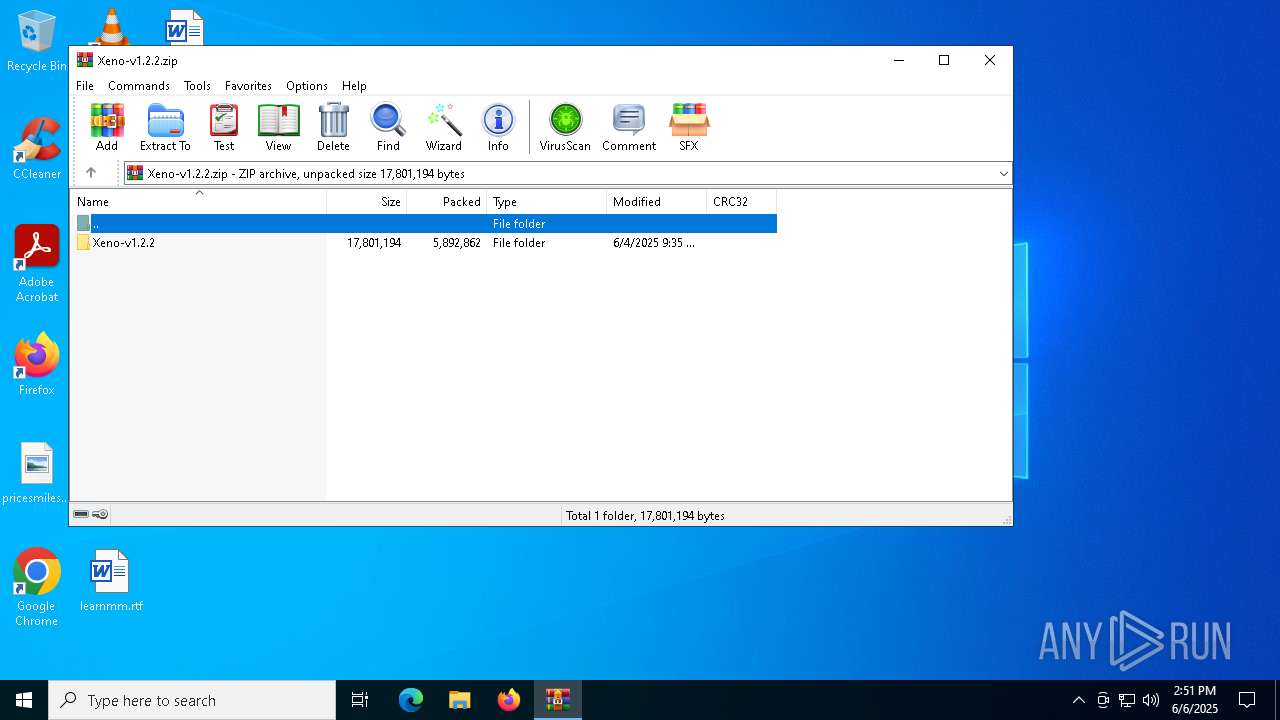
| File name: | Xeno-v1.2.2.zip |
| Full analysis: | https://app.any.run/tasks/7dc06d43-71ed-4ce9-9e93-704f4d1f73b1 |
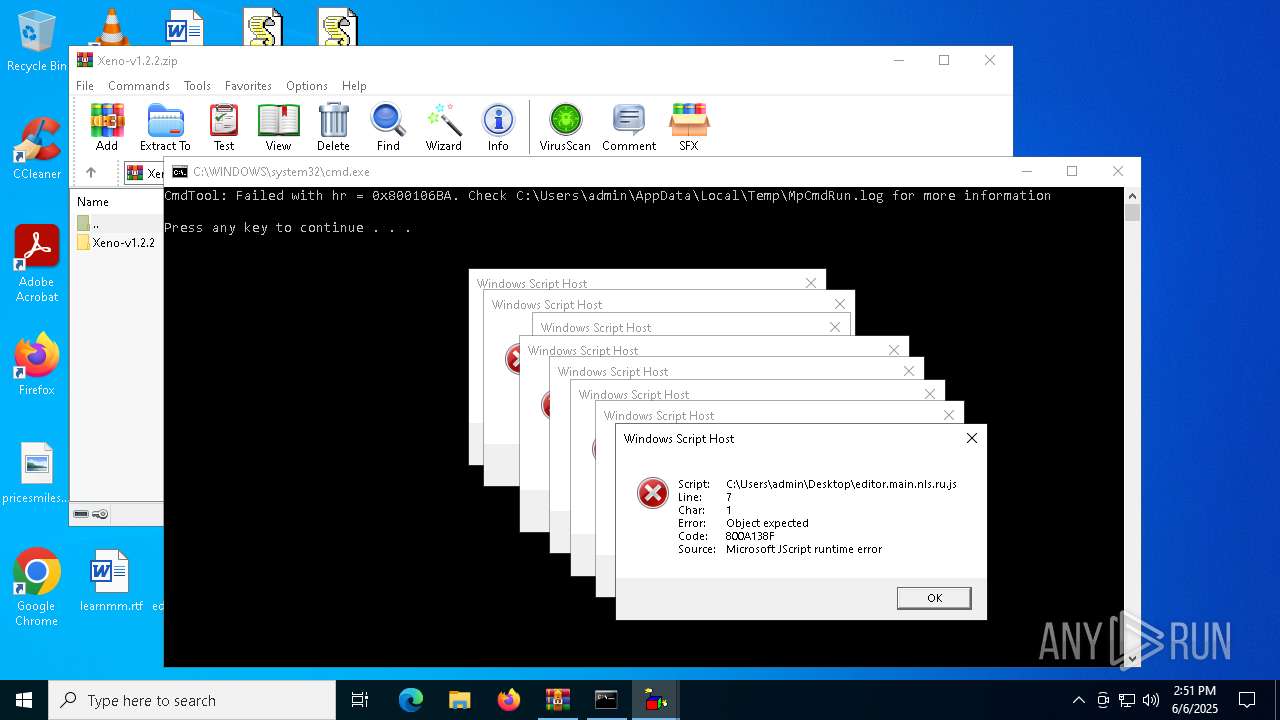
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2025, 14:51:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 057611A238D18A3E55E9BF68838FFB63 |
| SHA1: | 03C2F958A7DE89E6B095639537BFAE6791AD0A83 |
| SHA256: | E79DD40178D34945A7043B50F52EBE85E14A6720228AA71FBA26A436CA69D8F2 |
| SSDEEP: | 98304:LFD/qlipnX4eK0lJBSJc0uUL4PJ209hvygq+iDqA+j7bHn10pPS9nzOljtf8xMu/:pV9RybjJ6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 2652)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2652)
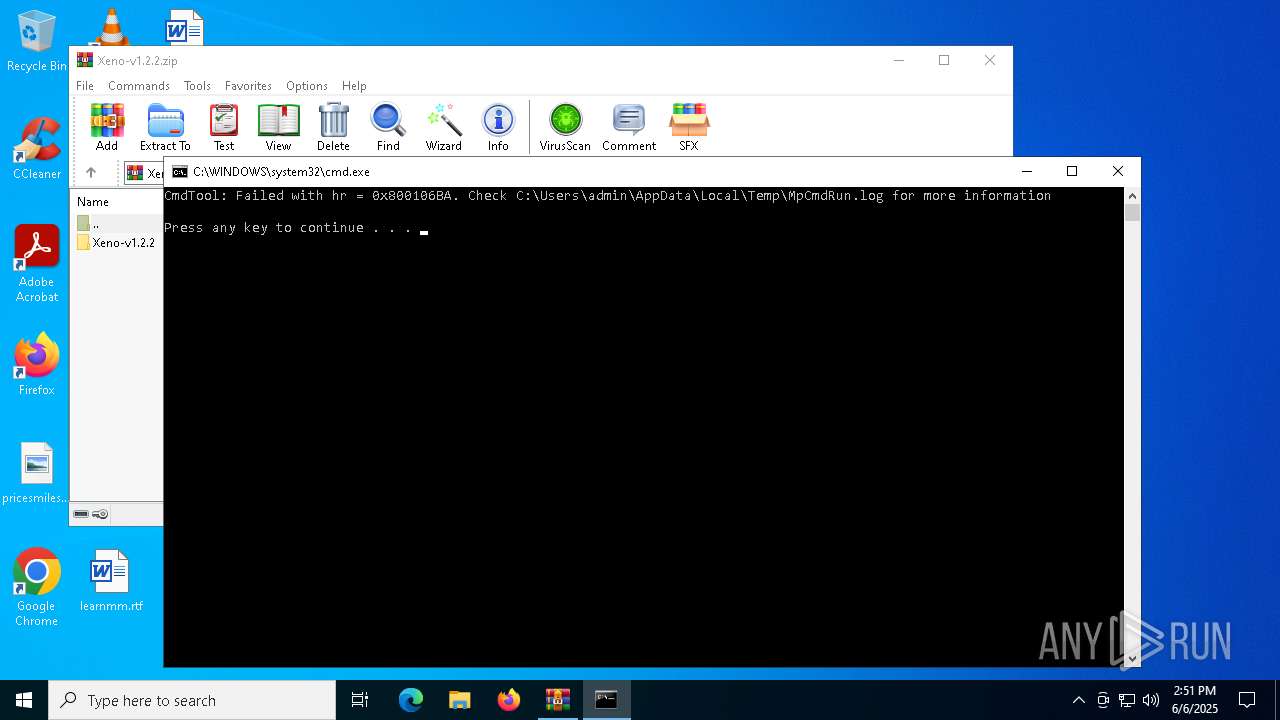
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2652)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 2652)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2652)
Reads the computer name
- MpCmdRun.exe (PID: 6992)
- Xeno.exe (PID: 5624)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2652)
Checks supported languages
- MpCmdRun.exe (PID: 6992)
- Xeno.exe (PID: 5624)
Manual execution by a user
- Xeno.exe (PID: 5624)
- wscript.exe (PID: 2568)
- wscript.exe (PID: 4616)
- wscript.exe (PID: 6880)
- wscript.exe (PID: 7252)
- wscript.exe (PID: 7296)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 7832)
- wscript.exe (PID: 7736)
Create files in a temporary directory
- MpCmdRun.exe (PID: 6992)
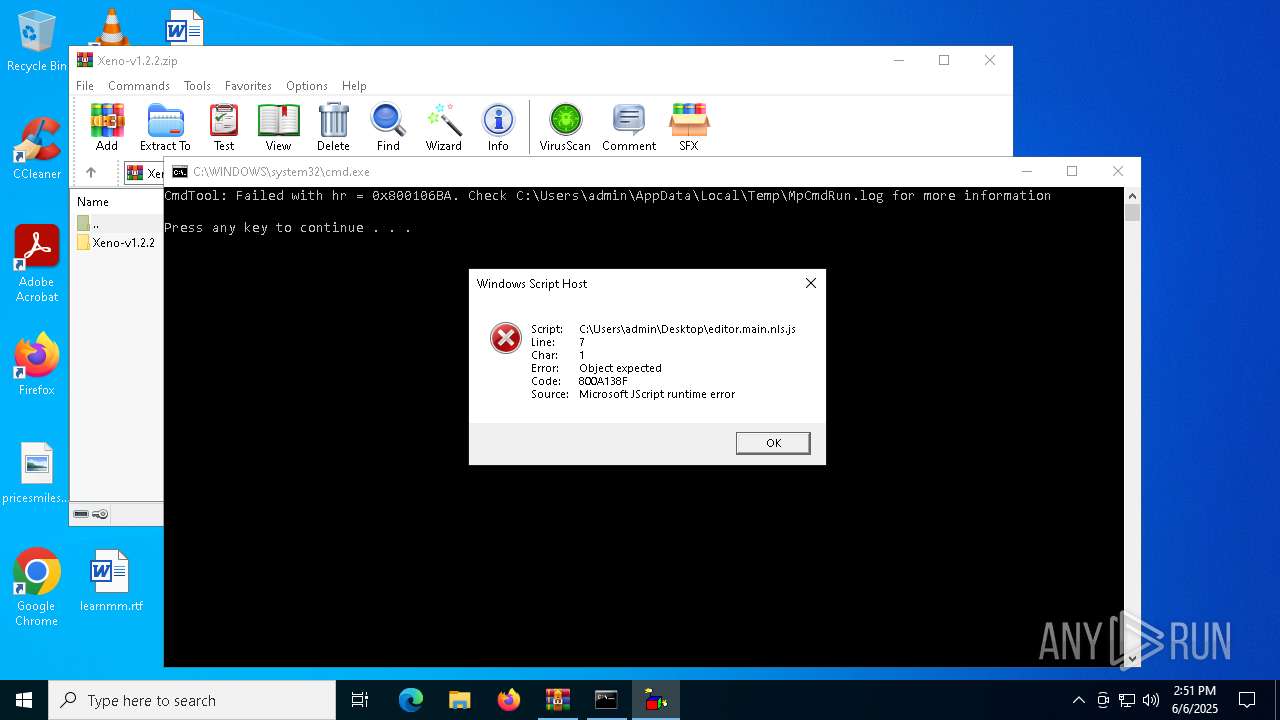
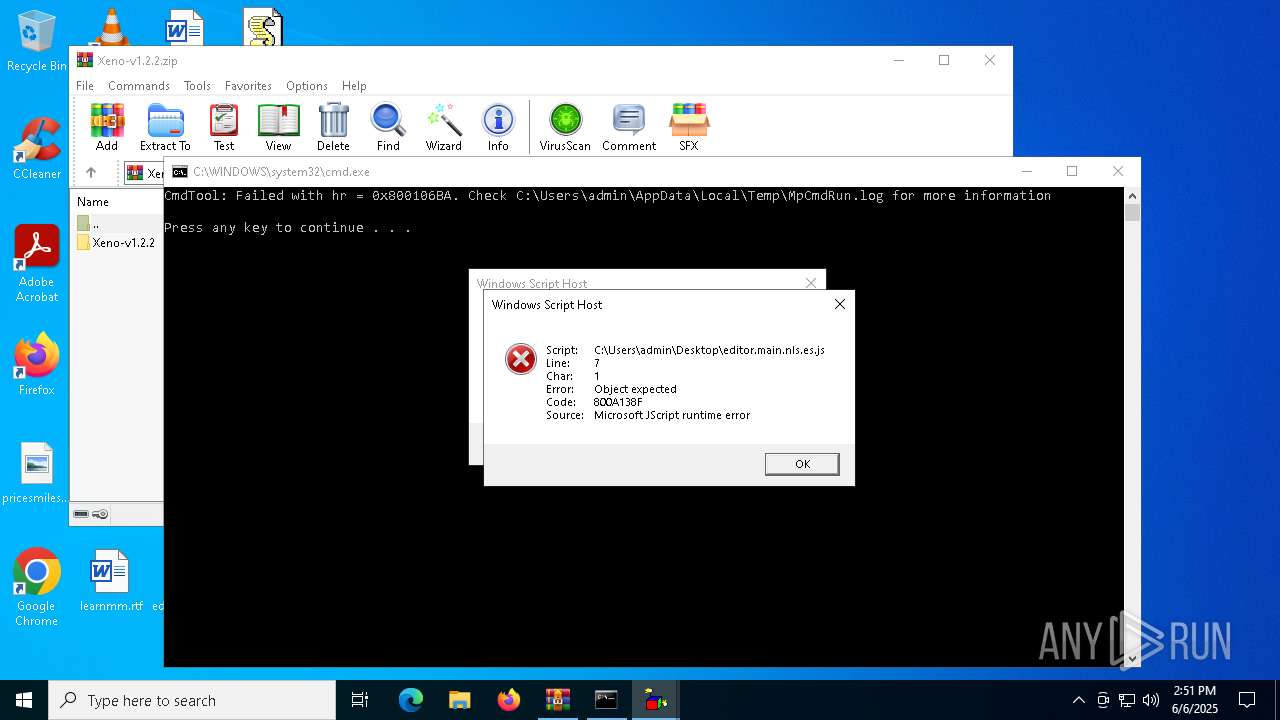
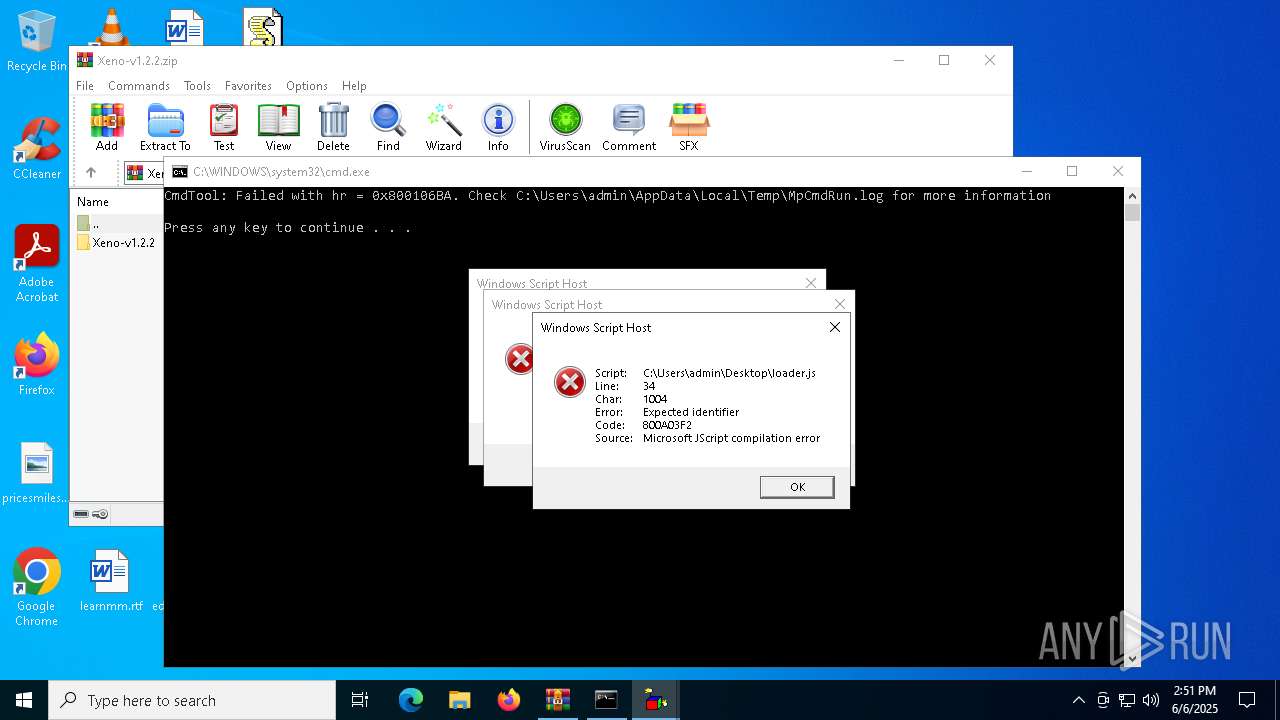
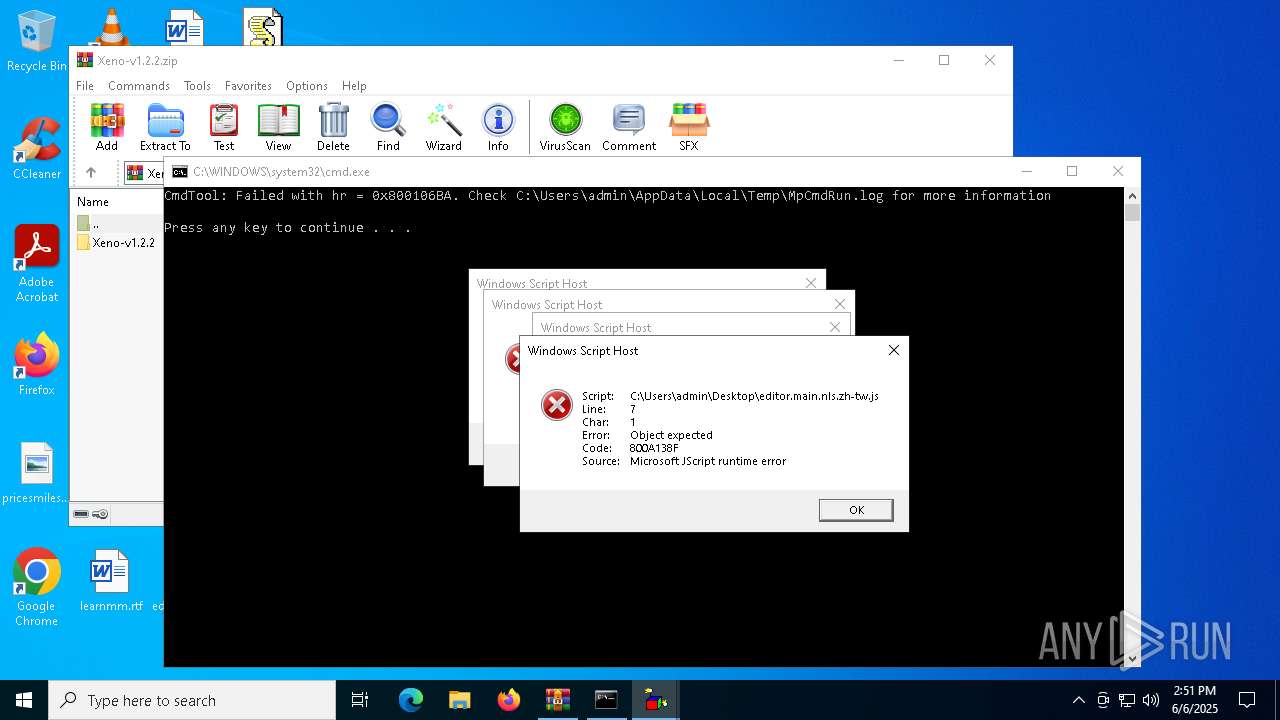
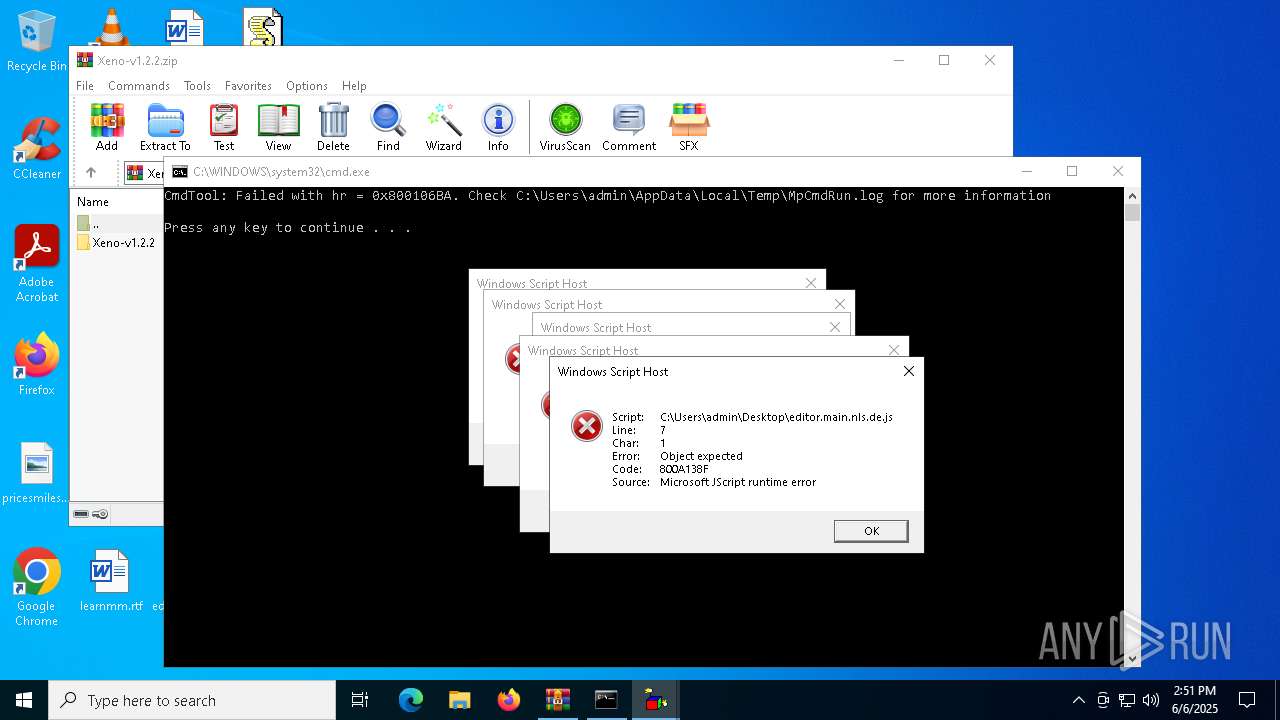
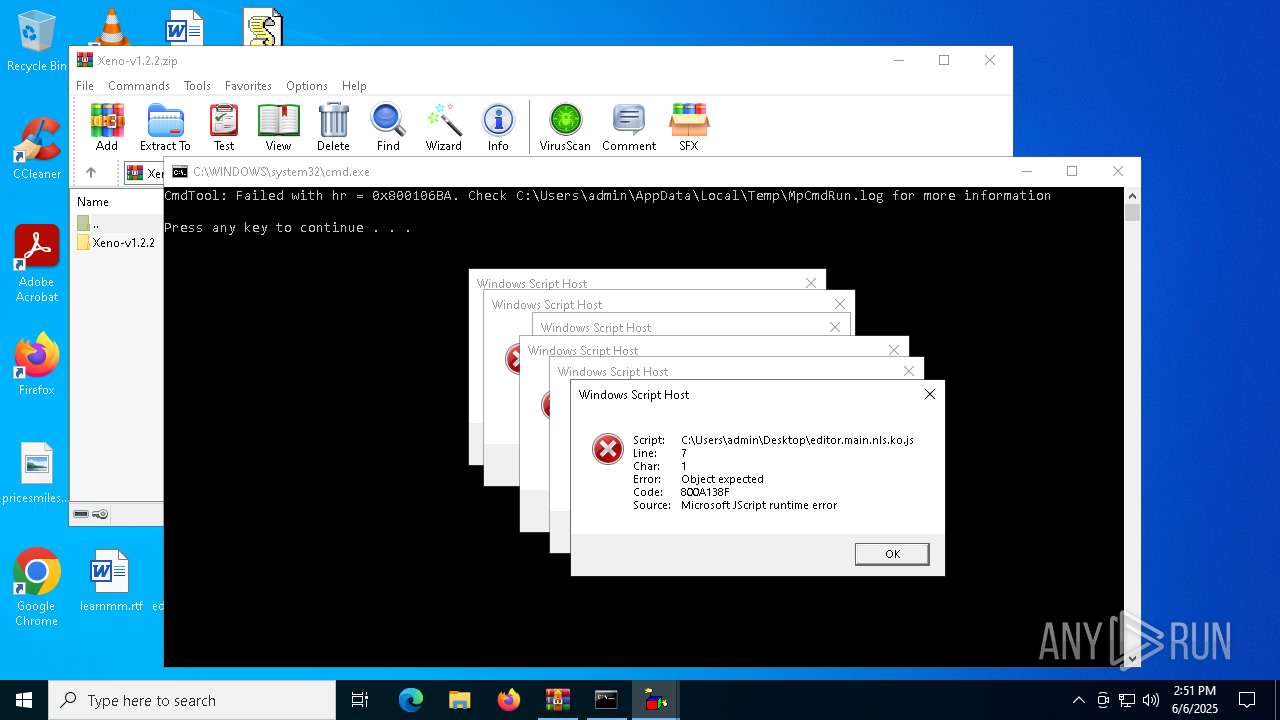
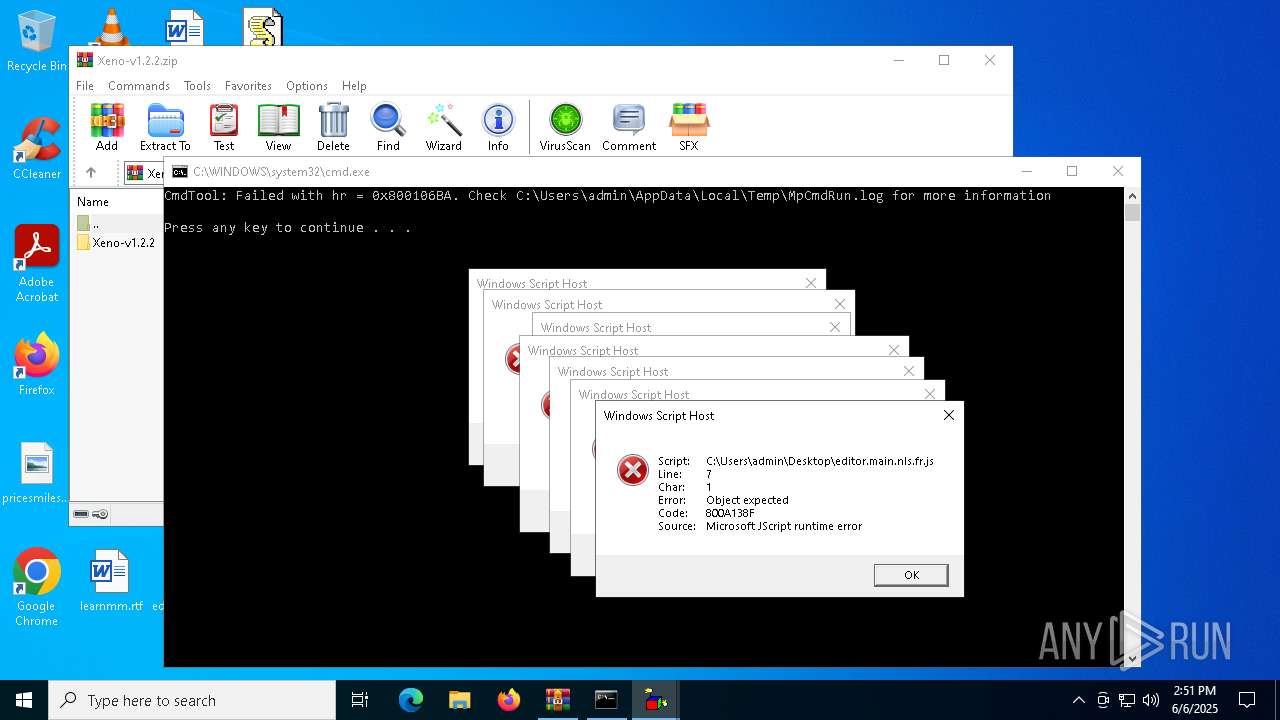
JScript runtime error (SCRIPT)
- wscript.exe (PID: 6880)
- wscript.exe (PID: 2568)
- wscript.exe (PID: 7252)
- wscript.exe (PID: 7832)
- wscript.exe (PID: 8148)
- wscript.exe (PID: 7736)
- wscript.exe (PID: 7296)
Checks proxy server information
- slui.exe (PID: 7800)
Reads the software policy settings
- slui.exe (PID: 7800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:04 17:35:28 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Xeno-v1.2.2/ |
Total processes
135
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\editor.main.nls.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Xeno-v1.2.2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4616 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\loader.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5124 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Rar$Scan12877.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5624 | "C:\Users\admin\Desktop\Xeno.exe" | C:\Users\admin\Desktop\Xeno.exe | — | explorer.exe | |||||||||||
User: admin Company: XenoUI Integrity Level: MEDIUM Description: XenoUI Exit code: 2147516570 Version: 1.2.2 Modules
| |||||||||||||||
| 6880 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\editor.main.nls.es.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
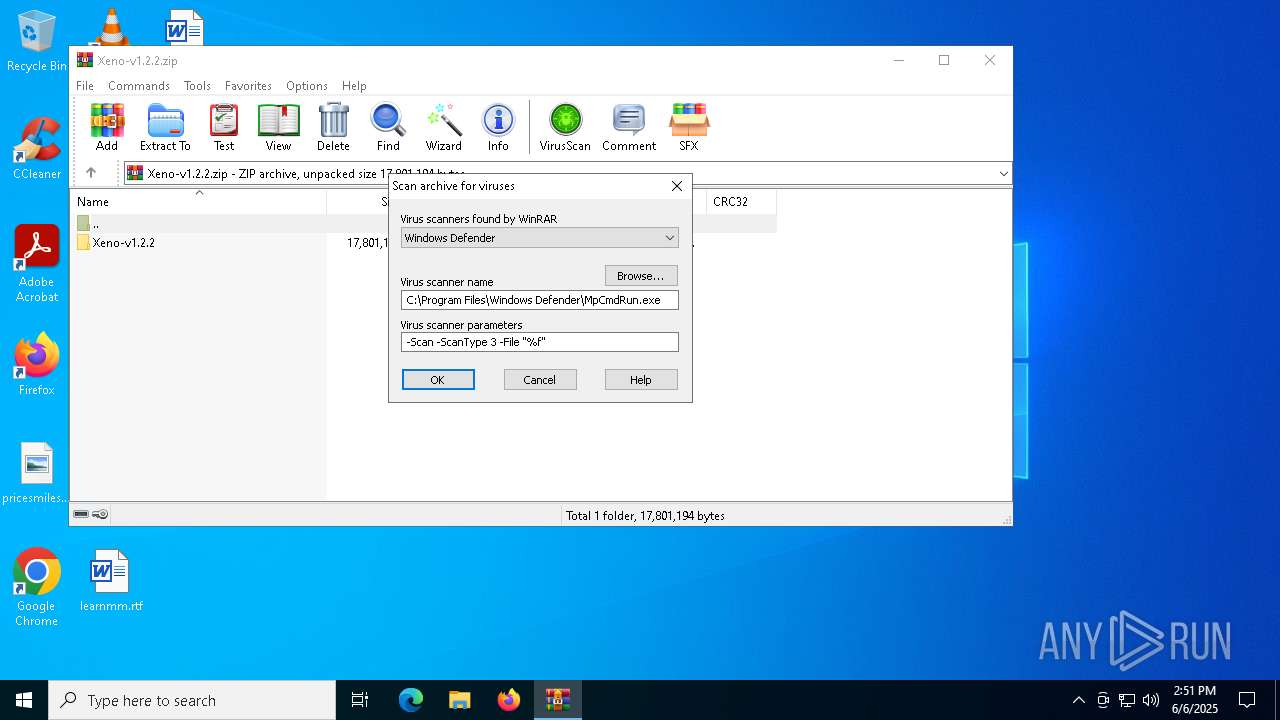
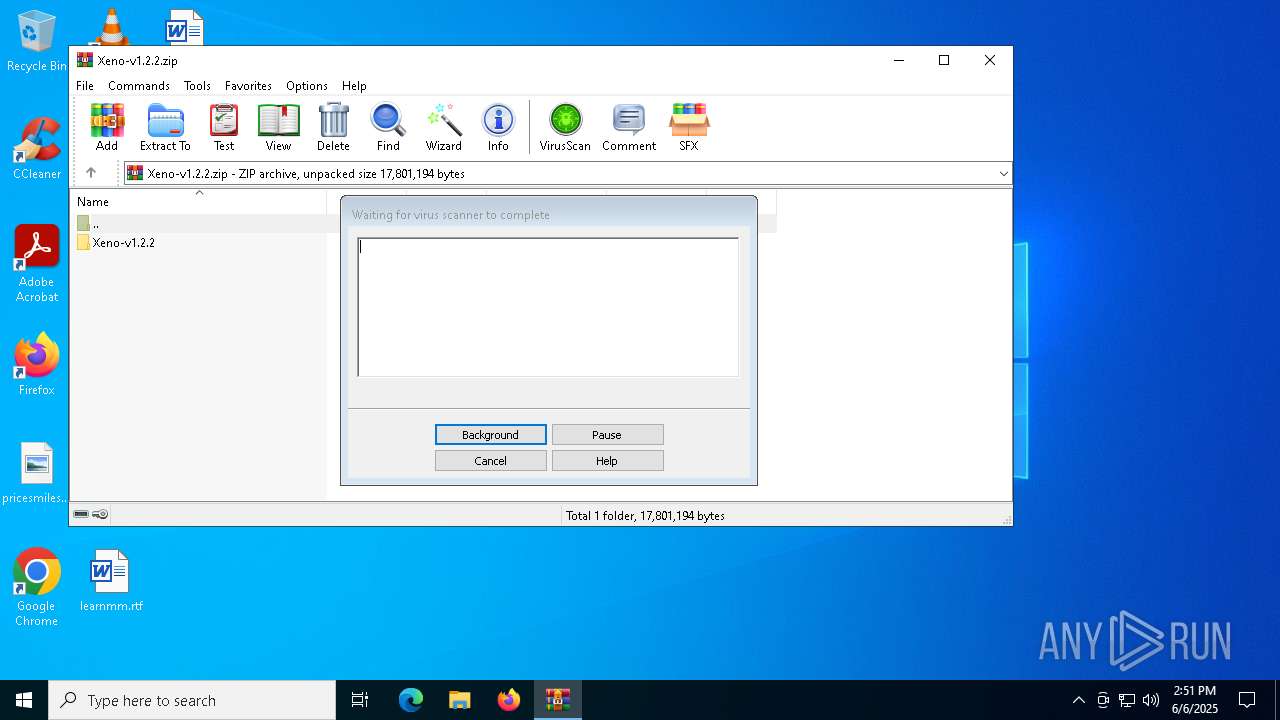
| 6992 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\editor.main.nls.zh-tw.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7296 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\editor.main.nls.de.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 948
Read events
5 938
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Xeno-v1.2.2.zip | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
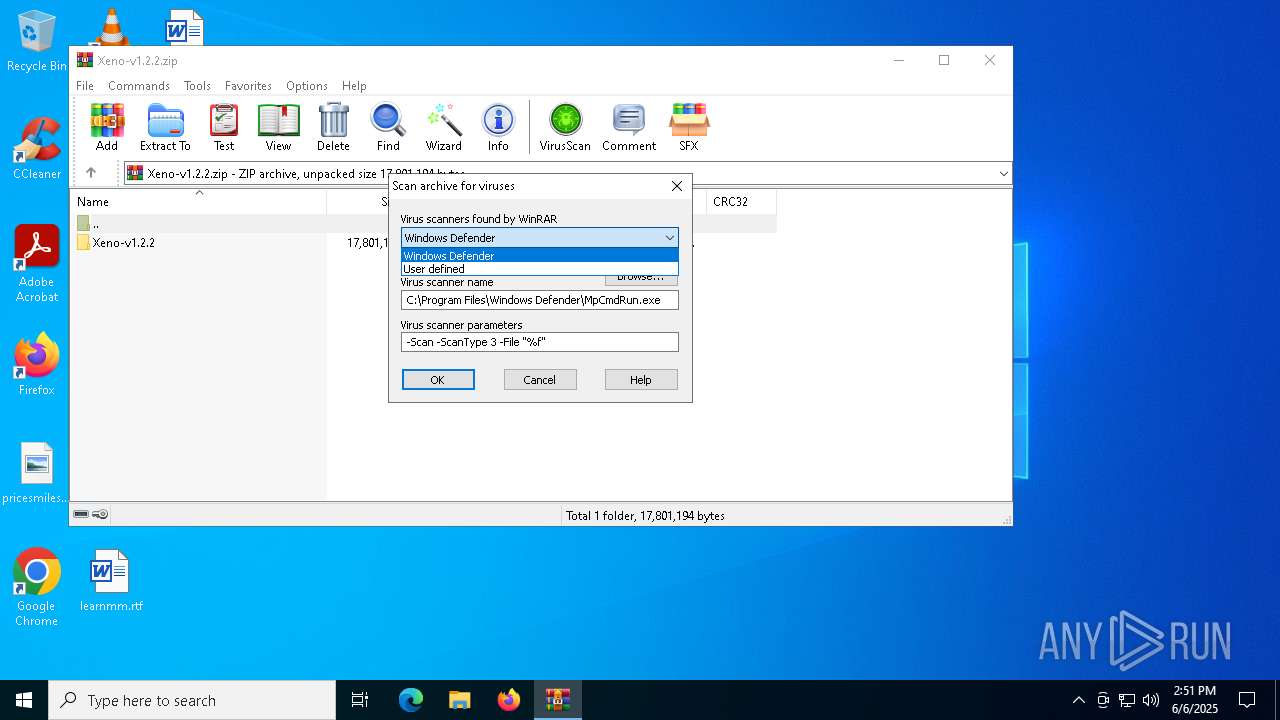
| (PID) Process: | (2652) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\VirusScan |
| Operation: | write | Name: | DefScanner |
Value: Windows Defender | |||
| (PID) Process: | (7736) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 14A2120000000000 | |||
Executable files
24
Suspicious files
5
Text files
16
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\api-ms-win-crt-stdio-l1-1-0.dll | executable | |
MD5:429C26ED27A026442F89C95FF16CE8C2 | SHA256:2A466648AFFD3D51B944F563BB65046A3DA91006A0D90FB2C0B123487A1FC1B3 | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\api-ms-win-crt-convert-l1-1-0.dll | executable | |
MD5:C8DBF0CA88FACFE87899168A7F7DB52C | SHA256:94B6E91B93C2202DABD659BFF294BEE87C22897A30A6B4930B49051C2FB502DC | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\api-ms-win-crt-string-l1-1-0.dll | executable | |
MD5:0F593E50BE4715AA8E1F6EB39434EDD5 | SHA256:BF4EA10BE1B64C442AC0CCF4BDF69F6703467176A27E9E14A488D26448A6E179 | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\bin\Monaco\index.html | html | |
MD5:001DCBB8F41CDCBF9B4D1E3A0ED4B2D2 | SHA256:F1D2C52F2803C29585B81D2EFF74C56242D27E9619EE6D38081D5604C5BB1951 | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\api-ms-win-crt-runtime-l1-1-0.dll | executable | |
MD5:F91E1FF896B5616919AC97C7095C513E | SHA256:07382C0D91DAD2BB6BA8BD06EA02F12C57ABF7C4E5A70672E9F2954D09A4FFD4 | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\bin\Monaco\vs\editor\editor.main.js | s | |
MD5:2DC0068CDBC03CE43A75AB0B2DF664E2 | SHA256:B604B6148F70FE9DB882CCE2A7D327B2422AD2F203A805491002A8C564E3C3FF | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\api-ms-win-crt-math-l1-1-0.dll | executable | |
MD5:E10E077BB06209AEDD0D0D378C758F73 | SHA256:8A7BFF1C918539A75C25568DB25933D653C003E016FD7791A37186B42BBB7C20 | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\bin\Monaco\vs\editor\editor.main.nls.js | text | |
MD5:E871D4D9539C26D7D2BF32801EBDECF0 | SHA256:5FF0084E6A7EEE82A735616239AAF2190EA9D90E89E19340831F3D590828016A | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\bin\Monaco\vs\base\worker\workerMain.js | s | |
MD5:D0AC5294C58E523CDDF25BC6D785FA48 | SHA256:E90D1A8F116FA74431117A3AD78DDE16DDE060A4BF7528DFE3D5A3AD6156504B | |||
| 2652 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR2652.29659\Xeno-v1.2.2.zip\Xeno-v1.2.2\bin\Monaco\vs\editor\editor.main.nls.de.js | text | |
MD5:D1FD2FB756C73970B9C5E0BA07BFF708 | SHA256:CB1C3416FF242A738C45C3B2590D7D222B159A95A69CE3B7B8D7C8D18EA70828 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
38
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4452 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
4452 | RUXIMICS.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.73:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
3872 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
3872 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
3872 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
3872 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4452 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4452 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4452 | RUXIMICS.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3872 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3872 | SIHClient.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3872 | SIHClient.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |