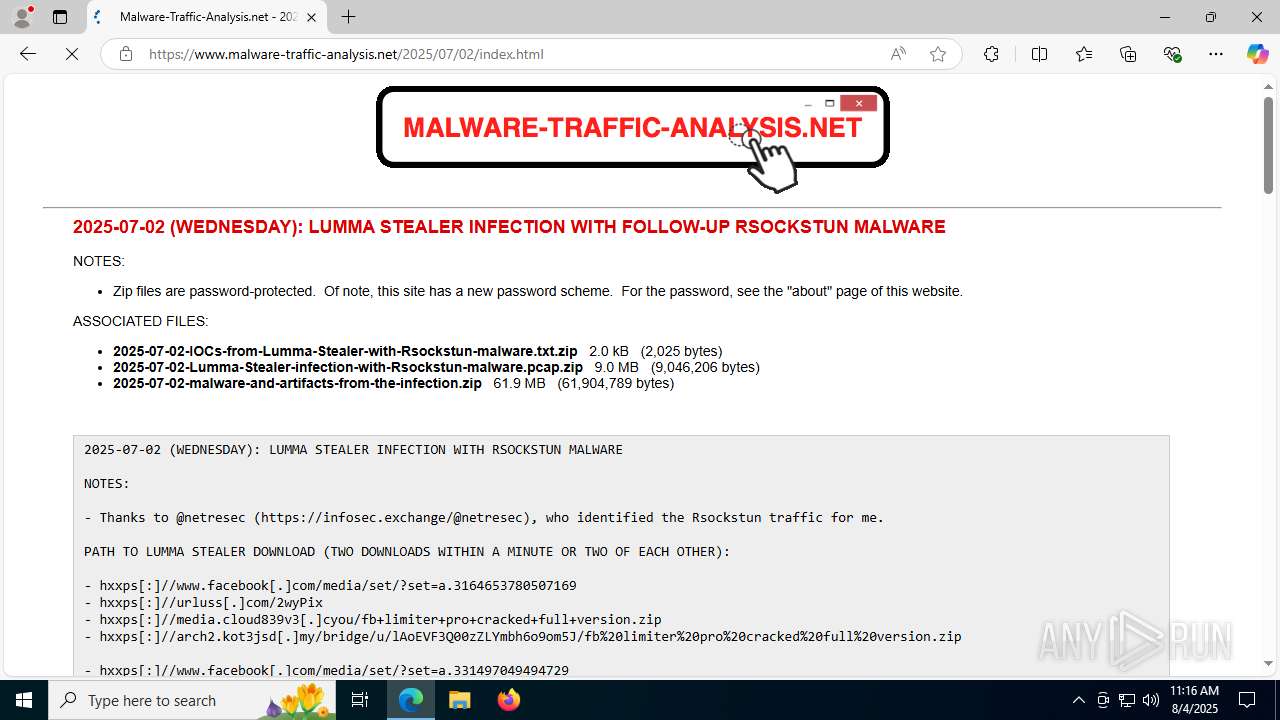
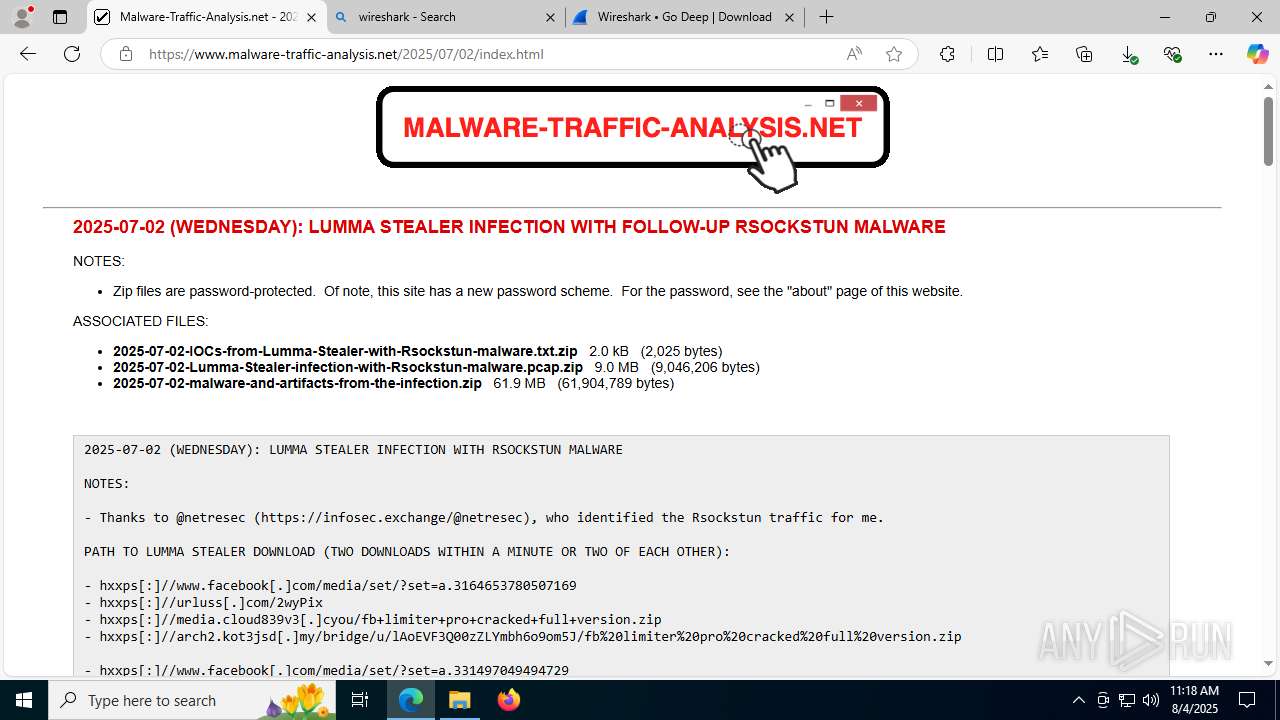
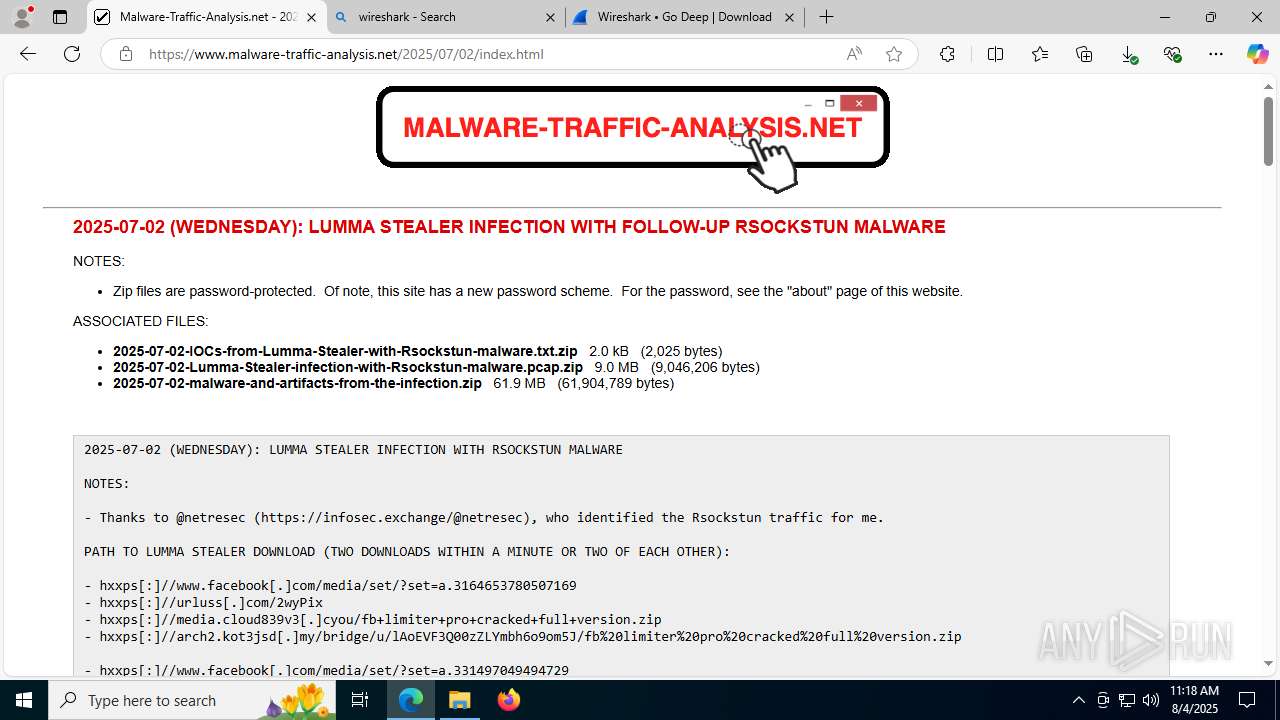
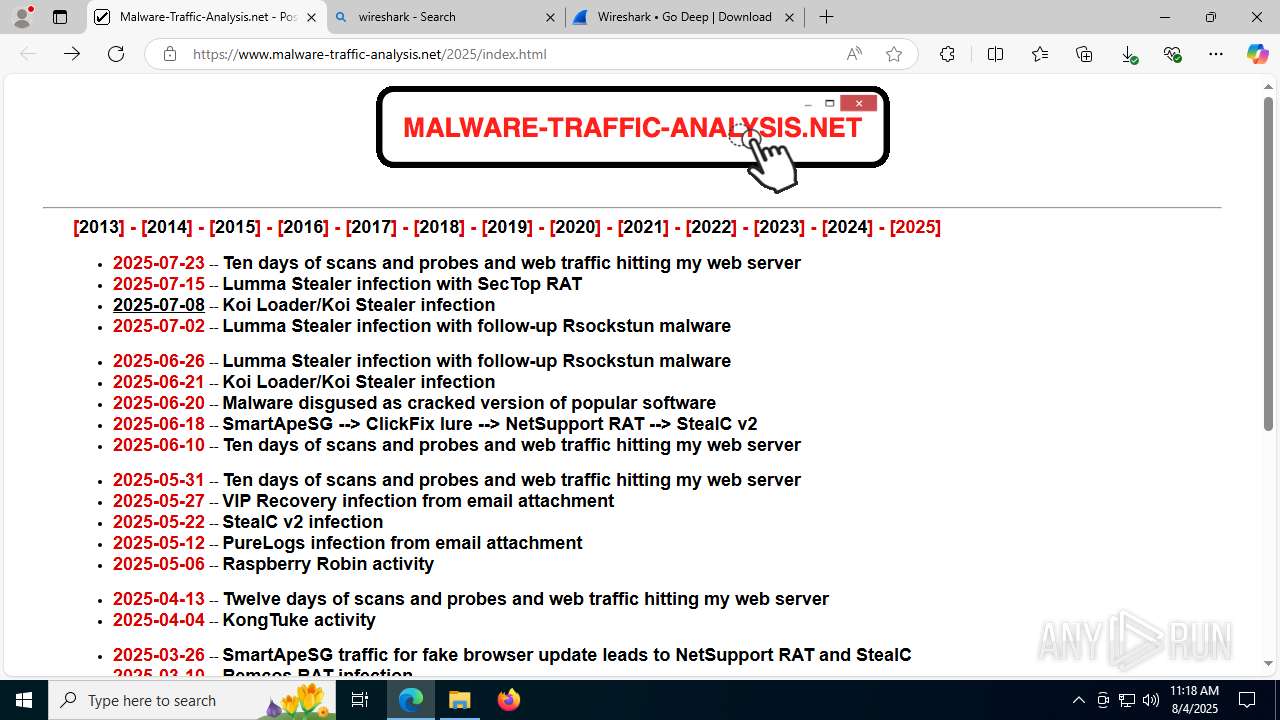
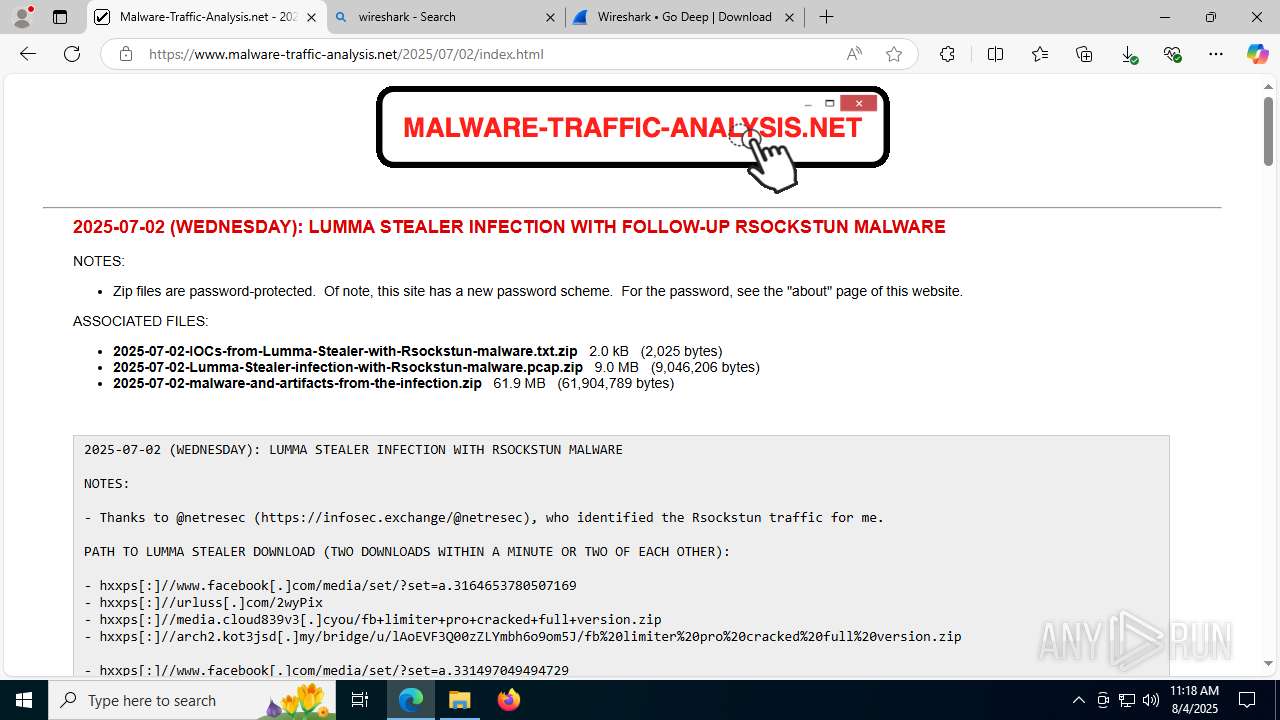
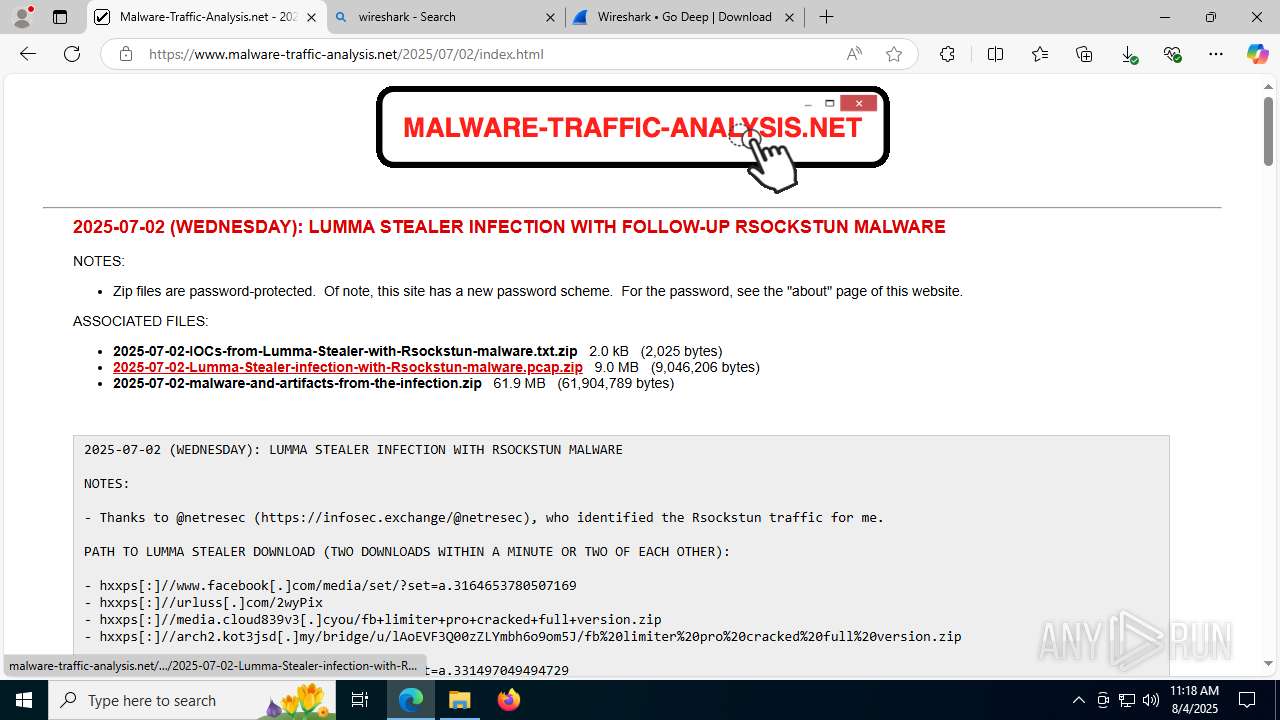
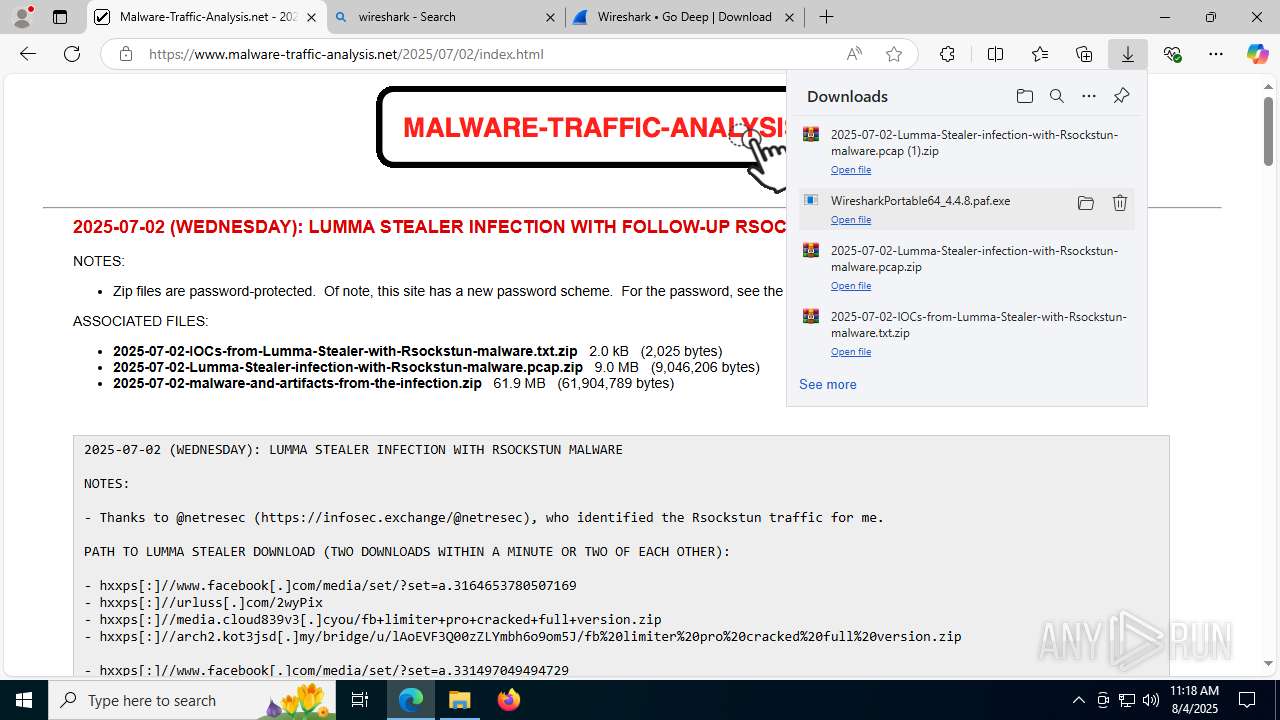
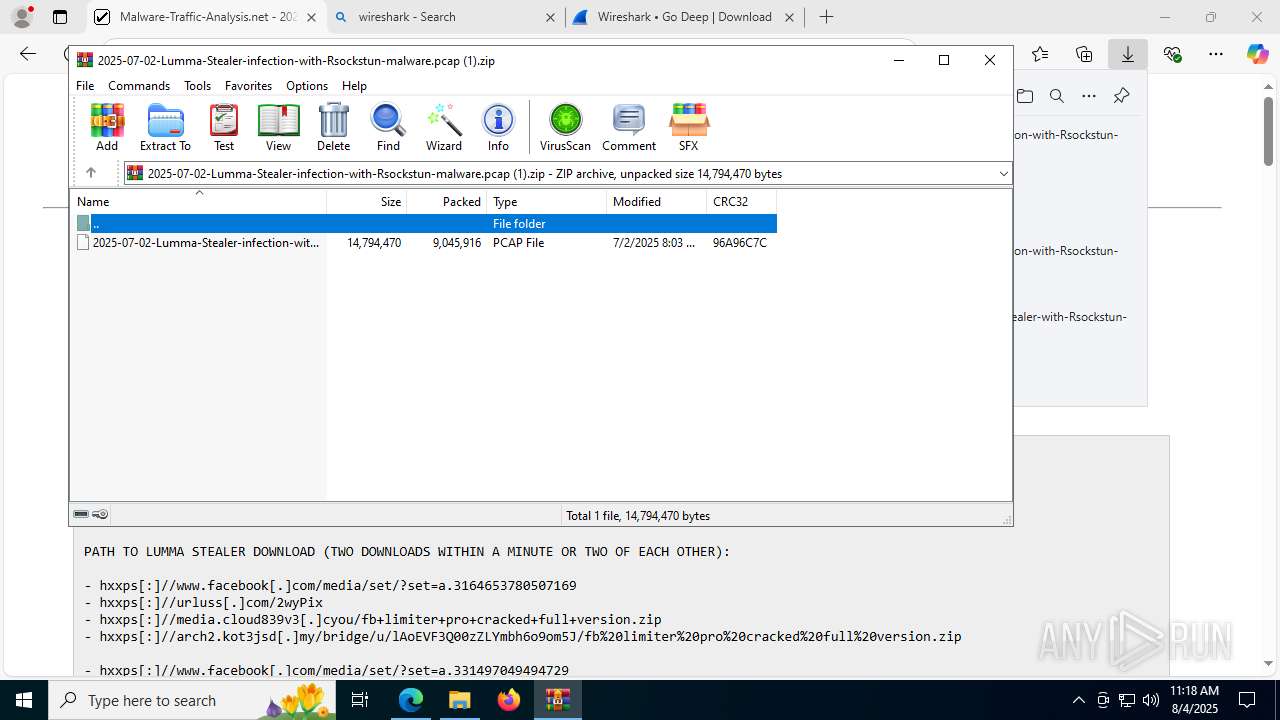
| URL: | https://www.malware-traffic-analysis.net/2025/index.html |
| Full analysis: | https://app.any.run/tasks/b9a3b7ad-e6b0-4326-b016-6e04f32e999a |
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2025, 11:16:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8402E725FA08C6B2252536BEEF0EAD2C |
| SHA1: | BB8D1D68678EABC53959758D5BF093517646F07A |
| SHA256: | E75BEC3C1A84FC14665D4D2832B58AACC440B4EE61E1331DDFCD55EDB9E4562B |
| SSDEEP: | 3:N8DSLHXWQfigcWMMLA2yXG5G:2OLHpJY5MG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 1136)
- WiresharkPortable64.exe (PID: 1268)
- Wireshark.exe (PID: 6308)
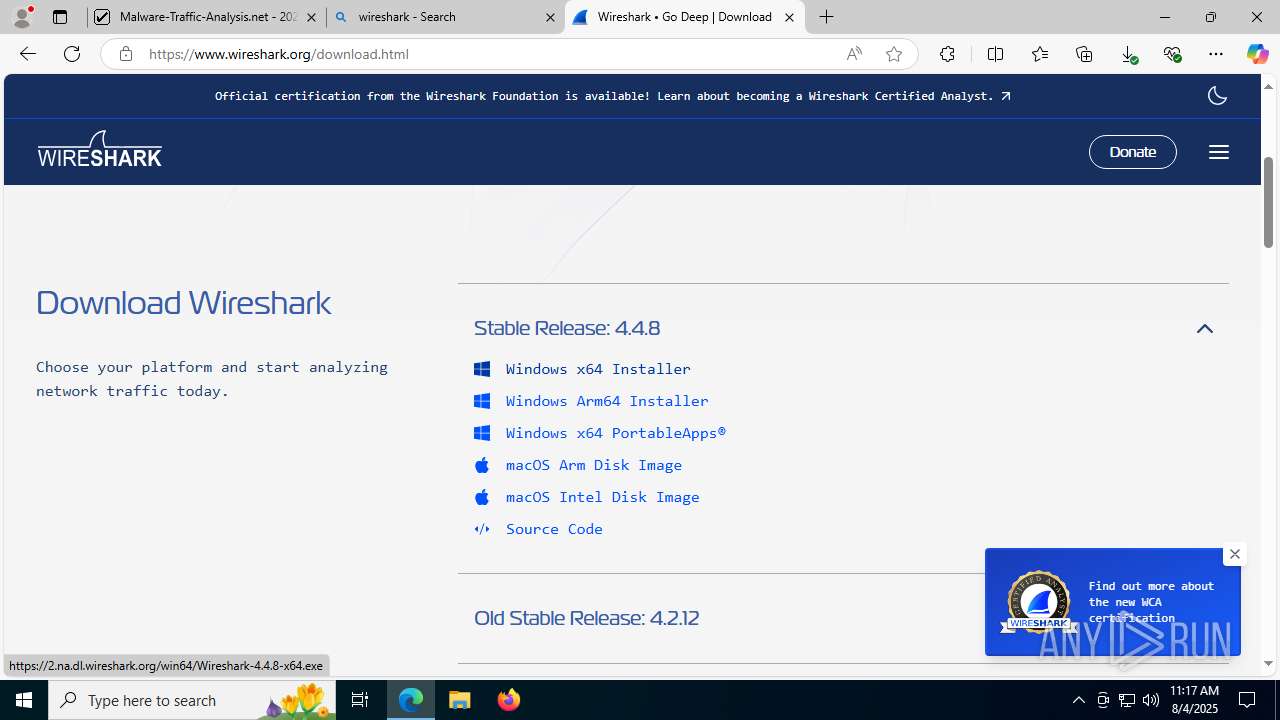
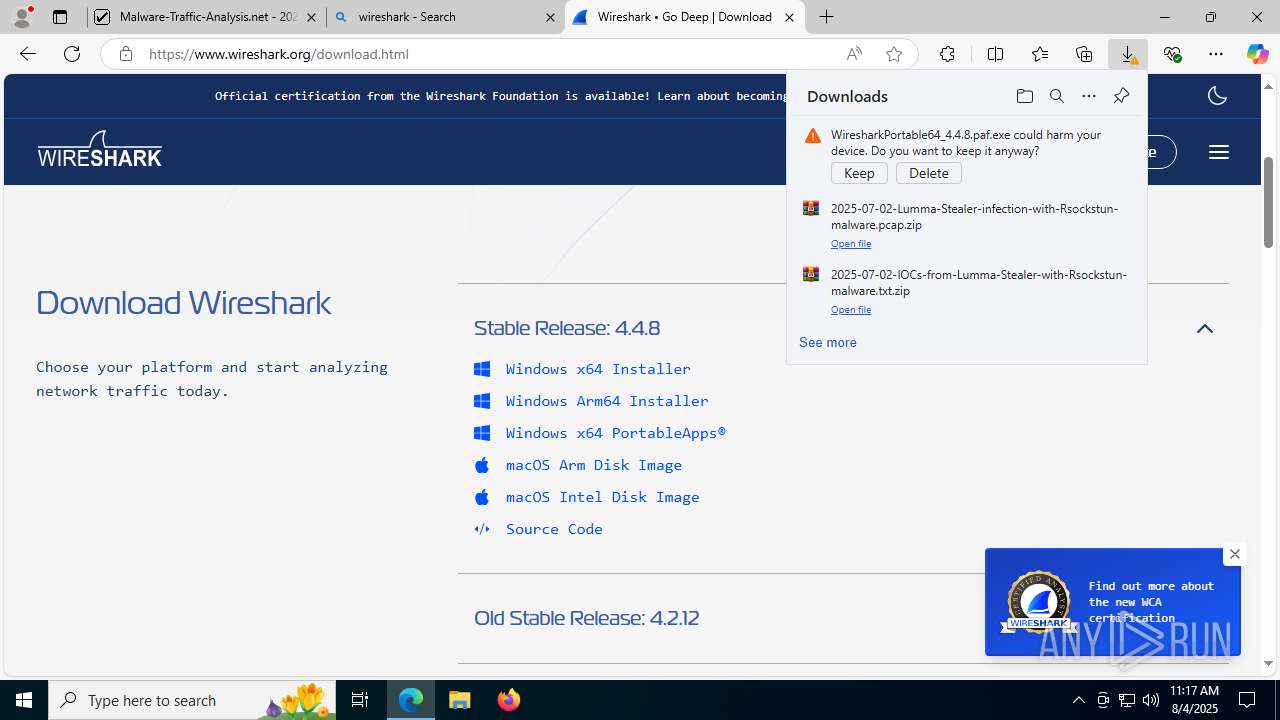
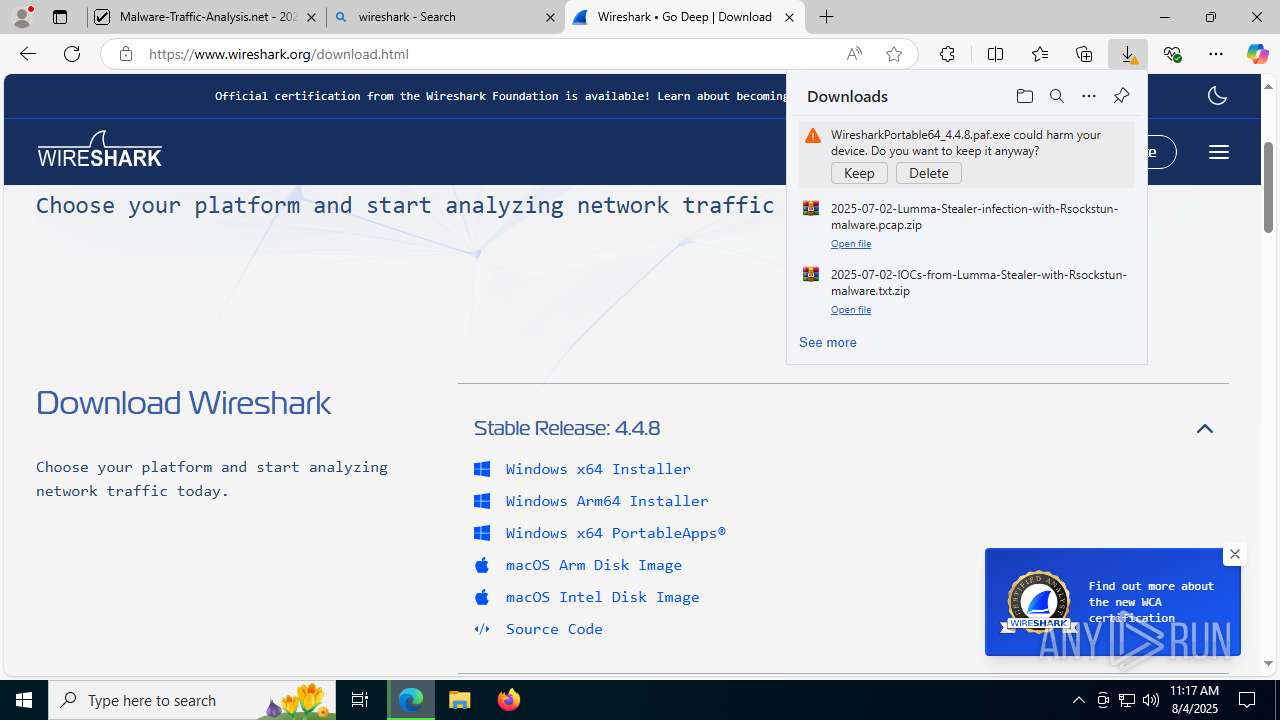
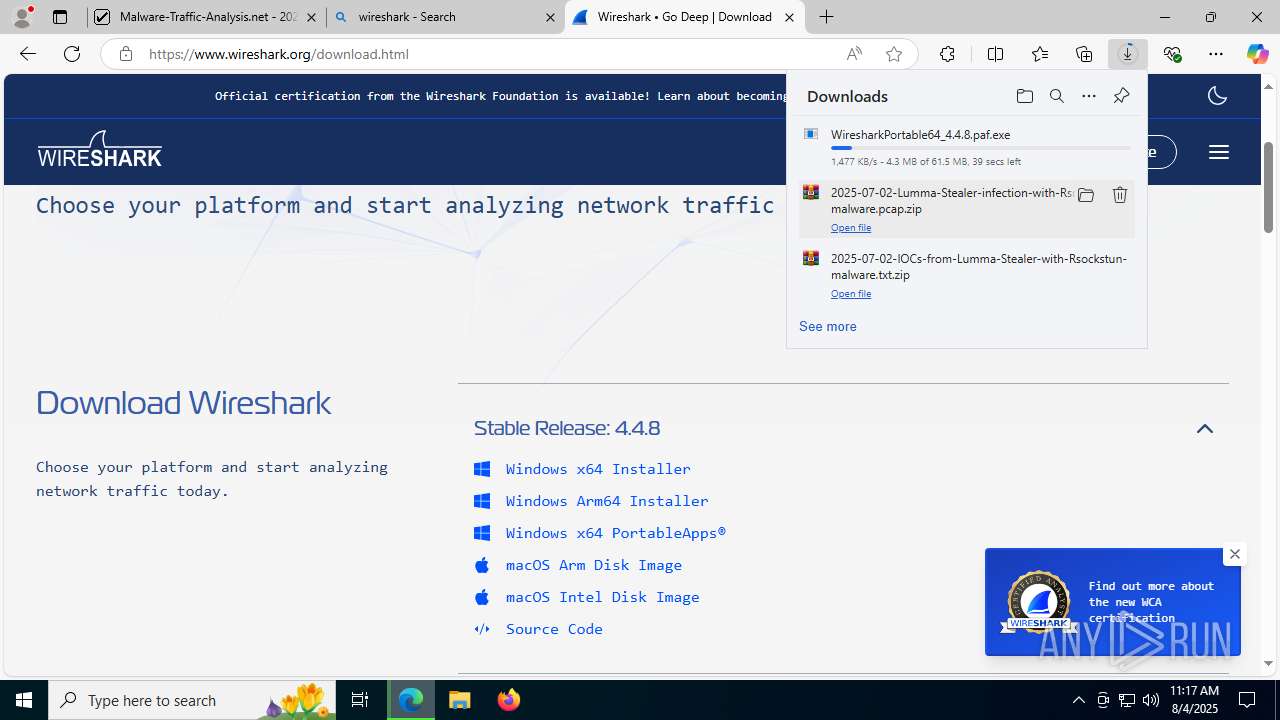
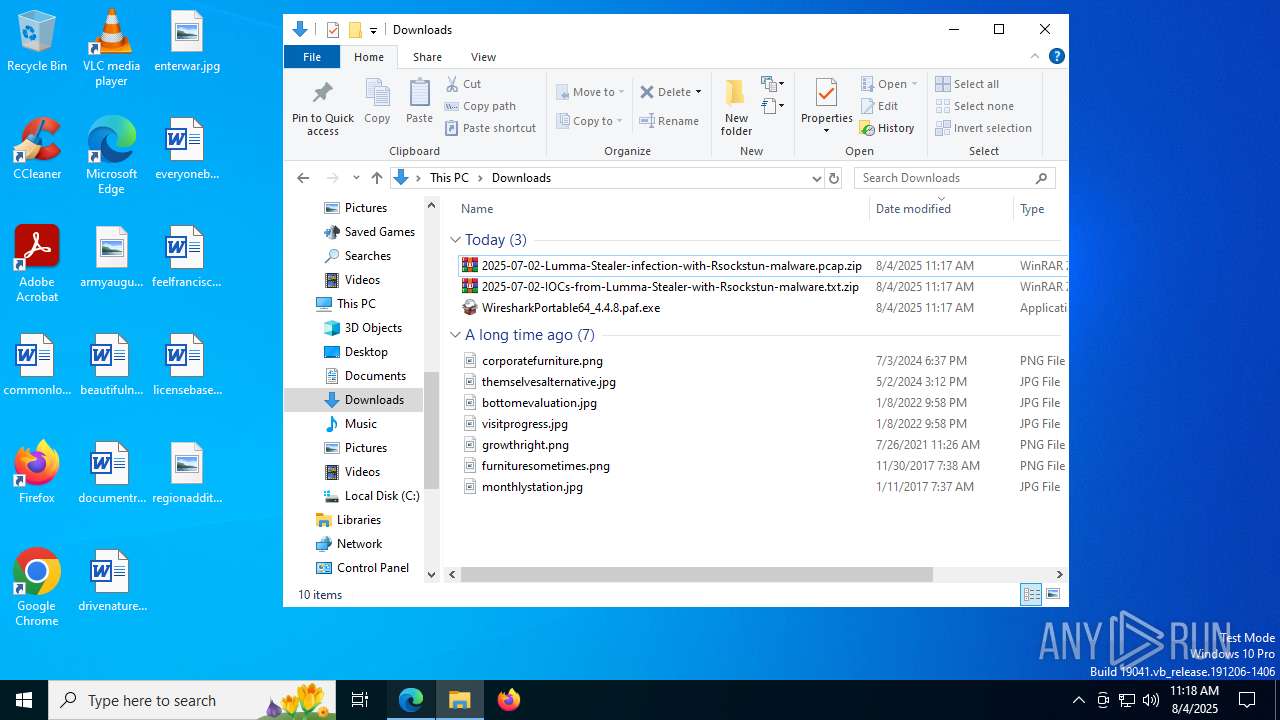
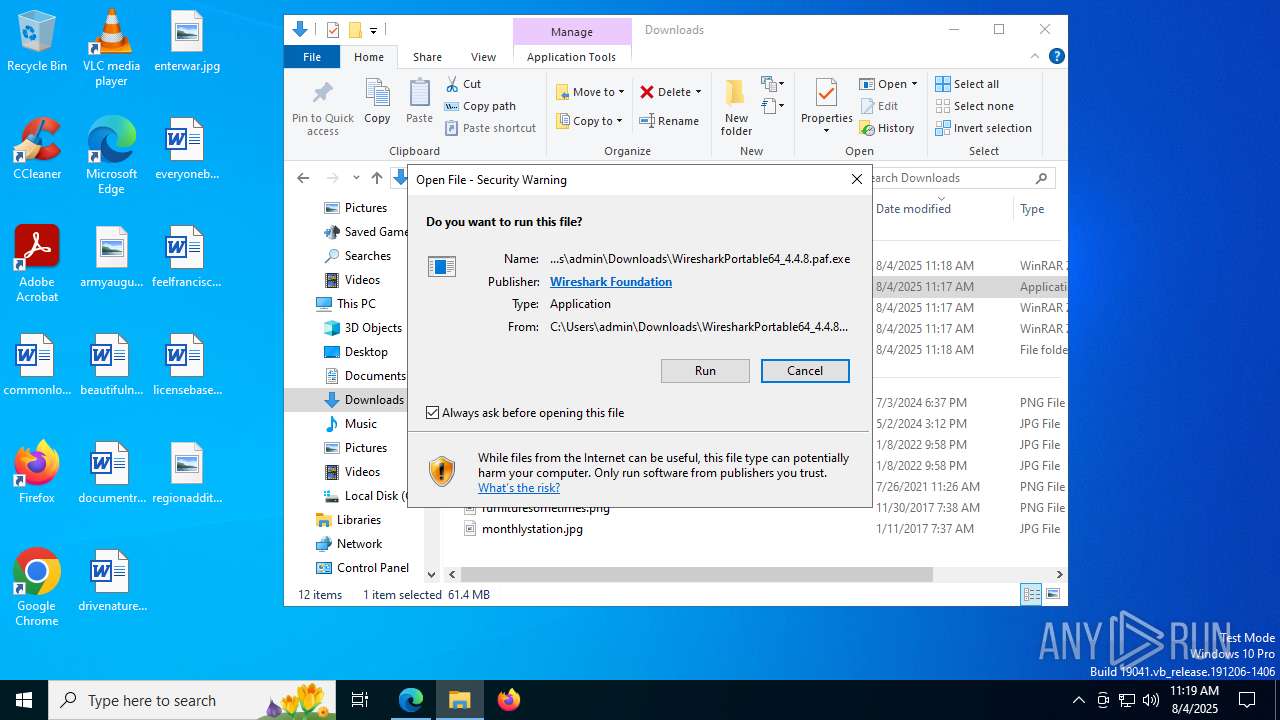
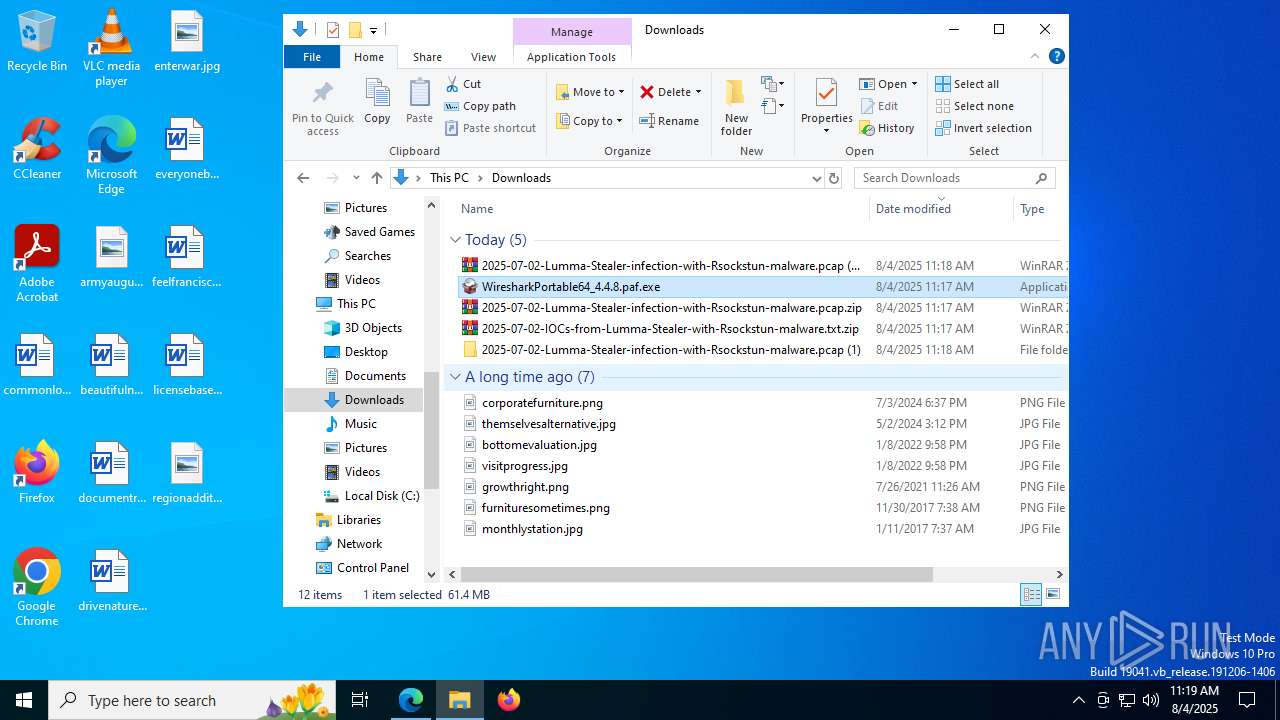
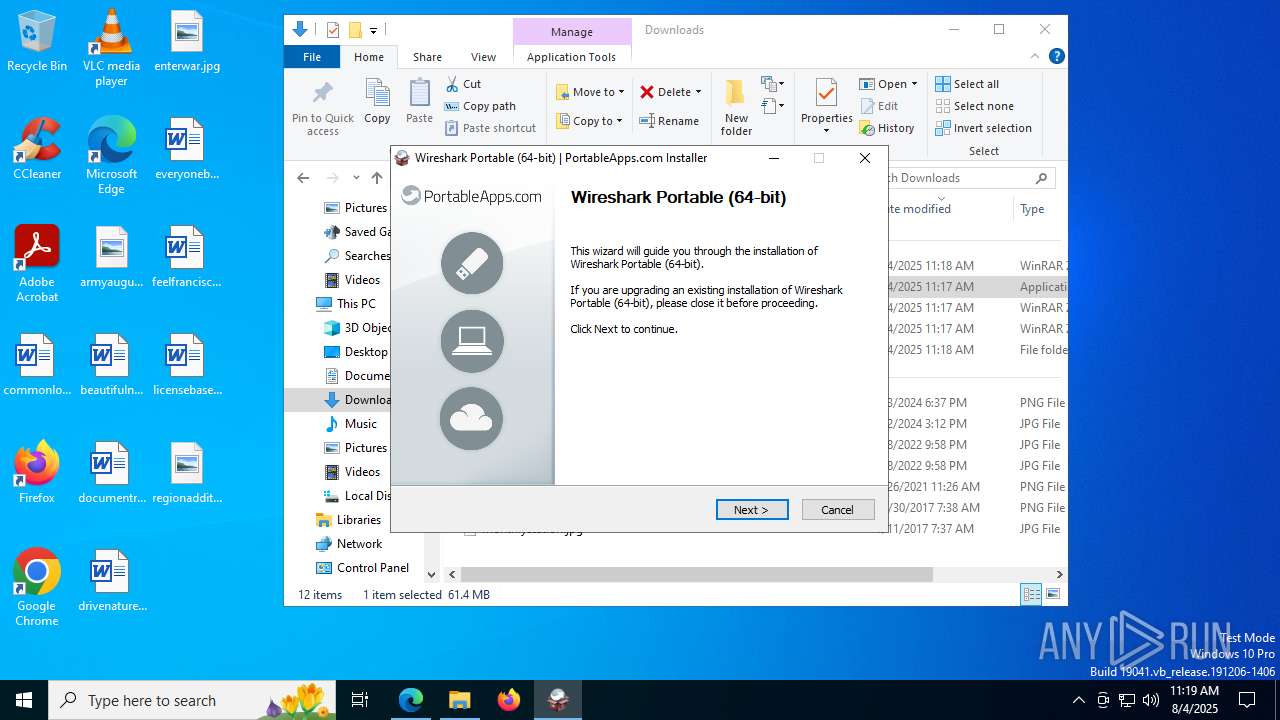
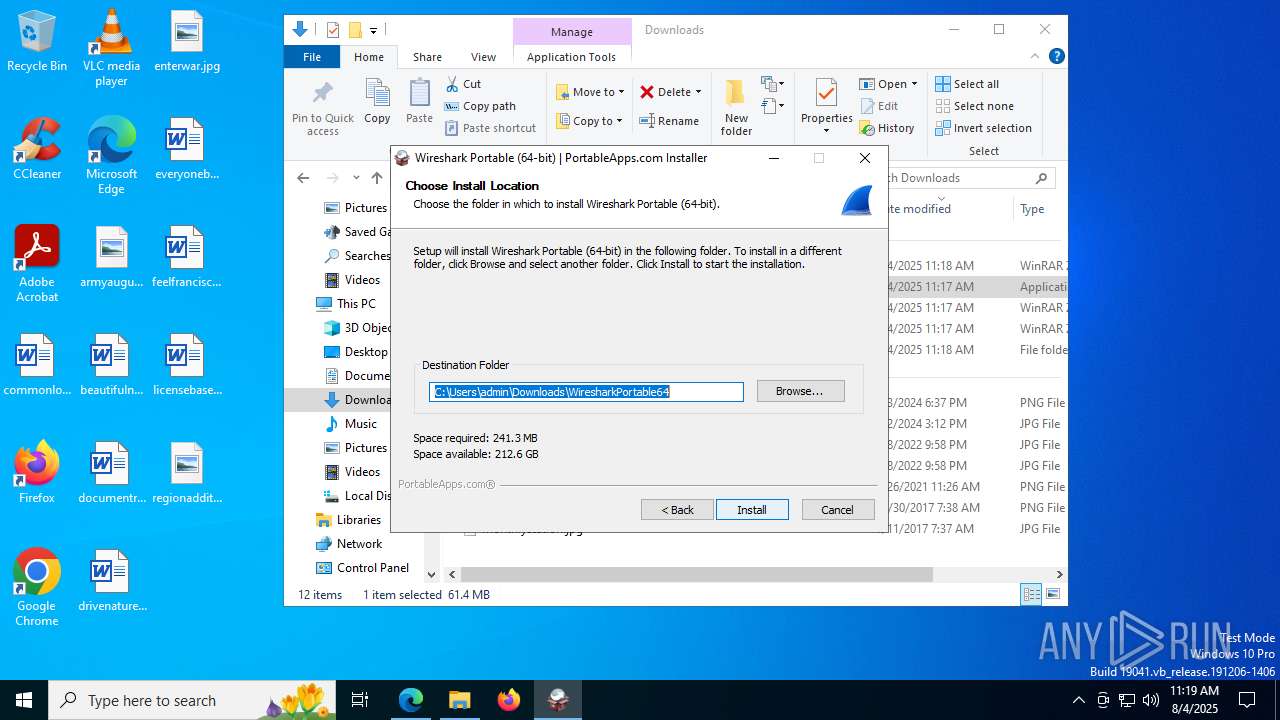
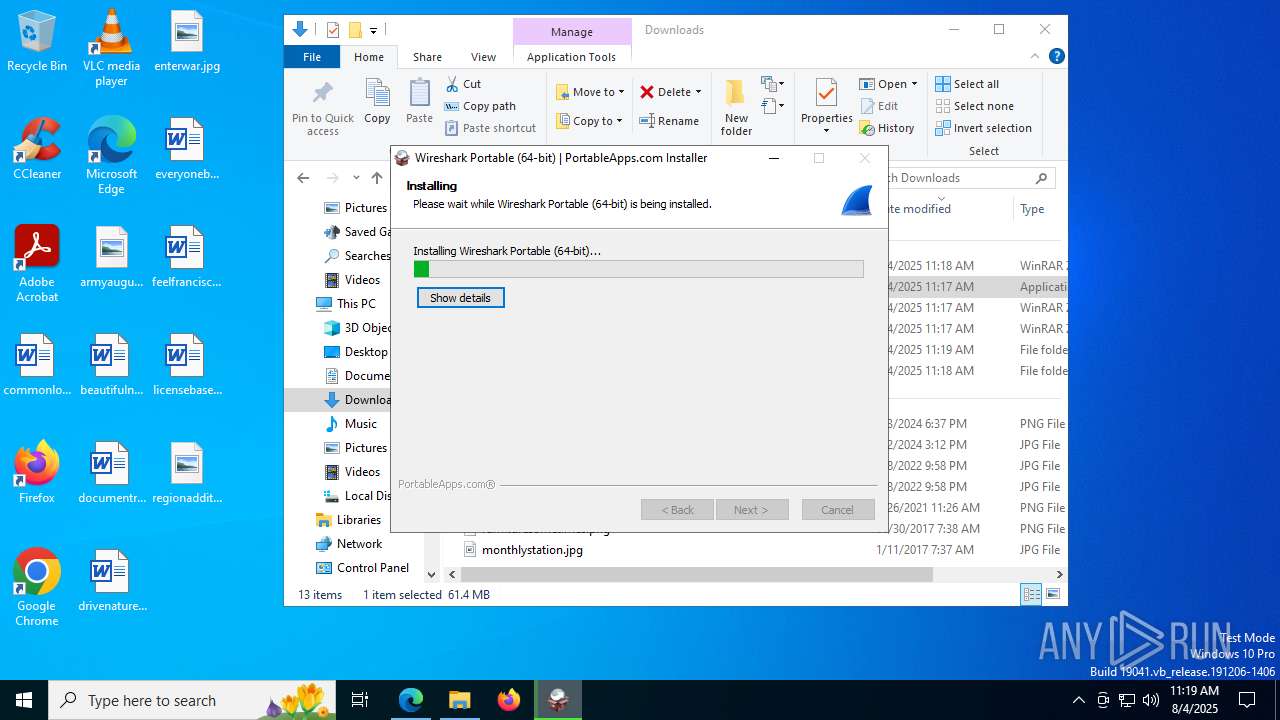
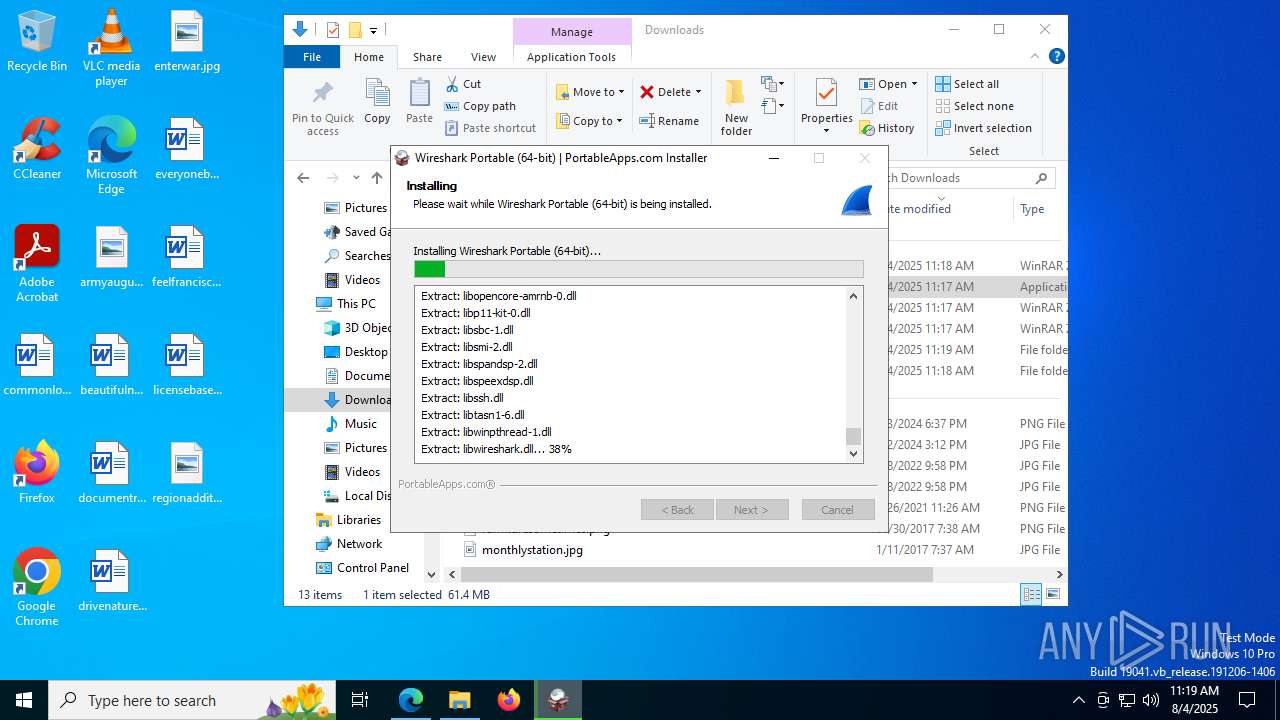
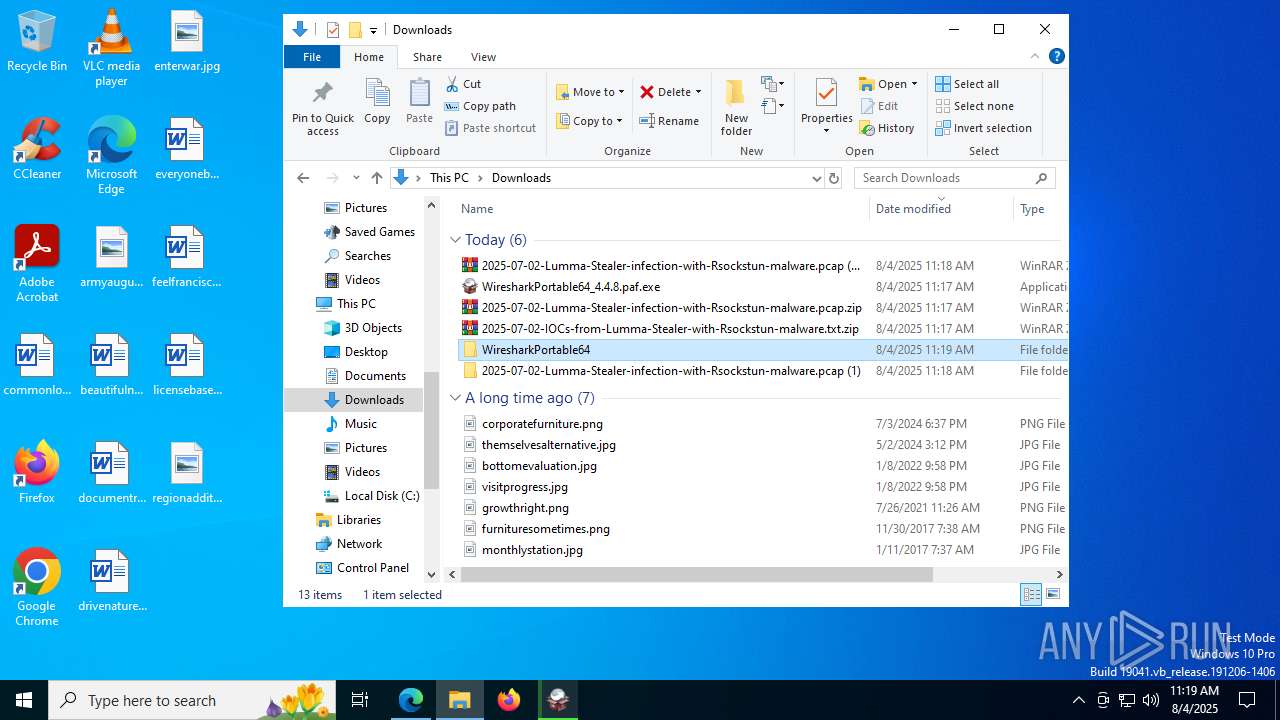
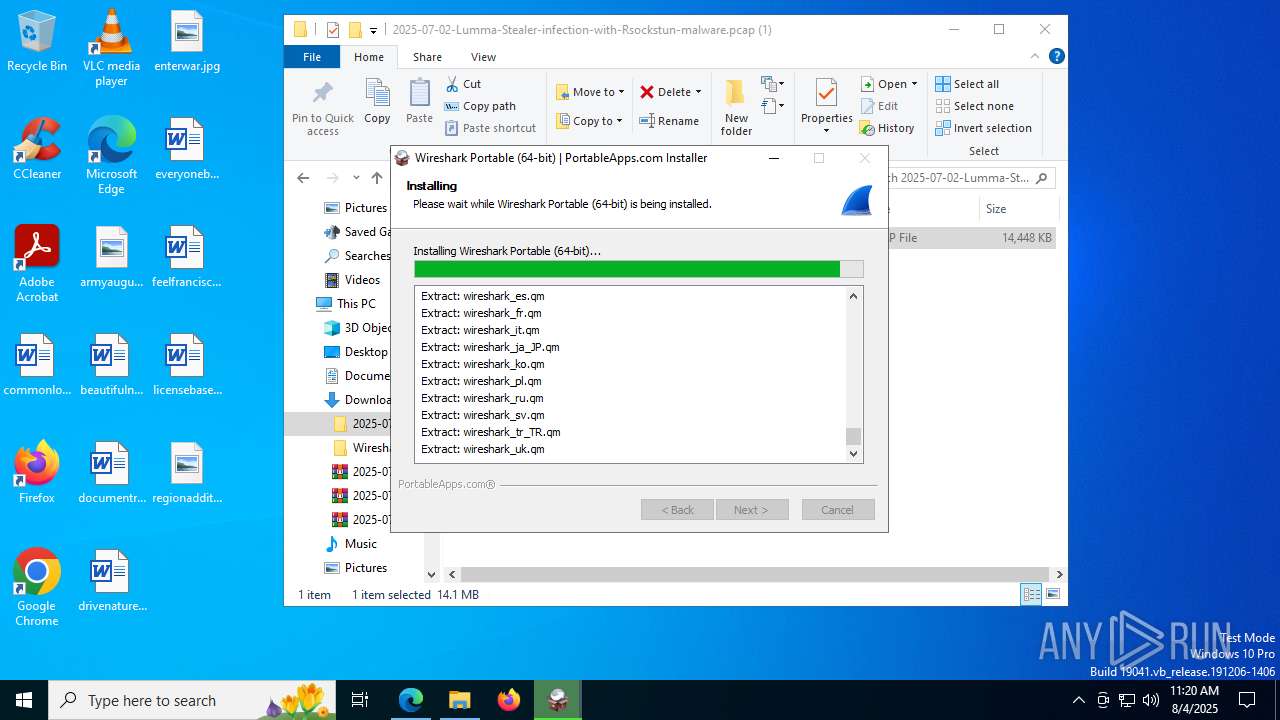
Executable content was dropped or overwritten
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
The process creates files with name similar to system file names
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
Process drops legitimate windows executable
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
Malware-specific behavior (creating "System.dll" in Temp)
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
There is functionality for taking screenshot (YARA)
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
The process drops C-runtime libraries
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
Creates file in the systems drive root
- Wireshark.exe (PID: 6308)
INFO
Reads Environment values
- identity_helper.exe (PID: 7592)
Checks supported languages
- identity_helper.exe (PID: 7592)
- ShellExperienceHost.exe (PID: 1136)
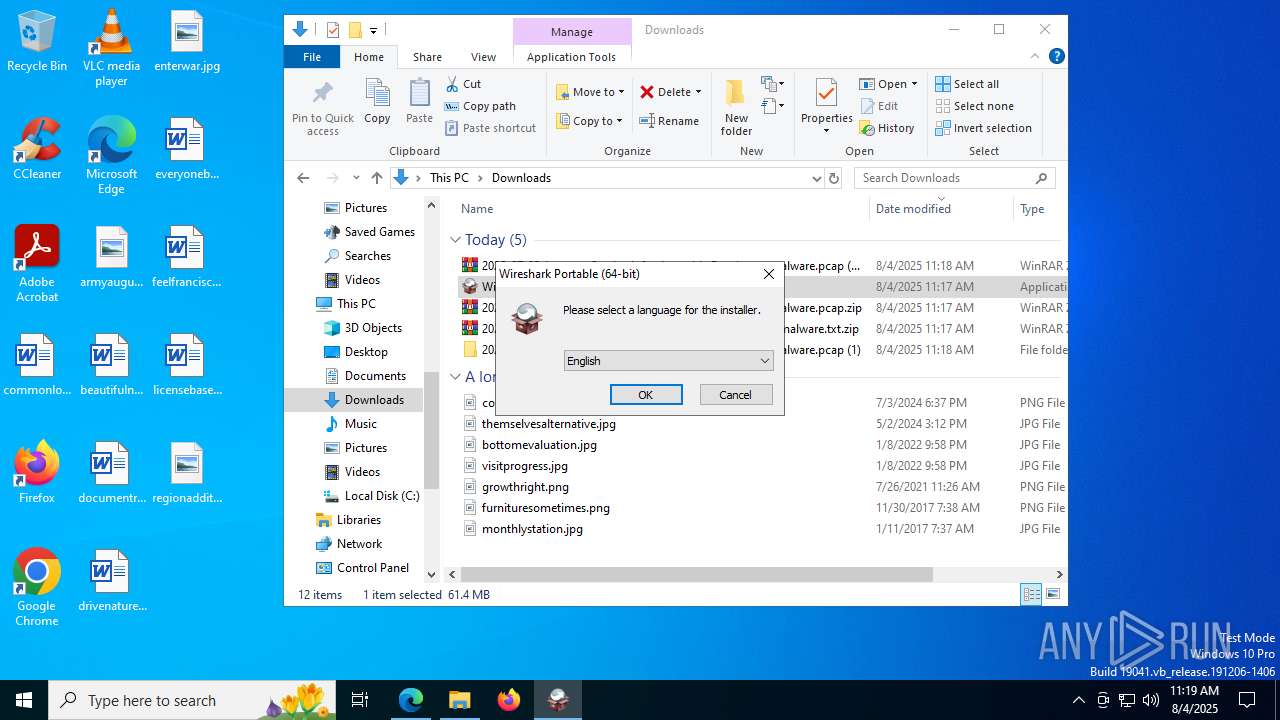
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
- Wireshark.exe (PID: 6308)
- androiddump.exe (PID: 8244)
- randpktdump.exe (PID: 9480)
- sshdump.exe (PID: 9572)
- wifidump.exe (PID: 9140)
- etwdump.exe (PID: 4456)
- ciscodump.exe (PID: 8520)
- randpktdump.exe (PID: 9068)
- ciscodump.exe (PID: 4844)
- udpdump.exe (PID: 8232)
- etwdump.exe (PID: 8584)
- sshdump.exe (PID: 7292)
- udpdump.exe (PID: 6856)
- wifidump.exe (PID: 1100)
- udpdump.exe (PID: 9564)
- dumpcap.exe (PID: 9752)
- etwdump.exe (PID: 3936)
- wifidump.exe (PID: 8712)
- randpktdump.exe (PID: 420)
- ciscodump.exe (PID: 8272)
- sshdump.exe (PID: 4232)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4772)
- firefox.exe (PID: 8004)
- msedge.exe (PID: 6948)
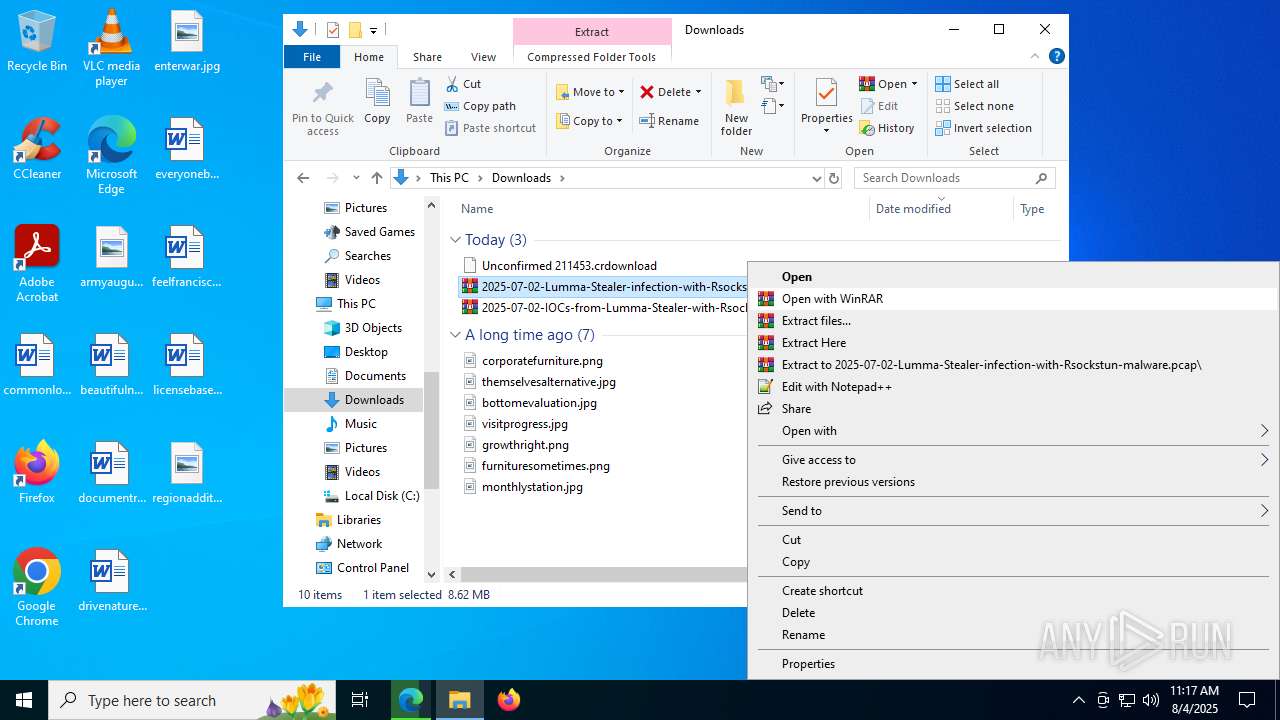
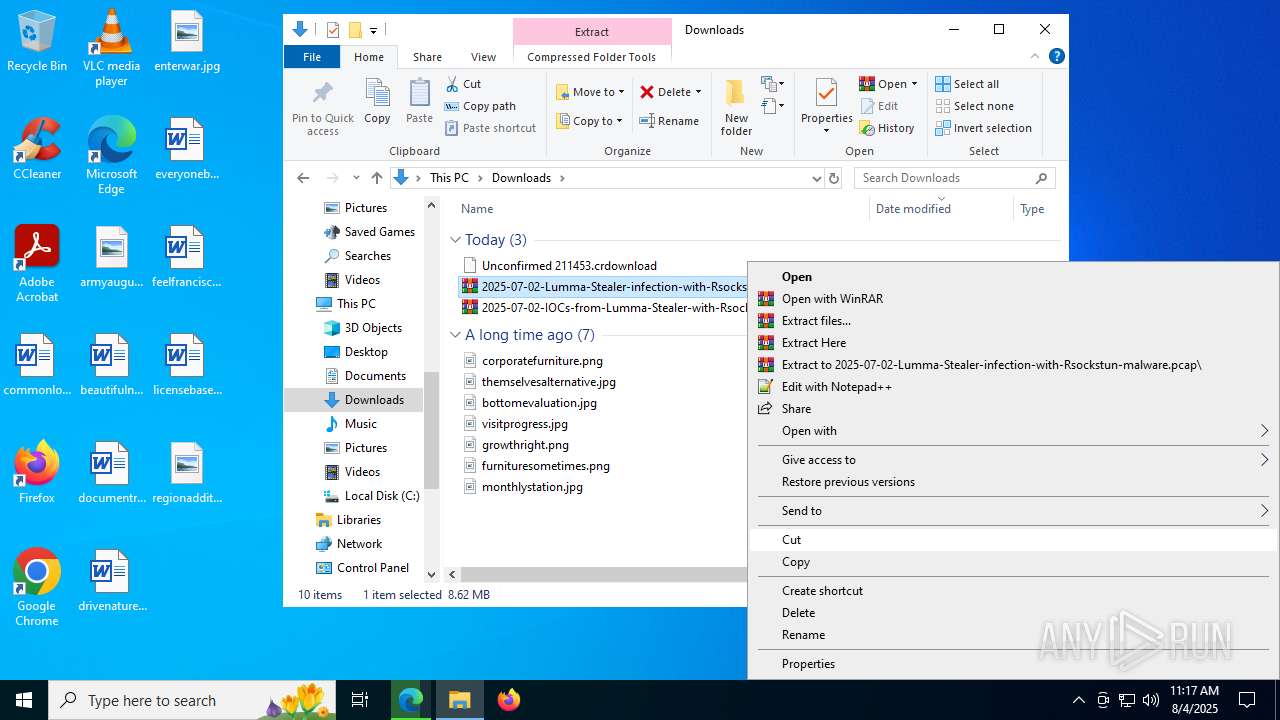
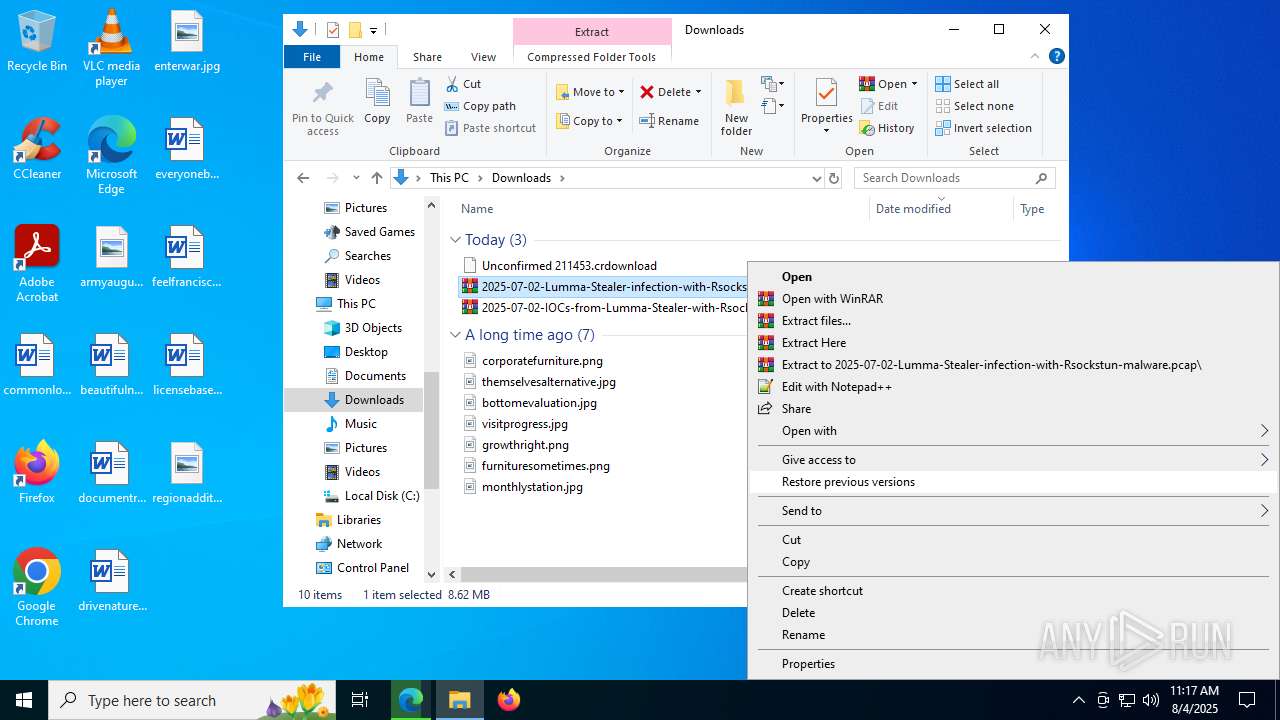
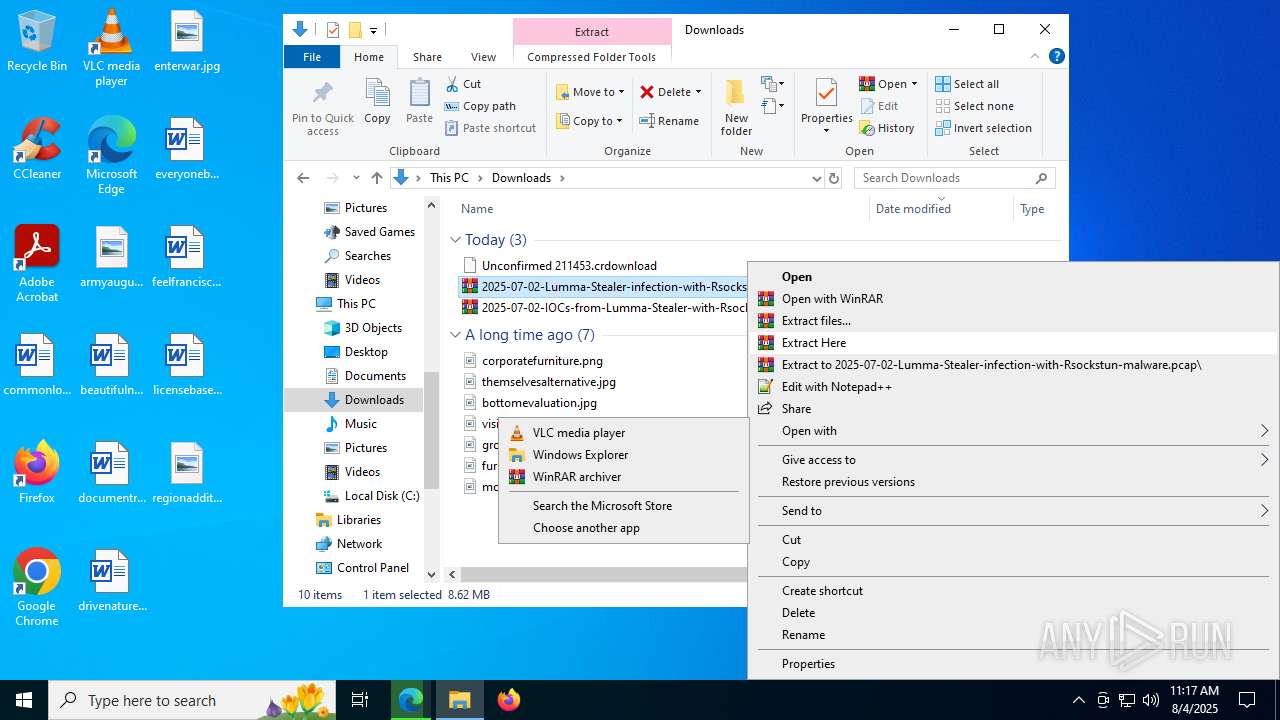
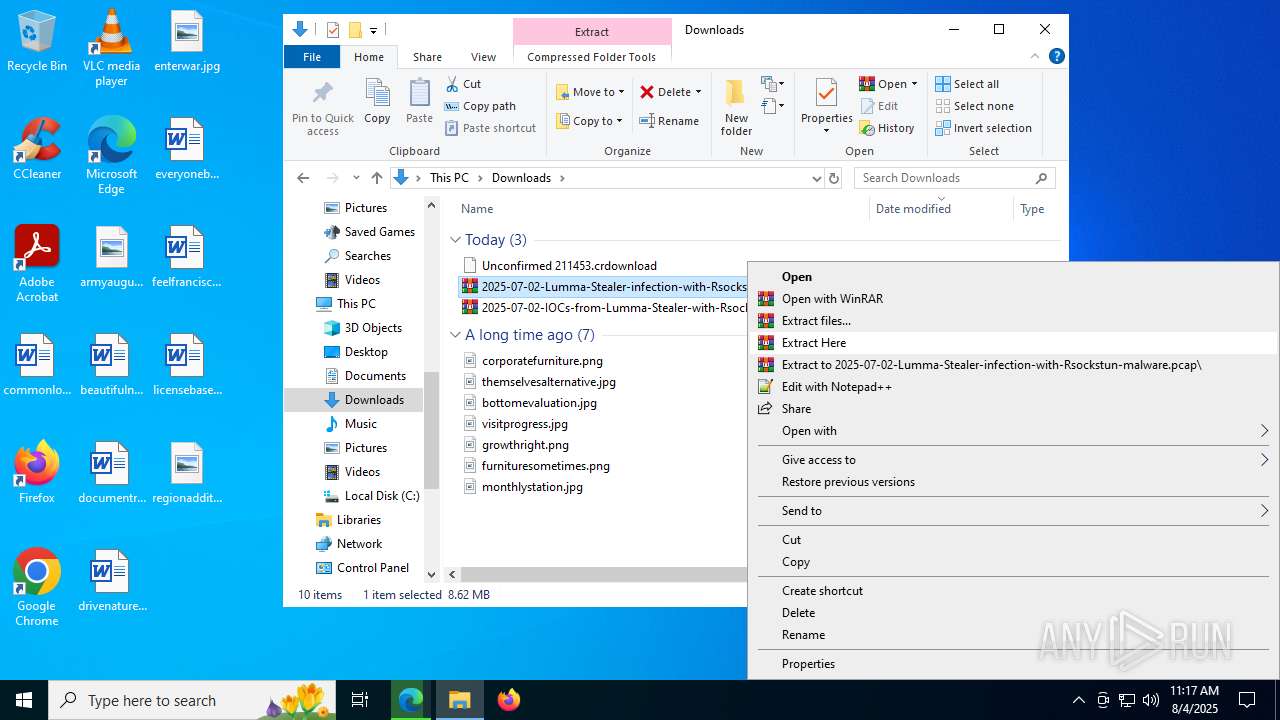
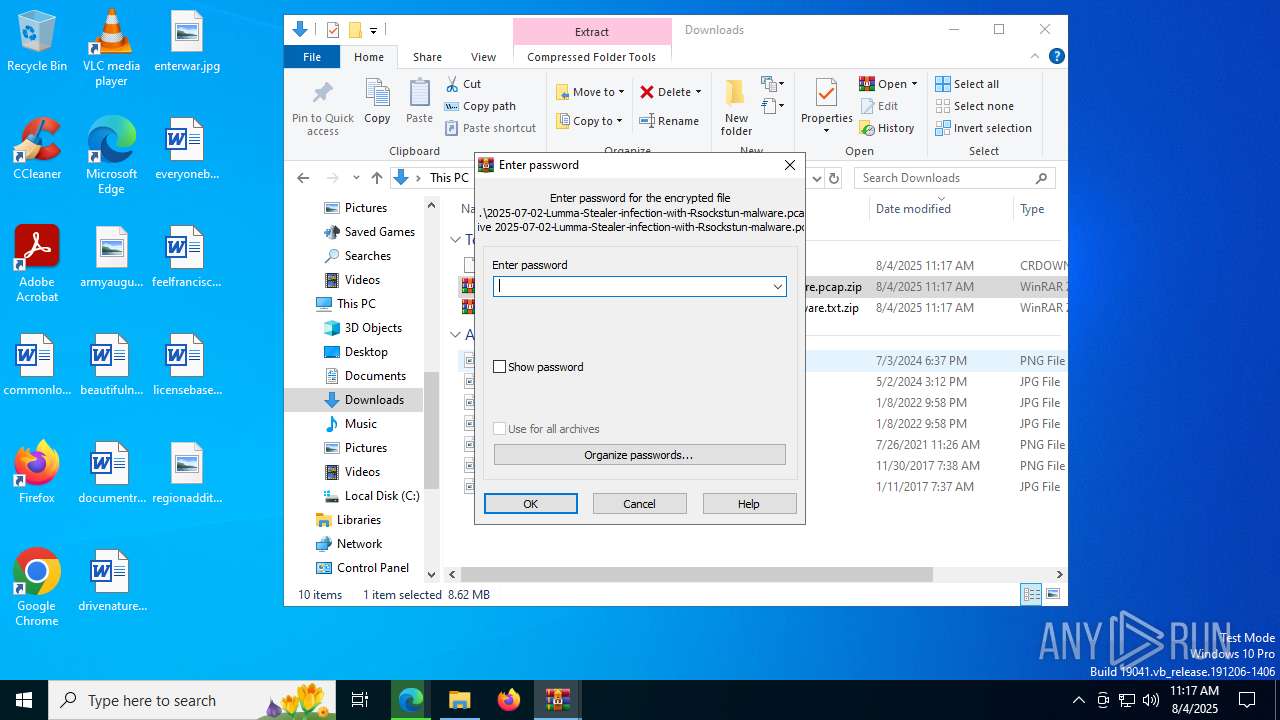
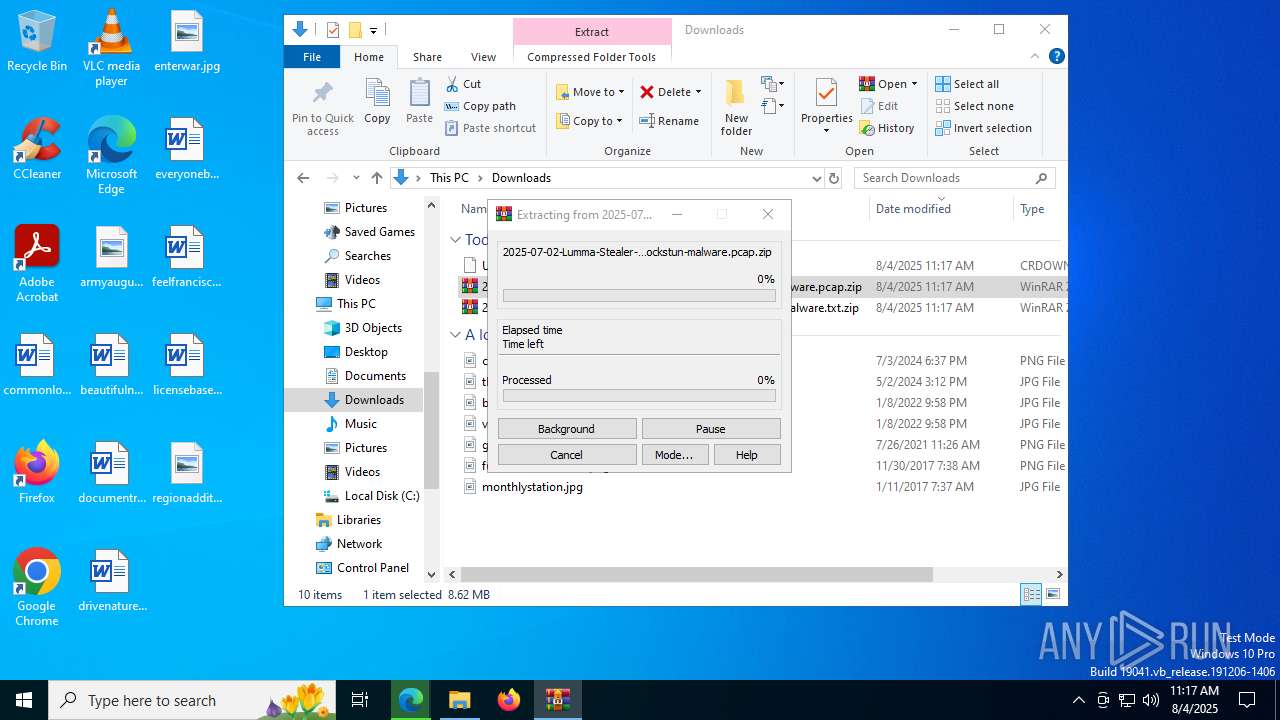
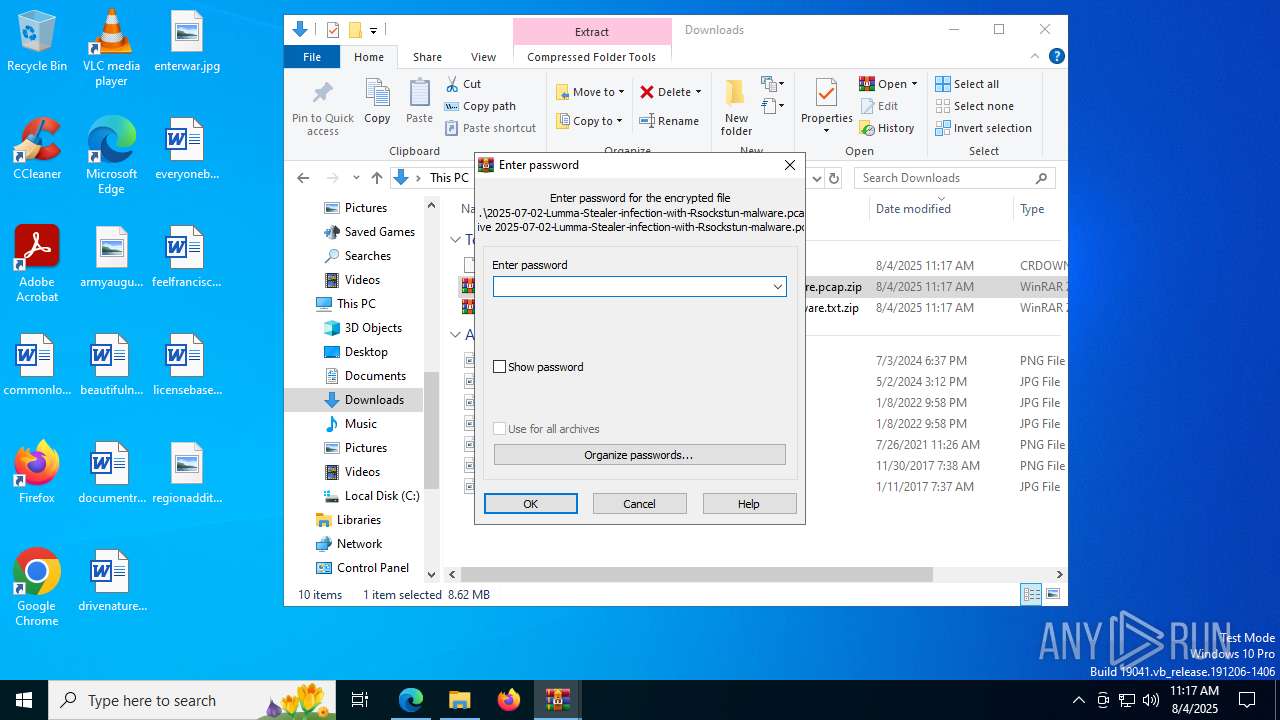
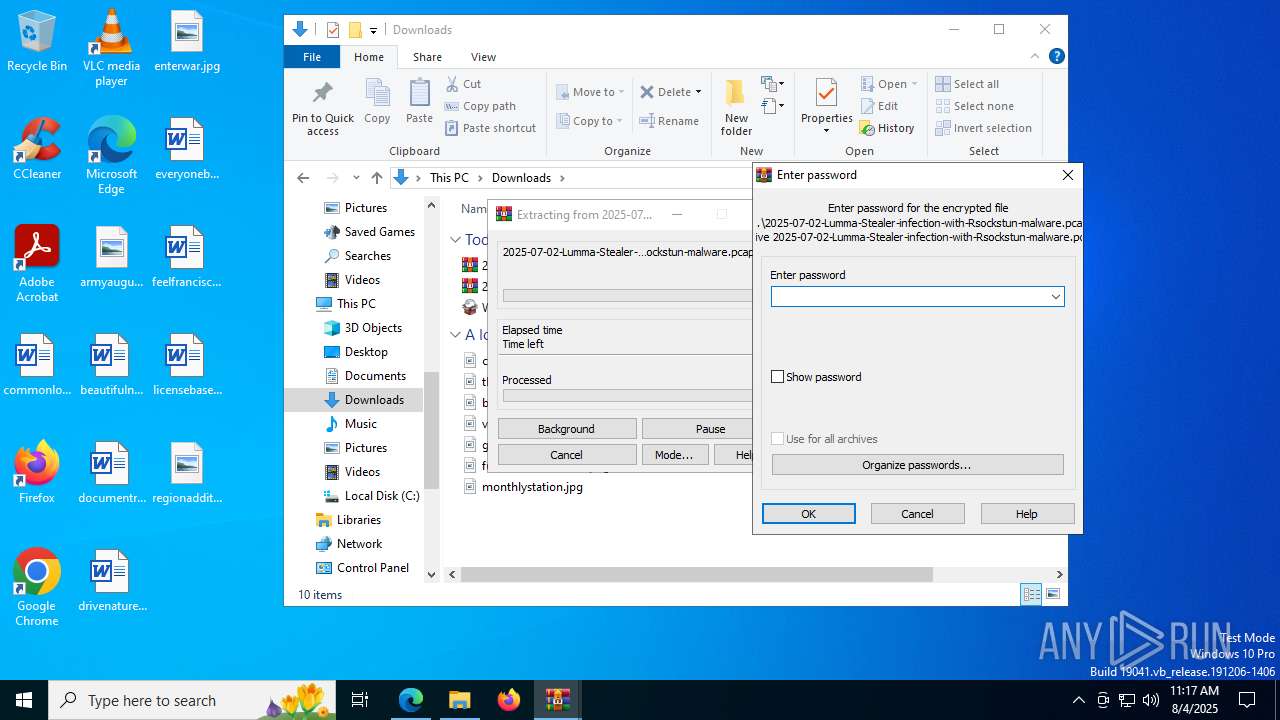
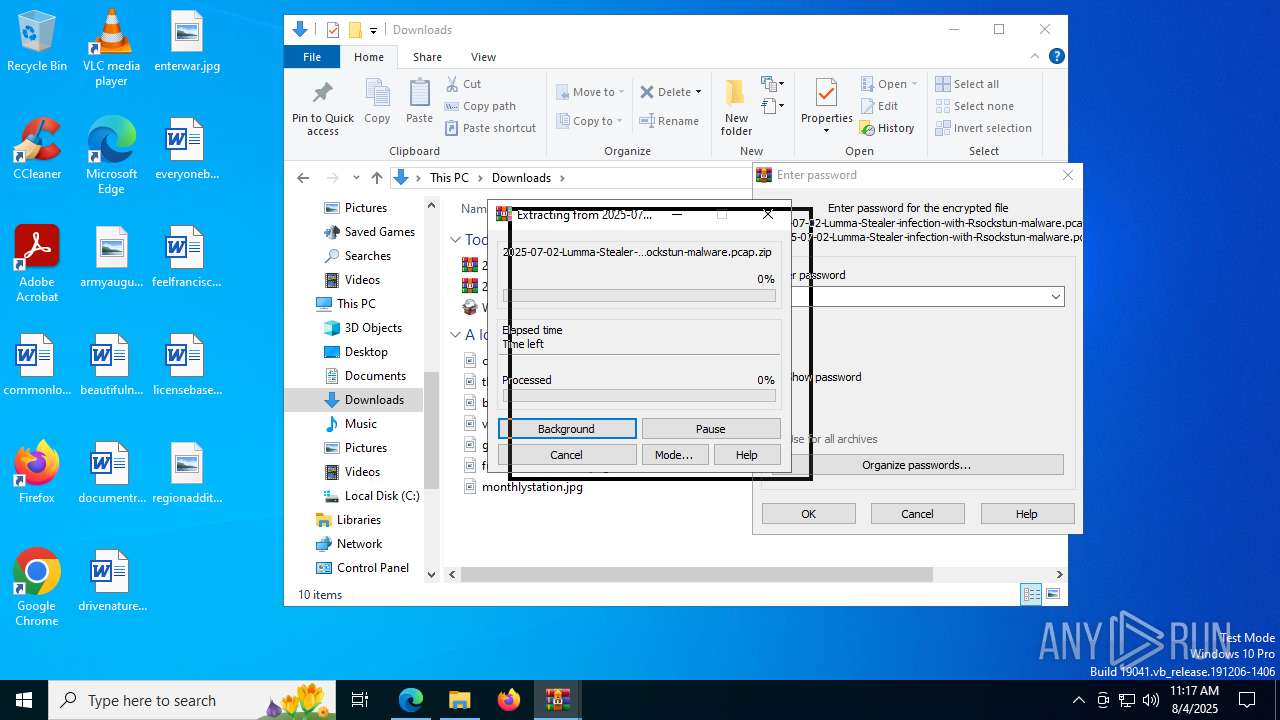
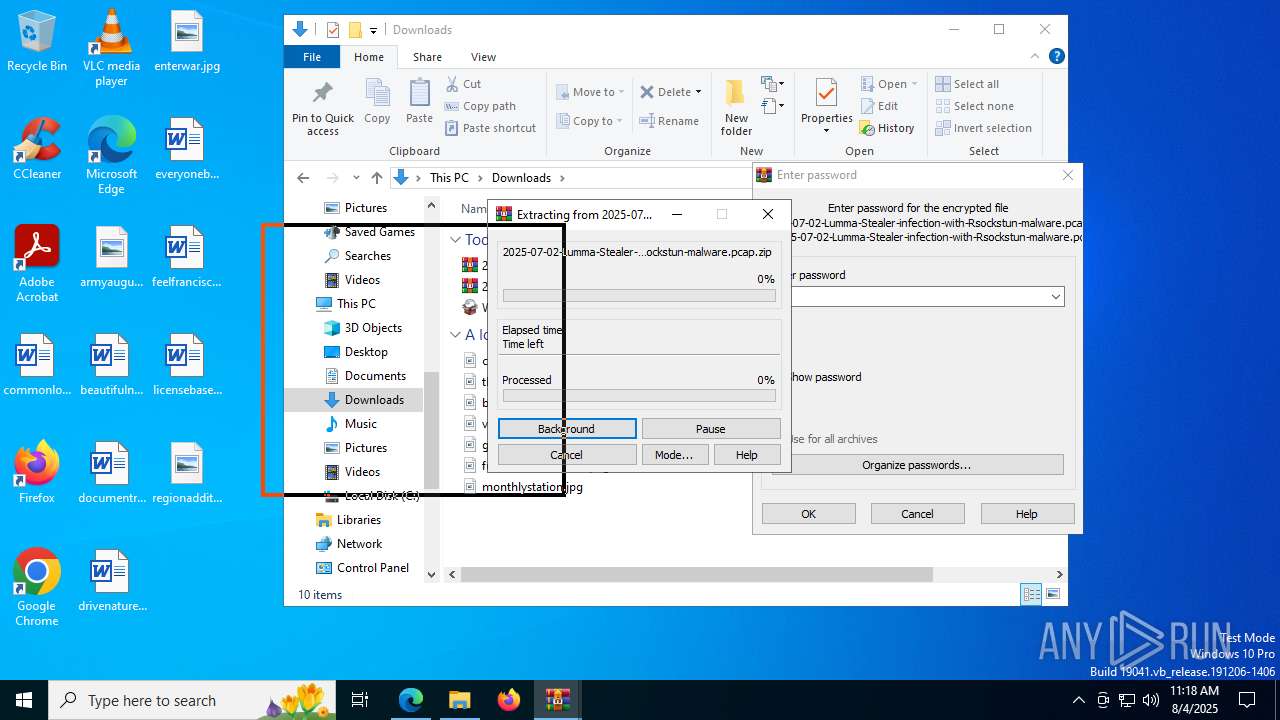
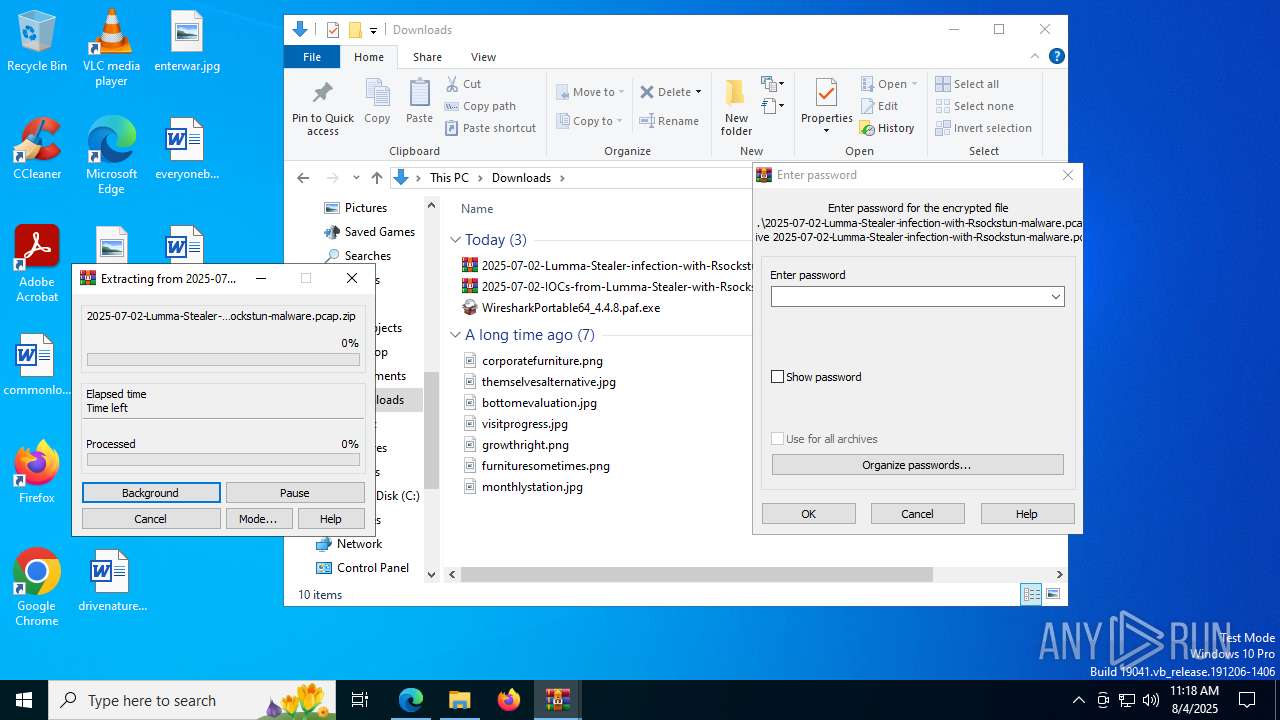
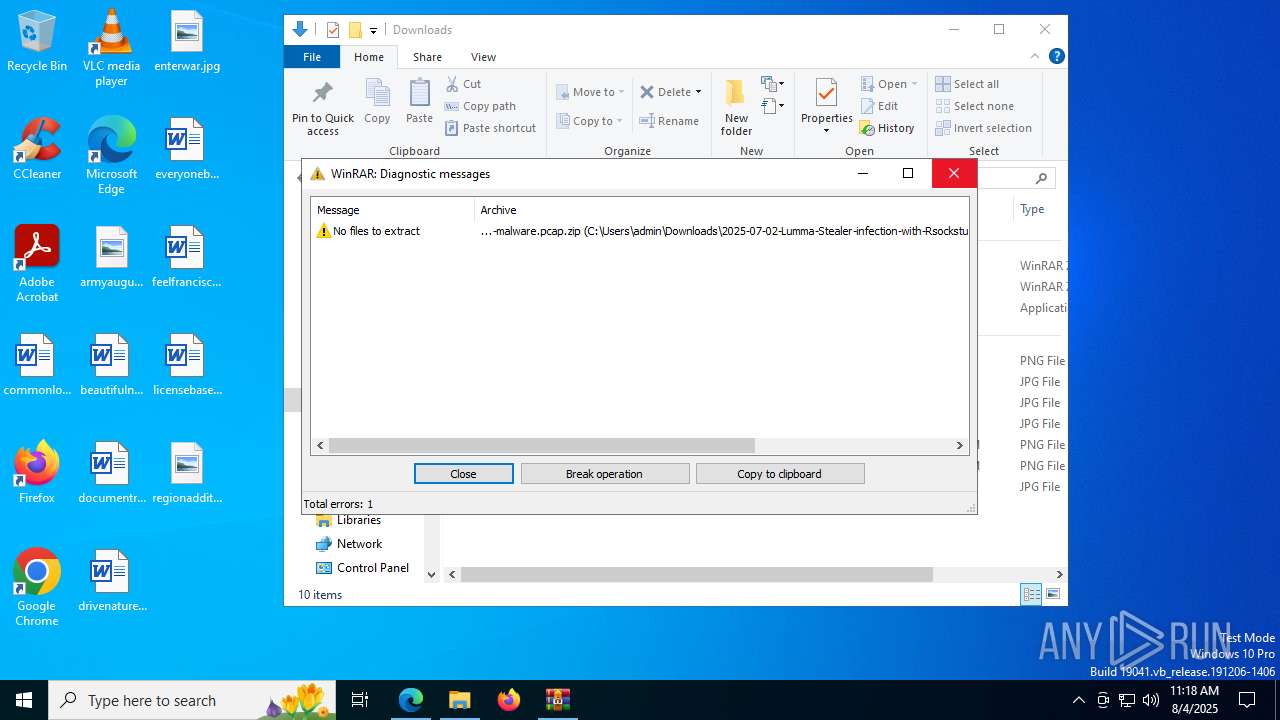
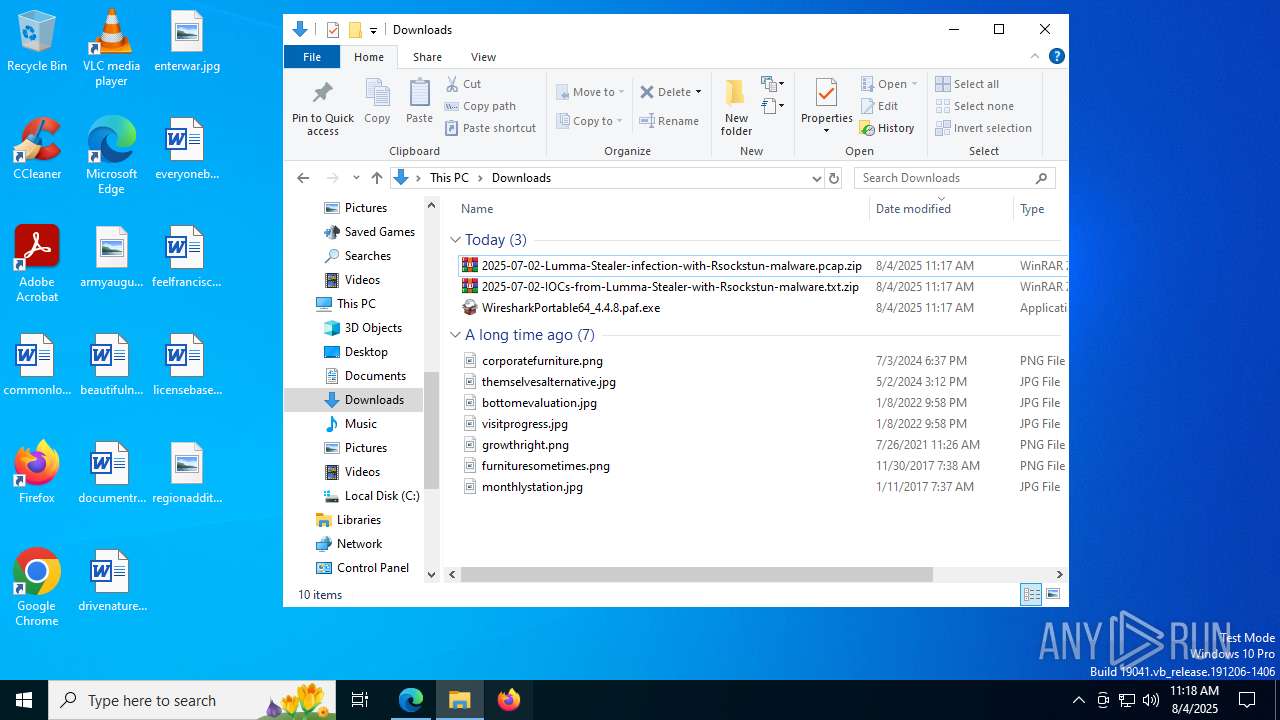
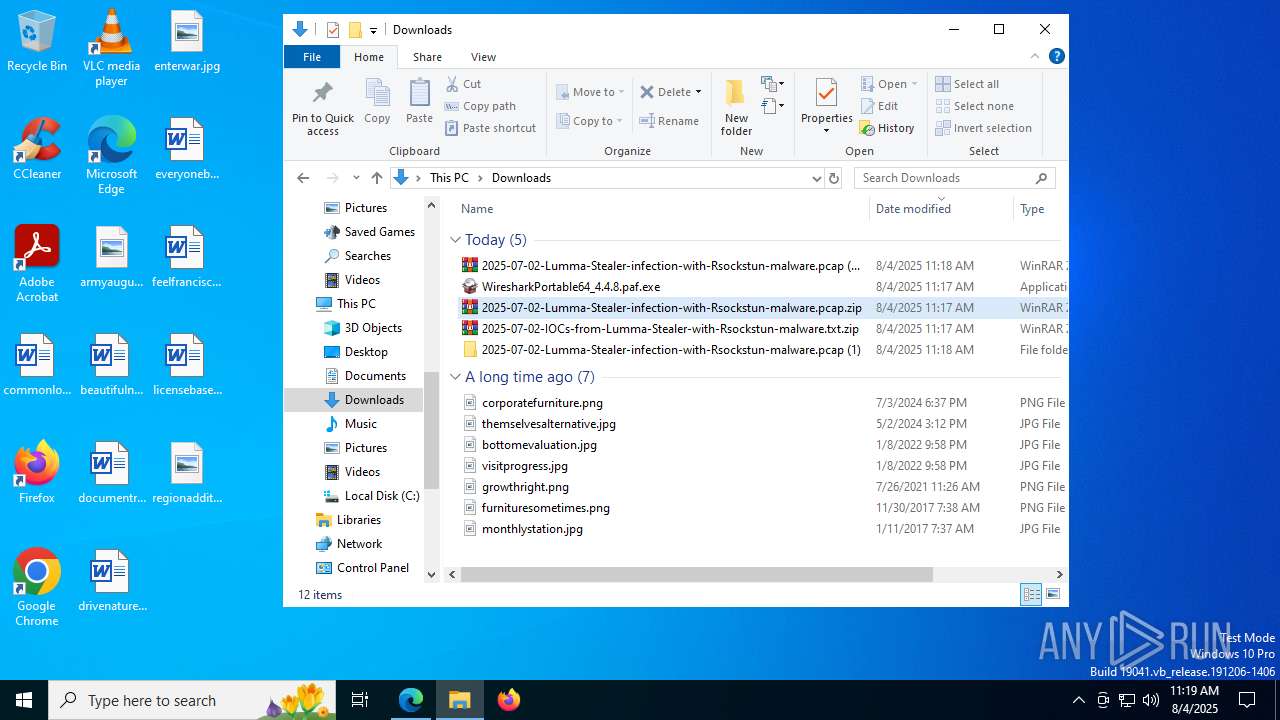
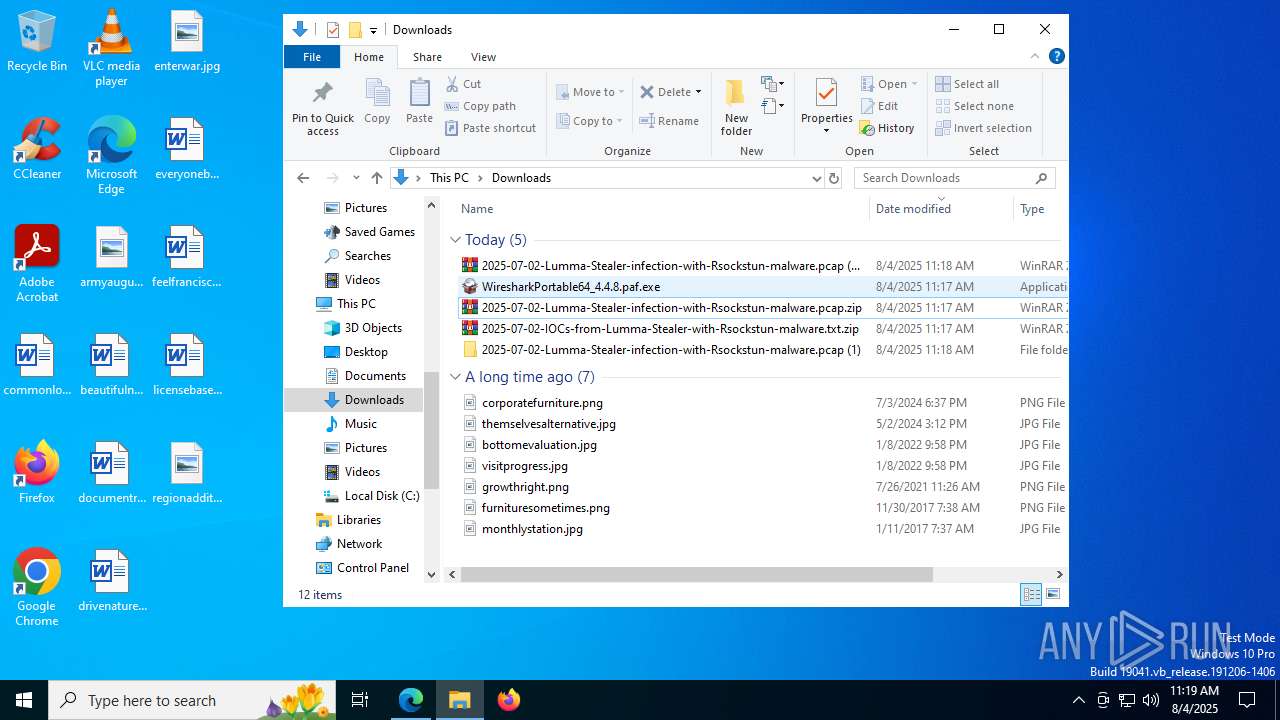
Manual execution by a user
- WinRAR.exe (PID: 7736)
- firefox.exe (PID: 7984)
Application launched itself
- firefox.exe (PID: 7984)
- firefox.exe (PID: 8004)
- msedge.exe (PID: 6948)
Reads the computer name
- ShellExperienceHost.exe (PID: 1136)
- identity_helper.exe (PID: 7592)
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
- Wireshark.exe (PID: 6308)
- sshdump.exe (PID: 7292)
- ciscodump.exe (PID: 8520)
Checks proxy server information
- slui.exe (PID: 5824)
- explorer.exe (PID: 4772)
- Wireshark.exe (PID: 6308)
Reads the software policy settings
- slui.exe (PID: 5824)
- explorer.exe (PID: 4772)
- Wireshark.exe (PID: 6308)
Creates files or folders in the user directory
- explorer.exe (PID: 4772)
- Wireshark.exe (PID: 6308)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
Create files in a temporary directory
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
- WiresharkPortable64.exe (PID: 1268)
The sample compiled with english language support
- WiresharkPortable64_4.4.8.paf.exe (PID: 8408)
Reads CPU info
- Wireshark.exe (PID: 6308)
- dumpcap.exe (PID: 9752)
Reads the machine GUID from the registry
- Wireshark.exe (PID: 6308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
146
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Users\admin\Downloads\WiresharkPortable64\App\Wireshark\extcap\randpktdump.exe" --extcap-dlts --extcap-interface randpkt | C:\Users\admin\Downloads\WiresharkPortable64\App\Wireshark\extcap\randpktdump.exe | — | Wireshark.exe | |||||||||||
User: admin Company: The Wireshark developer community Integrity Level: MEDIUM Description: randpktdump Exit code: 0 Version: 4.4.8 Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | "C:\Users\admin\Downloads\WiresharkPortable64\App\Wireshark\extcap\wifidump.exe" --extcap-dlts --extcap-interface wifidump.exe | C:\Users\admin\Downloads\WiresharkPortable64\App\Wireshark\extcap\wifidump.exe | — | Wireshark.exe | |||||||||||
User: admin Company: The Wireshark developer community Integrity Level: MEDIUM Description: Wifidump Exit code: 0 Version: 4.4.8 Modules
| |||||||||||||||
| 1136 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | "C:\Users\admin\Downloads\WiresharkPortable64\WiresharkPortable64.exe" | C:\Users\admin\Downloads\WiresharkPortable64\WiresharkPortable64.exe | WiresharkPortable64_4.4.8.paf.exe | ||||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: Wireshark Portable (64-bit) (PortableApps.com Launcher) Exit code: 0 Version: 2.2.3.0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc445df208,0x7ffc445df214,0x7ffc445df220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --always-read-main-dll --field-trial-handle=6100,i,1951081136202999266,18374699307286675602,262144 --variations-seed-version --mojo-platform-channel-handle=7848 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --always-read-main-dll --field-trial-handle=7832,i,1951081136202999266,18374699307286675602,262144 --variations-seed-version --mojo-platform-channel-handle=7952 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2552 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4072 -prefsLen 44823 -prefMapHandle 4076 -prefMapSize 272997 -jsInitHandle 4080 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4088 -initialChannelId {24691975-d620-4e91-849c-572911c97331} -parentPid 8004 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8004" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
90 165
Read events
89 869
Write events
268
Delete events
28
Modification events
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 70C151871E9A2F00 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000060312 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394002 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A0CC1B75-9F8E-4D0E-B680-24D7806BD02B} | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000C0230 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394002 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {39616703-D1CD-48BB-AD44-B69958C8EE85} | |||
| (PID) Process: | (6948) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
169
Suspicious files
796
Text files
1 297
Unknown types
170
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18dfdb.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18dfeb.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18dfeb.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18dfeb.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18dfdb.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
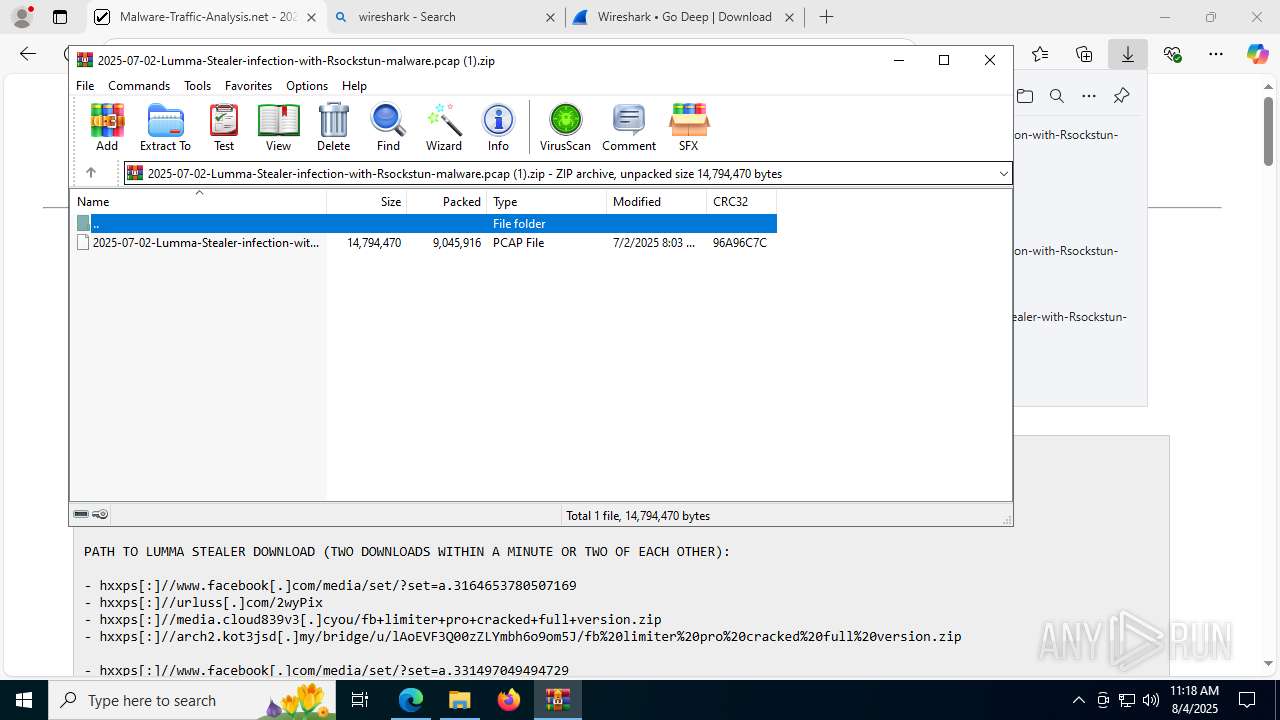
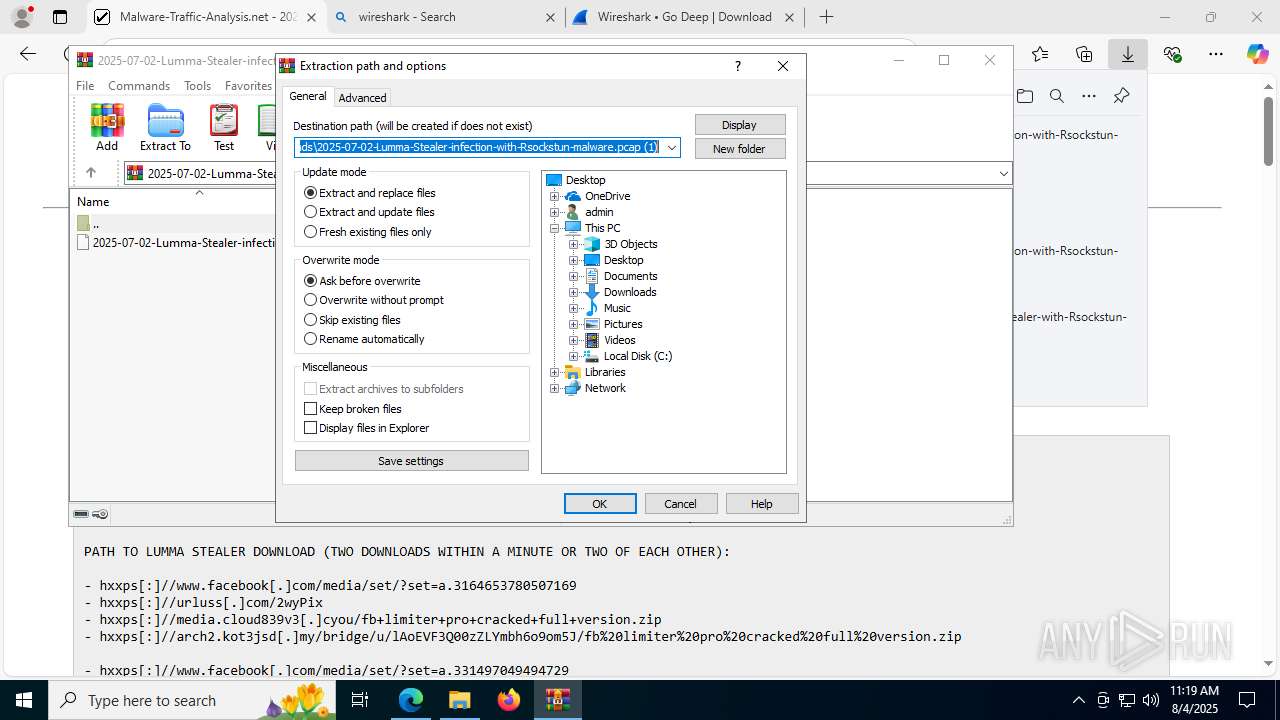
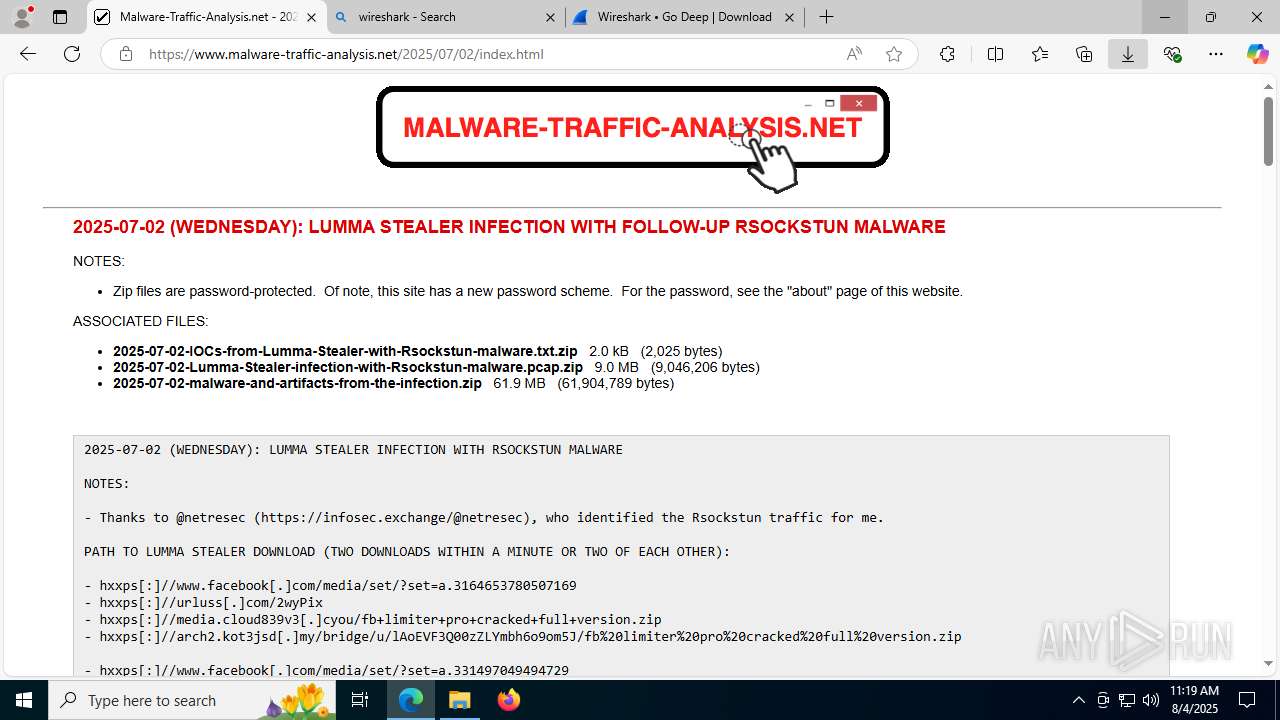
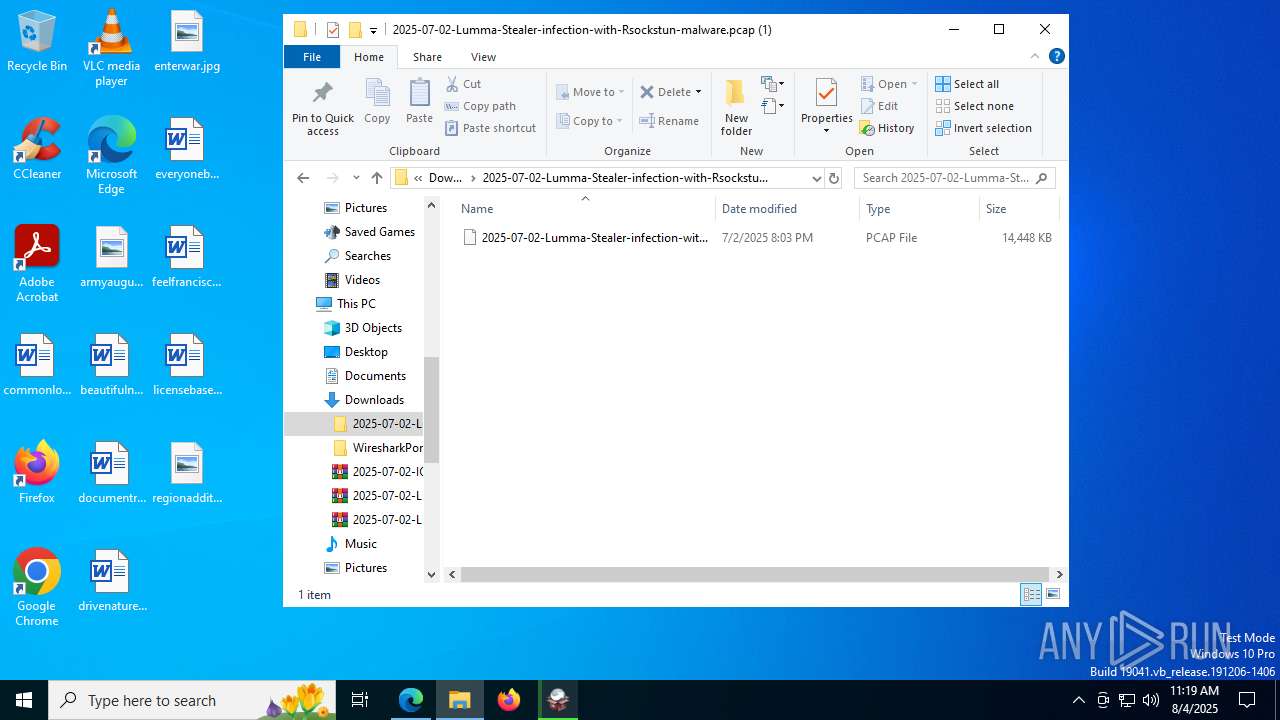
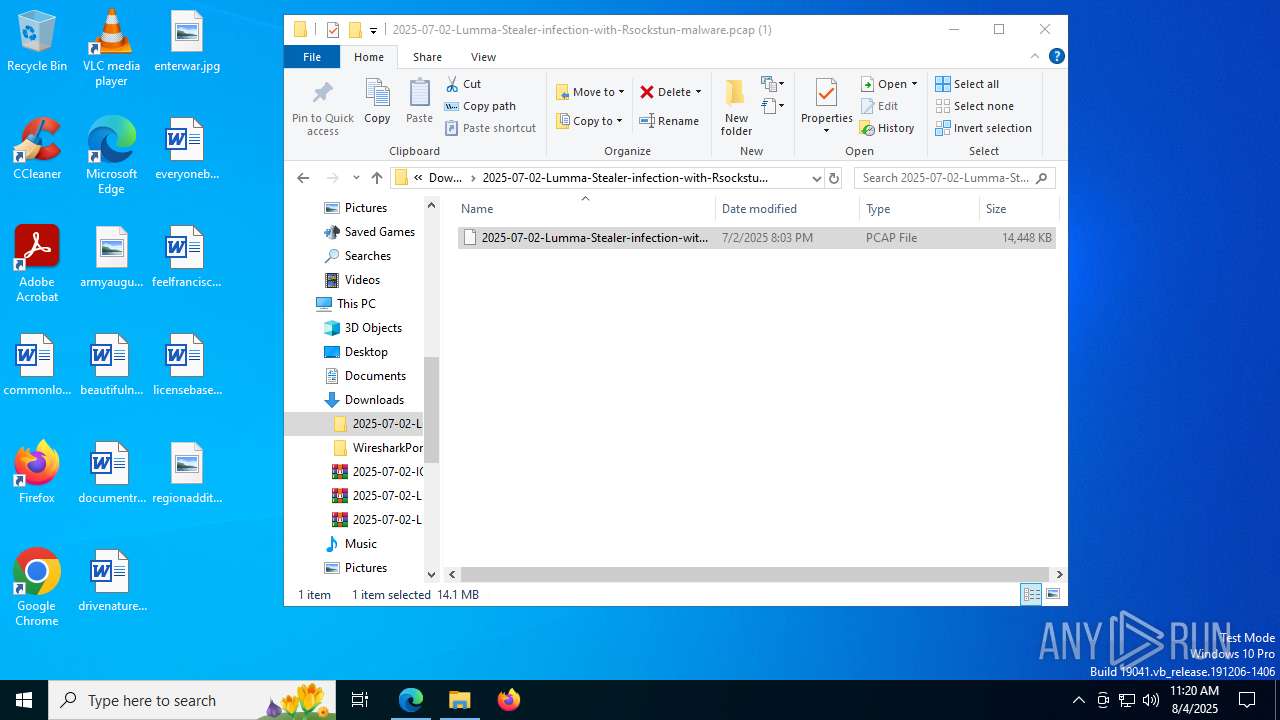
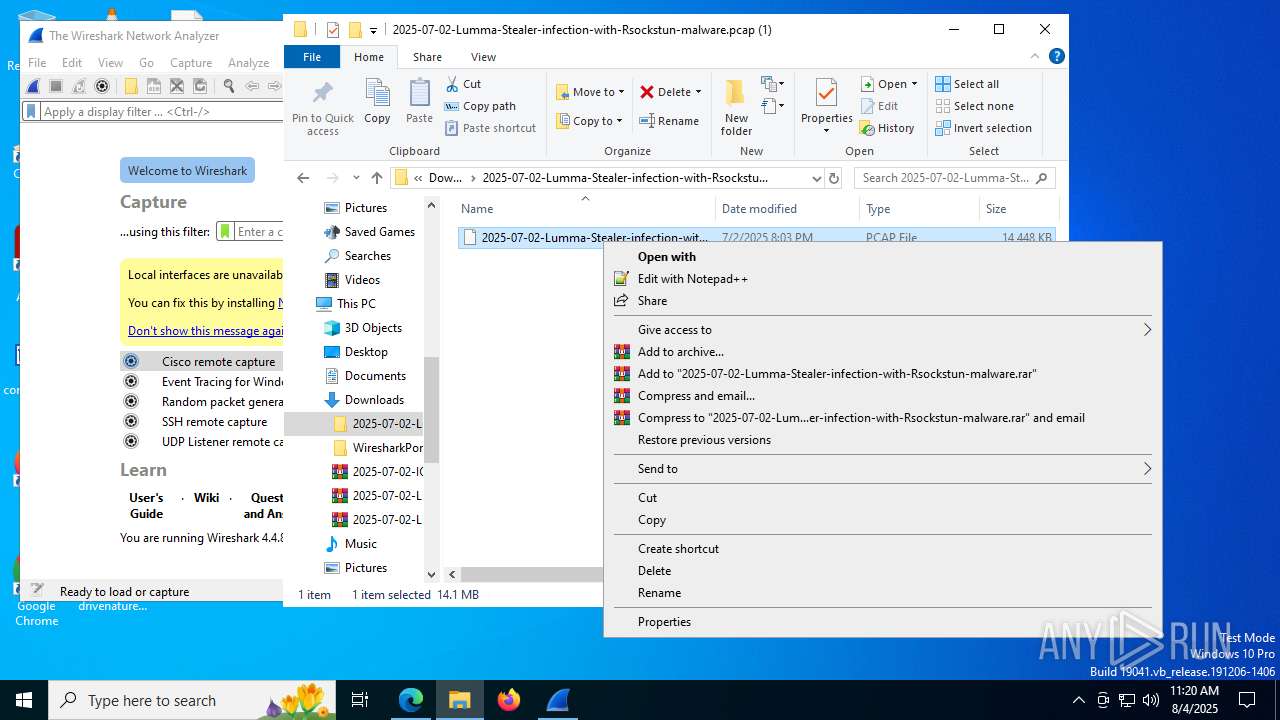
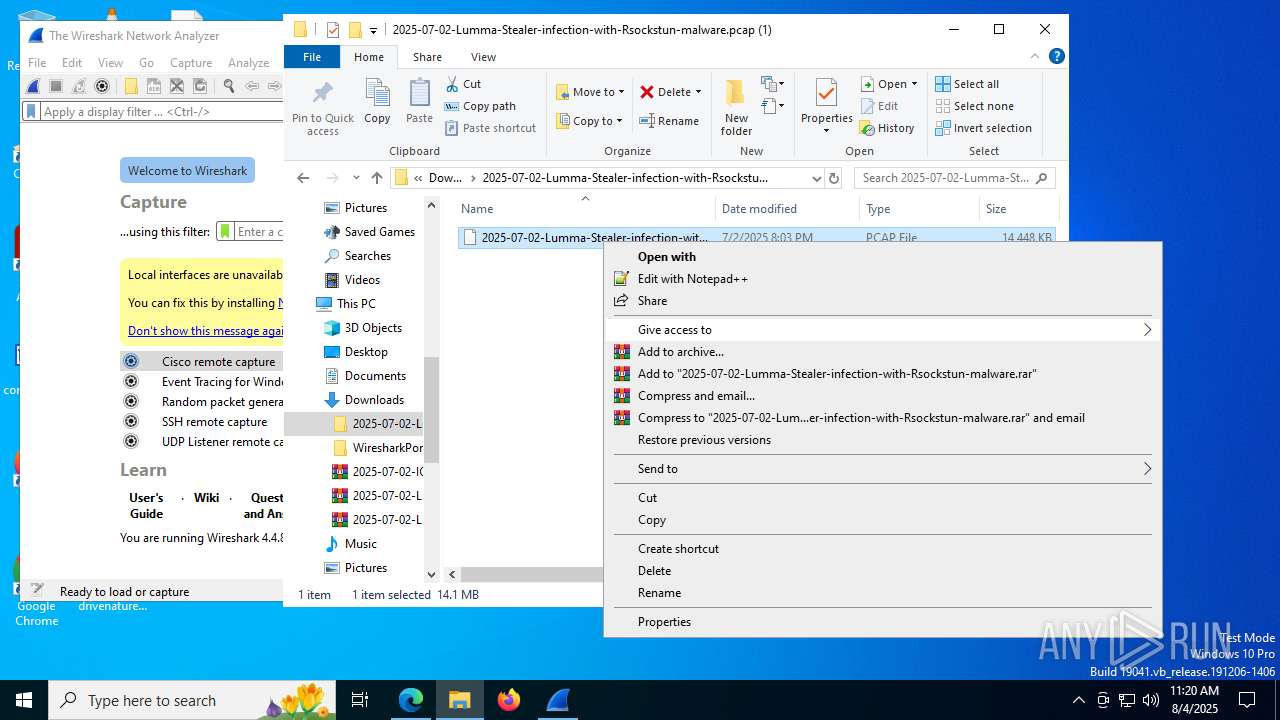
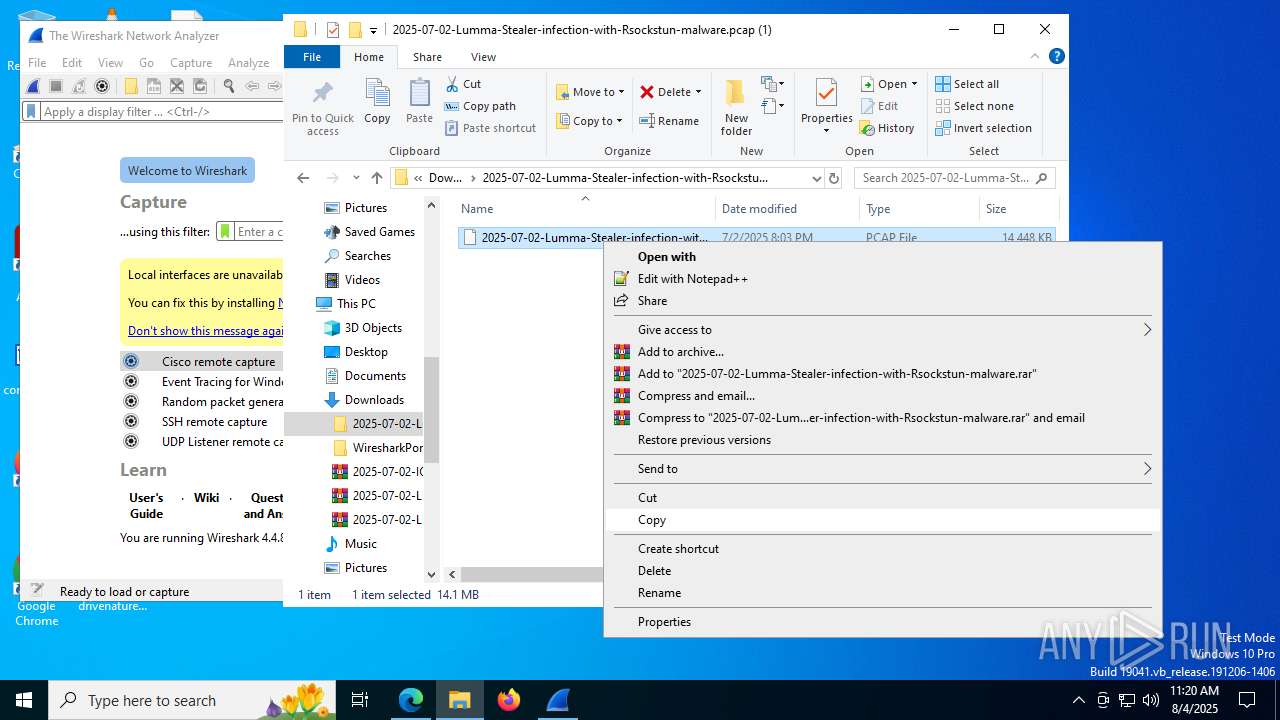
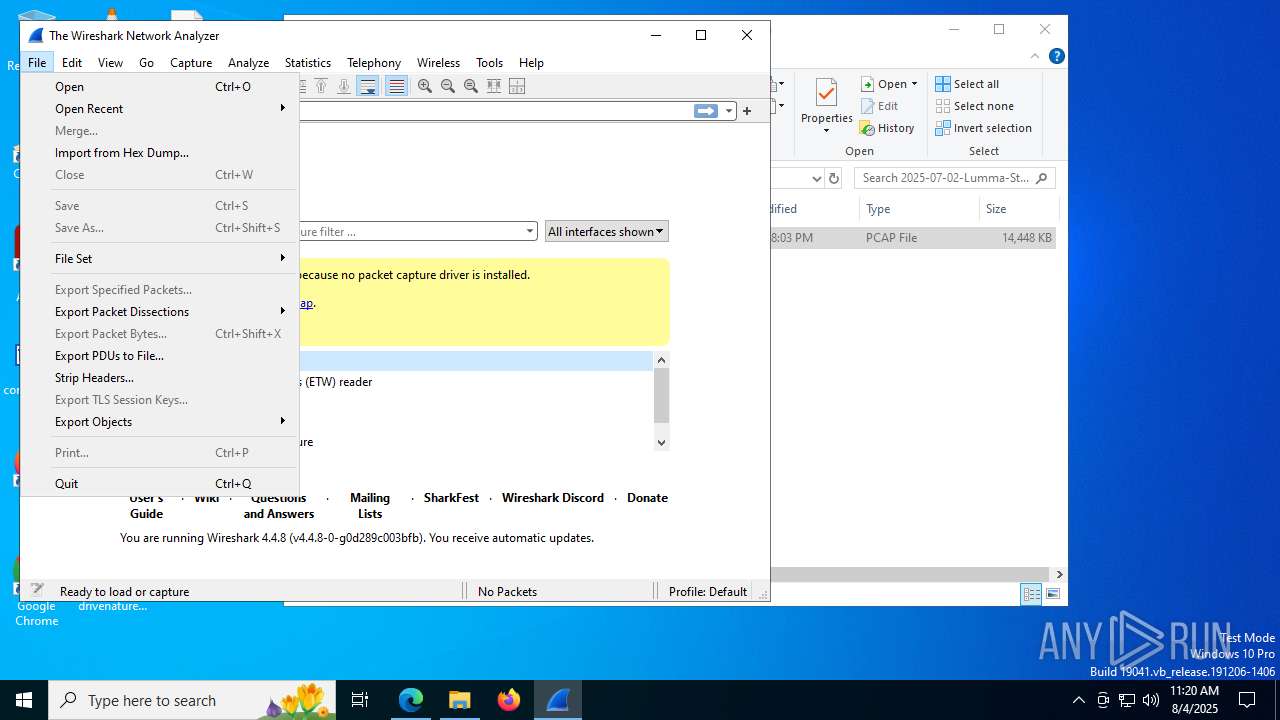
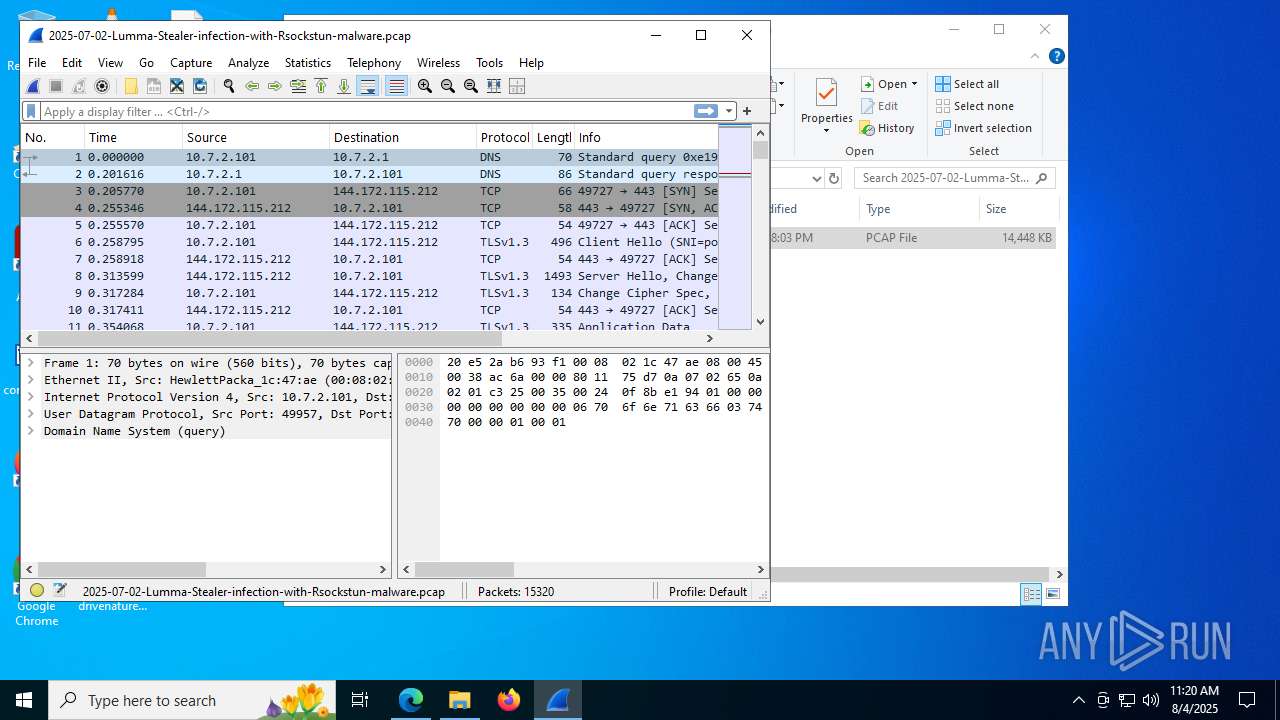
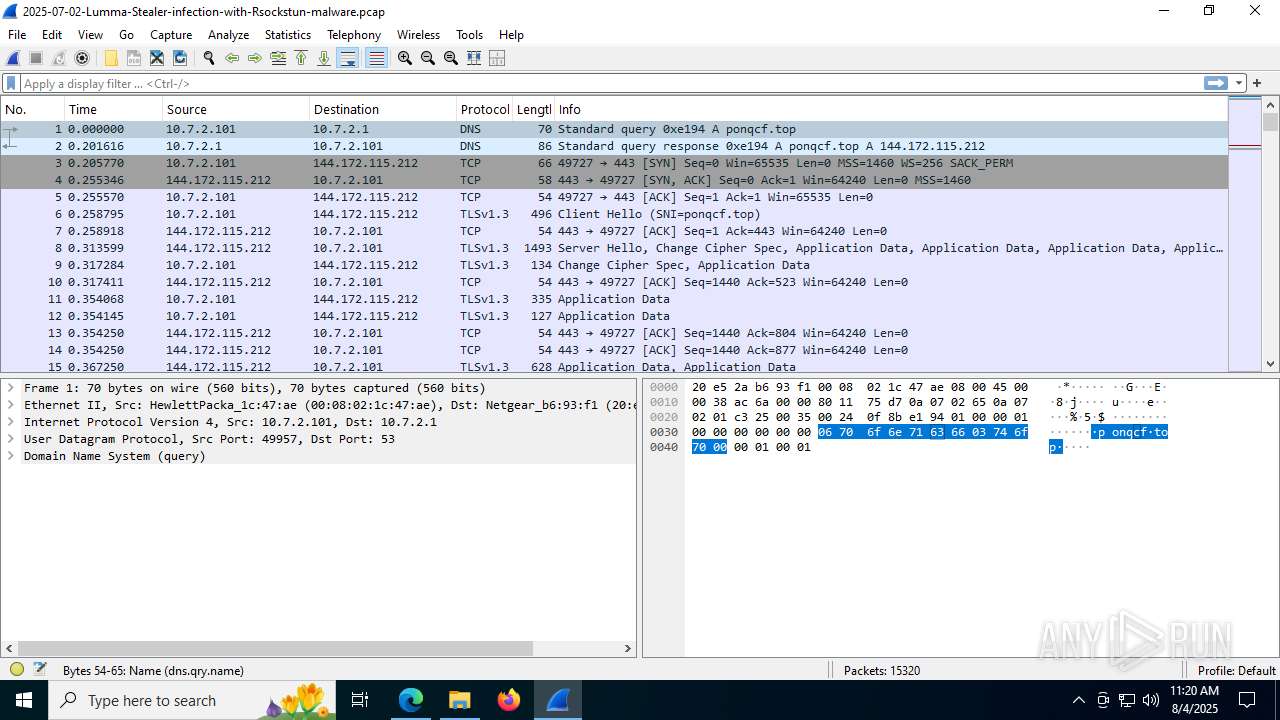
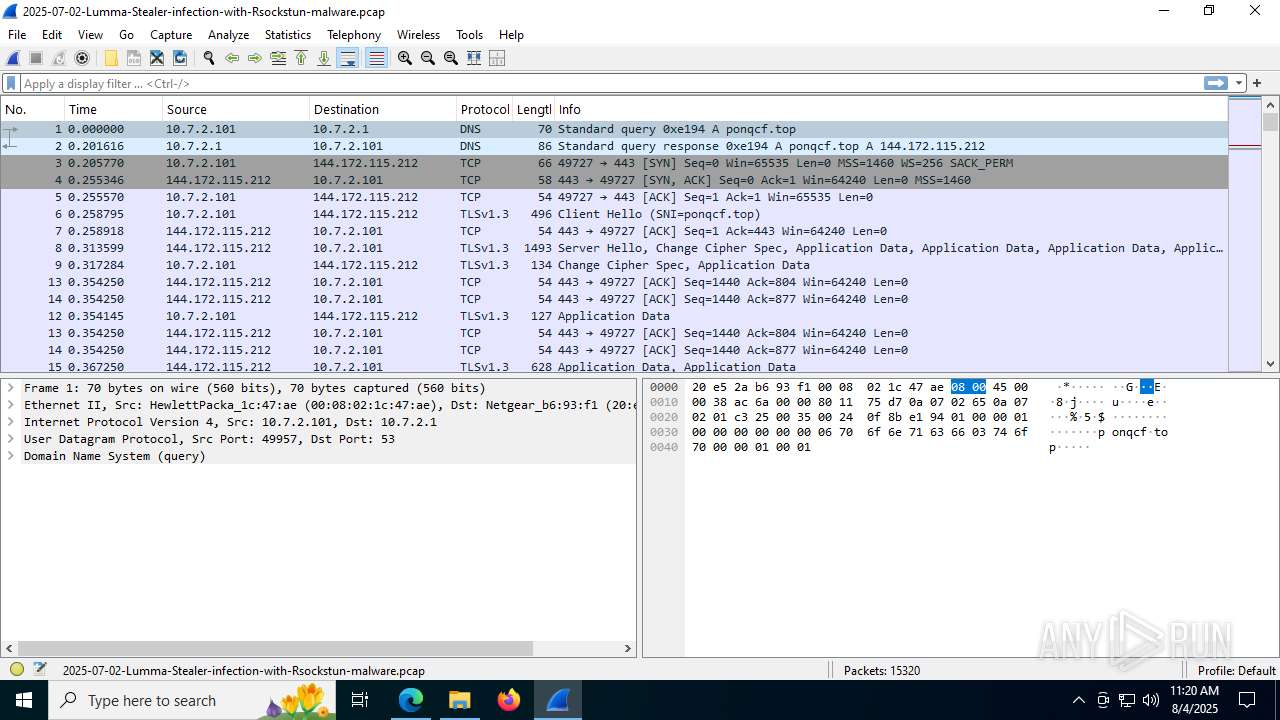
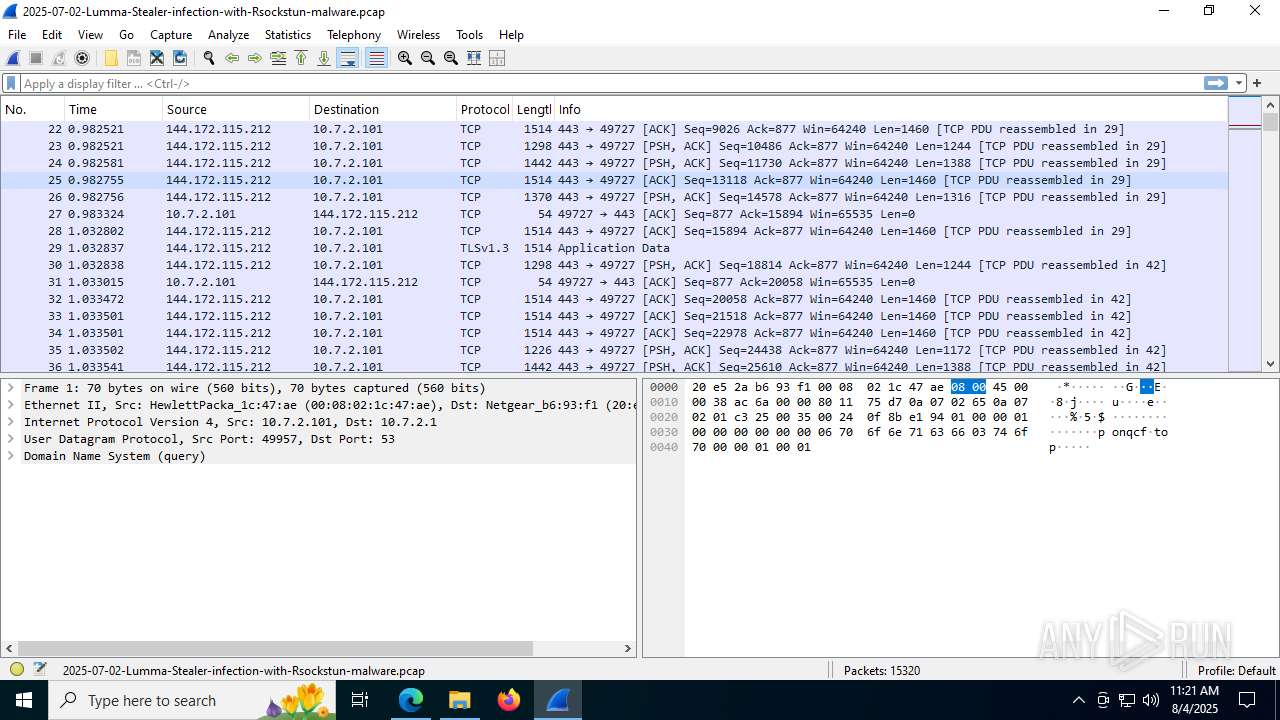
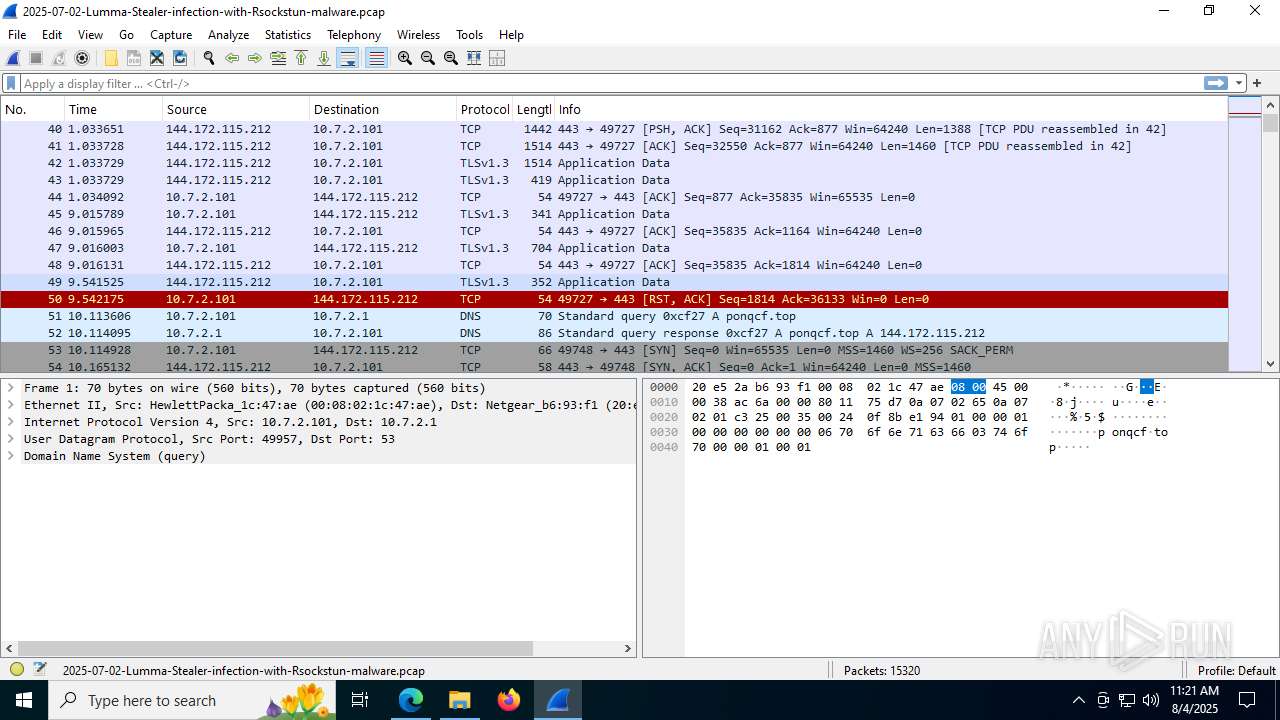
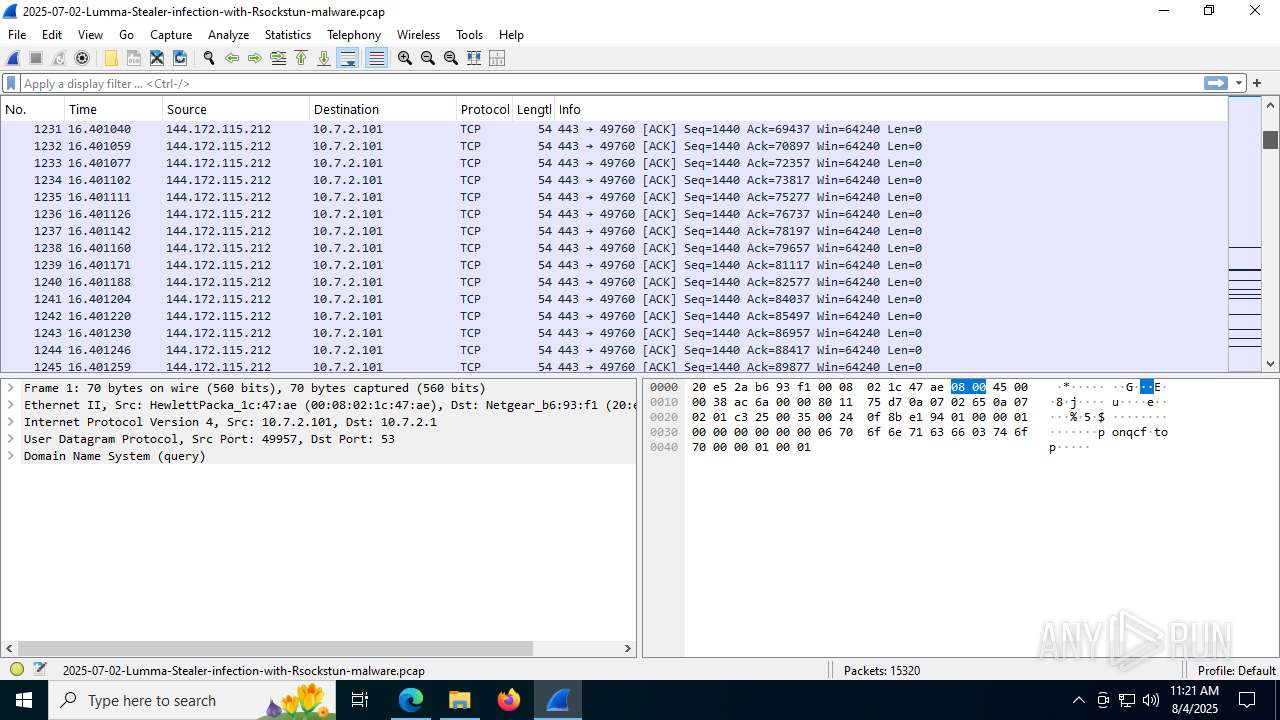
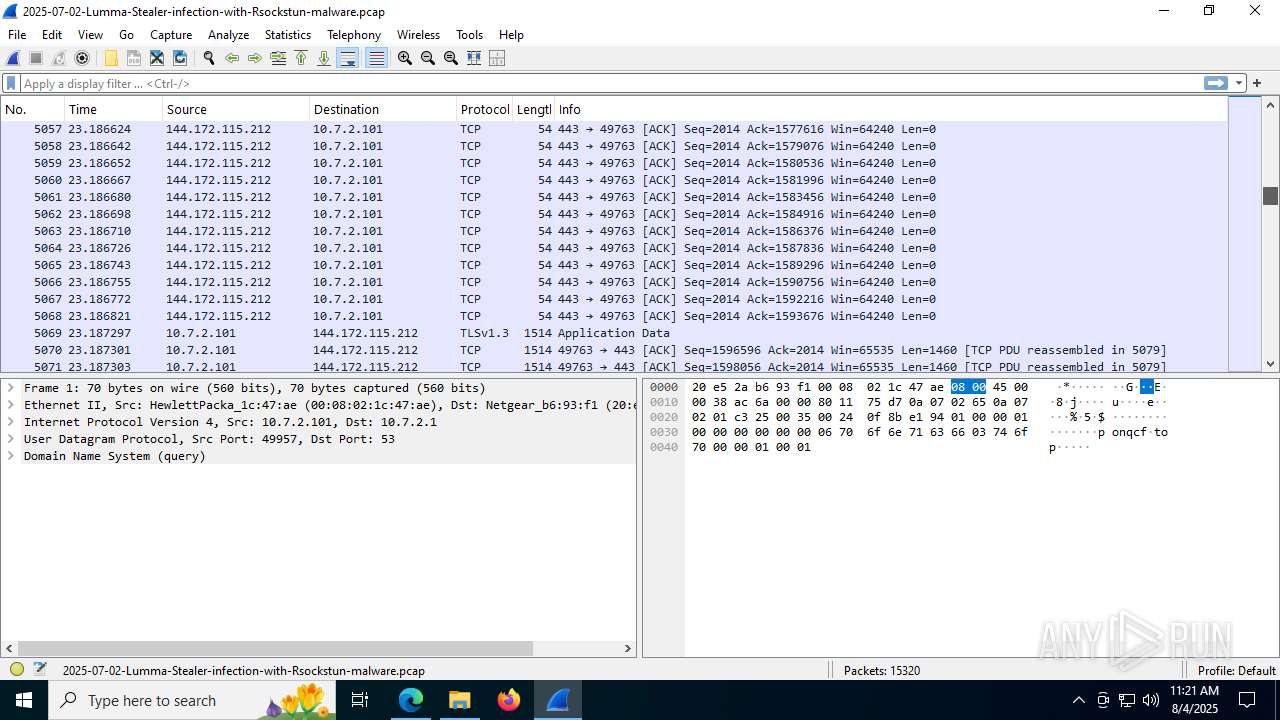
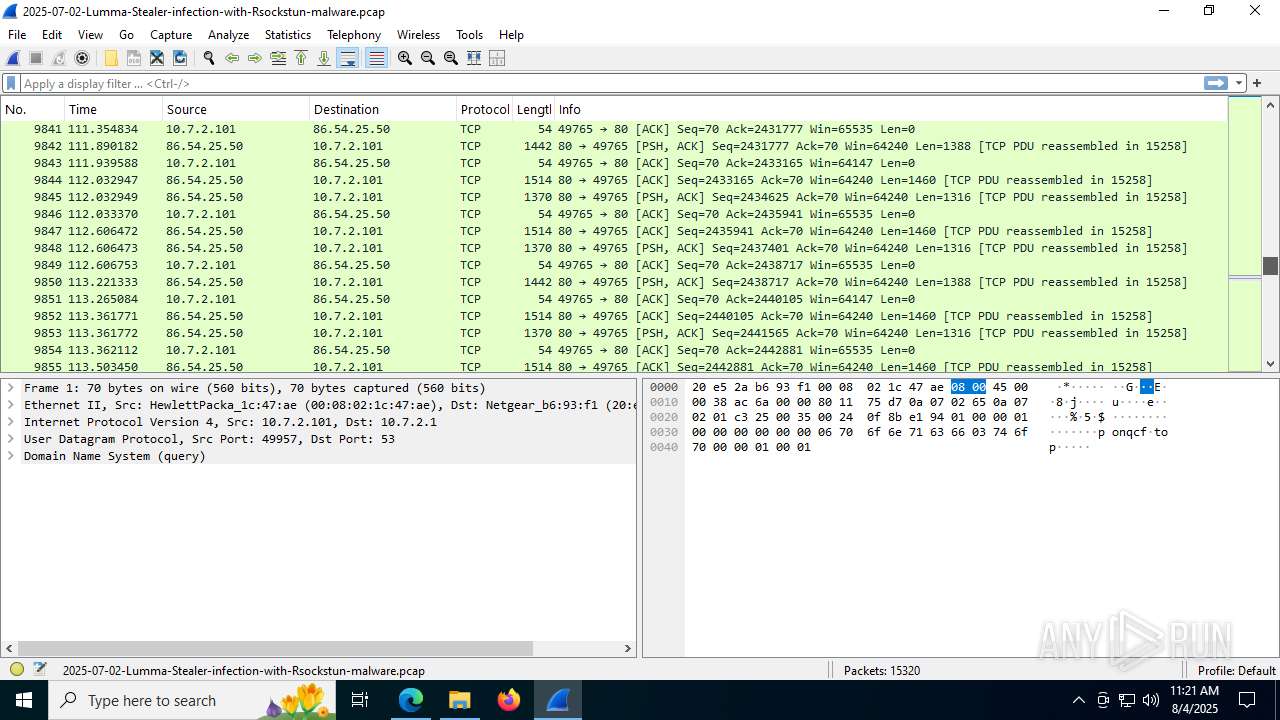
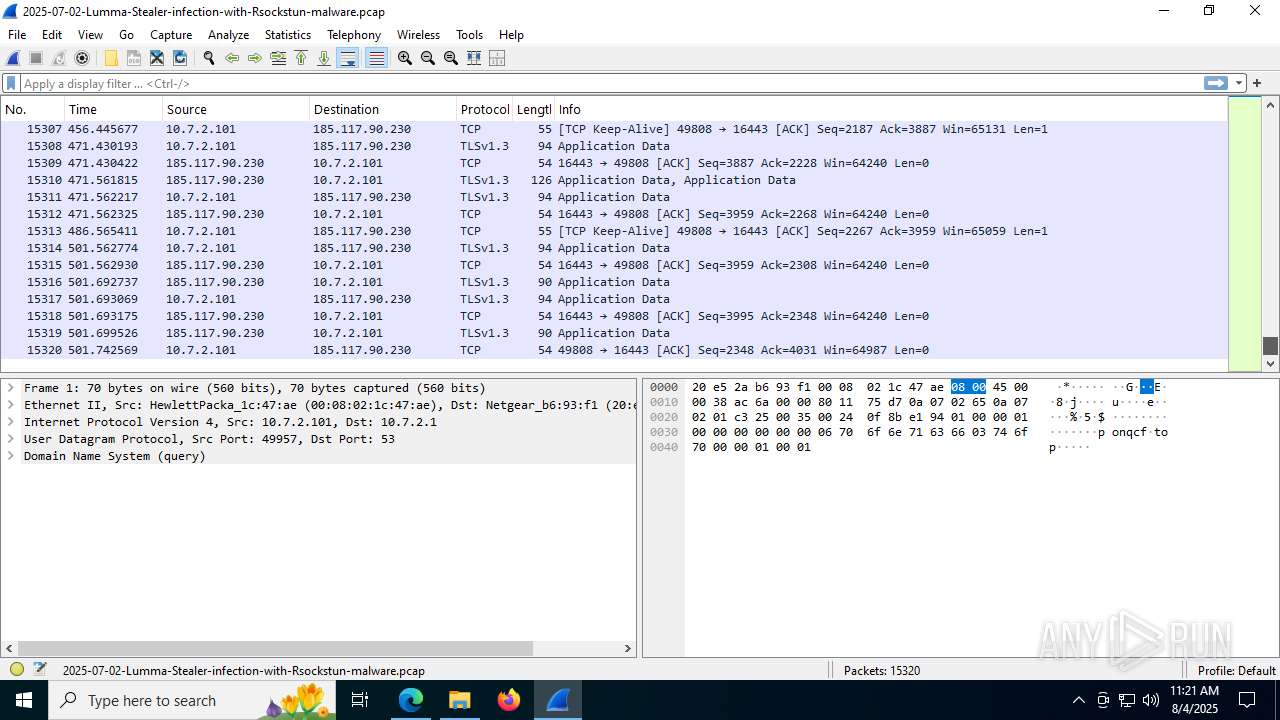
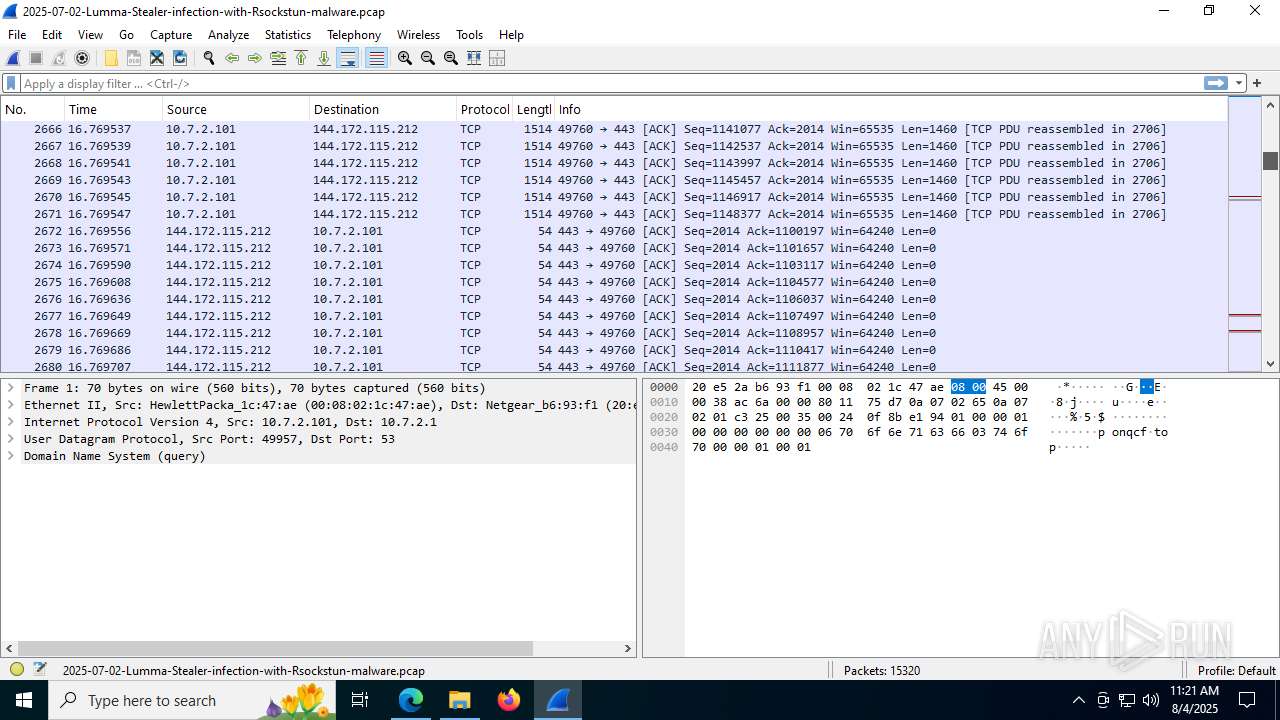
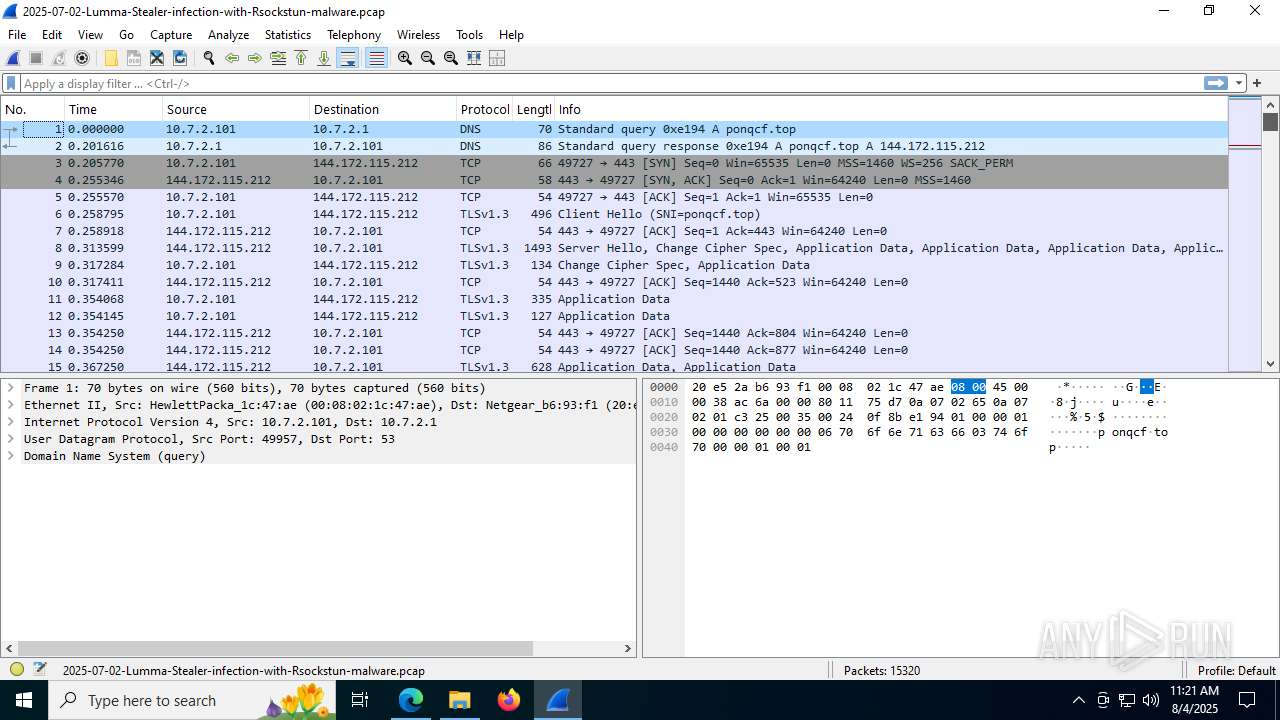
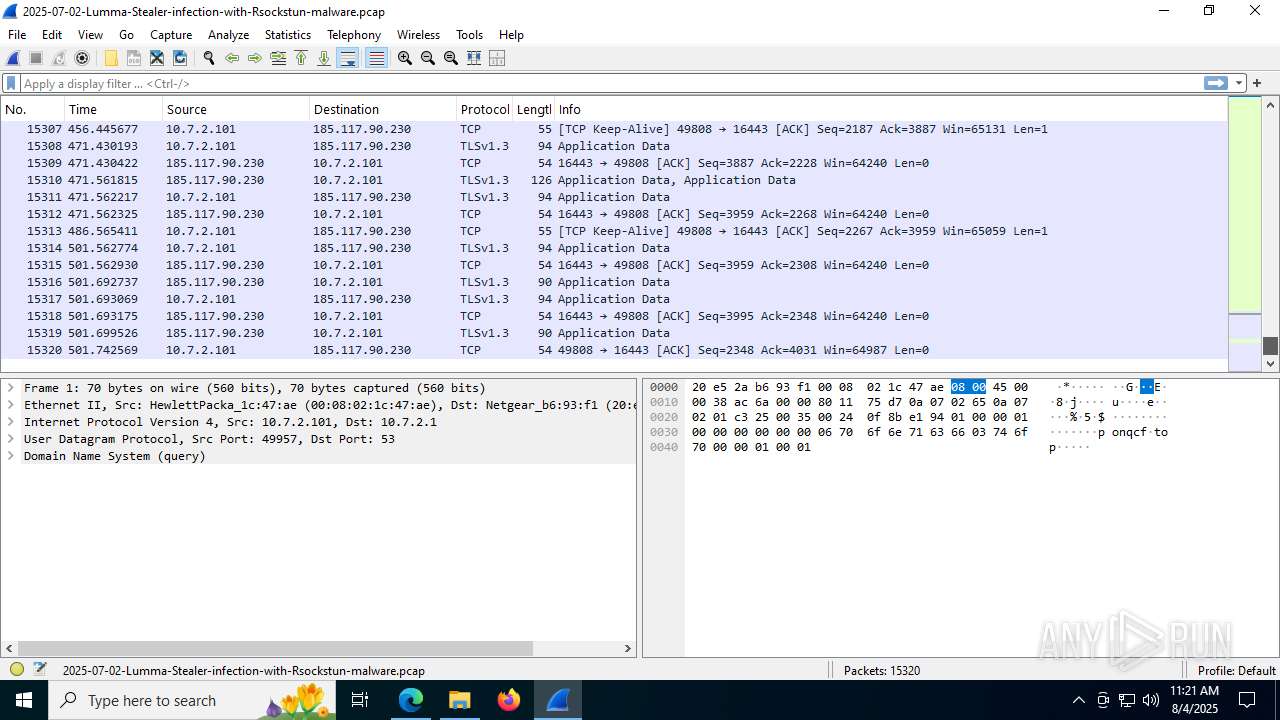
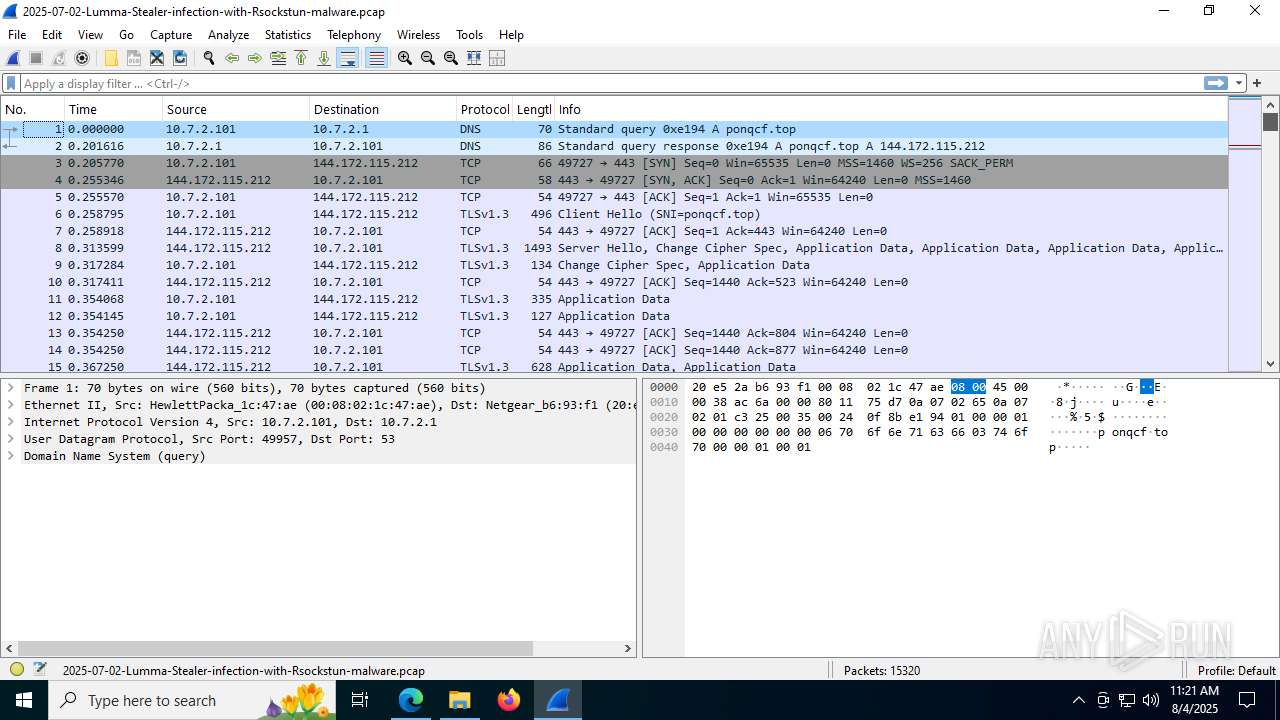
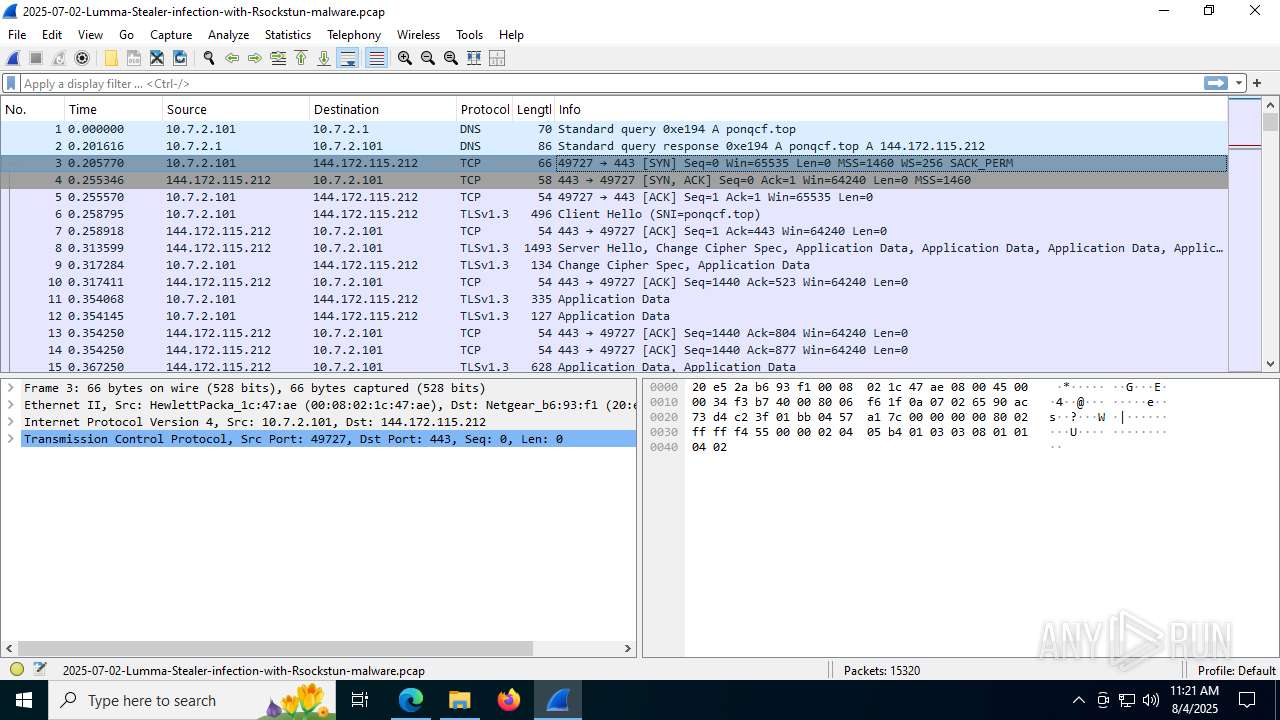
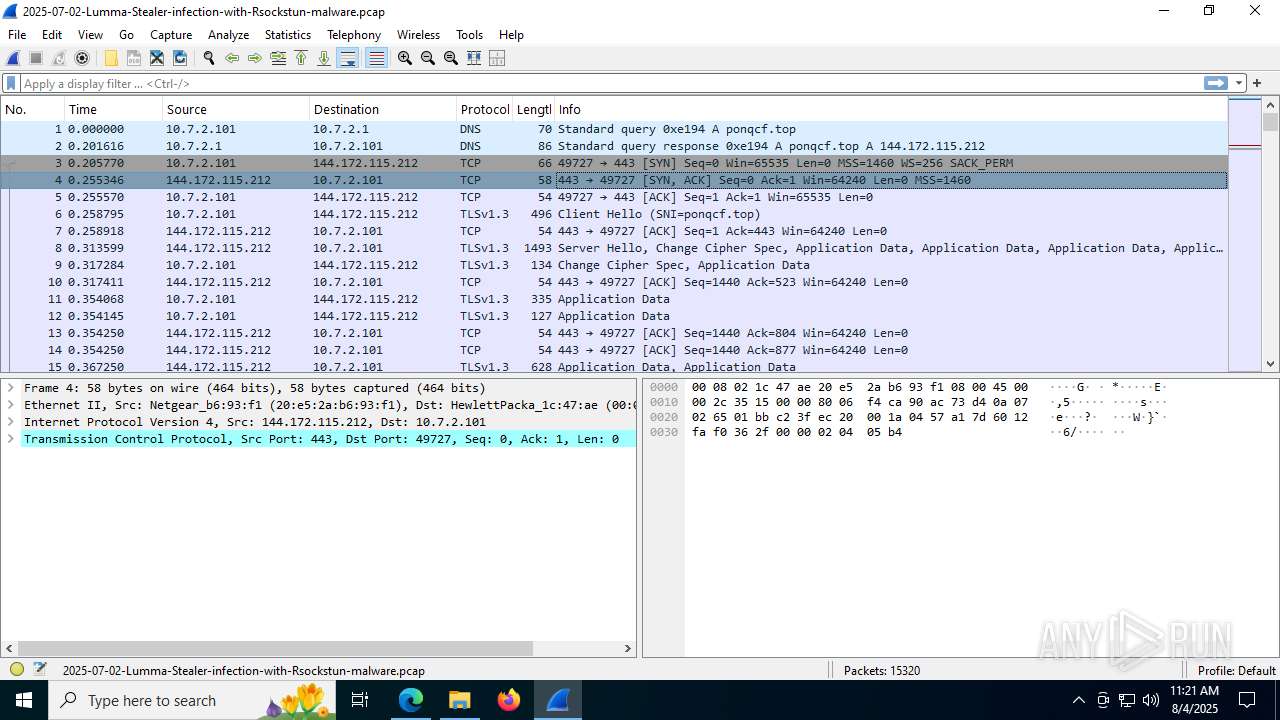
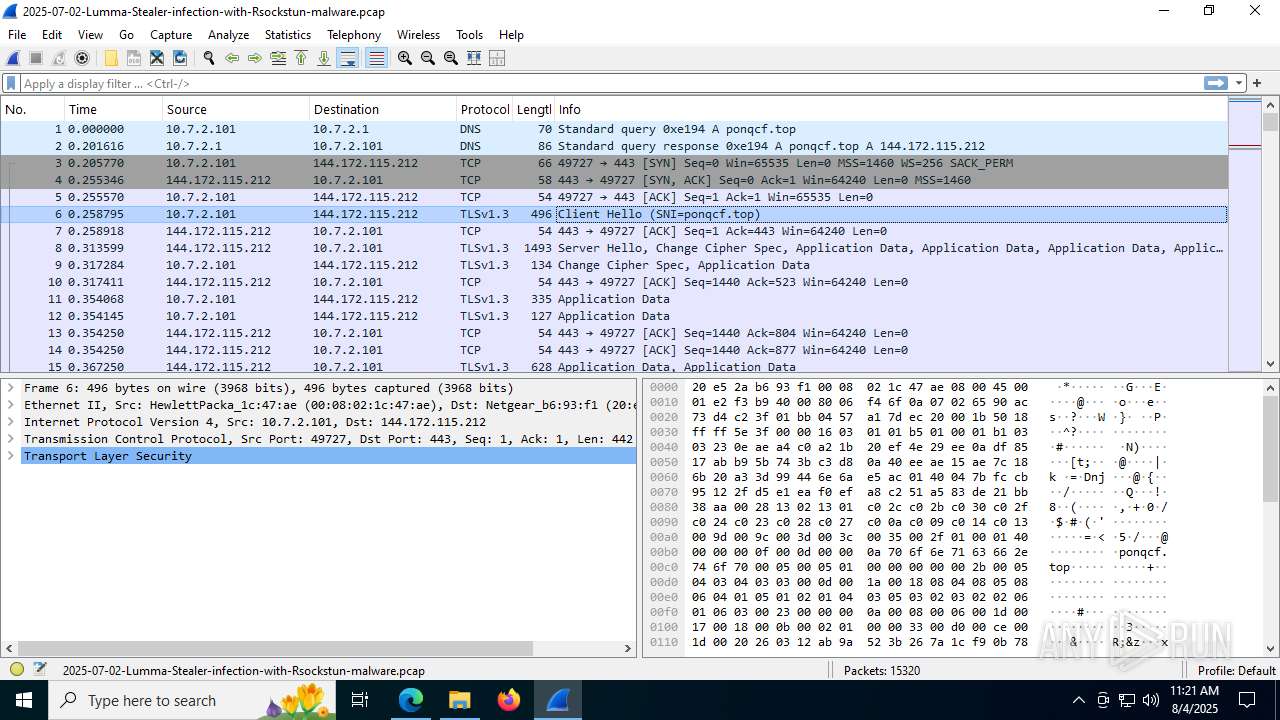
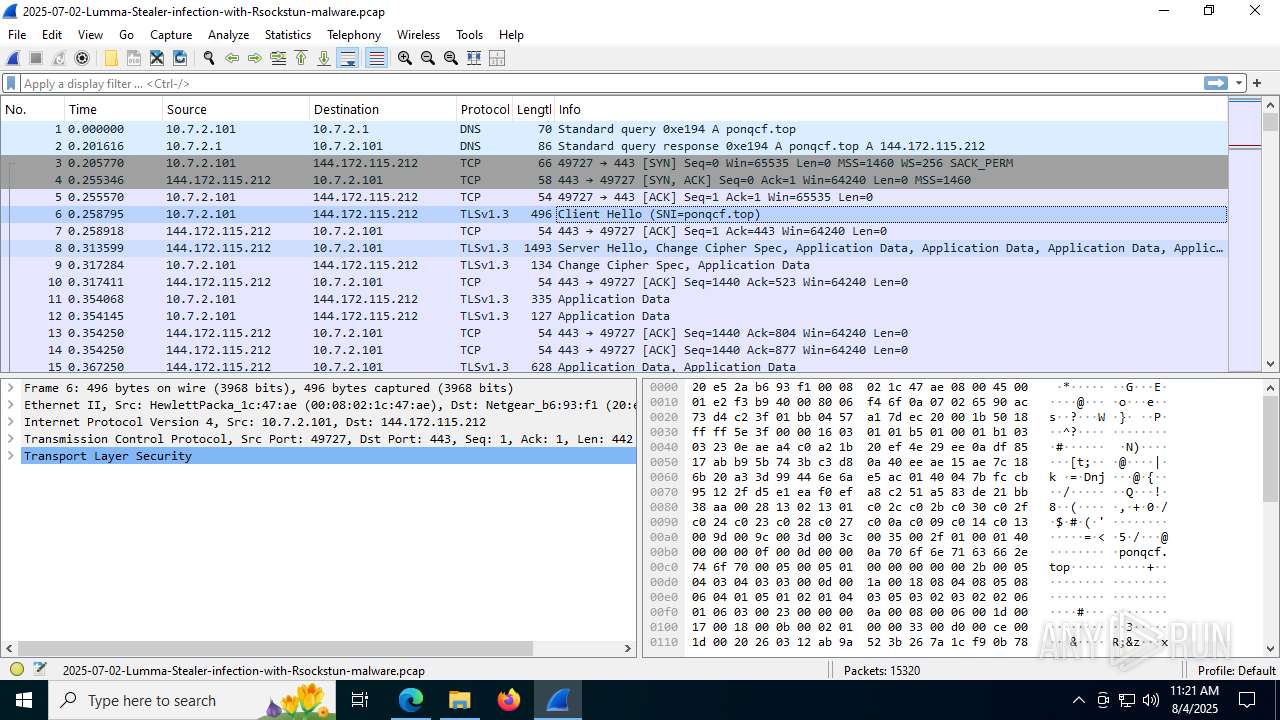
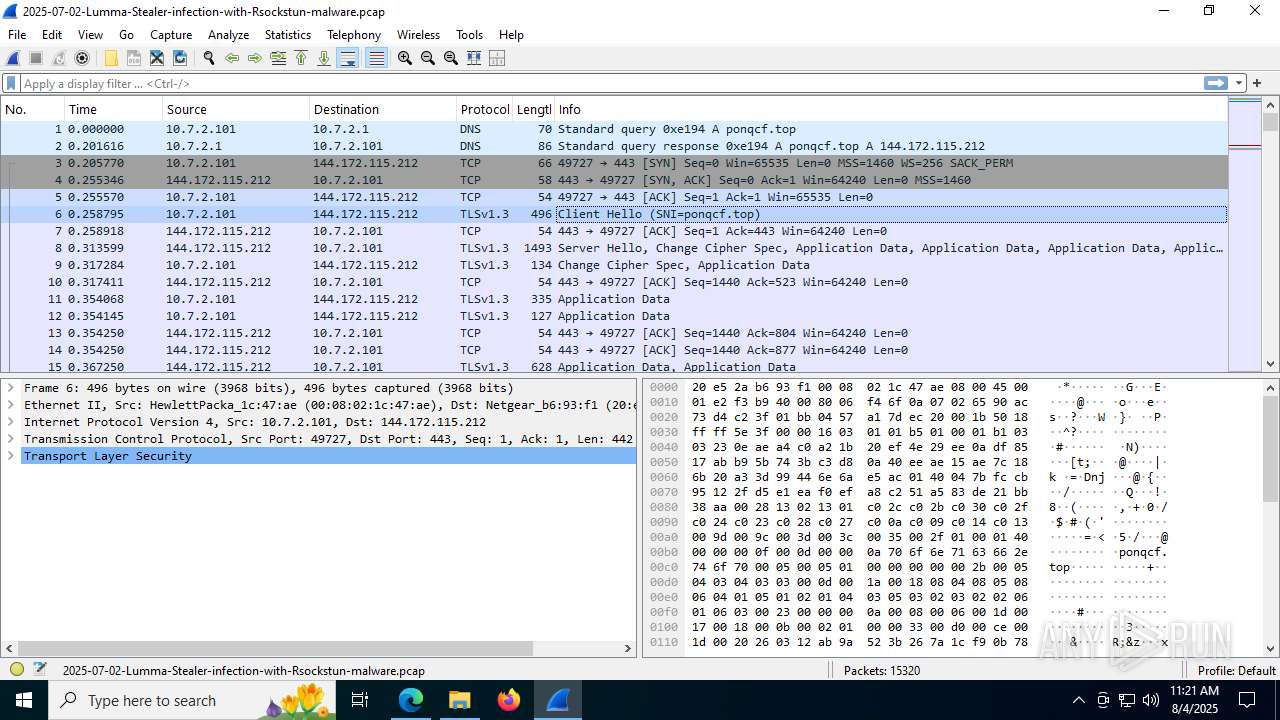
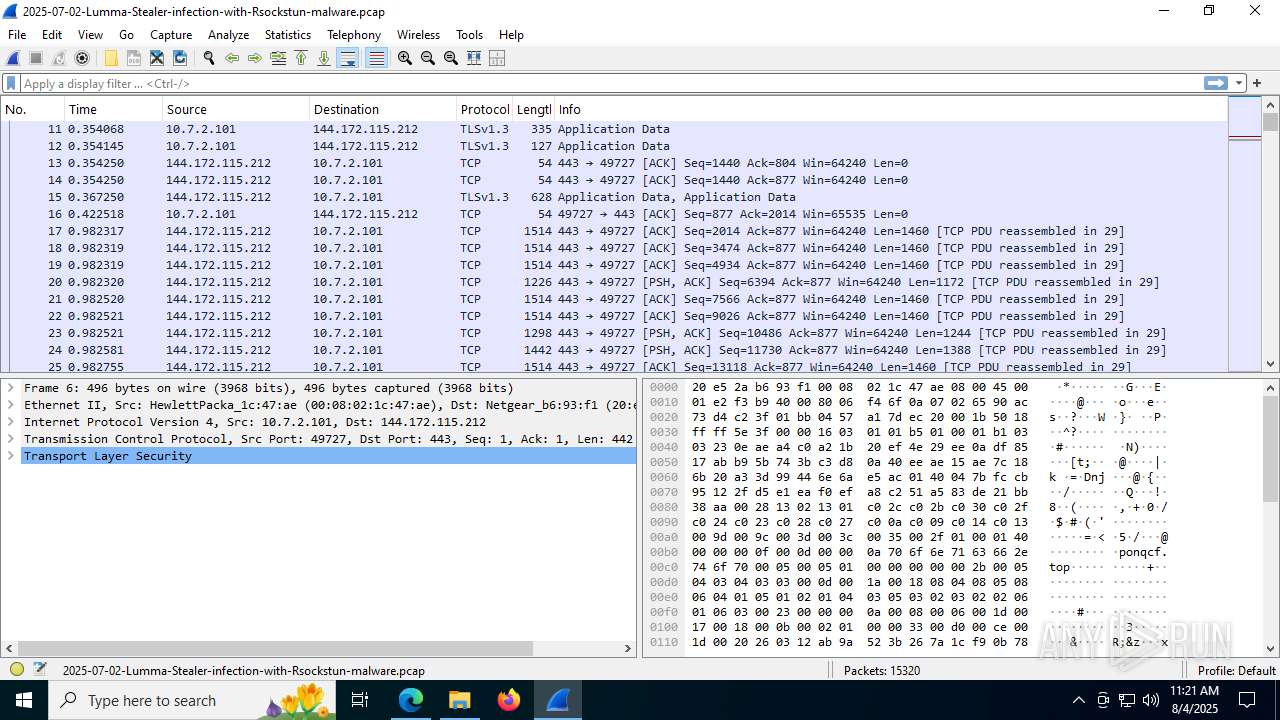
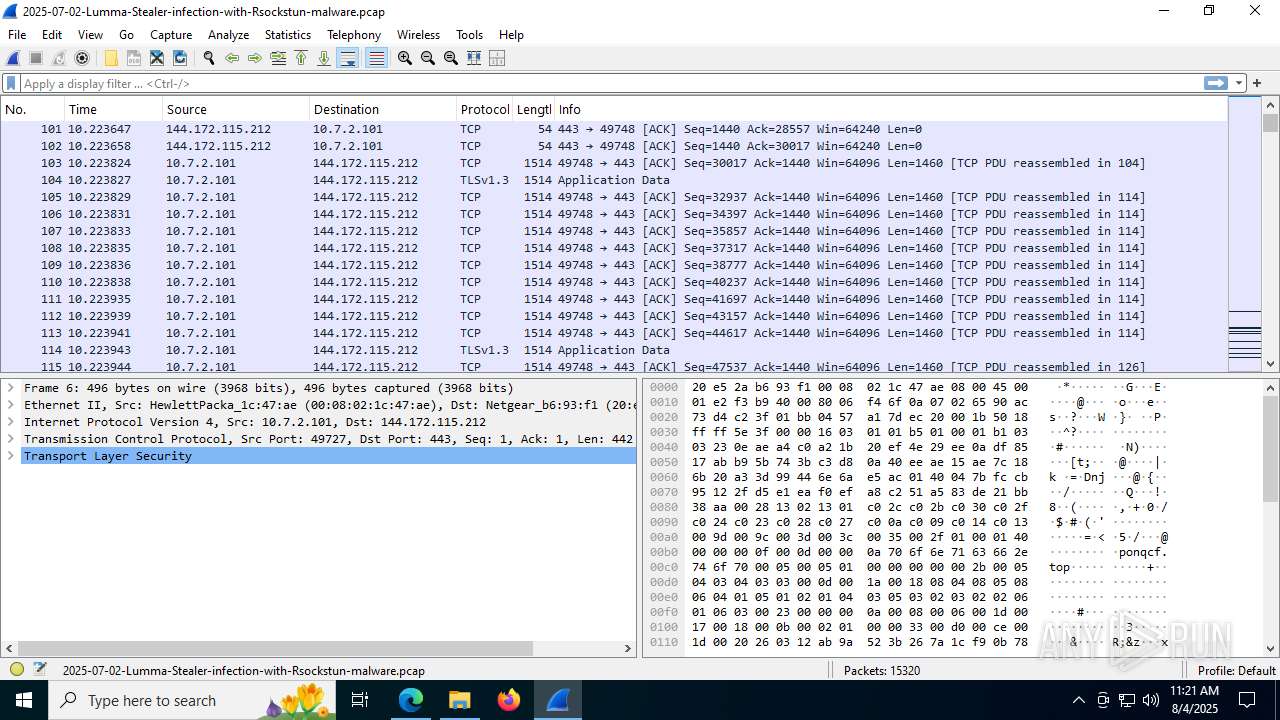
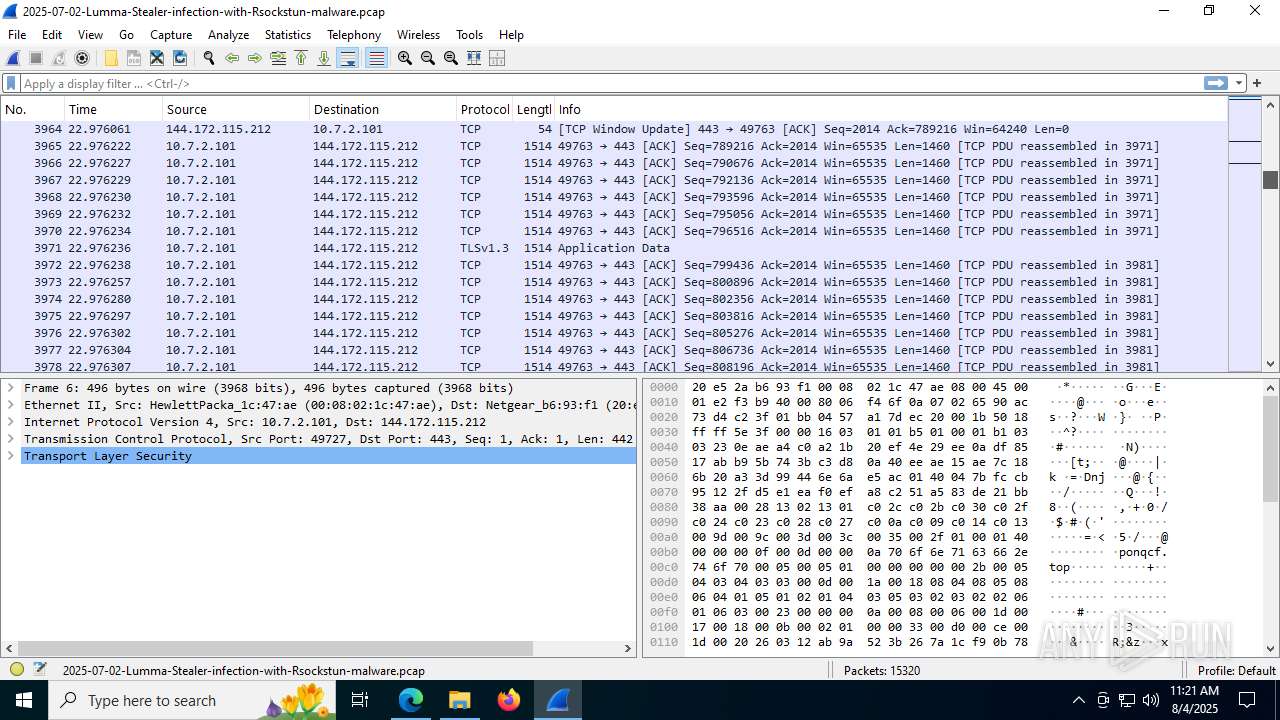
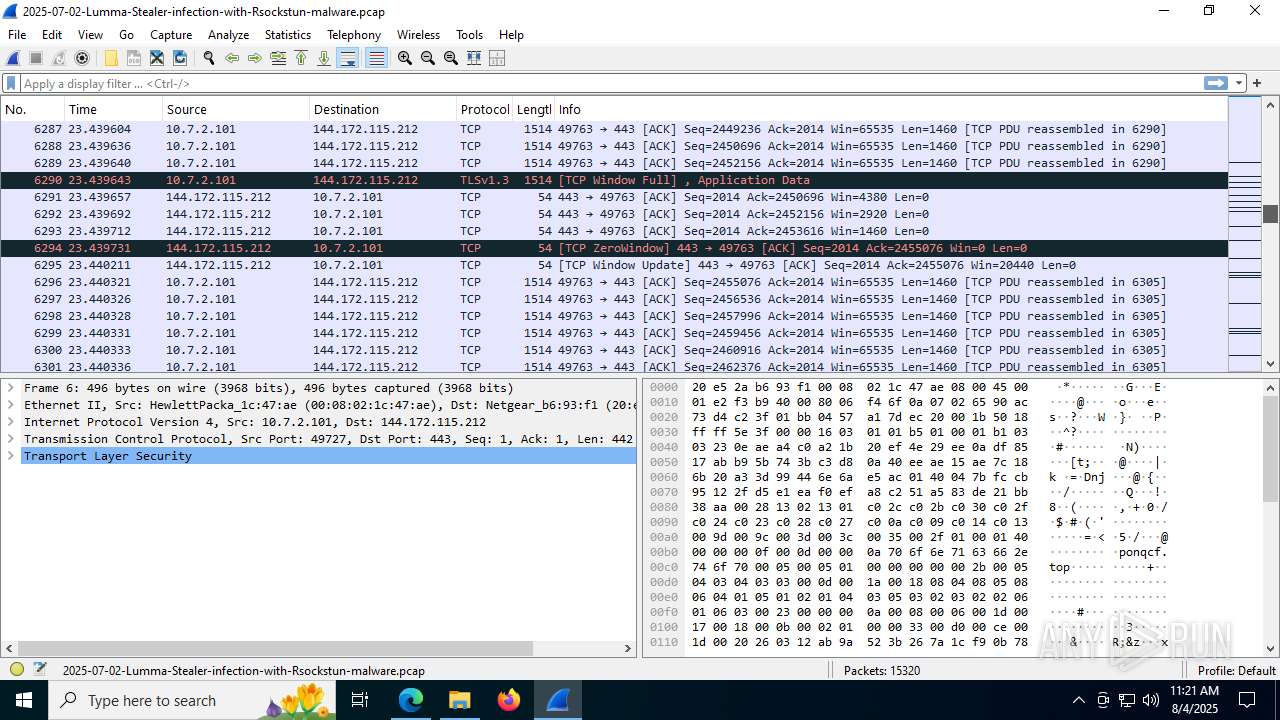
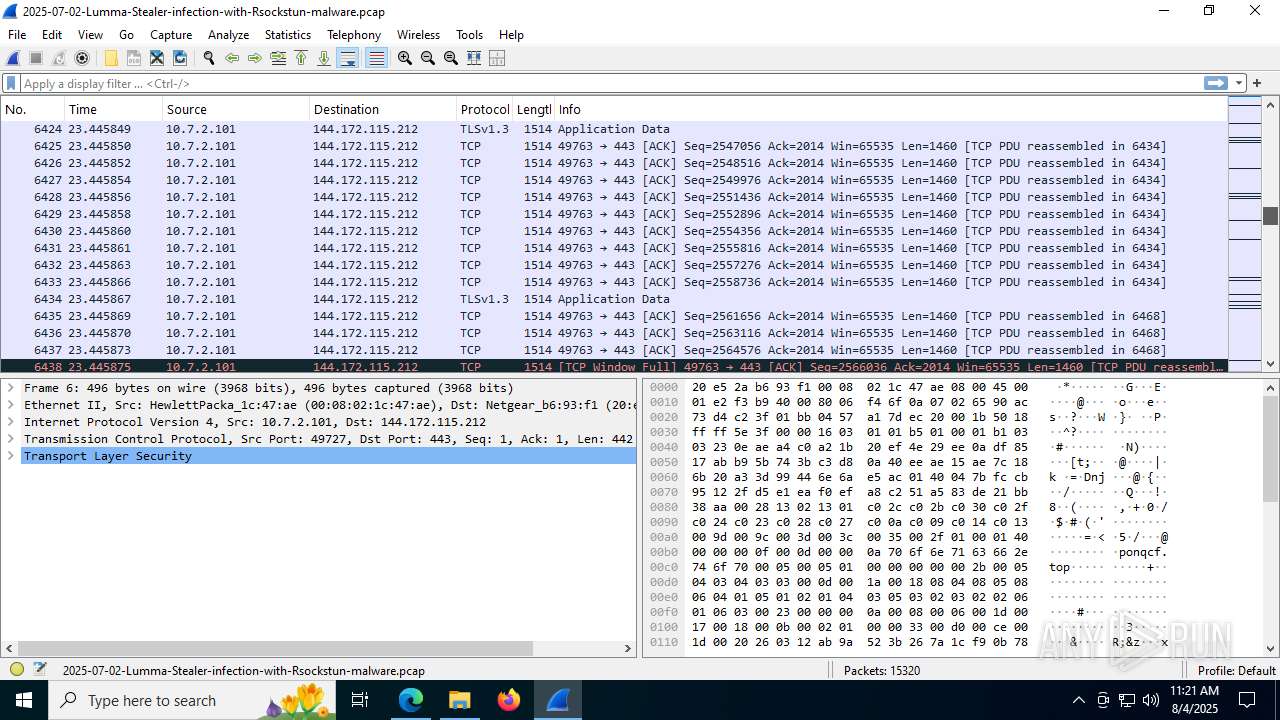
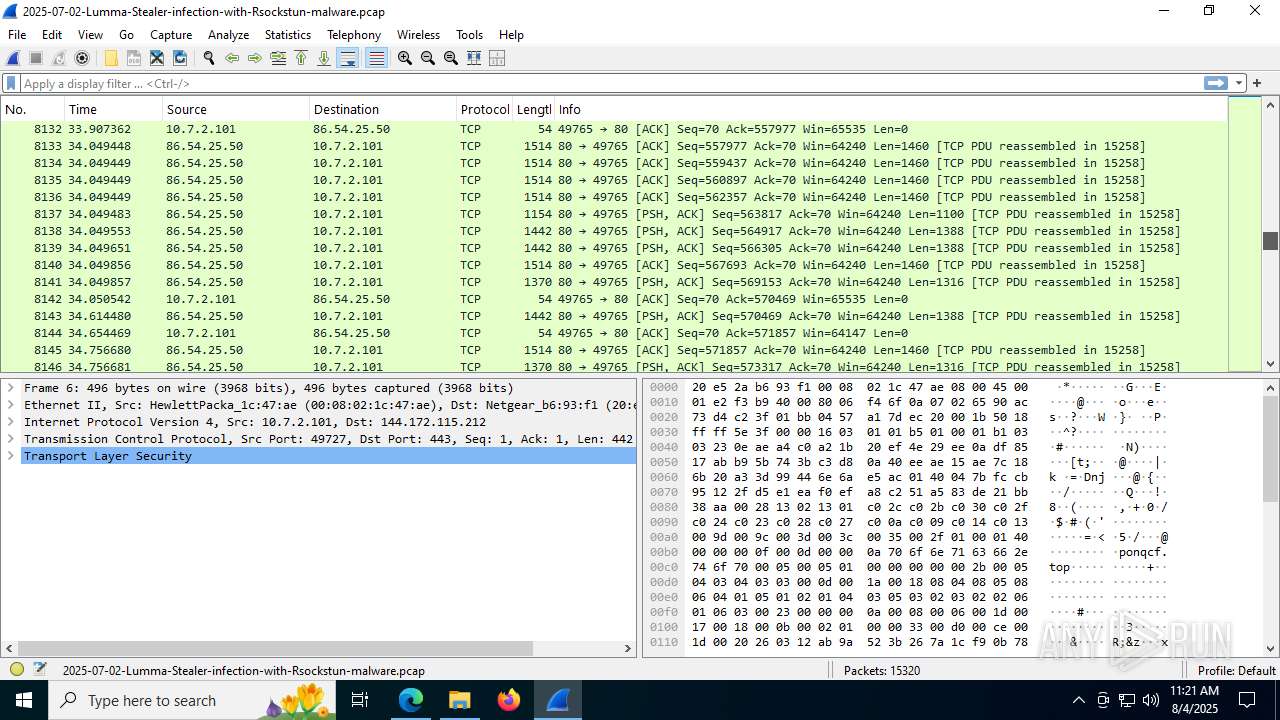
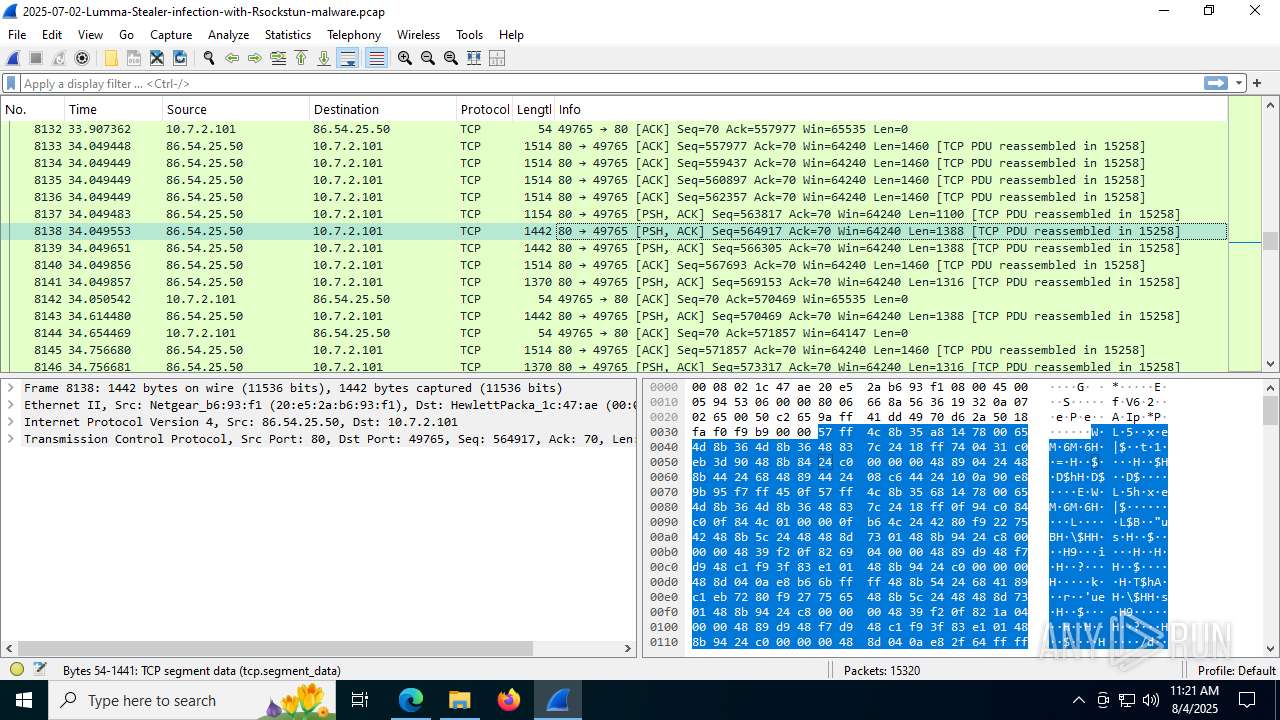
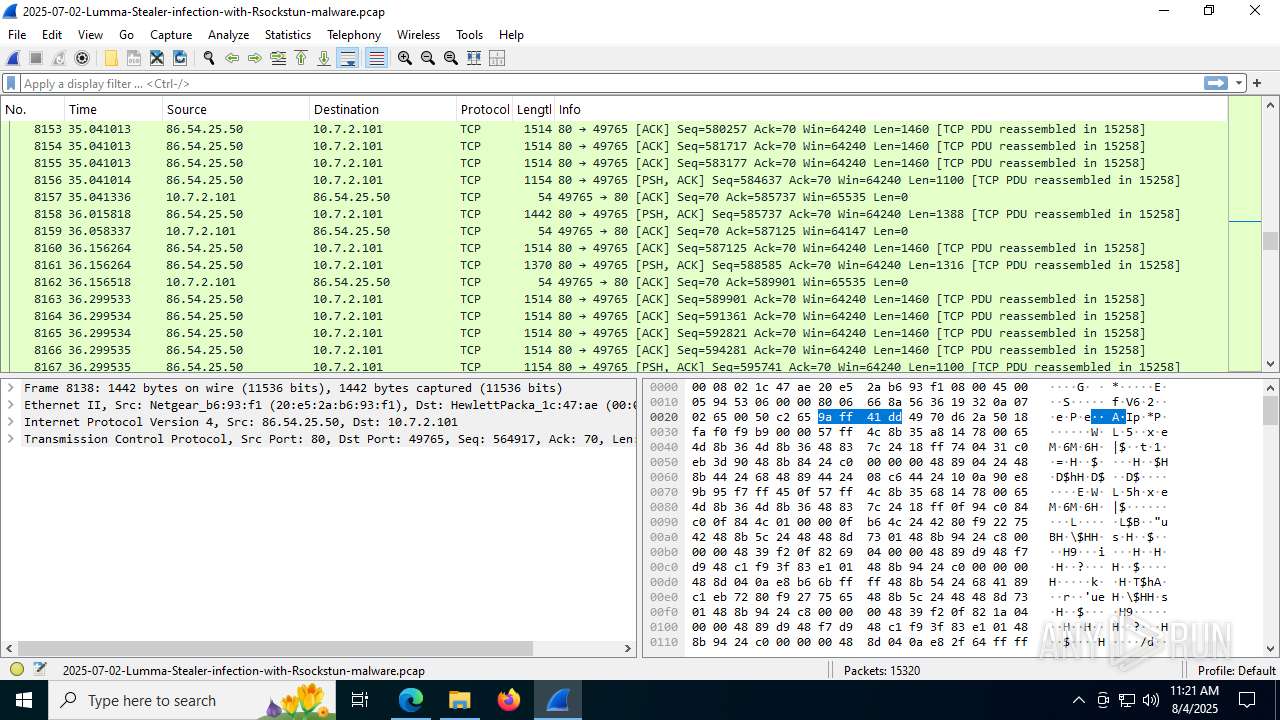
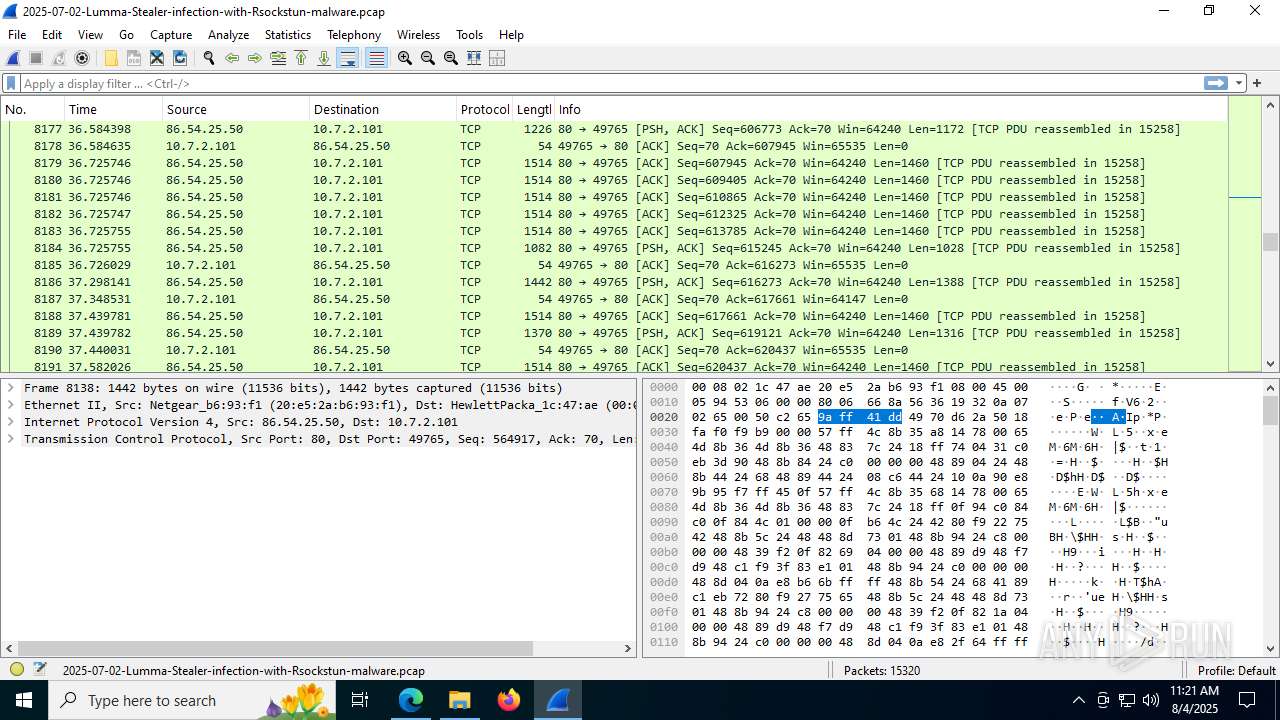
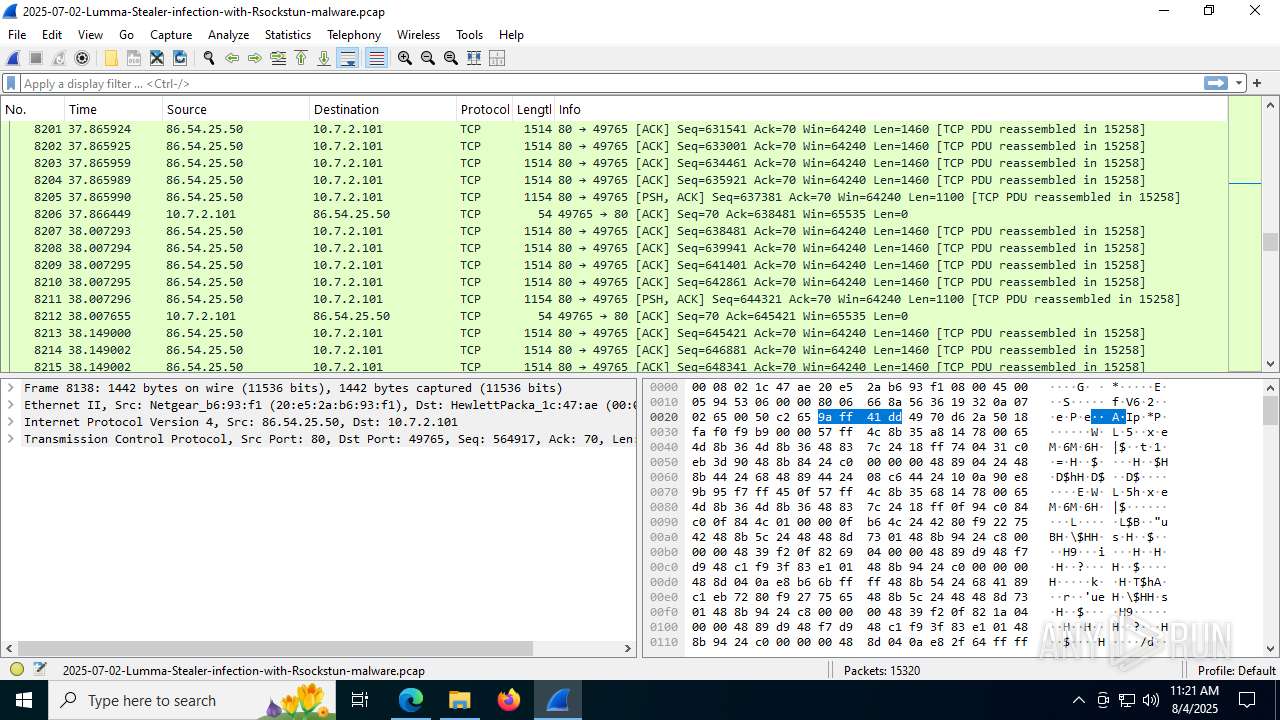
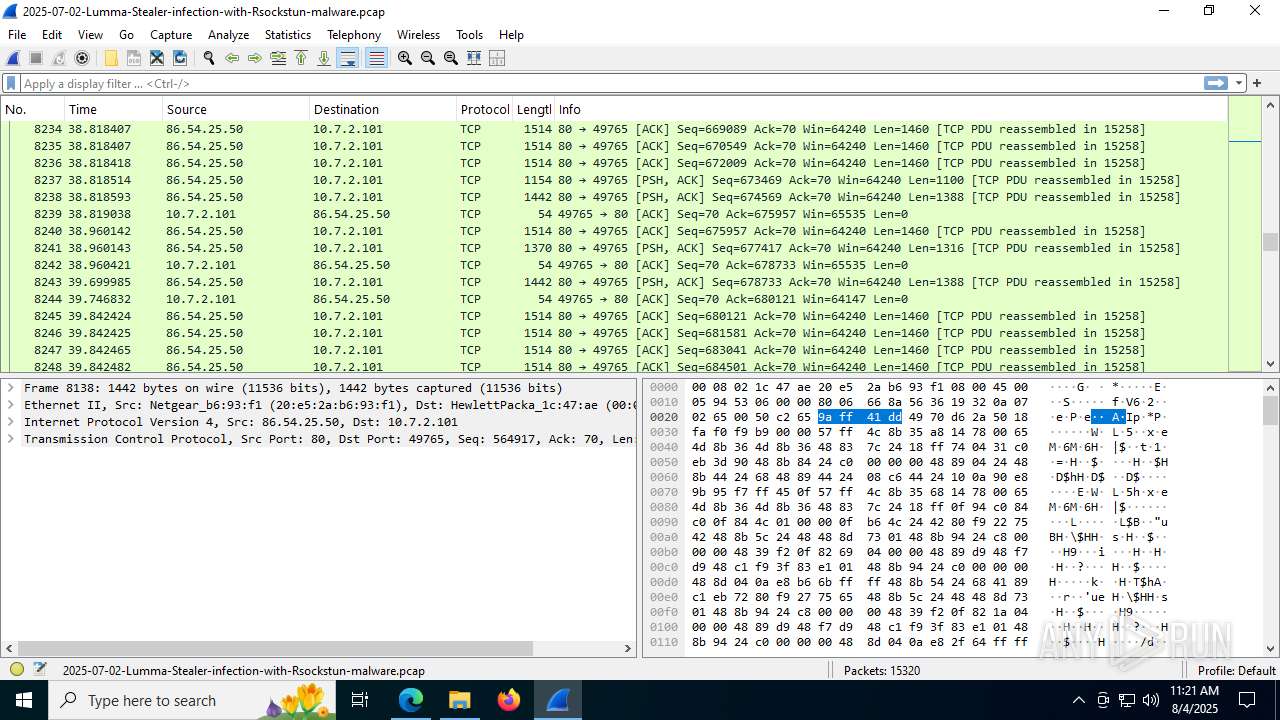
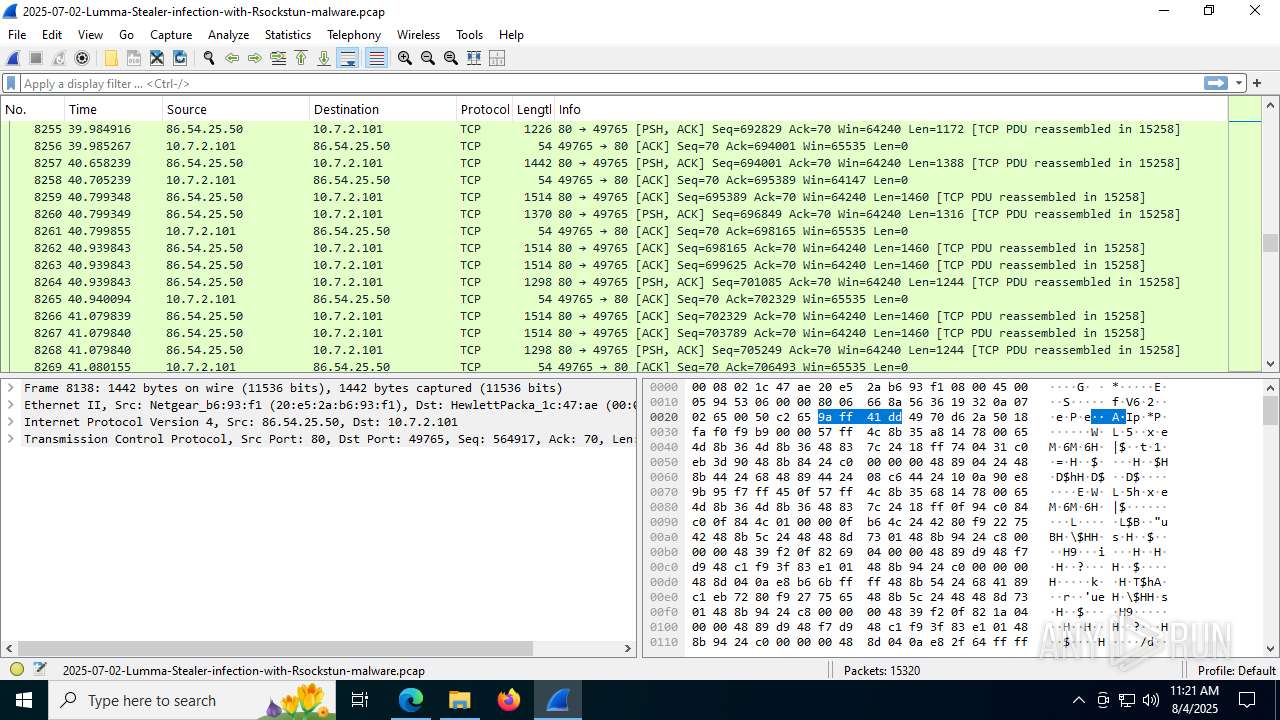
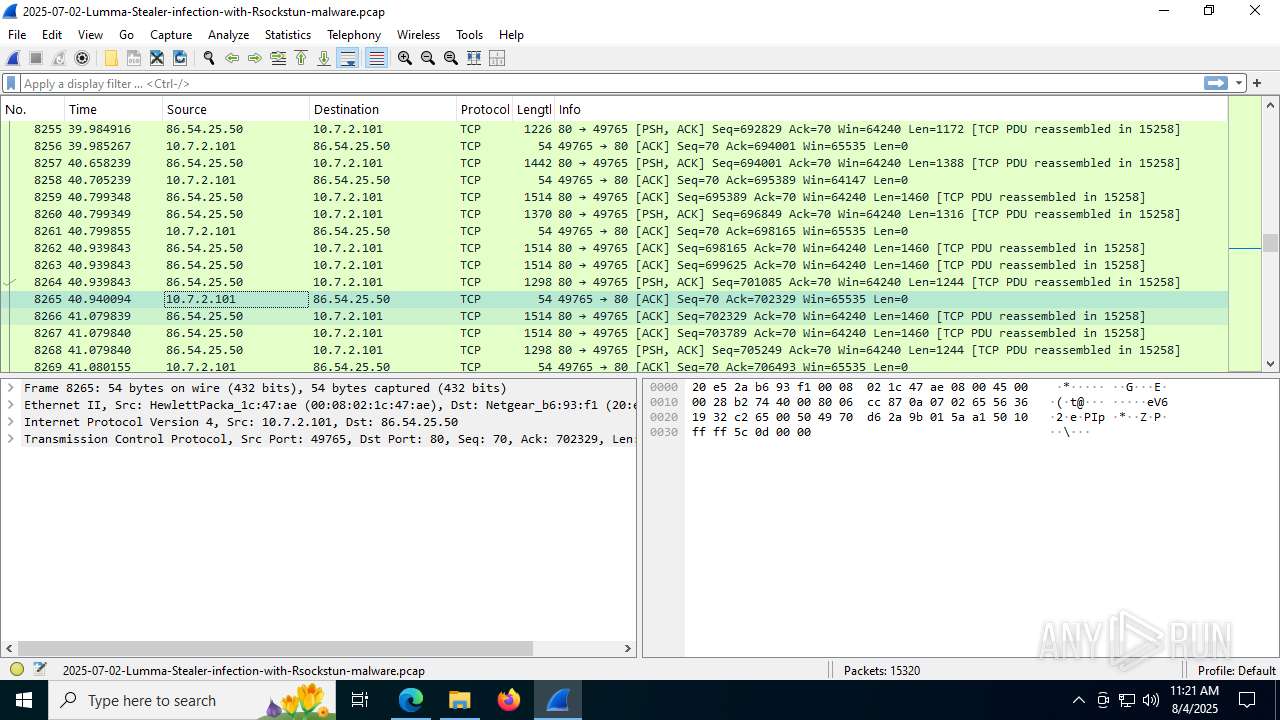
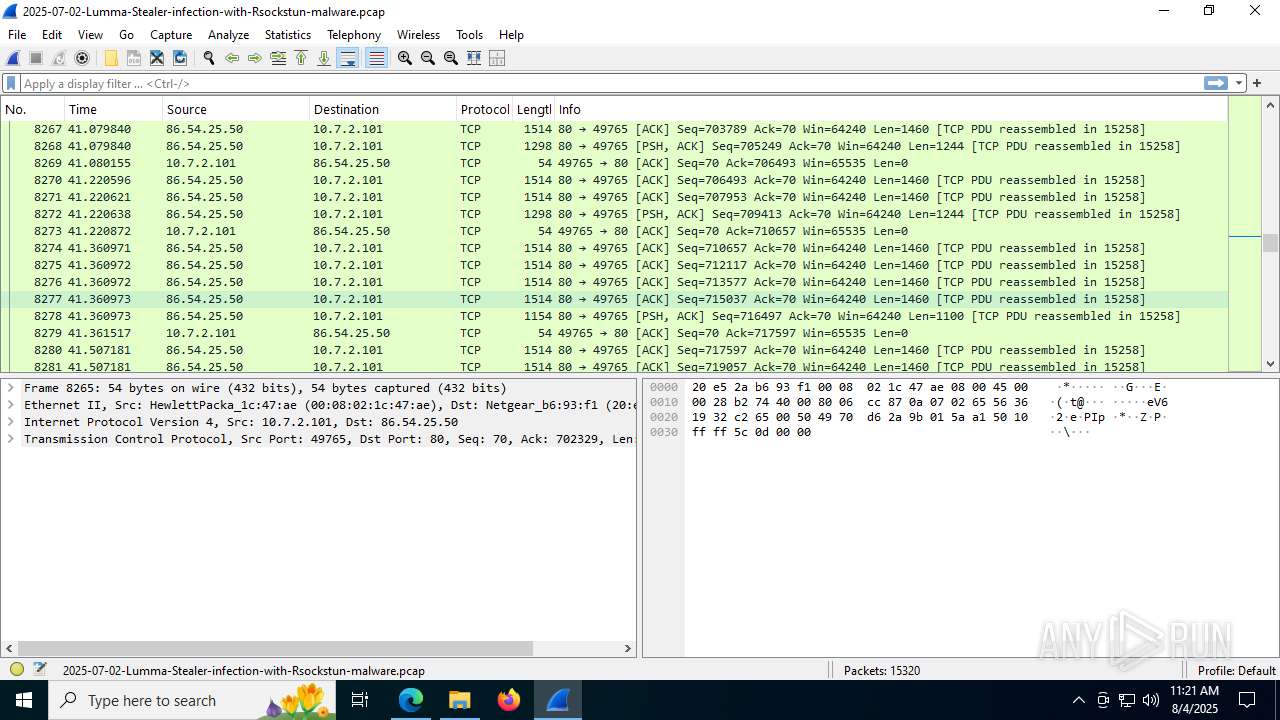
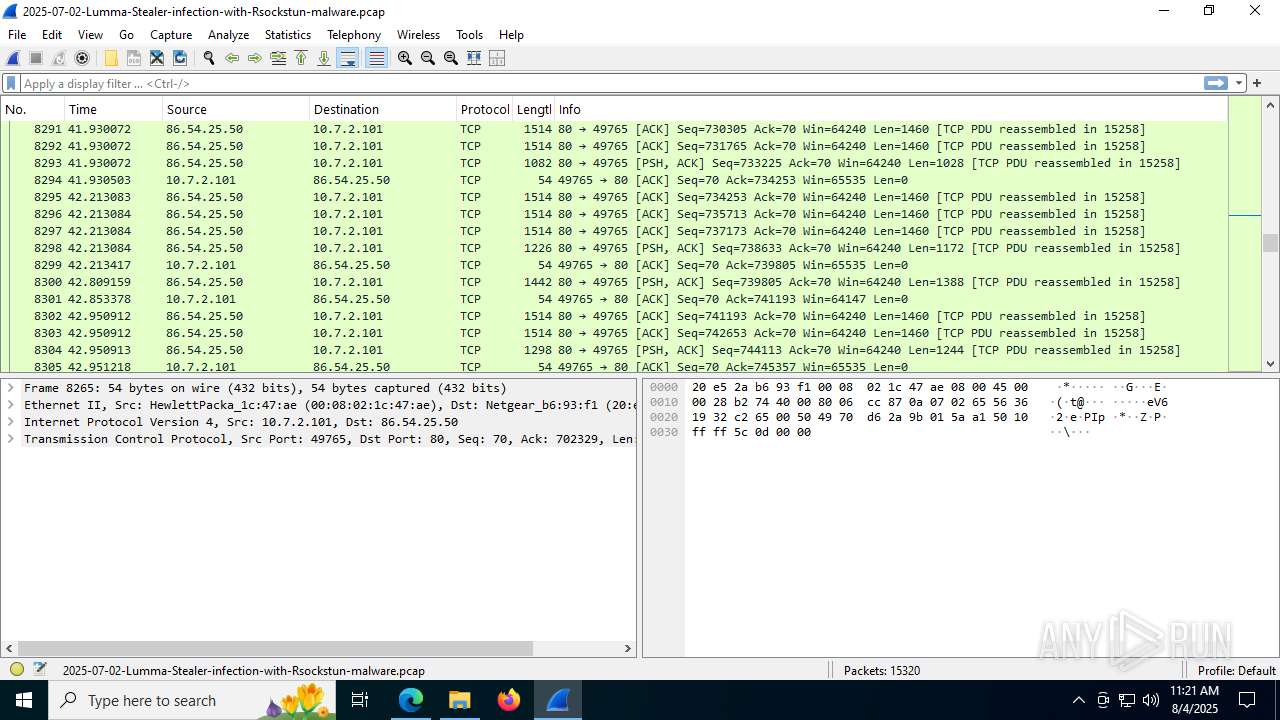
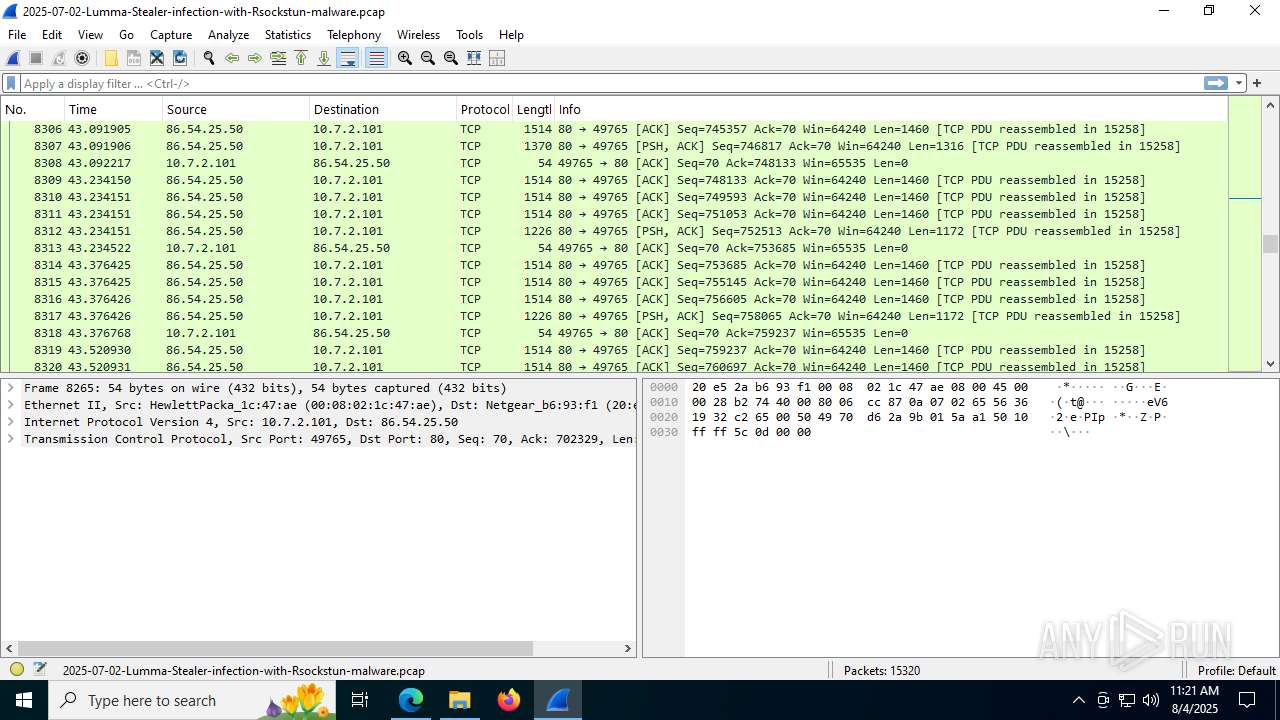
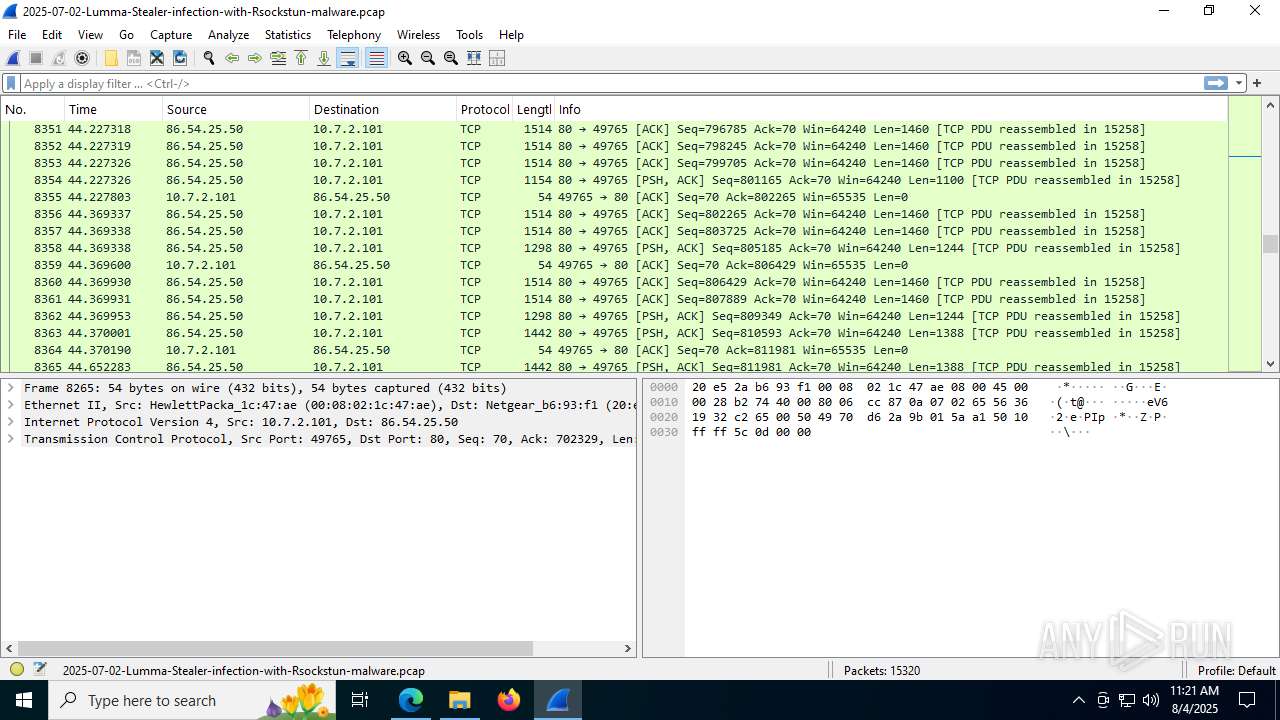
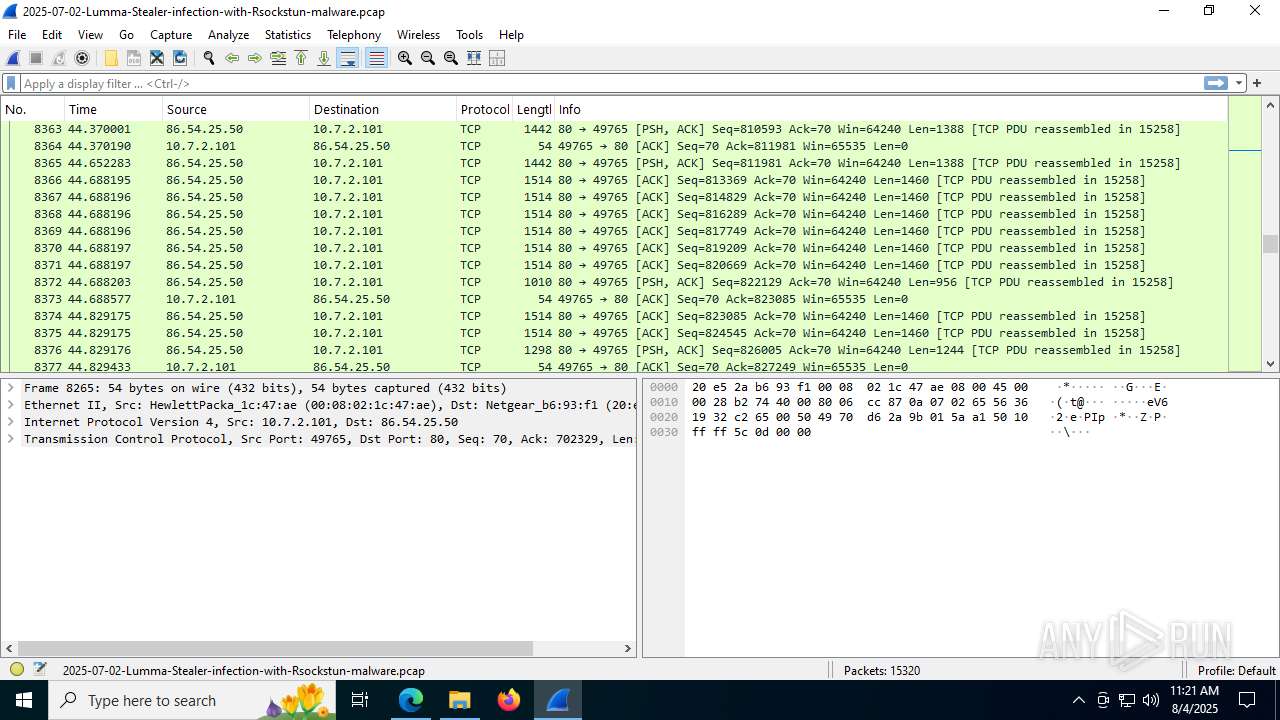
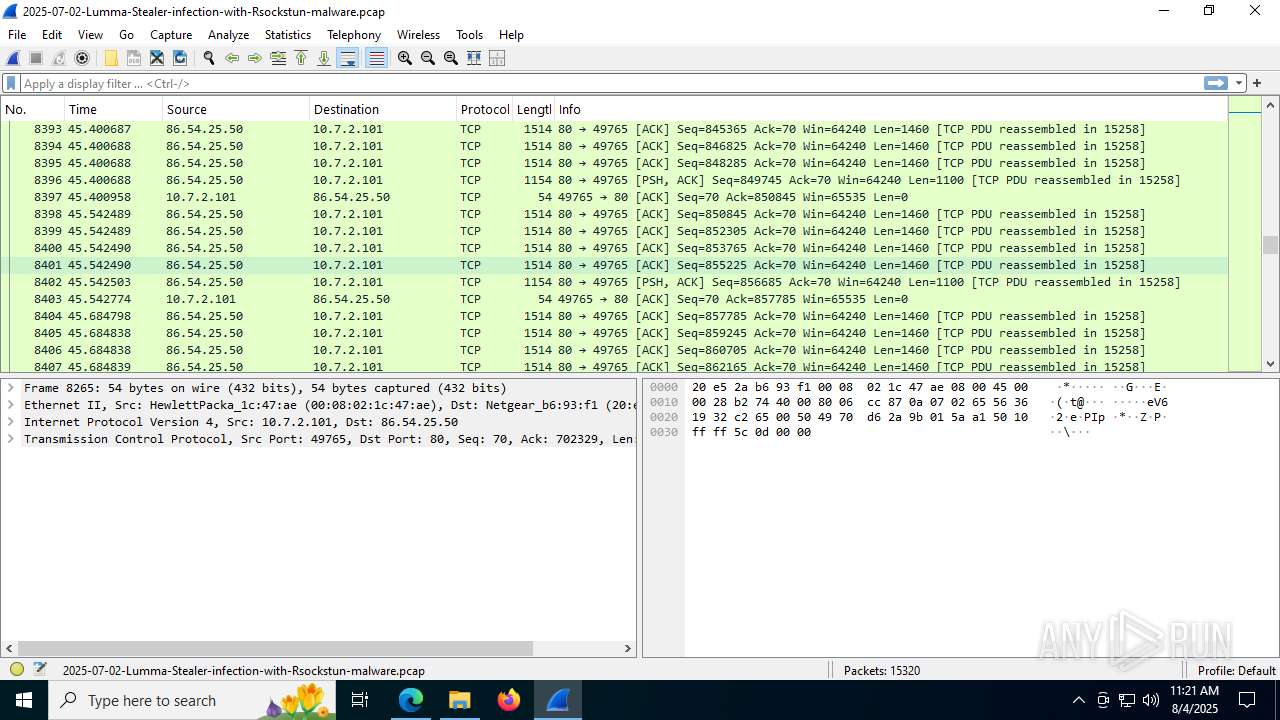
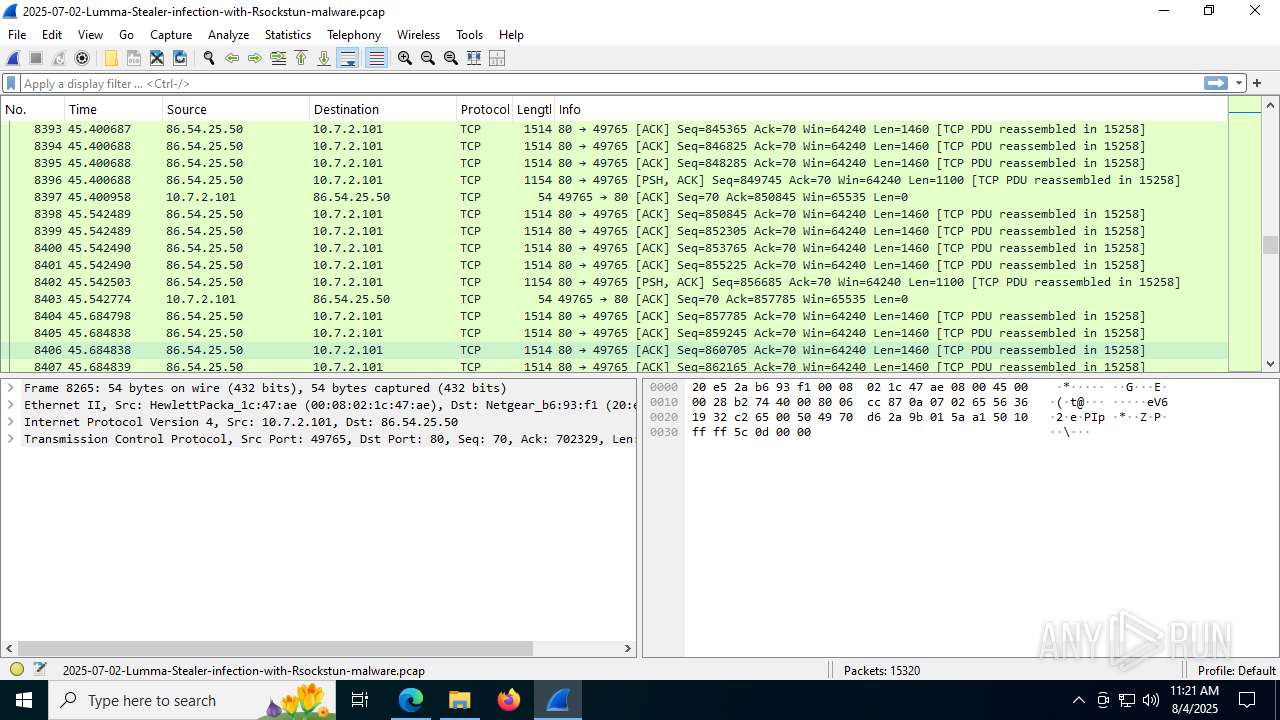
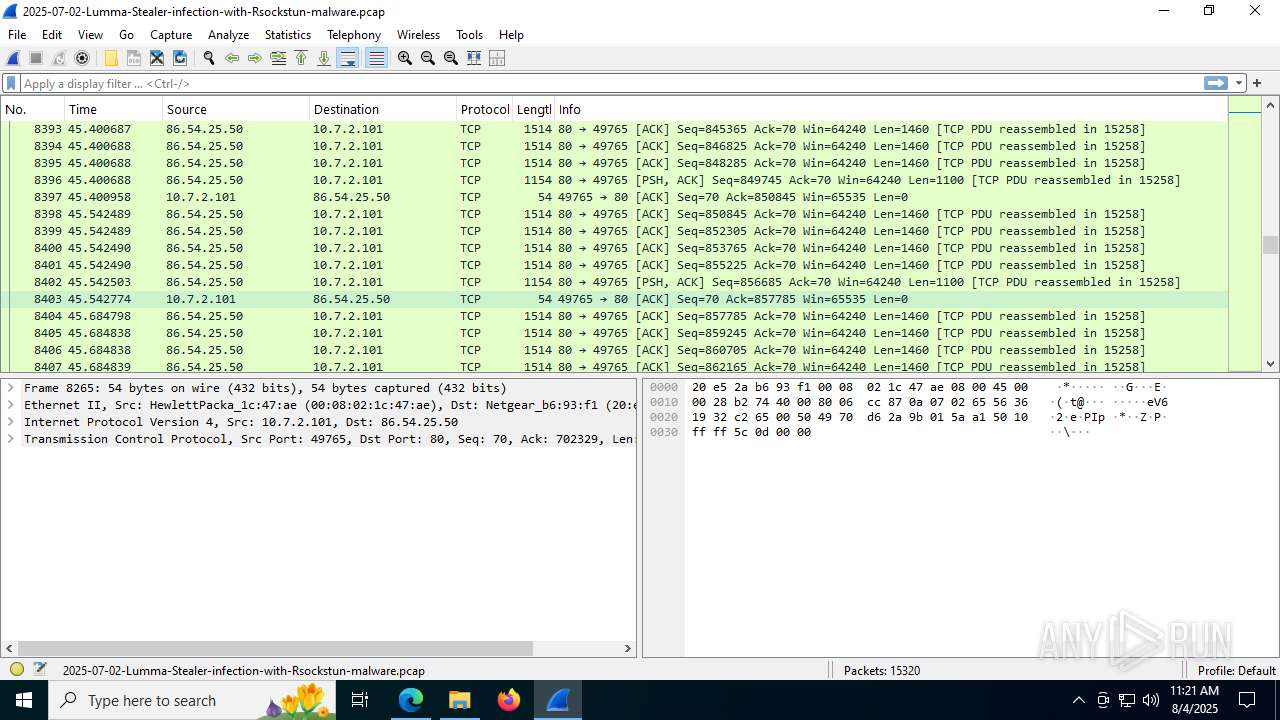
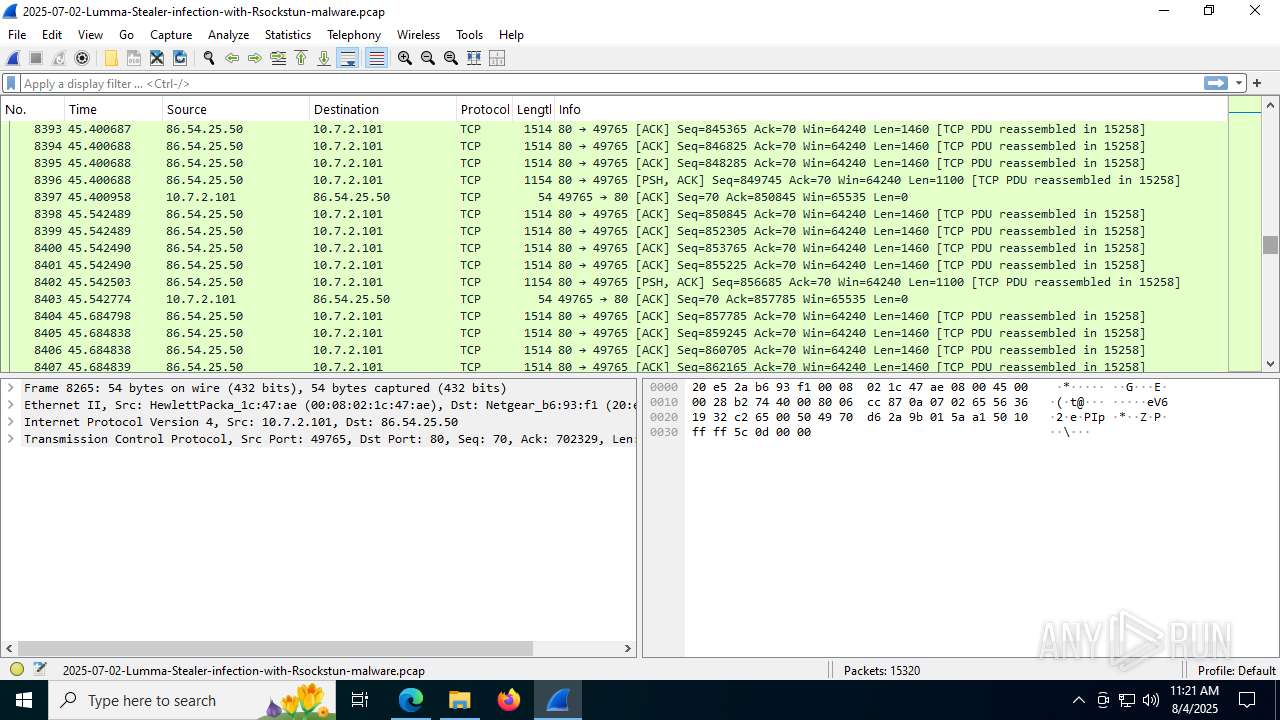
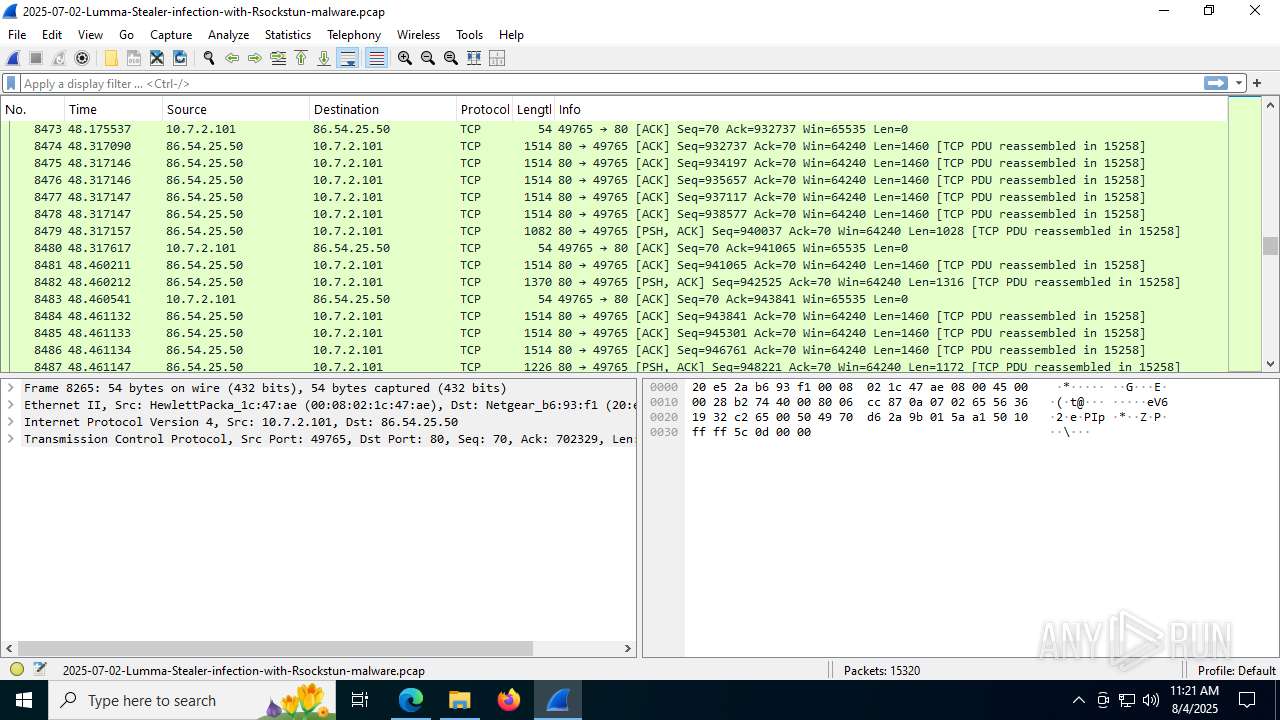
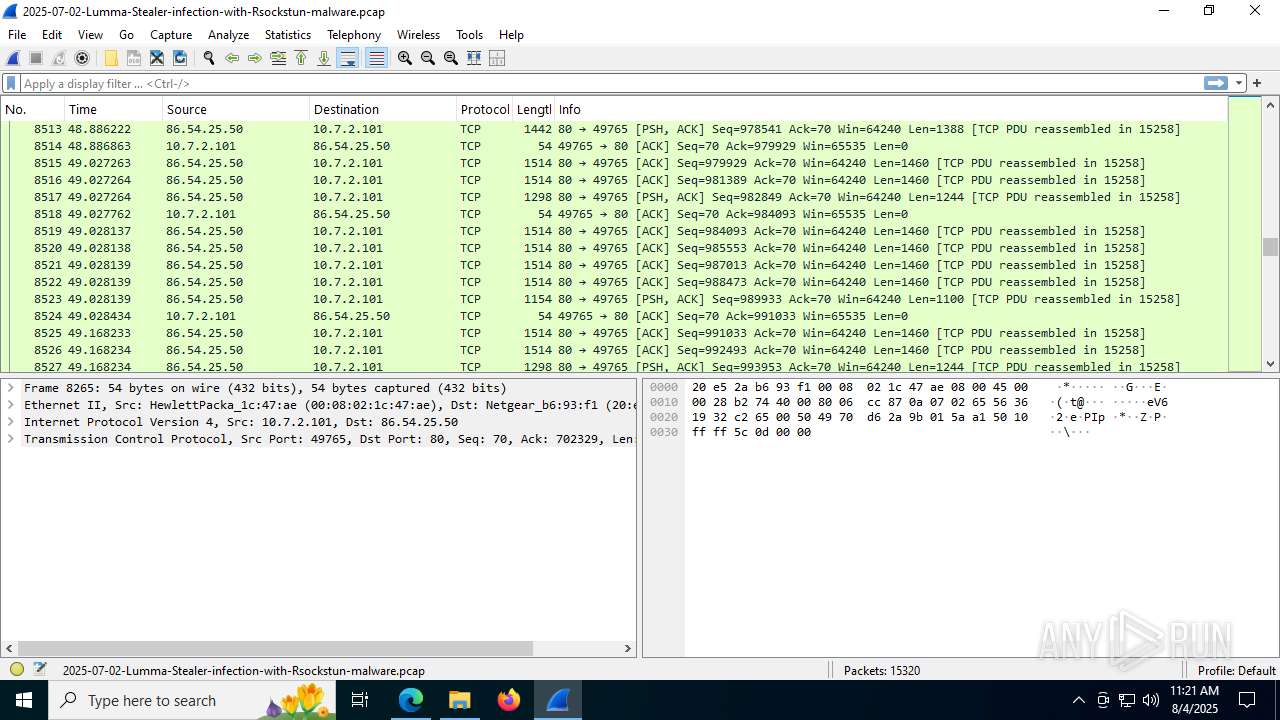
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
144
DNS requests
184
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3732 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:QuU82PNY0utM4jPMvOP063TTjFN1QPIngQUhXwXHZHQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7104 | svchost.exe | GET | 200 | 23.196.96.159:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1300 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7748 | svchost.exe | HEAD | 200 | 23.53.40.11:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754762014&P2=404&P3=2&P4=ag0wXYDPJ5oA2YTqJ%2ftVZ%2fE3w1xplVPsH1S%2f2sTHgwCWUdKLpQlcpb%2bzmR8FmIxDPMvtRKrJQ0PMbB9j%2bazAdA%3d%3d | unknown | — | — | whitelisted |
1300 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7748 | svchost.exe | GET | 206 | 23.53.40.11:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754762014&P2=404&P3=2&P4=ag0wXYDPJ5oA2YTqJ%2ftVZ%2fE3w1xplVPsH1S%2f2sTHgwCWUdKLpQlcpb%2bzmR8FmIxDPMvtRKrJQ0PMbB9j%2bazAdA%3d%3d | unknown | — | — | whitelisted |
7748 | svchost.exe | GET | 206 | 23.53.40.11:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1754762014&P2=404&P3=2&P4=ag0wXYDPJ5oA2YTqJ%2ftVZ%2fE3w1xplVPsH1S%2f2sTHgwCWUdKLpQlcpb%2bzmR8FmIxDPMvtRKrJQ0PMbB9j%2bazAdA%3d%3d | unknown | — | — | whitelisted |
7748 | svchost.exe | HEAD | 200 | 23.53.40.11:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1754762013&P2=404&P3=2&P4=epnYV790if8eLhgb1U6McQ%2fUzhbMuhkCE17K8zOn4WyXrUE67dB%2bm%2b67VAK9kZ4z44Xn3t9vDCsE5Q%2fjLf9L1w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3732 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3732 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3732 | msedge.exe | 199.201.110.204:443 | www.malware-traffic-analysis.net | NAMECHEAP-NET | US | suspicious |
3732 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3732 | msedge.exe | 95.101.142.195:443 | copilot.microsoft.com | Akamai International B.V. | SE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.malware-traffic-analysis.net |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3732 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |