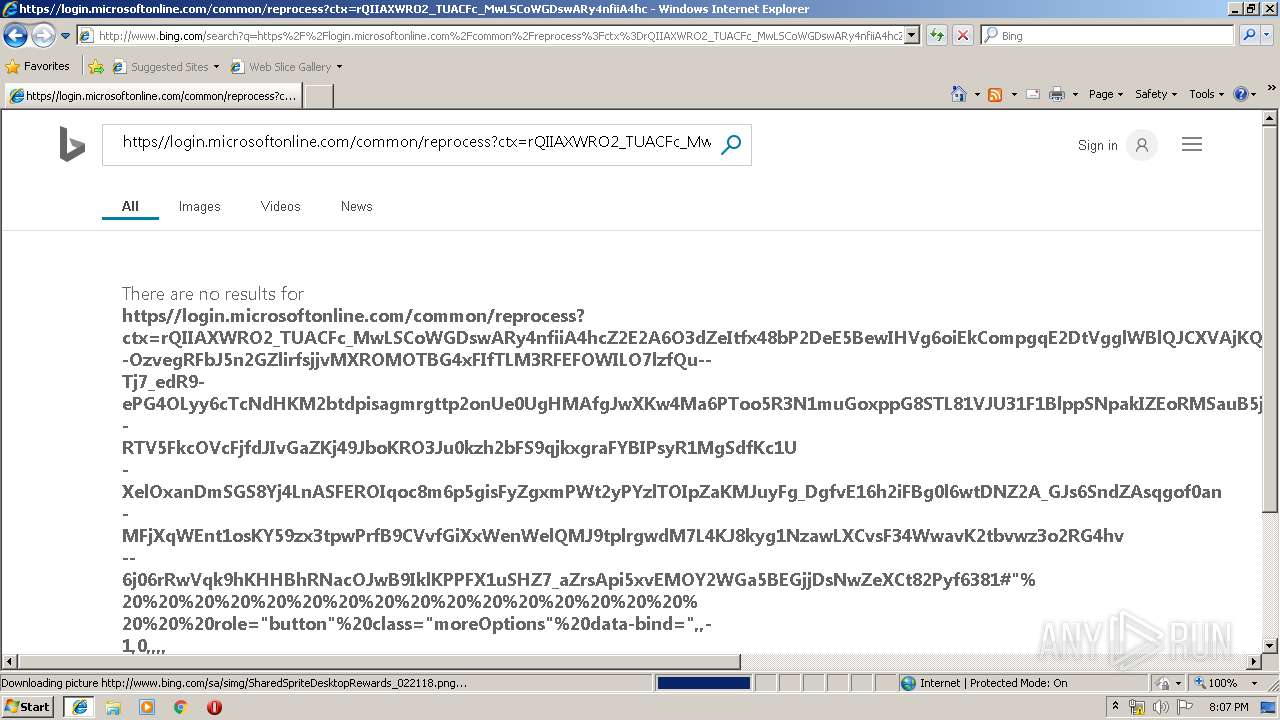
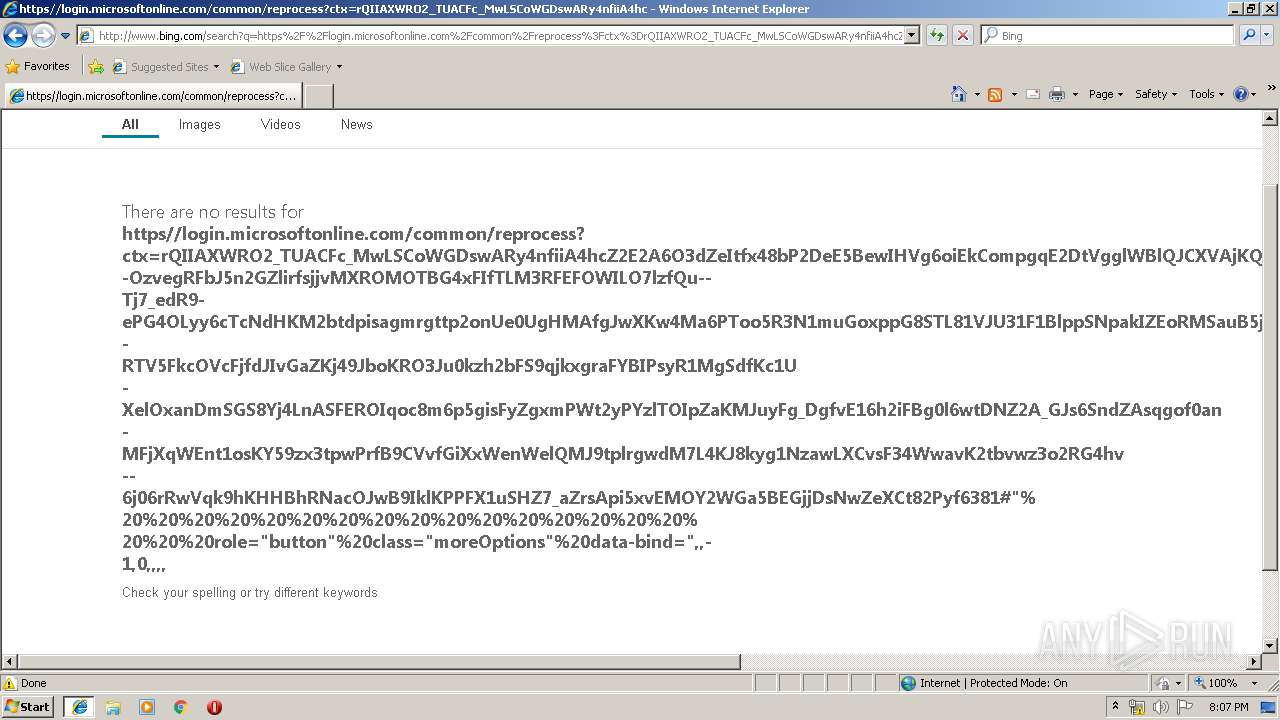
| URL: | https://login.microsoftonline.com/common/reprocess?ctx=rQIIAXWRO2_TUACFc_MwLSCoWGDswARy4nfiiA4hcZ2E2A6O3dZeItfx48bP2DeE5BewIHVg6oiEkCompgqE2DtVgglWBlQJCXVAjKQ_gOVMR5-OzvegRFbJ5n2GZlirfsjjvMXROMOTBG4xFIfTLM3RFEFOWILO7lzfQu--Tj7_edR9-ePG4OLyy6cTcNdHKM2btdpisagmrgttp2onUe0UgHMAfgJwXKw4Ma6PToo5R3N1muGoxppG8STL81VJU31F1BlppSNpakIZEoRMSauB5jHS9CmSRJ2StUlk7JuhFOmMMTVYRbMXSkdHZsePlDZBmOIuHOzvhvKaoYh7vjQNlsZKWMmRTn4r3lZac-RTV5FkcOVcFjfdJIvGaZKj49JboKRO3Ju0kzh2bFS9qjkxgraFYBIPsyR1MgSdfKc1U-XelOxanDmSGS8Yj4LnASFEROIqoc8m6p5gisFyZgxmPWt2yPYzlTOIpZaKMJuyFg_DgfvE16h2iFBg0l6wtDNZ2A_GJs6SndZAsqgof0an-MFjXqWEnt1osKY59zx3tpwPrfB9CVvfGiXxWenWelQMJ9tplrgwdM7L4KJ8kyg1NzawLXCvsF34WwavK2tbvwz3o2RG4hv--6j06rRwVqk9hKHHBhRNacOJwB9IklKPPFX1uSHZ7_aZrsApi5xvEMOY2WGa5BEGjjDsNwZeXCt82Pyf6381#"%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20role="button"%20class="moreOptions"%20data-bind= |
| Full analysis: | https://app.any.run/tasks/e978b18c-f96c-4102-b880-dbecffa0ea51 |
| Verdict: | No threats detected |
| Analysis date: | July 25, 2019, 19:06:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FA5679042028D5810D7D31BE00E7A0C9 |
| SHA1: | 76E6C27543B33675916099E98518FF5506001C3B |
| SHA256: | E830FCE2F6EB778321D1E4F39F11F6104B29964F117D5E559580D0220AE7F93F |
| SSDEEP: | 24:2v+smYw52w5Eey34AZ+0lNUnUT6wQAeVTTa1st8hErZw16EbY8VFt6T:u+smYw5VivR+0lNj6wAVT98hiZwQEDlS |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 3860)
Creates files in the user directory
- iexplore.exe (PID: 3440)
Reads Internet Cache Settings
- iexplore.exe (PID: 3440)
- iexplore.exe (PID: 3860)
Reads internet explorer settings
- iexplore.exe (PID: 3440)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3860 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3860 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
437
Read events
359
Write events
76
Delete events
2
Modification events
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {5E57E6A3-AF0F-11E9-95C0-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3860) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700040019001300060038005C02 | |||
Executable files
0
Suspicious files
0
Text files
25
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3860 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\THOJPES7\search[1].txt | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\8BW8CI0Y\f2056989[1].js | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@www.bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\THOJPES7\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RIMVM10U\Passport[1].aspx | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
13
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5m/cj,nj/c44ec255/9a358300.js?bu=EqQfxh_lHvAe0wT-HvUe2x-AH4ofkB_BH78fth-cHqkdrx2nHg | US | text | 4.95 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/83a49848/f2056989.js?bu=DikuX293e2tjZ7MBtwEupwEu | US | text | 7.54 Kb | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/25/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=D9007CE2B7E741C7844F32EAA53CEF43&CID=35AC056649496506171608C248616406&Type=Event.ClientInst&DATA=[{"T":"CI.GetError","FID":"CI","Name":"JSGetError","Text":"Member%20not%20found.%0D%0A","Meta":"http%3A//www.bing.com/rb/14/cj%2Cnj/83a49848/f2056989.js%3Fbu%3DDikuX293e2tjZ7MBtwEupwEu","Line":2,"Char":%20undefined}] | US | compressed | 181 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/31/2n/cj,nj/bf587ad6/f1d86b5a.js | US | text | 181 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 13.107.6.163:80 | http://8bfa24a8170831f51dbb598b89c49654.clo.footprintdns.com/apc/trans.gif | US | image | 43 b | suspicious |
3440 | iexplore.exe | GET | 200 | 52.231.32.10:80 | http://2903f793d7085b9b7dd43e9284c1b4a4.clo.footprintdns.com/apc/trans.gif | KR | image | 43 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/Passport.aspx?popup=1 | US | html | 230 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 13.107.4.254:80 | http://6a07806b92509335fae820de42ef5d2d.clo.footprintdns.com/apc/trans.gif | US | image | 43 b | suspicious |
3440 | iexplore.exe | POST | 204 | 204.79.197.200:80 | http://www.bing.com/fd/ls/lsp.aspx | US | compressed | 230 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 40.90.23.233:443 | login.live.com | Microsoft Corporation | US | unknown |
3440 | iexplore.exe | 52.231.32.10:80 | 2903f793d7085b9b7dd43e9284c1b4a4.clo.footprintdns.com | Microsoft Corporation | KR | whitelisted |
3440 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 13.107.6.163:80 | 8bfa24a8170831f51dbb598b89c49654.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 13.107.4.254:80 | 6a07806b92509335fae820de42ef5d2d.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
3440 | iexplore.exe | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
2903f793d7085b9b7dd43e9284c1b4a4.clo.footprintdns.com |
| unknown |
8bfa24a8170831f51dbb598b89c49654.clo.footprintdns.com |
| suspicious |
6a07806b92509335fae820de42ef5d2d.clo.footprintdns.com |
| suspicious |
fp.msedge.net |
| whitelisted |