| File name: | C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.zip |
| Full analysis: | https://app.any.run/tasks/e922123c-7362-4922-aca8-ad0c80c43783 |
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 15:04:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9DDCD8CD70D45EF87AF9F600D1541CD4 |
| SHA1: | CA690E748241345A9F09F25DCACAA66A0B4B82B1 |
| SHA256: | E82F0274F74174F0B3C8DED993086112158F3B3787127F8711DAFFBF1858A774 |
| SSDEEP: | 3072:eCv/e2LqBmQY4BTD1BBKjJmzcc9ijLSSdbfrqRP:eCO2us4VhWy9ijhbDqB |
MALICIOUS
Application was dropped or rewritten from another process
- C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe (PID: 3040)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2840)
Creates files in the user directory
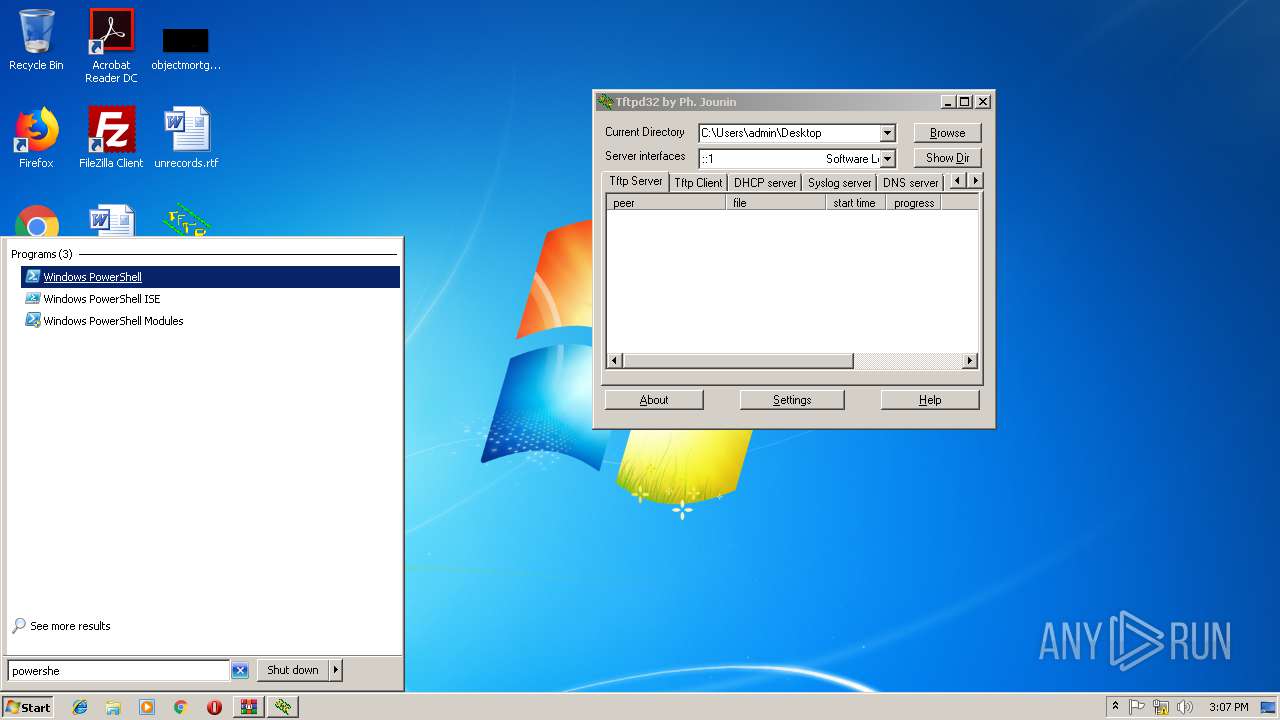
- powershell.exe (PID: 3900)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
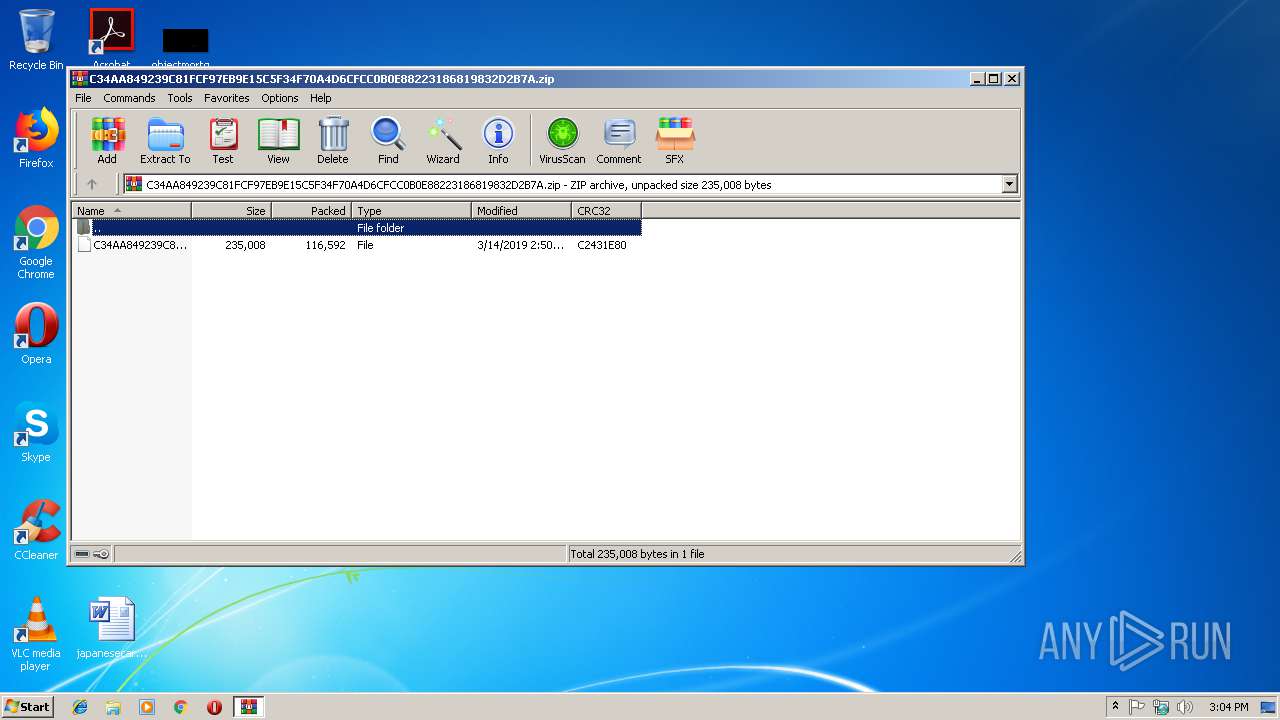
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:14 14:51:00 |
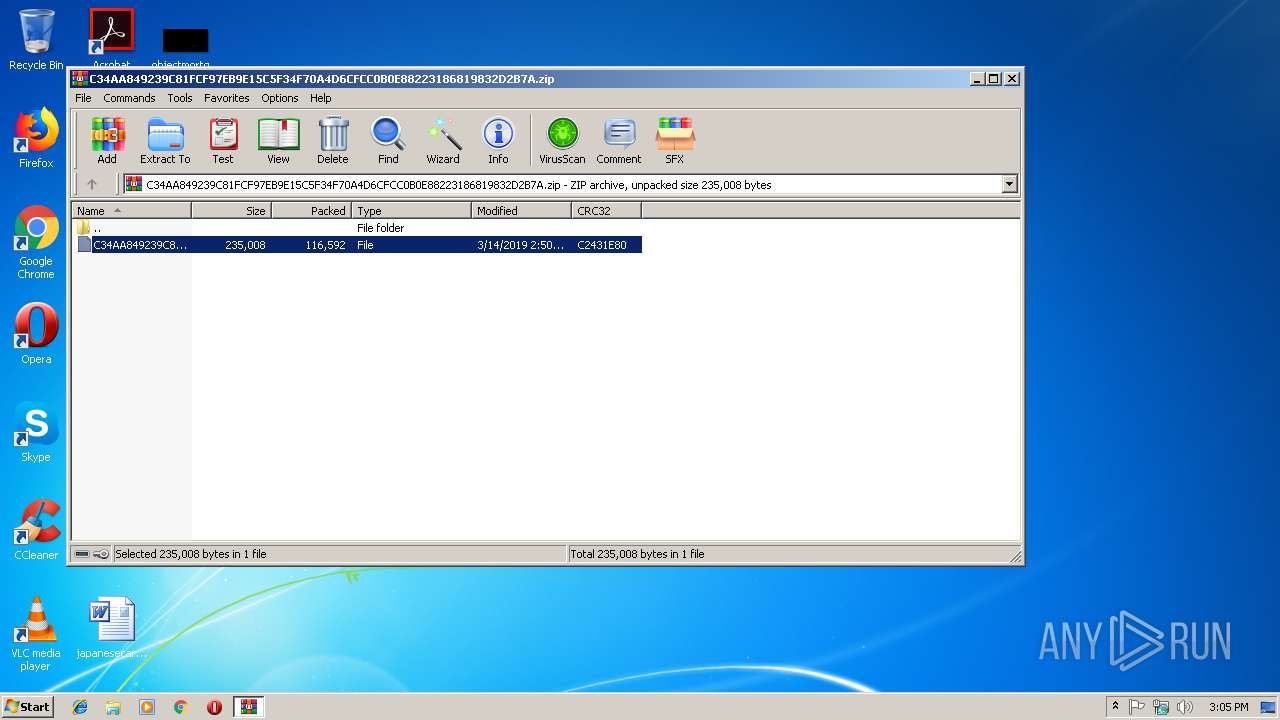
| ZipCRC: | 0xc2431e80 |
| ZipCompressedSize: | 116592 |
| ZipUncompressedSize: | 235008 |
| ZipFileName: | C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2512 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
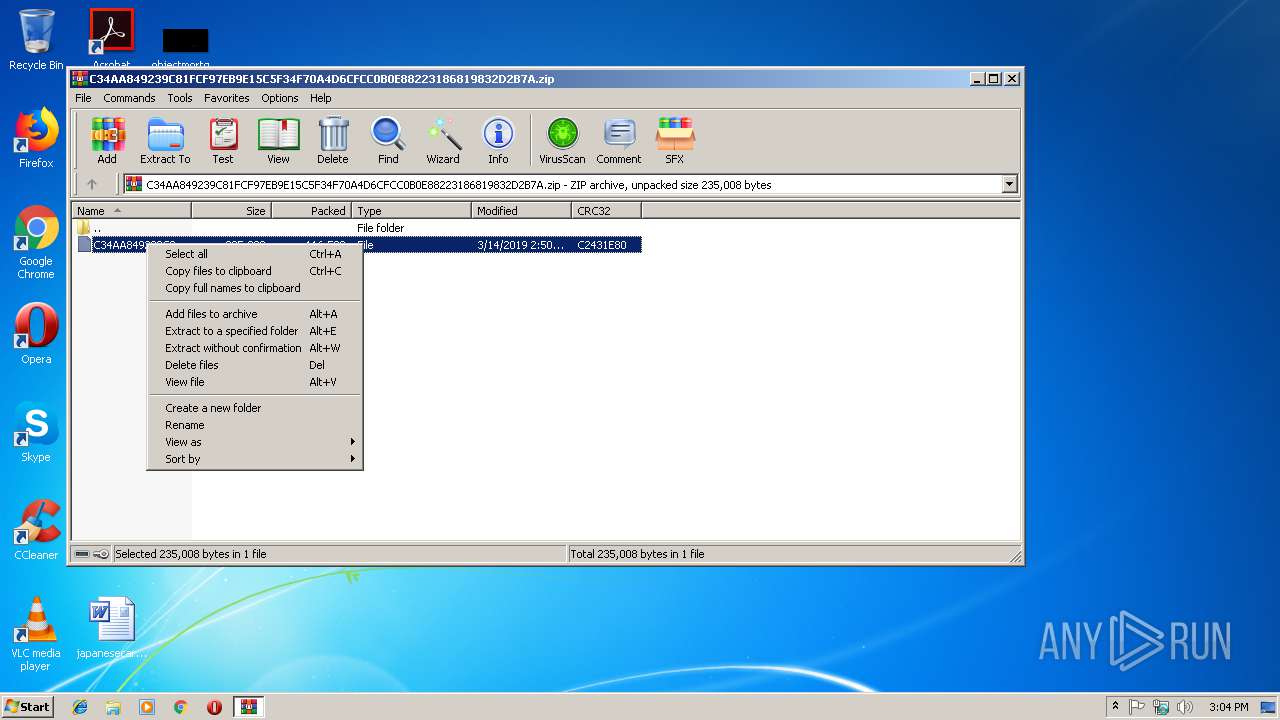
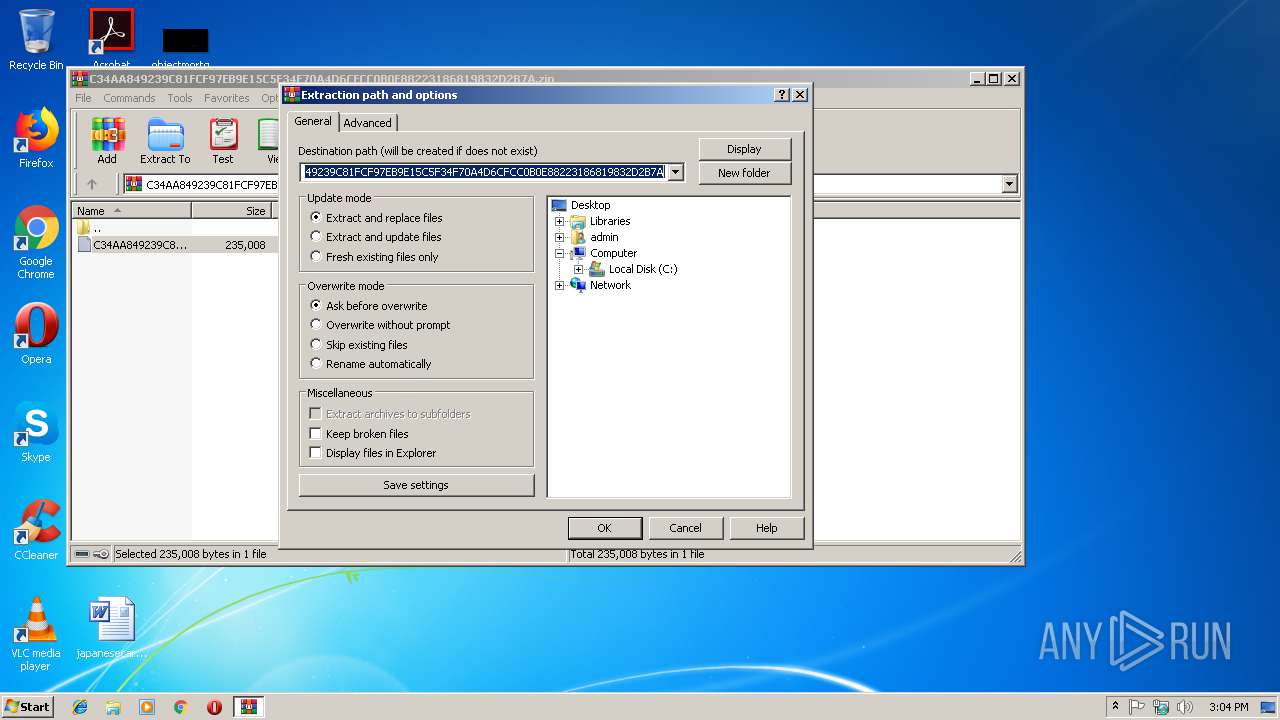
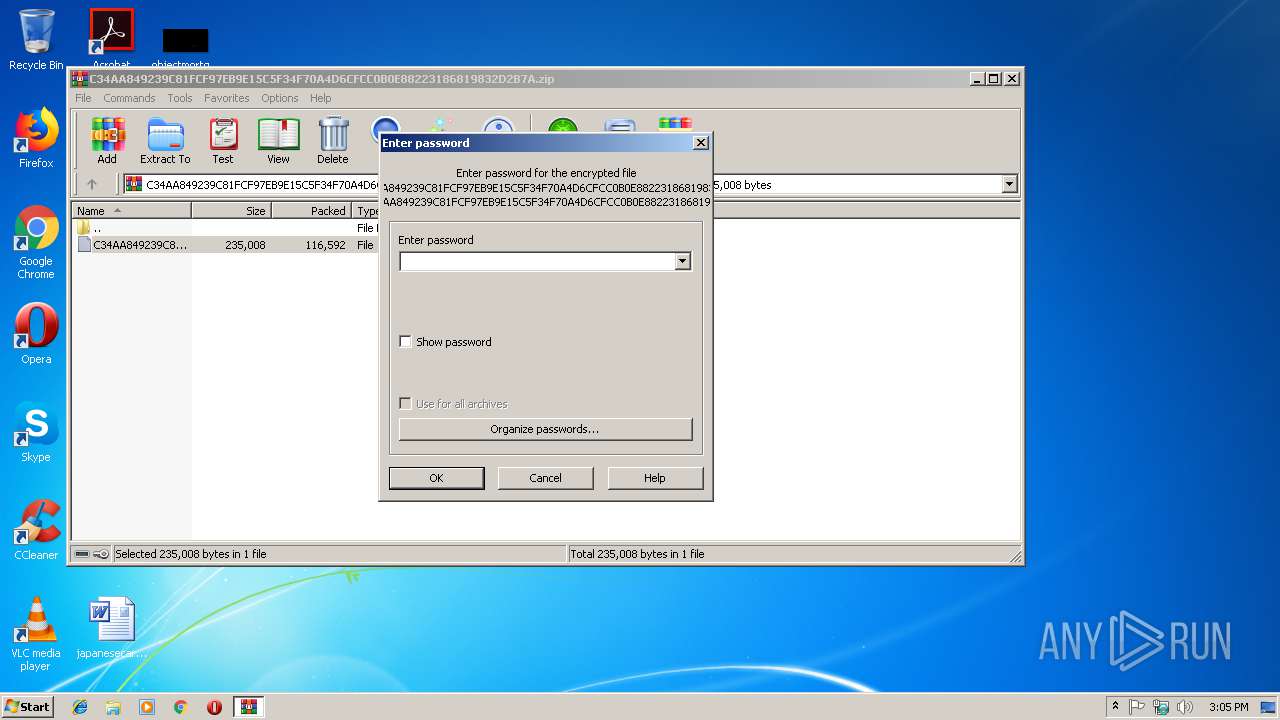
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
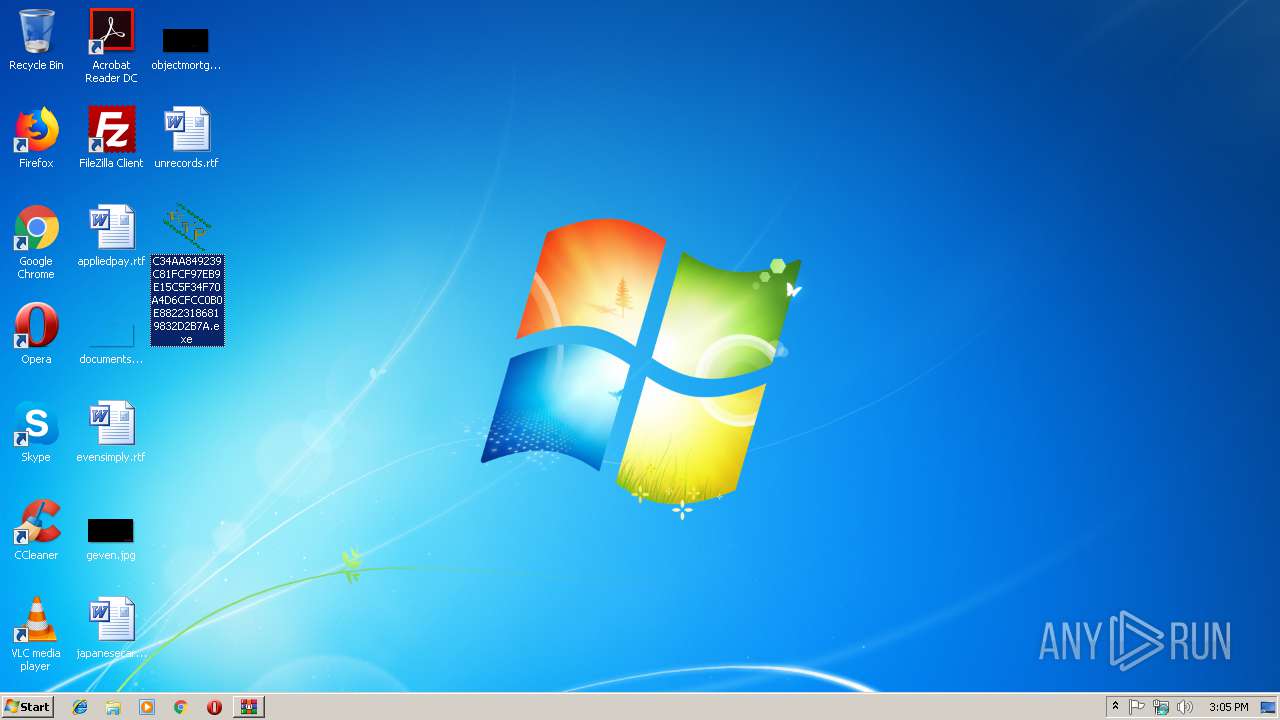
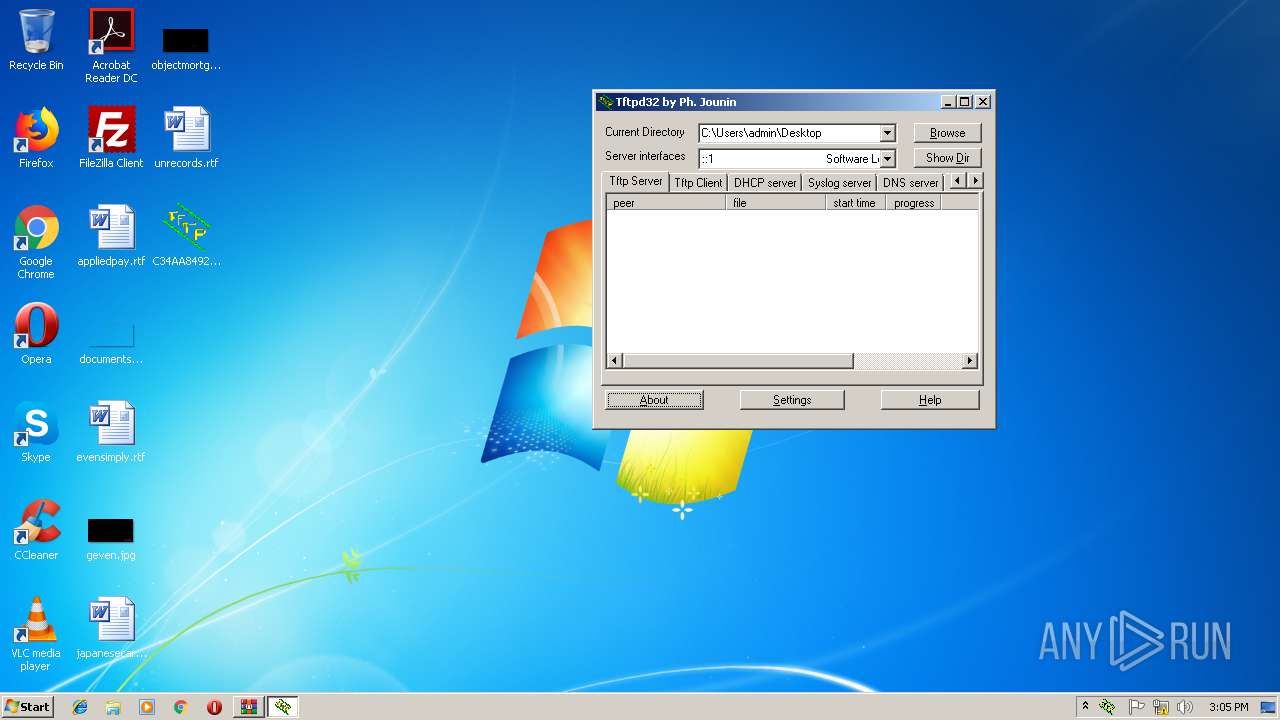
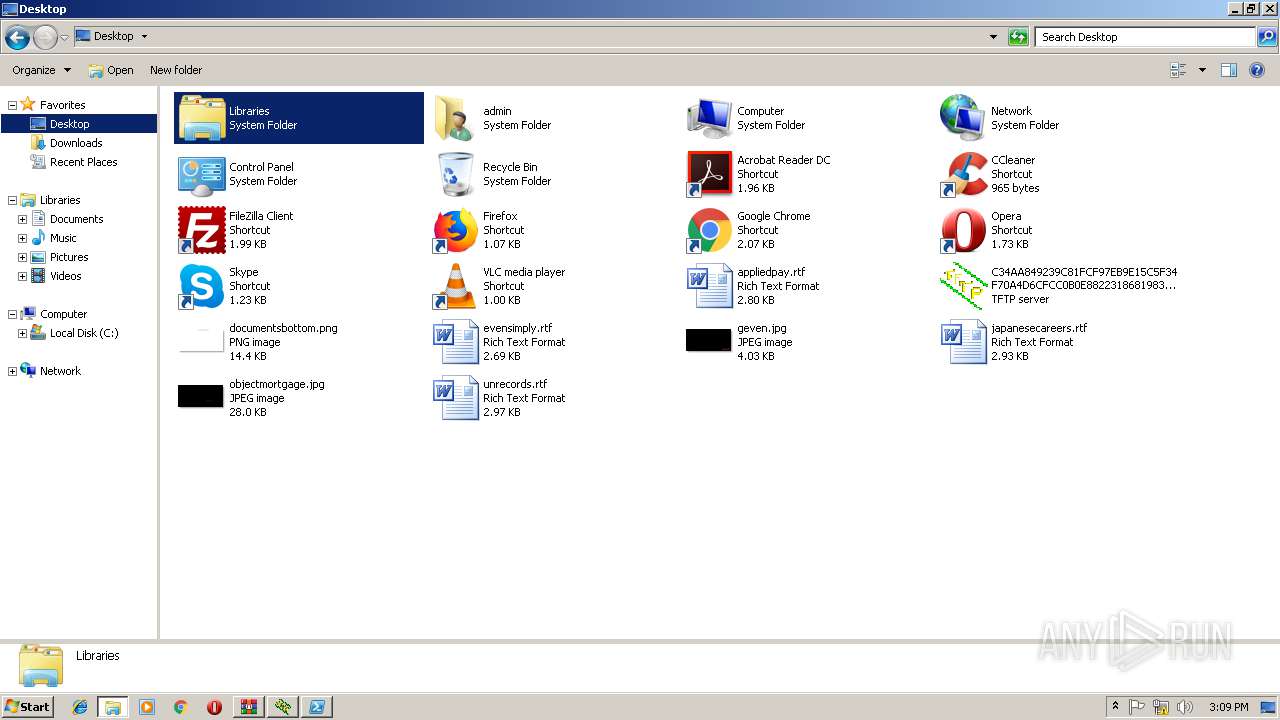
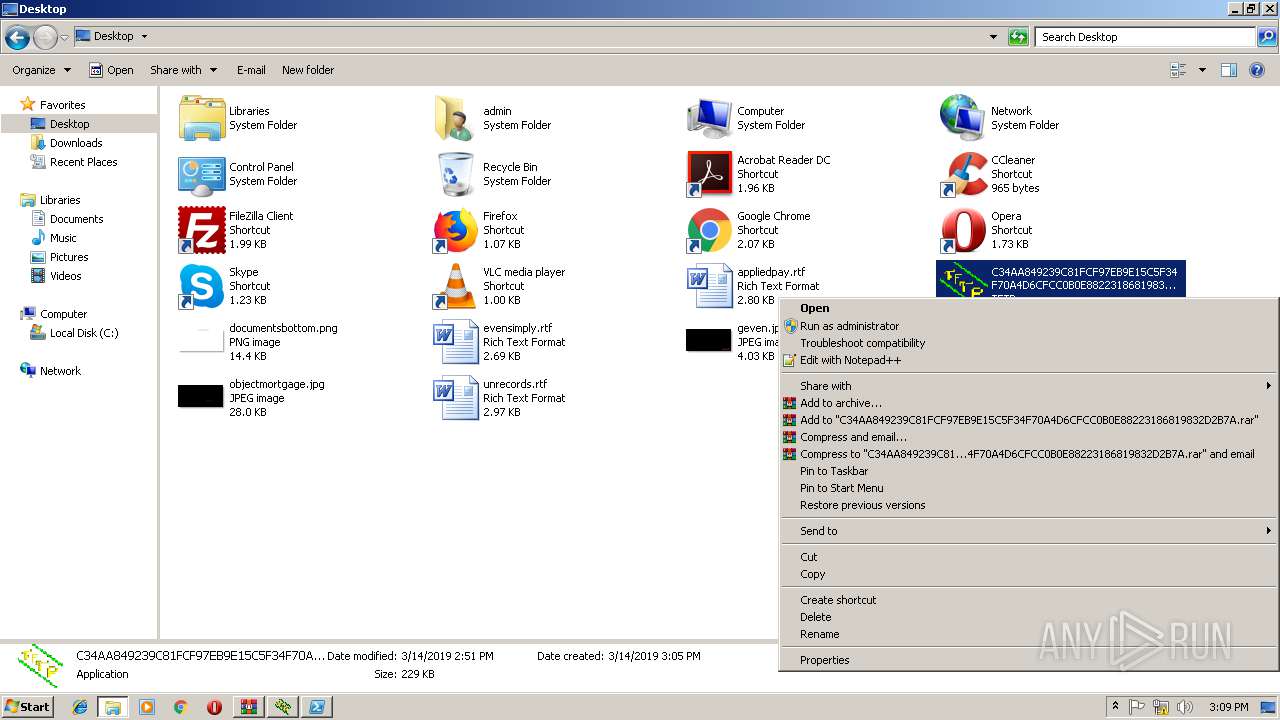
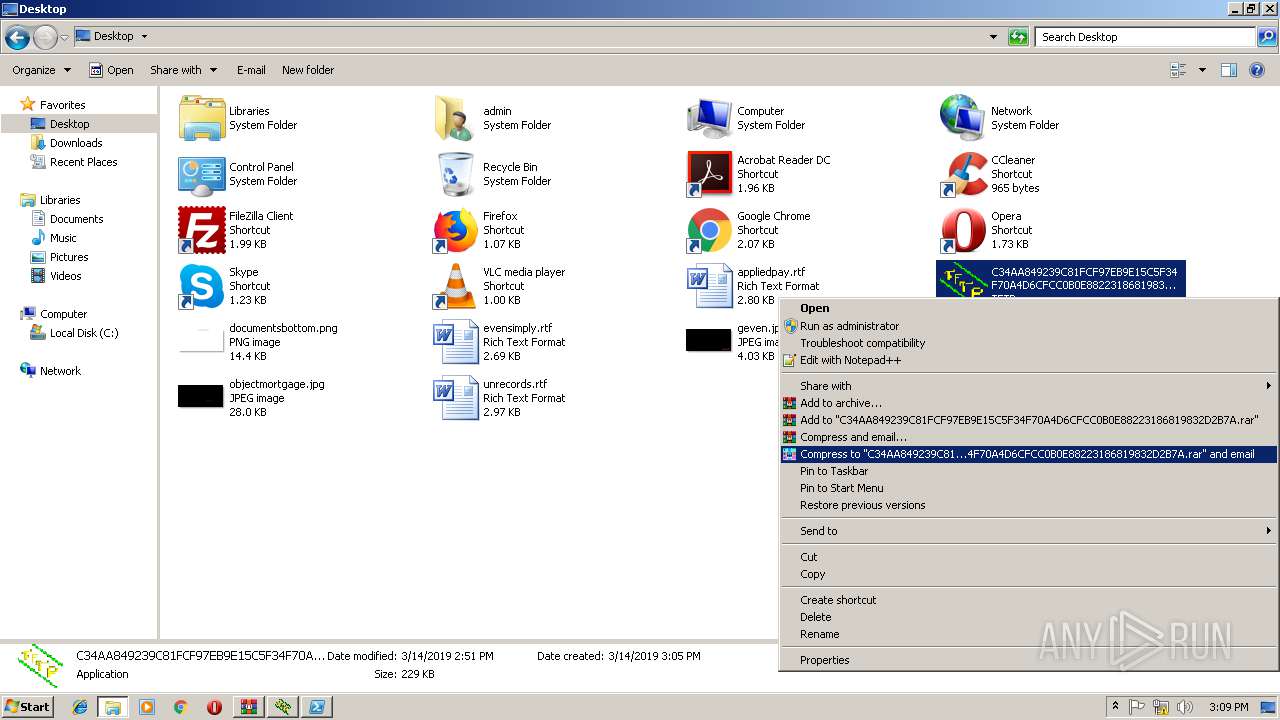
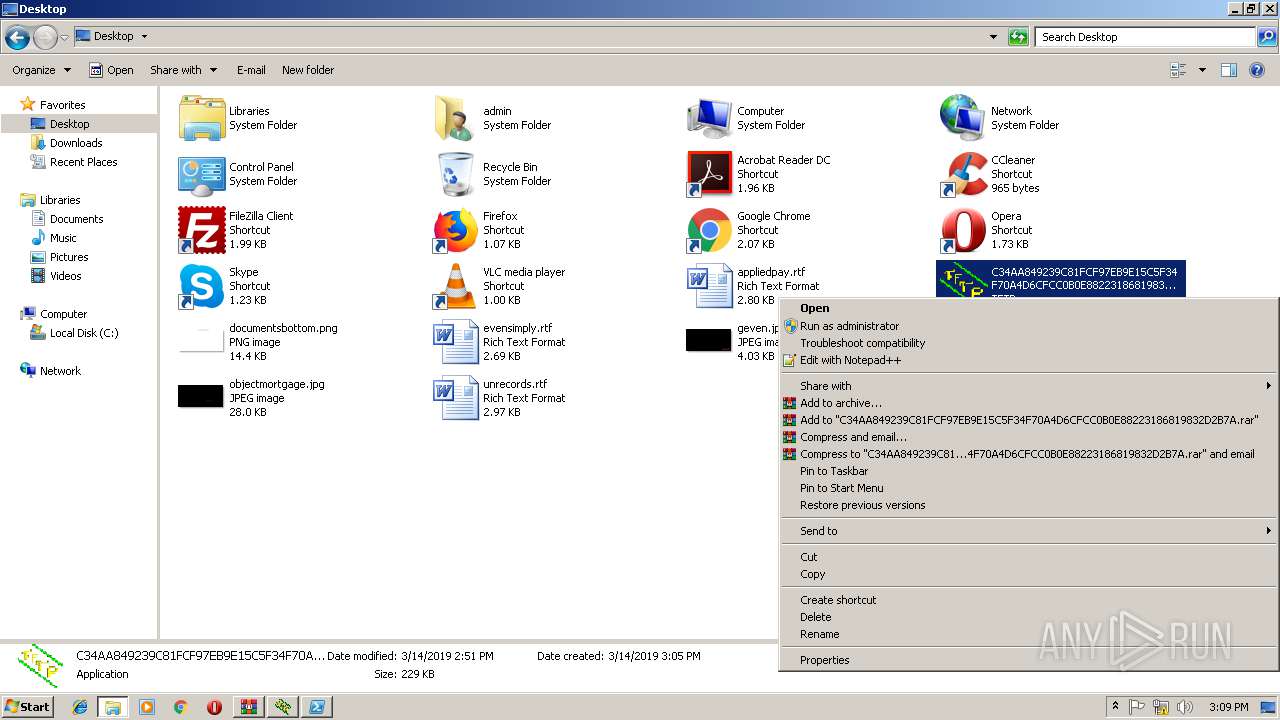
| 3040 | "C:\Users\admin\Desktop\C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe" | C:\Users\admin\Desktop\C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | explorer.exe | ||||||||||||
User: admin Company: Ph. Jounin Integrity Level: MEDIUM Description: TFTP server Exit code: 0 Modules
| |||||||||||||||
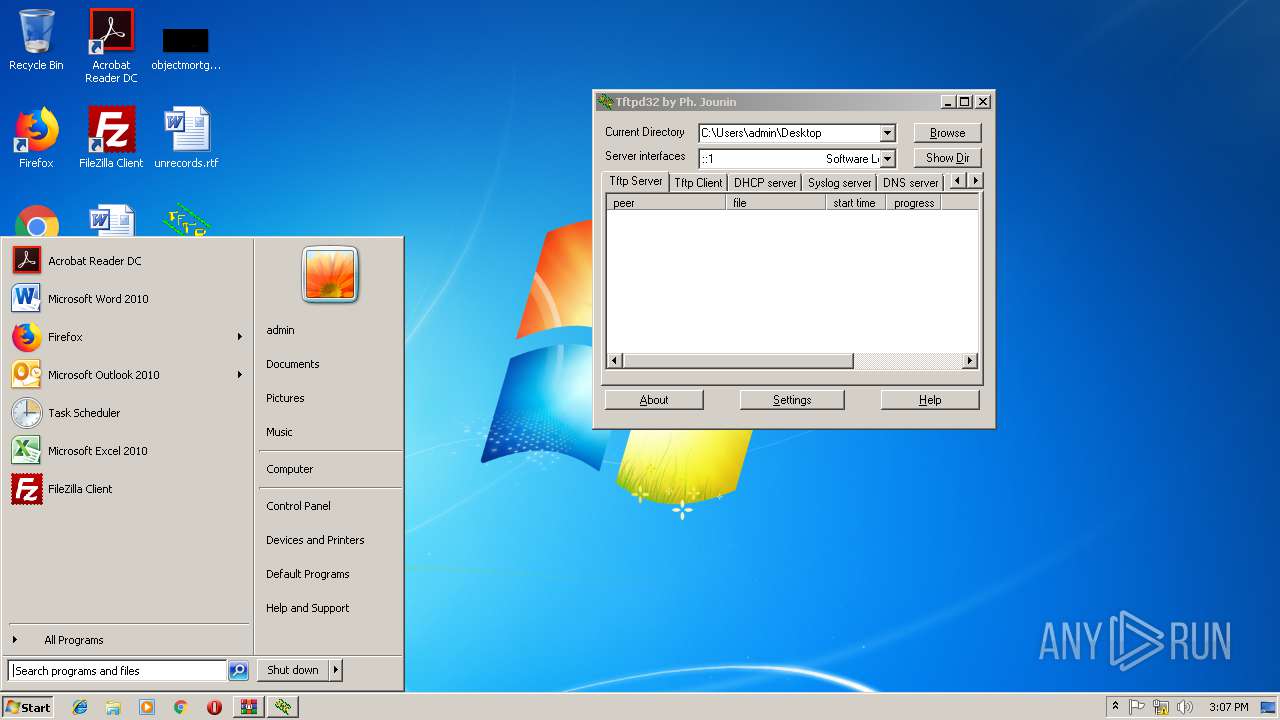
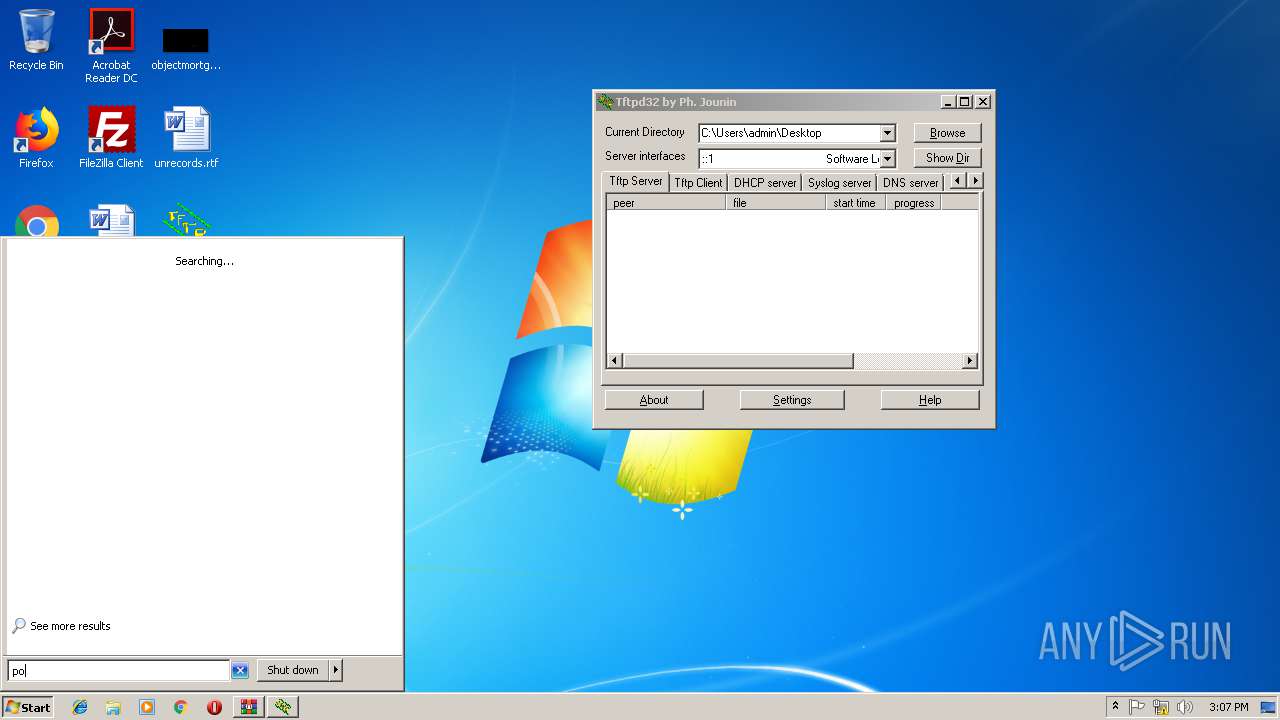
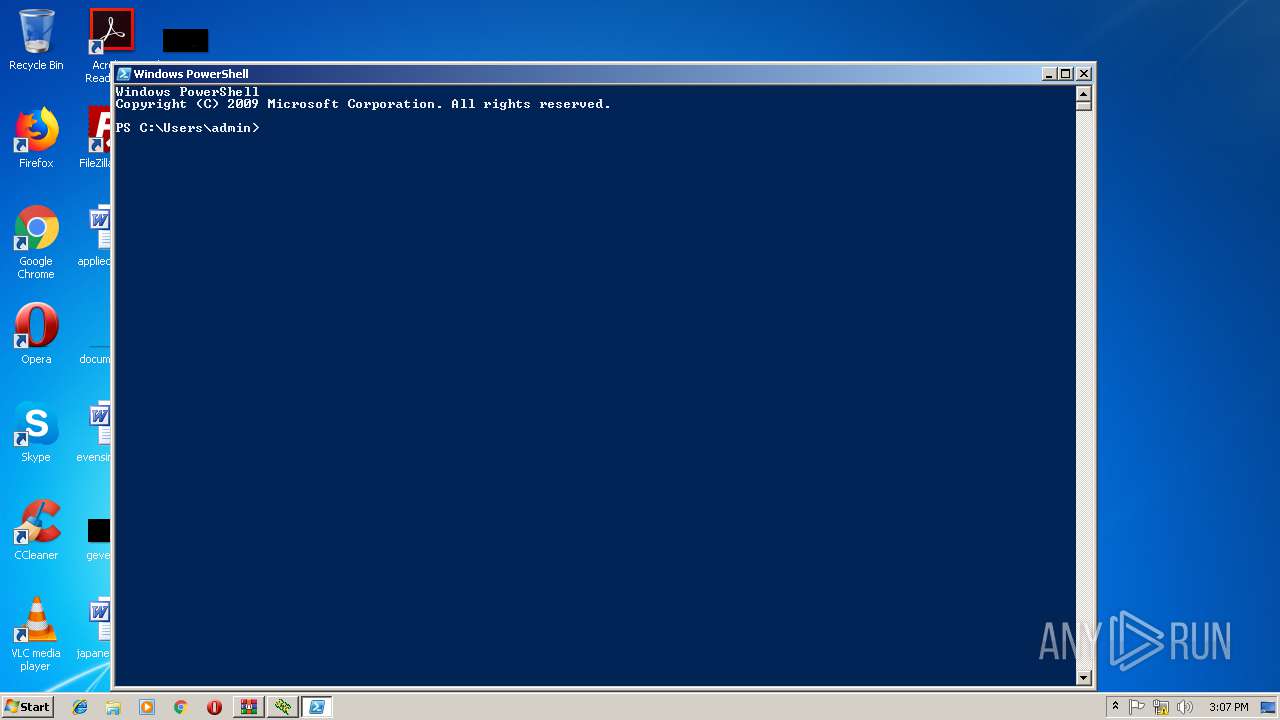
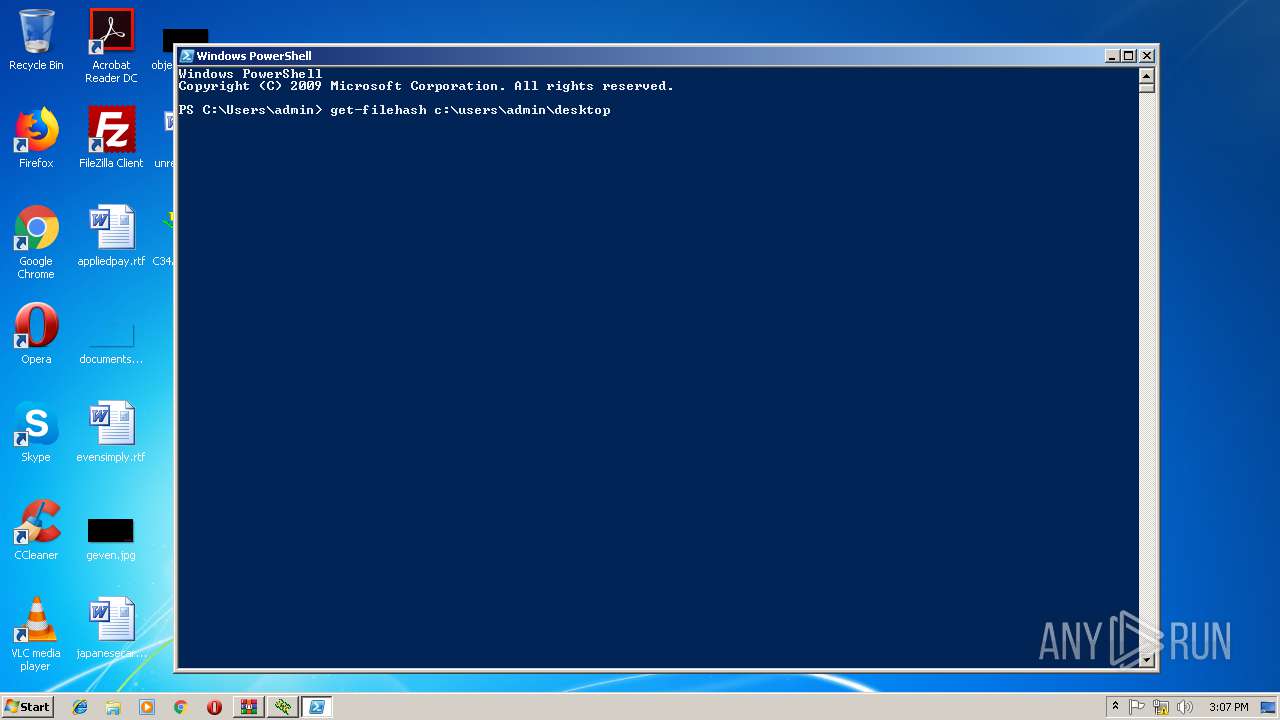
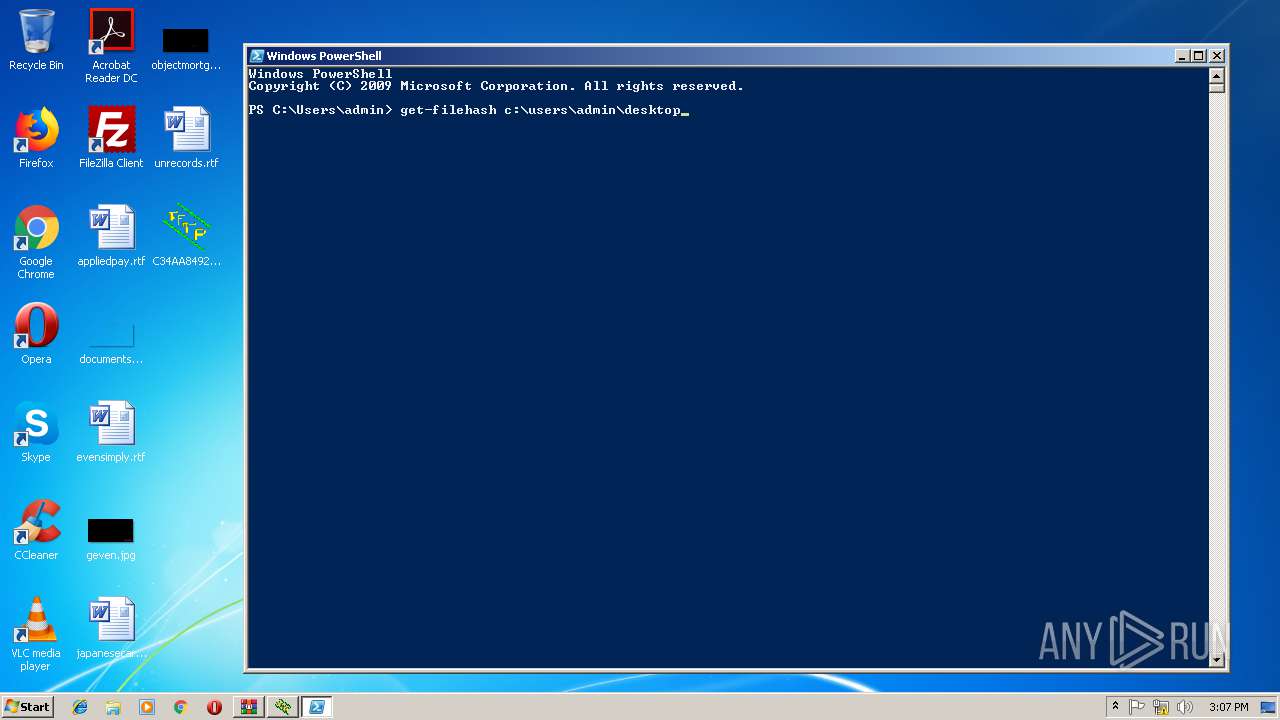
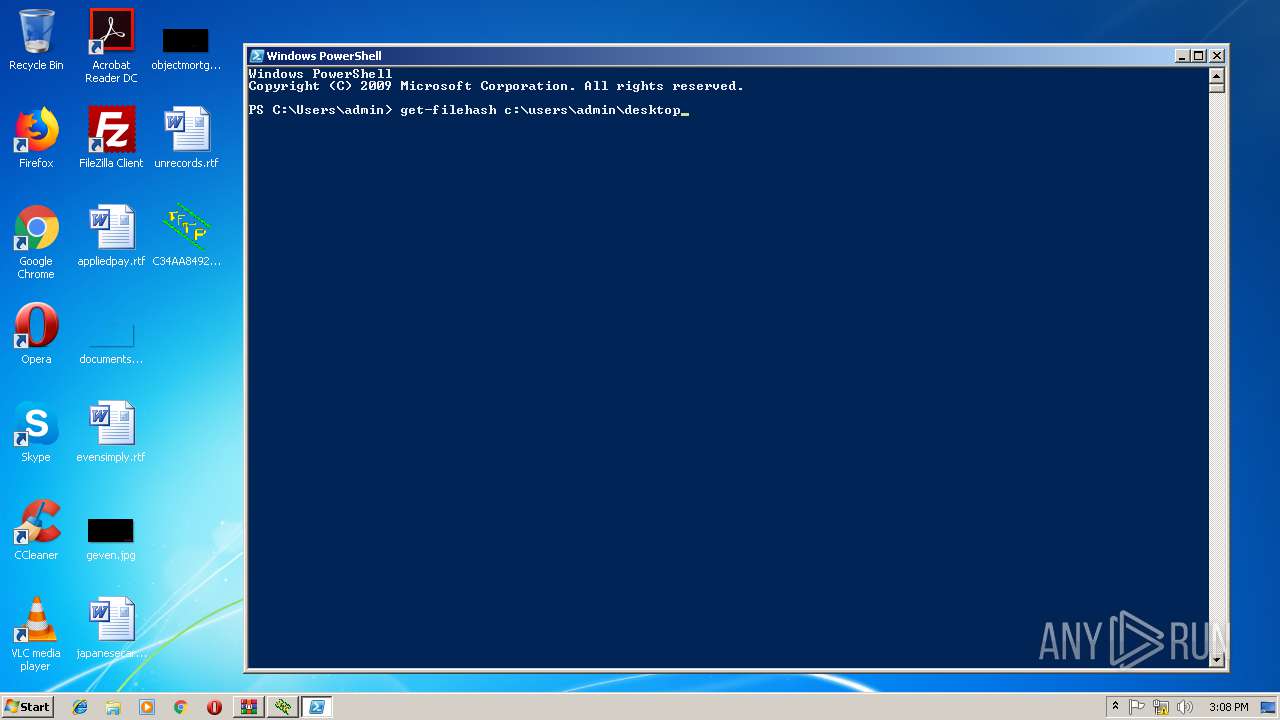
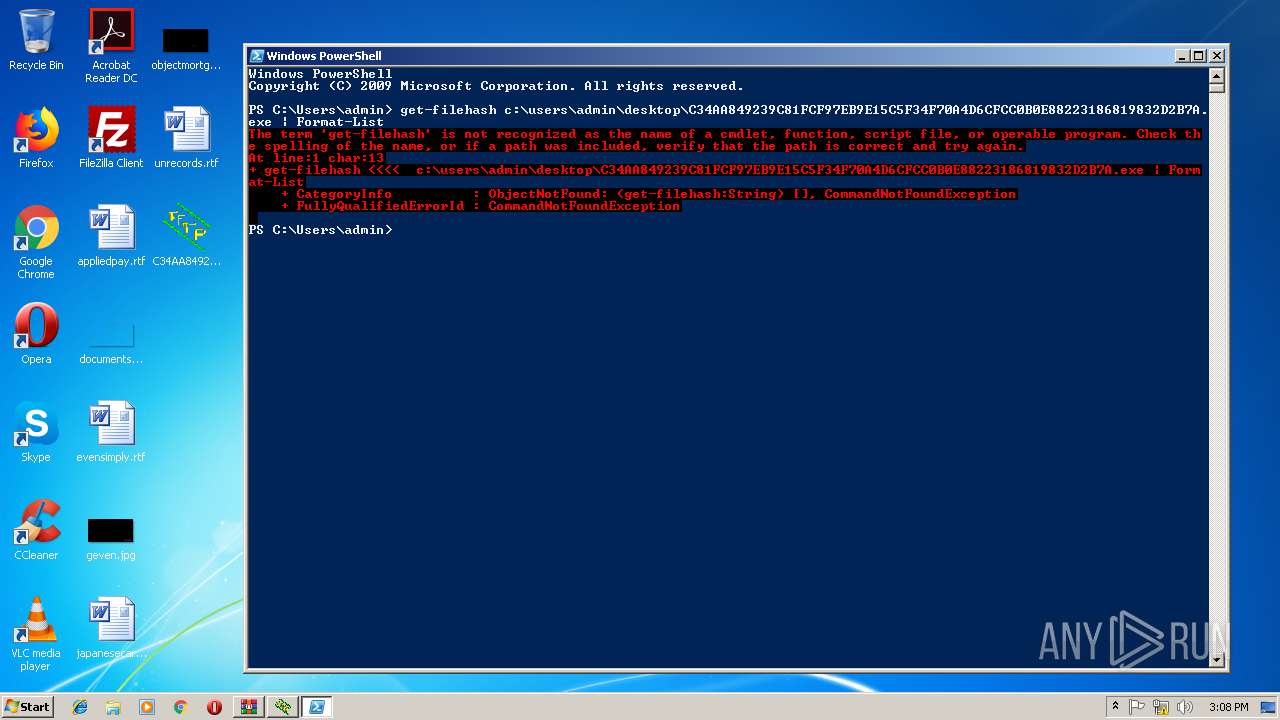
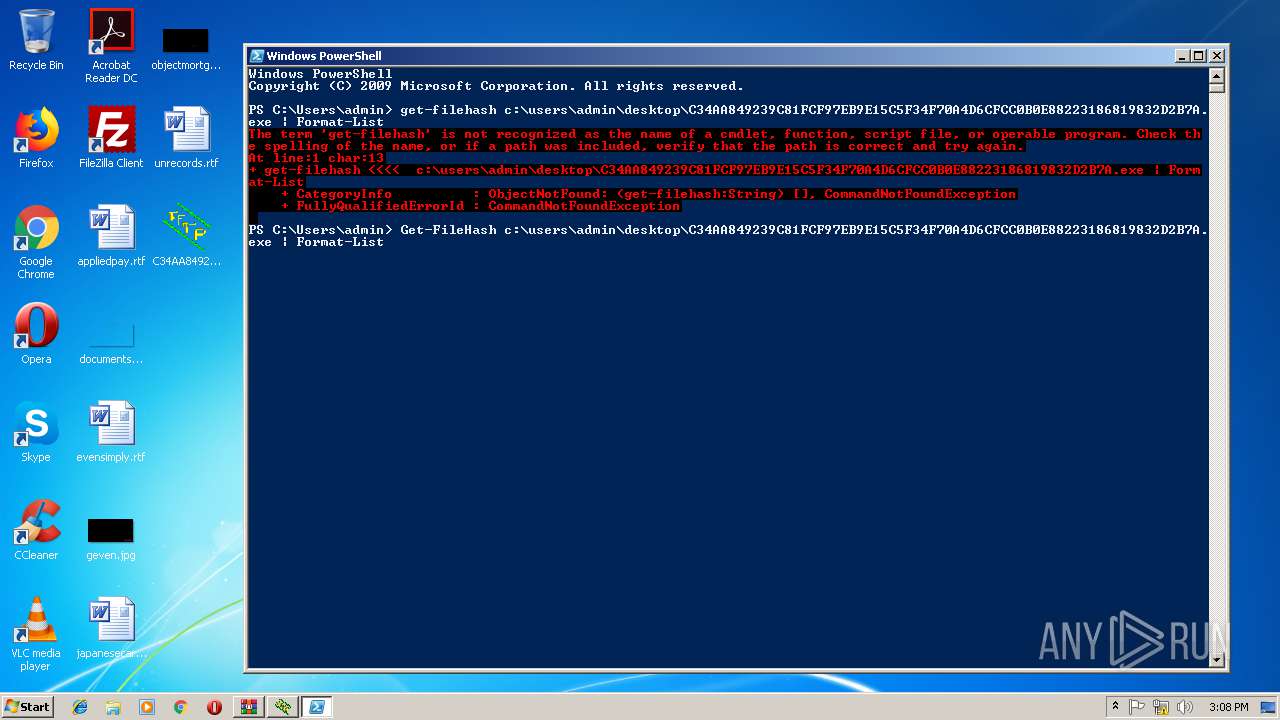
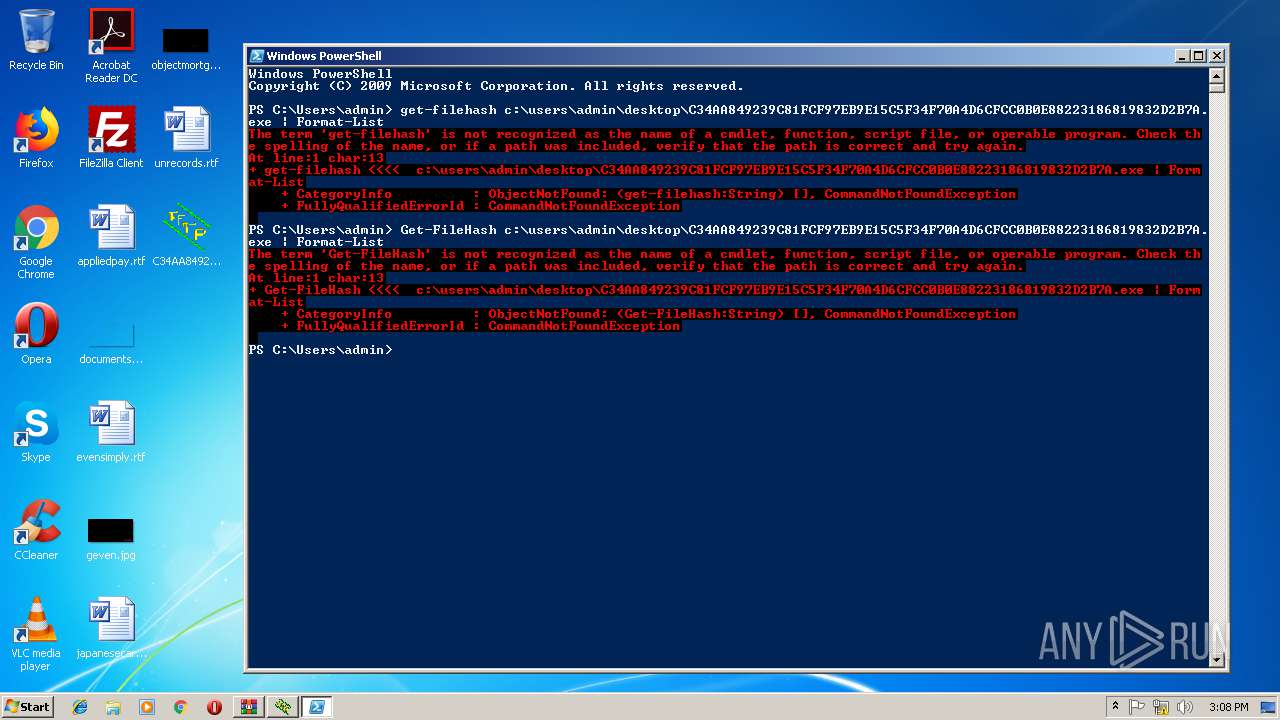
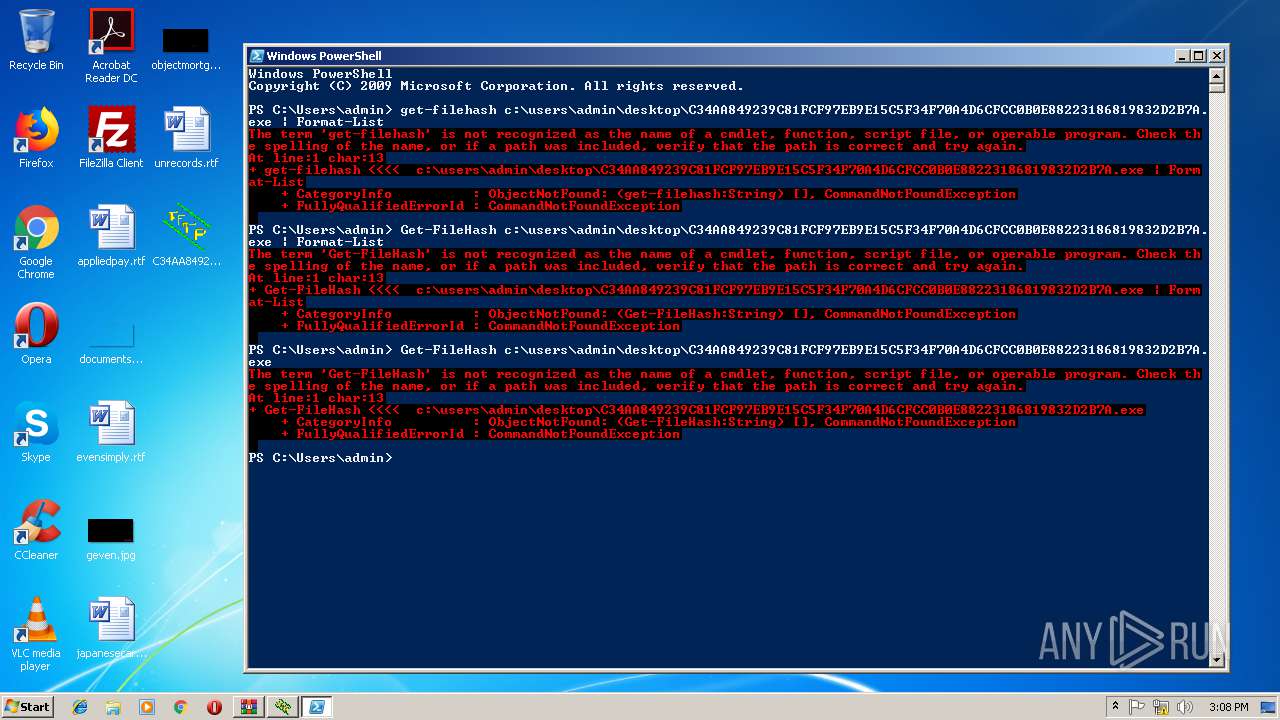
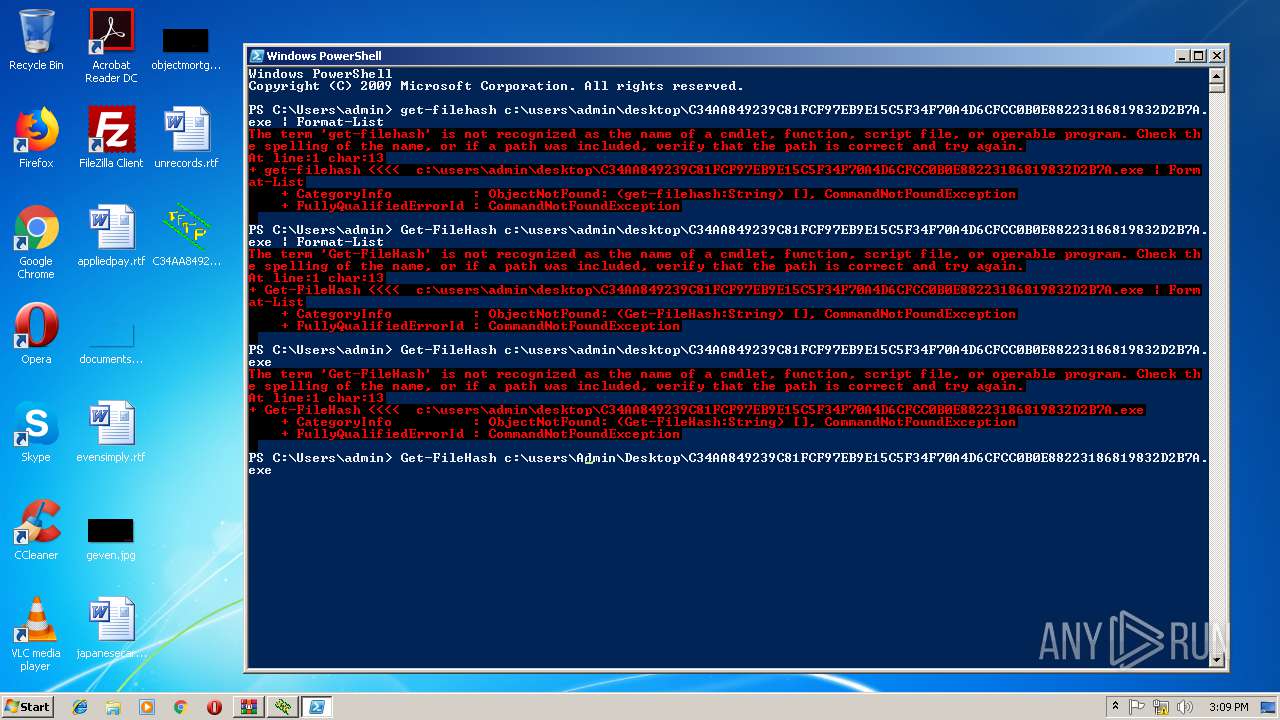
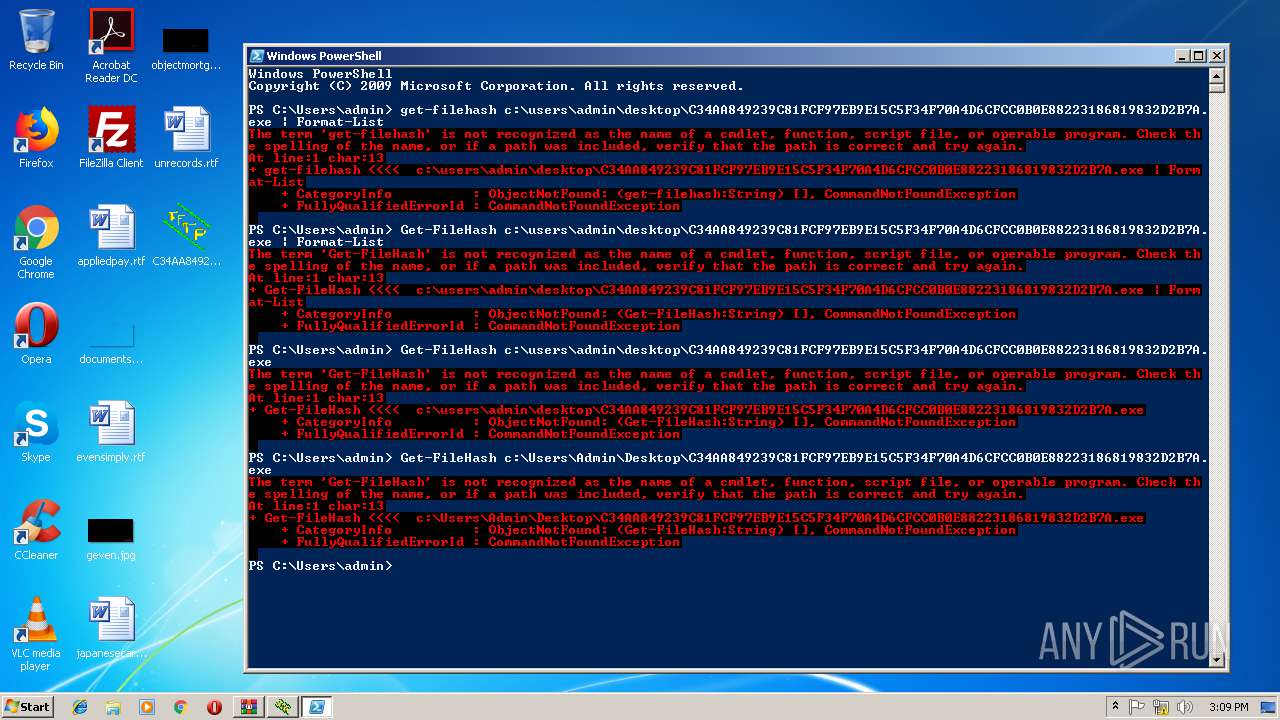
| 3900 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
598
Read events
533
Write events
65
Delete events
0
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.zip | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3900 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8WG0KI19SWIFC9F9RH7W.temp | — | |
MD5:— | SHA256:— | |||
| 3900 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3900 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1bd722.TMP | binary | |
MD5:— | SHA256:— | |||
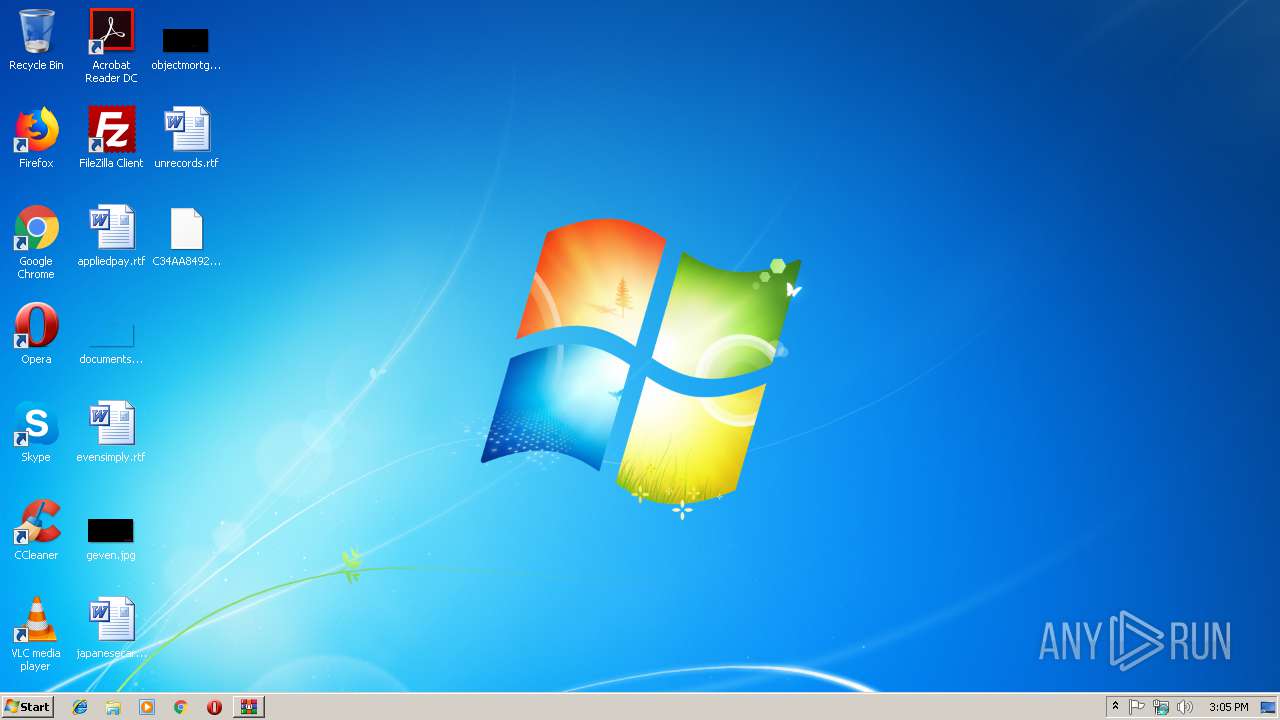
| 2840 | WinRAR.exe | C:\Users\admin\Desktop\C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A | executable | |
MD5:22A29CC2D405CB4A35692E44C5C66520 | SHA256:C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :opening comm socket
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :Console disconnected |
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3644 :Port 17152 may be reused
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3048 :connected to console
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :Verify Console/GUI parameters
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :Version check OK
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :Version check OK
|
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3680 :Console connected |
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3696 :Scheduler signal received |
C34AA849239C81FCF97EB9E15C5F34F70A4D6CFCC0B0E88223186819832D2B7A.exe | Th 3048 :GUI: new service 4 status 4
|