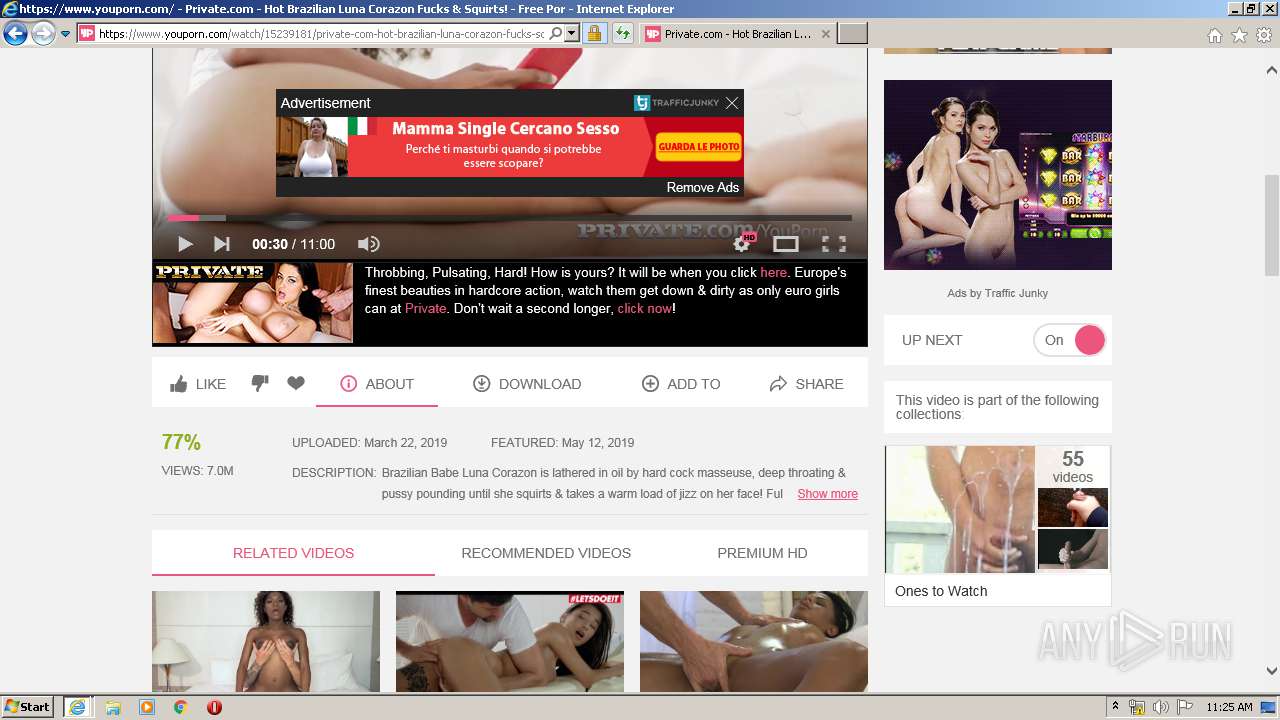
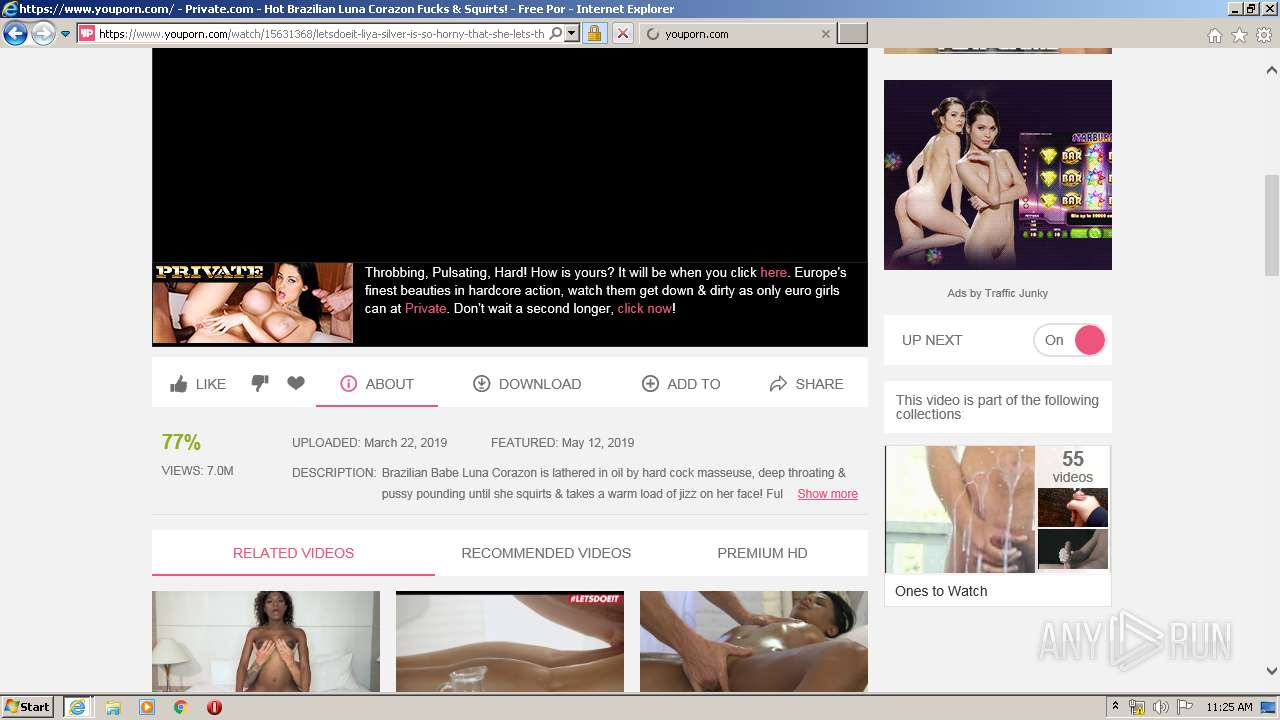
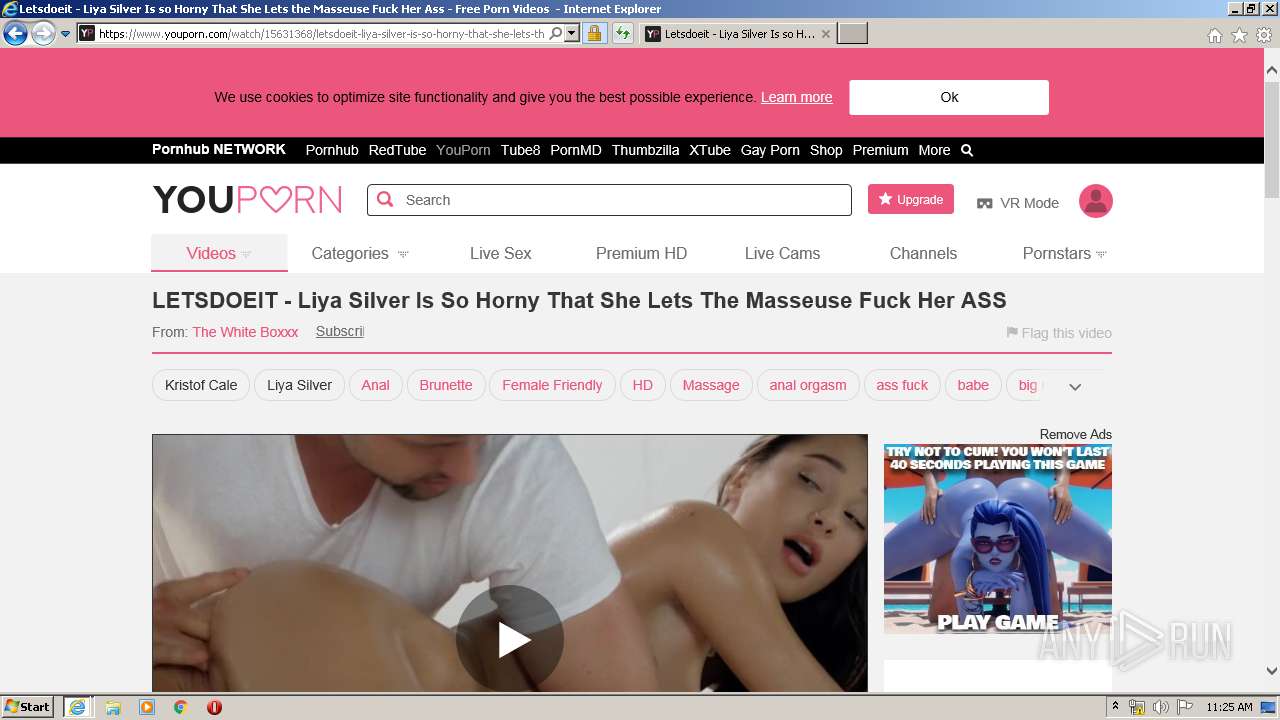
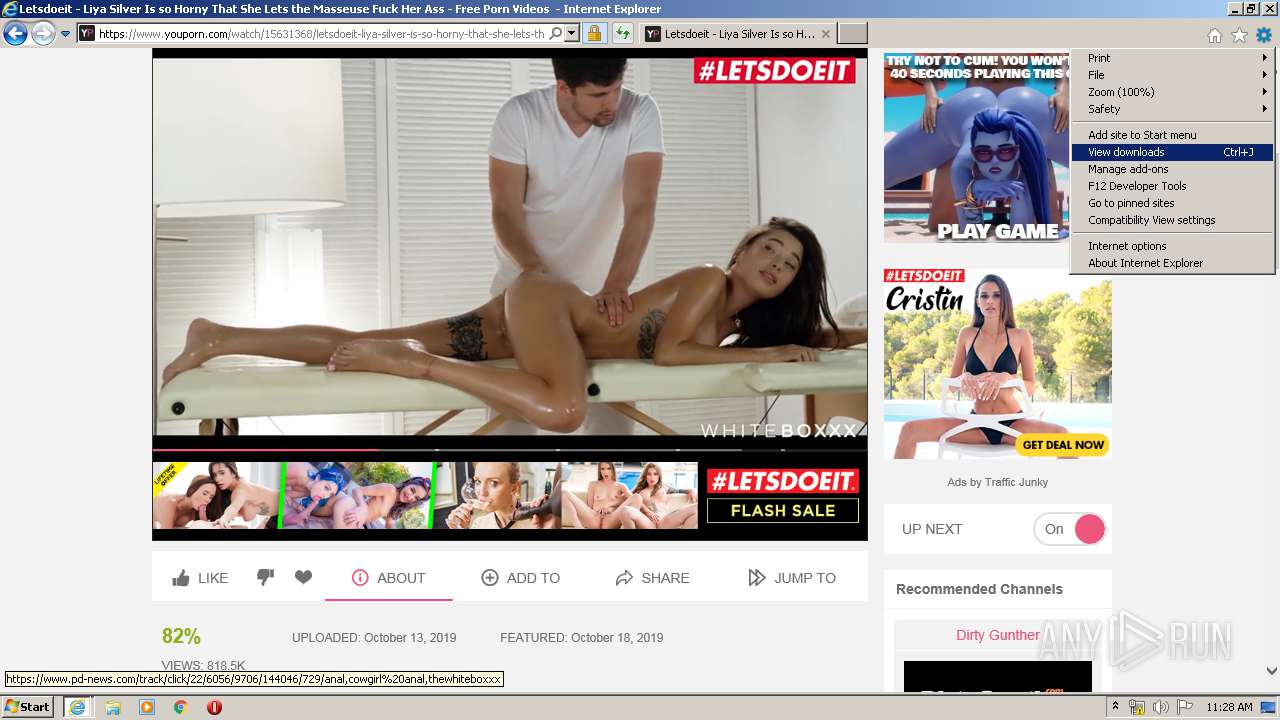
| URL: | https://www.youporn.com |
| Full analysis: | https://app.any.run/tasks/40880ec7-9aa0-41cd-9472-1ff0c305bc1c |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2020, 11:23:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4E468E7E31E2BDAD92504CB7A0E9C177 |
| SHA1: | 4761FAE17BE6739E5EEADF63A6349709E5313C1F |
| SHA256: | E81538F910FA0C0010F6D76190968528E2A982EEA665779E594102E3807CAB70 |
| SSDEEP: | 3:N8DSLURT:2OLURT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2132)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 2636)
- iexplore.exe (PID: 1500)
Changes internet zones settings
- iexplore.exe (PID: 2636)
Reads internet explorer settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 1500)
Application launched itself
- iexplore.exe (PID: 2636)
Creates files in the user directory
- iexplore.exe (PID: 2636)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2132)
- iexplore.exe (PID: 1500)
- iexplore.exe (PID: 3848)
Reads settings of System Certificates
- iexplore.exe (PID: 1500)
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 2636)
Changes settings of System certificates
- iexplore.exe (PID: 2636)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1500 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2636 CREDAT:2495760 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2132 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2636 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.youporn.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2636 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 038
Read events
1 329
Write events
4 597
Delete events
2 112
Modification events
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2777730100 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30792525 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2636) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
141
Text files
422
Unknown types
102
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6E72.tmp | — | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6E73.tmp | — | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PGXAICWX.txt | — | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3PCSQWH5.txt | — | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_A7D21A333B944838A83FE7E240434D45 | binary | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_A7D21A333B944838A83FE7E240434D45 | der | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\X7GO6VZI.htm | html | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\mg_utils-2.0.0[1].js | text | |
MD5:— | SHA256:— | |||
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
305
DNS requests
67
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAhXuZzybbPTaIhF13nYqnw%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAQMGRlQy5IewoZkhDn%2BmdA%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAQMGRlQy5IewoZkhDn%2BmdA%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA3hBbqb7pFPfKFAtRUkla4%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAQMGRlQy5IewoZkhDn%2BmdA%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAQMGRlQy5IewoZkhDn%2BmdA%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAvnxp7m2tvY5o8zBcUM7OI%3D | US | der | 471 b | whitelisted |
3848 | iexplore.exe | GET | 200 | 2.20.189.204:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3848 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA3hBbqb7pFPfKFAtRUkla4%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3848 | iexplore.exe | 66.254.122.100:443 | fs.ypncdn.com | Reflected Networks, Inc. | US | suspicious |
2636 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3848 | iexplore.exe | 66.254.114.79:443 | www.youporn.com | Reflected Networks, Inc. | US | unknown |
3848 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3848 | iexplore.exe | 66.254.122.104:443 | fs.ypncdn.com | Reflected Networks, Inc. | US | suspicious |
3848 | iexplore.exe | 205.185.208.142:443 | cdn1d-static-shared.phncdn.com | Highwinds Network Group, Inc. | US | suspicious |
3848 | iexplore.exe | 205.185.208.85:443 | media.trafficjunky.net | Highwinds Network Group, Inc. | US | unknown |
3848 | iexplore.exe | 66.254.114.32:443 | ht.youporn.com | Reflected Networks, Inc. | US | unknown |
3848 | iexplore.exe | 69.16.175.10:443 | smpop.icfcdn.com | Highwinds Network Group, Inc. | US | malicious |
3848 | iexplore.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youporn.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
fs.ypncdn.com |
| suspicious |
cdn1d-static-shared.phncdn.com |
| whitelisted |
media.trafficjunky.net |
| whitelisted |
smpop.icfcdn.com |
| malicious |
www.google-analytics.com |
| whitelisted |
ht.youporn.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ads.trafficjunky.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3848 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3848 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3848 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
3848 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |