analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
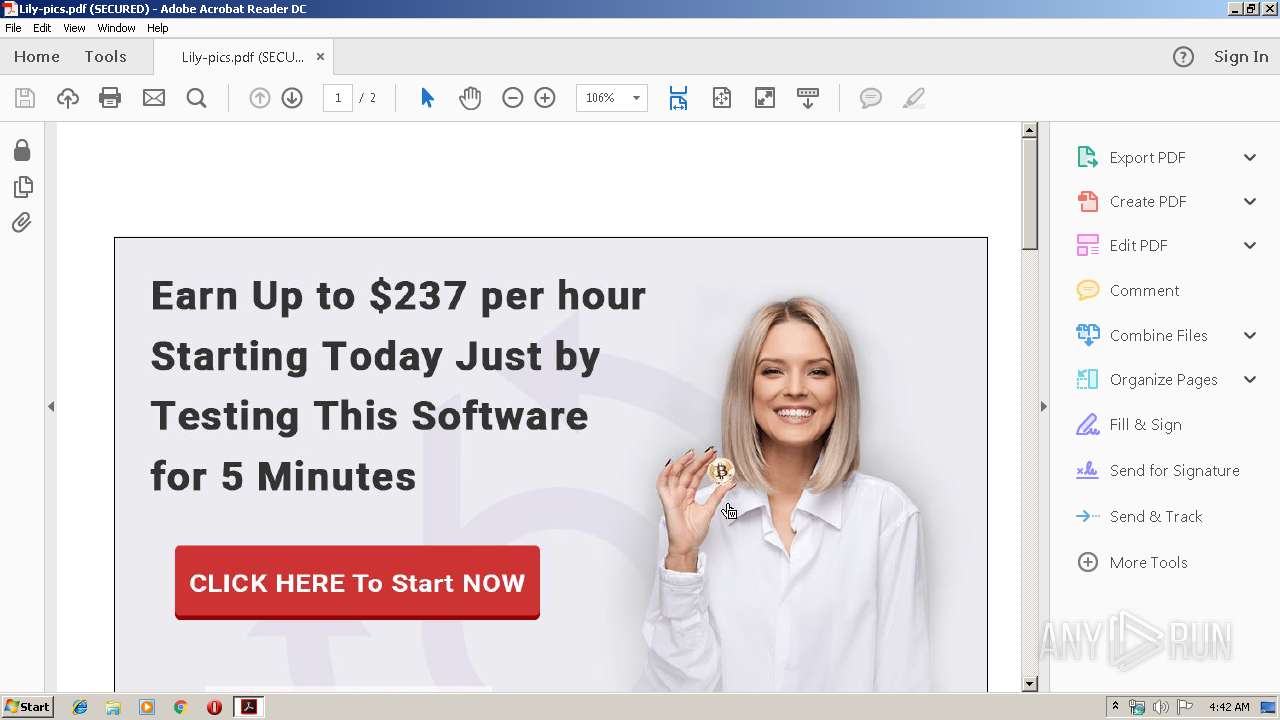
| File name: | Lily-pics.pdf |
| Full analysis: | https://app.any.run/tasks/ad6a12cc-8766-42fe-8898-3dbaf3de9793 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 03:42:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4 |
| MD5: | 3A57EF523D836AD5B76502658C8ED8CE |
| SHA1: | 8C27CABC33AC1C5CEF8AE9417CC2A134C11340A9 |
| SHA256: | E7C0AAE0F542D75FB1B1E6F005EBB3179B0CD1EA082B8E154EB4A9DEFA603FB2 |
| SSDEEP: | 1536:DBamNSCBlcwzwkO/hRzOa0evs0NlTeQWVhIOj2k+7UJ0DPB2N+grv:9NNSelcwzJQrs0N14hIc2kpJ0DP4N+6v |
MALICIOUS
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 2304)
- MsiExec.exe (PID: 2500)
SUSPICIOUS
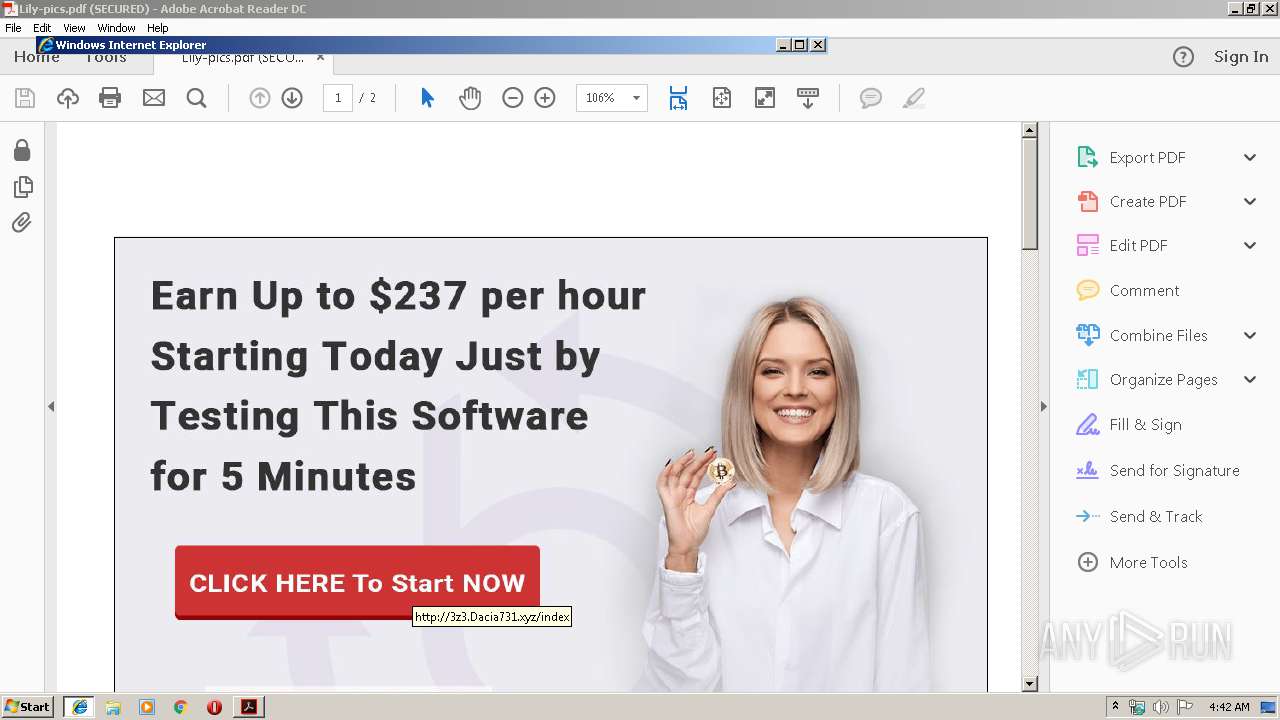
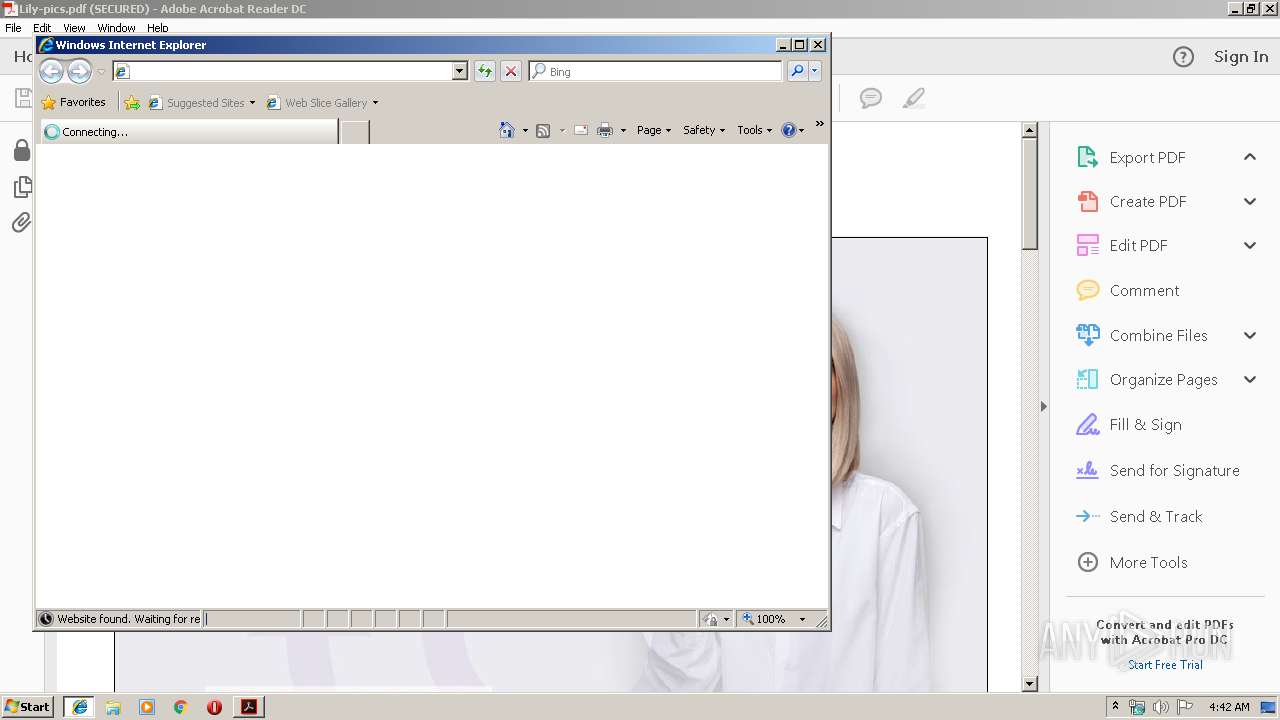
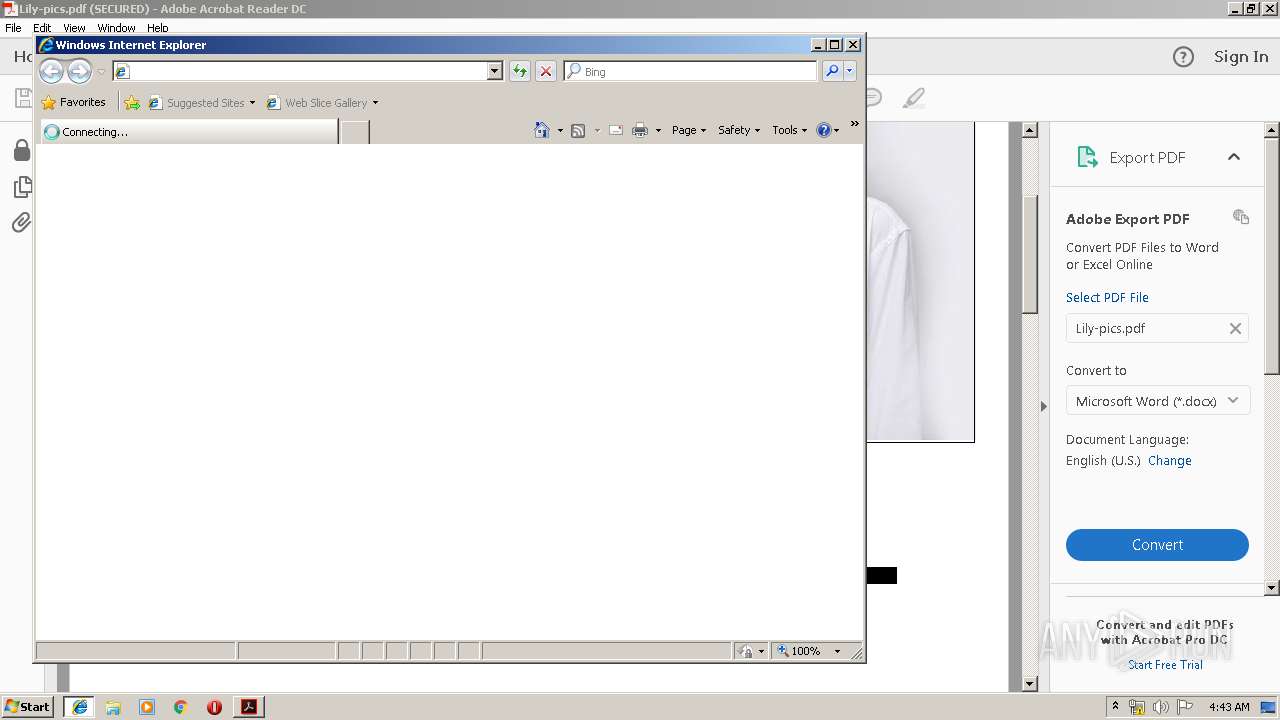
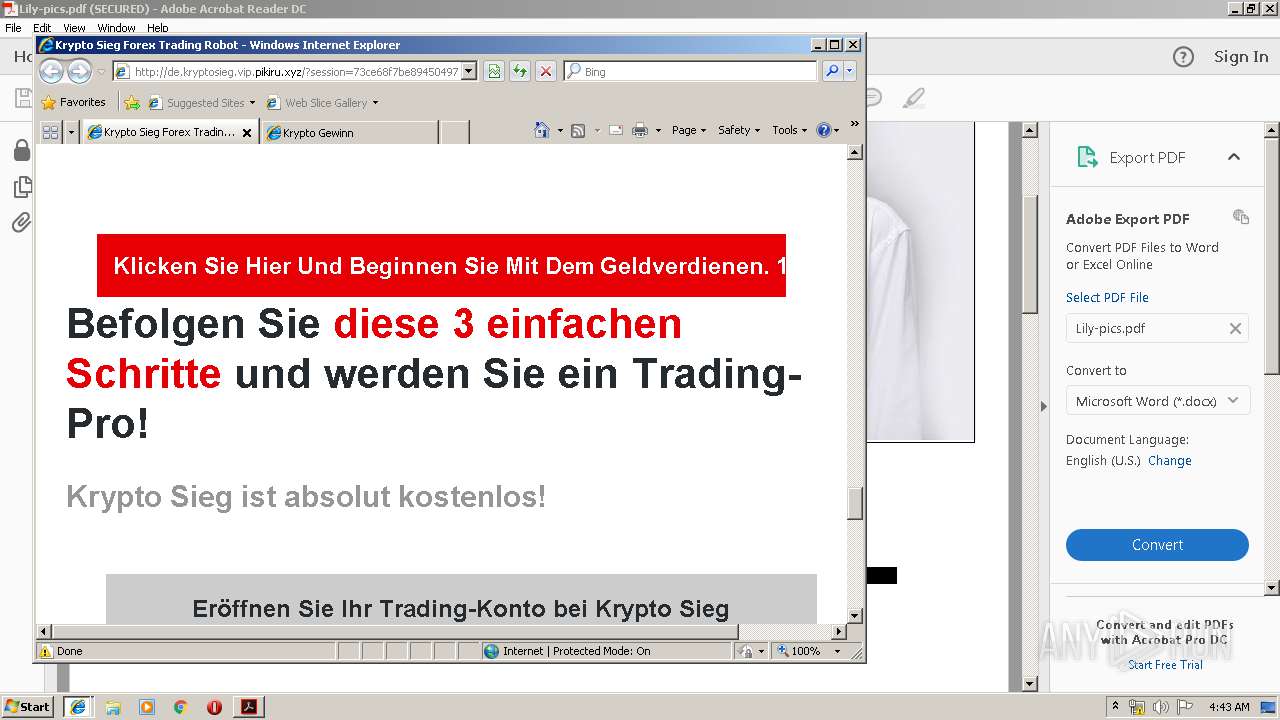
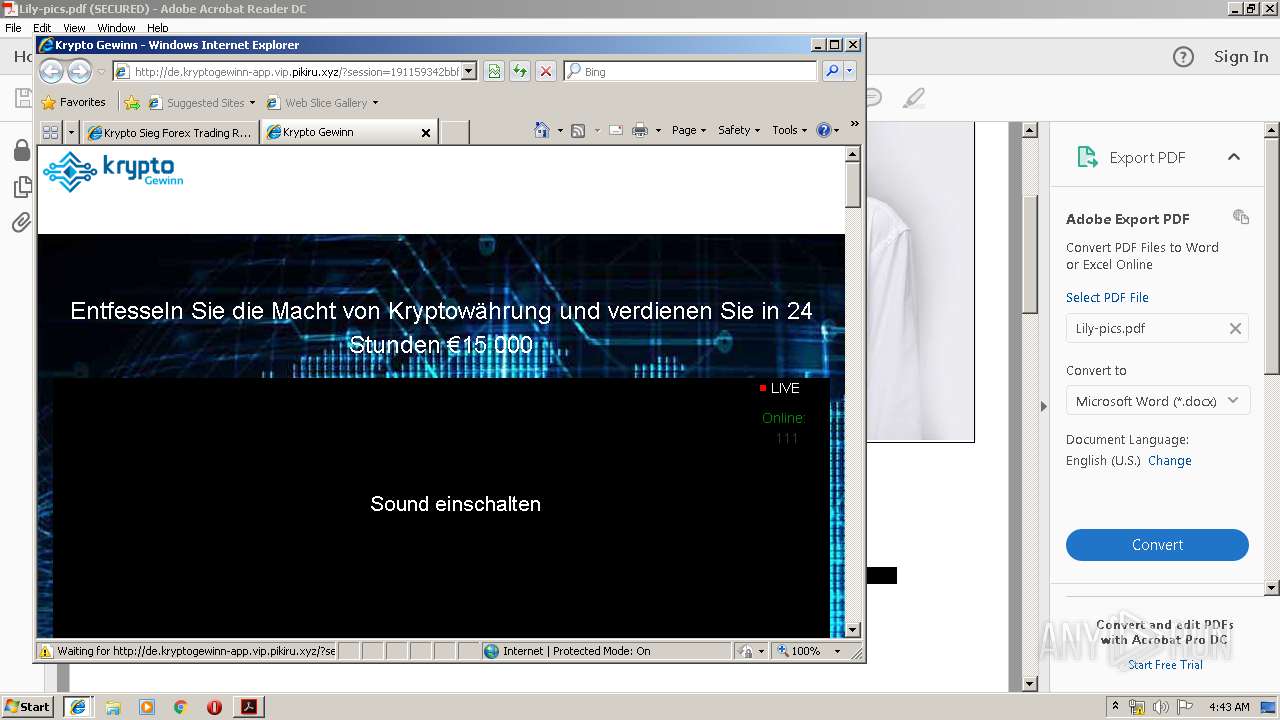
Starts Internet Explorer
- AcroRd32.exe (PID: 3628)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2380)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2480)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2416)
Creates files in the program directory
- AdobeARM.exe (PID: 3132)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 3132)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2072)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2380)
- iexplore.exe (PID: 2476)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2480)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 2352)
- AcroRd32.exe (PID: 3628)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2416)
Reads Internet Cache Settings
- iexplore.exe (PID: 2072)
- AcroRd32.exe (PID: 3628)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 2352)
Changes internet zones settings
- iexplore.exe (PID: 2476)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 2408)
Application launched itself
- iexplore.exe (PID: 2476)
- AcroRd32.exe (PID: 3628)
- RdrCEF.exe (PID: 2496)
- iexplore.exe (PID: 2920)
- msiexec.exe (PID: 2100)
Reads internet explorer settings
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 2352)
- iexplore.exe (PID: 3672)
Reads settings of System Certificates
- iexplore.exe (PID: 2476)
- iexplore.exe (PID: 2072)
- iexplore.exe (PID: 504)
- iexplore.exe (PID: 2352)
- iexplore.exe (PID: 3672)
- msiexec.exe (PID: 2100)
Creates files in the program directory
- msiexec.exe (PID: 2100)
Creates a software uninstall entry
- msiexec.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
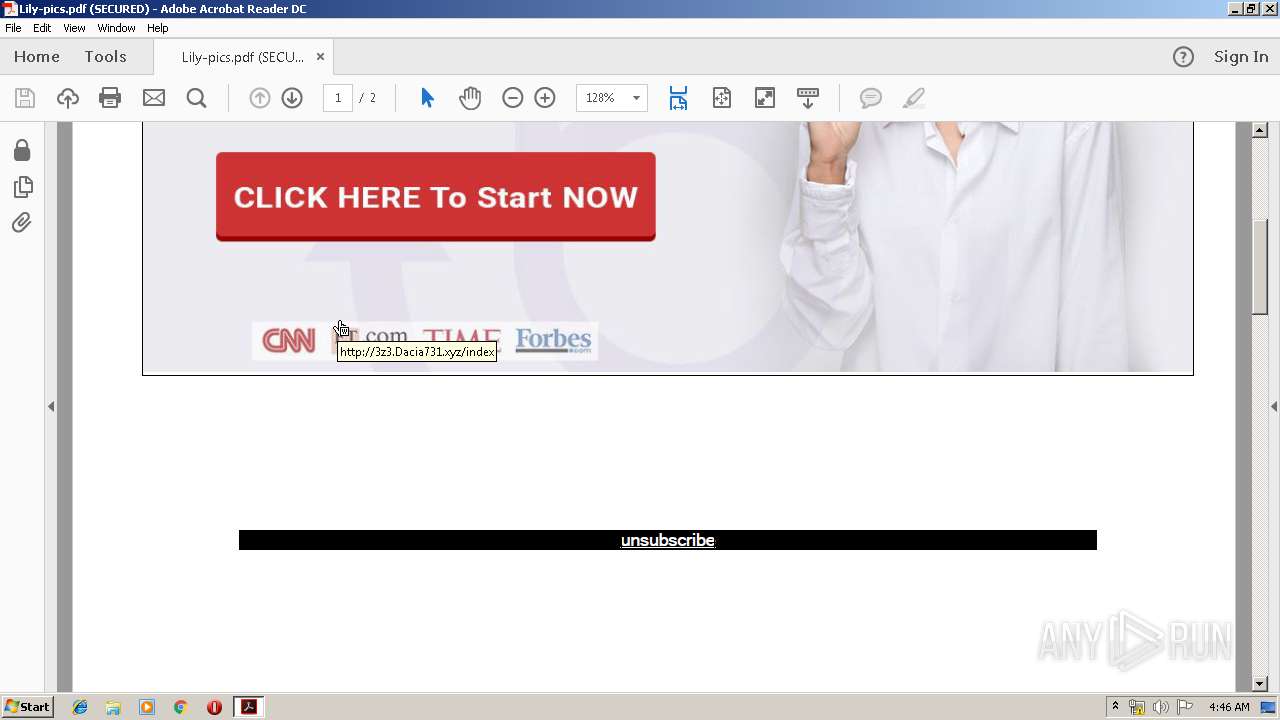
| PageCount: | 2 |
|---|---|
| Producer: | PDFsharp 1.31.1789-g (www.pdfsharp.com) |
| Creator: | Adobe Acrobat Reader |
| Author: | Костя Кузнецов |
| Title: | 34-Ilsfq_bzmox7rn |
| Subject: | Саратов 38 Male 410056 |
| CreateDate: | 2016:04:10 08:19:19-07:00 |
| UserAccess: | Print, Copy, Extract, Assemble |
| Encryption: | Standard V2.3 (128-bit) |
| Linearized: | No |
| PDFVersion: | 1.4 |
Total processes
55
Monitored processes
20
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3628 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\Lily-pics.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\Lily-pics.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2476 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 4072 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2496.0.1858561753\902703459" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2496.1.1018992275\1273879473" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2380 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2740 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
2 164
Read events
1 779
Write events
360
Delete events
25
Modification events
| (PID) Process: | (2916) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2916) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bForms_AdhocWorkflowBackup |
Value: 0 | |||
| (PID) Process: | (2916) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bJSCache_GlobSettings |
Value: 0 | |||
| (PID) Process: | (2916) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bJSCache_GlobData |
Value: 1 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
24
Text files
152
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RFMLGAHM\de_kryptogewinn-app_vip_pikiru_xyz[1].htm | — | |
MD5:— | SHA256:— | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:E6EFF1D72D5C4DD84B0BAD80486CB887 | SHA256:47F4A7B33F3676D0D7EBD4F24E1DB9146E0D2460AE1C2E95AD3D9298B83DFDE3 | |||
| 2916 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages | sqlite | |
MD5:71289F8F8D3000638A846F994C51E52B | SHA256:A67239B25EF289BB16B95FEB12A1D0A77FEF6772CD26901970BCE3116D81FCB9 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\[email protected][1].txt | text | |
MD5:FD2B496CF284481D9AE34E1F0169CCC9 | SHA256:8F047A8E62645A0756F55E5A94E2713B36F45D287F63BB2BAB504EF737F6398F | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:EC4F524779457FB5CB4654DD2F21DF48 | SHA256:3BE03E5EF9320318C5145F0F595457E6DC5939090A37F6F91EC33E5233AC0FAA | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@pikiru[1].txt | text | |
MD5:65D53AFF44F452C82E9FE44CC8F241D3 | SHA256:85C391531DA3912AE8E2389C99E9AB8449791F7DD096D8D24BF8B9639D148534 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019082620190827\index.dat | dat | |
MD5:A8D94516F1983E17617E0FB75D2B44EE | SHA256:05F00BF6246375198A05CF2F1917256F3A1A40D7FDACF8FA03E8FE510D219570 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6A2OB0X7\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6A2OB0X7\32[1].jpg | image | |
MD5:2D562B802AEDFA0D405A9778B0480D18 | SHA256:5A0224912D3B4404D87986DC107061F775395DC92BDCEDE79EAD6DE91DF0C387 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
76
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
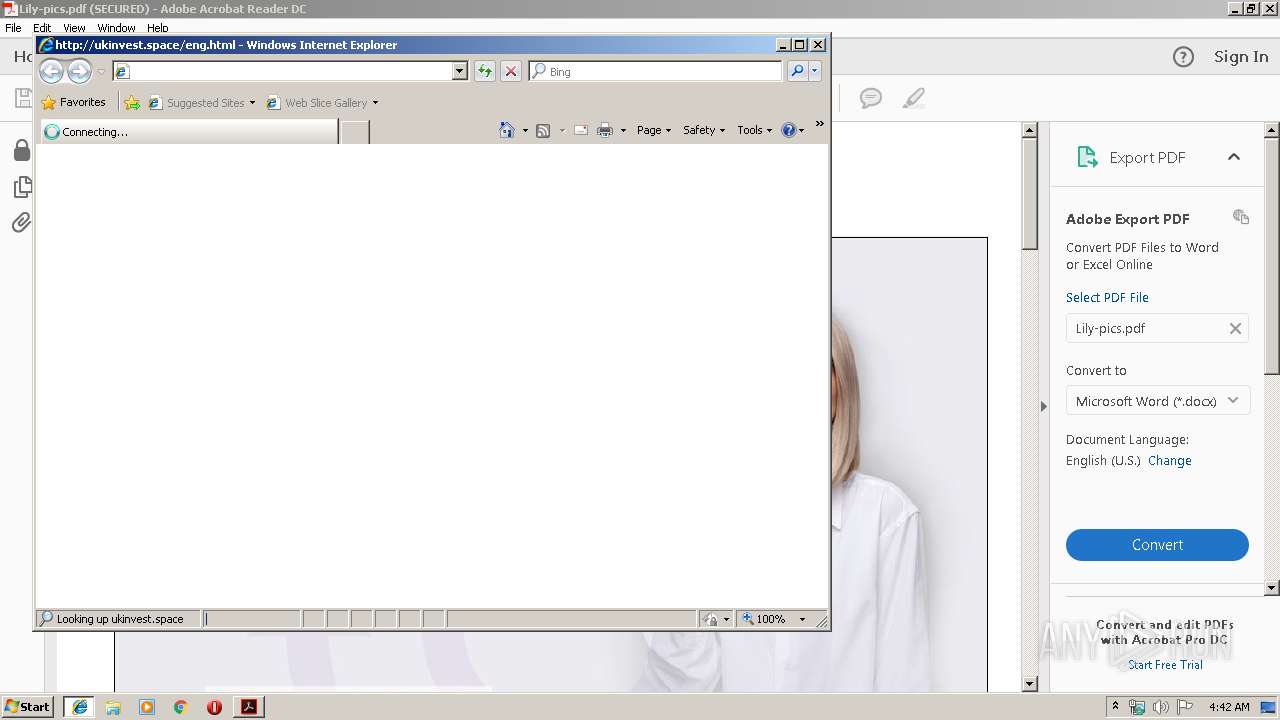
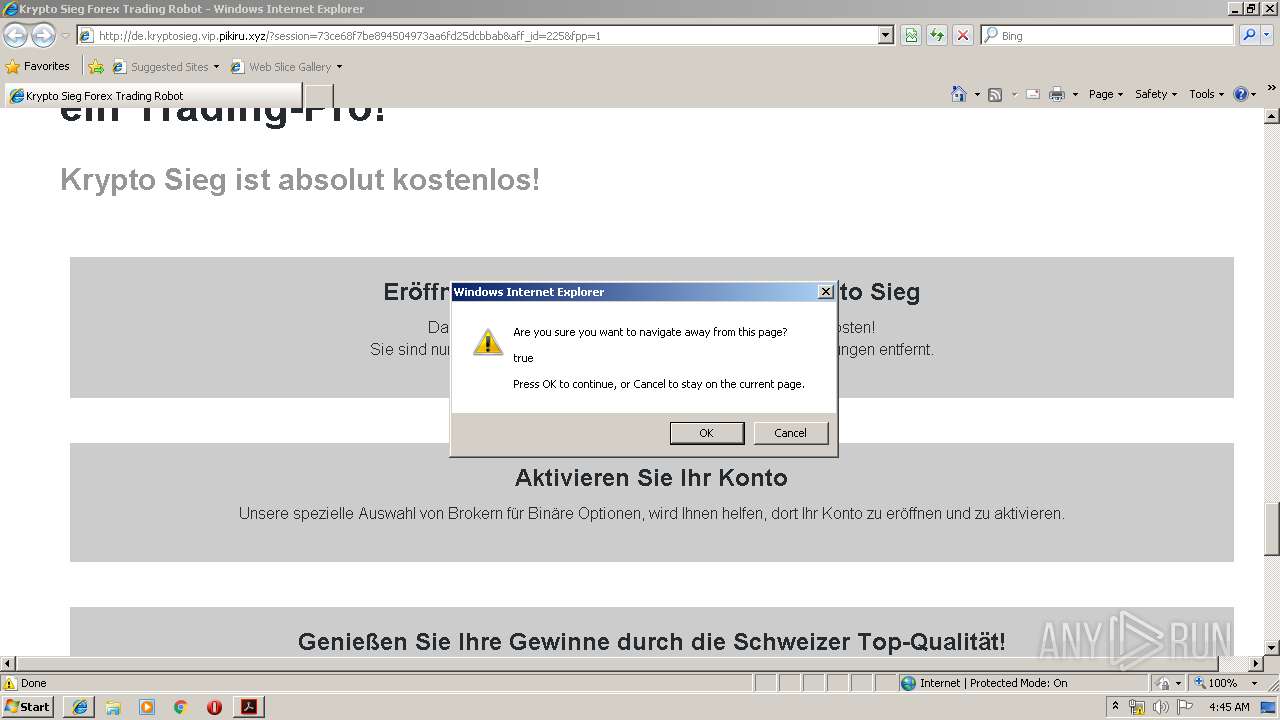
2476 | iexplore.exe | GET | 302 | 51.15.253.163:80 | http://ukinvest.space/favicon.ico | FR | — | — | suspicious |
2072 | iexplore.exe | GET | 302 | 104.31.81.87:80 | http://vip.pikiru.xyz/tracker?offer_id=3515&aff_id=225 | US | — | — | suspicious |
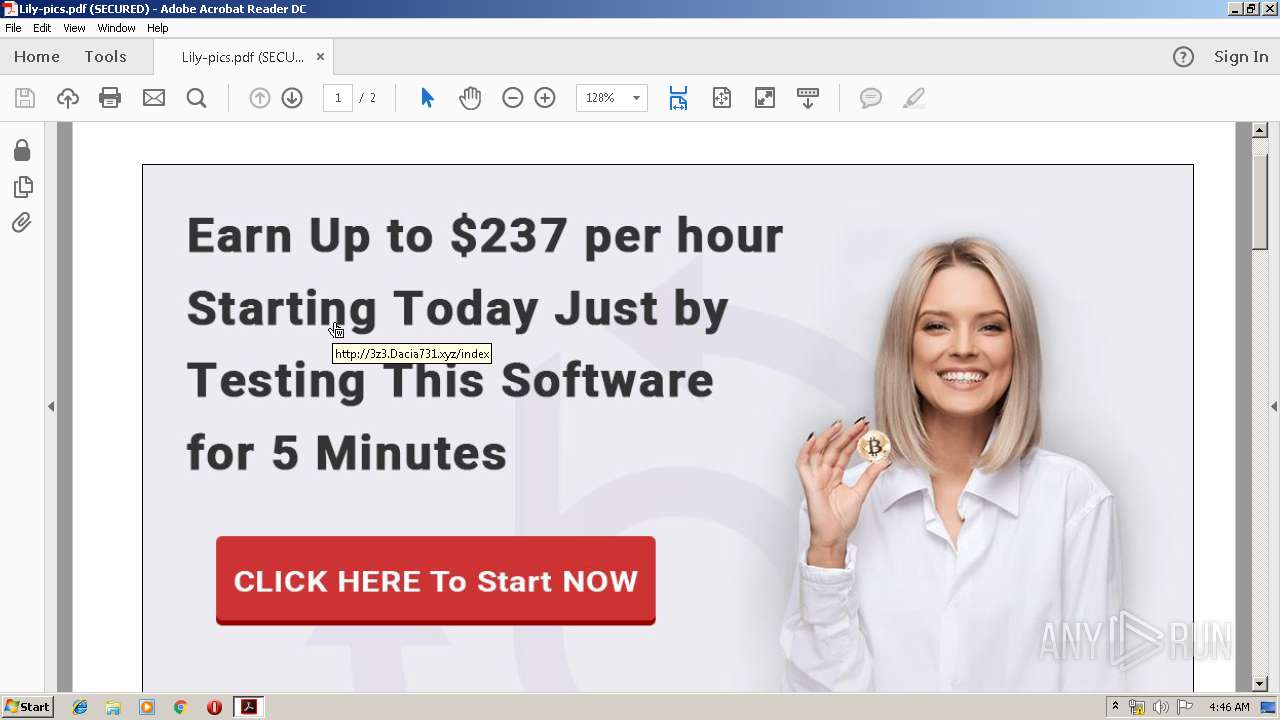
2072 | iexplore.exe | GET | 302 | 47.91.75.140:80 | http://3z3.dacia731.xyz/index | US | — | — | suspicious |
2072 | iexplore.exe | GET | 200 | 51.15.253.163:80 | http://ukinvest.space/eng.html | FR | html | 137 b | suspicious |
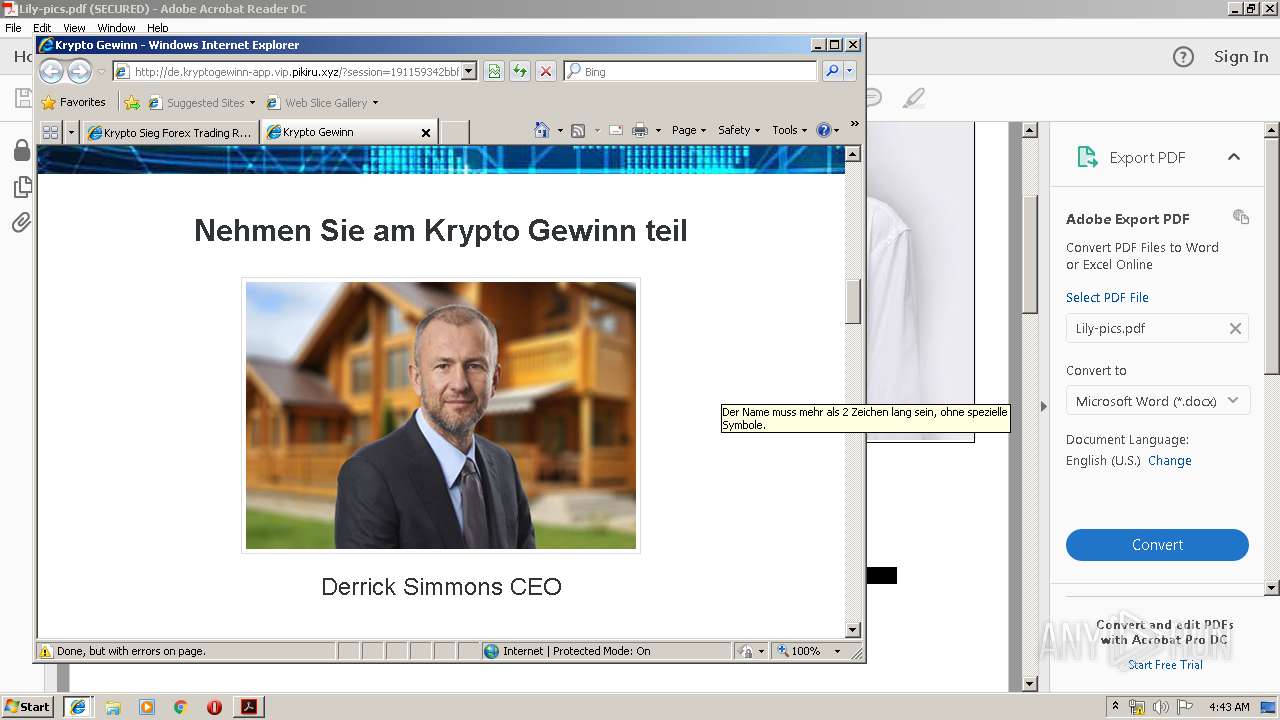
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/images/32.jpg | US | image | 7.10 Kb | suspicious |
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/?session=821790bf350940e99091d4608b2f14c7&aff_id=225&fpp=1 | US | html | 7.12 Kb | suspicious |
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/images/22.jpg | US | image | 4.64 Kb | suspicious |
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/images/arow.png | US | image | 2.51 Kb | suspicious |
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/images/77.jpg | US | image | 3.99 Kb | suspicious |
2072 | iexplore.exe | GET | 200 | 104.31.80.87:80 | http://de.kryptogewinn-app.vip.pikiru.xyz/css/style.css | US | text | 4.59 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2476 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2072 | iexplore.exe | 51.15.253.163:80 | ukinvest.space | Online S.a.s. | FR | unknown |
2476 | iexplore.exe | 51.15.253.163:80 | ukinvest.space | Online S.a.s. | FR | unknown |
2072 | iexplore.exe | 47.91.75.140:80 | 3z3.dacia731.xyz | Alibaba (China) Technology Co., Ltd. | US | suspicious |
2072 | iexplore.exe | 104.31.81.87:80 | vip.pikiru.xyz | Cloudflare Inc | US | shared |
2072 | iexplore.exe | 104.31.80.87:80 | vip.pikiru.xyz | Cloudflare Inc | US | shared |
2476 | iexplore.exe | 79.125.105.113:443 | duckduckgo.com | Amazon.com, Inc. | IE | suspicious |
2072 | iexplore.exe | 172.217.18.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
2072 | iexplore.exe | 172.217.22.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2476 | iexplore.exe | 79.125.105.113:80 | duckduckgo.com | Amazon.com, Inc. | IE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
3z3.dacia731.xyz |
| suspicious |
ukinvest.space |
| unknown |
vip.pikiru.xyz |
| suspicious |
de.kryptogewinn-app.vip.pikiru.xyz |
| suspicious |
duckduckgo.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2072 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |