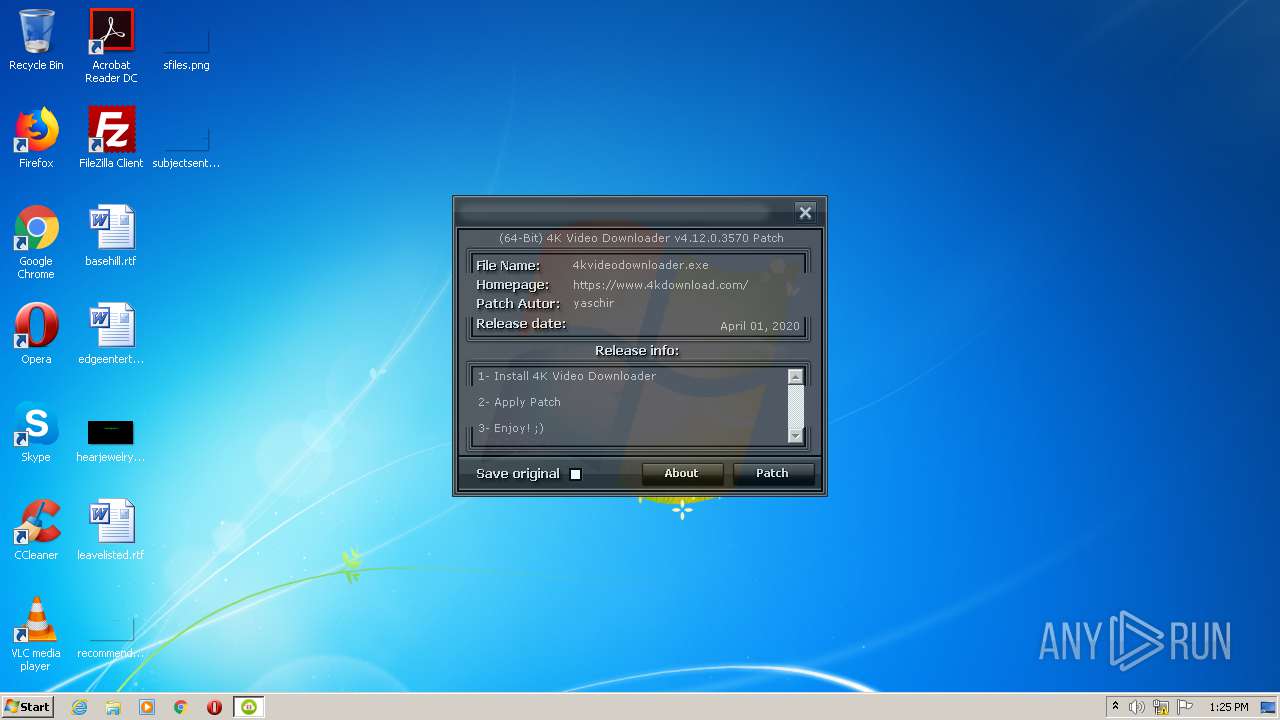
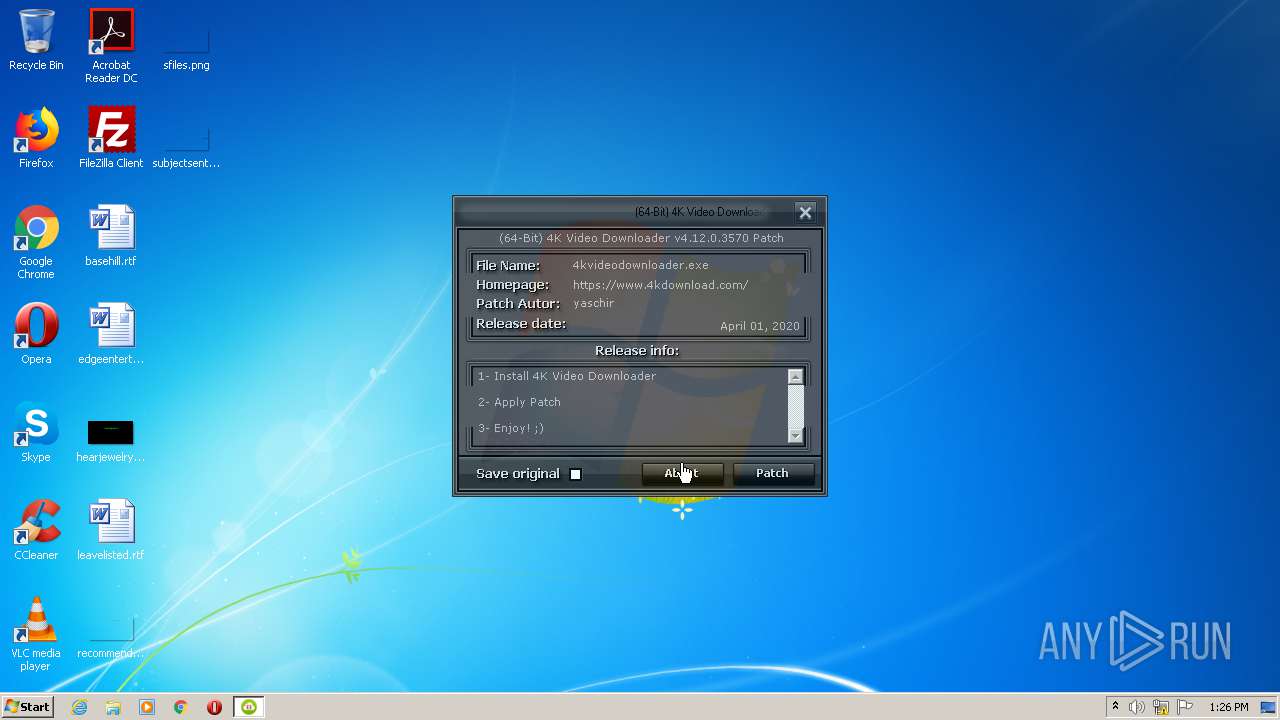
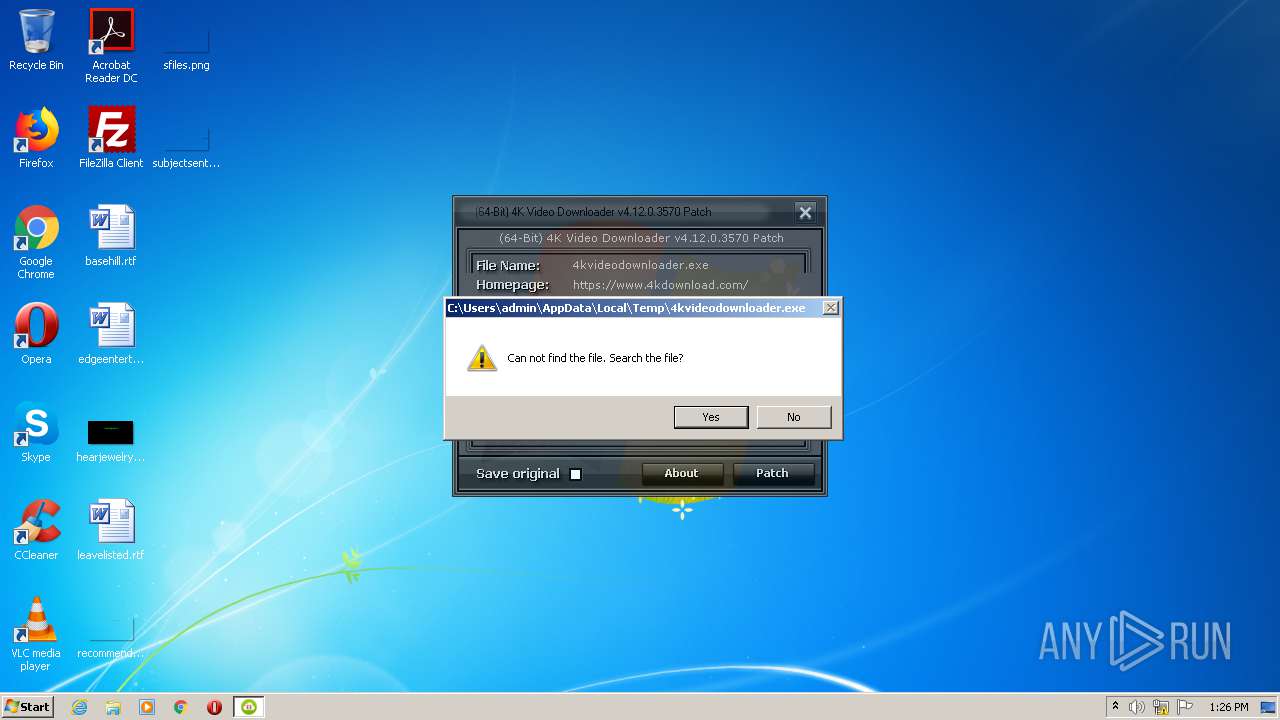
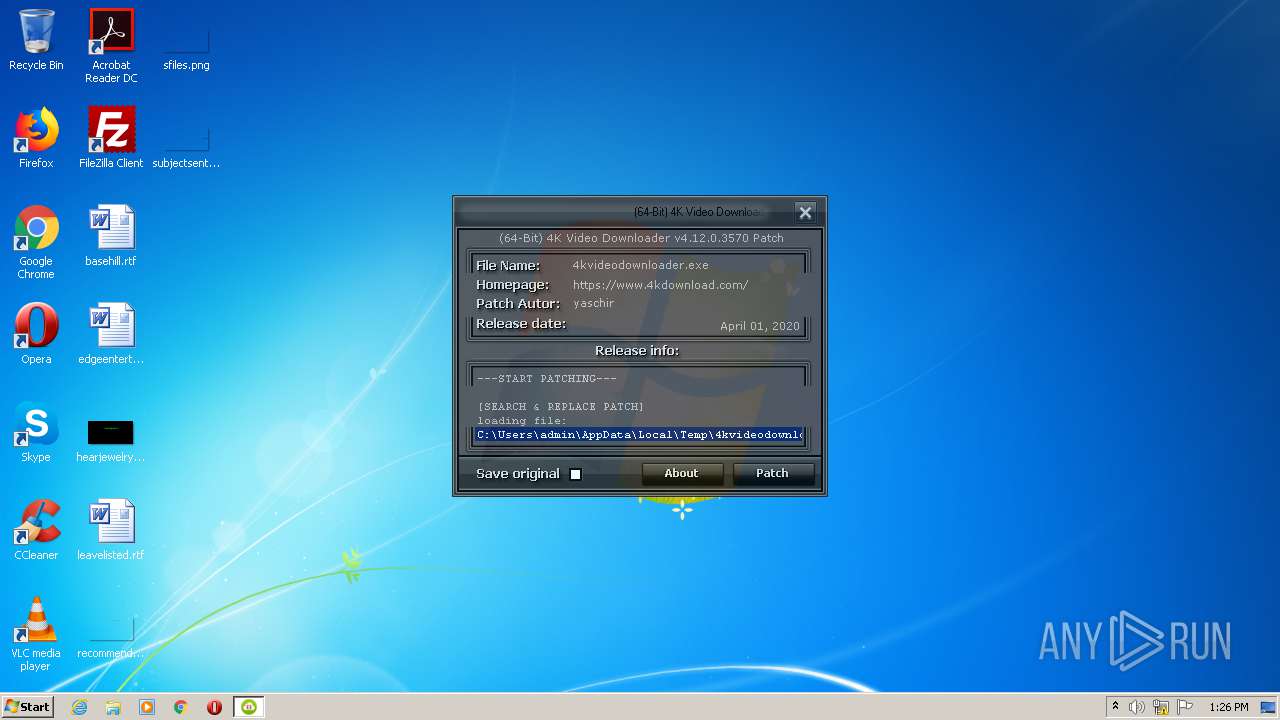
| File name: | (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe |
| Full analysis: | https://app.any.run/tasks/2731368c-338a-48c0-8bb6-45d70ea0c324 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 13:25:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FE71F947493742FA60F05154562B9F5E |
| SHA1: | 193267789B6A8D864D163F13CF7C82ED96FA37D5 |
| SHA256: | E74DFE49D0AA5892B7A4AD64851F6341903819FE7EA251C01D3C1404BF7E1F6D |
| SSDEEP: | 12288:bFjoam6oDhTRL3Ql0bZf1N5mCVIlikLVdKifuhte9SOl5P+AWJexwMAlKmXkm:bWGyFR3IQZf12CWpoifuhte9SA5QexzU |
MALICIOUS
Loads dropped or rewritten executable
- (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe (PID: 2736)
Drops executable file immediately after starts
- (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe (PID: 2736)
SUSPICIOUS
Drops a file with too old compile date
- (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe (PID: 2736)
Executable content was dropped or overwritten
- (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe (PID: 2736)
INFO
Dropped object may contain Bitcoin addresses
- (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 769024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000BB40C | 0x000BB600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.95749 |
.reloc | 0x000C0000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.45577 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.34485 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.71645 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.30312 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 7.95586 | 16386 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.15484 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.32027 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.4148 | 6760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 5.59221 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
kernel32.dll |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
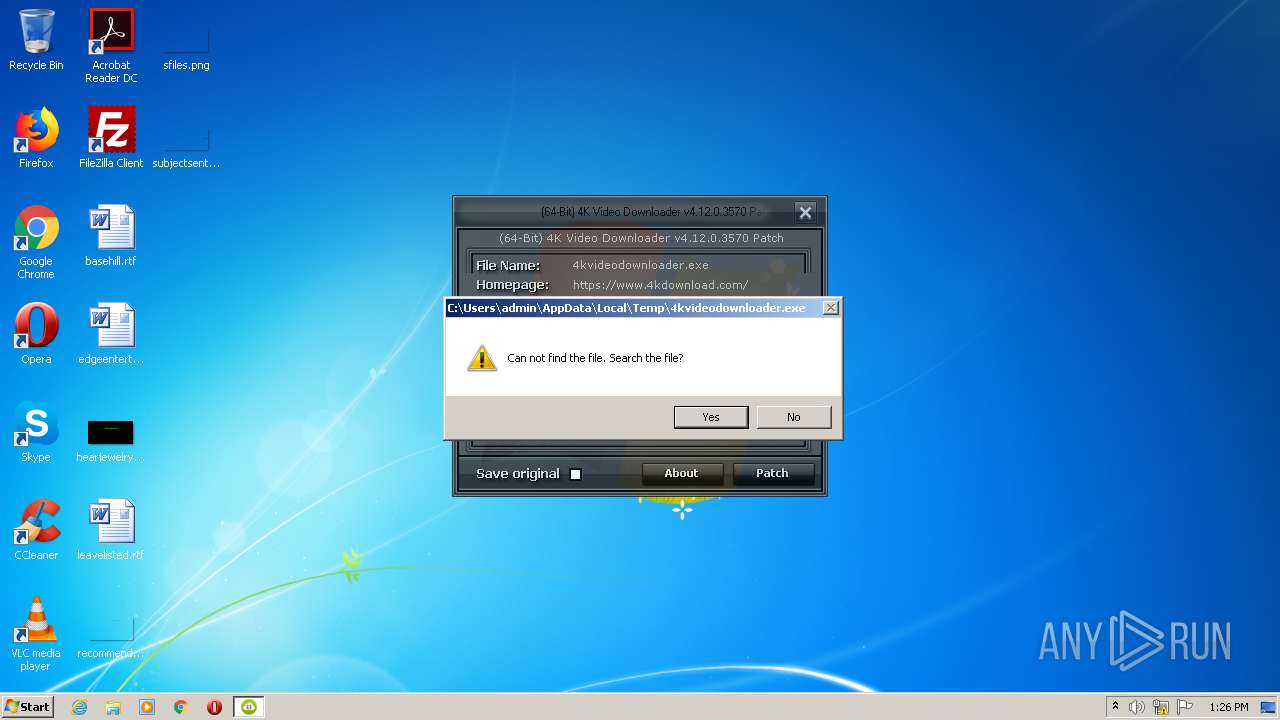
| 2540 | "C:\Users\admin\AppData\Local\Temp\(64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe" | C:\Users\admin\AppData\Local\Temp\(64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\(64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe" | C:\Users\admin\AppData\Local\Temp\(64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
549
Read events
535
Write events
14
Delete events
0
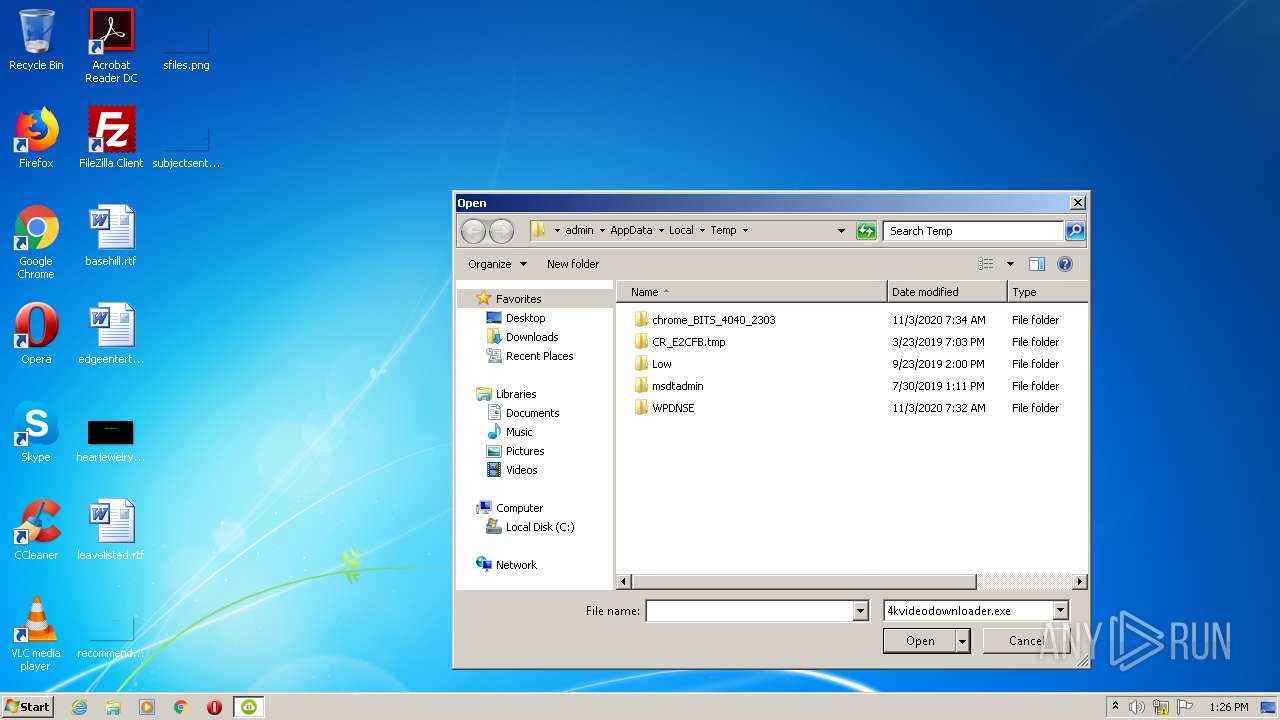
Modification events
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C002800360034002D004200690074002900200034004B00200056006900640065006F00200044006F0077006E006C006F0061006400650072002000760034002E00310032002E0030002E0033003500370030002000500061007400630068002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 070000000100000000000000020000000B0000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (2736) (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2736 | (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 2736 | (64-Bit) 4K Video Downloader v4.12.0.3570 Patch.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report