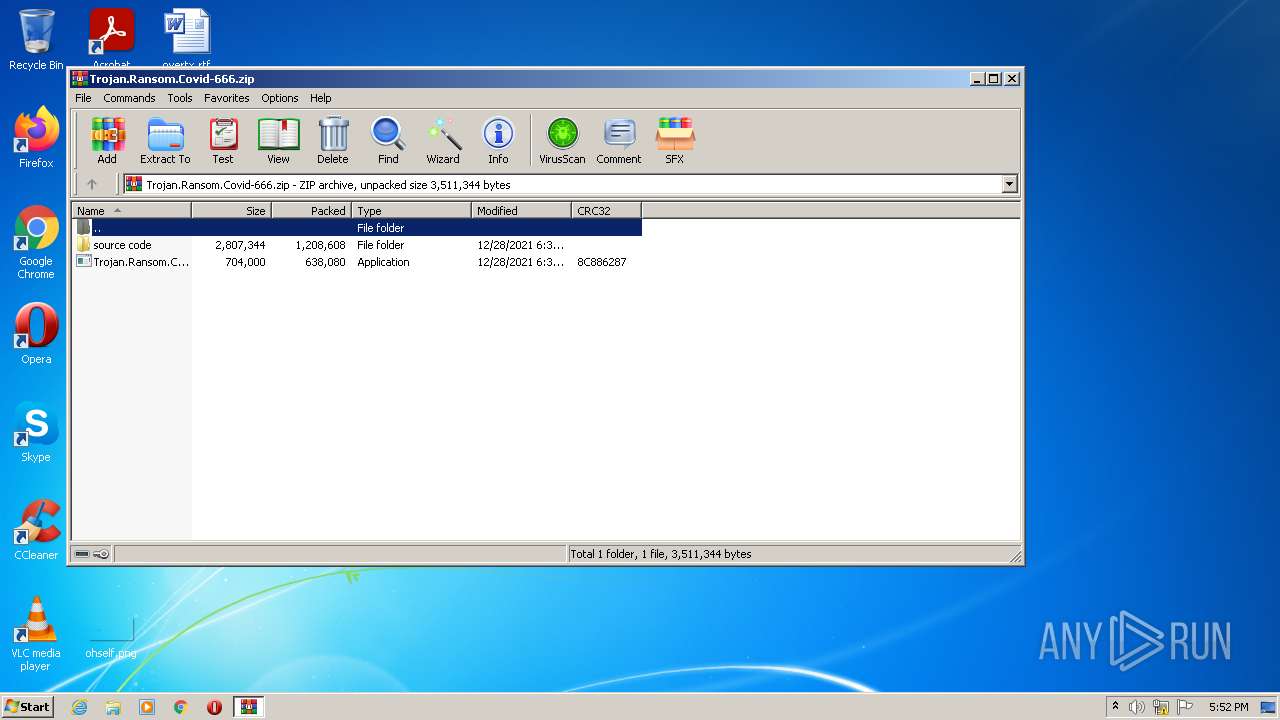
| File name: | Trojan.Ransom.Covid-666.zip |
| Full analysis: | https://app.any.run/tasks/b8213fcf-3c69-4e5f-b6fd-93e78f77ea0c |
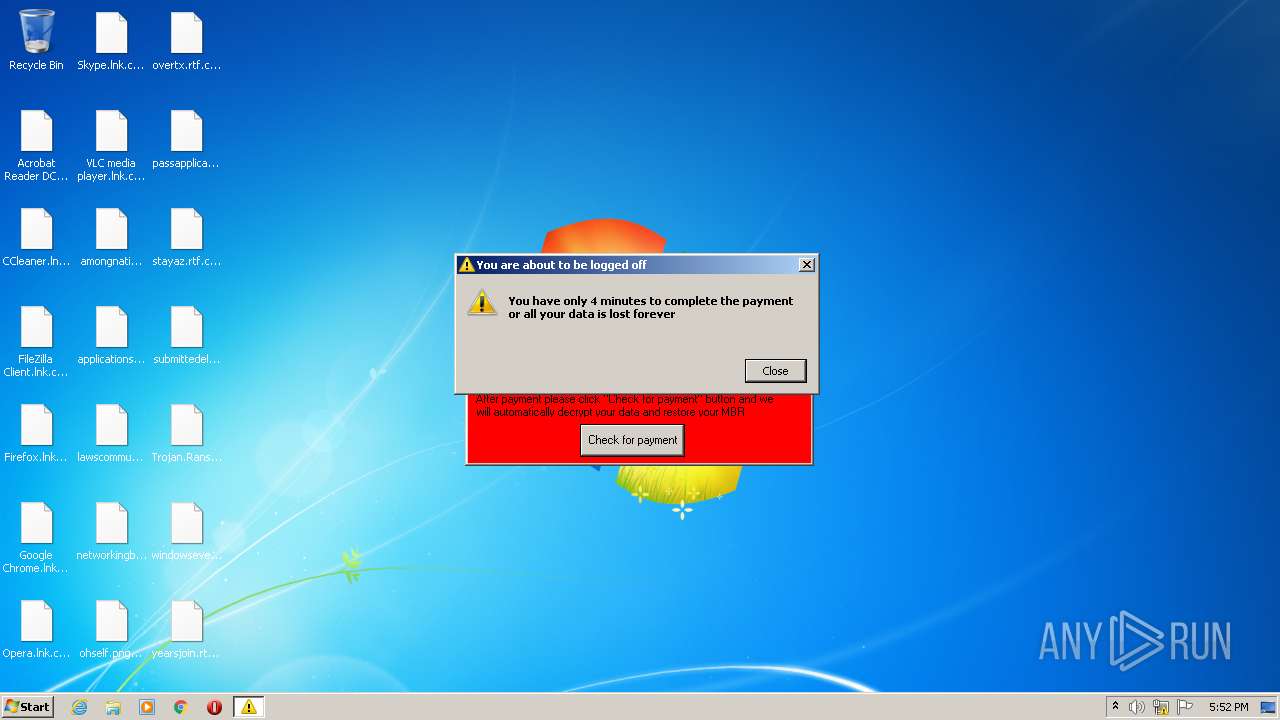
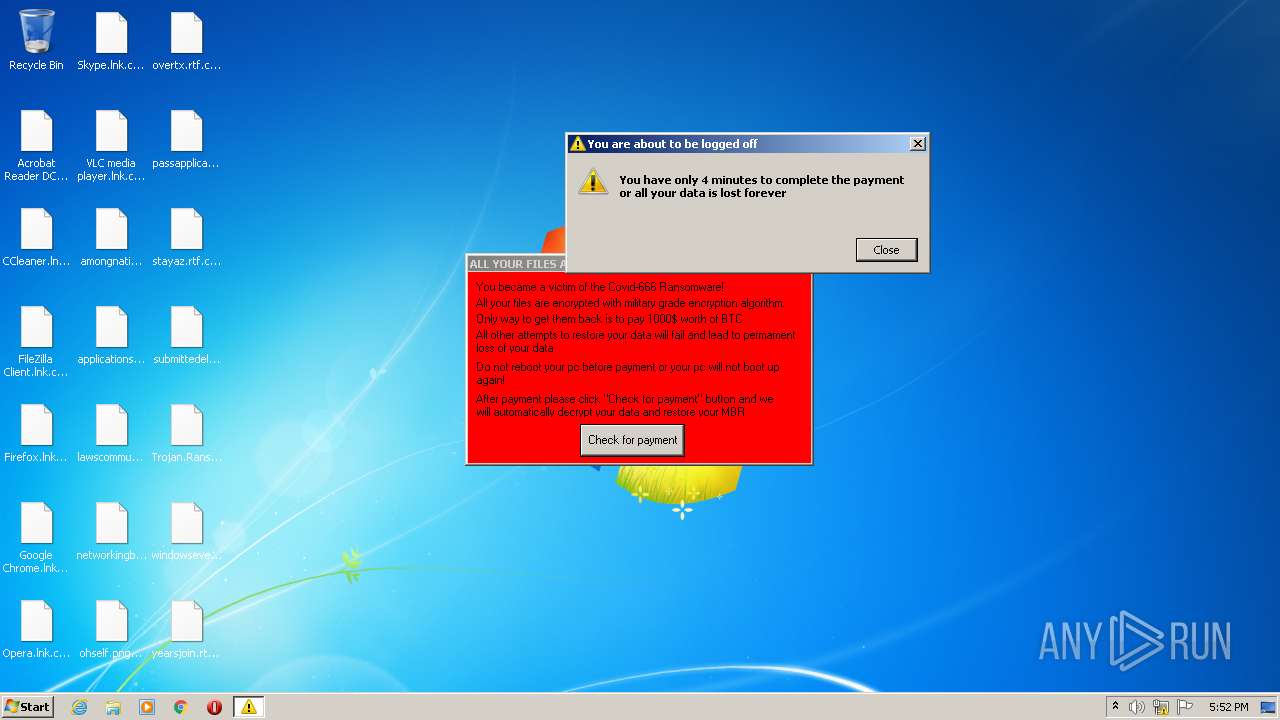
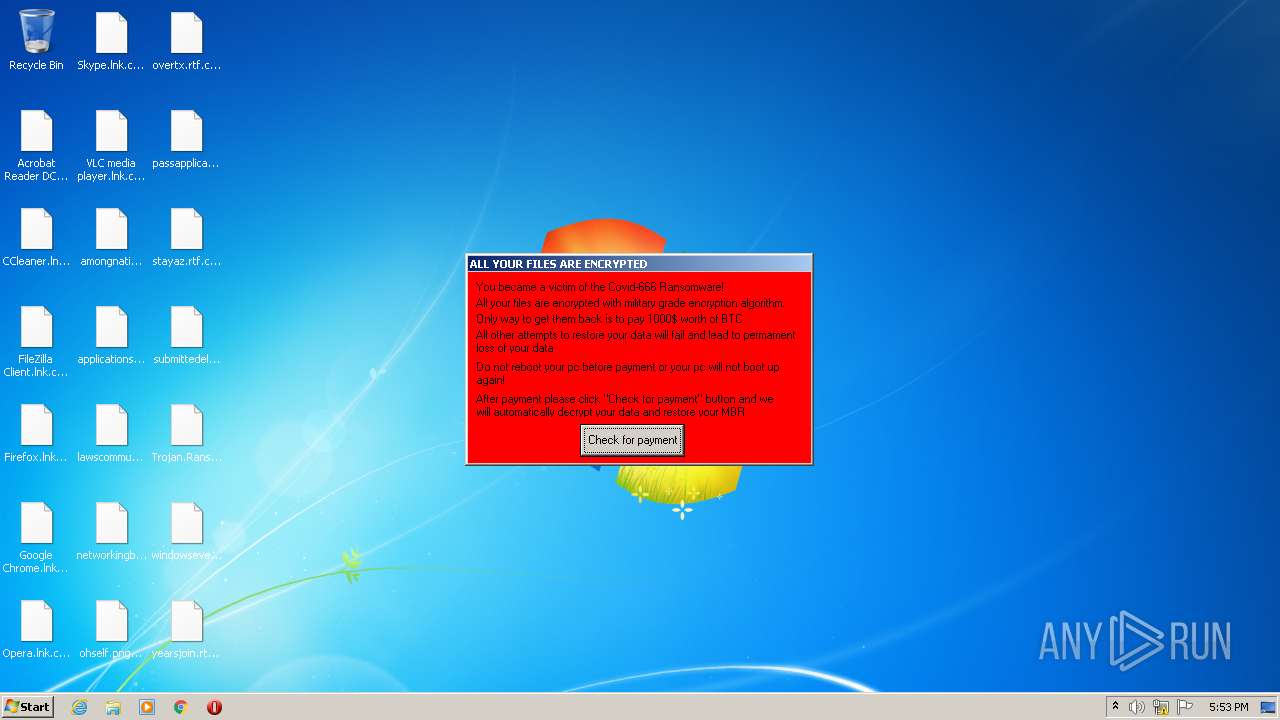
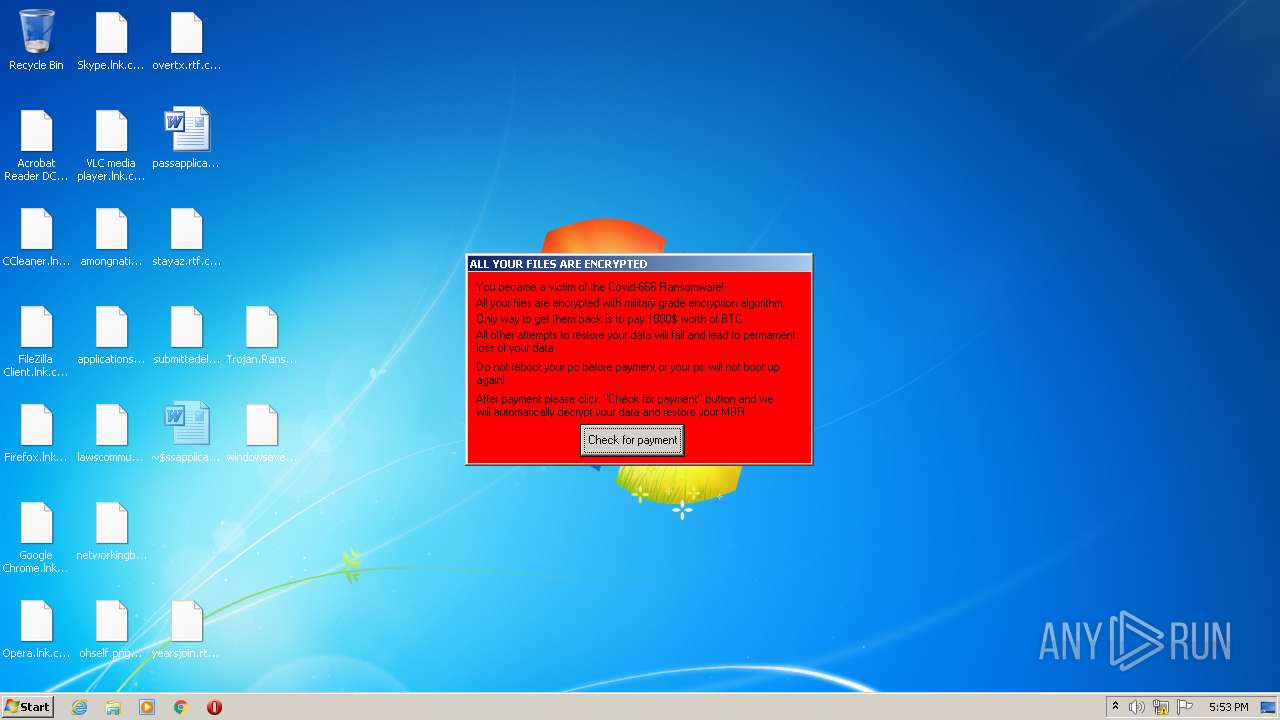
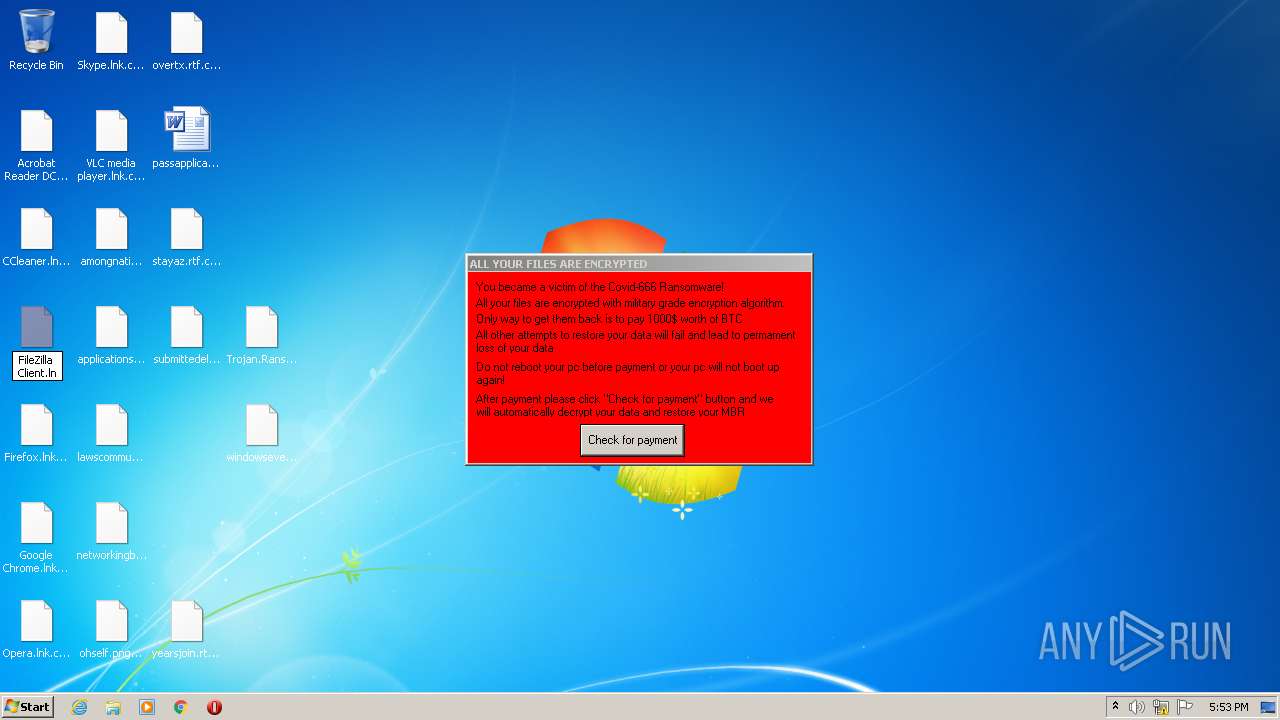
| Verdict: | Malicious activity |
| Analysis date: | January 06, 2022, 17:52:39 |
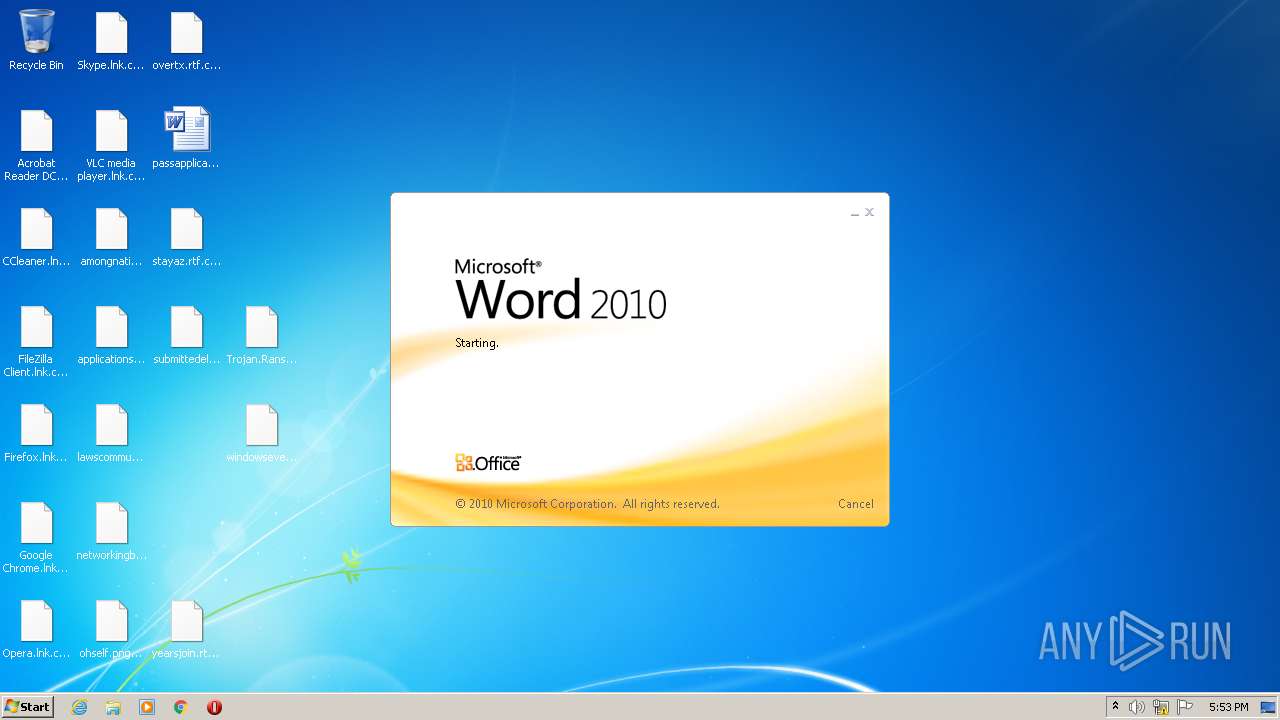
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 6913991E03E8224A3119F595408D3F29 |
| SHA1: | 088EA3A0809E5655232C3ED659EEE097FD5864E7 |
| SHA256: | E7EF23AF9ADEDDD5D43C3E6A736EA4FC3EB31CF6E08609DA01AC2CCC516216FB |
| SSDEEP: | 49152:hXjRG8OzbgFSXACZ4b1AEHAhovu+GEQMI1K+HMtX66JUku33Hg:hzRXOfZv4b1AQZvvXuK+HMB666B3A |
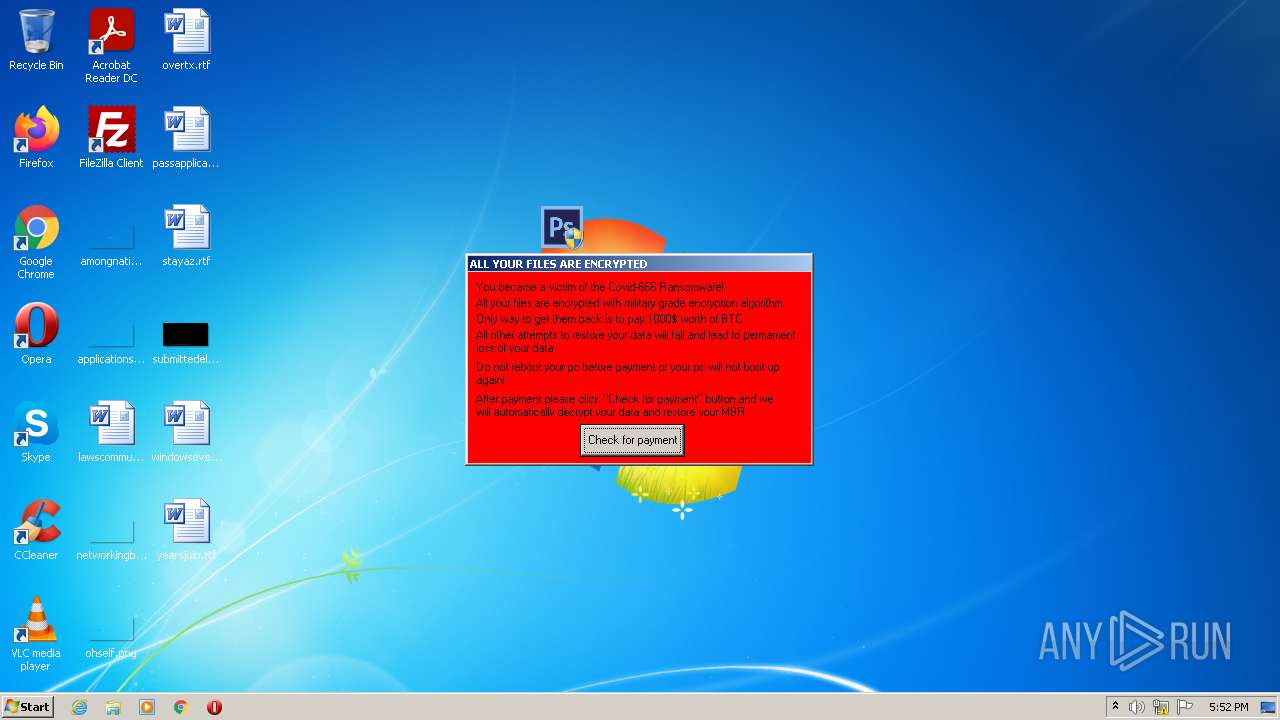
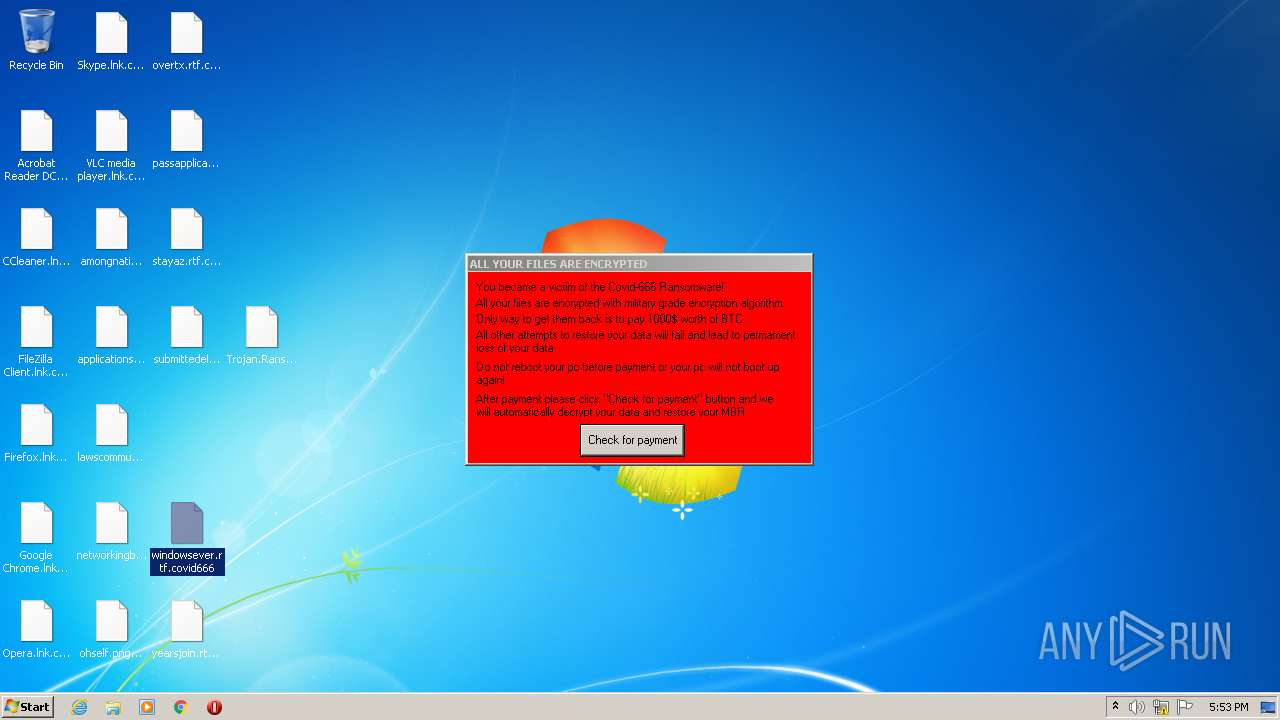
MALICIOUS
Application was dropped or rewritten from another process
- Trojan.Ransom.Covid-666.exe (PID: 2796)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
- MainWindow.exe (PID: 3156)
- mbr.exe (PID: 2460)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 1596)
Disables the LogOff in Start menu
- reg.exe (PID: 3636)
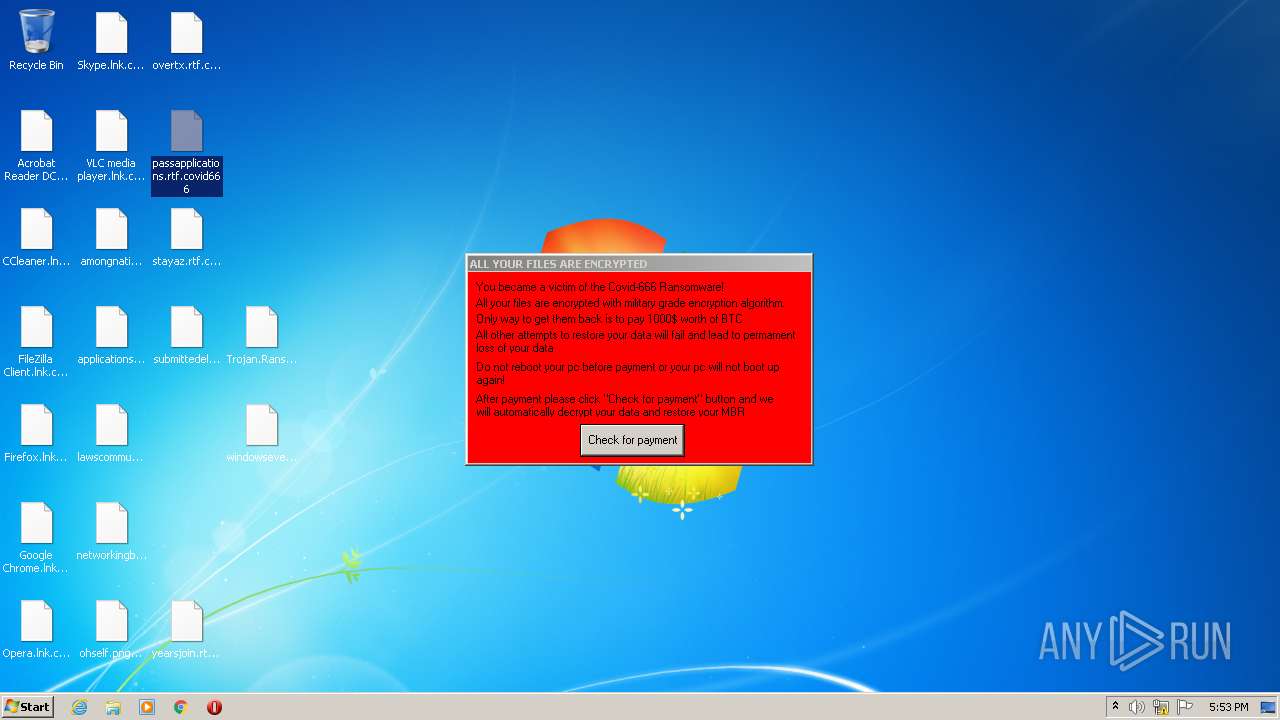
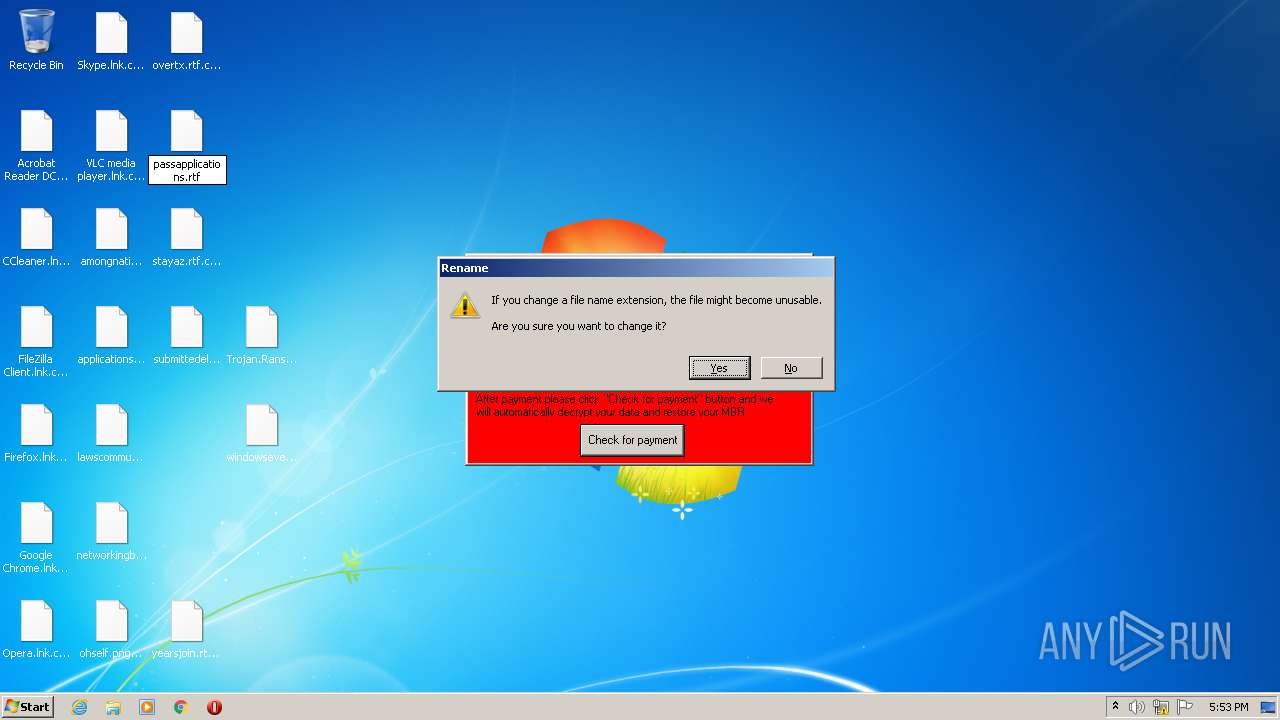
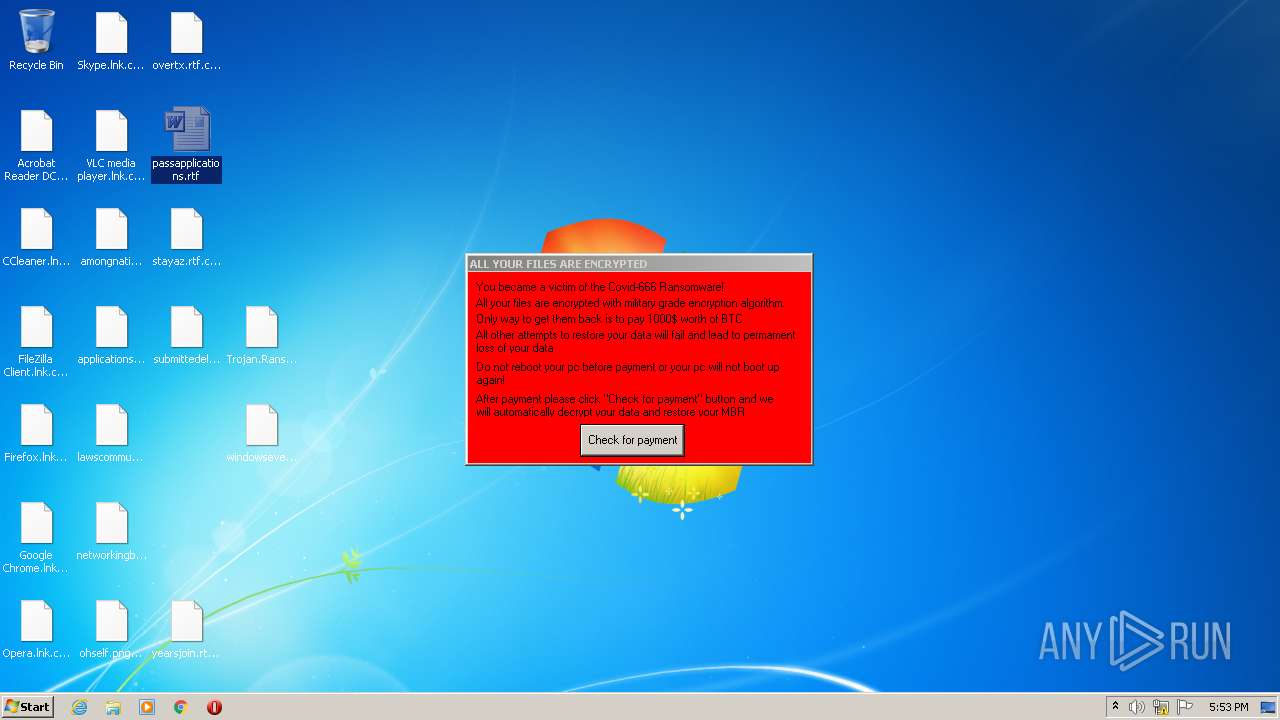
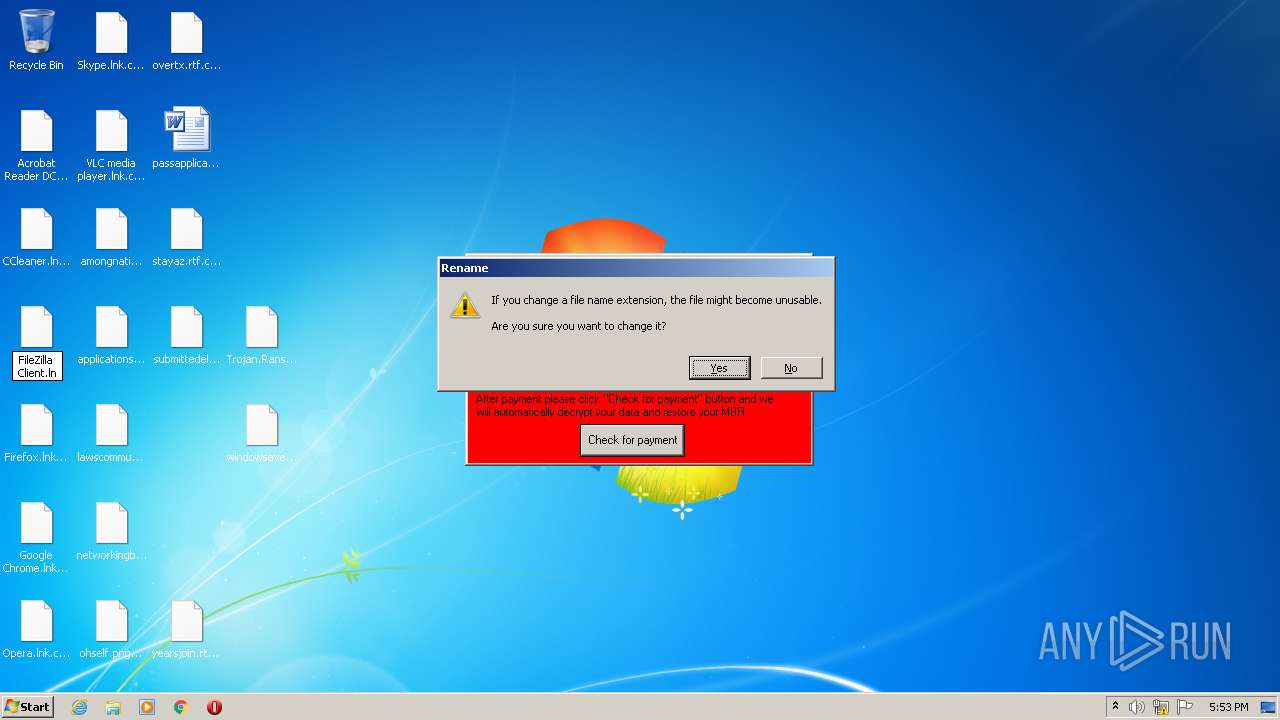
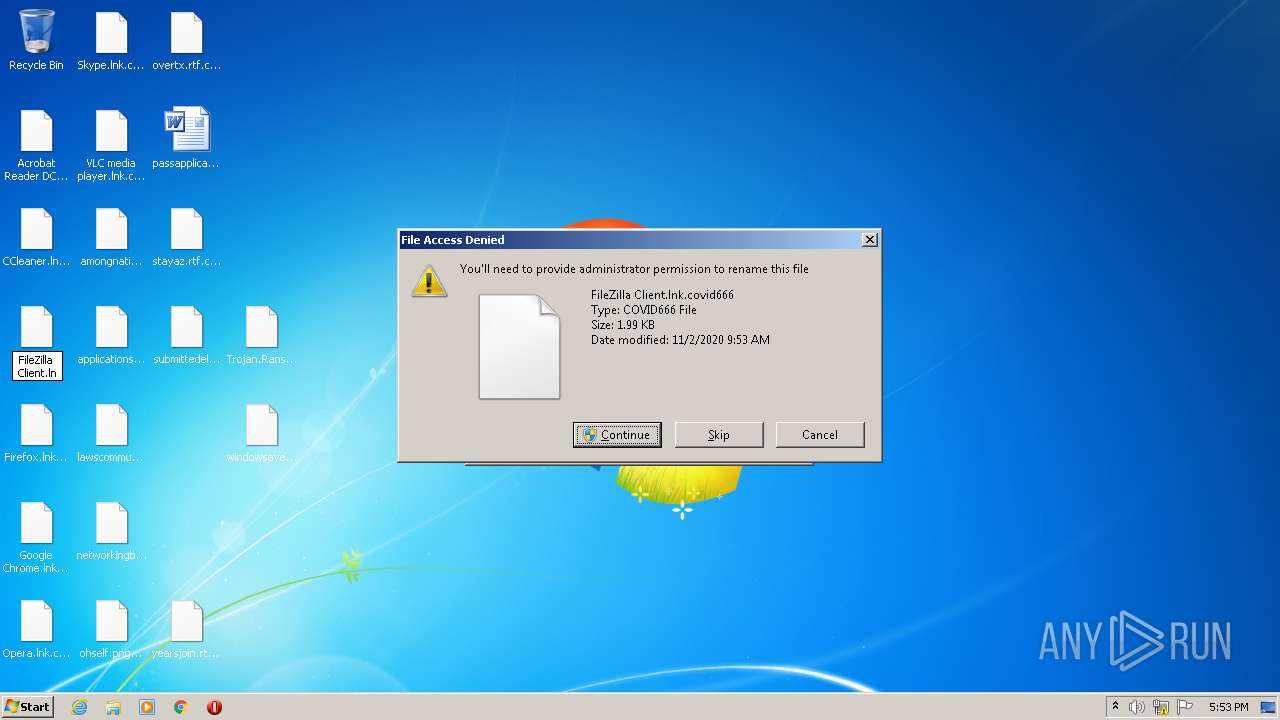
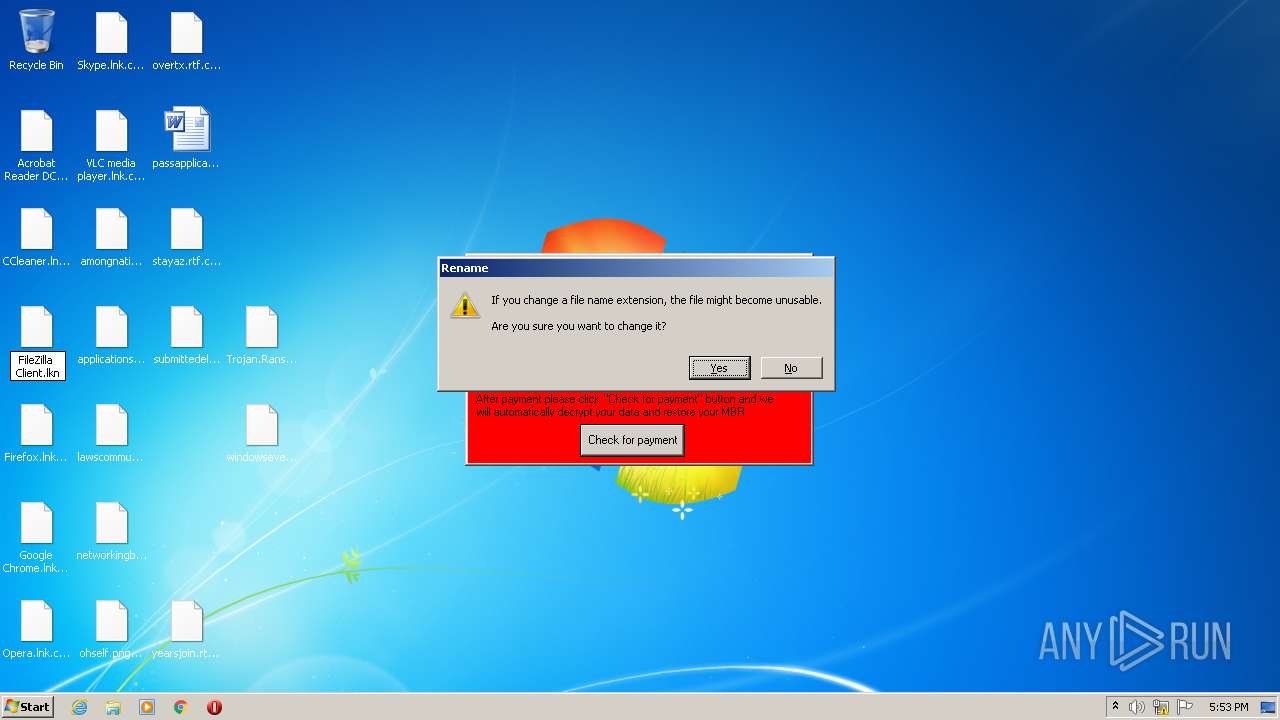
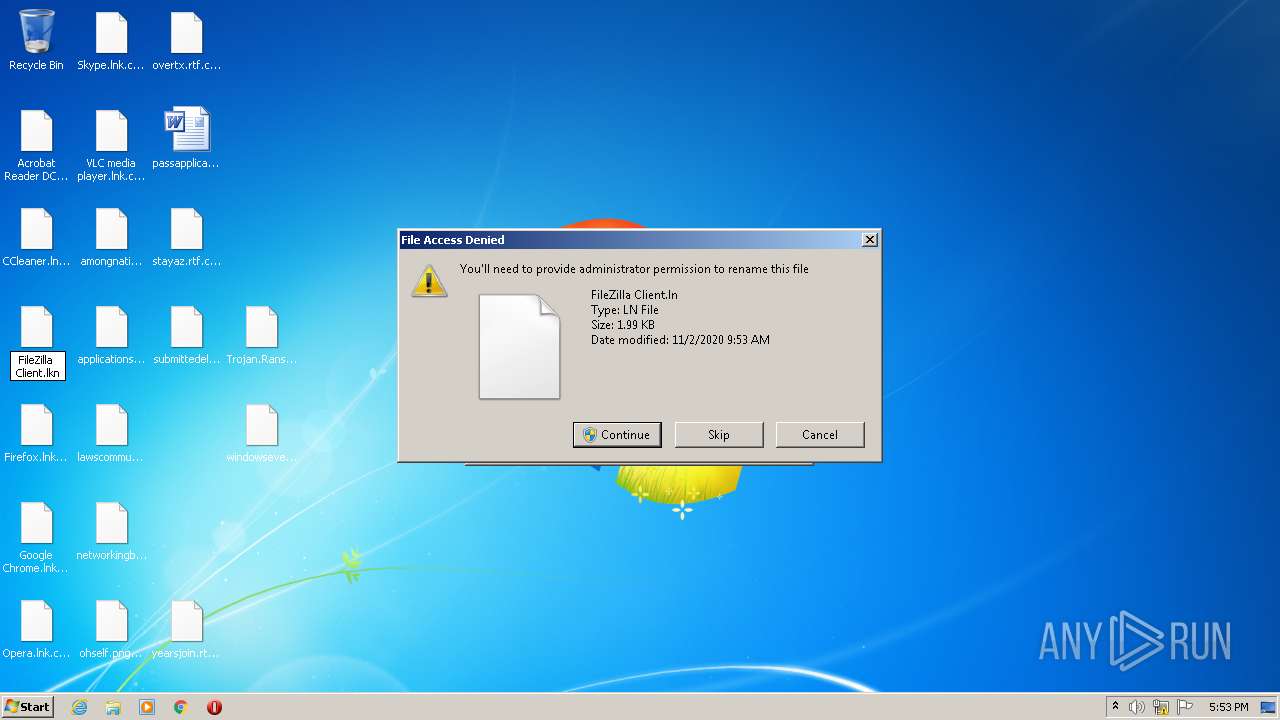
Renames files like Ransomware
- cmd.exe (PID: 3928)
Drops executable file immediately after starts
- cmd.exe (PID: 3928)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
SUSPICIOUS
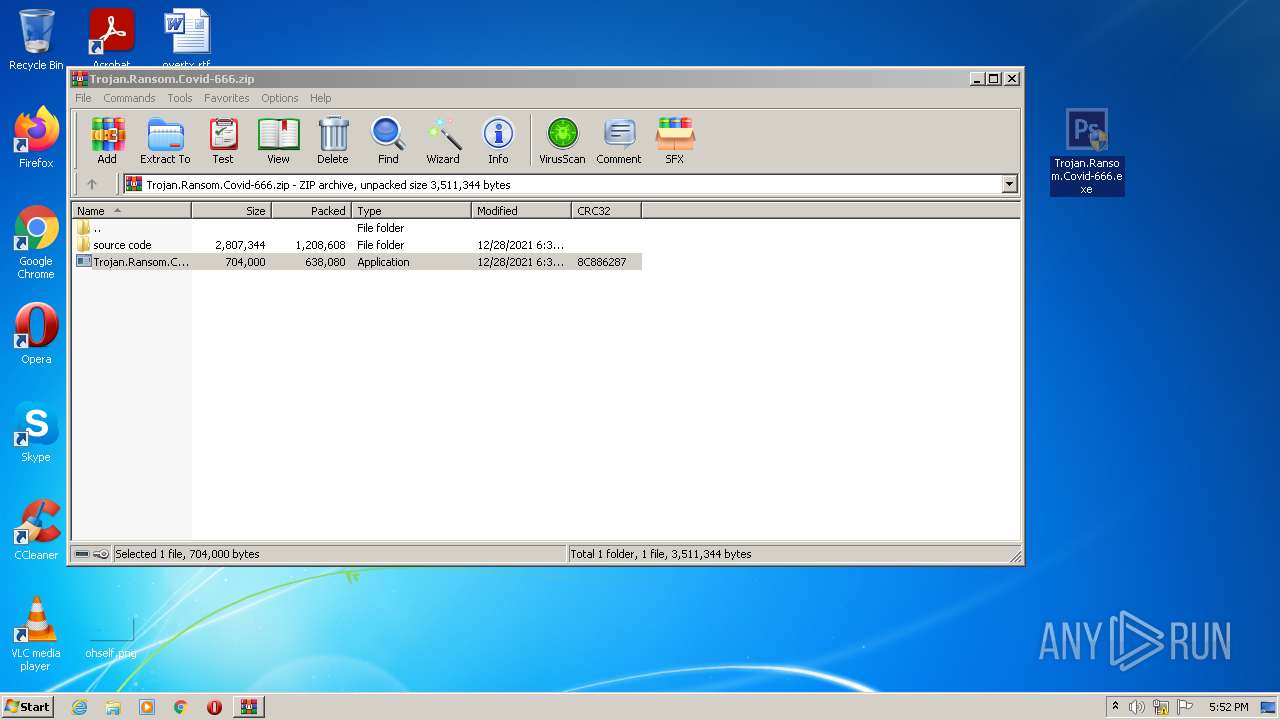
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1816)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
- cmd.exe (PID: 3928)
Checks supported languages
- WinRAR.exe (PID: 1816)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
- mbr.exe (PID: 2460)
- cmd.exe (PID: 3928)
- MainWindow.exe (PID: 3156)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3928)
Reads the computer name
- WinRAR.exe (PID: 1816)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3928)
Changes the desktop background image
- reg.exe (PID: 2544)
- reg.exe (PID: 3516)
Executed via COM
- DllHost.exe (PID: 3144)
Drops a file that was compiled in debug mode
- Trojan.Ransom.Covid-666.exe (PID: 3456)
Starts CMD.EXE for commands execution
- Trojan.Ransom.Covid-666.exe (PID: 3456)
Drops a file with a compile date too recent
- Trojan.Ransom.Covid-666.exe (PID: 3456)
INFO
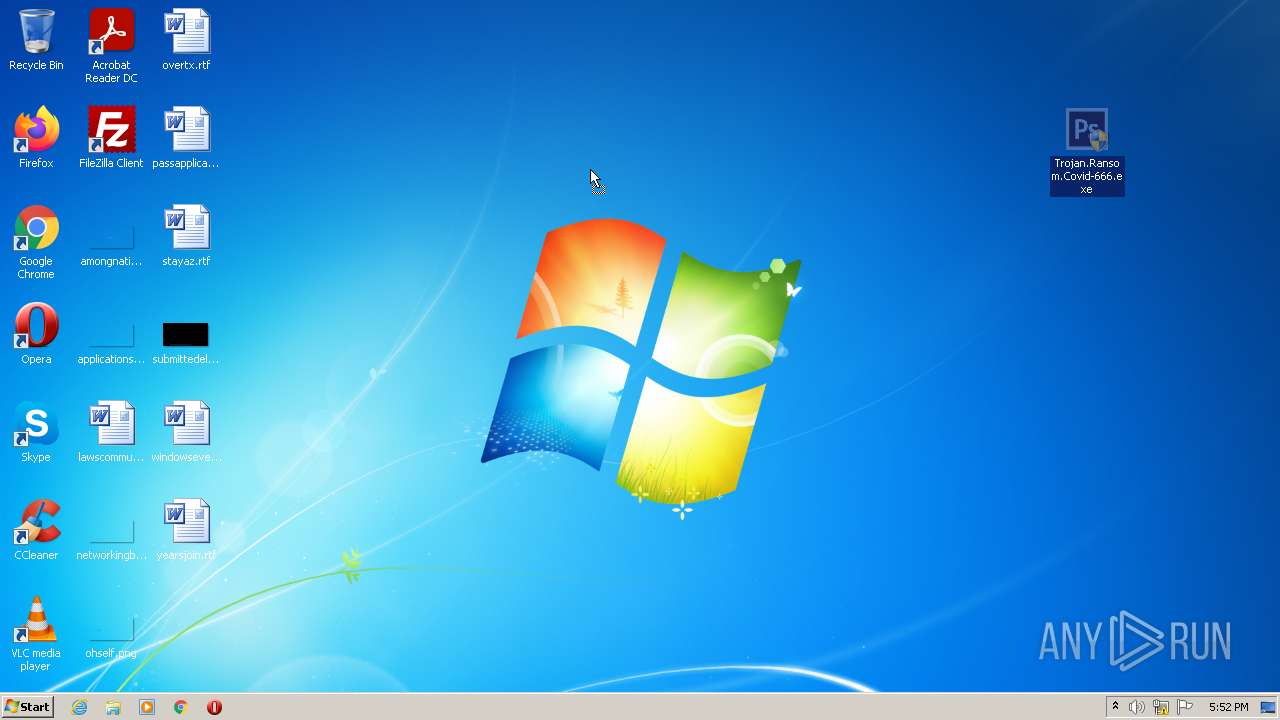
Manual execution by user
- Trojan.Ransom.Covid-666.exe (PID: 2796)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
- WINWORD.EXE (PID: 3428)
Checks supported languages
- reg.exe (PID: 1596)
- reg.exe (PID: 1104)
- reg.exe (PID: 3672)
- reg.exe (PID: 2544)
- reg.exe (PID: 188)
- reg.exe (PID: 3636)
- rundll32.exe (PID: 2208)
- rundll32.exe (PID: 3476)
- rundll32.exe (PID: 1424)
- rundll32.exe (PID: 2752)
- reg.exe (PID: 3244)
- shutdown.exe (PID: 3372)
- rundll32.exe (PID: 2004)
- rundll32.exe (PID: 3924)
- rundll32.exe (PID: 3792)
- rundll32.exe (PID: 2240)
- rundll32.exe (PID: 508)
- rundll32.exe (PID: 2768)
- rundll32.exe (PID: 2984)
- rundll32.exe (PID: 2580)
- reg.exe (PID: 3516)
- rundll32.exe (PID: 3824)
- rundll32.exe (PID: 1792)
- WINWORD.EXE (PID: 3428)
- DllHost.exe (PID: 3144)
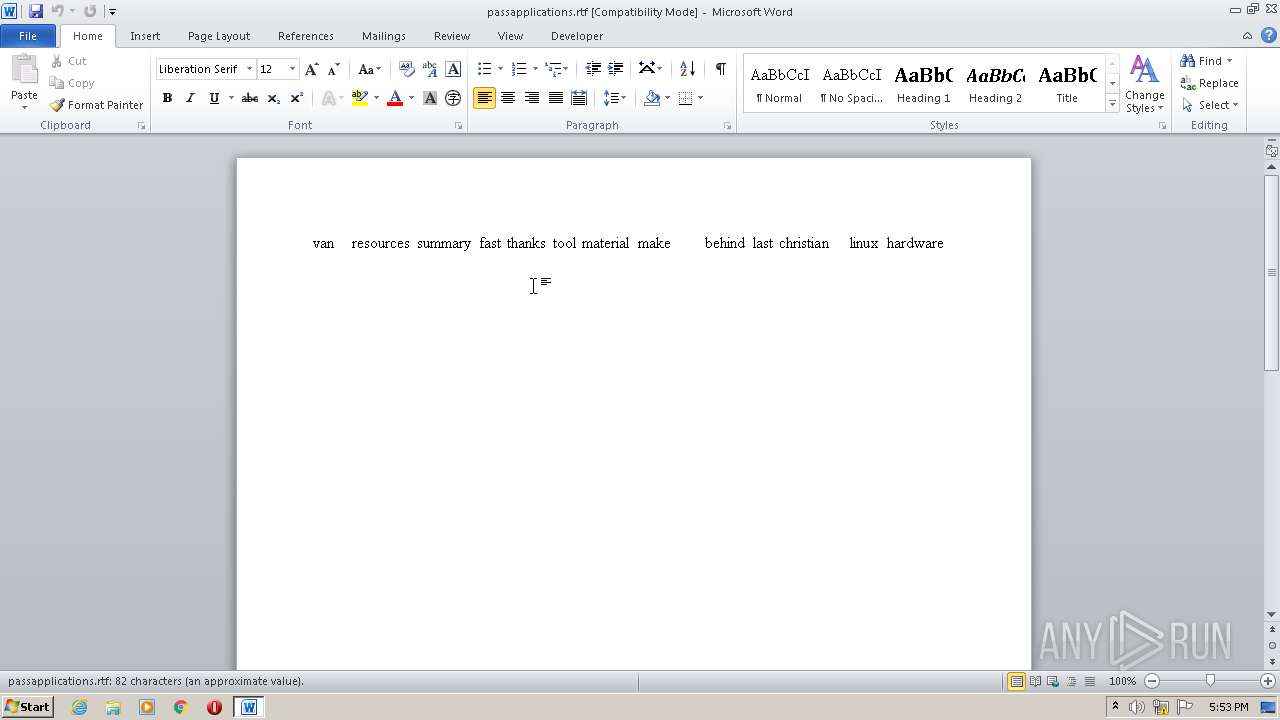
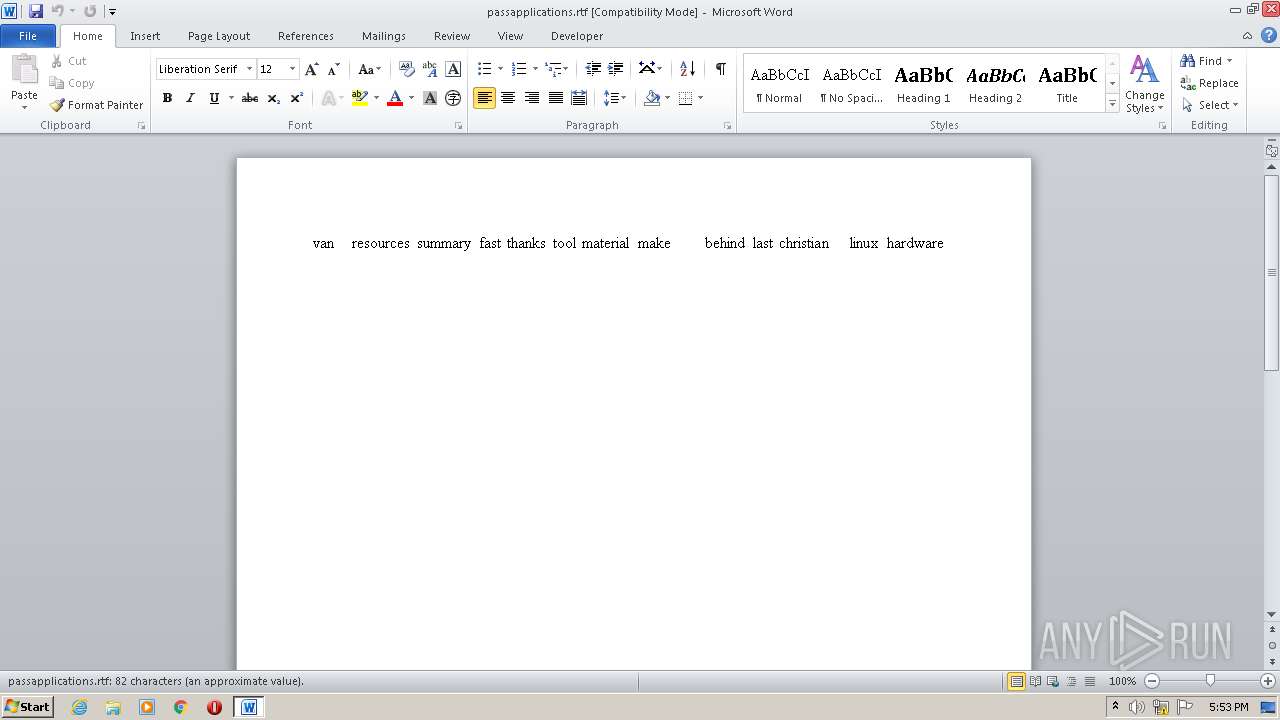
Drops Coronavirus (possible) decoy
- WinRAR.exe (PID: 1816)
- cmd.exe (PID: 3928)
- Trojan.Ransom.Covid-666.exe (PID: 3456)
Reads the computer name
- shutdown.exe (PID: 3372)
- WINWORD.EXE (PID: 3428)
- DllHost.exe (PID: 3144)
Creates files in the user directory
- WINWORD.EXE (PID: 3428)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | source code/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2021:12:28 19:35:07 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 10 |
Total processes
77
Monitored processes
31
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableLockWorkstation /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 508 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System /v HideFastUserSwitching /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.Ransom.Covid-666.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2004 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 041
Read events
4 685
Write events
209
Delete events
147
Modification events
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Trojan.Ransom.Covid-666.zip | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
1
Text files
16
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | cmd.exe | C:\Users\admin\Desktop\applicationsexecutive.png.covid666 | image | |
MD5:— | SHA256:— | |||
| 3928 | cmd.exe | C:\Users\admin\Desktop\ohself.png.covid666 | image | |
MD5:— | SHA256:— | |||
| 3928 | cmd.exe | C:\Users\admin\Desktop\amongnation.png.covid666 | image | |
MD5:— | SHA256:— | |||
| 3928 | cmd.exe | C:\Users\admin\Desktop\stayaz.rtf.covid666 | text | |
MD5:— | SHA256:— | |||
| 3928 | cmd.exe | C:\Users\admin\Desktop\passapplications.rtf.covid666 | text | |
MD5:— | SHA256:— | |||
| 3456 | Trojan.Ransom.Covid-666.exe | C:\Users\admin\AppData\Local\Temp\77CD.tmp\MainWindow.exe | executable | |
MD5:23AB00DEB47223BA73B700EB371FB0FE | SHA256:D42807867BD69D5DB2605E4E6F39E5F70E0CC9DB0CAC9216FD6A9CD8CC324E0D | |||
| 3928 | cmd.exe | C:\note.bmp | image | |
MD5:4A43A8B397043B6EB9C5359CF45DA6F8 | SHA256:3AABD4300D36CAC3E85DEE2274351B0E58C2F19B59B607751127F5AE0C2BC8A1 | |||
| 3456 | Trojan.Ransom.Covid-666.exe | C:\Users\admin\AppData\Local\Temp\77CD.tmp\Covid666.bat | text | |
MD5:5E19B2EEB24514E87AA6039BD012FA6E | SHA256:0CABBE47E3A8799502084B4C691634D16DC3BF317FC17D9D898ED336A476C778 | |||
| 3428 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE665.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3456 | Trojan.Ransom.Covid-666.exe | C:\Users\admin\AppData\Local\Temp\77CD.tmp\mbr.cpp | text | |
MD5:D20EDDECB5625B60D61D80C067537188 | SHA256:45EAA30A90C739FD9FB32D59B29D3E7CD8871431670A3E64D6C34FD53A08F979 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
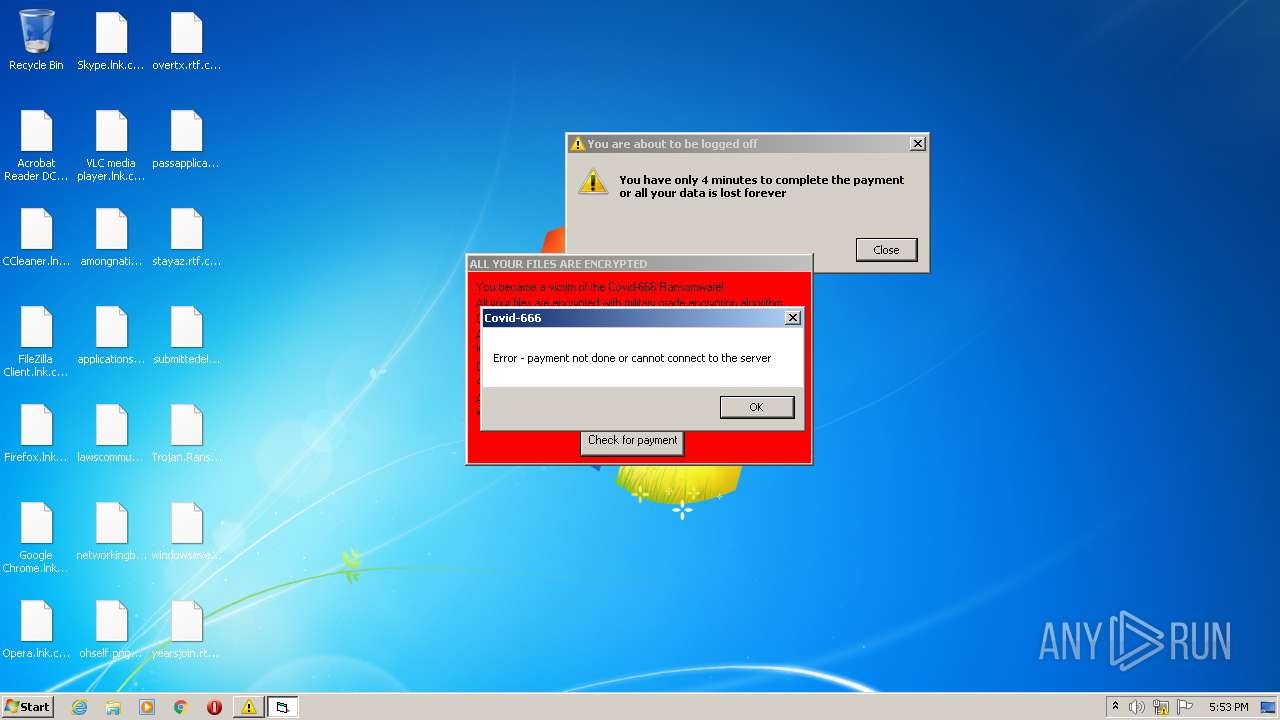
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report