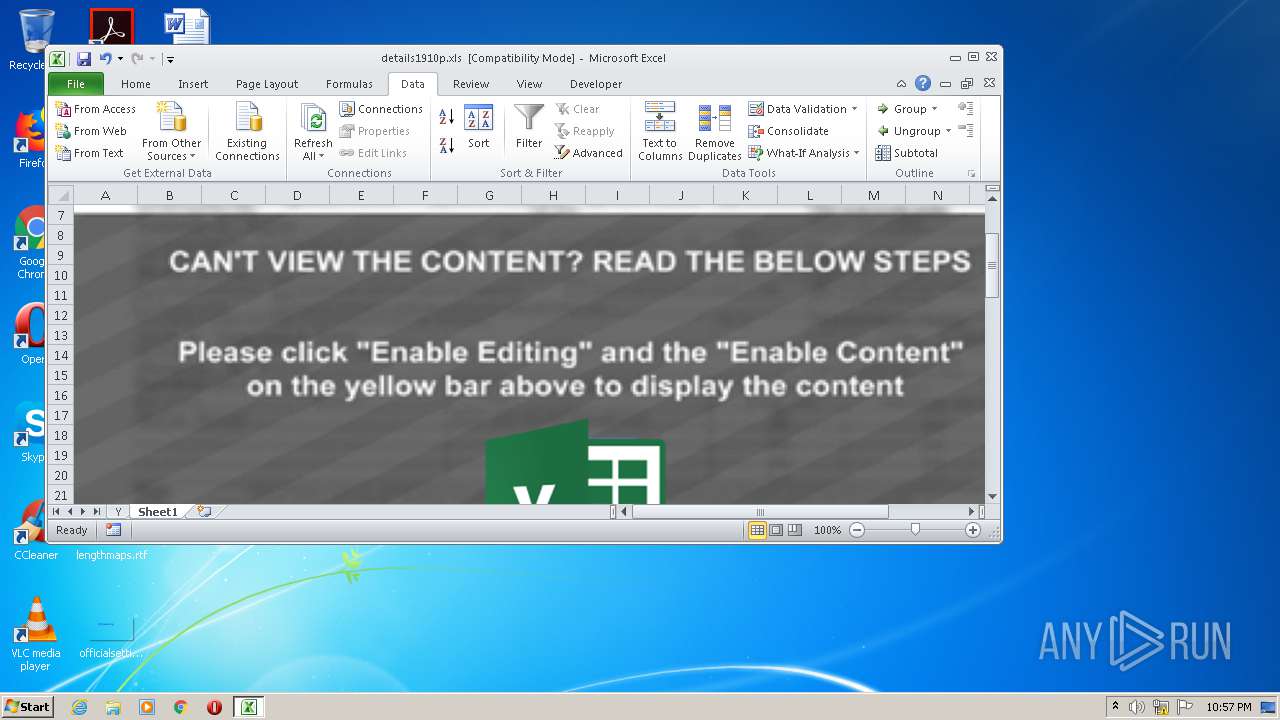
| File name: | details1910p.xls |
| Full analysis: | https://app.any.run/tasks/cbe9f116-076d-4345-81fe-2bfc04157551 |
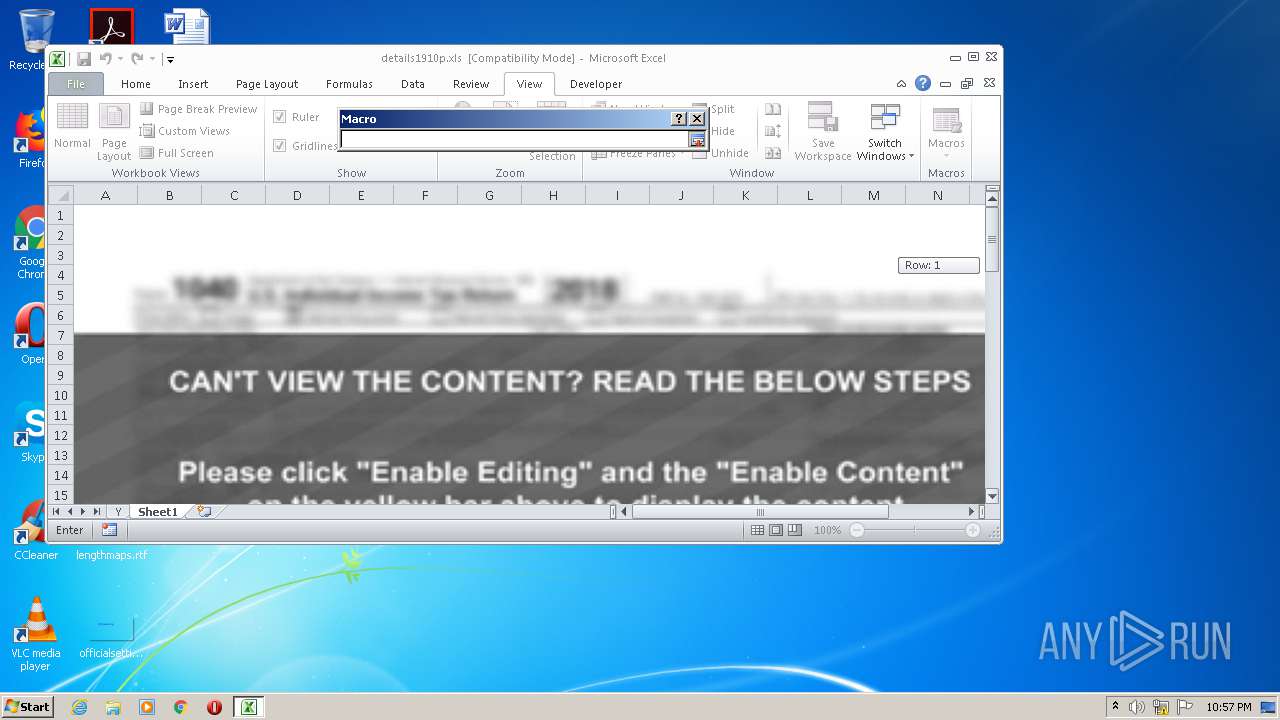
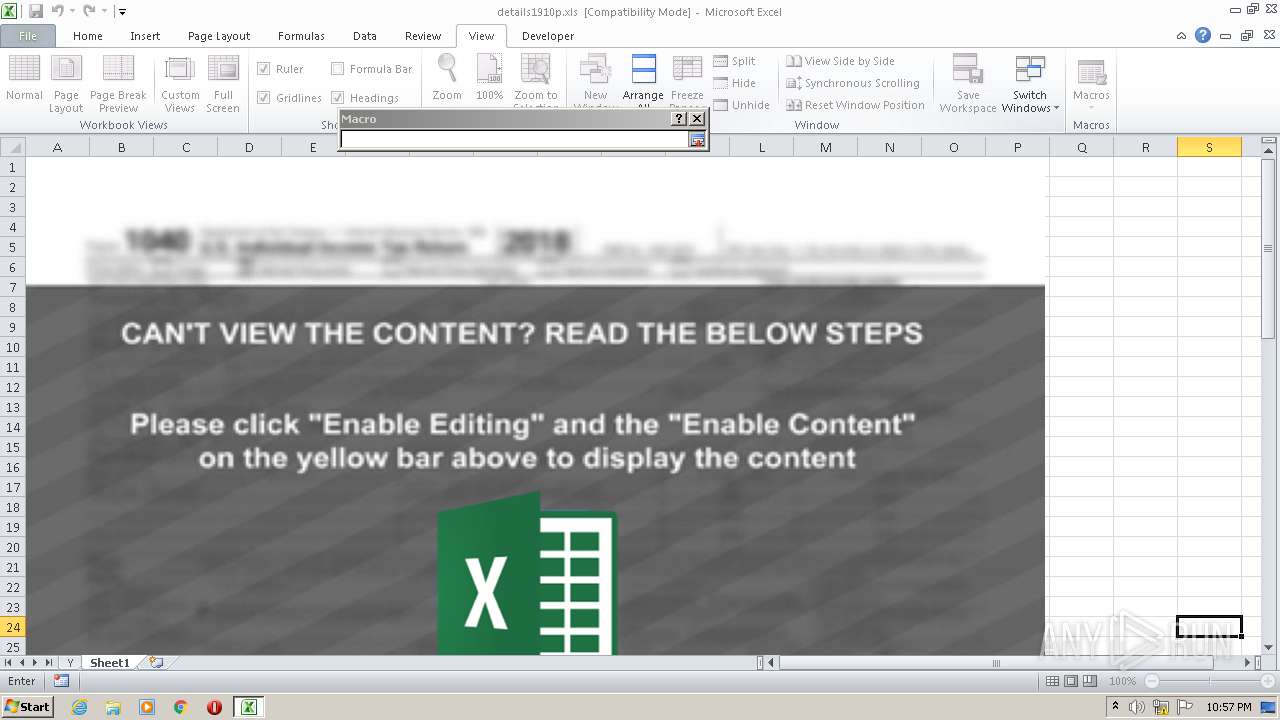
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 21:56:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: UJdTKYiRR, Last Saved By: fckav, Name of Creating Application: Microsoft Excel, Create Time/Date: Mon Sep 14 22:28:14 2020, Last Saved Time/Date: Mon Oct 19 12:56:47 2020, Security: 1 |
| MD5: | 81AE5B7E0425EF813F1876A287E3C19F |
| SHA1: | AFEB5B8A3FCC28152889600C86374D31B3A1E21E |
| SHA256: | E758B12EA734EE85058F8D42FC1DCE15F535BDA4DDFF3B424C92FA617622A675 |
| SSDEEP: | 6144:WDuwQe5W9G2ylfROuStedGVK5wnoq1Yw194oGAYUIW4yyfsrH2:CQl42yPNStedIK5qoz7ohYUI5fKH2 |
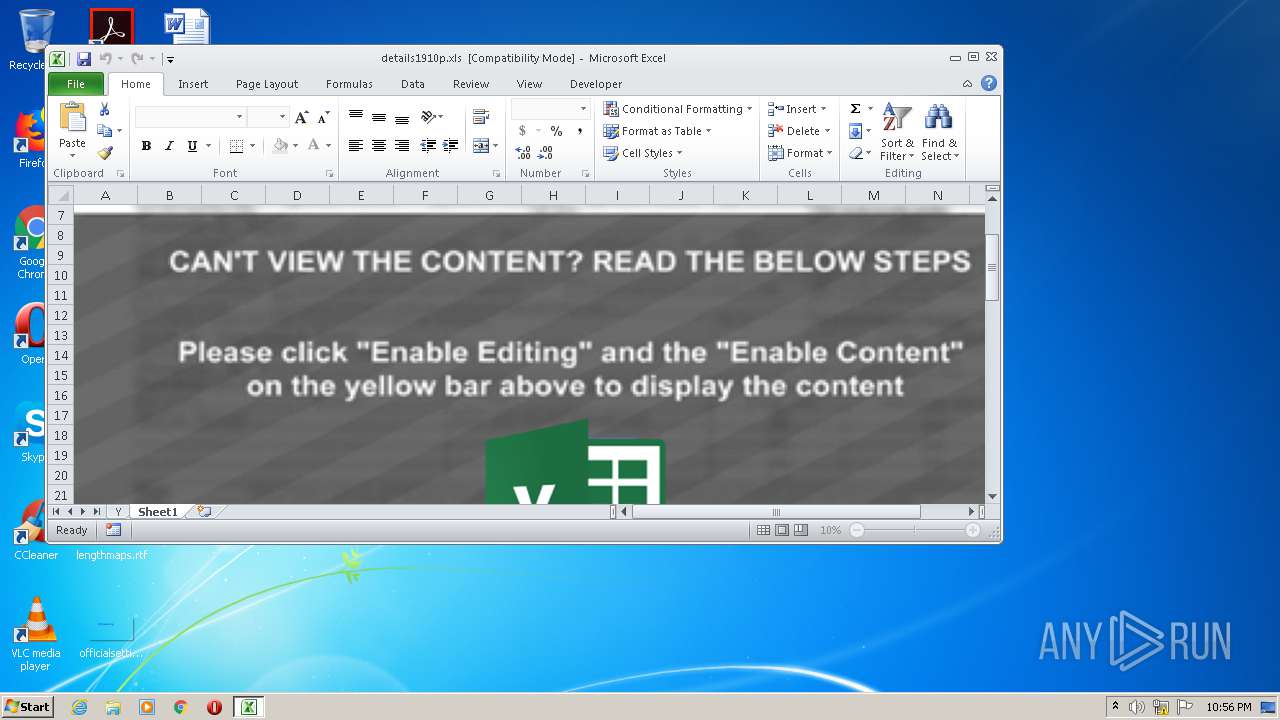
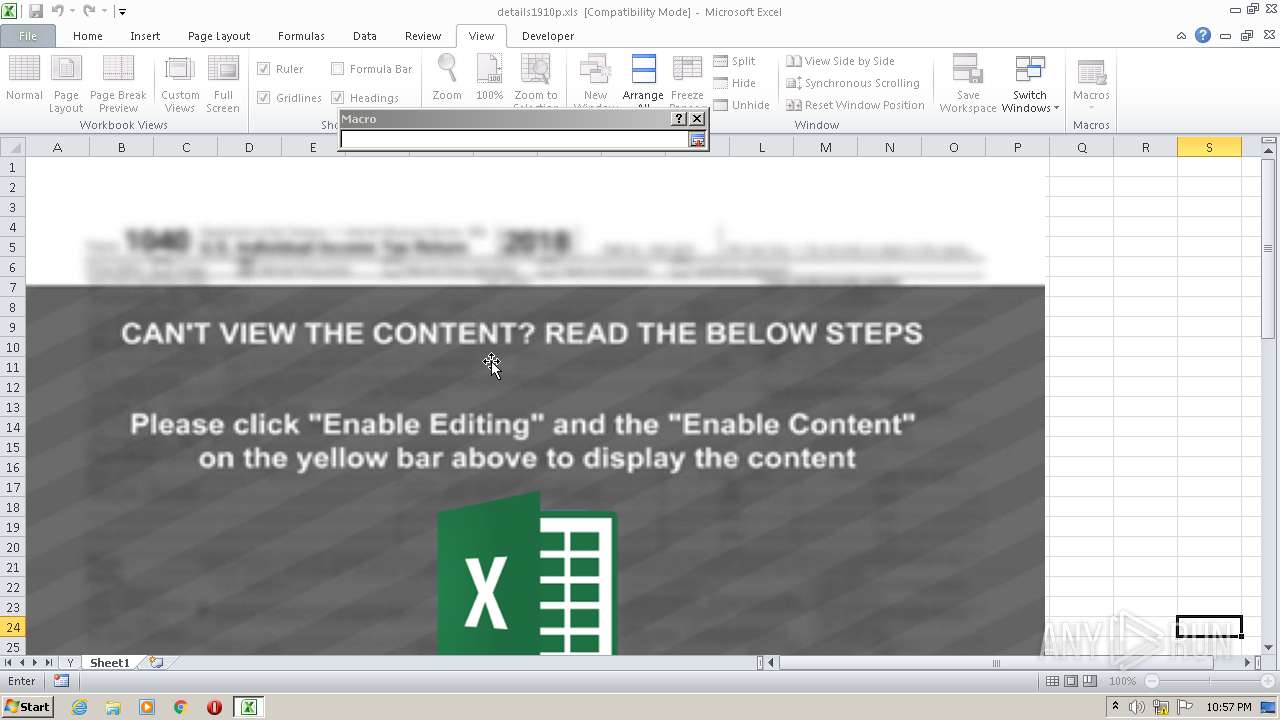
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 1436)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2536)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2536)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- EXCEL.EXE (PID: 2536)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2536)
Reads settings of System Certificates
- EXCEL.EXE (PID: 2536)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2536)
Dropped object may contain Bitcoin addresses
- EXCEL.EXE (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | UJdTKYiRR |
|---|---|
| LastModifiedBy: | fckav |
| Software: | Microsoft Excel |
| CreateDate: | 2020:09:14 21:28:14 |
| ModifyDate: | 2020:10:19 11:56:47 |
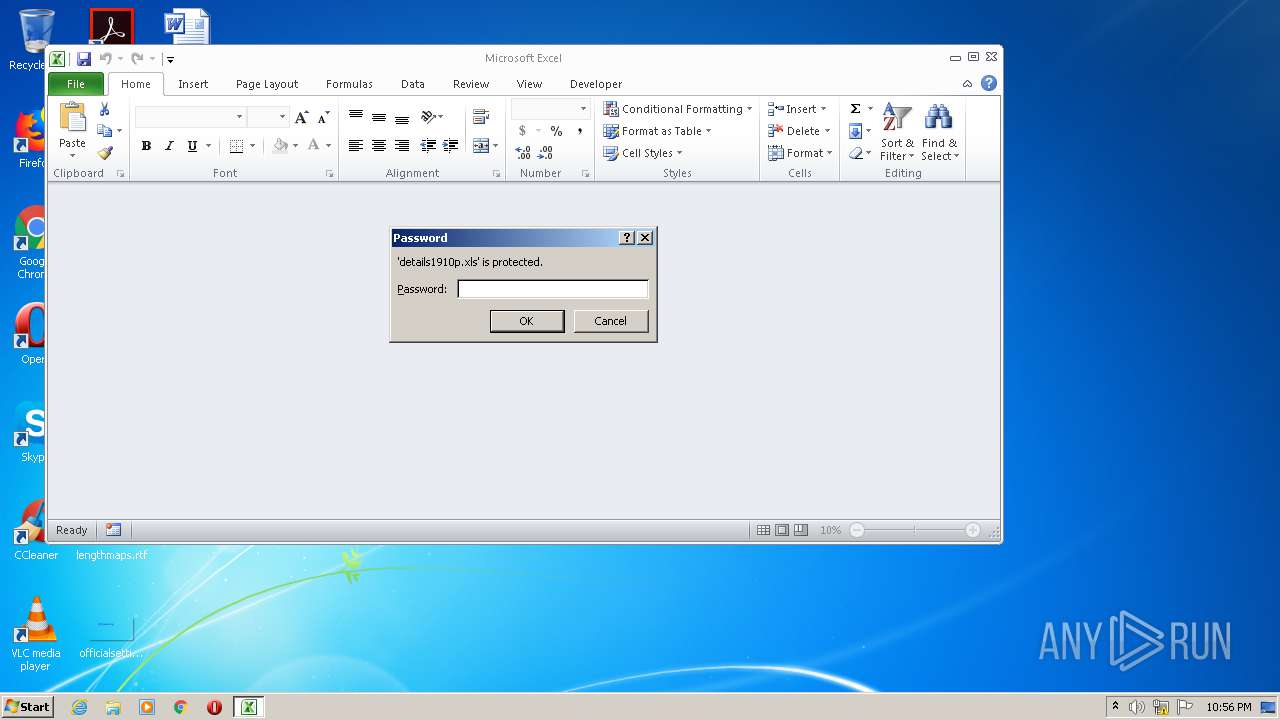
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
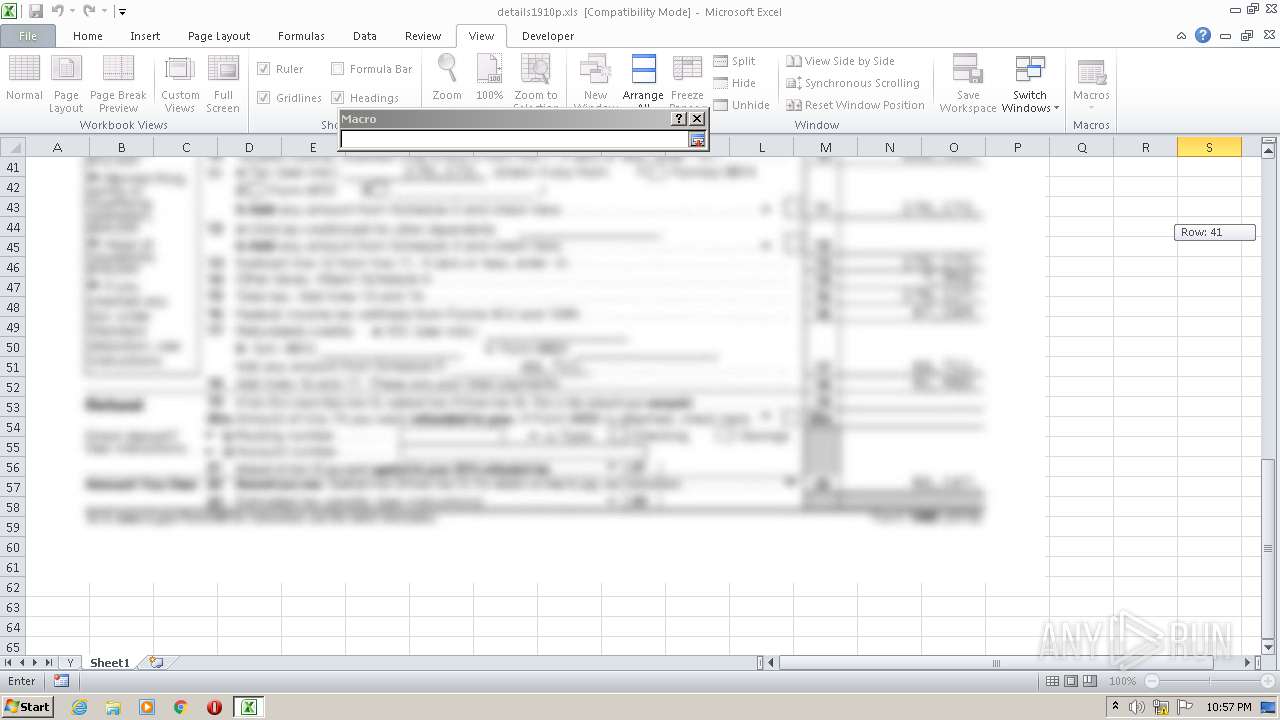
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
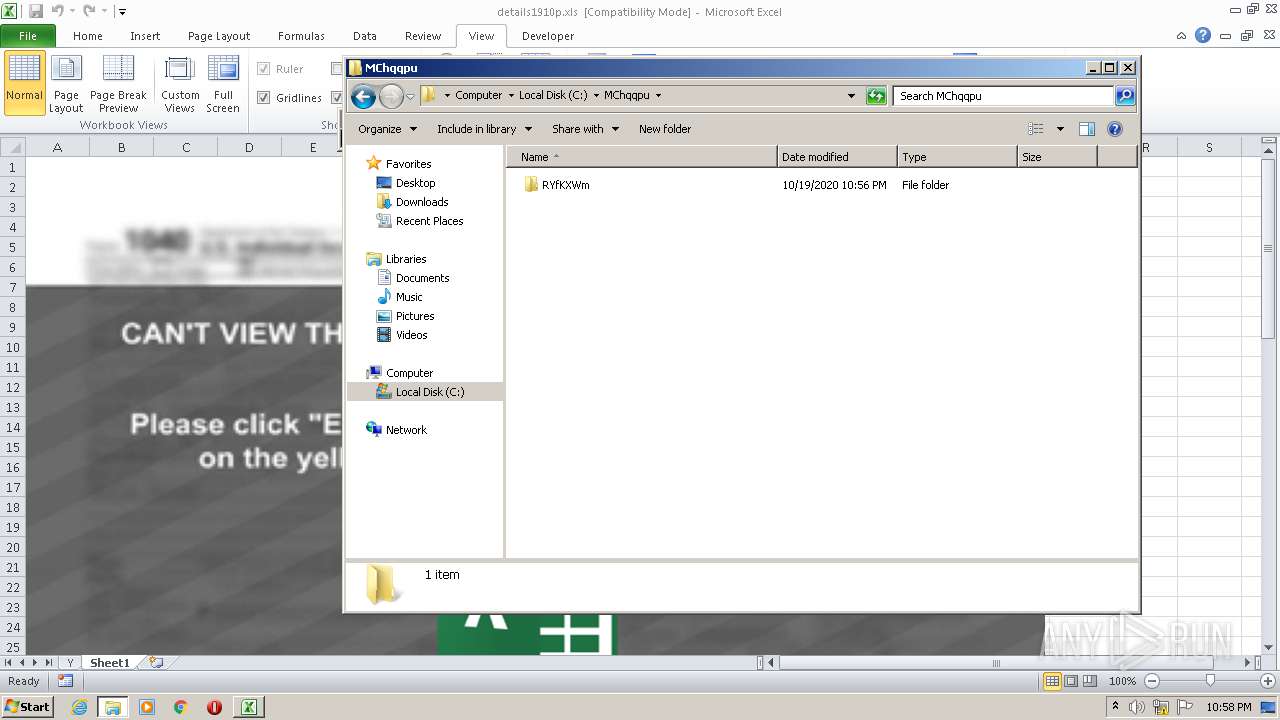
| 1436 | "C:\Windows\System32\rundll32.exe" C:\MChqqpu\RYfKXWm\YTvxeyE.dll,DllRegisterServer | C:\Windows\System32\rundll32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
632
Read events
570
Write events
51
Delete events
11
Modification events
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | !a0 |
Value: 21613000E8090000010000000000000000000000 | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2536) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
10 226
Text files
3 853
Unknown types
324
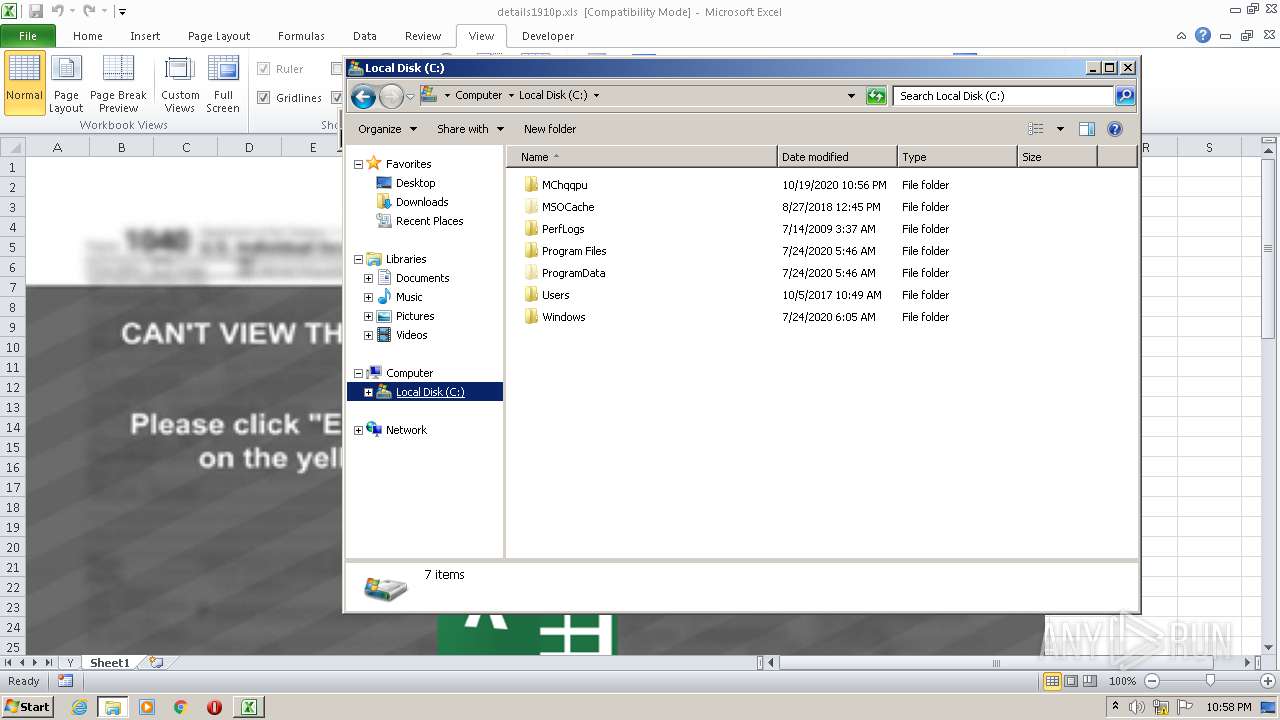
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR41A1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Cab5EC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\Tar5EC1.tmp | — | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B5FE026684E25755B7DDA2B6DA04802E | der | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\xlsp[1].c1 | executable | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B5FE026684E25755B7DDA2B6DA04802E | binary | |
MD5:— | SHA256:— | |||
| 2536 | EXCEL.EXE | C:\MChqqpu\RYfKXWm\YTvxeyE.dll | executable | |
MD5:— | SHA256:— | |||
| 1436 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\tmp.txt | pkr | |
MD5:6A718954D6485A2914AE5B6008299FDD | SHA256:E803661BF5A6E32AA747BE93DC4C524D83DDB96A249408A995DD70D8BD75B23D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
19
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | EXCEL.EXE | GET | 200 | 2.16.186.11:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgP%2FwJM4%2B%2BW8XmaTs%2B1dnHZ4sQ%3D%3D | unknown | der | 527 b | whitelisted |
2536 | EXCEL.EXE | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | EXCEL.EXE | 8.208.102.117:443 | donwloadfiles.top | Level 3 Communications, Inc. | US | unknown |
2536 | EXCEL.EXE | 2.16.186.35:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 45.128.207.226:443 | fqnceas.su | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
donwloadfiles.top |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
fqnceas.su |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
— | — | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |