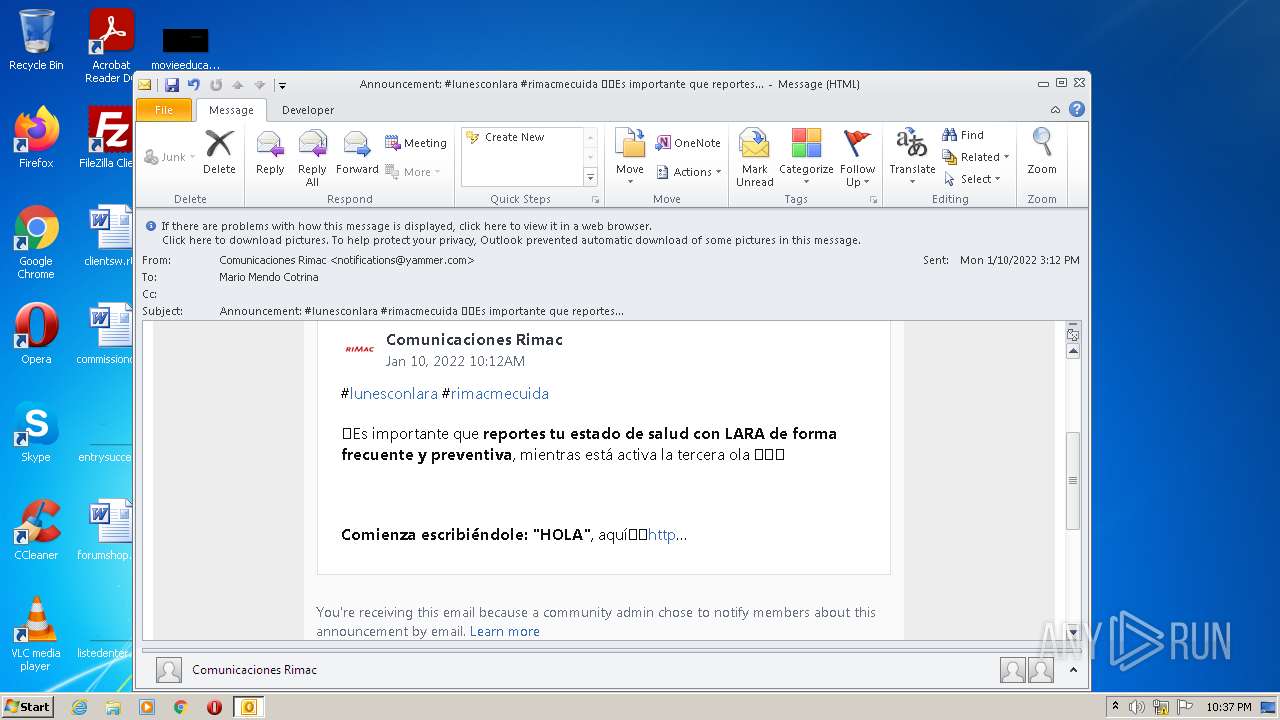
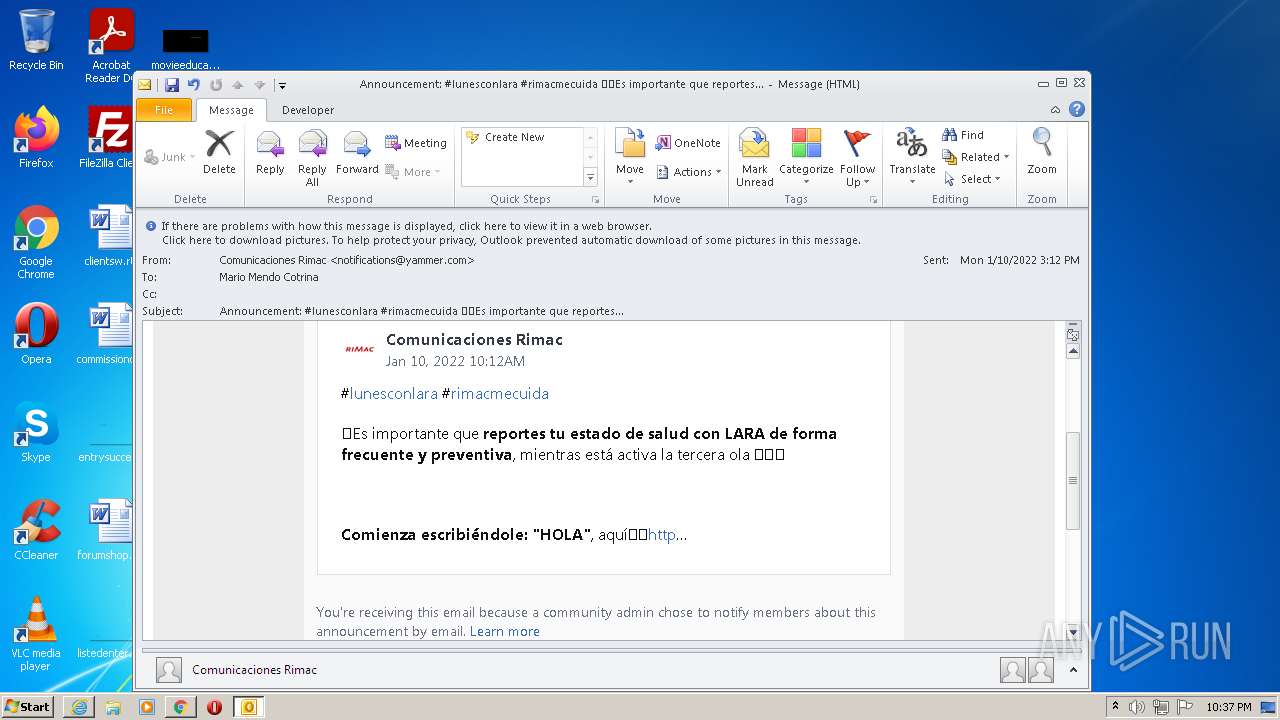
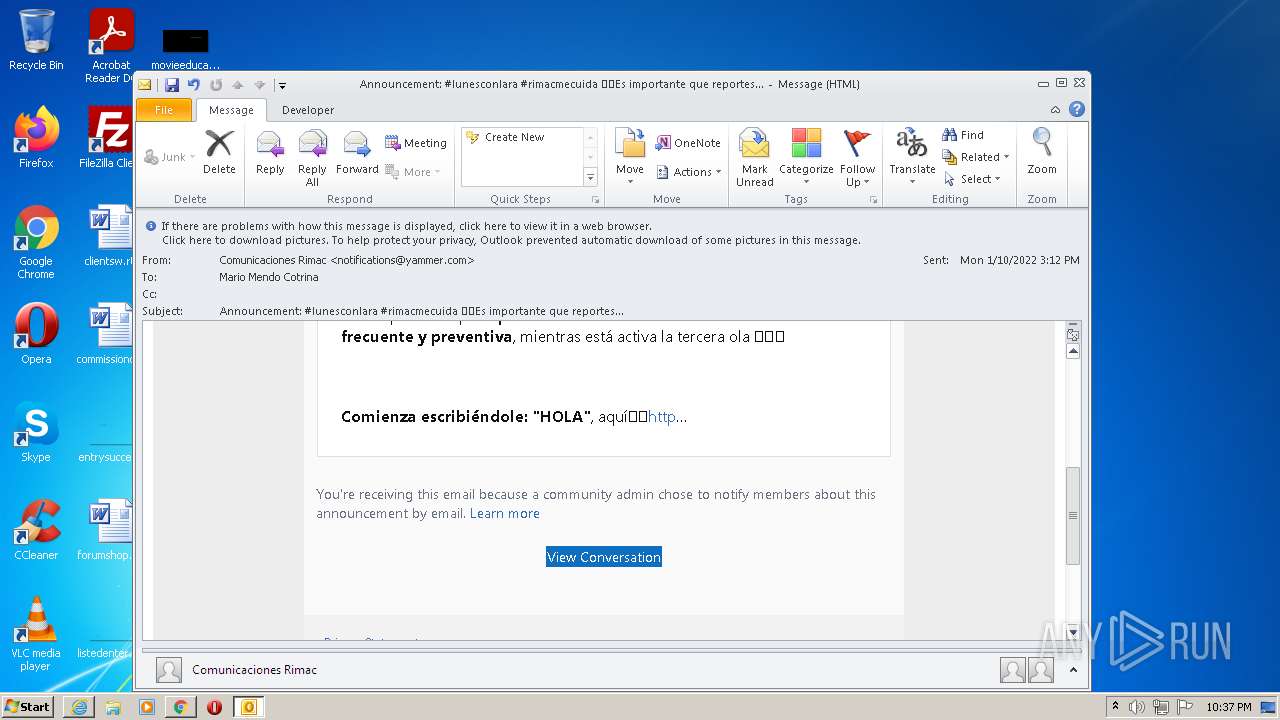
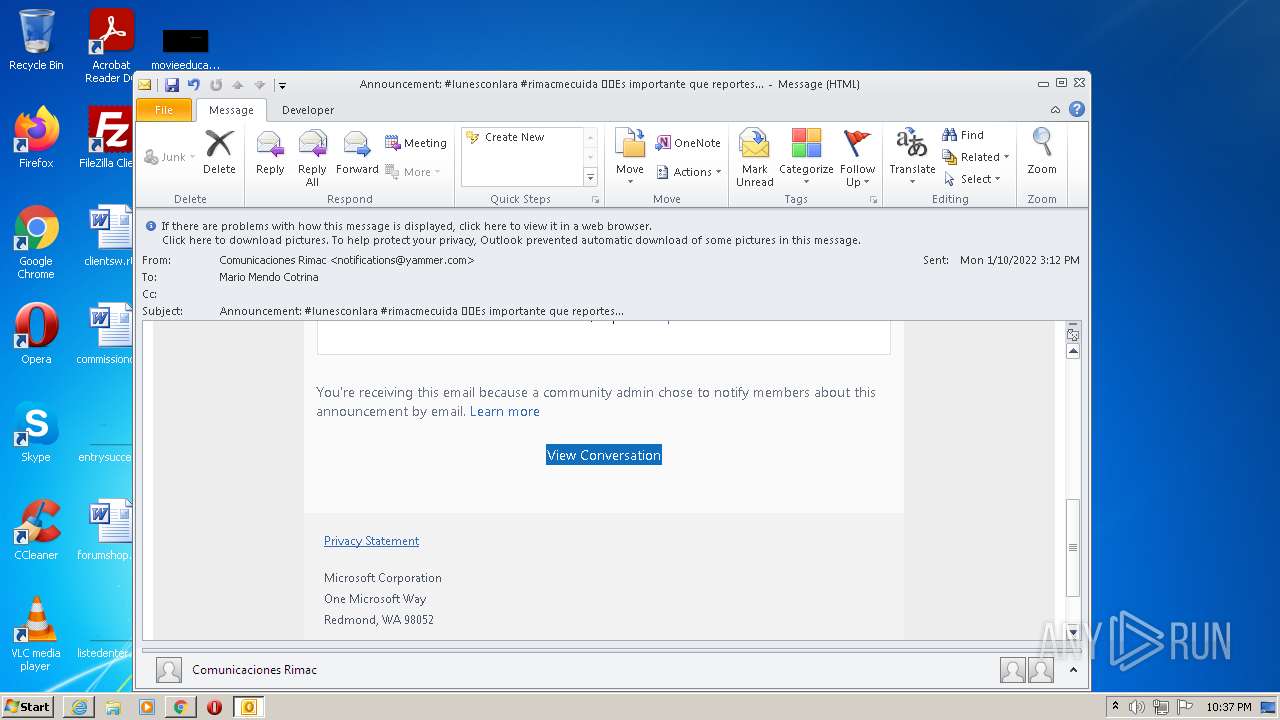
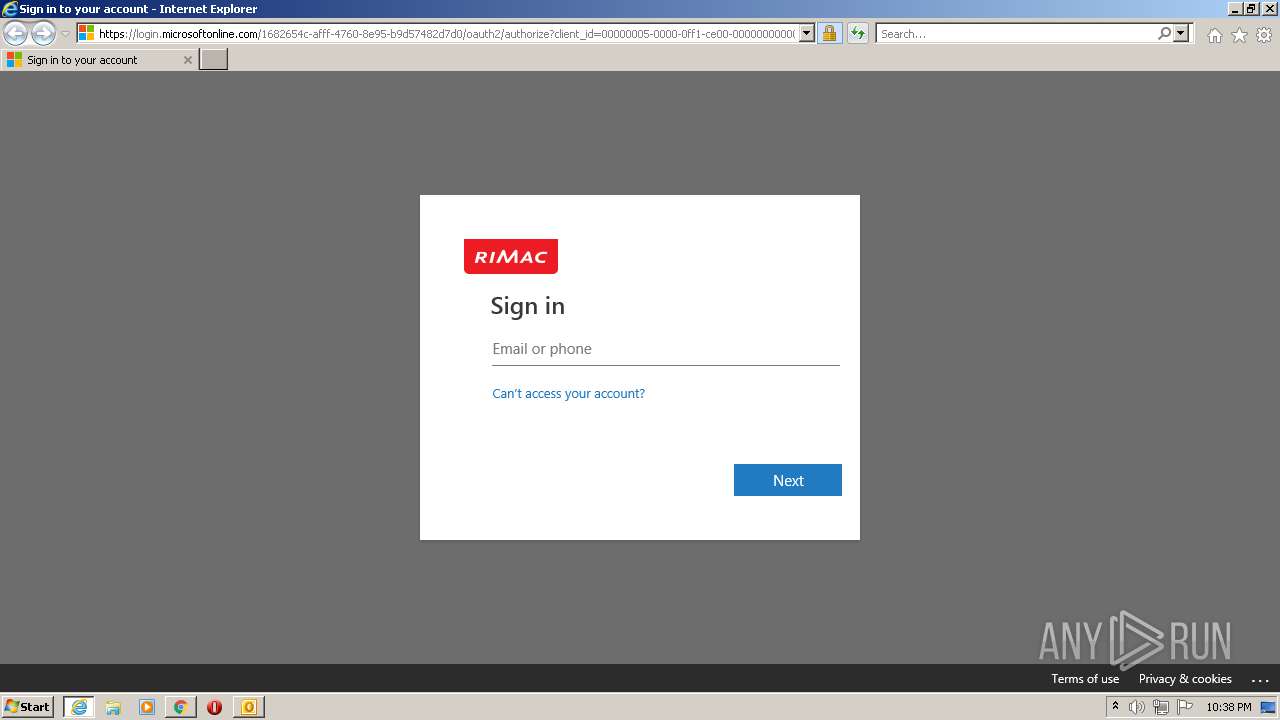
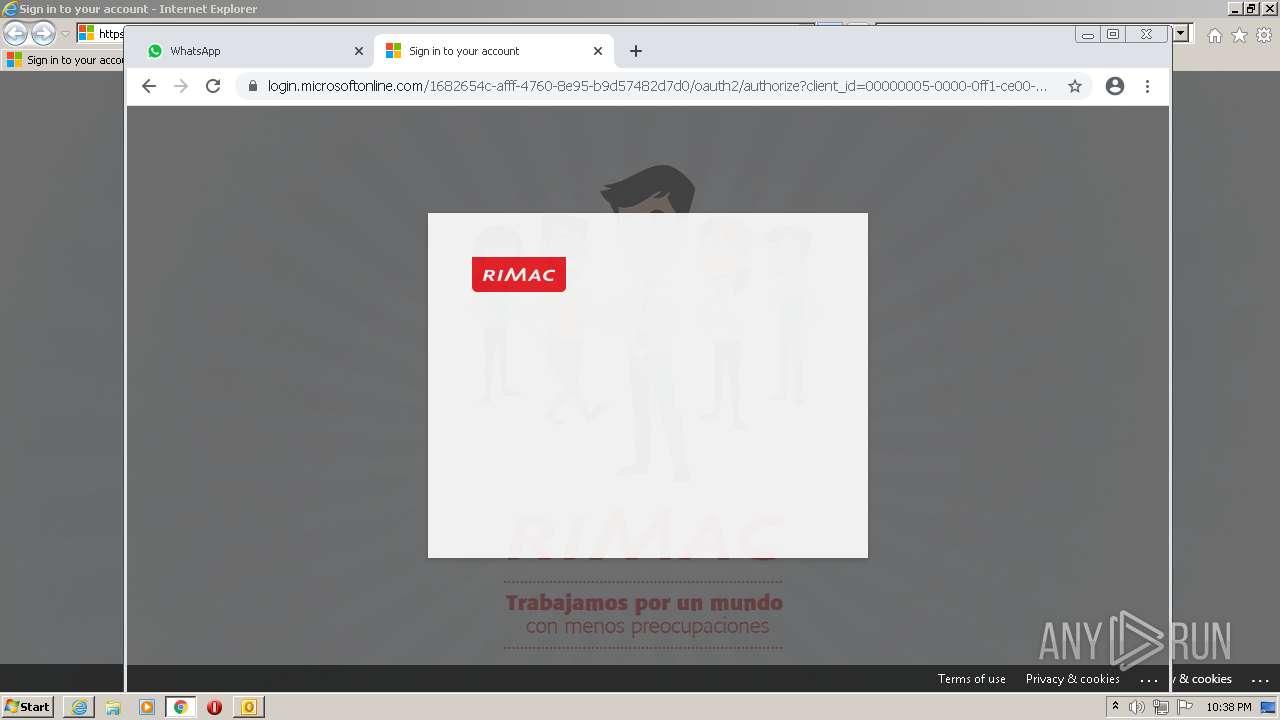
| File name: | Announcement_ #lunesconlara #rimacmecuida ⚠️Es importante que reportes.eml |
| Full analysis: | https://app.any.run/tasks/4349b56f-aa1c-4104-b4d8-4dab3a78aeee |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 22:36:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with CRLF line terminators |
| MD5: | 8D53132DE4CA23448A631D2D24808E0A |
| SHA1: | 4CA875AB2A71468D9A63ED7CEEB9D72C2177E6C8 |
| SHA256: | E7C242EBBA213DBDD6C43C87272FC6380D1586F29D79518B4CF4981A4B5A8186 |
| SSDEEP: | 1536:ld+J15nPivn8auY2SzZGoMDqMuYL7vNNpxcKBaNQTSZRFbVt172bL:ldFvn8GLNIqMumpmyamTSZRVT17E |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3208)
SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 1820)
Searches for installed software
- OUTLOOK.EXE (PID: 1820)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1820)
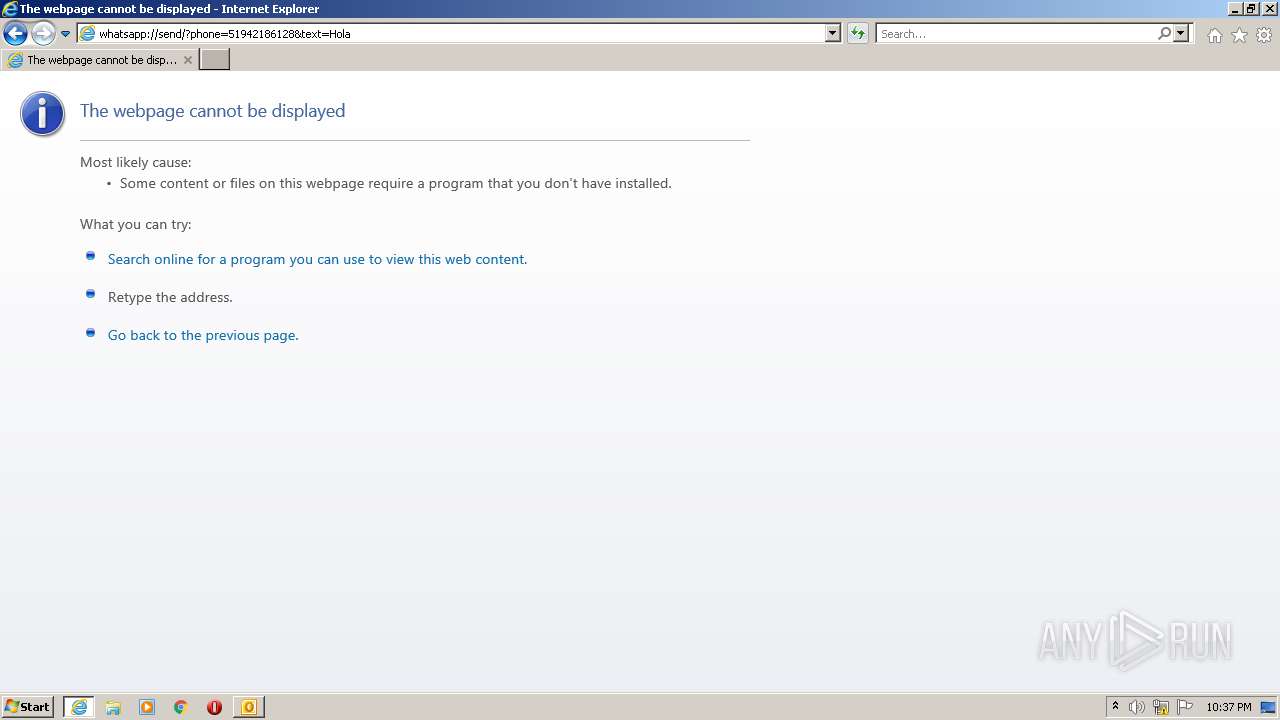
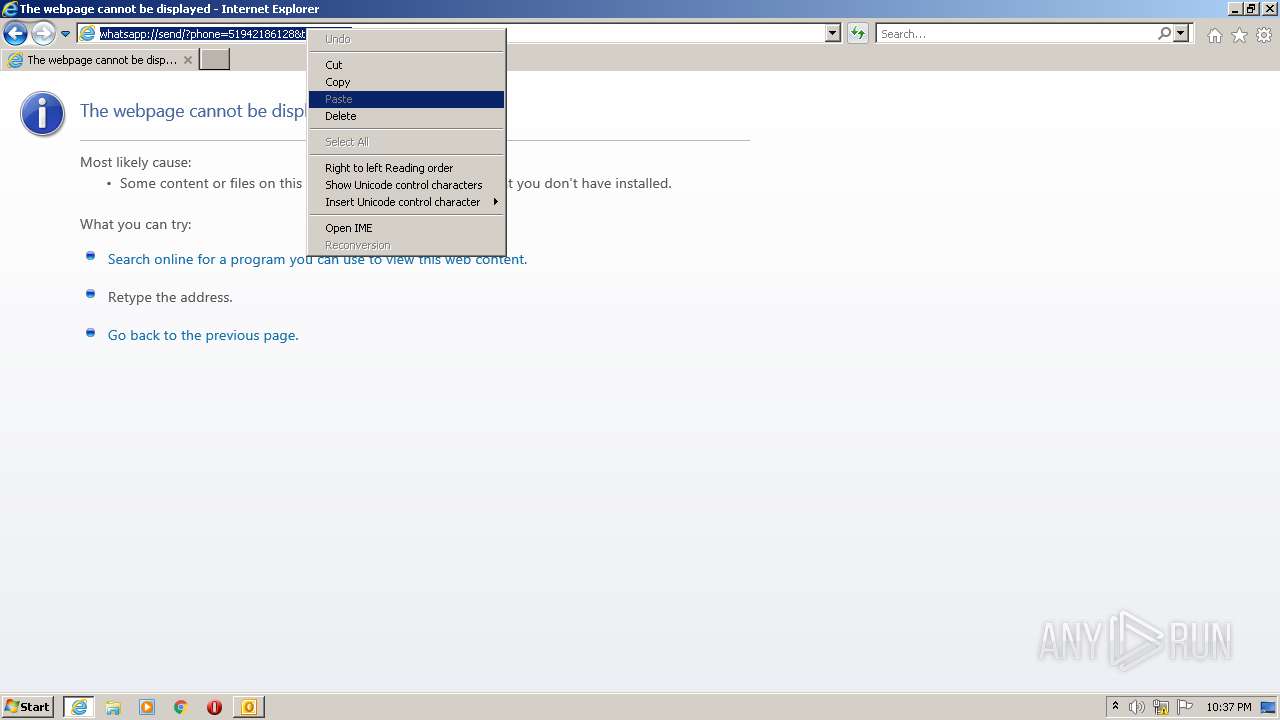
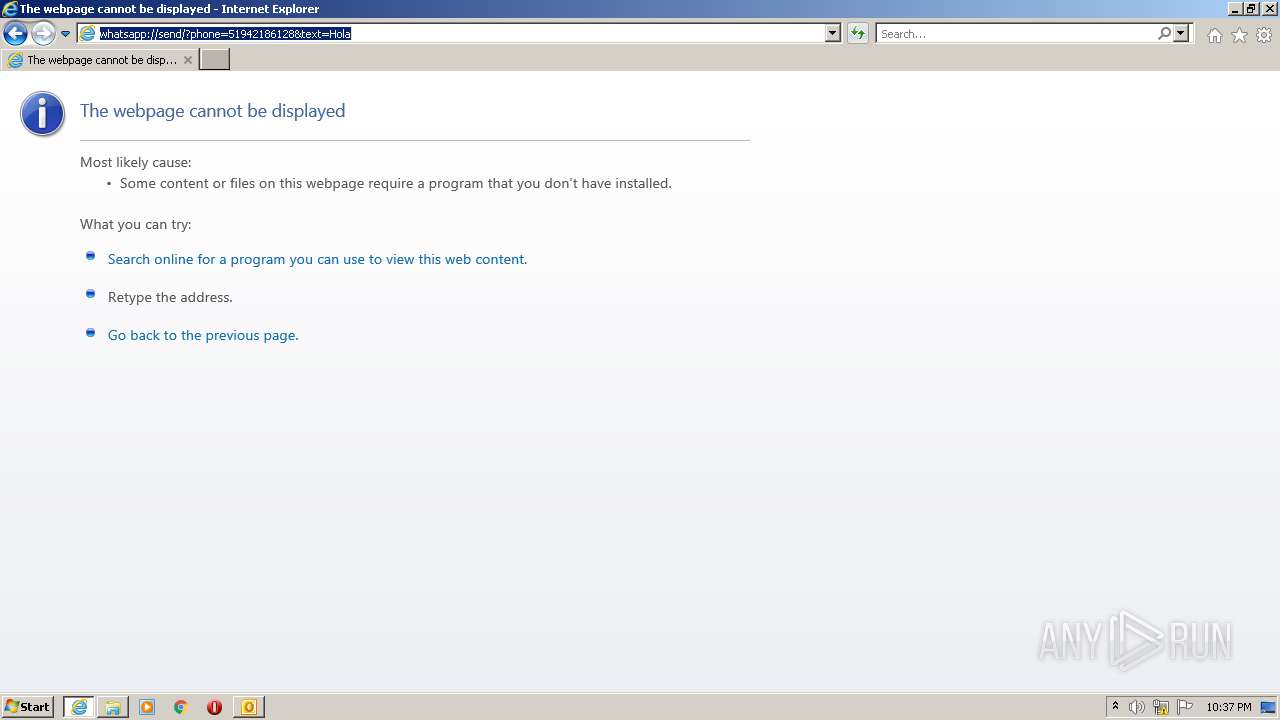
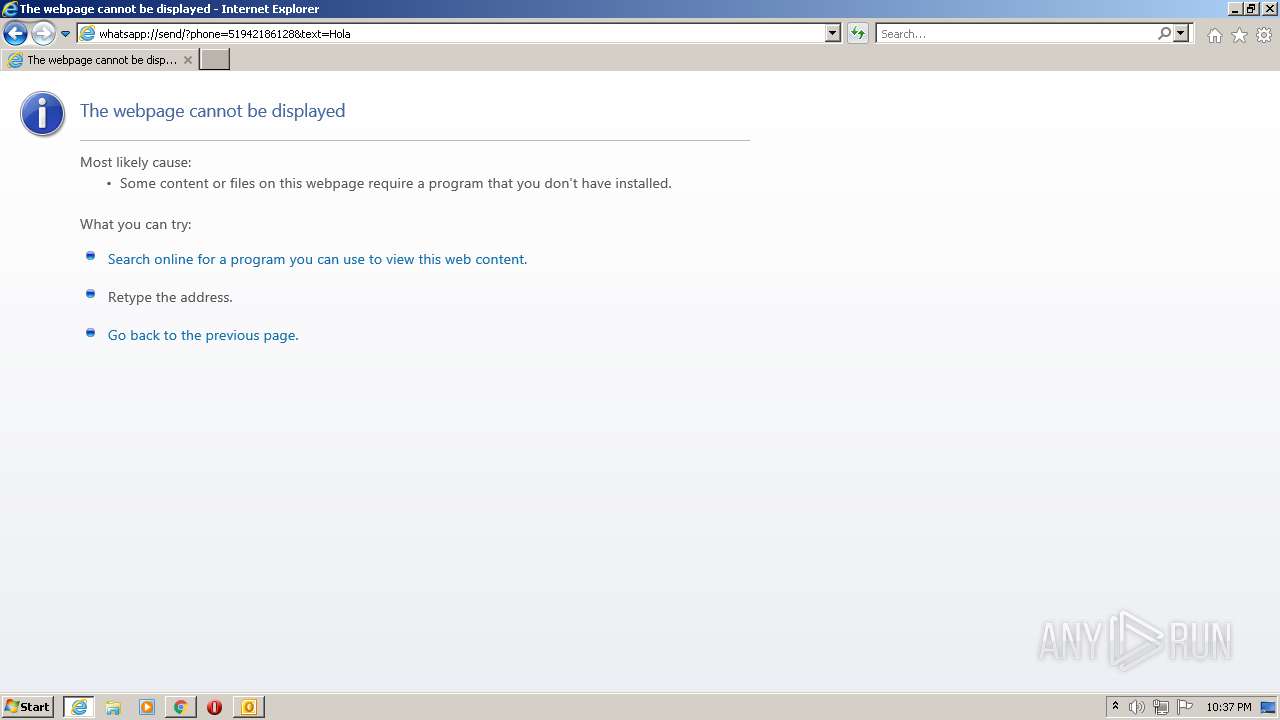
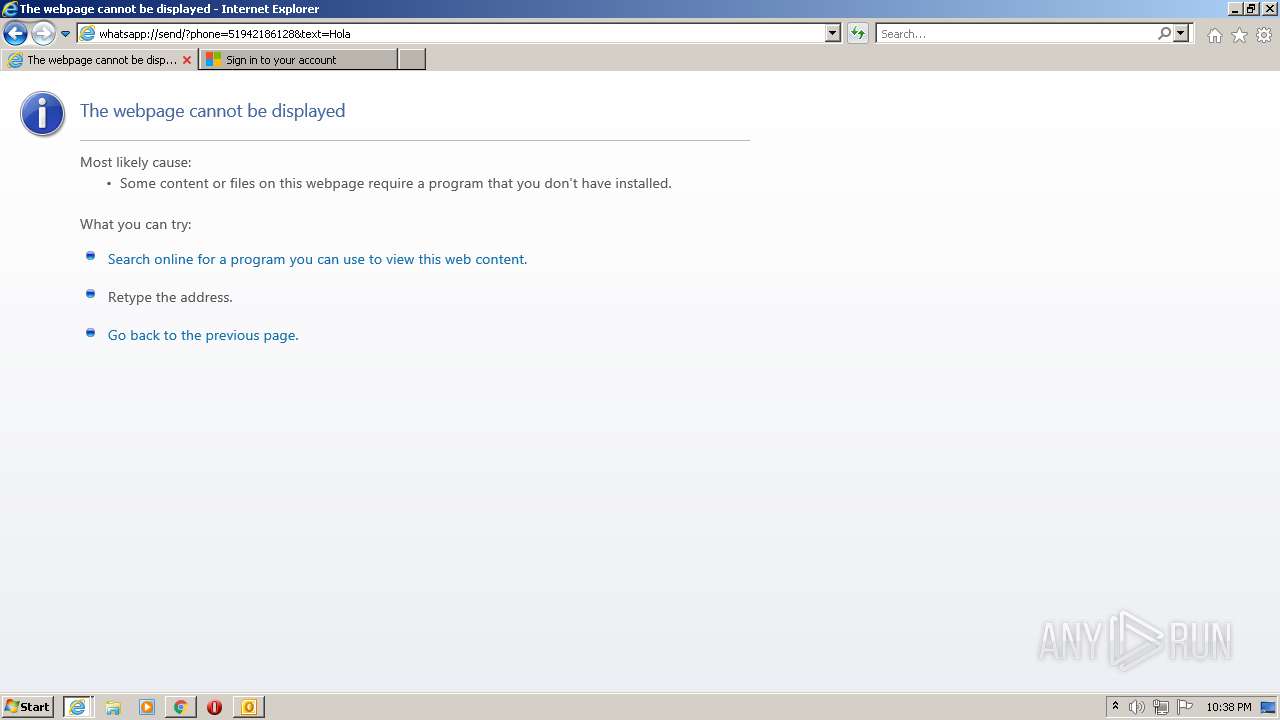
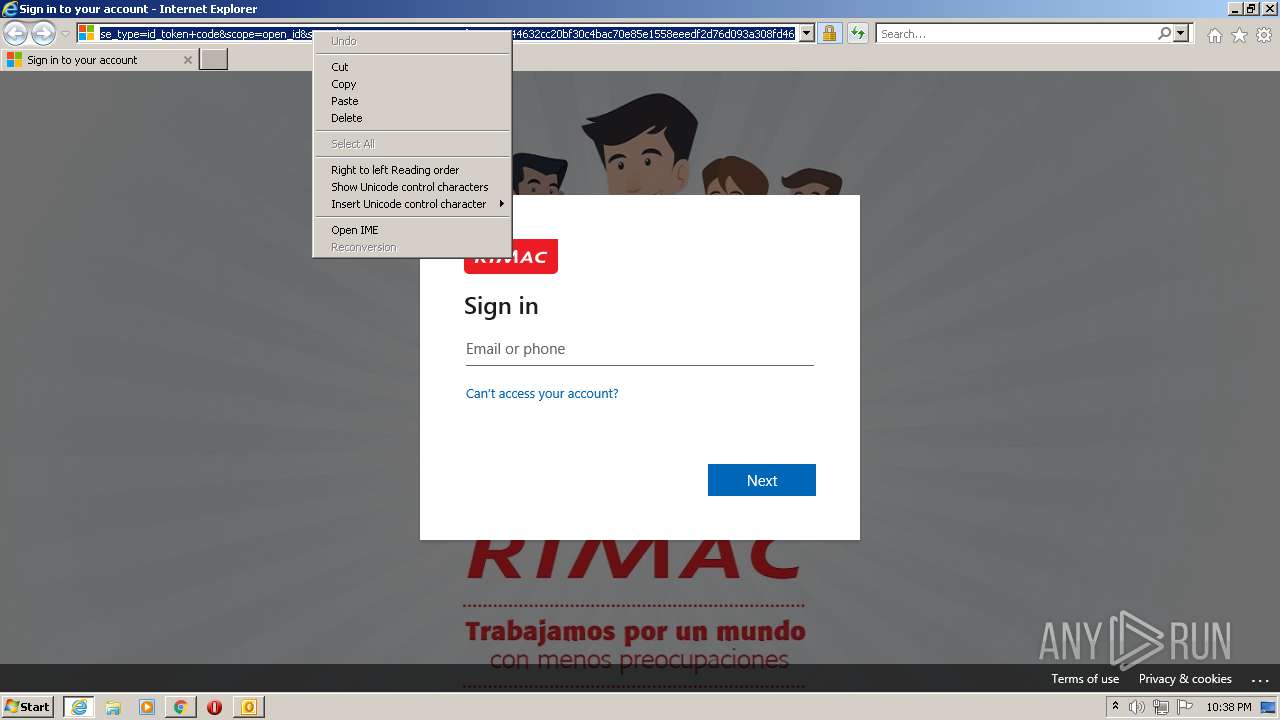
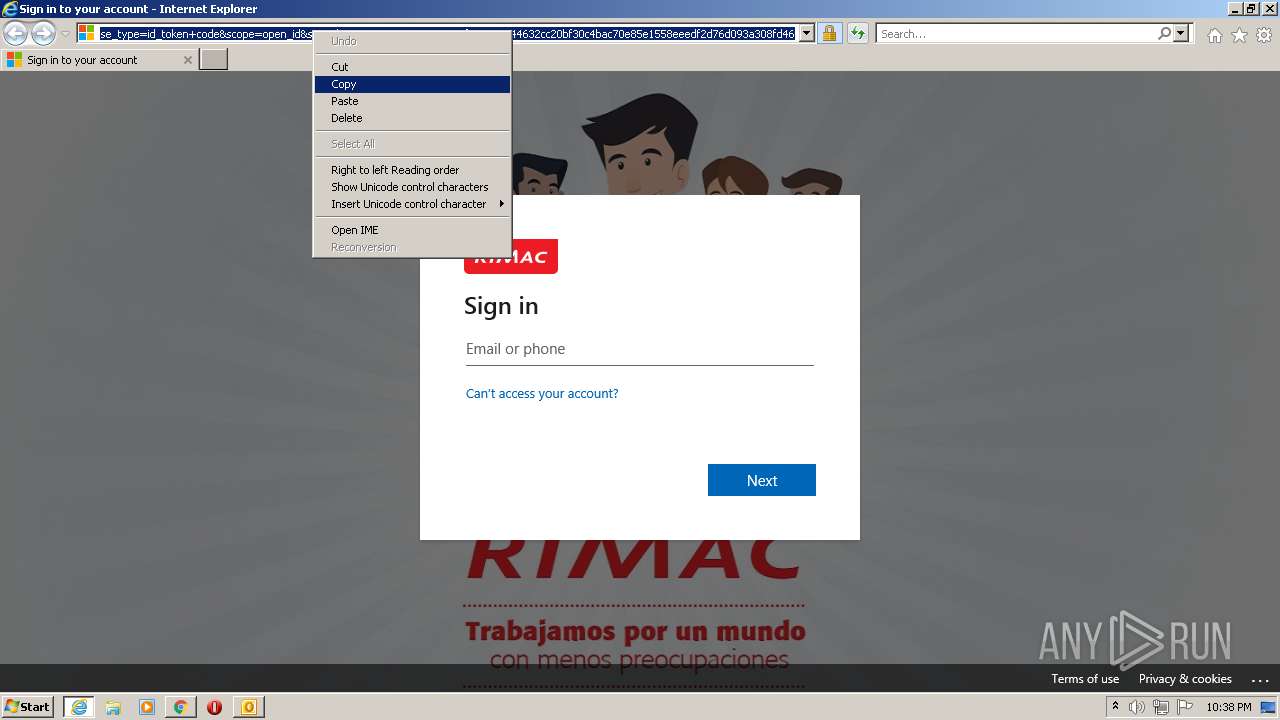
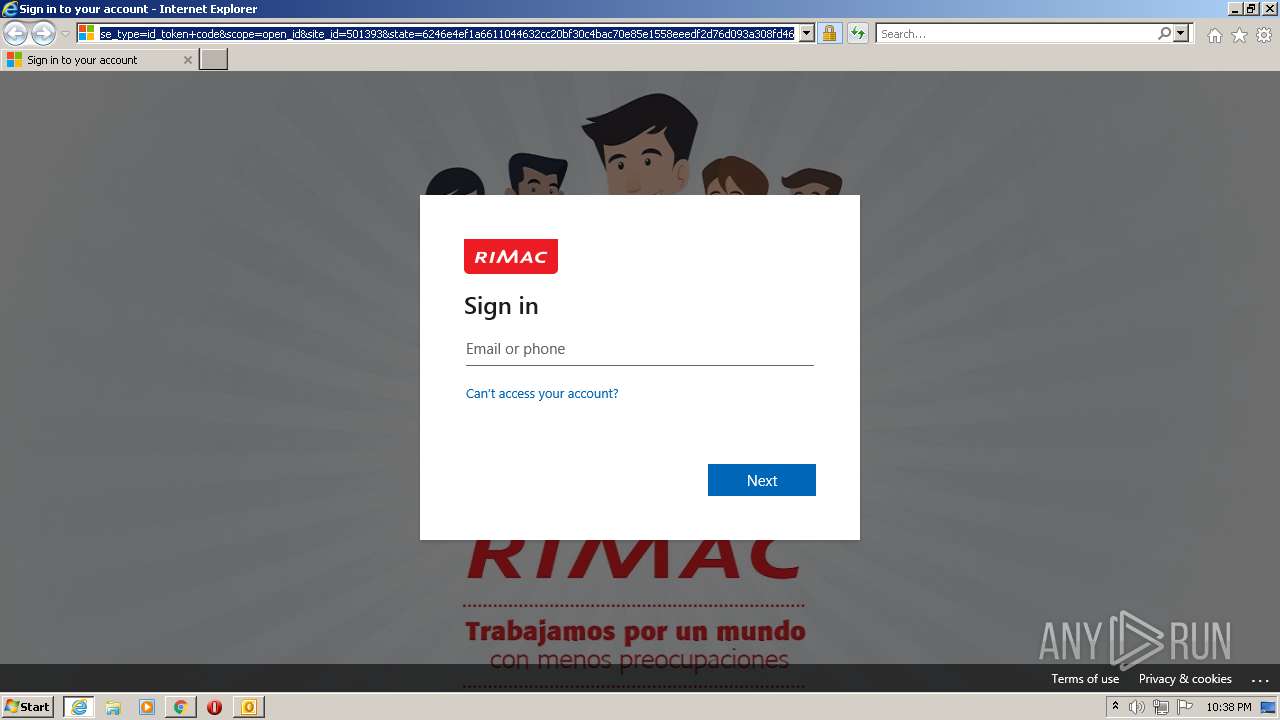
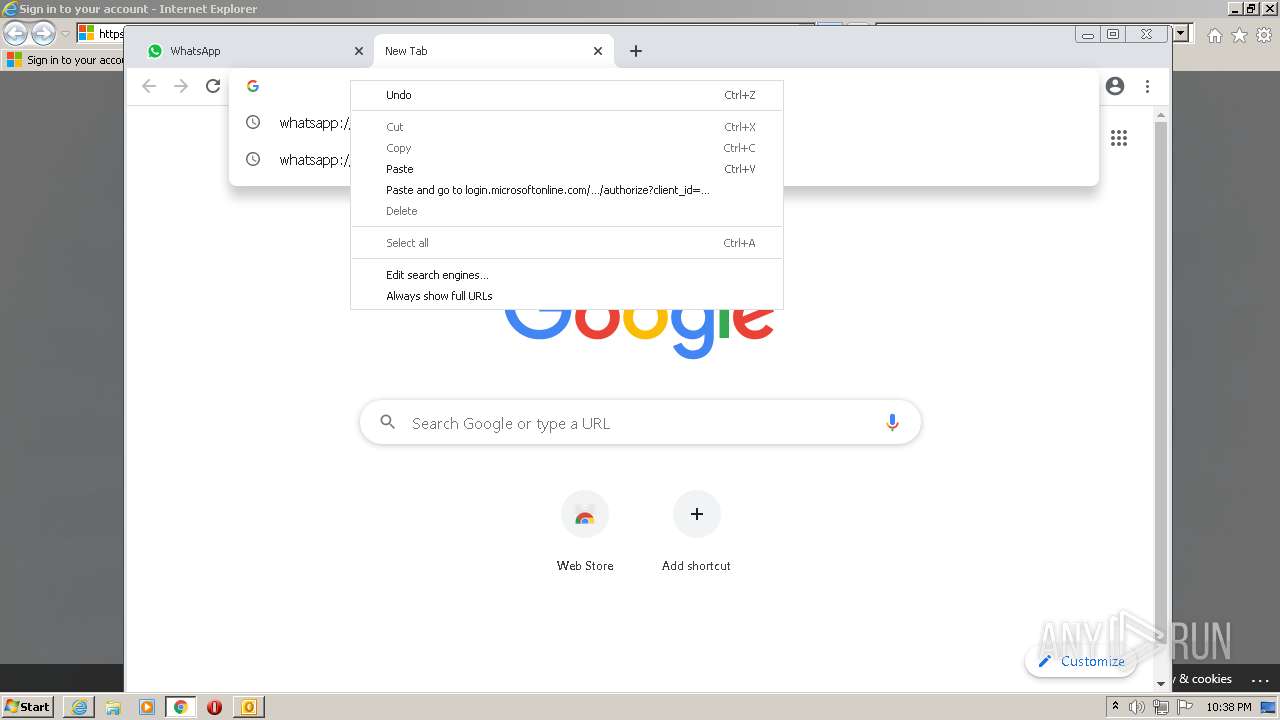
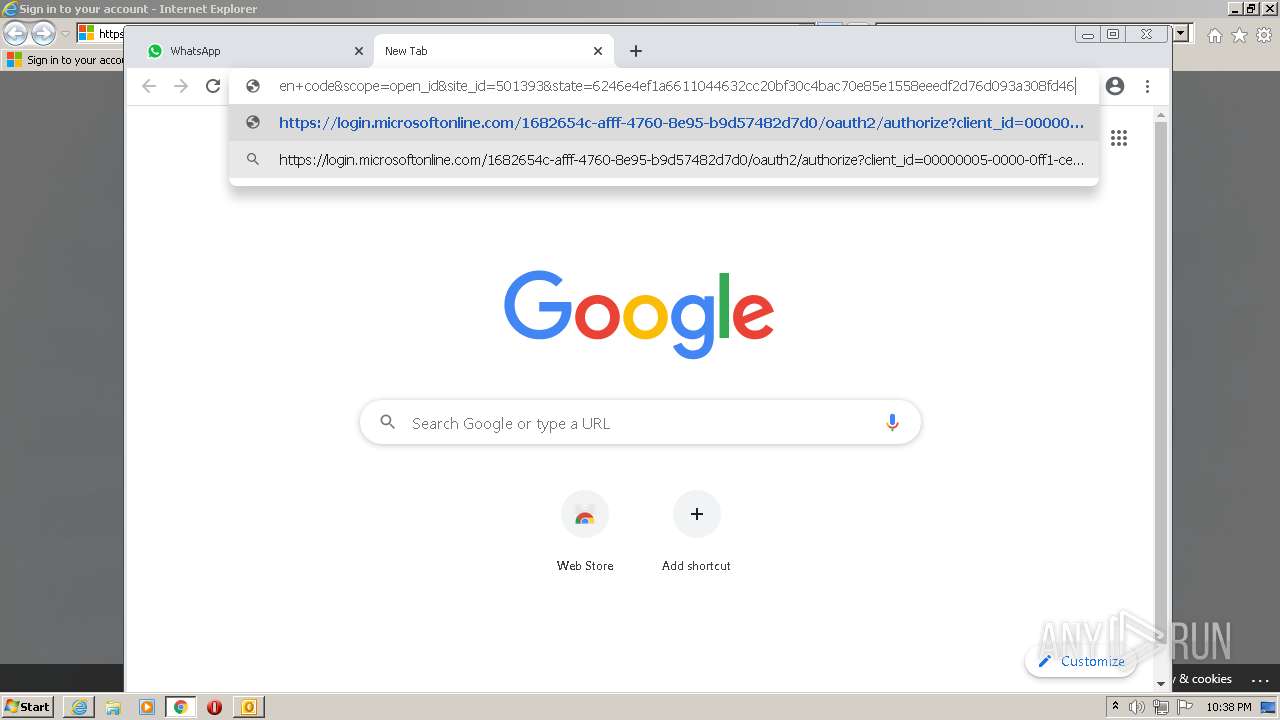
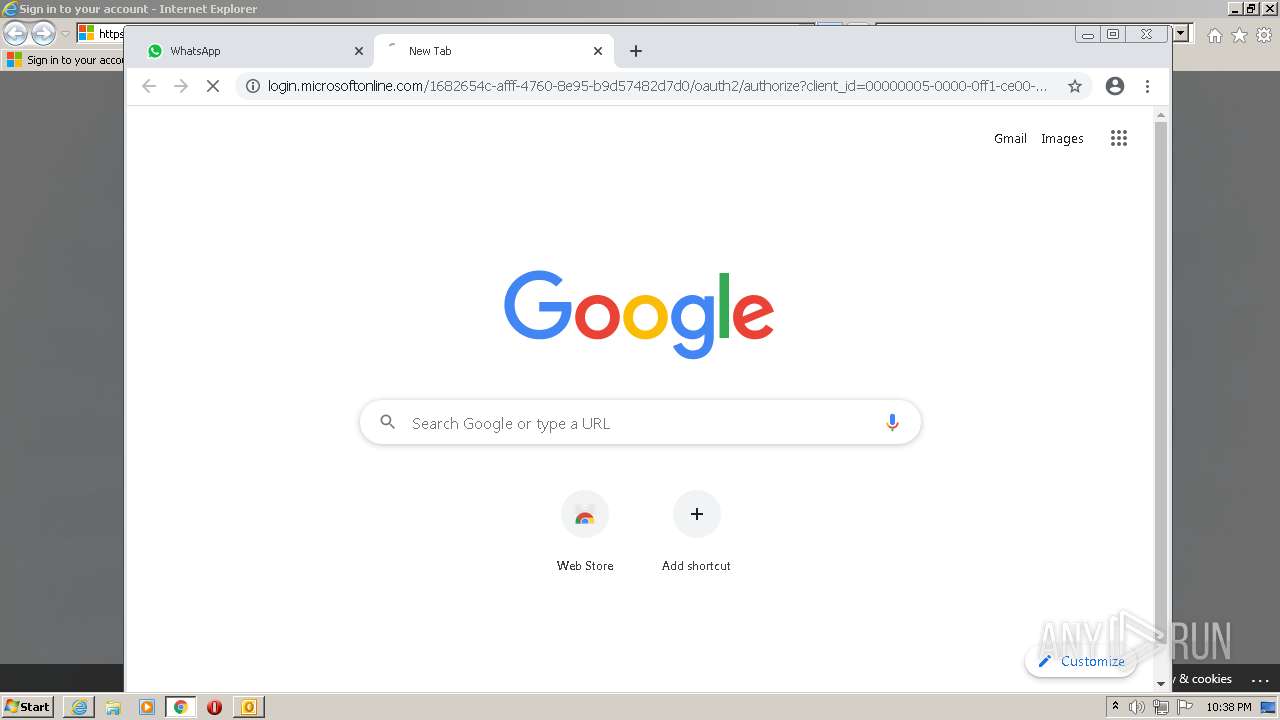
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1820)
Reads the computer name
- OUTLOOK.EXE (PID: 1820)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2516)
Modifies files in Chrome extension folder
- chrome.exe (PID: 516)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3208)
Executable content was dropped or overwritten
- chrome.exe (PID: 3208)
INFO
Reads the computer name
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 2784)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 516)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 3328)
- iexplore.exe (PID: 2516)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2408)
Checks supported languages
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 2784)
- chrome.exe (PID: 516)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3916)
- chrome.exe (PID: 296)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 4024)
- iexplore.exe (PID: 2516)
- chrome.exe (PID: 376)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 824)
Changes internet zones settings
- iexplore.exe (PID: 2212)
Reads settings of System Certificates
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2212)
- chrome.exe (PID: 3660)
- iexplore.exe (PID: 2516)
Checks Windows Trust Settings
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 2516)
Reads internet explorer settings
- iexplore.exe (PID: 2784)
- iexplore.exe (PID: 2516)
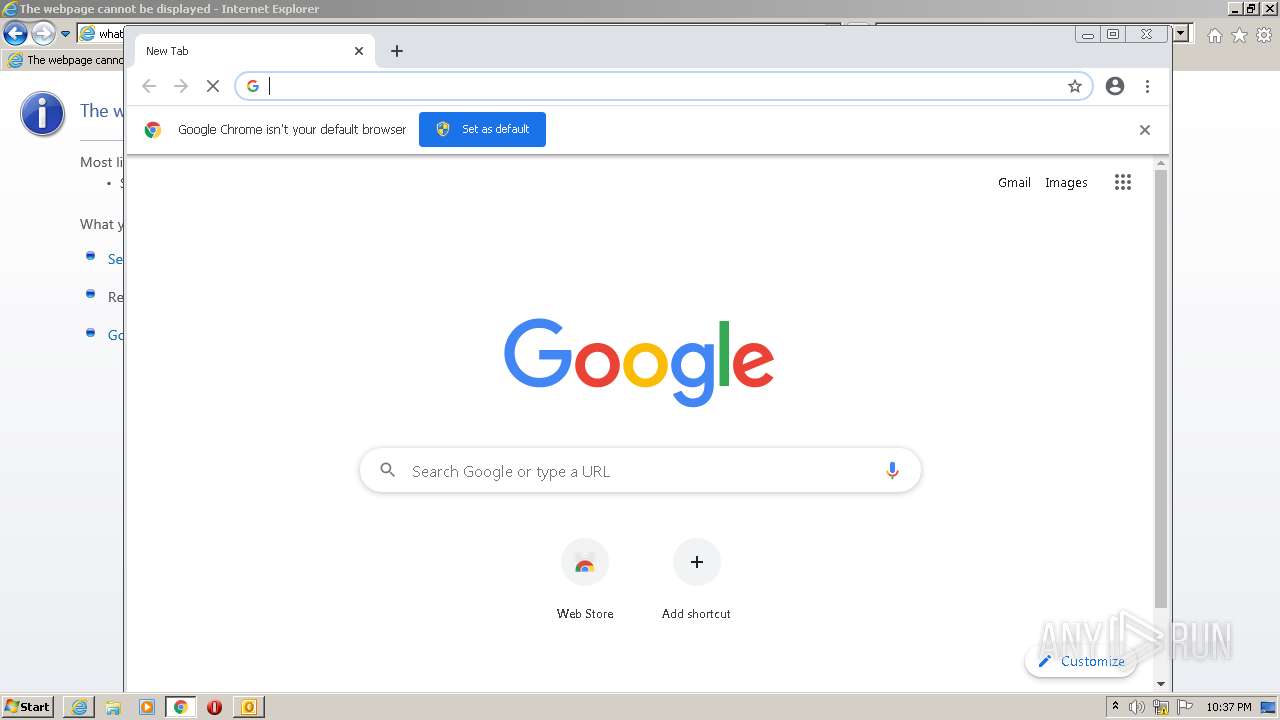
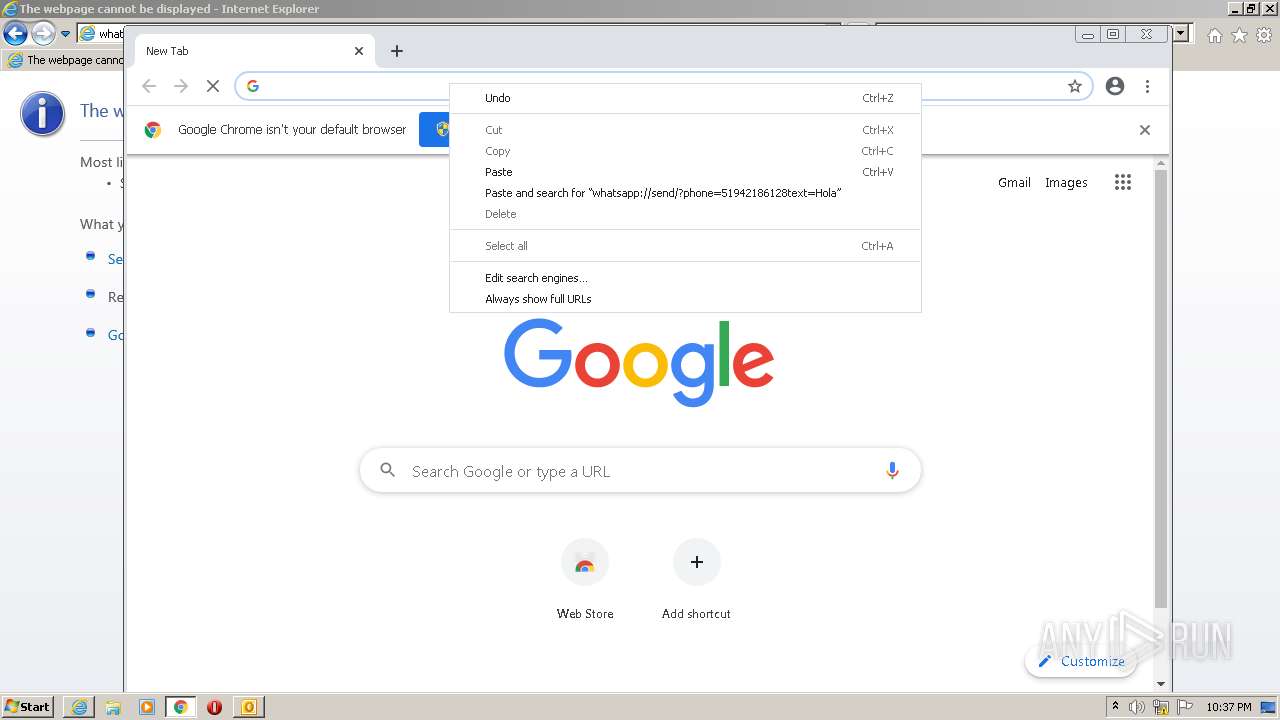
Application launched itself
- iexplore.exe (PID: 2212)
- chrome.exe (PID: 516)
Manual execution by user
- chrome.exe (PID: 516)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1820)
Reads the hosts file
- chrome.exe (PID: 516)
- chrome.exe (PID: 3660)
Creates files in the user directory
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 2212)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 2212)
Reads the date of Windows installation
- chrome.exe (PID: 2944)
Changes settings of System certificates
- iexplore.exe (PID: 2212)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
69
Monitored processes
29
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1820 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Announcement_ #lunesconlara #rimacmecuida ??Es importante que reportes.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
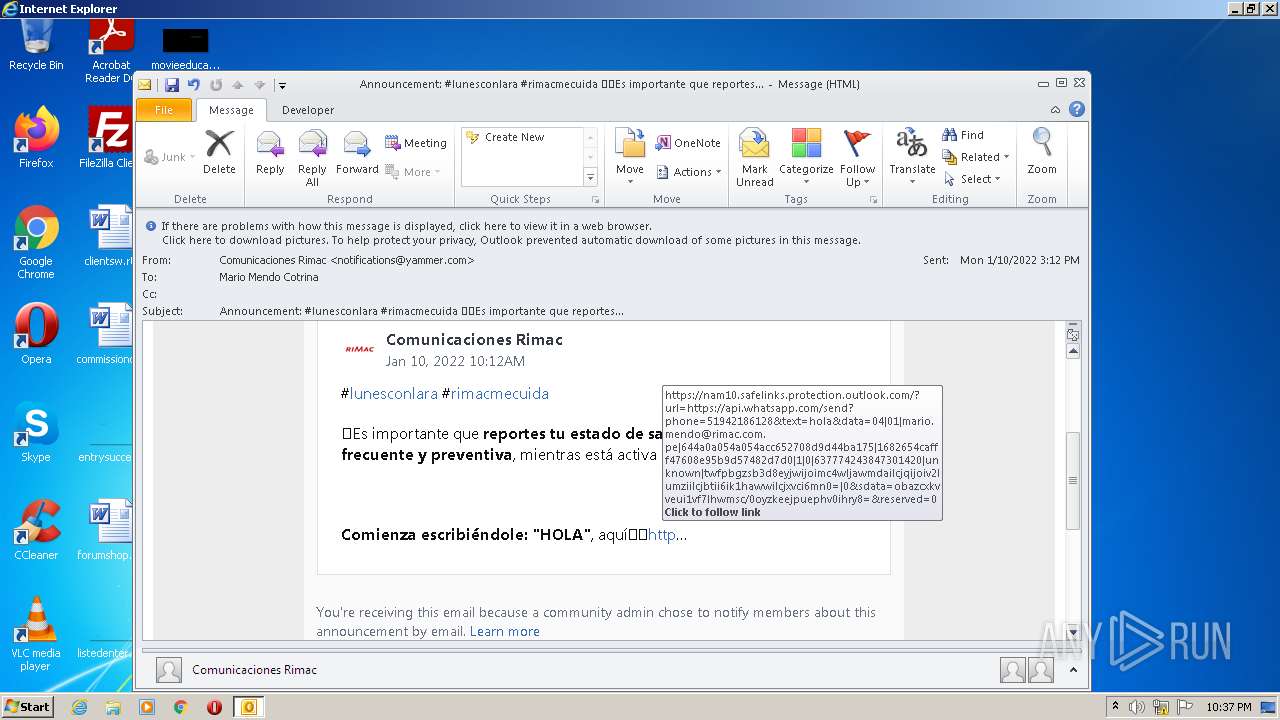
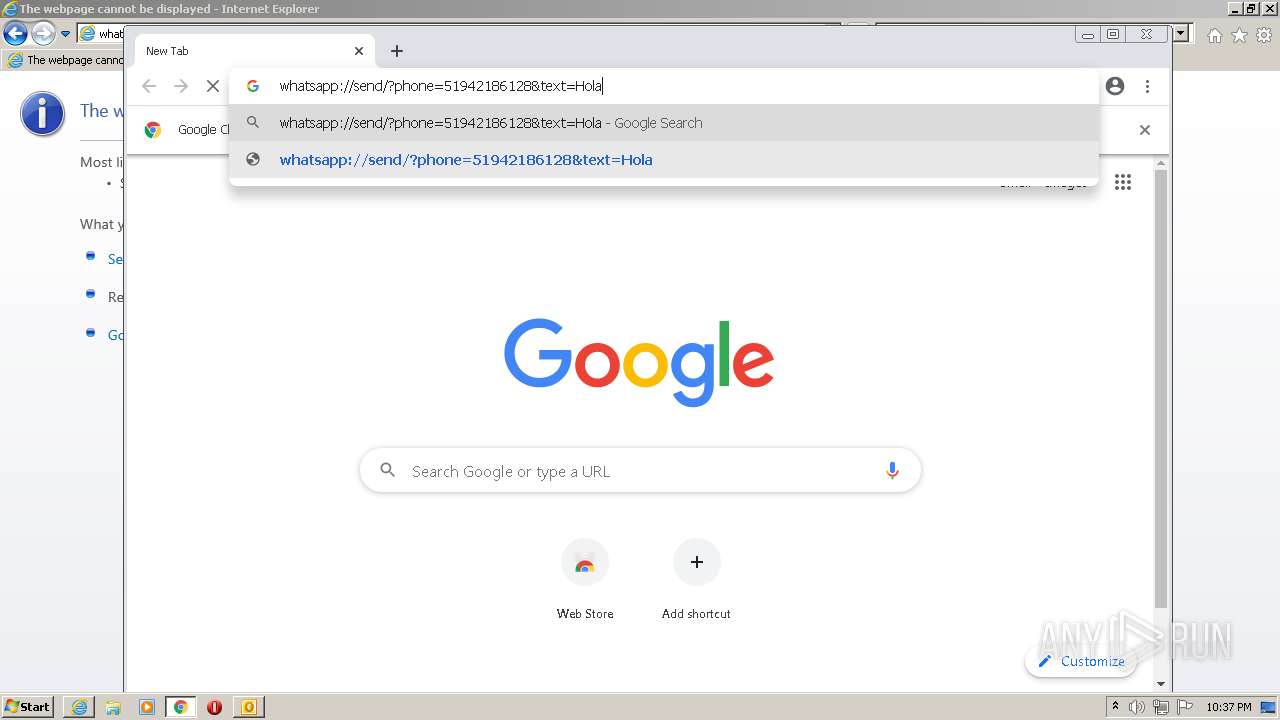
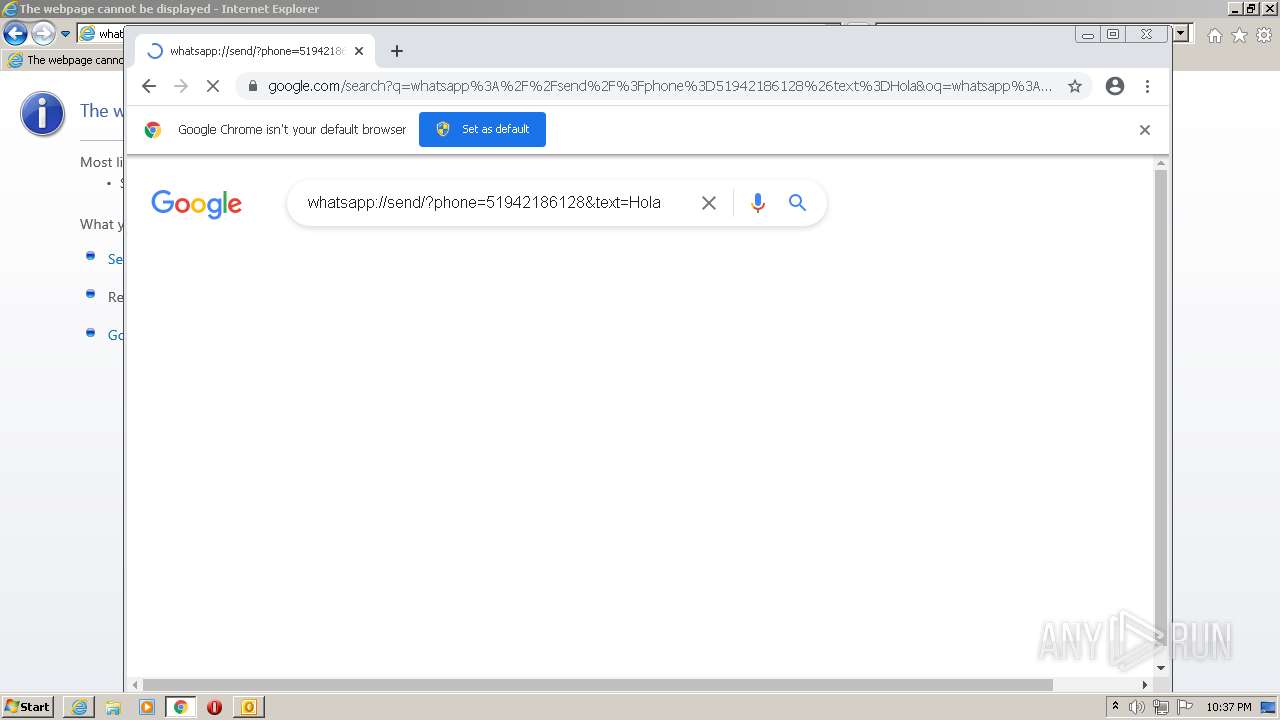
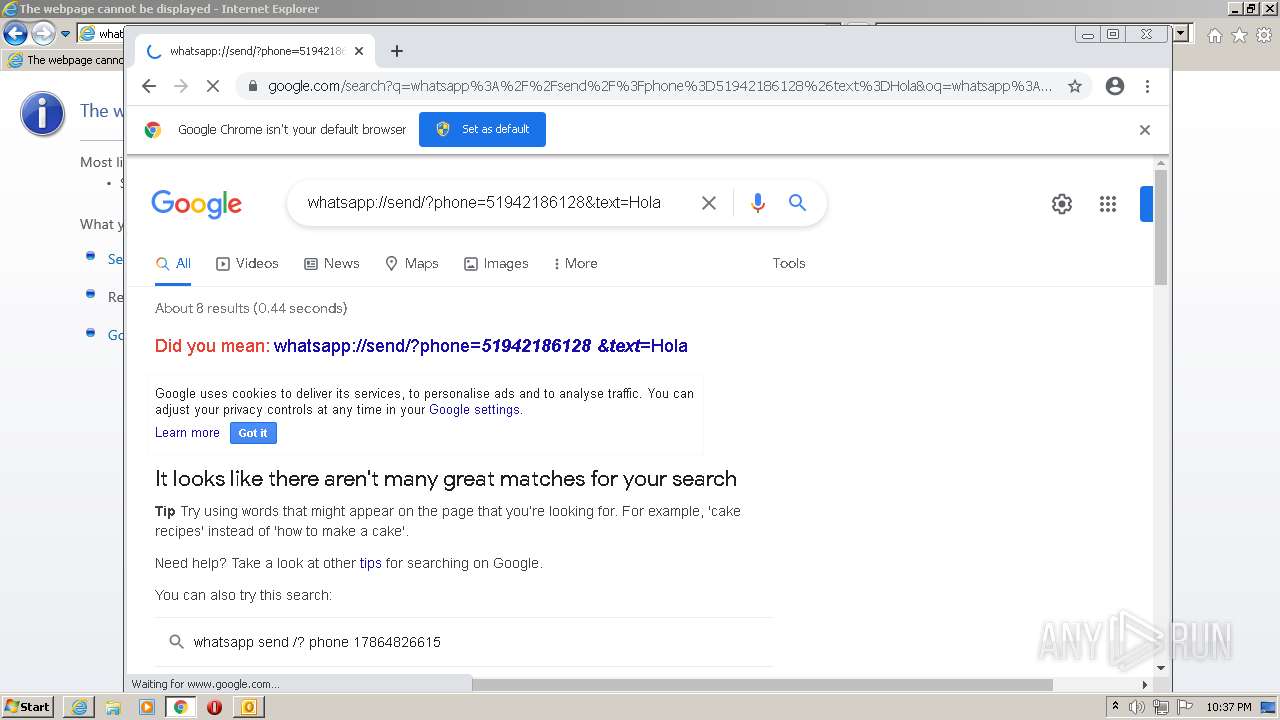
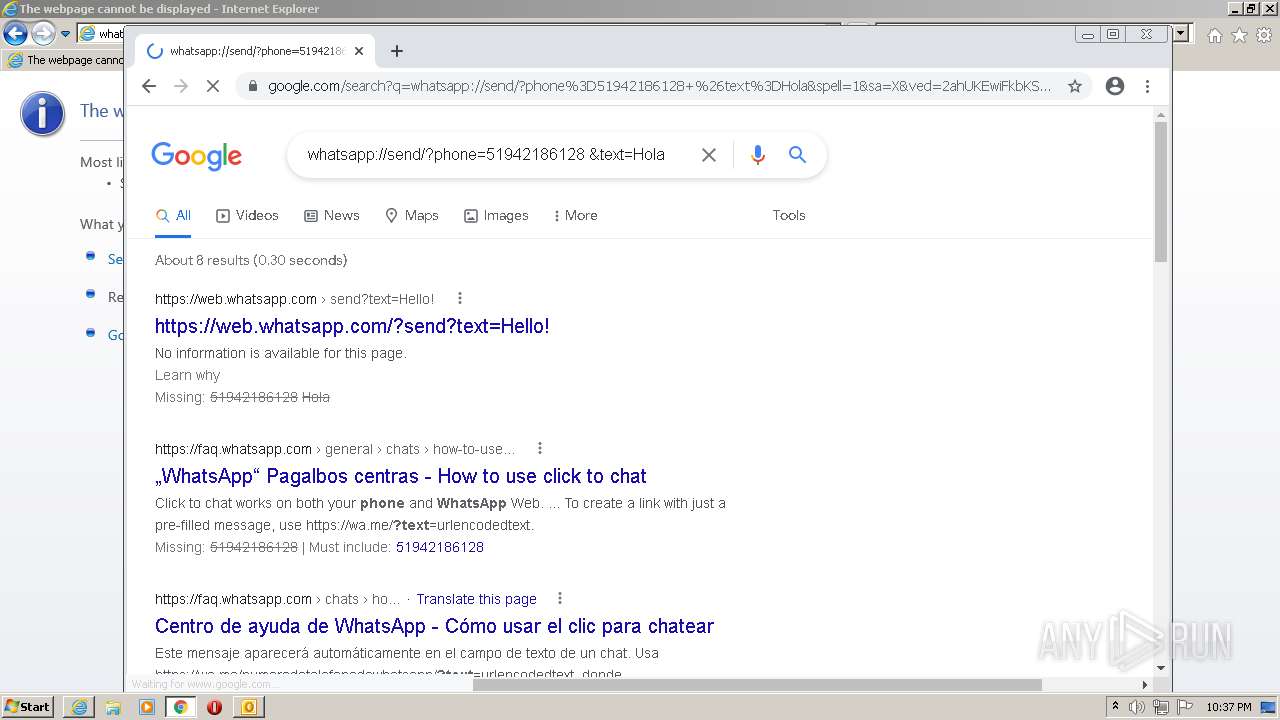
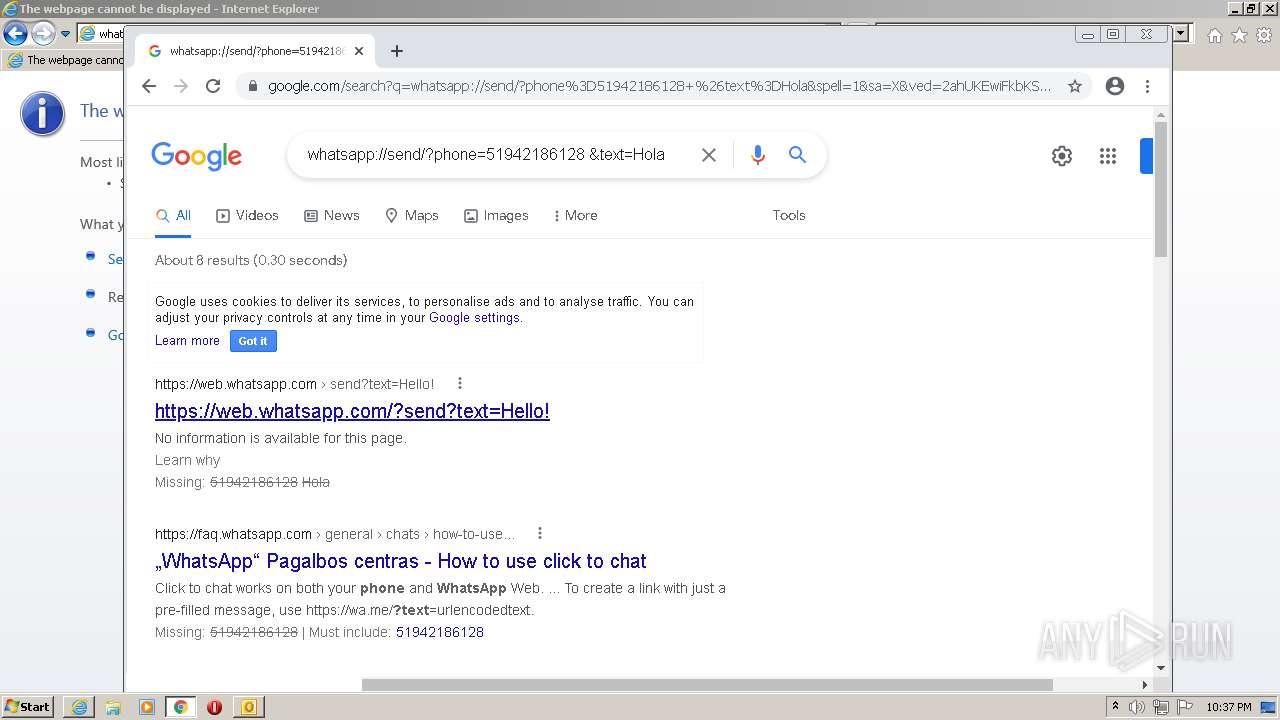
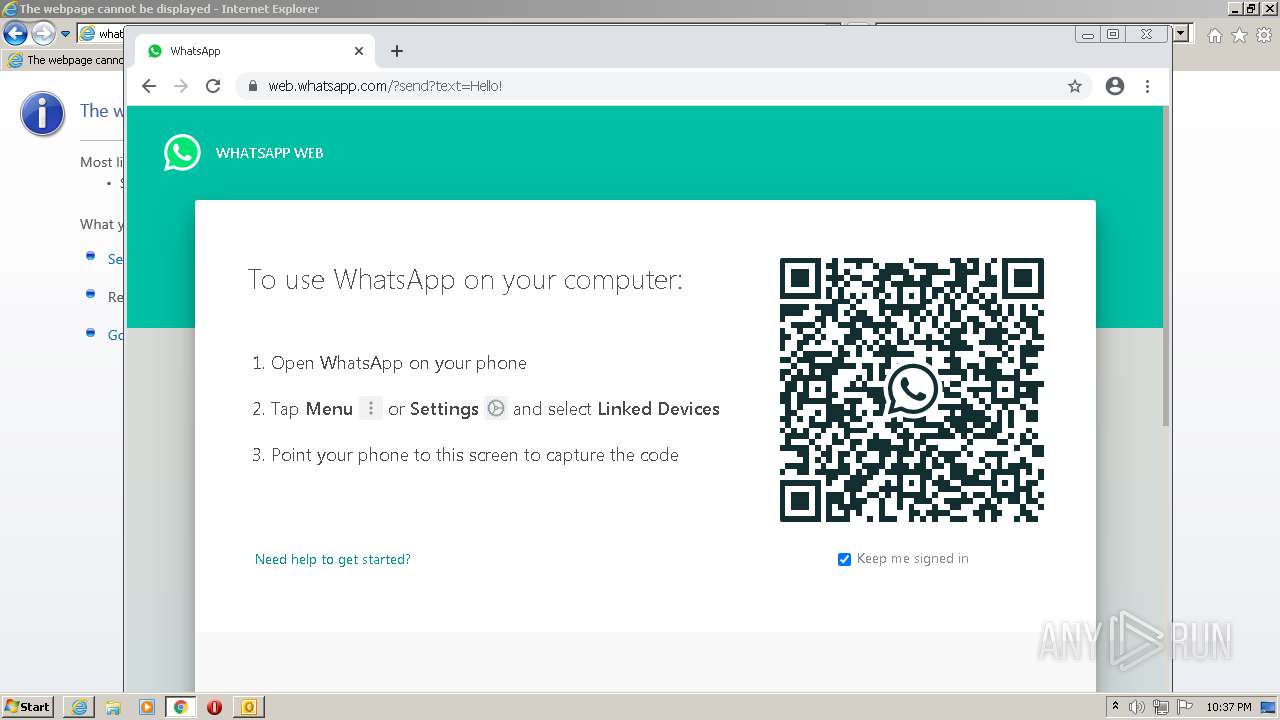
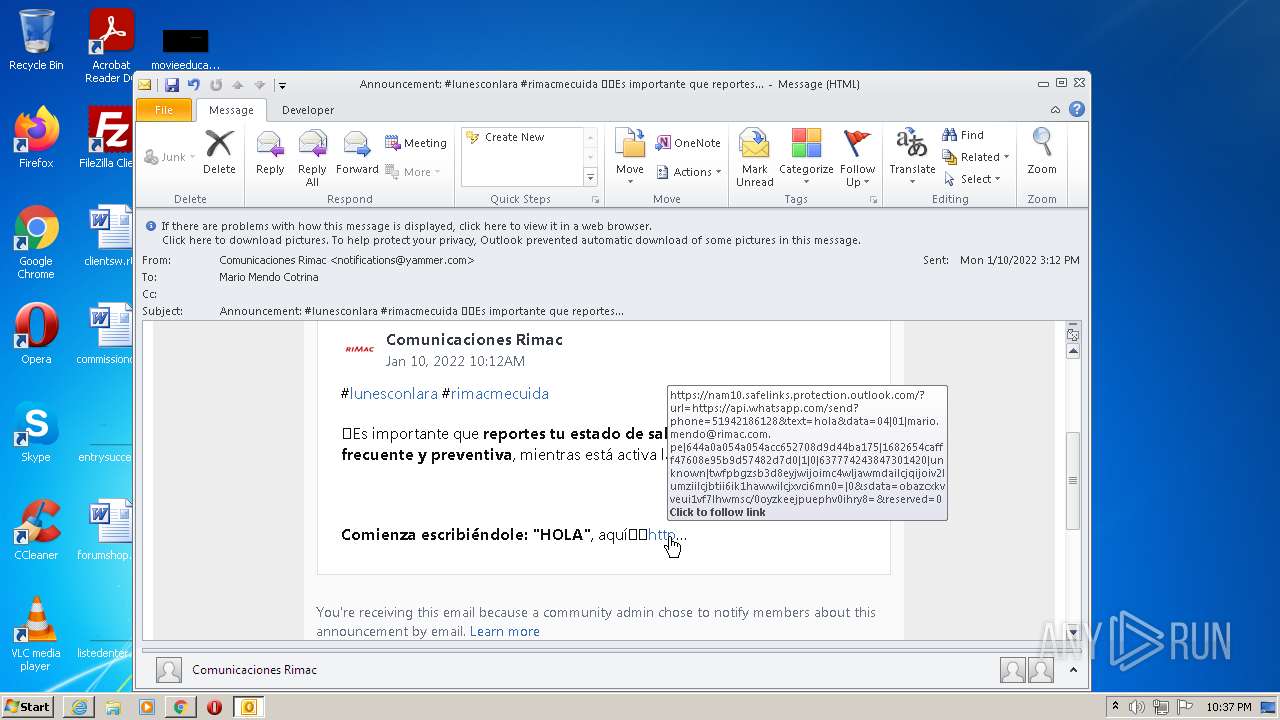
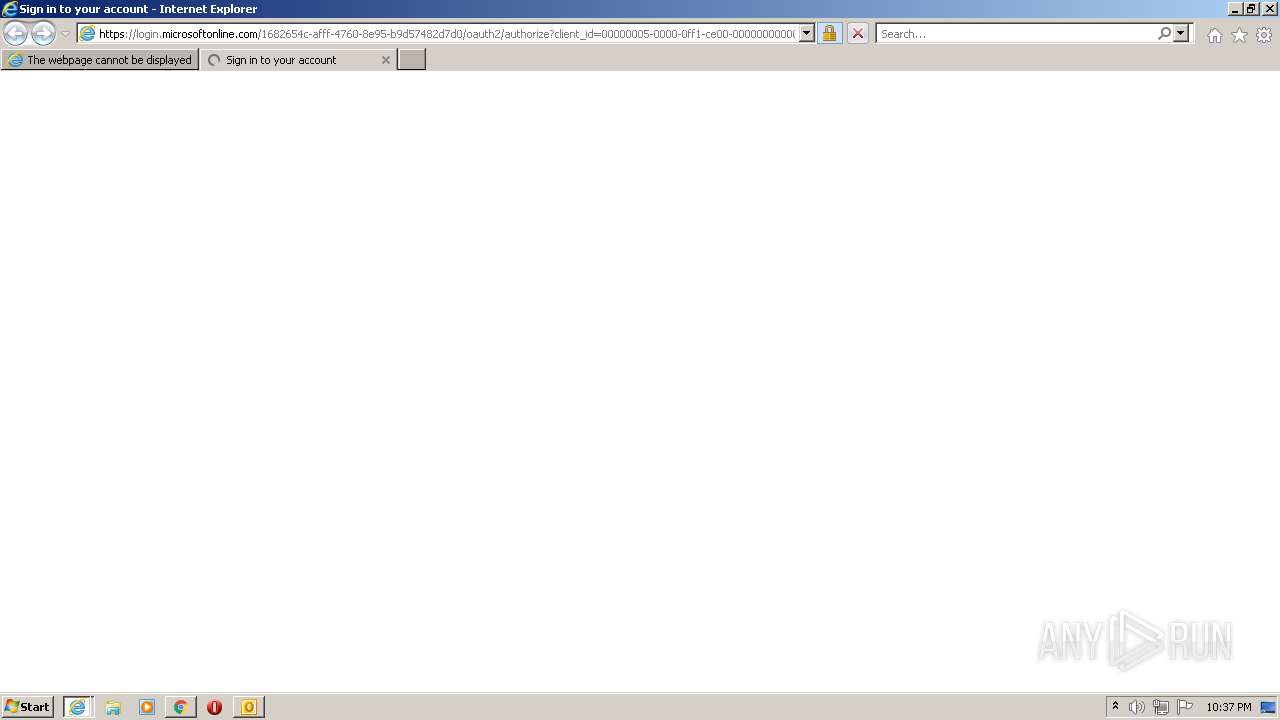
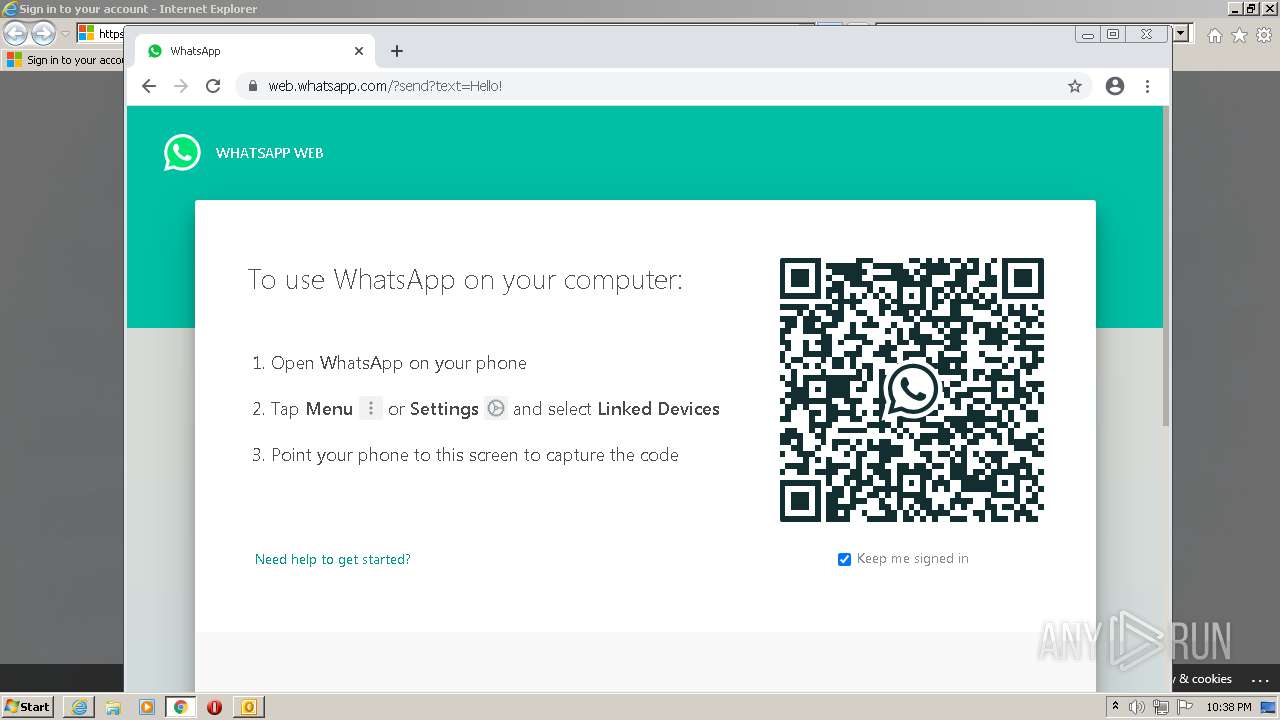
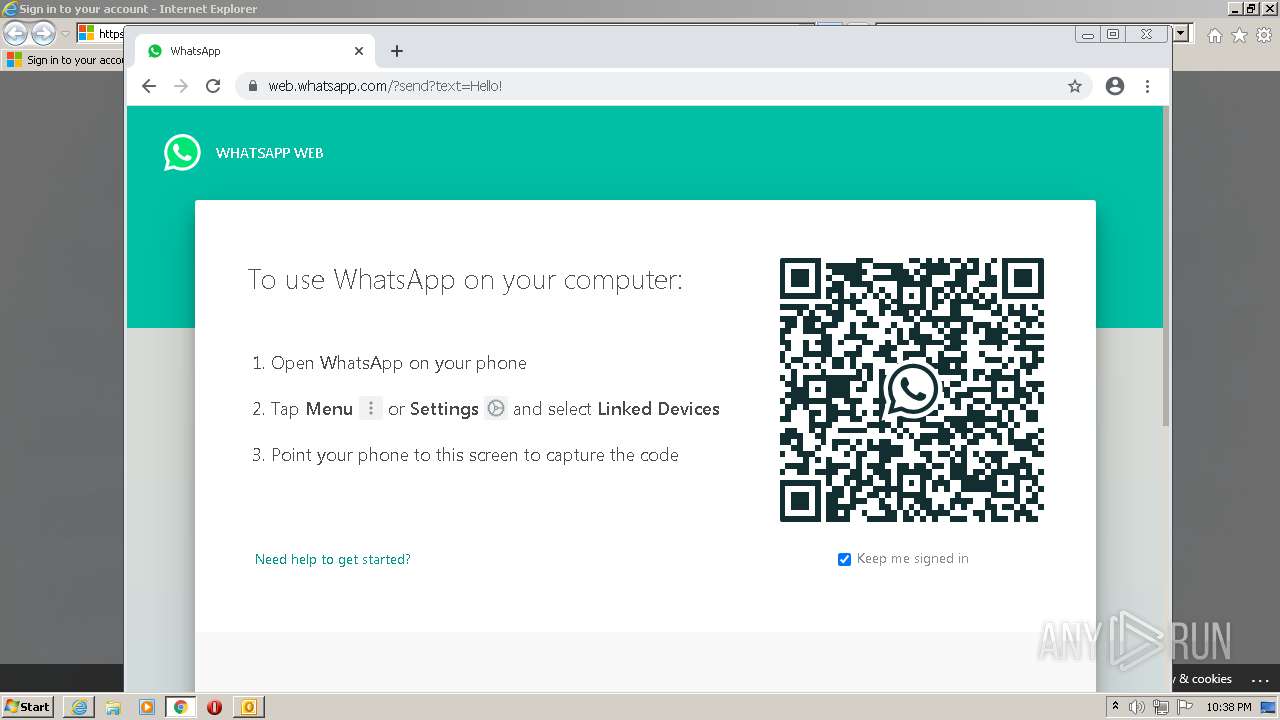
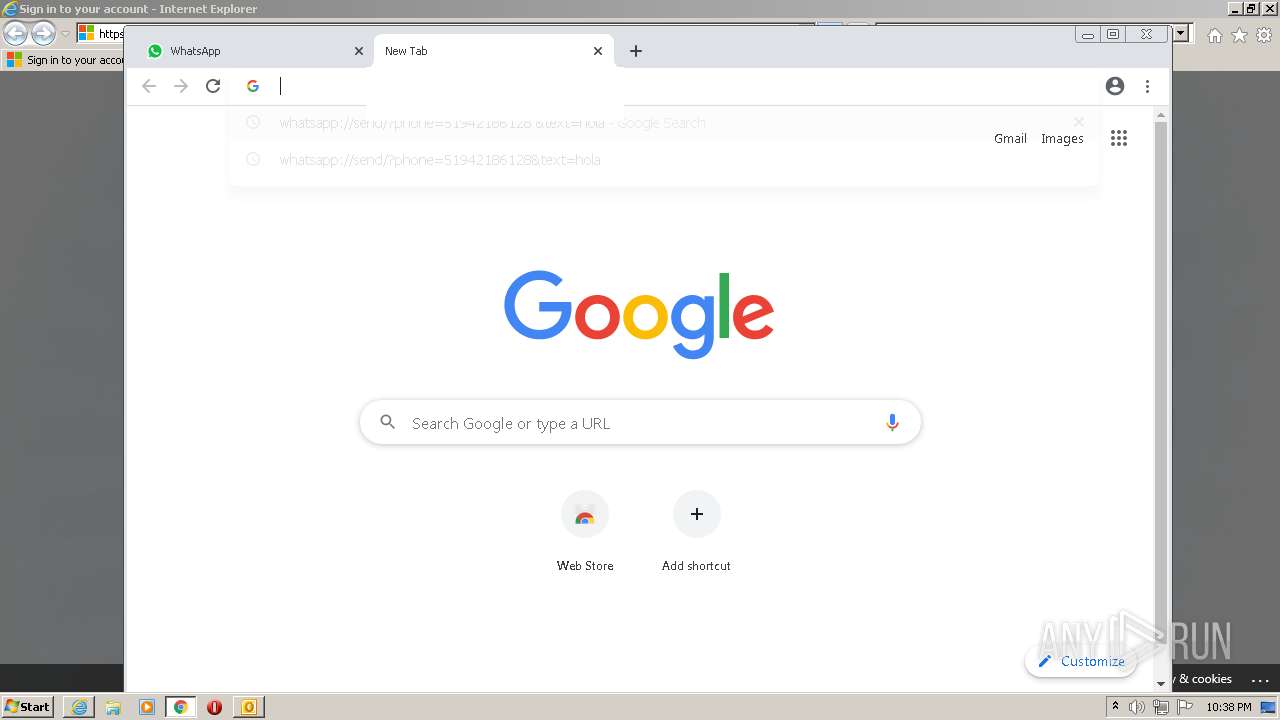
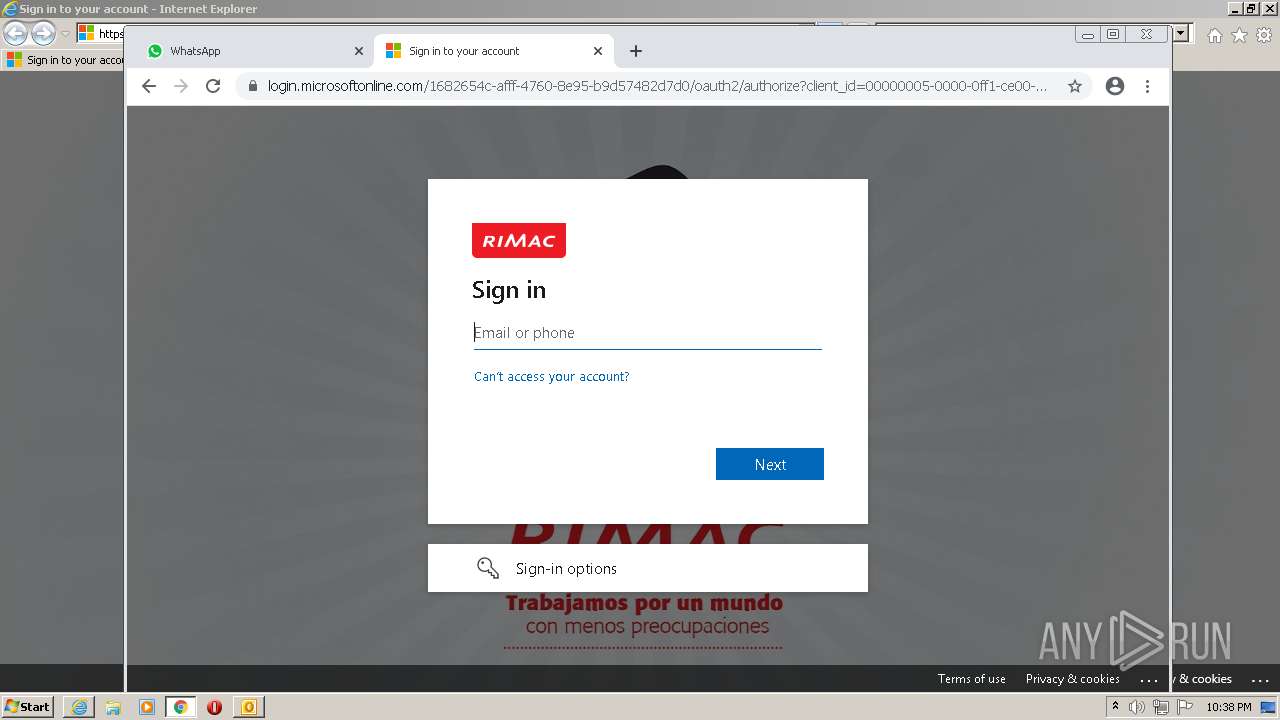
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam10.safelinks.protection.outlook.com/?url=https%3A%2F%2Fapi.whatsapp.com%2Fsend%3Fphone%3D51942186128%26text%3DHola&data=04%7C01%7Cmario.mendo%40rimac.com.pe%7C644a0a054a054acc652708d9d44ba175%7C1682654cafff47608e95b9d57482d7d0%7C1%7C0%7C637774243847301420%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C0&sdata=oBAZcXkvveUi1vF7lHWmsC%2F0OyzKEejPUephv0iHry8%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5850769246362361337,16740662958624255337,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2212 CREDAT:202000 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
33 938
Read events
33 055
Write events
853
Delete events
30
Modification events
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1820) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
231
Text files
183
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1820 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR317D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1820 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1820 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | der | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_A371495D1958289D6CA43CAA429AF26A | der | |
MD5:— | SHA256:— | |||
| 1820 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2F23D0F5E4D72862517E1CB26A329742_F6FACC49395CFA949BCE851E73323C49 | binary | |
MD5:— | SHA256:— | |||
| 2784 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
96
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1820 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 173.194.183.106:80 | http://r5---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx?cms_redirect=yes&mh=X7&mip=185.192.69.73&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1642199541&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigl6nek.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6nsr.gvt1.com | US | — | — | whitelisted |
2784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
2212 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA2pmcJTM%2F93f%2Bfswe%2F7nPE%3D | US | der | 471 b | whitelisted |
2784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAGewca9P1l7sgwzOOVR2Hc%3D | US | der | 471 b | whitelisted |
2784 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAhFMjccjkHQHxWs2V0z2XQ%3D | US | der | 471 b | whitelisted |
2516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
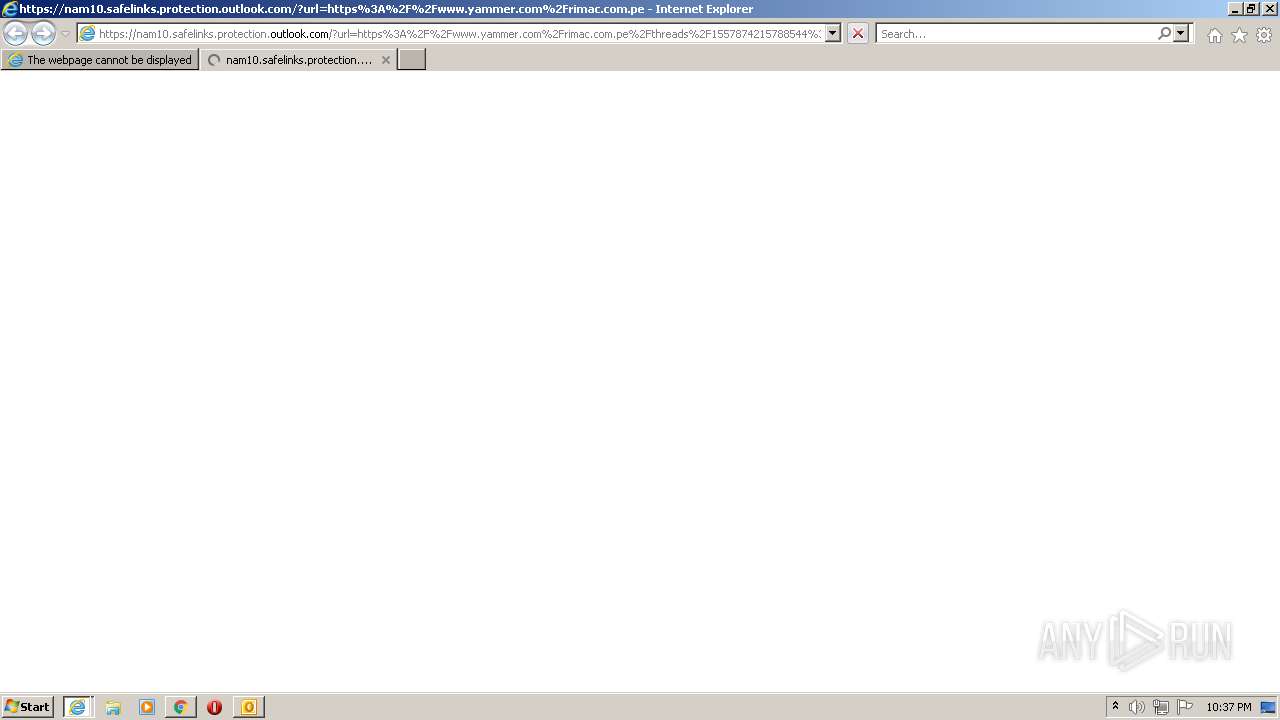
2784 | iexplore.exe | 104.47.58.28:443 | nam10.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
2784 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2784 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2784 | iexplore.exe | 31.13.84.51:443 | api.whatsapp.com | Facebook, Inc. | IE | suspicious |
2212 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2784 | iexplore.exe | 157.240.27.27:443 | static.xx.fbcdn.net | Facebook, Inc. | US | unknown |
3660 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3660 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3660 | chrome.exe | 142.250.186.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3660 | chrome.exe | 142.250.186.130:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nam10.safelinks.protection.outlook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.whatsapp.com |
| whitelisted |
static.xx.fbcdn.net |
| whitelisted |
pps.whatsapp.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |