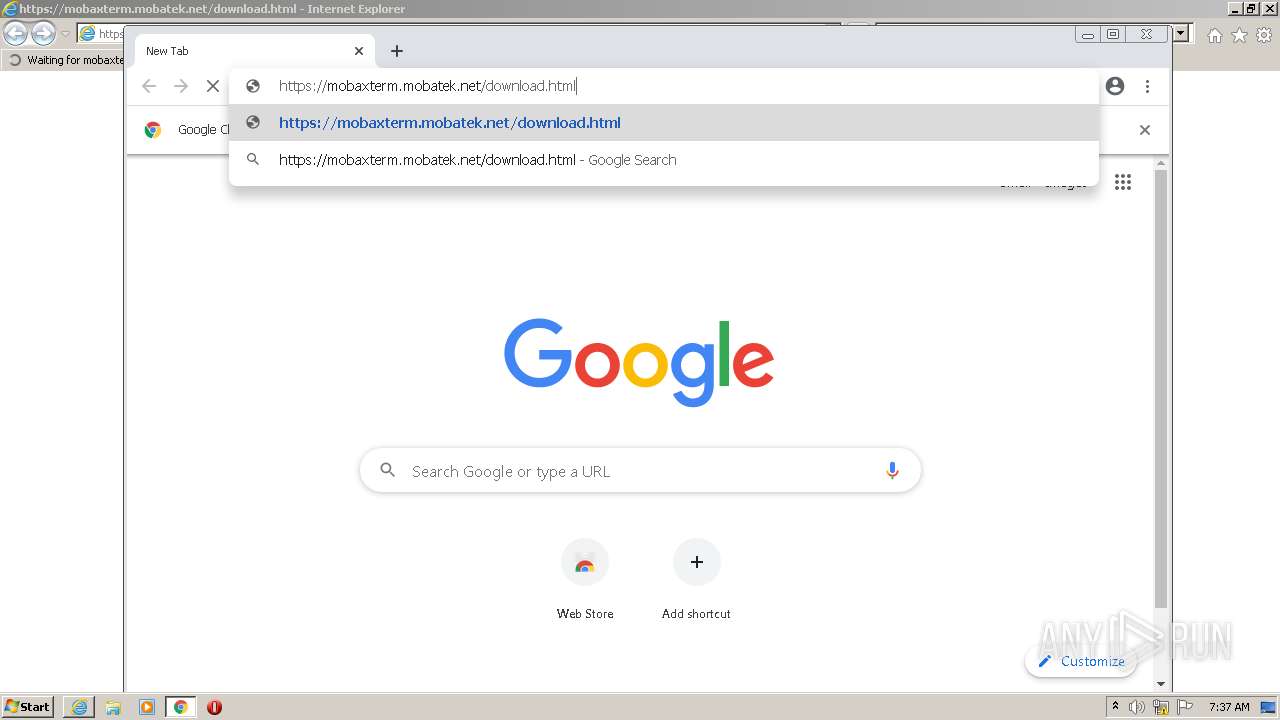
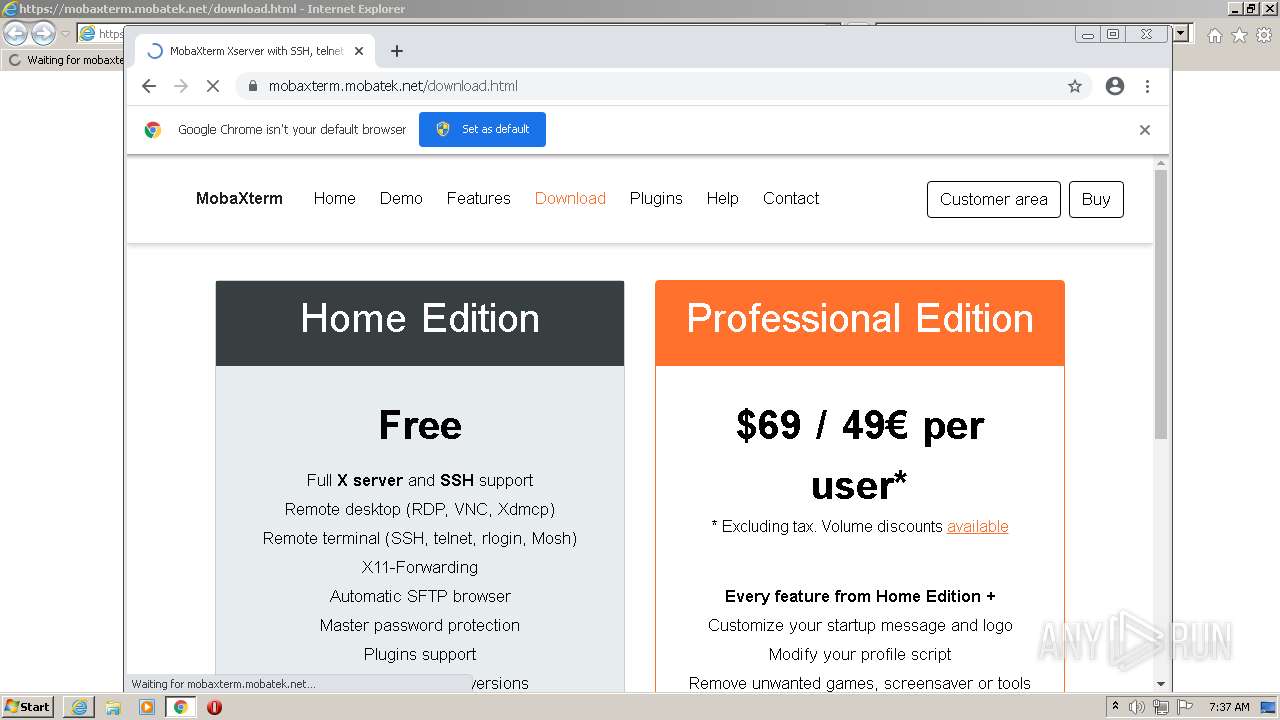
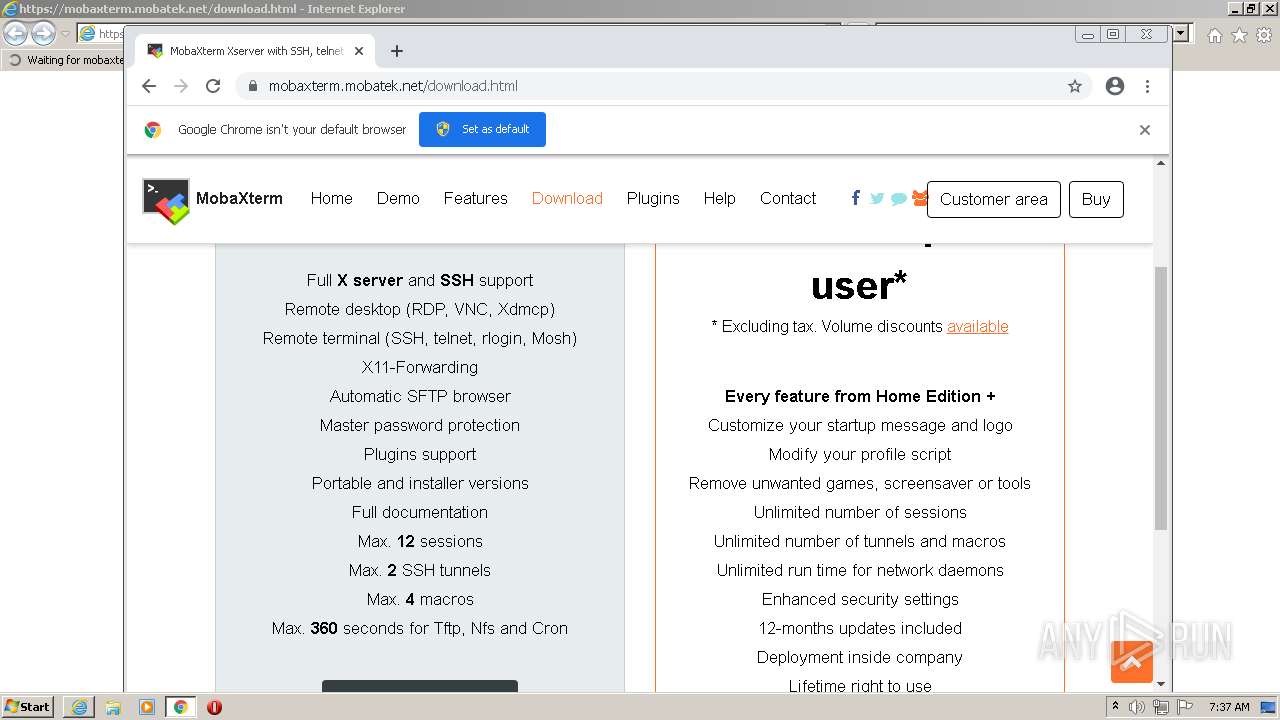
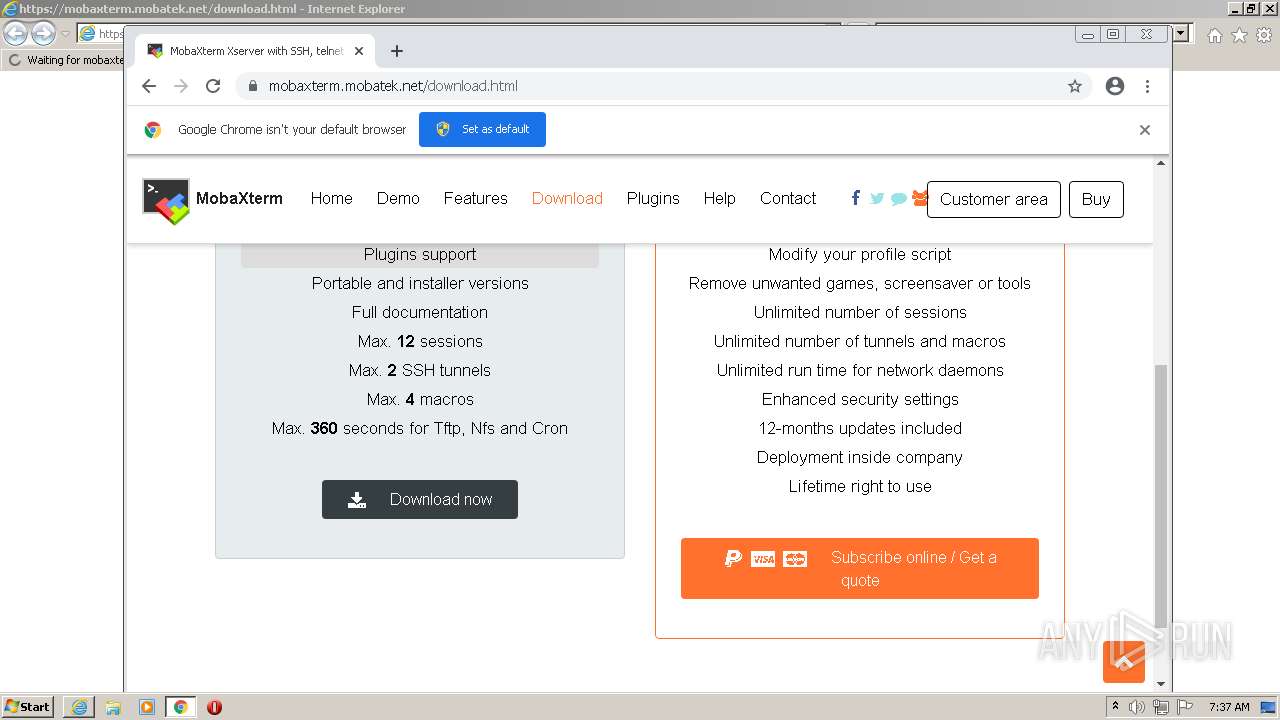
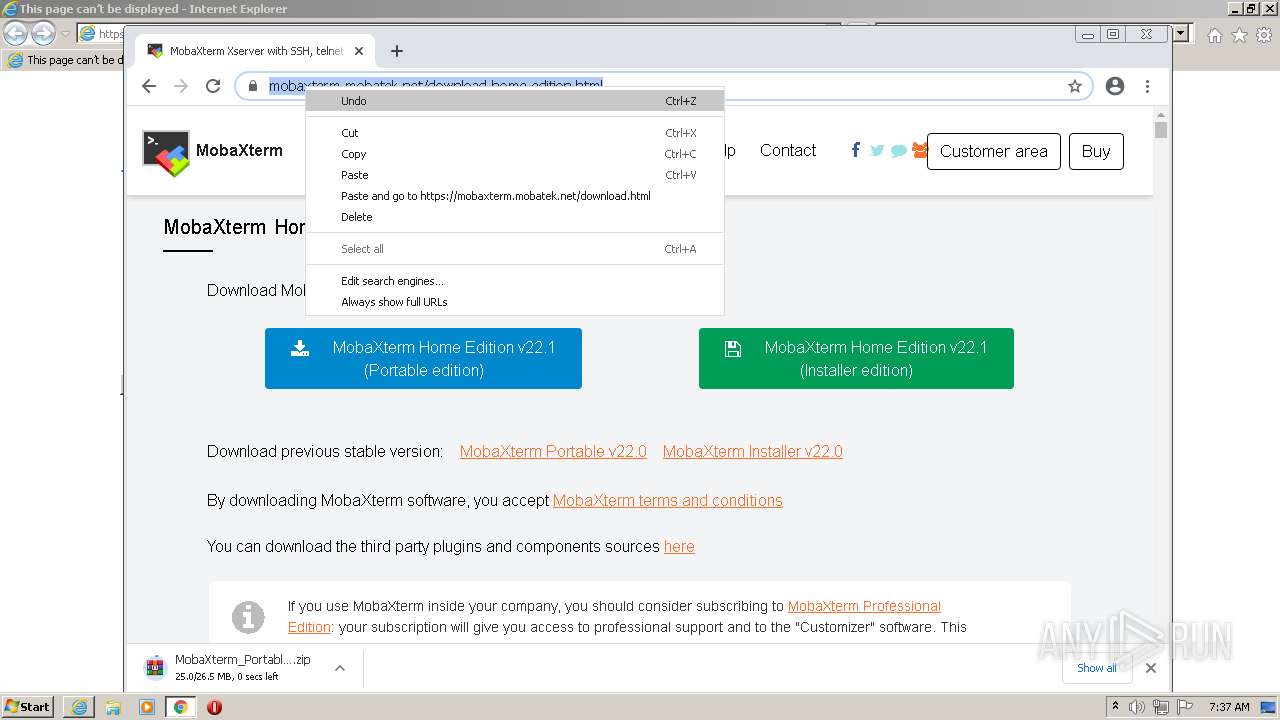
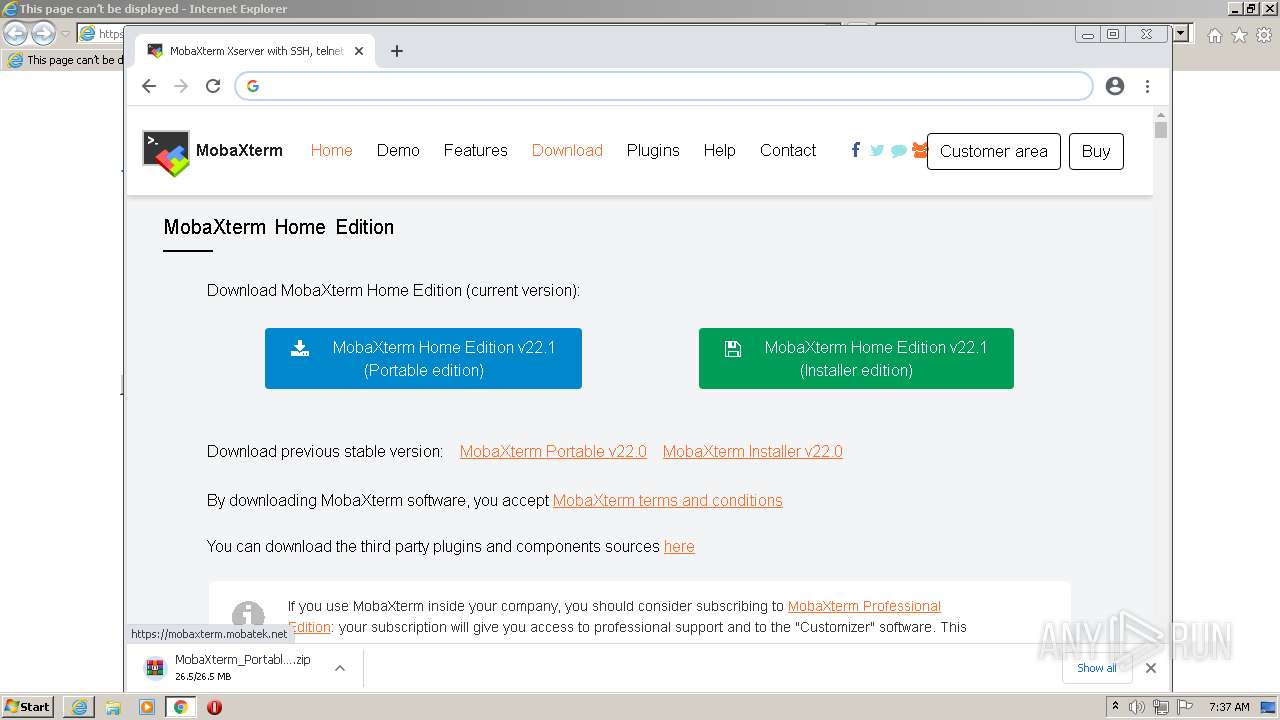
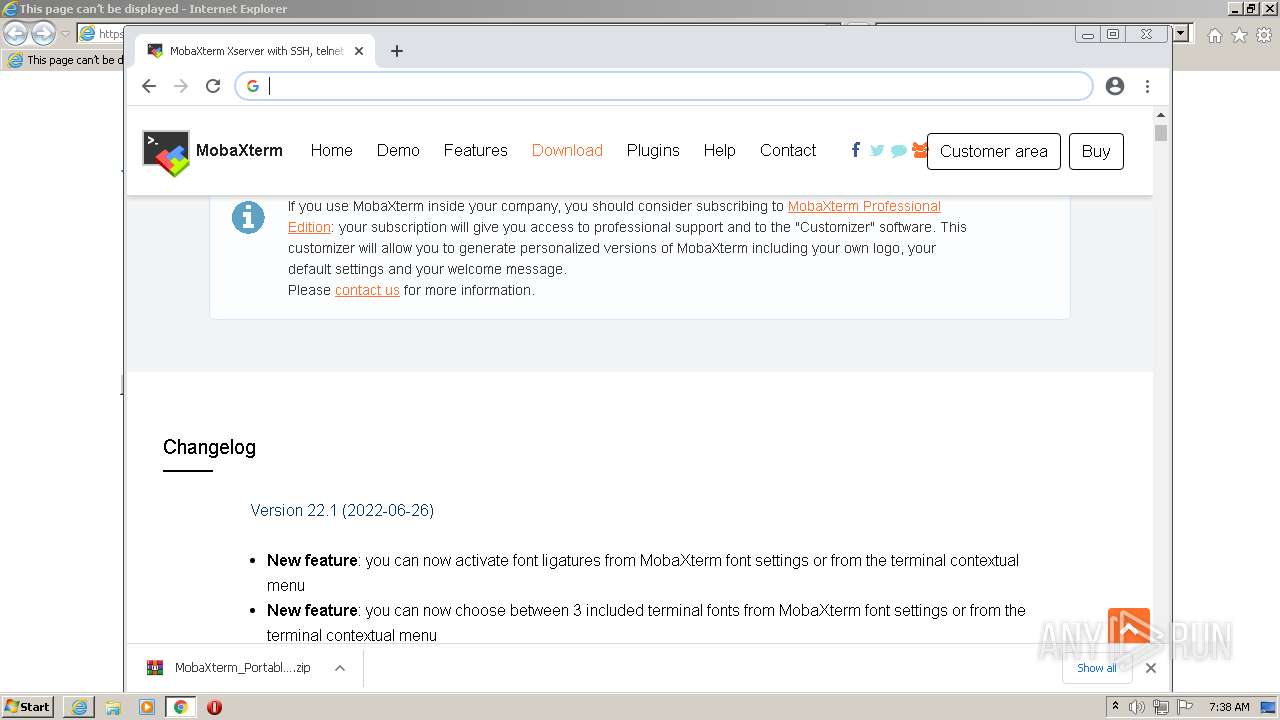
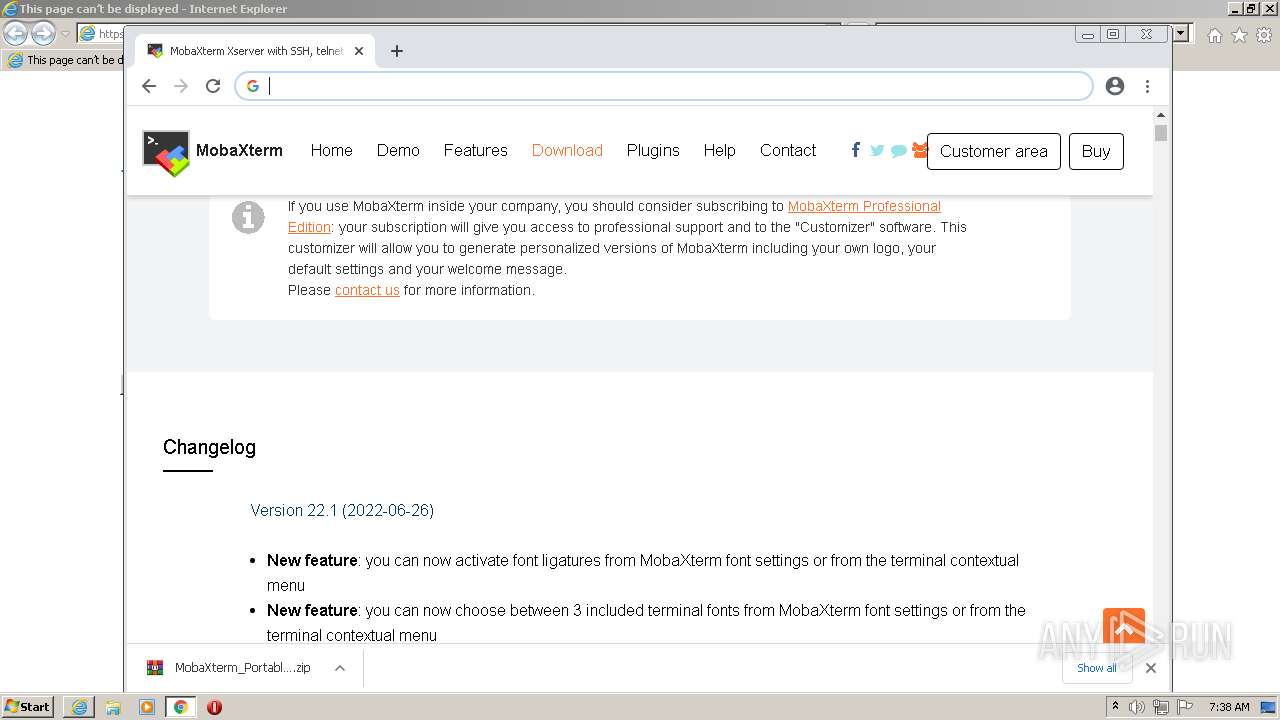
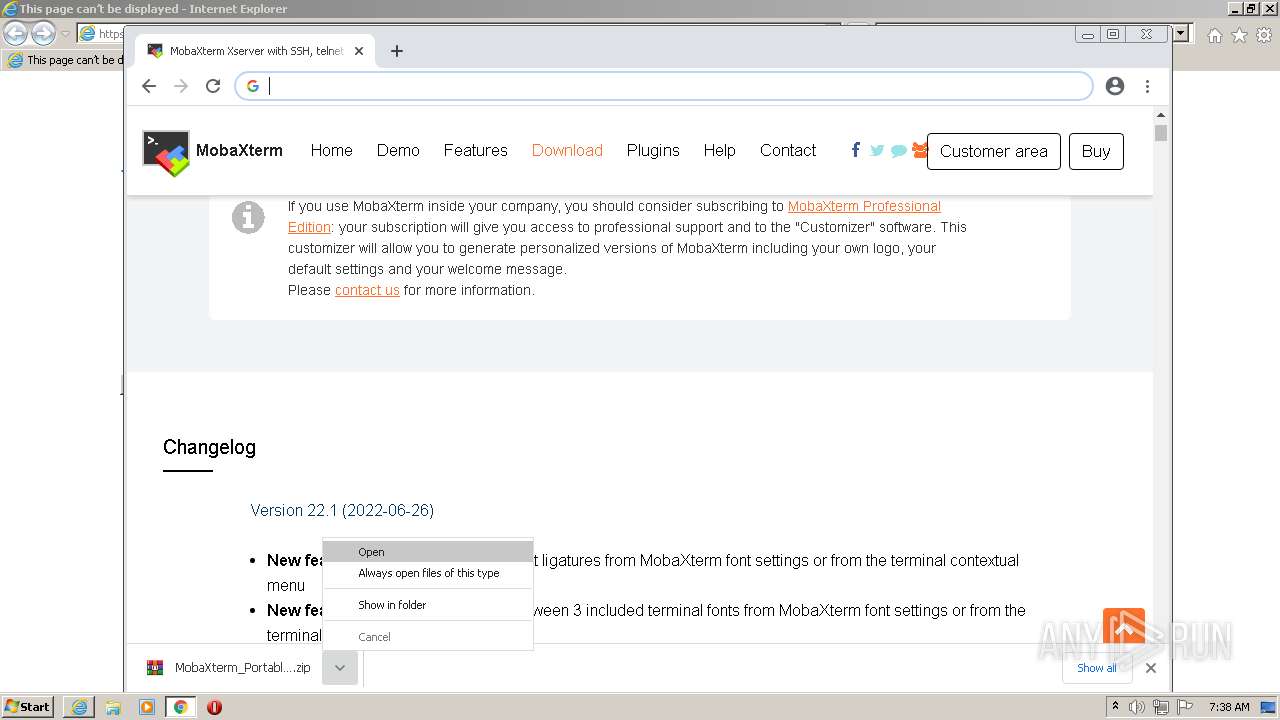
| URL: | https://mobaxterm.mobatek.net/download.html |
| Full analysis: | https://app.any.run/tasks/cb9df60e-9288-45f1-abe6-615f6e0a2850 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 06:36:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 92AA8B539B3810FD9992E3EA9BFEDD54 |
| SHA1: | A2C0597375104C3ACD6C91A2673BE30284D45D5C |
| SHA256: | E85C5EE1CE9E8A65036CF48180DF5D2917B1E4DBF5D58F9E8BA605AEB97651B6 |
| SSDEEP: | 3:N8lgHcsaKKQ:2QVKQ |
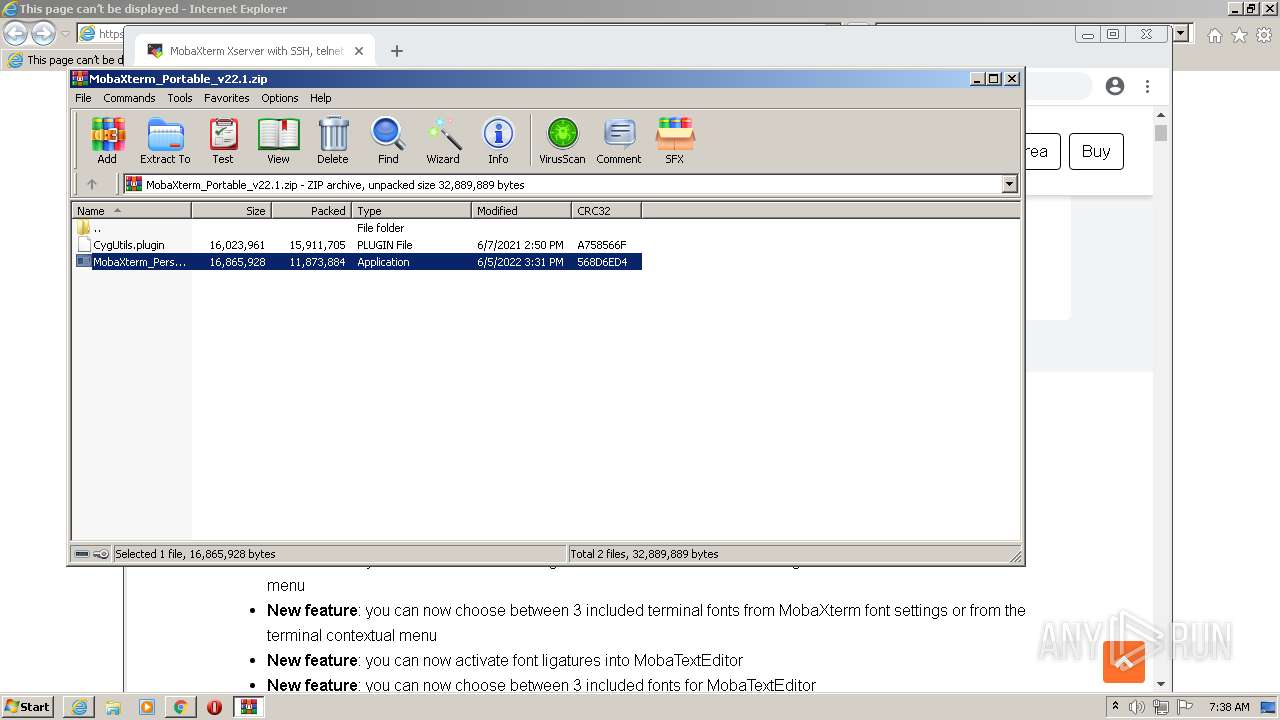
MALICIOUS
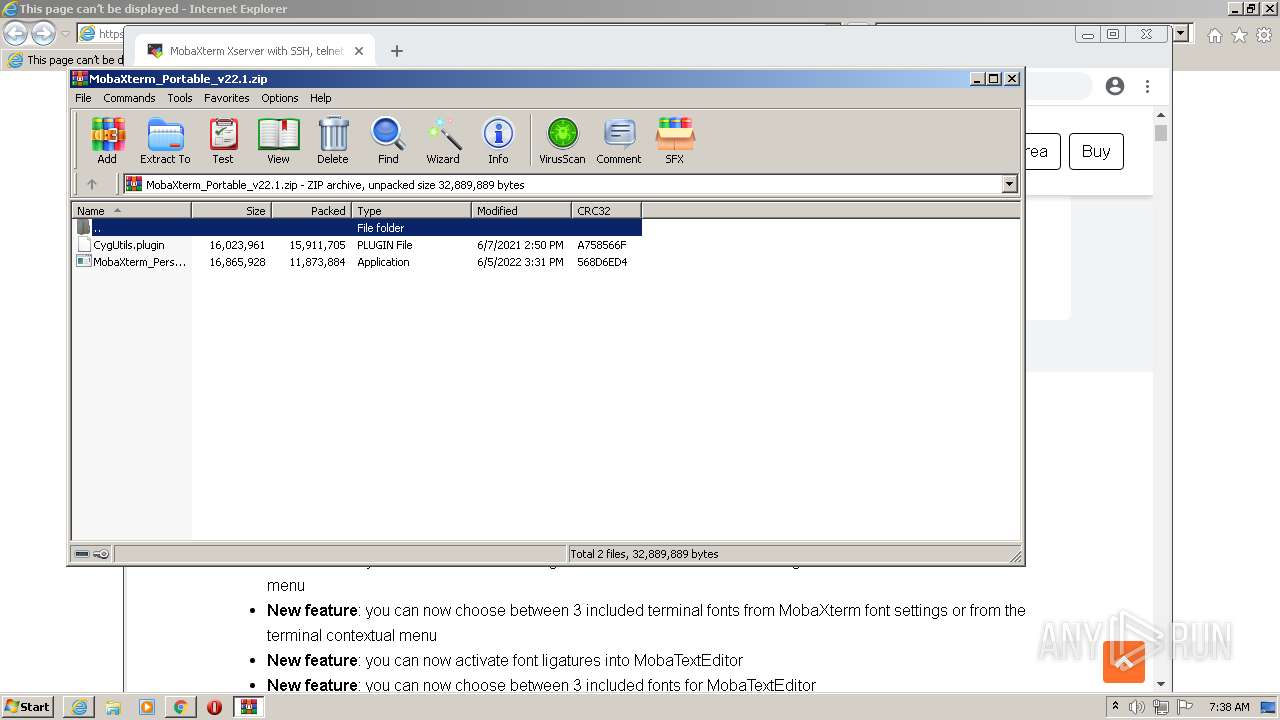
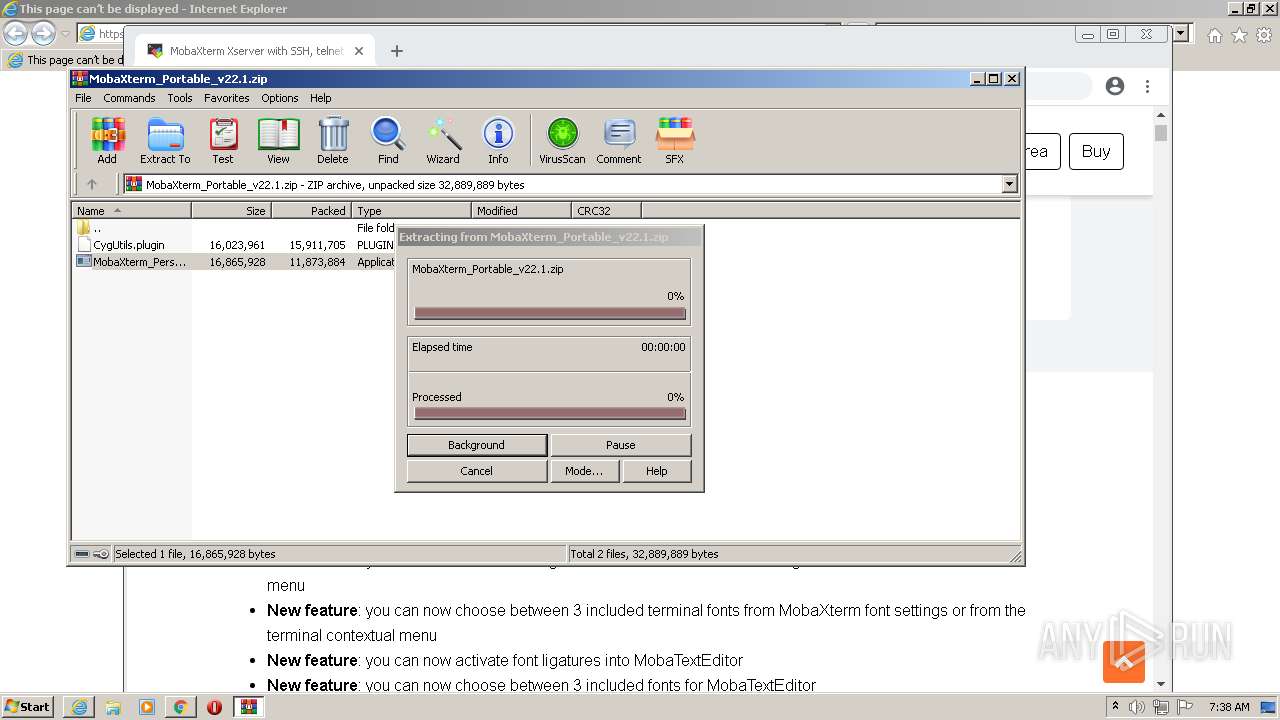
Drops executable file immediately after starts
- WinRAR.exe (PID: 3804)
- MobaXterm_Personal_22.1.exe (PID: 3252)
Application was dropped or rewritten from another process
- MobaXterm_Personal_22.1.exe (PID: 3252)
- mottynew.exe (PID: 2024)
- cygtermd.exe (PID: 2552)
- cygtermd.exe (PID: 2216)
- bash.exe (PID: 2520)
- busybox.exe (PID: 3192)
- bash.exe (PID: 3024)
- bash.exe (PID: 3476)
- busybox.exe (PID: 2940)
- bash.exe (PID: 2512)
- bash.exe (PID: 1732)
- bash.exe (PID: 2748)
- xkbcomp_w32.exe (PID: 1428)
- XWin_MobaX.exe (PID: 2840)
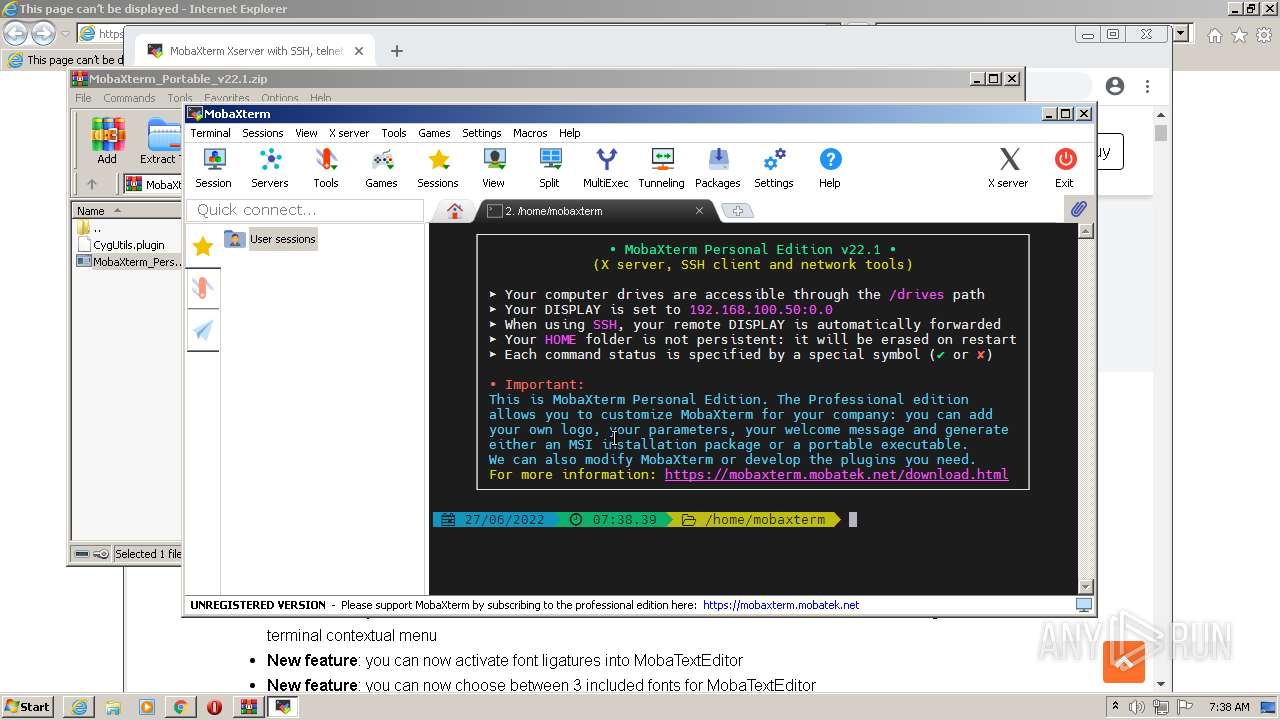
Detects Cygwin installation
- MobaXterm_Personal_22.1.exe (PID: 3252)
Loads dropped or rewritten executable
- cygtermd.exe (PID: 2552)
- bash.exe (PID: 2520)
- bash.exe (PID: 2512)
- busybox.exe (PID: 3192)
- bash.exe (PID: 3024)
- bash.exe (PID: 3476)
- cygtermd.exe (PID: 2216)
- svchost.exe (PID: 860)
- busybox.exe (PID: 2940)
- bash.exe (PID: 2748)
- bash.exe (PID: 1732)
- xkbcomp_w32.exe (PID: 1428)
- XWin_MobaX.exe (PID: 2840)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1952)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3440)
Reads the computer name
- WinRAR.exe (PID: 3804)
- MobaXterm_Personal_22.1.exe (PID: 3252)
- bash.exe (PID: 2520)
- XWin_MobaX.exe (PID: 2840)
Checks supported languages
- WinRAR.exe (PID: 3804)
- MobaXterm_Personal_22.1.exe (PID: 3252)
- mottynew.exe (PID: 2024)
- cygtermd.exe (PID: 2552)
- cygtermd.exe (PID: 2216)
- bash.exe (PID: 2512)
- busybox.exe (PID: 3192)
- bash.exe (PID: 3024)
- bash.exe (PID: 3476)
- busybox.exe (PID: 2940)
- bash.exe (PID: 2520)
- bash.exe (PID: 1732)
- bash.exe (PID: 2748)
- xkbcomp_w32.exe (PID: 1428)
- XWin_MobaX.exe (PID: 2840)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3804)
- MobaXterm_Personal_22.1.exe (PID: 3252)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3804)
- MobaXterm_Personal_22.1.exe (PID: 3252)
Reads Environment values
- MobaXterm_Personal_22.1.exe (PID: 3252)
Reads mouse settings
- MobaXterm_Personal_22.1.exe (PID: 3252)
Application launched itself
- cygtermd.exe (PID: 2552)
- bash.exe (PID: 2520)
Creates files in the user directory
- MobaXterm_Personal_22.1.exe (PID: 3252)
INFO
Application launched itself
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 3440)
Checks supported languages
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 1952)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 616)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 2400)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 1888)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2268)
- svchost.exe (PID: 860)
- chrome.exe (PID: 3336)
Reads the computer name
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 1952)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 616)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 1796)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2472)
Checks Windows Trust Settings
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 1952)
Reads settings of System Certificates
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 2208)
- iexplore.exe (PID: 1952)
Changes internet zones settings
- iexplore.exe (PID: 2948)
Reads internet explorer settings
- iexplore.exe (PID: 1952)
Manual execution by user
- chrome.exe (PID: 3440)
Reads the hosts file
- chrome.exe (PID: 3440)
- chrome.exe (PID: 2208)
Changes settings of System certificates
- iexplore.exe (PID: 2948)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2948)
Reads the date of Windows installation
- chrome.exe (PID: 2472)
Creates files in the user directory
- iexplore.exe (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
41
Malicious processes
14
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,4345152487158524759,8815610107642101492,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 860 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1428 | "C:\Users\admin\AppData\Local\Temp\Mxt221\bin\xkbcomp_w32.exe" -w 1 "-RC:\Users\admin\AppData\Local\Temp\Mxt221\usr\share\X11\xkb" -xkm "C:\Users\admin\AppData\Local\Temp\Mxt221\var\log\xwin\xkb_a02708" -em1 "The XKEYBOARD keymap compiler (xkbcomp) reports:" -emp "> " -eml "Errors from xkbcomp are not fatal to the X server" "C:\Users\admin\AppData\Local\Temp\Mxt221\var\log\xwin\server-0.xkm" | C:\Users\admin\AppData\Local\Temp\Mxt221\bin\xkbcomp_w32.exe | — | XWin_MobaX.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Temp\Mxt221\bin\bash.exe" | C:\Users\admin\AppData\Local\Temp\Mxt221\bin\bash.exe | — | bash.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1056,4345152487158524759,8815610107642101492,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,4345152487158524759,8815610107642101492,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,4345152487158524759,8815610107642101492,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3384 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2948 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6db9d988,0x6db9d998,0x6db9d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2024 | "C:\Users\admin\AppData\Local\Temp\Mxt221\bin\mottynew.exe" -load "TERM1971762" | C:\Users\admin\AppData\Local\Temp\Mxt221\bin\mottynew.exe | — | MobaXterm_Personal_22.1.exe | |||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm terminal emulator Exit code: 0 Version: Release 0.77 (without embedded help) Modules
| |||||||||||||||
Total events
27 103
Read events
26 335
Write events
757
Delete events
11
Modification events
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30968304 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30968304 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
53
Suspicious files
207
Text files
606
Unknown types
125
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62B95012-D70.pma | — | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2208 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF101ba8.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
56
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/epb4sdvq6vqrfeknwrmg74jhaa_2831/jflookgnkcckhobaglndicnbbgbonegd_2831_all_ilnjnaev3bhunvzfg33k3jlqbi.crx3 | US | — | — | whitelisted |
2948 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1952 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://crl.usertrust.com/USERTrustRSACertificationAuthority.crl | US | der | 978 b | whitelisted |
1952 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | US | der | 727 b | whitelisted |
2948 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2948 | iexplore.exe | GET | 200 | 8.238.30.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?58119ce511d89f2b | US | compressed | 4.70 Kb | whitelisted |
2208 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2948 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/epb4sdvq6vqrfeknwrmg74jhaa_2831/jflookgnkcckhobaglndicnbbgbonegd_2831_all_ilnjnaev3bhunvzfg33k3jlqbi.crx3 | US | binary | 5.67 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1952 | iexplore.exe | 46.105.198.129:443 | mobaxterm.mobatek.net | OVH SAS | FR | unknown |
2948 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2948 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2948 | iexplore.exe | 8.238.30.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2208 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 142.250.185.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 142.250.185.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2208 | chrome.exe | 142.250.184.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1952 | iexplore.exe | 172.64.155.188:80 | ocsp.usertrust.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mobaxterm.mobatek.net |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |