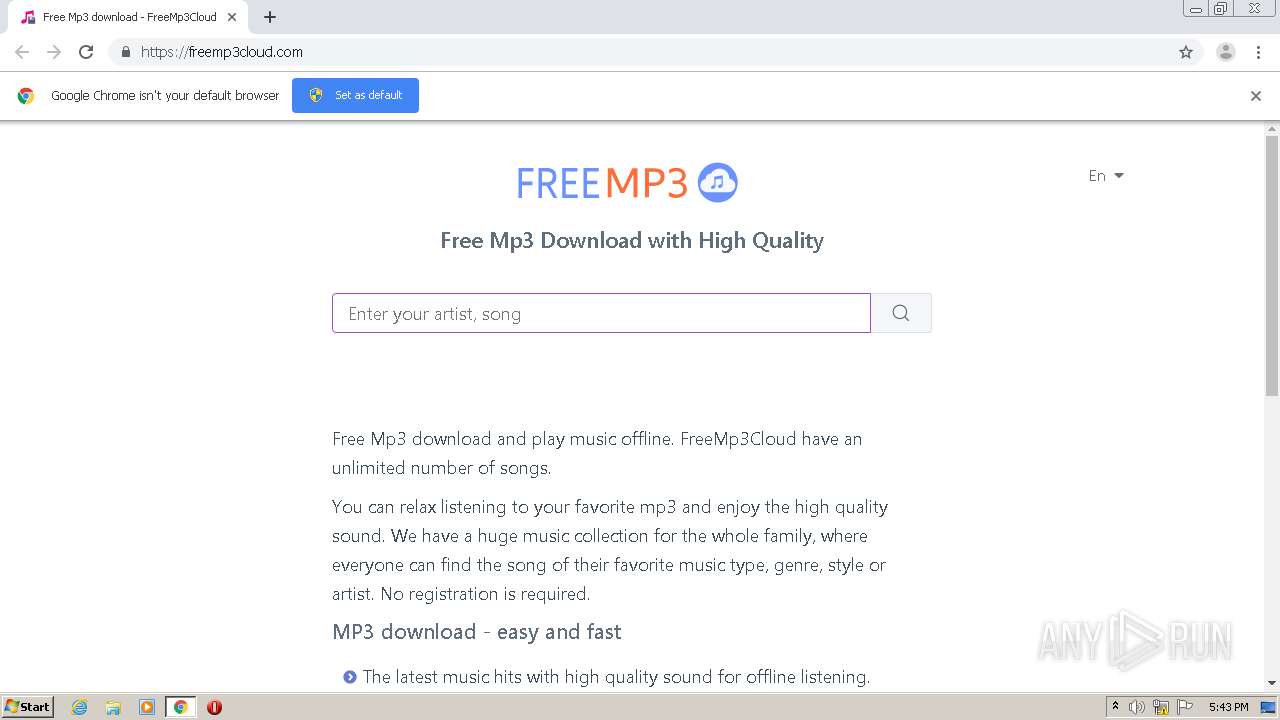
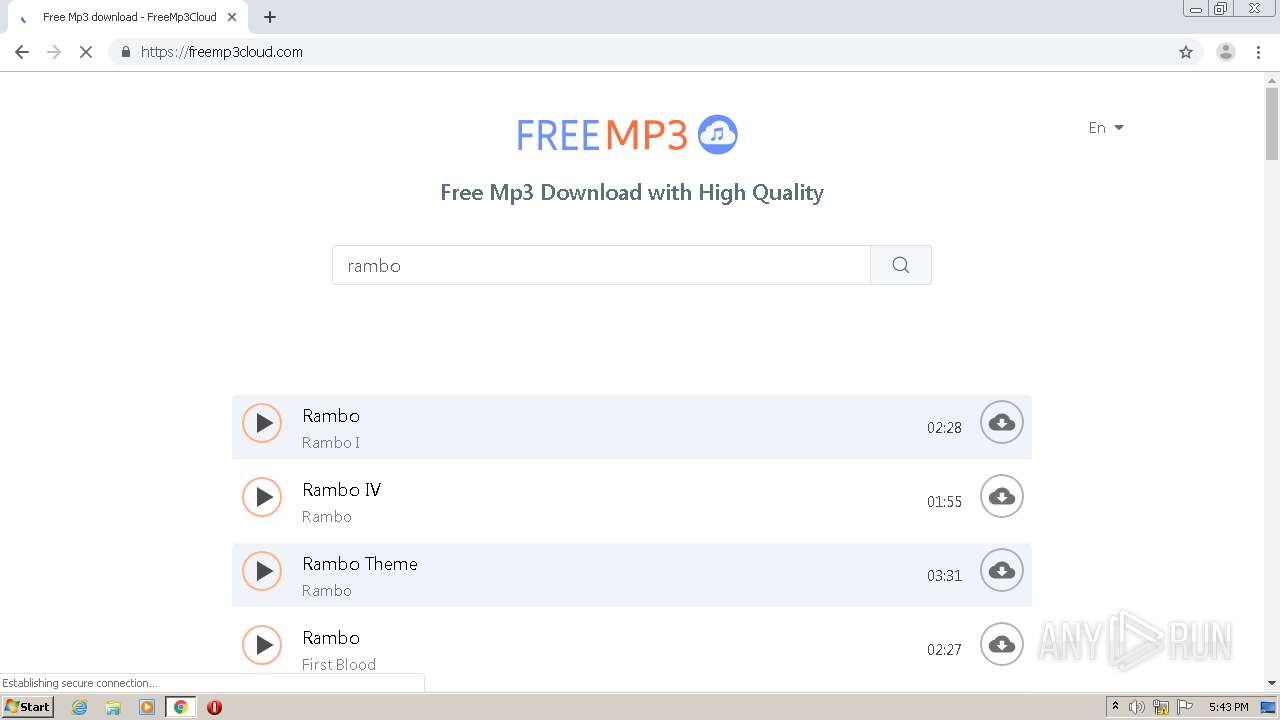
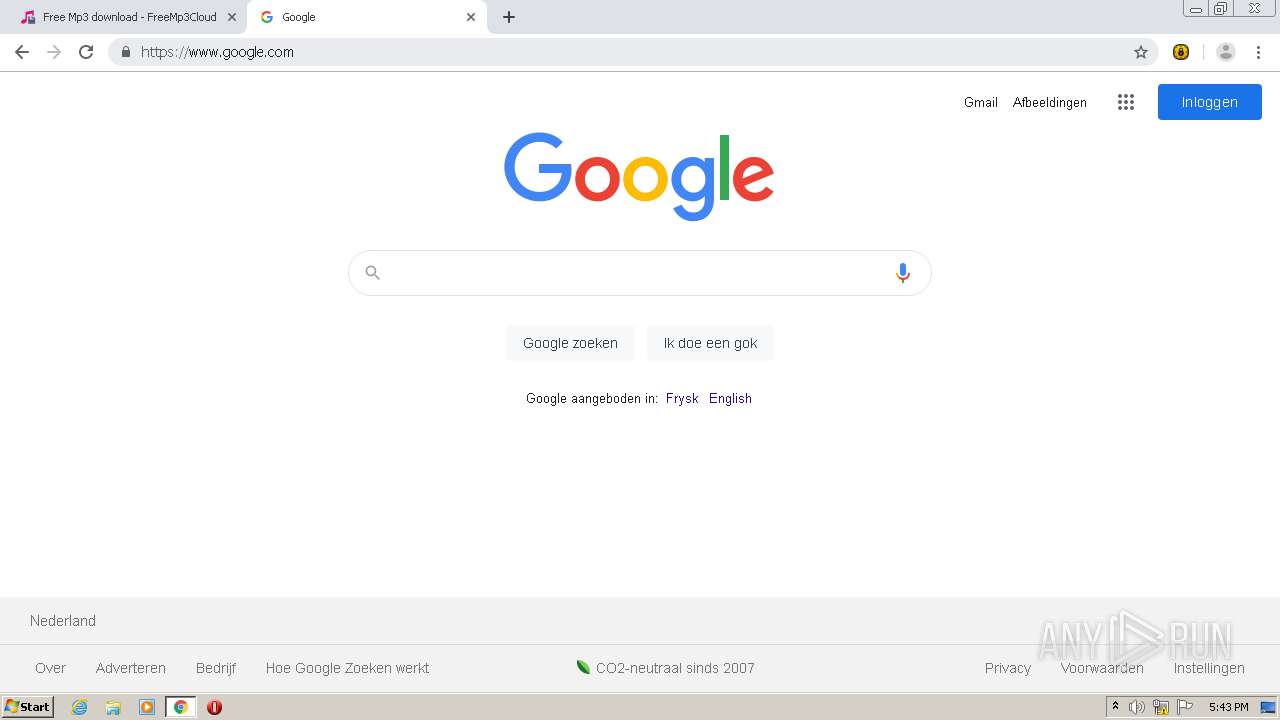
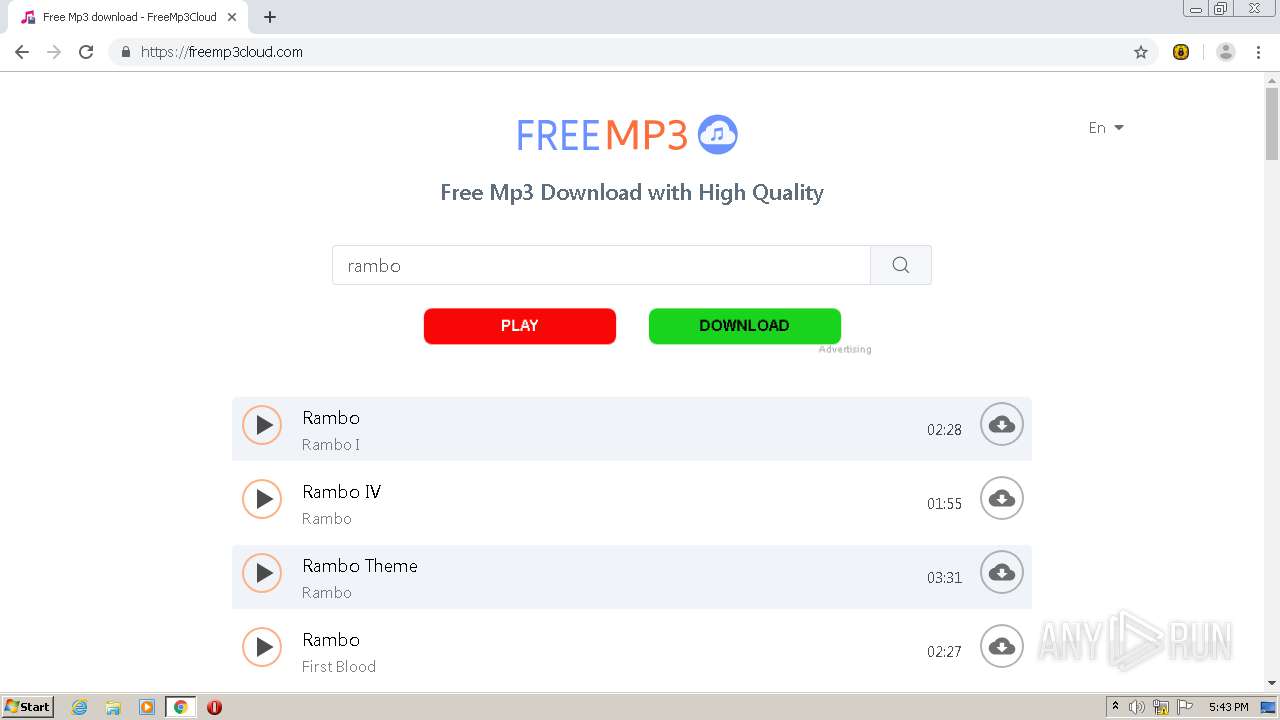
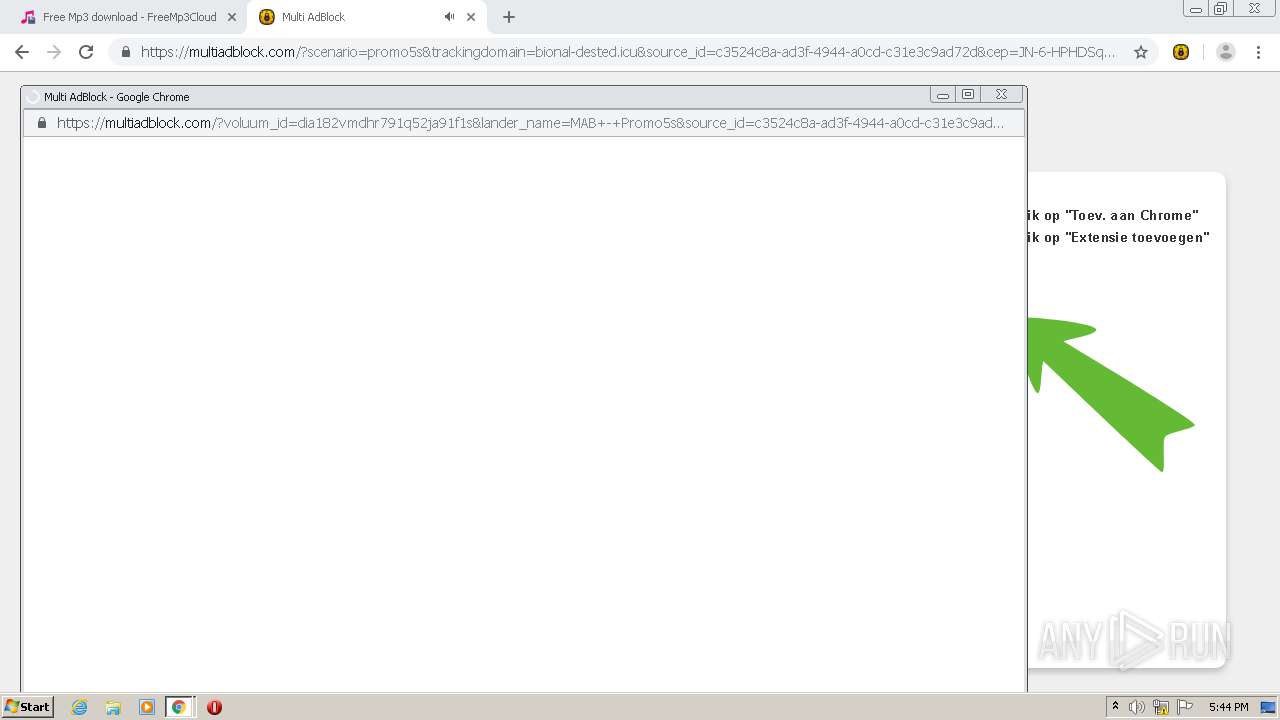
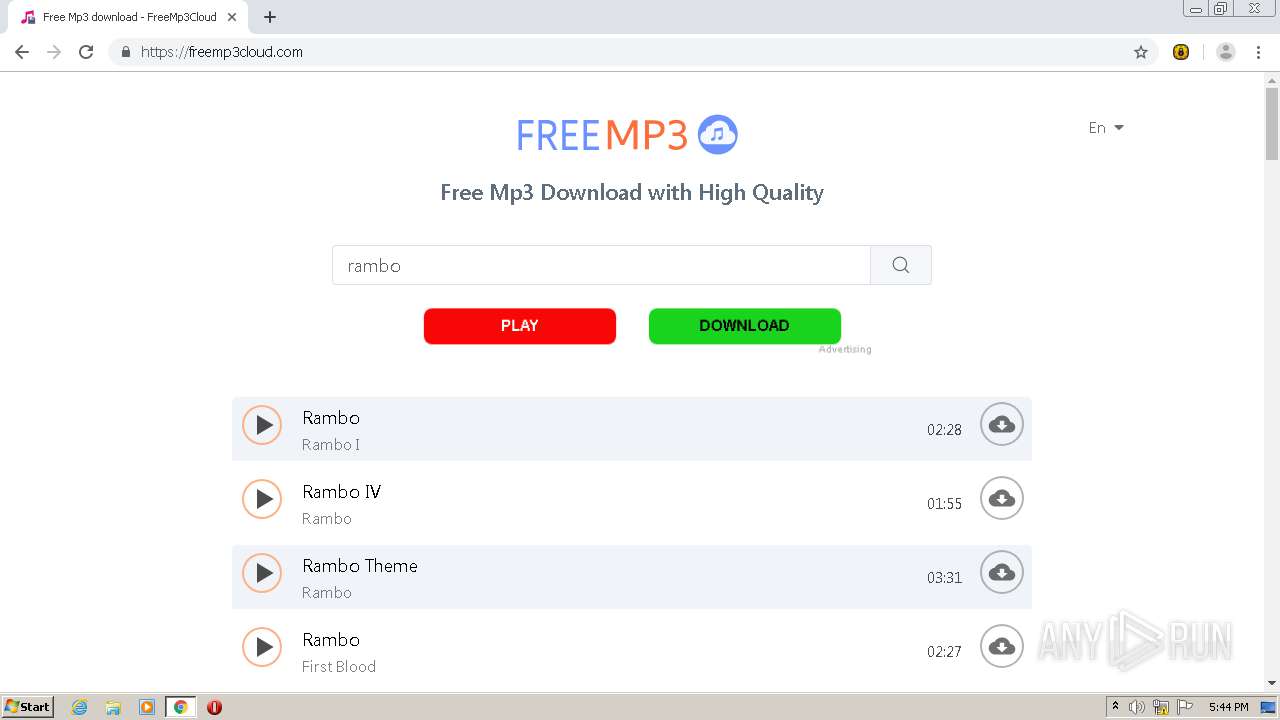
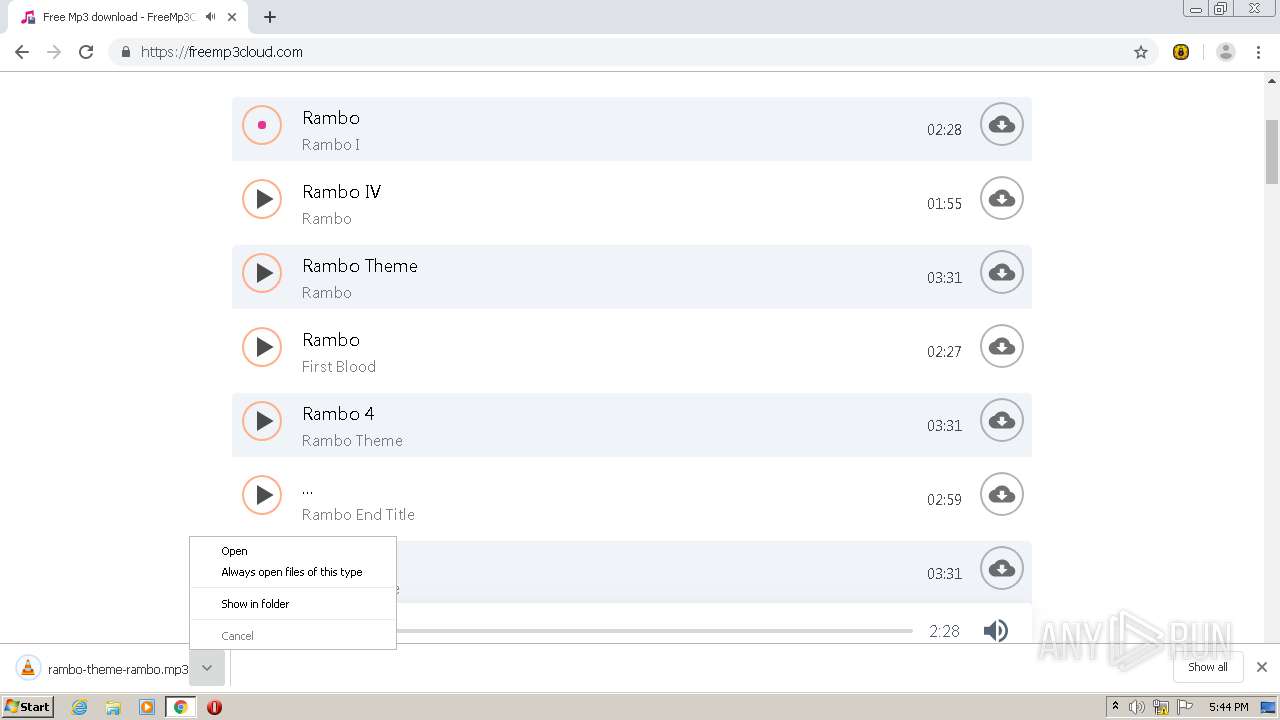
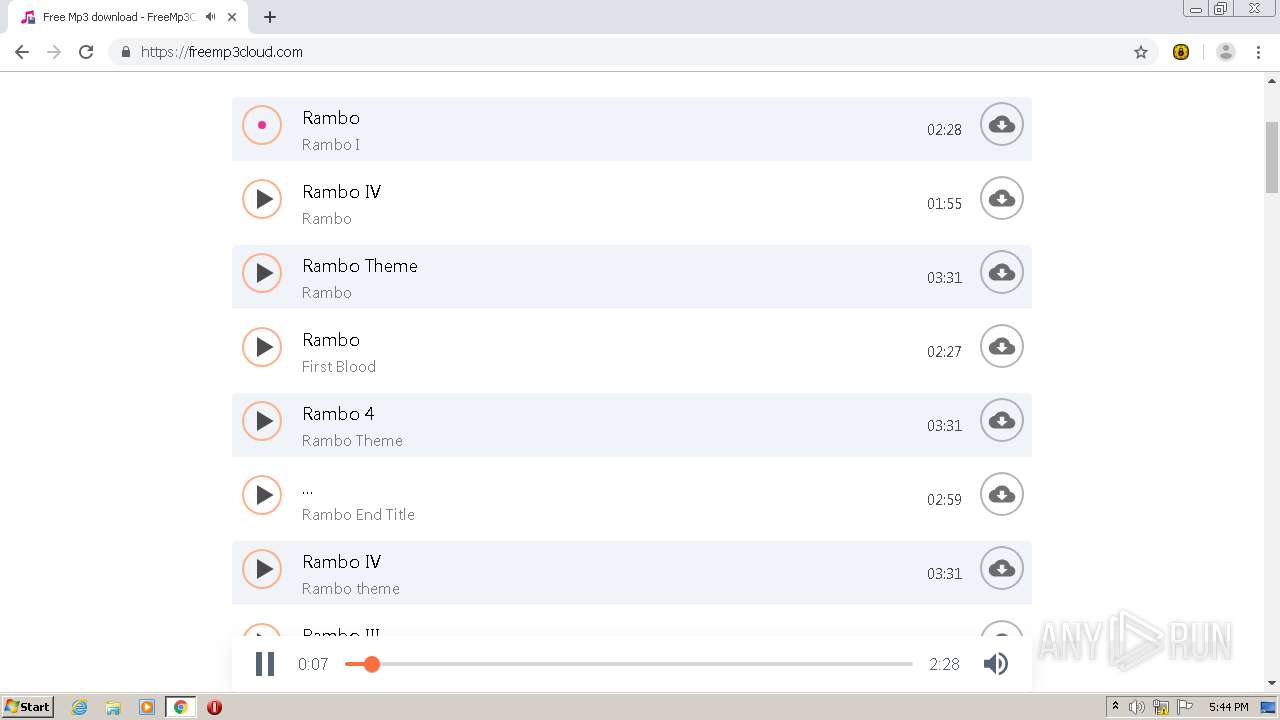
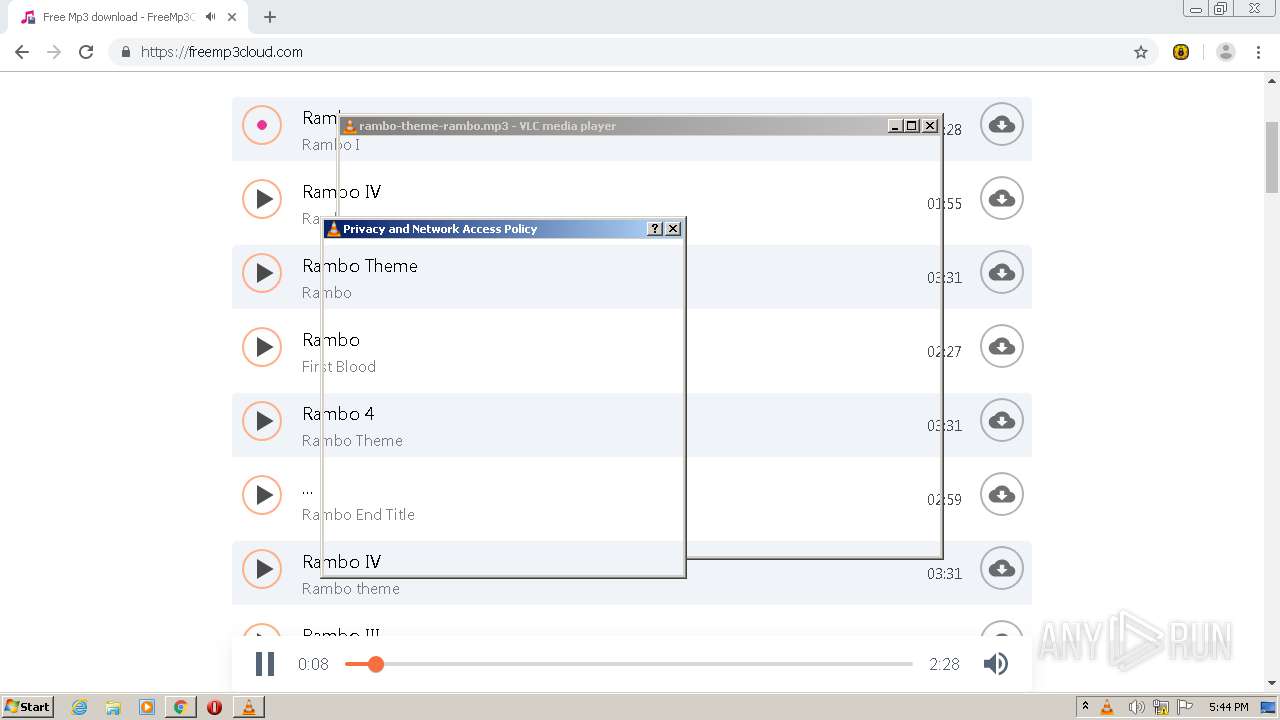
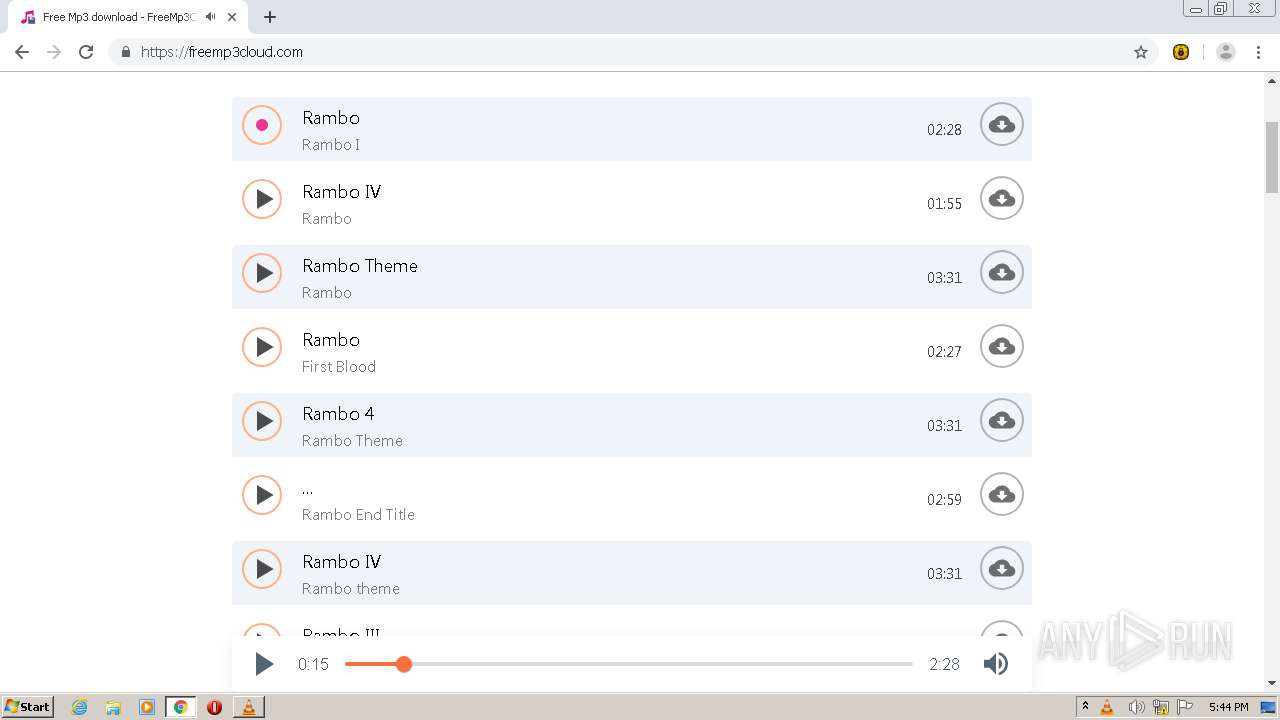
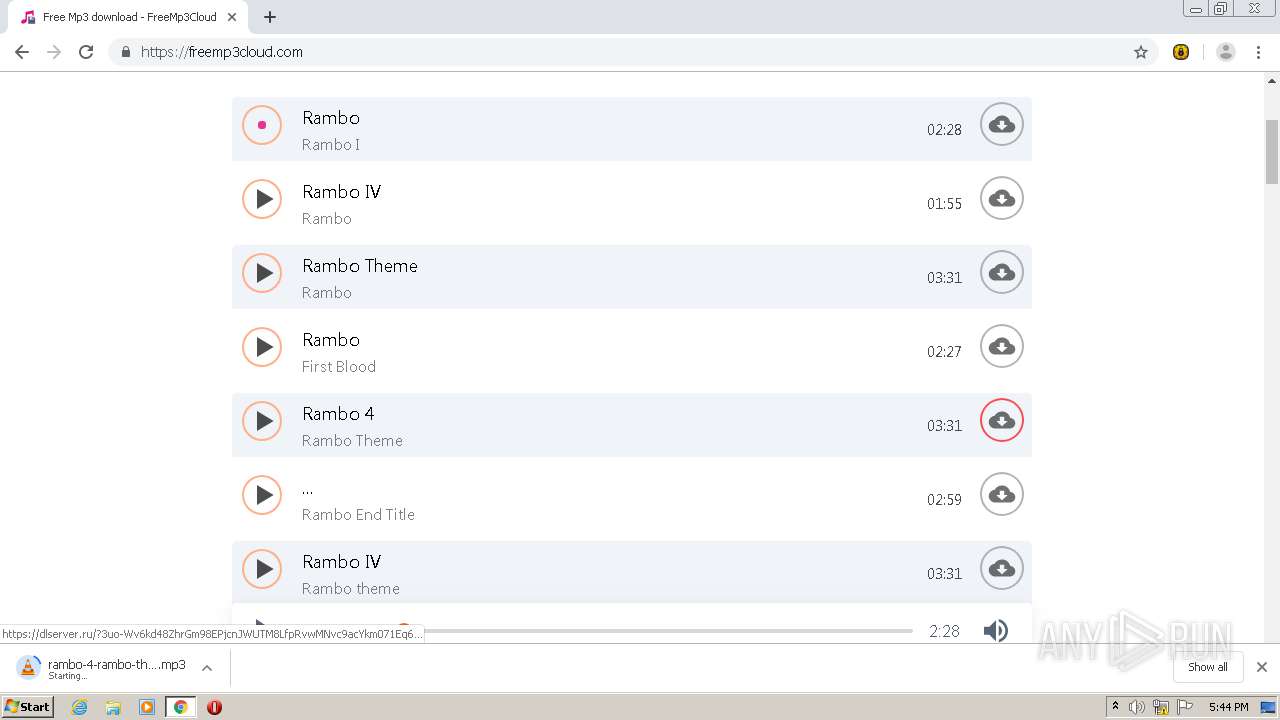
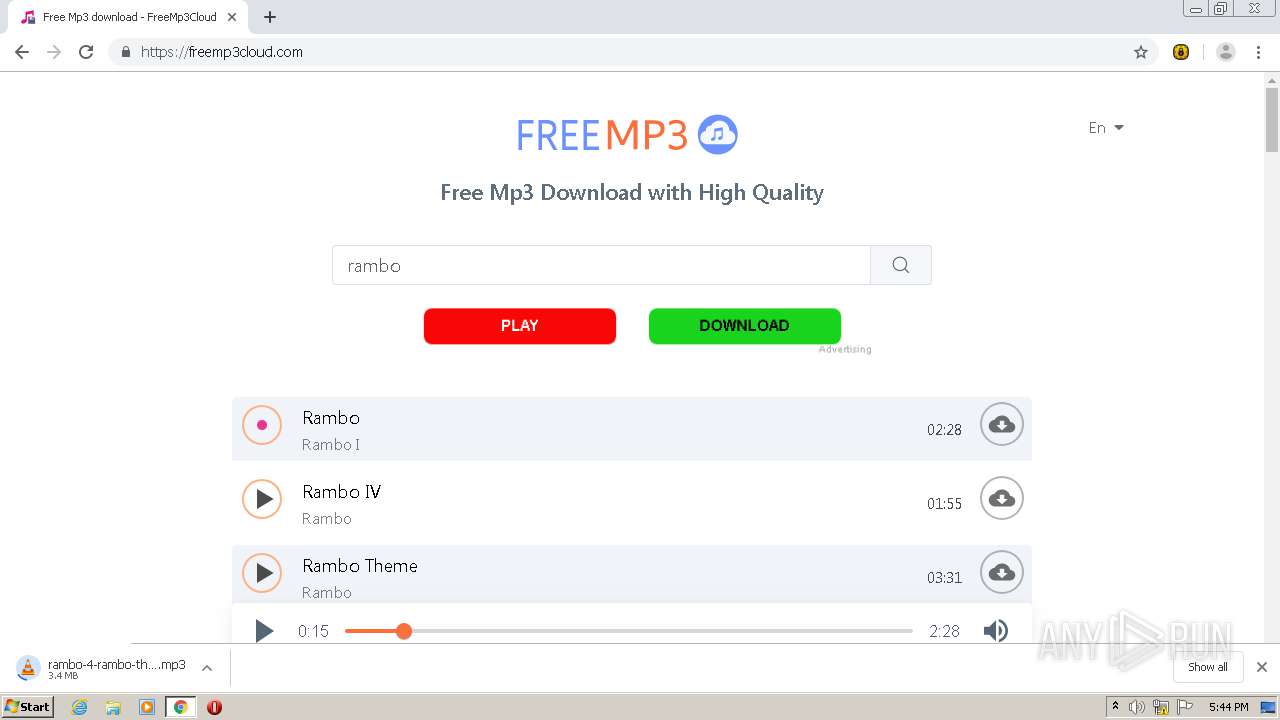
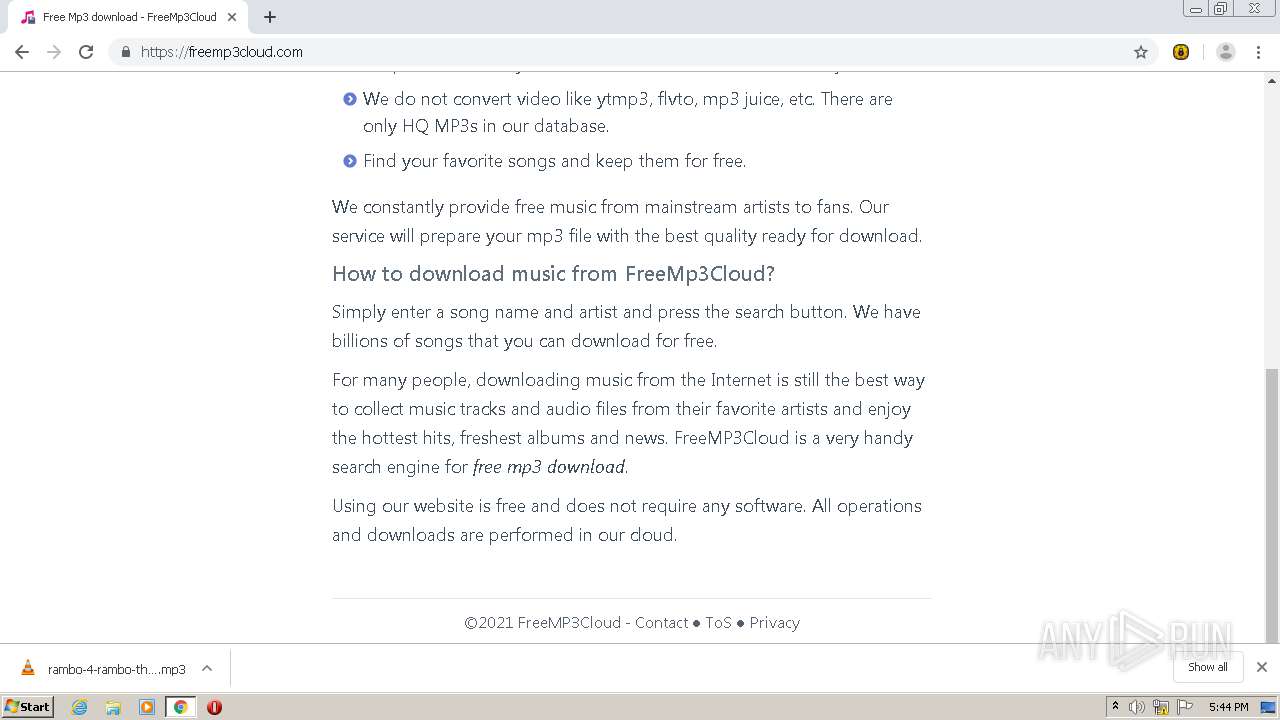
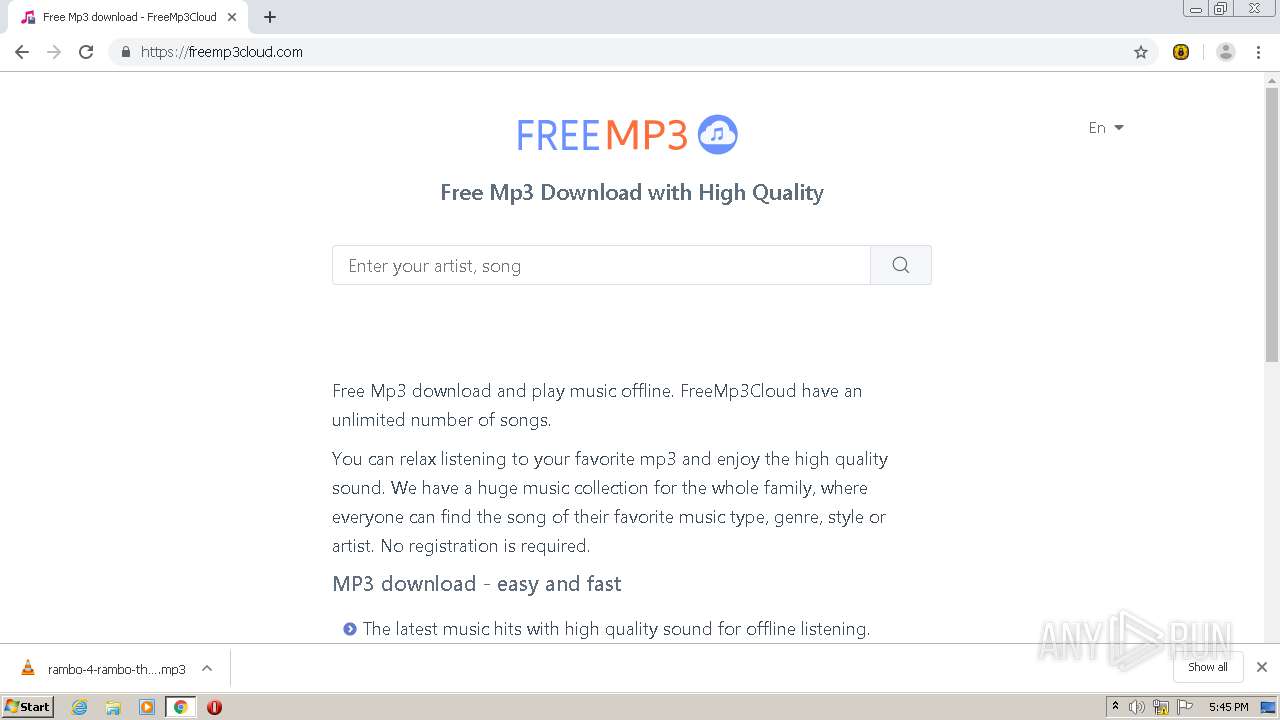
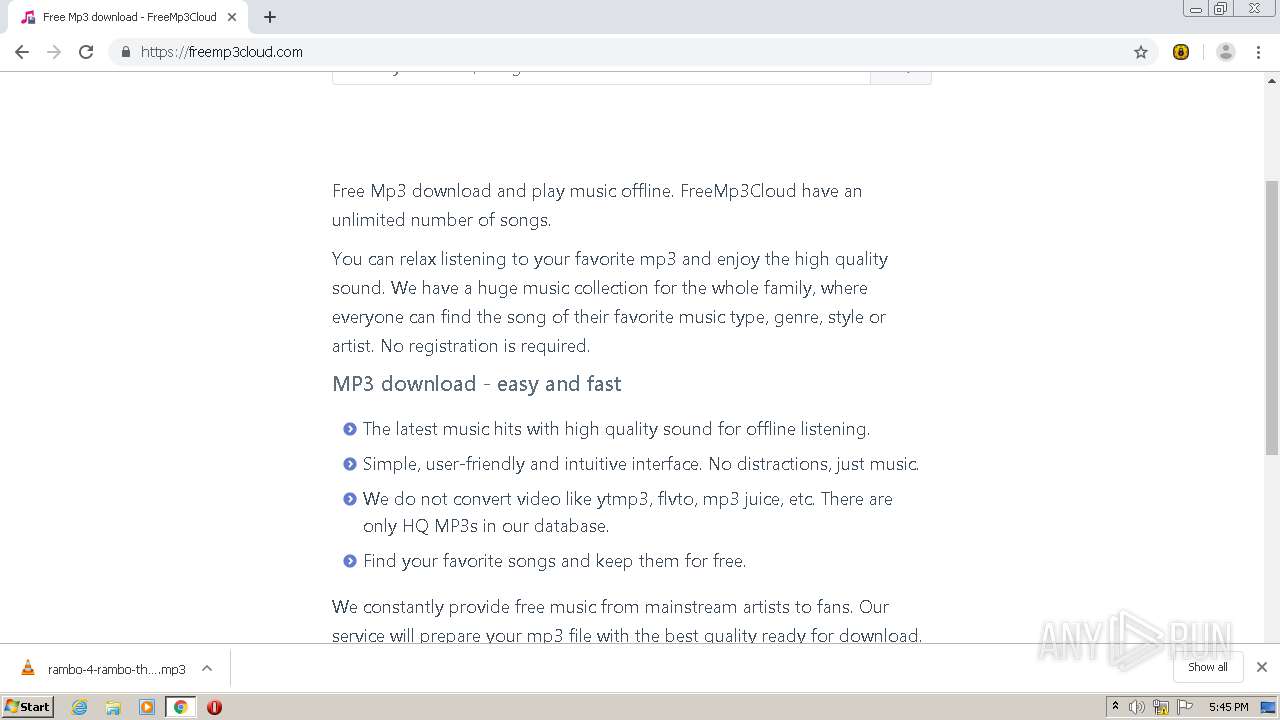
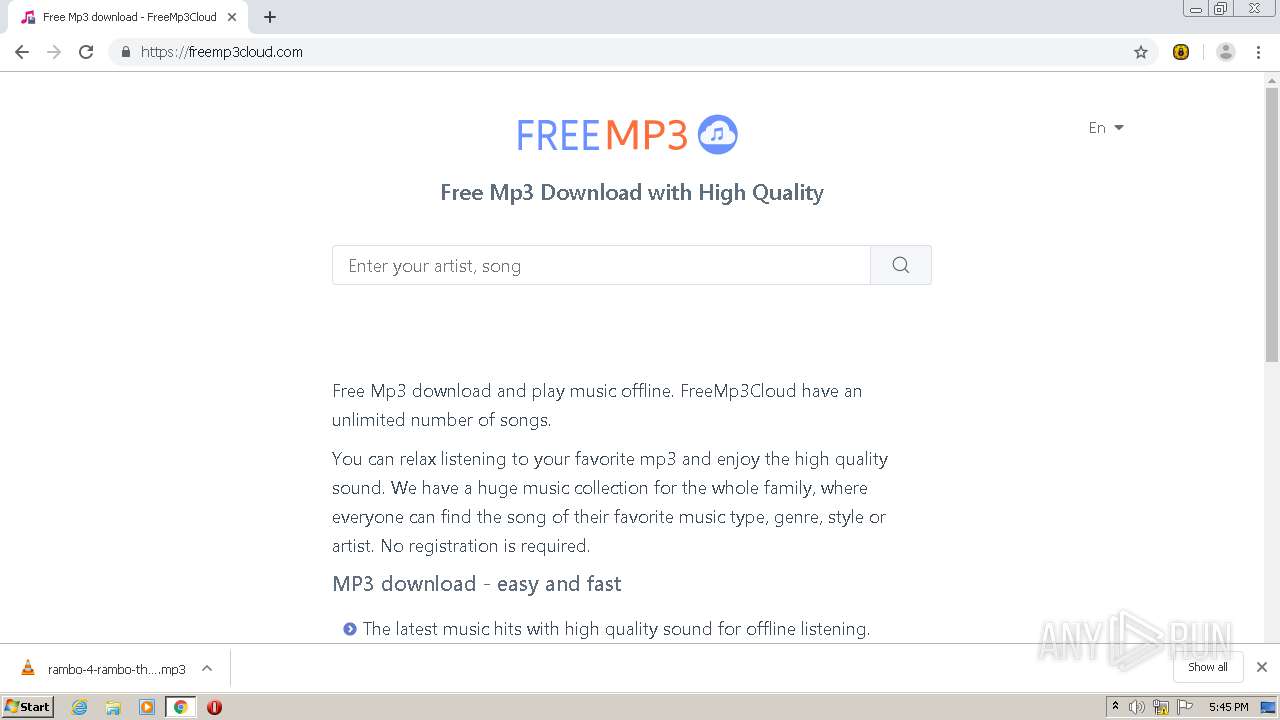
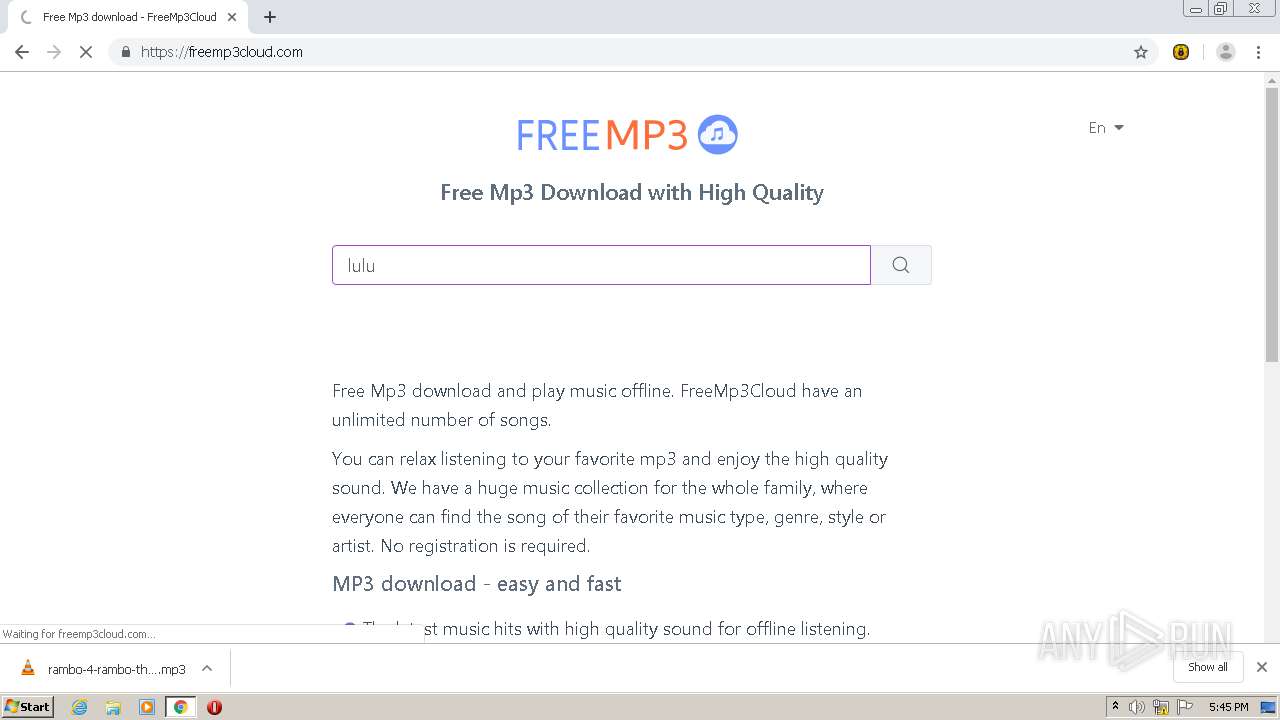
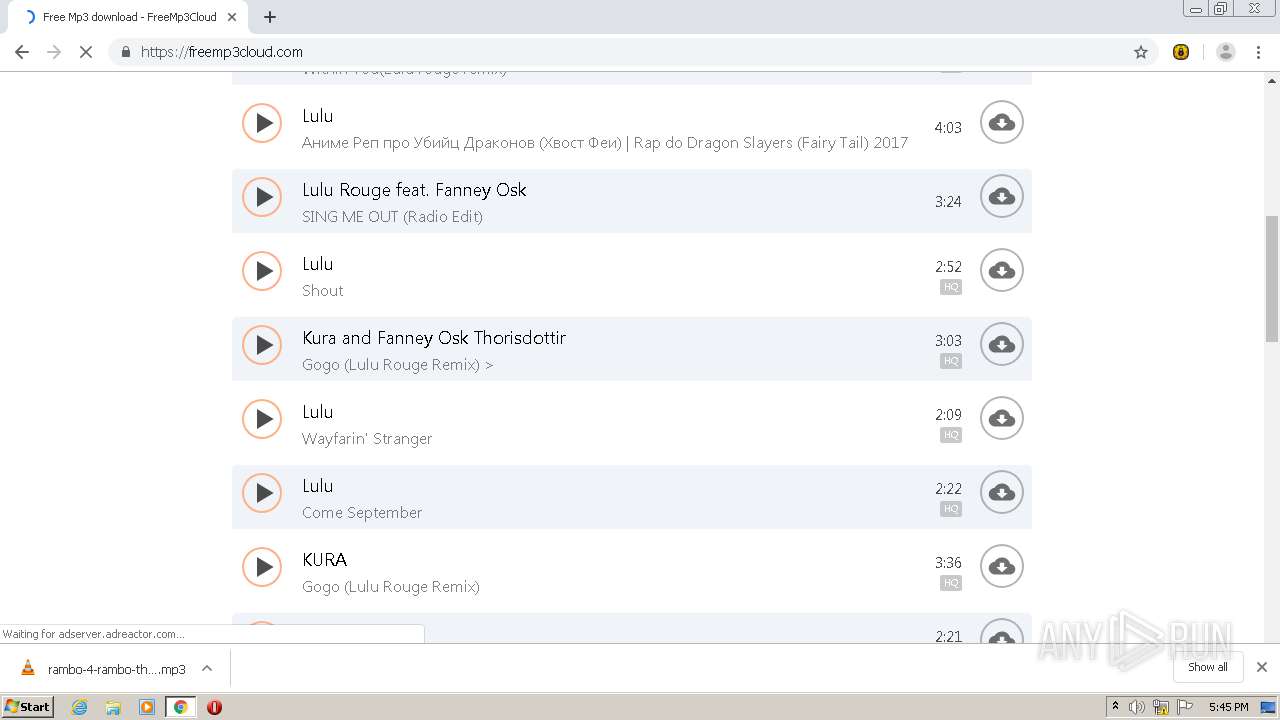
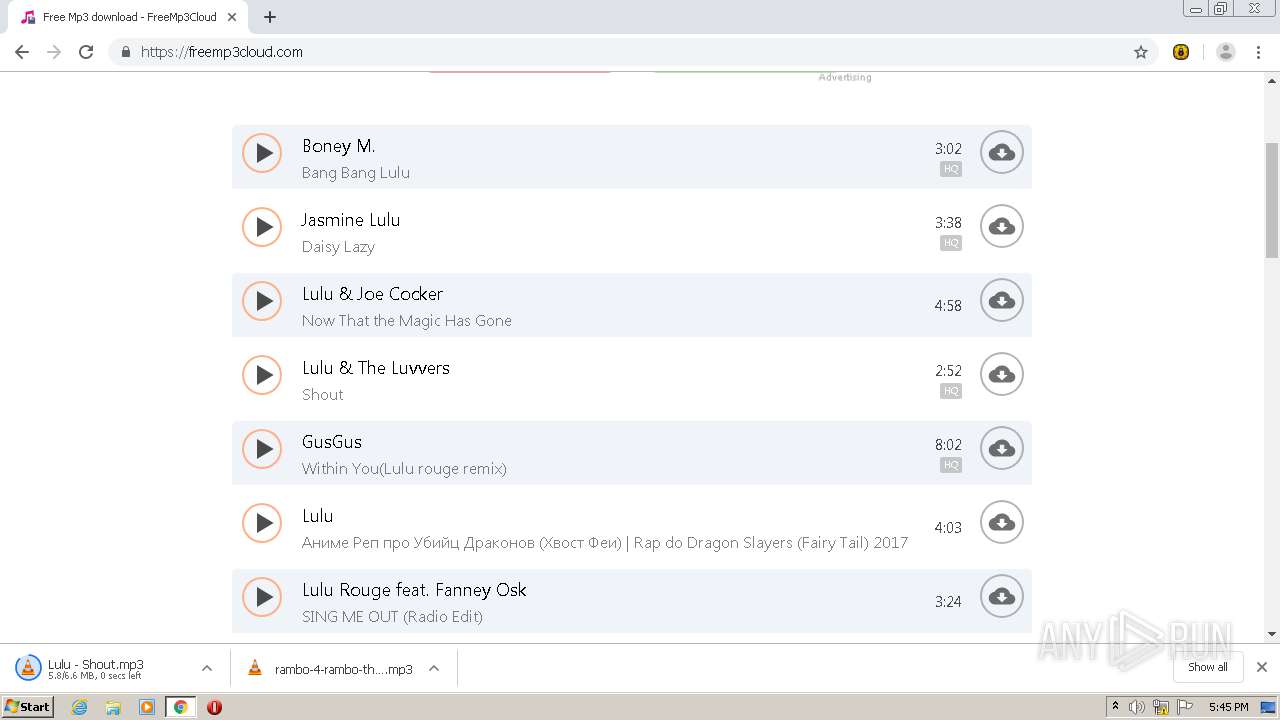
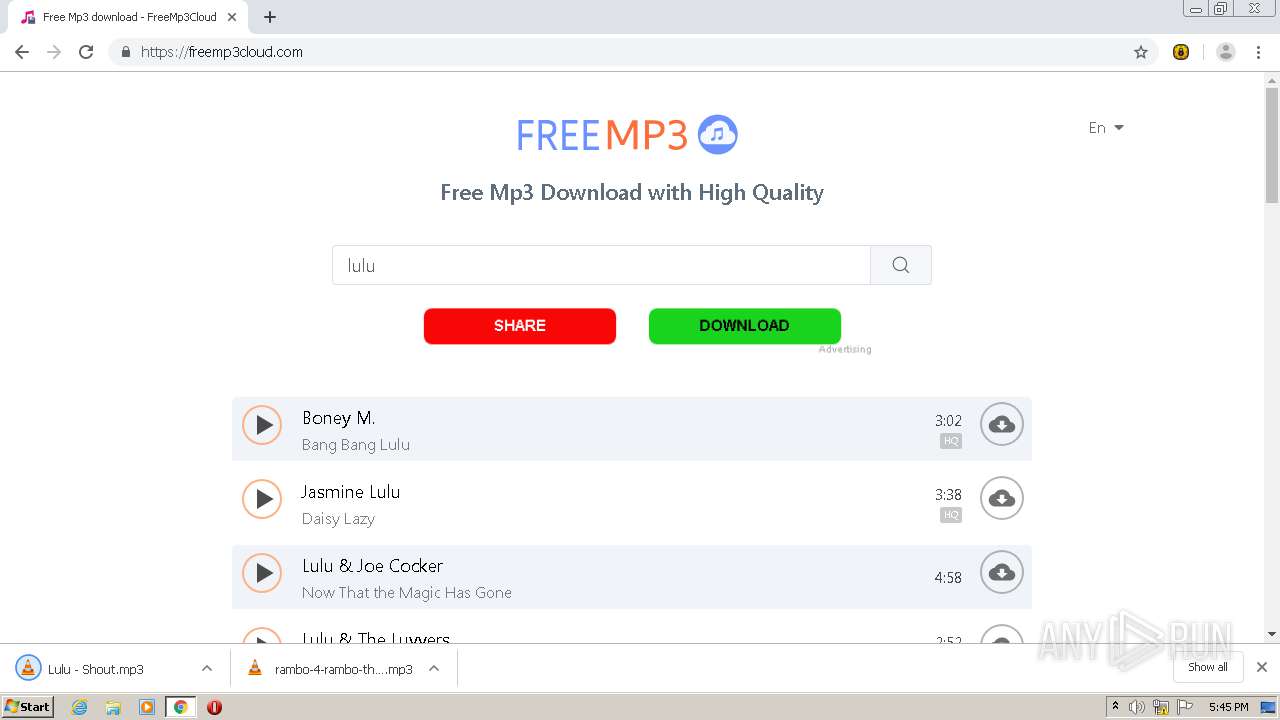
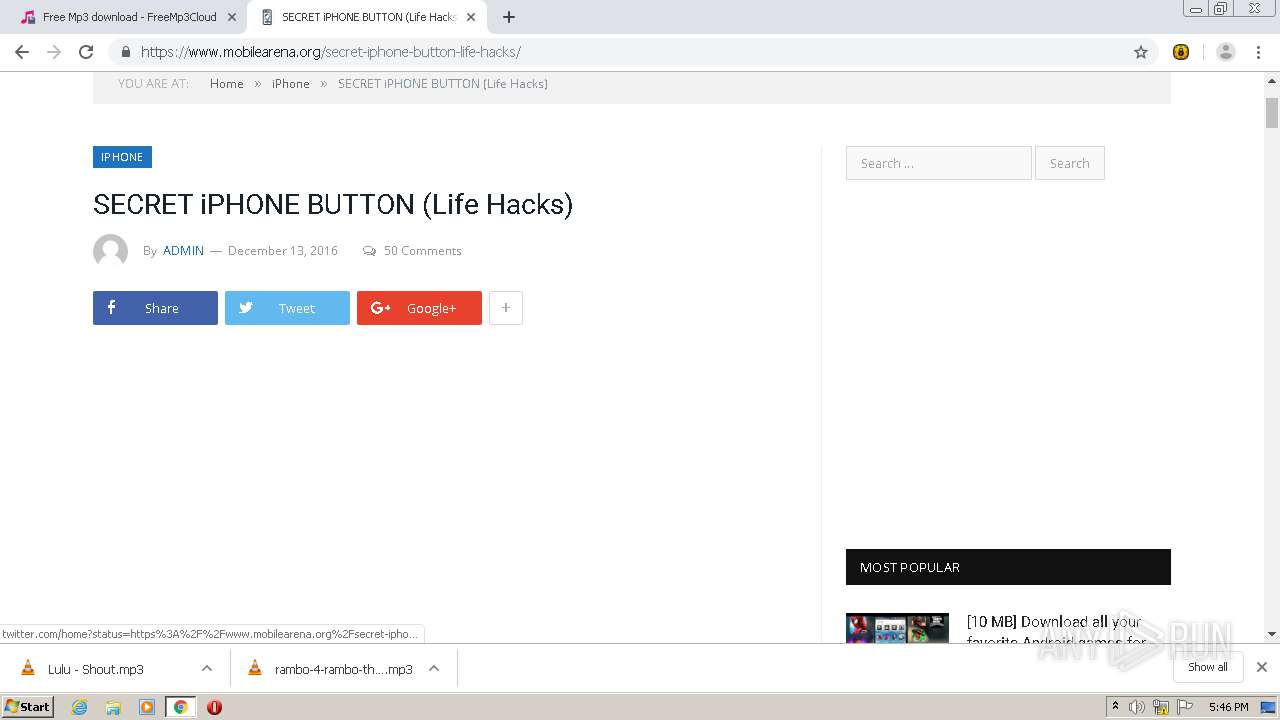
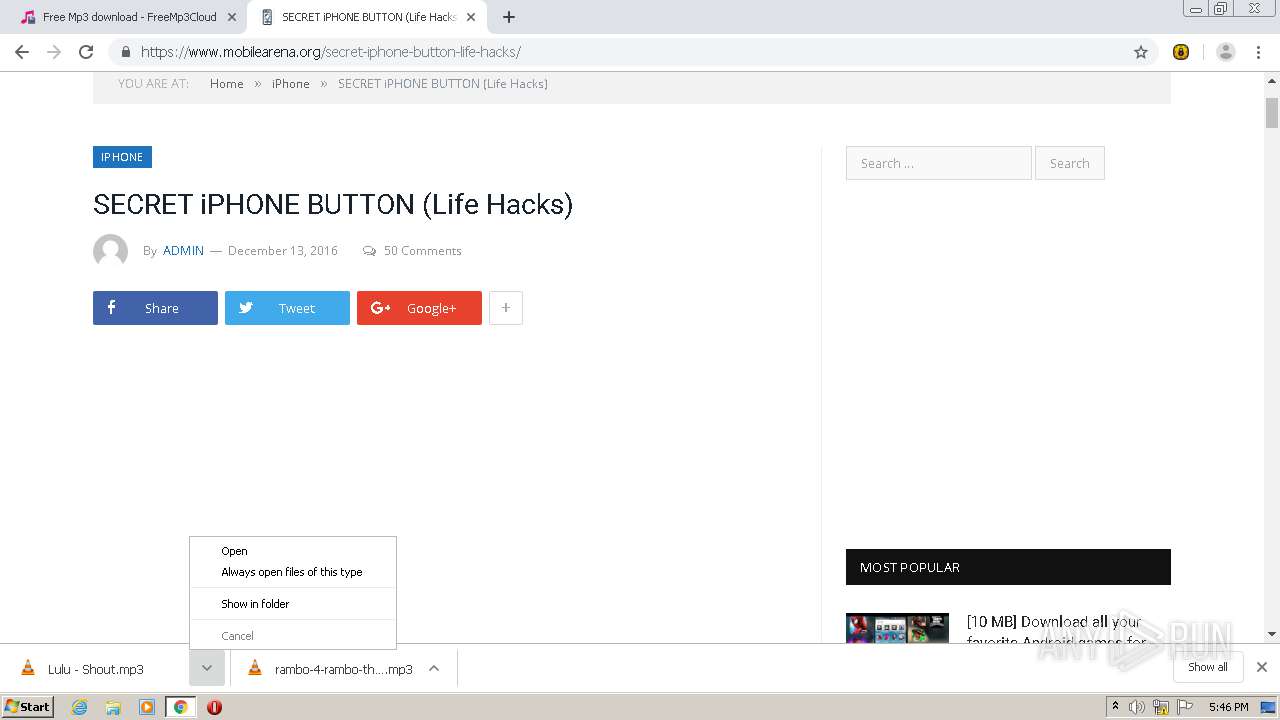
| URL: | https://freemp3cloud.com |
| Full analysis: | https://app.any.run/tasks/3ef0aaaf-1bb3-4139-bd9e-2ab91db75ad2 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2021, 17:42:26 |
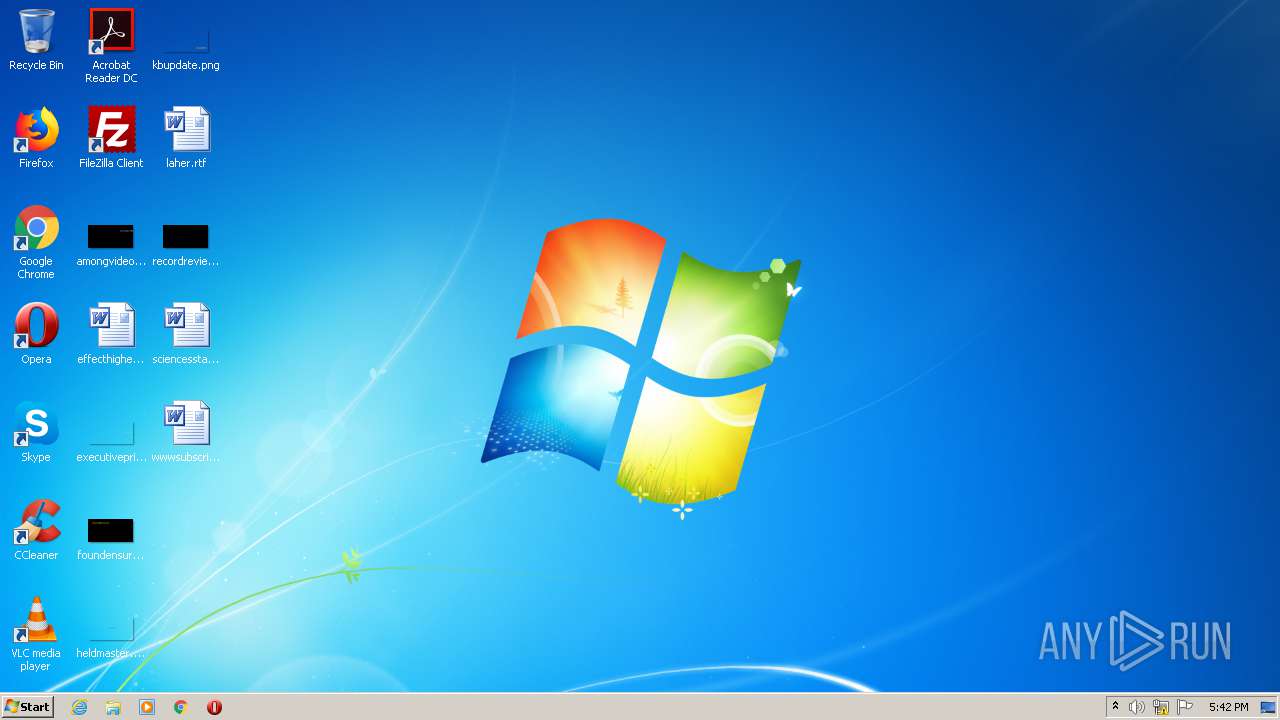
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7E17694AD164D25EE18D02E2B63B1EE4 |
| SHA1: | EA1EE4F51748FA7384AA4EC879877CB39ABF1F98 |
| SHA256: | E78E0A90CB33705F3D1BE0F5989416531CF3DFABE186991E21D11008B36A3E8A |
| SSDEEP: | 3:N88RI:28RI |
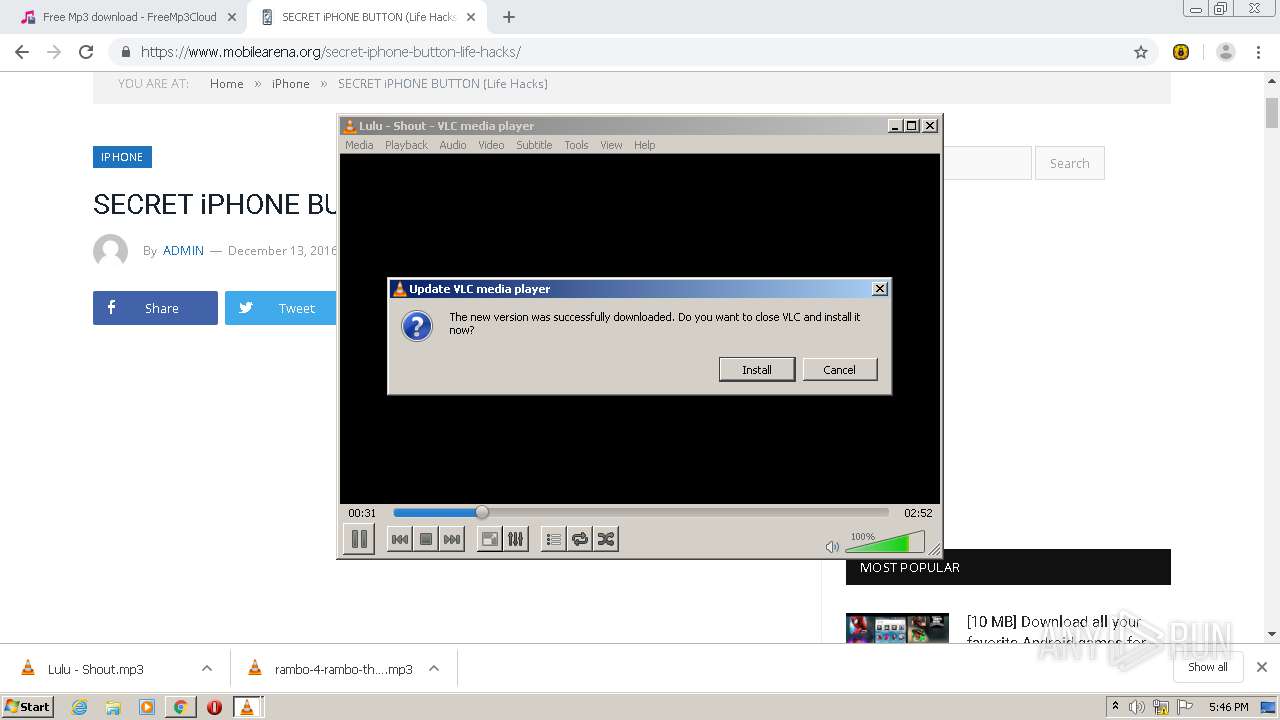
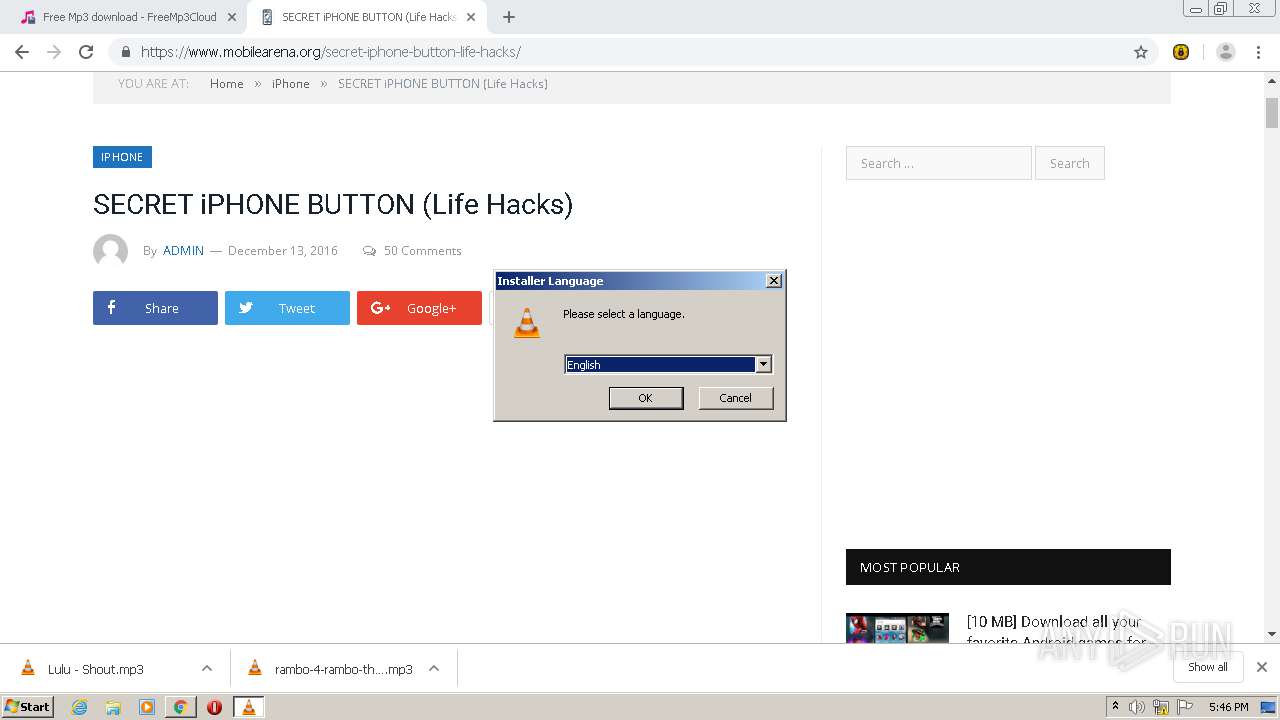
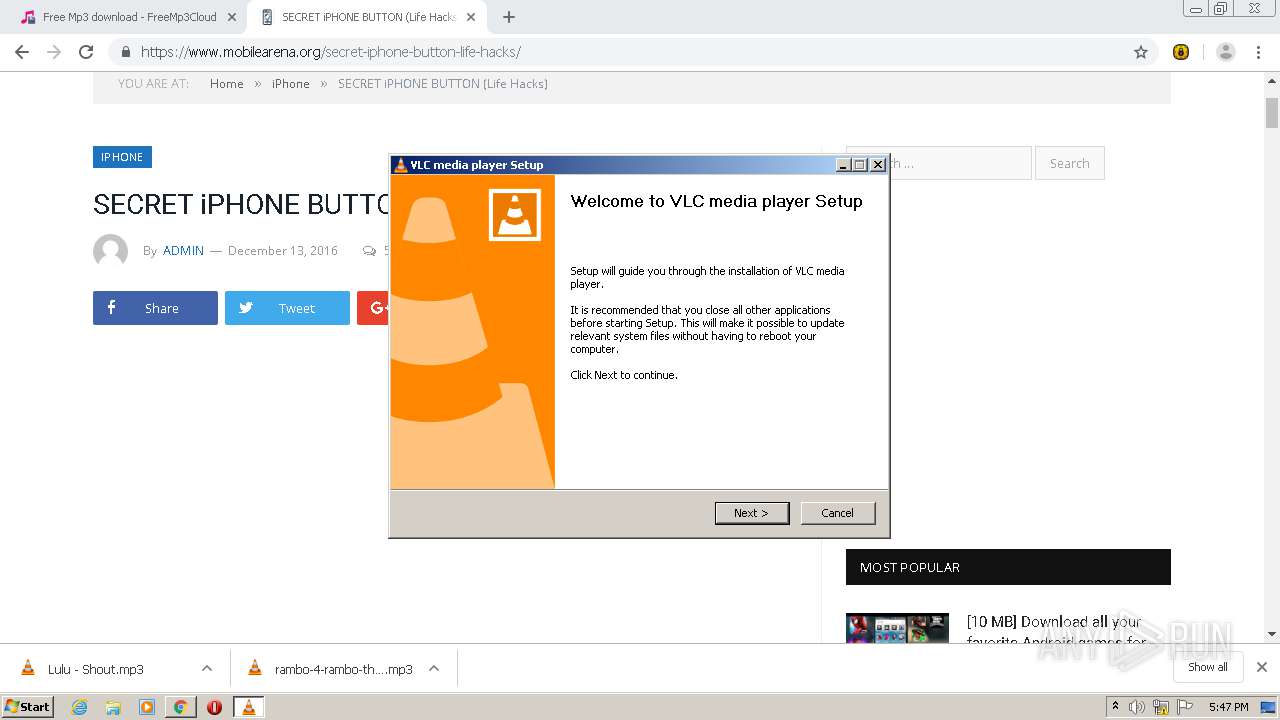
MALICIOUS
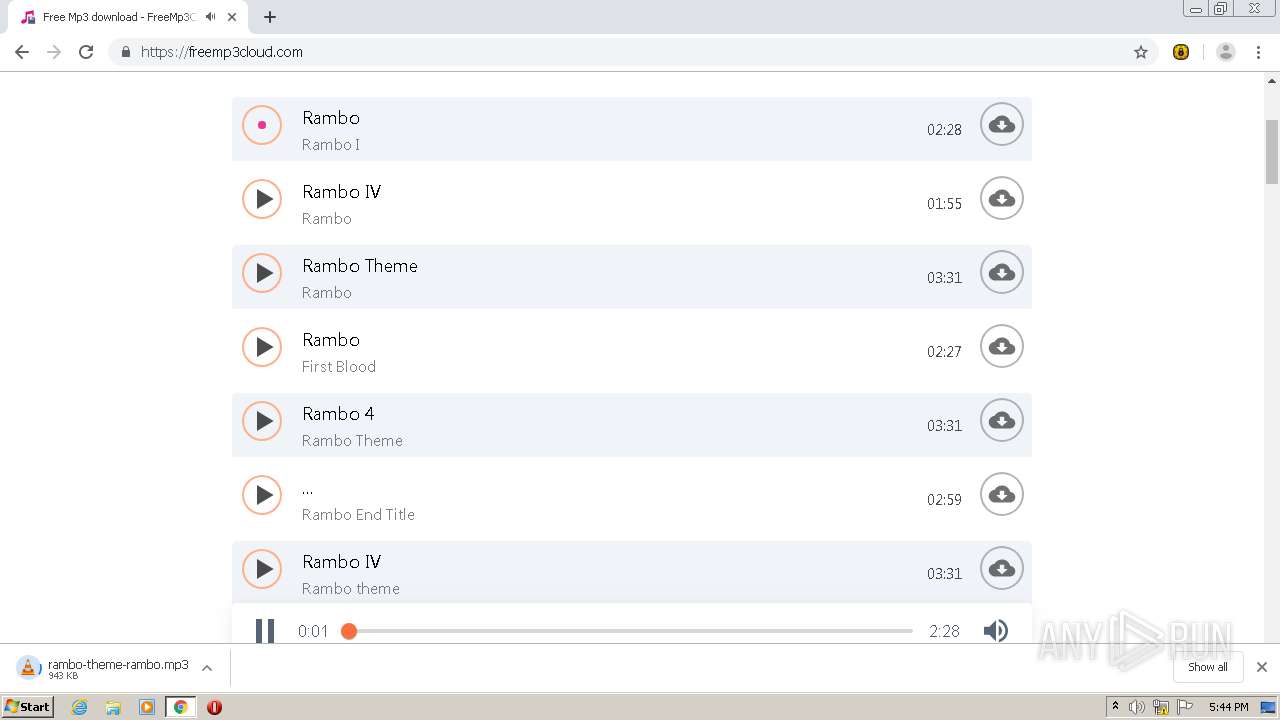
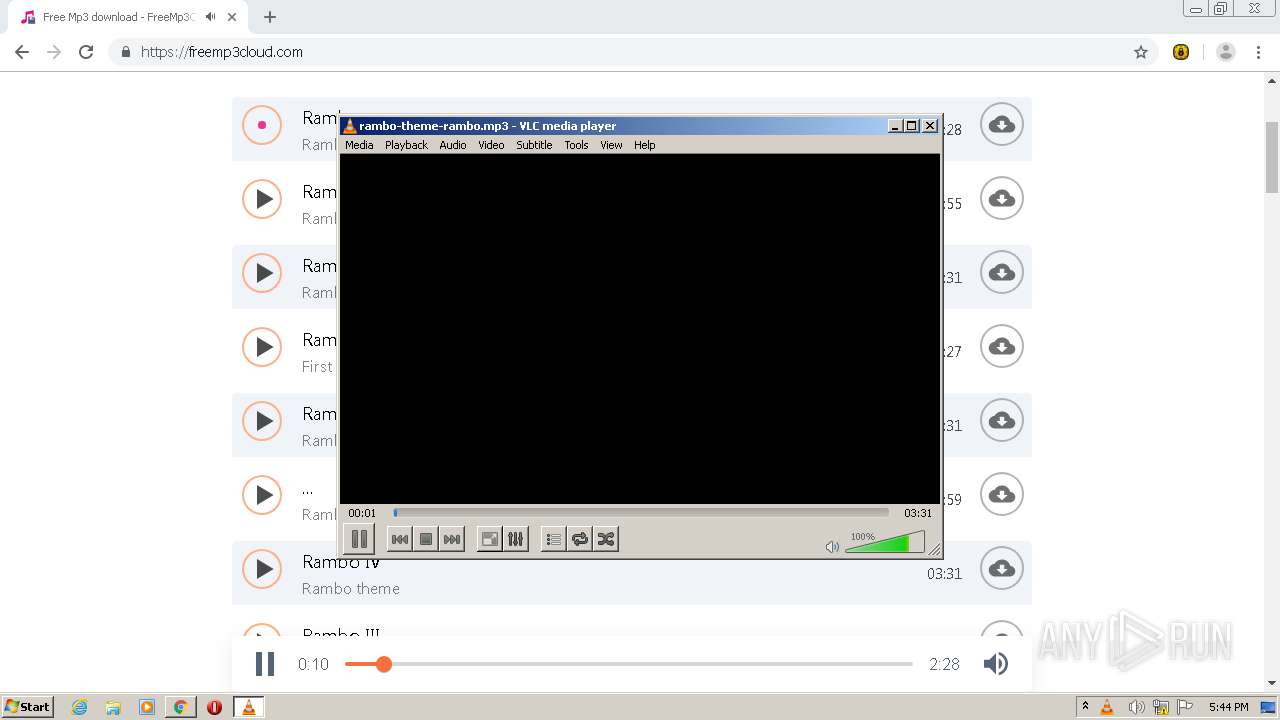
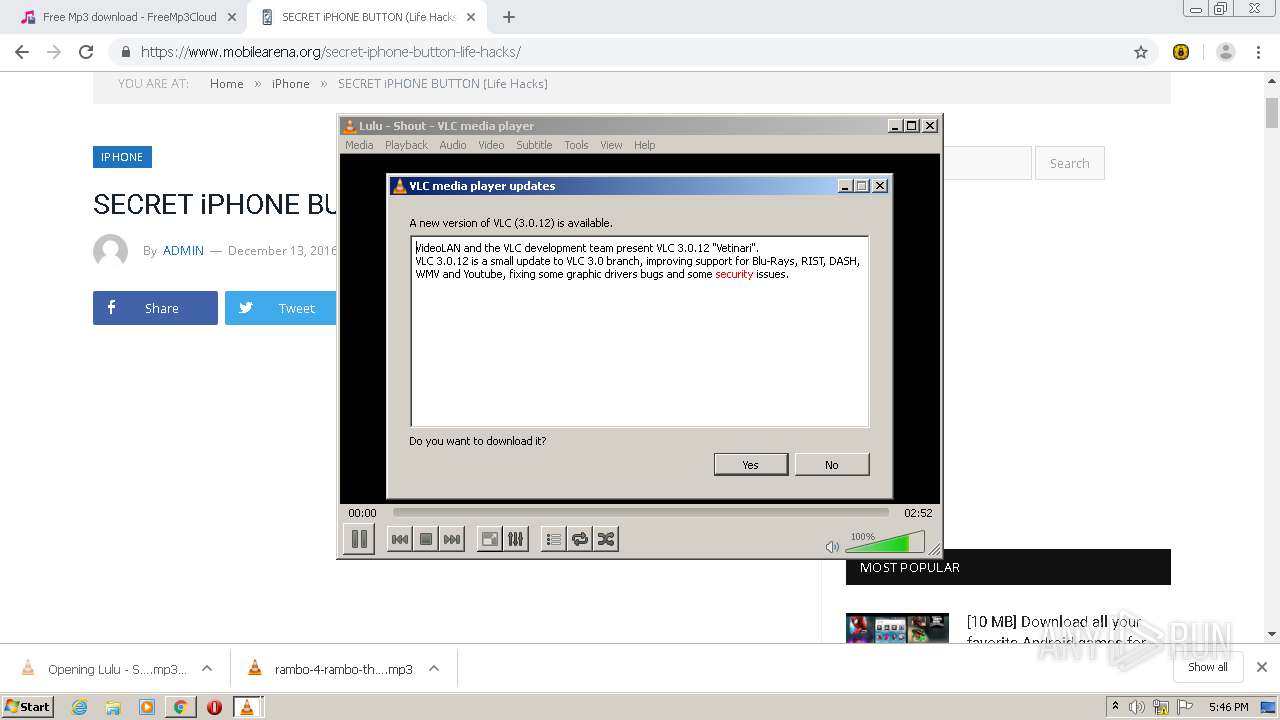
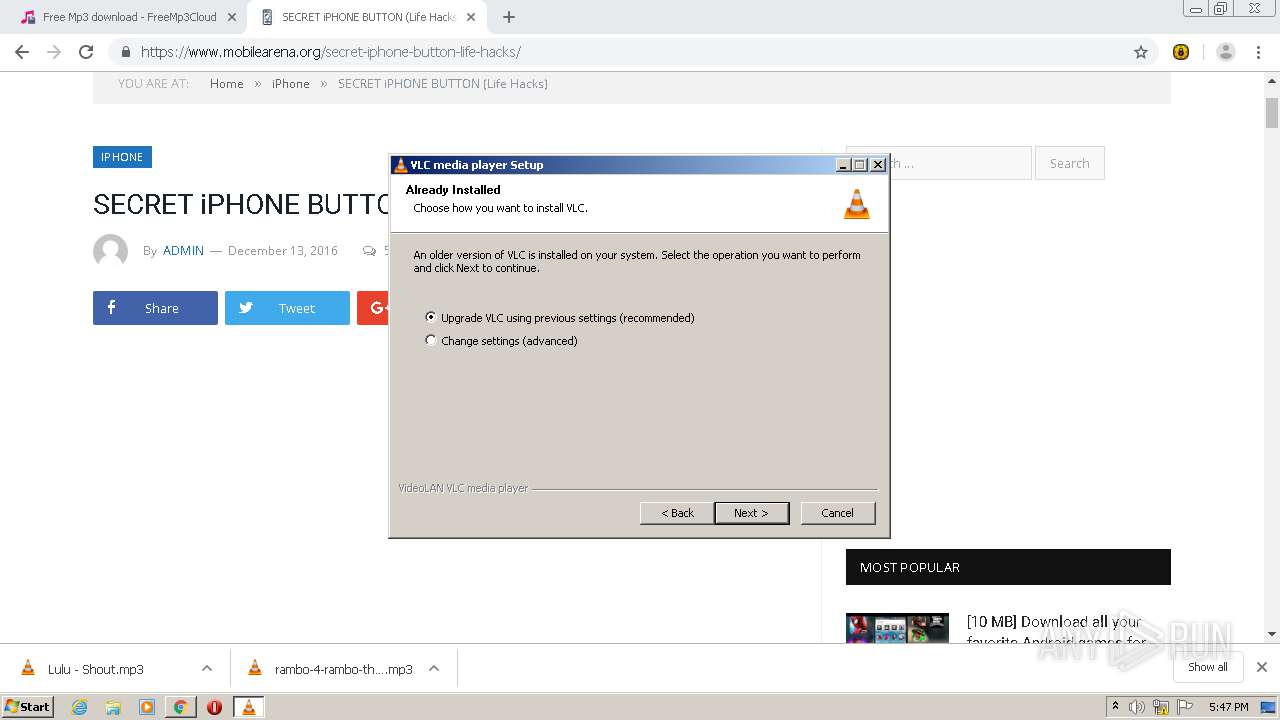
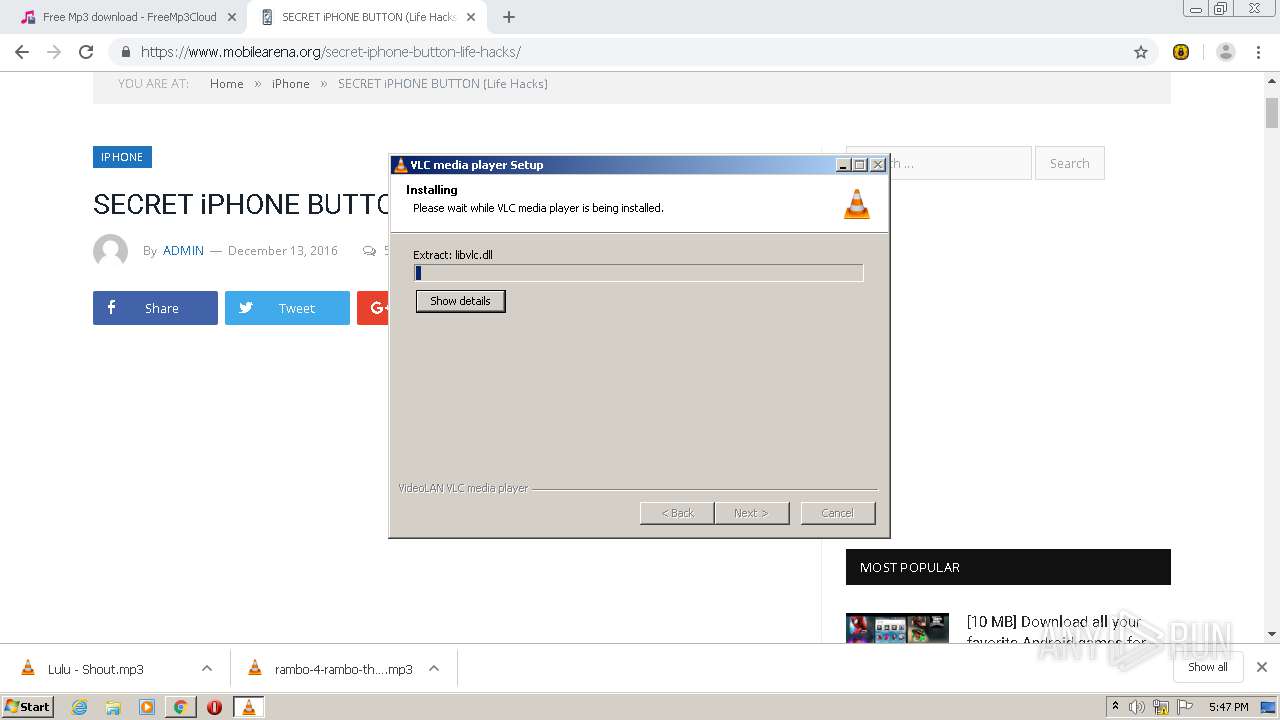
Loads dropped or rewritten executable
- vlc-3.0.12-win32.exe (PID: 632)
- vlc-cache-gen.exe (PID: 3836)
Application was dropped or rewritten from another process
- vlc-cache-gen.exe (PID: 3836)
- vlc-3.0.12-win32.exe (PID: 3876)
- ns6D62.tmp (PID: 2800)
- vlc-3.0.12-win32.exe (PID: 632)
- vlc.exe (PID: 1844)
SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 3380)
- vlc.exe (PID: 3468)
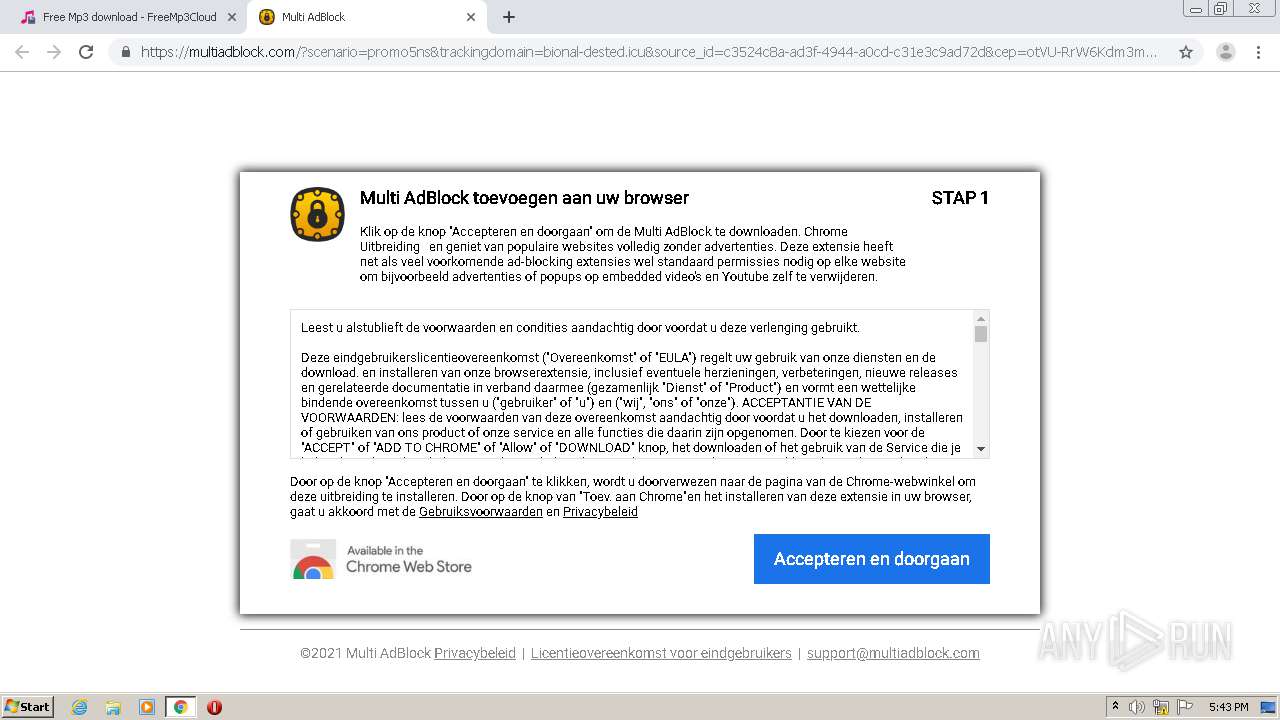
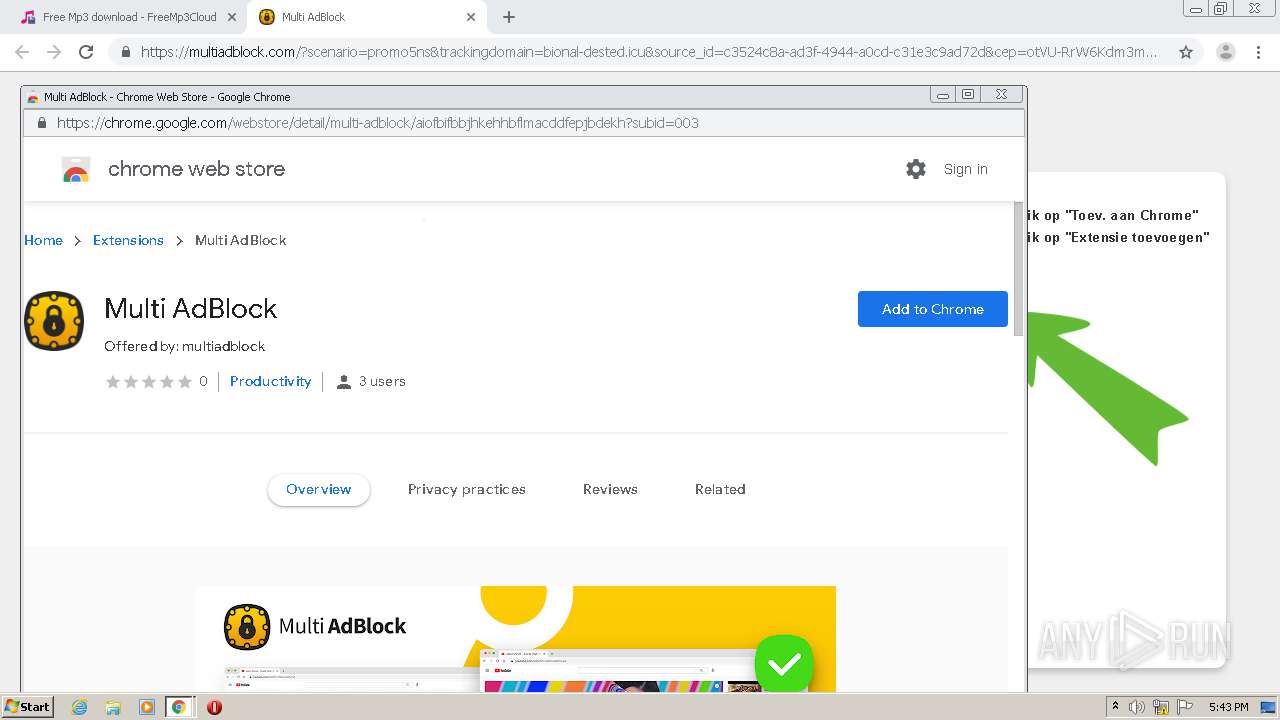
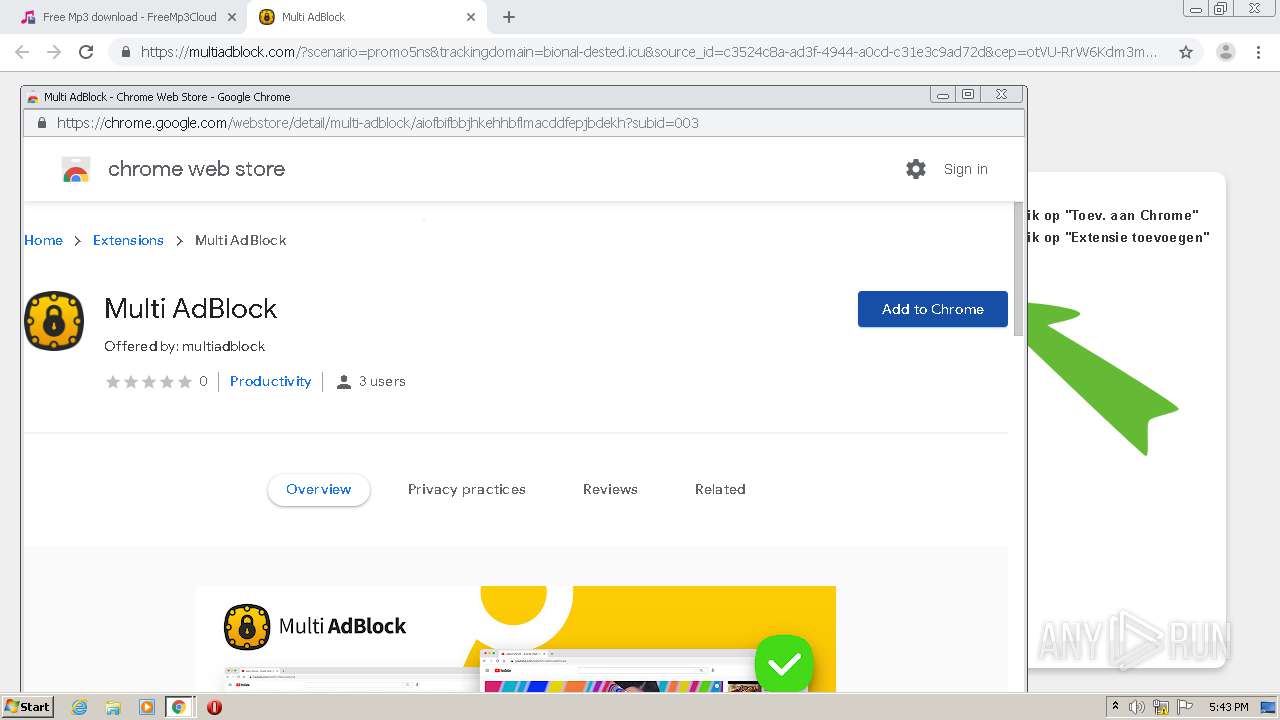
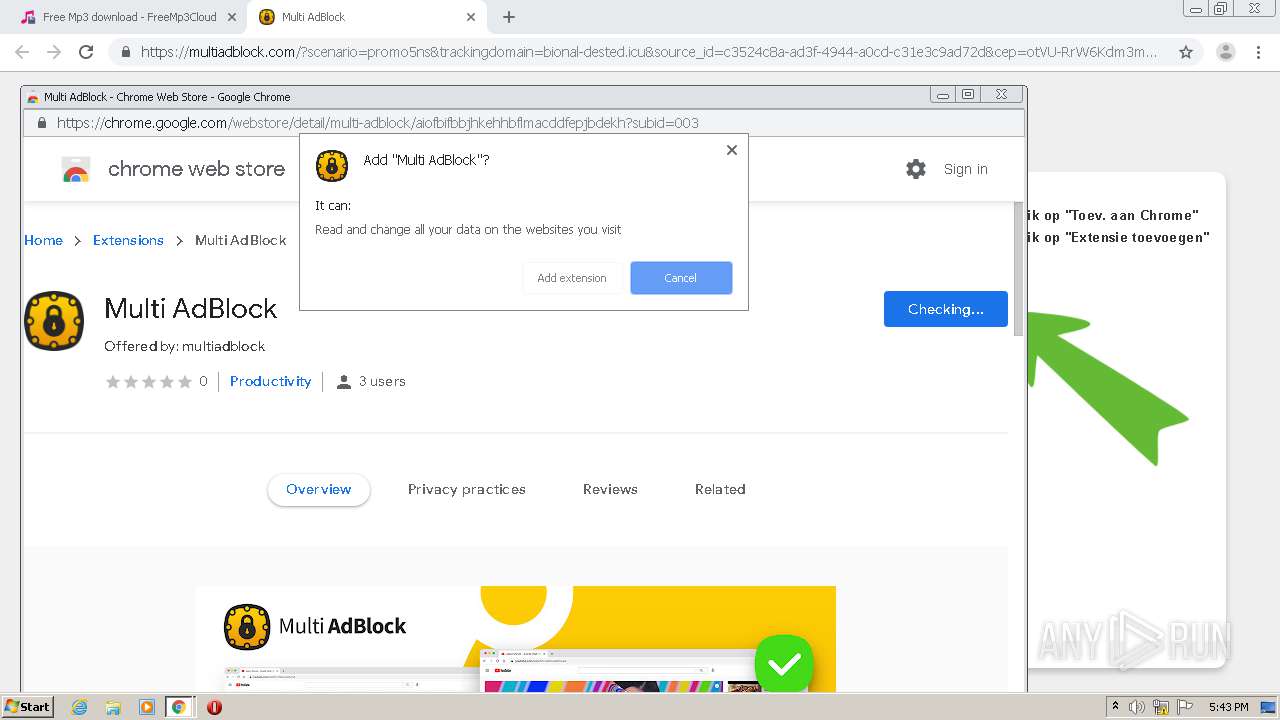
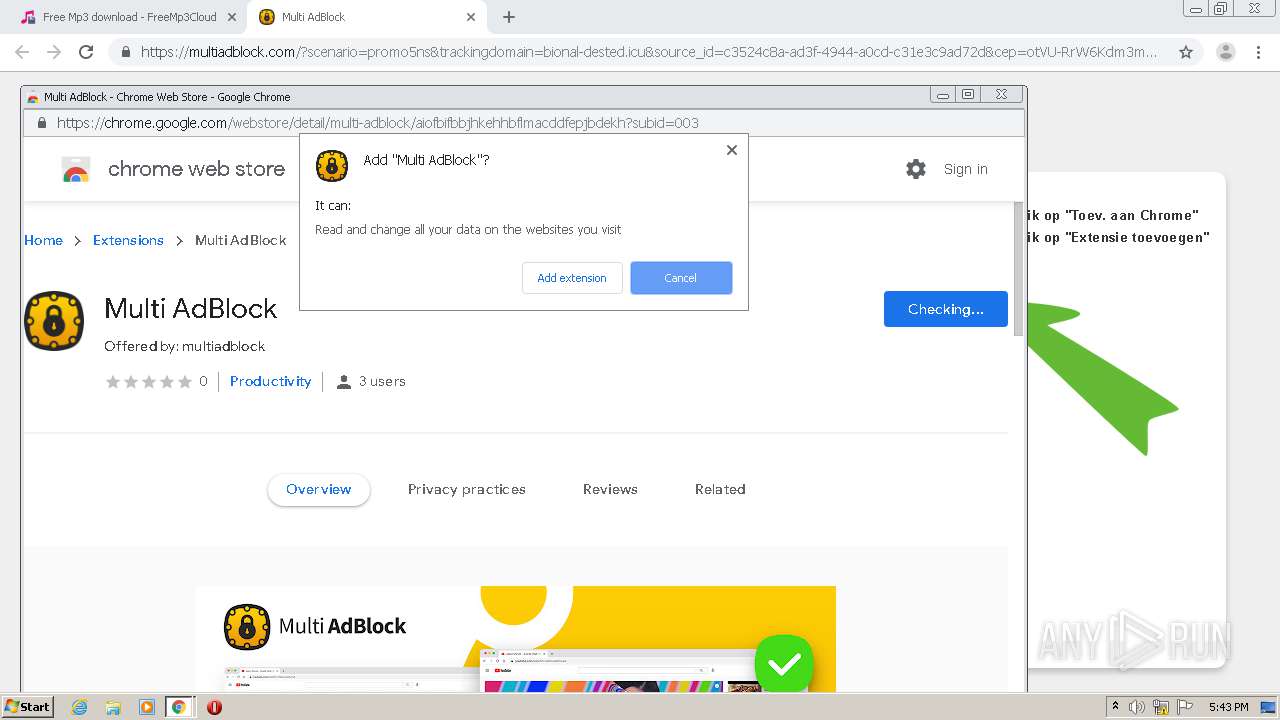
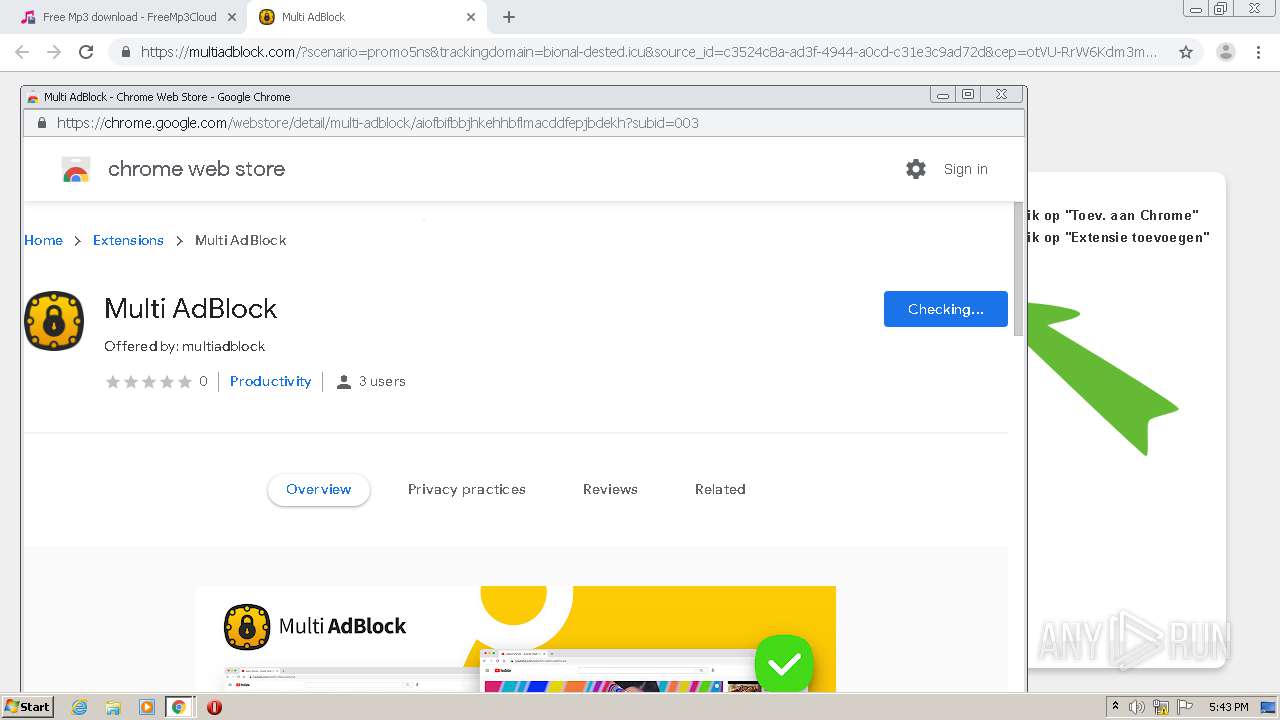
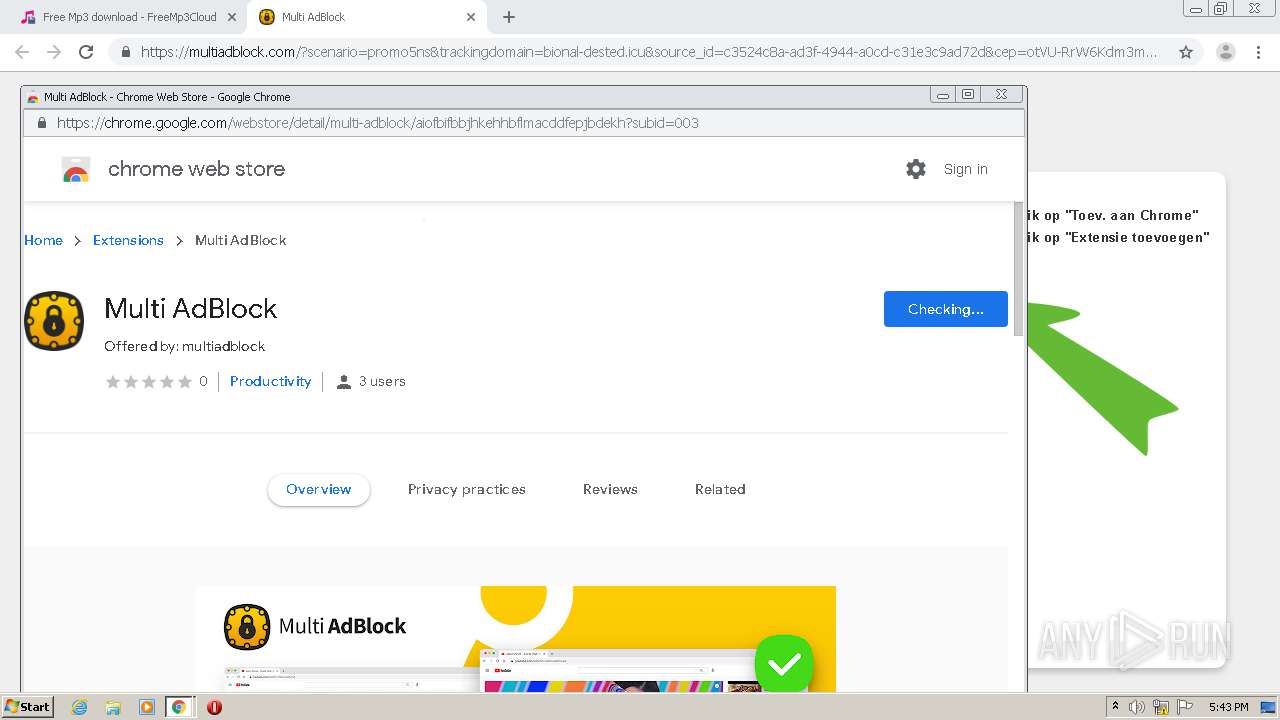
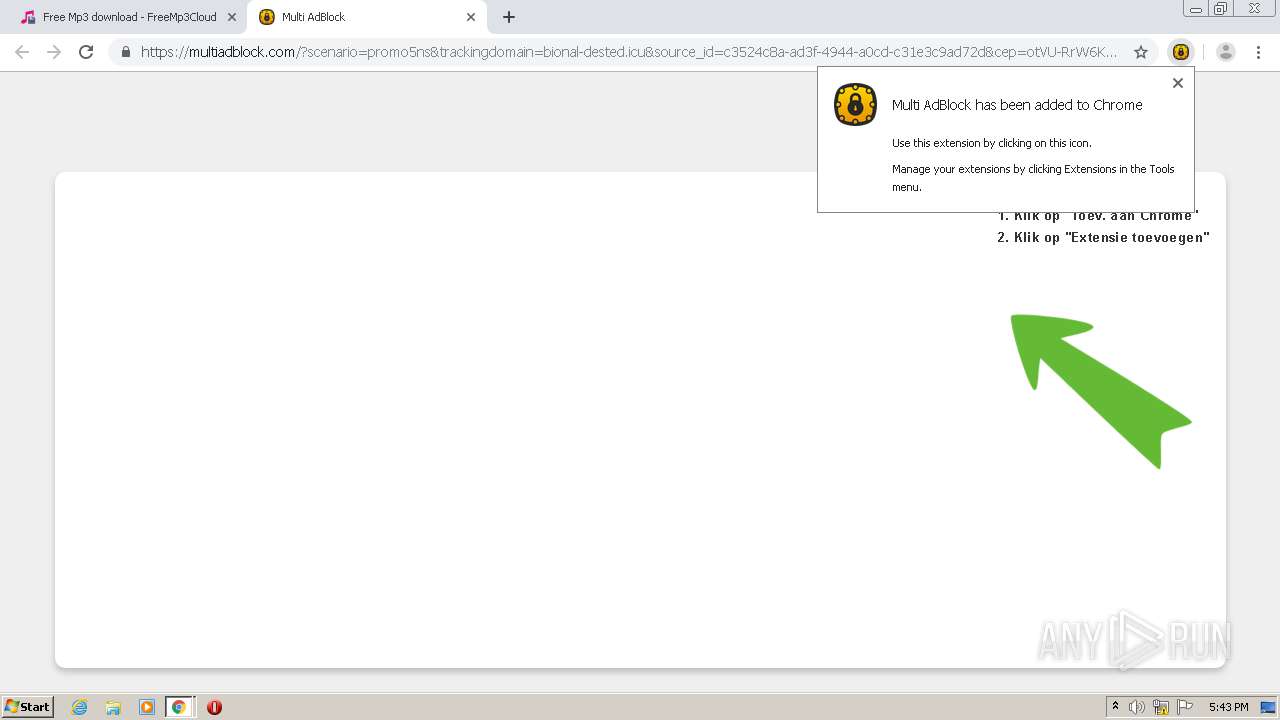
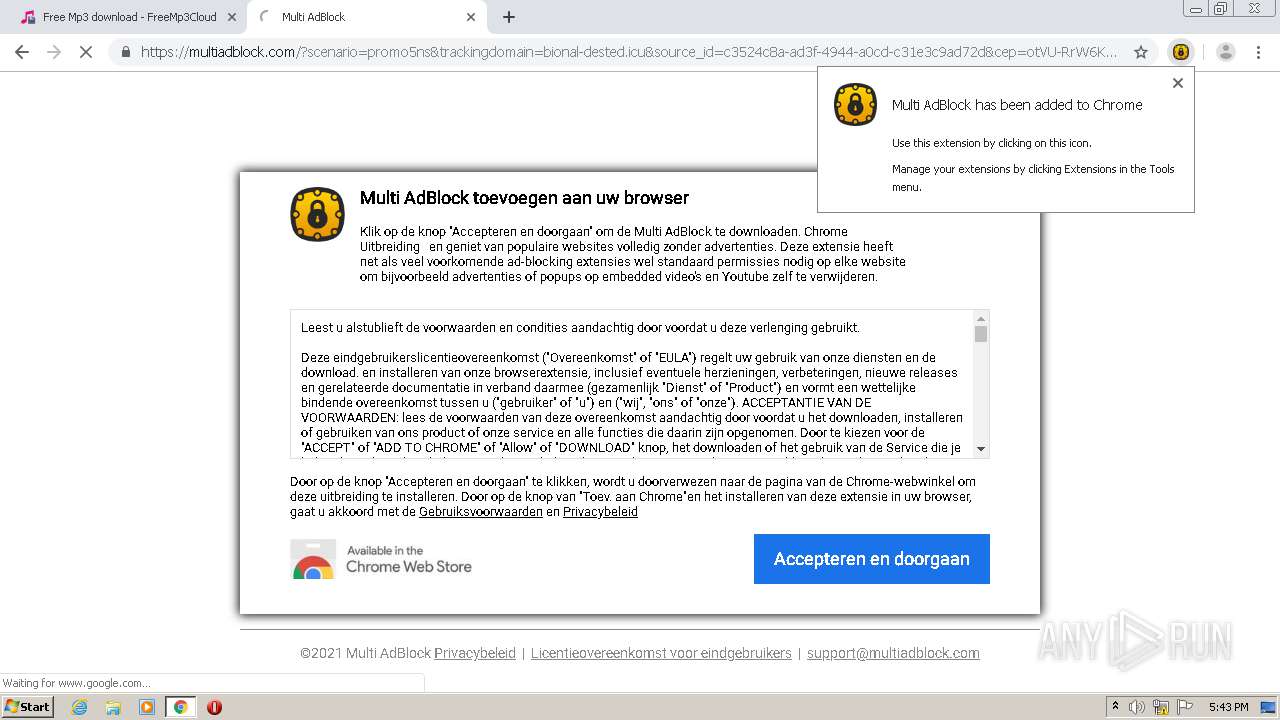
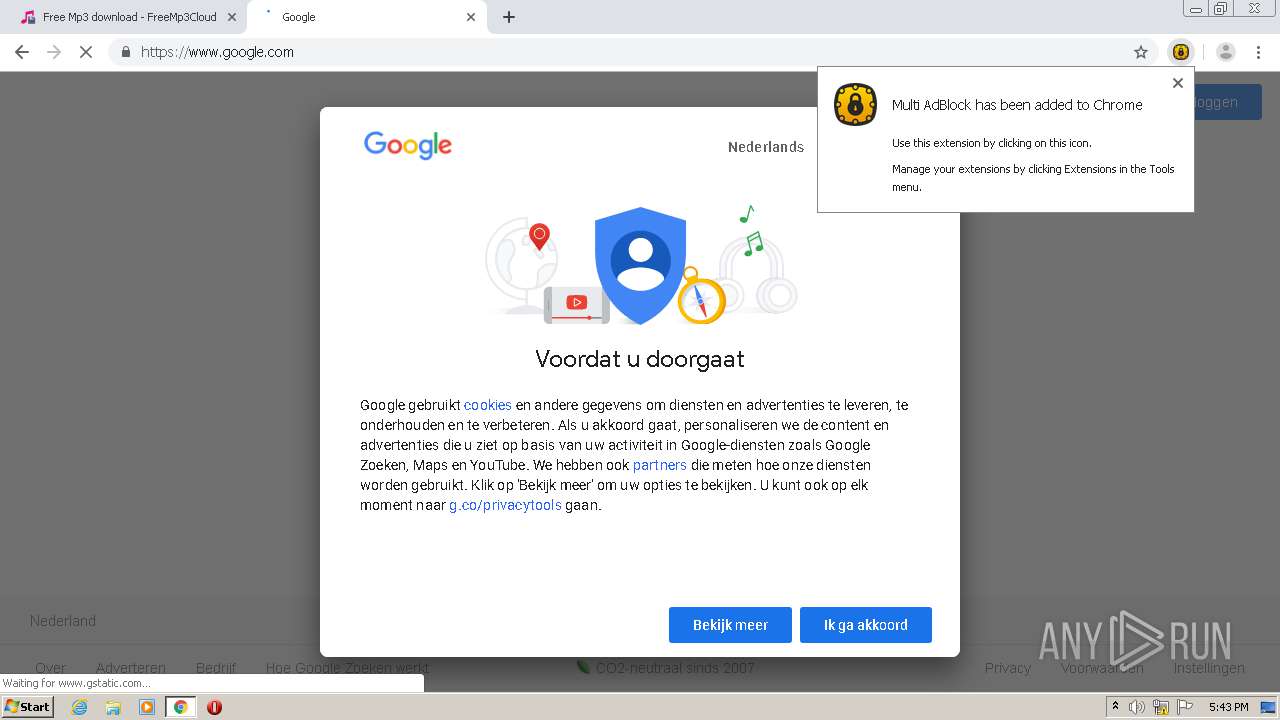
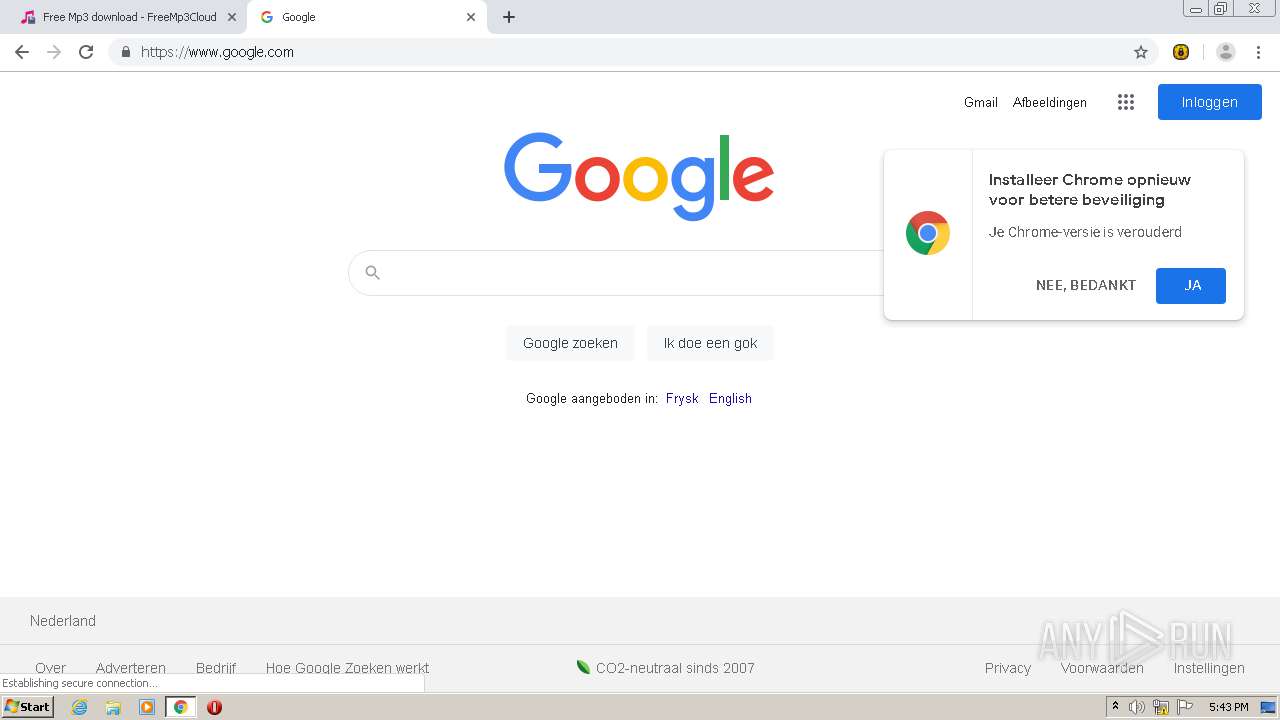
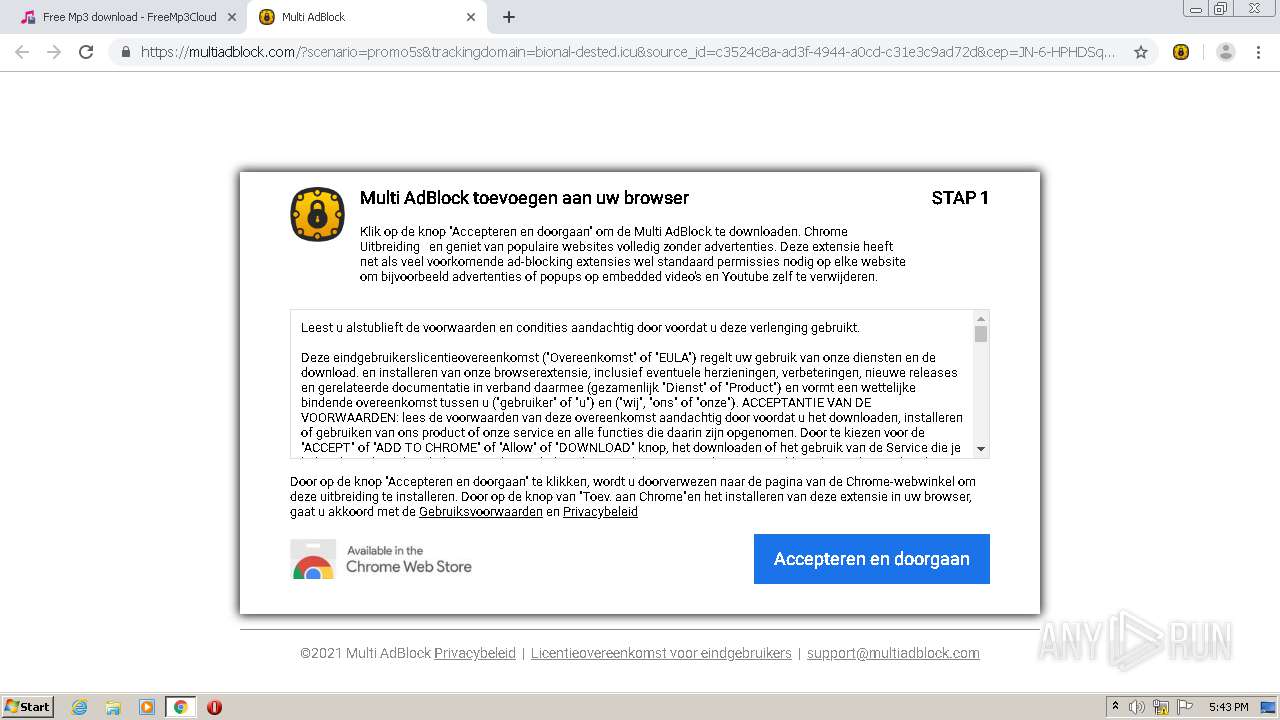
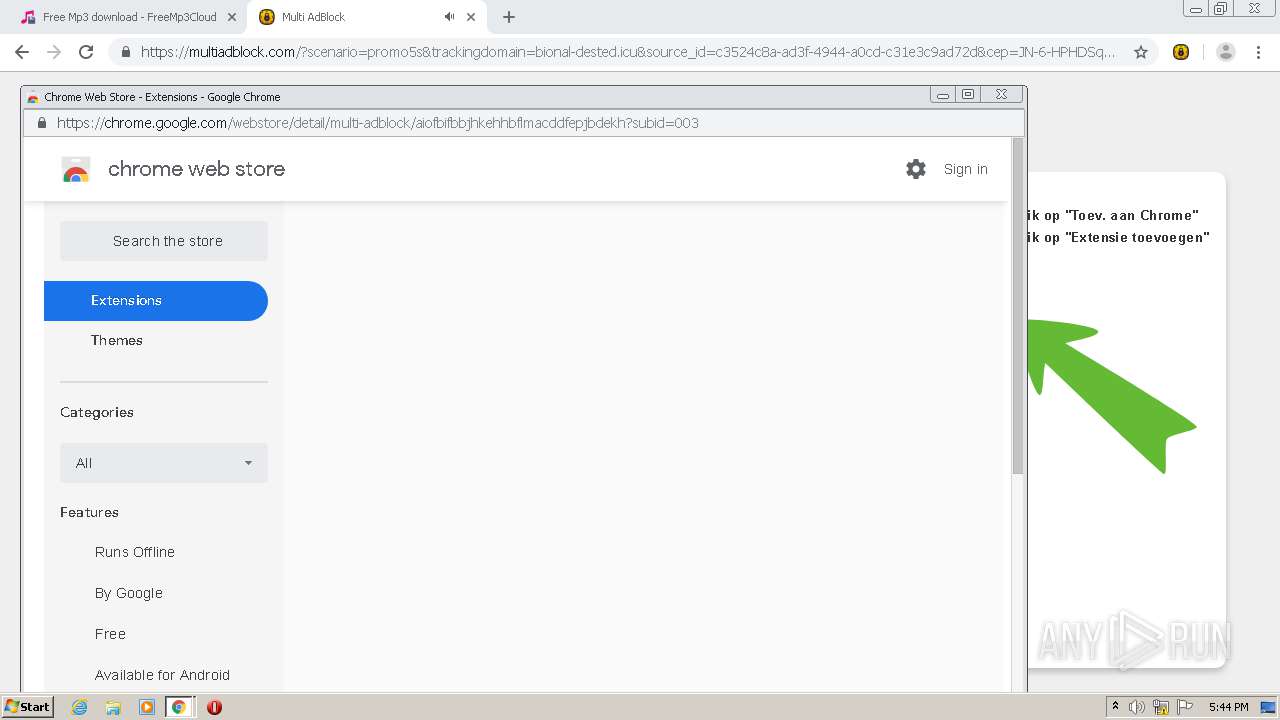
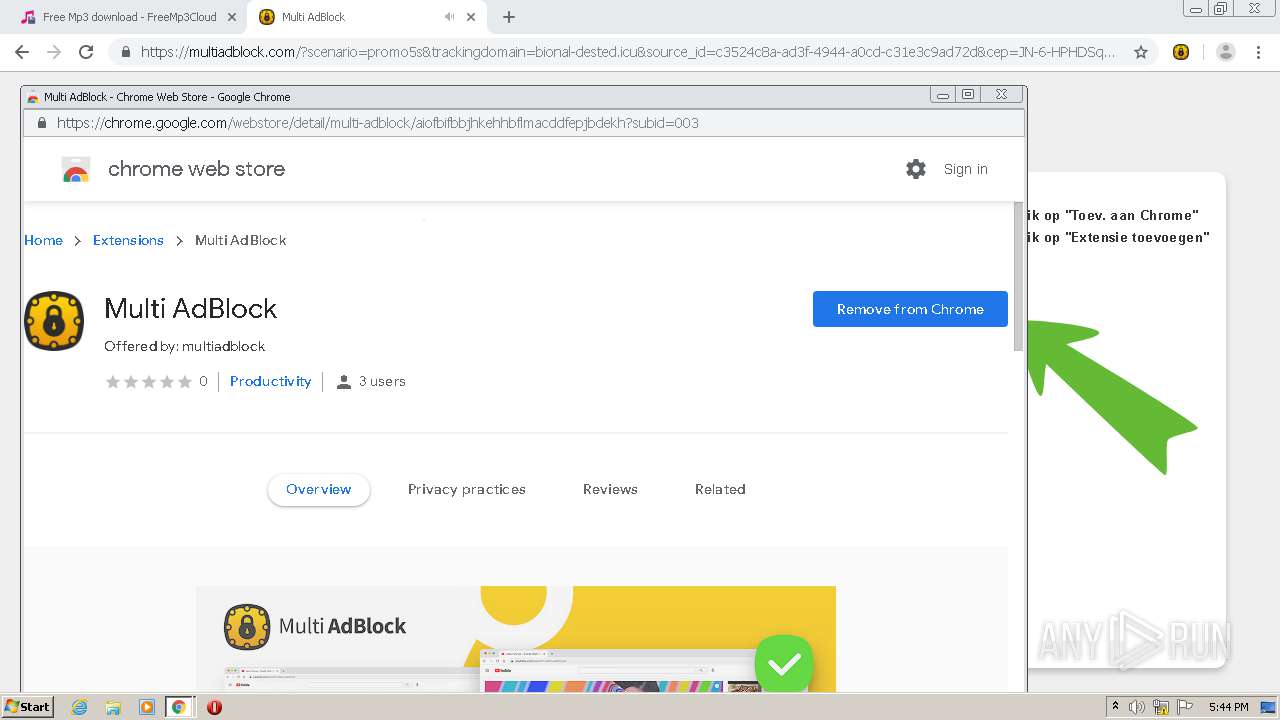
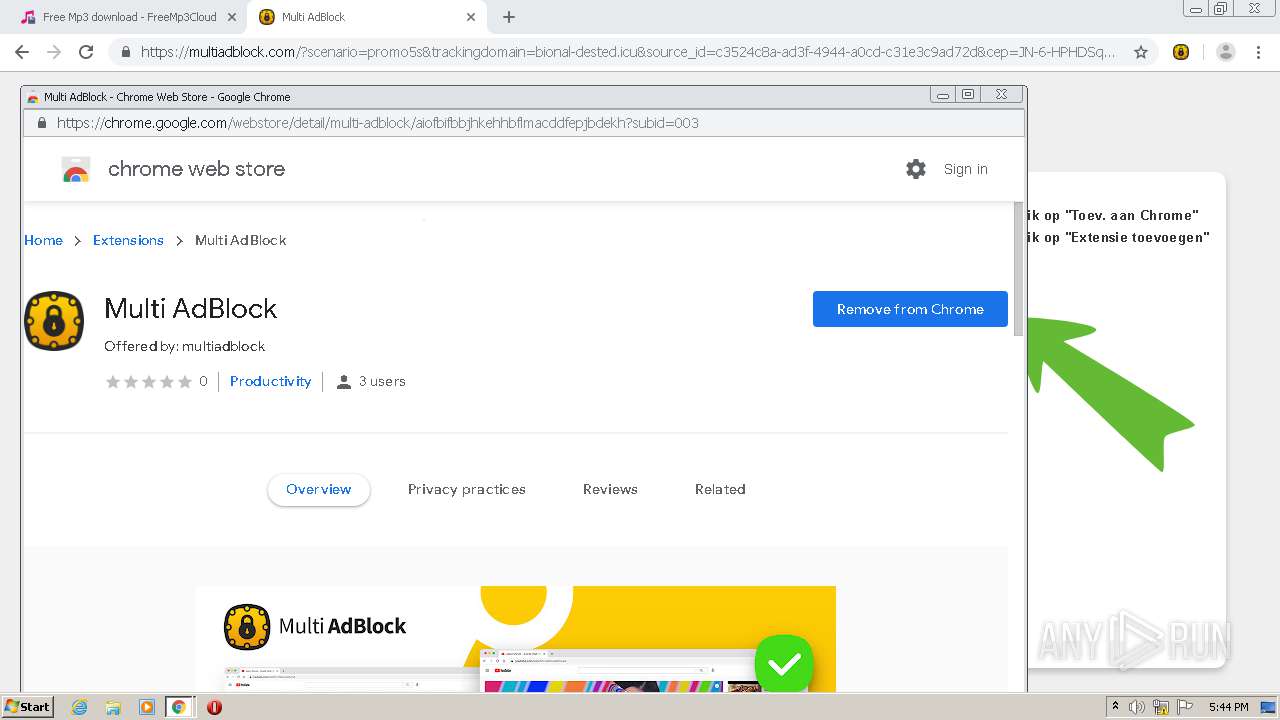
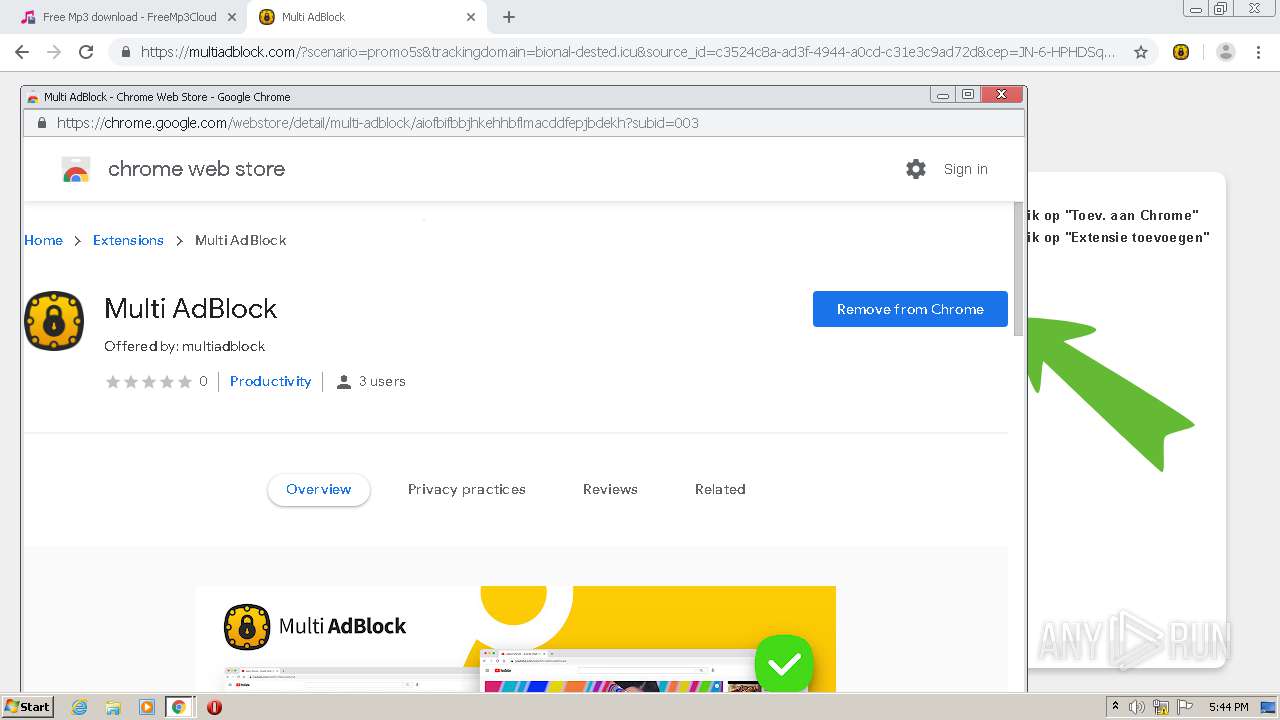
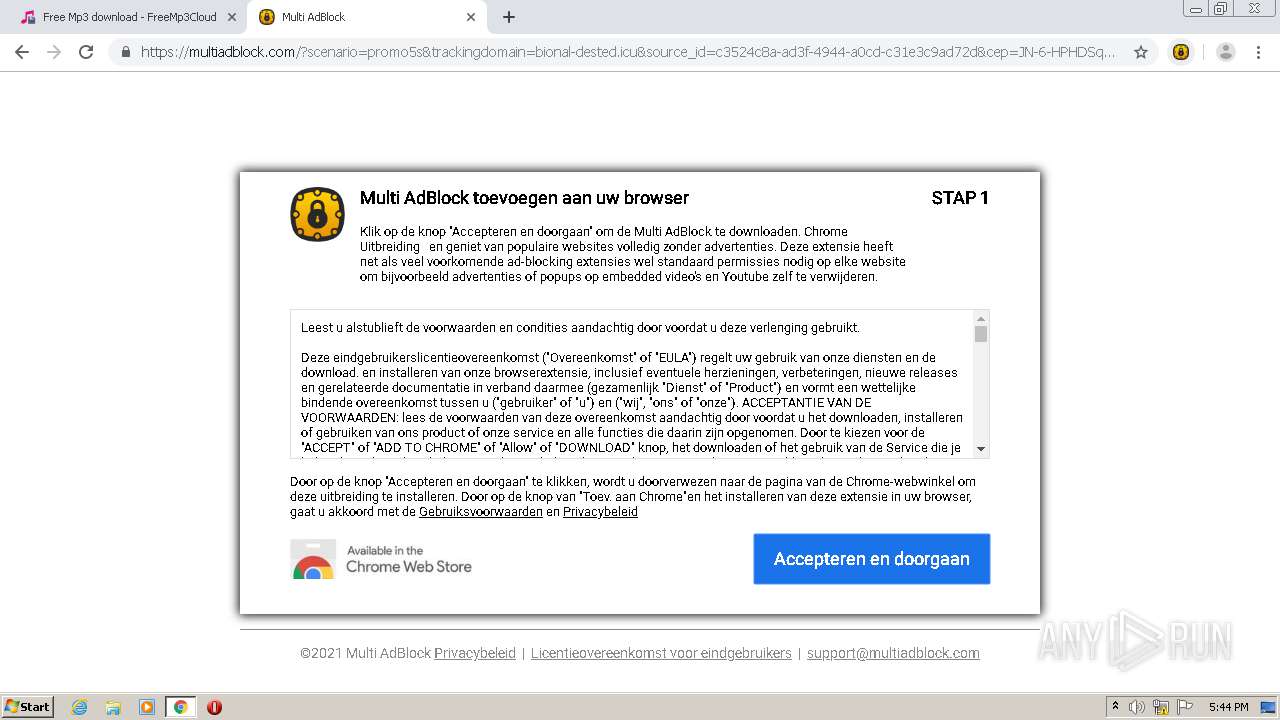
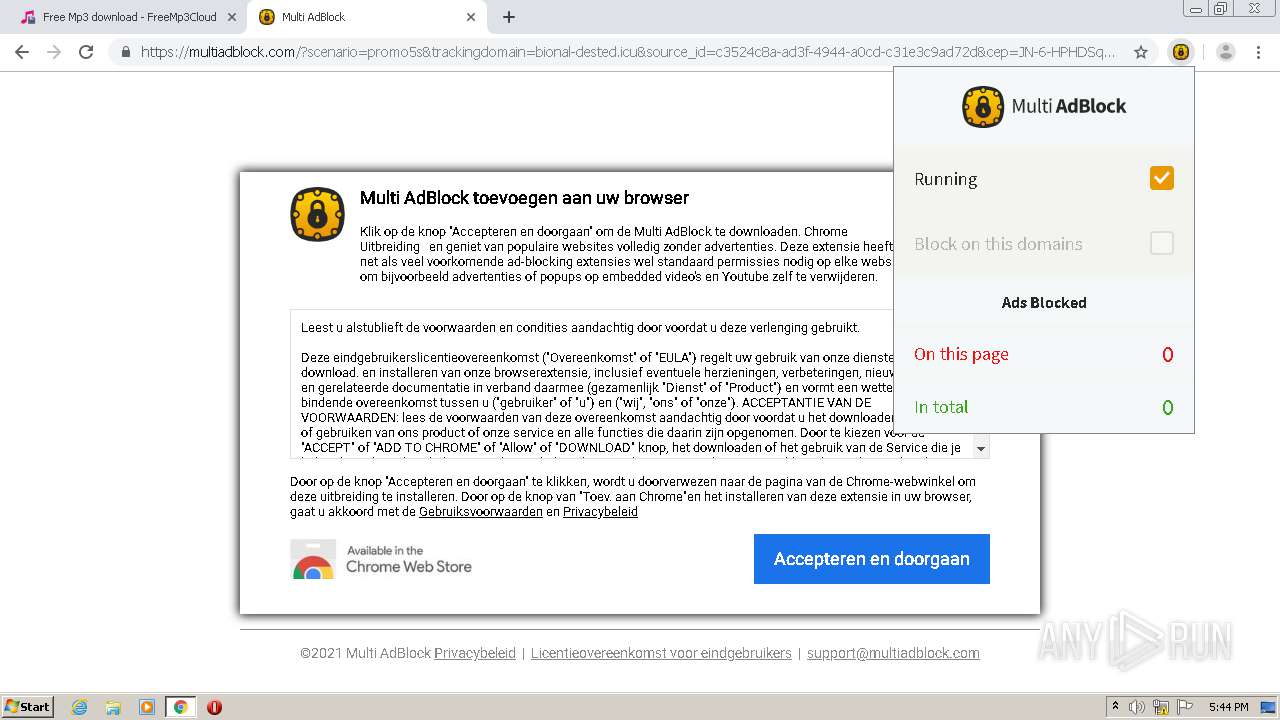
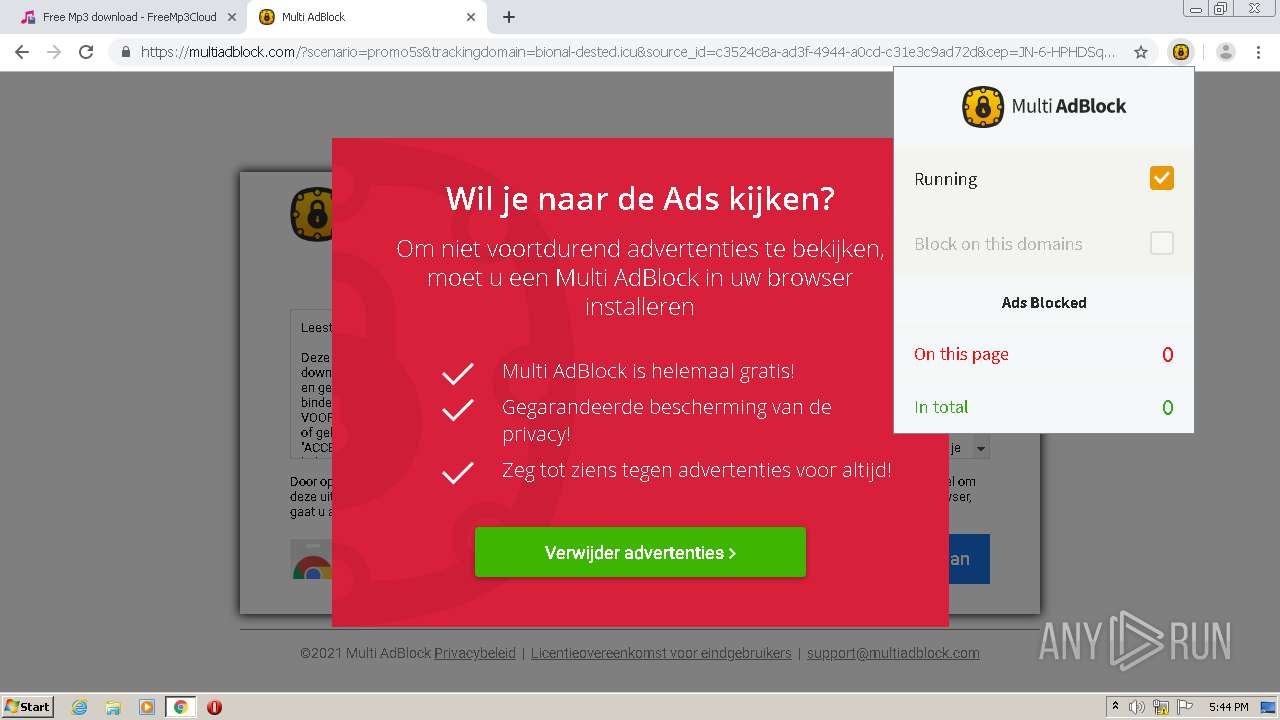
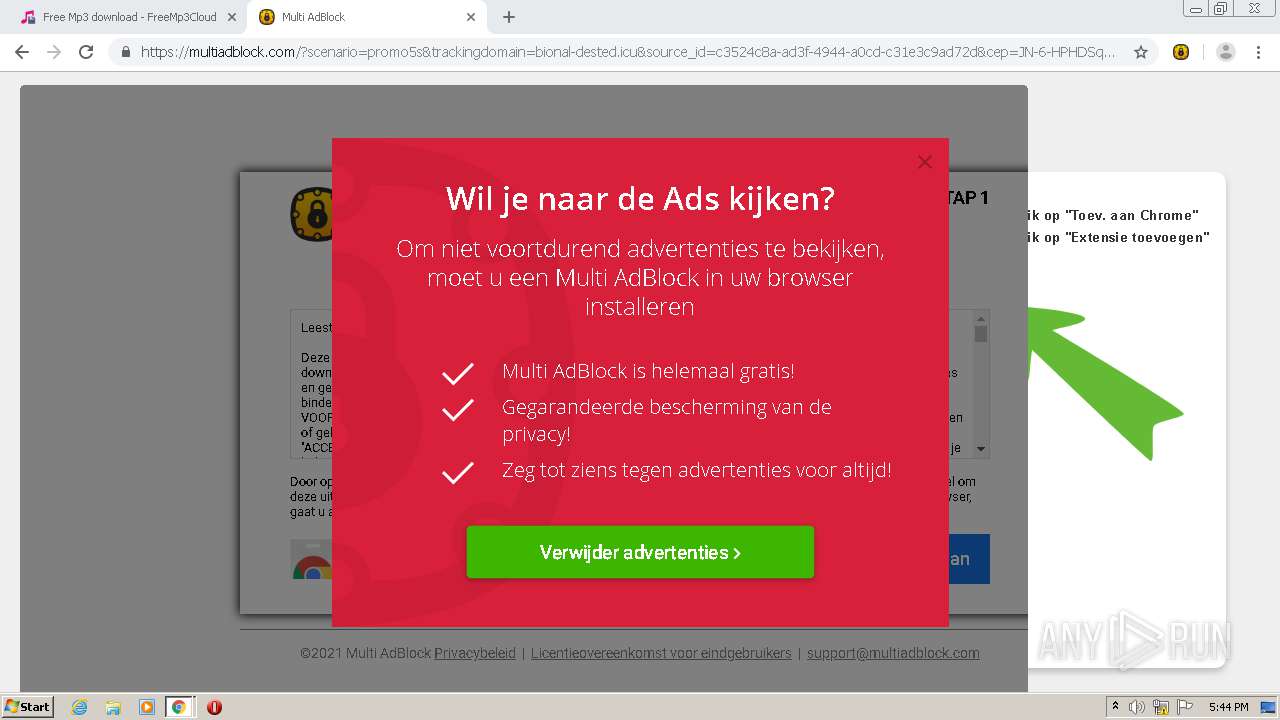
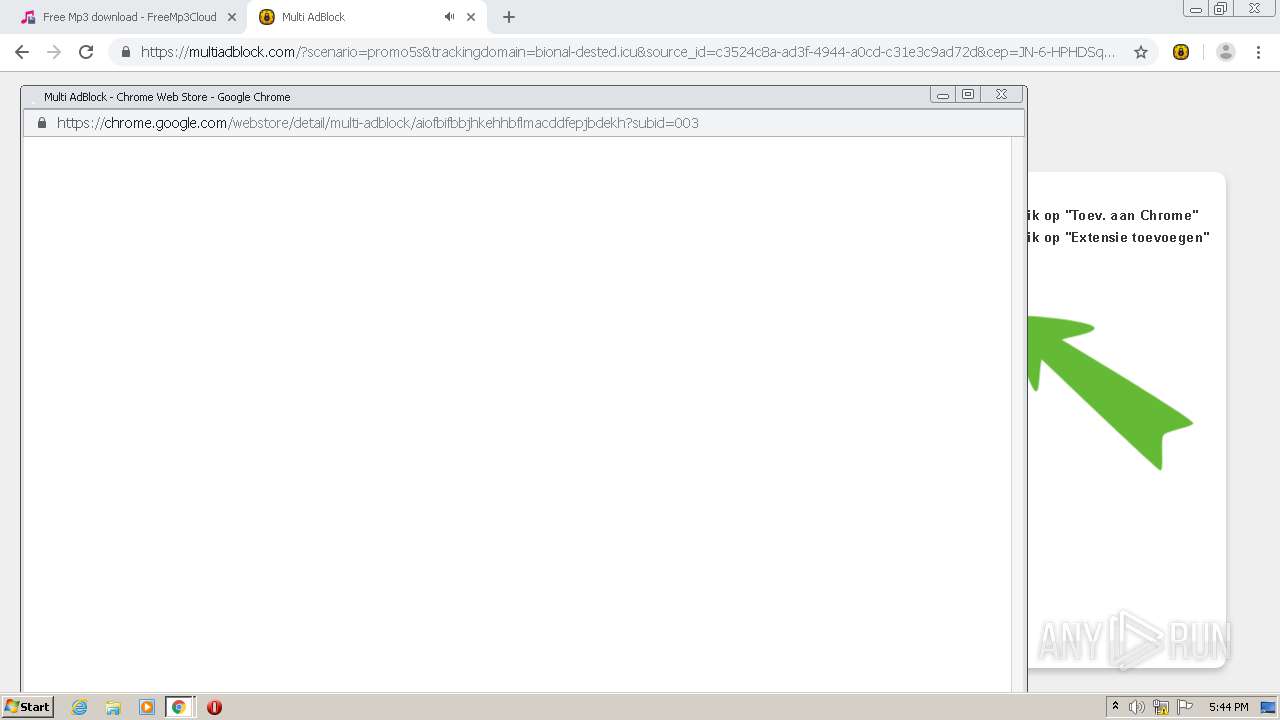
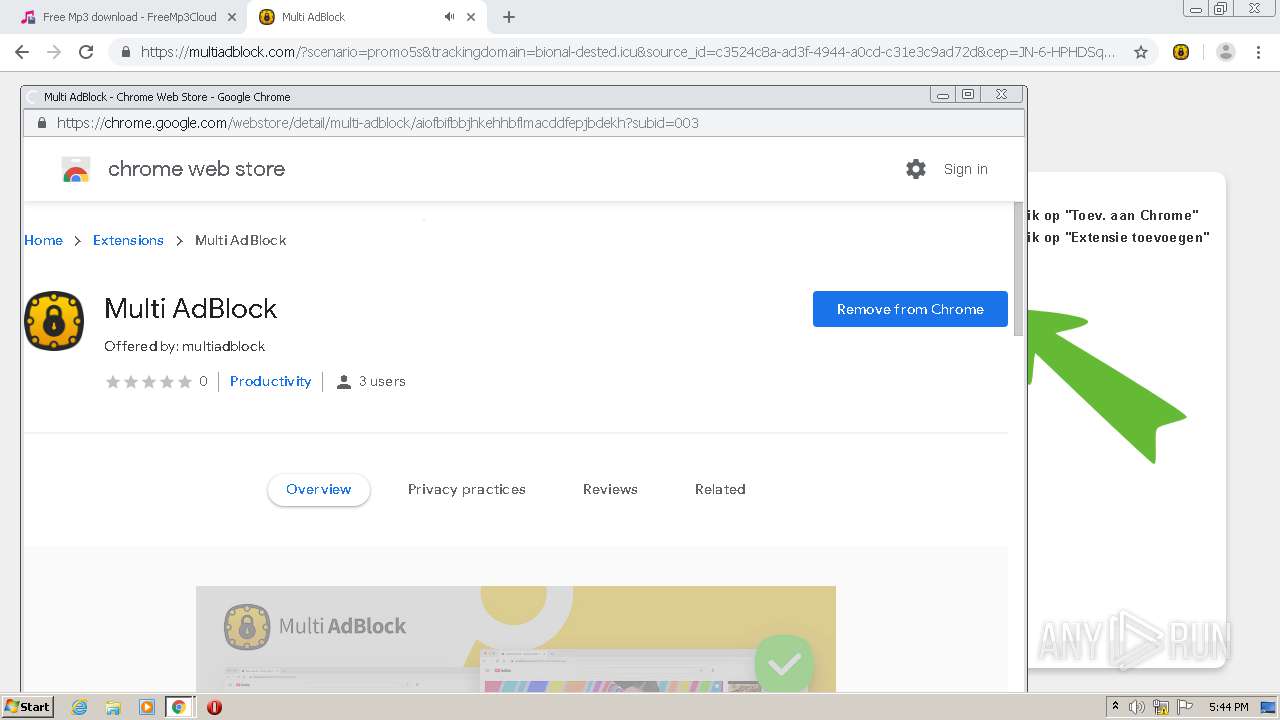
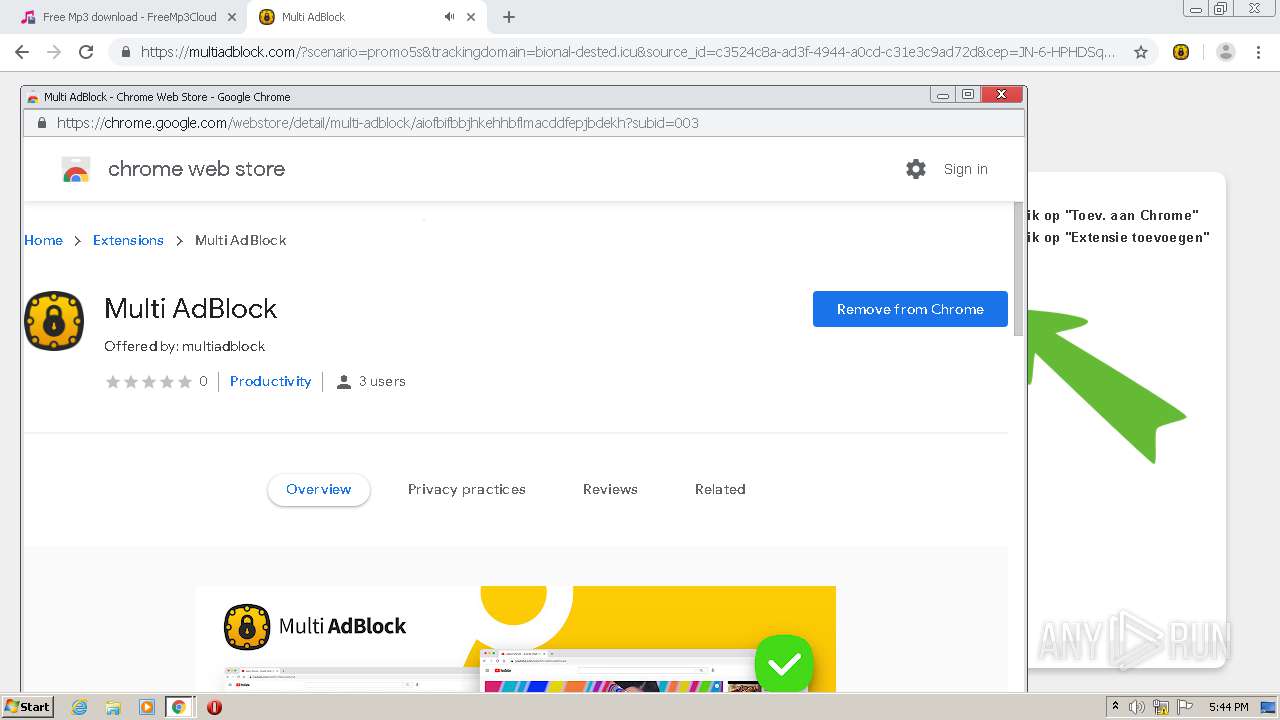
Modifies files in Chrome extension folder
- chrome.exe (PID: 2964)
Drops a file with a compile date too recent
- vlc-3.0.12-win32.exe (PID: 632)
Starts application with an unusual extension
- vlc-3.0.12-win32.exe (PID: 632)
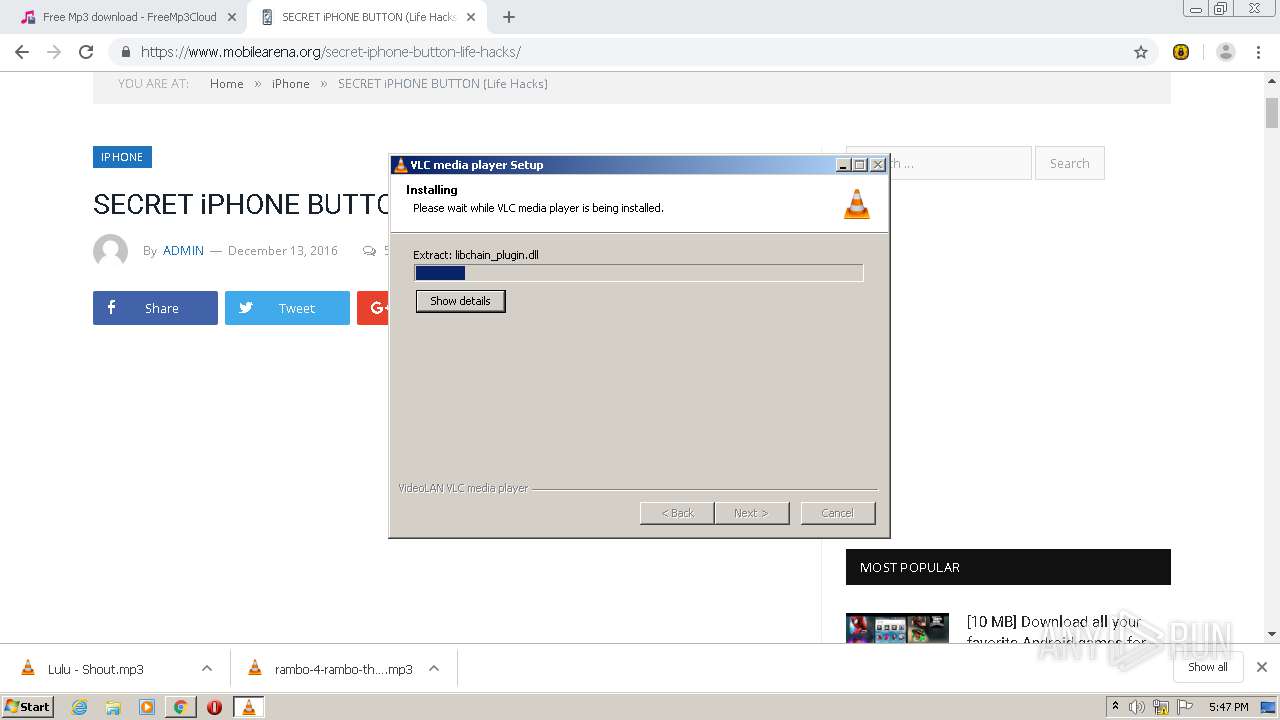
Creates files in the program directory
- vlc-cache-gen.exe (PID: 3836)
- vlc-3.0.12-win32.exe (PID: 632)
Creates/Modifies COM task schedule object
- vlc-3.0.12-win32.exe (PID: 632)
Executable content was dropped or overwritten
- vlc-3.0.12-win32.exe (PID: 632)
Executed via COM
- explorer.exe (PID: 2736)
Creates a directory in Program Files
- vlc-3.0.12-win32.exe (PID: 632)
Drops a file with too old compile date
- vlc-3.0.12-win32.exe (PID: 632)
Changes default file association
- vlc-3.0.12-win32.exe (PID: 632)
Creates a software uninstall entry
- vlc-3.0.12-win32.exe (PID: 632)
INFO
Reads the hosts file
- chrome.exe (PID: 2780)
- chrome.exe (PID: 2964)
Application launched itself
- chrome.exe (PID: 2964)
Creates files in the user directory
- chrome.exe (PID: 2964)
Dropped object may contain Bitcoin addresses
- vlc-3.0.12-win32.exe (PID: 632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
63
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=240497287874031372 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16211111076990924503 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 632 | "C:\Users\admin\AppData\Local\Temp\vlc-3.0.12-win32.exe" | C:\Users\admin\AppData\Local\Temp\vlc-3.0.12-win32.exe | vlc.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8059407388615246349 --mojo-platform-channel-handle=4388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4323075561702469082 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16499898610653375301 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6852492325727695374 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3764 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10520822376784434970 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10127545253176995318 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1000 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,12534845001336338054,11510577291136385178,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1842957060673738420 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 911
Read events
2 226
Write events
2 594
Delete events
91
Modification events
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2964-13258834962868250 |
Value: 259 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
379
Suspicious files
199
Text files
280
Unknown types
147
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60393313-B94.pma | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\709d4f1c-7d46-4895-a65b-4520cd09db1a.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1d4d09.TMP | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1d4ede.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
120
DNS requests
66
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
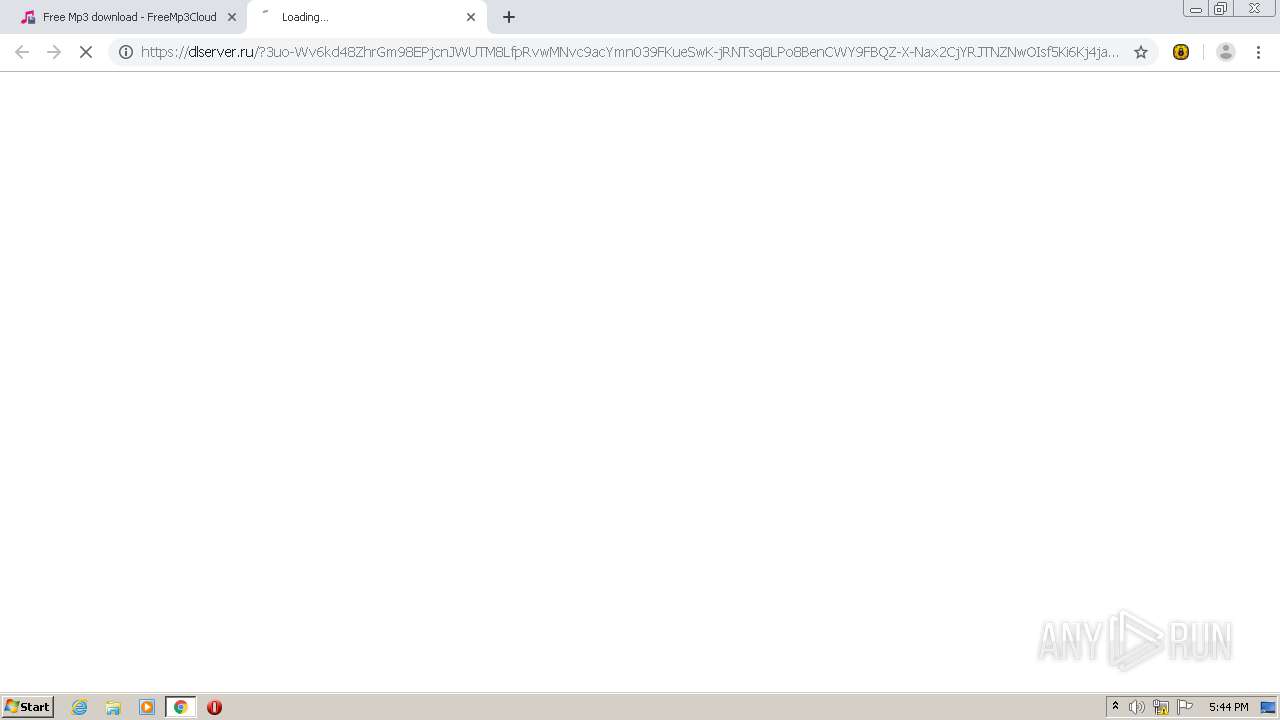
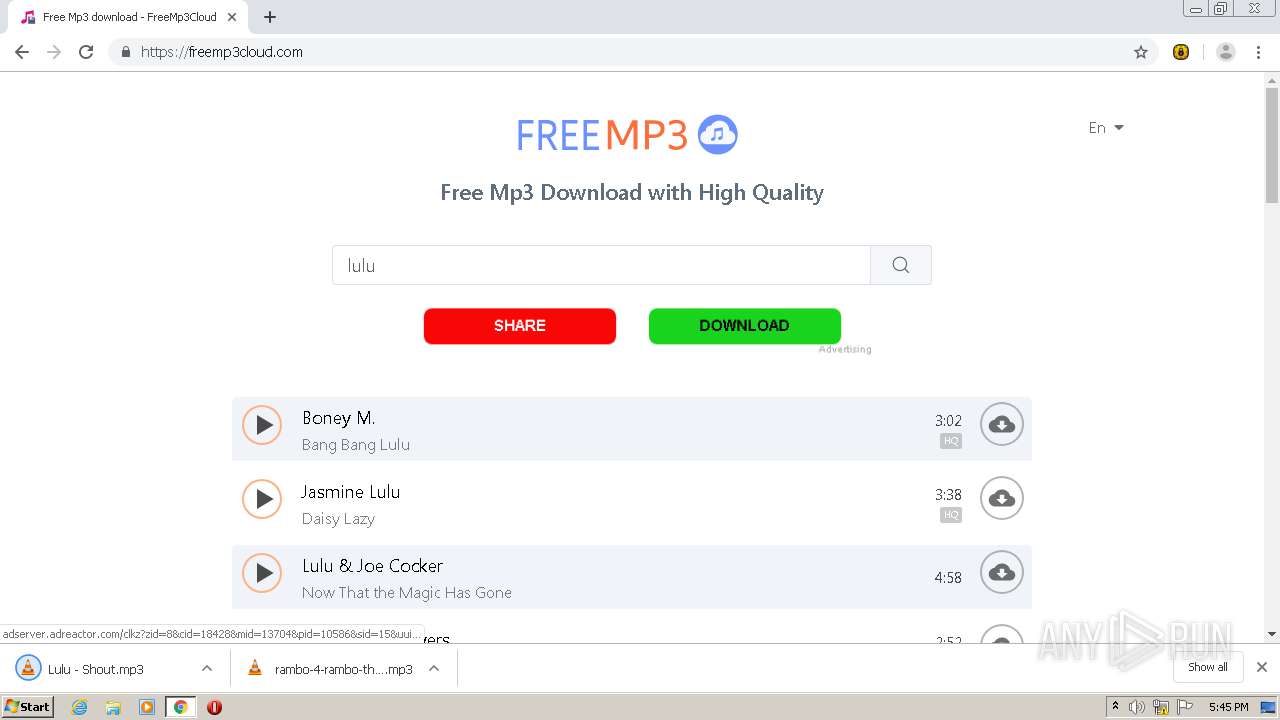
2780 | chrome.exe | GET | 302 | 46.166.179.121:80 | http://adserver.adreactor.com/clkz?zid=8&cid=22731&mid=14190&pid=10586&sid=15&uuid=e9c750837edc47a39d46db1340762c66&ip=85.203.44.27&default=false&random=16582145×tamp=20210226124313&test=false&resolution=1280x620&referrer=https%3A%2F%2Ffreemp3cloud.com%2F&redirect=https%3A%2F%2Fconityles-angths.com%2F21b22b56-30f7-4951-b6ae-5a67d1b78b05%3Fclickid%3De9c750837edc47a39d46db1340762c66-14190 | NL | — | — | suspicious |
2780 | chrome.exe | GET | 302 | 46.166.179.121:80 | http://adserver.adreactor.com/clkz?zid=8&cid=22731&mid=14190&pid=10586&sid=15&uuid=e9c750837edc47a39d46db1340762c66&ip=85.203.44.27&default=false&random=16582145×tamp=20210226124313&test=false&resolution=1280x620&referrer=https%3A%2F%2Ffreemp3cloud.com%2F&redirect=https%3A%2F%2Fconityles-angths.com%2F21b22b56-30f7-4951-b6ae-5a67d1b78b05%3Fclickid%3De9c750837edc47a39d46db1340762c66-14190 | NL | — | — | suspicious |
2780 | chrome.exe | GET | 302 | 46.166.179.121:80 | http://adserver.adreactor.com/clkz?zid=8&cid=18428&mid=13704&pid=10586&sid=15&uuid=e9c750837edc47a39d46db1340762c66&ip=85.203.44.27&default=false&random=26704061×tamp=20210226124524&test=false&resolution=1280x587&referrer=https%3A%2F%2Ffreemp3cloud.com%2F&redirect=https%3A%2F%2Fwww.mobilearena.org%2F%3Futm_source%3Ds-10586%26utm_medium%3Dbanner%26utm_campaign%3Dc-18428 | NL | — | — | suspicious |
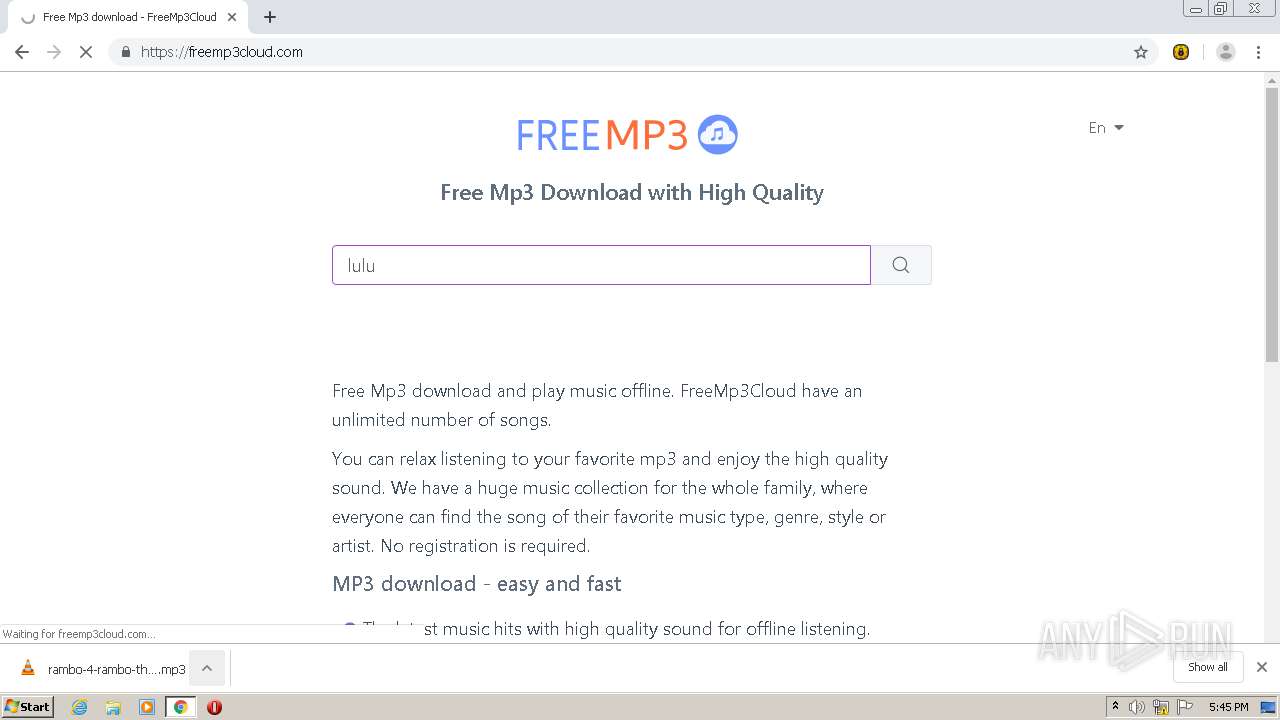
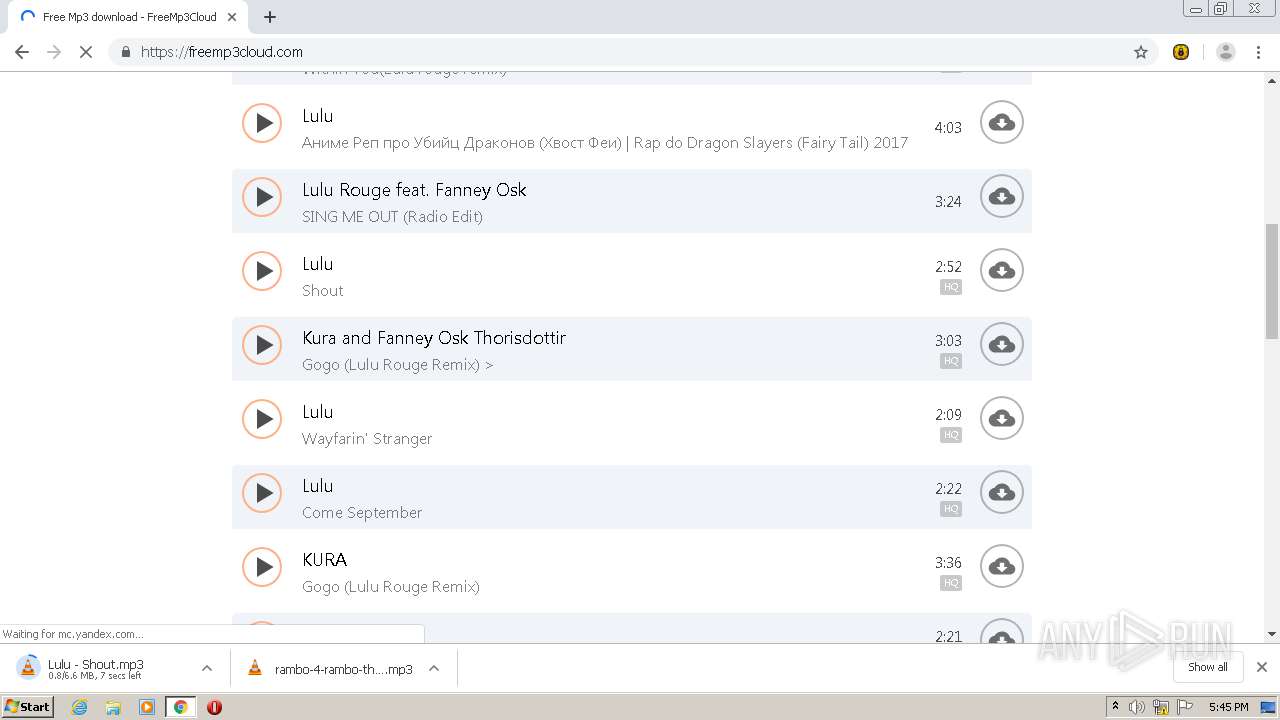
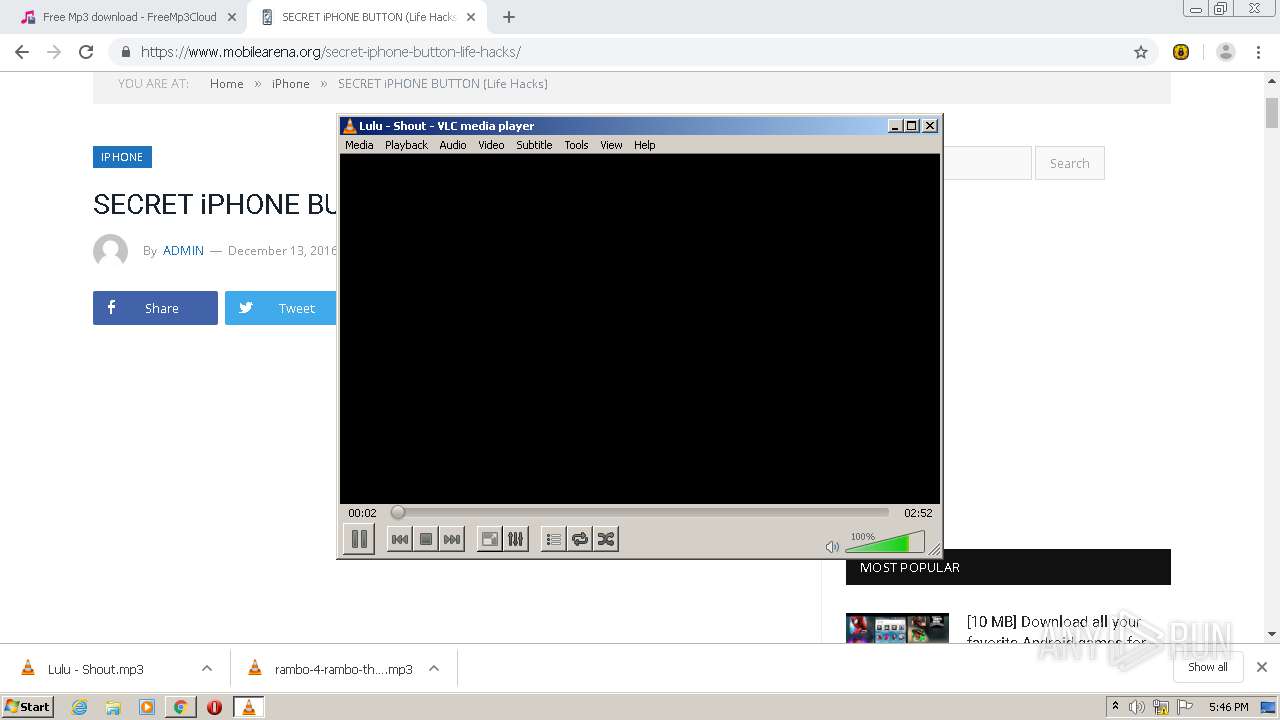
3380 | vlc.exe | GET | — | 142.250.185.164:80 | http://www.google.com/search?q=Lulu+Shout+cover&tbm=isch | US | — | — | malicious |
3380 | vlc.exe | GET | 200 | 213.36.253.2:80 | http://mb.videolan.org/ws/2/release/55bfeccb-40d7-49fd-8fe0-58c49a5cb74c | FR | xml | 826 b | malicious |
3380 | vlc.exe | GET | 200 | 213.36.253.2:80 | http://mb.videolan.org/ws/2/recording/?query=artist%3A%22Lulu%22%20AND%20recording%3A%22Shout%22 | FR | xml | 66.5 Kb | malicious |
2780 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.7 Kb | whitelisted |
3380 | vlc.exe | GET | 301 | 142.250.186.110:80 | http://images.google.com/search?q=Lulu+Shout+cover&tbm=isch | US | html | 257 b | whitelisted |
3380 | vlc.exe | GET | 200 | 142.250.185.164:80 | http://www.google.com/search?q=Lulu+Shout+cover&tbm=isch | US | html | 27.1 Kb | malicious |
3380 | vlc.exe | GET | 200 | 213.36.253.2:80 | http://mb.videolan.org/ws/2/release/55bfeccb-40d7-49fd-8fe0-58c49a5cb74c | FR | xml | 826 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2780 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 142.250.185.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2780 | chrome.exe | 93.158.134.119:443 | mc.yandex.com | YANDEX LLC | RU | whitelisted |
2780 | chrome.exe | 142.250.186.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 172.67.132.238:443 | freemp3cloud.com | — | US | suspicious |
2780 | chrome.exe | 46.166.179.121:443 | adserver.adreactor.com | NForce Entertainment B.V. | NL | suspicious |
2780 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2780 | chrome.exe | 46.166.179.118:443 | ads.a-static.com | NForce Entertainment B.V. | NL | unknown |
2780 | chrome.exe | 46.166.179.121:80 | adserver.adreactor.com | NForce Entertainment B.V. | NL | suspicious |
2780 | chrome.exe | 18.194.134.212:443 | conityles-angths.com | Amazon.com, Inc. | DE | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
freemp3cloud.com |
| suspicious |
accounts.google.com |
| shared |
mc.yandex.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
adserver.adreactor.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
ads.a-static.com |
| unknown |
conityles-angths.com |
| shared |
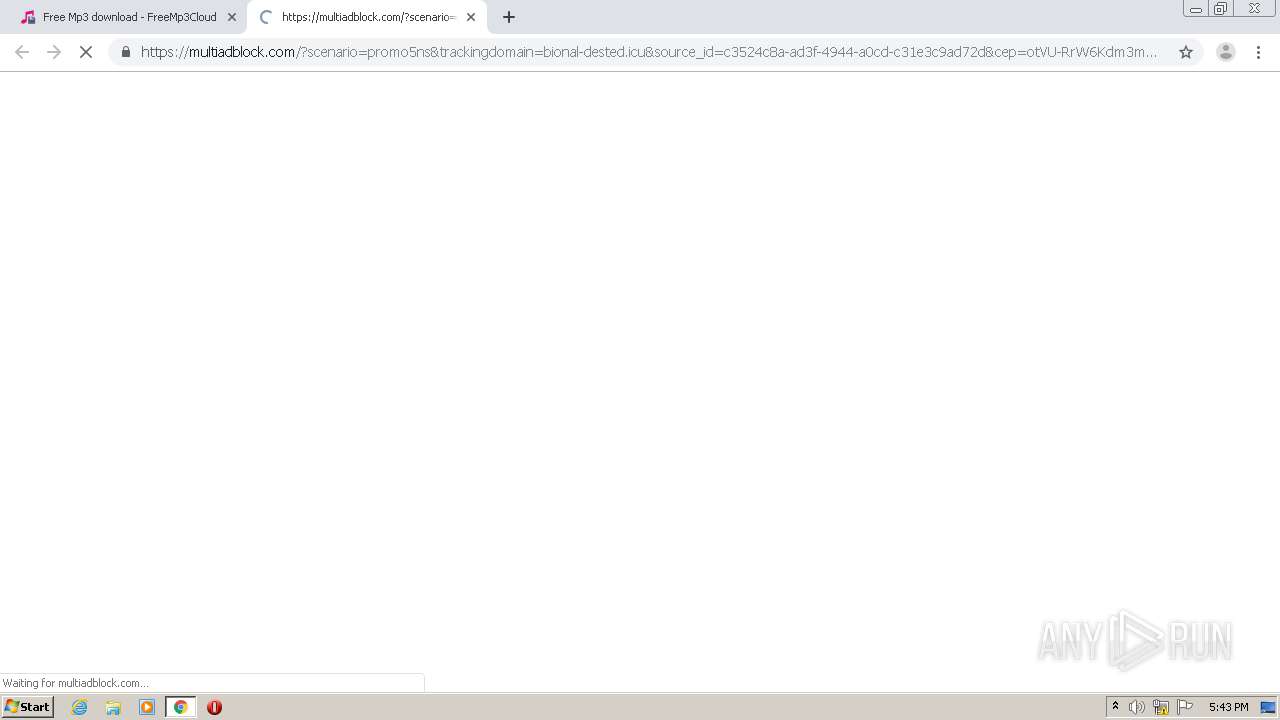
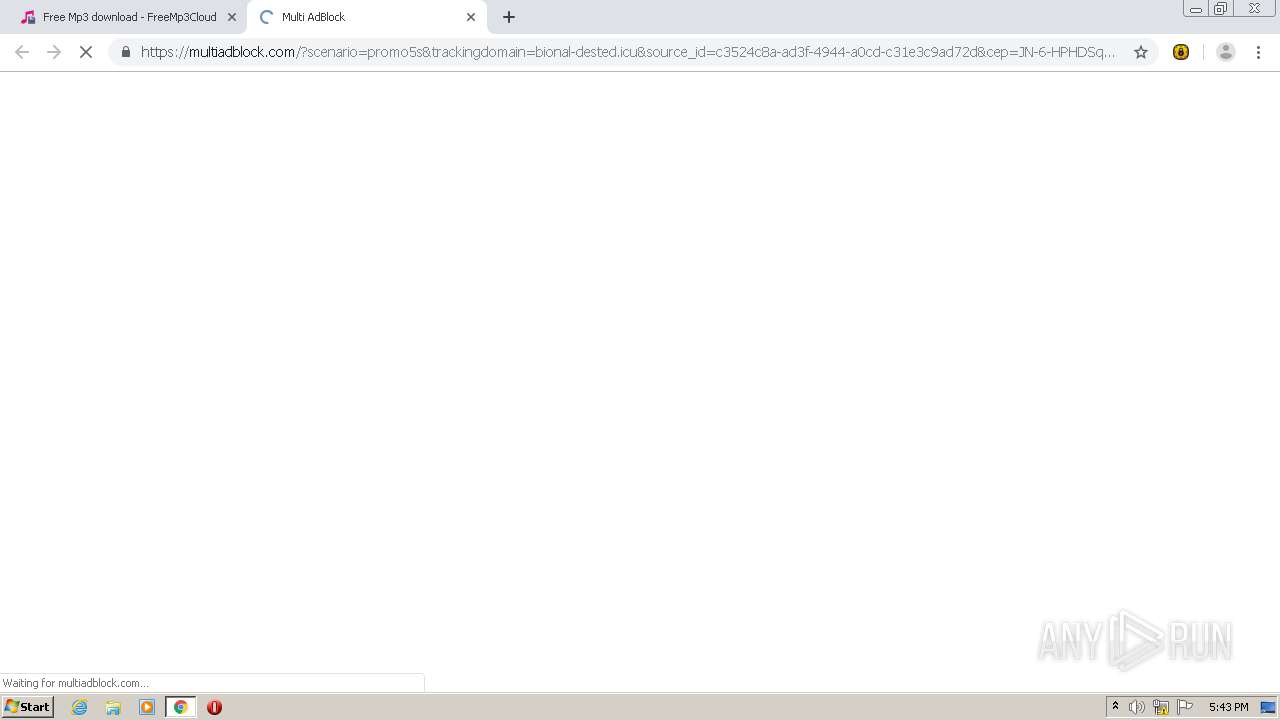
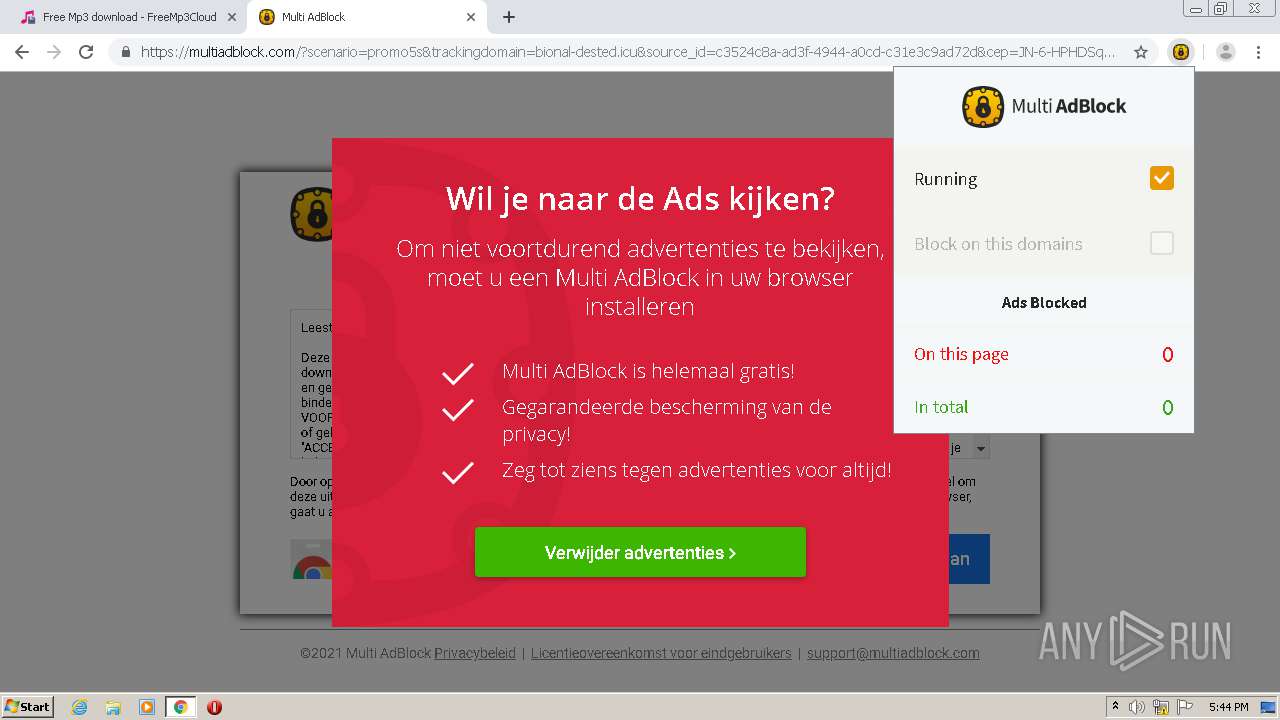
bional-dested.icu |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2780 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
2780 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |
1040 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
Process | Message |
|---|---|
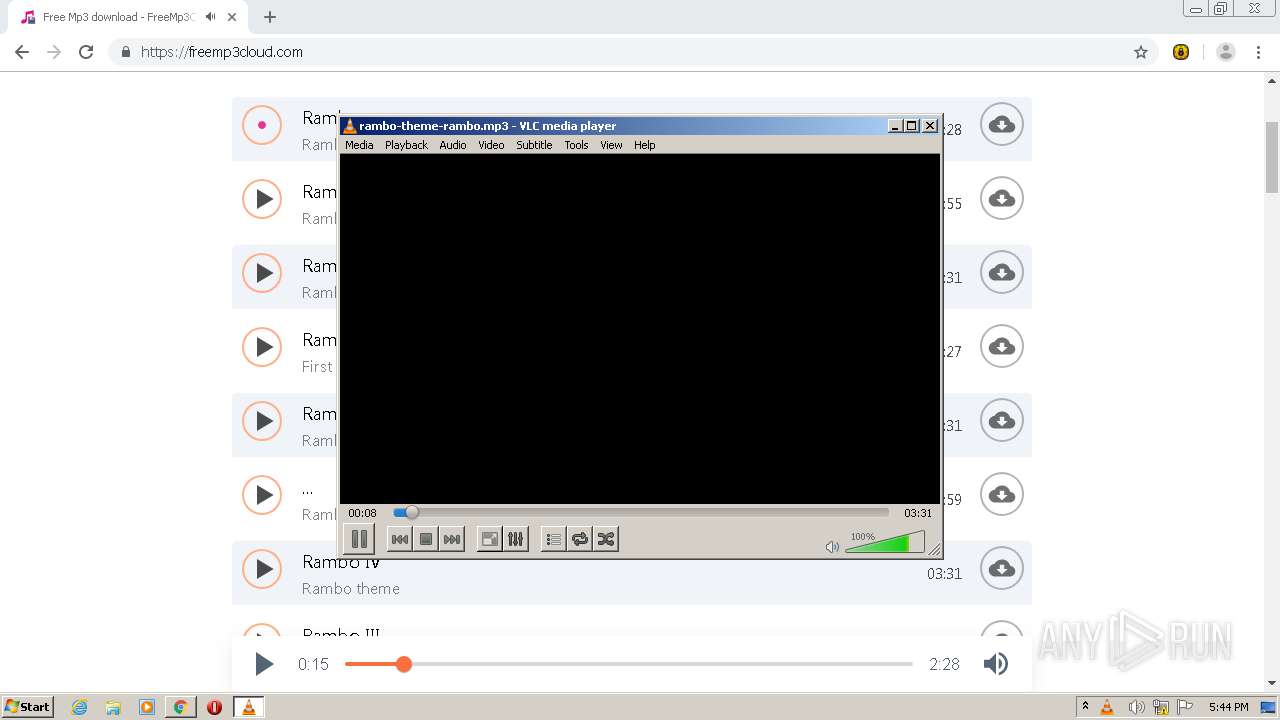
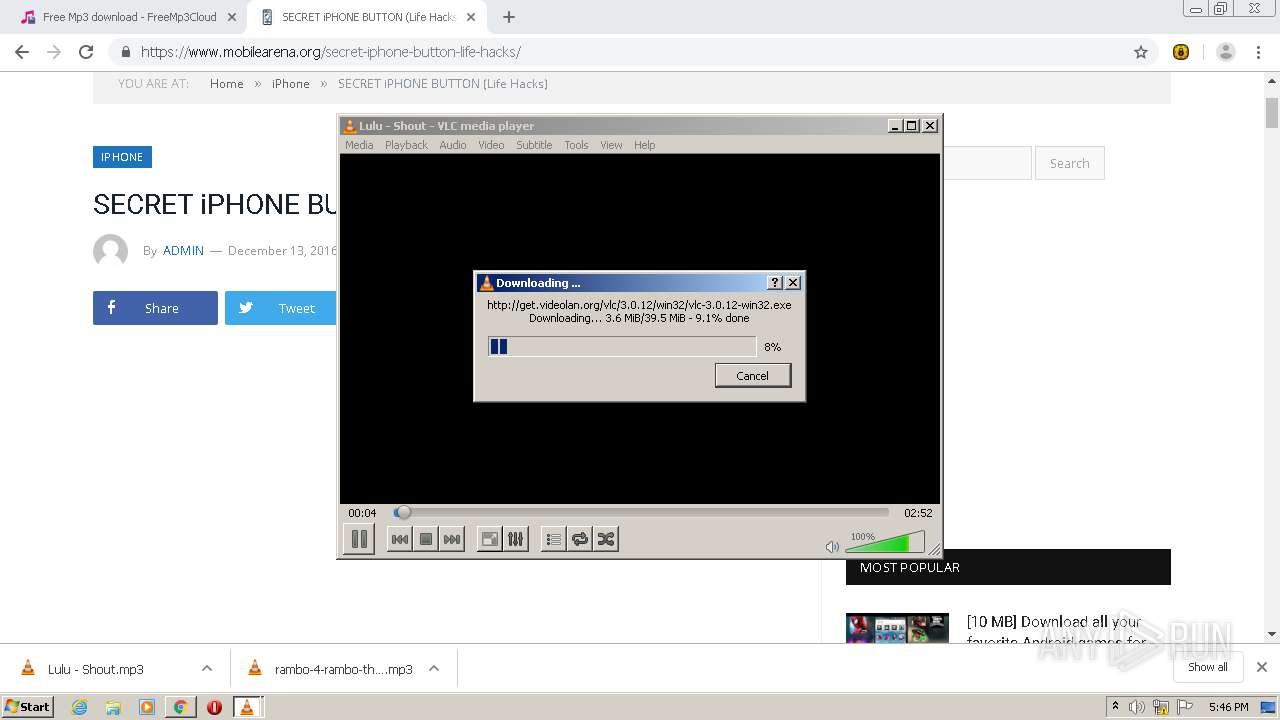
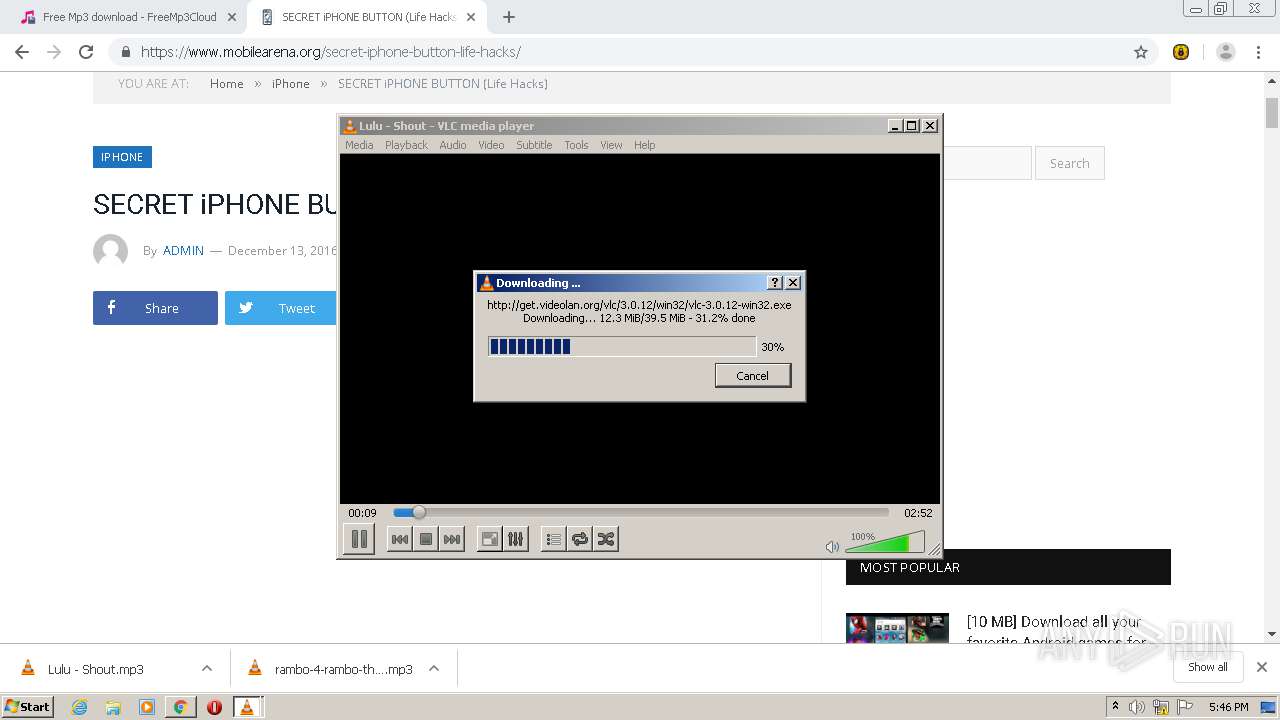
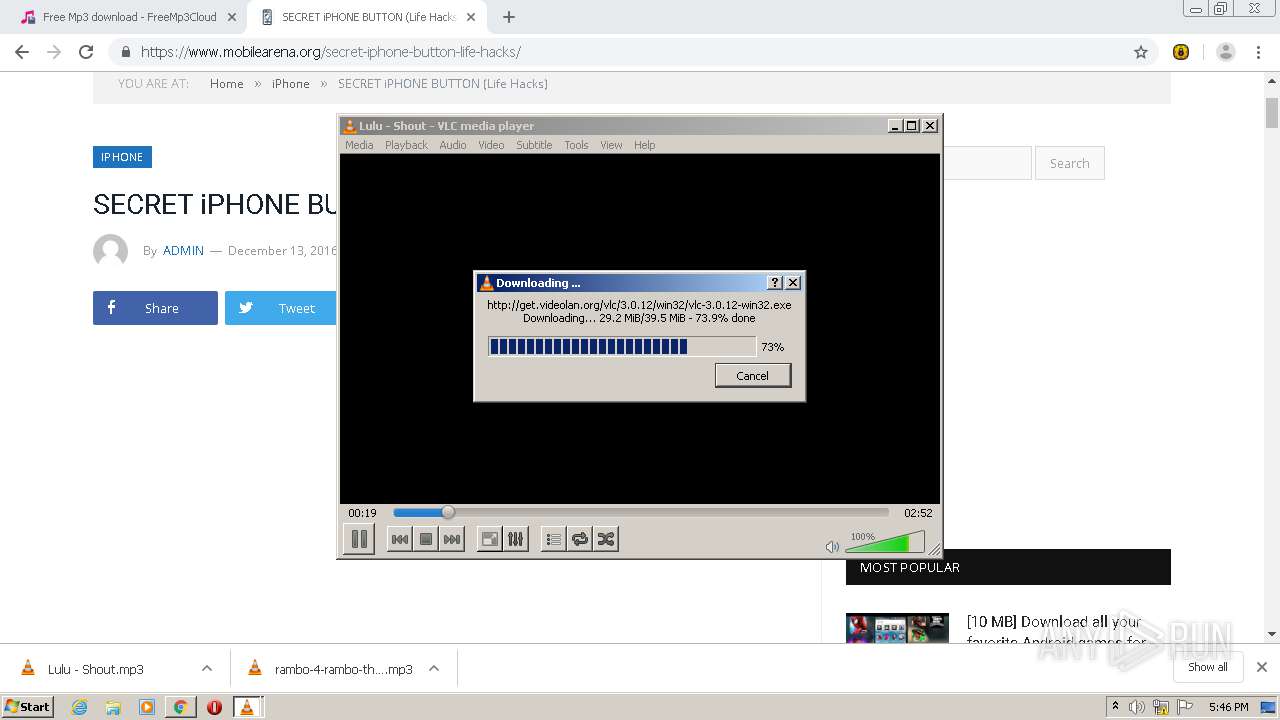
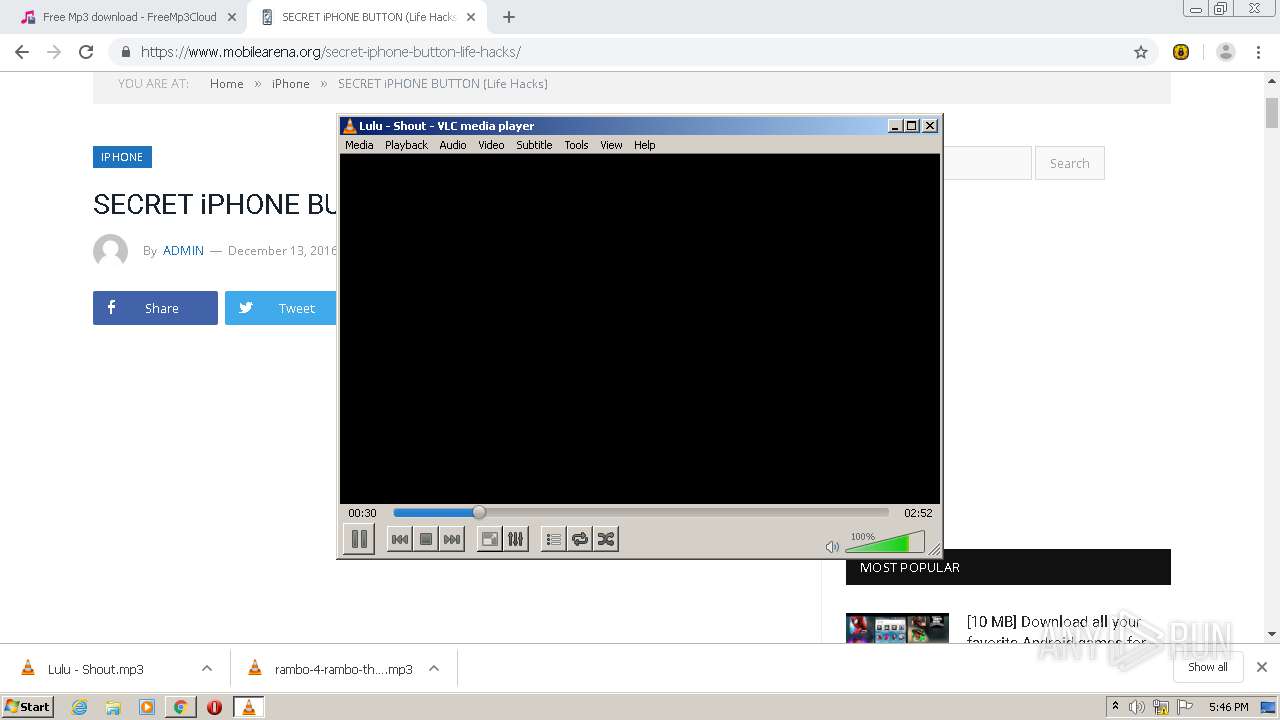
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | mpgatofixed32 audio converter error: libmad error: Huffman data overrun
|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | core libvlc: Status file authenticated
|
vlc.exe | core update download: C:\Users\admin\AppData\Local\Temp\vlc-3.0.12-win32.exe authenticated
|
vlc-cache-gen.exe | main libvlc debug: VLC media player - 3.0.12 Vetinari
|
vlc-cache-gen.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc-cache-gen.exe | main libvlc debug: revision 3.0.12-0-gd590d61de4
|