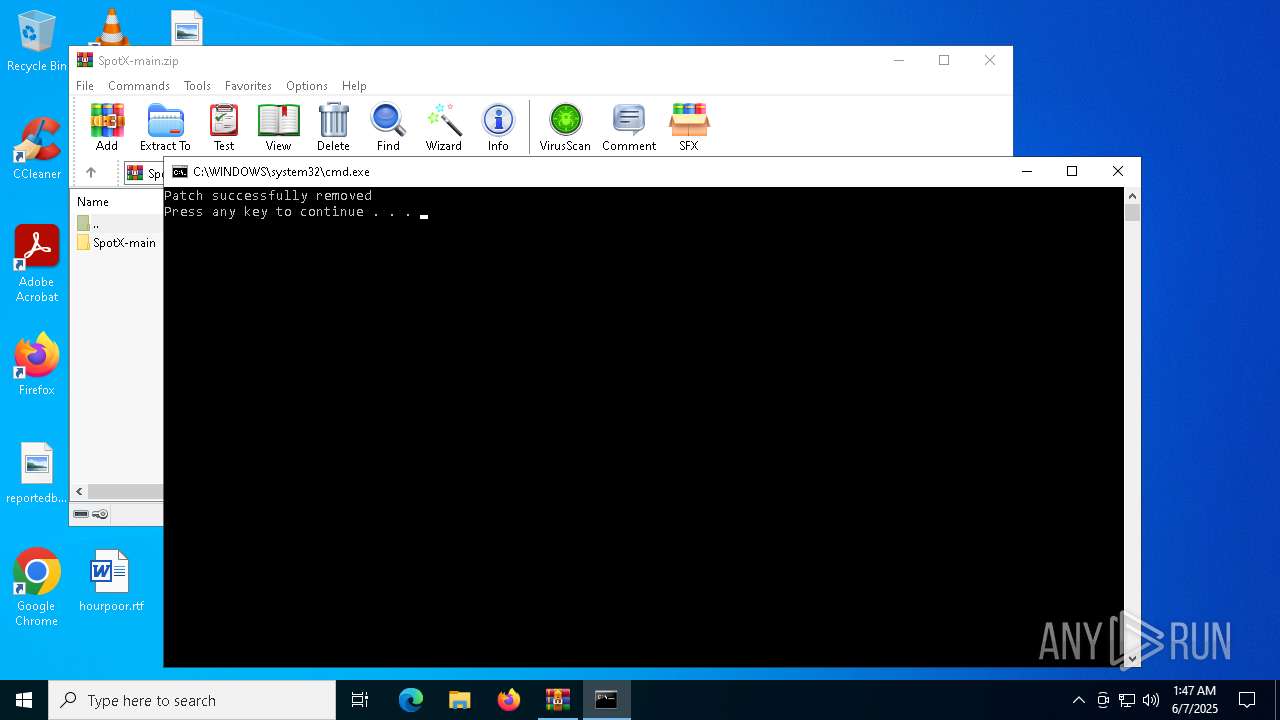
| File name: | SpotX-main.zip |
| Full analysis: | https://app.any.run/tasks/c1612184-78dd-4731-b767-280caa8b9609 |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2025, 01:46:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 0E480A085EFCD5AC23E036043D82A3B3 |
| SHA1: | A4D1344623B462184806DE87028CA604676E6492 |
| SHA256: | E741ADE701CFFF1B590EB63E9EF61DBB0EFE988D90DE63CF244D81C621D23E11 |
| SSDEEP: | 49152:PDqslyI5RmGzyzM49YiG03NyBoqTlRzFvg5JzROFZqxG515OdPF/amOvM45dCqzb:PDflyIZywcYix3NU/FvOJz8bAGYdPFSZ |
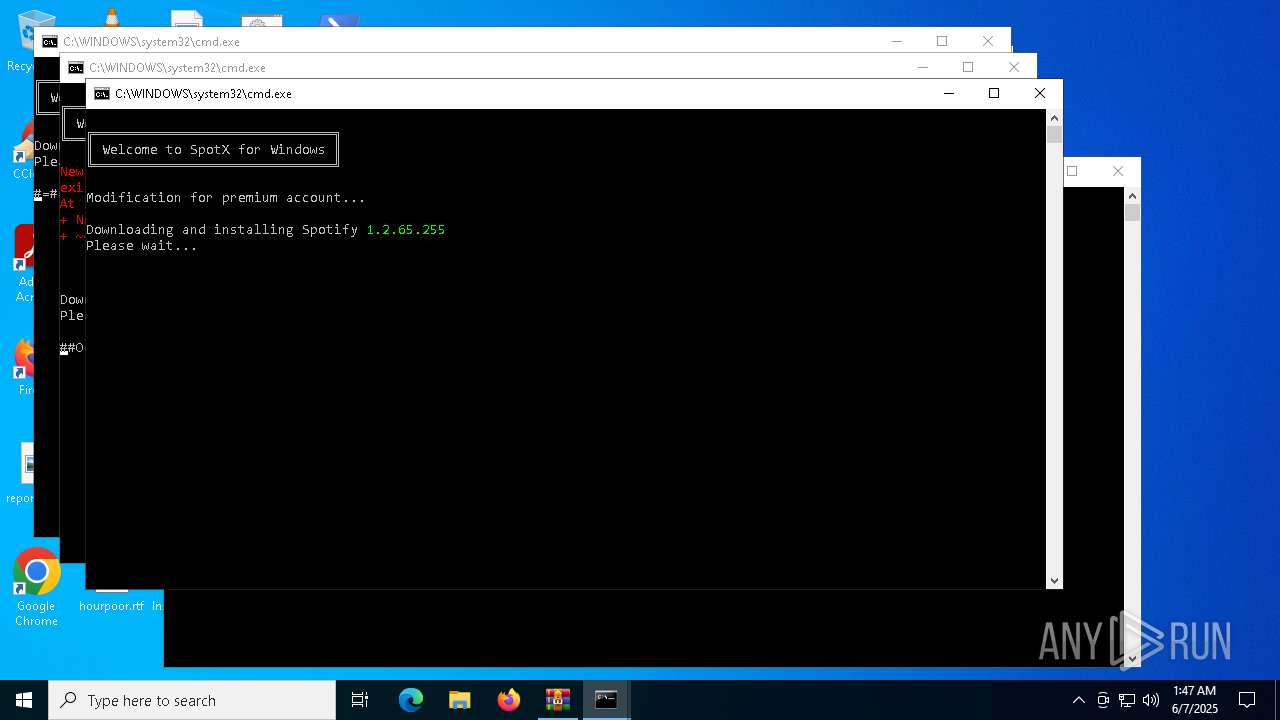
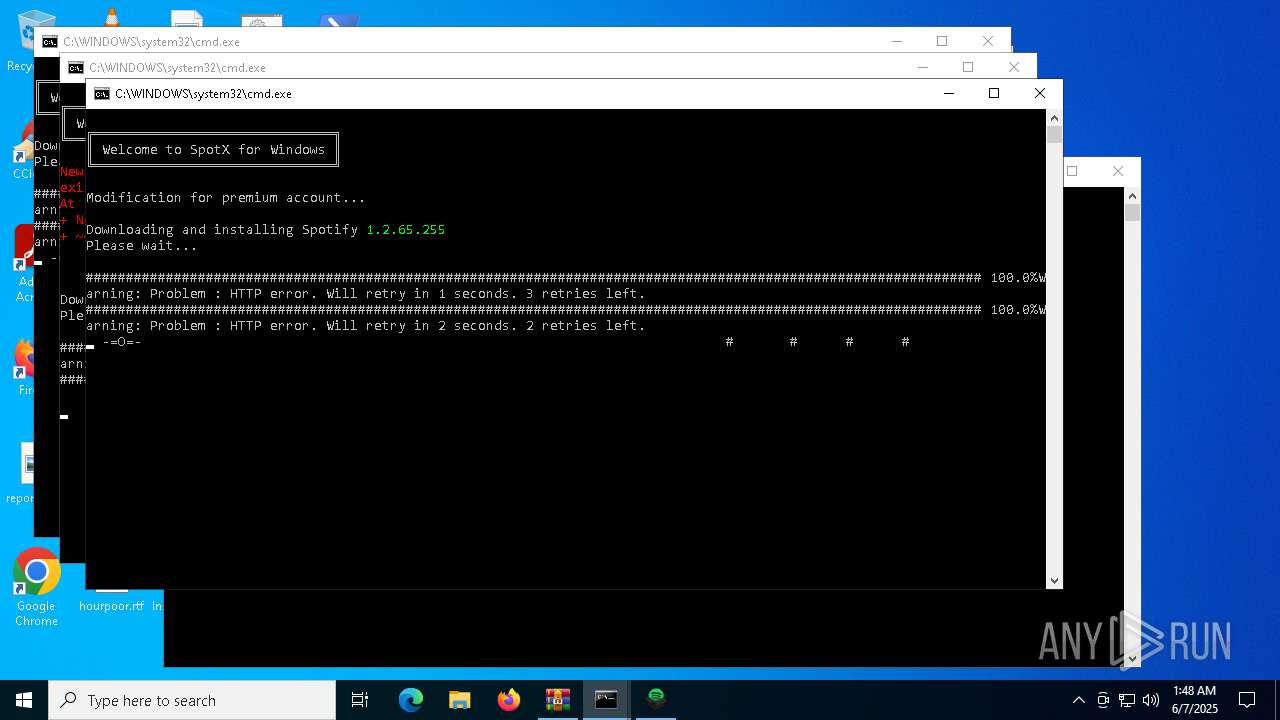
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2236)
Bypass execution policy to execute commands
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7012)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 208)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7756)
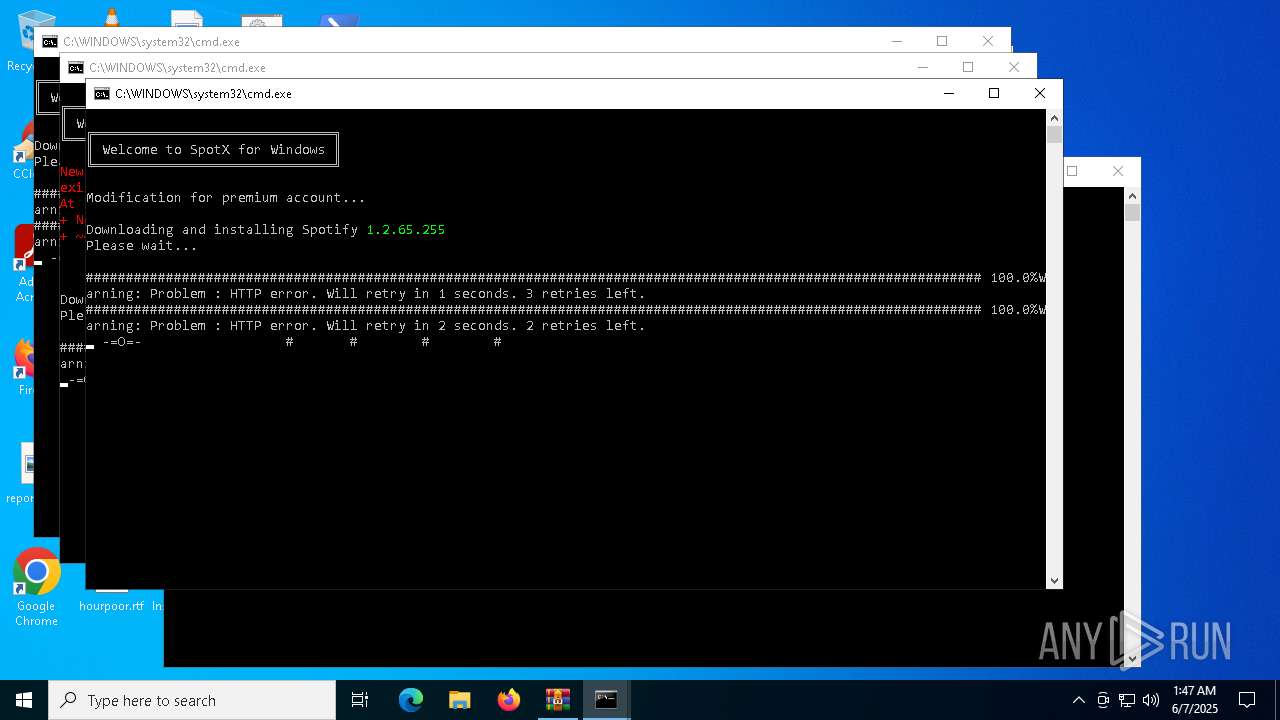
Downloads file from URI via Powershell
- powershell.exe (PID: 7368)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 6488)
The process executes Powershell scripts
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7756)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7756)
Found IP address in command line
- powershell.exe (PID: 4728)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 4728)
Creates a software uninstall entry
- SpotifySetup.exe (PID: 7732)
Explorer used for Indirect Command Execution
- explorer.exe (PID: 2136)
Process drops legitimate windows executable
- SpotifySetup.exe (PID: 7732)
Executable content was dropped or overwritten
- SpotifySetup.exe (PID: 7732)
INFO
Manual execution by a user
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 7756)
- powershell.exe (PID: 7012)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 208)
- iexplore.exe (PID: 6816)
- iexplore.exe (PID: 5600)
- rundll32.exe (PID: 4784)
- rundll32.exe (PID: 2268)
- iexplore.exe (PID: 5892)
- rundll32.exe (PID: 1120)
- iexplore.exe (PID: 8132)
- wscript.exe (PID: 8204)
- wscript.exe (PID: 8260)
- wscript.exe (PID: 8328)
- wscript.exe (PID: 8368)
- wscript.exe (PID: 8416)
- wscript.exe (PID: 8460)
- wscript.exe (PID: 8540)
- wscript.exe (PID: 8700)
- wscript.exe (PID: 8764)
- wscript.exe (PID: 8864)
- wscript.exe (PID: 8908)
- iexplore.exe (PID: 7604)
- wscript.exe (PID: 8500)
- wscript.exe (PID: 8956)
Checks proxy server information
- powershell.exe (PID: 7368)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 6488)
Disables trace logs
- powershell.exe (PID: 7368)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 6488)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 7012)
- powershell.exe (PID: 8136)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8084)
- powershell.exe (PID: 3176)
- powershell.exe (PID: 208)
Checks supported languages
- curl.exe (PID: 8164)
- curl.exe (PID: 32)
- curl.exe (PID: 236)
- curl.exe (PID: 7888)
- curl.exe (PID: 680)
- curl.exe (PID: 5512)
- curl.exe (PID: 4736)
- curl.exe (PID: 4748)
- curl.exe (PID: 4208)
- SpotifySetup.exe (PID: 7732)
- Spotify.exe (PID: 7704)
Reads the computer name
- curl.exe (PID: 4748)
- curl.exe (PID: 32)
- curl.exe (PID: 7888)
- curl.exe (PID: 680)
- curl.exe (PID: 4736)
- curl.exe (PID: 4208)
- SpotifySetup.exe (PID: 7732)
- Spotify.exe (PID: 7704)
Execution of CURL command
- powershell.exe (PID: 6488)
- powershell.exe (PID: 7368)
- powershell.exe (PID: 4728)
Create files in a temporary directory
- curl.exe (PID: 680)
- curl.exe (PID: 4208)
- curl.exe (PID: 7888)
Reads security settings of Internet Explorer
- explorer.exe (PID: 8156)
Creates files or folders in the user directory
- SpotifySetup.exe (PID: 7732)
The sample compiled with english language support
- SpotifySetup.exe (PID: 7732)
Application launched itself
- msedge.exe (PID: 7912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:31 12:53:08 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | SpotX-main/ |
Total processes
218
Monitored processes
93
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\WINDOWS\system32\curl.exe" -Is -w "%{http_code} \n" -o /dev/null -k https://download.scdn.co/upgrade/client/win32-x86/spotify_installer-1.2.13.661.ga588f749-4064.exe --retry 2 --ssl-no-revoke | C:\Windows\System32\curl.exe | powershell.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 23 Version: 8.4.0 Modules
| |||||||||||||||
| 208 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\el.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\WINDOWS\system32\curl.exe" -V | C:\Windows\System32\curl.exe | — | powershell.exe | |||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6728 --field-trial-handle=2396,i,17028002807572895790,16110368551640002031,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\system32\curl.exe" -q -k https://download.scdn.co/upgrade/client/win32-x86/spotify_installer-1.2.13.661.ga588f749-4064.exe -o C:\Users\admin\AppData\Local\Temp\SpotifySetup.exe --progress-bar --retry 3 --ssl-no-revoke | C:\Windows\System32\curl.exe | powershell.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5960 --field-trial-handle=2396,i,17028002807572895790,16110368551640002031,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1120 | "C:\WINDOWS\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\scrollbar-buttons.png | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3688 --field-trial-handle=2396,i,17028002807572895790,16110368551640002031,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
63 383
Read events
63 303
Write events
79
Delete events
1
Modification events
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SpotX-main.zip | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2236) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
23
Suspicious files
364
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jce01hut.340.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF12219a.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zuvrvfm1.wvr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6488 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_41e0hym5.xfi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\OK38QJQ4OFCRGWCTL4L6.temp | binary | |
MD5:BF53A4438CBF23D5C2F7C0C8D7831B4A | SHA256:7891103F259D193CC1D6B05E02FA267644A6270C945DE6F2A68E9EAE4566B25B | |||
| 7012 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_n01wfi14.gwq.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF122747.TMP | binary | |
MD5:BF53A4438CBF23D5C2F7C0C8D7831B4A | SHA256:7891103F259D193CC1D6B05E02FA267644A6270C945DE6F2A68E9EAE4566B25B | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FXZETHFWMW24MQ3QGZYI.temp | binary | |
MD5:9A40AD383093FD9FD73A4AD5219EDC40 | SHA256:B18694D15CA916F06448A9BE74D803852E71E8FE9C7A921288D9C10BDFBF4961 | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yjuaey5c.u2h.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yeyziz2p.5dx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
52
DNS requests
30
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1660 | RUXIMICS.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/spotx-official.github.io/main/run.ps1 | unknown | text | 1.25 Kb | whitelisted |
1660 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/SpotX/main/run.ps1 | unknown | text | 72.1 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/spotx-official.github.io/main/run.ps1 | unknown | text | 1.25 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/SpotX/main/run.ps1 | unknown | text | 72.1 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/SpotX/main/scripts/installer-lang/en.ps1 | unknown | text | 3.05 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/spotx-official.github.io/main/run.ps1 | unknown | text | 1.25 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/SpotX/main/scripts/installer-lang/en.ps1 | unknown | text | 3.05 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/SpotX-Official/SpotX/main/run.ps1 | unknown | text | 72.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1660 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1660 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1660 | RUXIMICS.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7368 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
4728 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
6488 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
4748 | curl.exe | 199.232.214.248:443 | download.scdn.co | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
download.scdn.co |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Potentially Bad Traffic | ET HUNTING Generic Powershell DownloadFile Command |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Get-CimInstance Cmdlet has been detected |
— | — | A Network Trojan was detected | LOADER [ANY.RUN] Gen.Powershell.Downloader Script Payload |