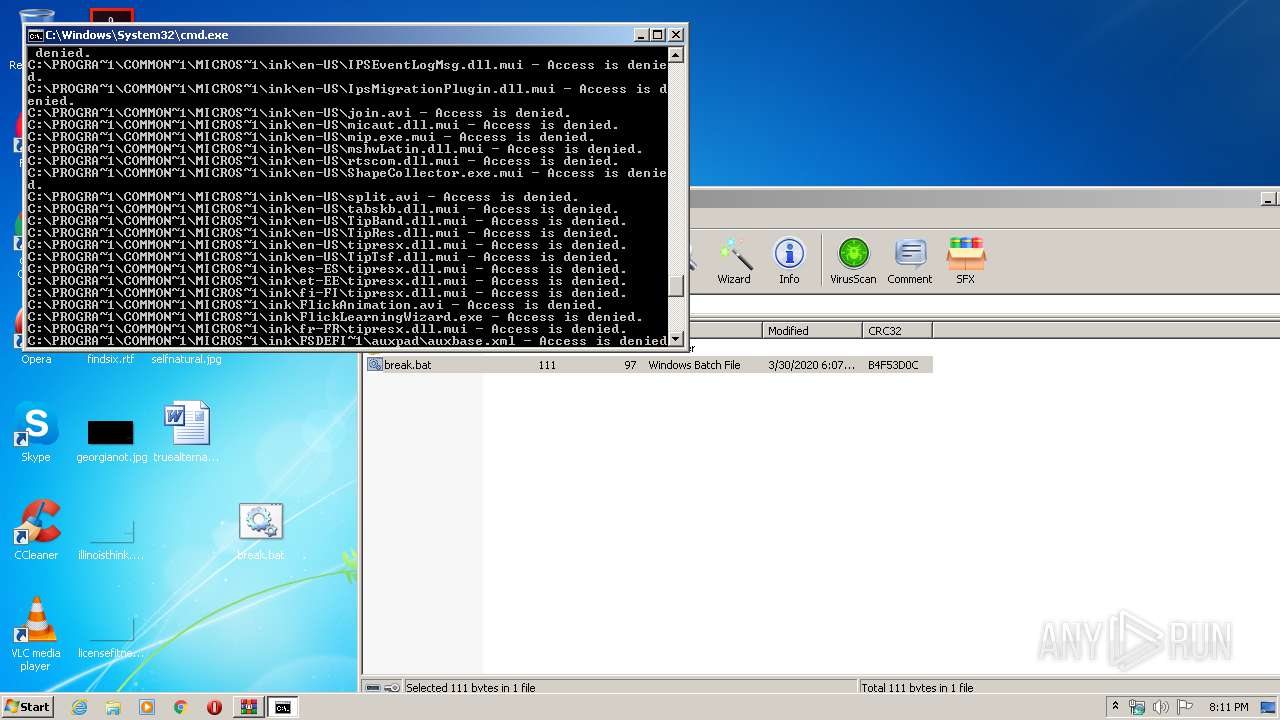
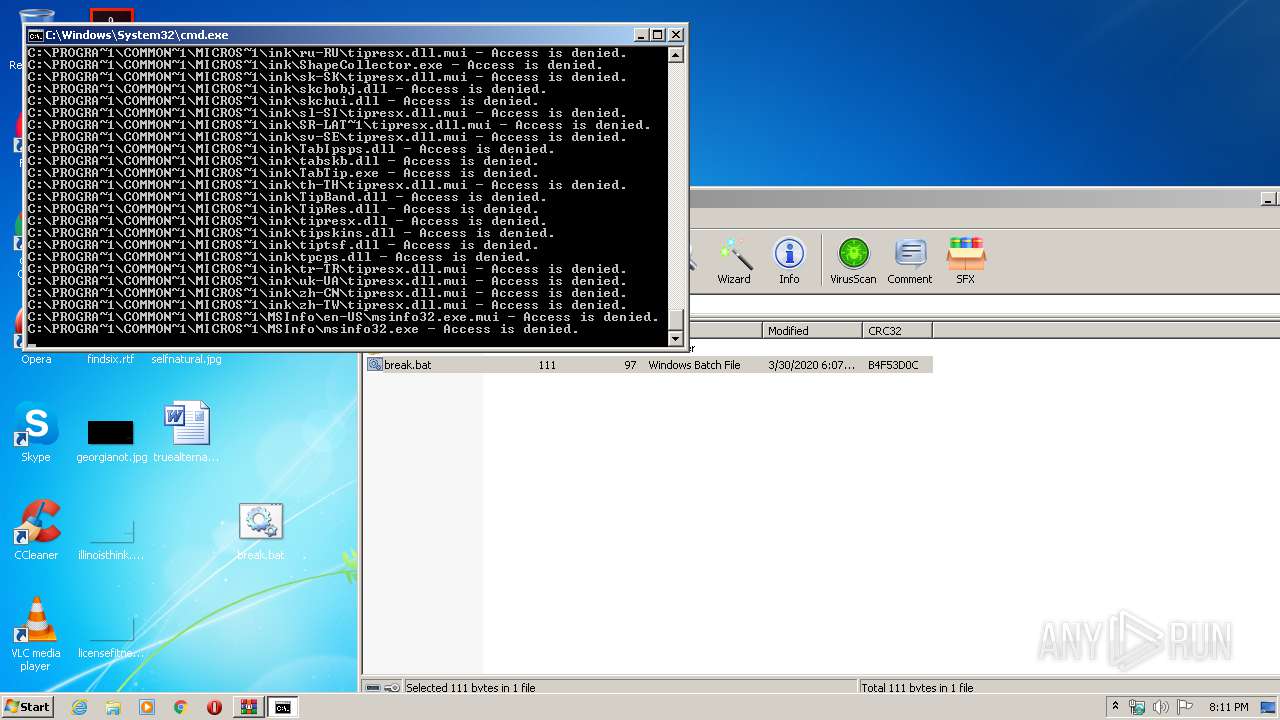
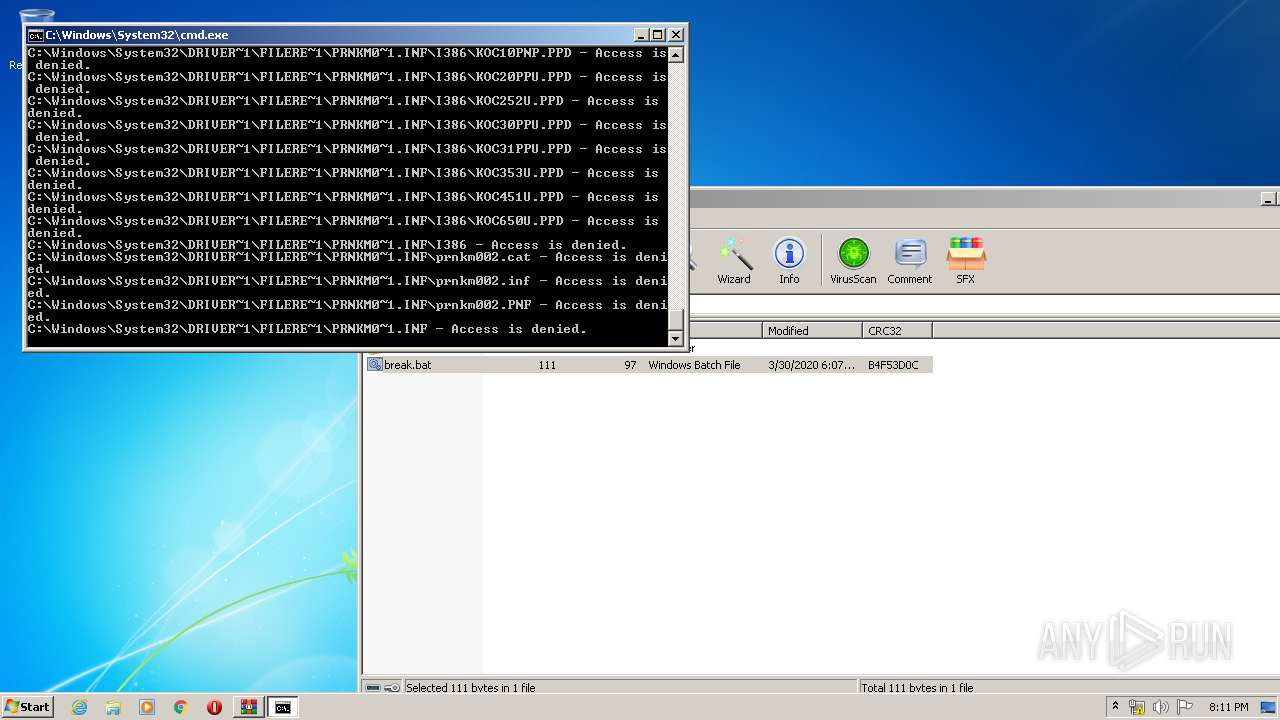
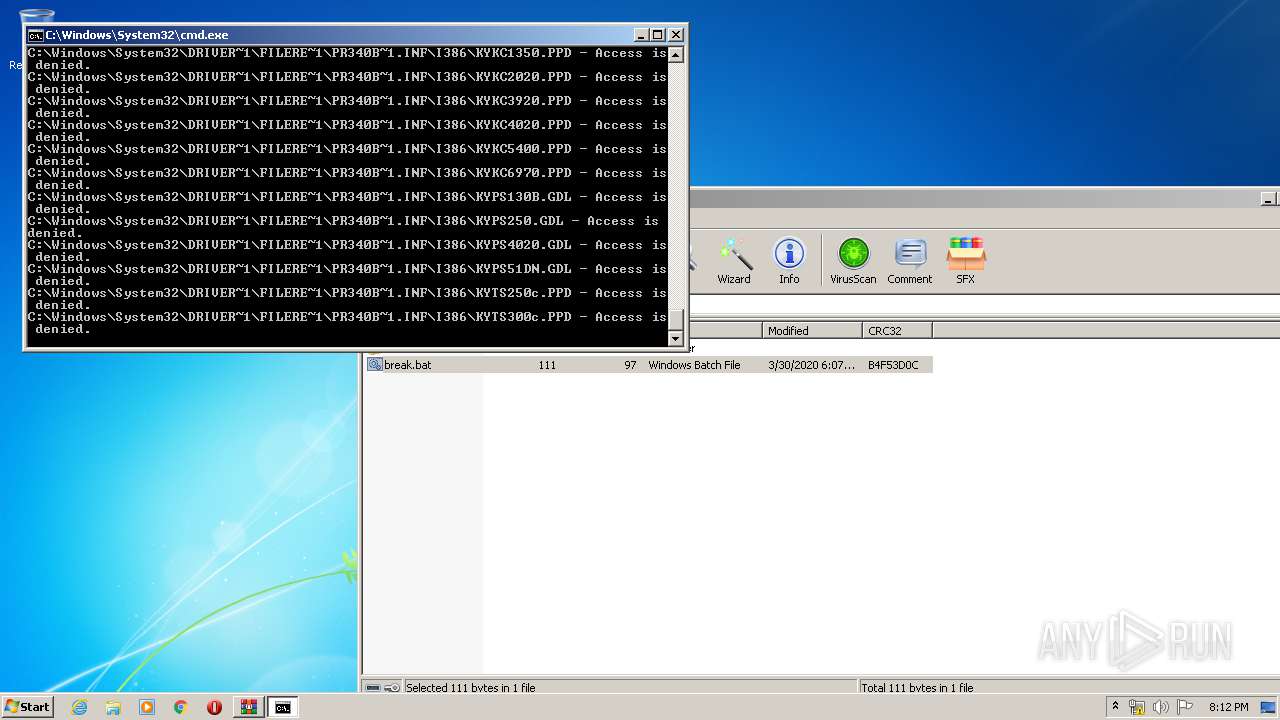
Tries to delete the host file
- cmd.exe (PID: 2816)
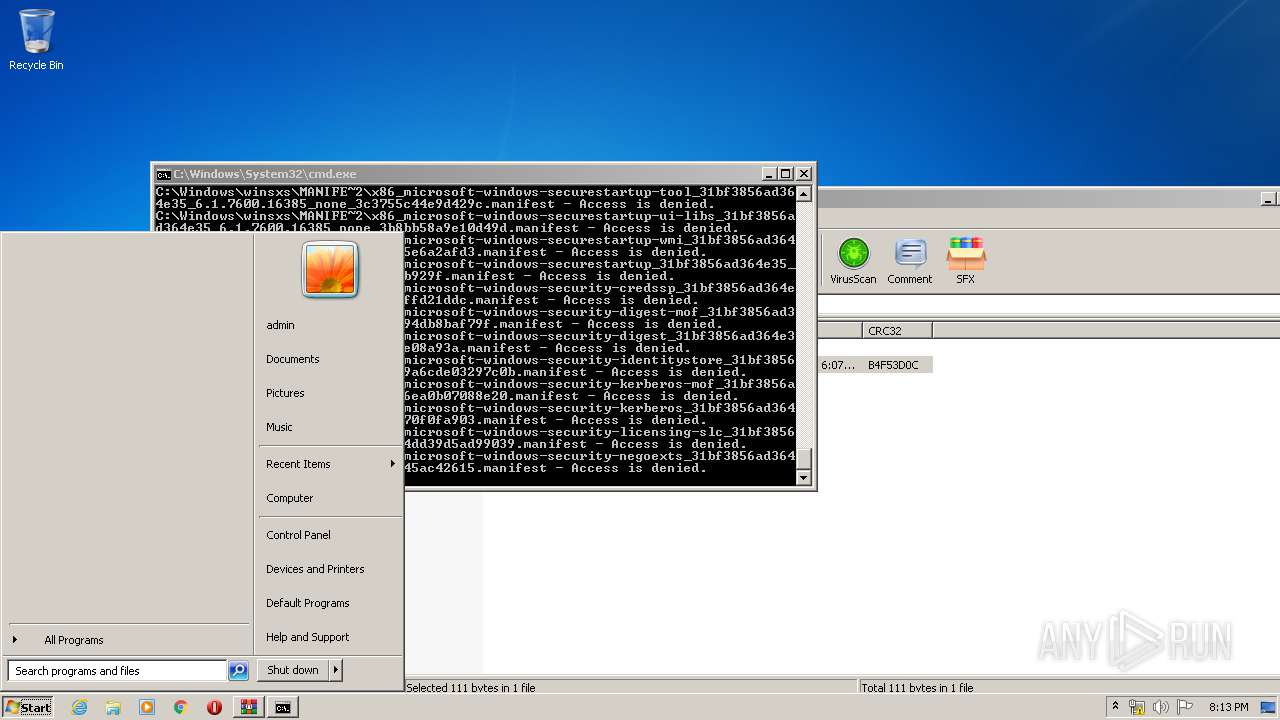
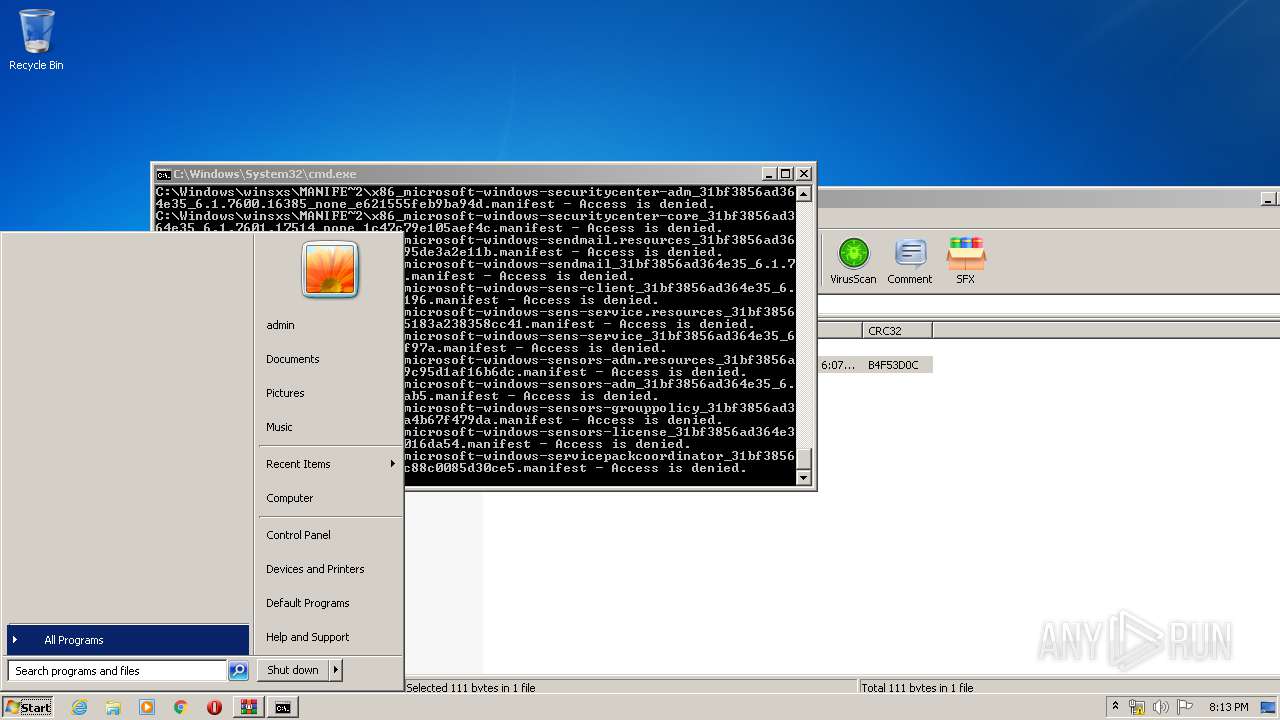
SUSPICIOUS
Executed as Windows Service
- SearchIndexer.exe (PID: 1548)
- SearchIndexer.exe (PID: 348)
Creates files in the program directory
- SearchIndexer.exe (PID: 1548)
- SearchIndexer.exe (PID: 348)
Creates files in the Windows directory
- SearchIndexer.exe (PID: 348)
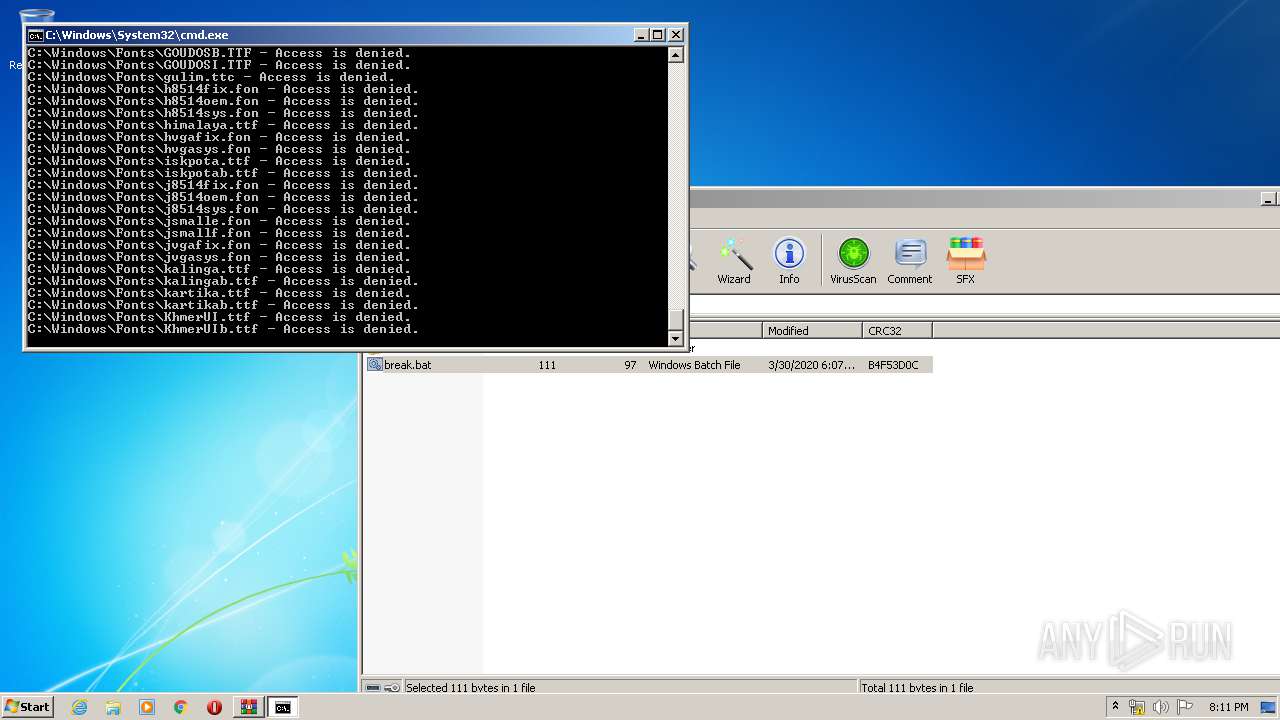
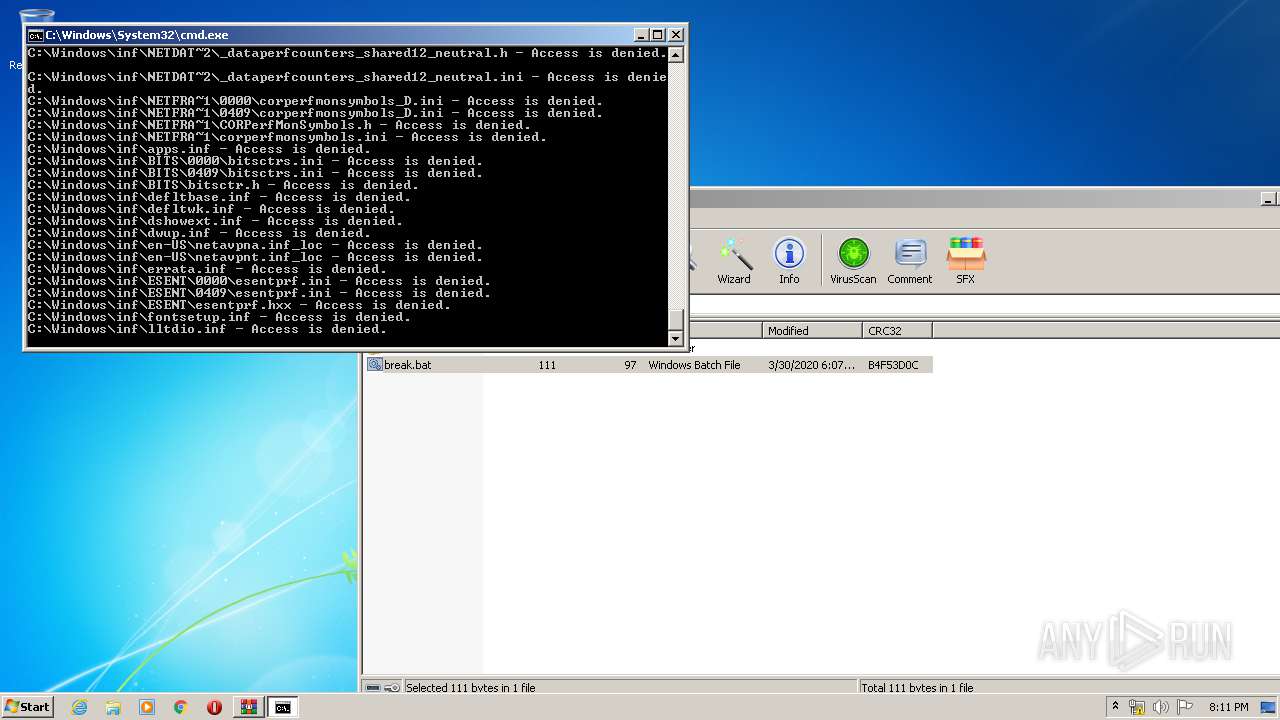
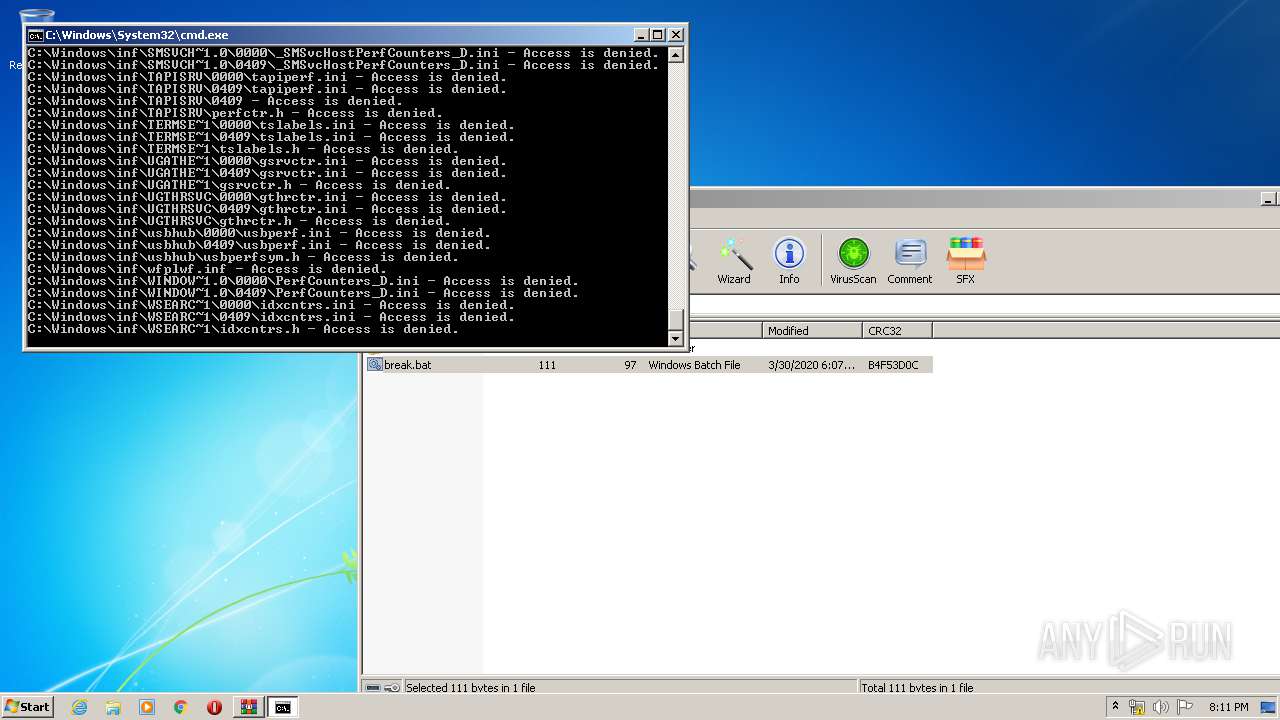
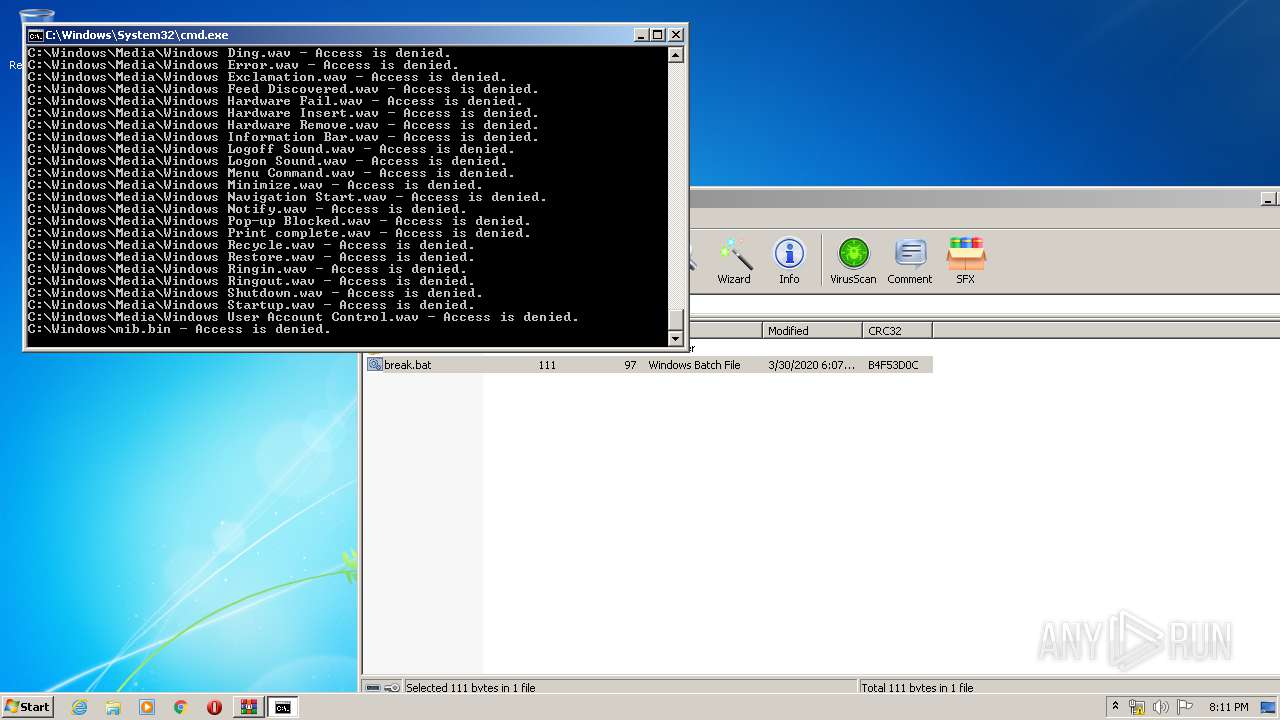
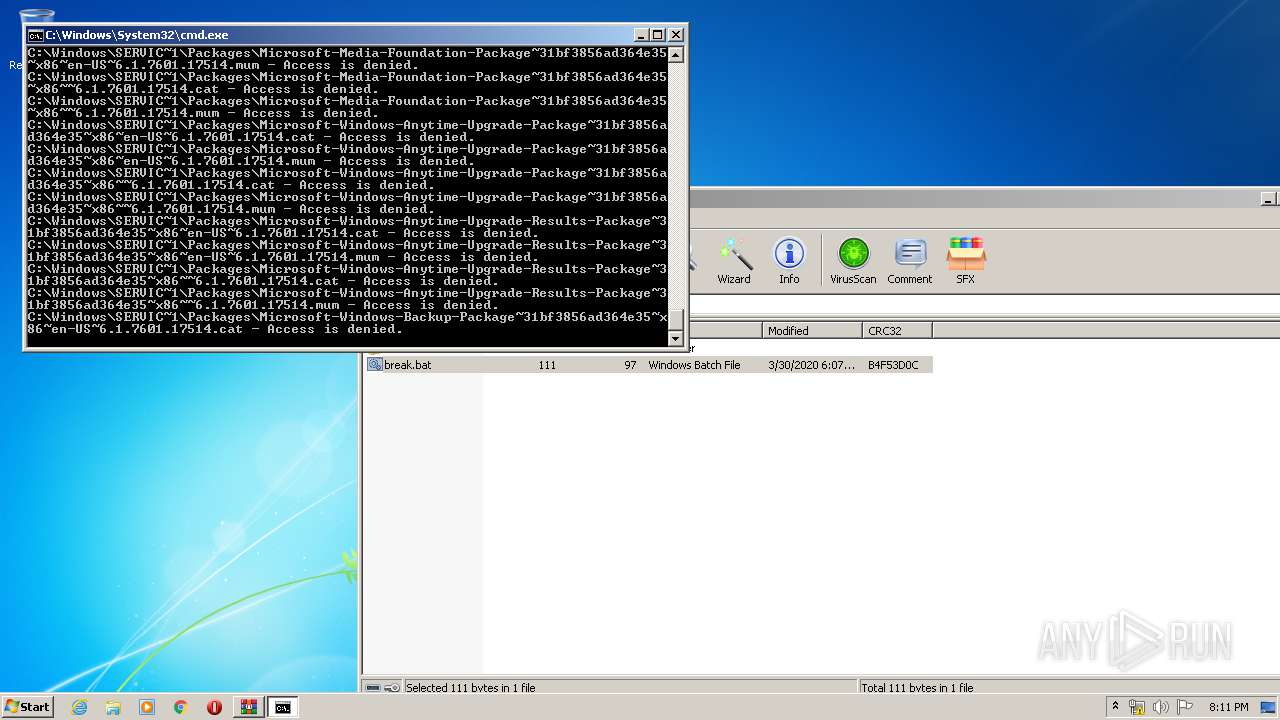
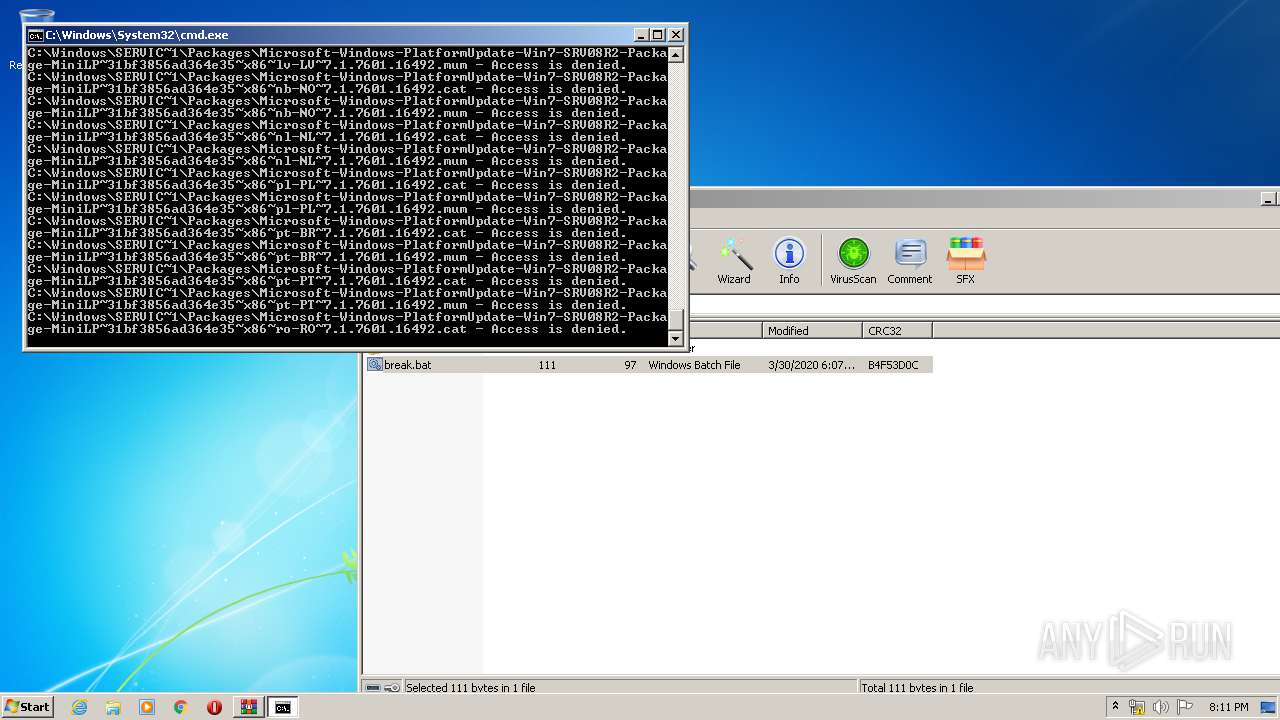
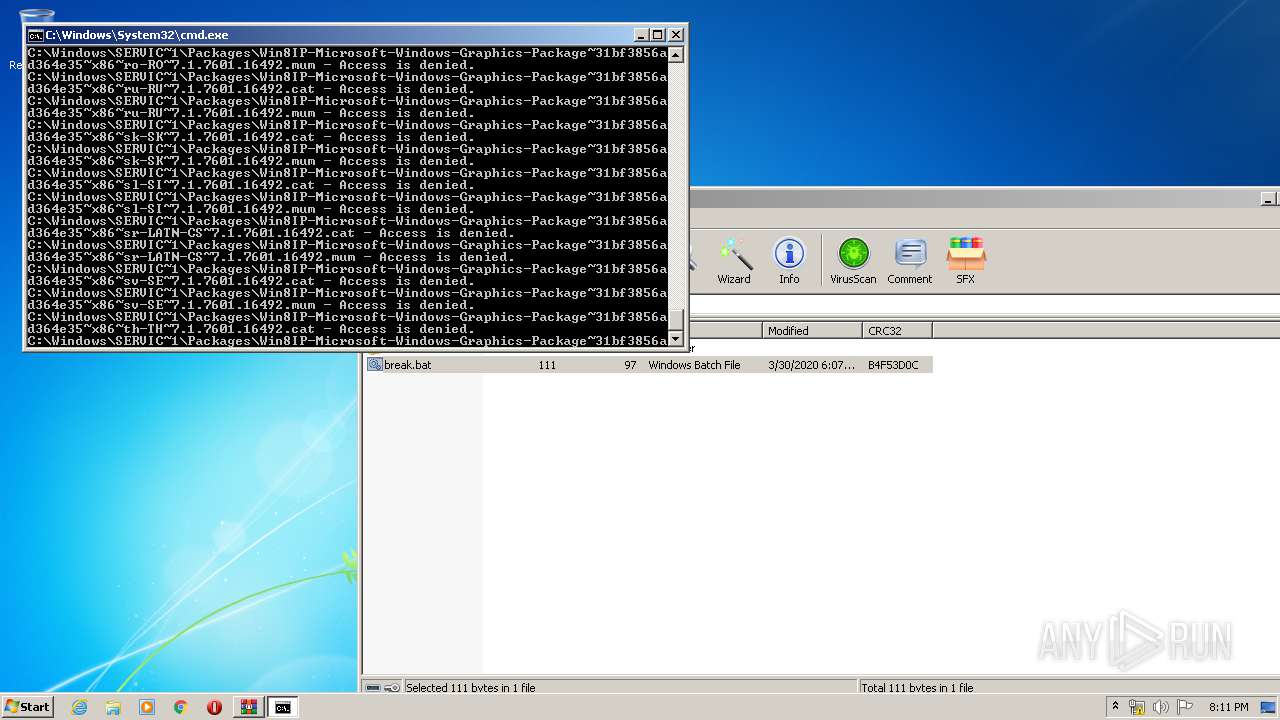
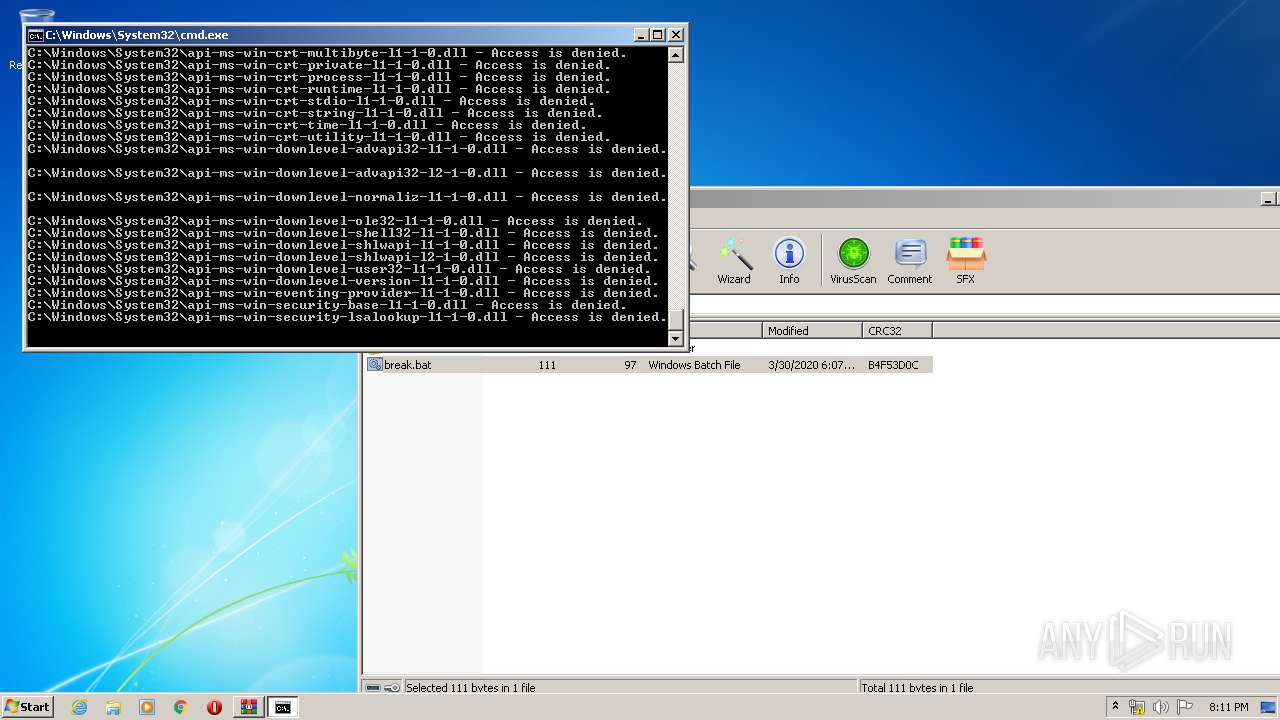
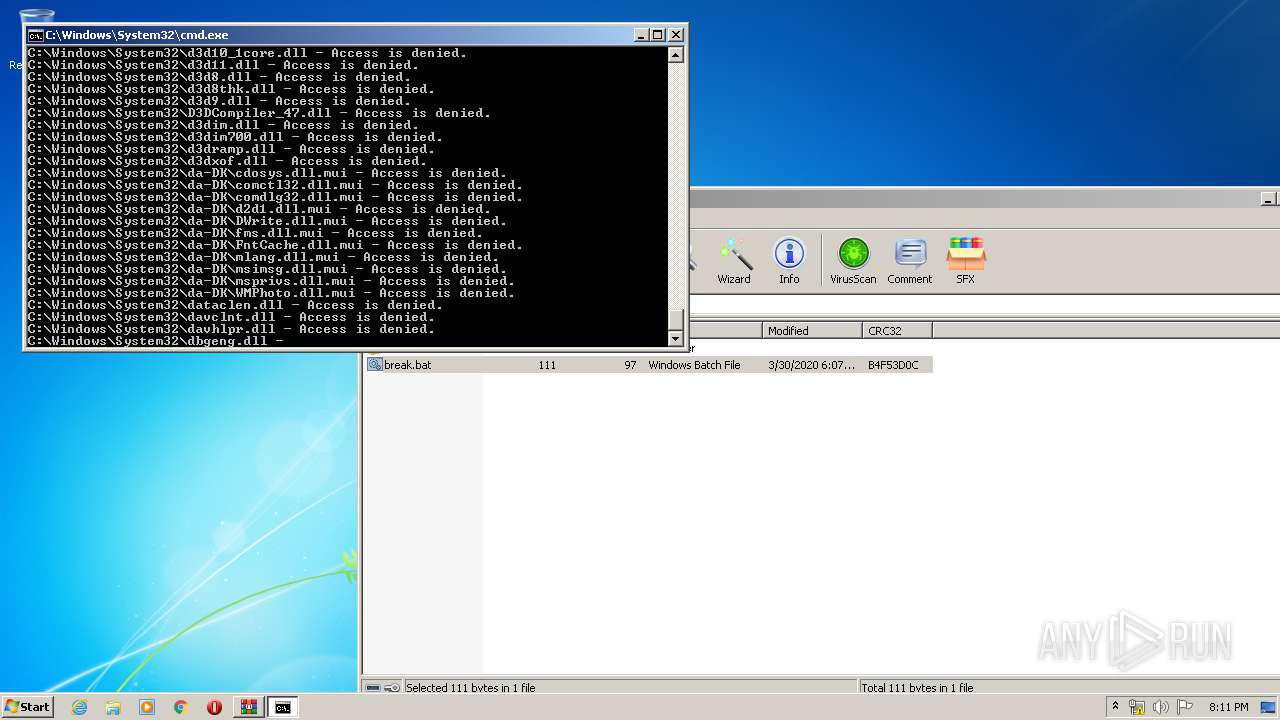
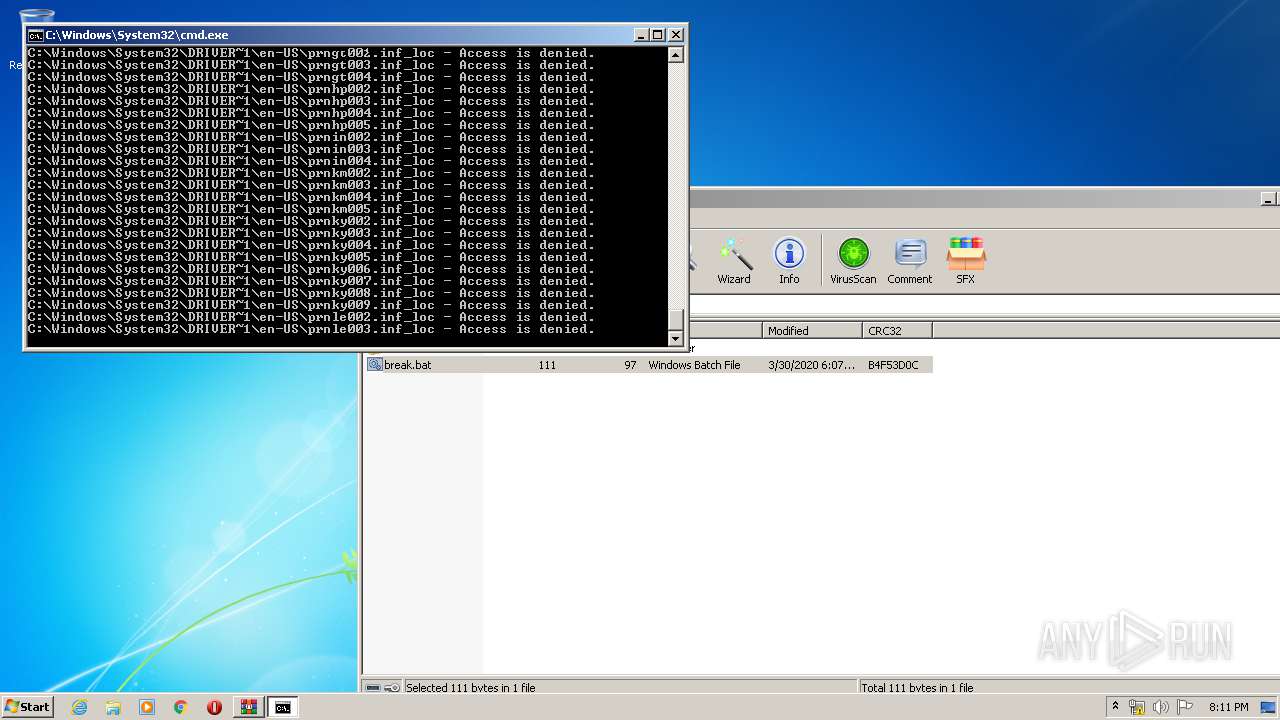
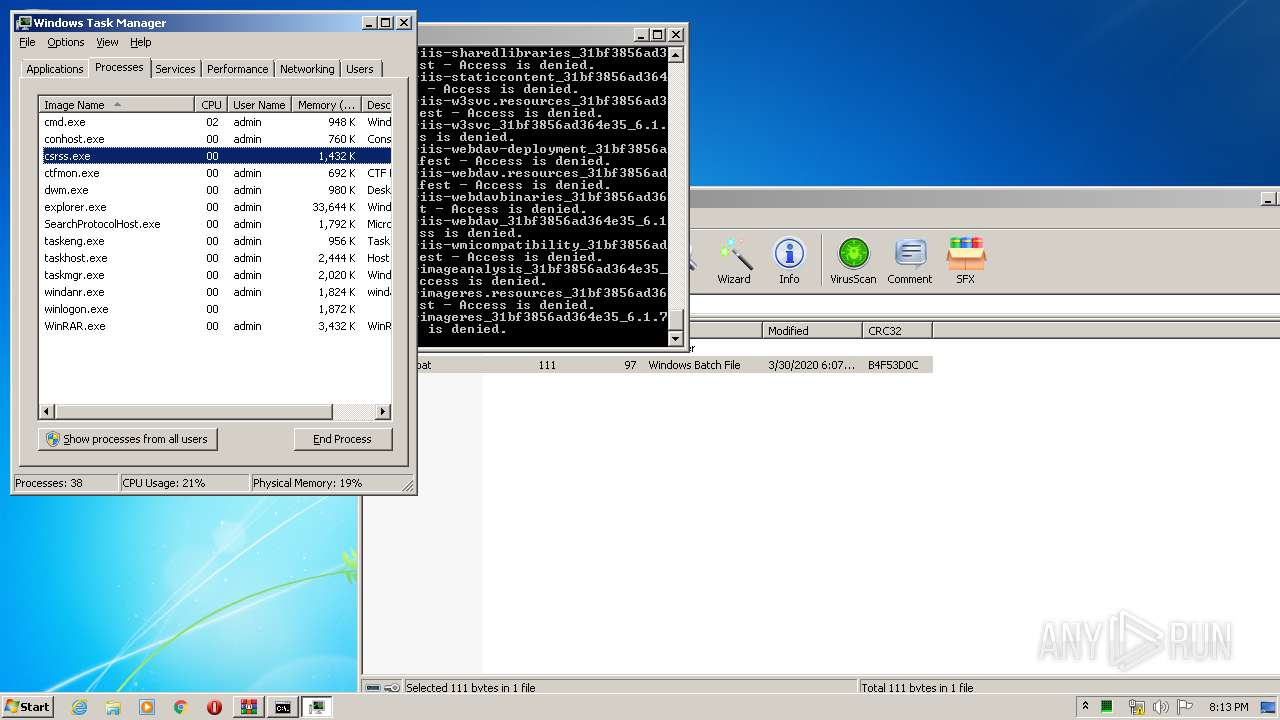
Removes files from Windows directory
- cmd.exe (PID: 2816)
INFO
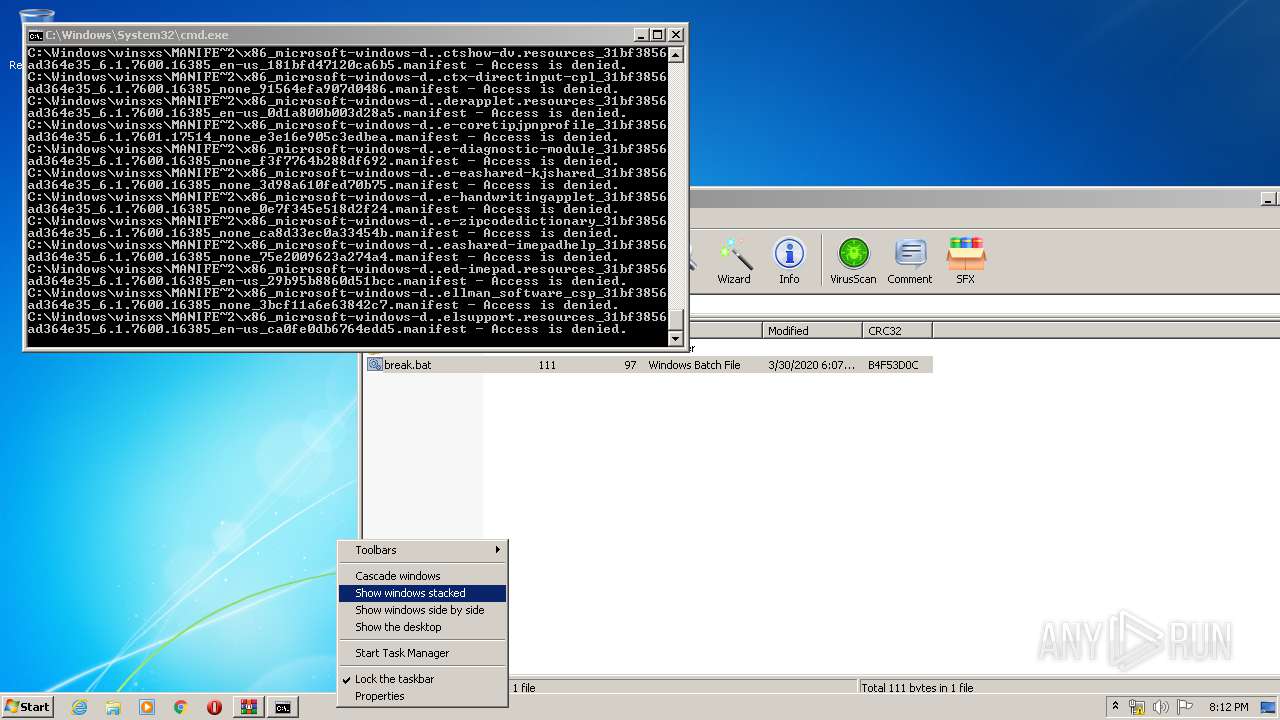
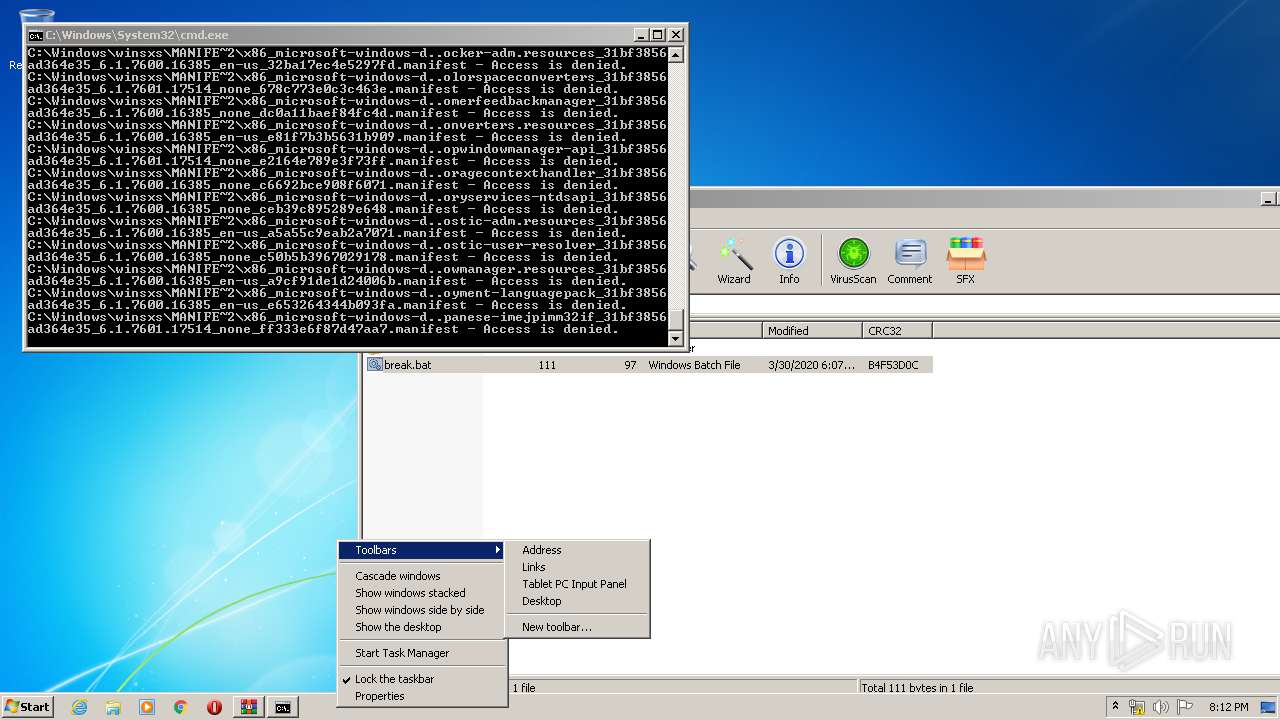
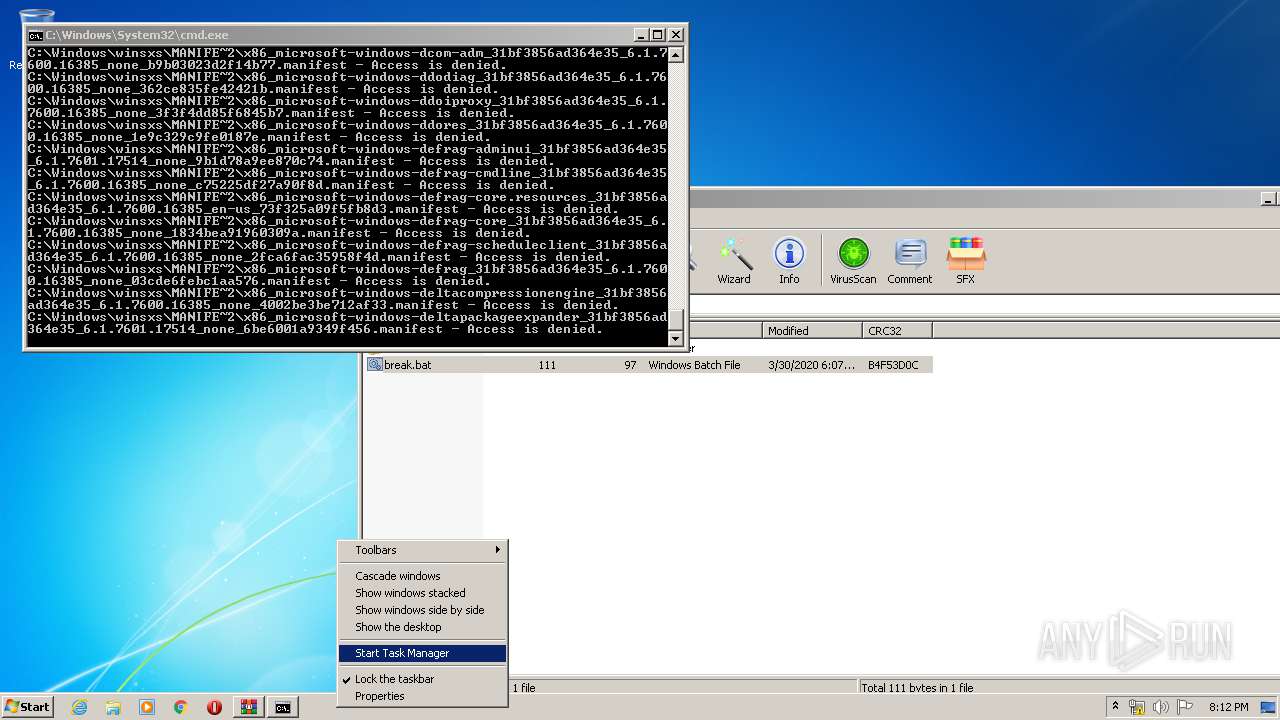
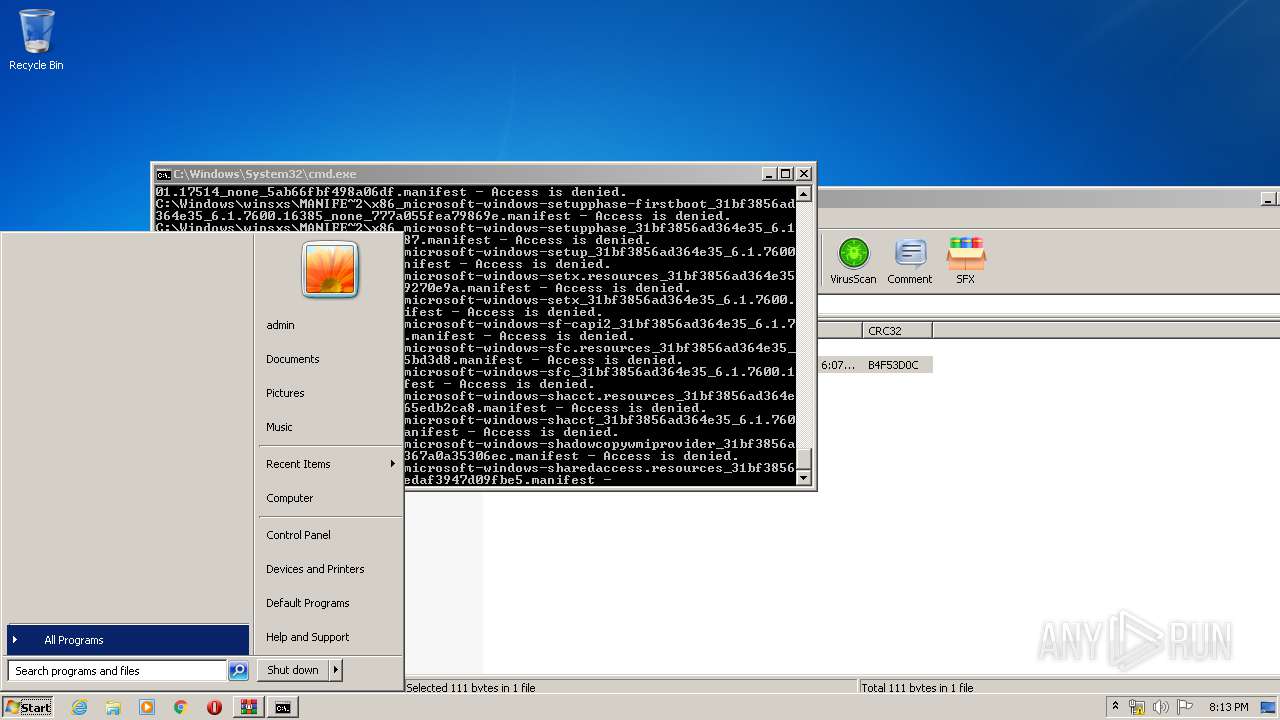
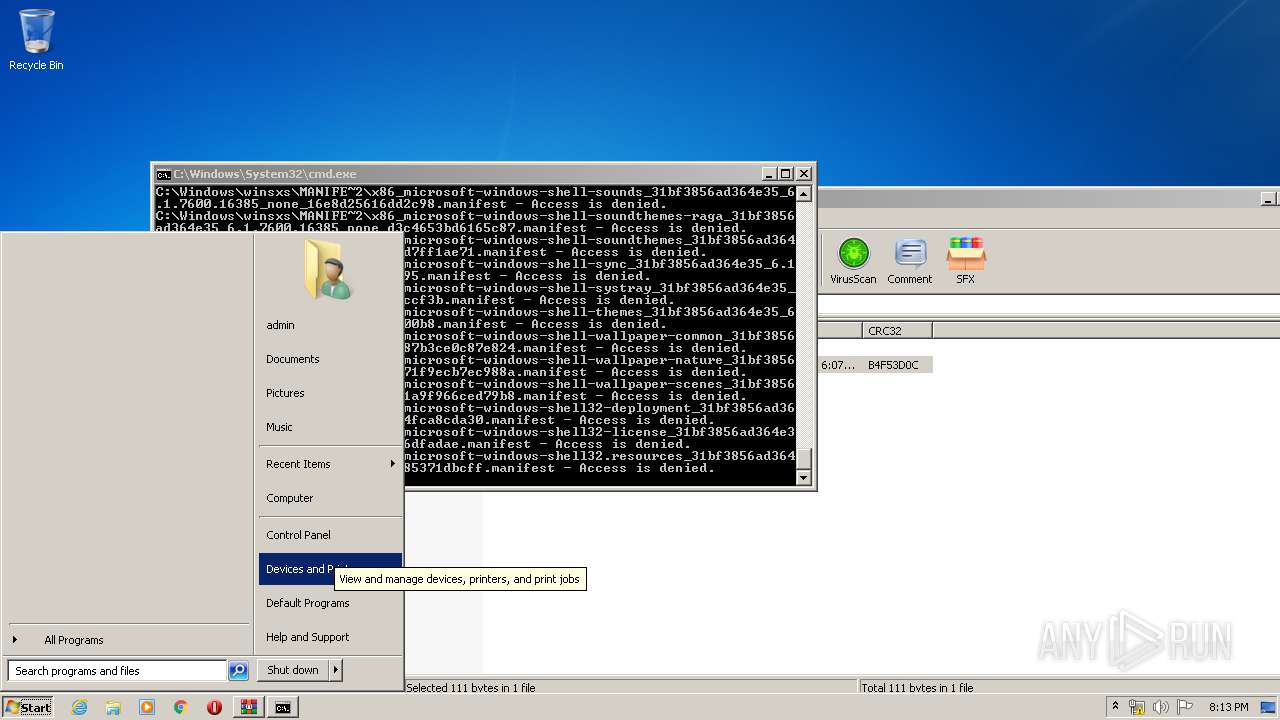
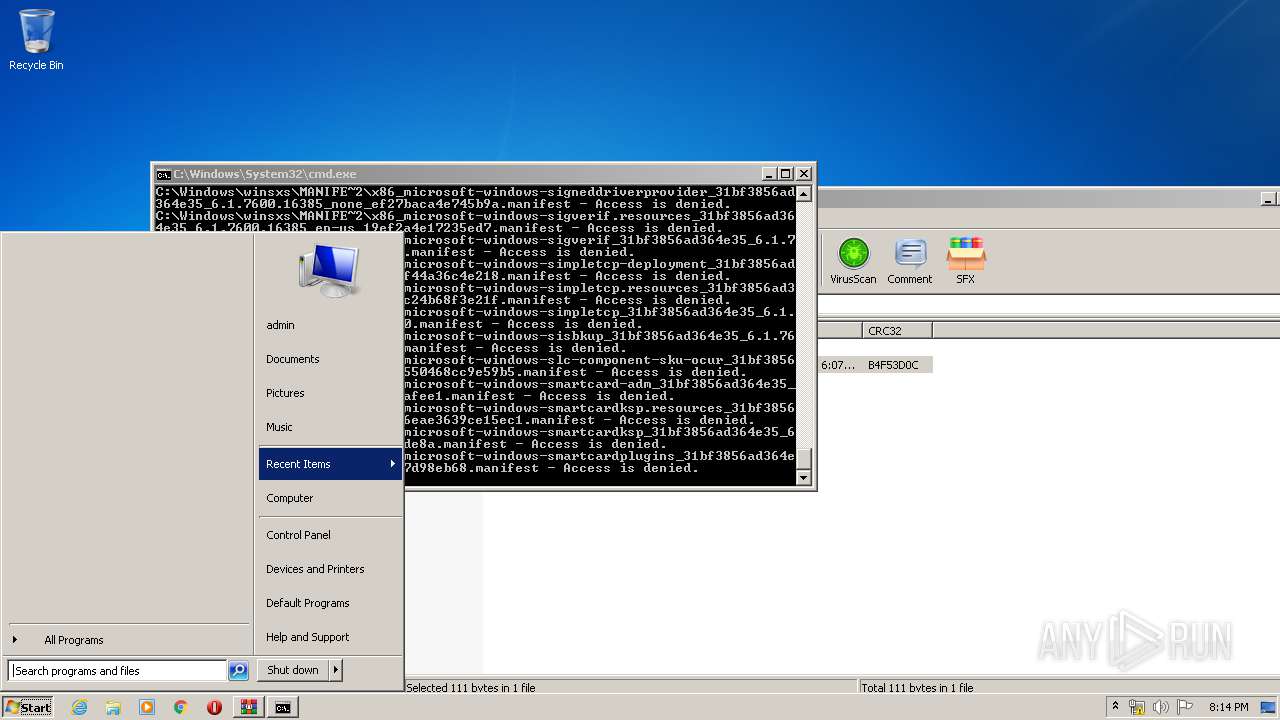
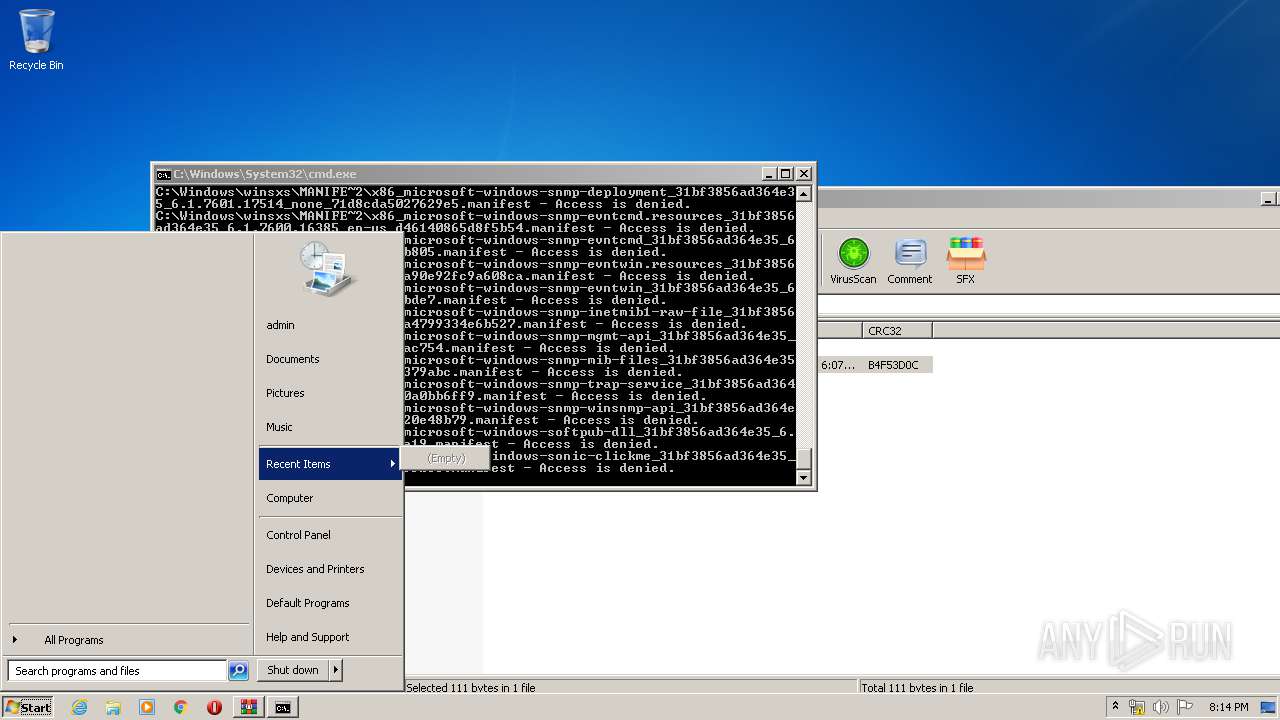
Manual execution by user
- cmd.exe (PID: 2816)
- taskmgr.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:30 19:07:05 |
| ZipCRC: | 0xb4f53d0c |
| ZipCompressedSize: | 97 |
| ZipUncompressedSize: | 111 |
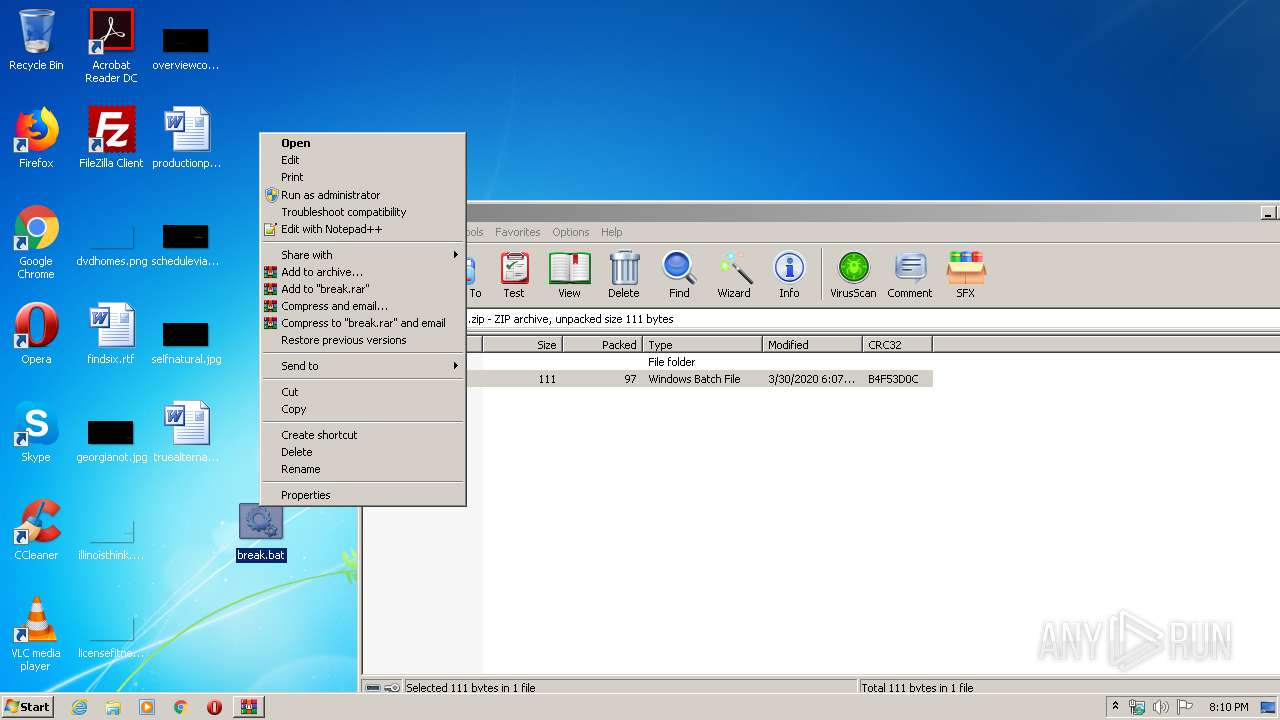
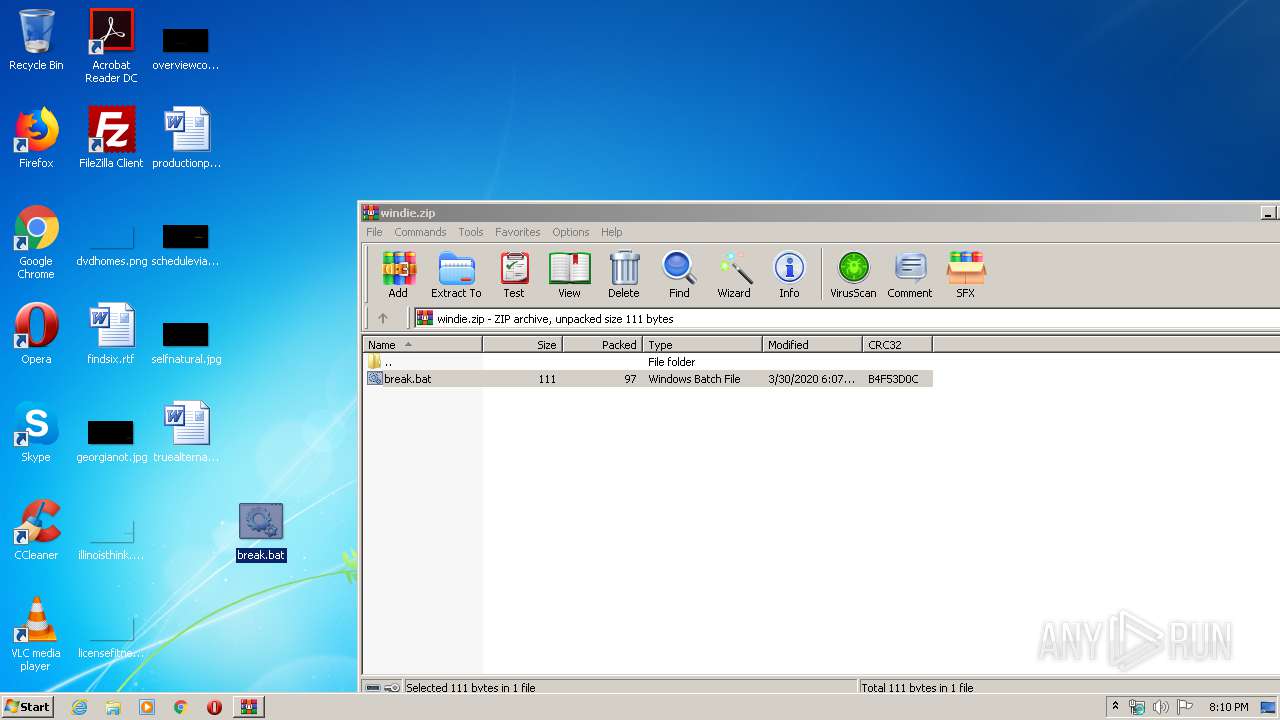
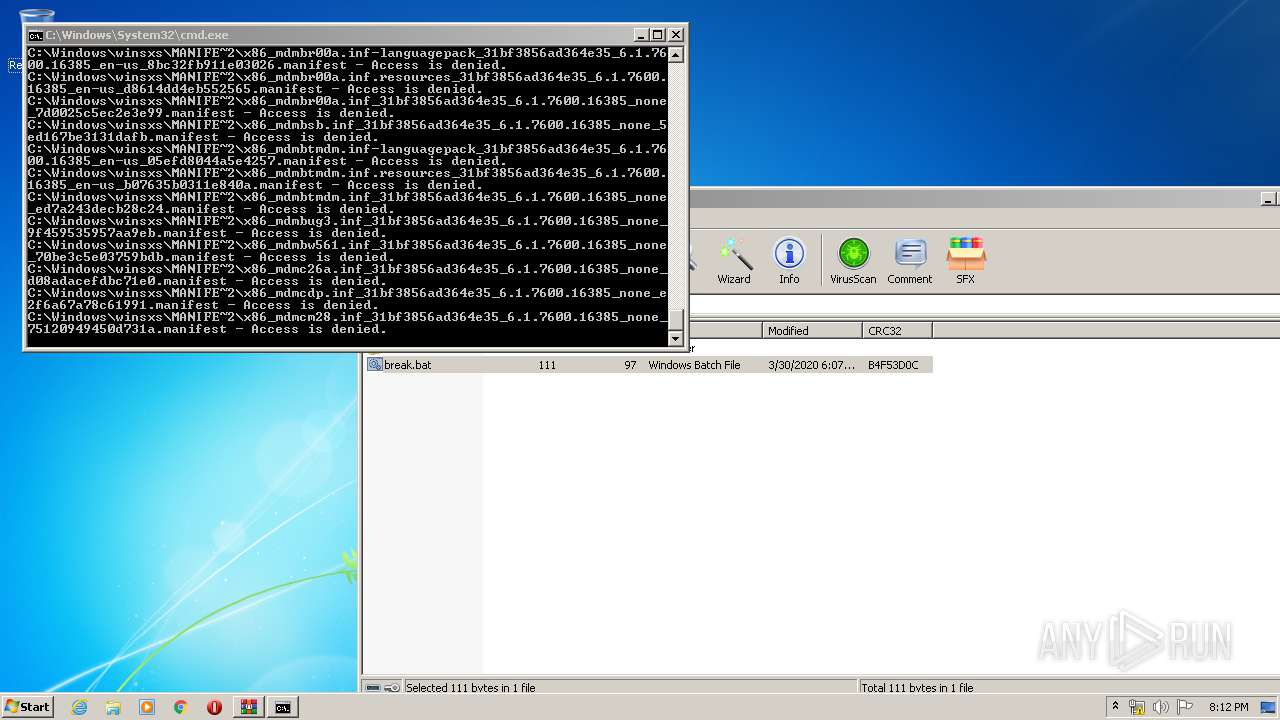
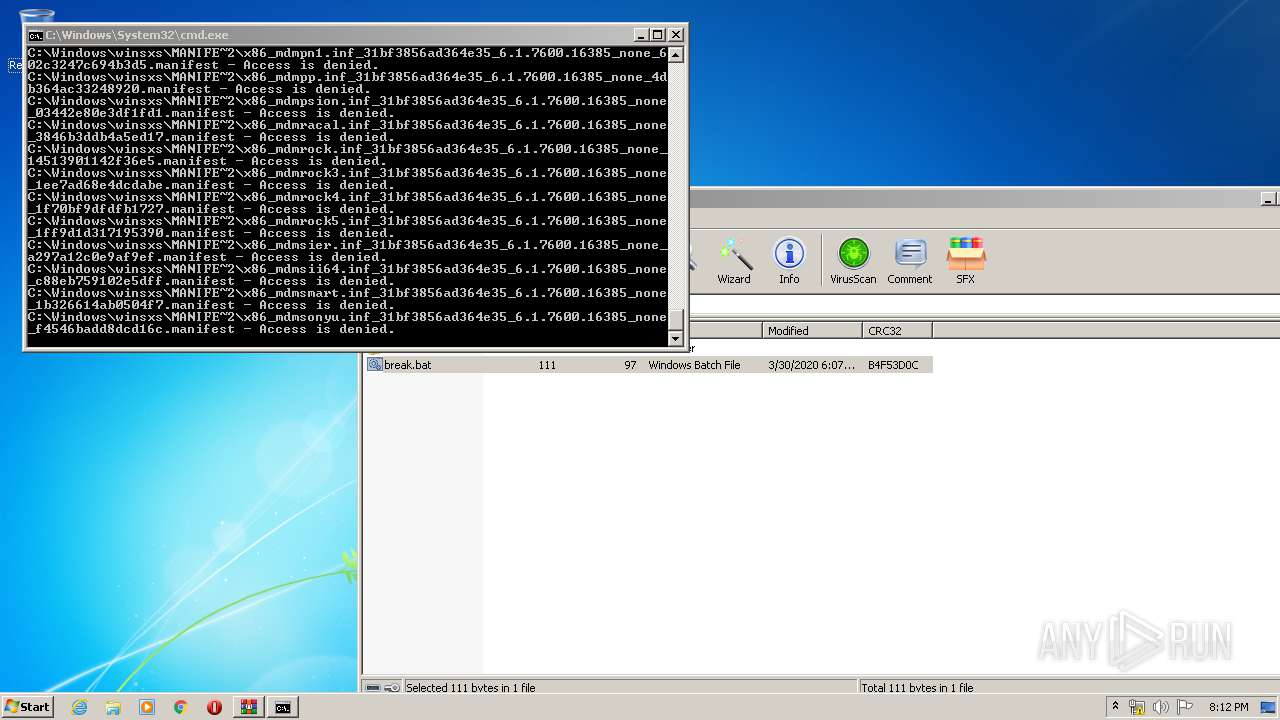
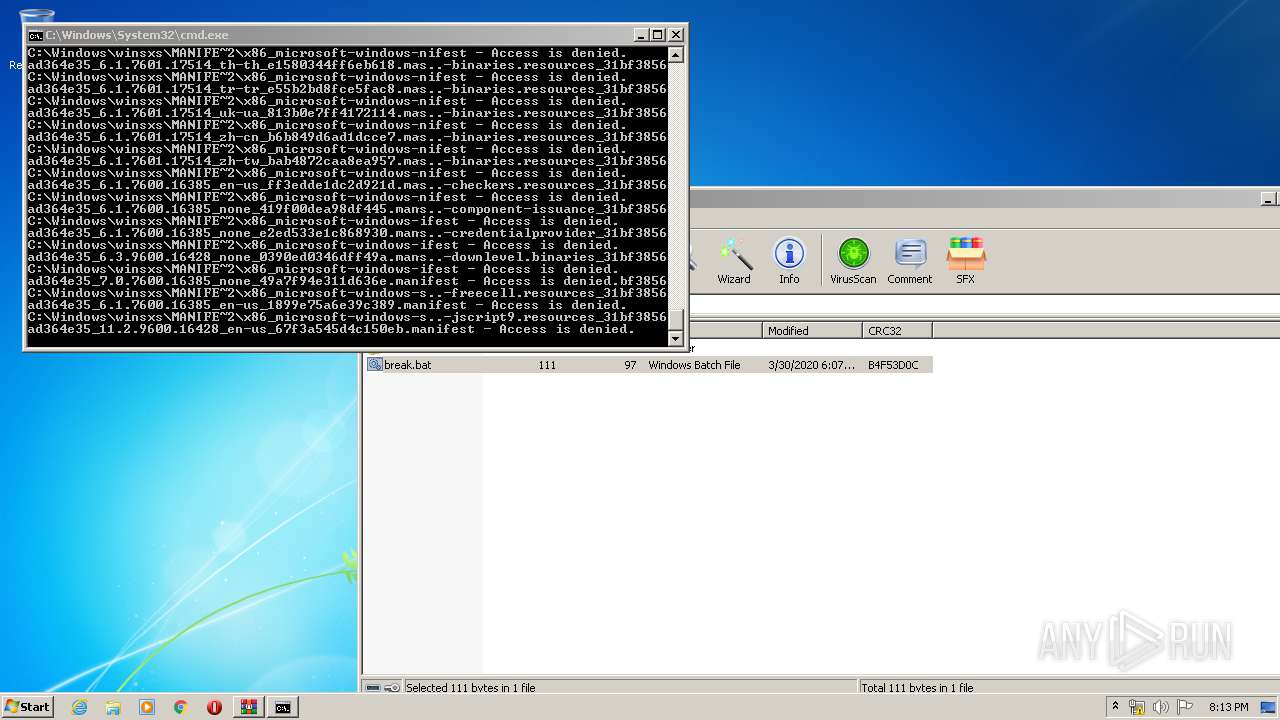
| ZipFileName: | break.bat |
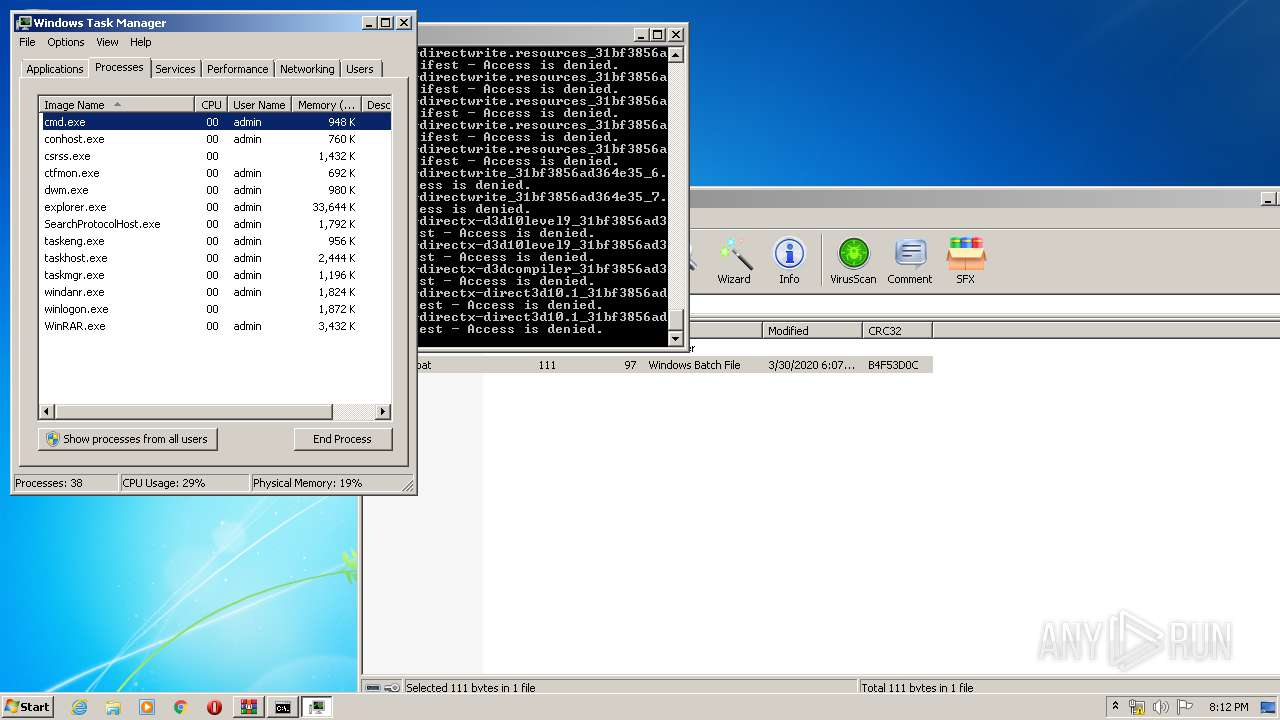
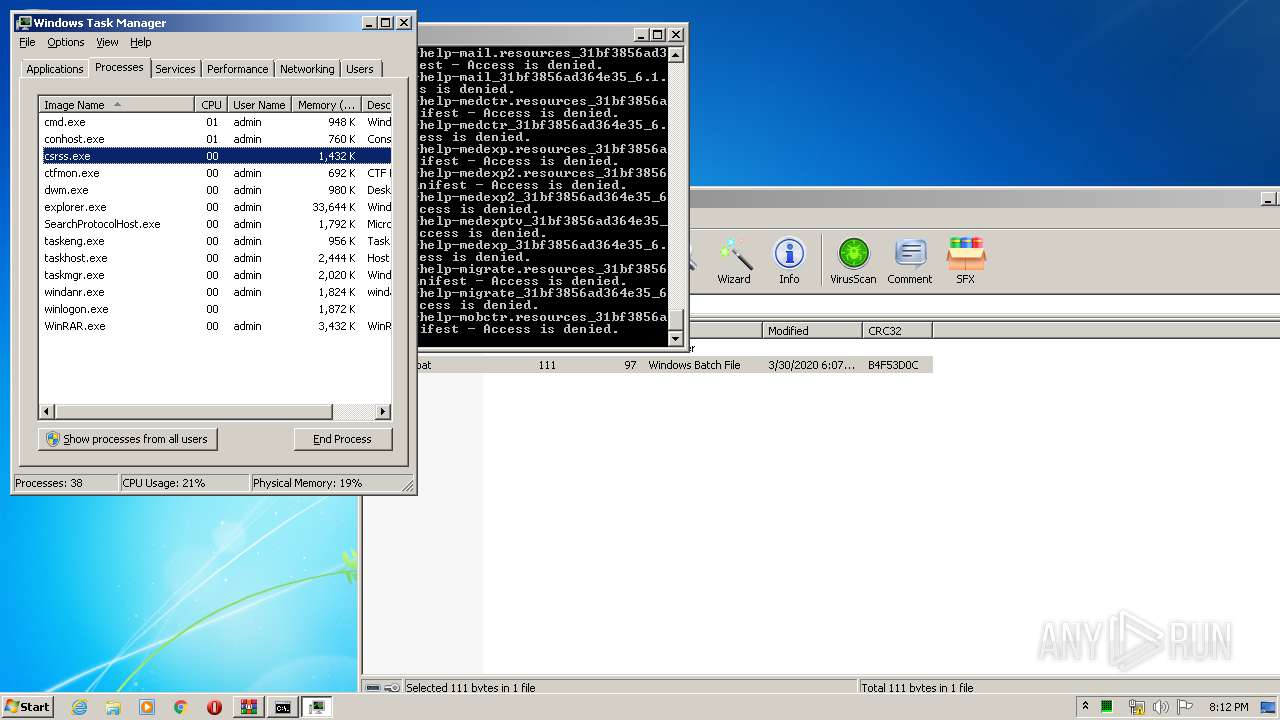
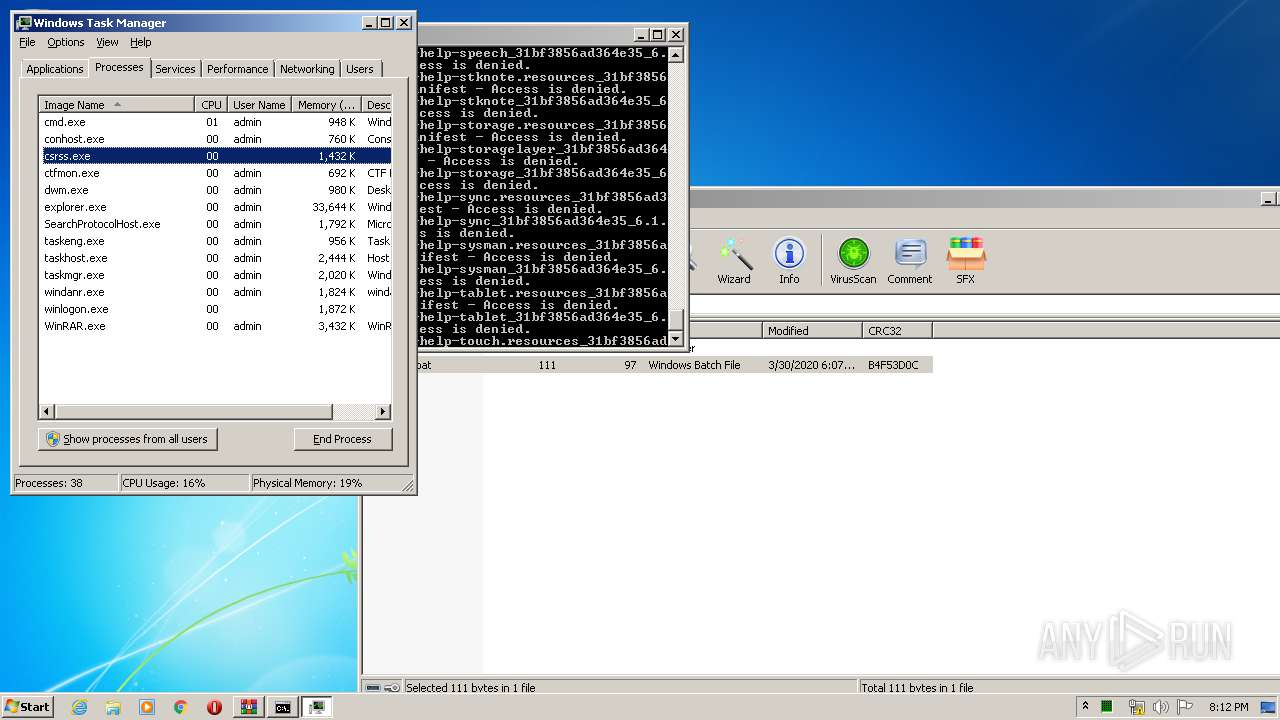
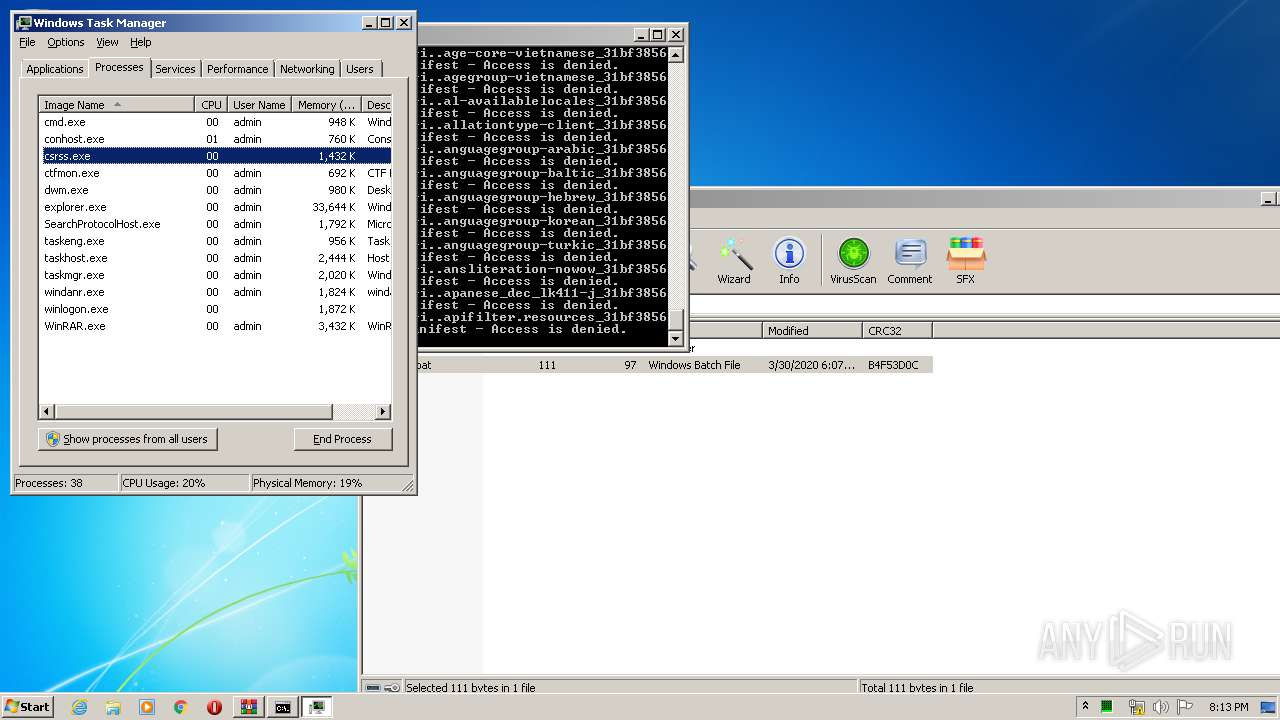
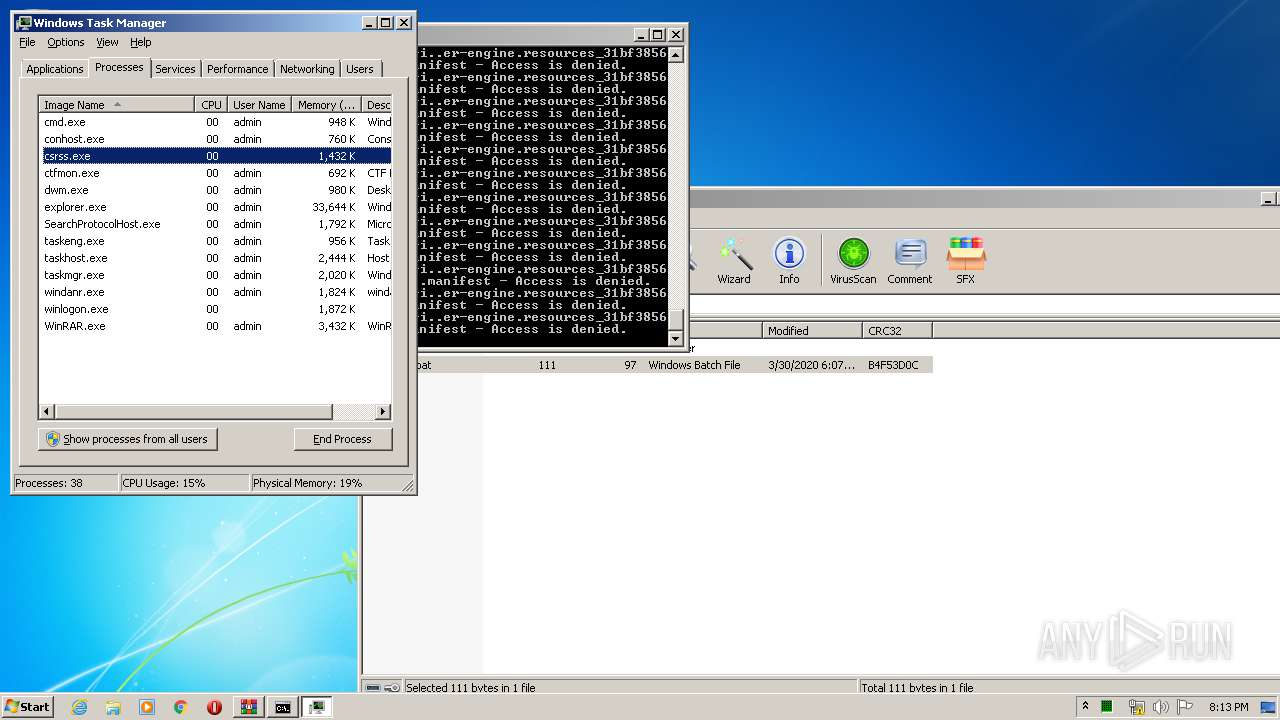
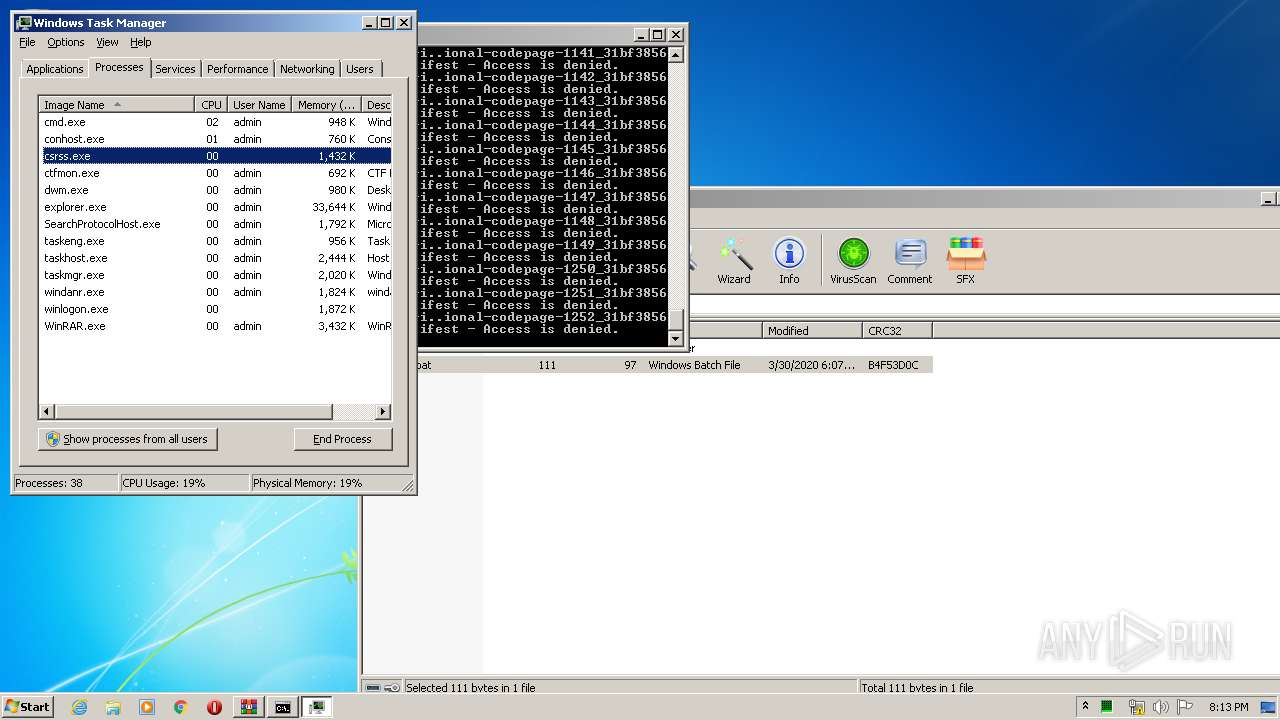
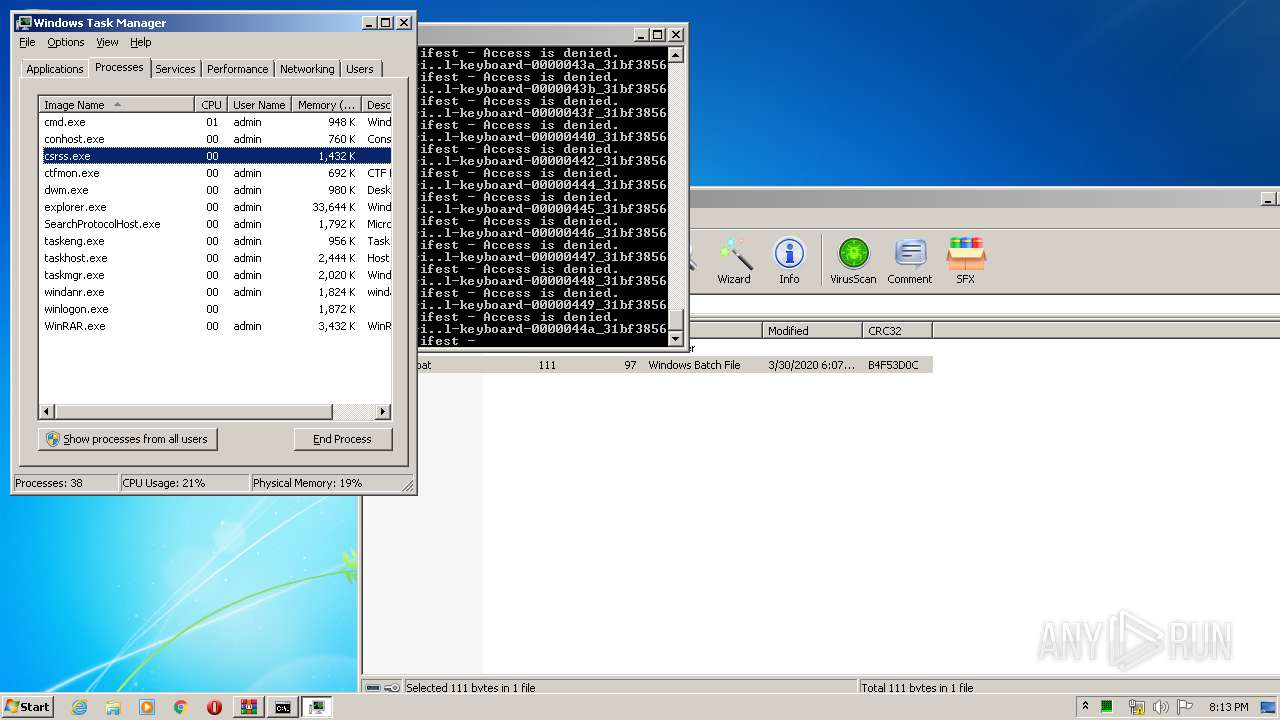
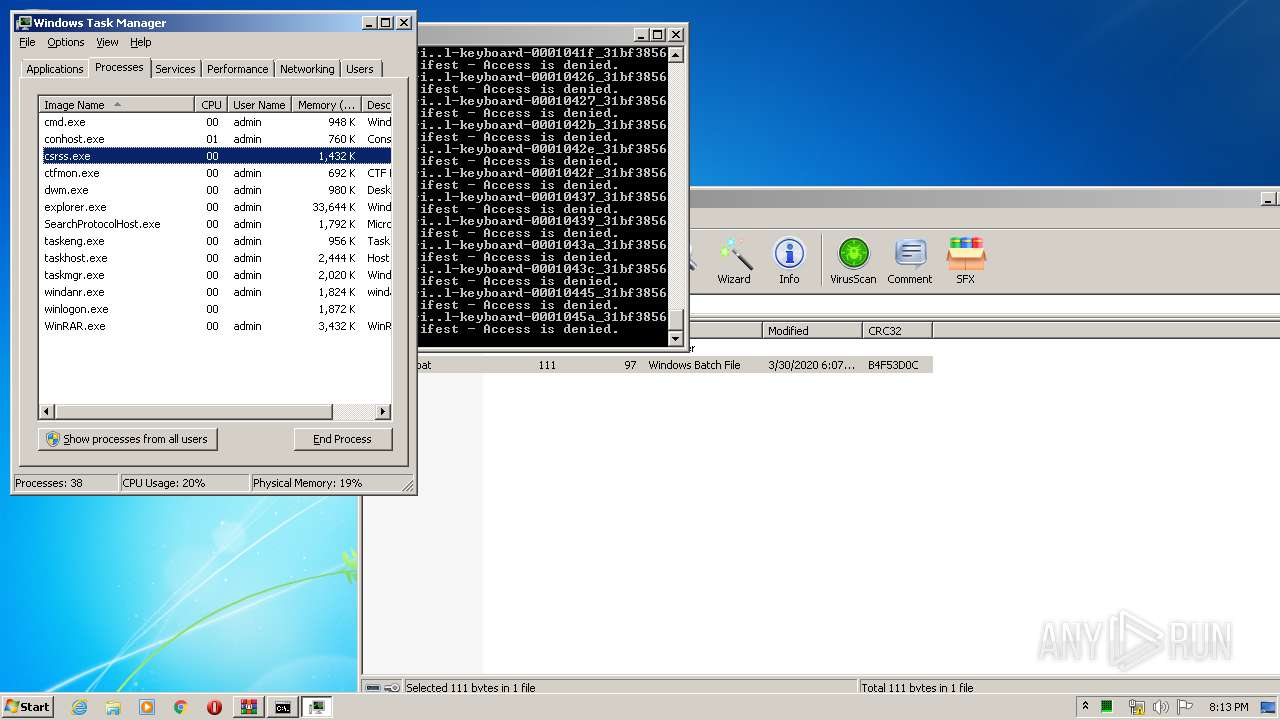
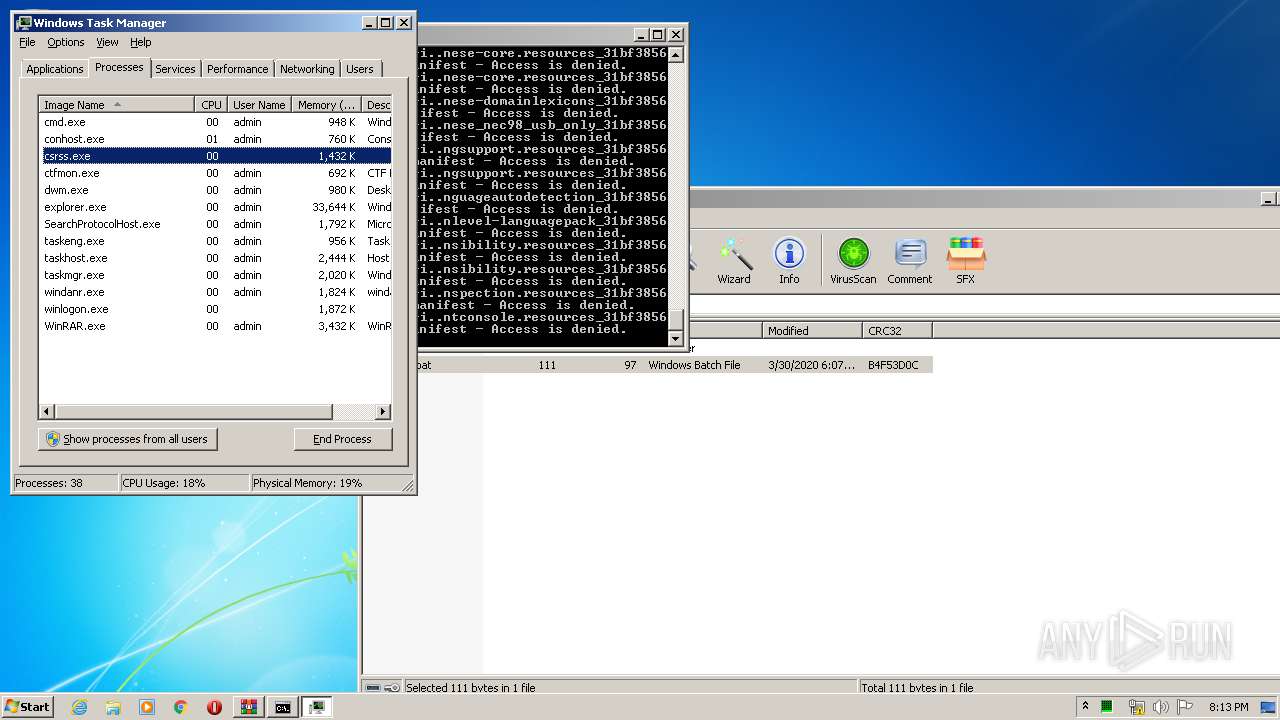
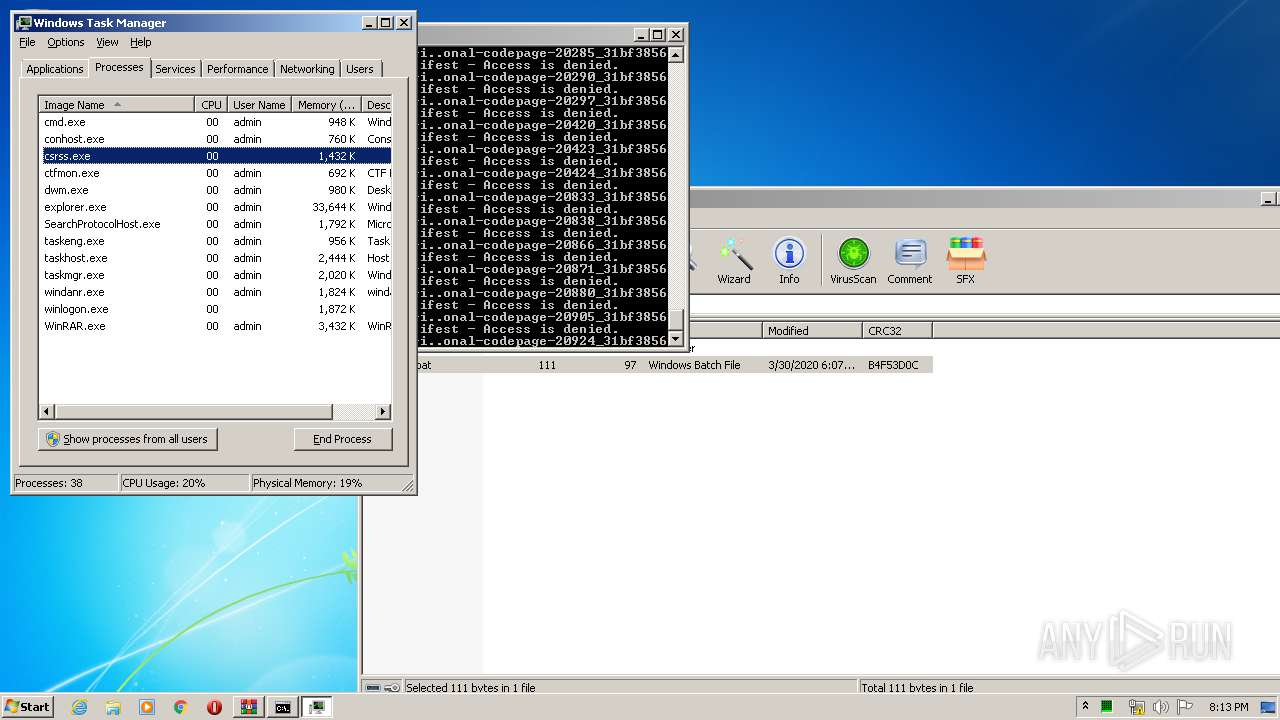
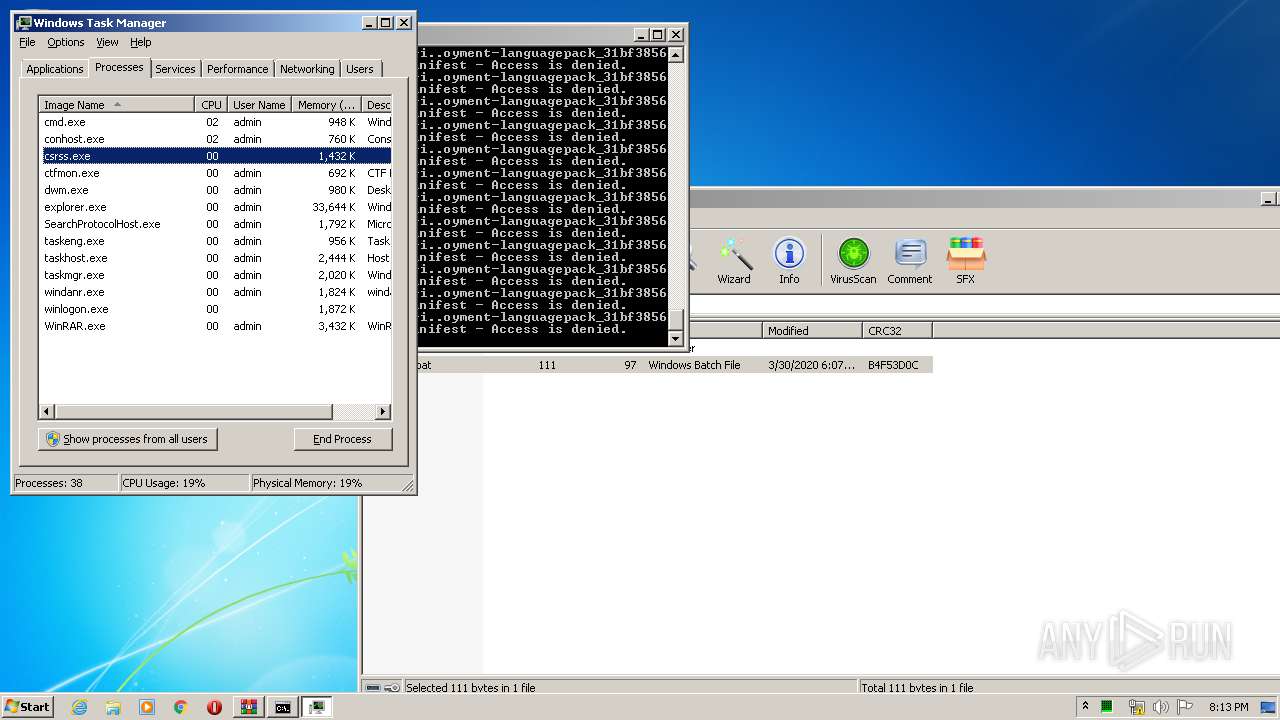
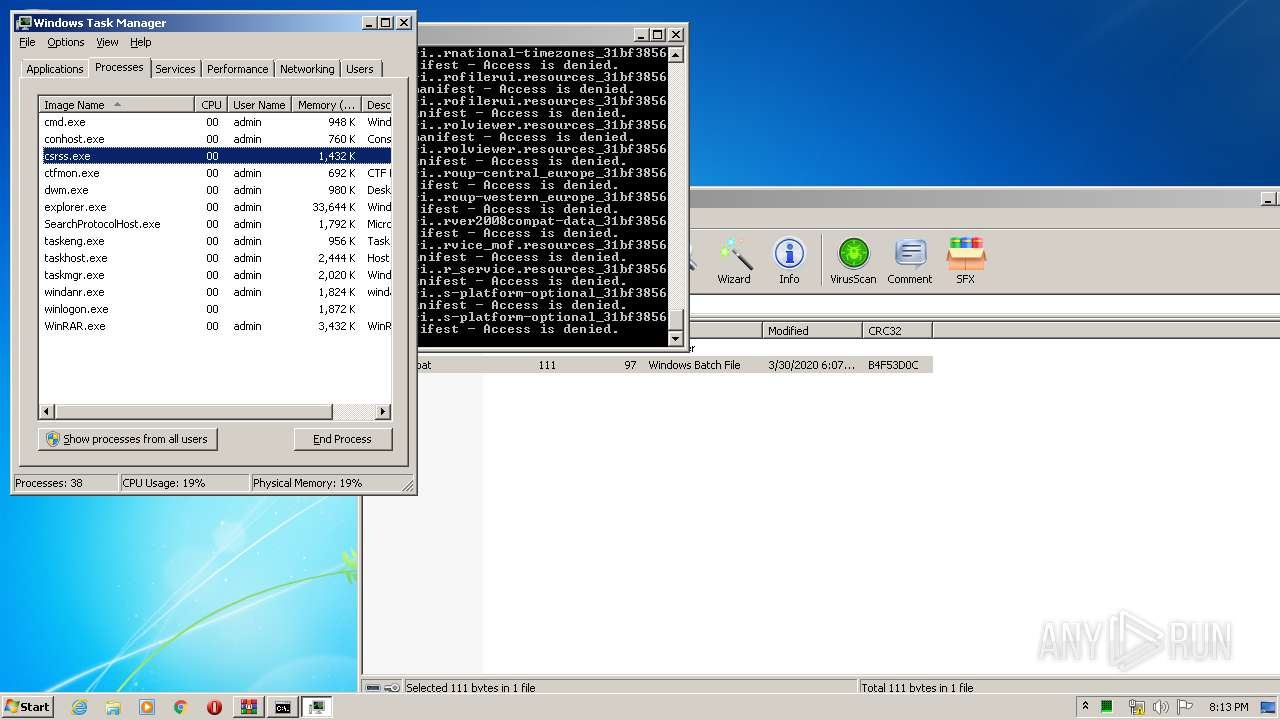
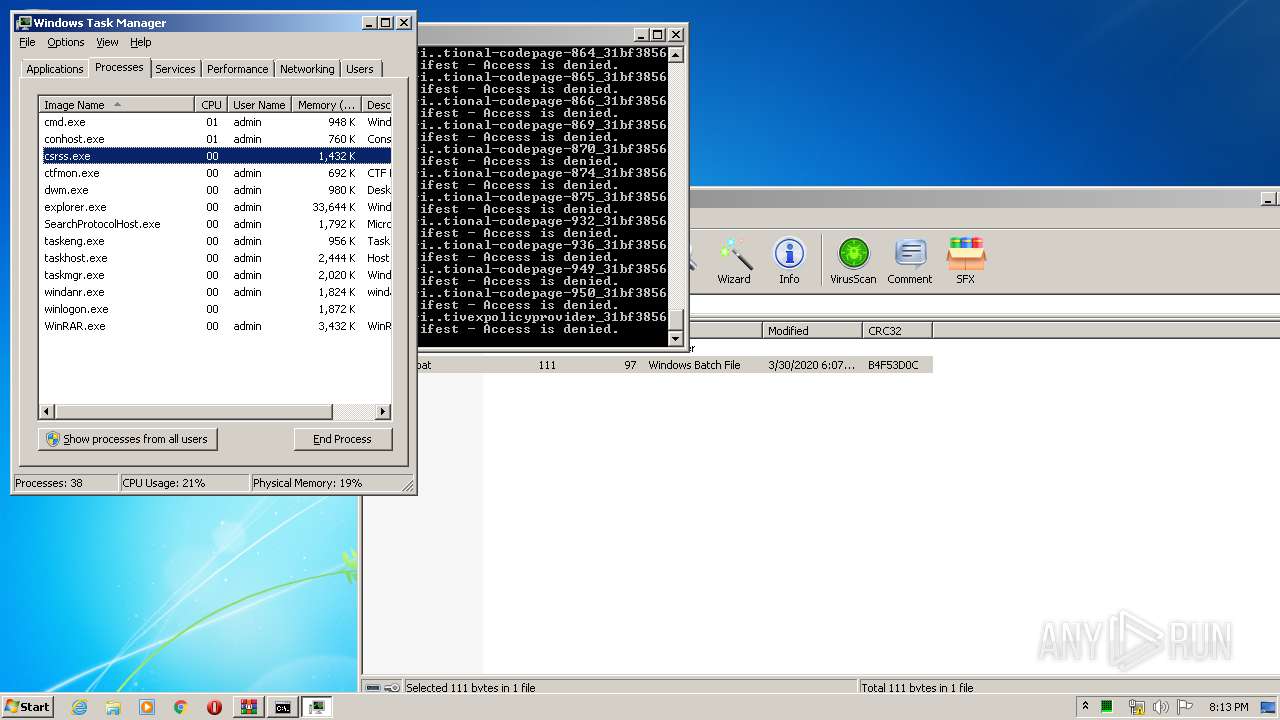
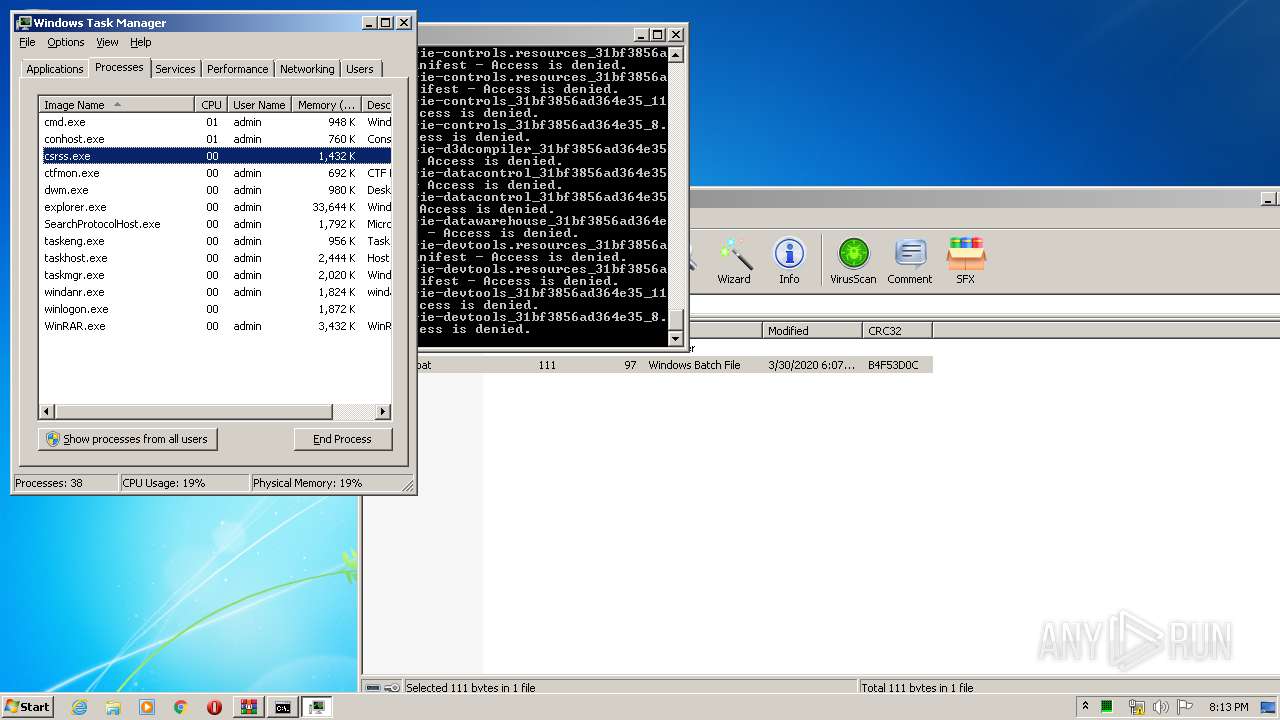
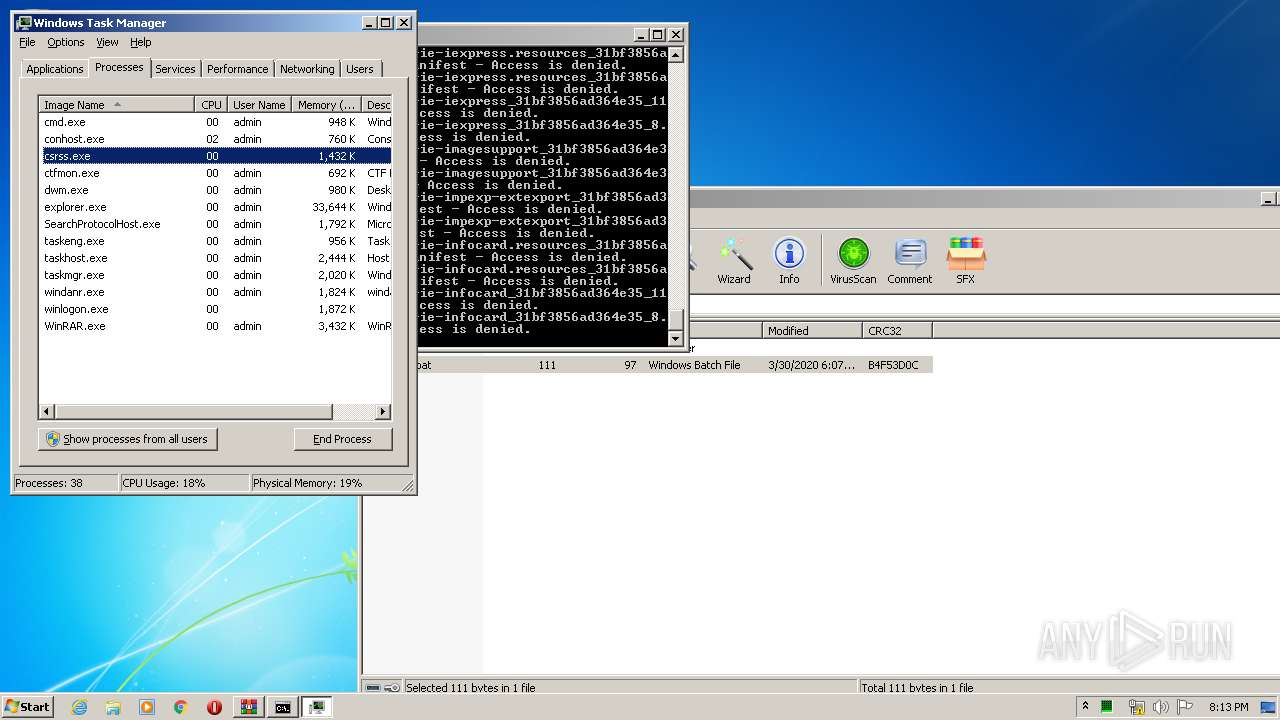
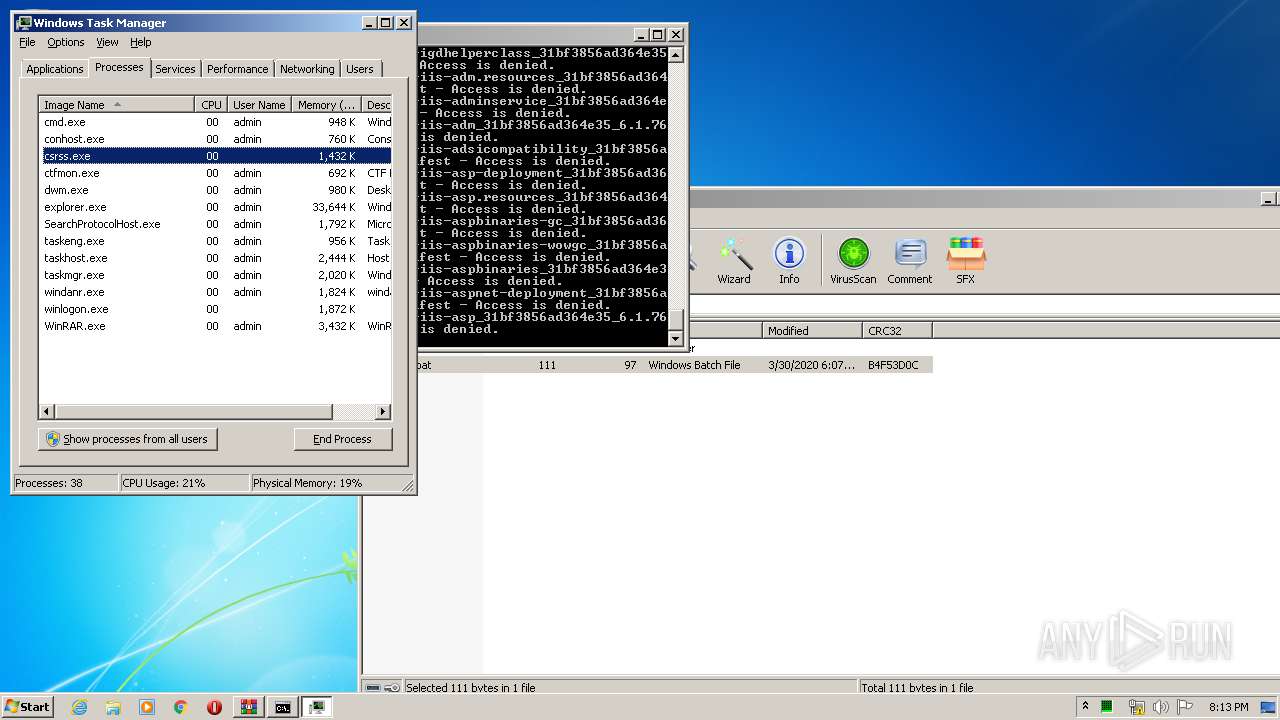
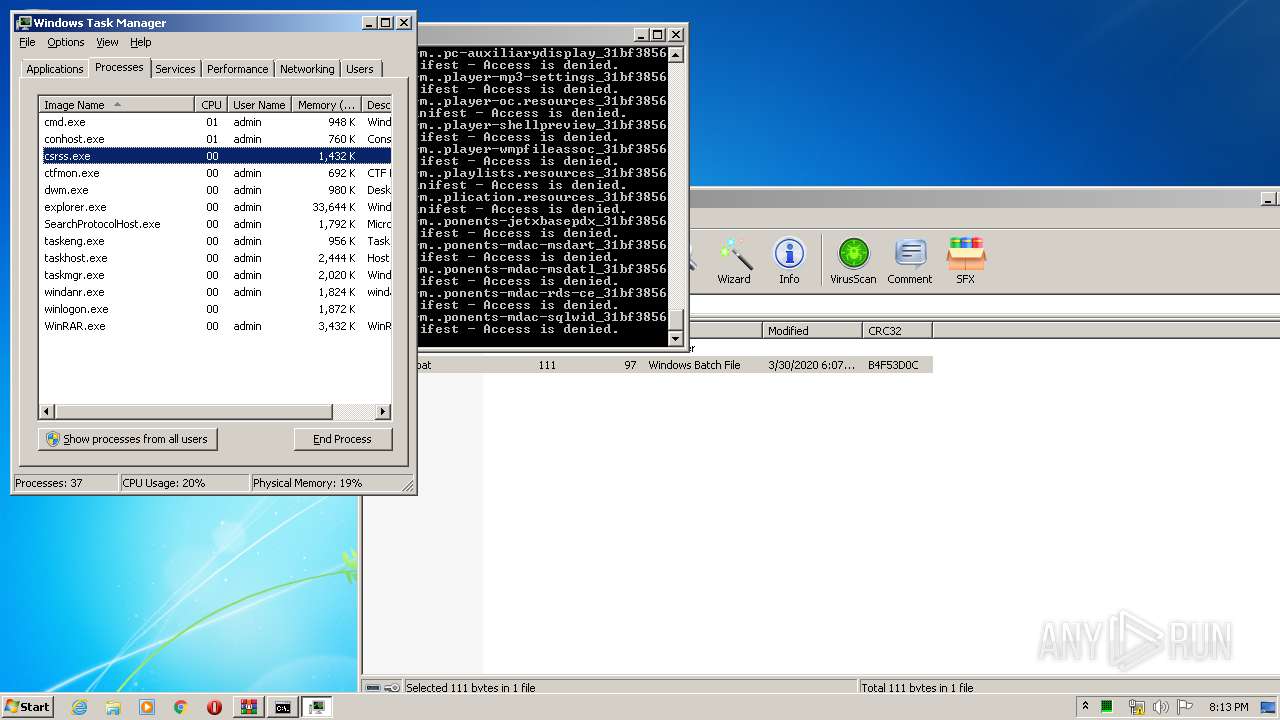
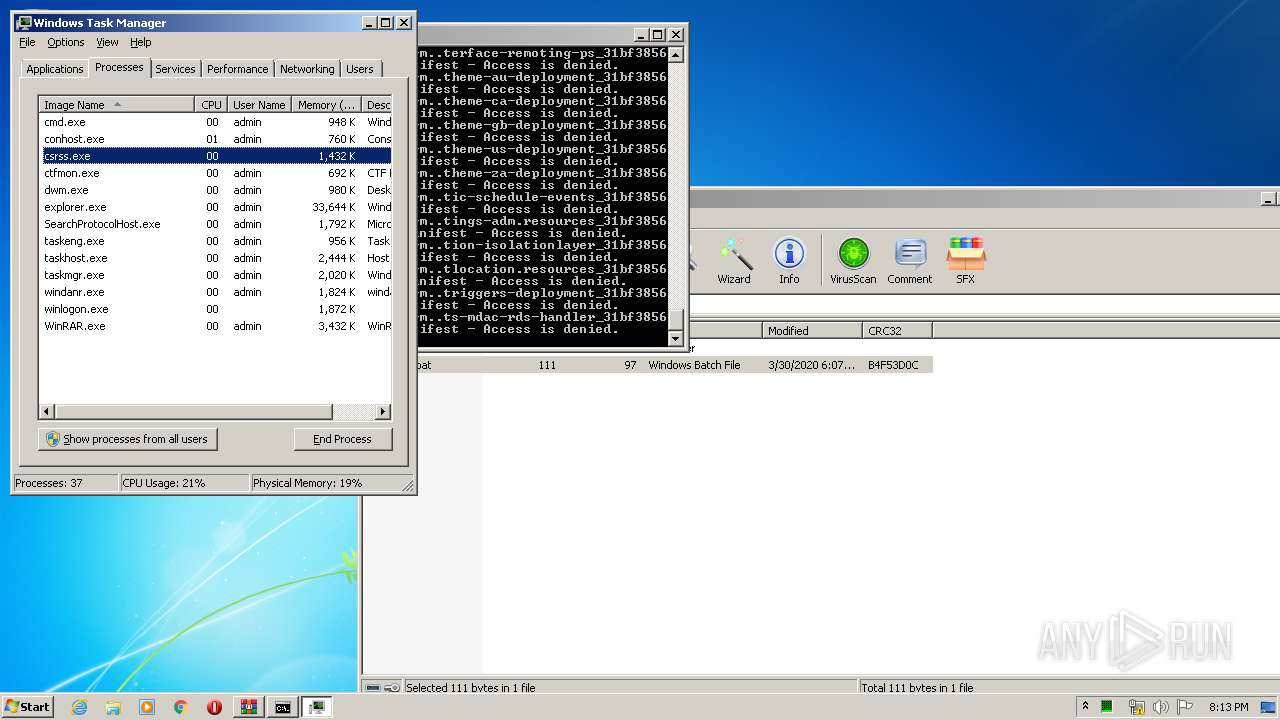
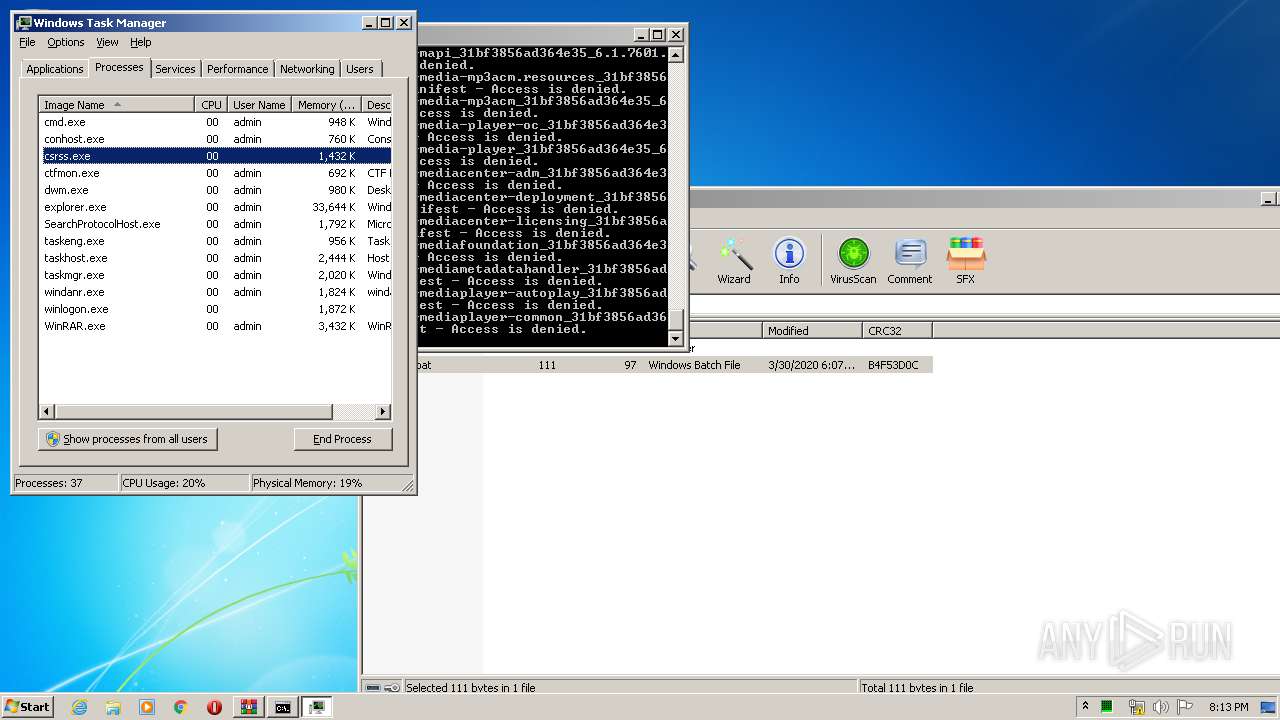
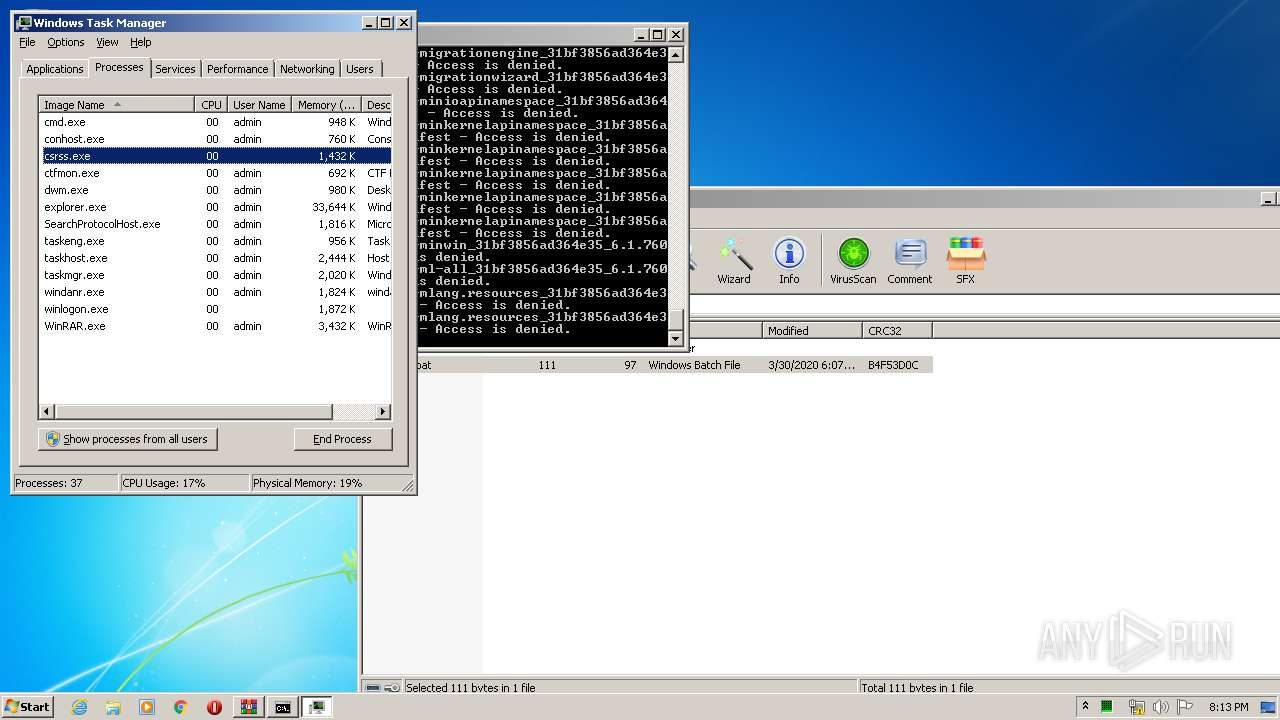
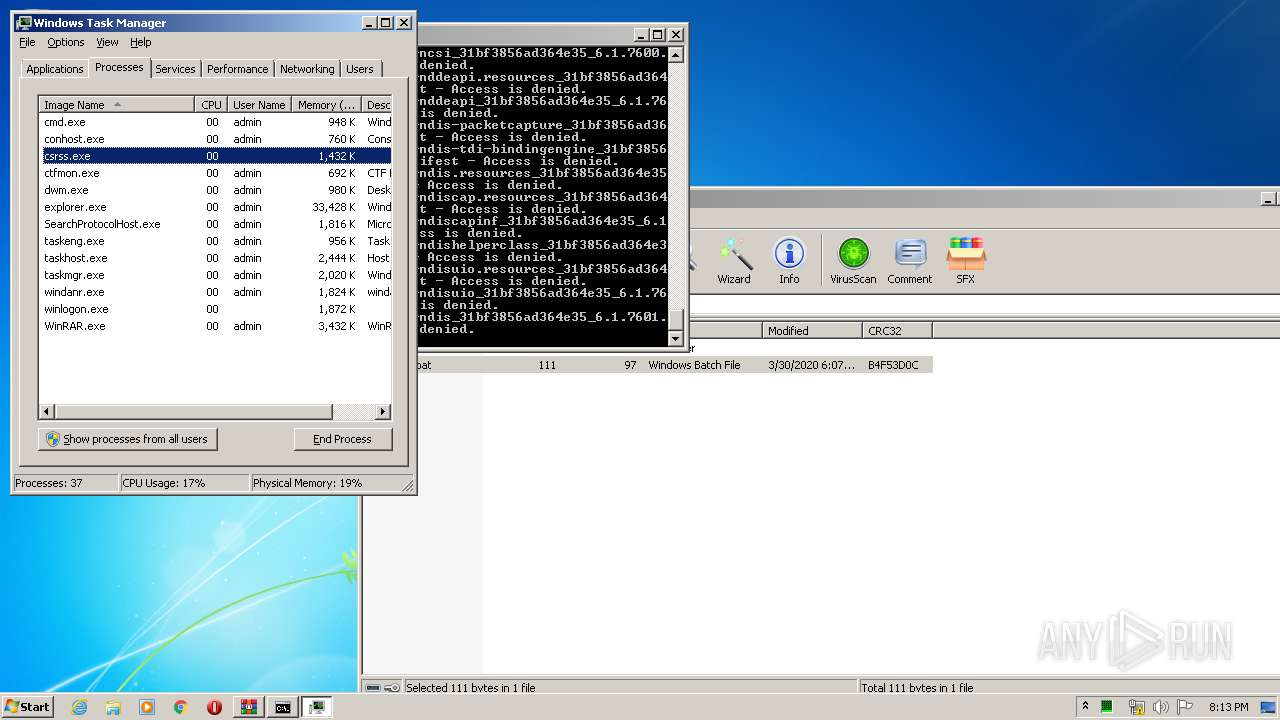
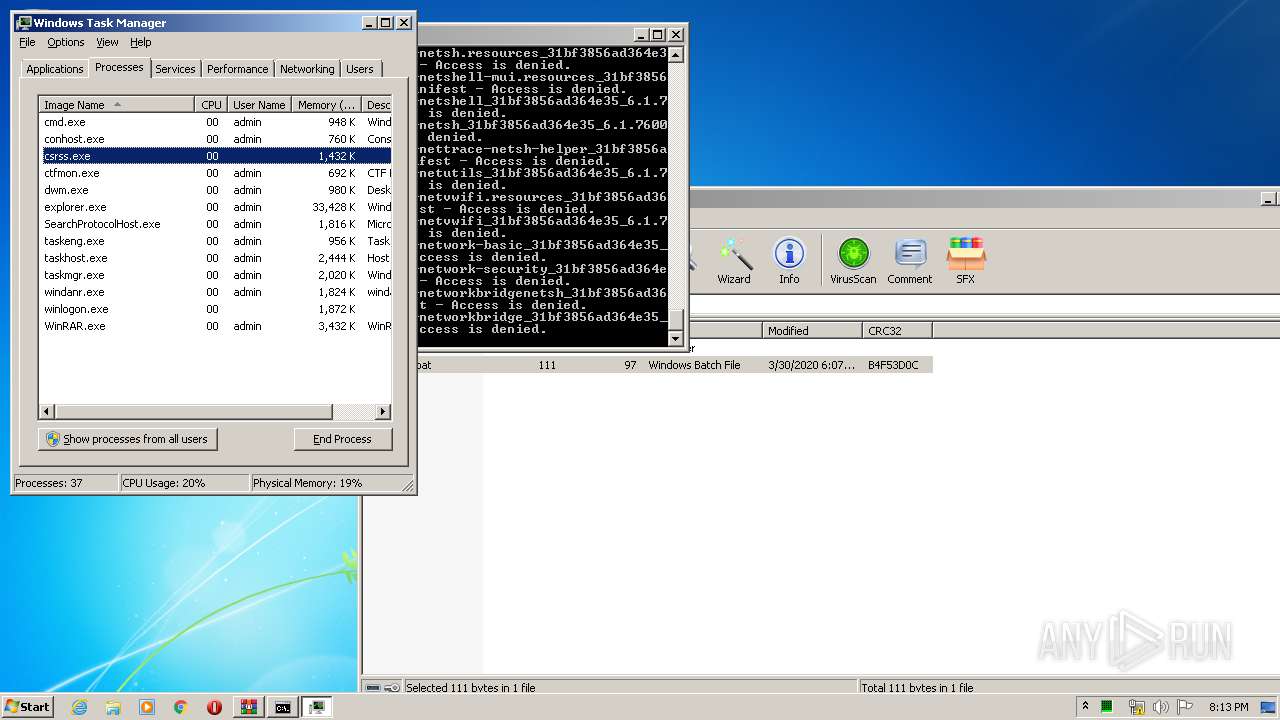
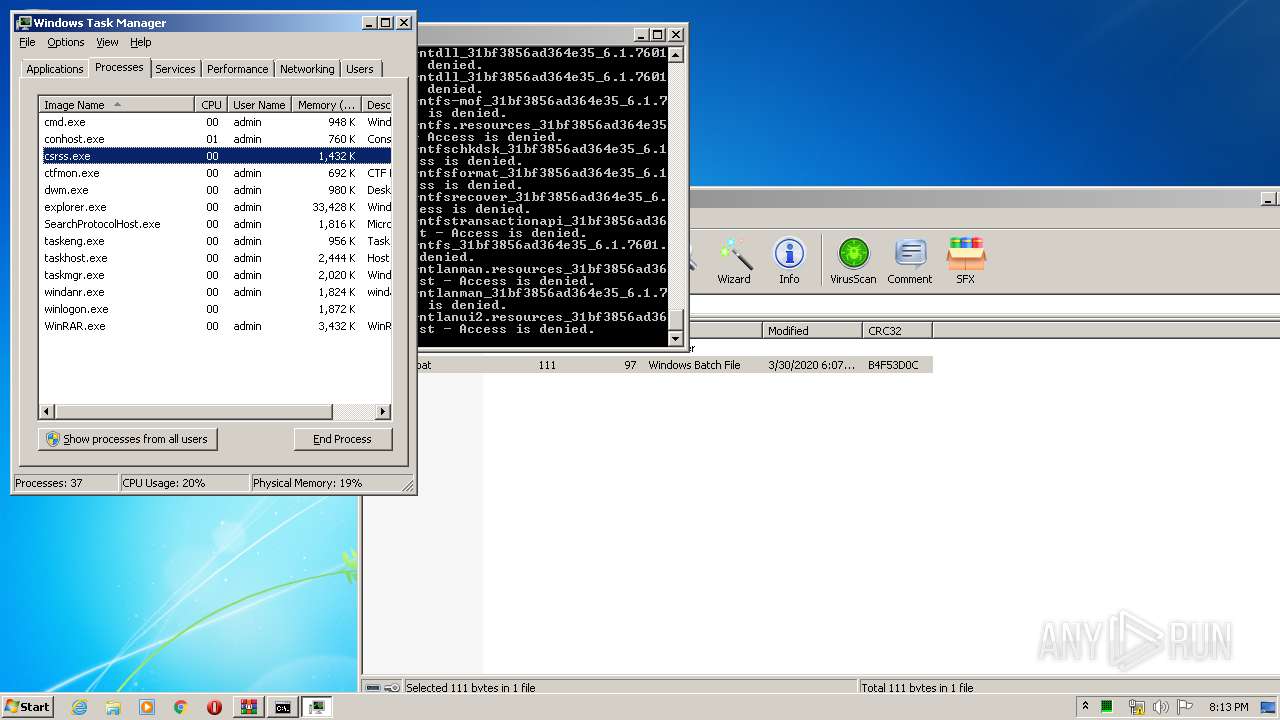
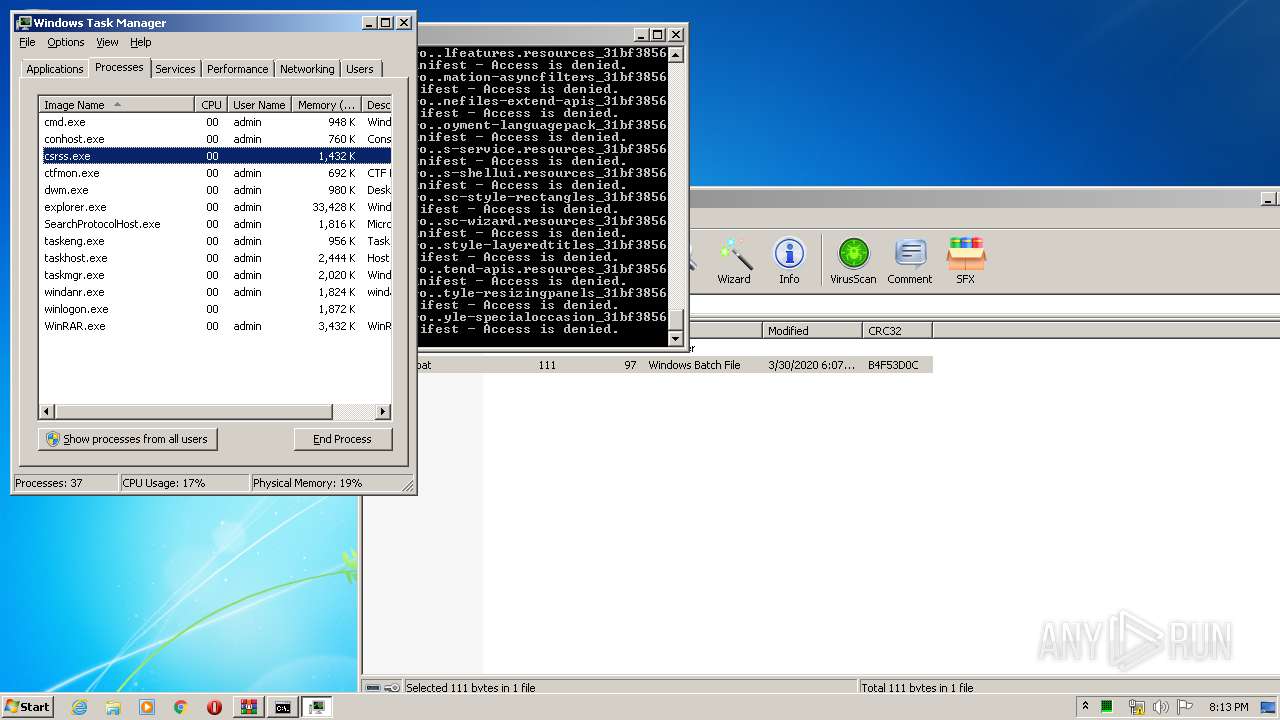
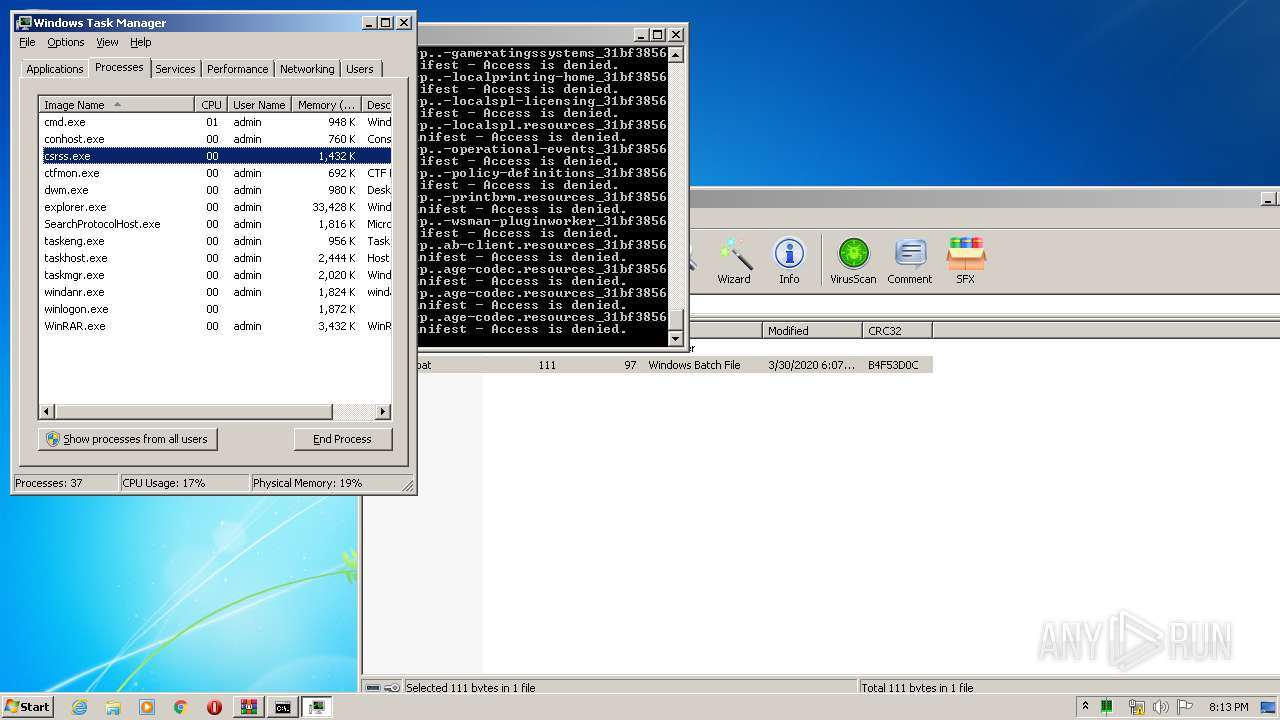
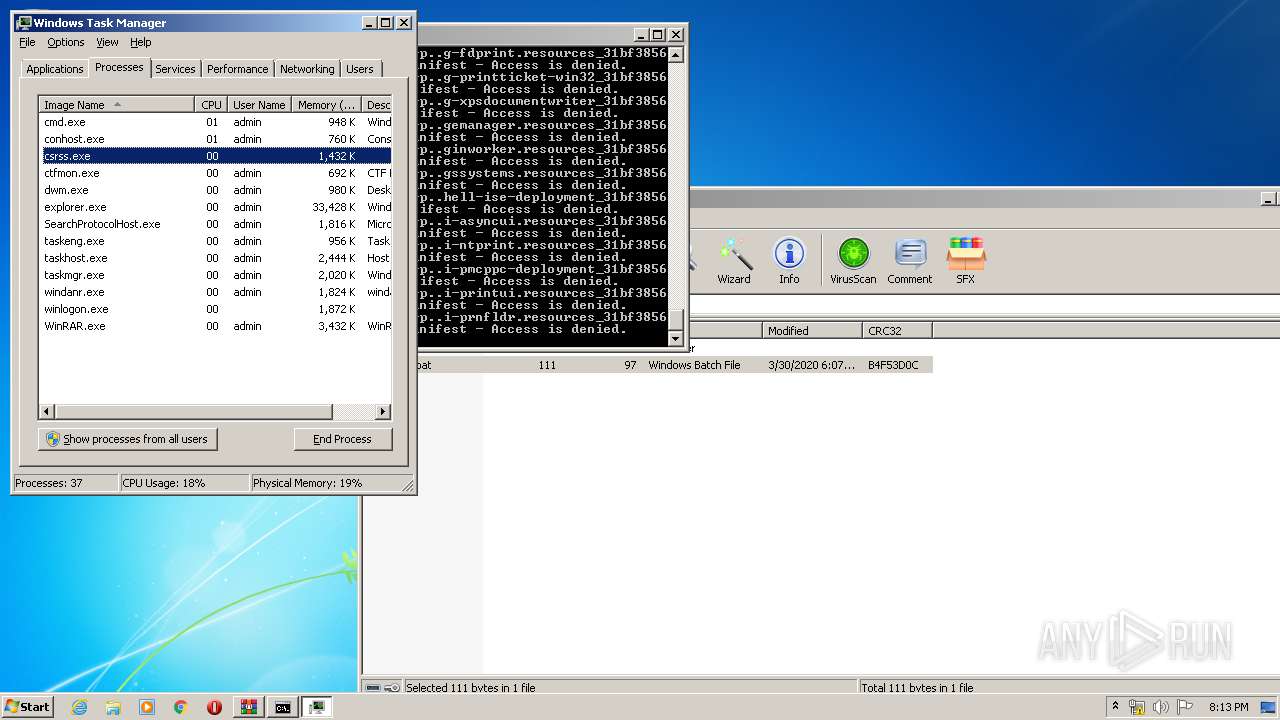
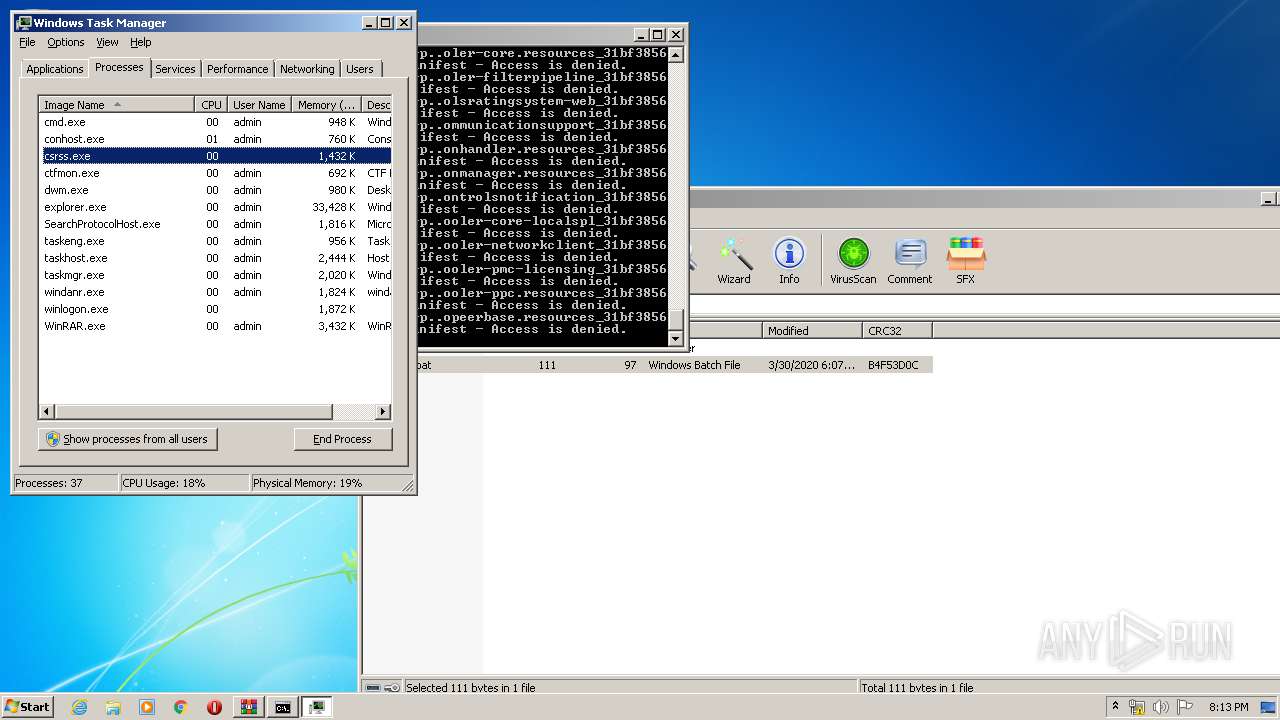
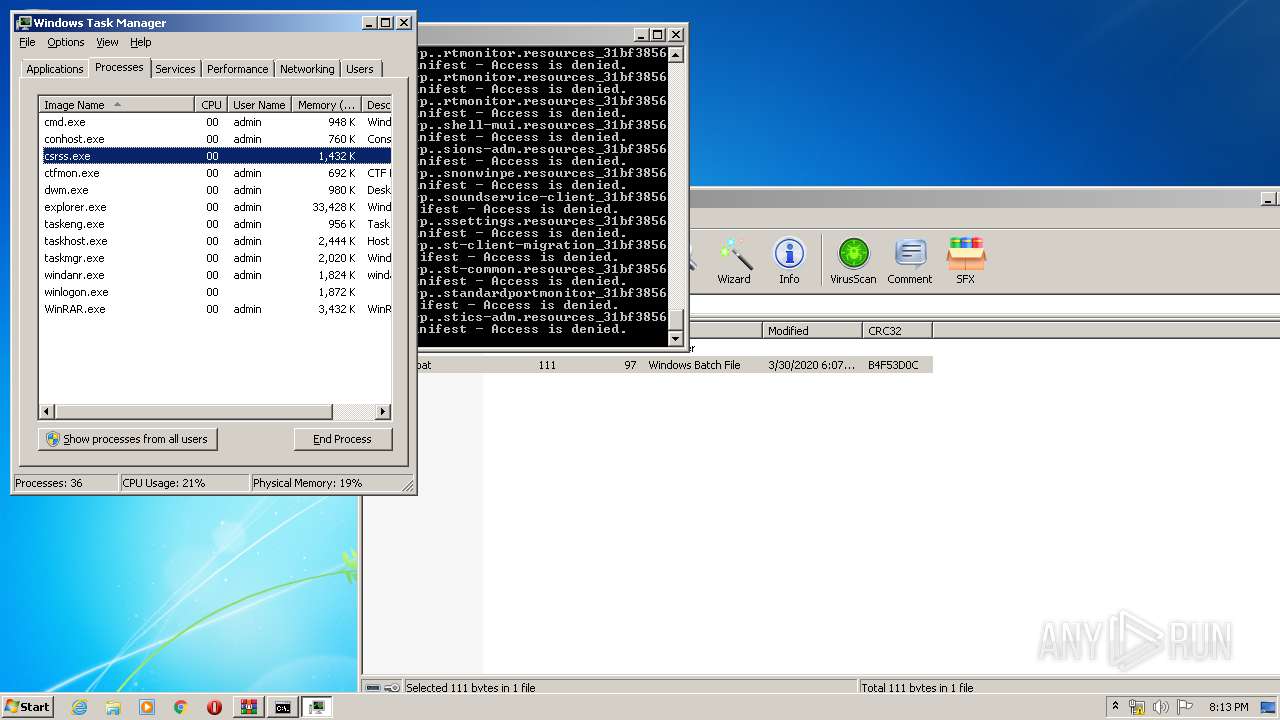
Total processes
50
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1548 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1900 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10002 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
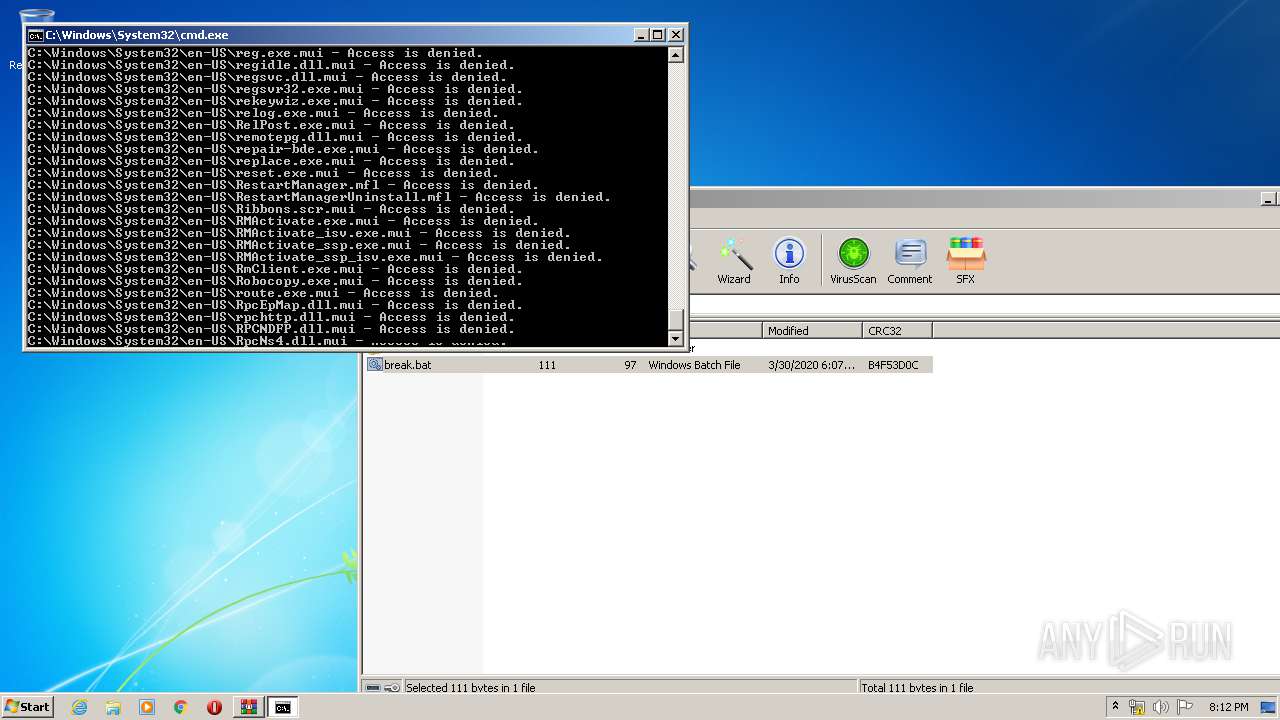
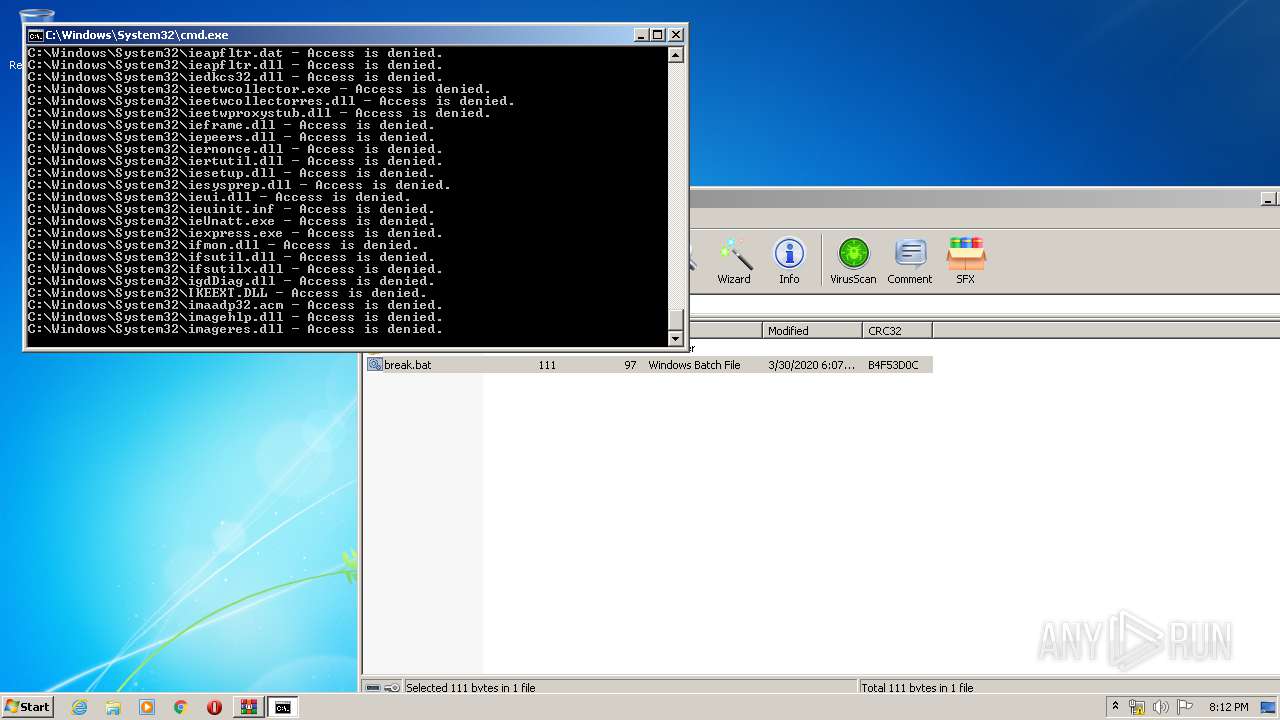
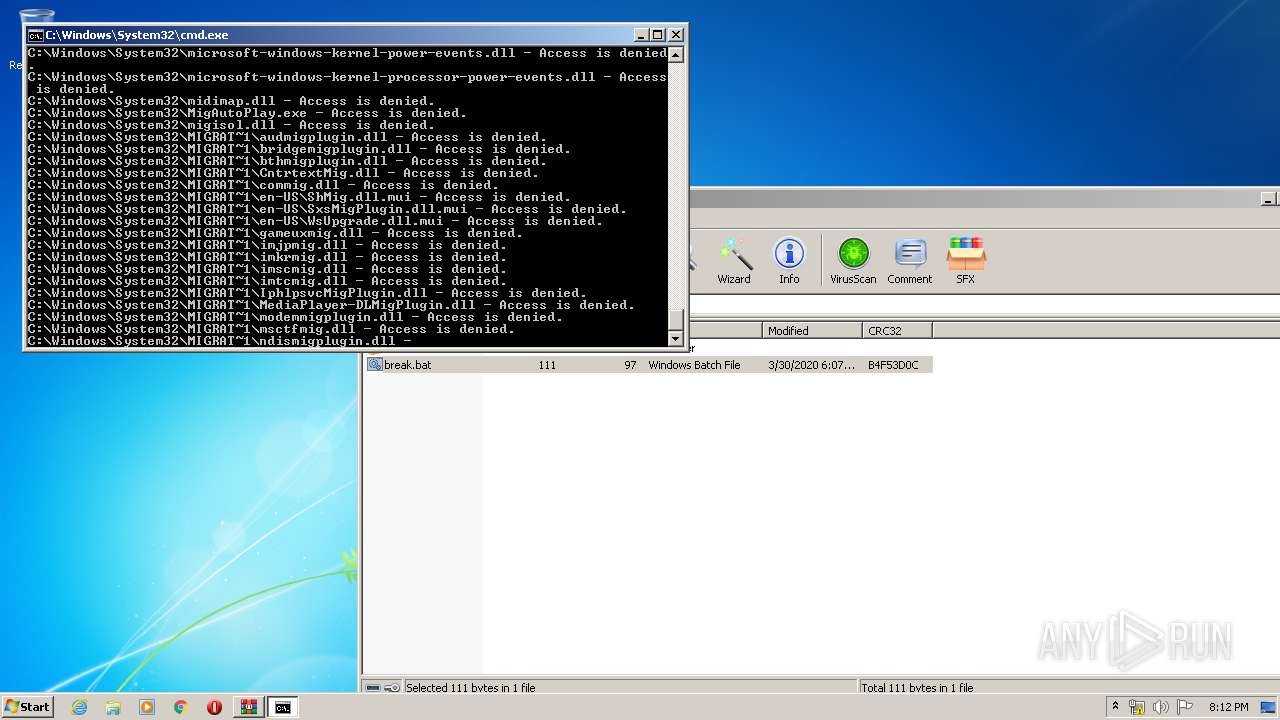
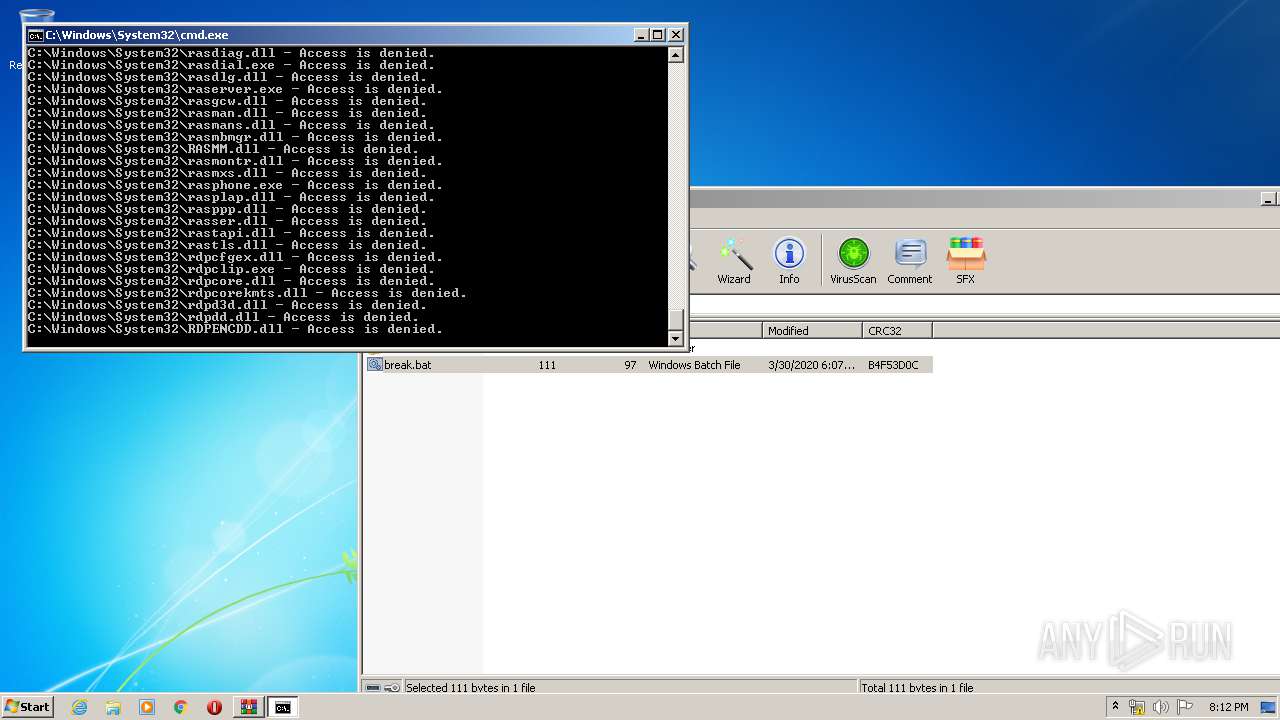
| 2816 | "C:\Windows\System32\cmd.exe" /C "C:\Users\admin\Desktop\break.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3052 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\windie.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3112 | timeout 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe1_ Global\UsGthrCtrlFltPipeMssGthrPipe1 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Windows\system32\SearchFilterHost.exe" 0 520 524 532 65536 528 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 631
Read events
1 988
Write events
1 436
Delete events
207
Modification events
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\windie.zip | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (1548) SearchIndexer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Search\Tracing\EventThrottleState |
| Operation: | delete value | Name: | 000003f5 |
Value: 01000000EAD2EB8E040C00000200000000000000 | |||
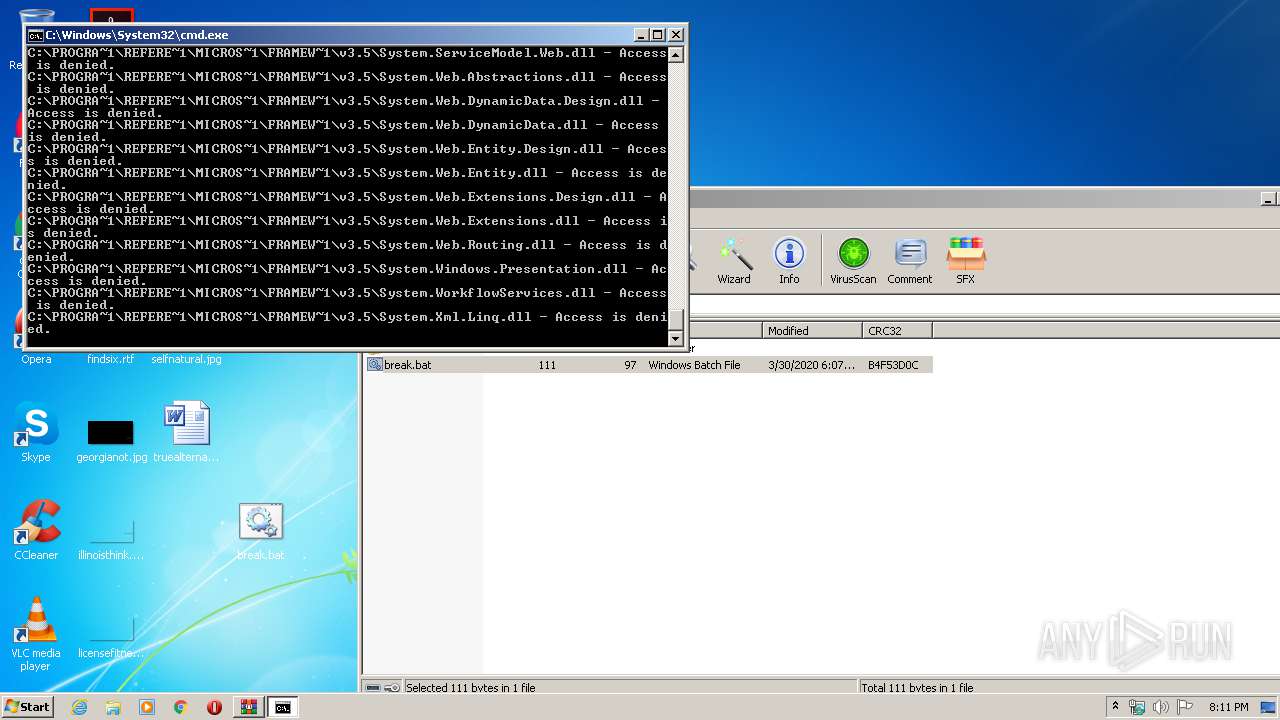
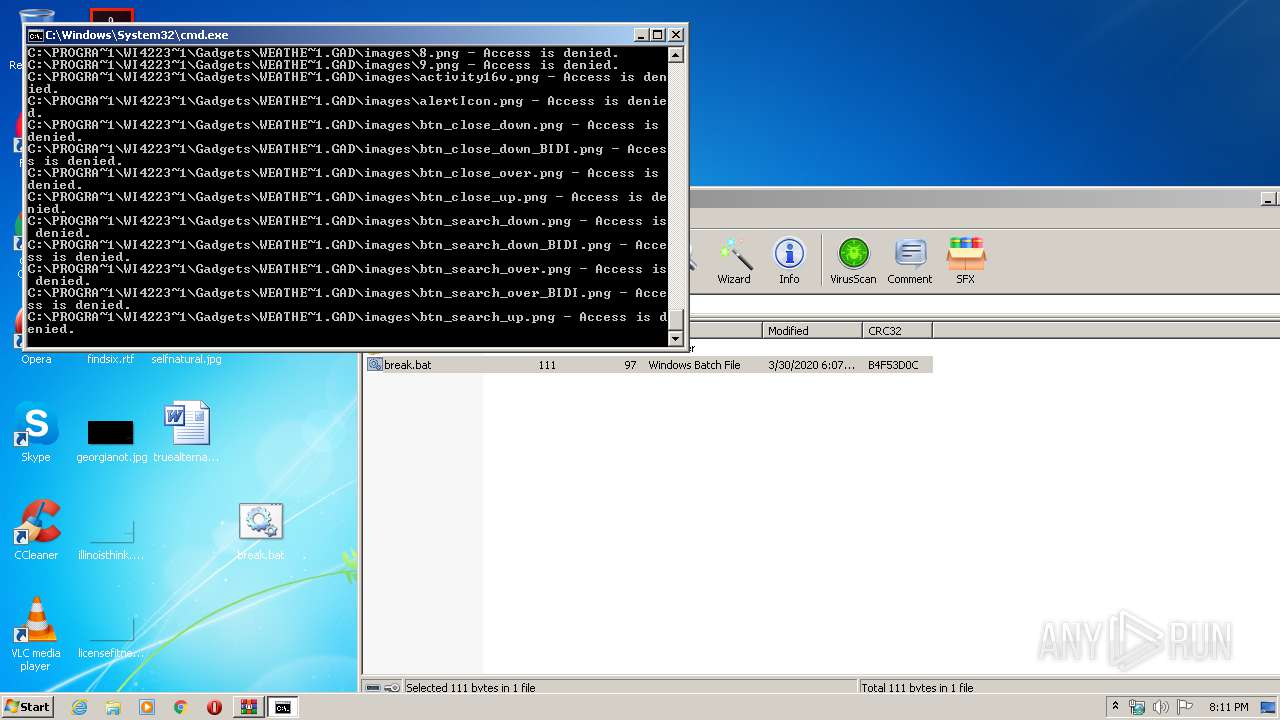
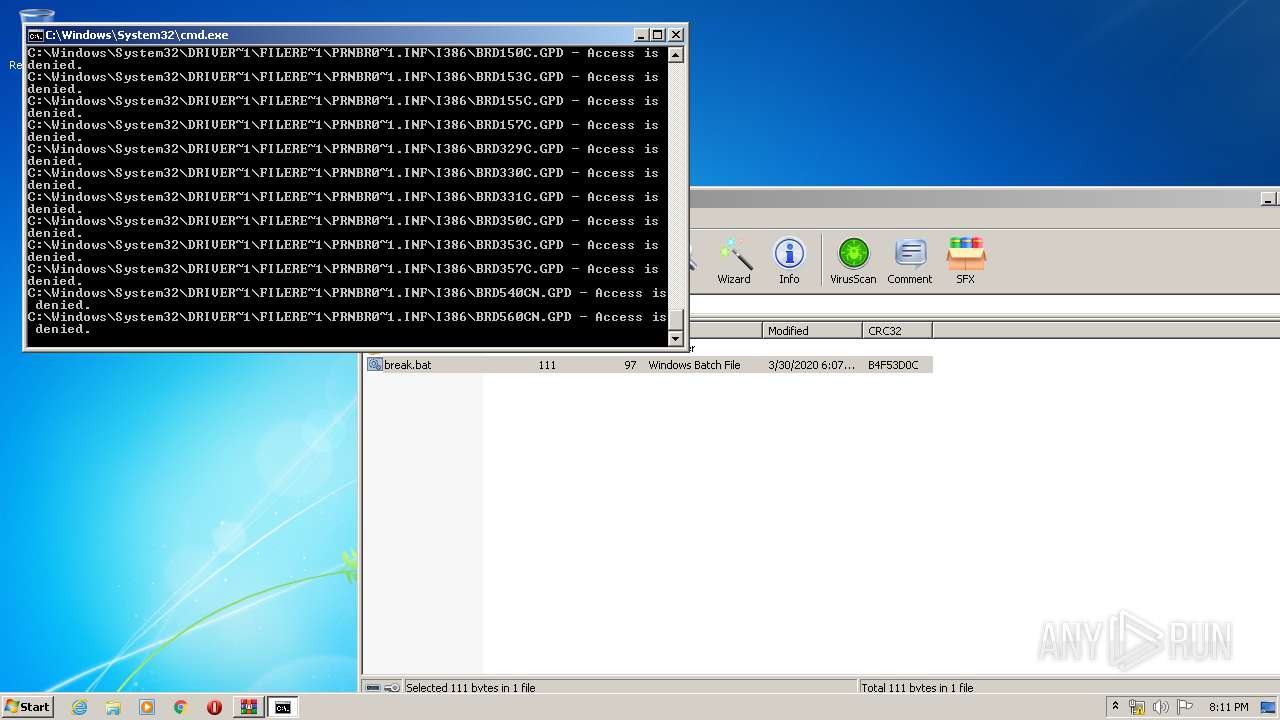
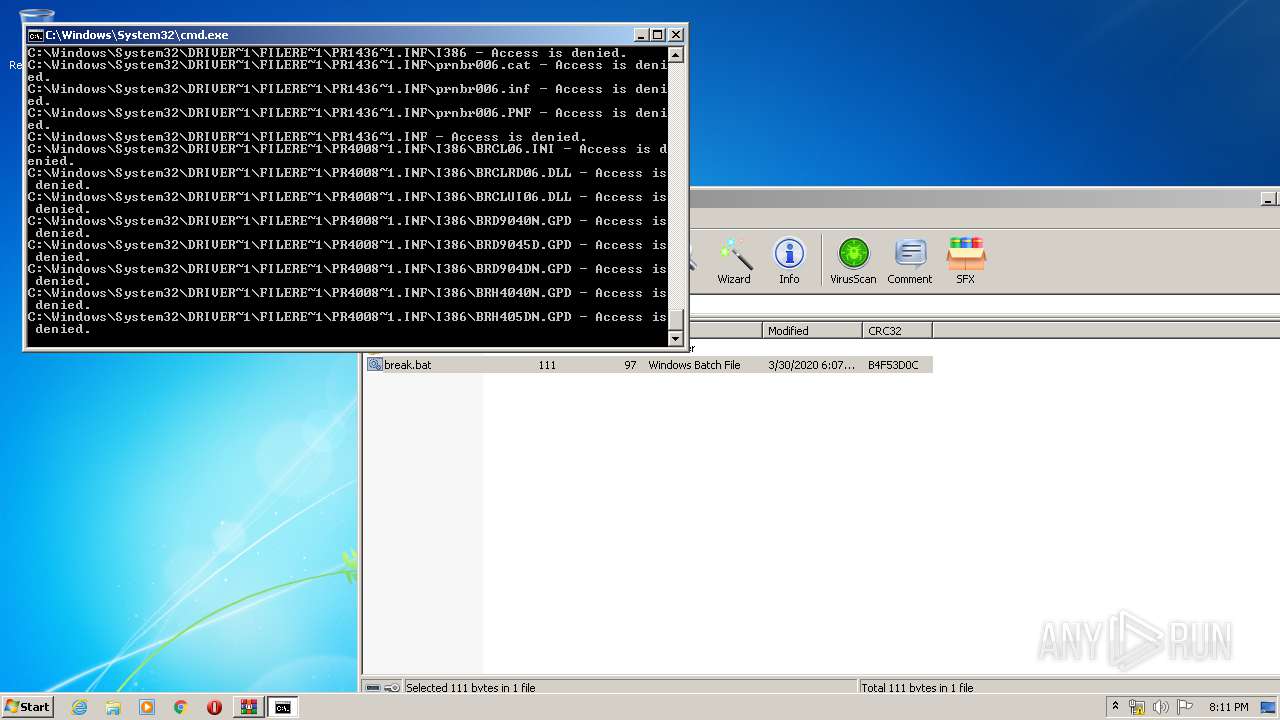
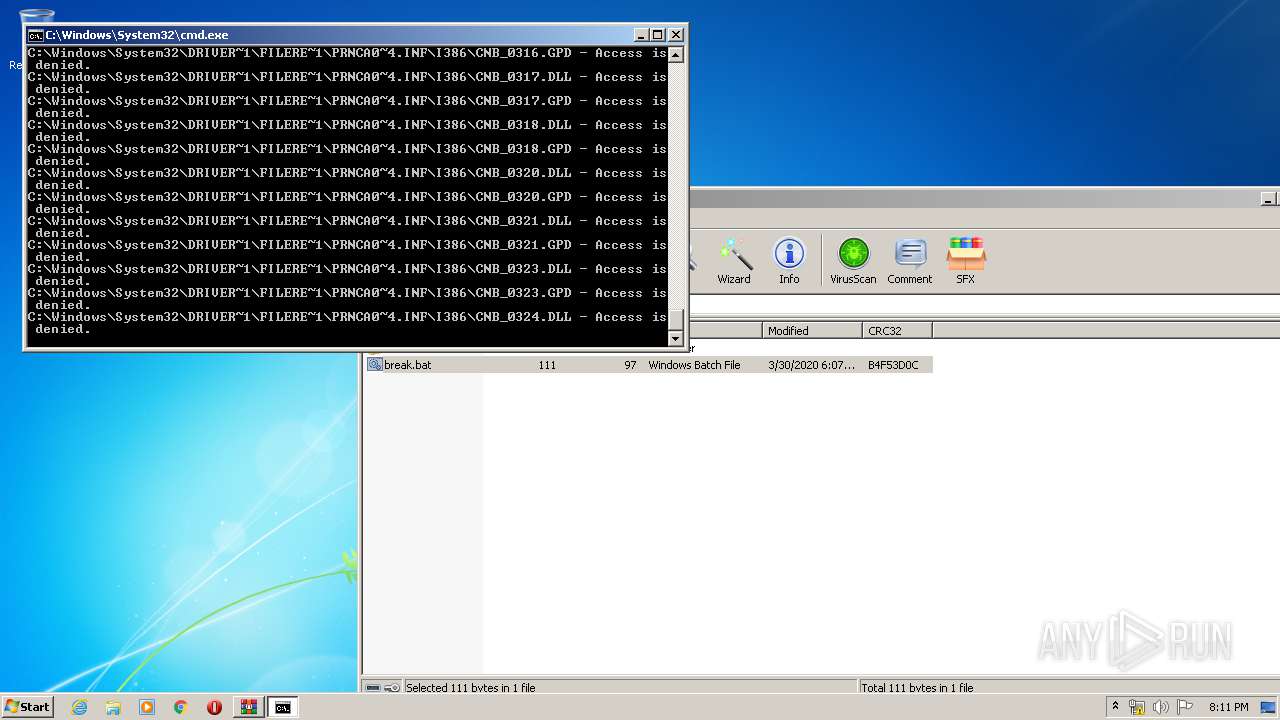
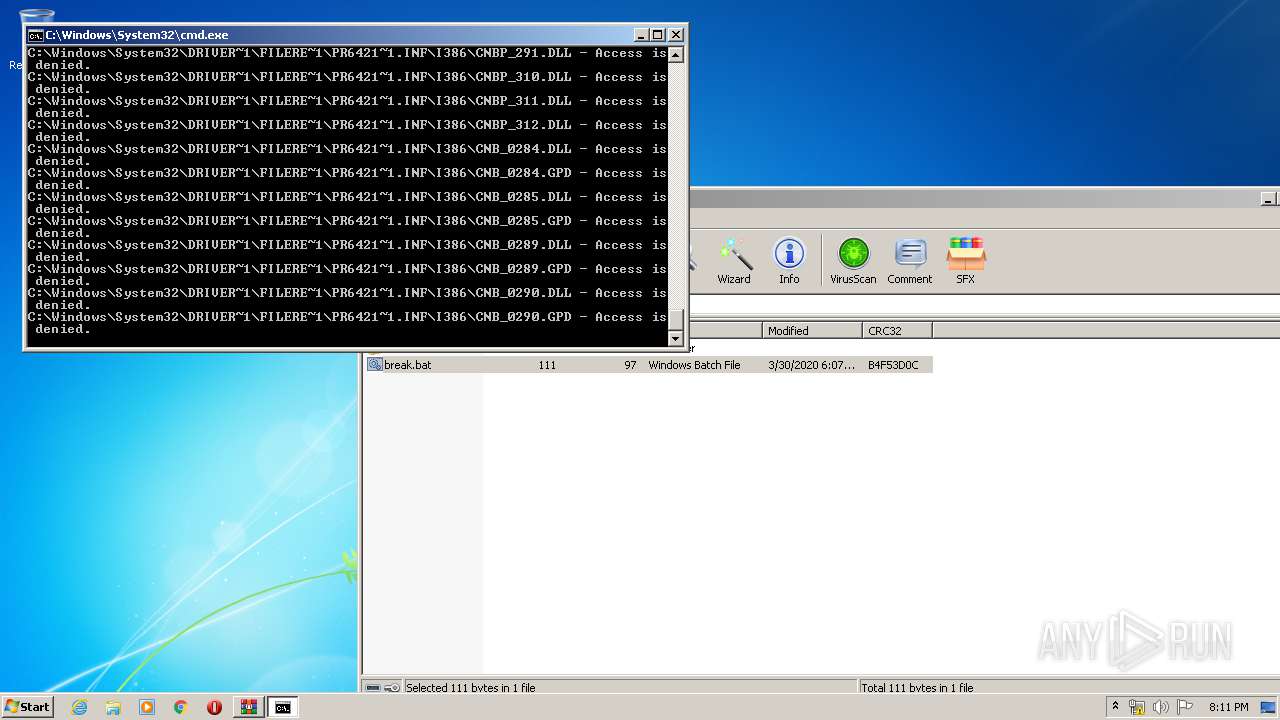
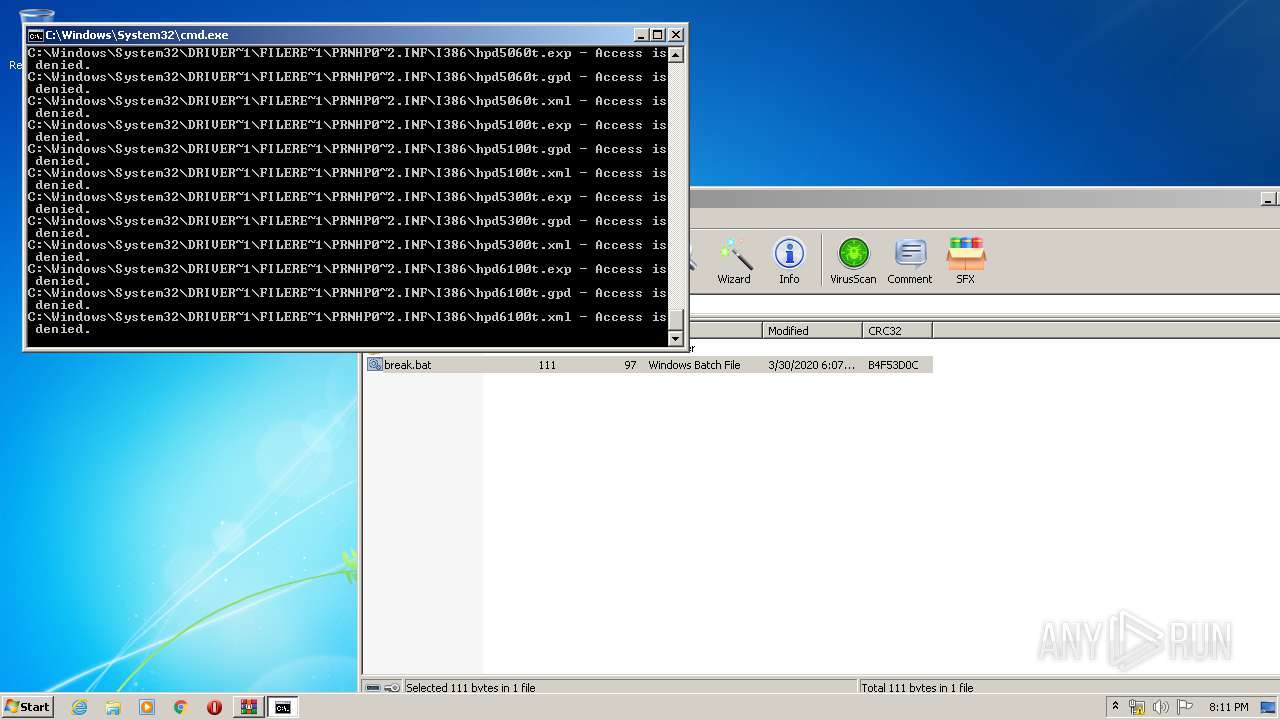
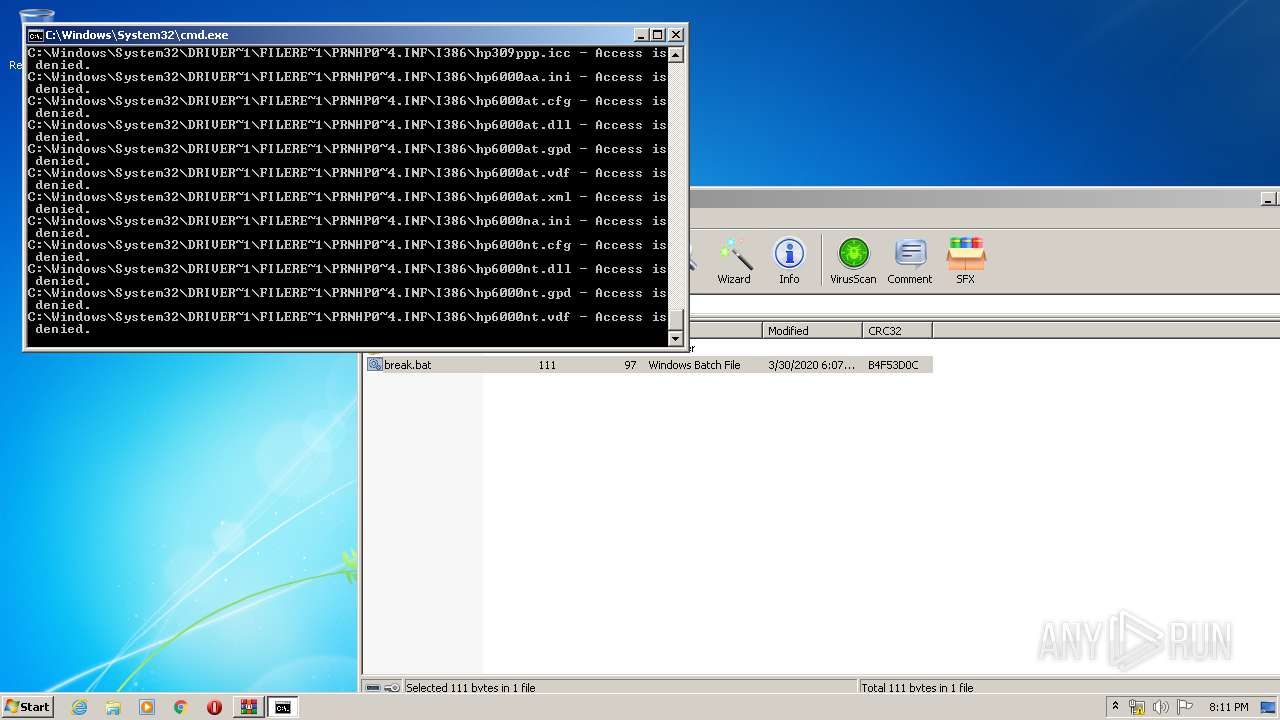
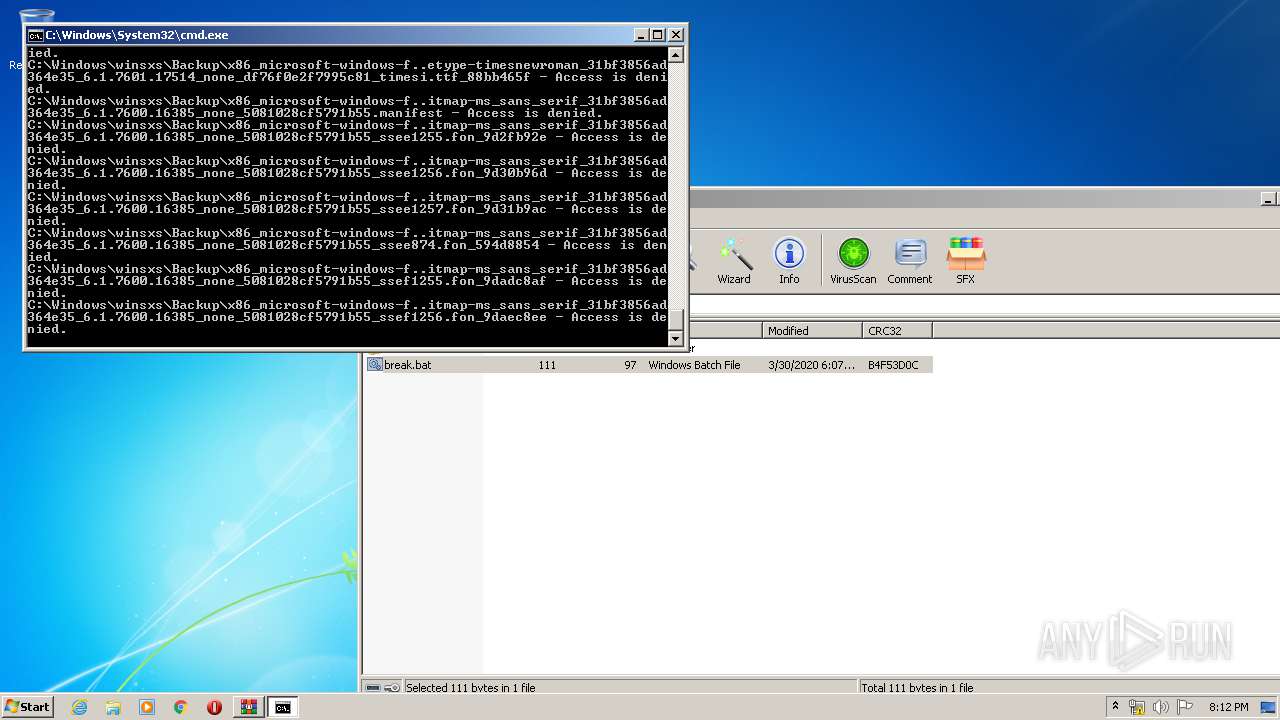
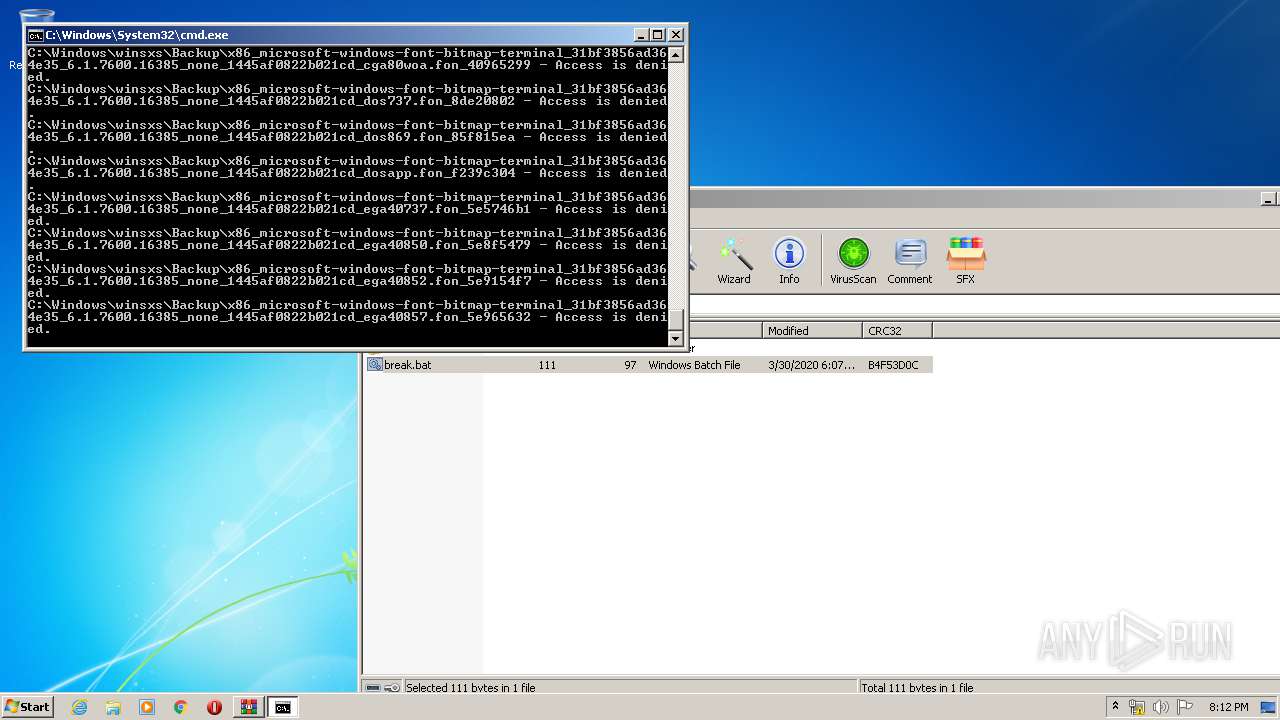
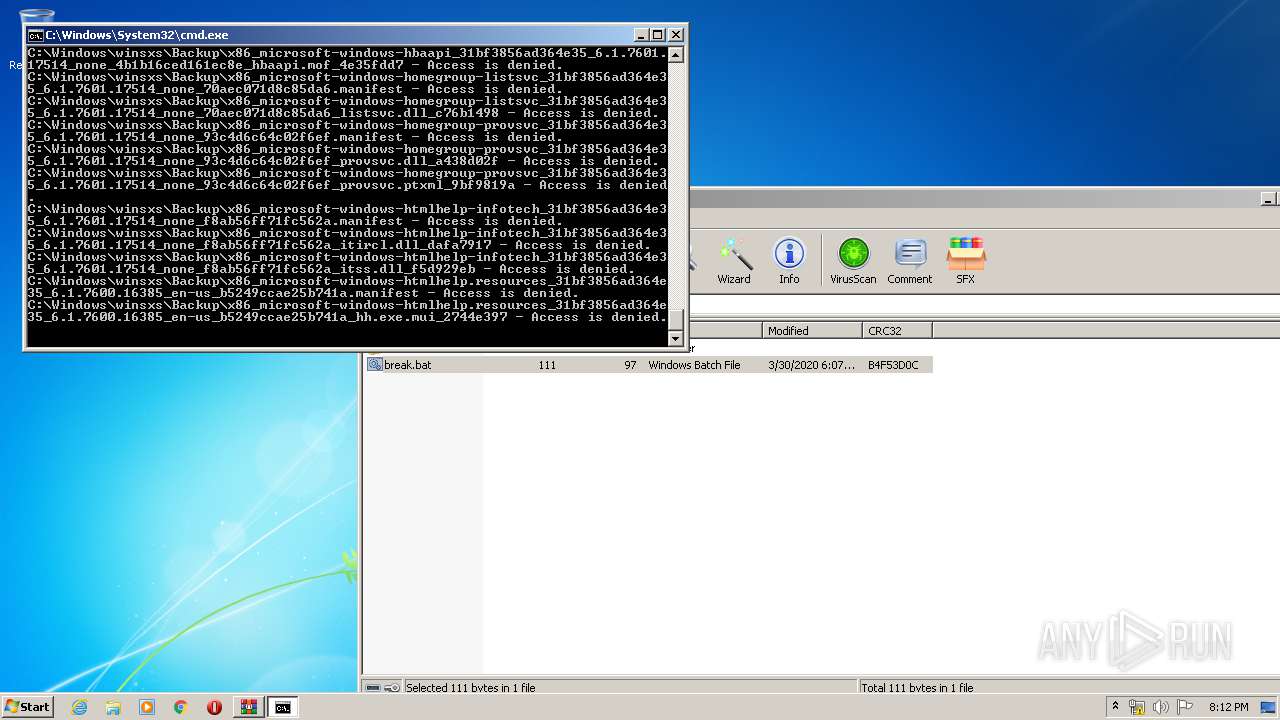
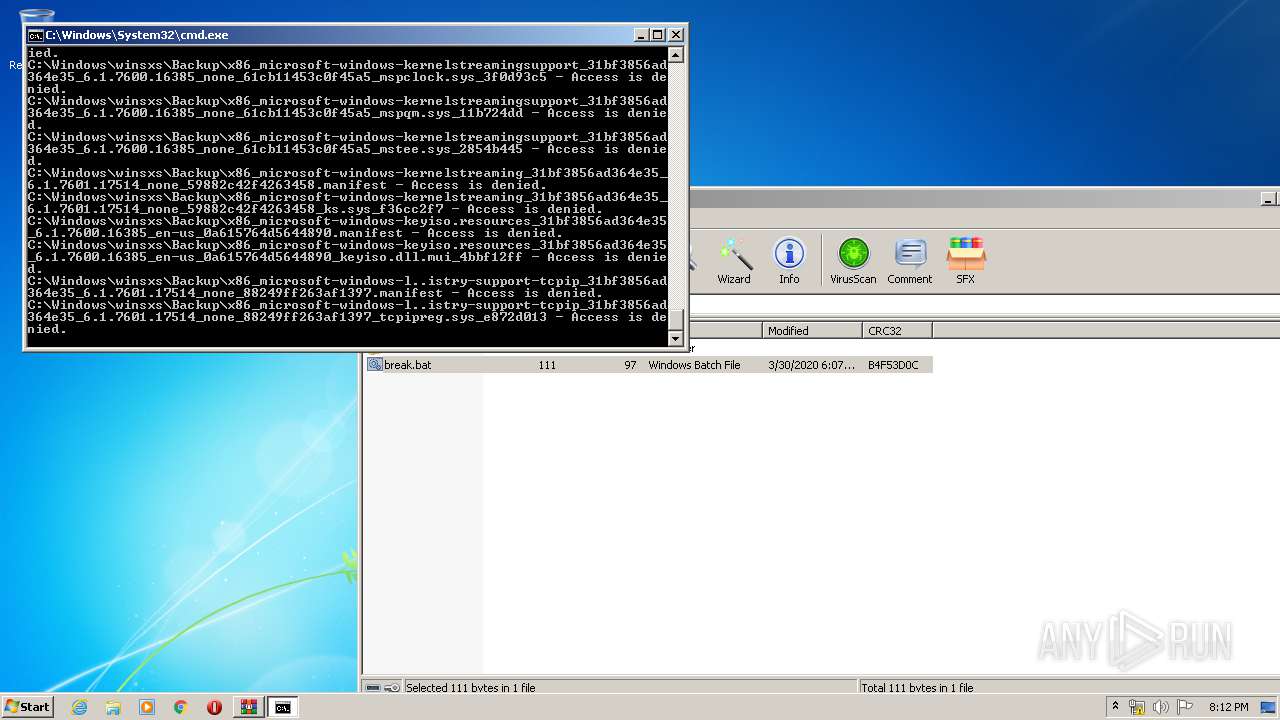
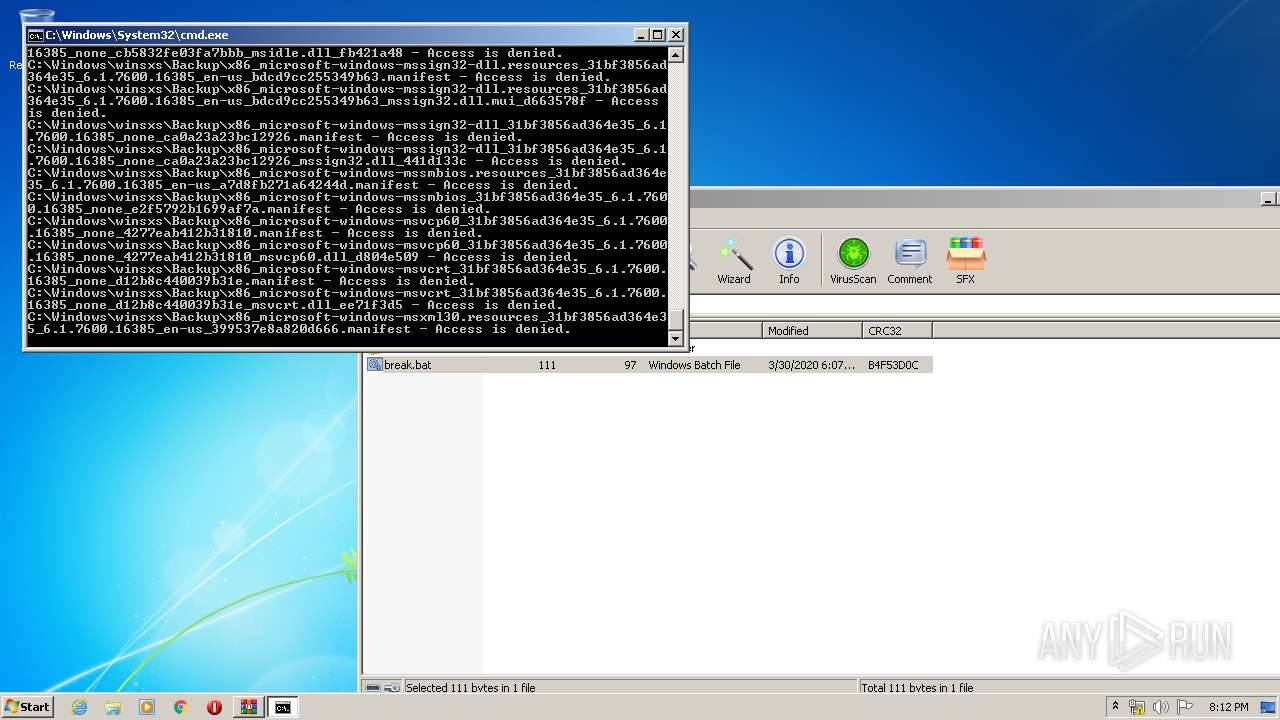
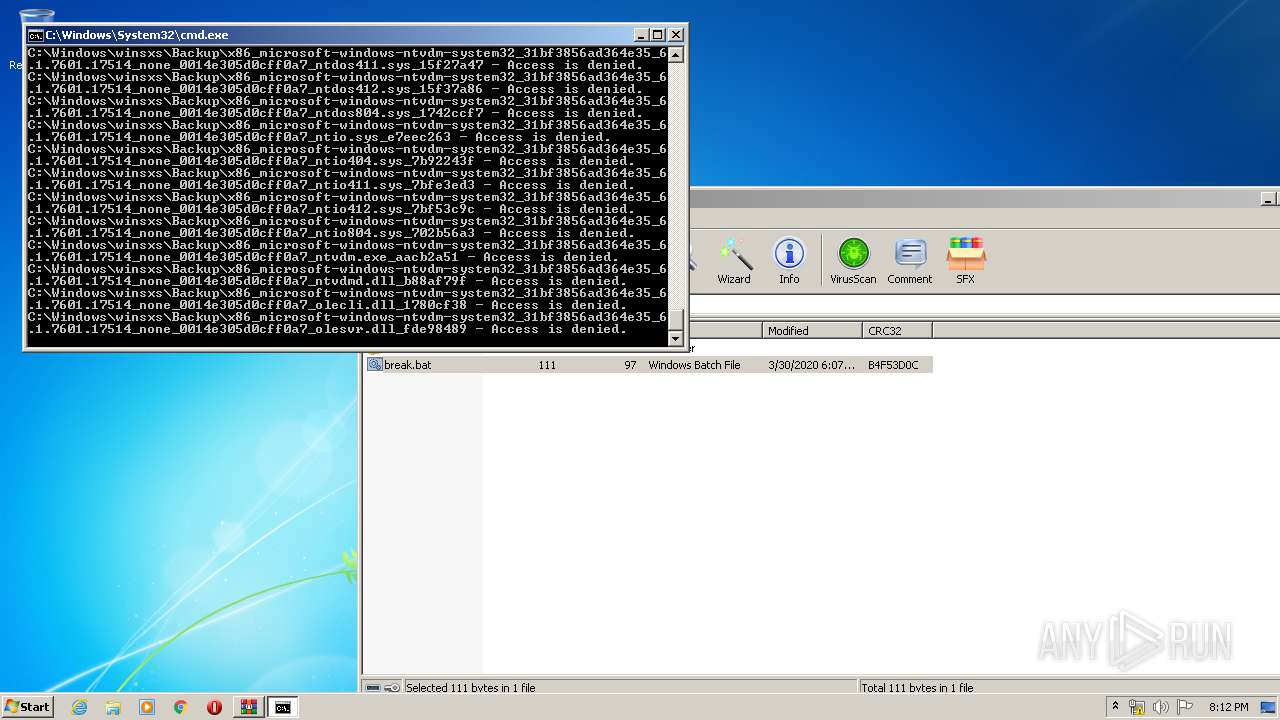
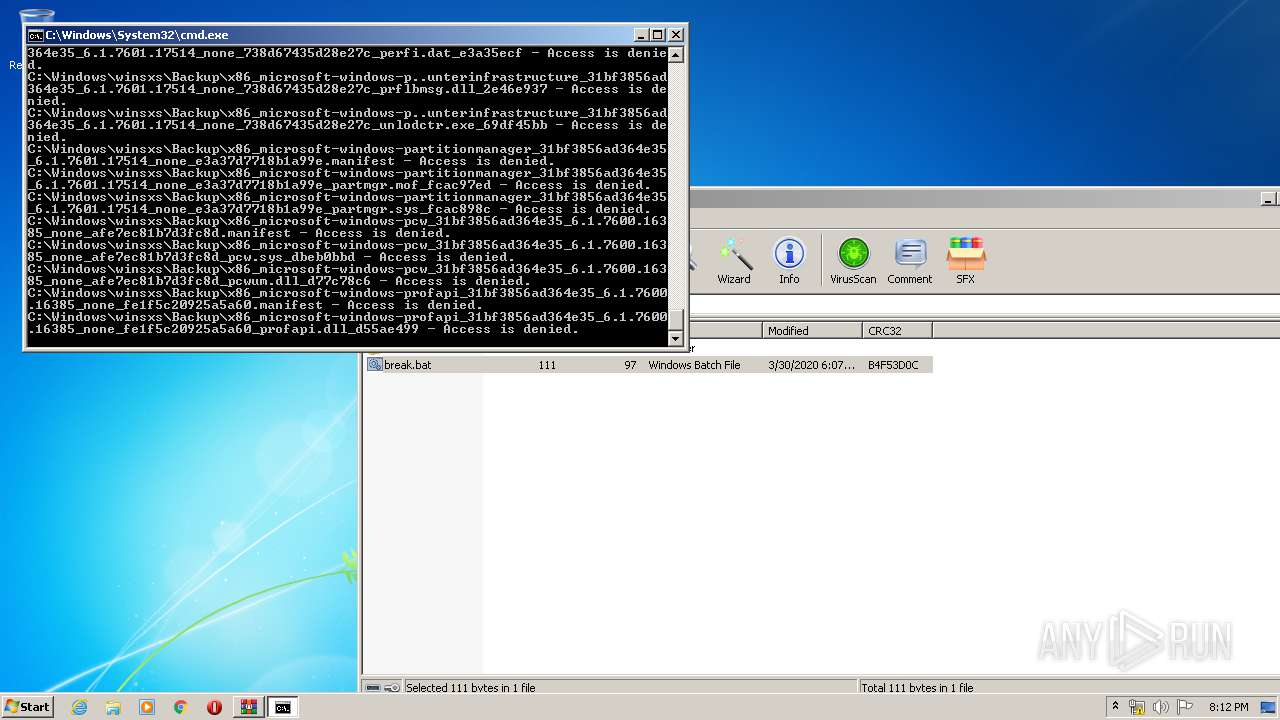
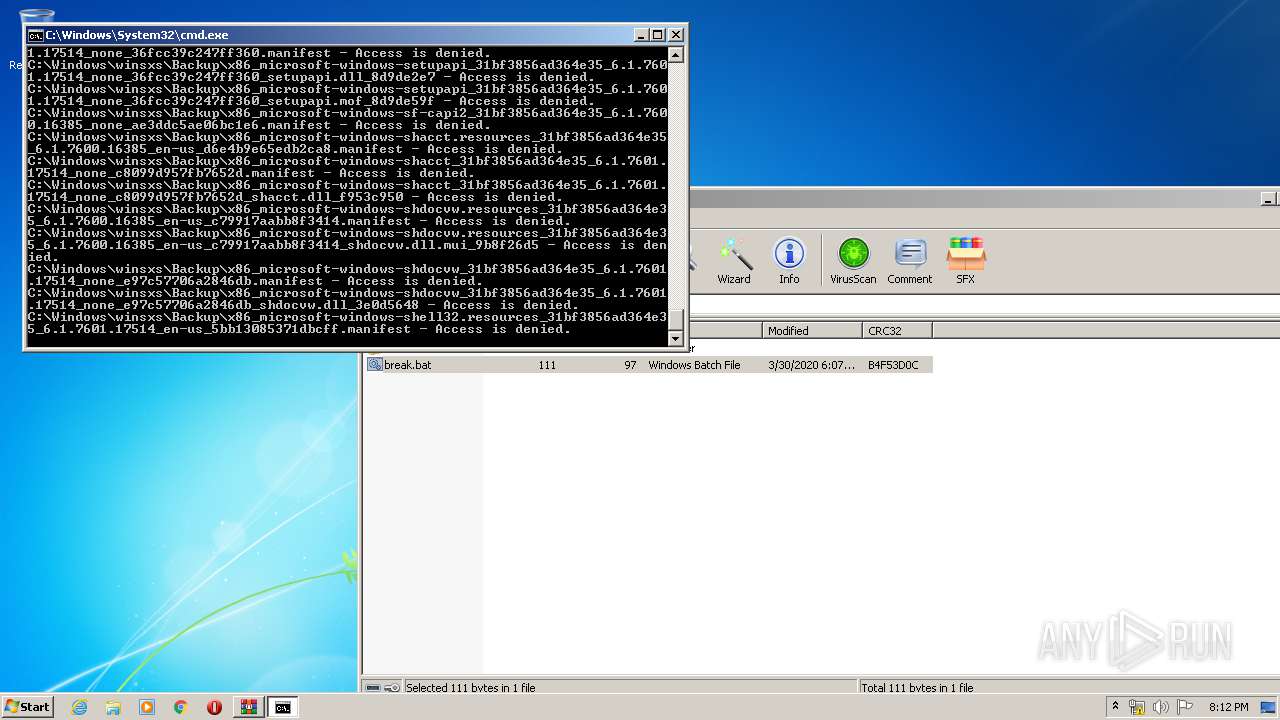
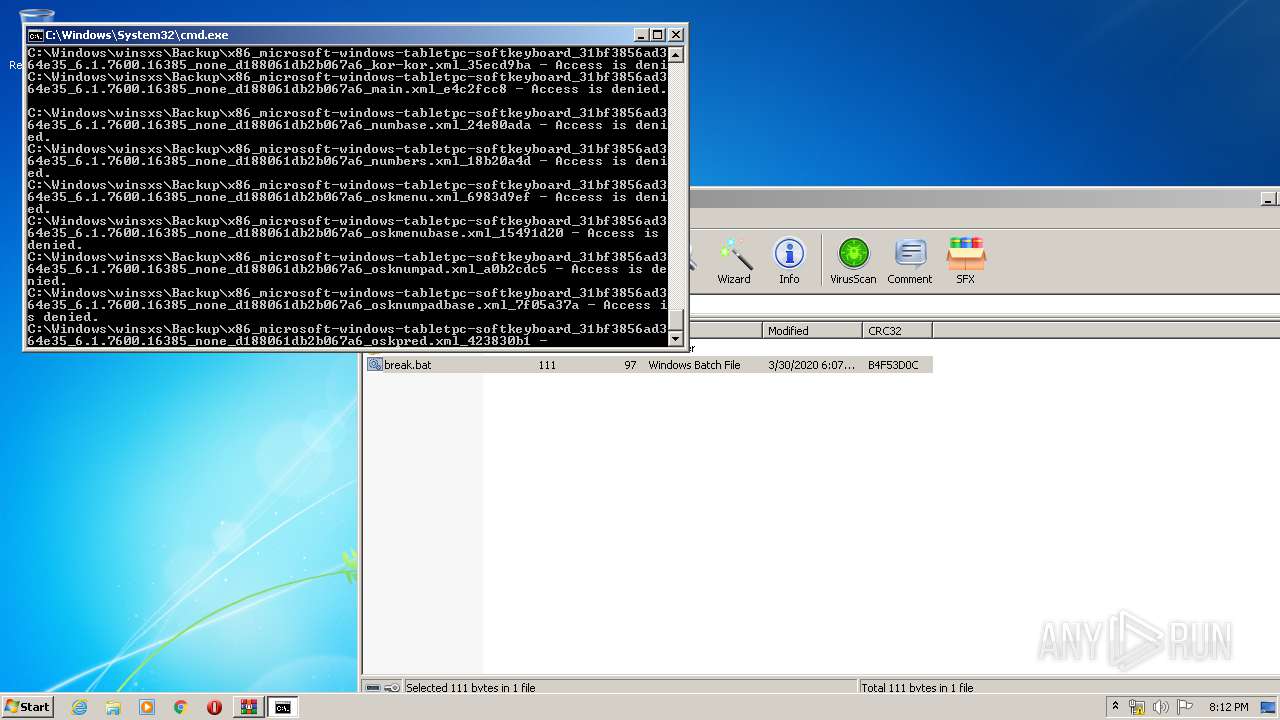
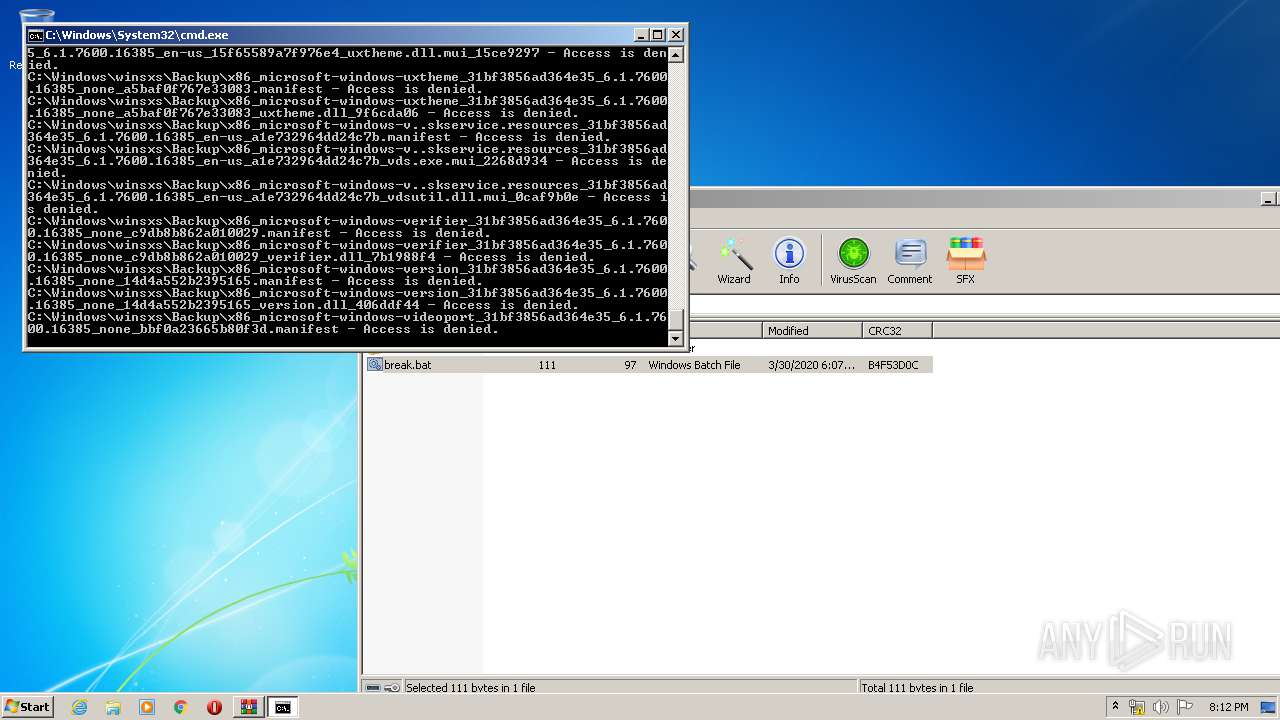
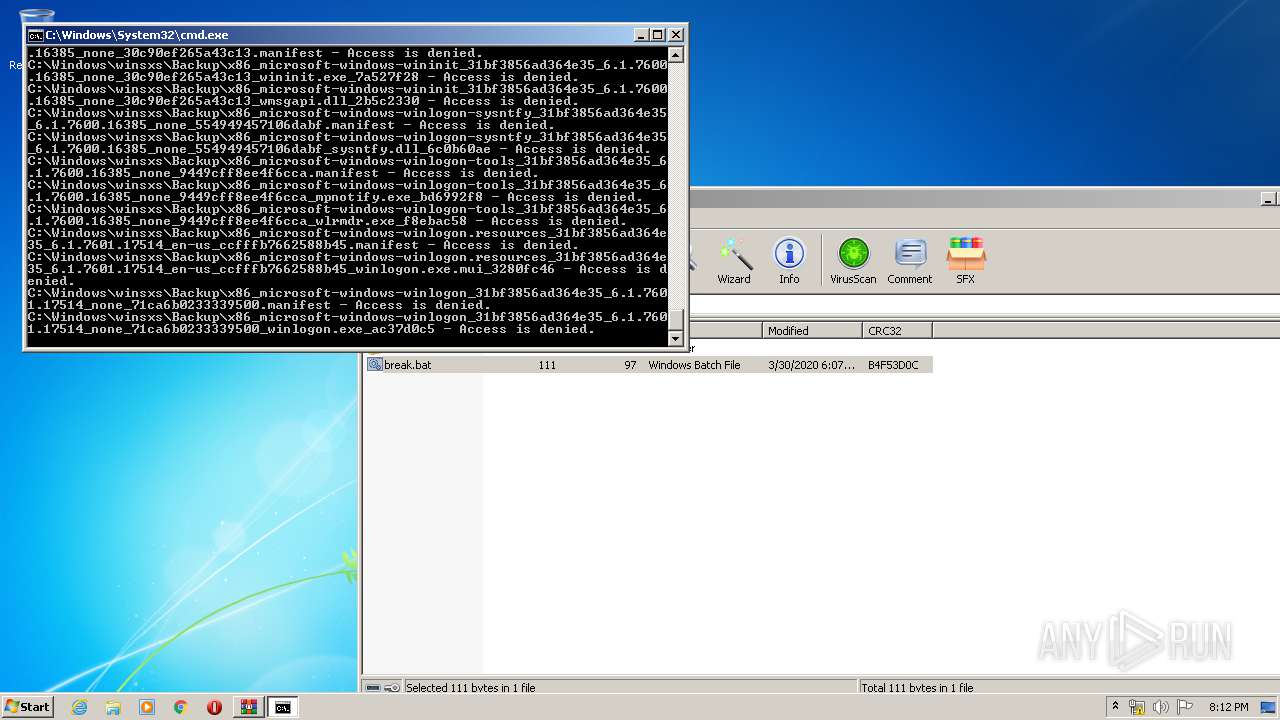
Executable files
0
Suspicious files
34
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3052.26063\break.bat | — | |
MD5:— | SHA256:— | |||
| 1548 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSS.log | — | |
MD5:— | SHA256:— | |||
| 1548 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Windows.edb | — | |
MD5:— | SHA256:— | |||
| 1548 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\tmp.edb | — | |
MD5:— | SHA256:— | |||
| 348 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSStmp.log | — | |
MD5:— | SHA256:— | |||
| 348 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSS.log | — | |
MD5:— | SHA256:— | |||
| 348 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Windows.edb | — | |
MD5:— | SHA256:— | |||
| 1548 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSSres00001.jrs | binary | |
MD5:87E50E8586DBA6B53A60855024388427 | SHA256:4EC923270DB17DB7609FE39206BEBBCE31483D4AEEE6A7D69D854BD89910B8B0 | |||
| 348 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Projects\SystemIndex\PropMap\CiPT0000.001 | binary | |
MD5:— | SHA256:— | |||
| 348 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\MSS.chk | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report