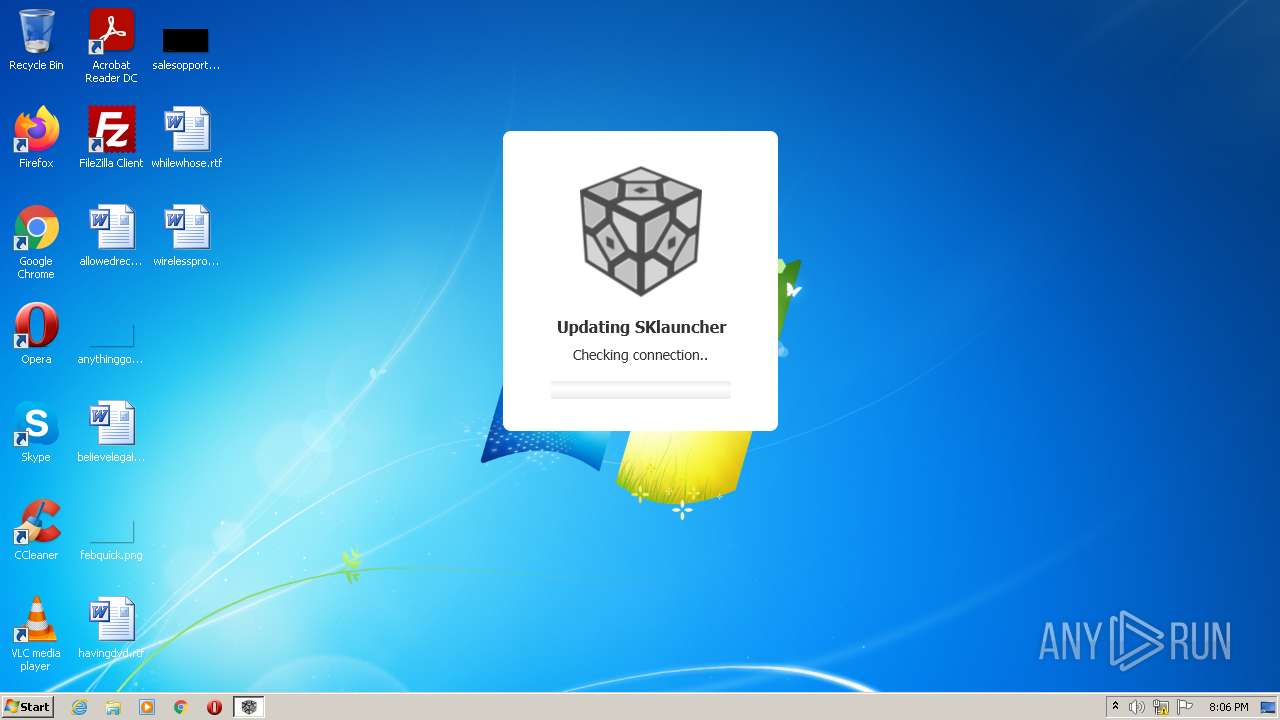
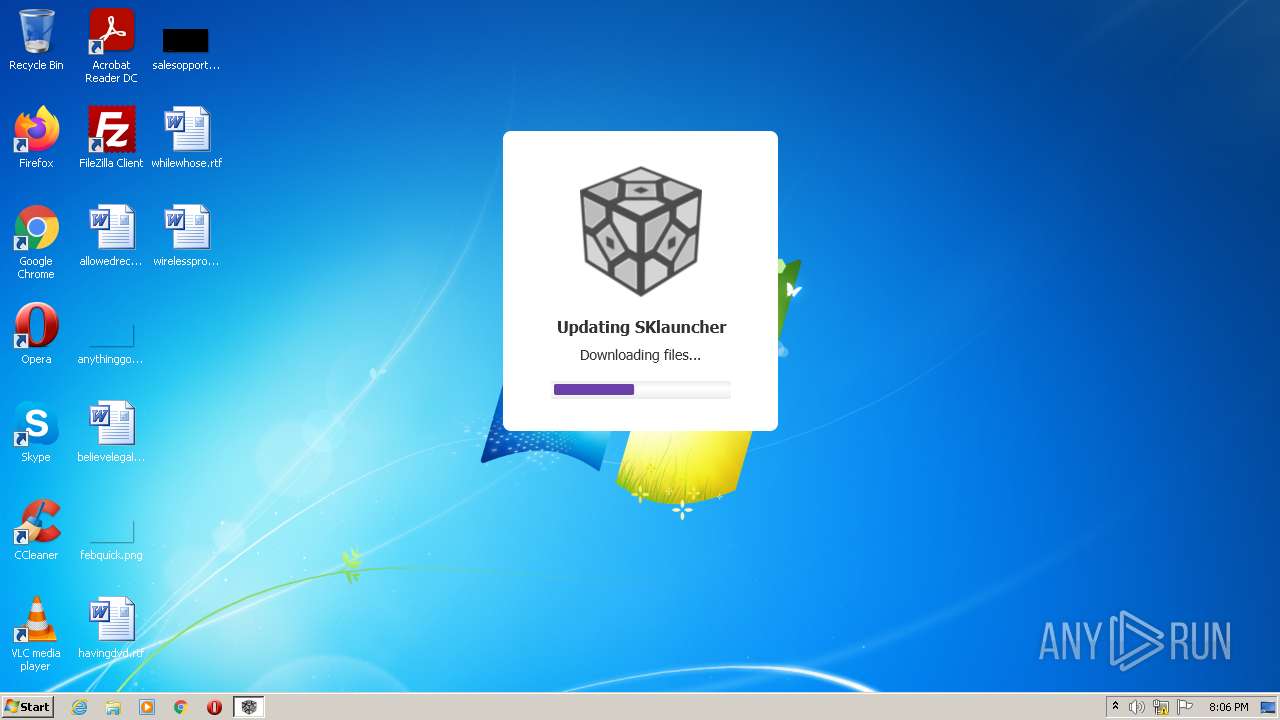
| File name: | SKlauncher 3-beta.21.exe |
| Full analysis: | https://app.any.run/tasks/6cc69303-472c-4674-97d2-e5b50f789243 |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2022, 19:06:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 4E137EDECC5F3EEB6ECC3F2CA1C88278 |
| SHA1: | 882B30957CC5BF736413AB916373230938797371 |
| SHA256: | E855BFEDBF5AEE0EE56B58B59C45C886219C290DAF3E23AF51126FE1862E613E |
| SSDEEP: | 6144:bch1HCBxAXouqxzk4kTdP9CSpBaQfV/RpO9jISSwh1v22R1FQpOY3C:wh1HsxAXEzk5qSCw/YISSoz6VC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- javaw.exe (PID: 3204)
- SKlauncher 3-beta.21.exe (PID: 2964)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 3900)
Executes JAVA applets
- SKlauncher 3-beta.21.exe (PID: 2964)
Check for Java to be installed
- SKlauncher 3-beta.21.exe (PID: 2964)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3204)
Creates files in the program directory
- javaw.exe (PID: 3204)
Reads the computer name
- javaw.exe (PID: 3204)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 3204)
Creates files in the user directory
- javaw.exe (PID: 3204)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3900)
- cmd.exe (PID: 3548)
INFO
Checks supported languages
- reg.exe (PID: 2480)
- icacls.exe (PID: 3432)
- reg.exe (PID: 2372)
Reads the computer name
- icacls.exe (PID: 3432)
Reads the hosts file
- javaw.exe (PID: 3204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
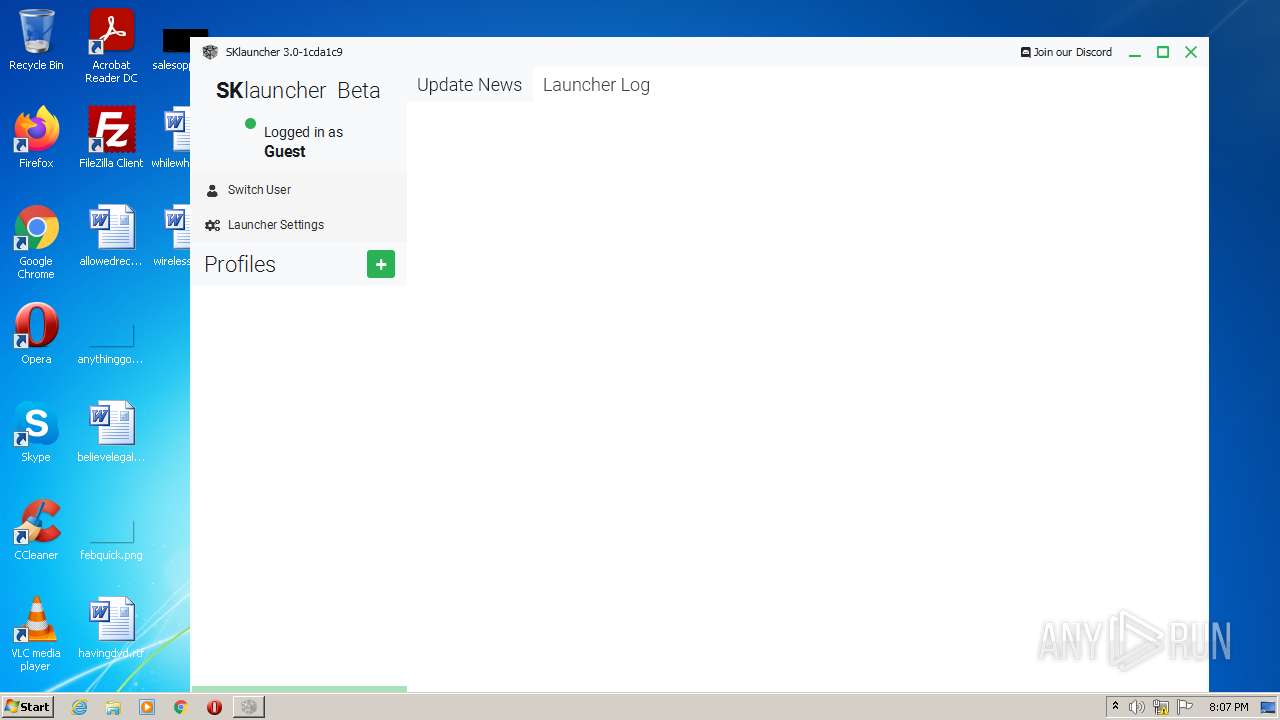
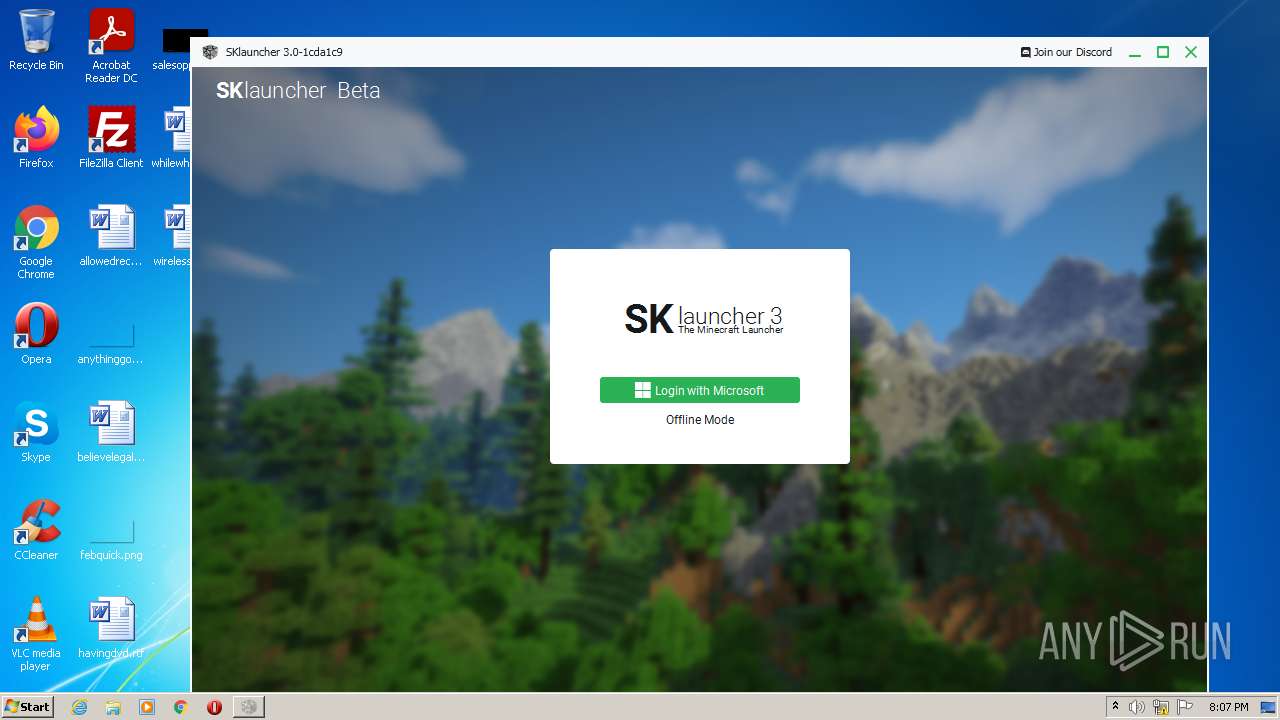
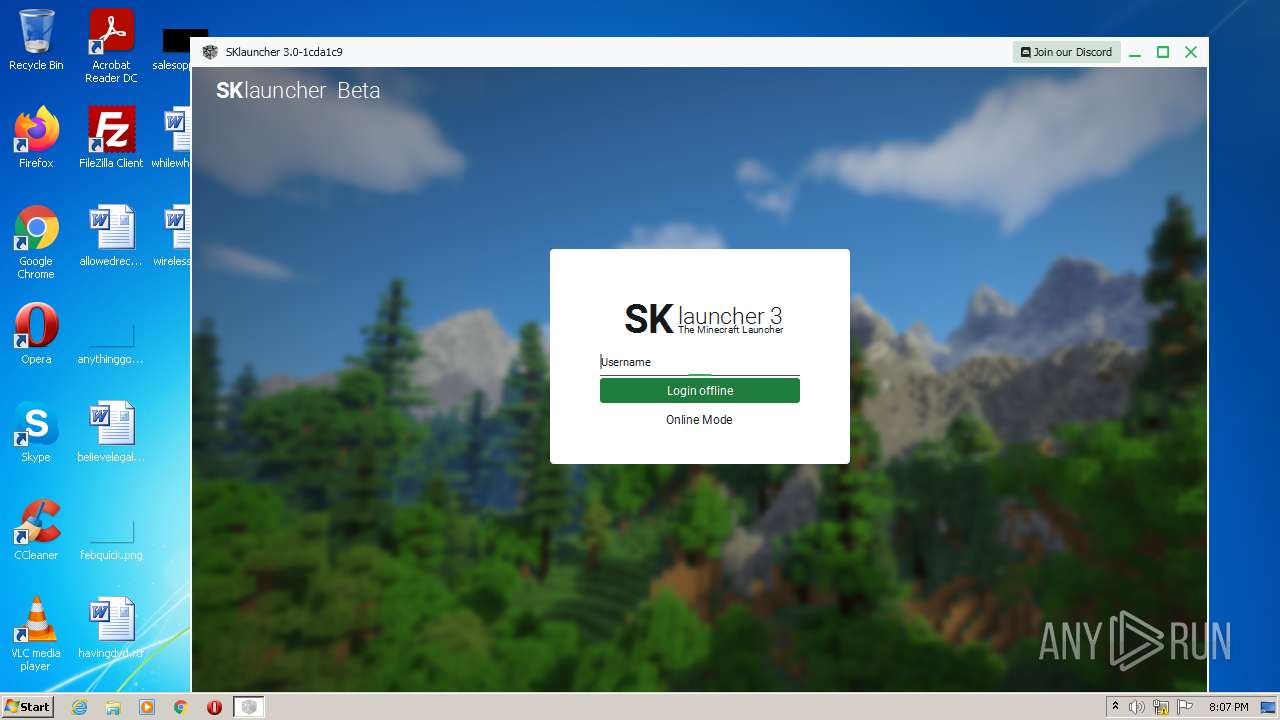
| ProductVersion: | 3.0.beta.21 |
|---|---|
| ProductName: | SKlauncher |
| OriginalFileName: | SKlauncher 3-beta.21.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Mojang |
| InternalName: | SKlauncher |
| FileVersion: | 3.0.beta.21 |
| FileDescription: | The Minecraft Launcher |
| CompanyName: | - |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.0.0.0 |
| FileVersionNumber: | 3.0.0.21 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 1 |
| OSVersion: | 4 |
| EntryPoint: | 0x1590 |
| UninitializedDataSize: | 36352 |
| InitializedDataSize: | 67072 |
| CodeSize: | 23040 |
| LinkerVersion: | 2.22 |
| PEType: | PE32 |
| TimeStamp: | 2022:04:08 16:05:33+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Apr-2022 14:05:33 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| CompanyName: | - |
| FileDescription: | The Minecraft Launcher |
| FileVersion: | 3.0.beta.21 |
| InternalName: | SKlauncher |
| LegalCopyright: | Mojang |
| LegalTrademarks: | - |
| OriginalFilename: | SKlauncher 3-beta.21.exe |
| ProductName: | SKlauncher |
| ProductVersion: | 3.0.beta.21 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 08-Apr-2022 14:05:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005970 | 0x00005A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.17063 |
.data | 0x00007000 | 0x00000010 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.11837 |
.rdata | 0x00008000 | 0x00000918 | 0x00000A00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.27517 |
.eh_fram\x14\x11 | 0x00009000 | 0x00001114 | 0x00001200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.82235 |
.bss | 0x0000B000 | 0x00008DCC | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00014000 | 0x00000CC0 | 0x00000E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.91037 |
.CRT | 0x00015000 | 0x00000018 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0980042 |
.tls | 0x00016000 | 0x00000020 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.231158 |
.rsrc | 0x00017000 | 0x0000D4E4 | 0x0000D600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.62467 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.29941 | 760 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 2.72548 | 9 | UNKNOWN | Process Default Language | RT_RCDATA |
3 | 2.64644 | 10 | UNKNOWN | Process Default Language | RT_RCDATA |
4 | 6.30866 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
5 | 7.97926 | 34399 | UNKNOWN | Process Default Language | RT_ICON |
10 | 3.61687 | 17 | UNKNOWN | Process Default Language | RT_RCDATA |
17 | 2.32193 | 5 | UNKNOWN | Process Default Language | RT_RCDATA |
18 | 1 | 2 | UNKNOWN | Process Default Language | RT_RCDATA |
20 | 1.58496 | 3 | UNKNOWN | Process Default Language | RT_RCDATA |
21 | 4.28034 | 49 | UNKNOWN | Process Default Language | RT_RCDATA |
Imports
advapi32.dll |
kernel32.dll |
msvcrt.dll |
shell32.dll |
user32.dll |
Total processes
43
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2964 | "C:\Users\admin\AppData\Local\Temp\SKlauncher 3-beta.21.exe" | C:\Users\admin\AppData\Local\Temp\SKlauncher 3-beta.21.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: The Minecraft Launcher Exit code: 0 Version: 3.0.beta.21 Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms32m -Xmx256m -jar "C:\Users\admin\AppData\Local\Temp\SKlauncher 3-beta.21.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | SKlauncher 3-beta.21.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3432 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | cmd /c reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3900 | cmd /c reg query HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize /v AppsUseLightTheme | C:\Windows\system32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
624
Read events
623
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3204) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
0
Suspicious files
4
Text files
6
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.pack | — | |
MD5:— | SHA256:— | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.data | text | |
MD5:5783DC92CB6B8FBE5E097B14F77CE6B5 | SHA256:C553B3A2374DB5B692C55C79FA4665FE80709FDDDEE8760804E55306F74350C3 | |||
| 3204 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:762CC4C9924BEEE11E5BBF63B74C68C4 | SHA256:753DB3DCE58D1F3AFBF0B0181B5610507726506644069D4F92214A7436DDEE79 | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher-fx.jar | compressed | |
MD5:71018DB378116973D0A39ECE4D75871C | SHA256:B1161109679D3C2D6AAB89A182AC5E313D94014370DA1FAD7CBEAAD43BB1676F | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Local\Temp\SKL_TempStyleClass7980135038845676120.css | text | |
MD5:F6BB54CC82CCCDE375586BD60956F8F0 | SHA256:CF7A773FEB617CFF6997958B31FA9A2002BDACE2906F6BB0FBC4FC8D2A81C88A | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio39187821722761363.tmp | image | |
MD5:8A3AA70CC7F4AB154945641A845505D2 | SHA256:8F7995E7DD527DACD3EAF2A64F24EB1F753DEC374A89615B4E9EC770EE0DDE06 | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF2992864646771934043.tmp | ttf | |
MD5:13685372945D816A2B474FC082FD9AAA | SHA256:A0C145382ACFE59767D1487D6505F349665B685C2885CD91B621D141A292B0F8 | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF1578419573494545839.tmp | ttf | |
MD5:DB78B9359171F24936B16D84F63AF378 | SHA256:F32B94A29060DFEC0C797A1DFE111357EB1D682F1ACA4AC4B95CF0F4C3E2BFA9 | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\launcher_profiles.json | binary | |
MD5:5FABCD9DB58925C6DAAB4CDD621C84B9 | SHA256:5287090CCC2607673B601C837CD8112216576B3351077A6810451AB7B840EE1C | |||
| 3204 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF8438291751003273182.tmp | ttf | |
MD5:1AB236ED440EE51810C56BD16628AEF0 | SHA256:231D68CEFBC6846FB78CAFCA8467401A4F371E226418662E8900E3D52ADC00AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
48
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
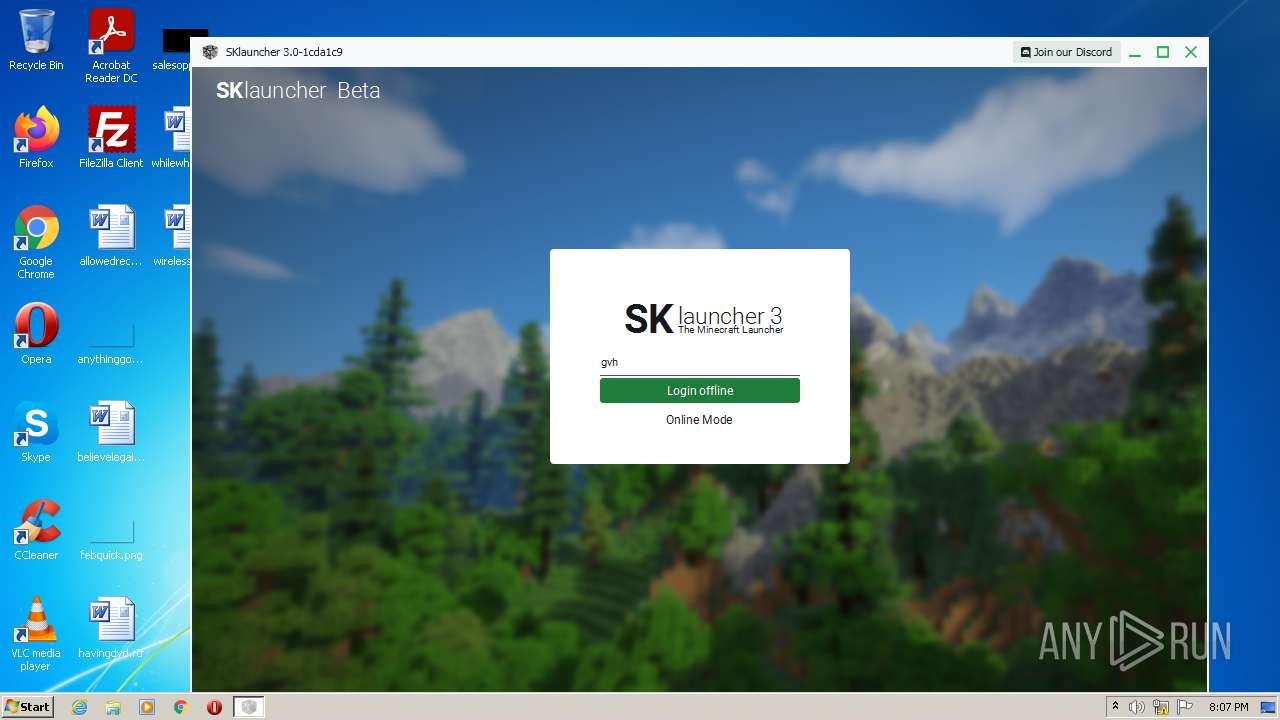
3204 | javaw.exe | GET | 204 | 188.114.97.3:80 | http://api.skmedix.pl/v2/skin/name/gvh | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
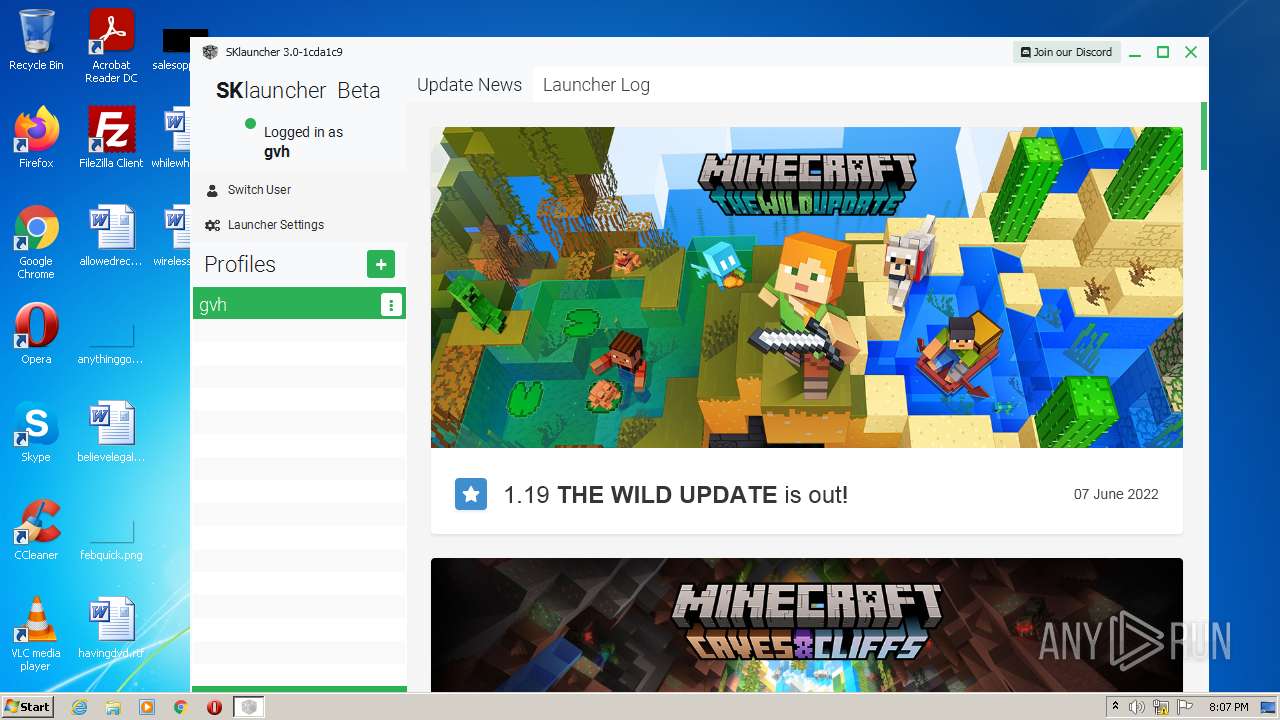
3204 | javaw.exe | 152.199.21.175:443 | piston-meta.mojang.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 188.114.96.3:443 | files.skmedix.pl | Cloudflare Inc | US | malicious |
3204 | javaw.exe | 142.250.185.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3204 | javaw.exe | 142.250.185.168:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3204 | javaw.exe | 104.18.47.230:443 | static.cloudflareinsights.com | Cloudflare Inc | US | malicious |
3204 | javaw.exe | 142.250.185.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3204 | javaw.exe | 142.250.181.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
3204 | javaw.exe | 142.250.185.194:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
3204 | javaw.exe | 142.250.184.194:443 | partner.googleadservices.com | Google Inc. | US | suspicious |
3204 | javaw.exe | 104.16.87.20:443 | cdn.jsdelivr.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.skmedix.pl |
| malicious |
bitbucket.org |
| shared |
bbuseruploads.s3.amazonaws.com |
| shared |
news.skmedix.pl |
| malicious |
www.google-analytics.com |
| whitelisted |
piston-meta.mojang.com |
| suspicious |
cdn.jsdelivr.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
twemoji.maxcdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3204 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |