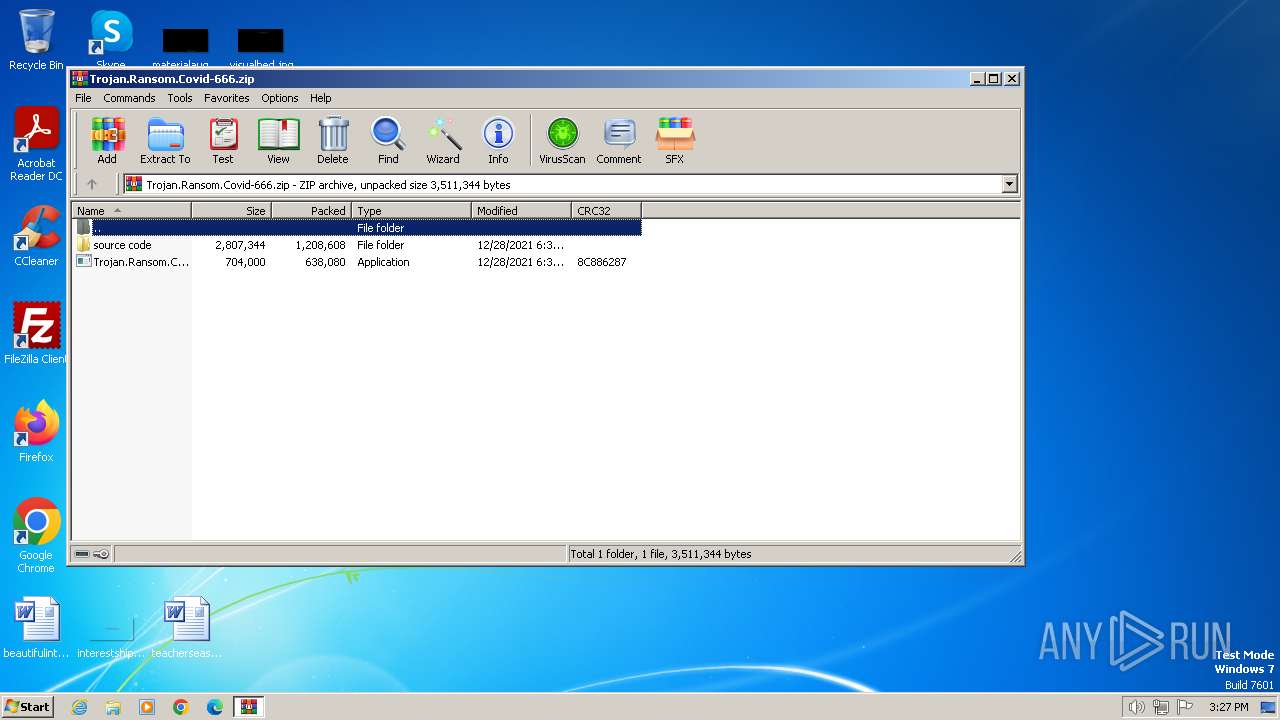
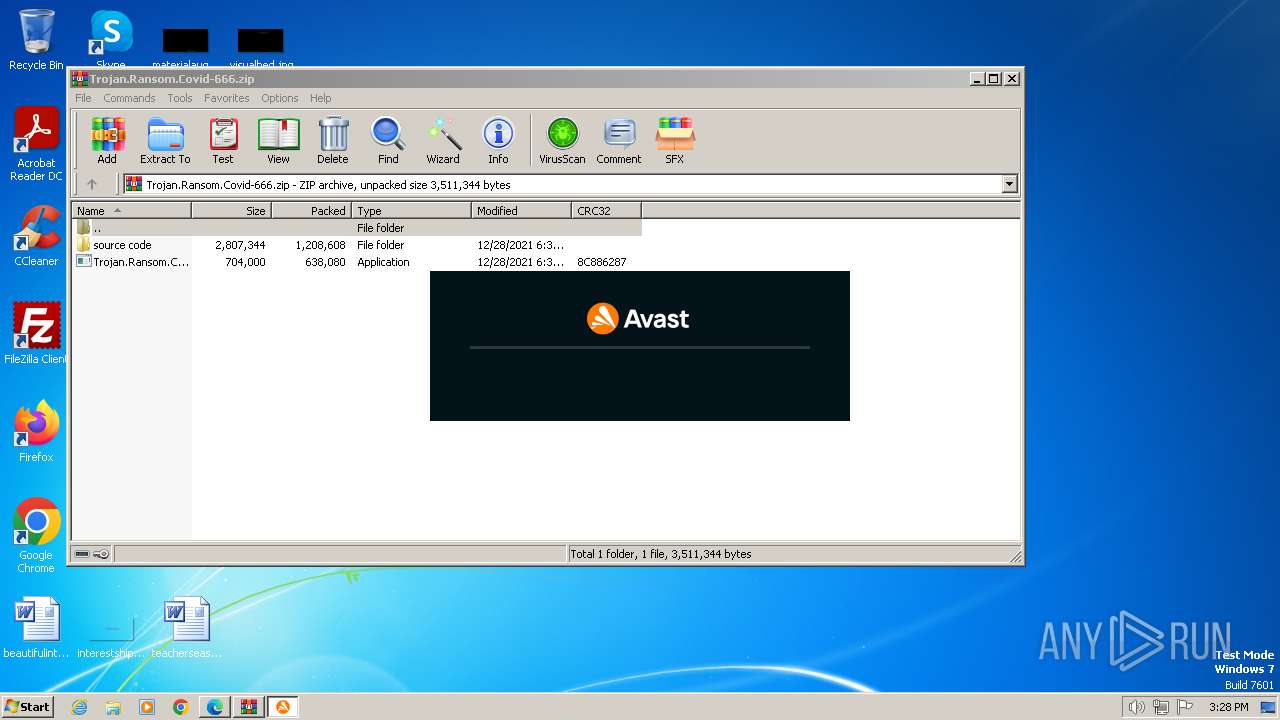
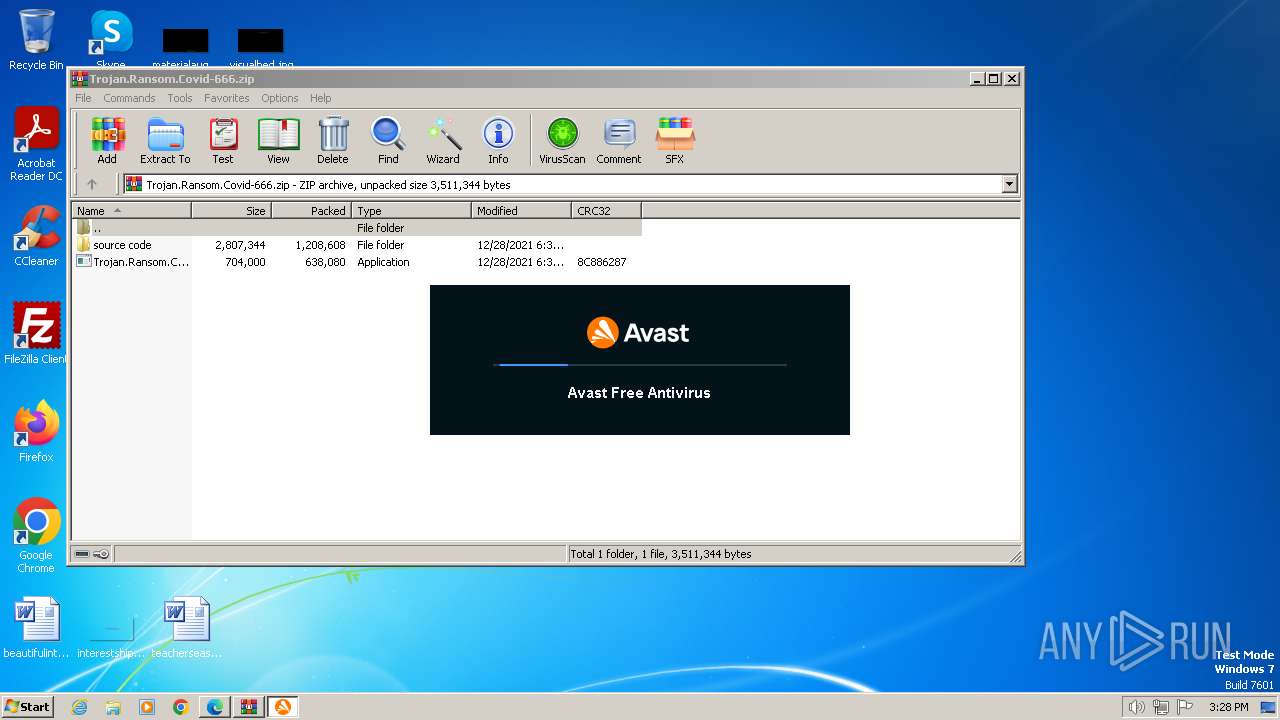
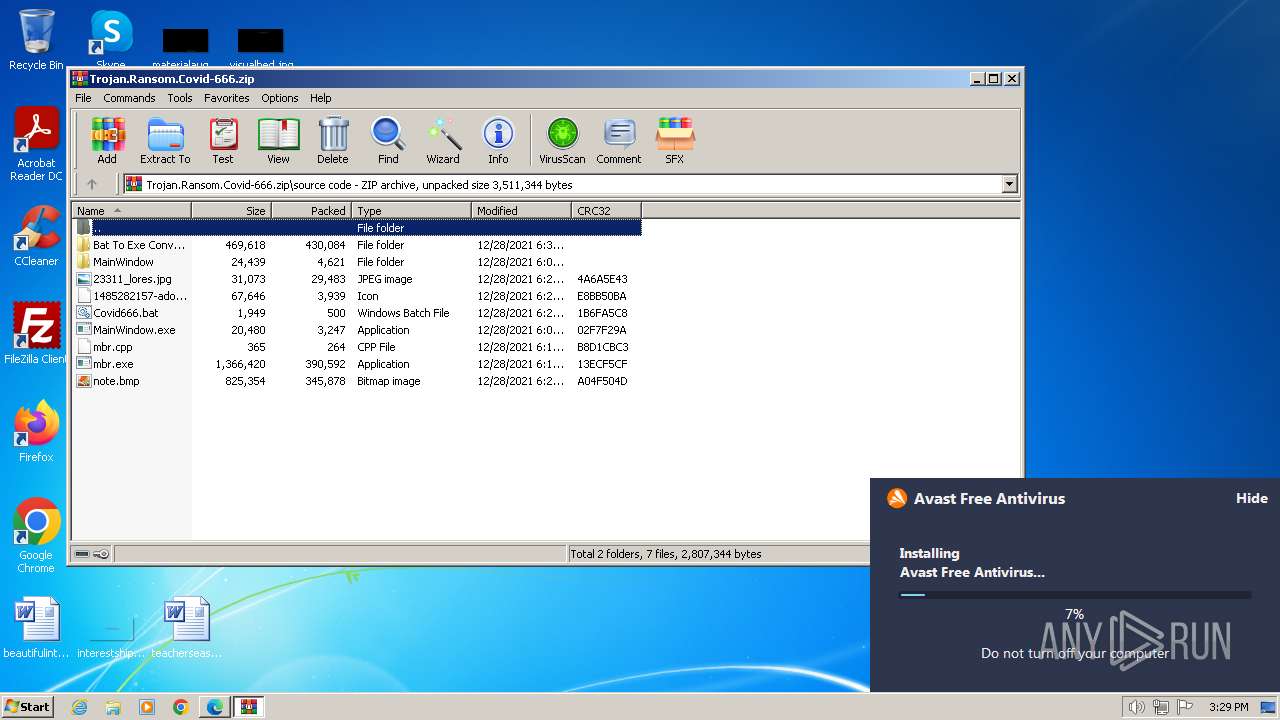
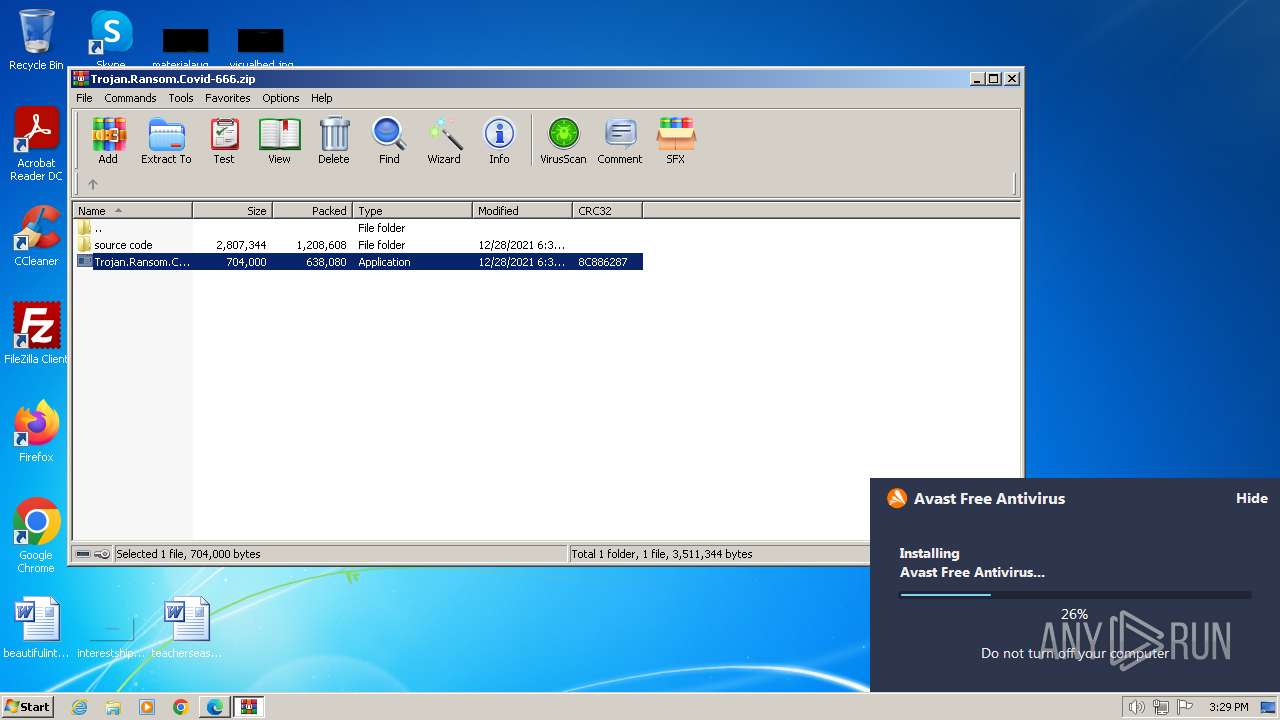
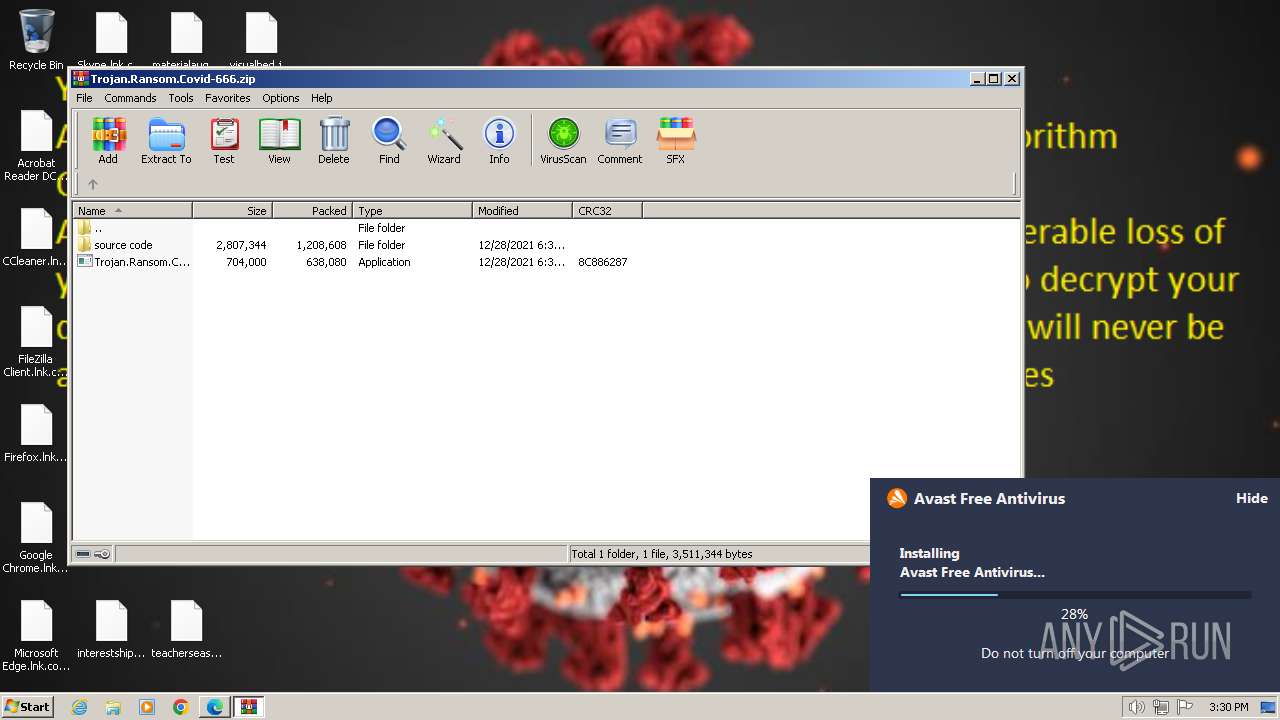
| File name: | Trojan.Ransom.Covid-666.zip |
| Full analysis: | https://app.any.run/tasks/a305fb32-aa6b-4893-acda-c170a13c33e8 |
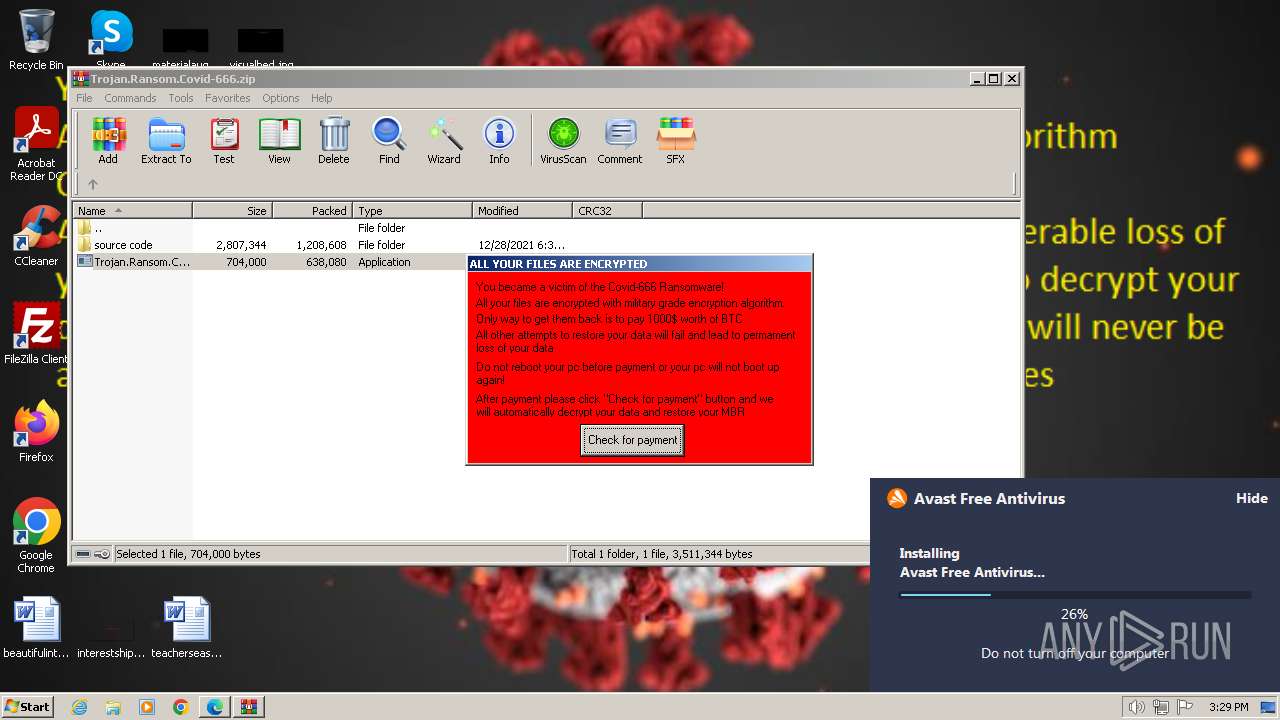
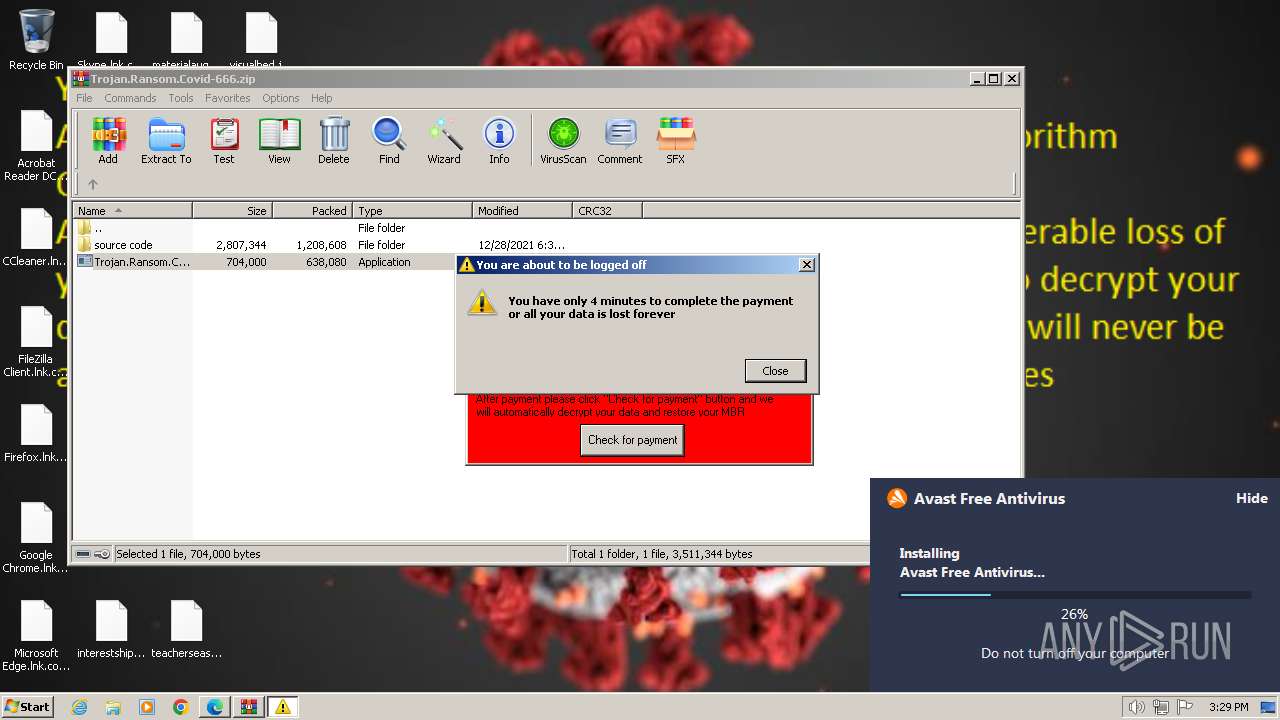
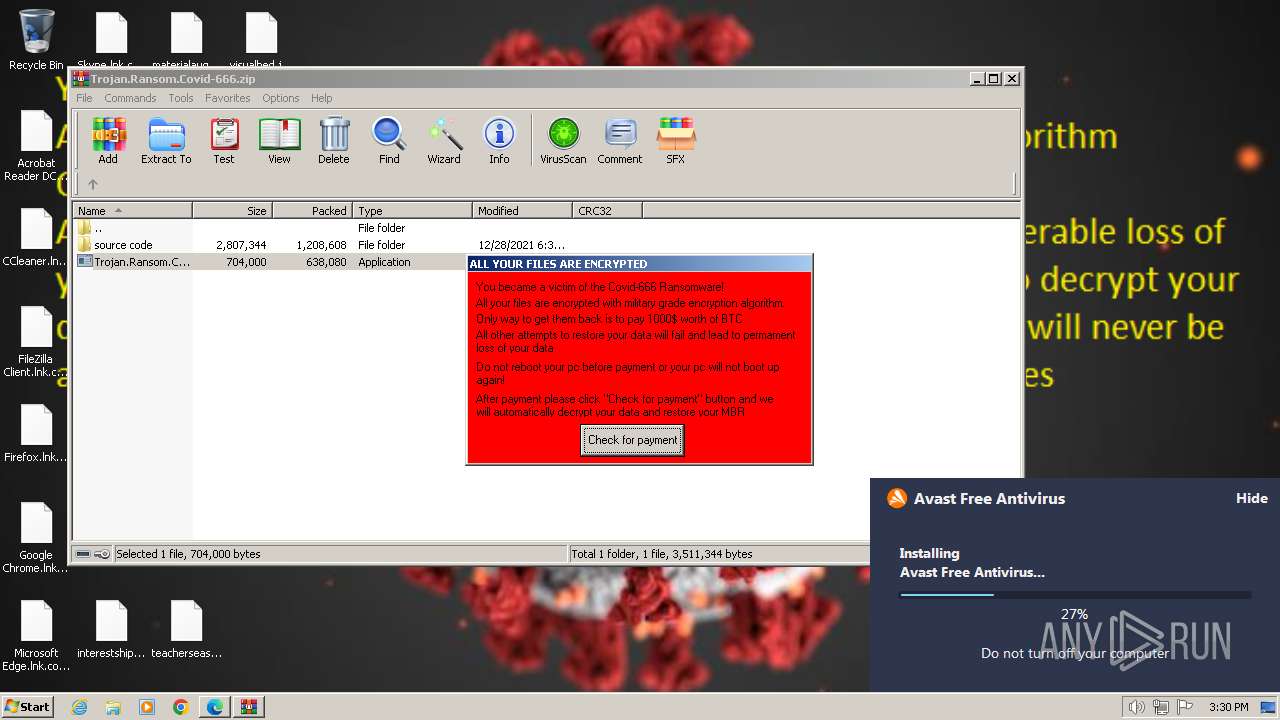
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
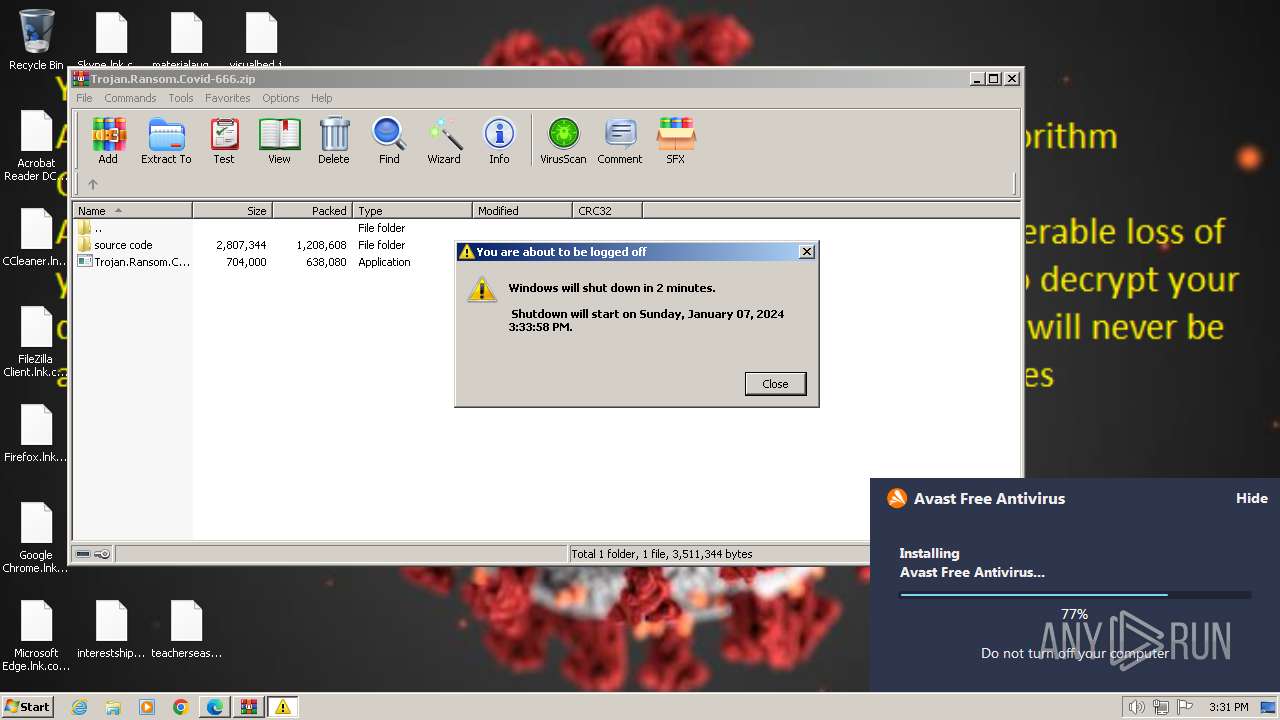
| Analysis date: | January 07, 2024, 15:27:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 6913991E03E8224A3119F595408D3F29 |
| SHA1: | 088EA3A0809E5655232C3ED659EEE097FD5864E7 |
| SHA256: | E7EF23AF9ADEDDD5D43C3E6A736EA4FC3EB31CF6E08609DA01AC2CCC516216FB |
| SSDEEP: | 98304:osNpUCfurixyMeYBz4hKPdmkLmYIWECmSnSurc8t1+4KvwJjXOAQSKHrXWeIxa2W:6W7BiV |
MALICIOUS
Renames files like ransomware
- cmd.exe (PID: 1548)
Creates a writable file in the system directory
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 2124)
- drvinst.exe (PID: 3712)
- SetupInf.exe (PID: 1832)
- AvastSvc.exe (PID: 2956)
Actions looks like stealing of personal data
- engsup.exe (PID: 3052)
- aswToolsSvc.exe (PID: 2176)
- AvastSvc.exe (PID: 2956)
Steals credentials from Web Browsers
- engsup.exe (PID: 3052)
- AvastSvc.exe (PID: 2956)
Disables Windows Defender
- wsc_proxy.exe (PID: 3004)
SUSPICIOUS
Reads settings of System Certificates
- avast_free_antivirus_setup_online.exe (PID: 2436)
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 3700)
- avBugReport.exe (PID: 3924)
- AvEmUpdate.exe (PID: 128)
- instup.exe (PID: 1812)
Reads the Internet Settings
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- Trojan.Ransom.Covid-666.exe (PID: 3236)
Starts CMD.EXE for commands execution
- Trojan.Ransom.Covid-666.exe (PID: 3236)
Executing commands from a ".bat" file
- Trojan.Ransom.Covid-666.exe (PID: 3236)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1548)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 1548)
Changes the desktop background image
- reg.exe (PID: 3344)
- reg.exe (PID: 2744)
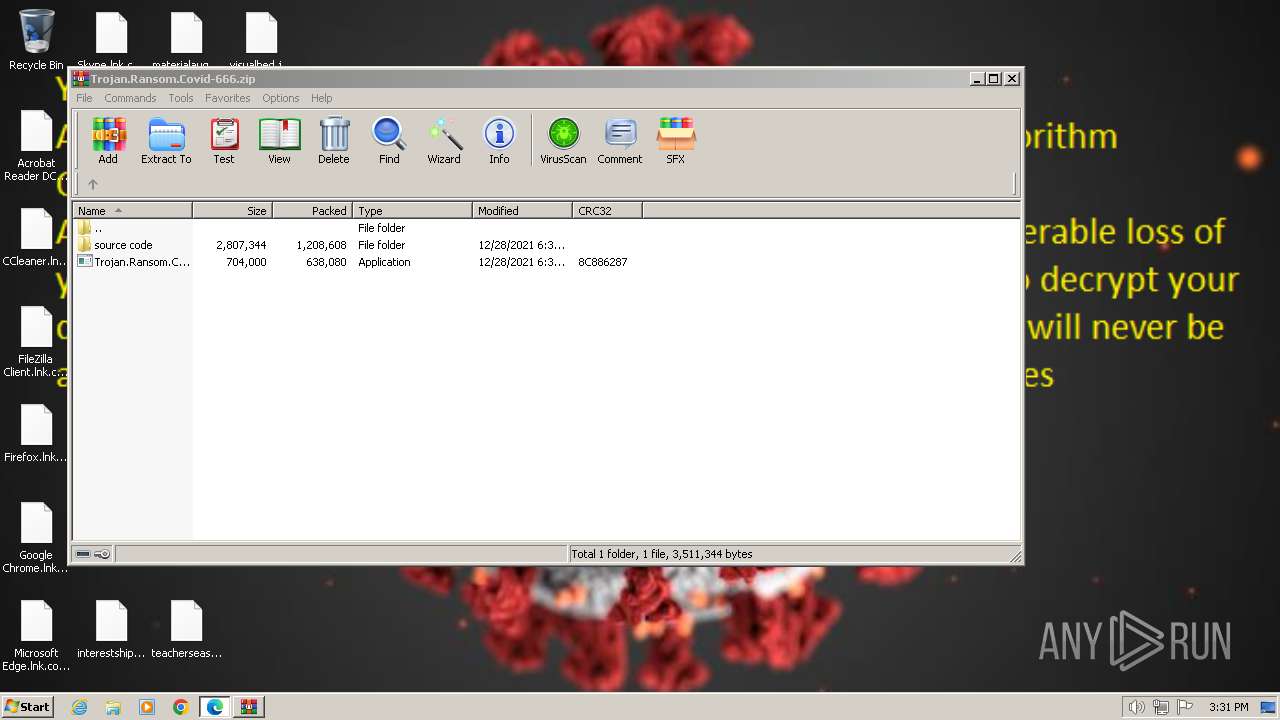
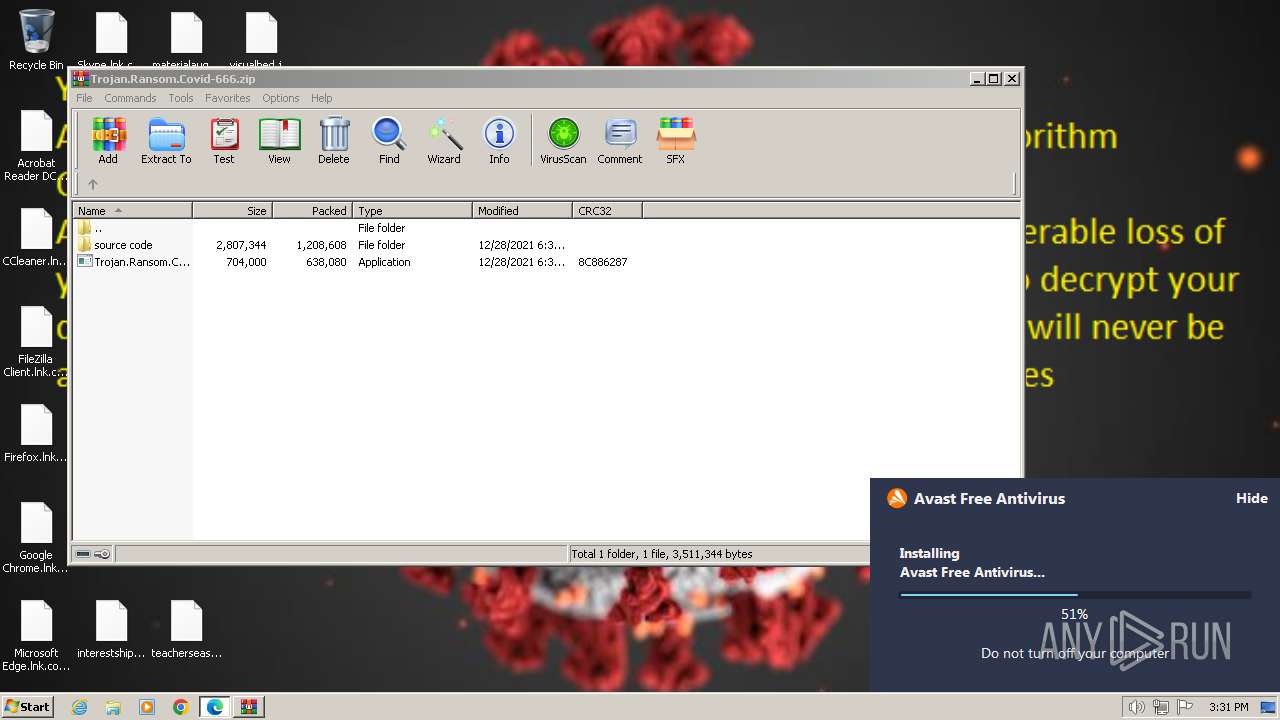
The system shut down or reboot
- cmd.exe (PID: 1548)
Creates files in the driver directory
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 2124)
- drvinst.exe (PID: 3712)
- SetupInf.exe (PID: 1832)
Drops a system driver (possible attempt to evade defenses)
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 2124)
- SetupInf.exe (PID: 1832)
- drvinst.exe (PID: 3712)
The process verifies whether the antivirus software is installed
- SetupInf.exe (PID: 1888)
- SetupInf.exe (PID: 2904)
- SetupInf.exe (PID: 1000)
- SetupInf.exe (PID: 3208)
- AvEmUpdate.exe (PID: 3600)
- AvEmUpdate.exe (PID: 3700)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 128)
- SetupInf.exe (PID: 1216)
- avBugReport.exe (PID: 3924)
- instup.exe (PID: 2156)
- SetupInf.exe (PID: 1832)
- RegSvr.exe (PID: 2576)
- AvastNM.exe (PID: 2624)
- overseer.exe (PID: 3740)
- RegSvr.exe (PID: 3540)
- engsup.exe (PID: 2128)
- wsc_proxy.exe (PID: 1808)
- wsc_proxy.exe (PID: 3004)
- engsup.exe (PID: 3052)
- aswToolsSvc.exe (PID: 2176)
- instup.exe (PID: 3740)
- instup.exe (PID: 4620)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 1812)
Creates or modifies Windows services
- instup.exe (PID: 2156)
Checks Windows Trust Settings
- drvinst.exe (PID: 3712)
- AvastSvc.exe (PID: 2956)
Searches for installed software
- overseer.exe (PID: 3740)
- aswToolsSvc.exe (PID: 2176)
Reads browser cookies
- engsup.exe (PID: 3052)
Adds/modifies Windows certificates
- AvastSvc.exe (PID: 2956)
Checks for Java to be installed
- AvastSvc.exe (PID: 2956)
- aswToolsSvc.exe (PID: 2176)
INFO
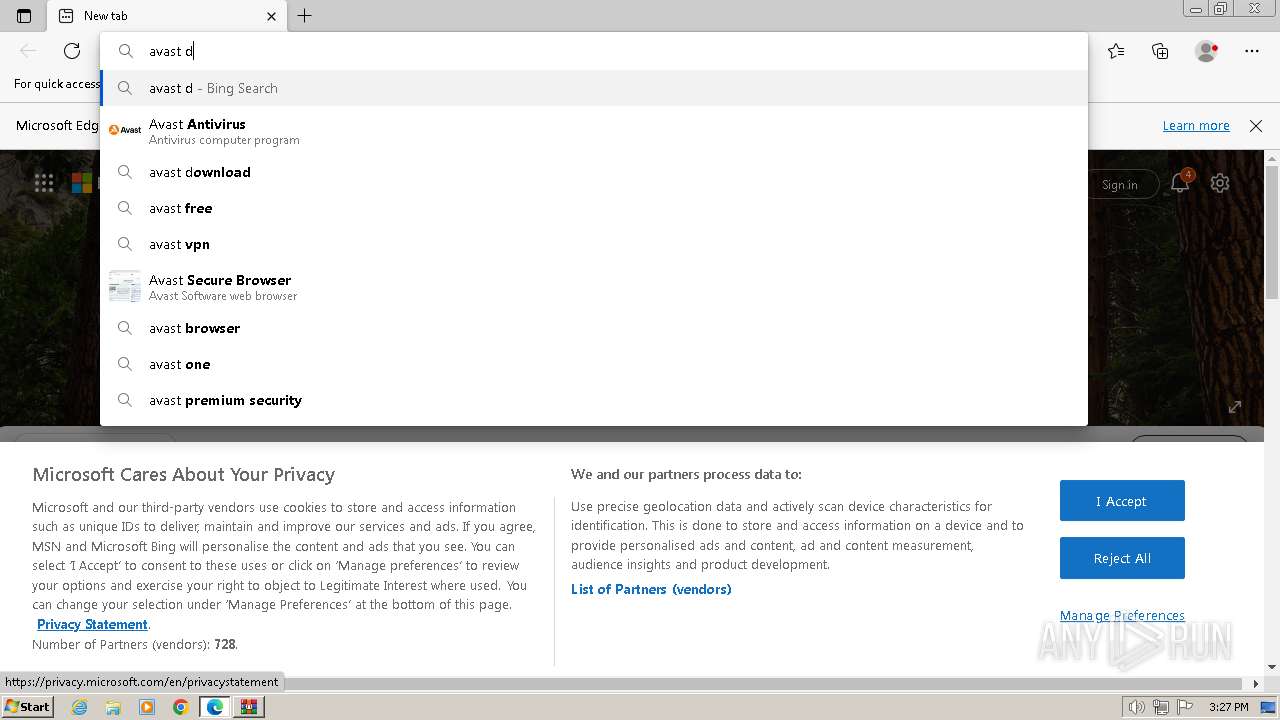
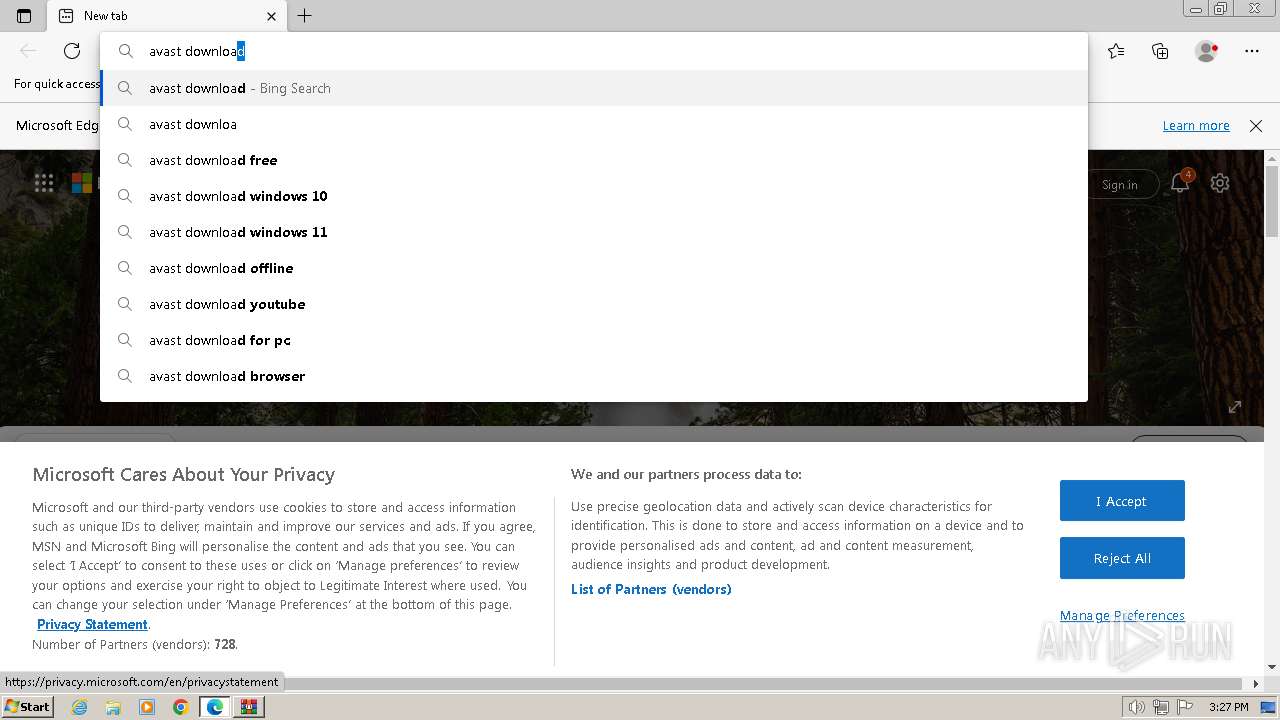
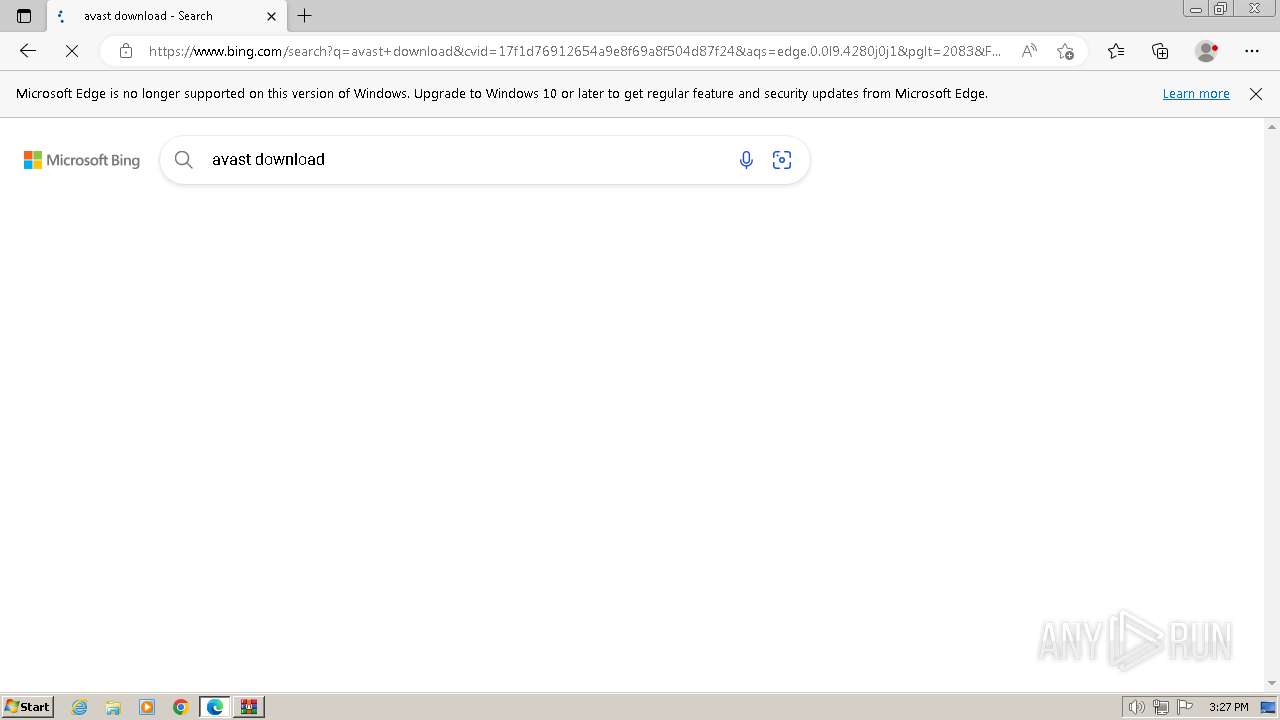
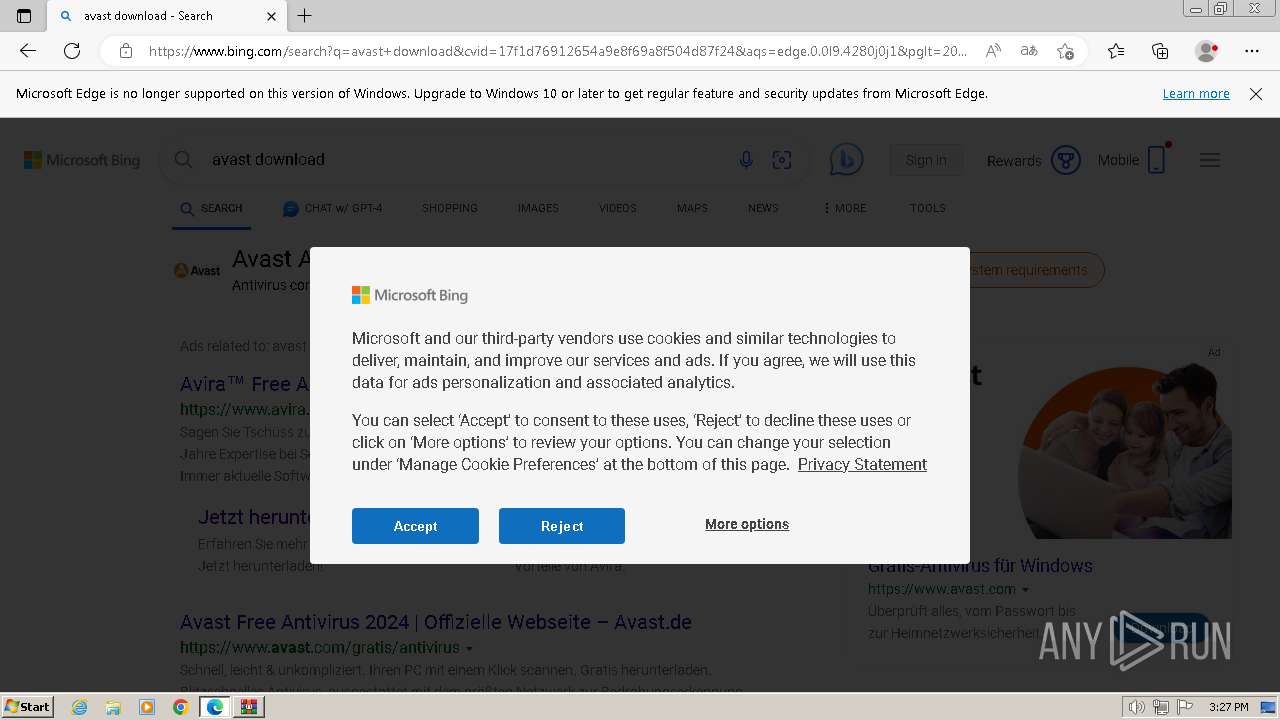
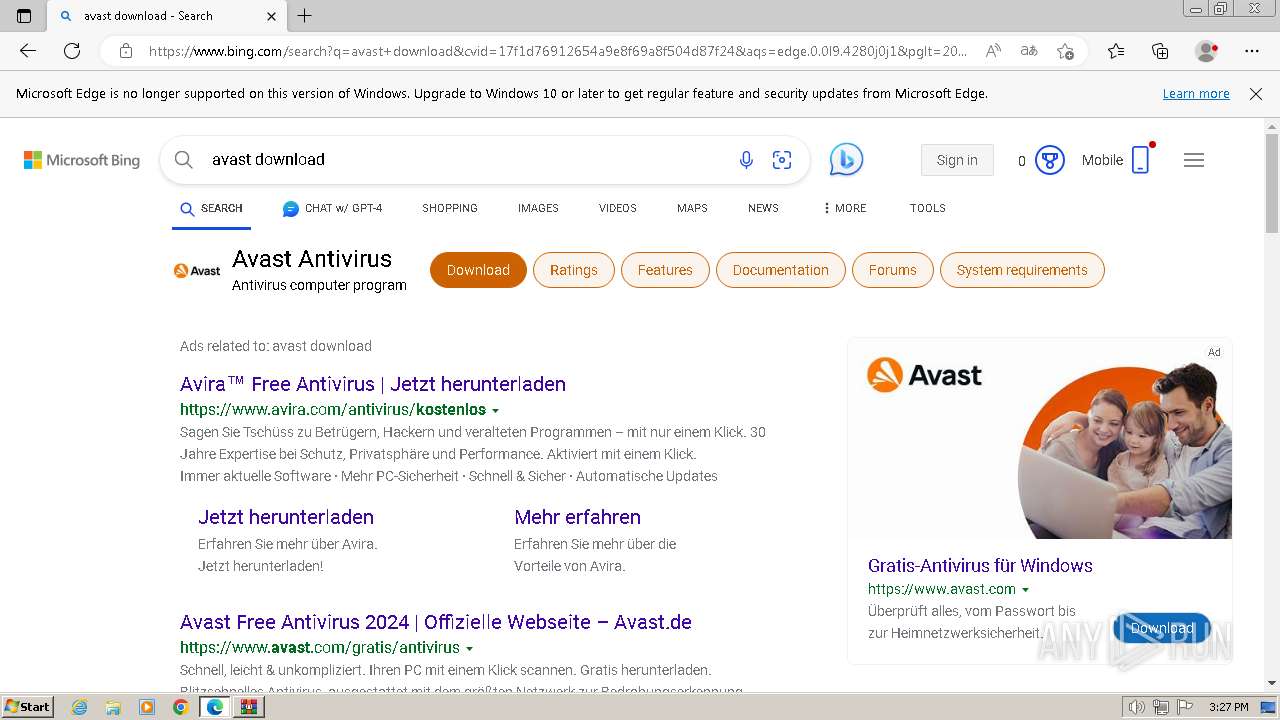
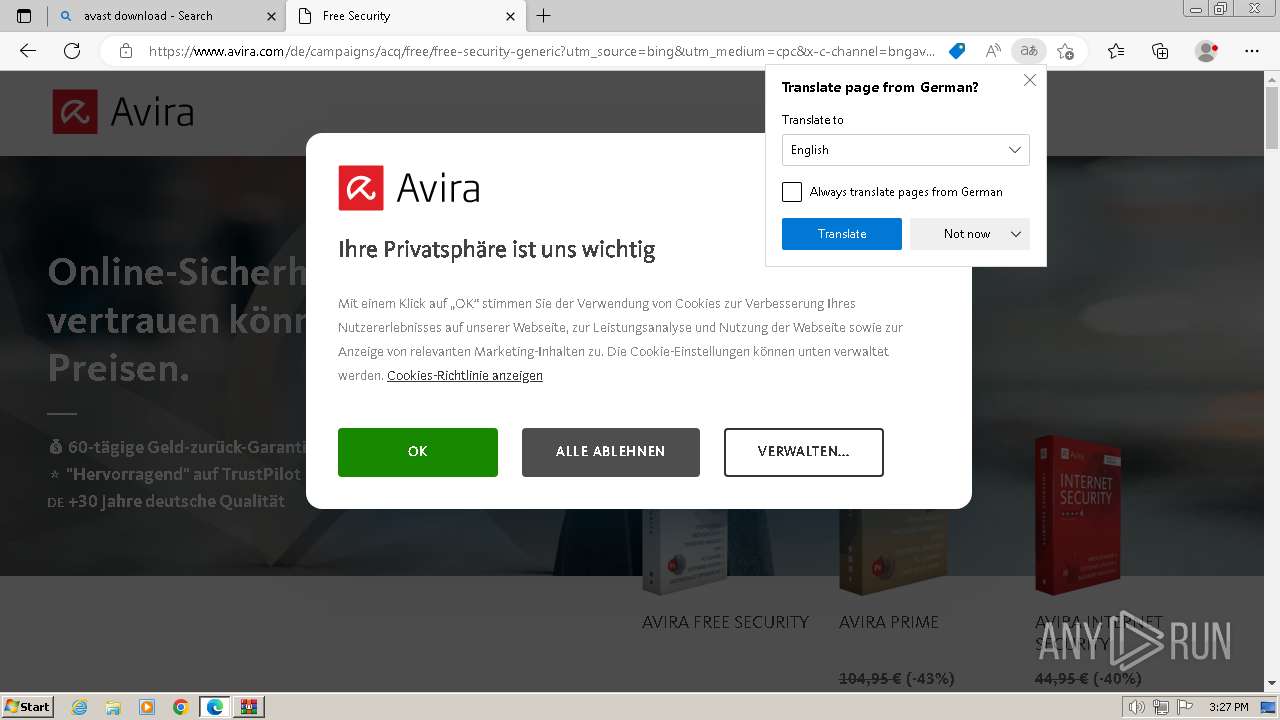
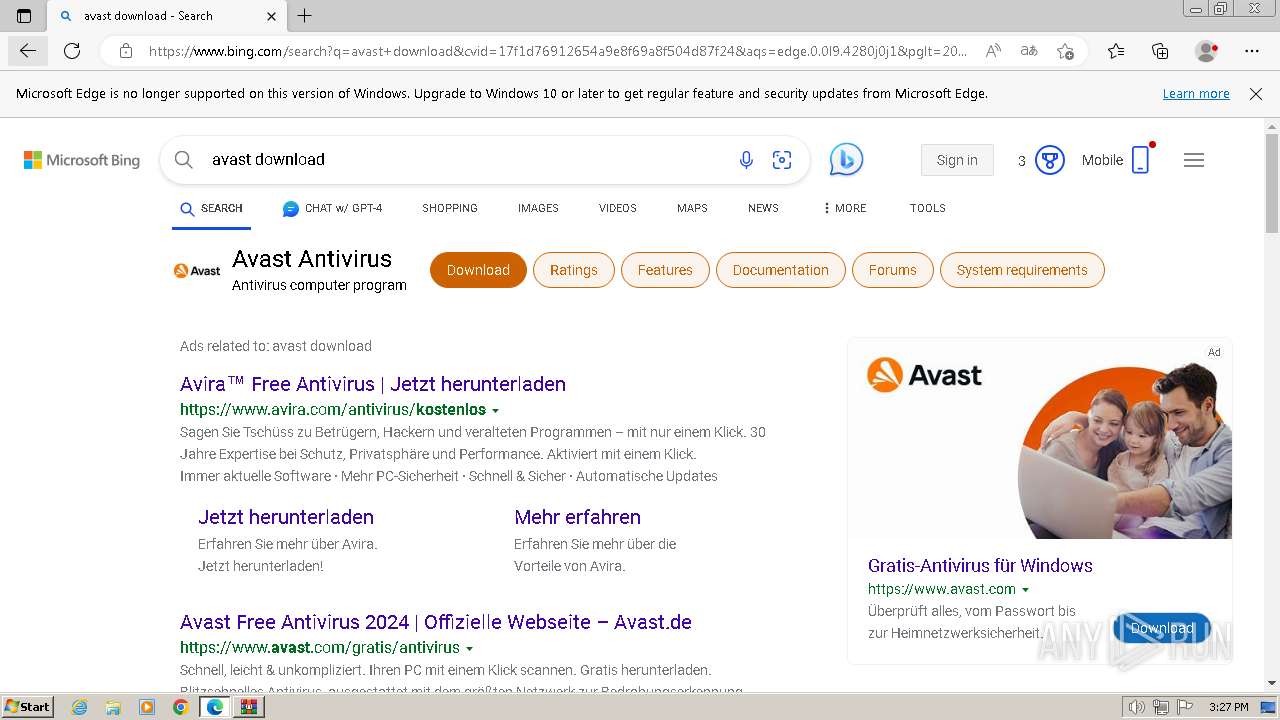
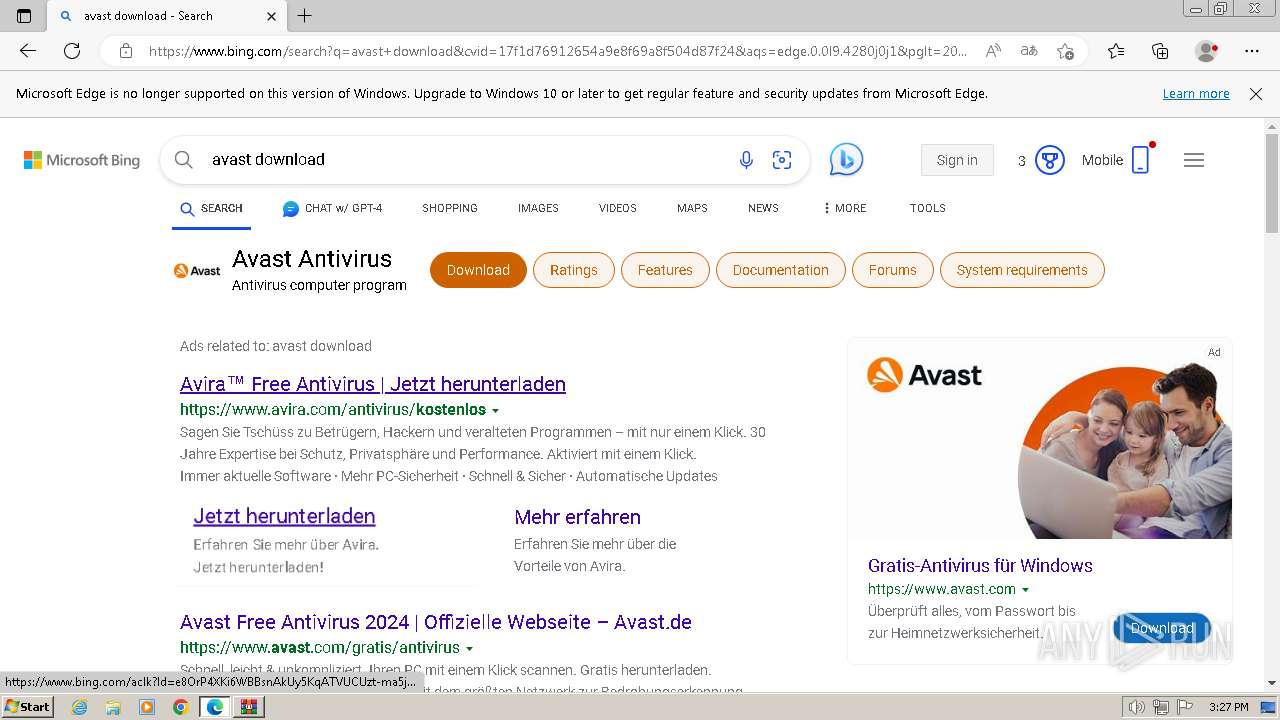
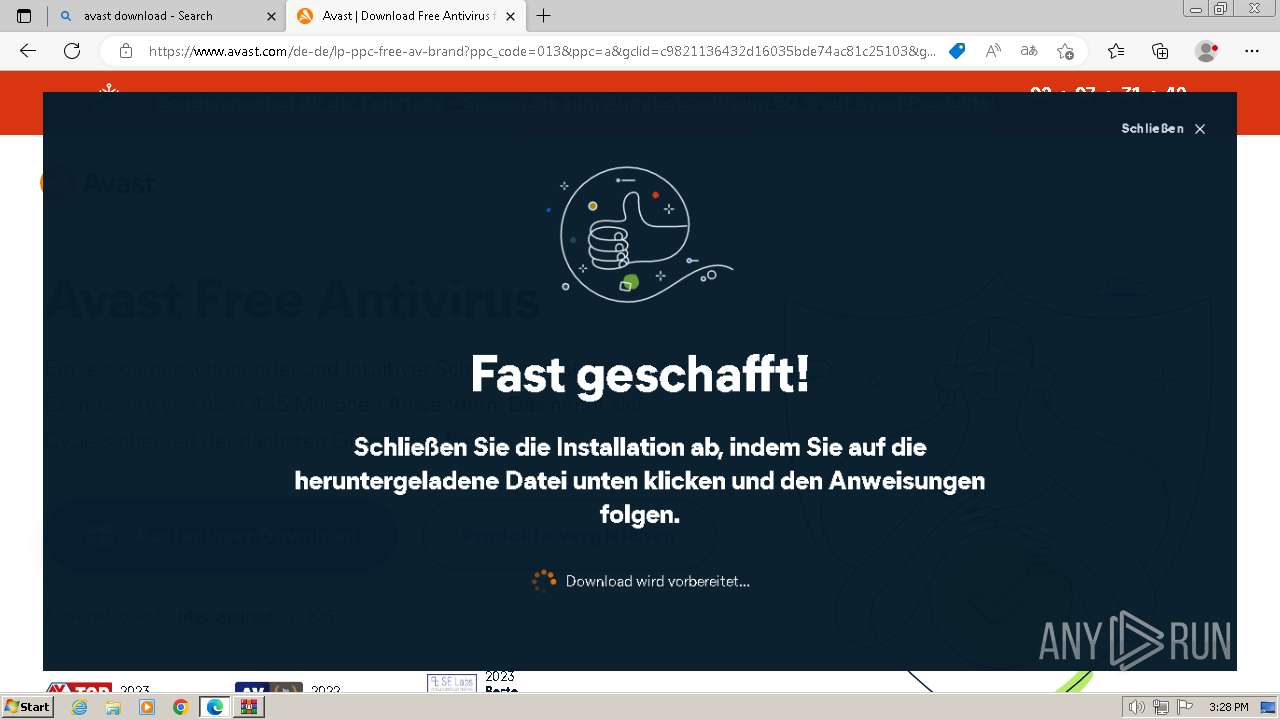
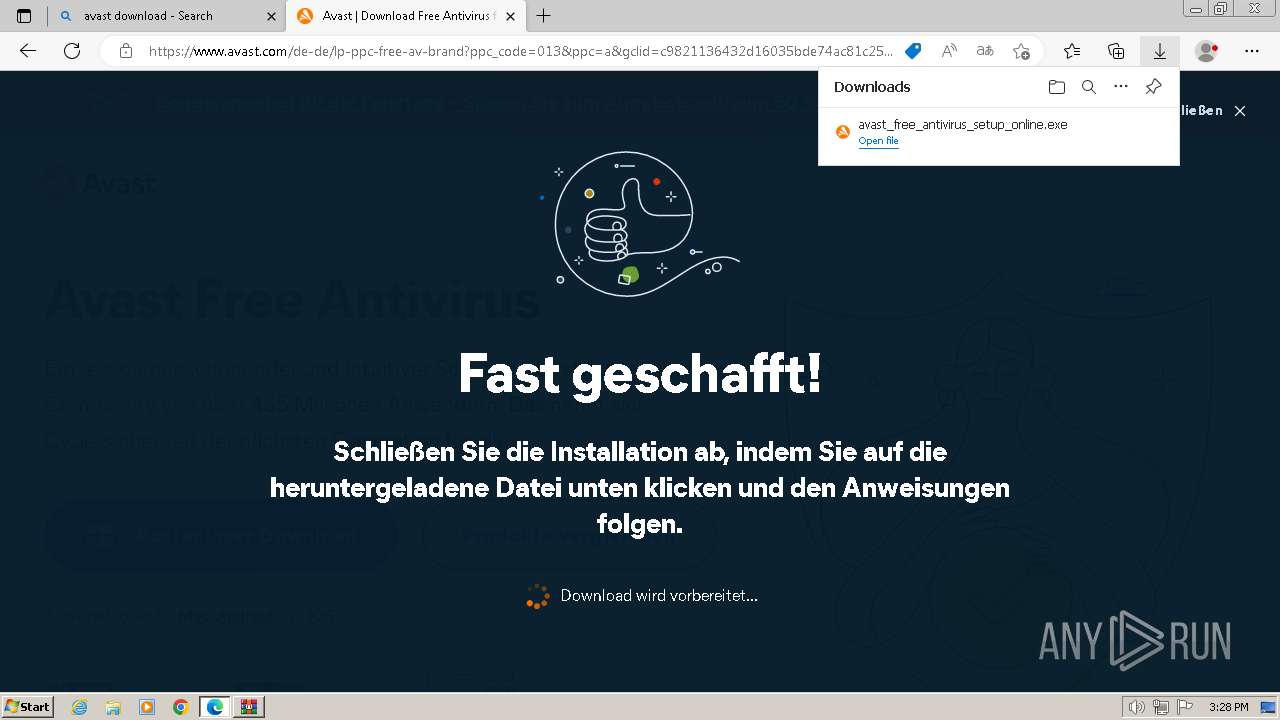
Manual execution by a user
- msedge.exe (PID: 1432)
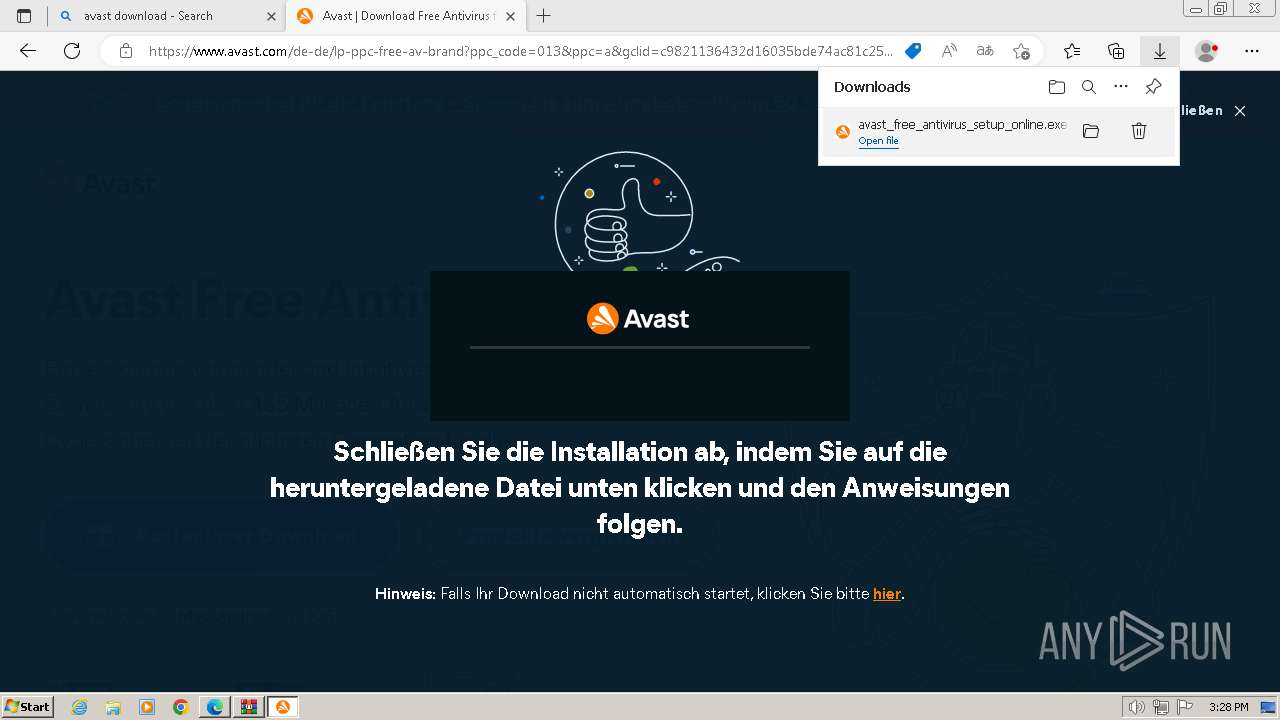
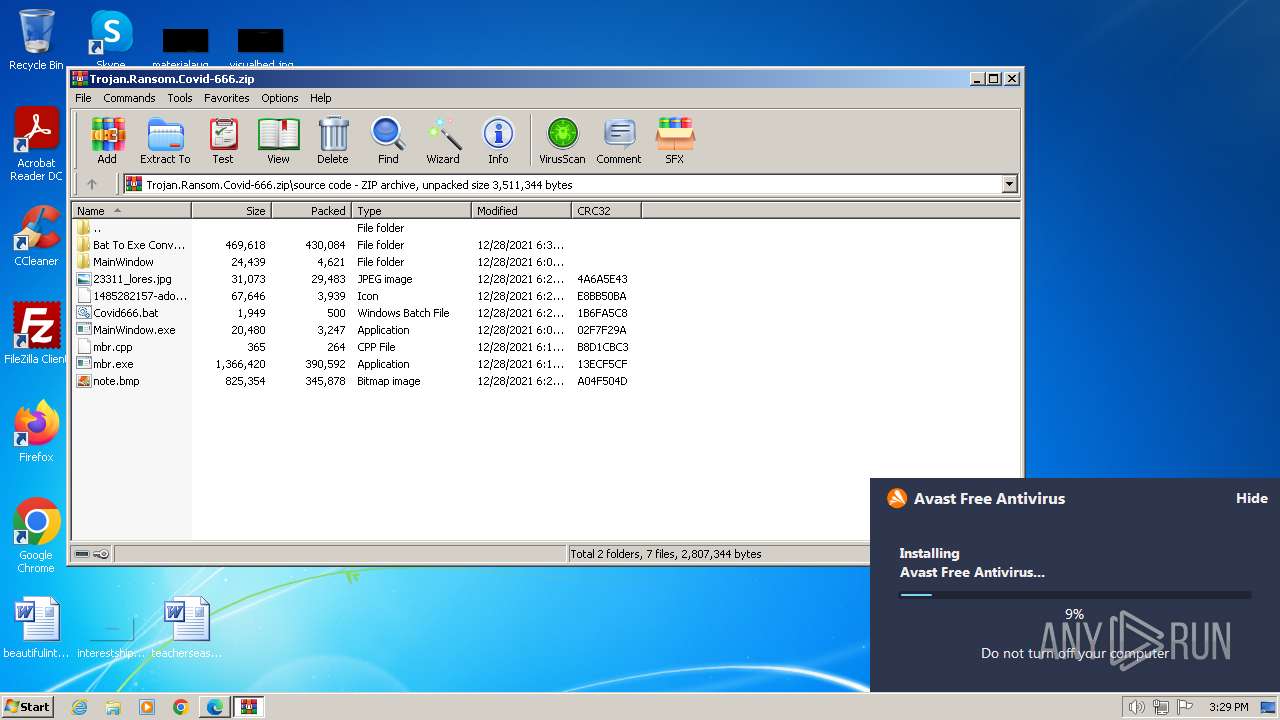
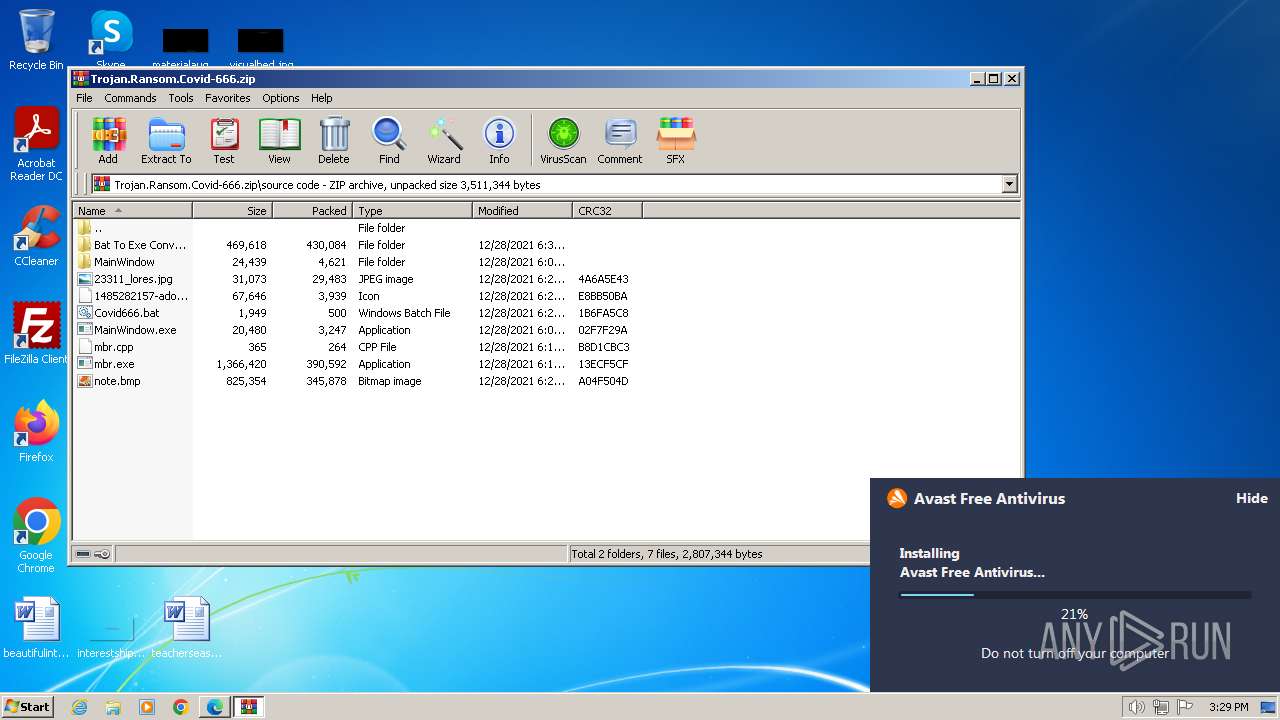
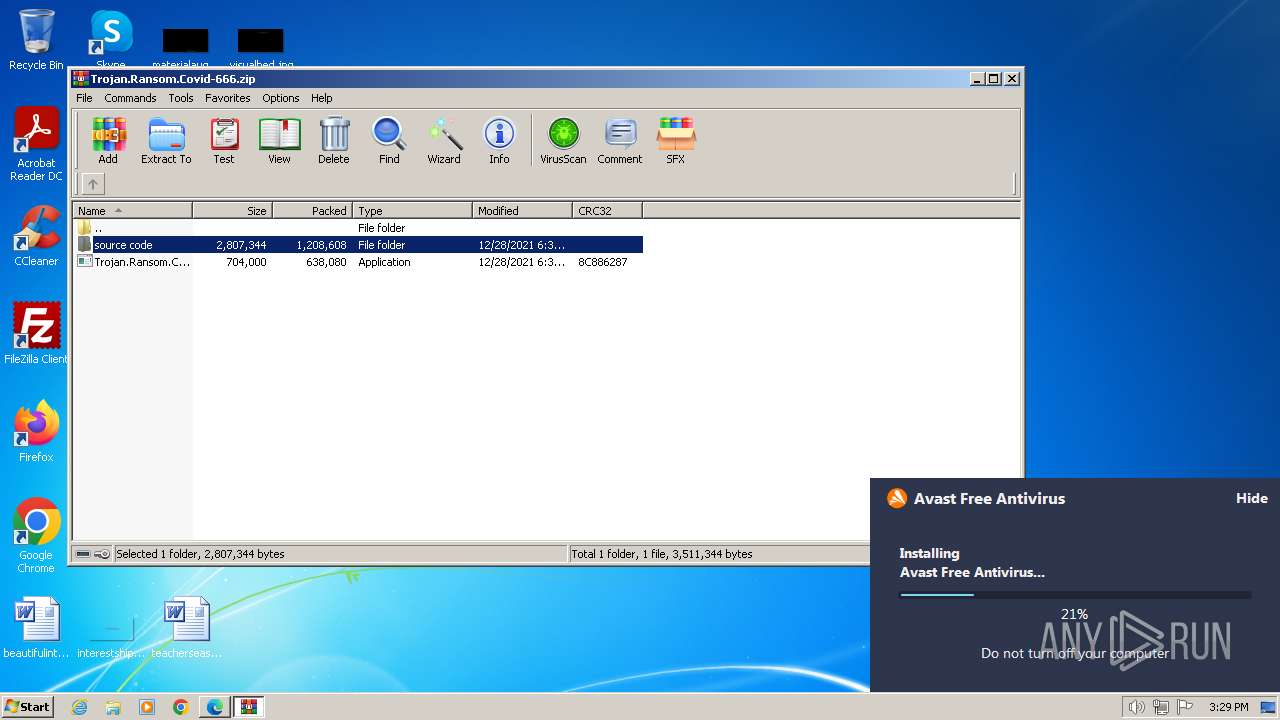
Drops the executable file immediately after the start
- msedge.exe (PID: 1432)
- msedge.exe (PID: 584)
- WinRAR.exe (PID: 120)
- avast_free_antivirus_setup_online.exe (PID: 2436)
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- aswOfferTool.exe (PID: 1232)
- aswOfferTool.exe (PID: 1072)
- aswOfferTool.exe (PID: 3636)
- Trojan.Ransom.Covid-666.exe (PID: 3236)
- AvEmUpdate.exe (PID: 2124)
- SetupInf.exe (PID: 1832)
- drvinst.exe (PID: 3712)
- instup.exe (PID: 2156)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 1812)
The process uses the downloaded file
- msedge.exe (PID: 3840)
- msedge.exe (PID: 1432)
Checks supported languages
- avast_free_antivirus_setup_online.exe (PID: 2436)
- avast_free_antivirus_setup_online.exe (PID: 1808)
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- aswOfferTool.exe (PID: 1484)
- aswOfferTool.exe (PID: 1072)
- aswOfferTool.exe (PID: 3636)
- aswOfferTool.exe (PID: 1232)
- sbr.exe (PID: 3296)
- aswOfferTool.exe (PID: 880)
- MainWindow.exe (PID: 3288)
- Trojan.Ransom.Covid-666.exe (PID: 3236)
- mbr.exe (PID: 3712)
- MainWindow.exe (PID: 2892)
- SetupInf.exe (PID: 1888)
- SetupInf.exe (PID: 2904)
- SetupInf.exe (PID: 1000)
- SetupInf.exe (PID: 3208)
- AvEmUpdate.exe (PID: 3600)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 128)
- AvEmUpdate.exe (PID: 3700)
- avBugReport.exe (PID: 3924)
- SetupInf.exe (PID: 1216)
- SetupInf.exe (PID: 1832)
- drvinst.exe (PID: 3712)
- RegSvr.exe (PID: 3540)
- RegSvr.exe (PID: 2576)
- AvastNM.exe (PID: 2624)
- overseer.exe (PID: 3740)
- engsup.exe (PID: 2128)
- wsc_proxy.exe (PID: 1808)
- wsc_proxy.exe (PID: 3004)
- aswToolsSvc.exe (PID: 2176)
- engsup.exe (PID: 3052)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 3740)
- instup.exe (PID: 1812)
- keytool.exe (PID: 4552)
- keytool.exe (PID: 4452)
- instup.exe (PID: 4620)
Application launched itself
- msedge.exe (PID: 1432)
- AvEmUpdate.exe (PID: 2124)
Reads the machine GUID from the registry
- avast_free_antivirus_setup_online.exe (PID: 2436)
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- SetupInf.exe (PID: 1888)
- SetupInf.exe (PID: 2904)
- SetupInf.exe (PID: 1000)
- SetupInf.exe (PID: 3208)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 3700)
- avBugReport.exe (PID: 3924)
- SetupInf.exe (PID: 1216)
- AvEmUpdate.exe (PID: 128)
- SetupInf.exe (PID: 1832)
- drvinst.exe (PID: 3712)
- RegSvr.exe (PID: 2576)
- overseer.exe (PID: 3740)
- RegSvr.exe (PID: 3540)
- wsc_proxy.exe (PID: 1808)
- wsc_proxy.exe (PID: 3004)
- aswToolsSvc.exe (PID: 2176)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 3740)
- instup.exe (PID: 1812)
- instup.exe (PID: 4620)
Reads the computer name
- avast_free_antivirus_setup_online.exe (PID: 2436)
- avast_free_antivirus_setup_online.exe (PID: 1808)
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- aswOfferTool.exe (PID: 3636)
- Trojan.Ransom.Covid-666.exe (PID: 3236)
- SetupInf.exe (PID: 1888)
- SetupInf.exe (PID: 2904)
- SetupInf.exe (PID: 1000)
- AvEmUpdate.exe (PID: 3600)
- SetupInf.exe (PID: 3208)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 3700)
- AvEmUpdate.exe (PID: 128)
- avBugReport.exe (PID: 3924)
- SetupInf.exe (PID: 1832)
- drvinst.exe (PID: 3712)
- SetupInf.exe (PID: 1216)
- RegSvr.exe (PID: 3540)
- RegSvr.exe (PID: 2576)
- wsc_proxy.exe (PID: 1808)
- overseer.exe (PID: 3740)
- wsc_proxy.exe (PID: 3004)
- aswToolsSvc.exe (PID: 2176)
- engsup.exe (PID: 3052)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 3740)
- instup.exe (PID: 1812)
- instup.exe (PID: 4620)
Process requests binary or script from the Internet
- avast_free_antivirus_setup_online.exe (PID: 2436)
- AvEmUpdate.exe (PID: 2124)
Creates files in the program directory
- avast_free_antivirus_setup_online.exe (PID: 2912)
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 3600)
- AvEmUpdate.exe (PID: 2124)
- avBugReport.exe (PID: 3924)
- AvastNM.exe (PID: 2624)
- engsup.exe (PID: 2128)
- wsc_proxy.exe (PID: 1808)
- aswToolsSvc.exe (PID: 2176)
- AvastSvc.exe (PID: 2956)
- engsup.exe (PID: 3052)
- instup.exe (PID: 3740)
- instup.exe (PID: 1812)
- keytool.exe (PID: 4452)
Reads Environment values
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- AvEmUpdate.exe (PID: 3600)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 3700)
- AvEmUpdate.exe (PID: 128)
- AvastSvc.exe (PID: 2956)
- instup.exe (PID: 3740)
- aswToolsSvc.exe (PID: 2176)
- instup.exe (PID: 4620)
- instup.exe (PID: 1812)
Reads CPU info
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
- SetupInf.exe (PID: 2904)
- SetupInf.exe (PID: 1888)
- SetupInf.exe (PID: 1000)
- SetupInf.exe (PID: 3208)
- AvEmUpdate.exe (PID: 3600)
- AvEmUpdate.exe (PID: 2124)
- AvEmUpdate.exe (PID: 3700)
- SetupInf.exe (PID: 1216)
- AvEmUpdate.exe (PID: 128)
- avBugReport.exe (PID: 3924)
- SetupInf.exe (PID: 1832)
- RegSvr.exe (PID: 3540)
- RegSvr.exe (PID: 2576)
- wsc_proxy.exe (PID: 1808)
- wsc_proxy.exe (PID: 3004)
- AvastSvc.exe (PID: 2956)
- aswToolsSvc.exe (PID: 2176)
- instup.exe (PID: 3740)
- instup.exe (PID: 1812)
- instup.exe (PID: 4620)
Starts itself from another location
- Instup.exe (PID: 2948)
- aswOfferTool.exe (PID: 3636)
Checks proxy server information
- Instup.exe (PID: 2948)
- instup.exe (PID: 2156)
Dropped object may contain TOR URL's
- Instup.exe (PID: 2948)
- aswOfferTool.exe (PID: 3636)
- instup.exe (PID: 2156)
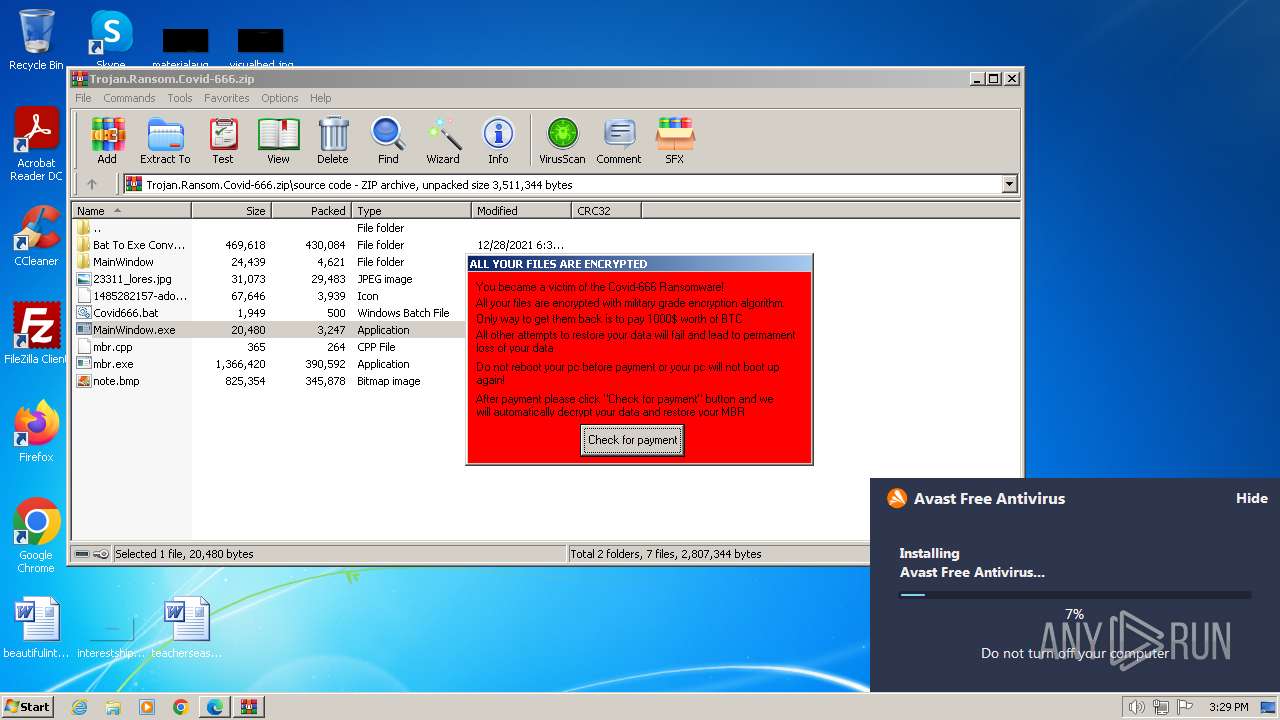
Drops a (possible) Coronavirus decoy
- WinRAR.exe (PID: 120)
- Trojan.Ransom.Covid-666.exe (PID: 3236)
- cmd.exe (PID: 1548)
Create files in a temporary directory
- Trojan.Ransom.Covid-666.exe (PID: 3236)
- SetupInf.exe (PID: 1832)
- engsup.exe (PID: 3052)
The executable file from the user directory is run by the CMD process
- mbr.exe (PID: 3712)
- MainWindow.exe (PID: 2892)
The process drops C-runtime libraries
- instup.exe (PID: 2156)
Process drops legitimate windows executable
- instup.exe (PID: 2156)
- instup.exe (PID: 1812)
Executes as Windows Service
- wsc_proxy.exe (PID: 3004)
- AvastSvc.exe (PID: 2956)
- aswToolsSvc.exe (PID: 2176)
Reads Microsoft Office registry keys
- aswToolsSvc.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2021:12:28 19:35:14 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | source code/ |
Total processes
184
Monitored processes
131
Malicious processes
32
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Trojan.Ransom.Covid-666.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 128 | AvEmUpdate.exe /installer1 /emupdater /applydll "C:\Program Files\Avast Software\Avast\Setup\7b90760b-5c45-427d-bfe4-309a8d7289dc.dll" | C:\Program Files\Avast Software\Avast\AvEmUpdate.exe | AvEmUpdate.exe | ||||||||||||
User: admin Company: AVAST Software Integrity Level: HIGH Description: Avast Emergency Update Exit code: 0 Version: 23.12.8700.0 Modules
| |||||||||||||||
| 240 | "C:\Users\admin\Downloads\avast_free_antivirus_setup_online.exe" | C:\Users\admin\Downloads\avast_free_antivirus_setup_online.exe | — | msedge.exe | |||||||||||
User: admin Company: AVAST Software Integrity Level: MEDIUM Description: Avast Installer Exit code: 3221226540 Version: 2.1.99.0 Modules
| |||||||||||||||
| 392 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6d54f598,0x6d54f5a8,0x6d54f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 480 | reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System /v HideFastUserSwitching /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 560 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4352 --field-trial-handle=1184,i,7379548780752197539,6179603659500882452,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1428 --field-trial-handle=1184,i,7379548780752197539,6179603659500882452,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --mojo-platform-channel-handle=4840 --field-trial-handle=1184,i,7379548780752197539,6179603659500882452,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 668 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableChangePassword /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3908 --field-trial-handle=1184,i,7379548780752197539,6179603659500882452,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
100 512
Read events
91 206
Write events
9 286
Delete events
20
Modification events
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1432) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
603
Suspicious files
2 202
Text files
478
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe172d.TMP | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe174c.TMP | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe1808.TMP | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:C7352A0E98449CC8AEDC1D6954C4CCD9 | SHA256:3A1591F52AD31B5B0B48F97AB5E1361D0AD0FA0F584E8FE8EFD482801DC2B9B5 | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | binary | |
MD5:9BE1E595404F8DCC1A1B06B1F39C5859 | SHA256:36A97008F8E7D1D2793F9B46E02C7A674DB5071212B9A0DA8C4D441C9AEB84F4 | |||
| 392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:C612E96CBFAC63232FC2062E15600FB1 | SHA256:DB3C05D5EC0B6719A73E7F0BE84BCE9342772DA70567E7CE08CF6573480B38FF | |||
| 1432 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:257D5DDA97D40A23552C7003202A2E48 | SHA256:65620F24B64726030DE5F0FD6AC7B2F97ACFC12C14187375B87E9EC4B7DF11C0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
97
TCP/UDP connections
277
DNS requests
341
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
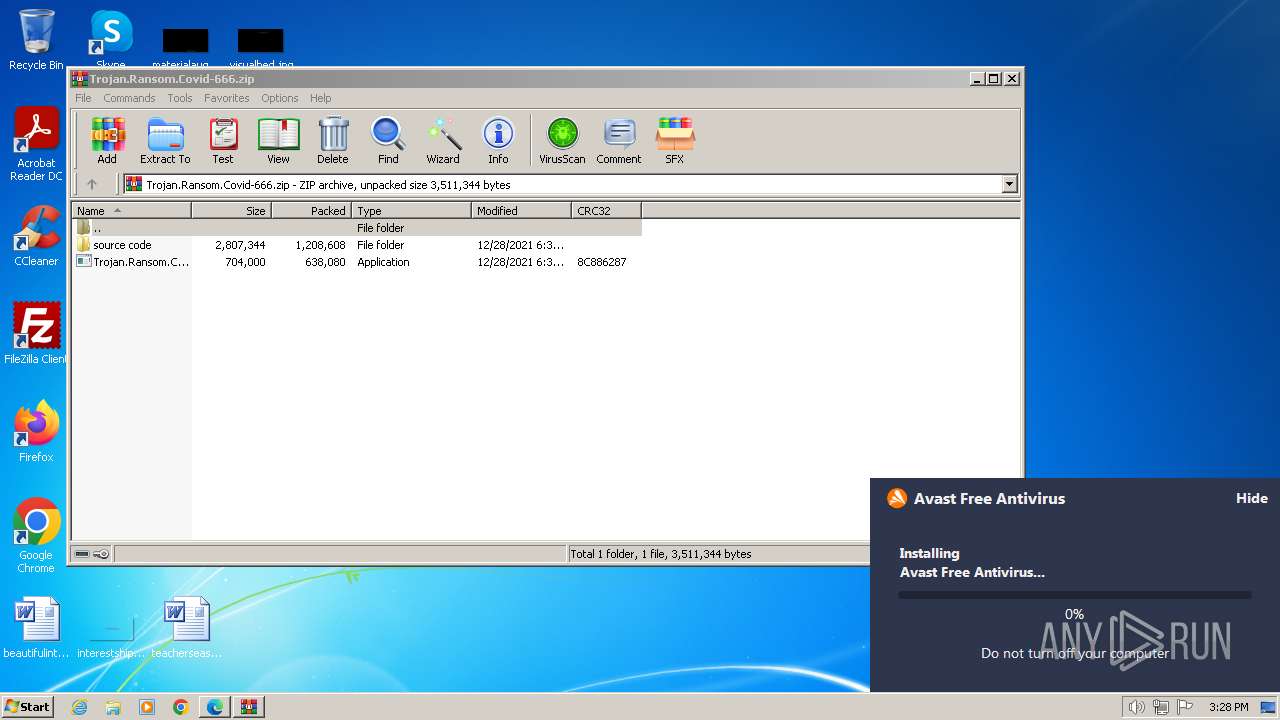
2436 | avast_free_antivirus_setup_online.exe | GET | 200 | 23.50.131.91:80 | http://iavs9x.u.avcdn.net/iavs9x/avast_free_antivirus_setup_online.exe | DE | executable | 9.10 Mb | unknown |
1808 | avast_free_antivirus_setup_online.exe | POST | 204 | 34.117.223.223:80 | http://v7event.stats.avast.com/cgi-bin/iavsevents.cgi | US | — | — | unknown |
2948 | Instup.exe | GET | 200 | 23.32.238.160:80 | http://l7814800.iavs9x.u.avast.com/iavs9x/offertool_ais-a27.vpx | DE | binary | 873 Kb | unknown |
2948 | Instup.exe | GET | 200 | 23.32.238.160:80 | http://l7814800.iavs9x.u.avast.com/iavs9x/sbr_x86_ais-a27.vpx | DE | binary | 11.0 Kb | unknown |
2948 | Instup.exe | GET | 200 | 23.32.238.160:80 | http://l7814800.iavs9x.u.avast.com/iavs9x/setgui_ais-a27.vpx | DE | binary | 1.17 Mb | unknown |
2156 | instup.exe | GET | 200 | 2.19.198.50:80 | http://y8002308.iavs9x.u.avast.com/iavs9x/prod-pgm.vpx | DE | binary | 572 b | unknown |
2948 | Instup.exe | GET | 200 | 23.32.238.160:80 | http://l7814800.iavs9x.u.avast.com/iavs9x/instup_ais-a27.vpx | DE | binary | 5.47 Mb | unknown |
1808 | avast_free_antivirus_setup_online.exe | POST | 200 | 216.58.212.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | unknown |
2436 | avast_free_antivirus_setup_online.exe | POST | 200 | 216.58.212.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | unknown |
2436 | avast_free_antivirus_setup_online.exe | POST | 200 | 216.58.212.142:80 | http://www.google-analytics.com/collect | US | image | 35 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
584 | msedge.exe | 204.79.197.203:443 | ntp.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1432 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
584 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
584 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
584 | msedge.exe | 23.53.42.147:443 | assets.msn.com | Akamai International B.V. | DE | unknown |
584 | msedge.exe | 2.21.20.136:443 | img-s-msn-com.akamaized.net | Akamai International B.V. | DE | unknown |
584 | msedge.exe | 13.32.99.105:443 | sb.scorecardresearch.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ntp.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
assets.msn.com |
| whitelisted |
img-s-msn-com.akamaized.net |
| whitelisted |
sb.scorecardresearch.com |
| shared |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.msn.com |
| whitelisted |
c.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2436 | avast_free_antivirus_setup_online.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2124 | AvEmUpdate.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
avast_free_antivirus_setup_online.exe | [2024-01-07 15:28:24.323] [info ] [sfxinst ] [ 2912: 2848] [000000: 0] Running SFX 'C:\Windows\Temp\asw.569a2443dc68c027\avast_free_antivirus_setup_online.exe'
|
avast_free_antivirus_setup_online.exe | [2024-01-07 15:28:24.495] [info ] [sfxinst ] [ 2912: 2848] [000000: 0] Moved extra data file 'ecoo.edat' to 'C:\Windows\Temp\asw.8db3806c5d781e4e\cookie.bin'.
|
avast_free_antivirus_setup_online.exe | [2024-01-07 15:28:24.651] [notice ] [burger_rep ] [ 2912: 2508] [000000: 0] The event '70.1' was successfully sent to burger: https://analytics.avcdn.net/v4/receive/json/70.
|
avast_free_antivirus_setup_online.exe | [2024-01-07 15:28:24.980] [info ] [sfxstats ] [ 2912: 2824] [000000: 0] Statistics sent successfully.
|
avast_free_antivirus_setup_online.exe | [2024-01-07 15:28:25.511] [info ] [sfxinst ] [ 2912: 2848] [000000: 0] Starting installer/updater executable 'C:\Windows\Temp\asw.8db3806c5d781e4e\instup.exe'
|
Instup.exe | [2024-01-07 15:28:25.823] [info ] [instup ] [ 2948: 2924] [000000: 0] Memory: 29% load. Phys:2214788/3145208K free, Page:4194303/4194303K free, Virt:1990888/2097024K free
|
Instup.exe | [2024-01-07 15:28:25.823] [info ] [instup ] [ 2948: 2924] [000000: 0] DISKs: C:\ - 221543MB free / 255GB total
|
Instup.exe | [2024-01-07 15:28:25.823] [info ] [instup ] [ 2948: 2924] [000000: 0] Running module version: instup.exe - '23.12.8700.0'
|
Instup.exe | [2024-01-07 15:28:25.823] [info ] [instup ] [ 2948: 2924] [000000: 0] Command: '"C:\Windows\Temp\asw.8db3806c5d781e4e\instup.exe" /sfx:lite /sfxstorage:C:\Windows\Temp\asw.8db3806c5d781e4e /edition:1 /prod:ais /stub_mapping_guid:6966fd0c-38dc-4be9-96b9-272de5ef7ee1:9543376 /guid:057e7b0c-5849-418b-ad38-72b32b0f50cb /ga_clientid:5458ab53-ff94-4e69-9b05-3eb671863f5e /cookie:mmm_ava_013_999_a8a_m /ga_clientid:5458ab53-ff94-4e69-9b05-3eb671863f5e /edat_dir:C:\Windows\Temp\asw.569a2443dc68c027'
|
Instup.exe | [2024-01-07 15:28:25.823] [info ] [instup ] [ 2948: 2924] [000000: 0] OS: Windows 7 SP1 x86
|