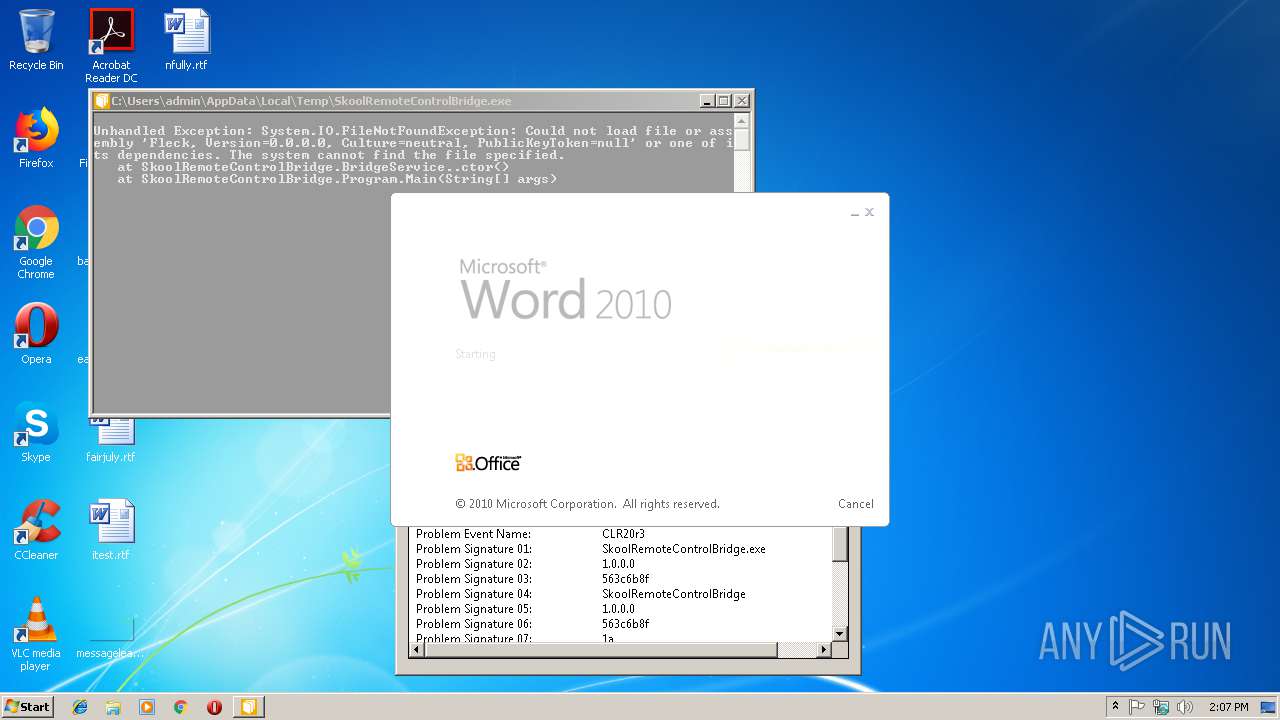
| File name: | SkoolRemoteControlBridge.exe |
| Full analysis: | https://app.any.run/tasks/3c8fa26d-f8e3-4e92-be89-b43974ec5be4 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 14:06:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 31E6D3AB67E17674BAFD984DA4D7CF9F |
| SHA1: | E04AACA1CFC2AEDC68BA61C6F80720361EED0DCB |
| SHA256: | E7D7A1B23472A5DC55EB07ED2B4F7B5F513CE8D67AC0BB3AAE293B7DF27F053B |
| SSDEEP: | 768:/egG3W9m84Pz/9m0DuLw4C/W4M24oP+syr:/e3Am8ez1mDLwRcwPJ |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 3032)
SUSPICIOUS
Application launched itself
- Skype.exe (PID: 2796)
- Skype.exe (PID: 2764)
- Skype.exe (PID: 2568)
Reads CPU info
- Skype.exe (PID: 2796)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2796)
Creates files in the user directory
- Skype.exe (PID: 2796)
- Skype.exe (PID: 2764)
Modifies the open verb of a shell class
- Skype.exe (PID: 2796)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3168)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3168)
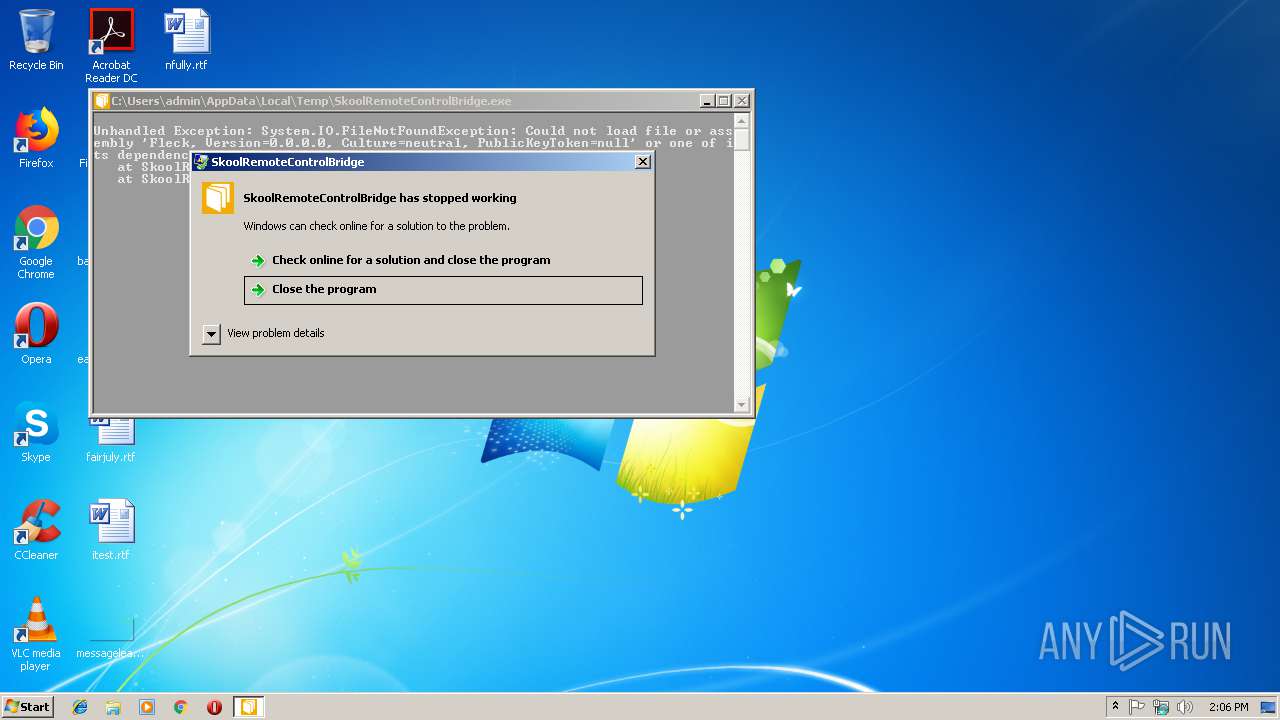
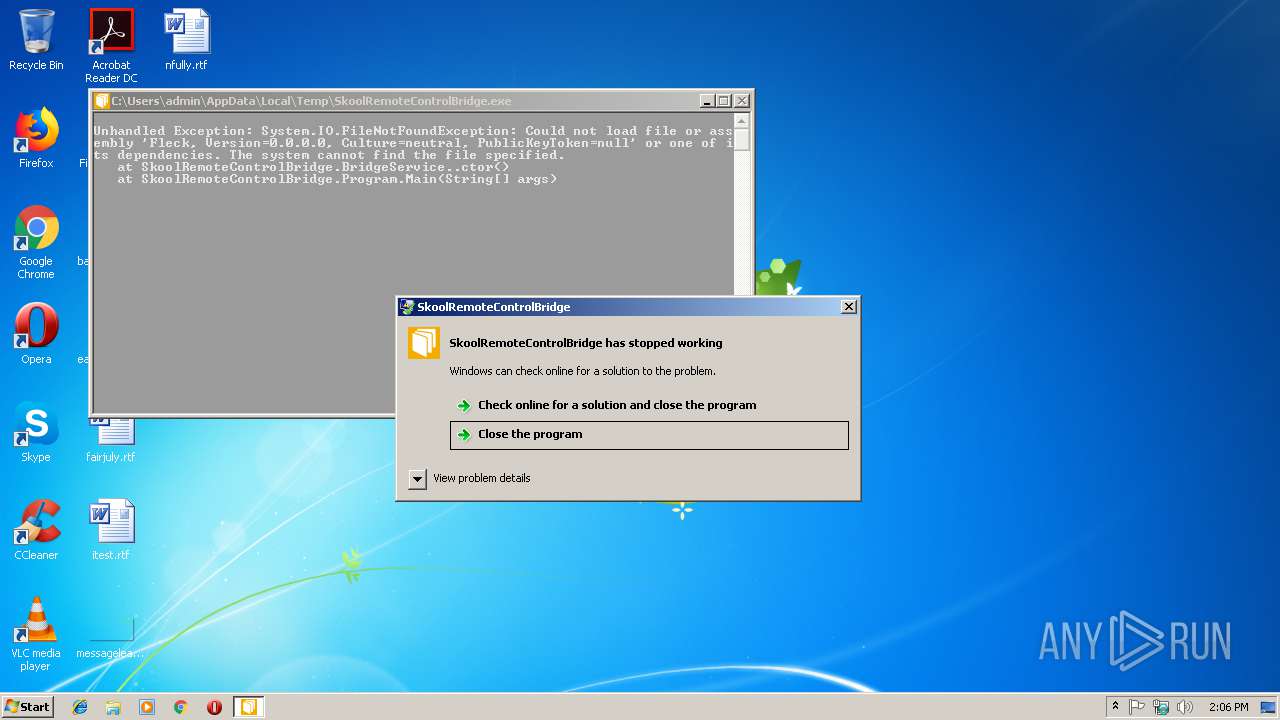
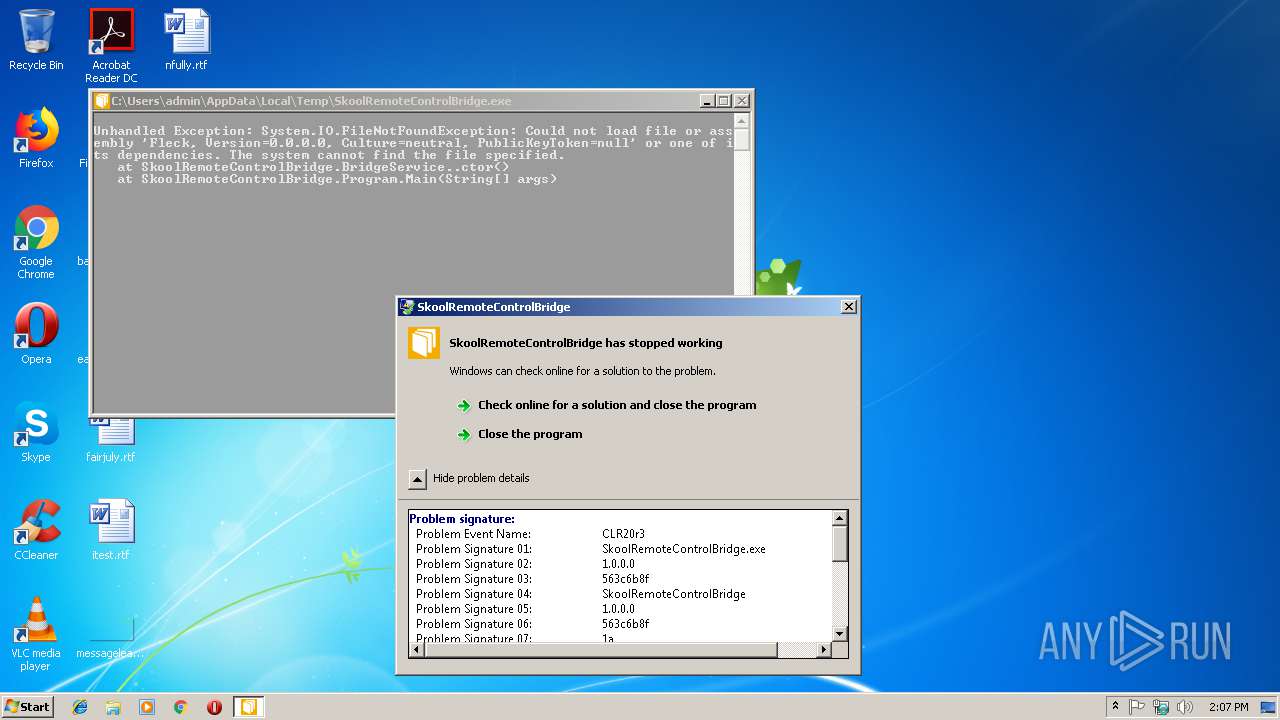
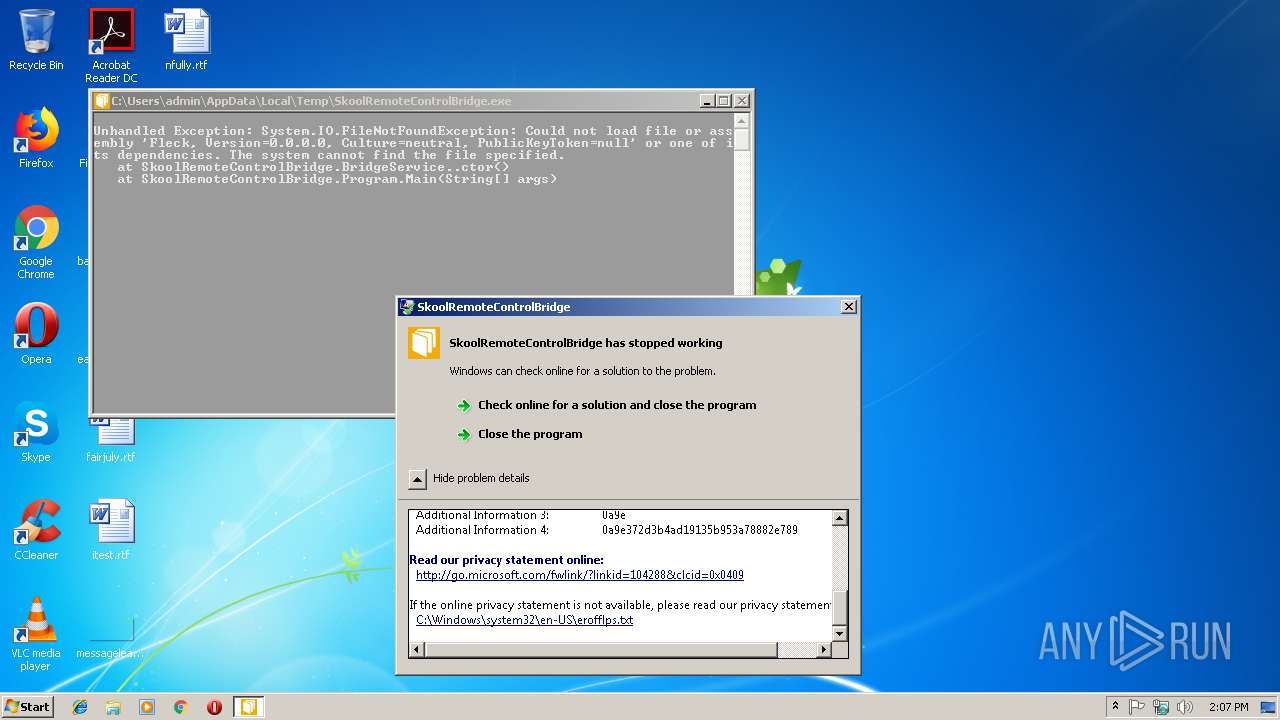
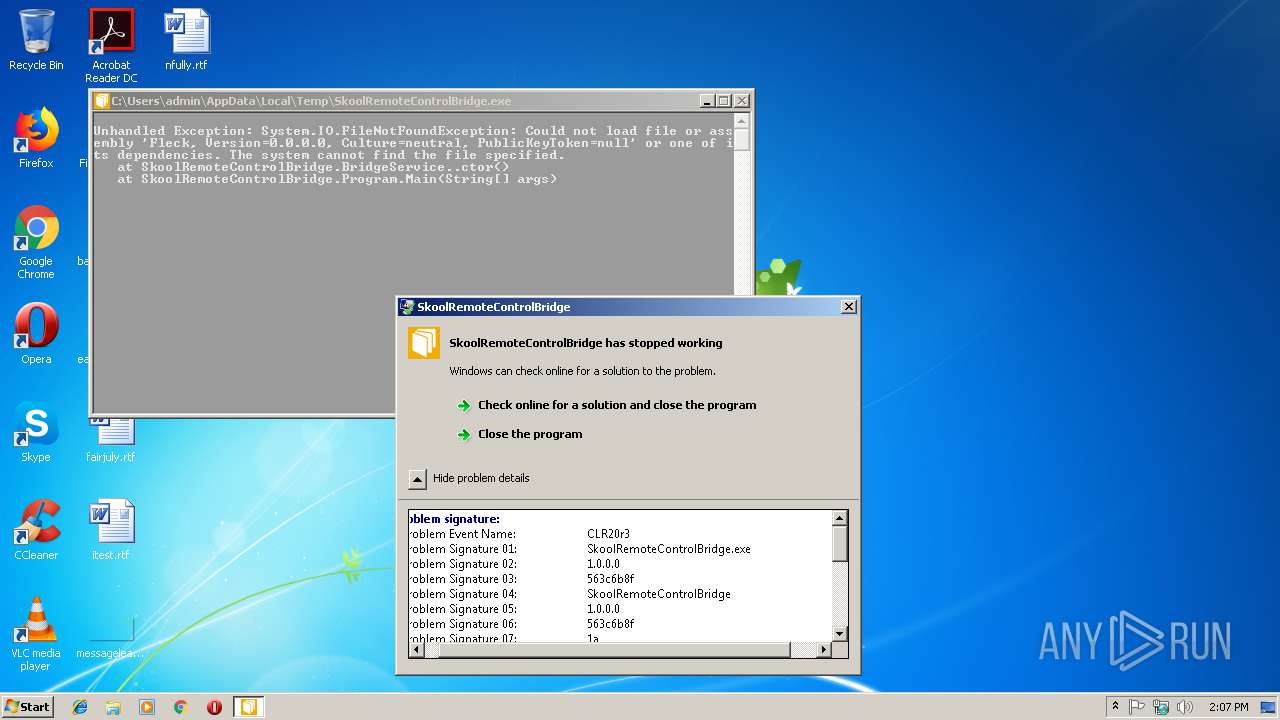
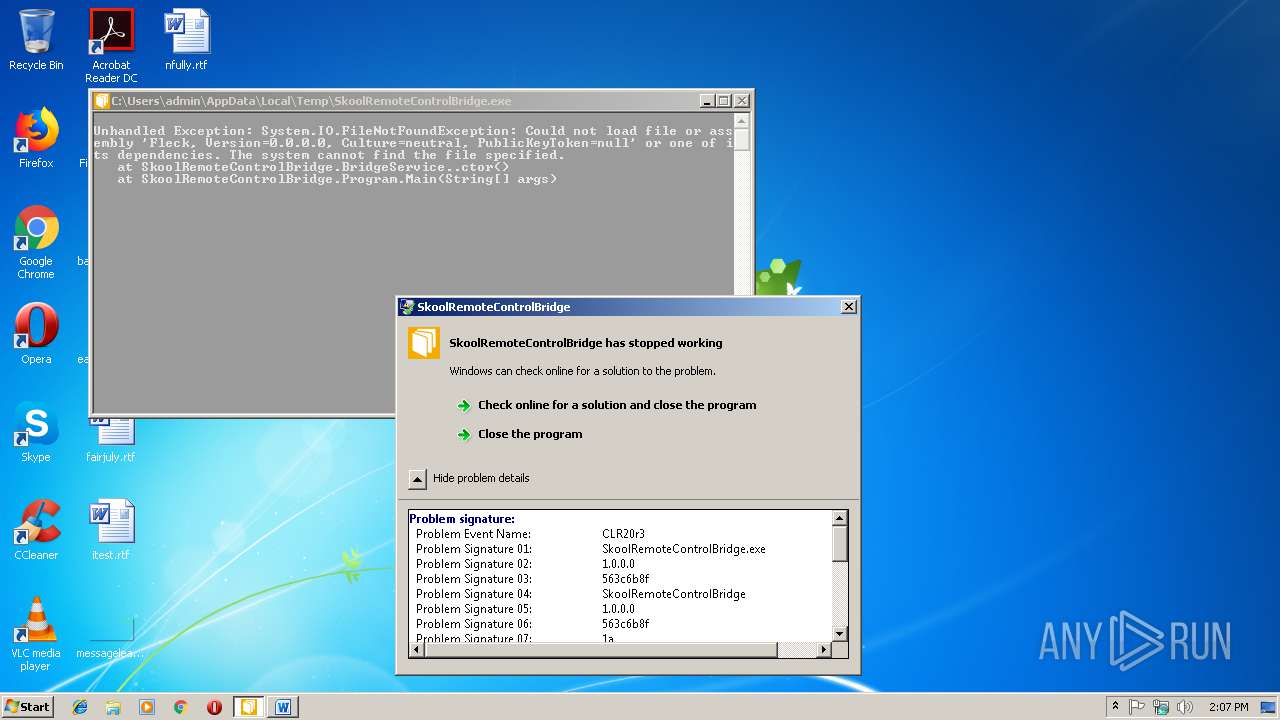
Application was crashed
- SkoolRemoteControlBridge.exe (PID: 3132)
Reads settings of System Certificates
- Skype.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:11:06 09:57:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 16384 |
| InitializedDataSize: | 26624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5e1e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Skool Automatisering B.V. |
| FileDescription: | SkoolRemoteControlBridge |
| FileVersion: | 1.0.0.0 |
| InternalName: | SkoolRemoteControlBridge.exe |
| LegalCopyright: | Copyright © Skool Automatisering B.V. 2015 |
| OriginalFileName: | SkoolRemoteControlBridge.exe |
| ProductName: | Skool Remote Control Bridge |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 06-Nov-2015 08:57:51 |
| Debug artifacts: |
|
| CompanyName: | Skool Automatisering B.V. |
| FileDescription: | SkoolRemoteControlBridge |
| FileVersion: | 1.0.0.0 |
| InternalName: | SkoolRemoteControlBridge.exe |
| LegalCopyright: | Copyright © Skool Automatisering B.V. 2015 |
| OriginalFilename: | SkoolRemoteControlBridge.exe |
| ProductName: | Skool Remote Control Bridge |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Nov-2015 08:57:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00003E24 | 0x00004000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.45236 |
.rsrc | 0x00006000 | 0x000064E8 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.36 |
.reloc | 0x0000E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.81748 | 6325 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.45556 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.00663 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.97697 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.6213 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.66463 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
45
Monitored processes
10
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=C8F1B767AD46E670C37966C17131EB86 --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=C8F1B767AD46E670C37966C17131EB86 --renderer-client-id=4 --mojo-platform-channel-handle=2644 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2764 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=49964F0EF0F2951E07B243CE300A73FA --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=49964F0EF0F2951E07B243CE300A73FA --renderer-client-id=3 --mojo-platform-channel-handle=1544 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3004 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\system32\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | C:\Windows\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\system32\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\SkoolRemoteControlBridge.exe" | C:\Users\admin\AppData\Local\Temp\SkoolRemoteControlBridge.exe | explorer.exe | ||||||||||||
User: admin Company: Skool Automatisering B.V. Integrity Level: MEDIUM Description: SkoolRemoteControlBridge Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\itest.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
1 048
Read events
701
Write events
340
Delete events
7
Modification events
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tm- |
Value: 746D2D00600C0000010000000000000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311834136 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834256 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834257 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 600C0000ECEDC5F46DAED40100000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {o- |
Value: 7B6F2D00600C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | {o- |
Value: 7B6F2D00600C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3168) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3168 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR69F4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2796 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0DQP3MIVGAPYCCUA4ROW.temp | — | |
MD5:— | SHA256:— | |||
| 2796 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\Skype-Setup.exe | — | |
MD5:— | SHA256:— | |||
| 2764 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\skylib\slimcore-0-1435538533.blog | — | |
MD5:— | SHA256:— | |||
| 3168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3168 | WINWORD.EXE | C:\Users\admin\Desktop\~$itest.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2796 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Skype for Desktop\ecscache.json | text | |
MD5:— | SHA256:— | |||
| 3200 | Skype.exe | C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\operation_log.txt | text | |
MD5:— | SHA256:— | |||
| 3168 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2796 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b916037c1e115fe0.customDestinations-ms~RF21a3e0.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
9
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2796 | Skype.exe | 13.90.95.57:443 | get.skype.com | Microsoft Corporation | US | whitelisted |
2796 | Skype.exe | 23.101.156.198:443 | a.config.skype.com | Microsoft Corporation | US | whitelisted |
2796 | Skype.exe | 52.114.32.7:443 | pipe.skype.com | Microsoft Corporation | JP | whitelisted |
2796 | Skype.exe | 23.210.249.5:443 | download.skype.com | Akamai International B.V. | NL | whitelisted |
2796 | Skype.exe | 157.55.135.128:443 | login.live.com | Microsoft Corporation | US | whitelisted |
2796 | Skype.exe | 172.217.16.170:443 | www.googleapis.com | Google Inc. | US | whitelisted |
2796 | Skype.exe | 13.68.117.223:443 | avatar.skype.com | Microsoft Corporation | US | whitelisted |
2796 | Skype.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
get.skype.com |
| whitelisted |
a.config.skype.com |
| whitelisted |
pipe.skype.com |
| whitelisted |
download.skype.com |
| whitelisted |
login.live.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
avatar.skype.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
Threats
Process | Message |
|---|---|
Skype.exe | [3416:3672:0117/140732.280:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3416:3672:0117/140732.280:VERBOSE1:crash_service.cc(145)] window handle is 000201A6
|
Skype.exe | [3416:3672:0117/140732.280:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hoɸ |
Skype.exe | [3416:3672:0117/140732.280:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [3416:3672:0117/140732.280:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [3416:2960:0117/140732.280:VERBOSE1:crash_service.cc(333)] client start. pid = 2796
|
Skype.exe | [3416:2960:0117/140734.405:VERBOSE1:crash_service.cc(333)] client start. pid = 2764
|
Skype.exe | [3200:3236:0117/140734.650:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3200:3236:0117/140734.651:VERBOSE1:crash_service.cc(145)] window handle is 000101C6
|
Skype.exe | [3200:3236:0117/140734.651:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|