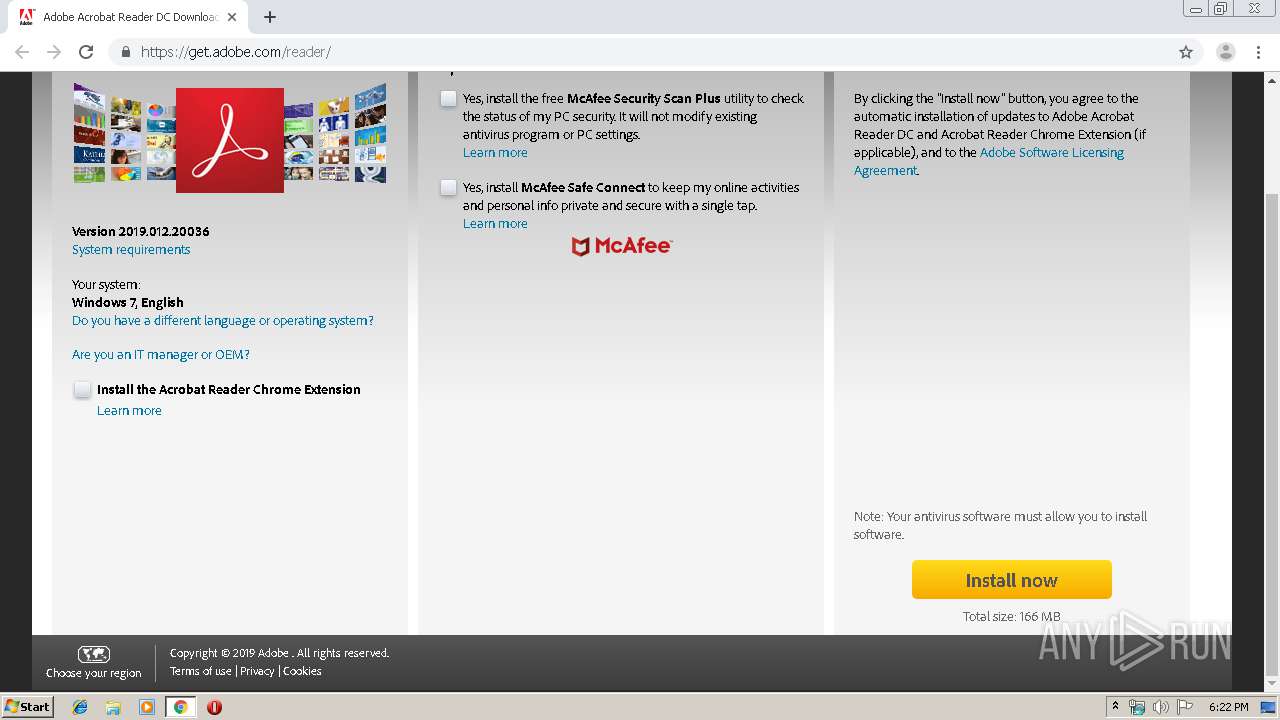
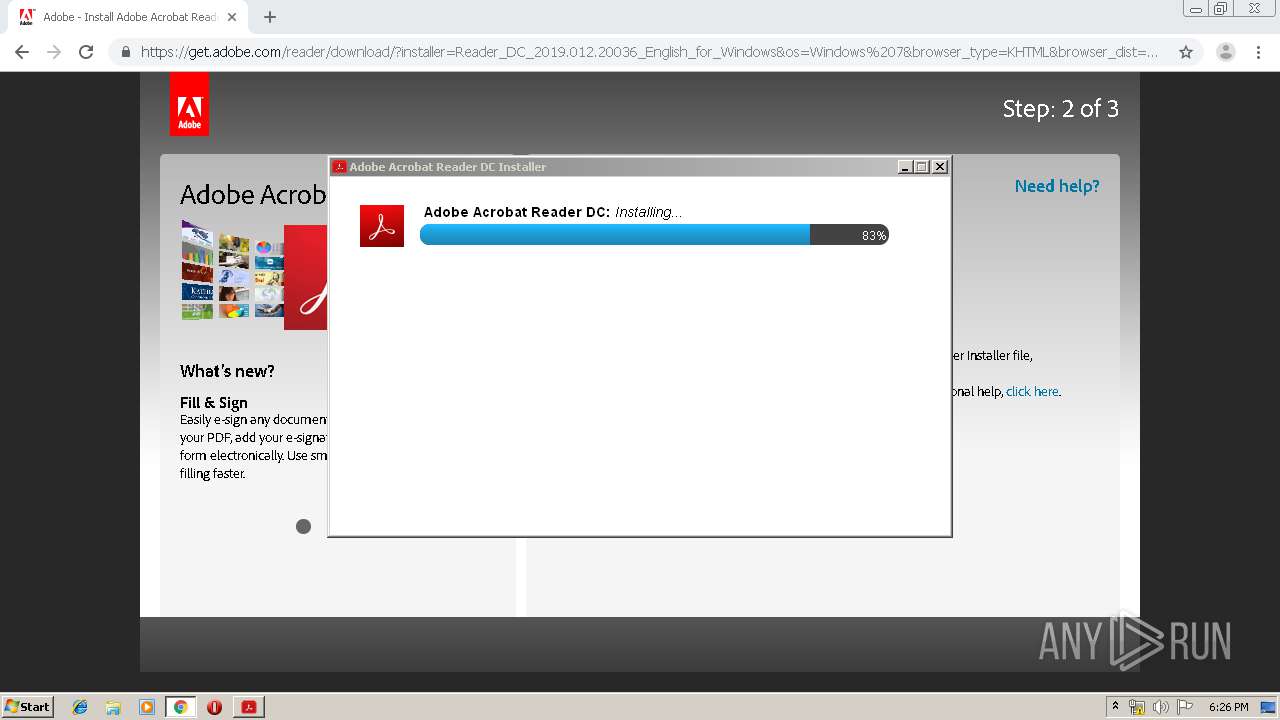
| URL: | http://www.adobe.com/products/acrobat/readstep2.html |
| Full analysis: | https://app.any.run/tasks/30fb3f01-701d-4904-9a5f-06d346e772ab |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 17:21:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 51DA98A8C698ADB8E61B761A47E6C1BE |
| SHA1: | 53FD3365E5B3AAC14FD405FF60978EADC4F7C0CE |
| SHA256: | E81C9F20CD917F3D168E41309E11B7EBED785567801666D146E05338873D4A13 |
| SSDEEP: | 3:N1KJS4X8VXaQGRWfAHw/0:Cc4/RWfN/0 |
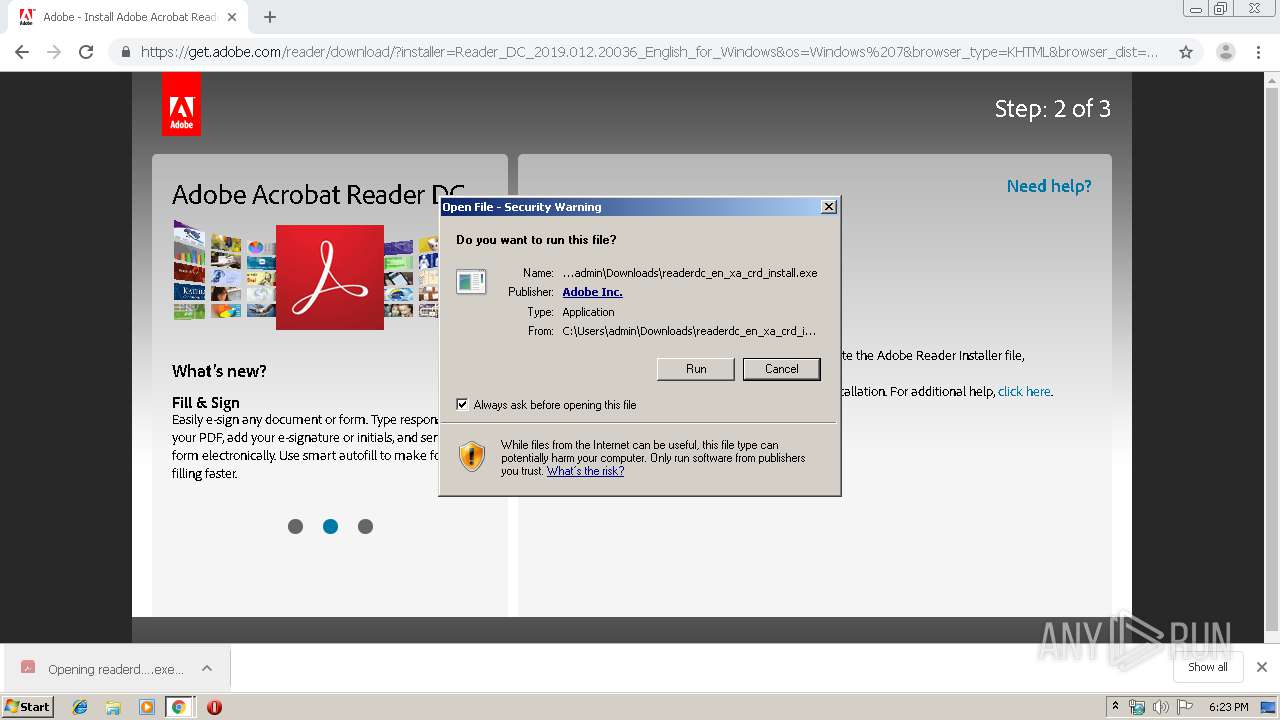
MALICIOUS
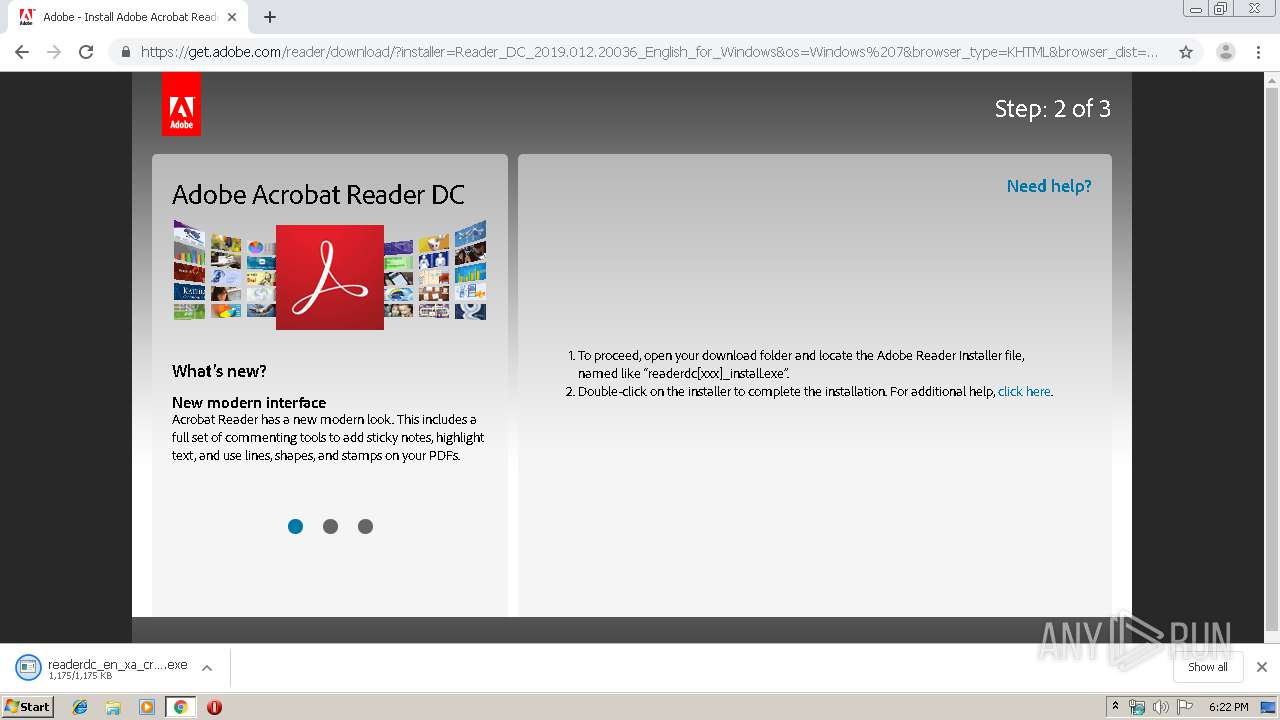
Application was dropped or rewritten from another process
- readerdc_en_xa_crd_install.exe (PID: 3960)
- readerdc_en_xa_crd_install.exe (PID: 3856)
- gtcheck.exe (PID: 3864)
- gccheck_small.exe (PID: 3424)
- gccheck_small.exe (PID: 3100)
- setup.exe (PID: 904)
Changes settings of System certificates
- readerdc_en_xa_crd_install.exe (PID: 3856)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
Executable content was dropped or overwritten
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2188)
- readerdc_en_xa_crd_install.exe (PID: 3960)
- C1041D1A-55C7-4ECE-8412-062E90EBEFF5 (PID: 3888)
- msiexec.exe (PID: 2224)
Application launched itself
- readerdc_en_xa_crd_install.exe (PID: 3960)
Reads internet explorer settings
- readerdc_en_xa_crd_install.exe (PID: 3960)
Adds / modifies Windows certificates
- readerdc_en_xa_crd_install.exe (PID: 3856)
Creates files in the user directory
- readerdc_en_xa_crd_install.exe (PID: 3960)
Starts application with an unusual extension
- readerdc_en_xa_crd_install.exe (PID: 3856)
Creates files in the program directory
- C1041D1A-55C7-4ECE-8412-062E90EBEFF5 (PID: 3888)
Creates files in the Windows directory
- MsiExec.exe (PID: 4004)
Removes files from Windows directory
- MsiExec.exe (PID: 4004)
INFO
Reads the hosts file
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2188)
Reads settings of System Certificates
- chrome.exe (PID: 2188)
- chrome.exe (PID: 2964)
Reads Internet Cache Settings
- chrome.exe (PID: 2964)
Application launched itself
- chrome.exe (PID: 2964)
- msiexec.exe (PID: 2224)
Application was dropped or rewritten from another process
- MSI996E.tmp (PID: 2416)
Starts application with an unusual extension
- msiexec.exe (PID: 2224)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4004)
- MsiExec.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
41
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\Windows\system32\MsiExec.exe -Embedding 5E22A1DD4D0FA73CBBA452DCF38EDFB7 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\ProgramData\Adobe\Setup\{AC76BA86-7AD7-1033-7B44-AC0F074E4100}\setup.exe" /sAll /re /msi OWNERSHIP_STATE=1 UPDATE_MODE=3 EULA_ACCEPT=YES ENABLE_CHROMEEXT=0 DISABLE_CACHE=1 | C:\ProgramData\Adobe\Setup\{AC76BA86-7AD7-1033-7B44-AC0F074E4100}\setup.exe | — | C1041D1A-55C7-4ECE-8412-062E90EBEFF5 | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Bootstrapper for Single Installation Exit code: 0 Version: 19.8.20071.303822 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12939359716981862918 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6695985155984234113 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2224 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13366444167737248850 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6419776456176762661 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2416 | "C:\Windows\Installer\MSI996E.tmp" /b 2 120 0 | C:\Windows\Installer\MSI996E.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3388233617219189724 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,8131406712034389645,8413944098546675028,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4907282884200232098 --mojo-platform-channel-handle=3528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
11 383
Read events
6 577
Write events
835
Delete events
3 971
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13215115334626000 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
534
Suspicious files
150
Text files
844
Unknown types
158
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fb3226d3-1fa2-48aa-bb63-ff01ab398a2a.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF114e2d.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF114f94.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
78
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | readerdc_en_xa_crd_install.exe | GET | 302 | 108.128.130.224:80 | http://stats.adobe.com/b/ss/adbacdcprod/1/H.25.4/s96527665875918?AQB=1&ndh=1&t=9%2F9%2F2019%2018%3A23%3A12%203%20-60&ce=UTF-8&ns=adobecorp&pageName=acdc_rdr_adm_launched&g=res%3A%2F%2FC%3A%5CUsers%5Cadmin%5CDownloads%5Creaderdc_en_xa_crd_install.exe%2F160&ch=acdc_reader&events=event96&products=%3Breader_adm&c1=adm&c2=acdc%20downloads&c3=get.adobe.com&c4=en_us&c5=en_us%3Aacdc_rdr_adm_launched&v18=new&v22=wednesday%20-%2011%3A00am&v73=acdc_reader&s=1280x720&c=32&j=1.5&v=Y&k=N&bw=620&bh=358&ct=lan&hp=N&AQE=1 | US | — | — | whitelisted |
2188 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2188 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
2188 | chrome.exe | GET | 301 | 172.227.83.12:80 | http://www.adobe.com/products/acrobat/readstep2.html | US | html | 261 b | whitelisted |
2188 | chrome.exe | GET | 200 | 13.225.239.93:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2188 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=89.187.165.47&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1570641684&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2188 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2188 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
3960 | readerdc_en_xa_crd_install.exe | GET | 200 | 108.128.130.224:80 | http://stats.adobe.com/b/ss/adbacdcprod/1/H.25.4/s96527665875918?AQB=1&pccr=true&vidn=2ECF0BC0FFFF8000-400D9FF62272993A&ndh=1&t=9%2F9%2F2019%2018%3A23%3A12%203%20-60&ce=UTF-8&ns=adobecorp&pageName=acdc_rdr_adm_launched&g=res%3A%2F%2FC%3A%5CUsers%5Cadmin%5CDownloads%5Creaderdc_en_xa_crd_install.exe%2F160&ch=acdc_reader&events=event96&products=%3Breader_adm&c1=adm&c2=acdc%20downloads&c3=get.adobe.com&c4=en_us&c5=en_us%3Aacdc_rdr_adm_launched&v18=new&v22=wednesday%20-%2011%3A00am&v73=acdc_reader&s=1280x720&c=32&j=1.5&v=Y&k=N&bw=620&bh=358&ct=lan&hp=N&AQE=1 | US | image | 43 b | whitelisted |
2188 | chrome.exe | GET | 301 | 193.104.215.66:80 | http://get.adobe.com/reader/ | unknown | html | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2188 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2188 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2188 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2188 | chrome.exe | 216.58.205.234:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2188 | chrome.exe | 172.227.83.12:443 | www.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
2188 | chrome.exe | 35.169.161.115:443 | fonts.adobe.com | Amazon.com, Inc. | US | unknown |
2188 | chrome.exe | 193.104.215.66:80 | get.adobe.com | Level 3 Communications, Inc. | — | malicious |
2188 | chrome.exe | 2.18.232.23:443 | assets.adobedtm.com | Akamai International B.V. | — | whitelisted |
2188 | chrome.exe | 52.30.78.155:443 | dpm.demdex.net | Amazon.com, Inc. | IE | unknown |
2188 | chrome.exe | 35.190.72.21:443 | idsync.rlcdn.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.adobe.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
get.adobe.com |
| whitelisted |
wwwimages2.adobe.com |
| whitelisted |
fonts.adobe.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |