| File name: | rufus-2.18.exe |
| Full analysis: | https://app.any.run/tasks/2b0301a7-af7c-4327-b3f6-c7aadbc84c7f |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2025, 15:04:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed, 3 sections |
| MD5: | D48615FA37605E2F53162F1D7021D937 |
| SHA1: | D0054FC533603004A107436F47BC020AFD54FA05 |
| SHA256: | E82ABD7F2C8F8C866141634A1CE10DA8EBF3C58B68CB2EAA351345777BB3F67C |
| SSDEEP: | 49152:t2zucUfKVJ/UIEQFup04g5BYHSVfY9usJ4LxigH4WC8KcCNZHmZhK0B36vBR46Dl:tJTfKVNU854tSKnJCx3HgNrNk34RaykS |
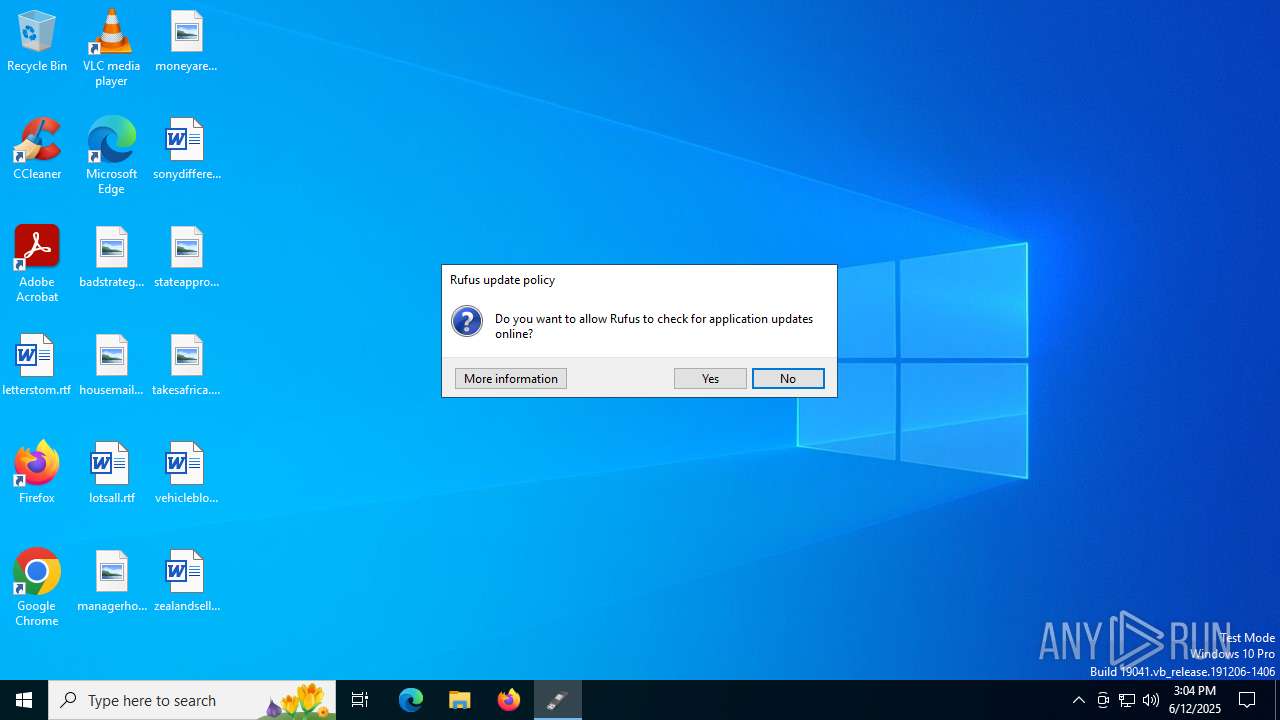
MALICIOUS
Executing a file with an untrusted certificate
- rufus-2.18.exe (PID: 1296)
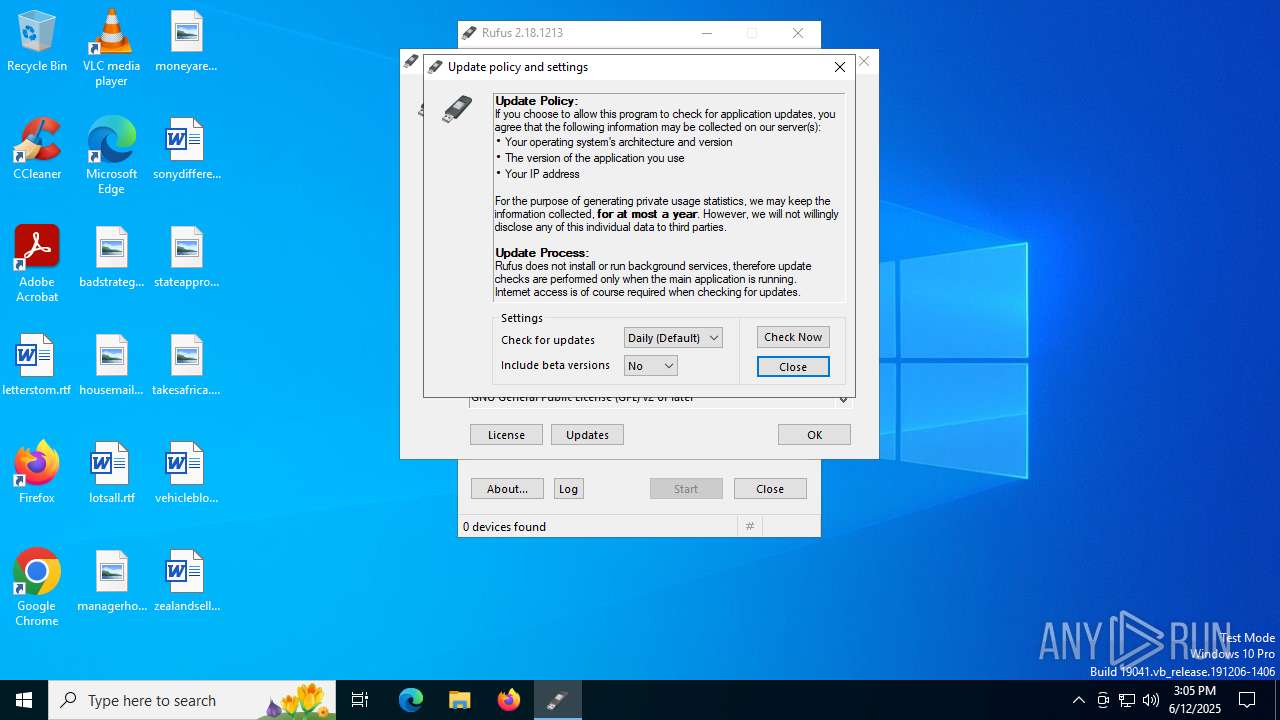
Changes the Windows auto-update feature
- rufus-2.18.exe (PID: 1296)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- rufus-2.18.exe (PID: 1296)
Reads security settings of Internet Explorer
- rufus-2.18.exe (PID: 1296)
INFO
Process checks whether UAC notifications are on
- rufus-2.18.exe (PID: 1296)
Create files in a temporary directory
- rufus-2.18.exe (PID: 1296)
Checks supported languages
- rufus-2.18.exe (PID: 1296)
Reads the computer name
- rufus-2.18.exe (PID: 1296)
Reads the machine GUID from the registry
- rufus-2.18.exe (PID: 1296)
UPX packer has been detected
- rufus-2.18.exe (PID: 1296)
Checks proxy server information
- rufus-2.18.exe (PID: 1296)
Reads the software policy settings
- rufus-2.18.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 2.29 |
| CodeSize: | 917504 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | 1740800 |
| EntryPoint: | 0x2888b0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
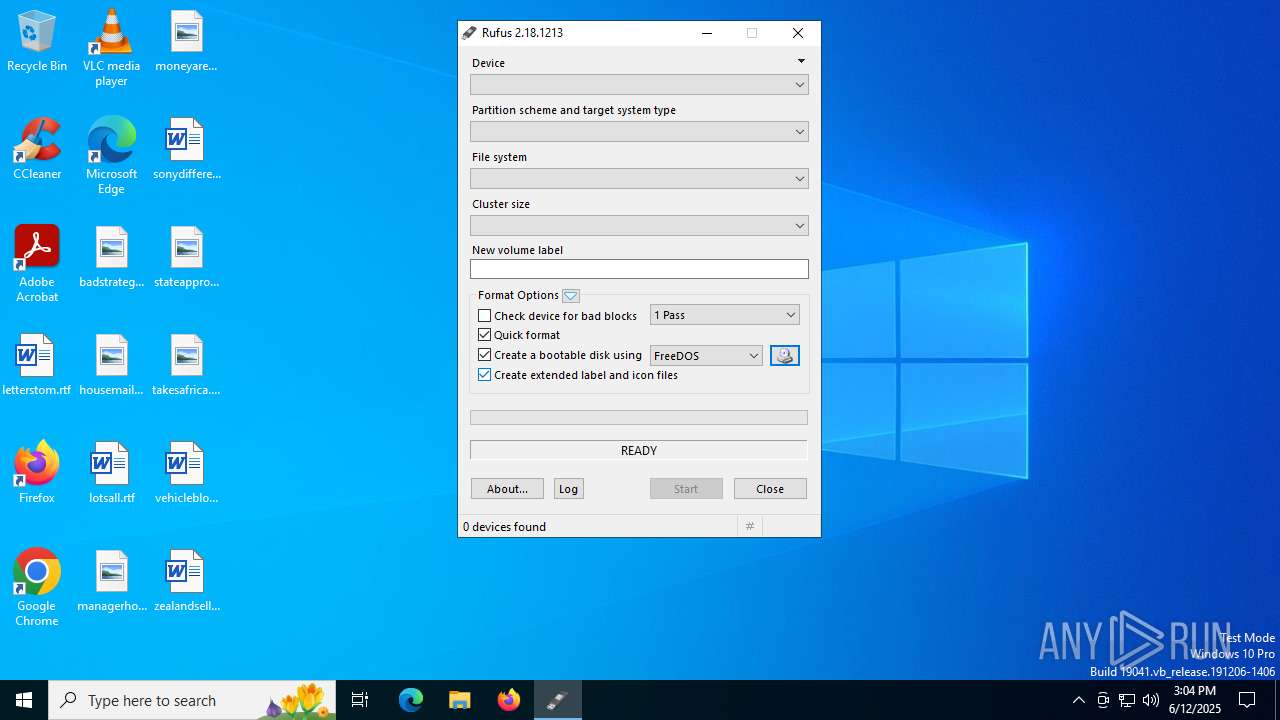
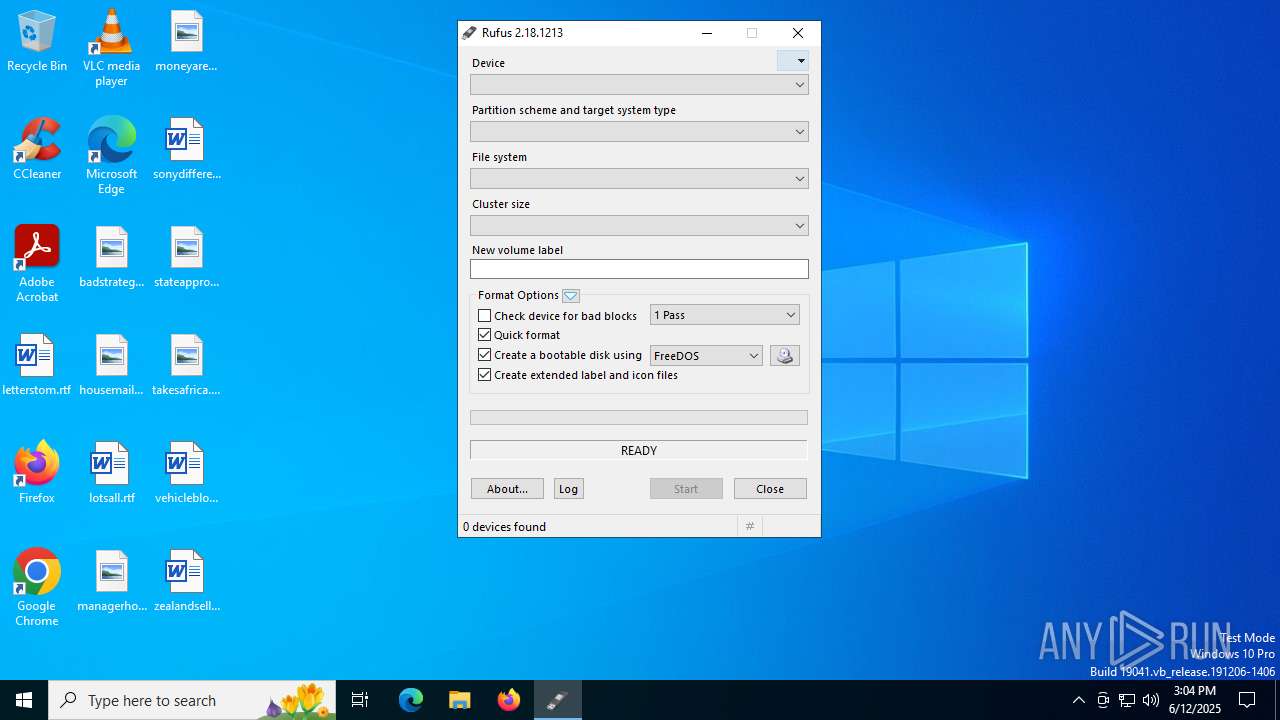
| FileVersionNumber: | 2.18.1213.0 |
| ProductVersionNumber: | 2.18.1213.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
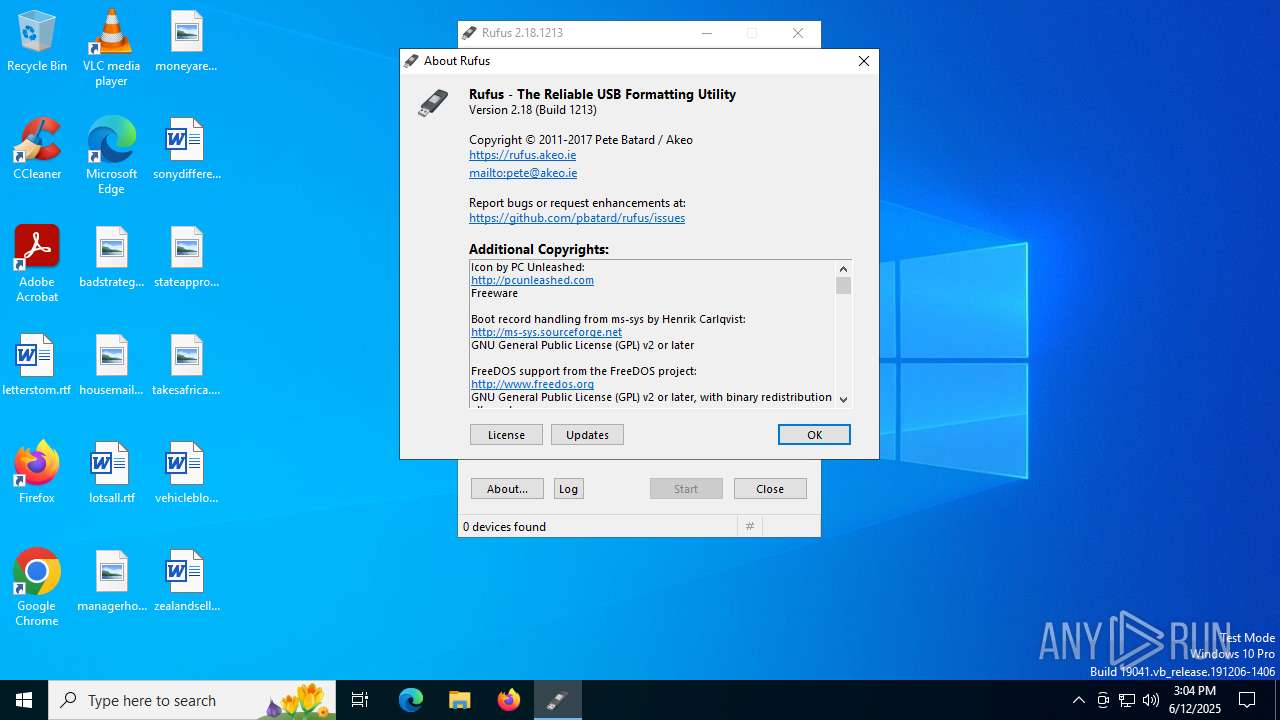
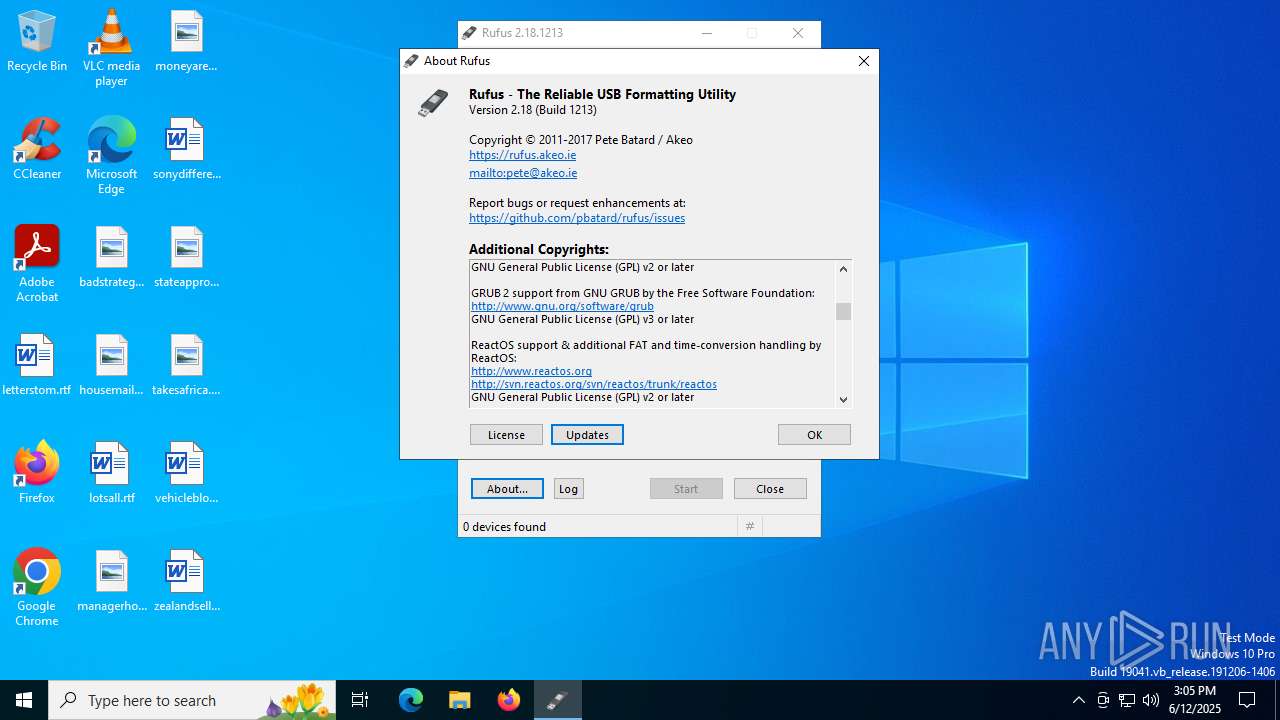
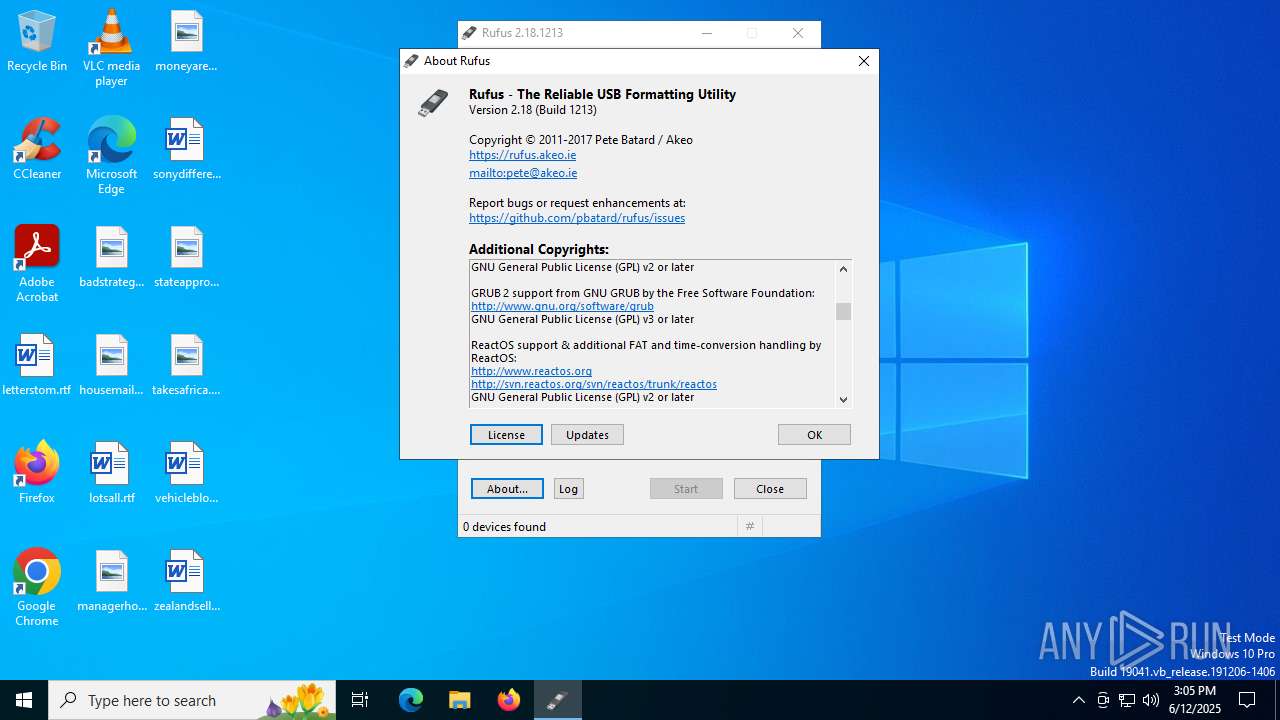
| CompanyName: | Akeo Consulting (http://akeo.ie) |
| FileDescription: | Rufus |
| FileVersion: | 2.18.1213 |
| InternalName: | Rufus |
| LegalCopyright: | © 2011-2017 Pete Batard (GPL v3) |
| LegalTrademarks: | http://www.gnu.org/copyleft/gpl.html |
| OriginalFileName: | rufus.exe |
| ProductName: | Rufus |
| ProductVersion: | 2.18.1213 |
Total processes
142
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Users\admin\AppData\Local\Temp\rufus-2.18.exe" | C:\Users\admin\AppData\Local\Temp\rufus-2.18.exe | explorer.exe | ||||||||||||
User: admin Company: Akeo Consulting (http://akeo.ie) Integrity Level: HIGH Description: Rufus Version: 2.18.1213 Modules
| |||||||||||||||
| 1964 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "C:\Users\admin\AppData\Local\Temp\rufus-2.18.exe" | C:\Users\admin\AppData\Local\Temp\rufus-2.18.exe | — | explorer.exe | |||||||||||
User: admin Company: Akeo Consulting (http://akeo.ie) Integrity Level: MEDIUM Description: Rufus Exit code: 3221226540 Version: 2.18.1213 Modules
| |||||||||||||||
Total events
817
Read events
753
Write events
32
Delete events
32
Modification events
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\AppHVSI |
| Operation: | write | Name: | AllowAppHVSI_ProviderSet |
Value: 0 | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UpdateDefault |
Value: 0 | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\Network Connections |
| Operation: | write | Name: | NC_DoNotShowLocalOnlyIcon |
Value: 1 | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\Windows Feeds |
| Operation: | write | Name: | EnableFeeds |
Value: 0 | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | WUStatusServer |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | UpdateServiceUrlAlternate |
Value: http://neverupdatewindows10.com | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate |
| Operation: | write | Name: | **del.FillEmptyContentUrls |
Value: | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | UseWUServer |
Value: 1 | |||
| (PID) Process: | (1296) rufus-2.18.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Group Policy Objects\{C979AD76-981C-4DCC-8C91-8805D4F0B853}Machine\Software\Policies\Microsoft\Windows\WindowsUpdate\AU |
| Operation: | write | Name: | NoAutoUpdate |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | rufus-2.18.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:2392F1772EA5EC57F3B38729204010E4 | SHA256:182966E809A108282397D80C3F82D0116CB437D1C90630FCB1F93F7CC8F6219D | |||
| 1296 | rufus-2.18.exe | C:\Windows\SysWOW64\GroupPolicy\gpt.ini | text | |
MD5:39DFFC602ED934569F26BE44EC645814 | SHA256:B57A88E5B1ACF3A784BE88B87FA3EE1F0991CB7C1C66DA423F3595FFC6E0C5C2 | |||
| 1296 | rufus-2.18.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:0C014C71A70DC7758BFDC822E974F1F3 | SHA256:8EBD915268E16B55A3ABDE6F612363576FAB5DF656F955D672CCE8889C5FF9CA | |||
| 1296 | rufus-2.18.exe | C:\Users\admin\AppData\Local\Temp\Ruf5F75.tmp | text | |
MD5:97F1600F3FC2BCBF40A3A51573BC82DE | SHA256:A7E57B7AD3A29A474DC57E65607B0AAE59EDED0754F928EA4417E3E6B8E23008 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 868 b | whitelisted |
5020 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
5020 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
1296 | rufus-2.18.exe | GET | 301 | 185.199.111.153:80 | http://rufus.akeo.ie/Rufus_win_x64_10.0.ver | US | html | 162 b | whitelisted |
1296 | rufus-2.18.exe | GET | 301 | 185.199.111.153:80 | http://rufus.akeo.ie/Rufus_win_x64_10.ver | US | html | 162 b | whitelisted |
1296 | rufus-2.18.exe | GET | 301 | 185.199.111.153:80 | http://rufus.akeo.ie/Rufus_win_x64.ver | US | html | 162 b | whitelisted |
2140 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1296 | rufus-2.18.exe | GET | 301 | 185.199.111.153:80 | http://rufus.akeo.ie/Rufus_win.ver | US | html | 162 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2320 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2200 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2200 | svchost.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
rufus.akeo.ie |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rufus-2.18.exe | *** Rufus init ***
|
rufus-2.18.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-2.18.exe | localization: extracted data to 'C:\Users\admin\AppData\Local\Temp\Ruf5F75.tmp'
|
rufus-2.18.exe | Will use settings from registry
|
rufus-2.18.exe | Binary executable is signed by 'Akeo Consulting'
|
rufus-2.18.exe | loc file not found in current directory - embedded one will be used
|
rufus-2.18.exe | localization: found locale 'zh-TW'
|
rufus-2.18.exe | localization: found locale 'fa-IR'
|
rufus-2.18.exe | localization: found locale 'fi-FI'
|
rufus-2.18.exe | localization: found locale 'it-IT'
|