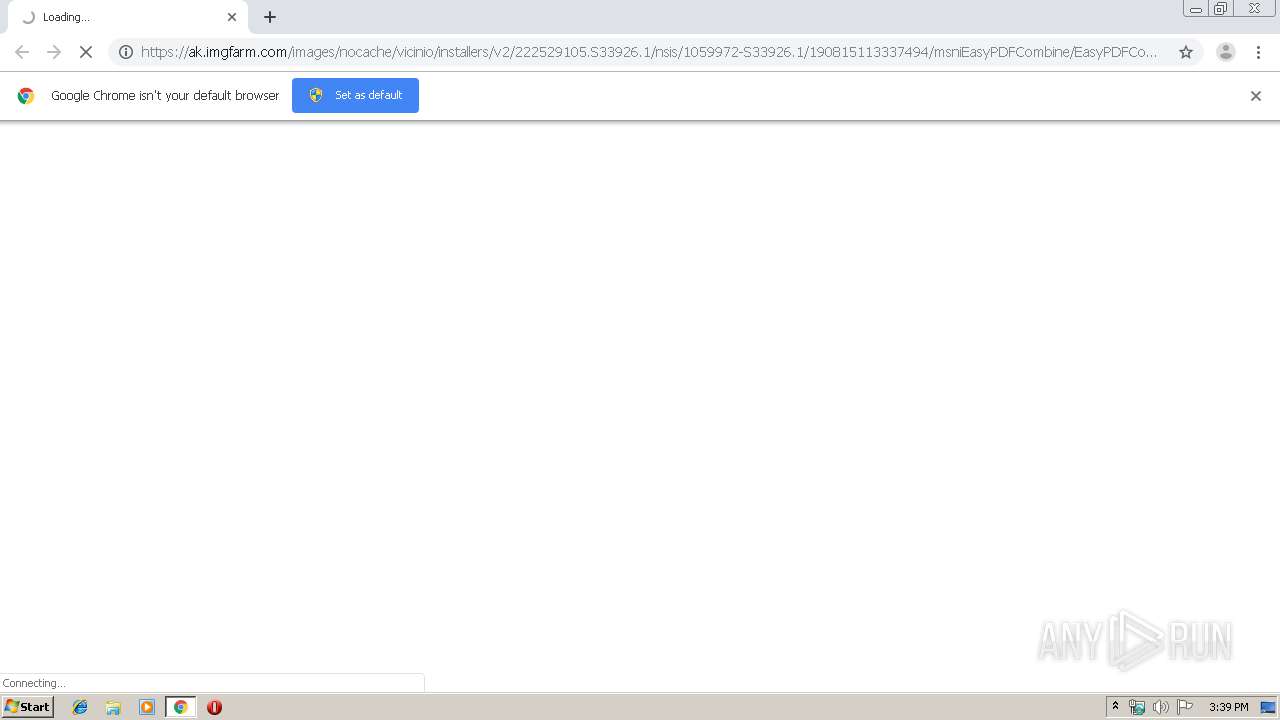
| URL: | https://ak.imgfarm.com/images/nocache/vicinio/installers/v2/222529105.S33926.1/nsis/1059972-S33926.1/190815113337494/msniEasyPDFCombine/EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe |
| Full analysis: | https://app.any.run/tasks/256788ea-7e35-4524-b5b6-40f924b4c905 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 14:39:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 400E1681D64628FF24767050A8D220E7 |
| SHA1: | 50B665FB58D79EBD58EFF7B7ECF4D02F1C753FA2 |
| SHA256: | E7FAA34A029AAB3CE04D7454E17CA3EF3703C4B3C38C145D0EA3471D36417A55 |
| SSDEEP: | 3:N8VEKCA0GEaAp3LWgOXBcXA/QNmfskI2WbDsUJNR7csrtUrjqq4EDqqMTV8E3WUS:2eTLpigOXBmA/QksBxbTNRcVZjuNh9GX |
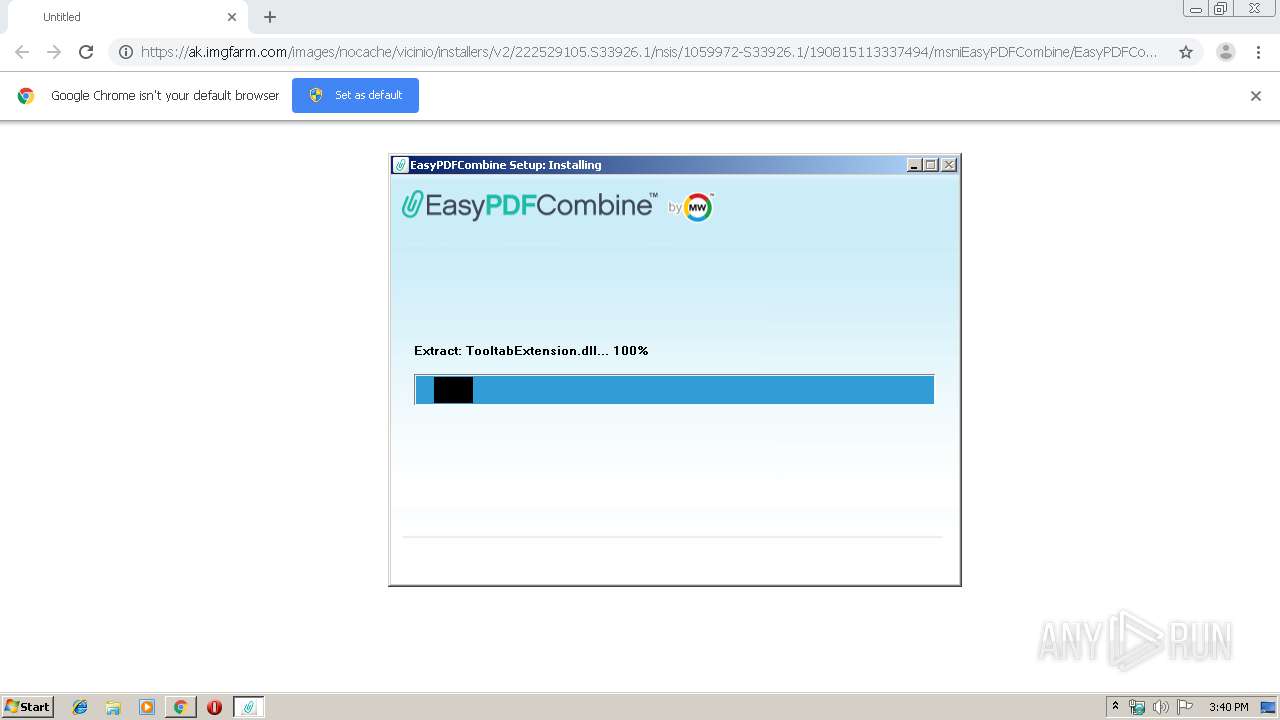
MALICIOUS
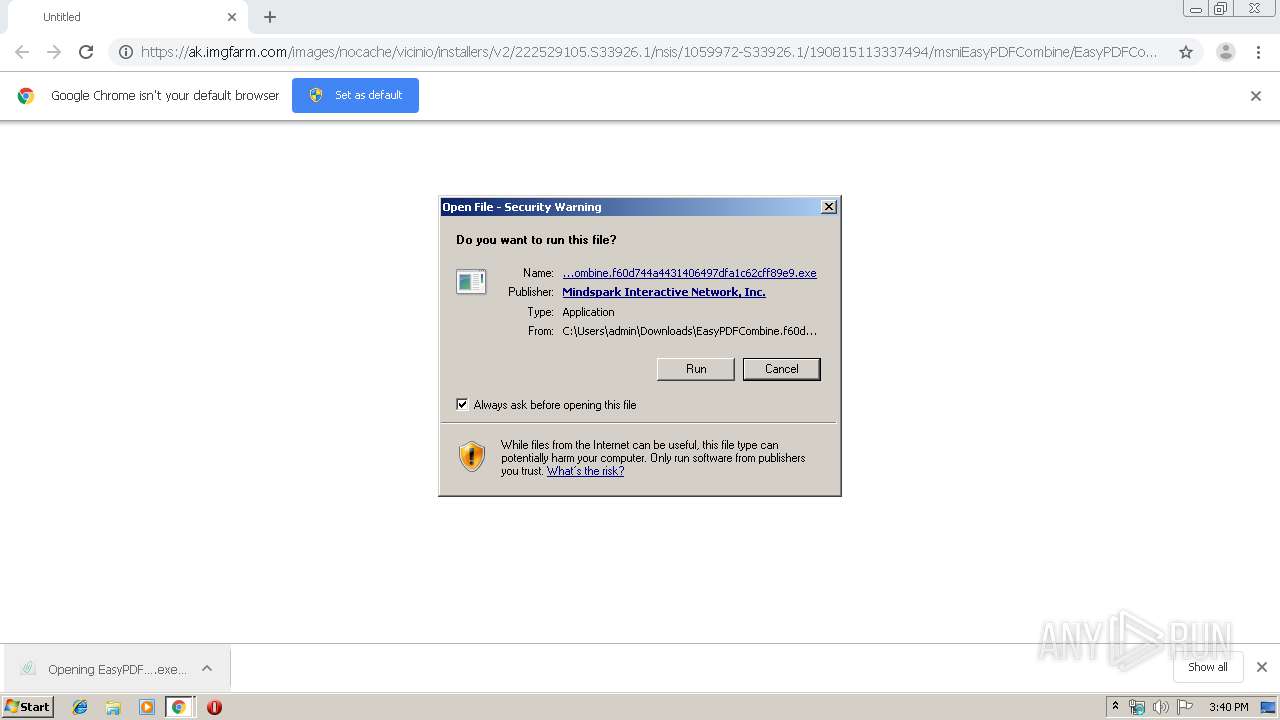
Application was dropped or rewritten from another process
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
Loads dropped or rewritten executable
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2812)
- chrome.exe (PID: 2464)
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
Creates files in the user directory
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
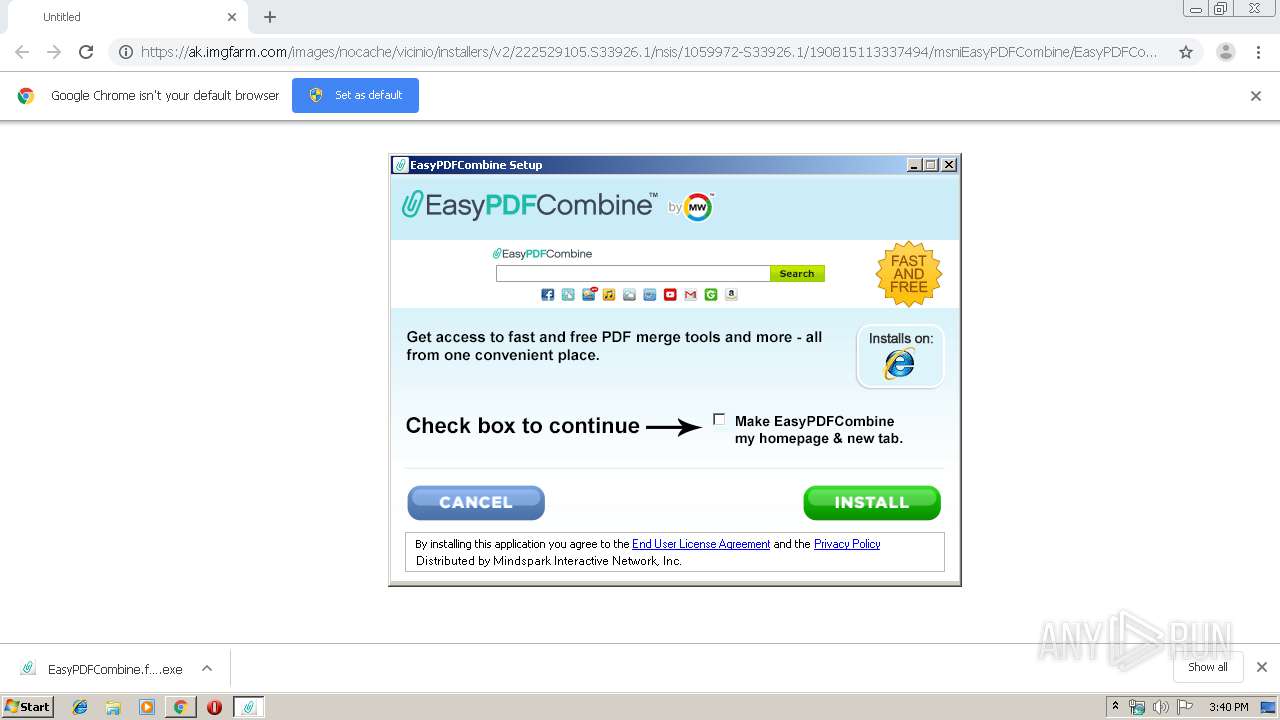
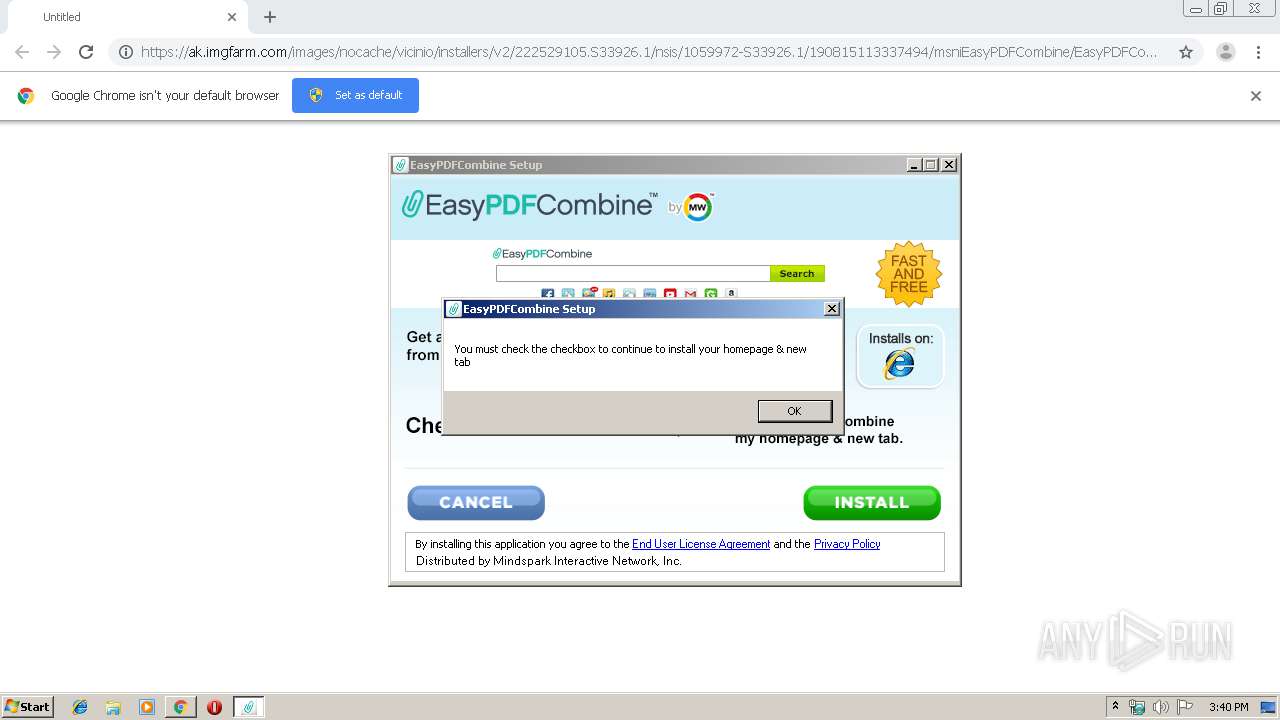
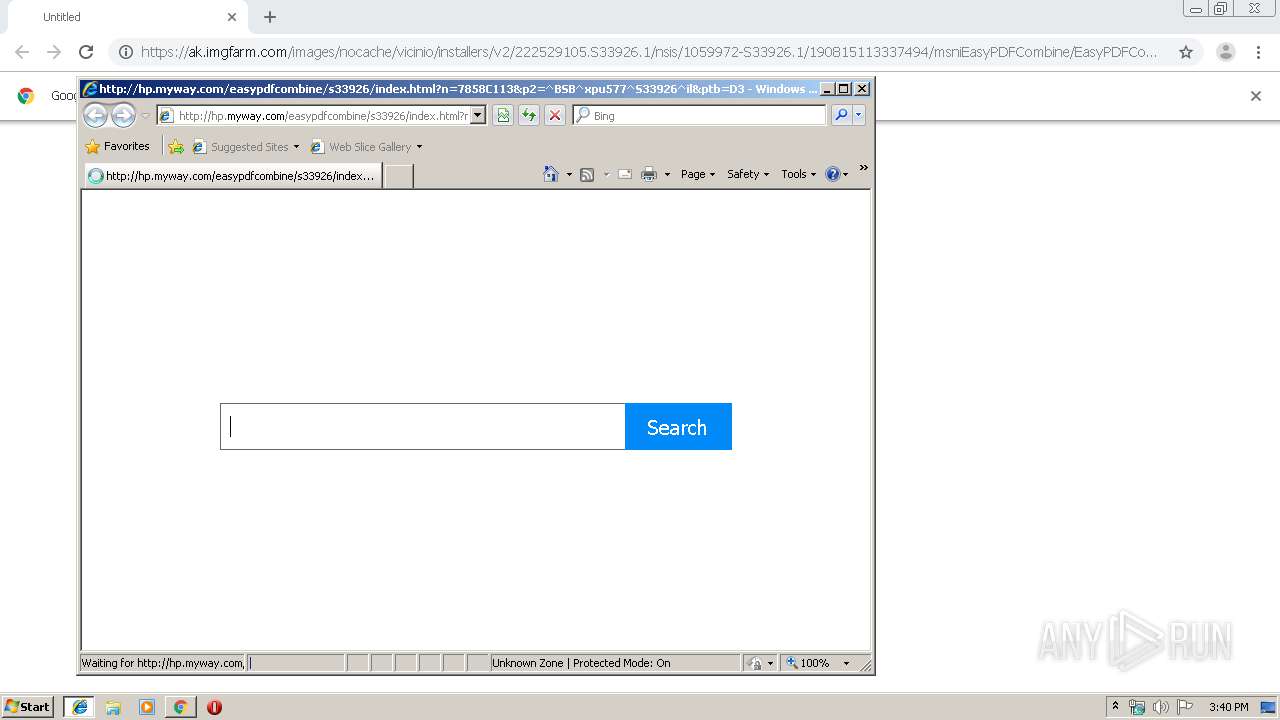
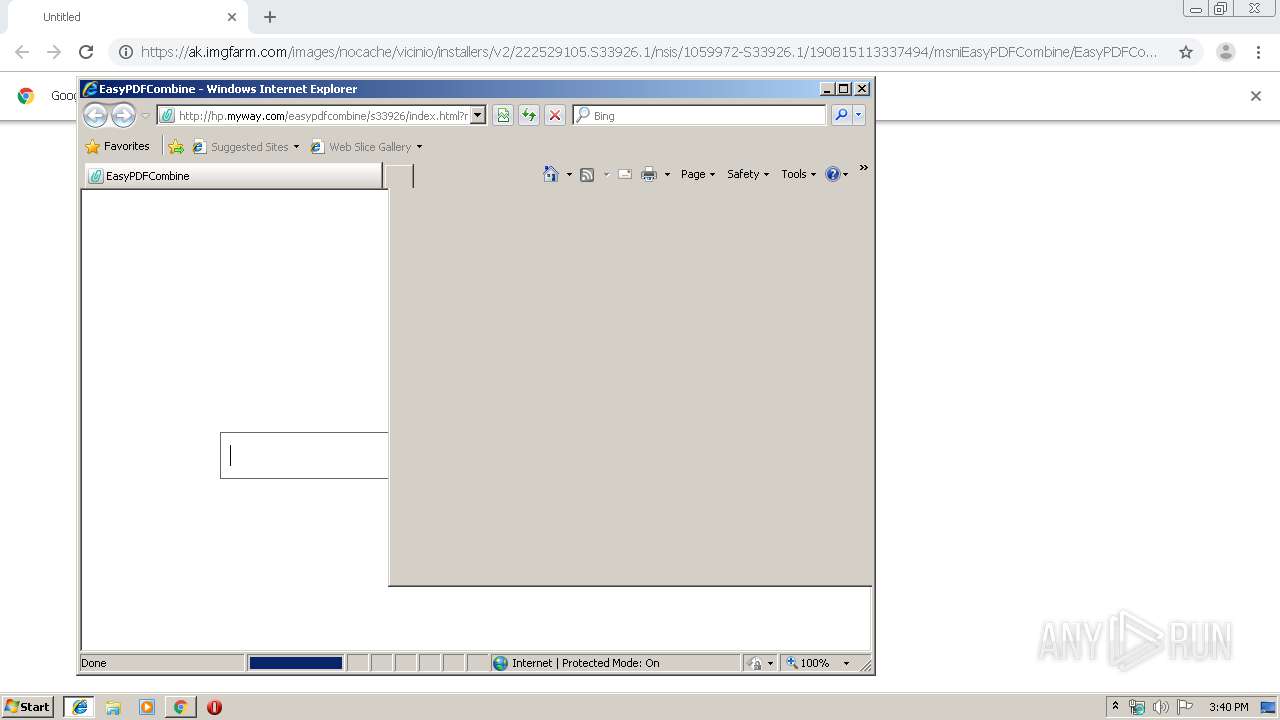
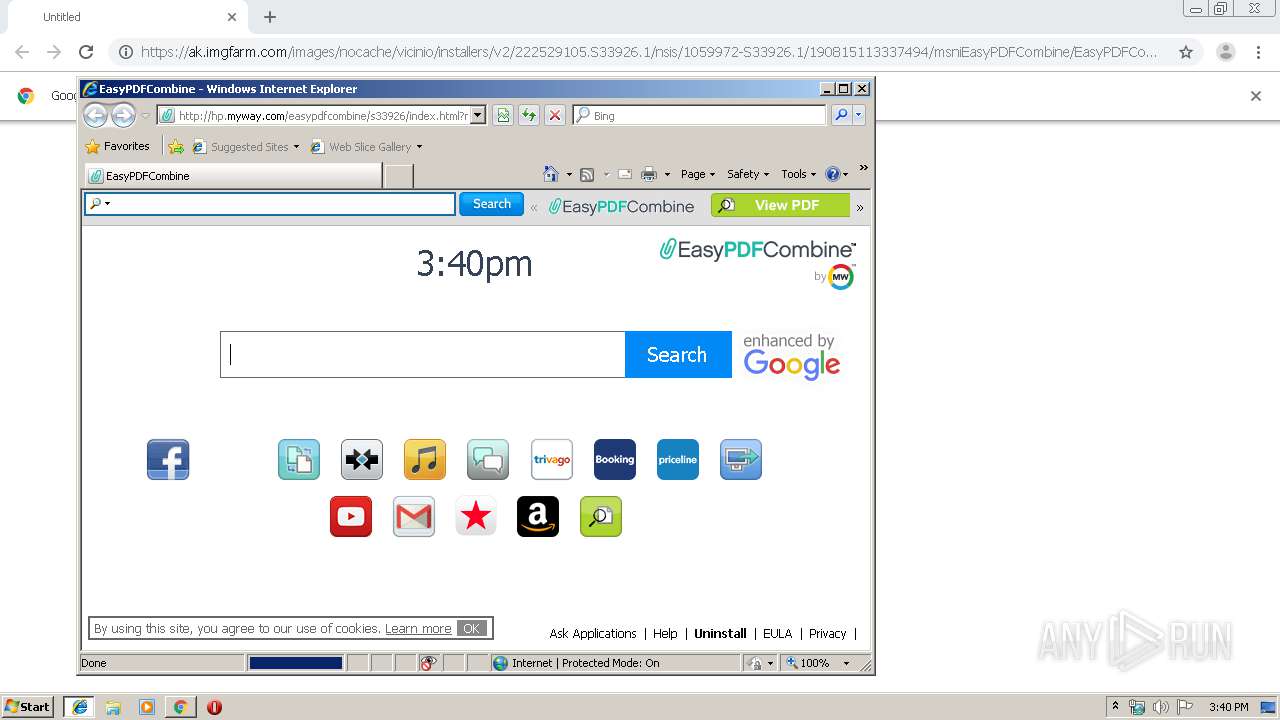
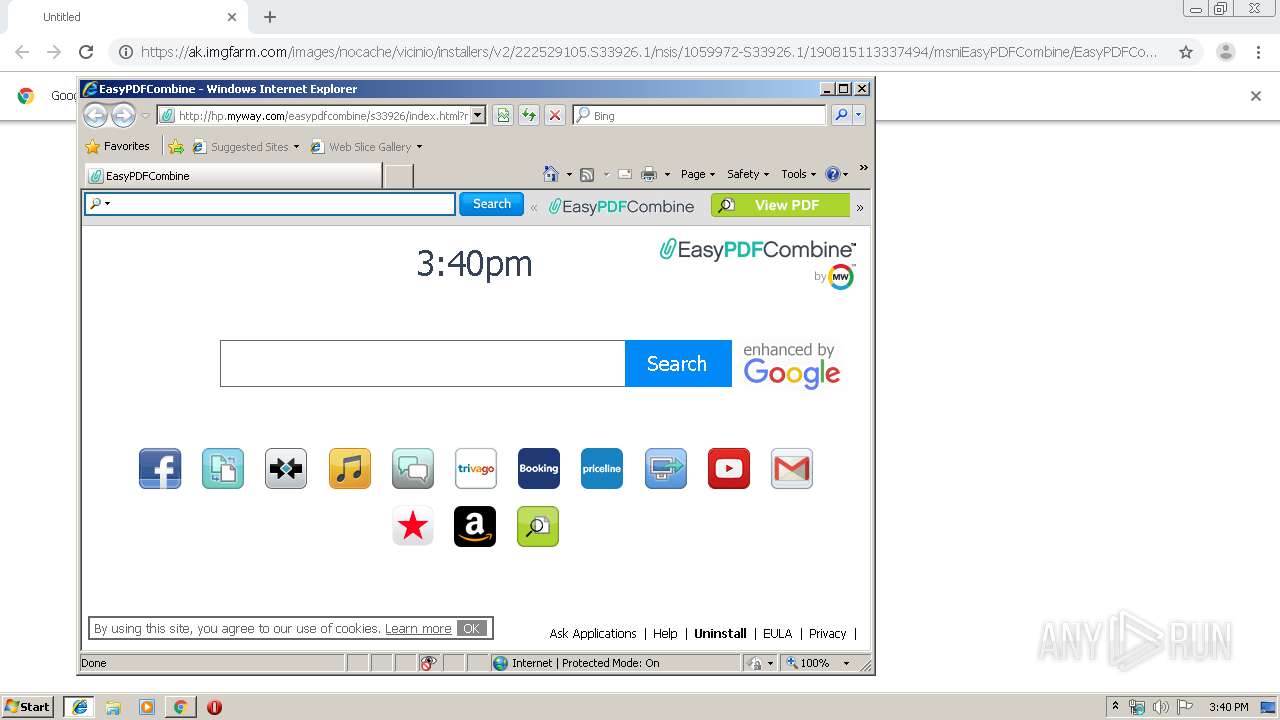
Changes the started page of IE
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
Creates a software uninstall entry
- EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe (PID: 2576)
Executed via COM
- iexplore.exe (PID: 2880)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3384)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2464)
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 3132)
Application launched itself
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 2880)
Reads Internet Cache Settings
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2484)
- iexplore.exe (PID: 3132)
Changes internet zones settings
- iexplore.exe (PID: 2880)
Creates files in the user directory
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2484)
- iexplore.exe (PID: 3132)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3384)
Reads internet explorer settings
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 2484)
- iexplore.exe (PID: 3132)
Changes settings of System certificates
- iexplore.exe (PID: 2880)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
16
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,9977176025106752179,601453240480611493,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16651441970469085702 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,9977176025106752179,601453240480611493,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8683357345826776574 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2880 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
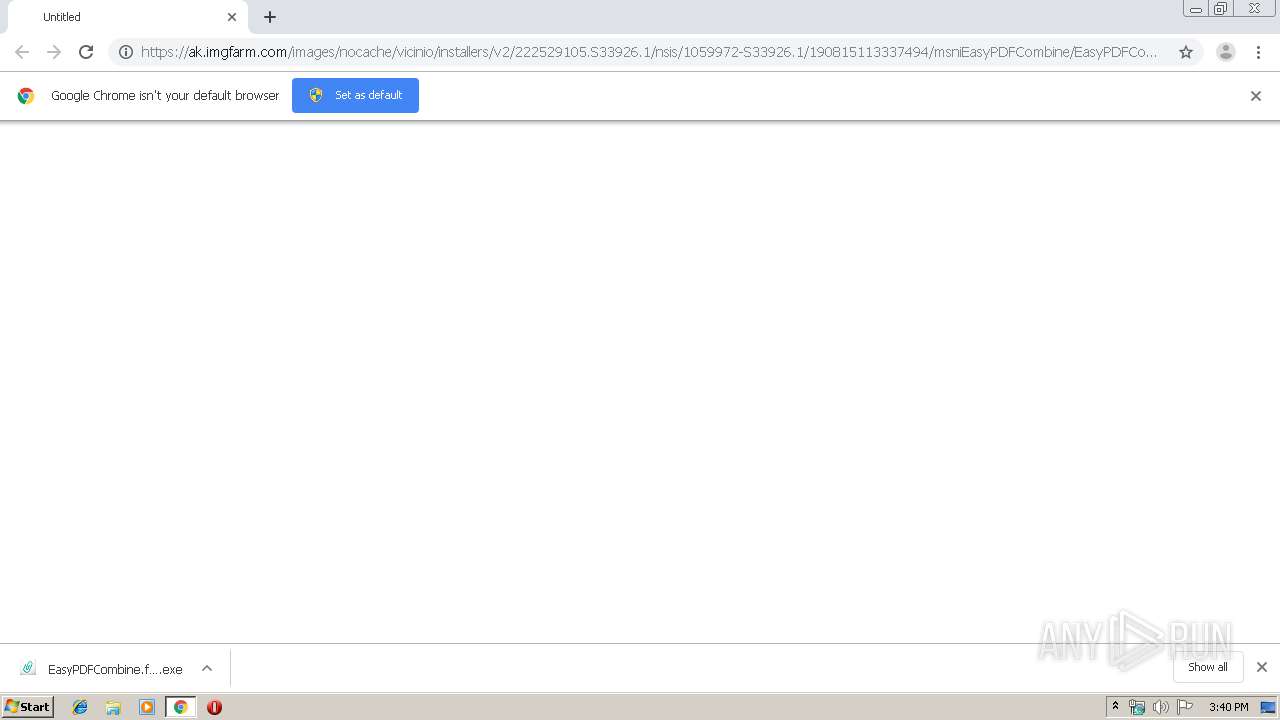
| 2576 | "C:\Users\admin\Downloads\EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe" | C:\Users\admin\Downloads\EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe | chrome.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: EasyPDFCombine Setup Exit code: 0 Version: 2.7.1.3000 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2880 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://ak.imgfarm.com/images/nocache/vicinio/installers/v2/222529105.S33926.1/nsis/1059972-S33926.1/190815113337494/msniEasyPDFCombine/EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2816 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,9977176025106752179,601453240480611493,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12979769489243317660 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,9977176025106752179,601453240480611493,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5711612155440392503 --mojo-platform-channel-handle=4092 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 276
Read events
2 021
Write events
249
Delete events
6
Modification events
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2812-13211217594408375 |
Value: 259 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
19
Text files
135
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d10d5b3a-947a-4054-8a4e-2a1ddd902355.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169c93.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c93.TMP | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
59
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/easypdfcombine/s33926/assets/1565723052965/ie8.js | NL | html | 870 b | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/easypdfcombine/s33926/index.html?n=7858C113&p2=^BSB^xpu577^S33926^il&ptb=D3D8E144-B4EE-48E4-B89B-EA60AA20C179&si=EAIaIQobChMIraOS952e5AIVaGAVCB321giiEAEYASAAEgLHjPD_BwE&coid=f60d744a4431406497dfa1c62cff89e9 | NL | html | 4.01 Kb | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/search/google_enhancedby_v2.png | NL | image | 5.21 Kb | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://hp.myway.com/easypdfcombine/s33926/assets/1565723052965/app.js | NL | text | 124 Kb | whitelisted |
2748 | iexplore.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/widgets/weatherblink/com.mindspark.weatherblink.unbranded-en/Background.html | NL | html | 235 b | whitelisted |
2880 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/223772257.png | NL | image | 776 b | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/searchbar/225376993.png | NL | image | 2.35 Kb | whitelisted |
3132 | iexplore.exe | GET | 200 | 23.38.53.120:80 | http://ak.staticimgfarm.com/images/webtooltab/assets/logos/BSB.png | NL | image | 6.15 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | iexplore.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
2464 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 23.38.53.120:443 | ak.imgfarm.com | Akamai International B.V. | NL | whitelisted |
— | — | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2464 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2576 | EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe | 74.113.237.192:443 | anx.mindspark.com | Mindspark Interactive Network, Inc. | US | malicious |
2576 | EasyPDFCombine.f60d744a4431406497dfa1c62cff89e9.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
2880 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
hp.myway.com |
| whitelisted |
www.bing.com |
| whitelisted |