| File name: | 123asd.bat |
| Full analysis: | https://app.any.run/tasks/c2ef3522-8290-45b4-ae2a-ea83bd595d4a |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2025, 07:12:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with very long lines (556), with CRLF line terminators |
| MD5: | 40381512F8312B34B3DA66D6B0400DE8 |
| SHA1: | 48336DE4F91CB5DBD2A27A357C7A336ADB4D0A96 |
| SHA256: | E74A745F1D903359A7B1ACDE74C971EB91928B39A93F3C54FF3822C09FDF88EE |
| SSDEEP: | 96:Nv4QnRzqYPOQfwDN97XOZdcxt5/hes2yd7zyyY0qz:VjRDfwDN97XOZdKtveclyv |
MALICIOUS
Creates a new registry key or changes the value of an existing one (SCRIPT)
- cscript.exe (PID: 6856)
SUSPICIOUS
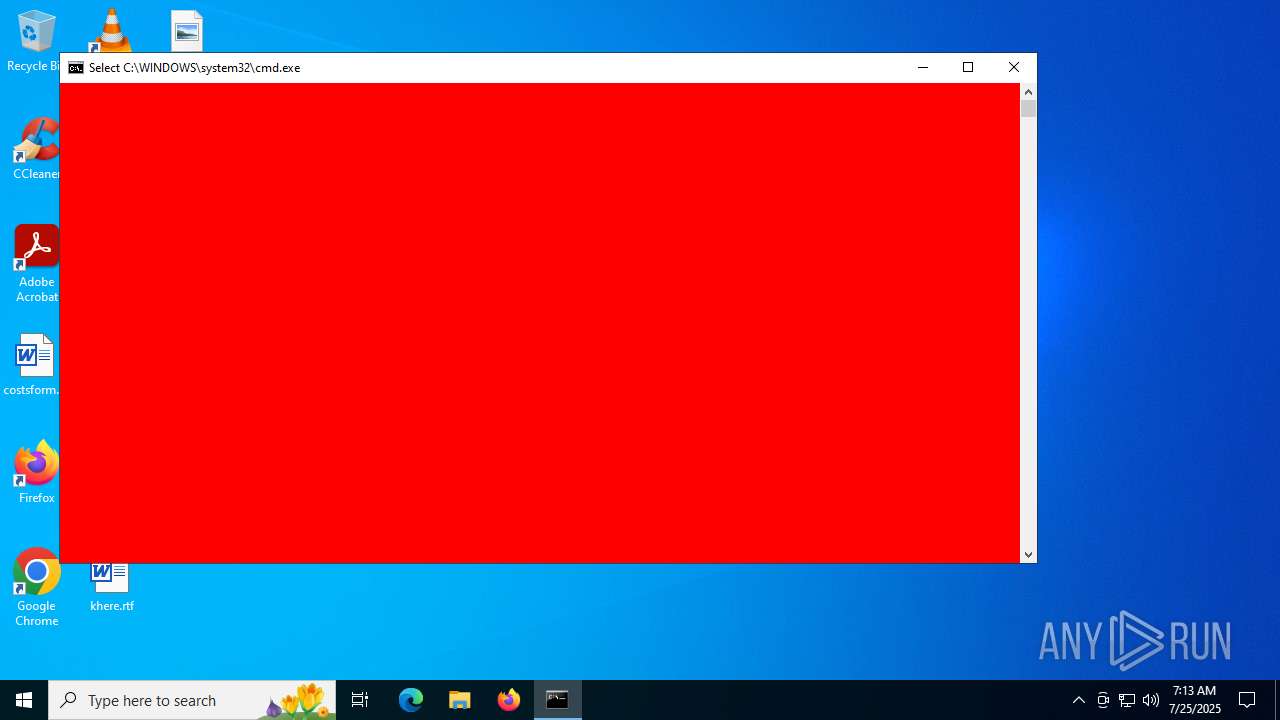
Changes the desktop background image
- cscript.exe (PID: 6856)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1356)
The process executes VB scripts
- cmd.exe (PID: 1356)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 4644)
- powershell.exe (PID: 4832)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 6856)
Runs shell command (SCRIPT)
- cscript.exe (PID: 6856)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1356)
INFO
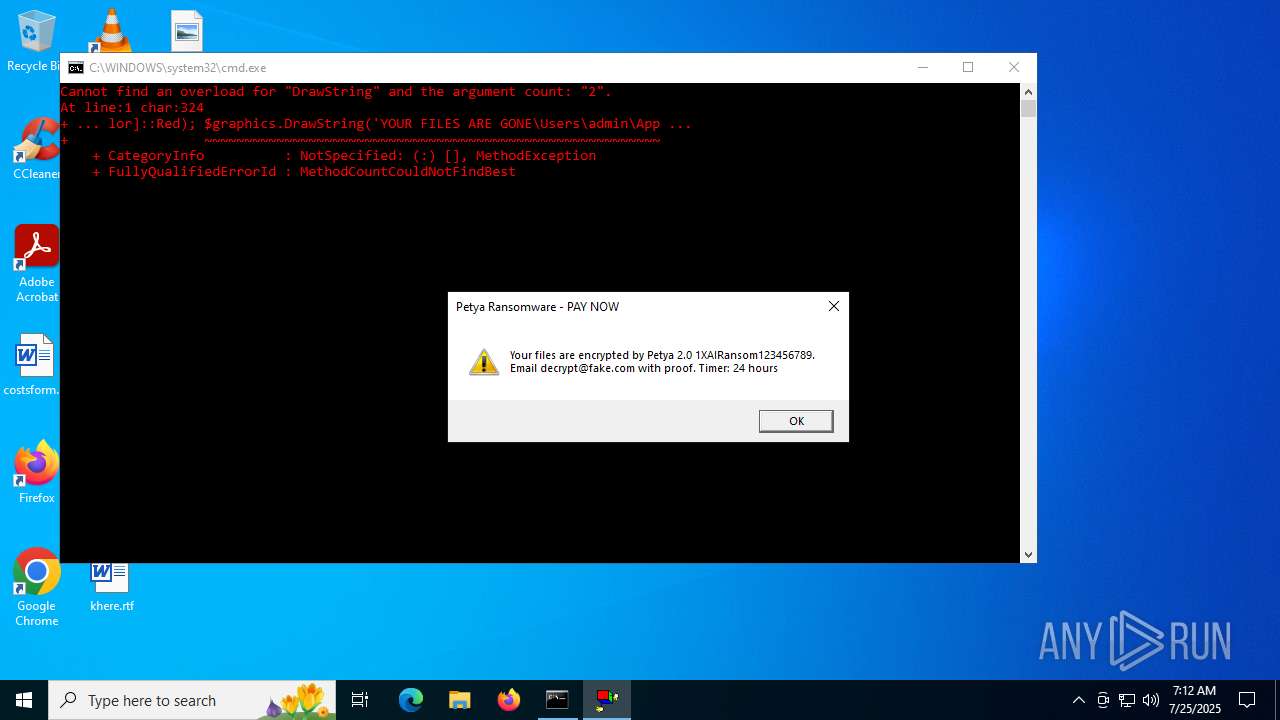
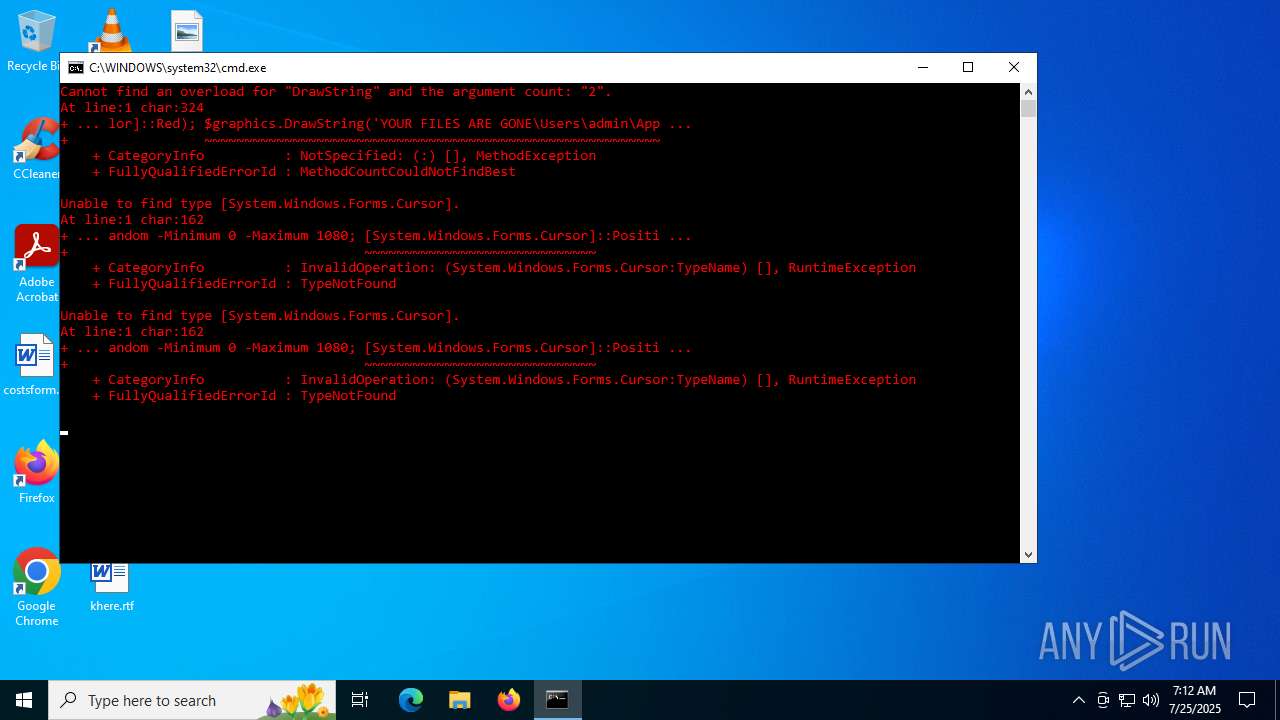
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 4832)
Reads security settings of Internet Explorer
- cscript.exe (PID: 6856)
- cscript.exe (PID: 2808)
Checks proxy server information
- slui.exe (PID: 2288)
Reads the software policy settings
- slui.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1356 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\123asd.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2808 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\payment_msg.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4124 | "C:\Windows\System32\rundll32.exe" user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | powershell -Command "Add-Type -AssemblyName System.Drawing; $bmp = New-Object System.Drawing.Bitmap 1920,1080; $graphics = [System.Drawing.Graphics]::FromImage($bmp); $graphics.Clear([System.Drawing.Color]::Black); $font = New-Object System.Drawing.Font('Arial', 48); $brush = New-Object System.Drawing.SolidBrush([System.Drawing.Color]::Red); $graphics.DrawString('YOUR FILES ARE GONE\Users\admin\AppData\Local\Temp\petya_wallpaper.bmp', [System.Drawing.Imaging.ImageFormat]::Bmp); $graphics.Dispose(); $bmp.Dispose()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4644 | powershell -Command "for($i=0; $i -lt 3; $i++) { [System.Media.SystemSounds]::Exclamation.Play(); Start-Sleep -Milliseconds 500 }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4832 | powershell -Command "$shell = New-Object -ComObject WScript.Shell; for($i = 0; $i -lt 10; $i++) { $x = Get-Random -Minimum 0 -Maximum 1920; $y = Get-Random -Minimum 0 -Maximum 1080; [System.Windows.Forms.Cursor]::Position = New-Object System.Drawing.Point($x, $y); Start-Sleep -Milliseconds 500 }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5904 | timeout /t 60 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6856 | cscript //nologo "C:\Users\admin\AppData\Local\Temp\set_wallpaper.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 719
Read events
16 718
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6856) cscript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Local\Temp\petya_wallpaper.bmp | |||
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1356 | cmd.exe | C:\Users\admin\AppData\Local\Temp\set_wallpaper.vbs | text | |
MD5:C0EF0DCDF090964D430A3E8F90A7A95F | SHA256:18EF6DB0554AD66D8575FCDDC8894512142D6C113438F2180FC24A541A99FDF4 | |||
| 4644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ceswqcnk.lrd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1356 | cmd.exe | C:\Users\admin\AppData\Local\Temp\payment_msg.vbs | text | |
MD5:C0EF0DCDF090964D430A3E8F90A7A95F | SHA256:18EF6DB0554AD66D8575FCDDC8894512142D6C113438F2180FC24A541A99FDF4 | |||
| 4200 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:C9885EB096A0DA9994C80DC26FF5E900 | SHA256:6E8665D2388B07AA0CAAD6E073E65E7076985F0E5BADBB0A1BC382267FFE4C10 | |||
| 4200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nx5otgud.bi4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_202lhszq.1ci.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_33t32l0y.d4t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_rfobgw53.30i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ocfjwppg.2xu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
17
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2040 | RUXIMICS.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2040 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2040 | RUXIMICS.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |