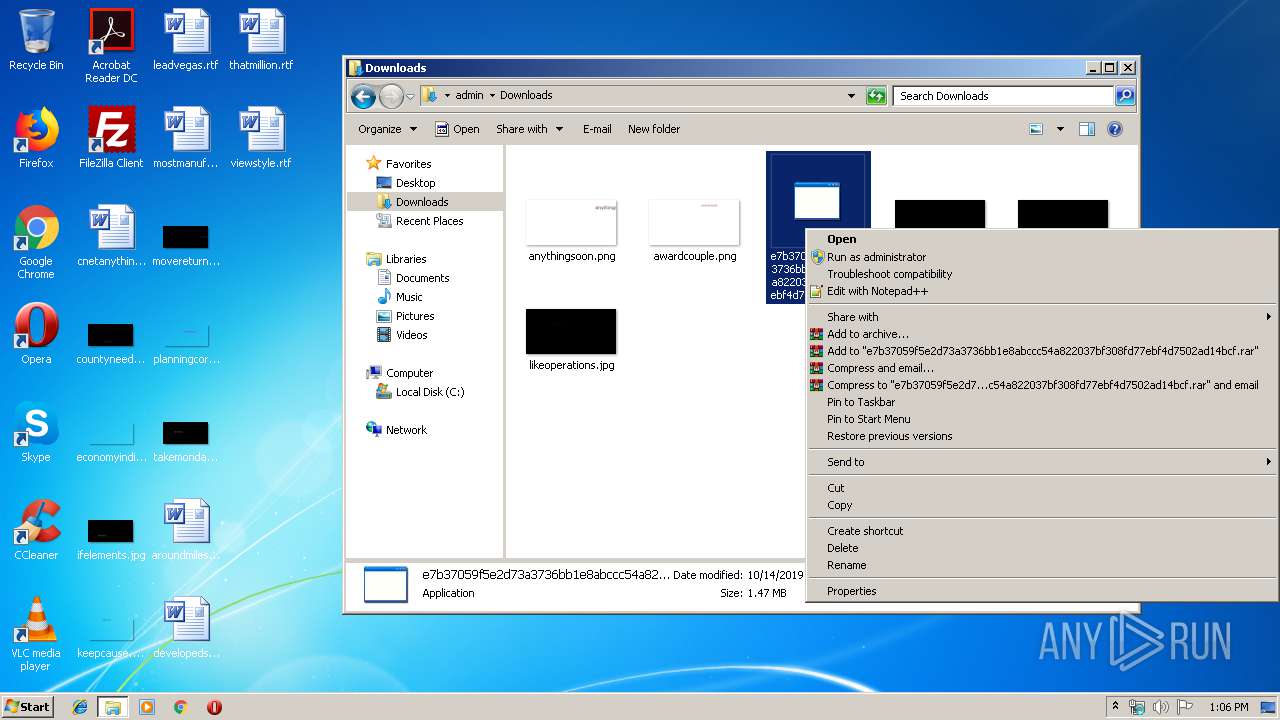
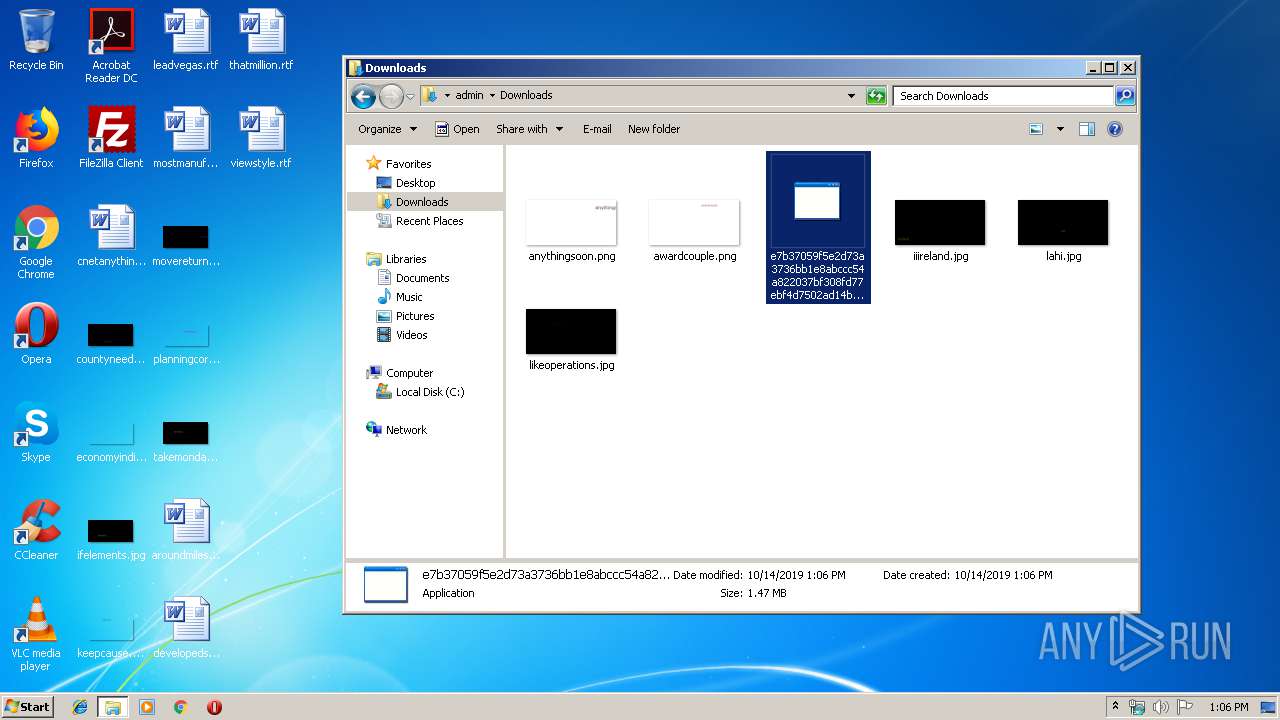
| File name: | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf |
| Full analysis: | https://app.any.run/tasks/390aa65d-6984-4266-af21-d1f0a97389f7 |
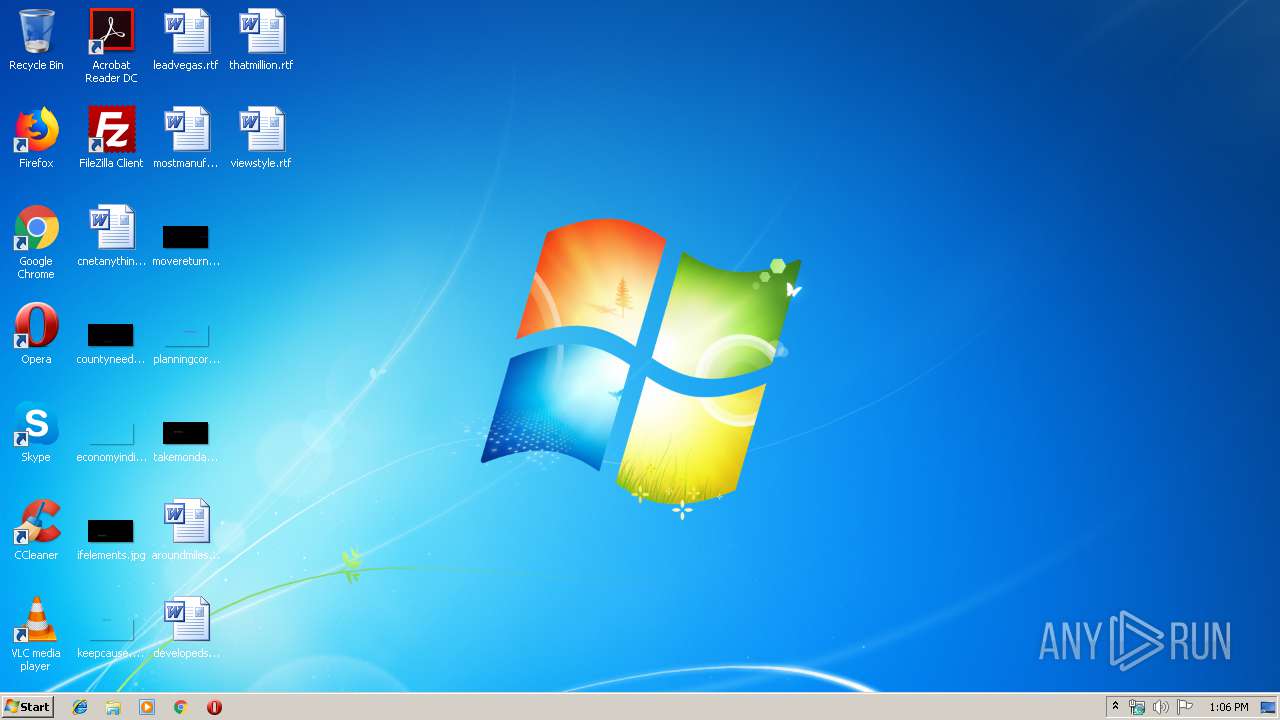
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 12:05:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4EBA4B70D57EB00ADB403F68601AC8CF |
| SHA1: | 9136BF4DE47F8333915816D1E5FB136FCED20ECC |
| SHA256: | E7B37059F5E2D73A3736BB1E8ABCCC54A822037BF308FD77EBF4D7502AD14BCF |
| SSDEEP: | 24576:kdJJRY2rxSZoCeas3kPOBGLDDiljAT1G0i2VVa5nxOOq4095u4qT/GX5Wb15V+U5:a/RYkM31RVVc5ELuJu2gK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the cookies of Mozilla Firefox
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3332)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 1848)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 1976)
Application launched itself
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3084)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3896)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3948)
Reads Internet Cache Settings
- IELowutil.exe (PID: 3400)
Changes tracing settings of the file or console
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3332)
Reads the cookies of Google Chrome
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3332)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 1848)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 1976)
INFO
Manual execution by user
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3896)
- explorer.exe (PID: 3780)
- e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe (PID: 3948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 13:49:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 538112 |
| InitializedDataSize: | 1012736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x58f50 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Oct-2019 11:49:42 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Oct-2019 11:49:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000834F1 | 0x00083600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.13549 |
.rdata | 0x00085000 | 0x0001E680 | 0x0001E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17088 |
.data | 0x000A4000 | 0x000074A8 | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.51065 |
.rsrc | 0x000AC000 | 0x000D5D18 | 0x000D5E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.96614 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94917 | 146 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.54353 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 4.35478 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.17501 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 3.47748 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 2.83156 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 3.44197 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
8 | 4.05874 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 3.02695 | 308 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
10 | 2.74274 | 180 | Latin 1 / Western European | Chinese - PRC | RT_CURSOR |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1848 | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | — | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1976 | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | — | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe" | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3332 | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | — | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Internet Explorer\IELowutil.exe" -embedding | C:\Program Files\Internet Explorer\IELowutil.exe | — | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Low-Mic Utility Tool Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe" | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe" | C:\Users\admin\Downloads\e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
110
Read events
80
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3332) e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
1
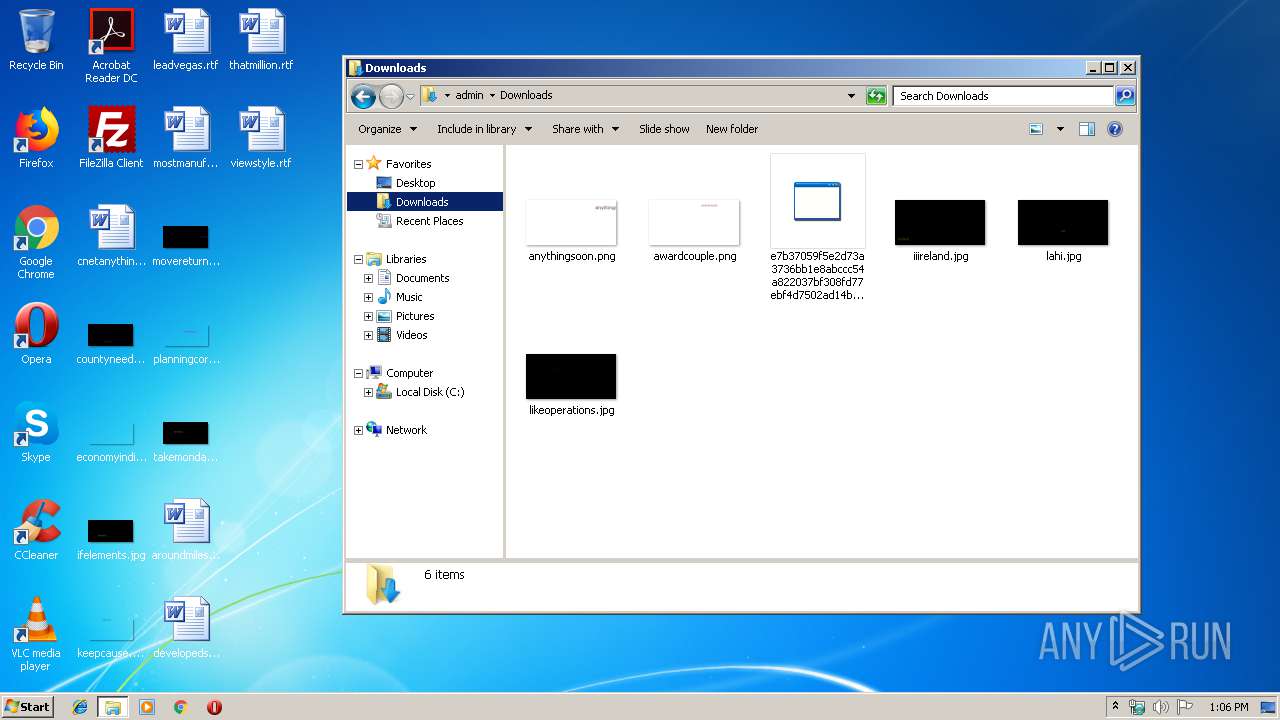
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d | — | |
MD5:— | SHA256:— | |||
| 3332 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d-shm | — | |
MD5:— | SHA256:— | |||
| 1848 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d | — | |
MD5:— | SHA256:— | |||
| 1848 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d-shm | — | |
MD5:— | SHA256:— | |||
| 1976 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d | — | |
MD5:— | SHA256:— | |||
| 1976 | e7b37059f5e2d73a3736bb1e8abccc54a822037bf308fd77ebf4d7502ad14bcf.exe | C:\Users\admin\Downloads\d-shm | — | |
MD5:— | SHA256:— | |||
| 3400 | IELowutil.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3400 | IELowutil.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7QD72ZLS\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3400 | IELowutil.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\HA7AUGN1\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3400 | IELowutil.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BGSH7MYD\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report