| File name: | Driver Easy Pro License Keys.exe |
| Full analysis: | https://app.any.run/tasks/e4c1386a-4a54-4e95-80eb-dfb1d33d4154 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2022, 10:29:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 780590EB879AC5B9F203472A26928F41 |
| SHA1: | 997DEB0D74667F9E4744B1D6DA213A6C54CE185E |
| SHA256: | E80BBA031FE9E4FECE00E6B17EE11051F3554320DD299C7566E126E7C50EE838 |
| SSDEEP: | 196608:YJIPbvcyNSN/KPKpT9/3fXrLBuUHXIhXuS8KzBE3apfbX7pF2RpoGzjI:NlNDSn/3f7luUHYcadEWPyo+M |
MALICIOUS
Application was dropped or rewritten from another process
- KiffAppE2.exe (PID: 3024)
- License Keys.exe (PID: 3308)
- file.exe (PID: 2460)
- License Keys.exe (PID: 1468)
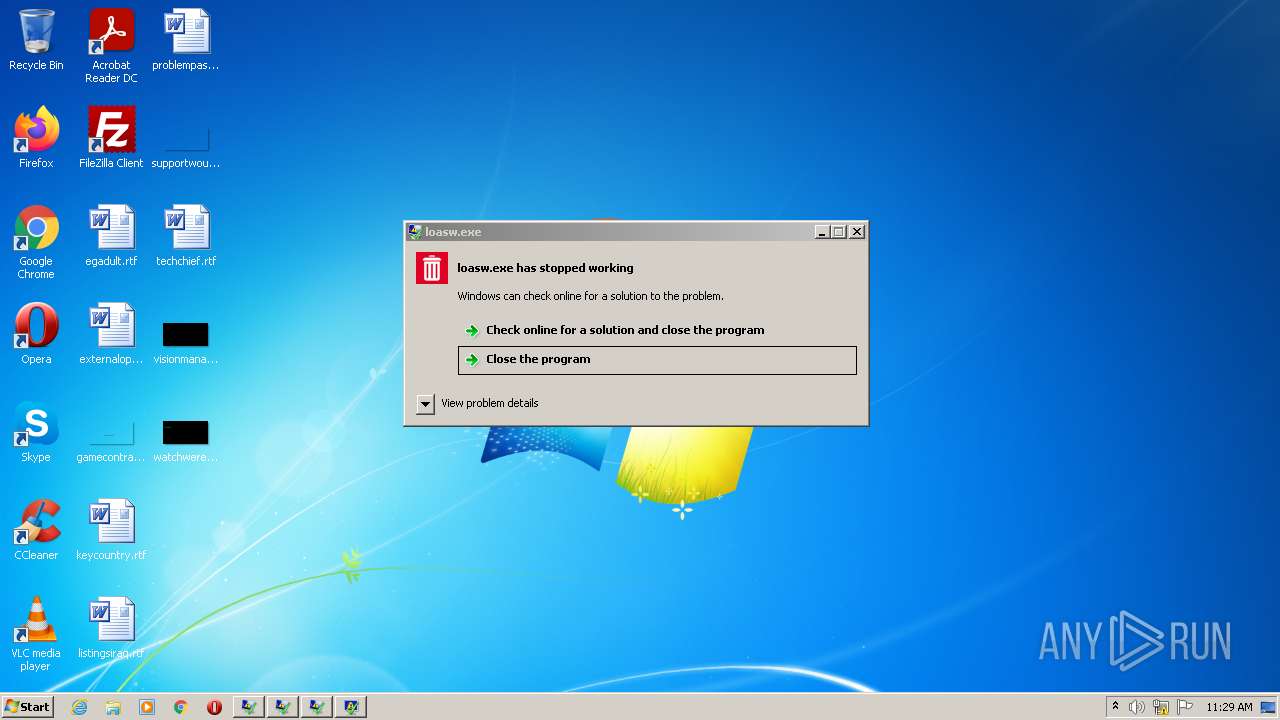
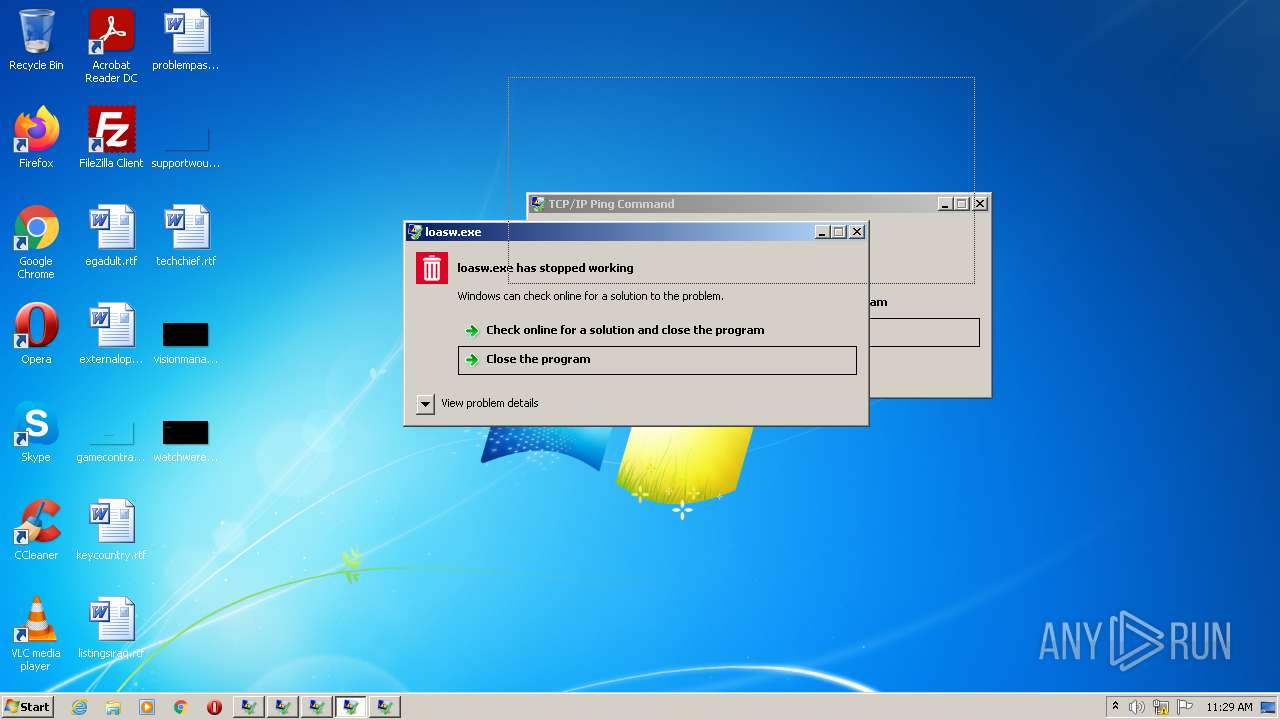
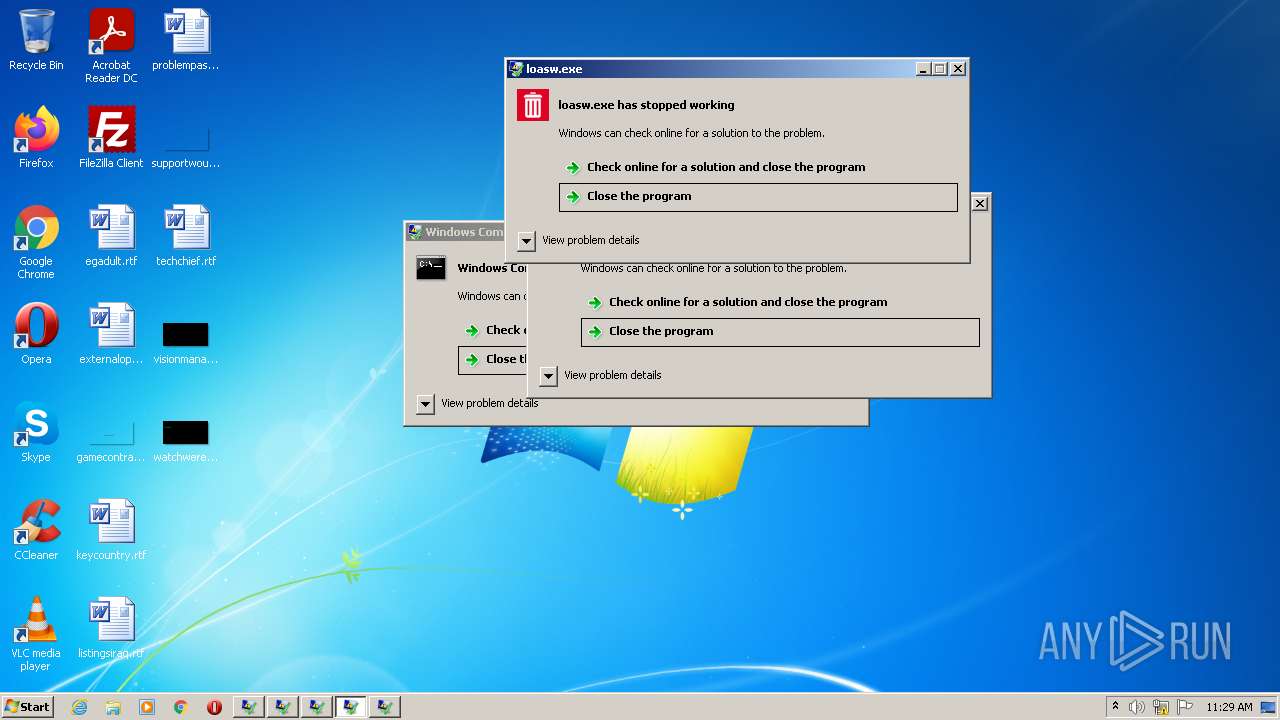
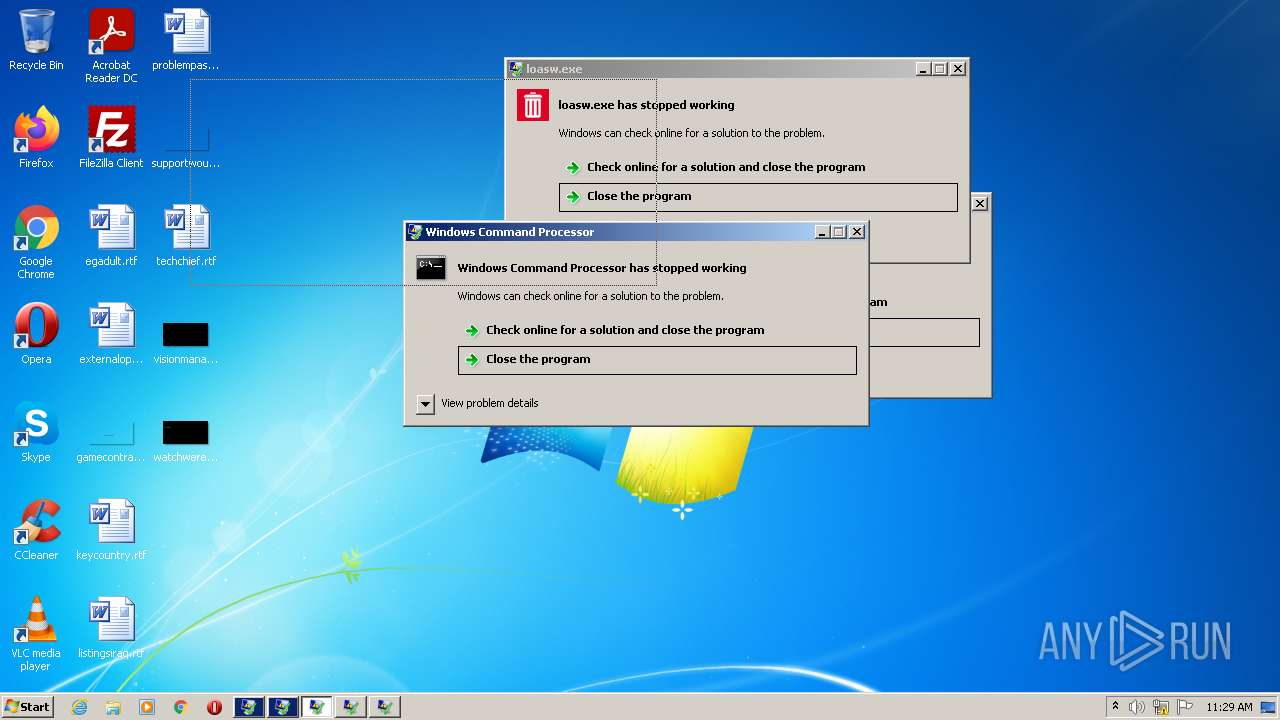
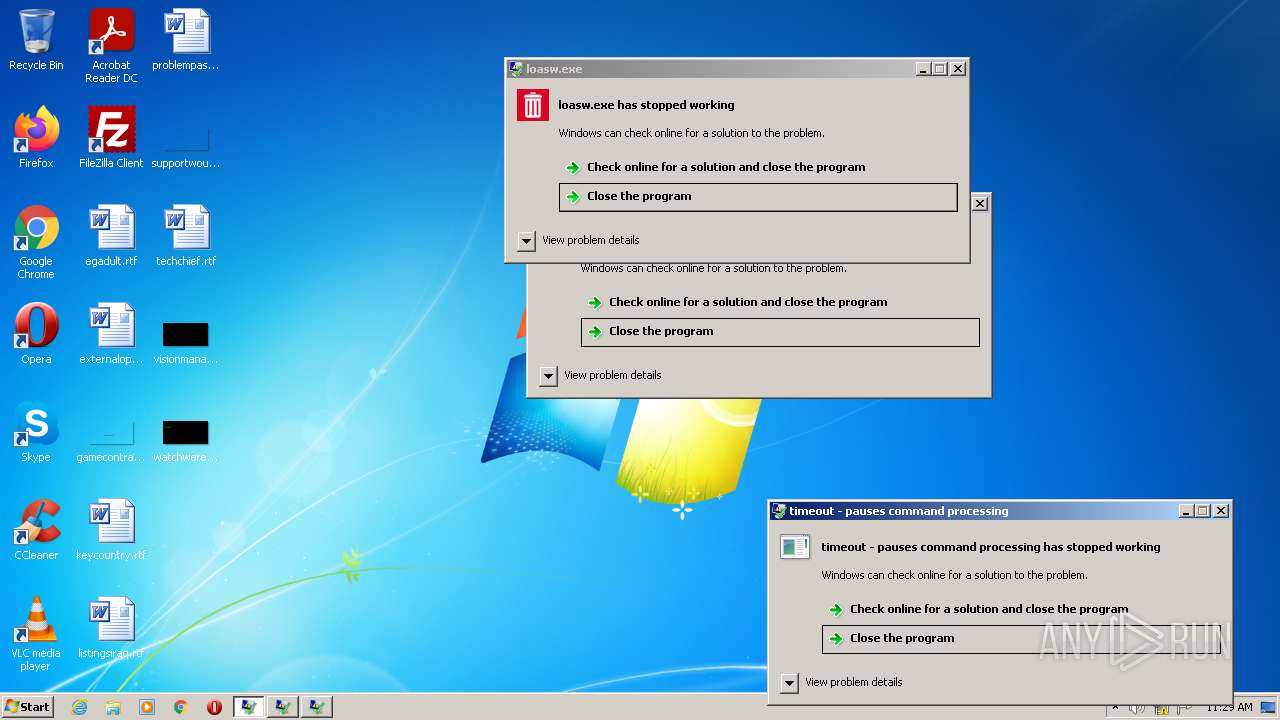
- loasw.exe (PID: 2584)
- 00004823..exe (PID: 3920)
- 00000029..exe (PID: 1132)
- search_hyperfs_212.exe (PID: 2304)
Changes settings of System certificates
- License Keys.exe (PID: 1468)
Drops executable file immediately after starts
- file.exe (PID: 2460)
- 00004823..exe (PID: 3920)
- License Keys.exe (PID: 1468)
- Driver Easy Pro License Keys.exe (PID: 2716)
Writes to a start menu file
- 00004823..exe (PID: 3920)
Runs injected code in another process
- 00004823..exe (PID: 3920)
- rundll32.exe (PID: 2480)
Application was injected by another process
- taskeng.exe (PID: 1136)
- Dwm.exe (PID: 584)
- Explorer.EXE (PID: 528)
- ctfmon.exe (PID: 1368)
- DllHost.exe (PID: 2376)
- conhost.exe (PID: 3968)
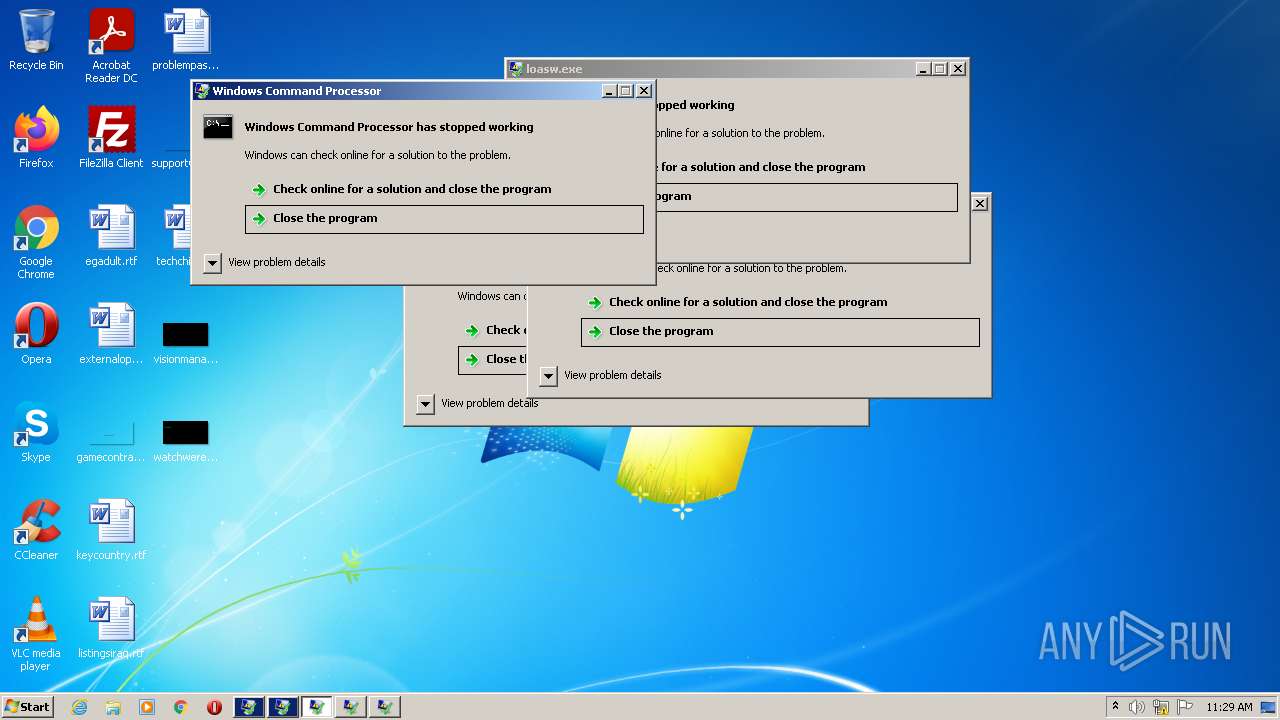
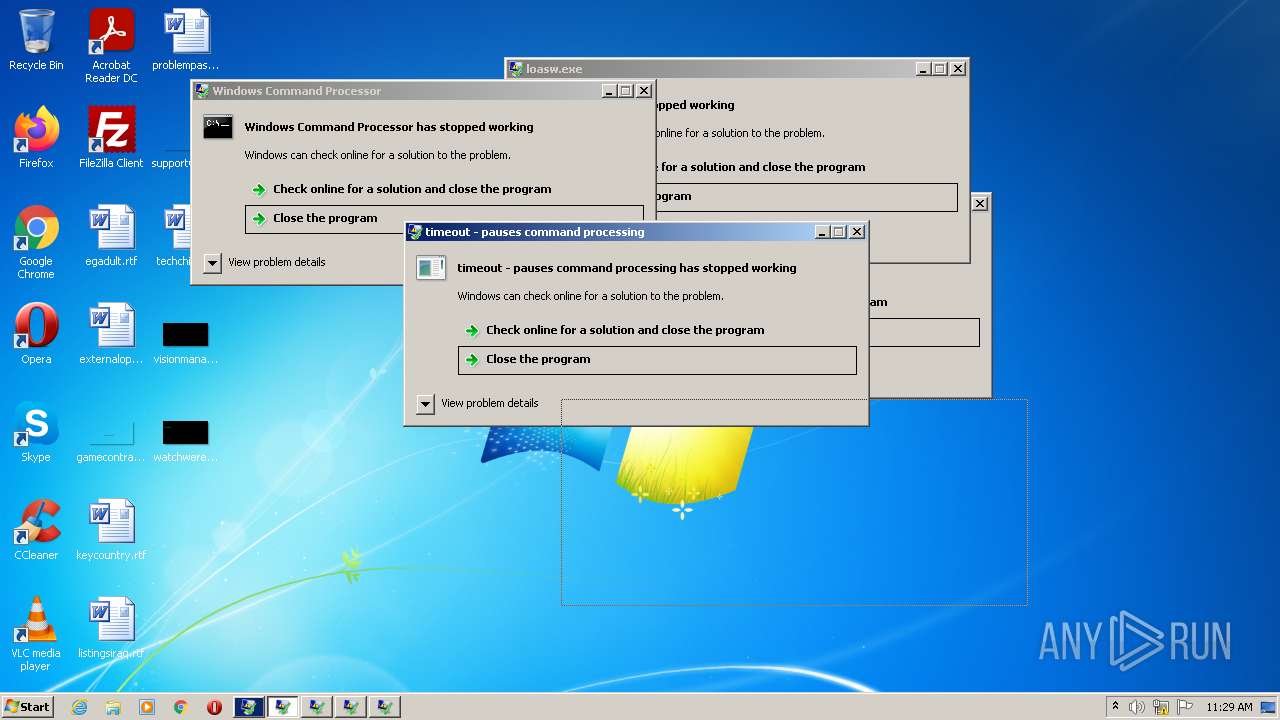
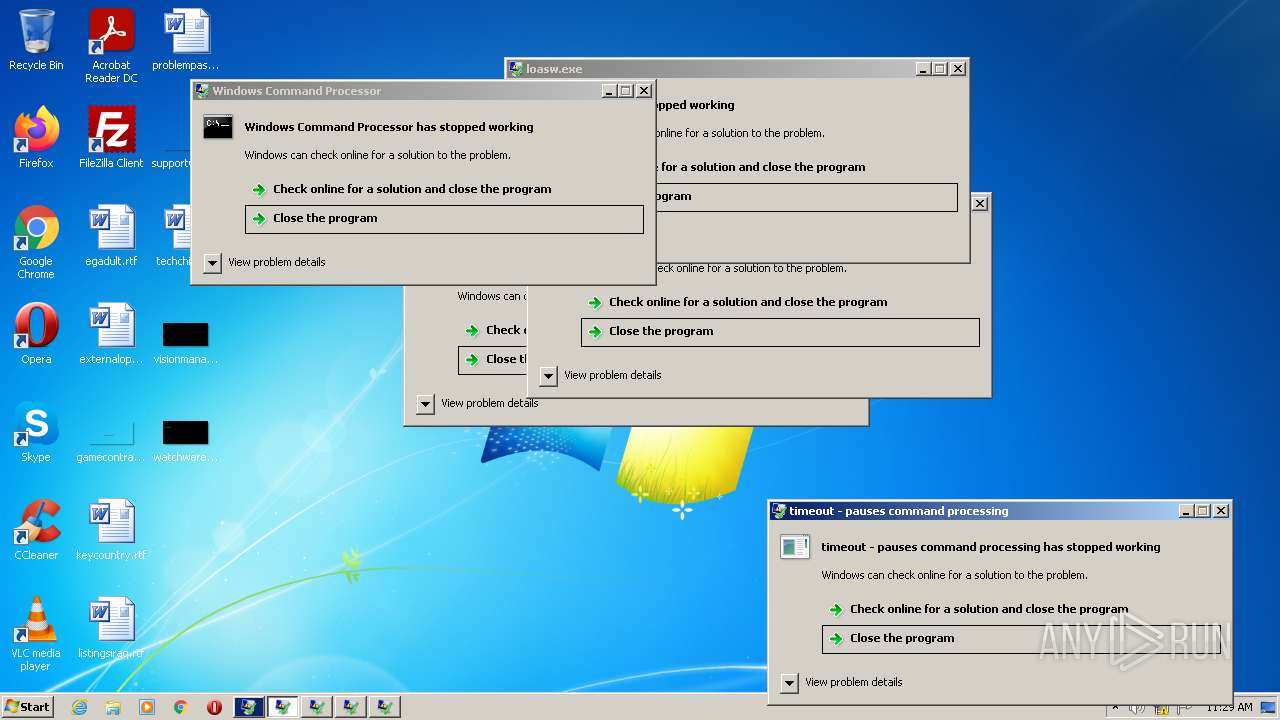
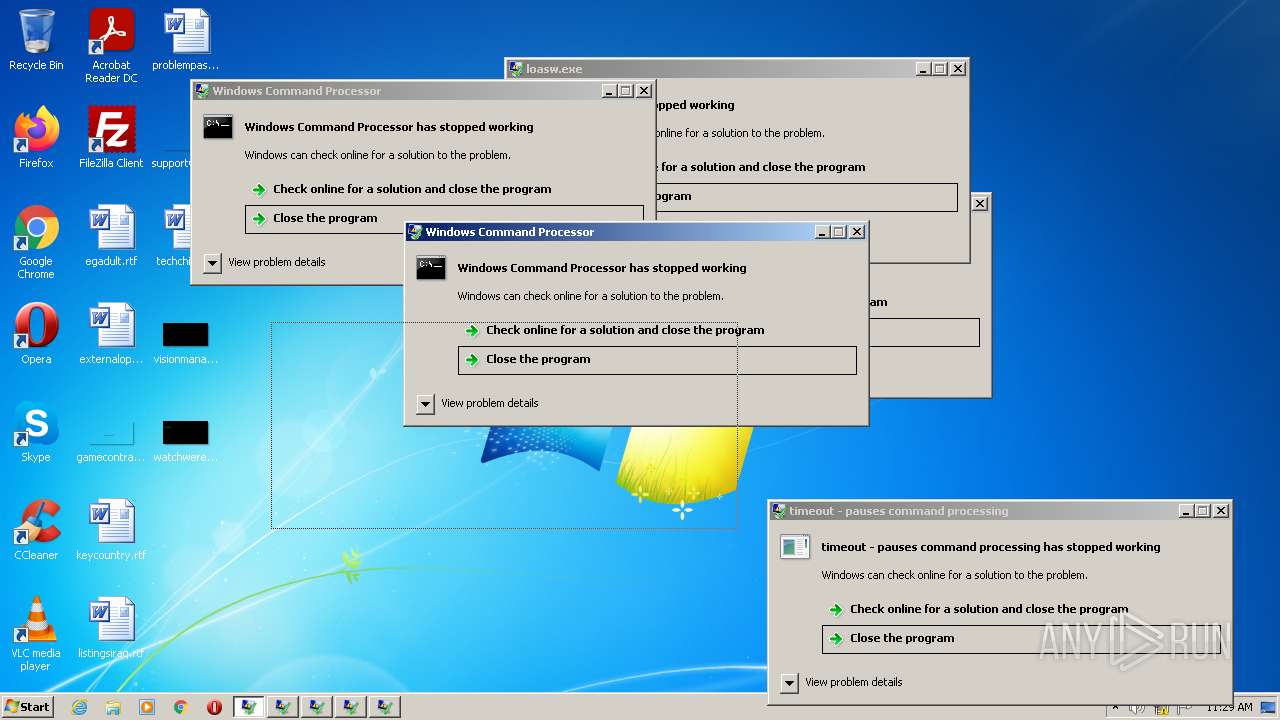
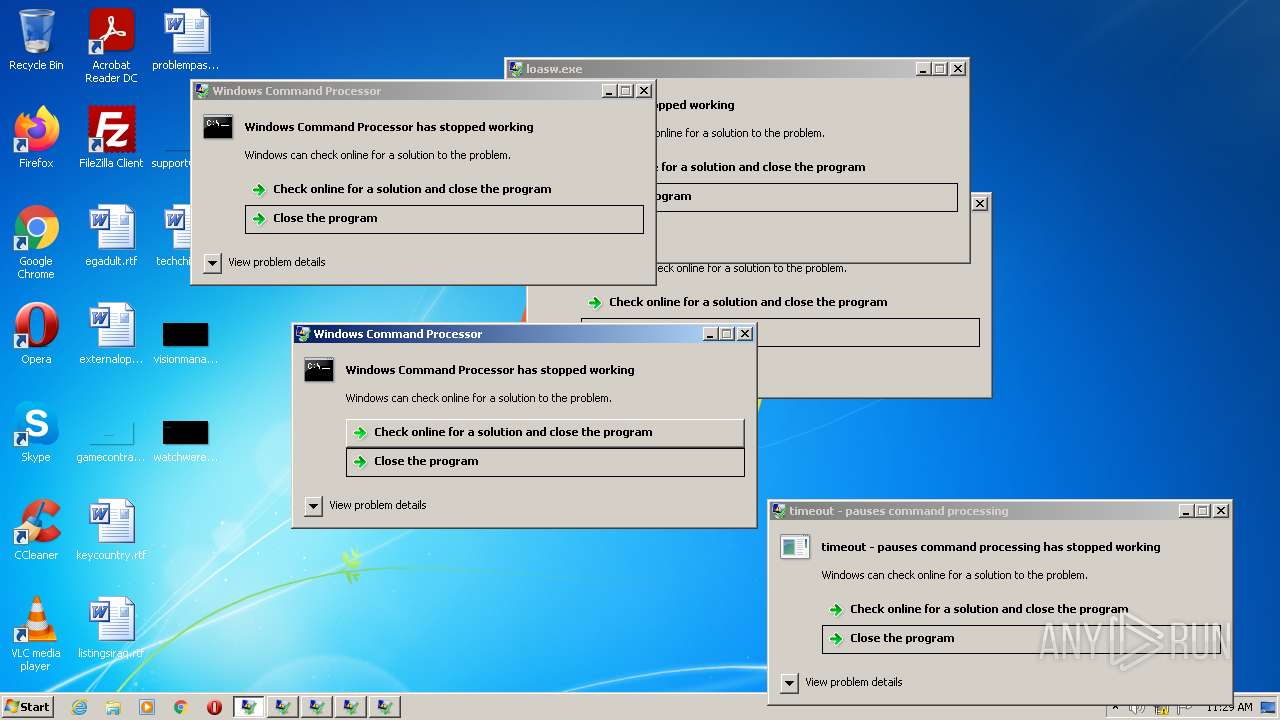
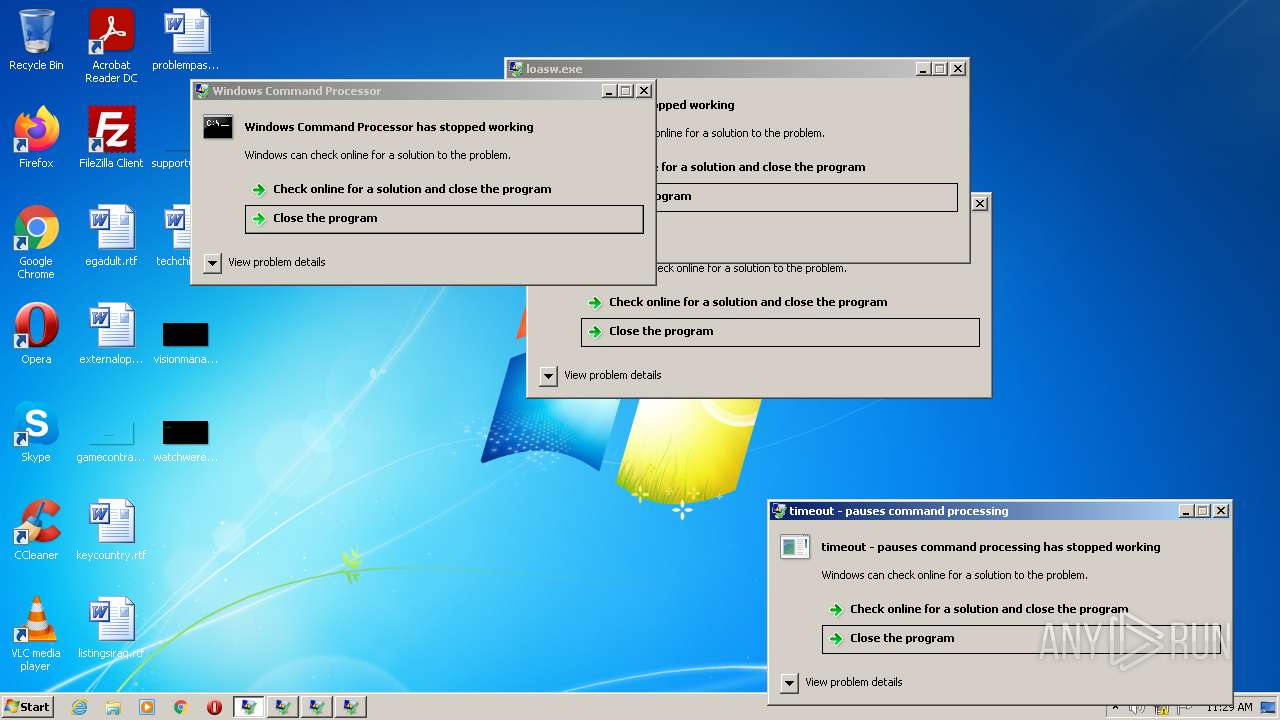
- WerFault.exe (PID: 1296)
- WerFault.exe (PID: 3612)
- svchost.exe (PID: 912)
- conhost.exe (PID: 3916)
- WerFault.exe (PID: 1740)
- WerFault.exe (PID: 3876)
- WerFault.exe (PID: 888)
Loads dropped or rewritten executable
- rundll32.exe (PID: 2480)
SUSPICIOUS
Checks supported languages
- Driver Easy Pro License Keys.exe (PID: 2716)
- License Keys.exe (PID: 3308)
- License Keys.exe (PID: 1468)
- file.exe (PID: 2460)
- 00000029..exe (PID: 1132)
- 00004823..exe (PID: 3920)
- conhost.exe (PID: 3916)
- conhost.exe (PID: 3968)
- cmd.exe (PID: 2324)
- loasw.exe (PID: 2584)
- cmd.exe (PID: 2408)
- search_hyperfs_212.exe (PID: 2304)
- KiffAppE2.exe (PID: 3024)
Reads the computer name
- KiffAppE2.exe (PID: 3024)
- License Keys.exe (PID: 3308)
- file.exe (PID: 2460)
- License Keys.exe (PID: 1468)
- 00000029..exe (PID: 1132)
- search_hyperfs_212.exe (PID: 2304)
- Driver Easy Pro License Keys.exe (PID: 2716)
Drops a file with a compile date too recent
- Driver Easy Pro License Keys.exe (PID: 2716)
- file.exe (PID: 2460)
- 00004823..exe (PID: 3920)
- License Keys.exe (PID: 1468)
Reads Environment values
- KiffAppE2.exe (PID: 3024)
- 00000029..exe (PID: 1132)
Application launched itself
- License Keys.exe (PID: 3308)
Adds / modifies Windows certificates
- License Keys.exe (PID: 1468)
Creates files in the user directory
- file.exe (PID: 2460)
- 00004823..exe (PID: 3920)
Executable content was dropped or overwritten
- file.exe (PID: 2460)
- 00004823..exe (PID: 3920)
- License Keys.exe (PID: 1468)
- Driver Easy Pro License Keys.exe (PID: 2716)
Starts CMD.EXE for self-deleting
- 00000029..exe (PID: 1132)
- file.exe (PID: 2460)
Starts CMD.EXE for commands execution
- 00000029..exe (PID: 1132)
- file.exe (PID: 2460)
Executed via WMI
- rundll32.exe (PID: 2480)
Reads default file associations for system extensions
- search_hyperfs_212.exe (PID: 2304)
Uses RUNDLL32.EXE to load library
- control.exe (PID: 956)
INFO
Reads settings of System Certificates
- KiffAppE2.exe (PID: 3024)
- License Keys.exe (PID: 1468)
- file.exe (PID: 2460)
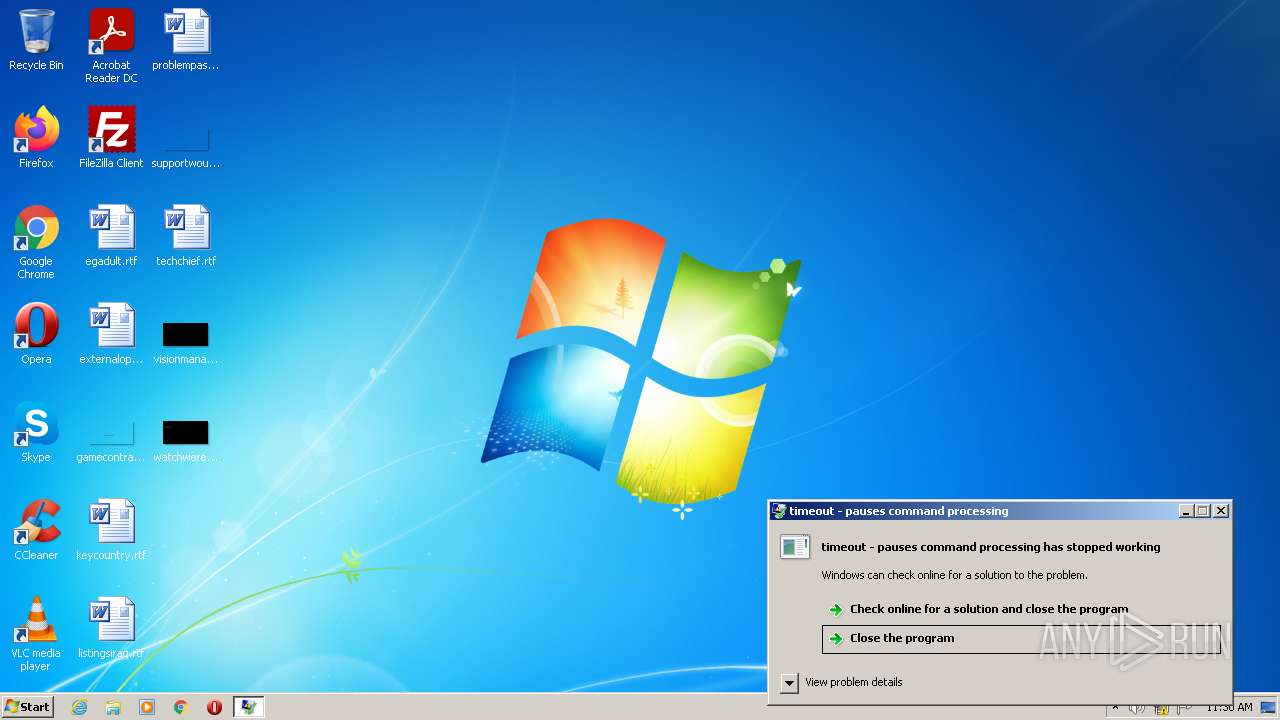
Checks supported languages
- DllHost.exe (PID: 2376)
- timeout.exe (PID: 2392)
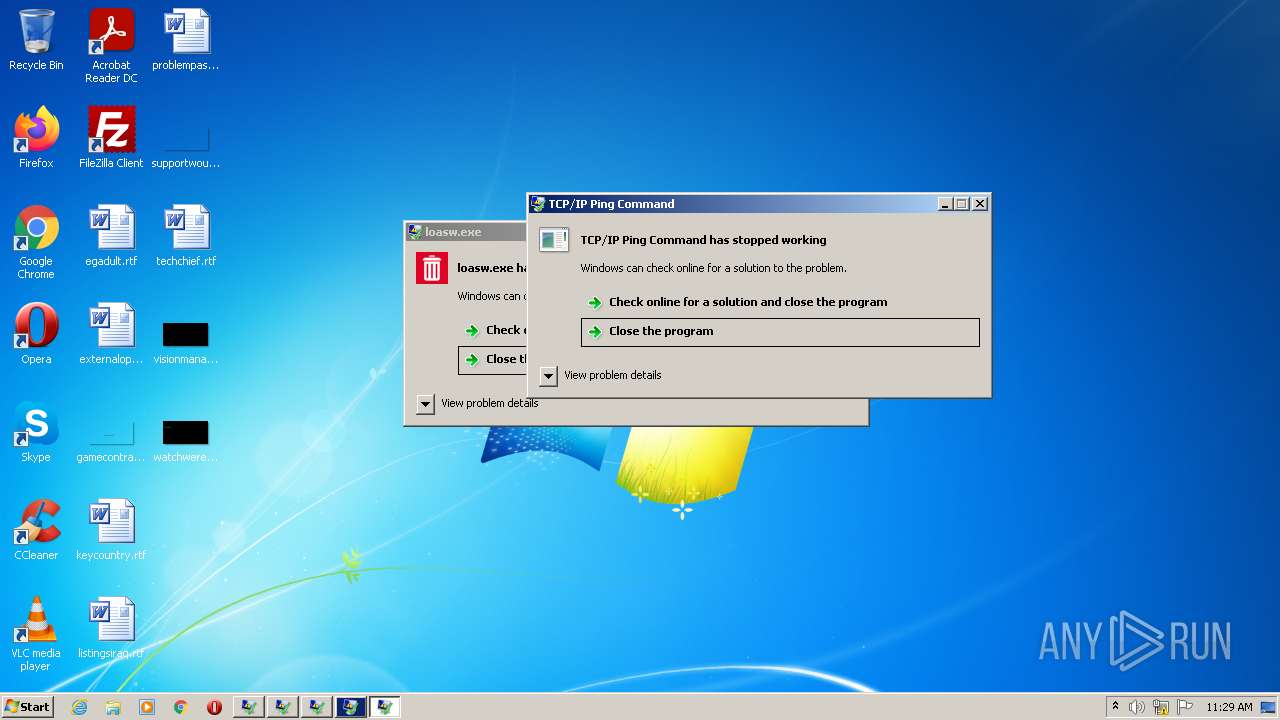
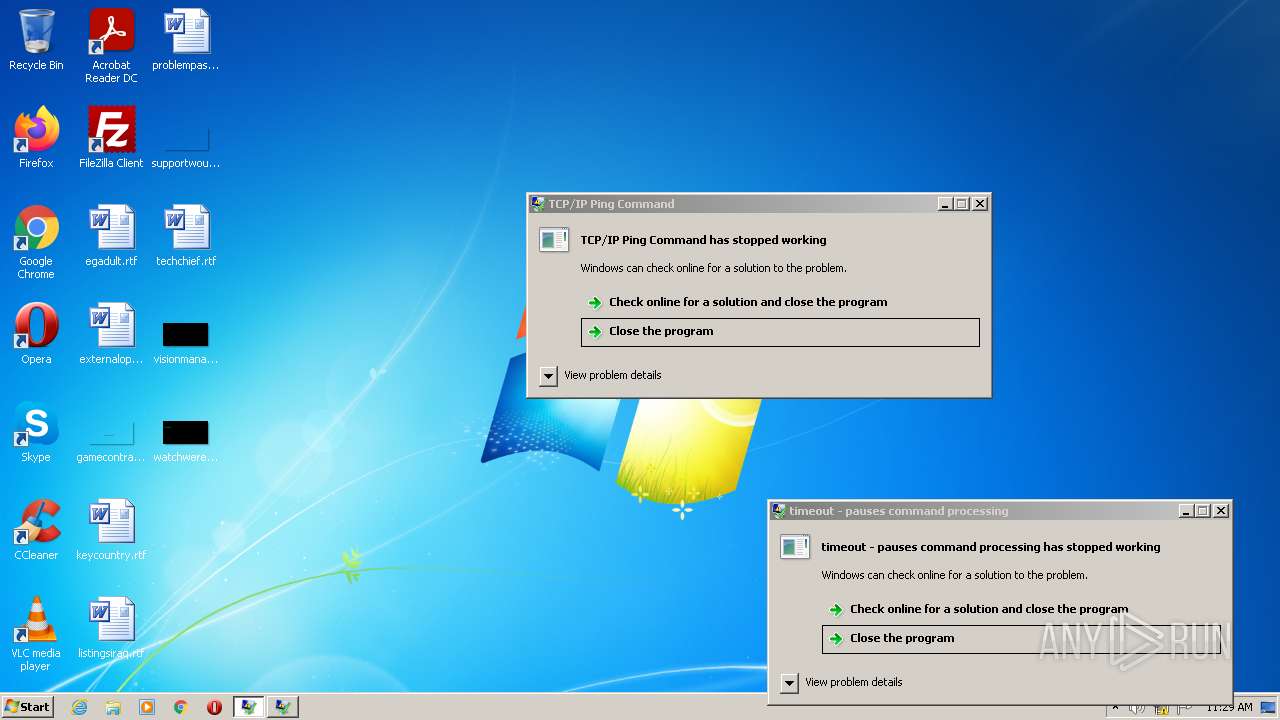
- PING.EXE (PID: 3708)
- WerFault.exe (PID: 1740)
- WerFault.exe (PID: 3612)
- WerFault.exe (PID: 1296)
- WerFault.exe (PID: 888)
- WerFault.exe (PID: 3876)
- rundll32.exe (PID: 2480)
- rundll32.exe (PID: 2224)
- control.exe (PID: 956)
Reads the computer name
- DllHost.exe (PID: 2376)
- PING.EXE (PID: 3708)
- WerFault.exe (PID: 1740)
- WerFault.exe (PID: 1296)
- WerFault.exe (PID: 3612)
- WerFault.exe (PID: 888)
- WerFault.exe (PID: 3876)
- rundll32.exe (PID: 2480)
- control.exe (PID: 956)
- rundll32.exe (PID: 2224)
Checks Windows Trust Settings
- file.exe (PID: 2460)
Dropped object may contain Bitcoin addresses
- file.exe (PID: 2460)
- 00004823..exe (PID: 3920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x14220 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 189952 |
| CodeSize: | 156160 |
| LinkerVersion: | 14.3 |
| PEType: | PE32 |
| TimeStamp: | 2022:03:03 14:16:04+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2022 13:16:04 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Mar-2022 13:16:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000261EC | 0x00026200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69378 |
.rdata | 0x00028000 | 0x0000A2DE | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26322 |
.data | 0x00033000 | 0x00035D60 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.07618 |
.didat | 0x00069000 | 0x00000160 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.04904 |
.rsrc | 0x0006A000 | 0x000204C0 | 0x00020600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20007 |
.reloc | 0x0008B000 | 0x00002878 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6547 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.94962 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 4.01018 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.06215 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.21098 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 4.32824 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.11236 | 440 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
62
Monitored processes
29
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\system32\Dwm.exe" | C:\Windows\system32\Dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | C:\Windows\system32\WerFault.exe -u -p 2584 -s 52 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 912 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Windows\System32\control.exe" "C:\Users\admin\AppData\Local\Temp\6X91w.cpL", | C:\Windows\System32\control.exe | — | search_hyperfs_212.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Roaming\00000029..exe" | C:\Users\admin\AppData\Roaming\00000029..exe | — | file.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1136 | taskeng.exe {30594FB5-CCA3-48AF-911A-8916FFBF6C74} | C:\Windows\system32\taskeng.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Engine Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | C:\Windows\system32\WerFault.exe -u -p 2324 -s 92 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1368 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1468 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\License Keys.exe" H | C:\Users\admin\AppData\Local\Temp\RarSFX0\License Keys.exe | License Keys.exe | ||||||||||||
User: admin Company: TODO: <Company name> Integrity Level: HIGH Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
18 148
Read events
17 996
Write events
152
Delete events
0
Modification events
| (PID) Process: | (2716) Driver Easy Pro License Keys.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2716) Driver Easy Pro License Keys.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2716) Driver Easy Pro License Keys.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2716) Driver Easy Pro License Keys.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_CURRENT_USER\KiffAppApi |
| Operation: | write | Name: | DataSet |
Value: 7/13/2022 10:29:08 AM | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KiffAppE2_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KiffAppE2_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KiffAppE2_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KiffAppE2_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3024) KiffAppE2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\KiffAppE2_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
13
Suspicious files
8
Text files
0
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2716 | Driver Easy Pro License Keys.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\KiffAppE2.exe | executable | |
MD5:— | SHA256:— | |||
| 2716 | Driver Easy Pro License Keys.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\License Keys.exe | executable | |
MD5:— | SHA256:— | |||
| 1468 | License Keys.exe | C:\Users\admin\AppData\Local\Temp\TarD876.tmp | cat | |
MD5:— | SHA256:— | |||
| 2716 | Driver Easy Pro License Keys.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\loasw.exe | executable | |
MD5:— | SHA256:— | |||
| 2716 | Driver Easy Pro License Keys.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\search_hyperfs_212.exe | executable | |
MD5:— | SHA256:— | |||
| 1468 | License Keys.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 1296 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_cmd.exe_b2786caf465bfd146e2ce5f653571bd9ef577a93_05002656\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1468 | License Keys.exe | C:\Users\admin\AppData\Local\Temp\CabD875.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3612 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_cmd.exe_b2786caf465bfd146e2ce5f653571bd9ef577a93_0e0c29c1\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2460 | file.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
9
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | file.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
2460 | file.exe | GET | 200 | 184.24.77.53:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMSA3WNynf%2BEEaynHJMuIKUbA%3D%3D | US | der | 503 b | shared |
2460 | file.exe | GET | 200 | 178.79.242.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9b6675ab255b70c3 | DE | compressed | 4.70 Kb | whitelisted |
1468 | License Keys.exe | GET | 200 | 178.79.242.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?df1e9fcbac6f49a9 | DE | compressed | 60.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3024 | KiffAppE2.exe | 198.11.173.37:443 | mycrashed.tech | Alibaba (China) Technology Co., Ltd. | US | unknown |
1468 | License Keys.exe | 172.67.188.70:443 | v.xyzgamev.com | — | US | suspicious |
1468 | License Keys.exe | 178.79.242.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | malicious |
2460 | file.exe | 185.175.200.64:443 | yesilyasam.eu | Astralus B.V. | NL | suspicious |
2460 | file.exe | 178.79.242.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | DE | malicious |
2460 | file.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
3024 | KiffAppE2.exe | 54.91.59.199:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
2460 | file.exe | 184.24.77.53:80 | r3.o.lencr.org | Time Warner Cable Internet LLC | US | unknown |
— | — | 34.64.183.91:443 | toa.mygametoa.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
mycrashed.tech |
| unknown |
v.xyzgamev.com |
| suspicious |
yesilyasam.eu |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
toa.mygametoa.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | svchost.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Reserved Bit Set |
1 ETPRO signatures available at the full report