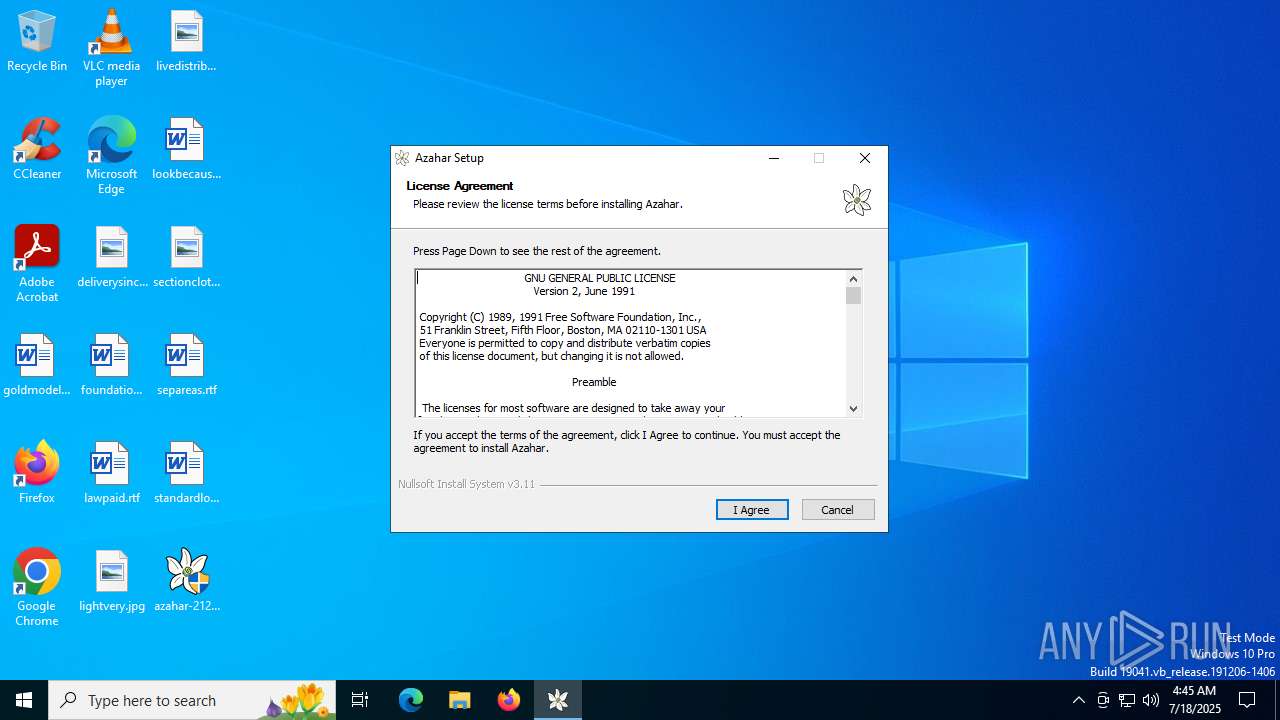
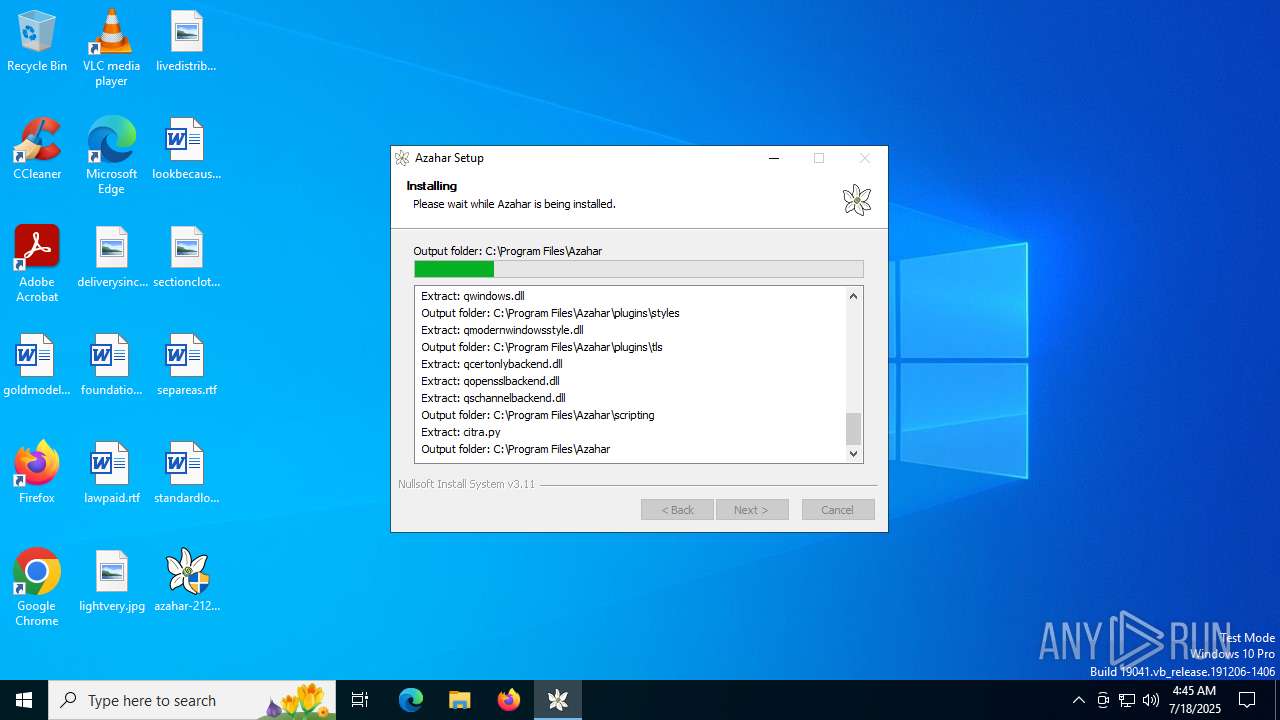
| File name: | azahar-2122.1-windows-msvc-installer.exe |
| Full analysis: | https://app.any.run/tasks/cafa25c0-6a5b-4201-9b01-9856c487b4b7 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 04:45:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 5C01D873B0AEE2C3E8C18150960DA244 |
| SHA1: | CA813338982877BE155B32013F4C479BE3F9136E |
| SHA256: | E7B8F3E38775AB4604AE74335DEB434D32502E514FB12775FD3A63C3BCF17A17 |
| SSDEEP: | 196608:BgaUT2iWeWZCLNNiTKWZZ+7iR2njmhmEYhJ0l7rDWdAA8szKyIx:BgZT2i3WYhh7iUnOmEf5OAA8smy+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
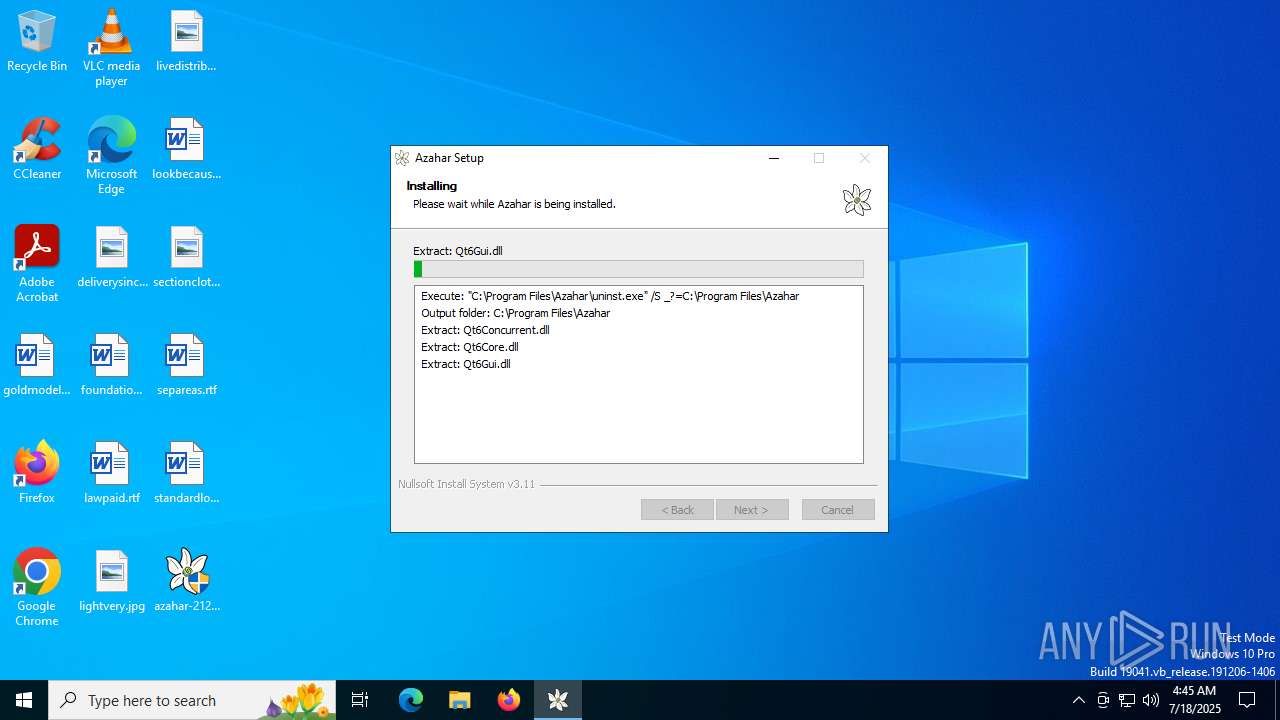
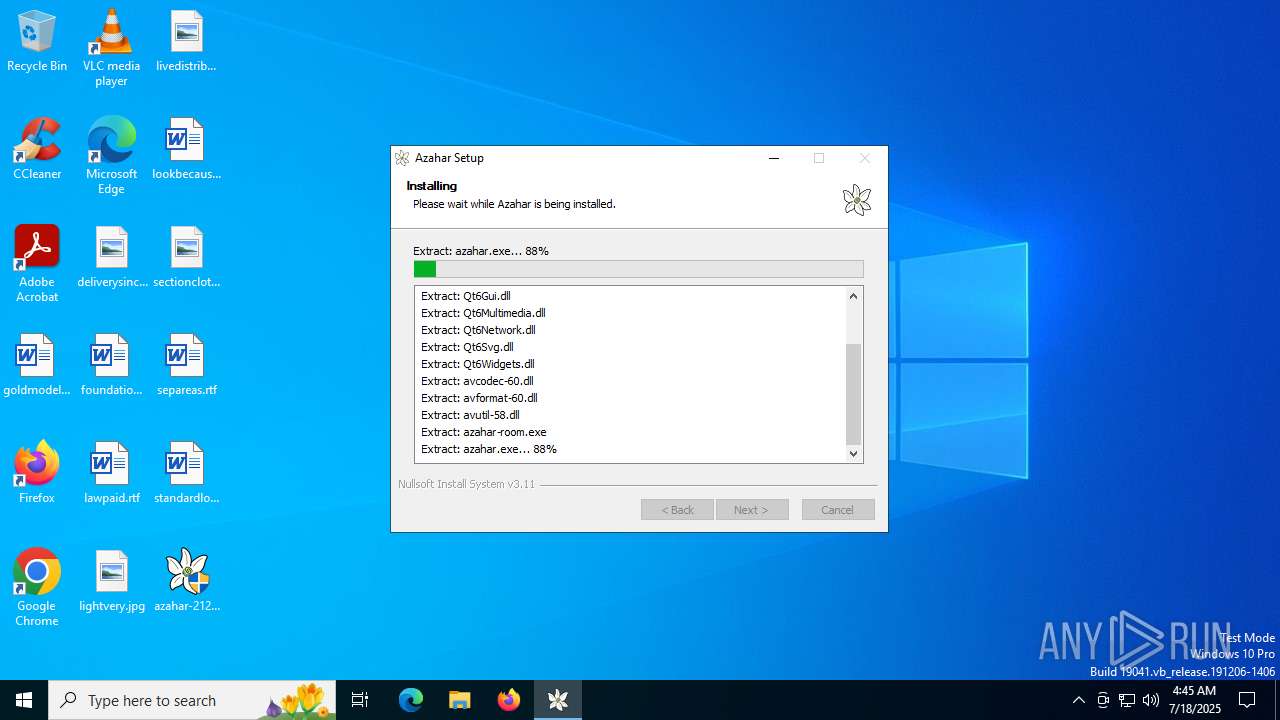
Executable content was dropped or overwritten
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
There is functionality for taking screenshot (YARA)
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Process drops legitimate windows executable
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
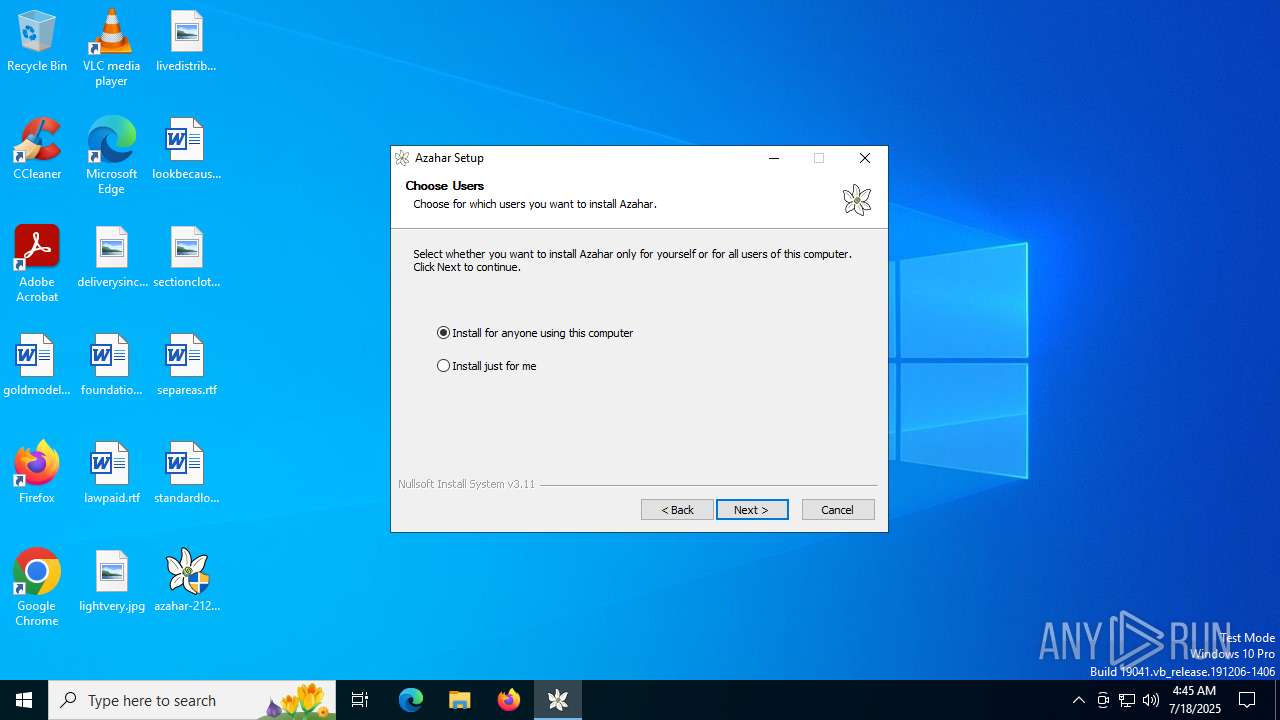
Creates a software uninstall entry
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
The process creates files with name similar to system file names
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Malware-specific behavior (creating "System.dll" in Temp)
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
INFO
Checks supported languages
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Reads the computer name
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
The sample compiled with english language support
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Create files in a temporary directory
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Creates files in the program directory
- azahar-2122.1-windows-msvc-installer.exe (PID: 2632)
Checks proxy server information
- slui.exe (PID: 5432)
Reads the software policy settings
- slui.exe (PID: 5432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:03:08 23:05:20+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 139776 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x369f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
134
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2632 | "C:\Users\admin\Desktop\azahar-2122.1-windows-msvc-installer.exe" | C:\Users\admin\Desktop\azahar-2122.1-windows-msvc-installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5240 | "C:\Users\admin\Desktop\azahar-2122.1-windows-msvc-installer.exe" | C:\Users\admin\Desktop\azahar-2122.1-windows-msvc-installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5432 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 690
Read events
3 681
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | DisplayName |
Value: Azahar | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Azahar\uninst.exe /AllUsers | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Azahar\azahar.exe | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | DisplayVersion |
Value: 2122.1 | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | URLInfoAbout |
Value: https://azahar-emu.org/ | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | Publisher |
Value: Azahar Emulator Developers | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Azahar | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | EstimatedSize |
Value: 89311 | |||
| (PID) Process: | (2632) azahar-2122.1-windows-msvc-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Azahar |
| Operation: | write | Name: | Comments |
Value: 3DS emulator based on Citra | |||
Executable files
34
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Users\admin\AppData\Local\Temp\nspE51D.tmp\LangDLL.dll | executable | |
MD5:4B8A750993567AC9A350BA9768FABFA0 | SHA256:4CF25411F28F639F72156C24B0F66EA42F5AEE5973F6C137D901DA6AE42D5B7E | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\Qt6Gui.dll | executable | |
MD5:817B182E009F388672445E69144F8543 | SHA256:CFCE665B7C477EBFF815FB27A9B55D0B629183C0CECB5282A87BAD666D76DAA8 | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\Qt6Widgets.dll | executable | |
MD5:C3241A2E538115DBADDF3A8C283C7966 | SHA256:6A97350BBFE5518C5E41453062548F493014F8037A70645246549DE33E6CFC17 | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Users\admin\AppData\Local\Temp\nspE51D.tmp\UserInfo.dll | executable | |
MD5:E6F30908ABFC6F53B7C3C36DAEC4586D | SHA256:E0DC3112796DBAA37F25AB54B7FAC2FBF791CBC6E36A84FC61C6423B84A3677B | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Users\admin\AppData\Local\Temp\nspE51D.tmp\nsDialogs.dll | executable | |
MD5:8F0E7415F33843431DF308BB8E06AF81 | SHA256:BB49F15FA83452370047A7801E39FC7F64E70C7545B8999BB85AA4749EAA048B | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Users\admin\AppData\Local\Temp\nspE51D.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\Qt6Network.dll | executable | |
MD5:794760C25A8DE30DCB152808DD5B7416 | SHA256:F6702966E341D9A2F1707DF5833DB984205B3717FB5CE3CD2A37383AC347905D | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\Qt6Svg.dll | executable | |
MD5:3B75CF39102E5152A34BAB94EDF82167 | SHA256:CC8FEFC7BFF06FE18E7994039B0943A26B3FED4D5C9B09845E464BAD3ADF4F66 | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\dxil.dll | executable | |
MD5:384AA622EA0A5262E23CB020F0FD3190 | SHA256:3D030CCA37F03955C95DA0978026FC06D45C49FE4E6F9D4A8CB5B9E9ADF2959D | |||
| 2632 | azahar-2122.1-windows-msvc-installer.exe | C:\Program Files\Azahar\Qt6Core.dll | executable | |
MD5:B5FDC51AAABE8C0F1B611E003817B3E0 | SHA256:8A1AF6B5EA341EF0D01573A9005E5C68206CFEF6853B5584E8A737C26C9D9EE7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
41
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
6164 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6164 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.68:443 | https://login.live.com/RST2.srf | unknown | — | — | whitelisted |
— | — | POST | 400 | 20.190.159.68:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | GET | 200 | 52.149.20.212:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3644 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |