| File name: | DCRatBuild.exe |
| Full analysis: | https://app.any.run/tasks/e7692a81-e550-4c74-8e2a-fed9d998c6d7 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | December 15, 2024, 18:20:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 332D70EC07F0AD63CEBEACEF8ABF0580 |
| SHA1: | B5315B0A19E638AC31CF441C7A7F500F119ADA55 |
| SHA256: | E77BD7804AD9349FF2B1BDA6C4772CE3C1FC6E7DF4F86D353CB3B11A94207594 |
| SSDEEP: | 12288:VWjGLA4uDgDZrLWkzDNhCa287MochrSvUJZVVVVVVVVVAtVVVUvPIwQZJFFhZbj+:HZPrK87M5rSv0lvPZQXjxtbl1K |
MALICIOUS
UAC/LUA settings modification
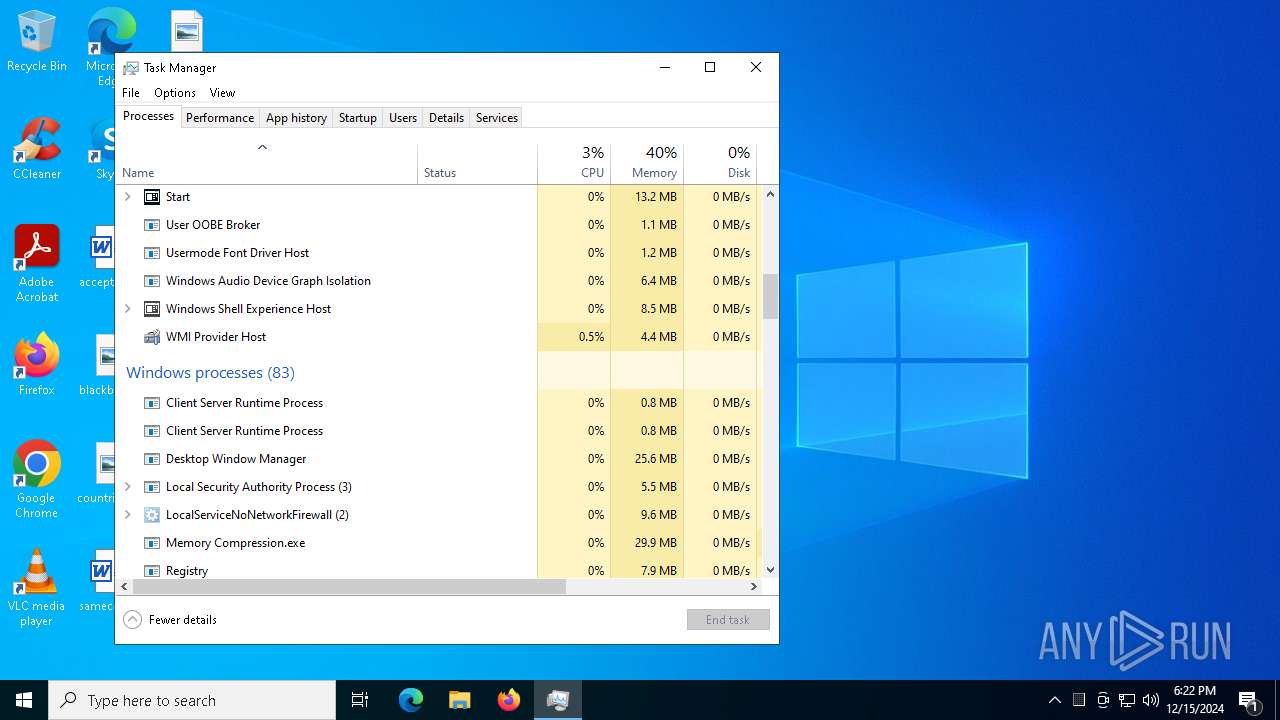
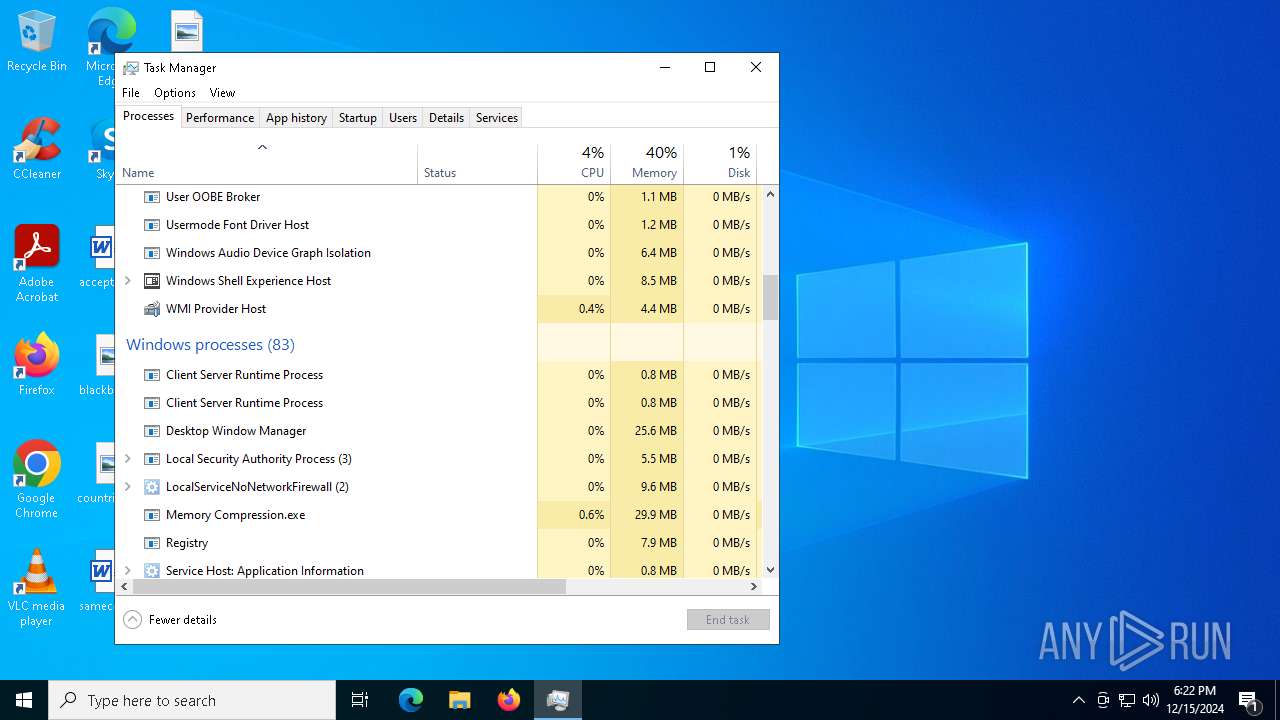
- Memory Compression.exe (PID: 6512)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3988)
- wscript.exe (PID: 3984)
Actions looks like stealing of personal data
- Memory Compression.exe (PID: 6512)
DARKCRYSTAL has been detected (SURICATA)
- Memory Compression.exe (PID: 6512)
Connects to the CnC server
- Memory Compression.exe (PID: 6512)
DCRAT has been detected (YARA)
- Memory Compression.exe (PID: 6512)
SUSPICIOUS
Reads security settings of Internet Explorer
- DCRatBuild.exe (PID: 1744)
- ShellExperienceHost.exe (PID: 6884)
- Memory Compression.exe (PID: 6512)
Executable content was dropped or overwritten
- DCRatBuild.exe (PID: 1744)
- Memory Compression.exe (PID: 6512)
Executed via WMI
- schtasks.exe (PID: 7012)
- schtasks.exe (PID: 7048)
- schtasks.exe (PID: 7076)
- schtasks.exe (PID: 7092)
- schtasks.exe (PID: 7116)
- schtasks.exe (PID: 7140)
- schtasks.exe (PID: 6184)
- schtasks.exe (PID: 6192)
- schtasks.exe (PID: 6244)
- schtasks.exe (PID: 512)
- schtasks.exe (PID: 3532)
- schtasks.exe (PID: 5304)
- schtasks.exe (PID: 5604)
- schtasks.exe (PID: 2356)
- schtasks.exe (PID: 5640)
- schtasks.exe (PID: 3724)
- schtasks.exe (PID: 3816)
- schtasks.exe (PID: 5696)
- schtasks.exe (PID: 3420)
- schtasks.exe (PID: 5872)
- schtasks.exe (PID: 5008)
- schtasks.exe (PID: 5588)
- schtasks.exe (PID: 6384)
- schtasks.exe (PID: 4592)
- schtasks.exe (PID: 5236)
- schtasks.exe (PID: 6340)
- schtasks.exe (PID: 6268)
- schtasks.exe (PID: 6600)
- schtasks.exe (PID: 6512)
- schtasks.exe (PID: 6476)
- schtasks.exe (PID: 6428)
- schtasks.exe (PID: 7116)
- schtasks.exe (PID: 6844)
- schtasks.exe (PID: 7016)
- schtasks.exe (PID: 7056)
- schtasks.exe (PID: 7076)
- schtasks.exe (PID: 4872)
- schtasks.exe (PID: 4244)
- schtasks.exe (PID: 2324)
- schtasks.exe (PID: 3724)
- schtasks.exe (PID: 4932)
- schtasks.exe (PID: 3692)
- schtasks.exe (PID: 3984)
- schtasks.exe (PID: 3092)
- schtasks.exe (PID: 5640)
- schtasks.exe (PID: 6904)
- schtasks.exe (PID: 4548)
- schtasks.exe (PID: 6496)
- schtasks.exe (PID: 6184)
- schtasks.exe (PID: 5748)
- schtasks.exe (PID: 5040)
- schtasks.exe (PID: 6276)
- schtasks.exe (PID: 6388)
- schtasks.exe (PID: 4592)
- schtasks.exe (PID: 6384)
- schtasks.exe (PID: 4400)
- schtasks.exe (PID: 5460)
Likely accesses (executes) a file from the Public directory
- schtasks.exe (PID: 5460)
- schtasks.exe (PID: 5040)
- schtasks.exe (PID: 6276)
The process executes VB scripts
- Memory Compression.exe (PID: 6512)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3984)
- wscript.exe (PID: 3988)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 3988)
Reads the date of Windows installation
- Memory Compression.exe (PID: 6512)
Contacting a server suspected of hosting an CnC
- Memory Compression.exe (PID: 6512)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 1344)
- dllhost.exe (PID: 1684)
- smss.exe (PID: 6344)
INFO
Checks supported languages
- DCRatBuild.exe (PID: 1744)
- ShellExperienceHost.exe (PID: 6884)
- Memory Compression.exe (PID: 6512)
- default-browser-agent.exe (PID: 1344)
- dllhost.exe (PID: 1684)
- smss.exe (PID: 6344)
Reads the computer name
- DCRatBuild.exe (PID: 1744)
- ShellExperienceHost.exe (PID: 6884)
- Memory Compression.exe (PID: 6512)
- default-browser-agent.exe (PID: 1344)
- dllhost.exe (PID: 1684)
- smss.exe (PID: 6344)
The sample compiled with english language support
- DCRatBuild.exe (PID: 1744)
- Memory Compression.exe (PID: 6512)
Process checks computer location settings
- DCRatBuild.exe (PID: 1744)
- Memory Compression.exe (PID: 6512)
Drops encrypted VBS script (Microsoft Script Encoder)
- DCRatBuild.exe (PID: 1744)
The process uses the downloaded file
- DCRatBuild.exe (PID: 1744)
- Memory Compression.exe (PID: 6512)
Reads Environment values
- Memory Compression.exe (PID: 6512)
- default-browser-agent.exe (PID: 1344)
- dllhost.exe (PID: 1684)
- smss.exe (PID: 6344)
Process checks whether UAC notifications are on
- Memory Compression.exe (PID: 6512)
Reads Microsoft Office registry keys
- Memory Compression.exe (PID: 6512)
Create files in a temporary directory
- Memory Compression.exe (PID: 6512)
Reads the machine GUID from the registry
- Memory Compression.exe (PID: 6512)
- default-browser-agent.exe (PID: 1344)
- dllhost.exe (PID: 1684)
- smss.exe (PID: 6344)
Checks proxy server information
- Memory Compression.exe (PID: 6512)
Disables trace logs
- Memory Compression.exe (PID: 6512)
Reads the software policy settings
- Memory Compression.exe (PID: 6512)
Found Base64 encoded reference to WMI classes (YARA)
- Memory Compression.exe (PID: 6512)
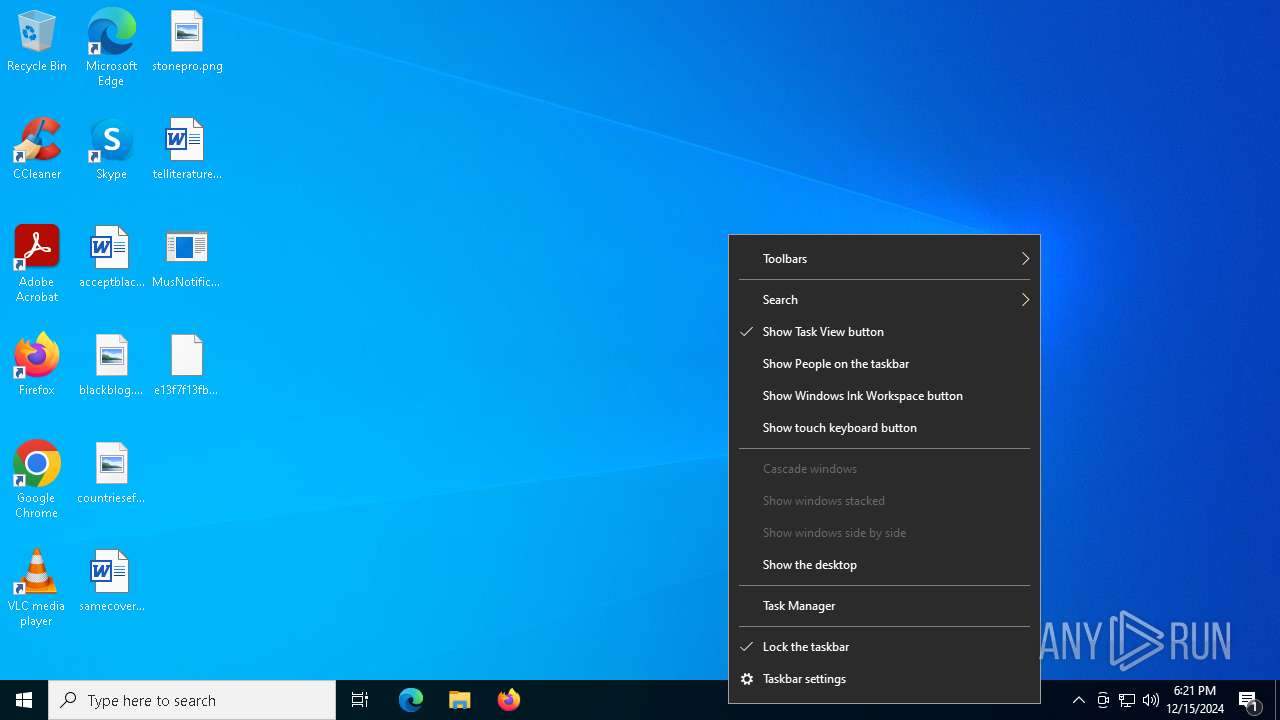
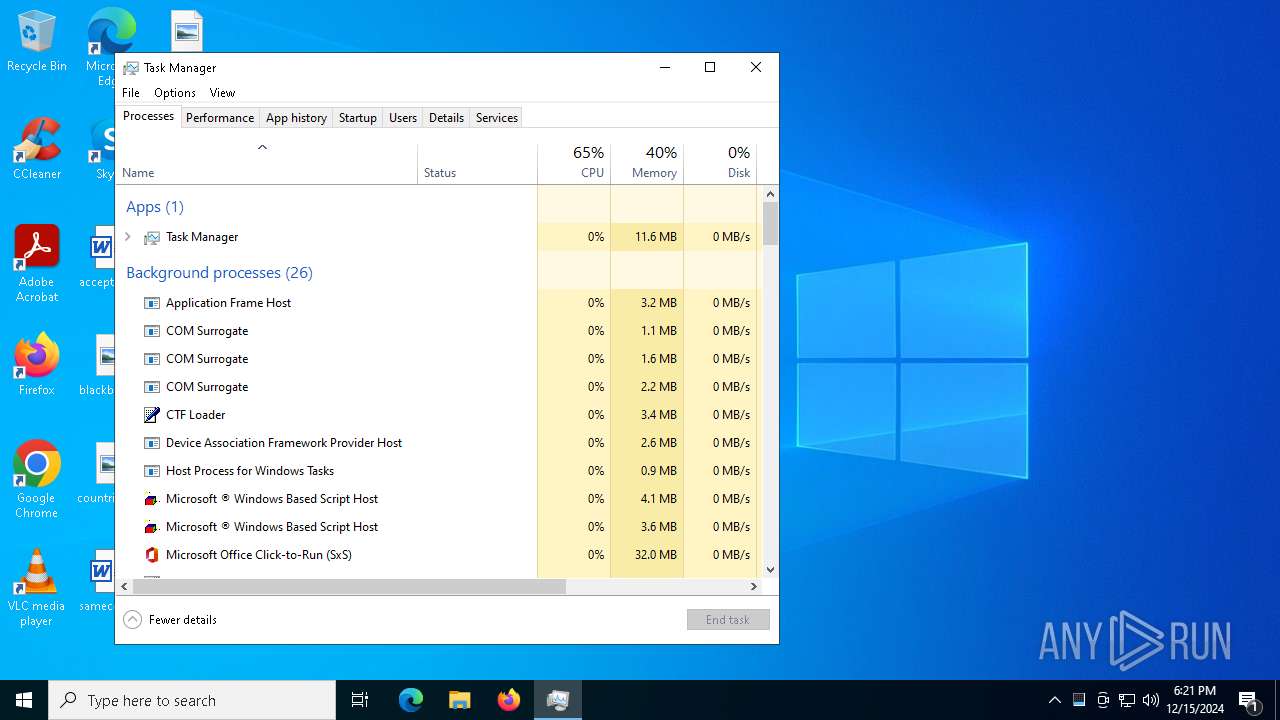
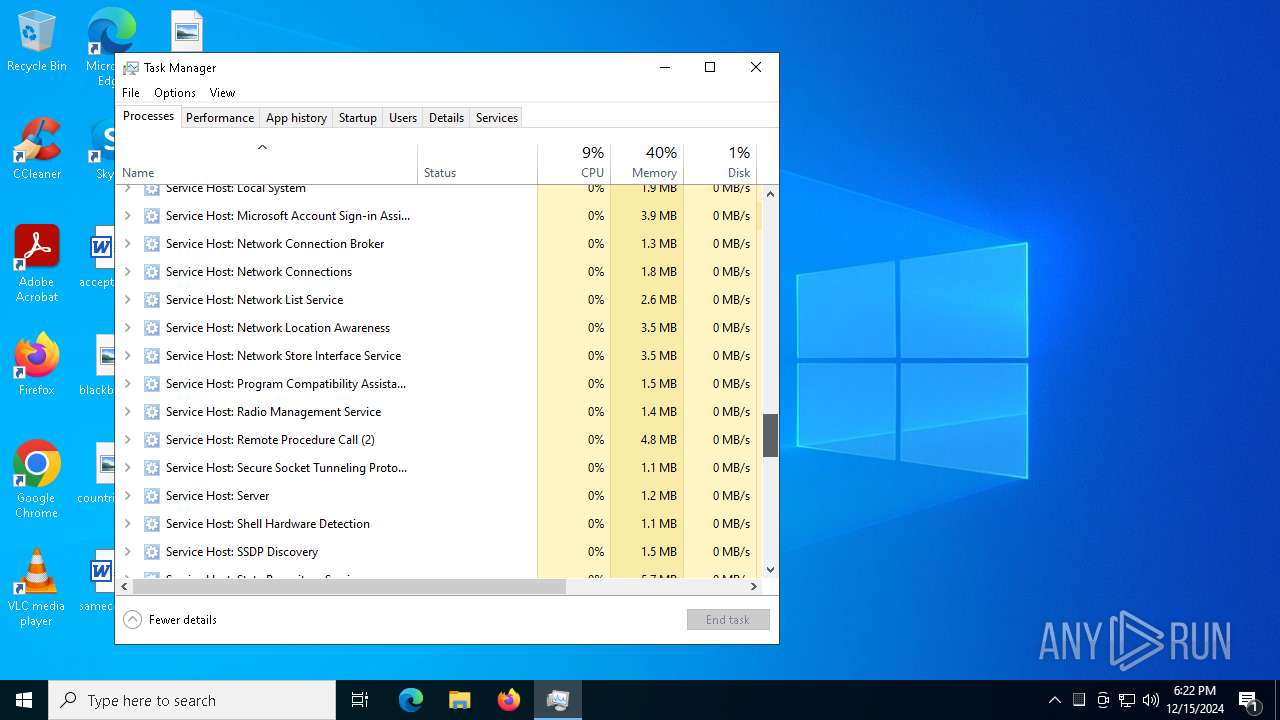
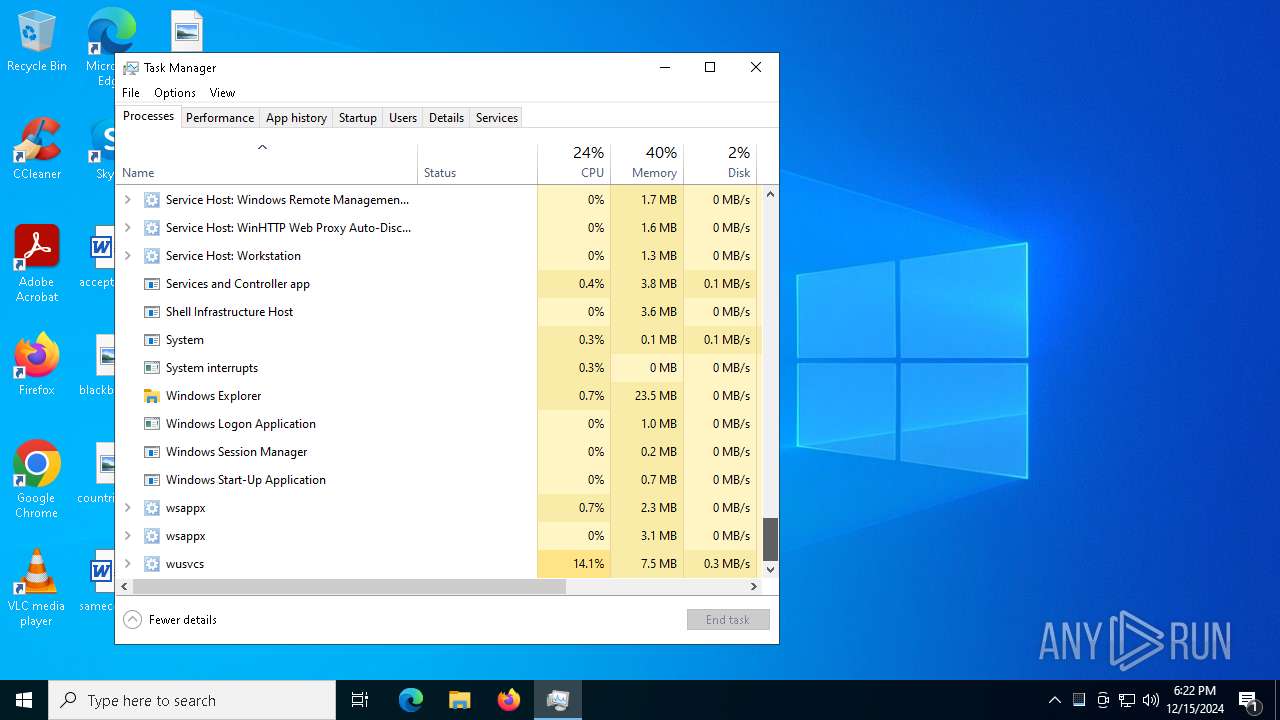
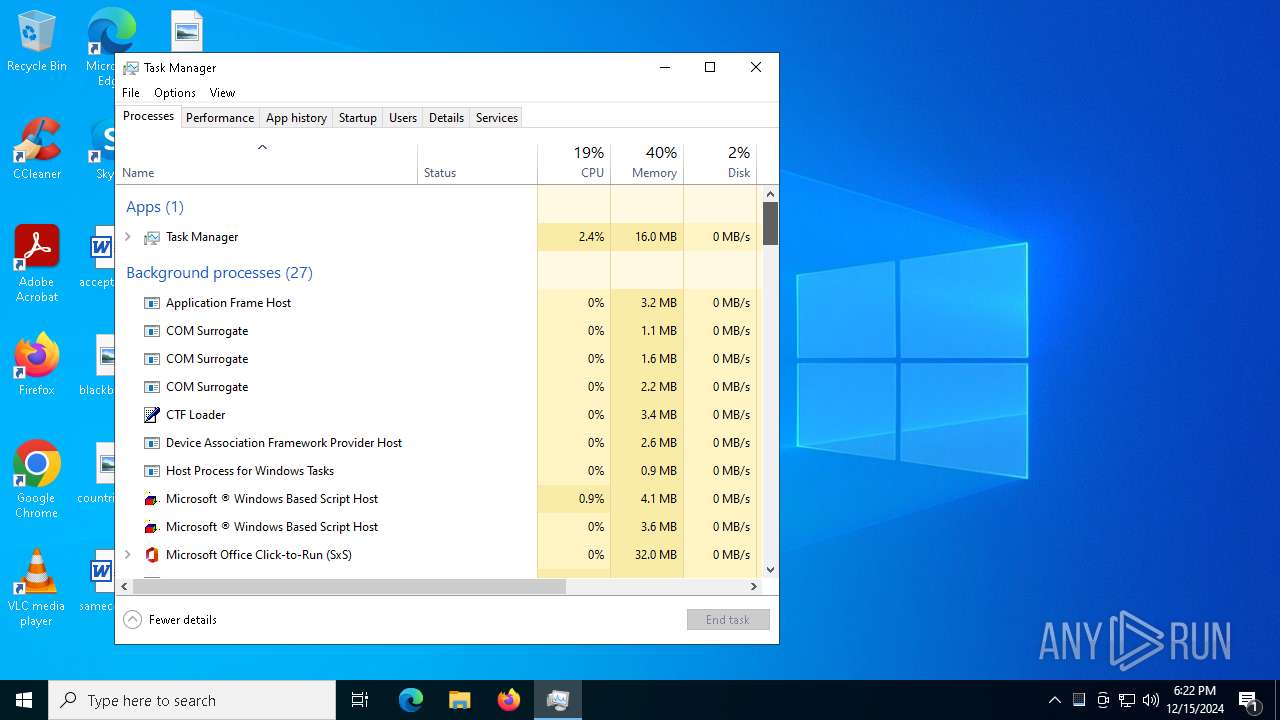
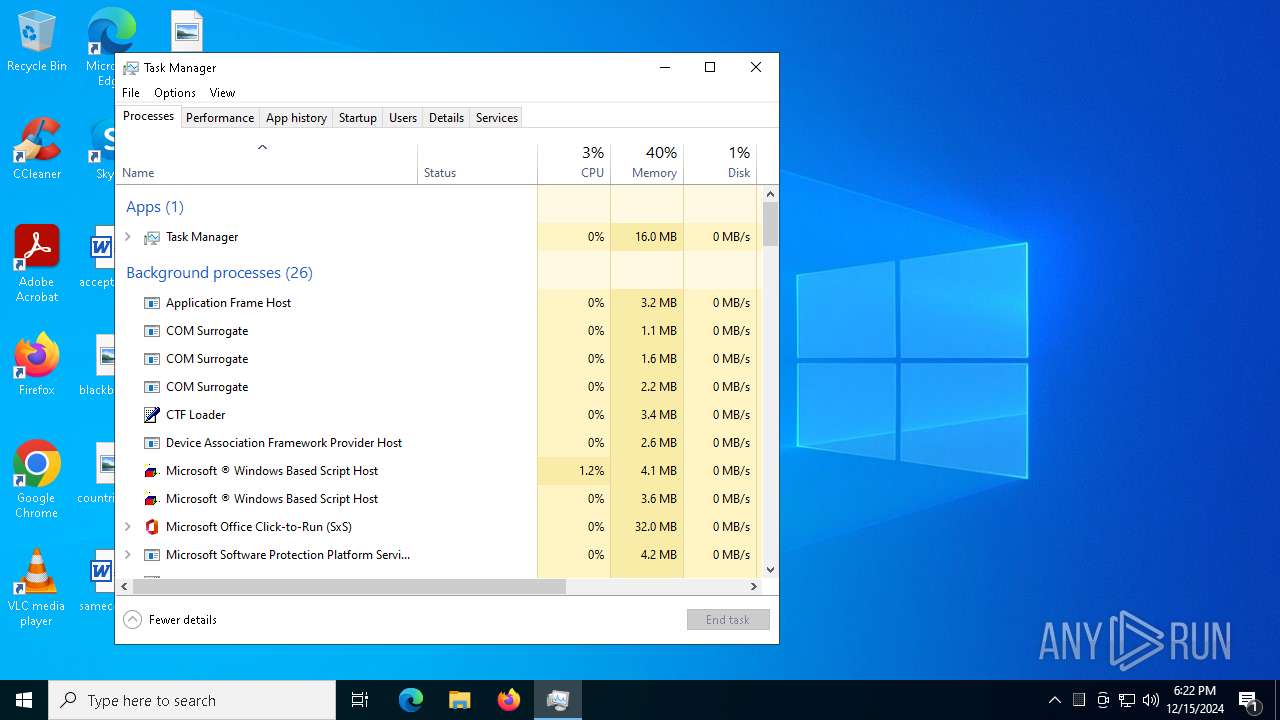
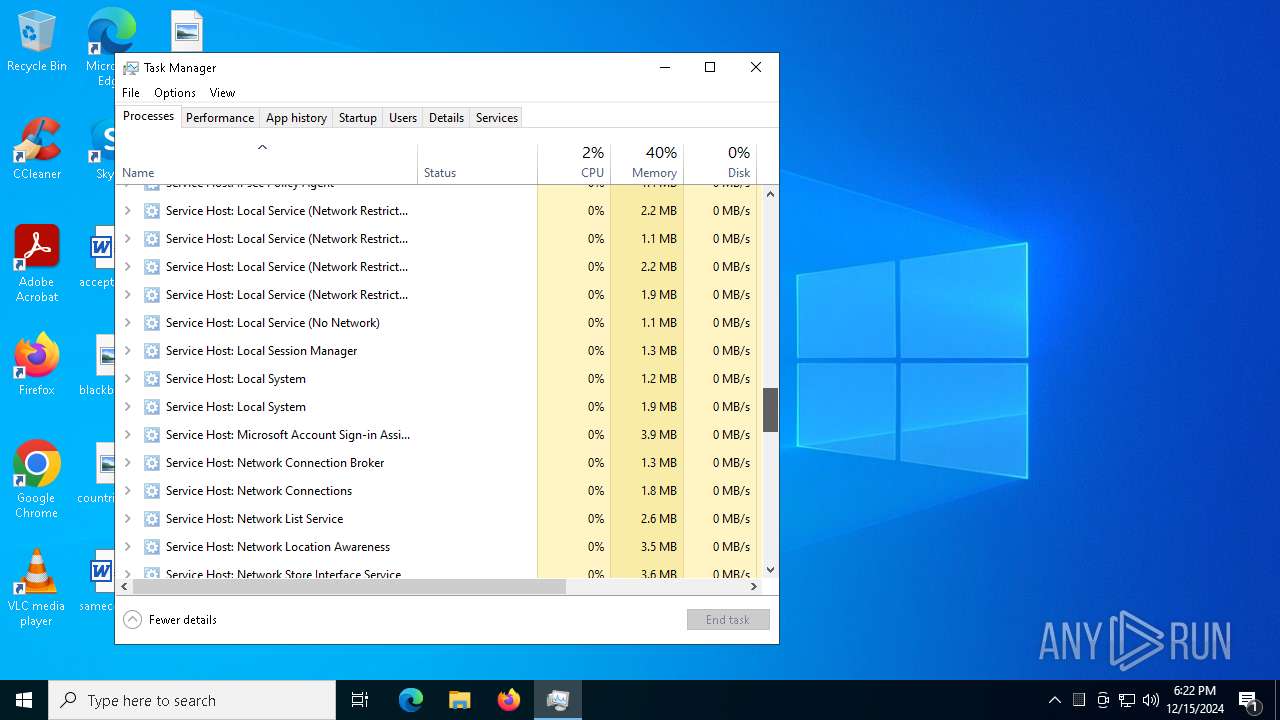
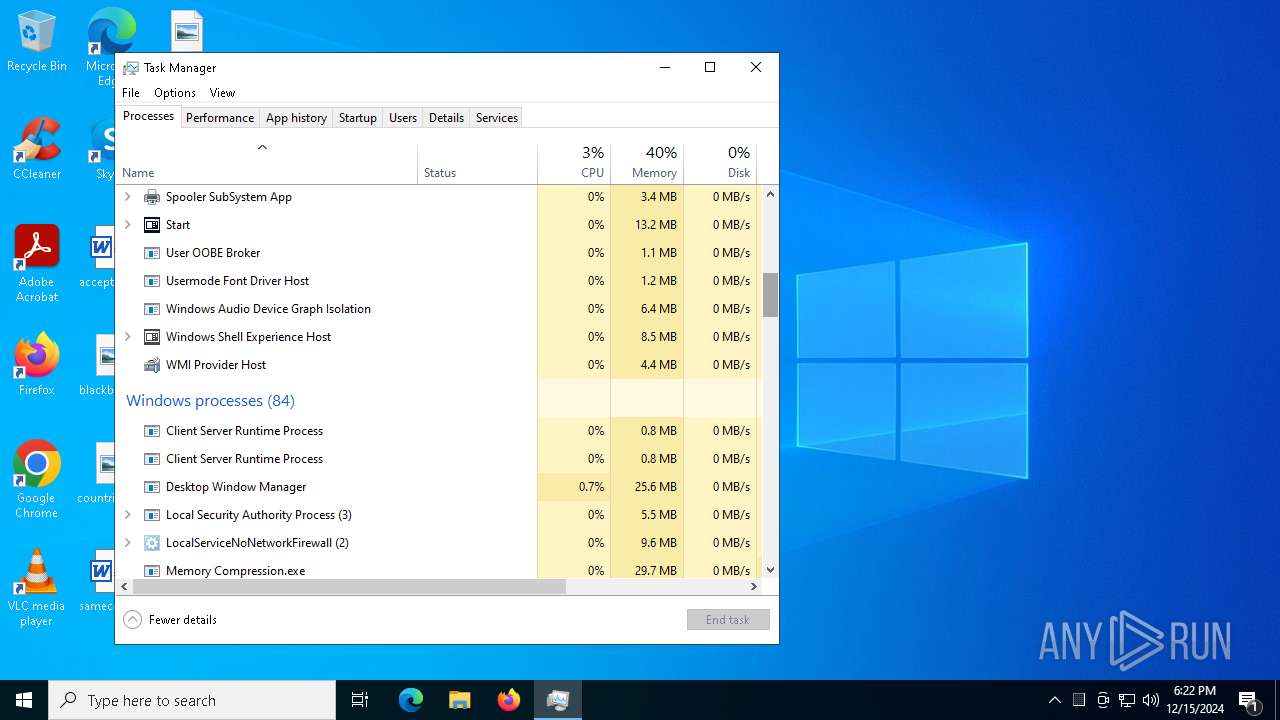
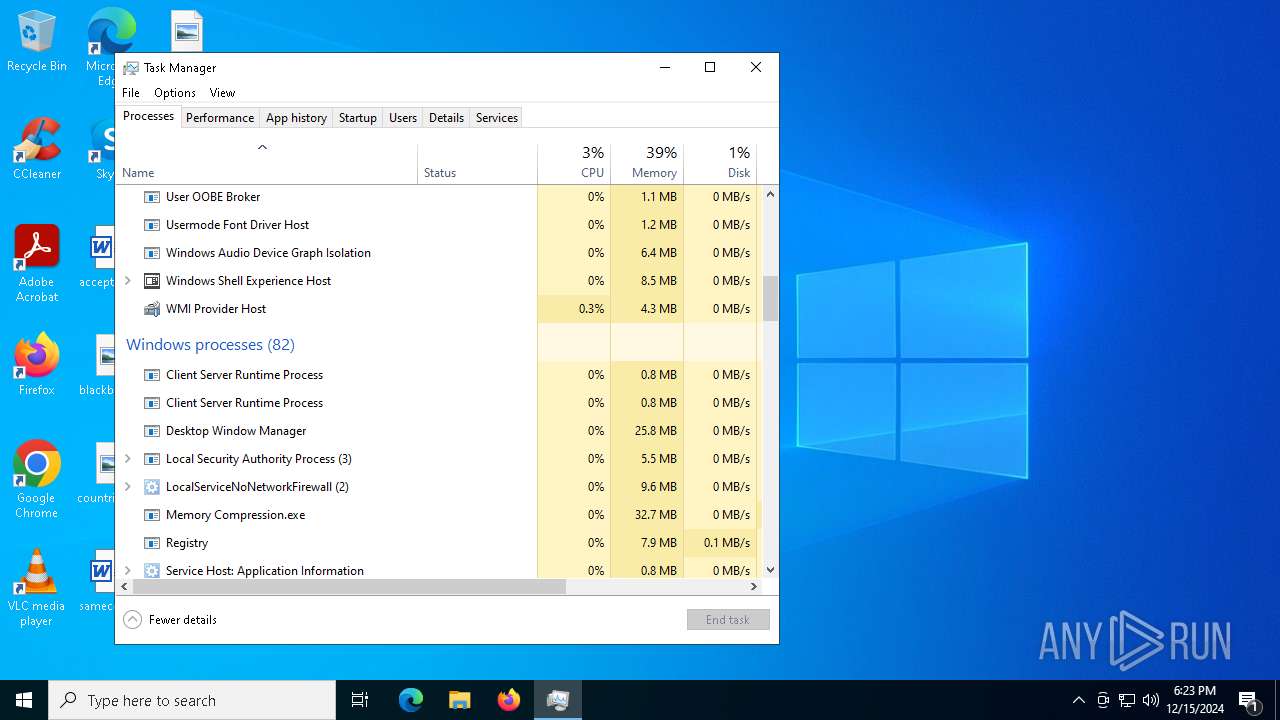
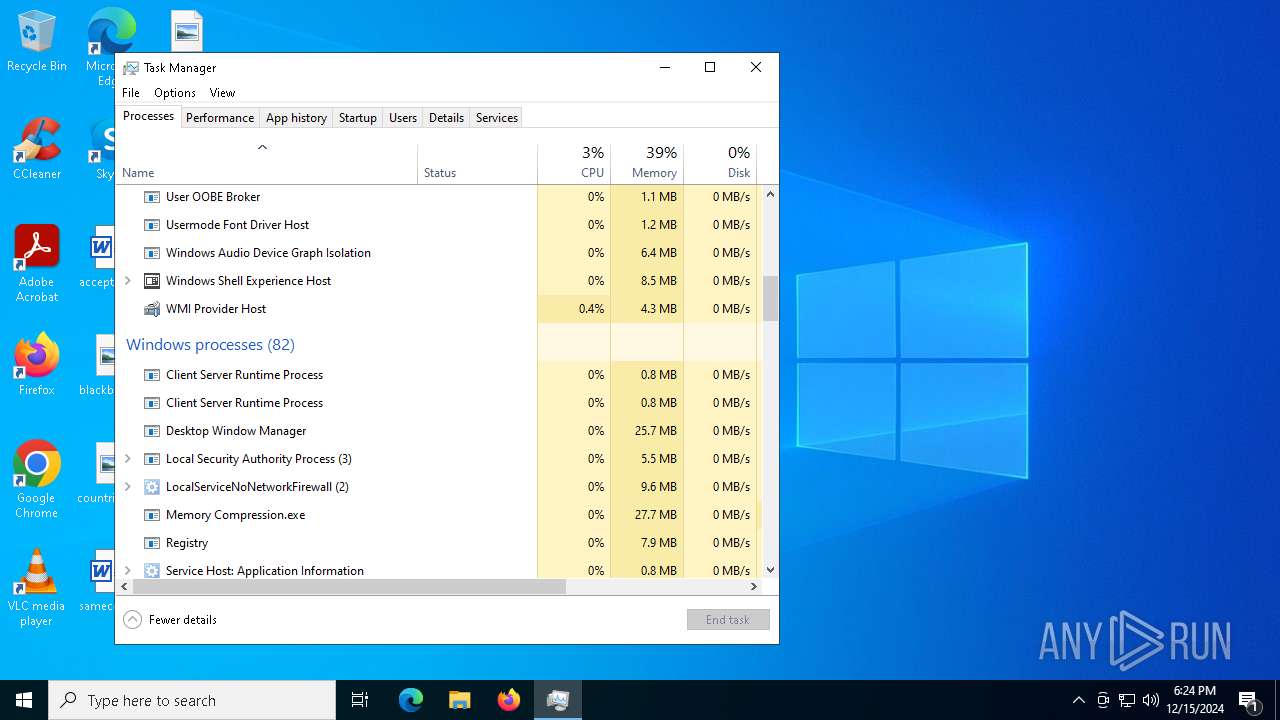
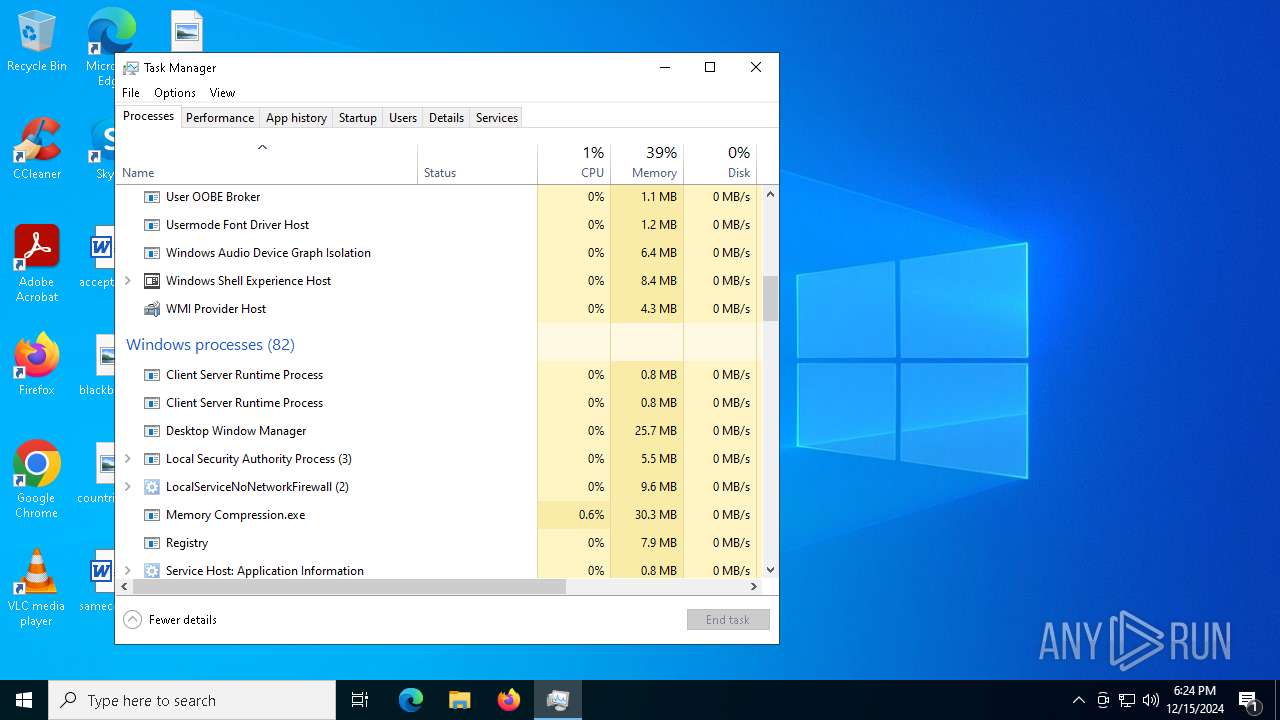
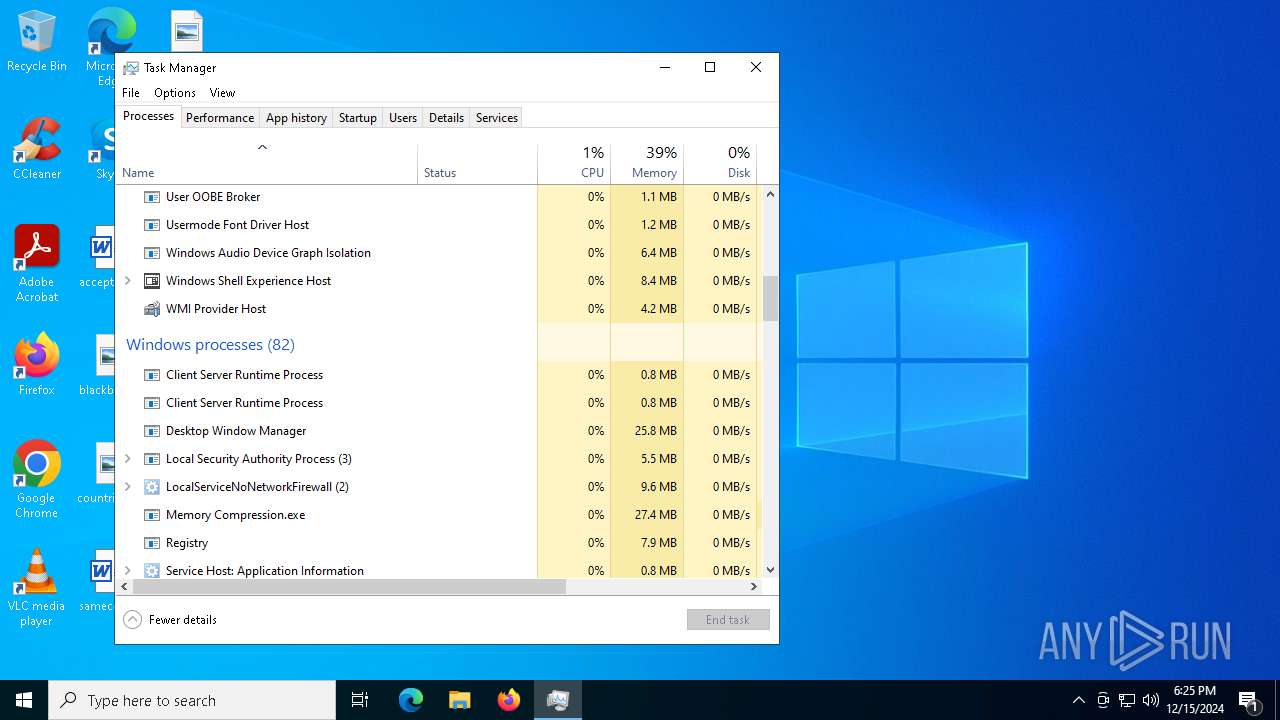
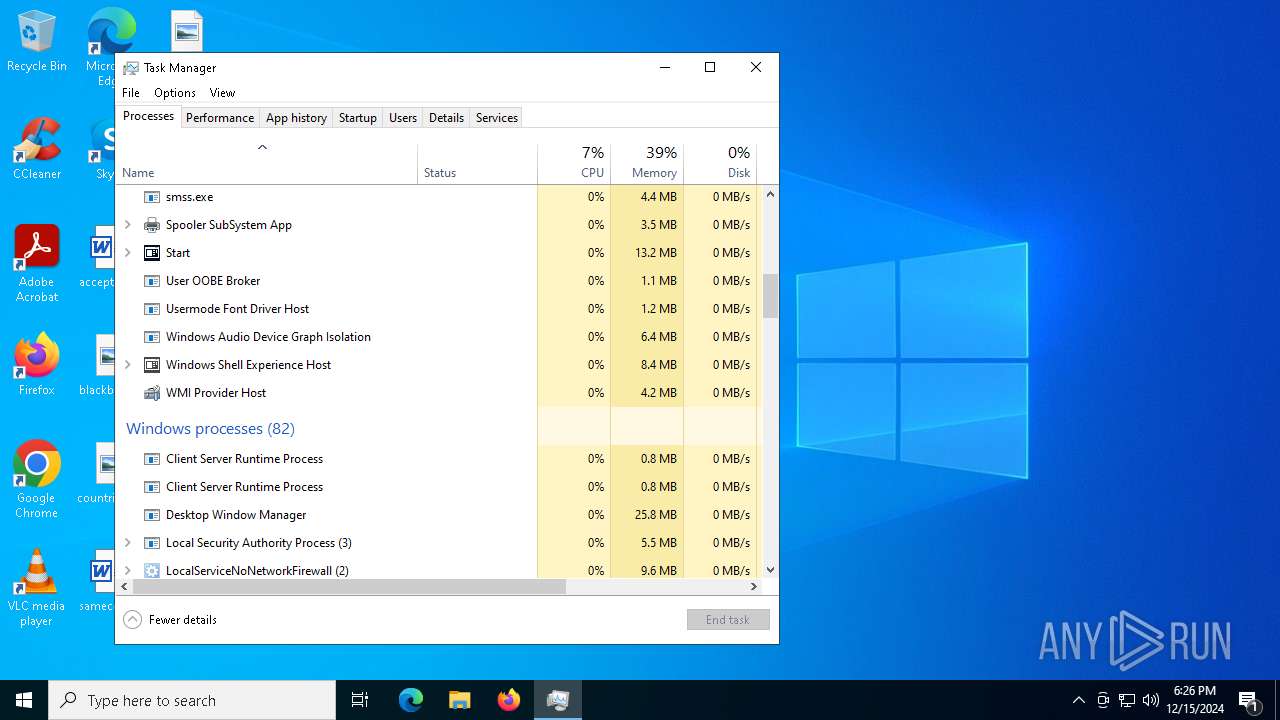
Manual execution by a user
- Taskmgr.exe (PID: 6704)
- Taskmgr.exe (PID: 6644)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:01 18:00:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201216 |
| InitializedDataSize: | 255488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ec40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
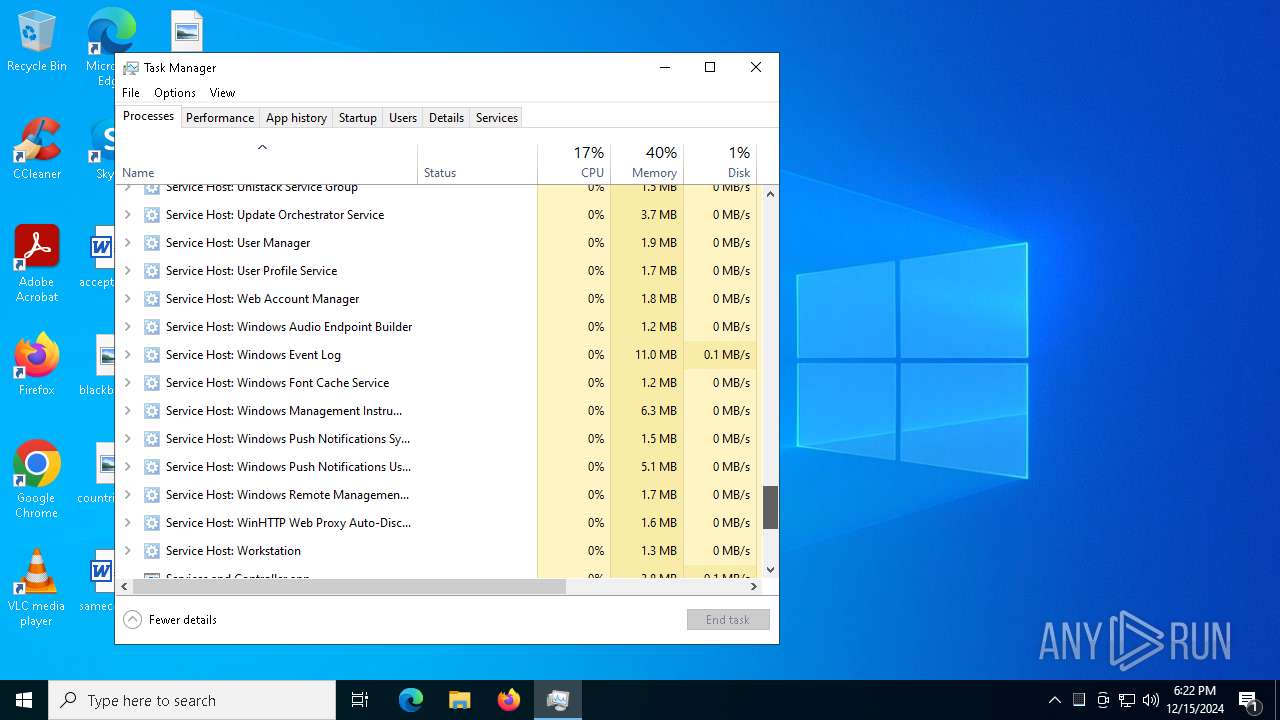
Total processes
199
Monitored processes
68
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | schtasks.exe /create /tn "RegistryR" /sc MINUTE /mo 5 /tr "'C:\Recovery\Logs\Registry.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | "C:\msPortServer\default-browser-agent.exe" | C:\msPortServer\default-browser-agent.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Version: 5.15.2.0 Modules
| |||||||||||||||
| 1684 | "C:\found.000\dir0001.chk\dllhost.exe" | C:\found.000\dir0001.chk\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Version: 5.15.2.0 Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\AppData\Local\Temp\DCRatBuild.exe" | C:\Users\admin\AppData\Local\Temp\DCRatBuild.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | schtasks.exe /create /tn "wininitw" /sc MINUTE /mo 9 /tr "'C:\found.000\dir_00000002.chk\wininit.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | schtasks.exe /create /tn "RegistryR" /sc MINUTE /mo 14 /tr "'C:\Recovery\Logs\Registry.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3092 | schtasks.exe /create /tn "backgroundTaskHostb" /sc MINUTE /mo 9 /tr "'C:\Program Files (x86)\Windows Portable Devices\backgroundTaskHost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | schtasks.exe /create /tn "default-browser-agent" /sc ONLOGON /tr "'C:\msPortServer\default-browser-agent.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3532 | schtasks.exe /create /tn "surrogateContainers" /sc MINUTE /mo 13 /tr "'C:\Users\All Users\surrogateContainer.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 861
Read events
7 835
Write events
25
Delete events
1
Modification events
| (PID) Process: | (1744) DCRatBuild.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (6884) ShellExperienceHost.exe | Key: | \REGISTRY\A\{5fec0346-7415-664c-666e-4df00eb61645}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000CD7E251D1E4FDB01 | |||
| (PID) Process: | (6884) ShellExperienceHost.exe | Key: | \REGISTRY\A\{5fec0346-7415-664c-666e-4df00eb61645}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D000000F7E1271D1E4FDB01 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Memory Compression_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6512) Memory Compression.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Memory Compression_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1744 | DCRatBuild.exe | C:\msPortServer\55CGRc9aUJ.vbe | binary | |
MD5:BE355227928FCC042D23C408ADB28E4D | SHA256:04FEA8C0D9972F07109512859A2E89D3FA0CEF44549E05A00F367AEB539BB5CD | |||
| 1744 | DCRatBuild.exe | C:\msPortServer\surrogateContainer.exe | executable | |
MD5:E6572EBD79AC9368802823C065F4C2F2 | SHA256:E20B44CA40799EB83AC9CF63EEB043E03FD6E6DBB3DA917D8F6B06A0E1F95CE2 | |||
| 6644 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 6512 | Memory Compression.exe | C:\Users\admin\AppData\Local\Temp\6f7e3d239d84bc4d07b67c564f12cf2e62a4a79f.exe | executable | |
MD5:E6572EBD79AC9368802823C065F4C2F2 | SHA256:E20B44CA40799EB83AC9CF63EEB043E03FD6E6DBB3DA917D8F6B06A0E1F95CE2 | |||
| 6512 | Memory Compression.exe | C:\Users\admin\AppData\Local\Temp\6e1dead7-db67-49bc-81f2-d1e43c0a1bed.vbs | text | |
MD5:D0C836F1DC31BD1752E8A8156A5A1D5E | SHA256:BE95075EC2259B1859AB817EFA4AB96D9A4AE8DB1A174CB0A06AD99B11802432 | |||
| 1744 | DCRatBuild.exe | C:\msPortServer\l9TUj.bat | text | |
MD5:DD2D3197DCB964C910A135E408663FA4 | SHA256:52E6B0709032956386475B2DA3975FBCA841051EEBB3C7F358E9C772516F6CD9 | |||
| 6512 | Memory Compression.exe | C:\Users\admin\AppData\Local\Temp\018771df-4d3d-4d99-9025-50be8e03b32f.vbs | text | |
MD5:3BBF4E3ADC0EE9BA3DCF65AADD255FBB | SHA256:0572036CB079CF3D76A347D9615C19F16D00D68E6AF8BAAA8AD9E71EC7ECEA1B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
111
TCP/UDP connections
39
DNS requests
18
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6512 | Memory Compression.exe | GET | 200 | 92.53.106.114:80 | http://cc00465.tw1.ru/L1nc0In.php?hDuTO4w5yztb8kcGQP=lXF&a26a303a4fe8a6d6015d043a75bc91fe=2a04b0e33bde3693385239da2b629932&48a77528059d3b866006b02eb8deba53=QNwYWN2YWNjJDO5UzY0Q2MzEmZkZTNyUTM3MTZzMjYwMGOiVTN2QmZ&hDuTO4w5yztb8kcGQP=lXF | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6512 | Memory Compression.exe | GET | 200 | 92.53.106.114:80 | http://cc00465.tw1.ru/L1nc0In.php?Td23poUhP13AUu9zfHmRwz=YpyKR7I3a8tNGcxSjT0Li0Hva7&NHeJ4epdN0dCkH7cBlg2Wry=86n&43405bde86dc134f4ca46f906493b1f1=QO5ETOzUGOwgTZ3gTOyUzMjJ2YkRmYhJDNxYjMiVmYjR2MkJWNjFmM0ITMwUDM1ATM0AzM2gDN&48a77528059d3b866006b02eb8deba53=AOjdjNzIDO0MDZjZWMlN2YmRzM5kTZiJWO0QmMhhTMkVDZlZmMxgjM&844463d37be14612629561a0bf6df072=0VfiIiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiIycDMhVGM4UTMxIWOjZTYyMGMxMjYzIWYhFTZlJzNykzNzM2M4YmZ0IiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W | unknown | — | — | whitelisted |
6512 | Memory Compression.exe | GET | 200 | 92.53.106.114:80 | http://cc00465.tw1.ru/L1nc0In.php?Td23poUhP13AUu9zfHmRwz=YpyKR7I3a8tNGcxSjT0Li0Hva7&NHeJ4epdN0dCkH7cBlg2Wry=86n&43405bde86dc134f4ca46f906493b1f1=QO5ETOzUGOwgTZ3gTOyUzMjJ2YkRmYhJDNxYjMiVmYjR2MkJWNjFmM0ITMwUDM1ATM0AzM2gDN&48a77528059d3b866006b02eb8deba53=AOjdjNzIDO0MDZjZWMlN2YmRzM5kTZiJWO0QmMhhTMkVDZlZmMxgjM&0b4699873302d8742364f340bfbe4c6f=d1nI3gTY5kTYwE2MzAjY5YzY1MWZ1UWOyMjMkBzYjNWZiNTNihjMxIGNiJiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W&844463d37be14612629561a0bf6df072=0VfiIiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiI3gTY5kTYwE2MzAjY5YzY1MWZ1UWOyMjMkBzYjNWZiNTNihjMxIGNiJiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNisHL9JSUmljS5NGdCNVTykUaPl2ZE9UMJ1mW5FleNlmTXpFejpWW6lERatmWUllaSdVTyU1RaNTVHpVbKJTWyU1RNNTWH5UaS1WS3AnaJhmUYlVRShUZsp0QMFzbqlEMWNjYsFzVhVlQYpFb4JTVpdXaJxmWYFGMOdVUp9maJpnVIRGaSNTV1IFWhJDbHRmaGtWSzlUajxGZXlVdGdFVnBzVZlHZyIWeCxWS2kUekZnUtJGckZkVEZ0aJNXSpRVavpWS0ZkMZlmVyYles1WSzl0UXl2bqlEb1IjYvJ0MilnTXFmTOhVYpdXaJBHNyQmd1ITY1ZlRLdGNyQmd1ITY1ZFbJZTSTpFdG1GVWJUMRl2dplEc0IDZ2VjMhVnVGt0Z0IDZ2VjMhVnVslkNJNlW0ZUbUZlQxIVa3lWSapUaPlGNXFGdSdVU6xWbJNXSplkNJlnUCJFbJNXSDRGcKVUSwkFRJxmTYFWeC52YsJlbiZkQD1EeBl3YzkzRaVHbyYVavpWS5ZVbWVHbyYVa3NlZpRzVhNnSYp1Q5MlW3lTbjFjVrlkNJNlW1lTblxWMXFGMKNETpFERNdXQE10dJl2Tpd3VZBjTzI2dKNETptmbihWMtNGbkVUS0F0QaxGbtpFcOdlW35ESJBTOtRVavpWSup0Mil2dplUNZRUTwQTeNh3dp5UNFRlT1lEVOl2bqlka5ckYpdXaJZkUrlkNJNVZ5JlbiFTOykVa3lWS1x2RilnVtF1ZR1mYoh3aJZTSpJmdsJjWspkbJNXSpJGc412Ysp0aJZTSTVGMsJTWpdXaJdXQU1UdNpnT4RzQOhXSqxEenRVTp9maJdHbtl0NwpWS2pVbipkQYNVa3lWS1x2VitmRtlkNJNlW0ZUbUlnVyMmVKNETpFVRUtEeFRFSwVFTRlTRWxkTWJVRKl2TpV1VihWNwEVUKNETplkeNVXVqxEMJl2TplEWadlSYplMKhlWUp0QMlWT5FVavpWSsJEWlVlSYplMKhlWUpUelJiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiIjZGOzMGOwIDN3MGOkVGNjVGNjJ2NjZDMxMGOkNTN1EmMlRzYwgTZ5IiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W | unknown | — | — | malicious |
6512 | Memory Compression.exe | GET | 200 | 92.53.106.114:80 | http://cc00465.tw1.ru/L1nc0In.php?Td23poUhP13AUu9zfHmRwz=YpyKR7I3a8tNGcxSjT0Li0Hva7&NHeJ4epdN0dCkH7cBlg2Wry=86n&43405bde86dc134f4ca46f906493b1f1=QO5ETOzUGOwgTZ3gTOyUzMjJ2YkRmYhJDNxYjMiVmYjR2MkJWNjFmM0ITMwUDM1ATM0AzM2gDN&48a77528059d3b866006b02eb8deba53=AOjdjNzIDO0MDZjZWMlN2YmRzM5kTZiJWO0QmMhhTMkVDZlZmMxgjM&e599abfd1b07bf0fe4a29ac95bc07ec9=0VfikjSp1ken5WT6dnRYpnVykVeWNjY6ZVbjNGeGRWdWdVYz5URJFlUsJ1ZFdkYzxWbXxGeXF2R4ZEW6Z1RiBnWFlEdG12YulTbjFFeGhlNNtWS2k0QhBjRHVVa3lWS1R2MiVHdtJmVKl2Tpd2RkhmQGpVe5ITW6x2RSl2dplUavpWSvJFWZFVMXlVekdlWzZ1RWl2dplUavpWS6JESjJUMXlFbSNTVpdXaJVHZzIWd01mYWpUaPlWUVNVeWJzYWFzVZxmUzUVa3lWS1R2MiVHdtJmVKl2TplEWapnVWJGaWdEZUp0QMlGNyQmd1ITY1ZFbJZTS5pVdGdEV0Z0VaBjTsl0cJlmYzkTbiJXNXZVavpWSvJFWZFVMXlFbSNTVpdXaJZHbHpVMGVUSzsmeKRkRFlkcWdEZzZ0VaNlQTxUenNUS1xWRJxWNXFWT1cEW5hnVkJkQ55UNjlXUCJUehxmUIJGaW1WVnBTaN9WQTpVd5cUY3lTbjpGbXRVavpWS6ZVbiZHaHNmdKNTWwFzaJNXSplkNJl3Y0ZkMZlmVyYVa3lWS1hHbjNmRUdlQ4VUVUxWRSNGesx0Y4ZEWjpUaPlWTuJGbW12Yq5EbJNXS5tEN0MkTp9maJVXOXFmeKhlWXRXbjZHZYpFdG12YHpUelJiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiIycDMhVGM4UTMxIWOjZTYyMGMxMjYzIWYhFTZlJzNykzNzM2M4YmZ0IiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W | unknown | — | — | whitelisted |
6512 | Memory Compression.exe | GET | 200 | 92.53.106.114:80 | http://cc00465.tw1.ru/L1nc0In.php?Td23poUhP13AUu9zfHmRwz=YpyKR7I3a8tNGcxSjT0Li0Hva7&NHeJ4epdN0dCkH7cBlg2Wry=86n&43405bde86dc134f4ca46f906493b1f1=QO5ETOzUGOwgTZ3gTOyUzMjJ2YkRmYhJDNxYjMiVmYjR2MkJWNjFmM0ITMwUDM1ATM0AzM2gDN&48a77528059d3b866006b02eb8deba53=AOjdjNzIDO0MDZjZWMlN2YmRzM5kTZiJWO0QmMhhTMkVDZlZmMxgjM&0b4699873302d8742364f340bfbe4c6f=d1nI3gTY5kTYwE2MzAjY5YzY1MWZ1UWOyMjMkBzYjNWZiNTNihjMxIGNiJiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W&844463d37be14612629561a0bf6df072=0VfiIiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiI3gTY5kTYwE2MzAjY5YzY1MWZ1UWOyMjMkBzYjNWZiNTNihjMxIGNiJiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNisHL9JSUmljS5NGdCNVTykUaPl2ZE9UMJ1mW5FleNlmTXpFejpWW6lERatmWUllaSdVTyU1RaNTVHpVbKJTWyU1RNNTWH5UaS1WS3AnaJhmUYlVRShUZsp0QMFzbqlEMWNjYsFzVhVlQYpFb4JTVpdXaJxmWYFGMOdVUp9maJpnVIRGaSNTV1IFWhJDbHRmaGtWSzlUajxGZXlVdGdFVnBzVZlHZyIWeCxWS2kUekZnUtJGckZkVEZ0aJNXSpRVavpWS0ZkMZlmVyYles1WSzl0UXl2bqlEb1IjYvJ0MilnTXFmTOhVYpdXaJBHNyQmd1ITY1ZlRLdGNyQmd1ITY1ZFbJZTSTpFdG1GVWJUMRl2dplEc0IDZ2VjMhVnVGt0Z0IDZ2VjMhVnVslkNJNlW0ZUbUZlQxIVa3lWSapUaPlGNXFGdSdVU6xWbJNXSplkNJlnUCJFbJNXSDRGcKVUSwkFRJxmTYFWeC52YsJlbiZkQD1EeBl3YzkzRaVHbyYVavpWS5ZVbWVHbyYVa3NlZpRzVhNnSYp1Q5MlW3lTbjFjVrlkNJNlW1lTblxWMXFGMKNETpFERNdXQE10dJl2Tpd3VZBjTzI2dKNETptmbihWMtNGbkVUS0F0QaxGbtpFcOdlW35ESJBTOtRVavpWSup0Mil2dplUNZRUTwQTeNh3dp5UNFRlT1lEVOl2bqlka5ckYpdXaJZkUrlkNJNVZ5JlbiFTOykVa3lWS1x2RilnVtF1ZR1mYoh3aJZTSpJmdsJjWspkbJNXSpJGc412Ysp0aJZTSTVGMsJTWpdXaJdXQU1UdNpnT4RzQOhXSqxEenRVTp9maJdHbtl0NwpWS2pVbipkQYNVa3lWS1x2VitmRtlkNJNlW0ZUbUlnVyMmVKNETpFVRUtEeFRFSwVFTRlTRWxkTWJVRKl2TpV1VihWNwEVUKNETplkeNVXVqxEMJl2TplEWadlSYplMKhlWUp0QMlWT5FVavpWSsJEWlVlSYplMKhlWUpUelJiOiYjMjJWYiNGOyIGNhVDM5cjYihTZ3kDMkNzYwMmYyMTOiwiIjZGOzMGOwIDN3MGOkVGNjVGNjJ2NjZDMxMGOkNTN1EmMlRzYwgTZ5IiOiITM0MzY3ATY4AjN0gzN2UjY4QDZxgTNzYWO5UjYwYjNiwiImlzNhRTYyYTZyY2YyEjZ0YTNjdjNidDMkRzYiRDOklzMyQ2MldjZ2IiOigDOiJDM4kDOxUWZ2UWY3UTY0kzMxgDOiZGNwMGO3UWNis3W | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 92.123.104.38:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
pastebin.com |
| shared |
cc00465.tw1.ru |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
6512 | Memory Compression.exe | A Network Trojan was detected | ET MALWARE DCRAT Activity (GET) |
6 ETPRO signatures available at the full report