| File name: | AndroidSideloader (1).exe |
| Full analysis: | https://app.any.run/tasks/b0d43a4d-4f7b-4477-9f9f-eb94894122ae |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 21:32:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 7217E01AE397FCA628AE75E48D5AFC01 |
| SHA1: | BD7785122291870BC118D81E215B9BC0B2FC7D06 |
| SHA256: | E7557E48EA1E5FAF1880FD50AAB3EC04A15A6A617EA65C090FF8A619B8FC3B22 |
| SSDEEP: | 98304:UcEQQLhicXQ+9nWuWqVM5XflB2bz14ZPQ:I |
MALICIOUS
No malicious indicators.SUSPICIOUS
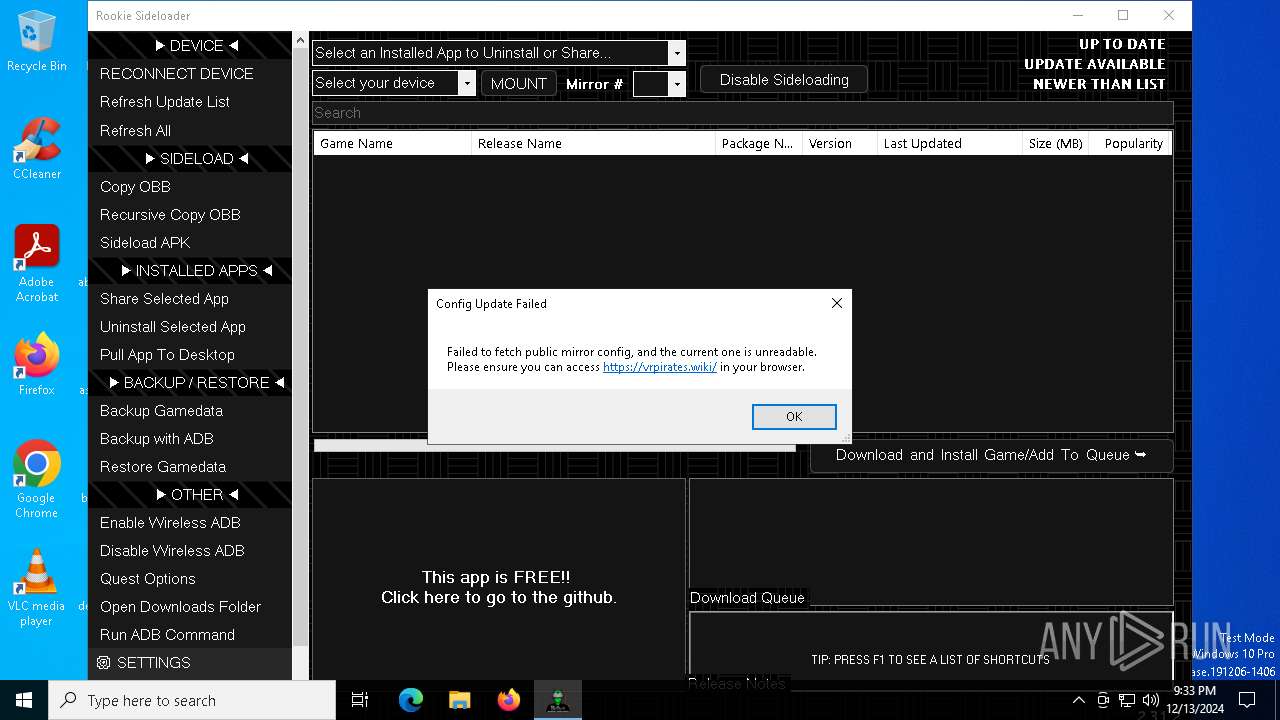
Reads security settings of Internet Explorer
- AndroidSideloader (1).exe (PID: 6240)
Drops 7-zip archiver for unpacking
- AndroidSideloader (1).exe (PID: 6240)
Executable content was dropped or overwritten
- AndroidSideloader (1).exe (PID: 6240)
- 7z.exe (PID: 6776)
Application launched itself
- adb.exe (PID: 7008)
RCLONE has been detected
- rclone.exe (PID: 4520)
- rclone.exe (PID: 4120)
- rclone.exe (PID: 6212)
INFO
Checks supported languages
- AndroidSideloader (1).exe (PID: 6240)
- 7z.exe (PID: 6776)
- adb.exe (PID: 6944)
- adb.exe (PID: 7008)
- adb.exe (PID: 7112)
- rclone.exe (PID: 4120)
- 7z.exe (PID: 6876)
- rclone.exe (PID: 4520)
- rclone.exe (PID: 6212)
Reads the computer name
- AndroidSideloader (1).exe (PID: 6240)
- 7z.exe (PID: 6776)
- adb.exe (PID: 7112)
- 7z.exe (PID: 6876)
- rclone.exe (PID: 6212)
- rclone.exe (PID: 4520)
Create files in a temporary directory
- AndroidSideloader (1).exe (PID: 6240)
- 7z.exe (PID: 6876)
- adb.exe (PID: 7112)
Reads the machine GUID from the registry
- AndroidSideloader (1).exe (PID: 6240)
The process uses the downloaded file
- AndroidSideloader (1).exe (PID: 6240)
Checks proxy server information
- AndroidSideloader (1).exe (PID: 6240)
Disables trace logs
- AndroidSideloader (1).exe (PID: 6240)
The sample compiled with english language support
- AndroidSideloader (1).exe (PID: 6240)
- 7z.exe (PID: 6776)
Reads the software policy settings
- AndroidSideloader (1).exe (PID: 6240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2092:08:12 03:01:05+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 3984896 |
| InitializedDataSize: | 413184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3cec0e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
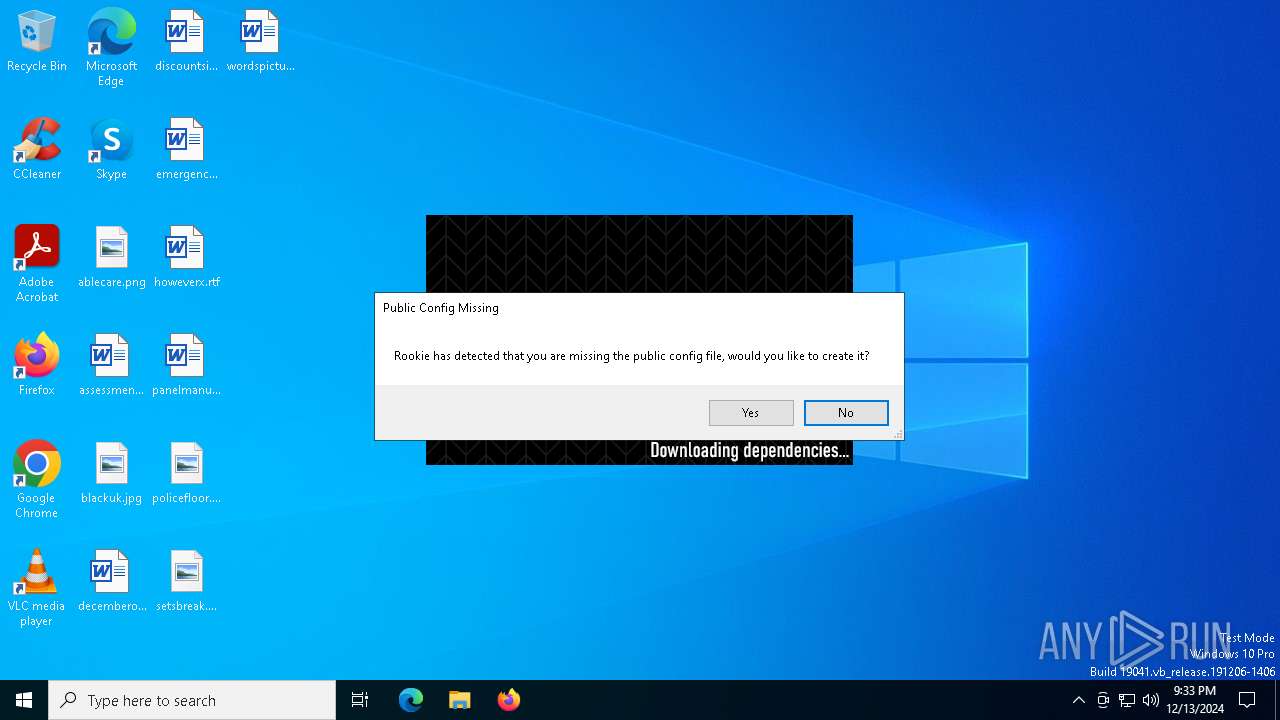
| Comments: | Rookie Sideloader |
| CompanyName: | Rookie.AndroidSideloader |
| FileDescription: | AndroidSideloader |
| FileVersion: | 2.0.0.0 |
| InternalName: | AndroidSideloader.exe |
| LegalCopyright: | Copyright © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | AndroidSideloader.exe |
| ProductName: | AndroidSideloader |
| ProductVersion: | 2.0.0.0 |
| AssemblyVersion: | 2.0.0.0 |
Total processes
144
Monitored processes
16
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4120 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" sync ":Quest Games/.meta/notes" "C:\Users\admin\AppData\Local\Temp\notes" --config vrp.download.config --inplace | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | AndroidSideloader (1).exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 1 Version: 1.68.2 Modules
| |||||||||||||||
| 4520 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" listremotes --config vrp.download.config --inplace | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | AndroidSideloader (1).exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 0 Version: 1.68.2 Modules
| |||||||||||||||
| 5096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | rclone.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6212 | "C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe" sync ":Quest Games/.meta/thumbnails" "C:\Users\admin\AppData\Local\Temp\thumbnails" --transfers 10 --config vrp.download.config --inplace | C:\Users\admin\AppData\Local\Temp\rclone\rclone.exe | AndroidSideloader (1).exe | ||||||||||||
User: admin Company: https://rclone.org Integrity Level: MEDIUM Description: Rclone Exit code: 1 Version: 1.68.2 Modules
| |||||||||||||||
| 6240 | "C:\Users\admin\AppData\Local\Temp\AndroidSideloader (1).exe" | C:\Users\admin\AppData\Local\Temp\AndroidSideloader (1).exe | explorer.exe | ||||||||||||
User: admin Company: Rookie.AndroidSideloader Integrity Level: MEDIUM Description: AndroidSideloader Exit code: 4294967295 Version: 2.0.0.0 Modules
| |||||||||||||||
| 6776 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\dependencies.7z" -y -o"C:\RSL\platform-tools" -bsp1 | C:\Users\admin\AppData\Local\Temp\7z.exe | AndroidSideloader (1).exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 6784 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6876 | "7z.exe" x "C:\Users\admin\AppData\Local\Temp\rclone.zip" -y -o"C:\Users\admin\AppData\Local\Temp" -bsp1 | C:\Users\admin\AppData\Local\Temp\7z.exe | — | AndroidSideloader (1).exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
Total events
10 544
Read events
10 530
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6240) AndroidSideloader (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\AndroidSideloader (1)_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
16
Suspicious files
2
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\dependencies.7z | — | |
MD5:— | SHA256:— | |||
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\CleanupInstall.cmd | text | |
MD5:90B4AFB2EAA57F8C8C2DD43EB9F3339E | SHA256:B3AC3DC1F31FC857A53A5670740EB9666682F03B0552EB1E4AE4E48A51DDC259 | |||
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\7z.dll | executable | |
MD5:71EBAC040D32560BB9D76A552A7CB986 | SHA256:1AA51AA9BB50B26BB652D9C442208DB76546286B0DB169C8882DE97D1117029D | |||
| 6776 | 7z.exe | C:\RSL\platform-tools\NOTICE.txt | text | |
MD5:E7E8B9497810834CAB9522FE5DD80560 | SHA256:D25FAFFB58D73FEF75D10B7D9B49D8D9872CBB33018F23232D04E8C3EA9DC4DB | |||
| 6776 | 7z.exe | C:\RSL\platform-tools\hprof-conv.exe | executable | |
MD5:1952192783C64352A6C93F2562FAAA56 | SHA256:35D9734B4F8A0F82698578F3529E946C6FE21F70AE245ABA61AADE6B52CC6E14 | |||
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\settings.json | binary | |
MD5:0F242917356505631FBC083BBDD88AB4 | SHA256:7641FC841919815AB250CAA8110CCB7BBCCFB9E989F3FB0D82C3BF8CE3EB039C | |||
| 6776 | 7z.exe | C:\RSL\platform-tools\mke2fs.conf | text | |
MD5:699098CA95F87BA48BB94A3E848549B3 | SHA256:AD58A58DCDD24D85055814CA9CAC67DB89D4E67C434E96774BDCE0D0A007D067 | |||
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\debuglog.txt | text | |
MD5:D85BF0E65B56BD56EFF7C62B8A43B85C | SHA256:64F7E806BE24F936CB4CC20292CA606FF212D5B122E55F451A09815E155890CC | |||
| 6240 | AndroidSideloader (1).exe | C:\Users\admin\AppData\Local\Temp\Rookie Offline.cmd | text | |
MD5:513248E44025E42FD2B8F9280501A8BB | SHA256:7DD245A6267A6D9500EE6B13A29FBDD80CEF9A020162C0E24A228558C58FA092 | |||
| 6876 | 7z.exe | C:\Users\admin\AppData\Local\Temp\rclone-v1.68.2-windows-amd64\rclone.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
38
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
396 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
396 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6148 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6148 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4308 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1480 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
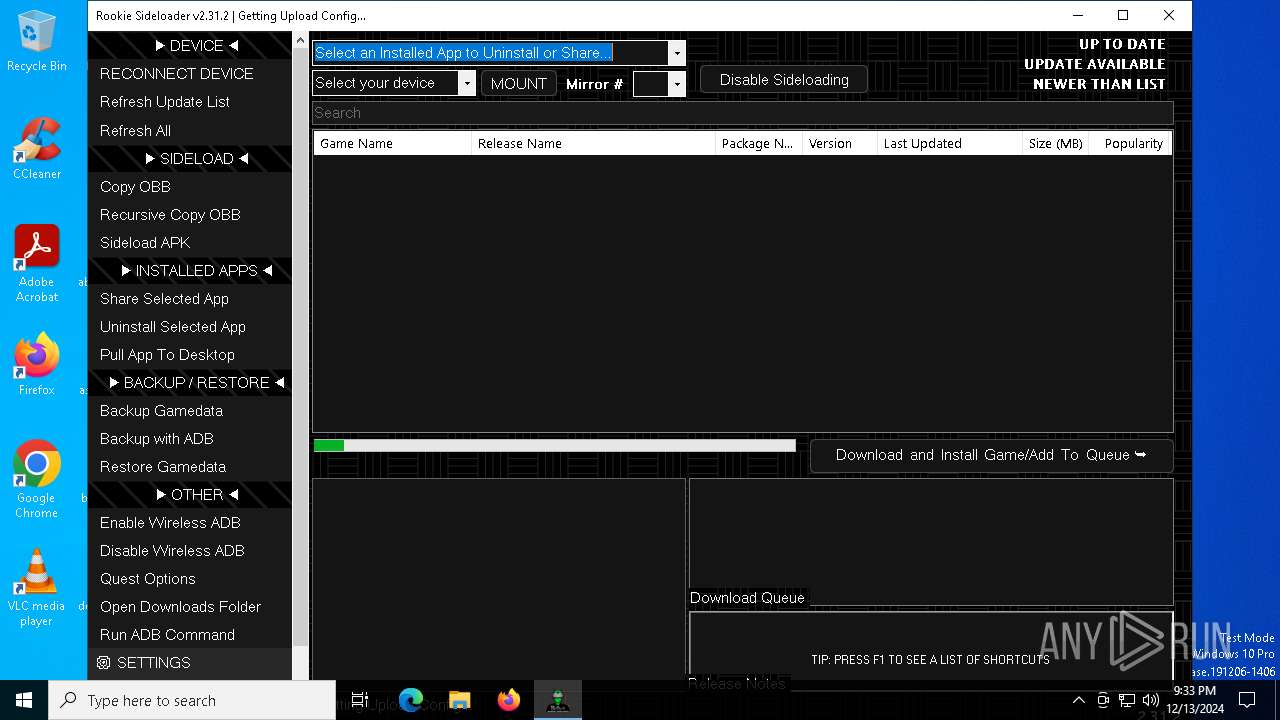
github.com |
| shared |
raw.githubusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
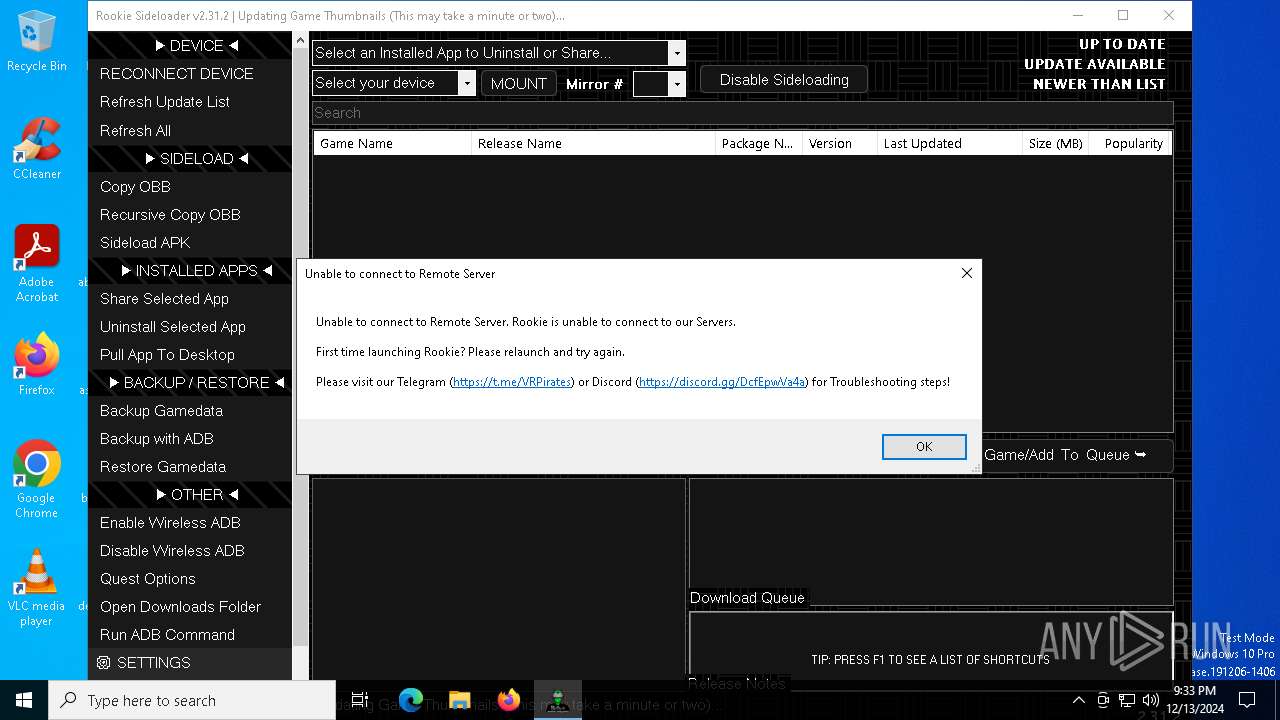
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6240 | AndroidSideloader (1).exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |