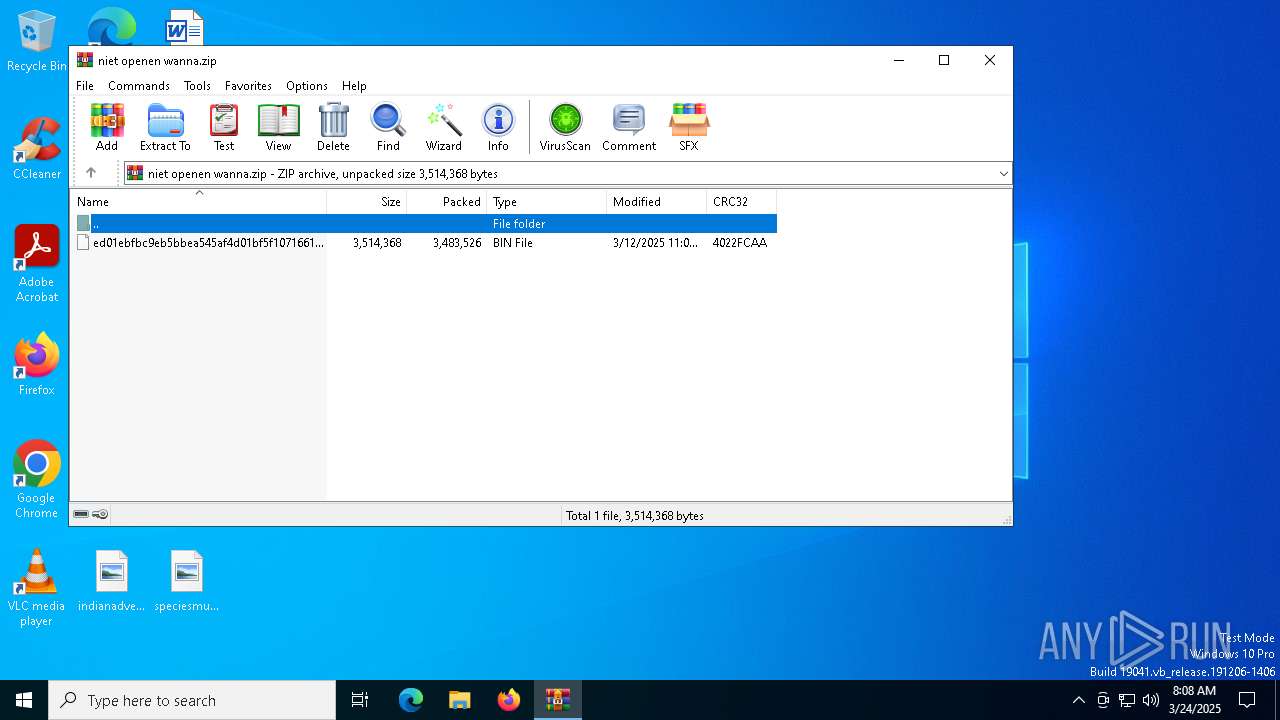
| File name: | niet openen wanna.zip |
| Full analysis: | https://app.any.run/tasks/673fb597-b4f9-435e-b704-6a54f342a6cf |
| Verdict: | Malicious activity |
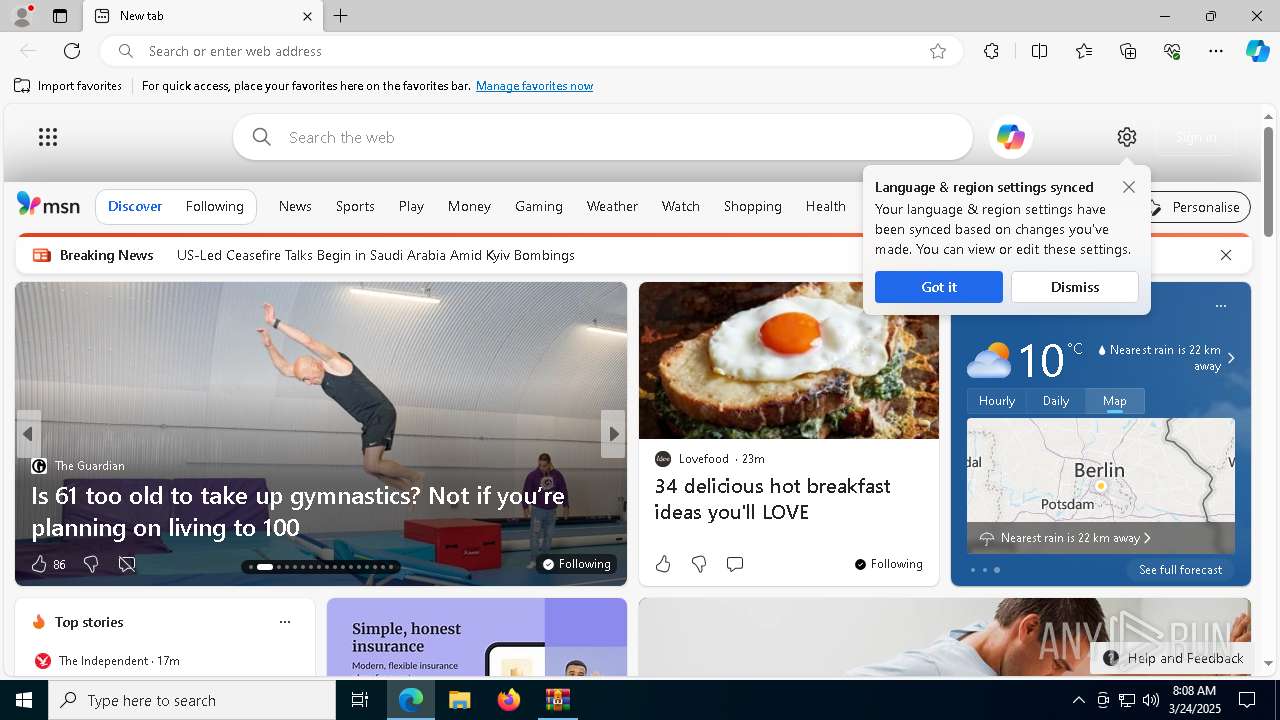
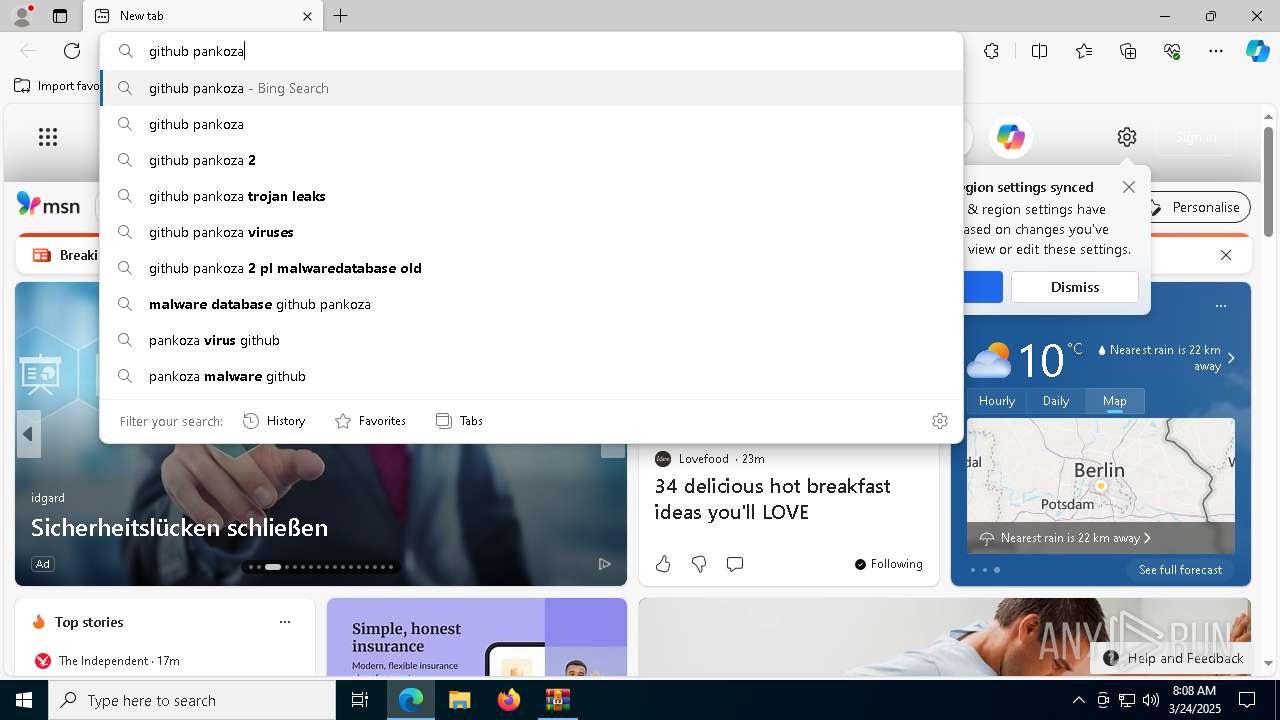
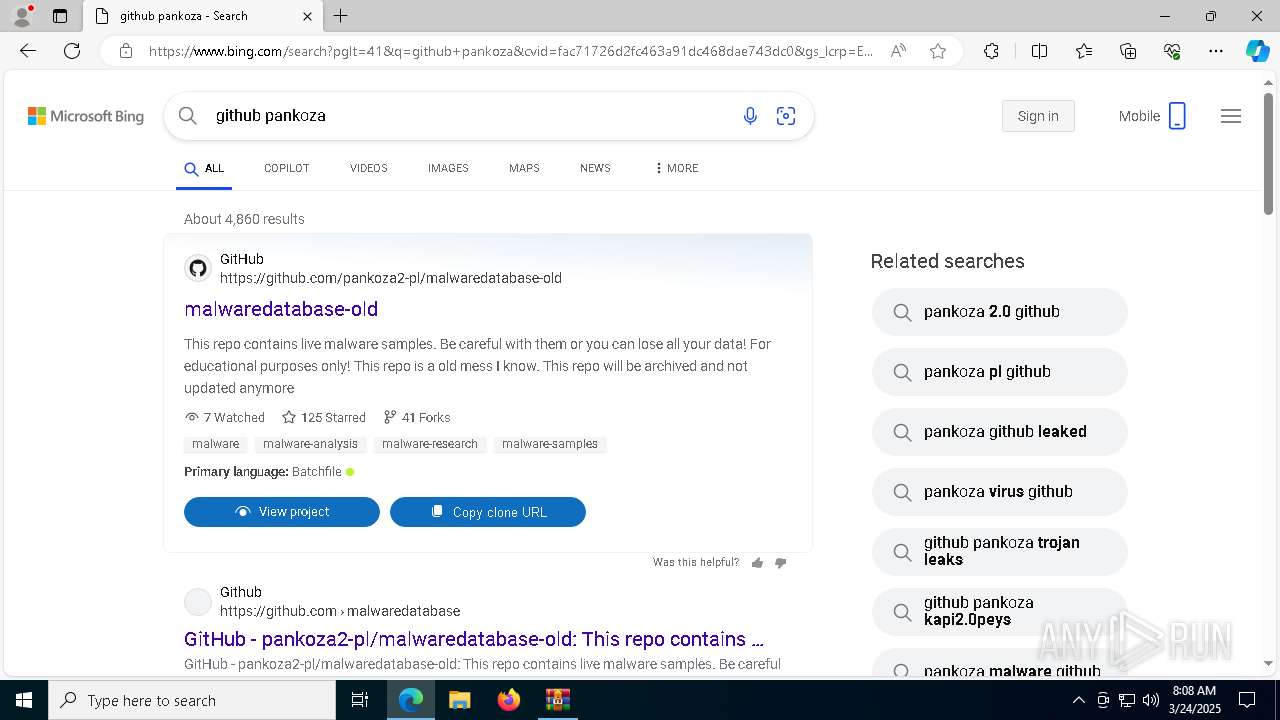
| Analysis date: | March 24, 2025, 08:08:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 19FDBA59A26F762D4BD1E2E577C131C1 |
| SHA1: | CE2B3D172CD42577C848293E5AA5D924A6CE7A7C |
| SHA256: | E7CF8B546CAB018D43BAC3DCC54BEA5C4FD90E2EB889C113C5D7F4CE7081D331 |
| SSDEEP: | 98304:5BS3YTJ6PpMu8xj9HHdbNraPwpj0+P/80f16X+rXM82AUDlyExu5eA4QONTZugTH:x0m8bG+4W |
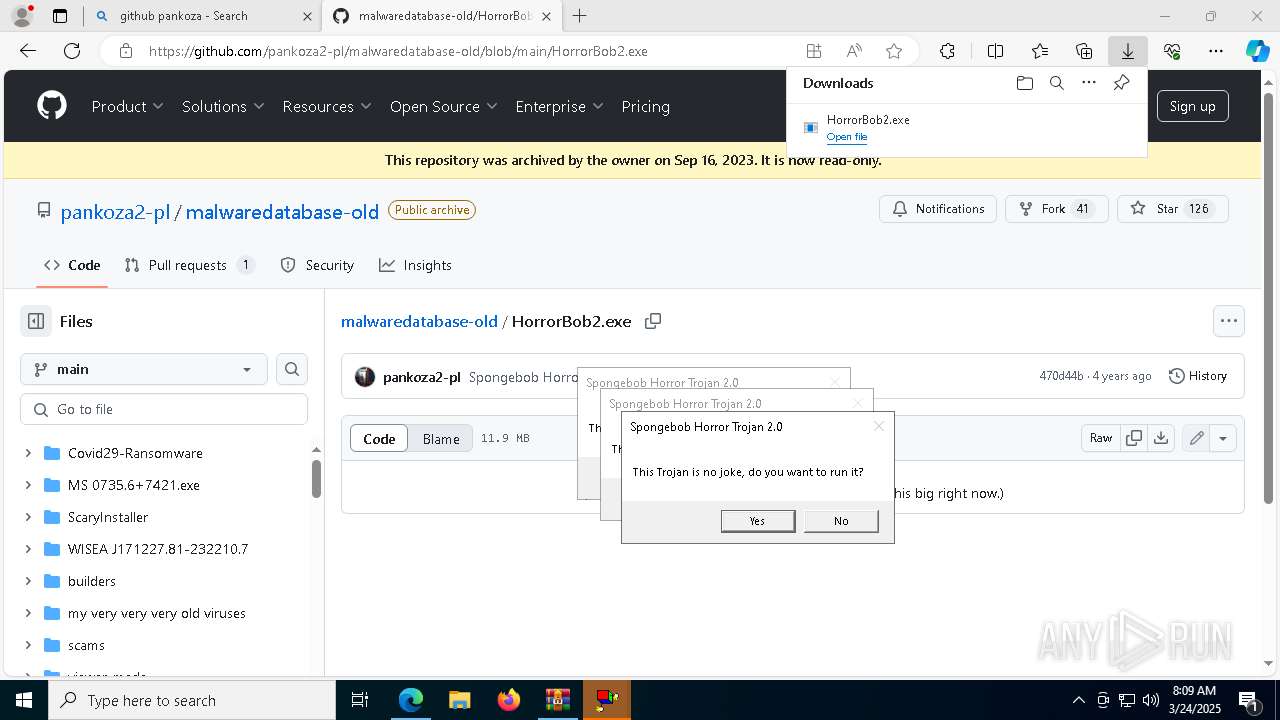
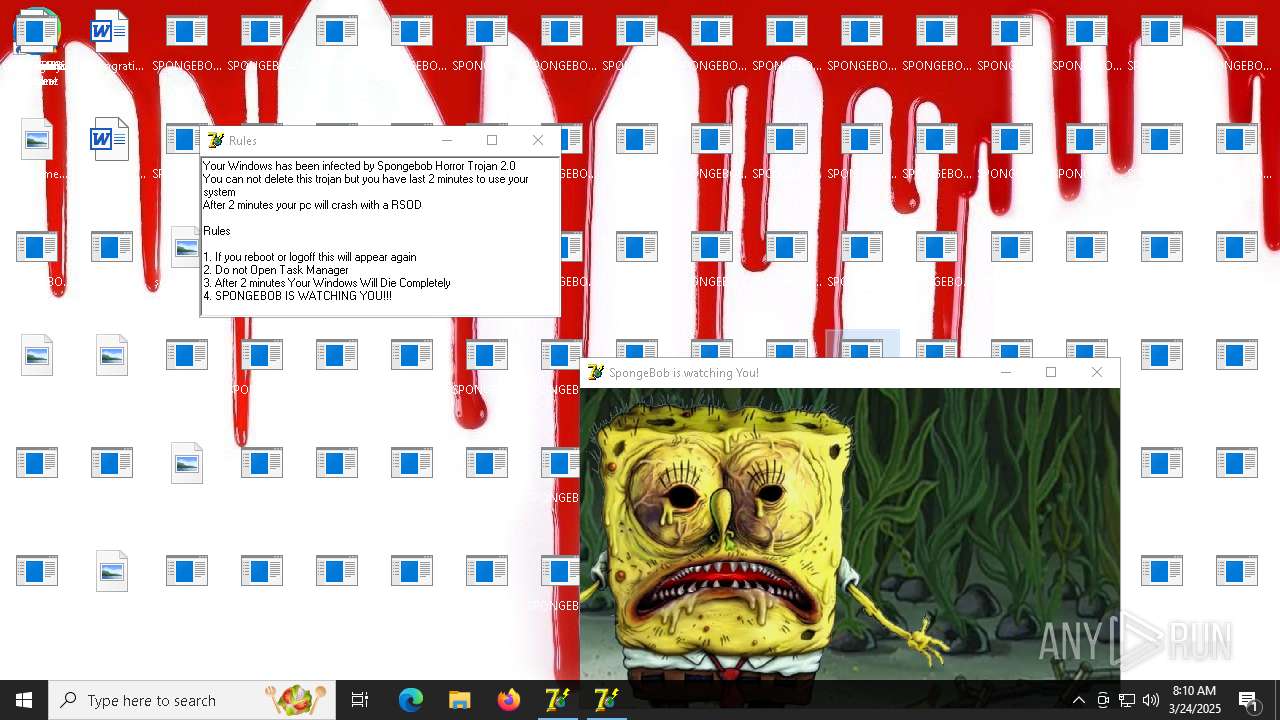
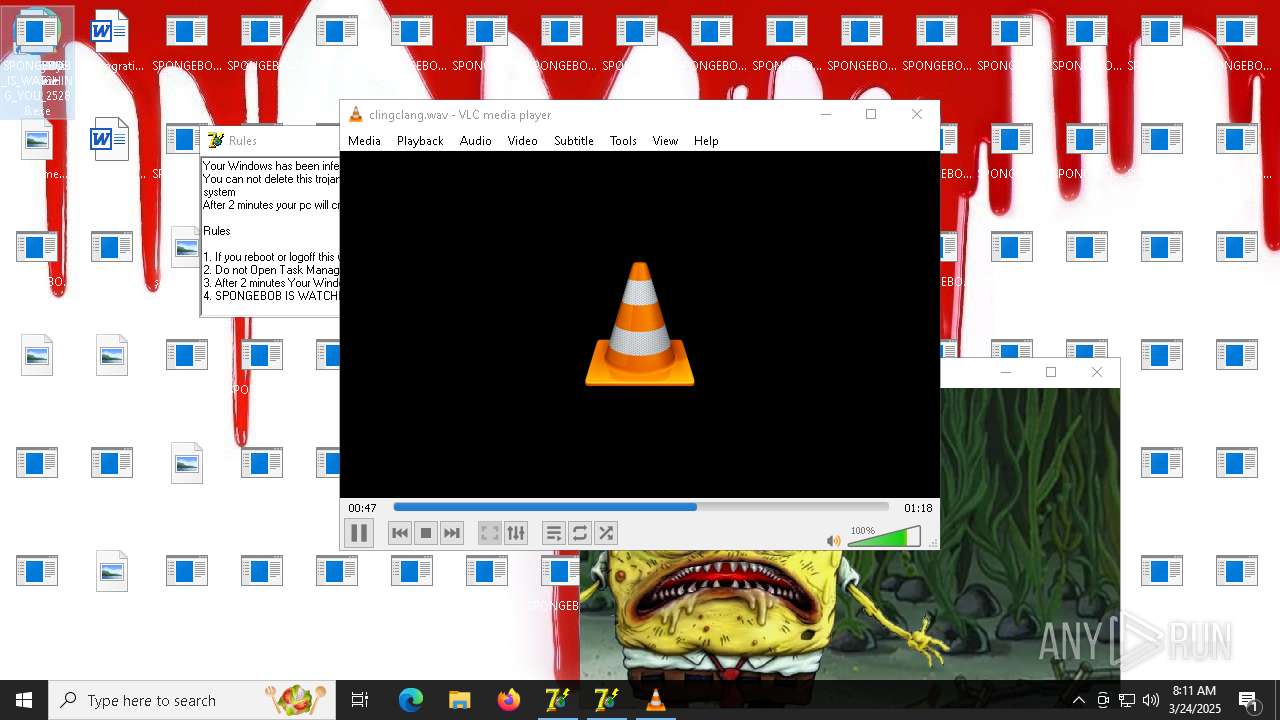
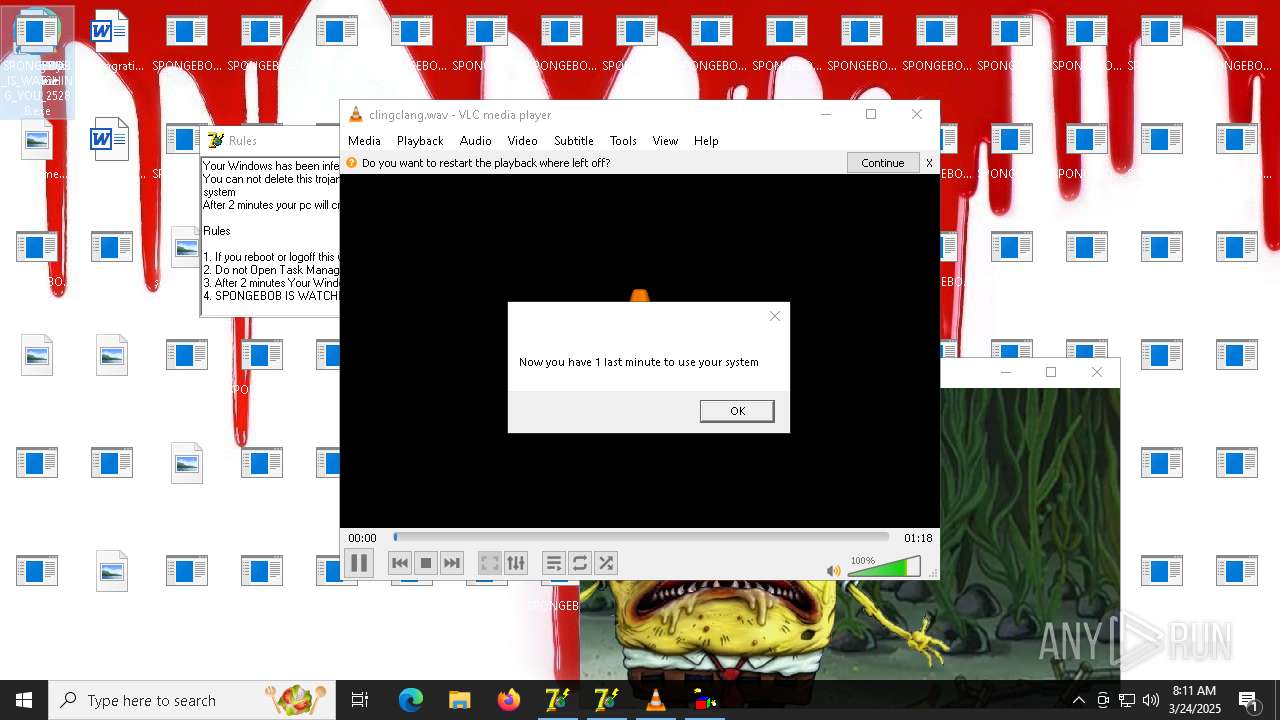
MALICIOUS
Disables Windows Defender
- reg.exe (PID: 8756)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 8528)
- net.exe (PID: 8828)
Uses Task Scheduler to run other applications
- endpc.exe (PID: 5860)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 4652)
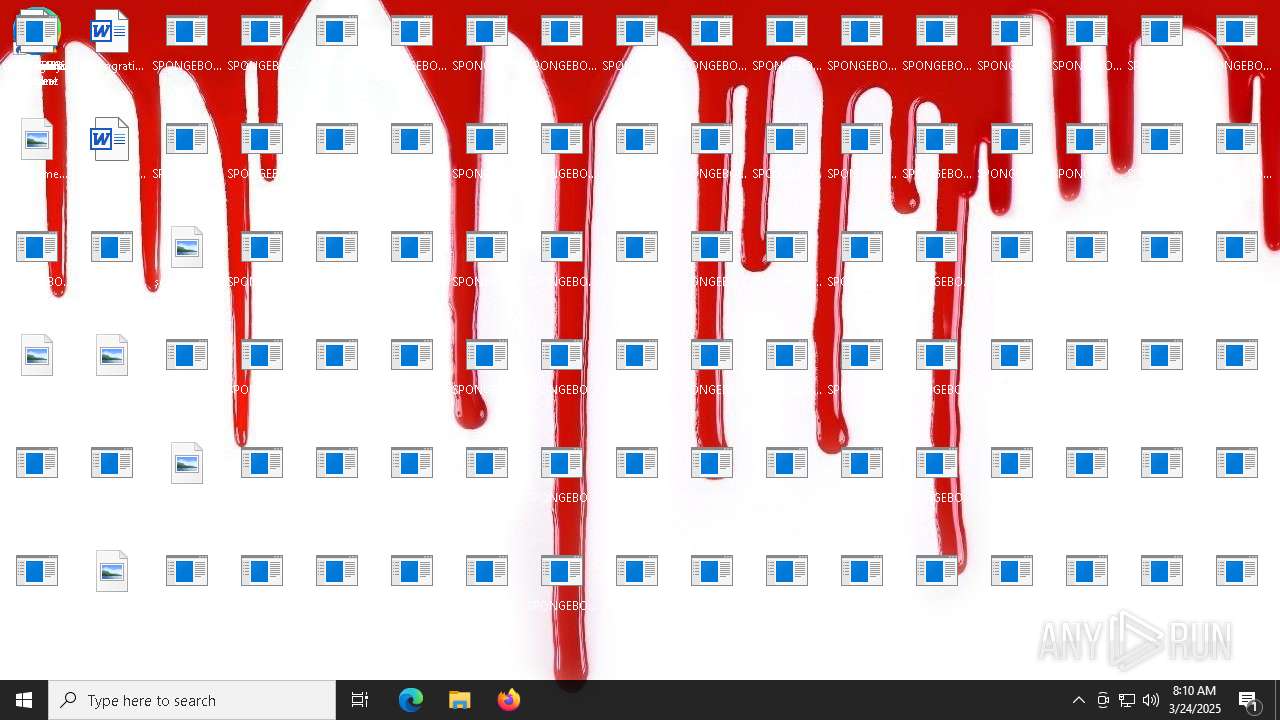
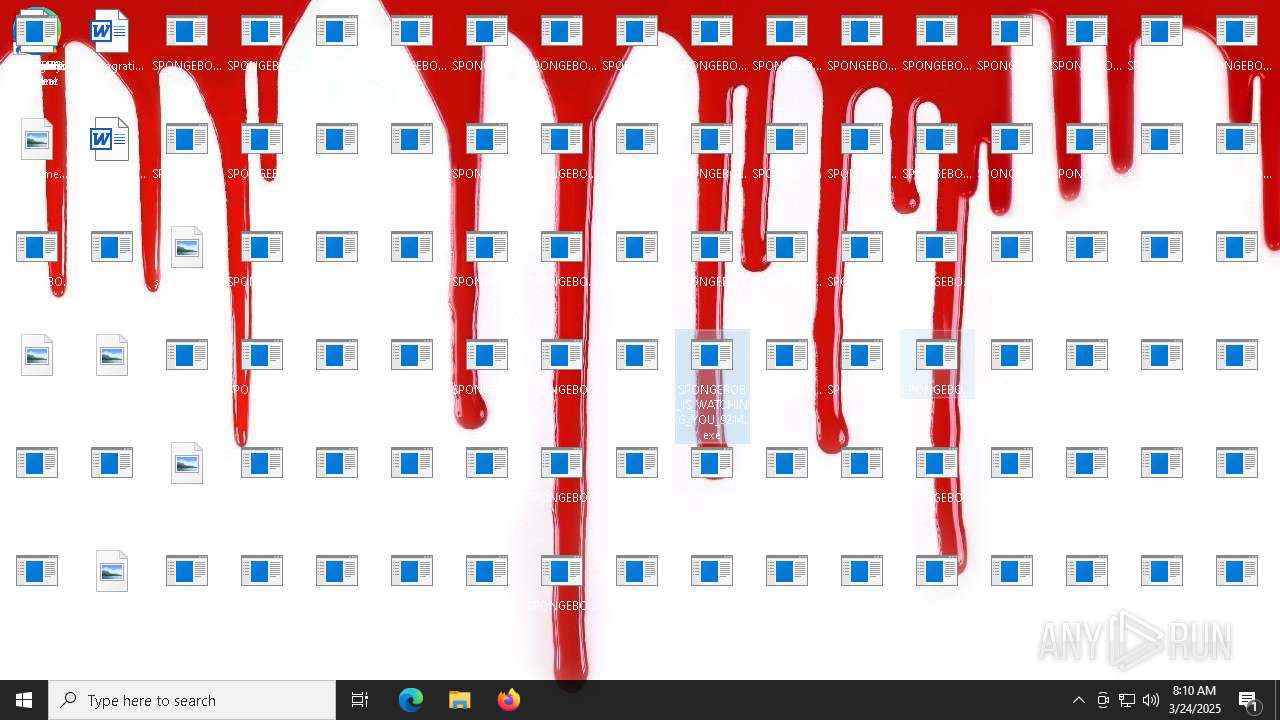
Executable content was dropped or overwritten
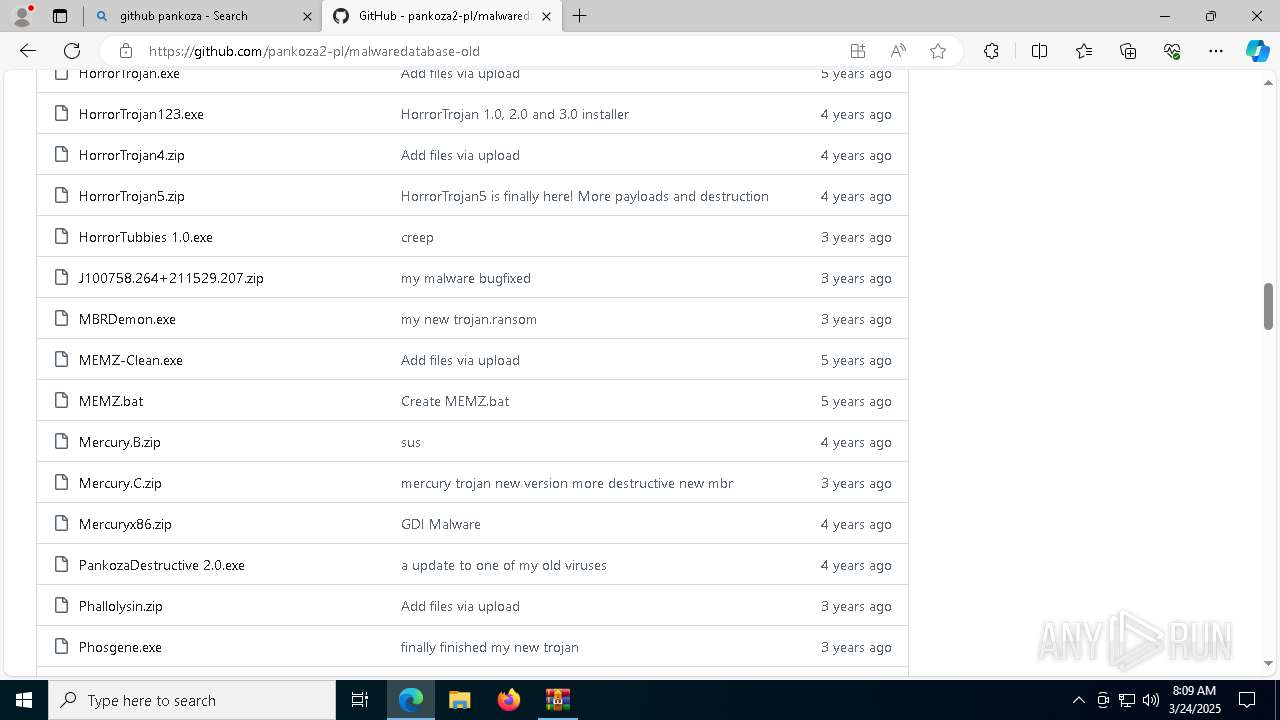
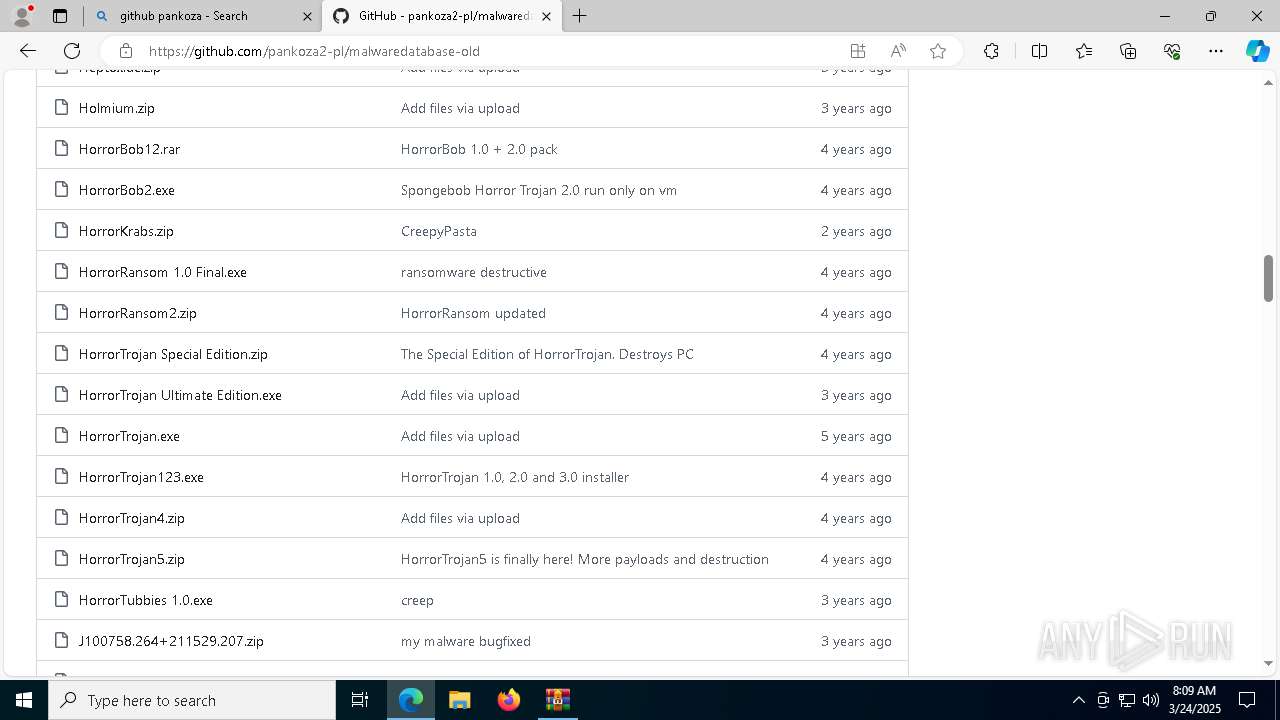
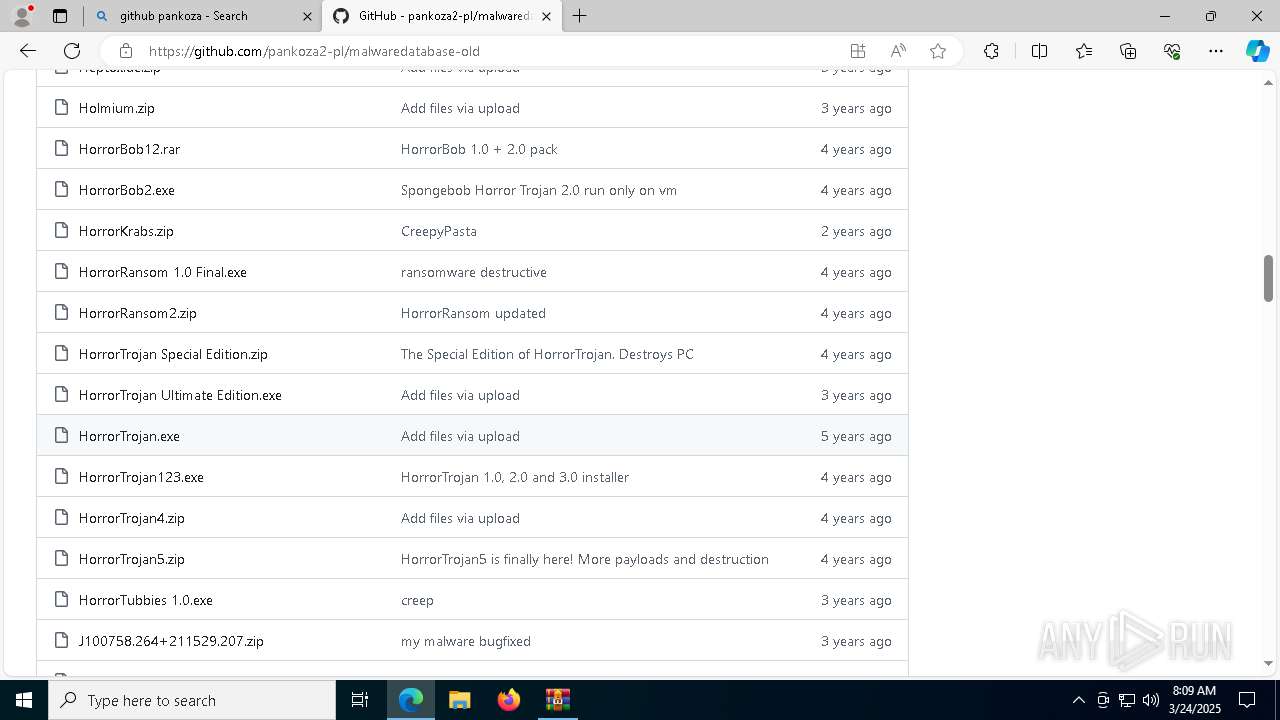
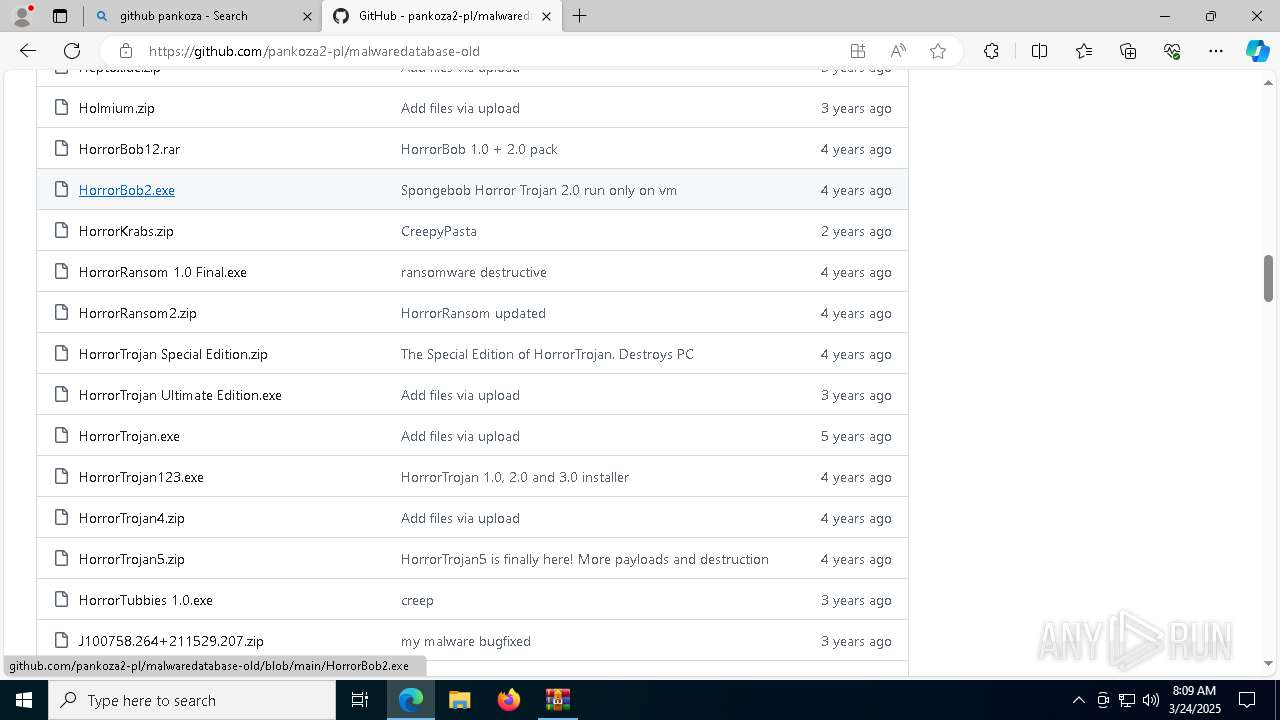
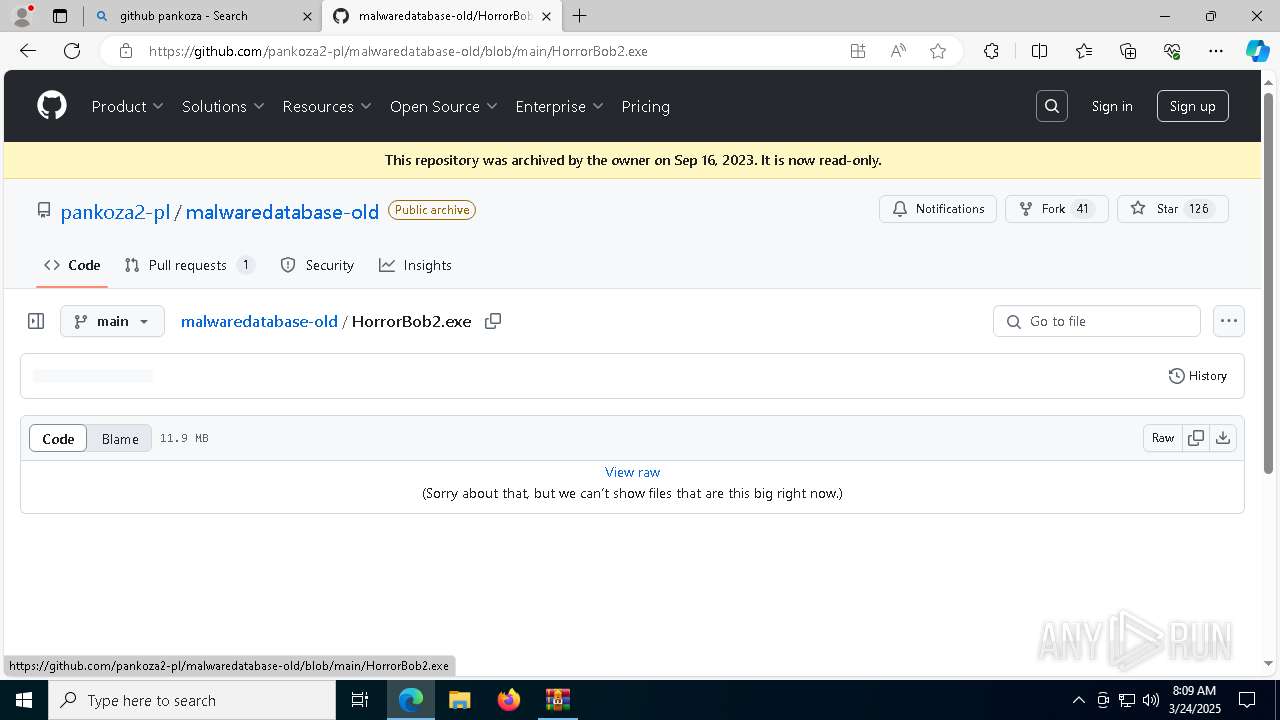
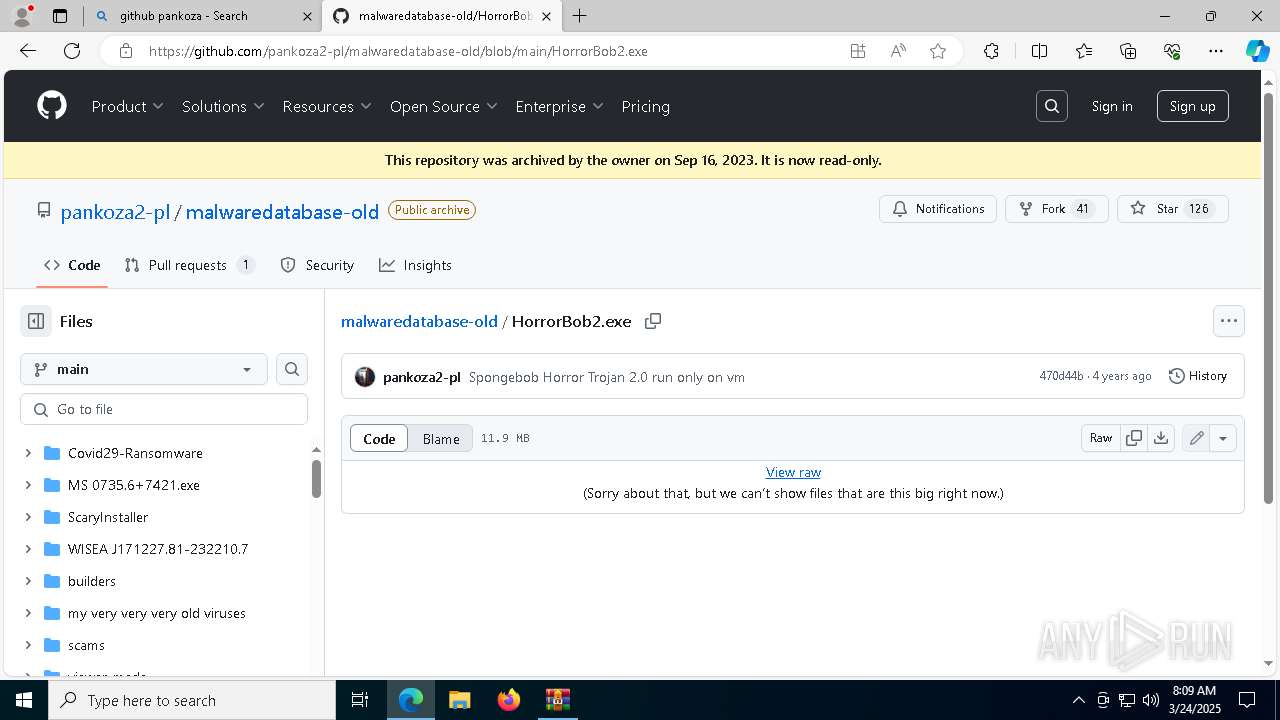
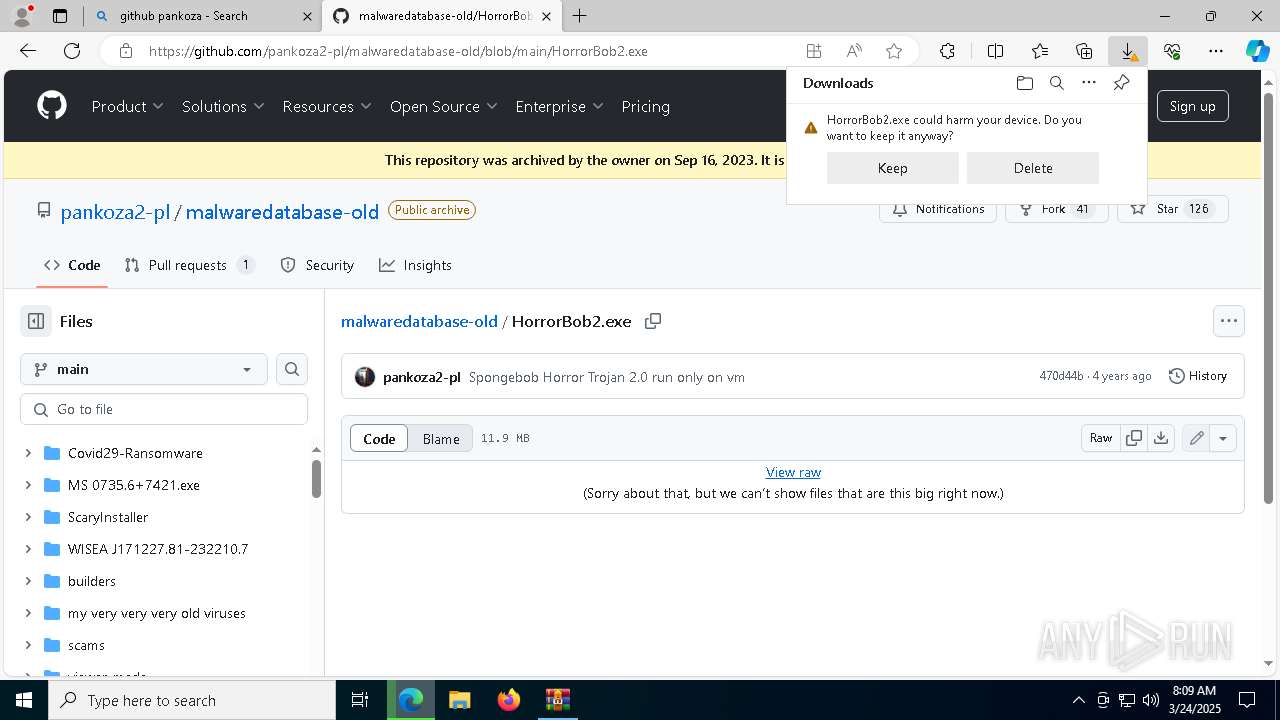
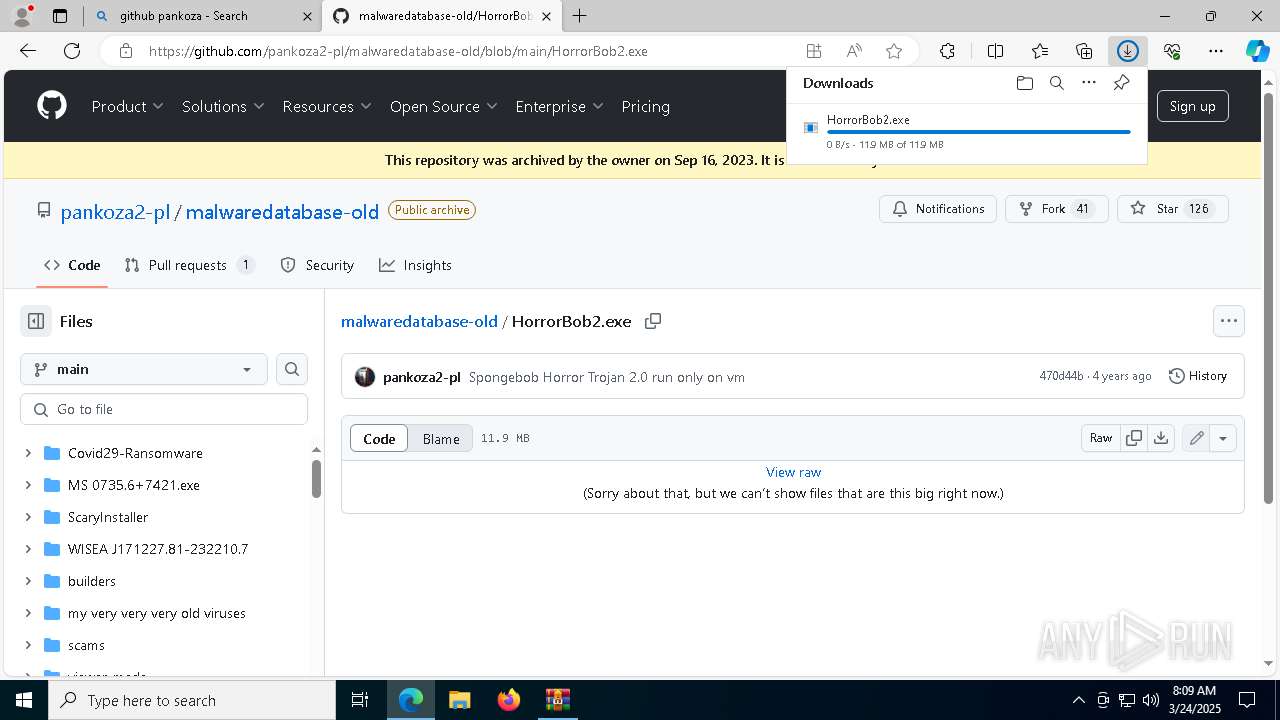
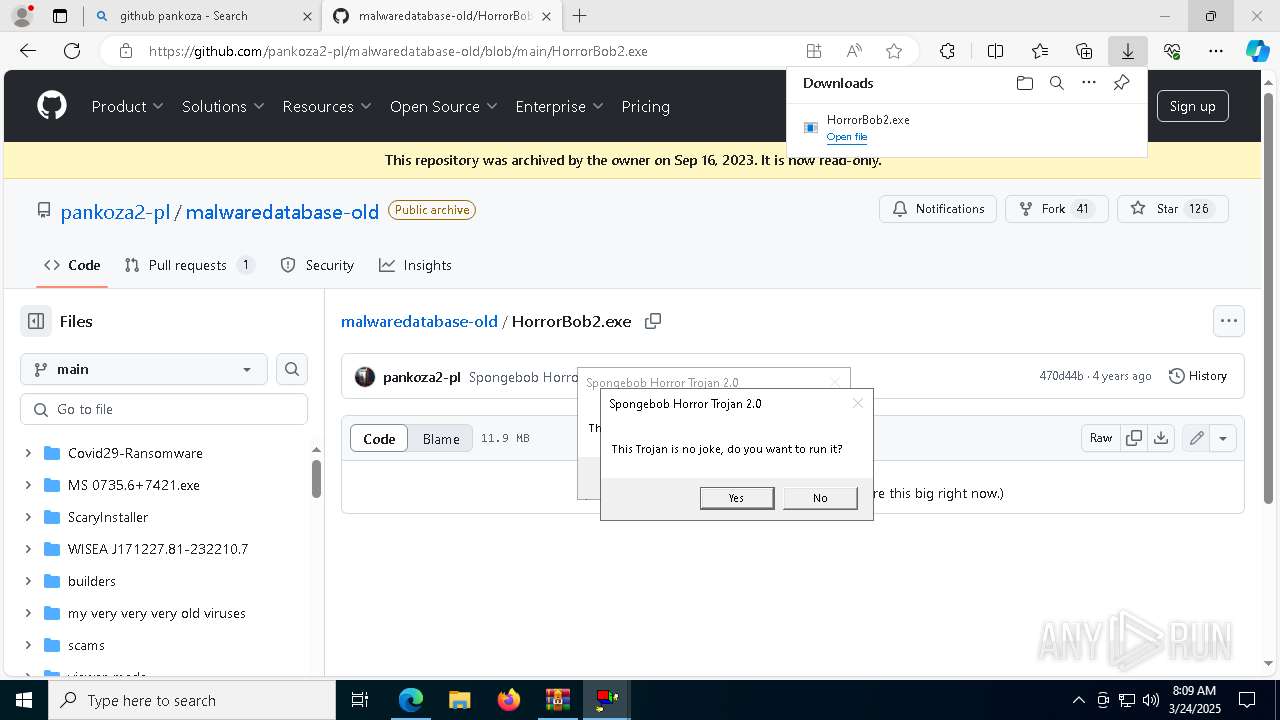
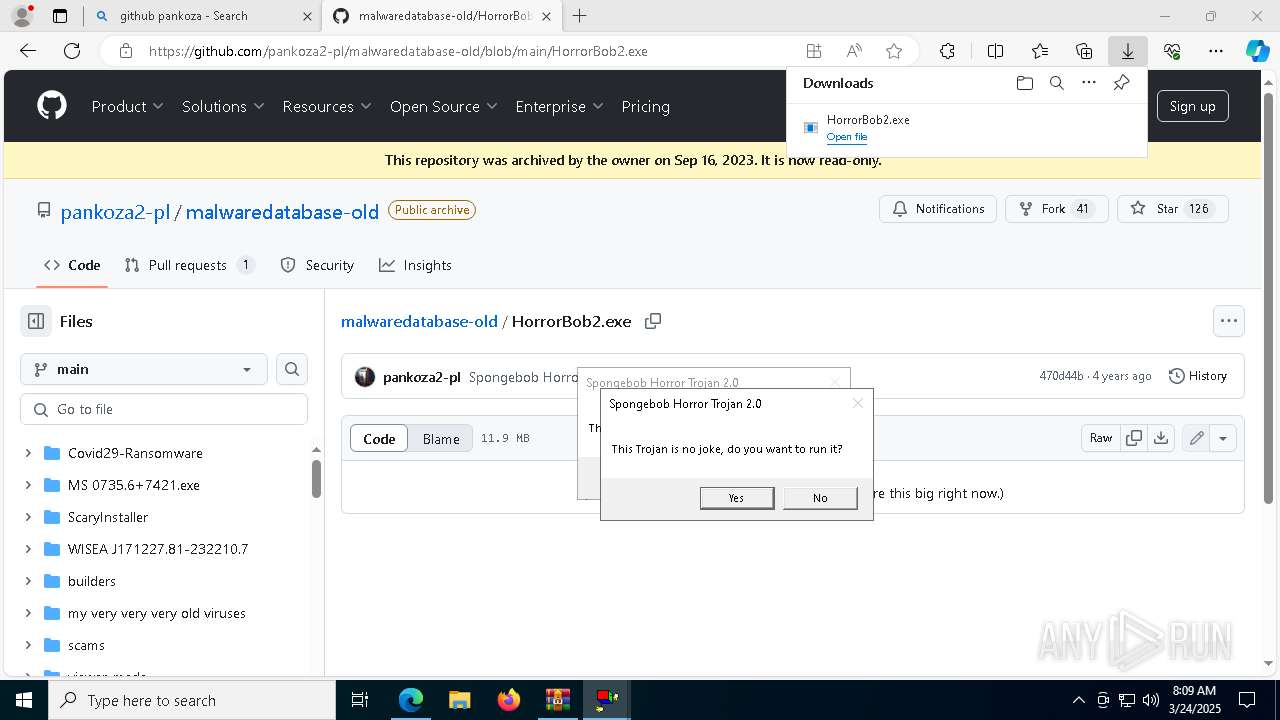
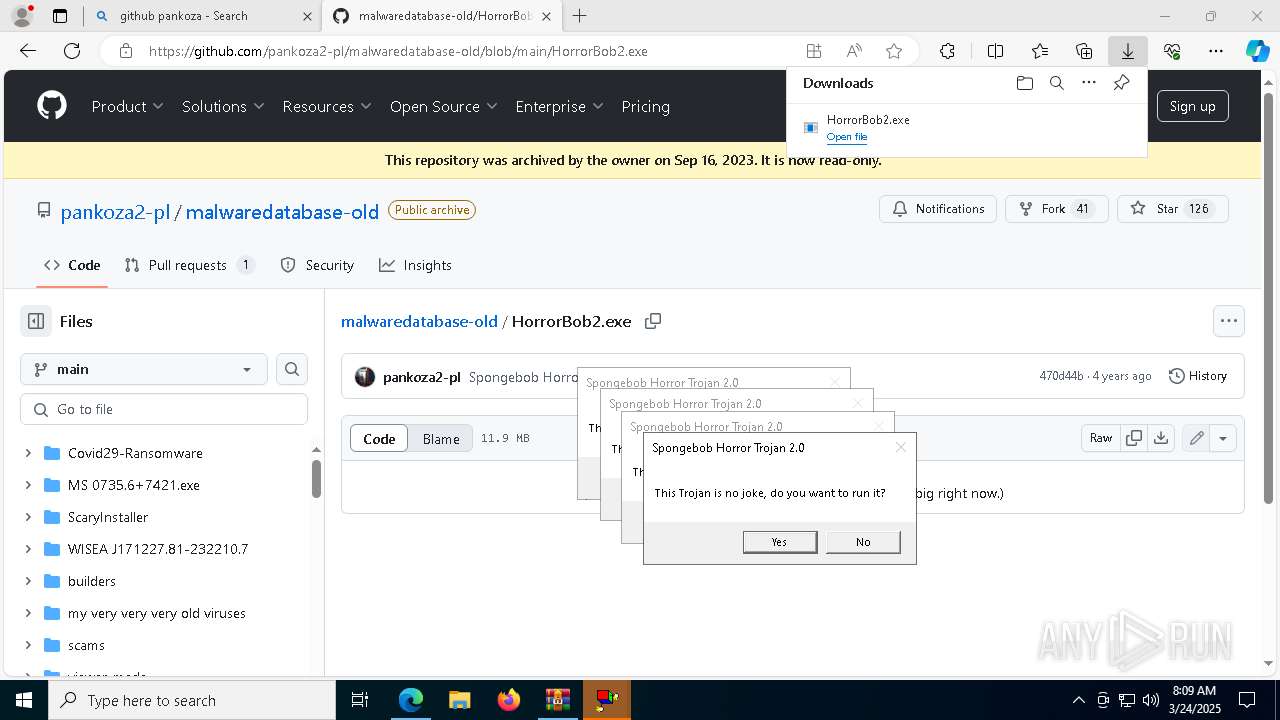
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 8356)
- HorrorBob2.exe (PID: 8328)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 6452)
- Service64.exe (PID: 6408)
- endpc.exe (PID: 5860)
Reads security settings of Internet Explorer
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 8356)
- ShellExperienceHost.exe (PID: 8940)
Starts CMD.EXE for commands execution
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 8328)
- HorrorBob2.exe (PID: 8356)
- Service64.exe (PID: 6408)
- RulesLauncher.exe (PID: 6568)
- BobLauncher.exe (PID: 6560)
Executing commands from a ".bat" file
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 8328)
- HorrorBob2.exe (PID: 8356)
- Service64.exe (PID: 6408)
- RulesLauncher.exe (PID: 6568)
- BobLauncher.exe (PID: 6560)
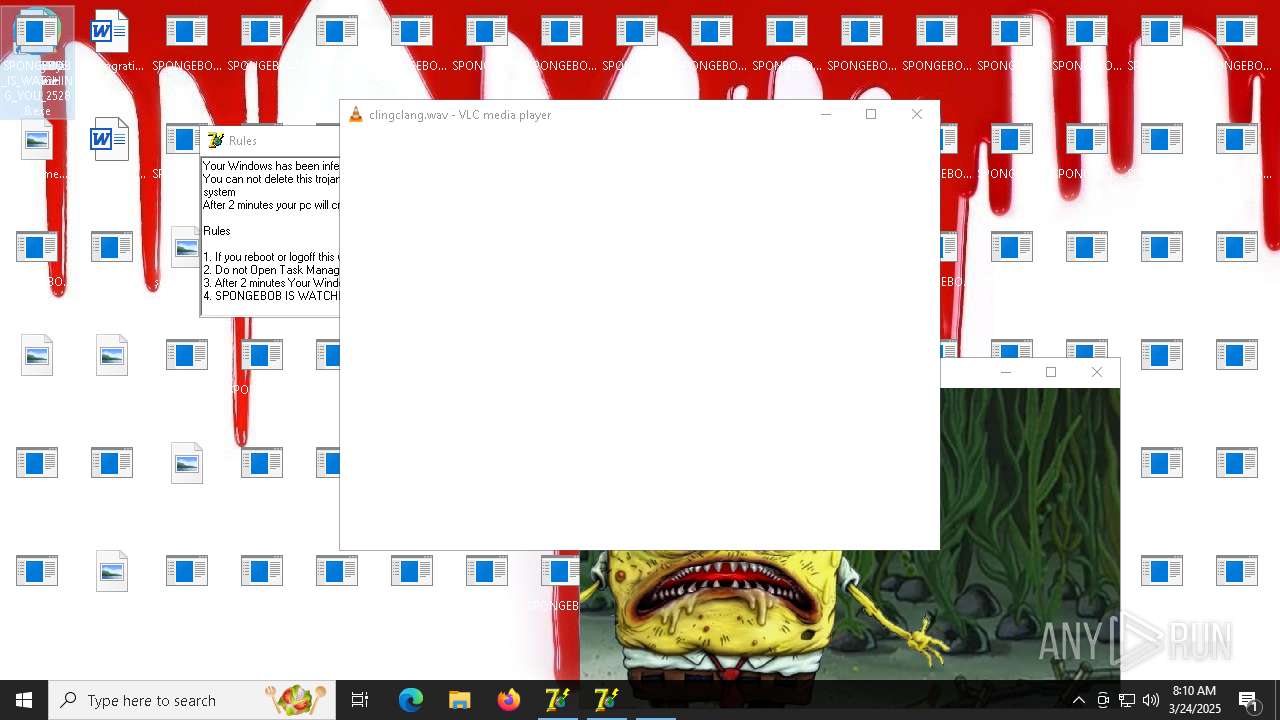
The process executes VB scripts
- cmd.exe (PID: 8116)
- cmd.exe (PID: 3300)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 4628)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 8484)
- cmd.exe (PID: 8528)
- cmd.exe (PID: 6452)
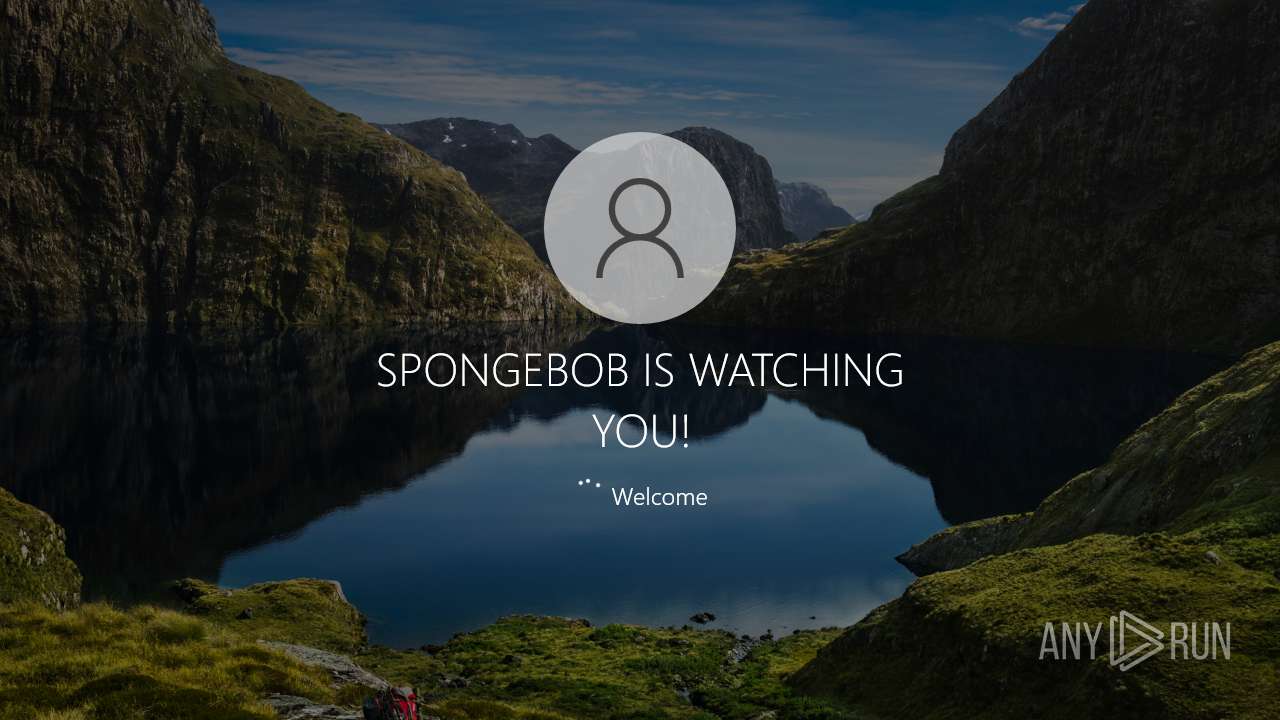
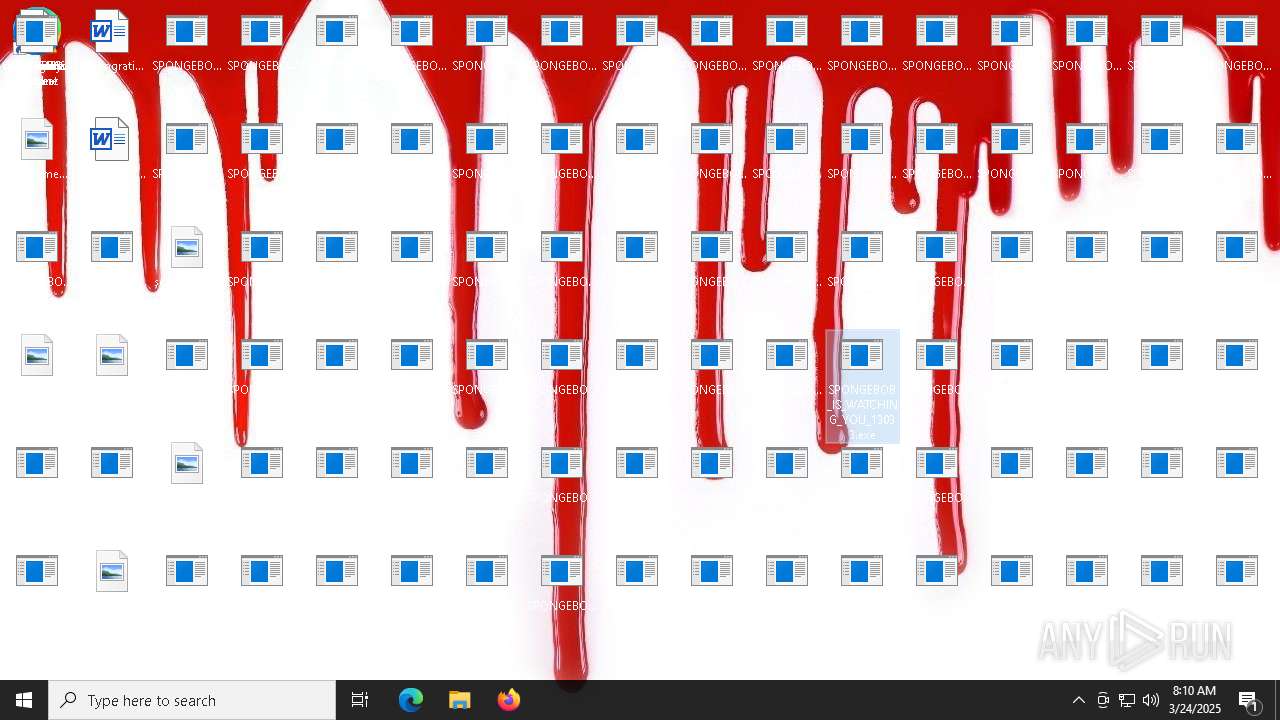
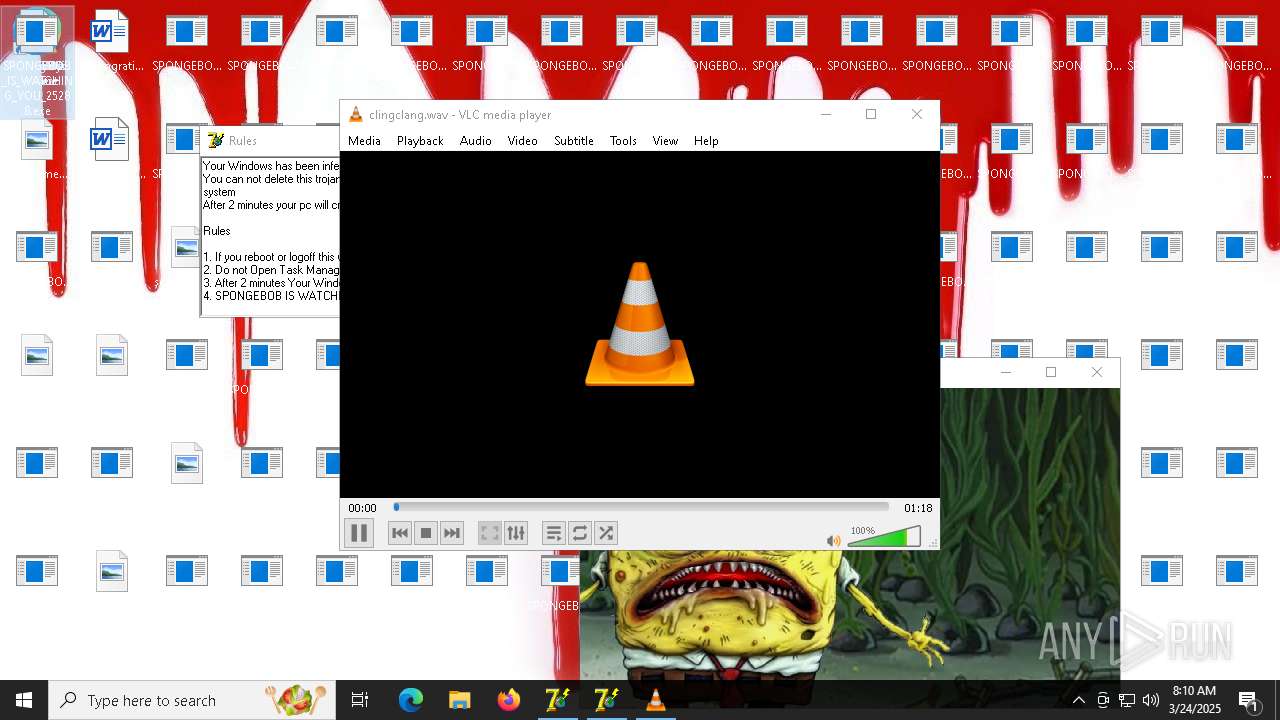
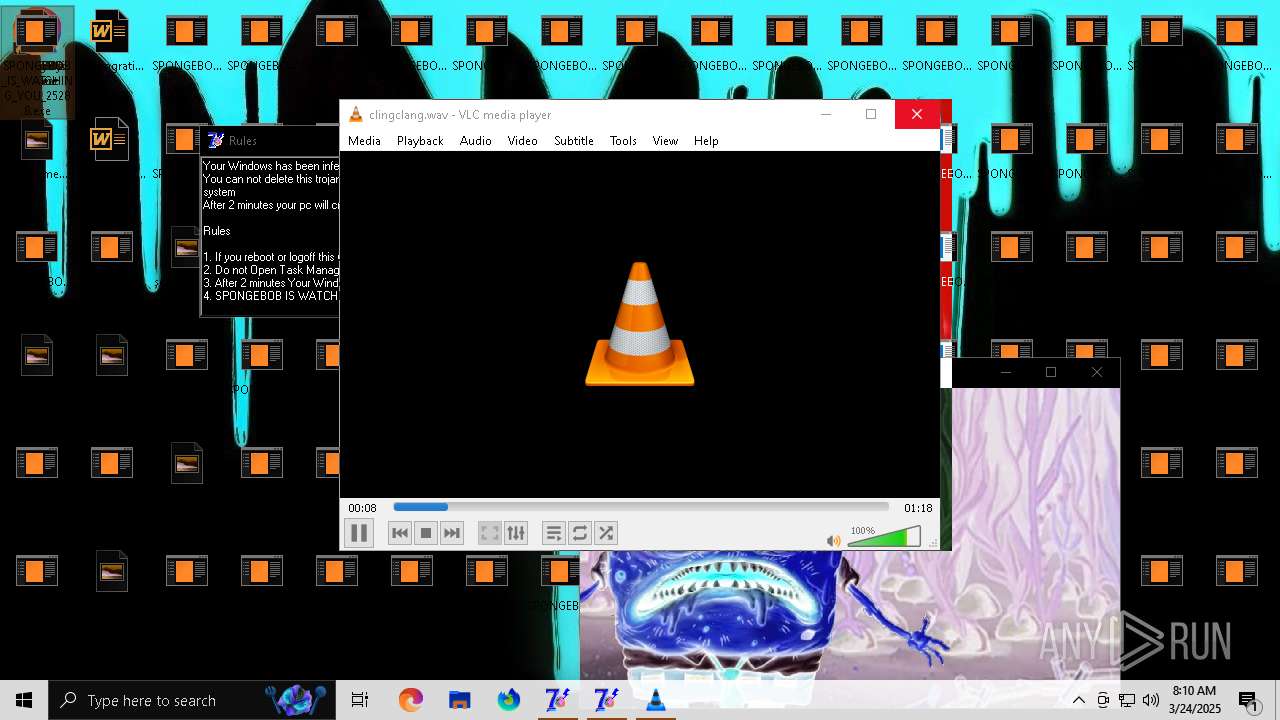
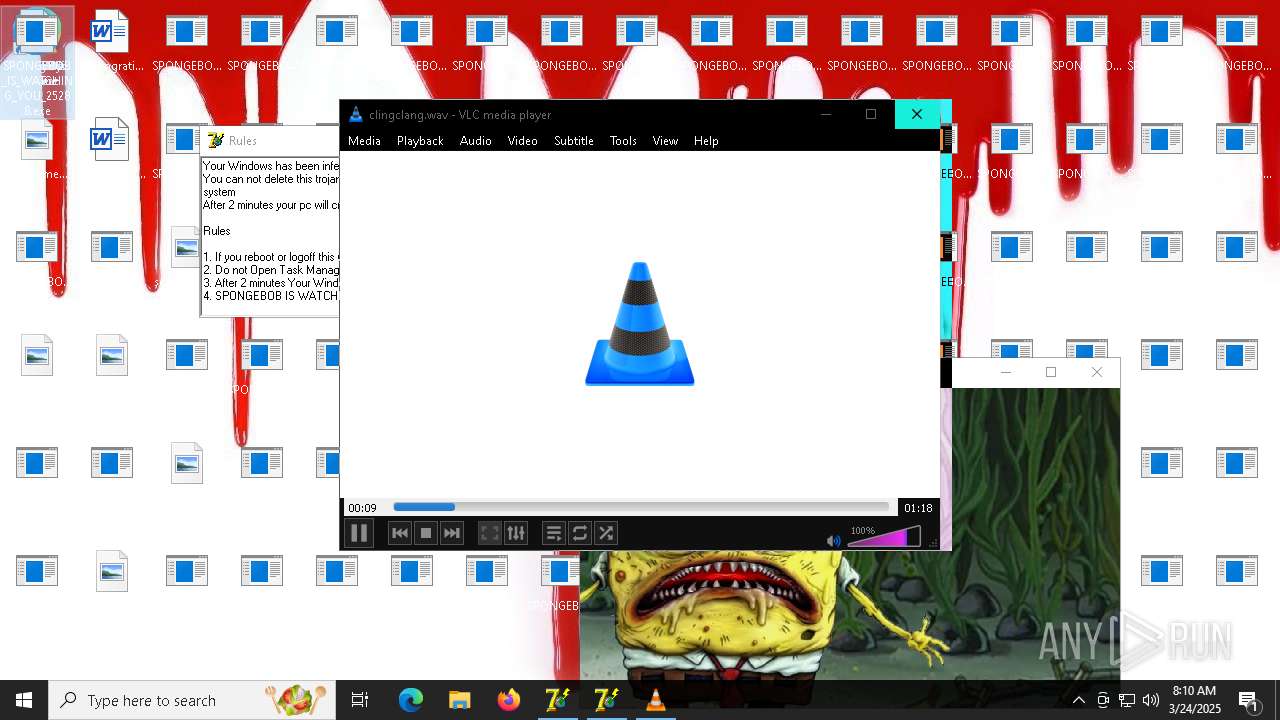
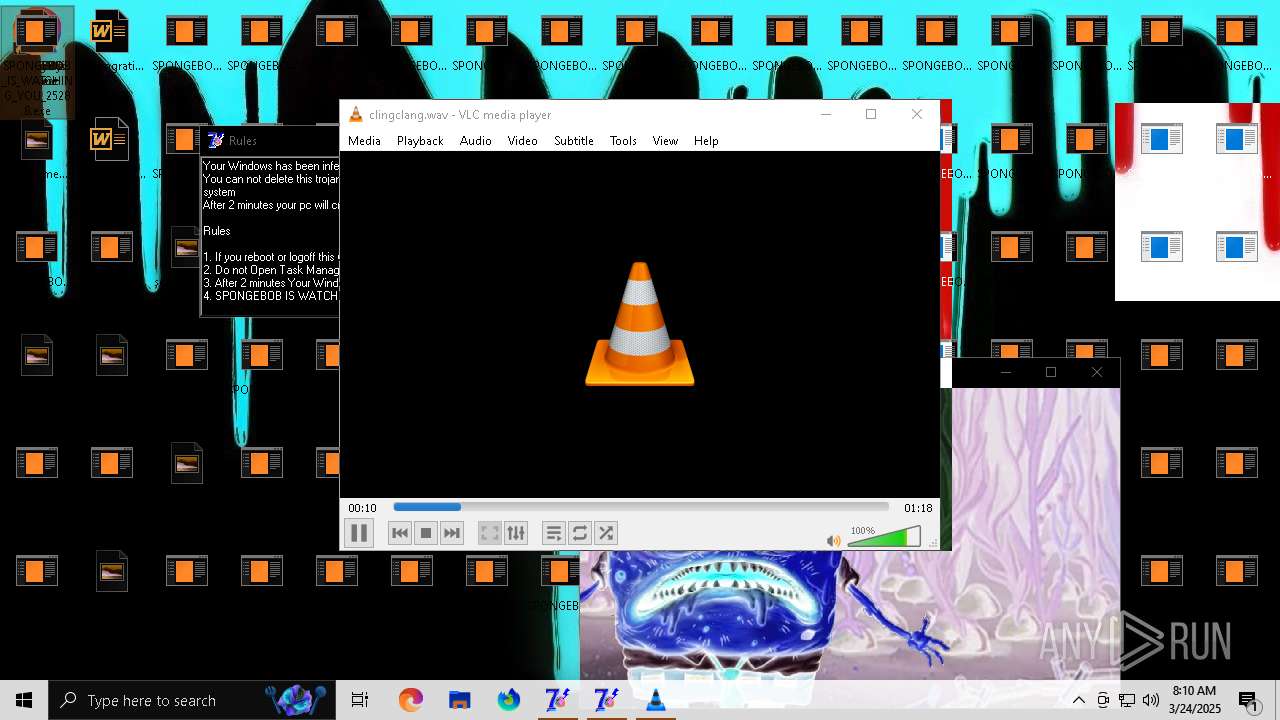
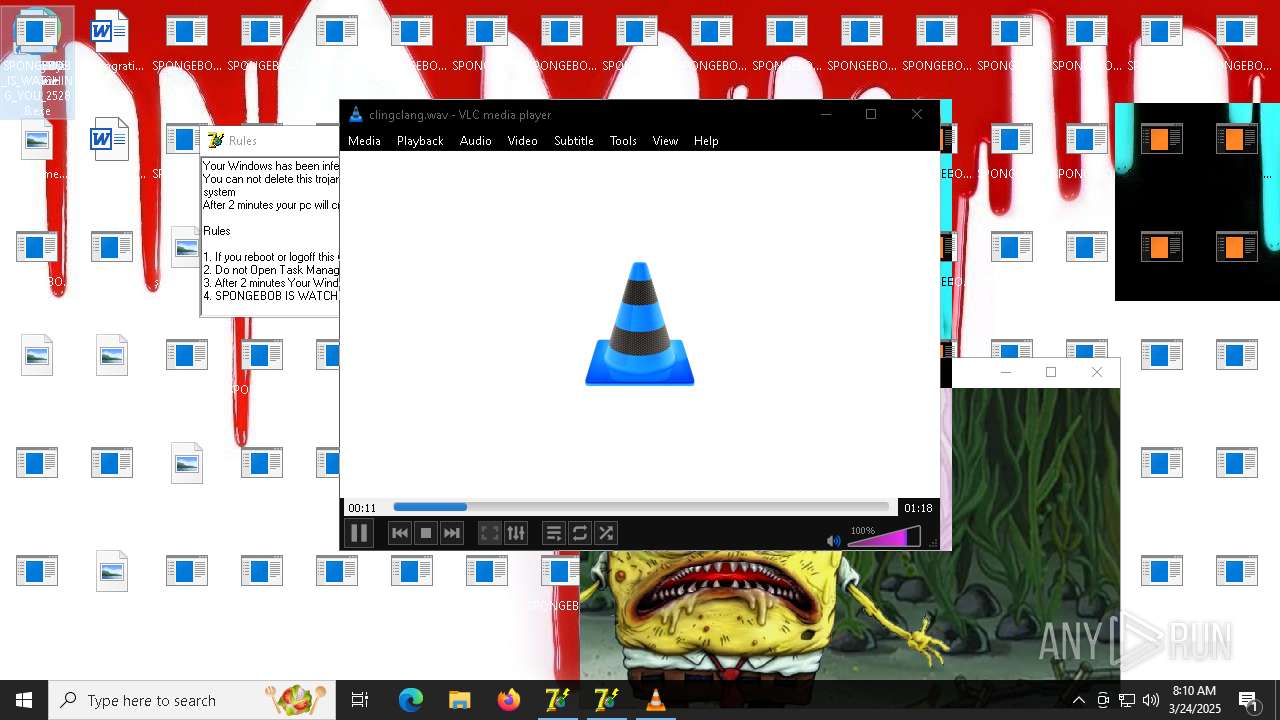
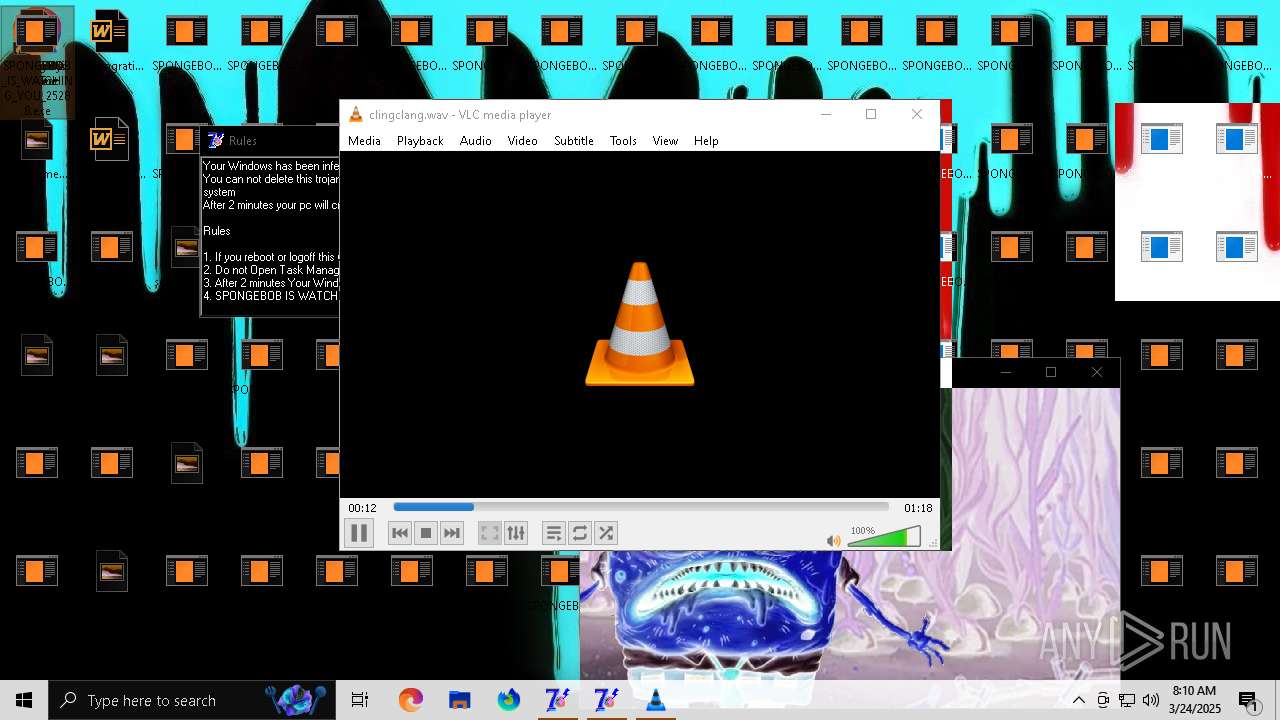
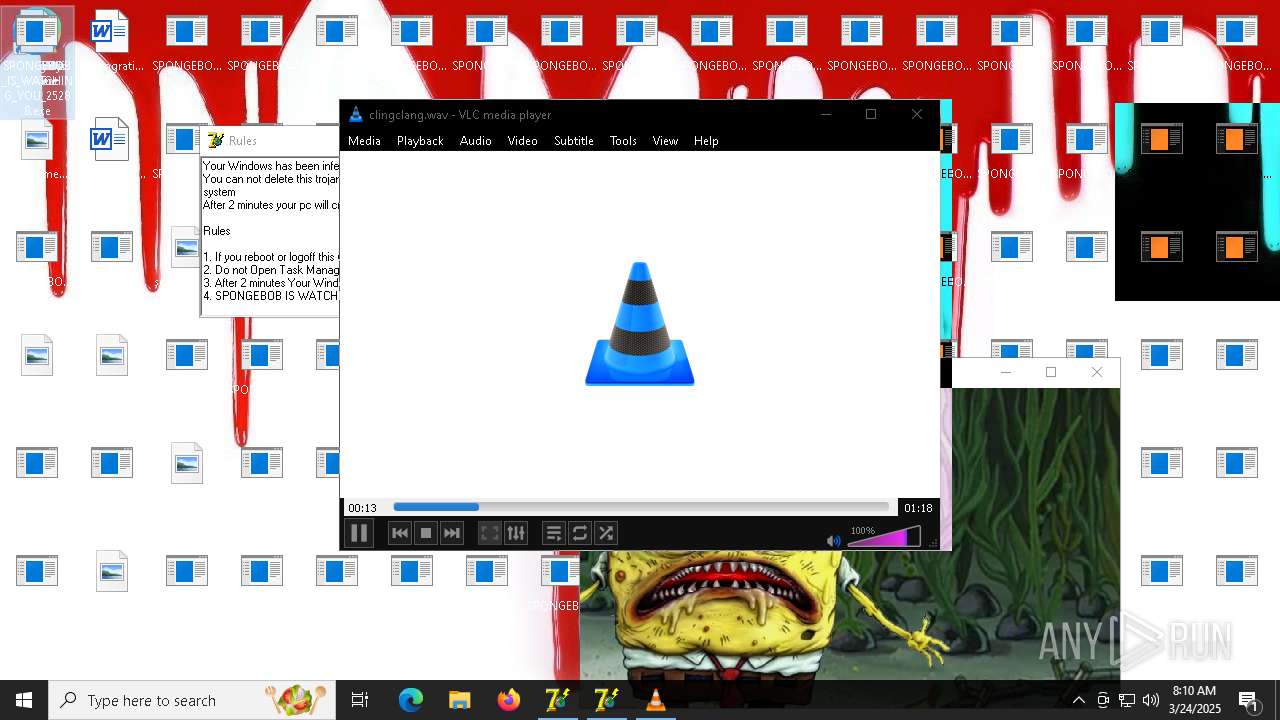
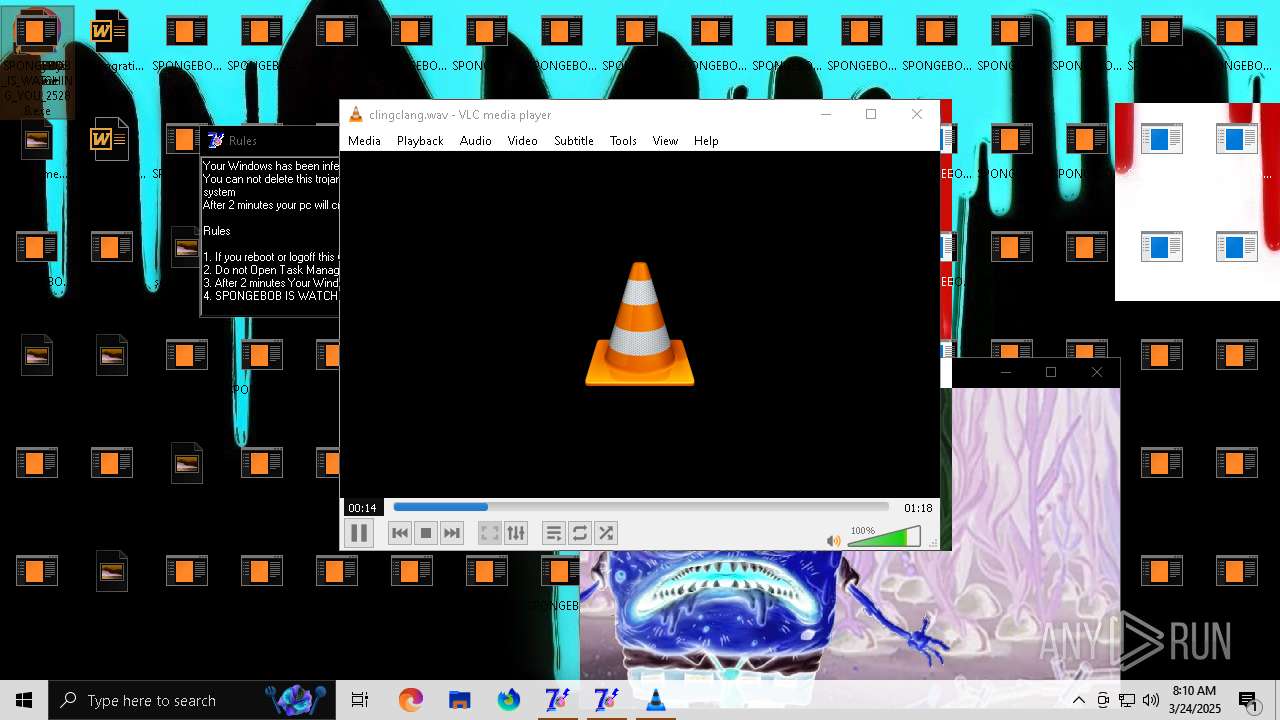
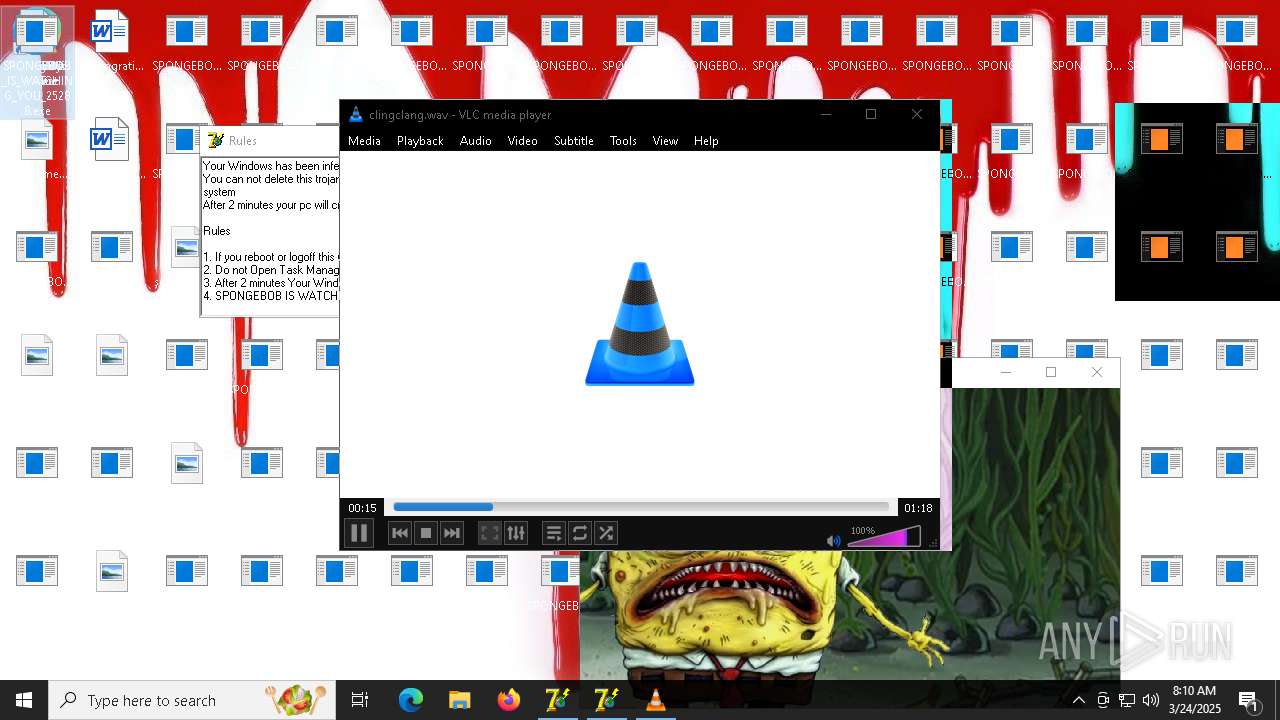
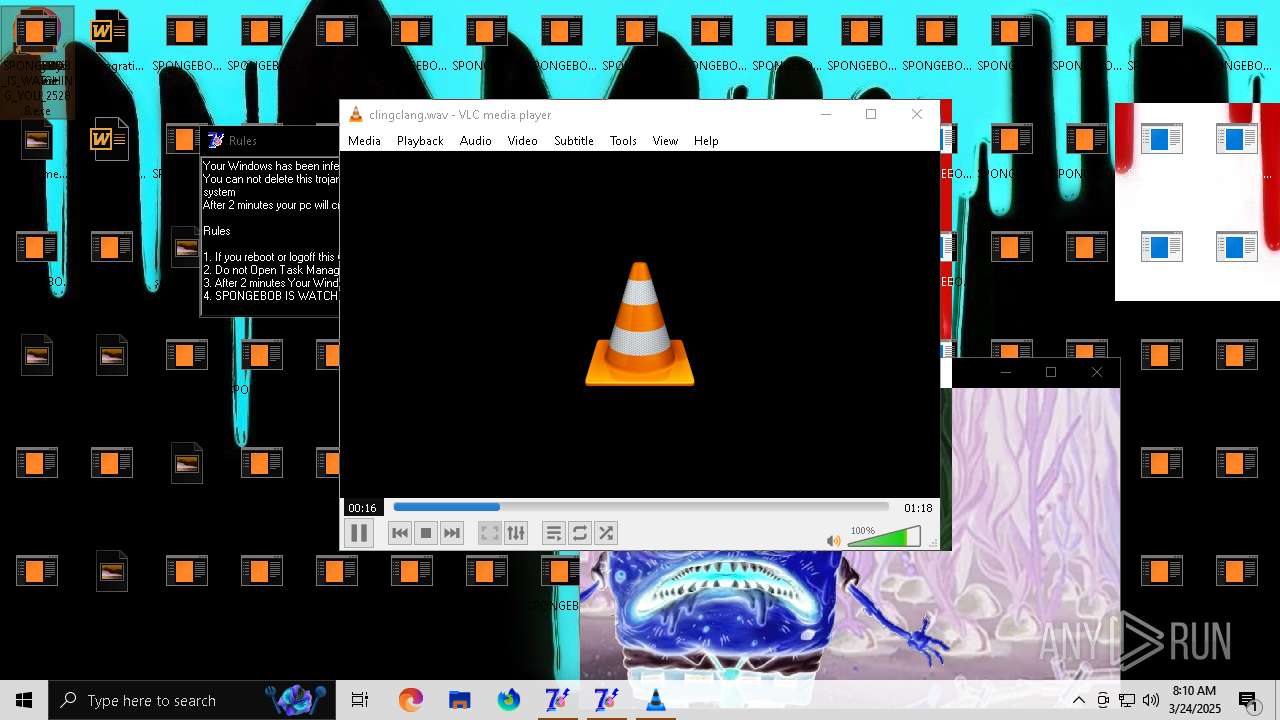
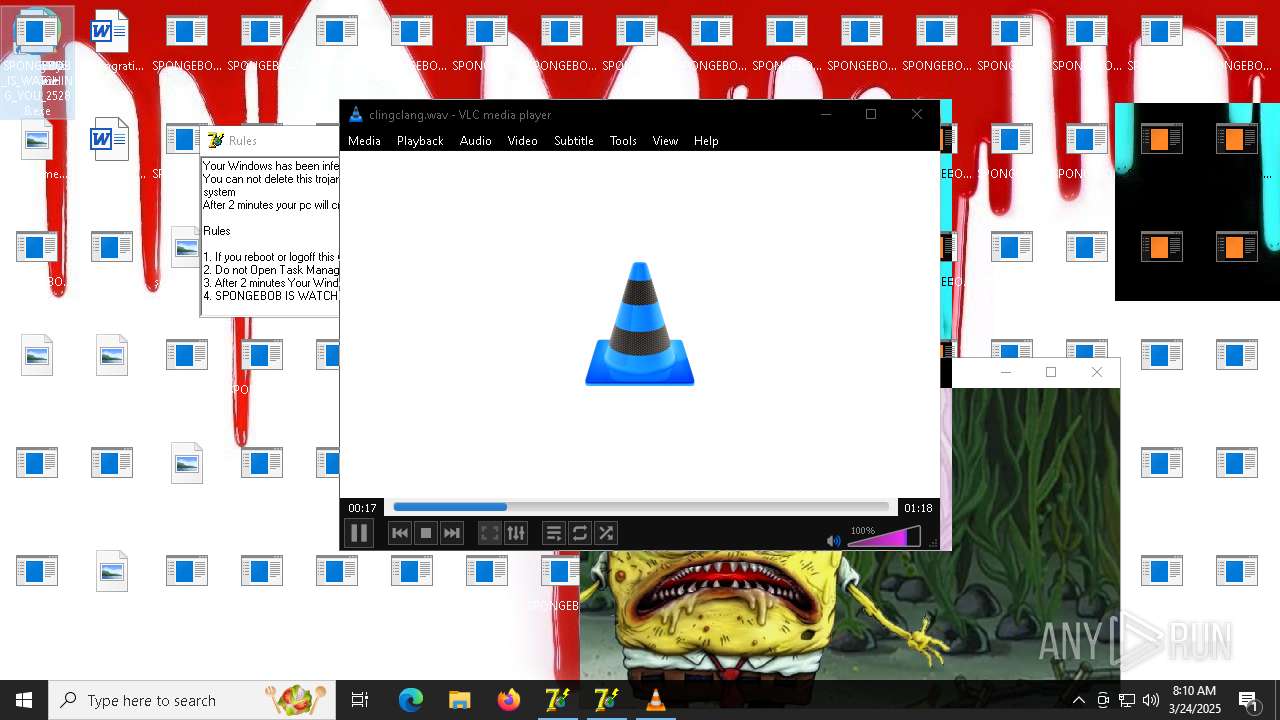
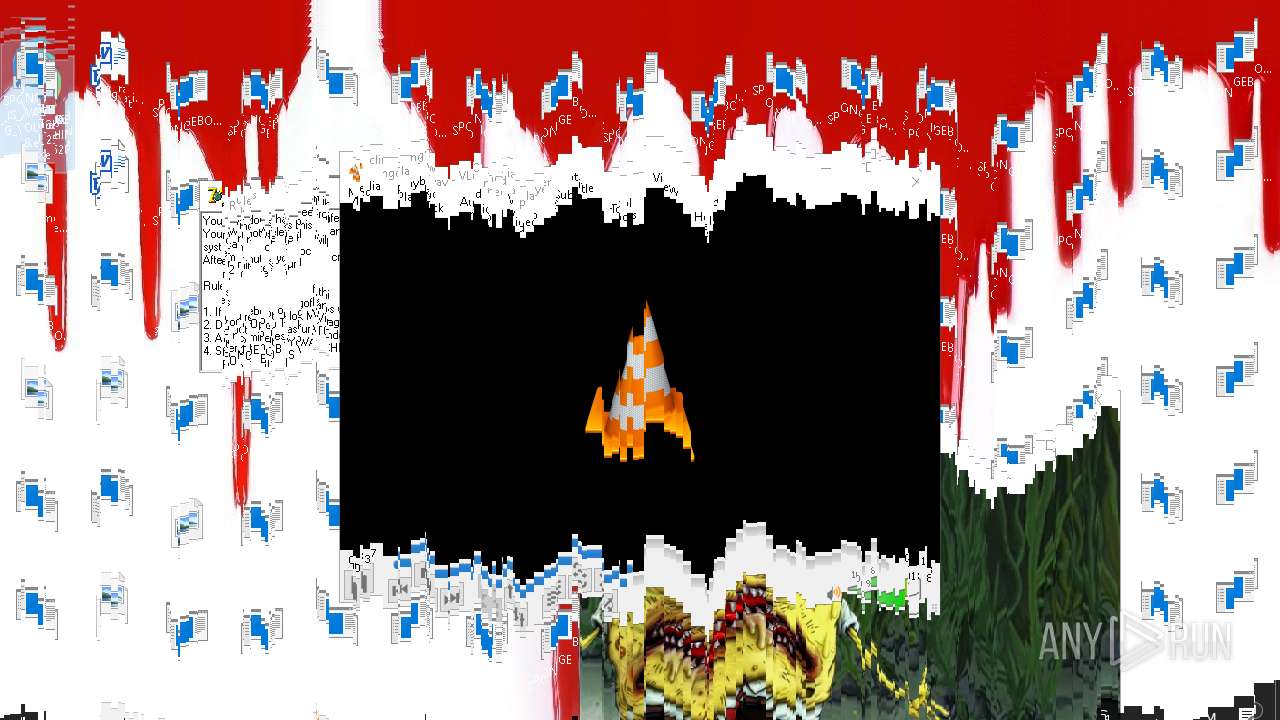
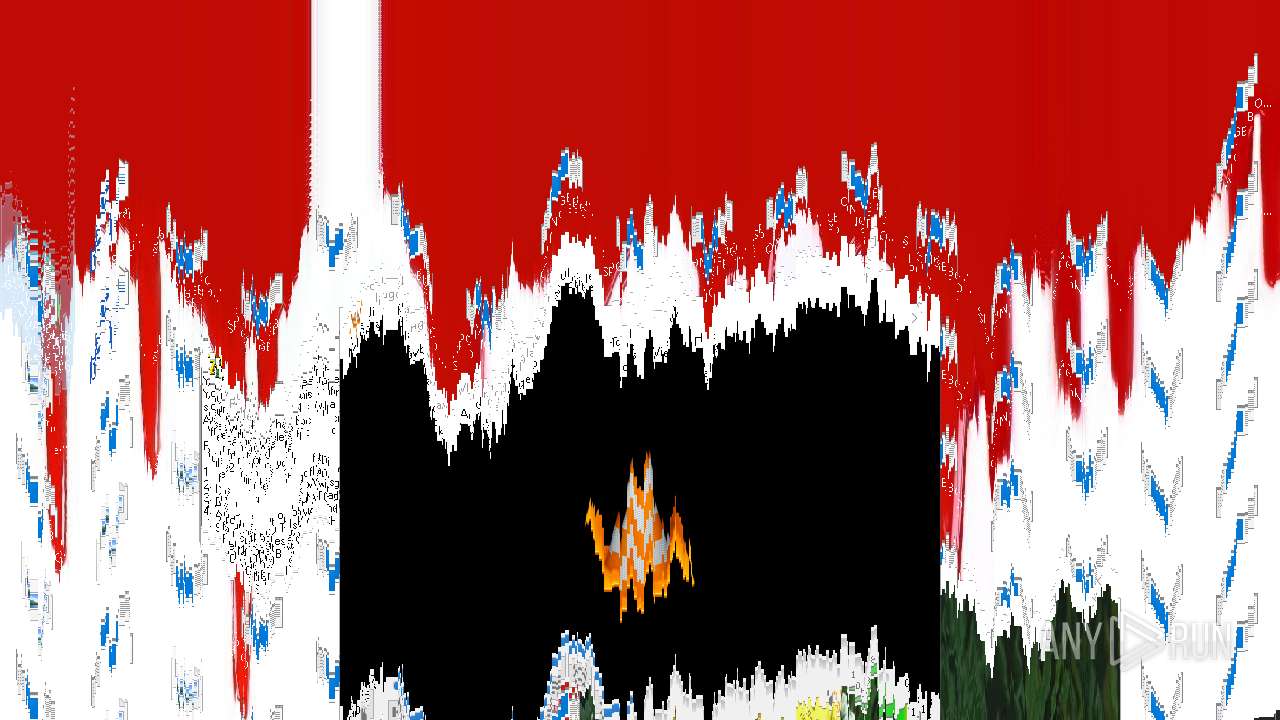
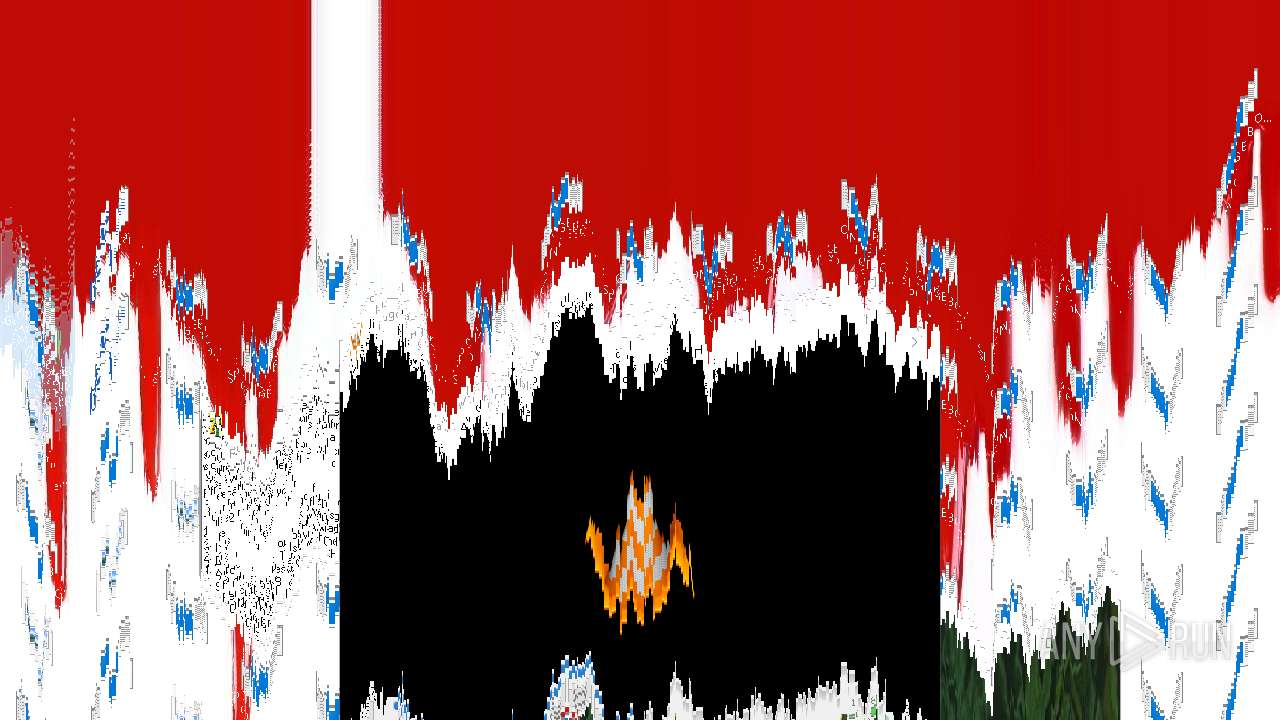
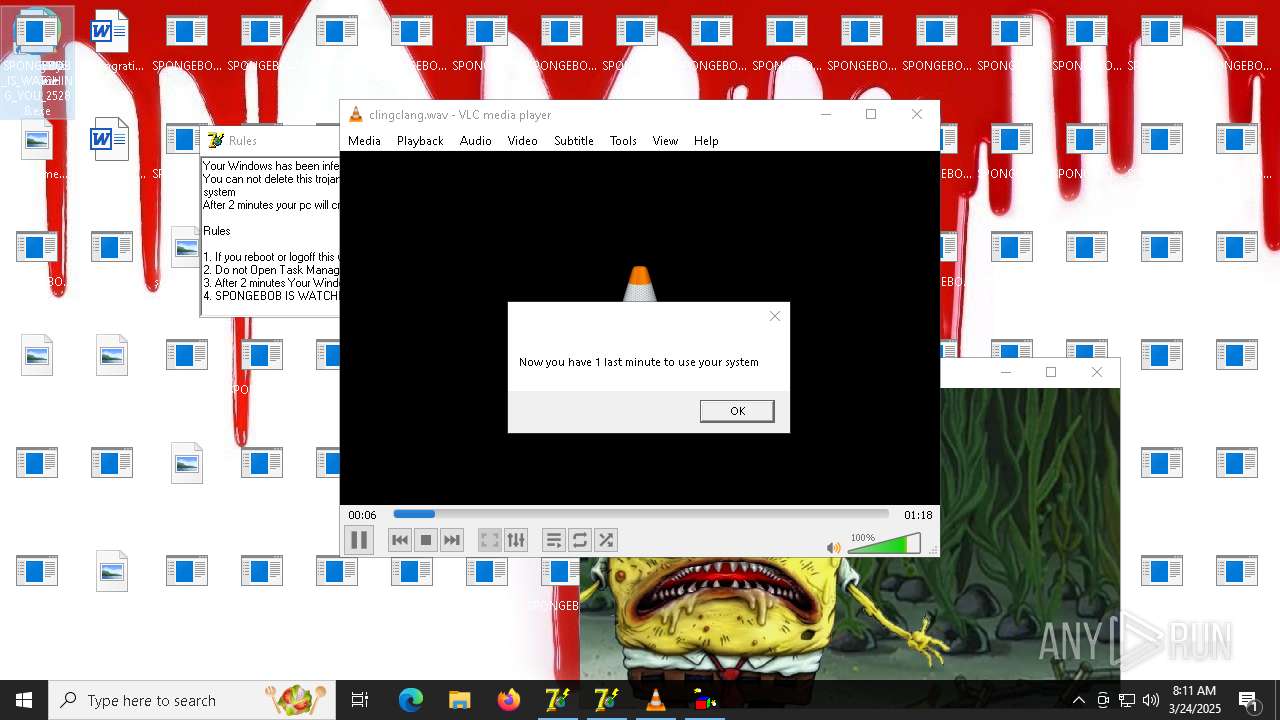
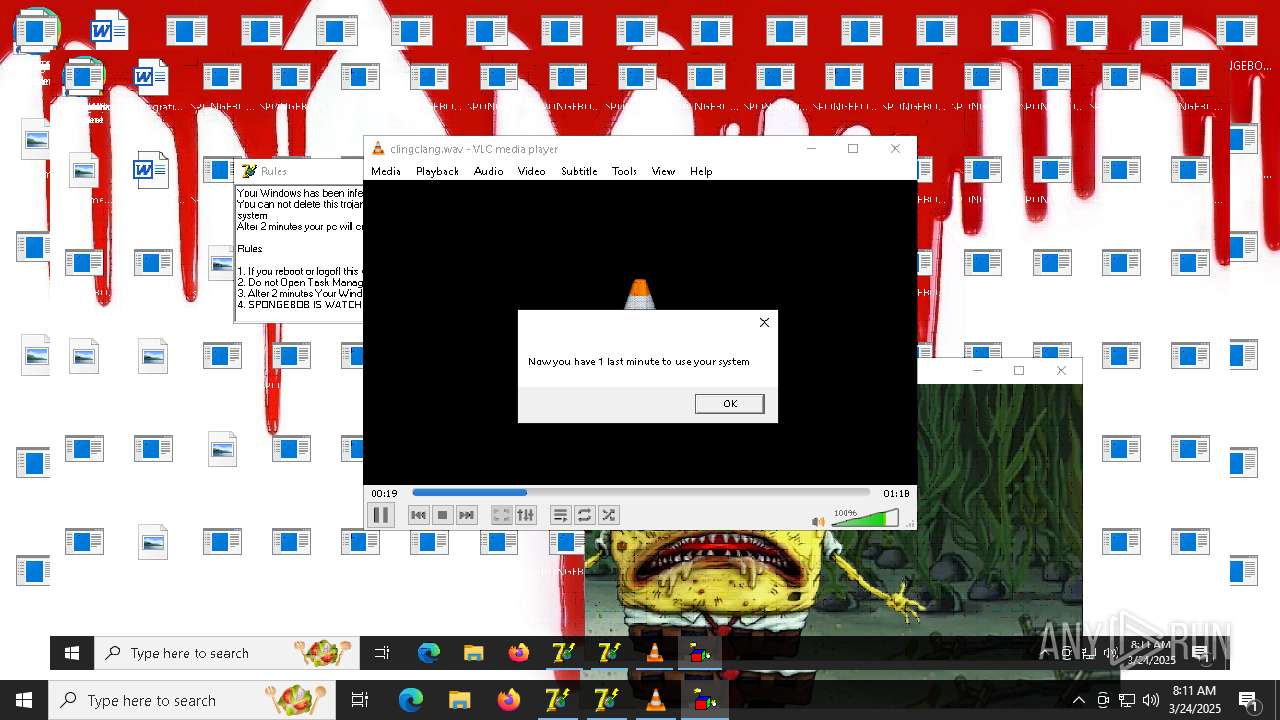
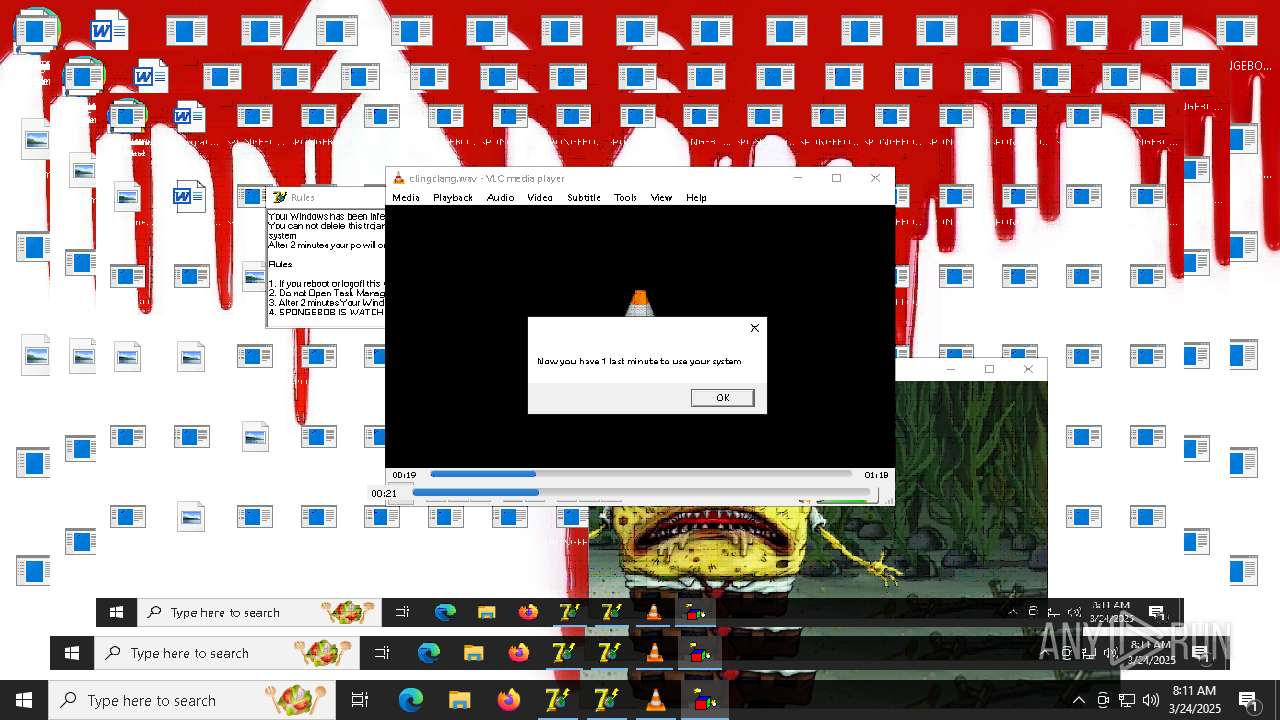
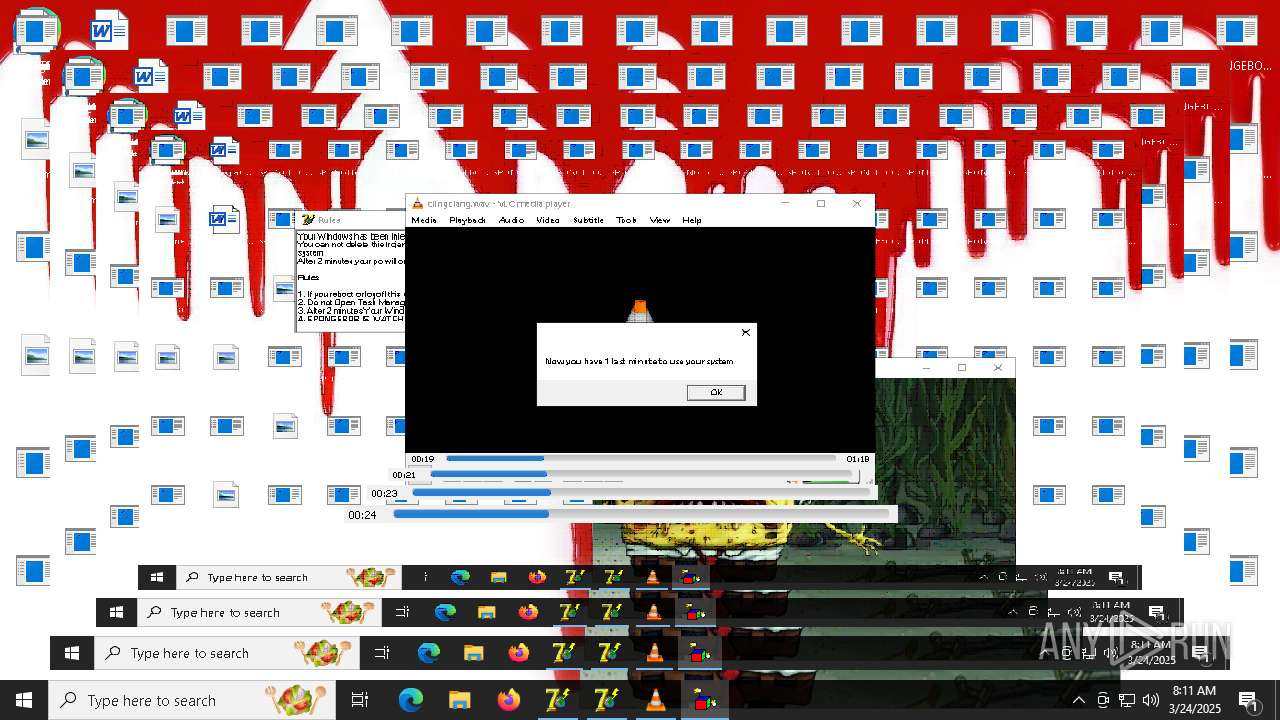
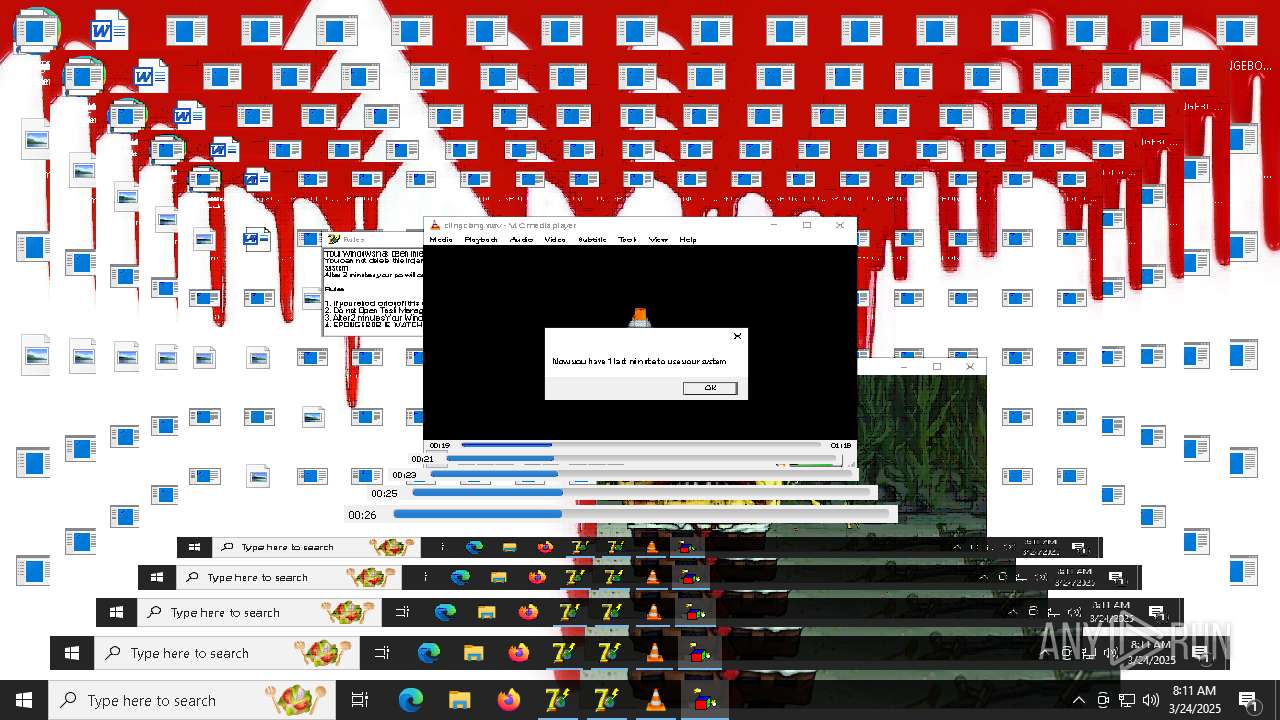
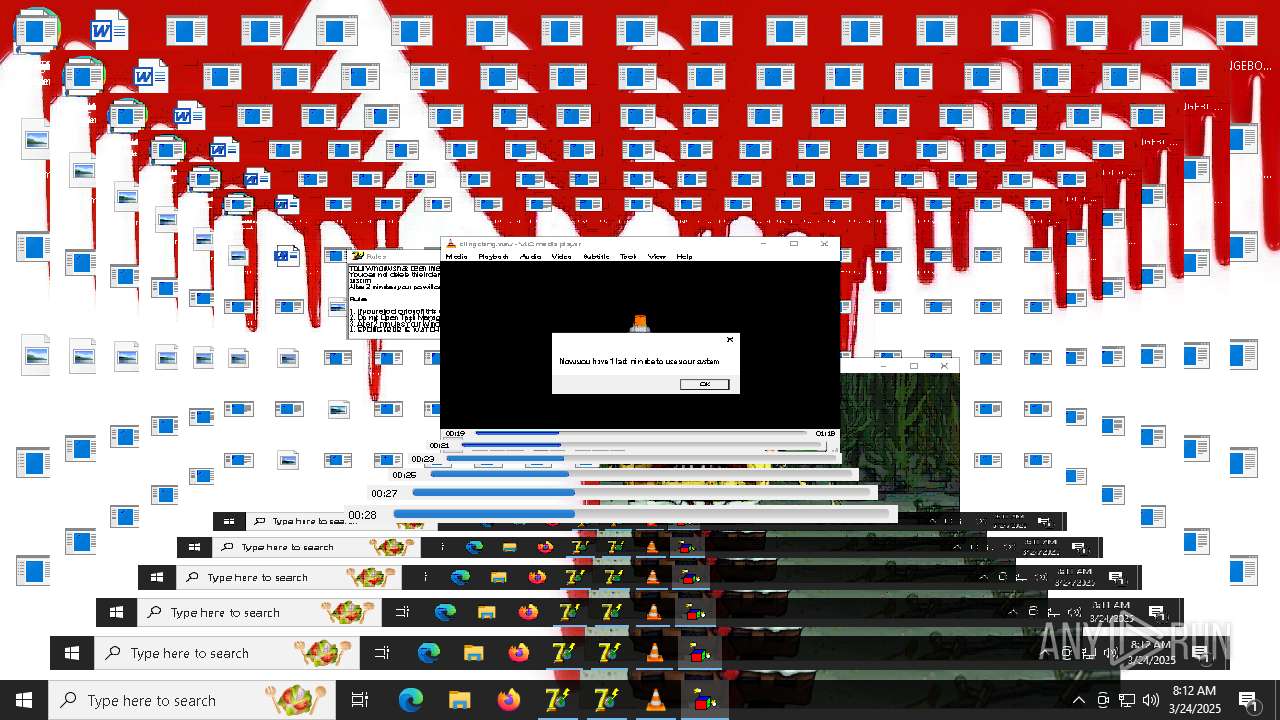
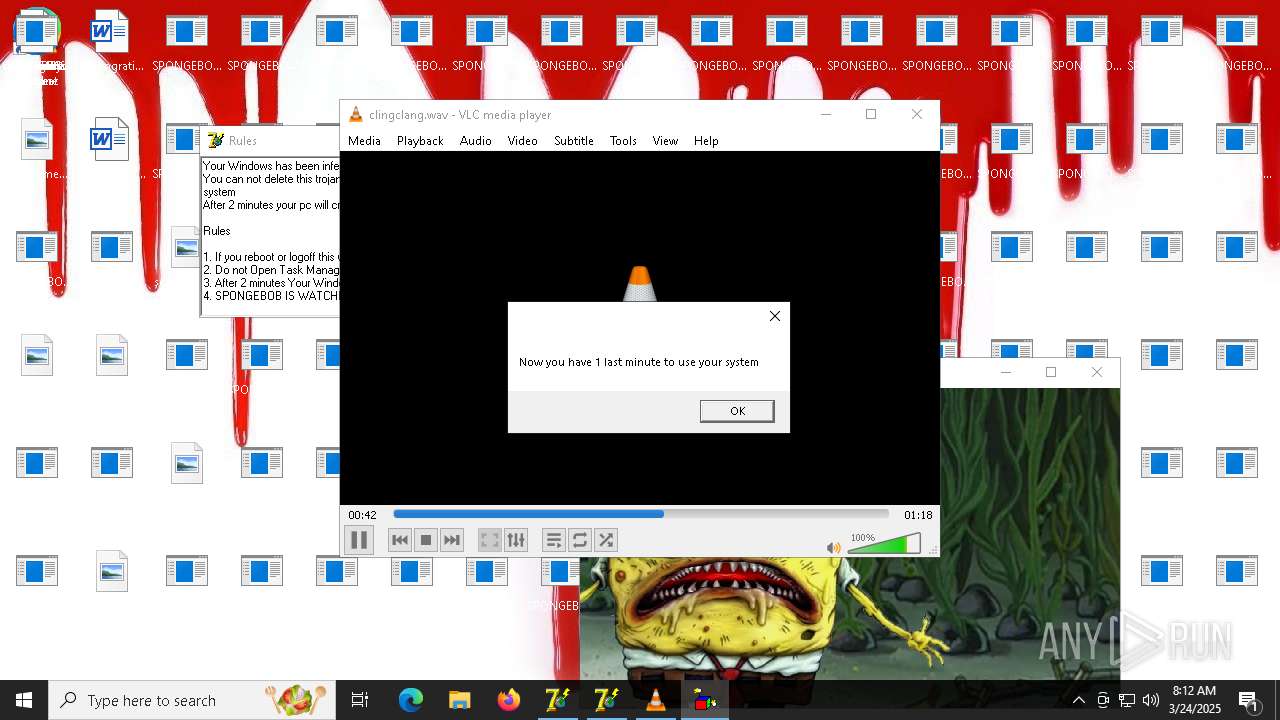
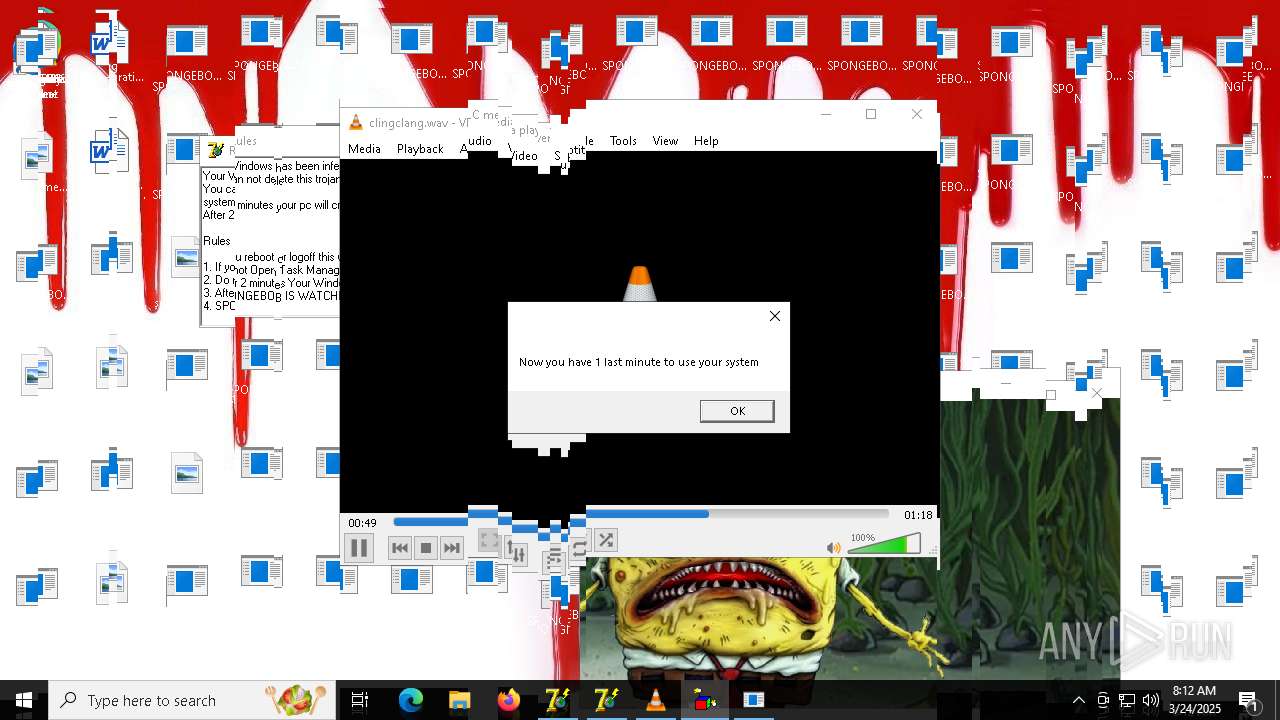
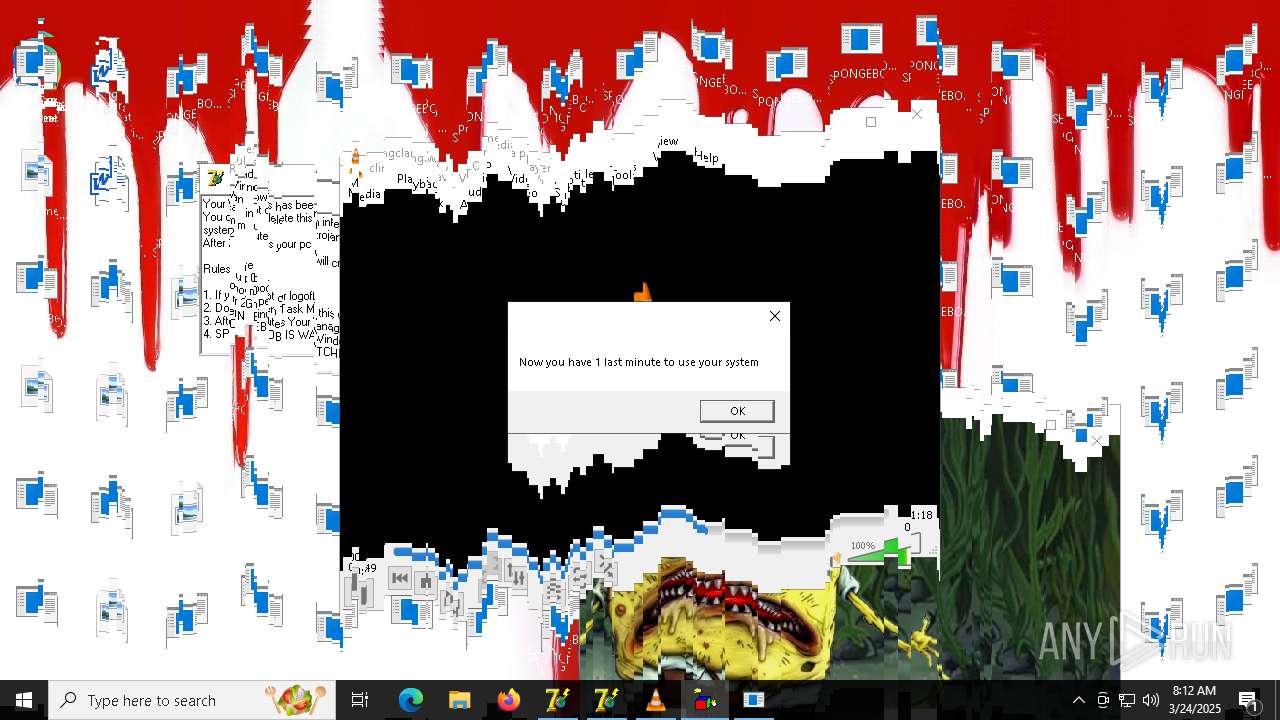
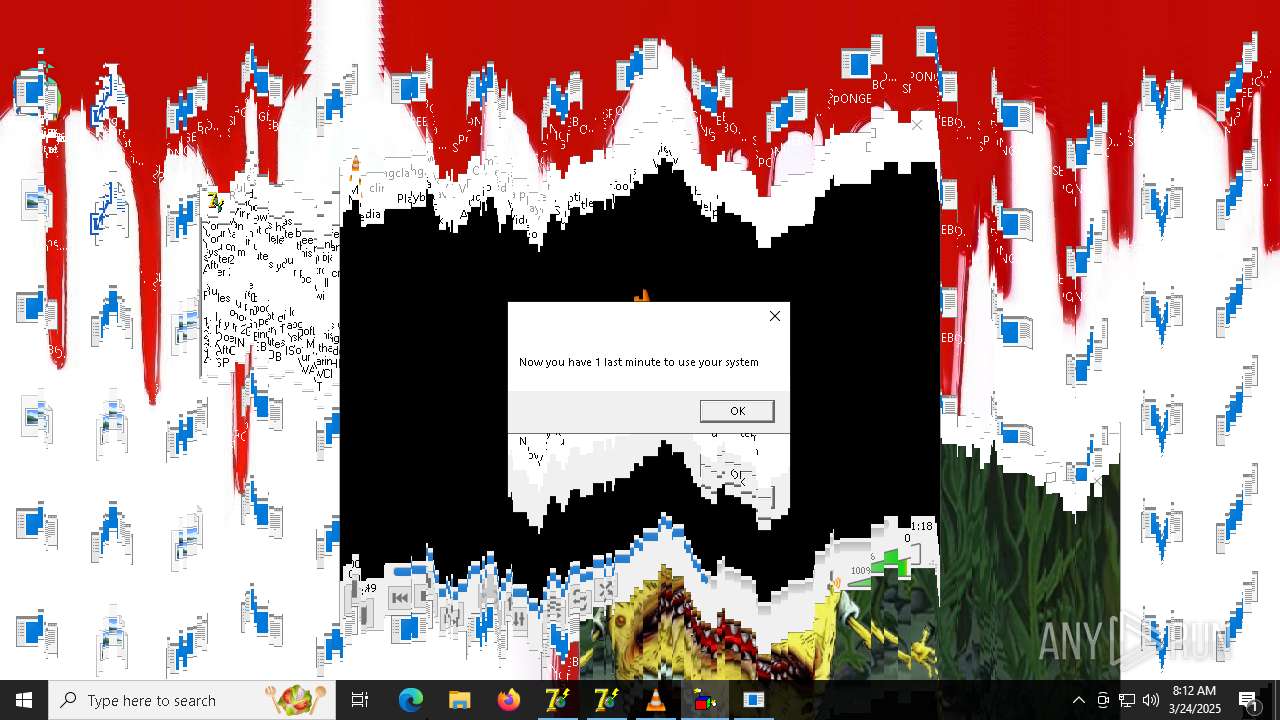
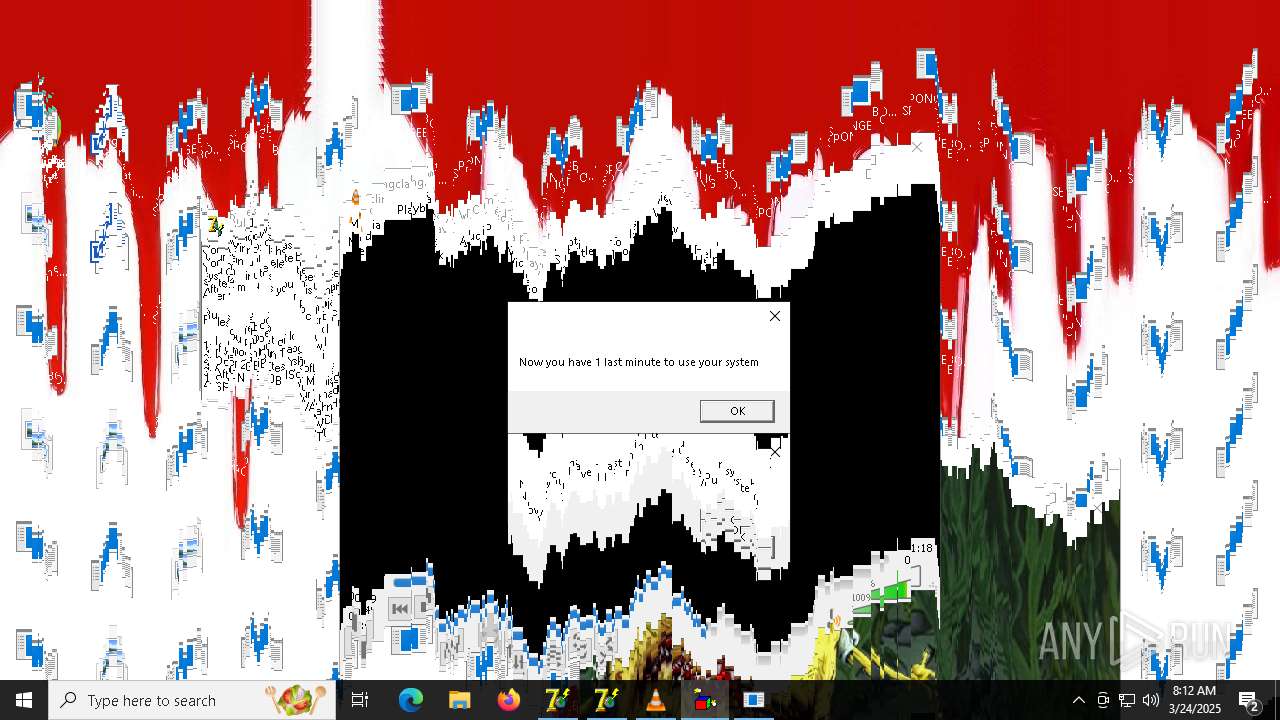
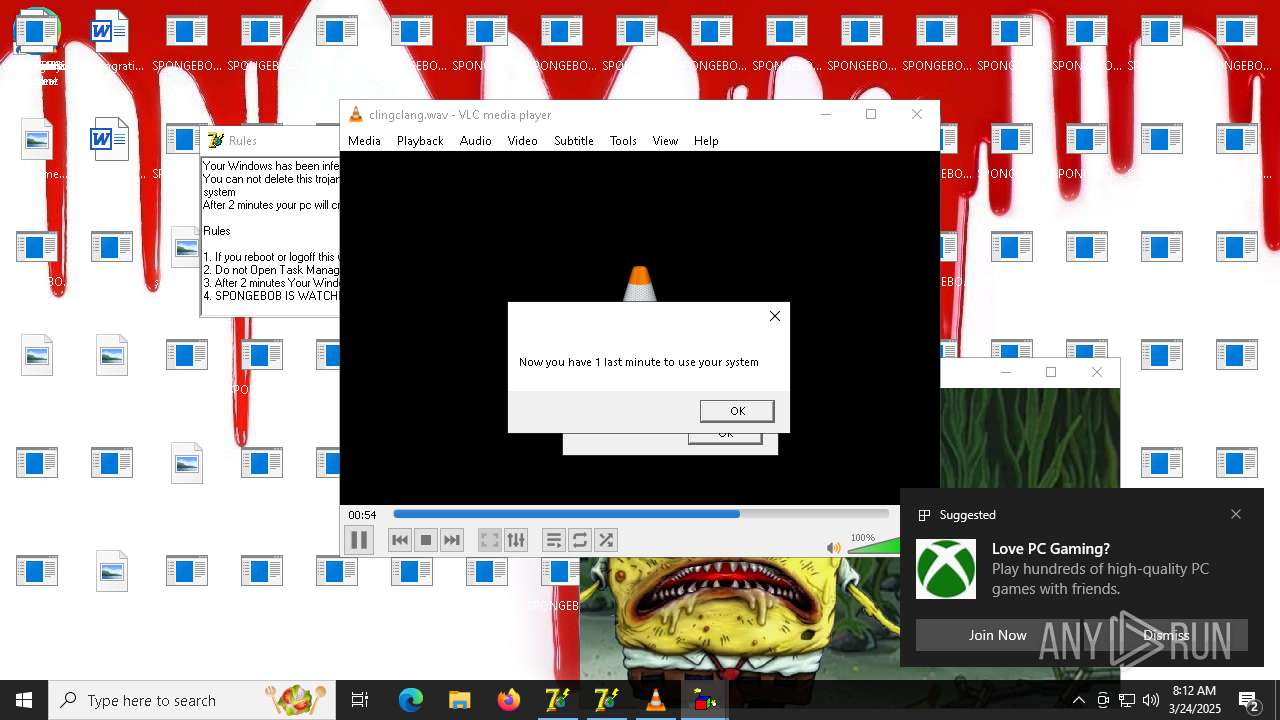
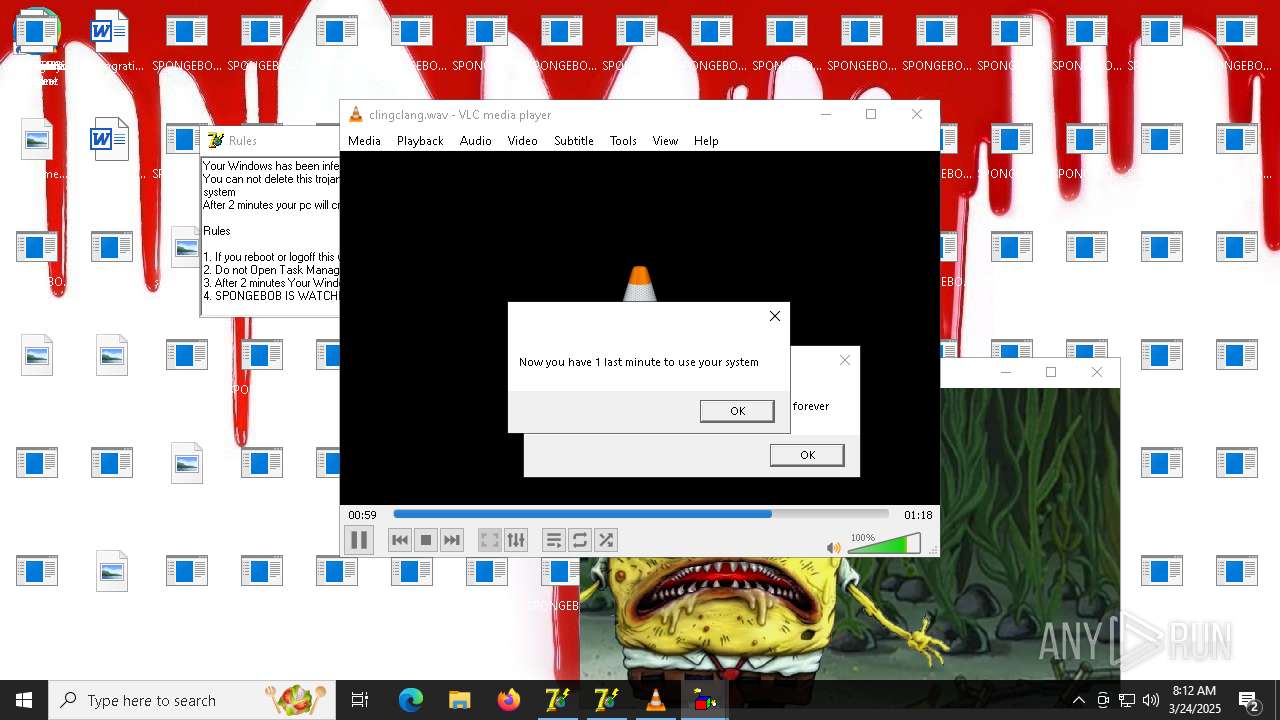
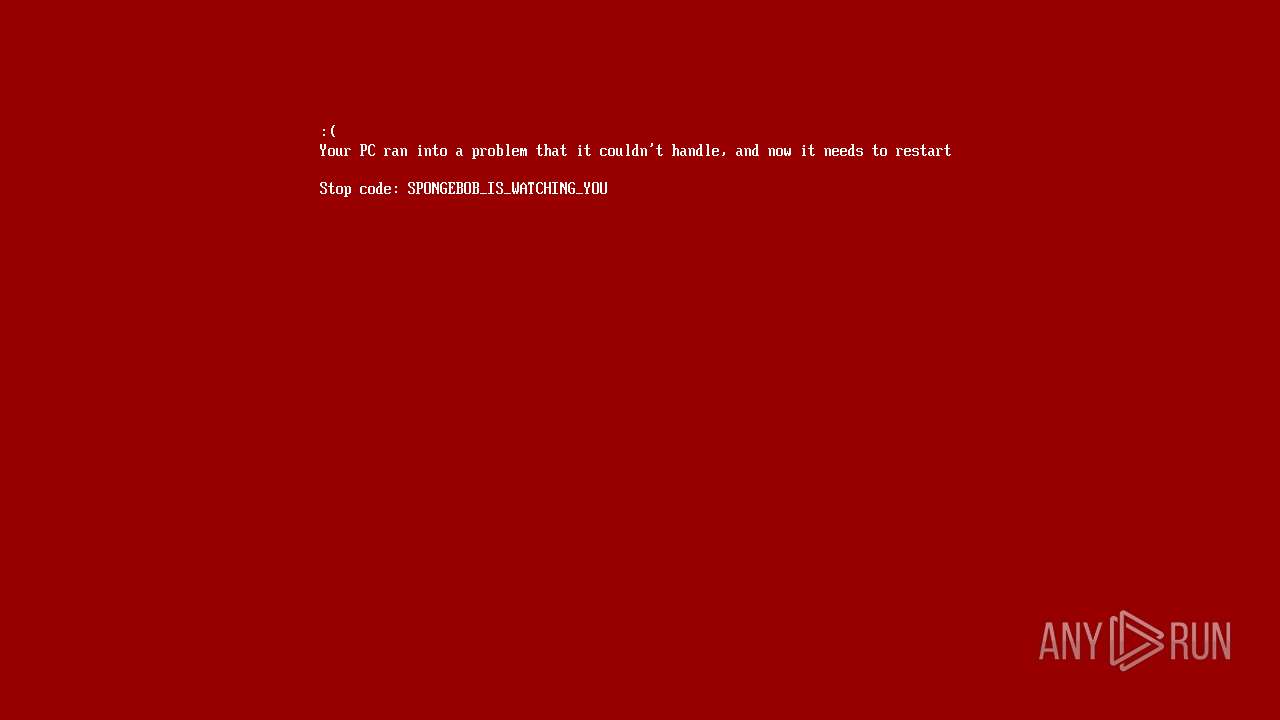
Changes the desktop background image
- reg.exe (PID: 8736)
- reg.exe (PID: 8692)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8528)
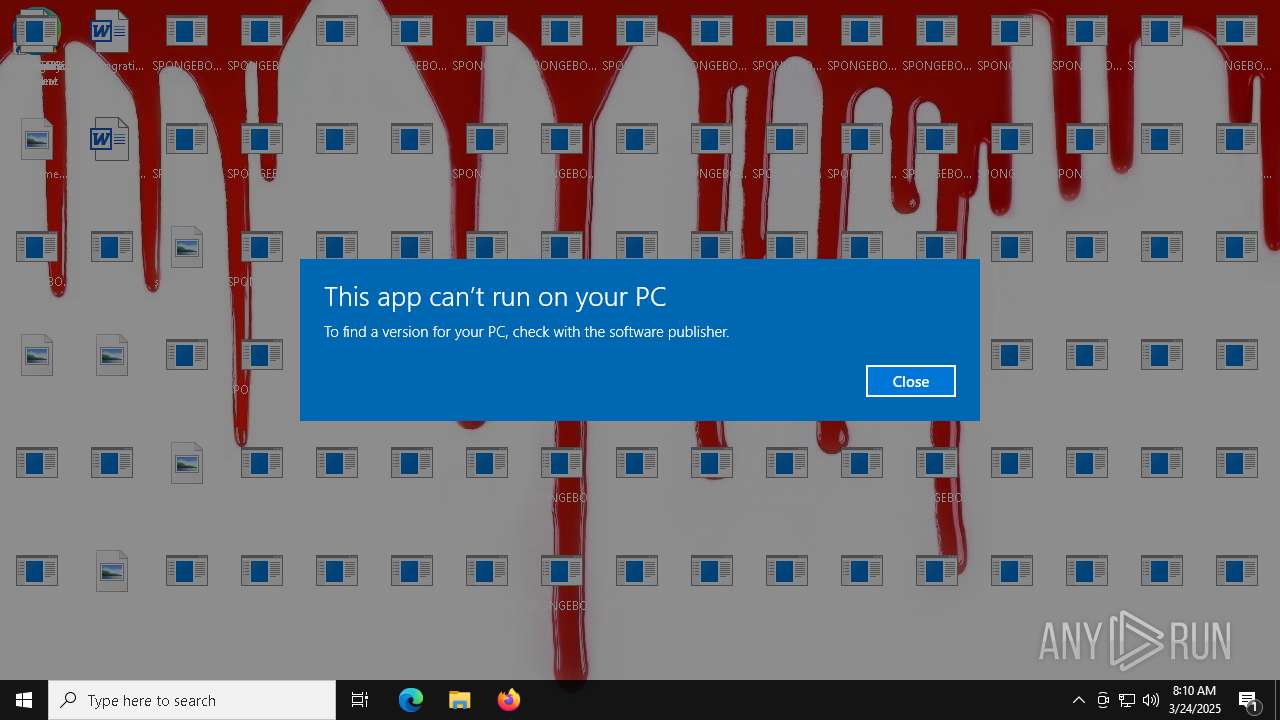
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4148)
The system shut down or reboot
- cmd.exe (PID: 8528)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6452)
The executable file from the user directory is run by the CMD process
- BobLauncher.exe (PID: 6560)
- RulesLauncher.exe (PID: 6568)
- inv.exe (PID: 7072)
- melter.exe (PID: 1160)
- melter.exe (PID: 1144)
- tunnel.exe (PID: 1212)
- endpc.exe (PID: 5860)
- icons.exe (PID: 2524)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6452)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8132)
- BackgroundTransferHost.exe (PID: 7884)
- BackgroundTransferHost.exe (PID: 4224)
- BackgroundTransferHost.exe (PID: 7700)
- BackgroundTransferHost.exe (PID: 3300)
- BackgroundTransferHost.exe (PID: 1244)
- cscript.exe (PID: 7600)
- cscript.exe (PID: 7472)
- cscript.exe (PID: 8256)
- cscript.exe (PID: 8284)
- cscript.exe (PID: 5720)
- cscript.exe (PID: 8612)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8132)
The sample compiled with english language support
- WinRAR.exe (PID: 4652)
- msedge.exe (PID: 3008)
- msedge.exe (PID: 7728)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8132)
Reads the computer name
- identity_helper.exe (PID: 7652)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 8328)
- ShellExperienceHost.exe (PID: 8940)
- PLUGScheduler.exe (PID: 4148)
- BobLauncher.exe (PID: 6560)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8132)
Executable content was dropped or overwritten
- msedge.exe (PID: 3008)
- msedge.exe (PID: 7728)
Reads Environment values
- identity_helper.exe (PID: 7652)
Manual execution by a user
- msedge.exe (PID: 7728)
- Service64.exe (PID: 6408)
Checks supported languages
- identity_helper.exe (PID: 7652)
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 8328)
- HorrorBob2.exe (PID: 8356)
- ShellExperienceHost.exe (PID: 8940)
- Service64.exe (PID: 6408)
- BobLauncher.exe (PID: 6560)
- RulesLauncher.exe (PID: 6568)
- sbob.exe (PID: 6804)
- melter.exe (PID: 1144)
Application launched itself
- msedge.exe (PID: 7728)
Autorun file from Downloads
- msedge.exe (PID: 7728)
- msedge.exe (PID: 6876)
Create files in a temporary directory
- HorrorBob2.exe (PID: 6248)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 8356)
- HorrorBob2.exe (PID: 8328)
- Service64.exe (PID: 6408)
- RulesLauncher.exe (PID: 6568)
- BobLauncher.exe (PID: 6560)
Process checks computer location settings
- HorrorBob2.exe (PID: 7292)
- HorrorBob2.exe (PID: 7556)
- HorrorBob2.exe (PID: 5452)
- HorrorBob2.exe (PID: 6708)
- HorrorBob2.exe (PID: 8356)
- HorrorBob2.exe (PID: 8328)
- BobLauncher.exe (PID: 6560)
Reads the time zone
- net1.exe (PID: 8856)
Creates files in the program directory
- PLUGScheduler.exe (PID: 4148)
Autorun file from Task Scheduler
- endpc.exe (PID: 5860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:03:12 11:07:04 |
| ZipCRC: | 0x4022fcaa |
| ZipCompressedSize: | 3483526 |
| ZipUncompressedSize: | 3514368 |
| ZipFileName: | ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa.exe.bin |
Total processes
420
Monitored processes
140
Malicious processes
6
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\9A0D.tmp\0.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7484 --field-trial-handle=2204,i,11643335414648627750,4609042156073069222,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | timeout 20 /nobreak | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5272 --field-trial-handle=2204,i,11643335414648627750,4609042156073069222,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=5440 --field-trial-handle=2204,i,11643335414648627750,4609042156073069222,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1064 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tunnel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | taskkill /f /im explorer.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1144 | melter.exe | C:\Users\admin\AppData\Local\Temp\9A0D.tmp\melter.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1152 | timeout 10 /nobreak | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | melter.exe | C:\Users\admin\AppData\Local\Temp\9A0D.tmp\melter.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
18 520
Read events
18 436
Write events
82
Delete events
2
Modification events
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\niet openen wanna.zip | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7884) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7884) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
67
Suspicious files
638
Text files
106
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8132 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | — | |
MD5:— | SHA256:— | |||
| 8132 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\6835171f-b692-4e50-bc86-aa29991356af.down_data | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10fea5.TMP | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10feb5.TMP | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10feb5.TMP | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10fec4.TMP | — | |
MD5:— | SHA256:— | |||
| 7728 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
174
DNS requests
165
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8132 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7200 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3008 | msedge.exe | GET | 304 | 23.209.209.135:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
3008 | msedge.exe | GET | 304 | 23.209.209.135:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
5308 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6824 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7200 | backgroundTaskHost.exe | 20.103.156.88:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7200 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3008 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3008 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
3008 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
3008 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
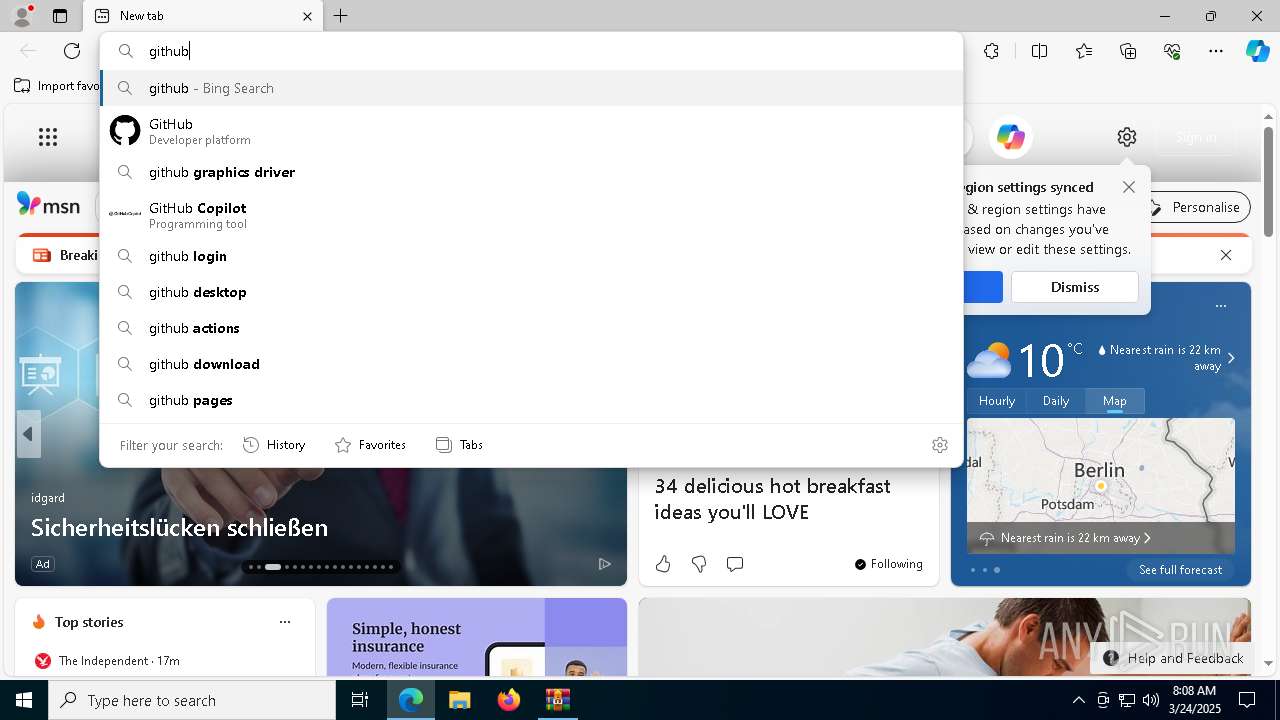
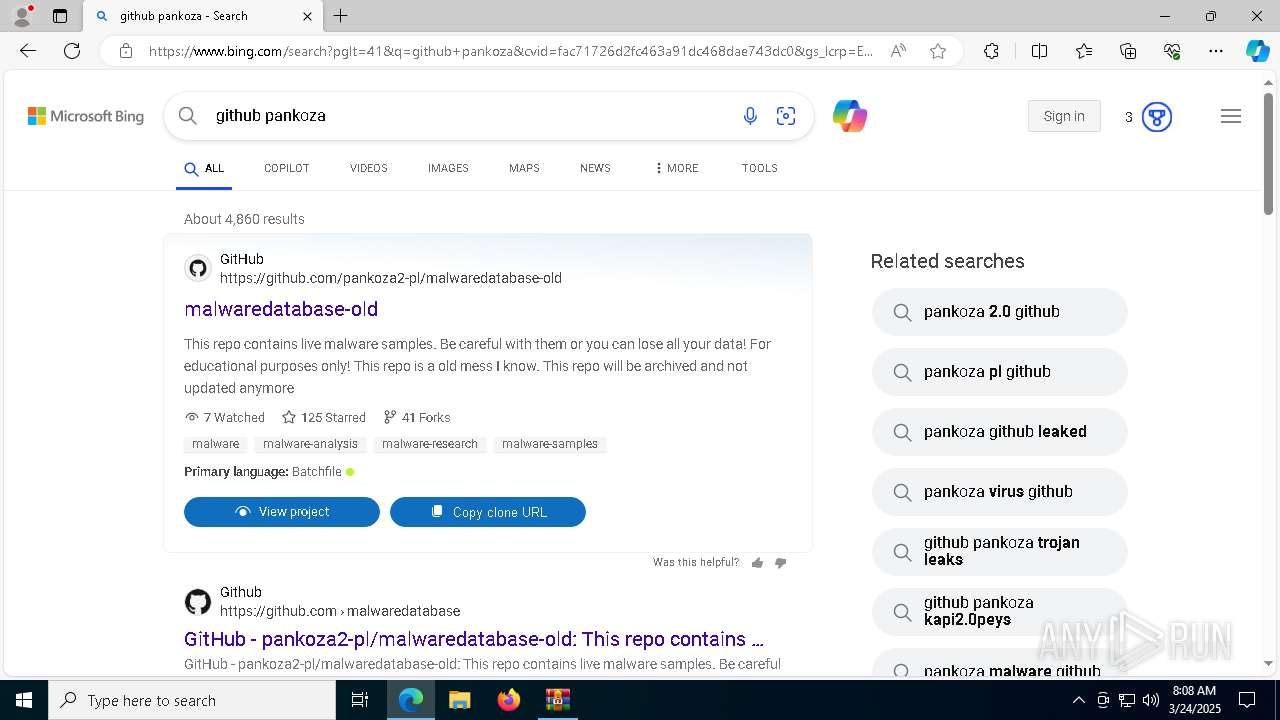
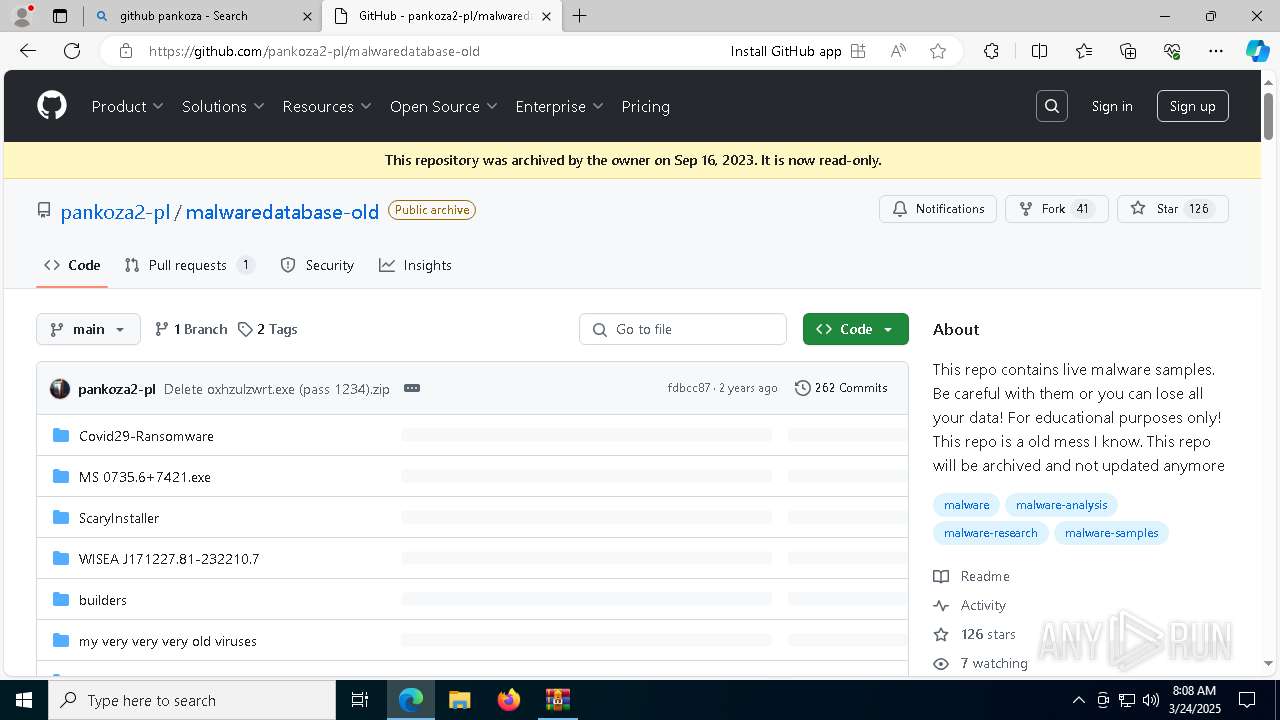
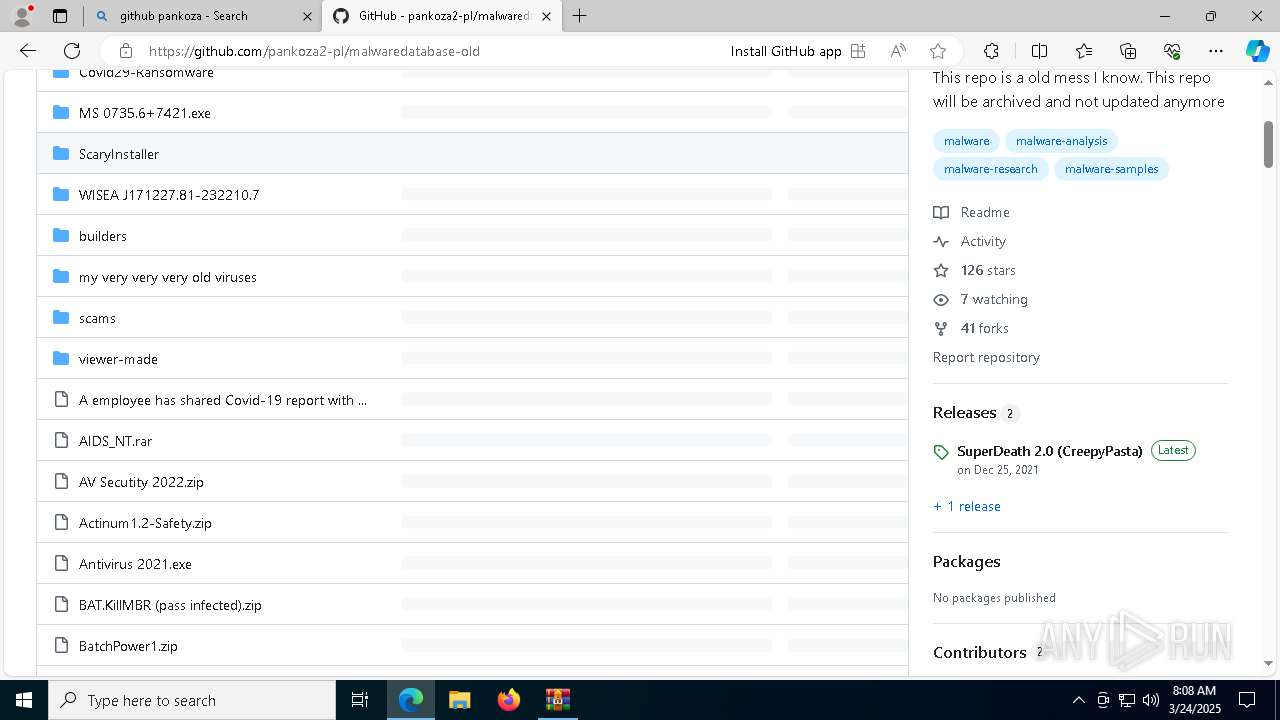
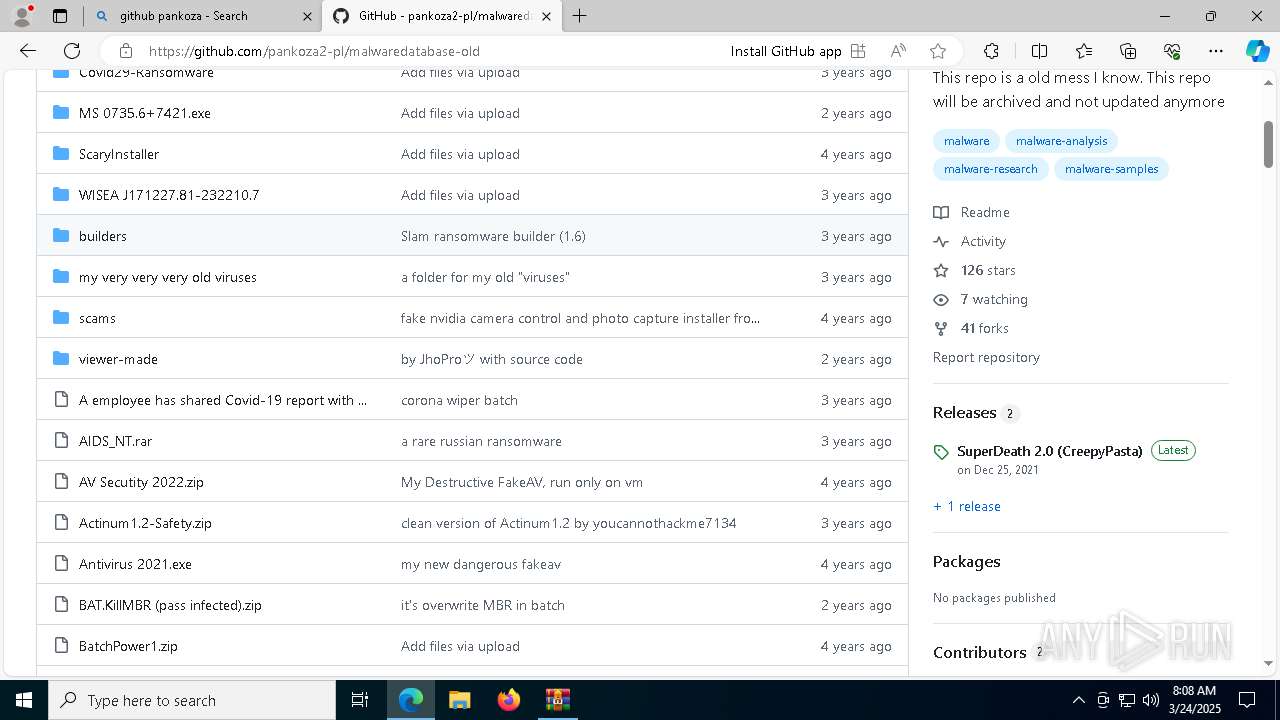
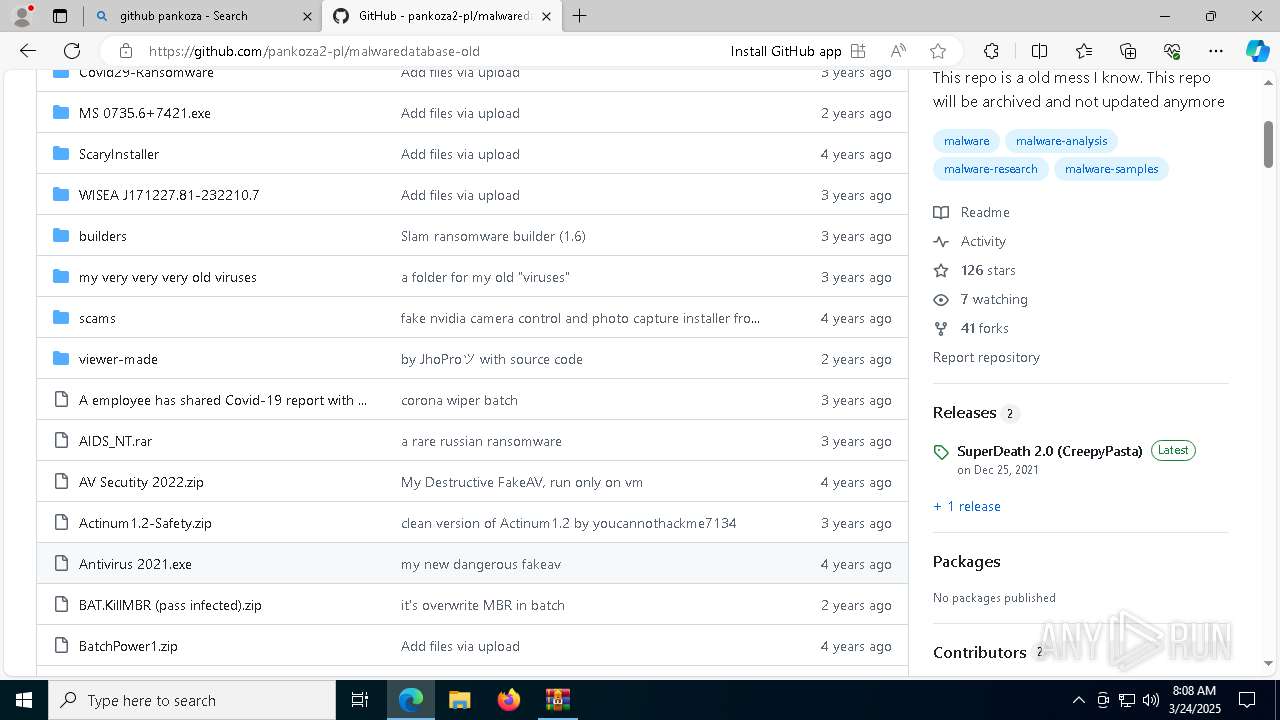
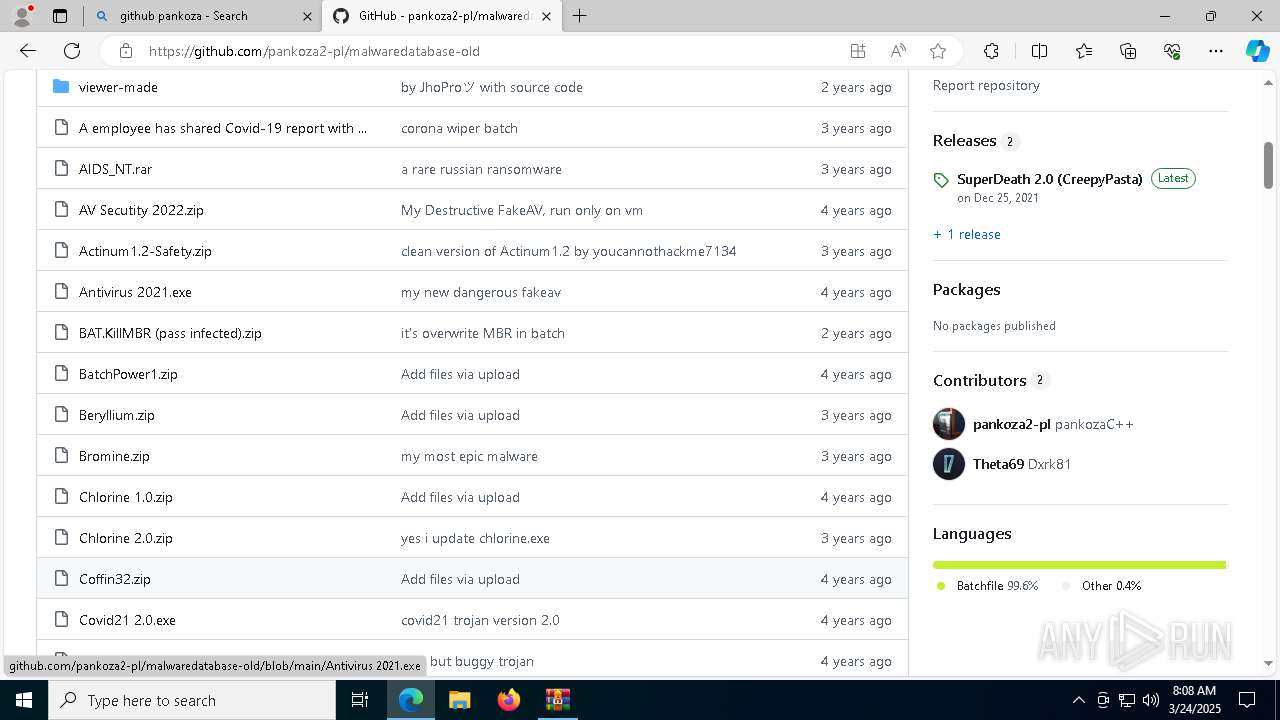
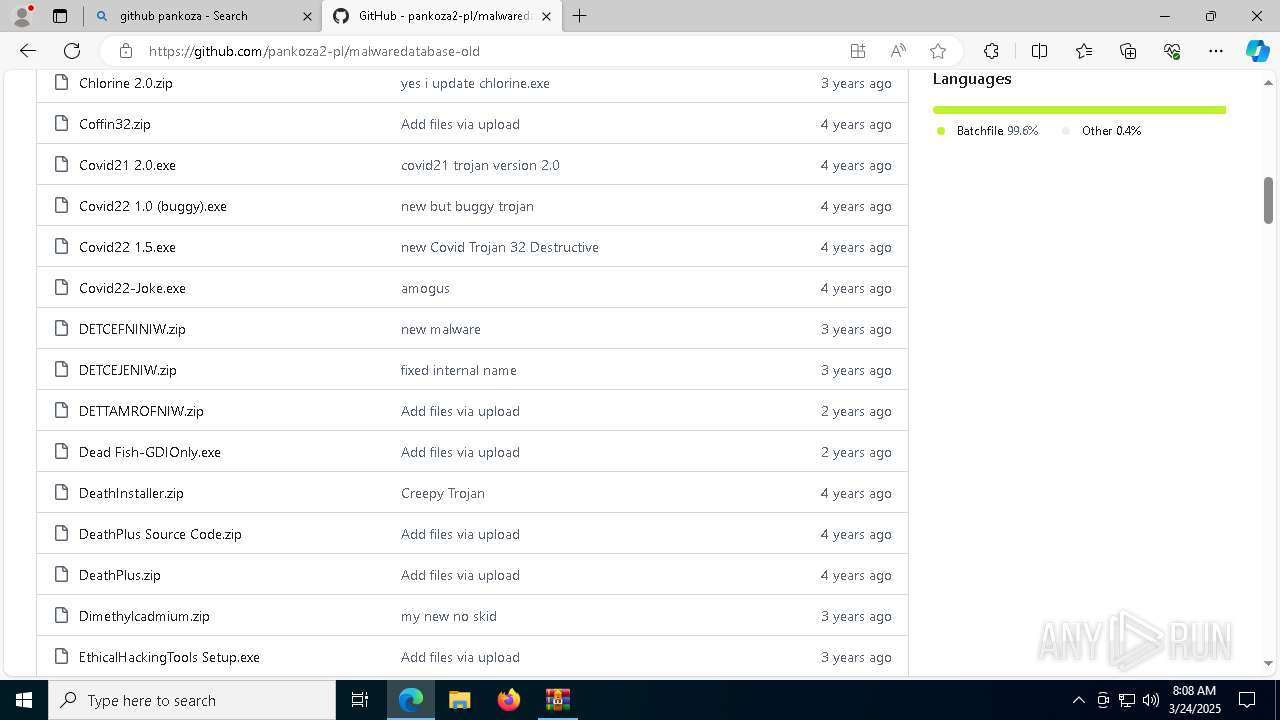
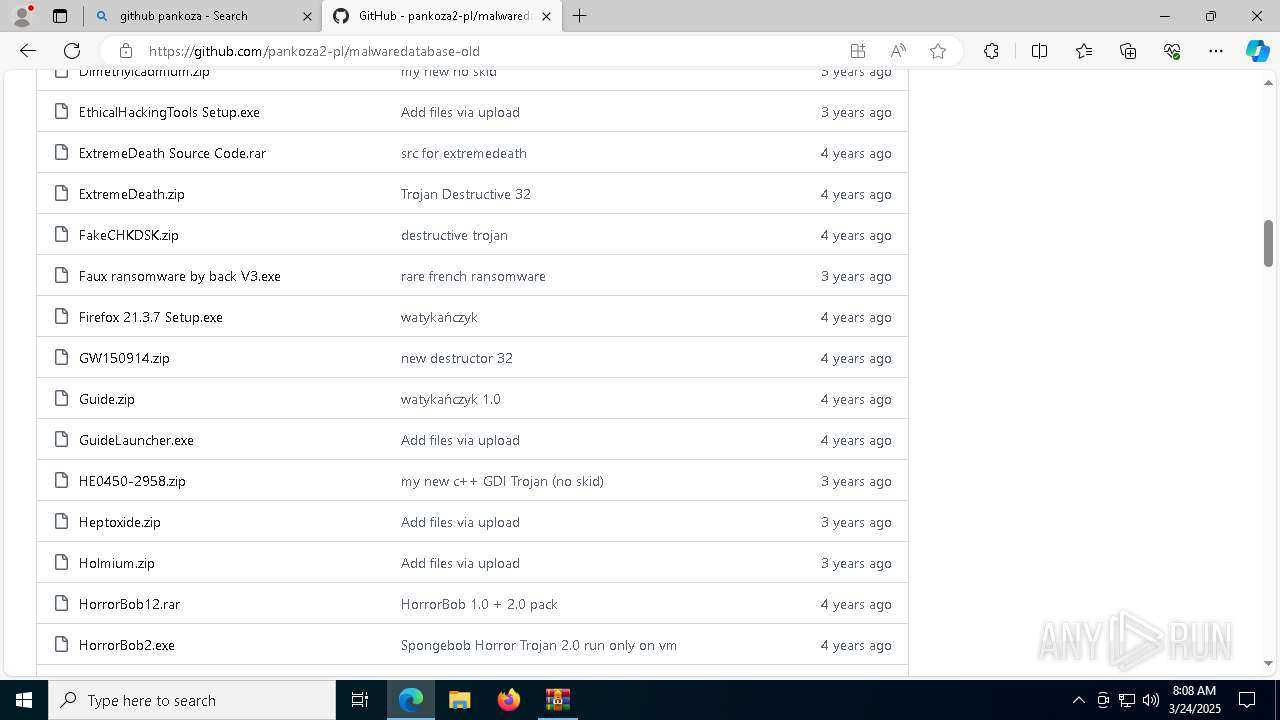
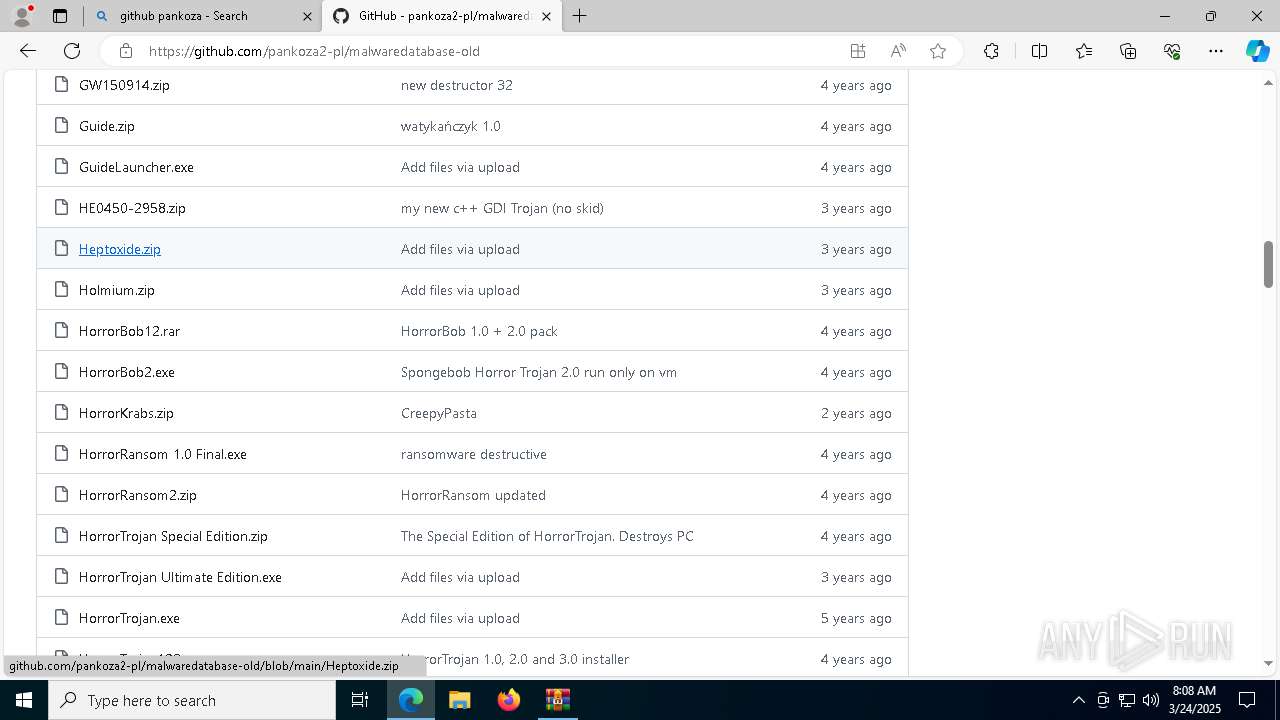
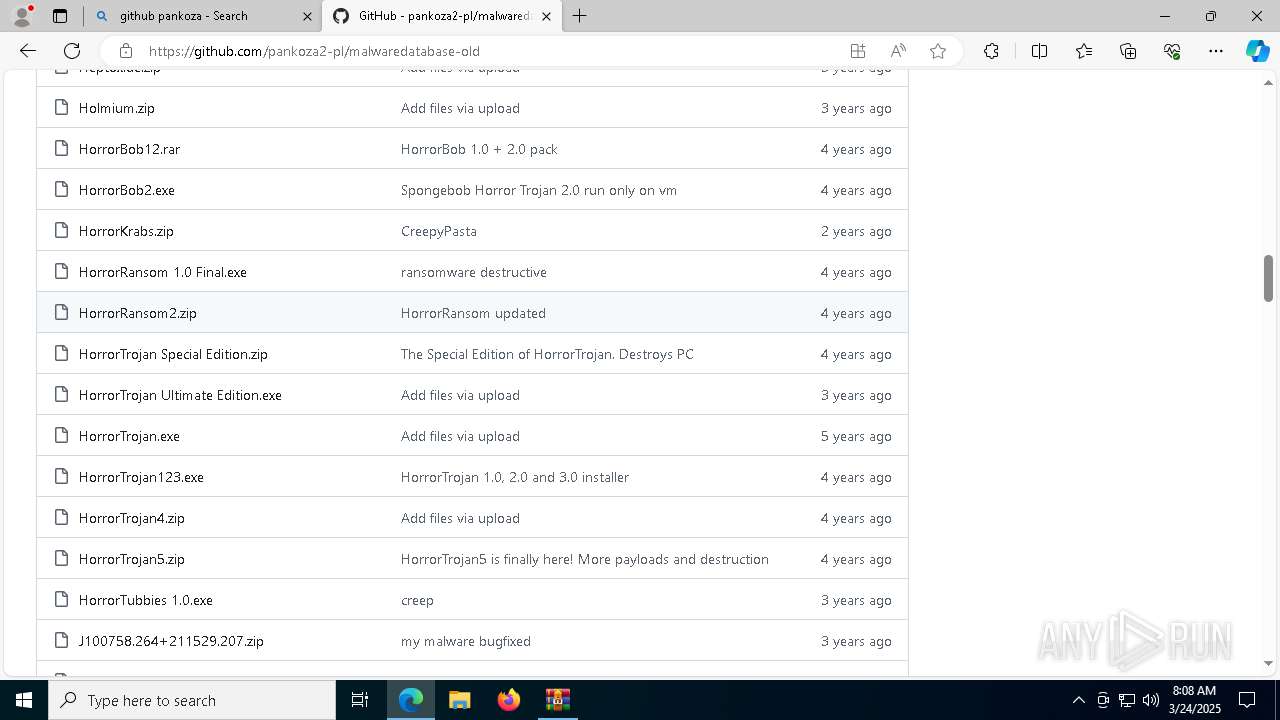
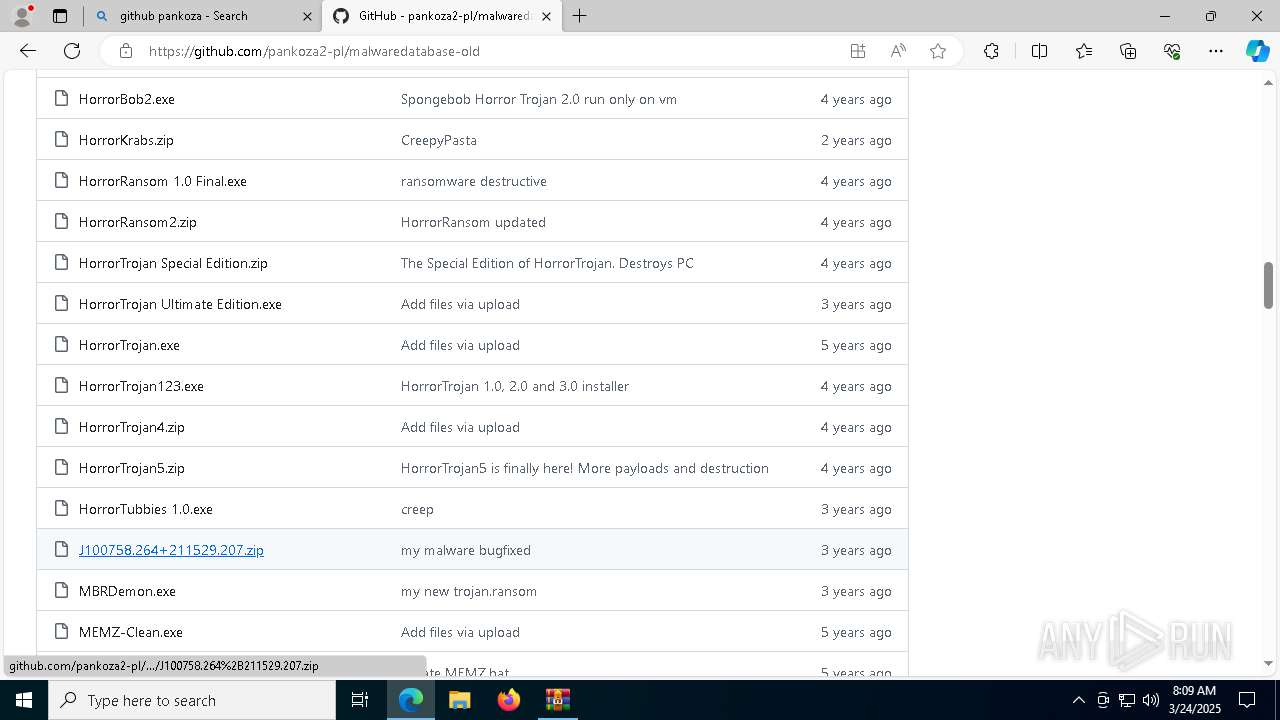
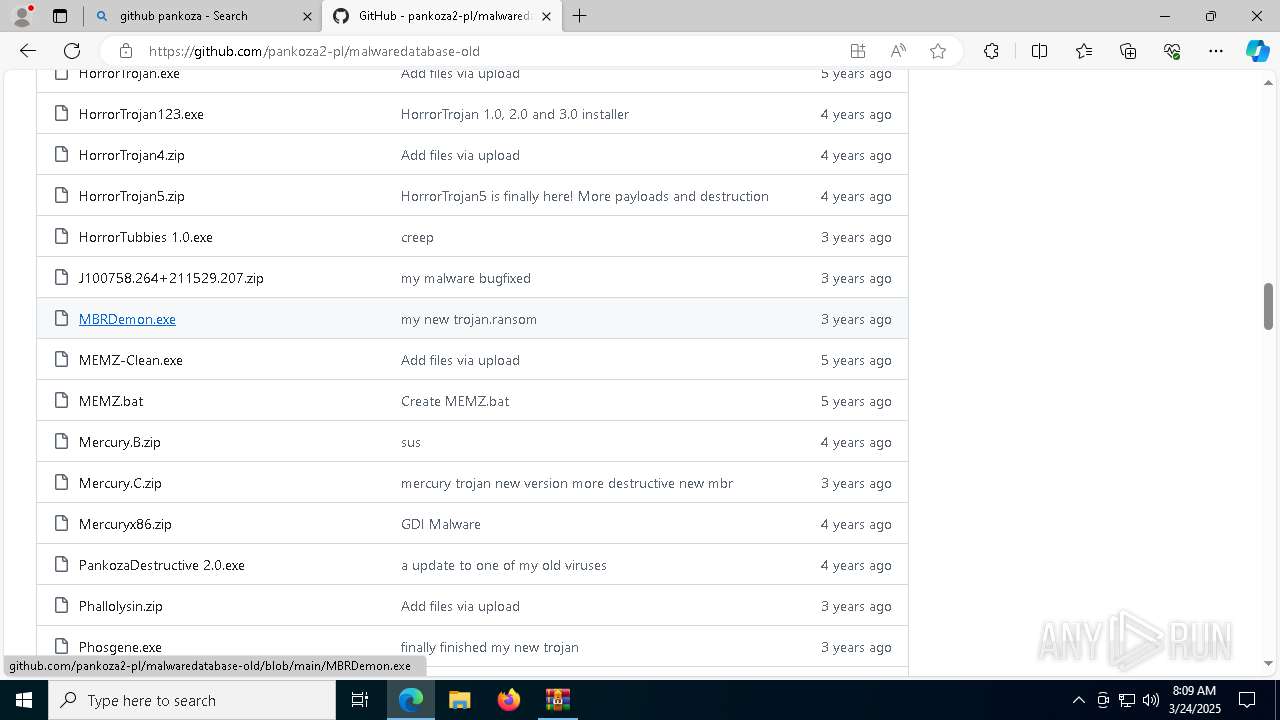
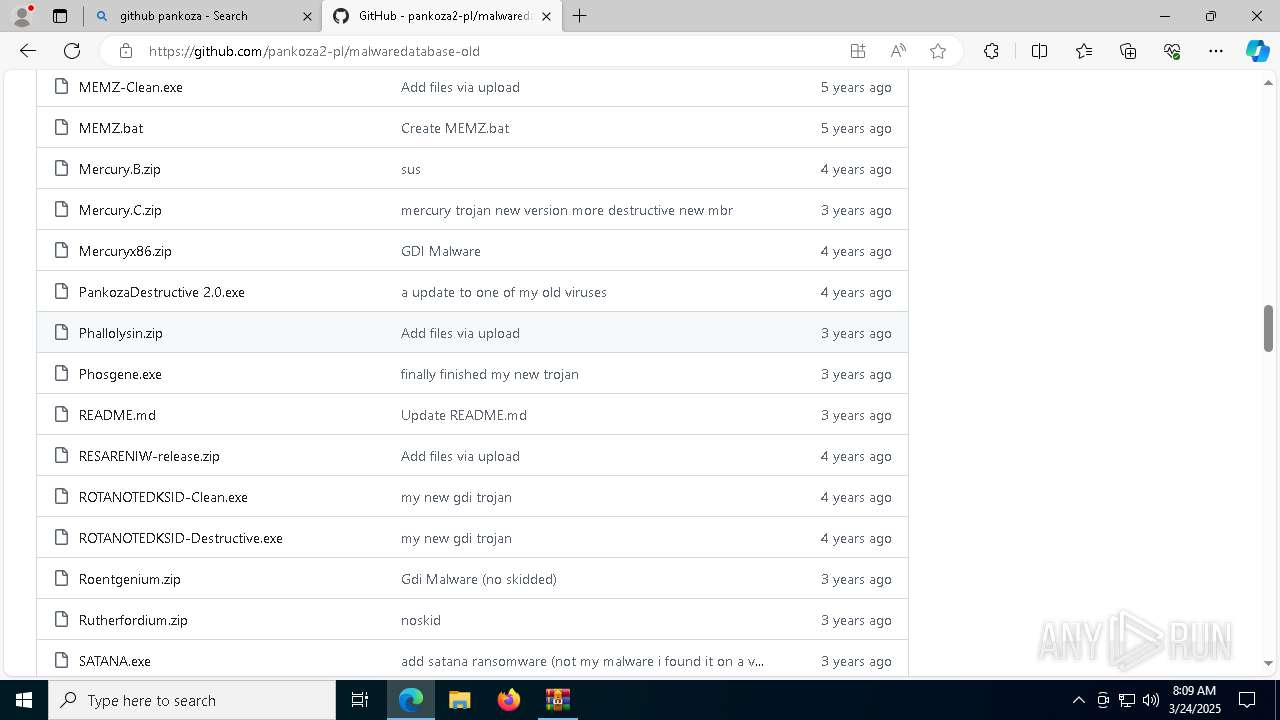
3008 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3008 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3008 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
3008 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |