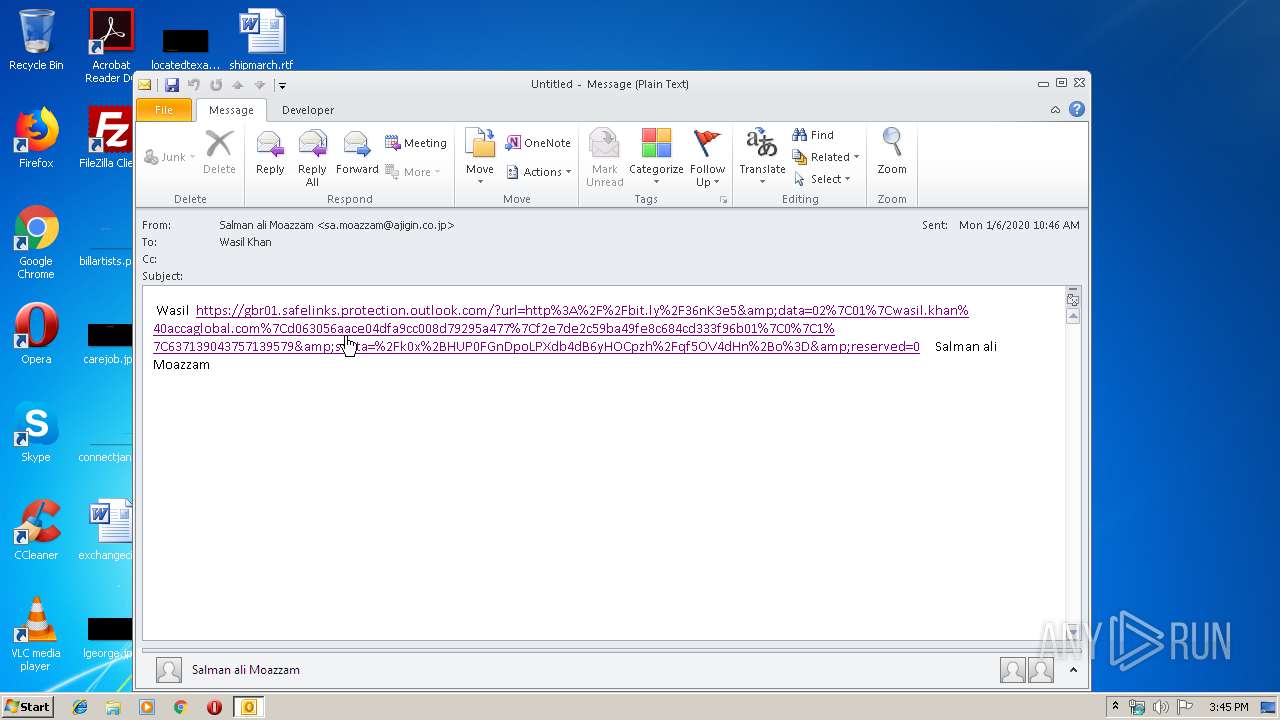
| File name: | Untitled.msg |
| Full analysis: | https://app.any.run/tasks/a8c3896d-4a2a-41db-b910-01bc728fc17c |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 15:45:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | E8D15A57DD84A7C5183206F7FDEFEE83 |
| SHA1: | 944CD92D298734BAE1F1E57F2A3384F2F9F2036D |
| SHA256: | E721EAF14107FE3079868CE4EAA75077881792D4B46465B482EA11218CADB2D8 |
| SSDEEP: | 768:tCQ7KxEmqMiVTfkWsKCAoBWsKPOAmWDNhUs1/L5hEa6oC7MWsKGlZ5MAWAV9Mg4:5hZTfkWGW3krMWOr1l |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2416)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2416)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2416)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2416)
INFO
Changes internet zones settings
- iexplore.exe (PID: 272)
Creates files in the user directory
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 272)
Reads internet explorer settings
- iexplore.exe (PID: 1292)
Reads Internet Cache Settings
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 272)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
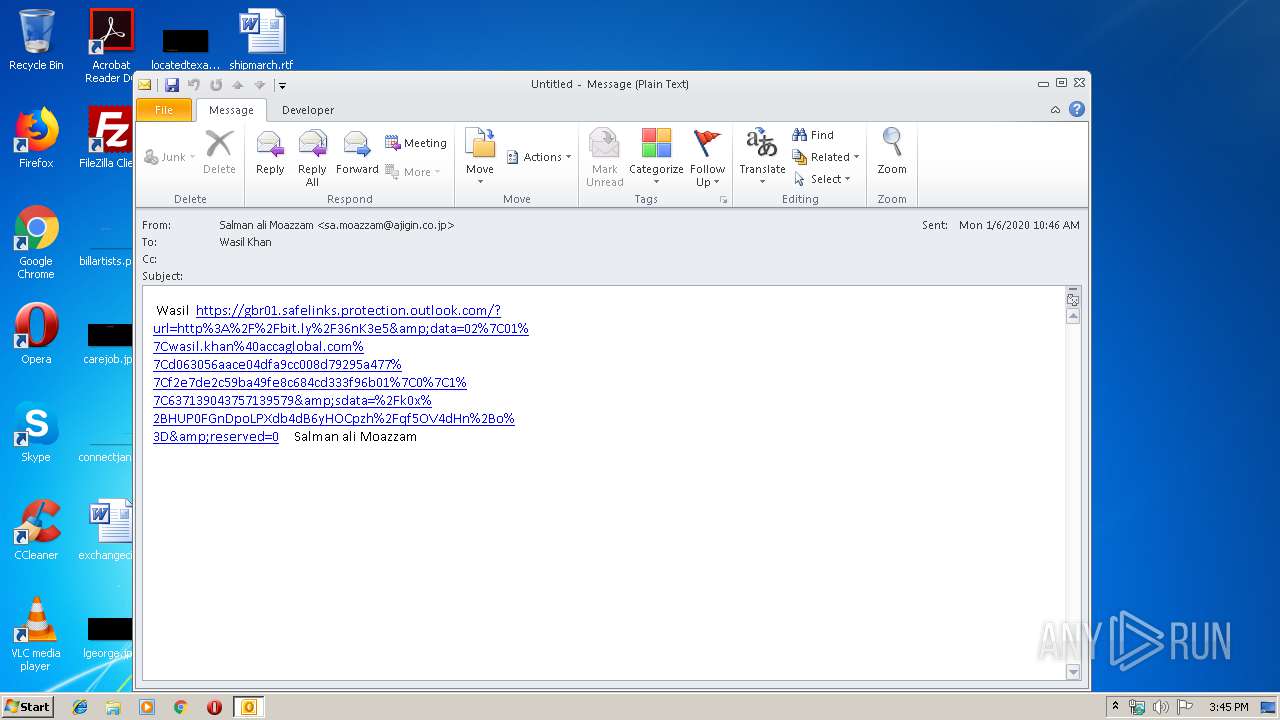
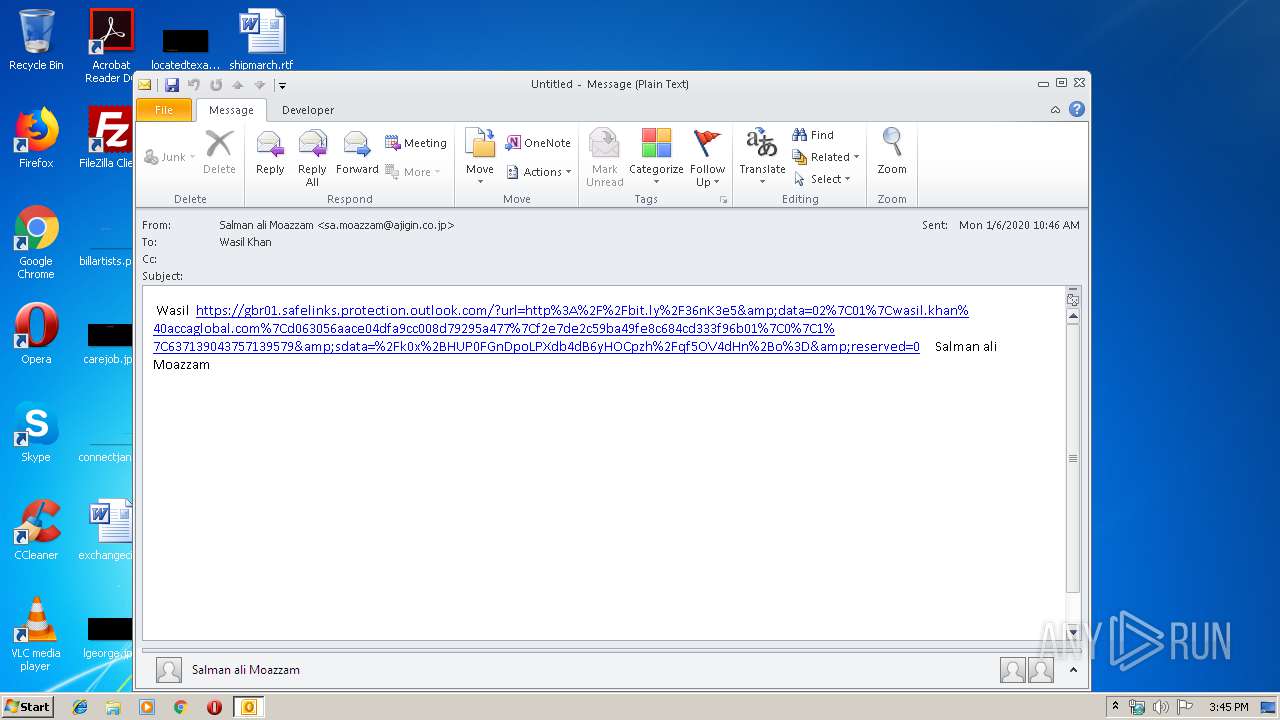
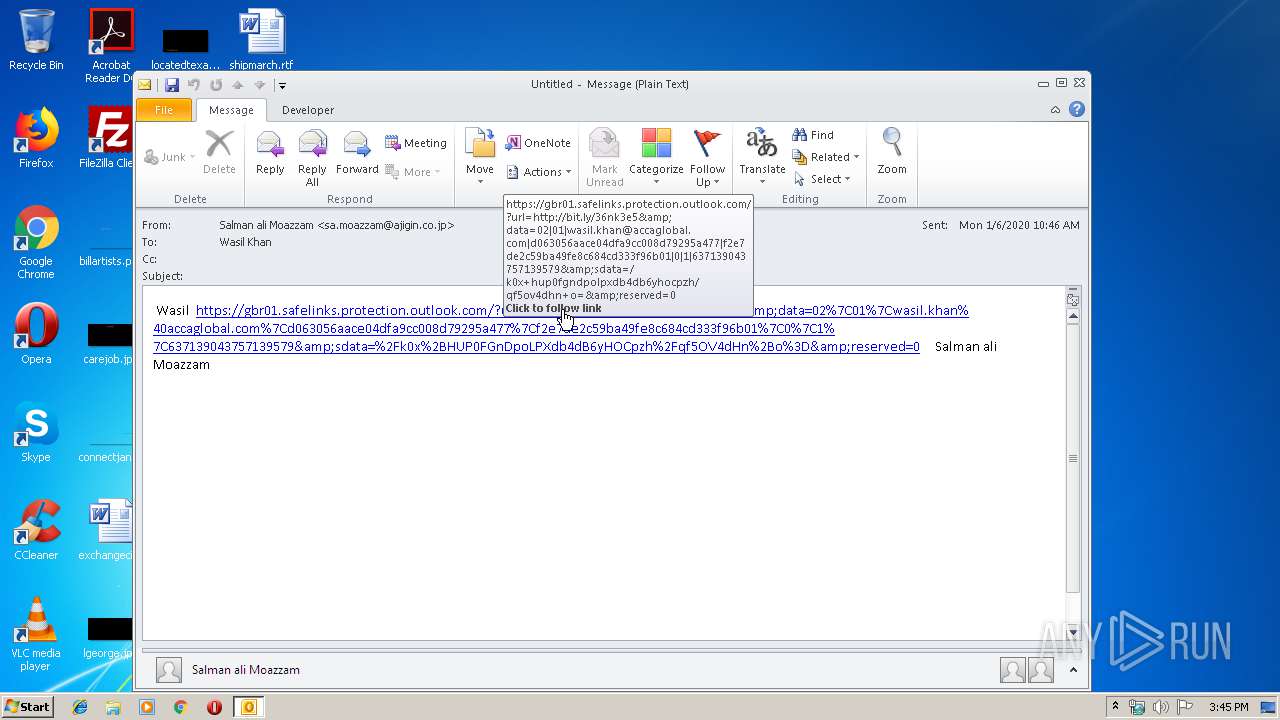
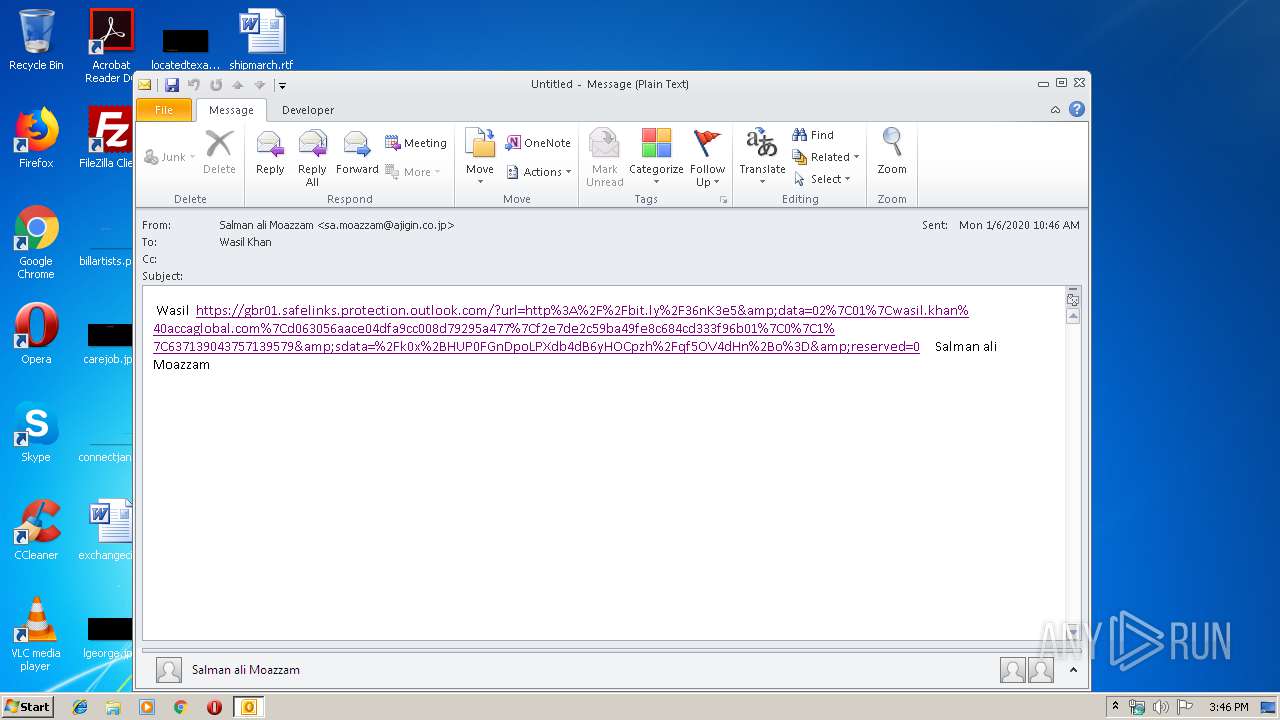
| 272 | "C:\Program Files\Internet Explorer\iexplore.exe" https://gbr01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fbit.ly%2F36nK3e5&data=02%7C01%7Cwasil.khan%40accaglobal.com%7Cd063056aace04dfa9cc008d79295a477%7Cf2e7de2c59ba49fe8c684cd333f96b01%7C0%7C1%7C637139043757139579&sdata=%2Fk0x%2BHUP0FGnDpoLPXdb4dB6yHOCpzh%2Fqf5OV4dHn%2Bo%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:272 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Untitled.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 951
Read events
1 324
Write events
605
Delete events
22
Modification events
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1345388724 | |||
| (PID) Process: | (2416) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
6
Text files
36
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA737.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 272 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2416 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\P4IWW6BE\ncvn[1].txt | — | |
MD5:— | SHA256:— | |||
| 2416 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabDDE7.tmp | — | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarDDE8.tmp | — | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabDDF9.tmp | — | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarDDFA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
14
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
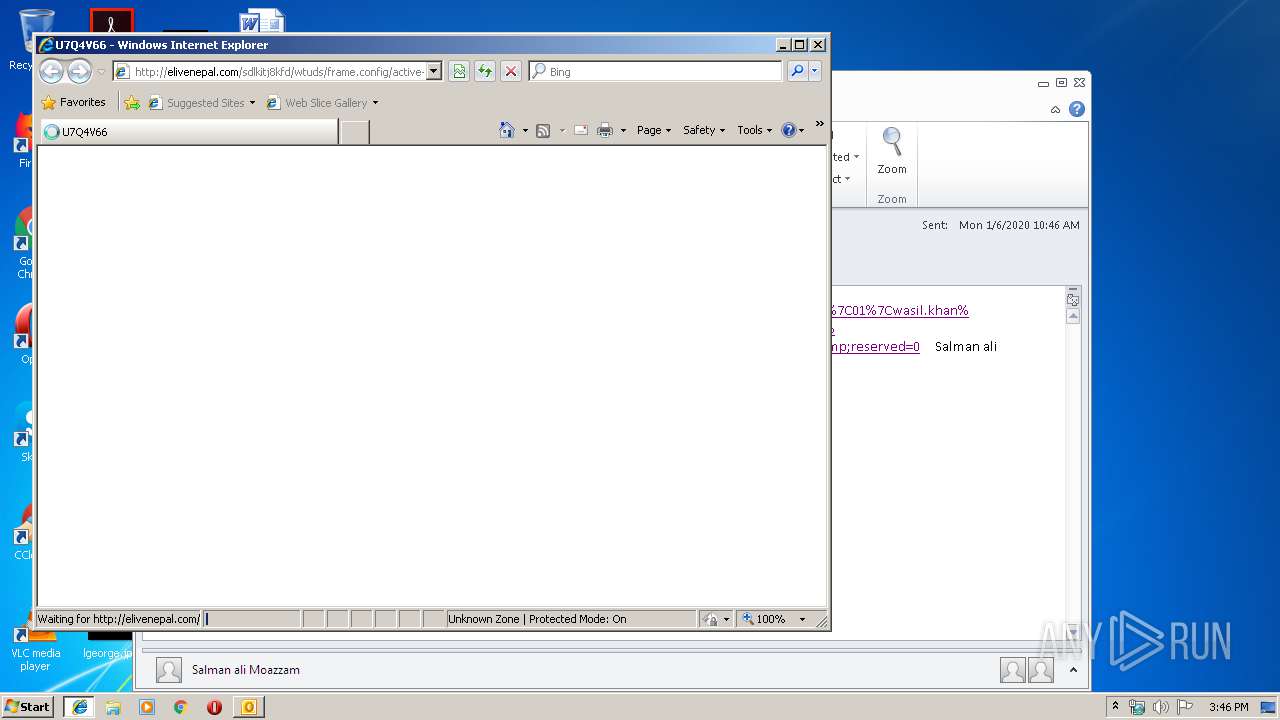
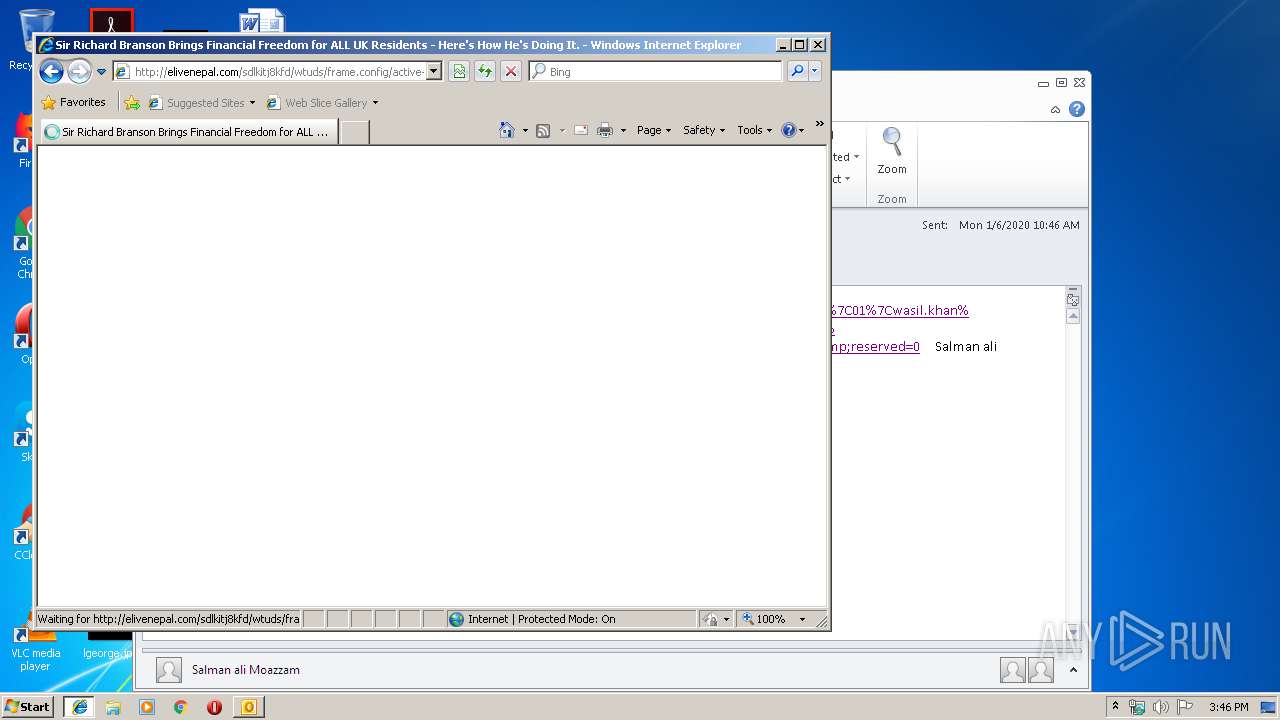
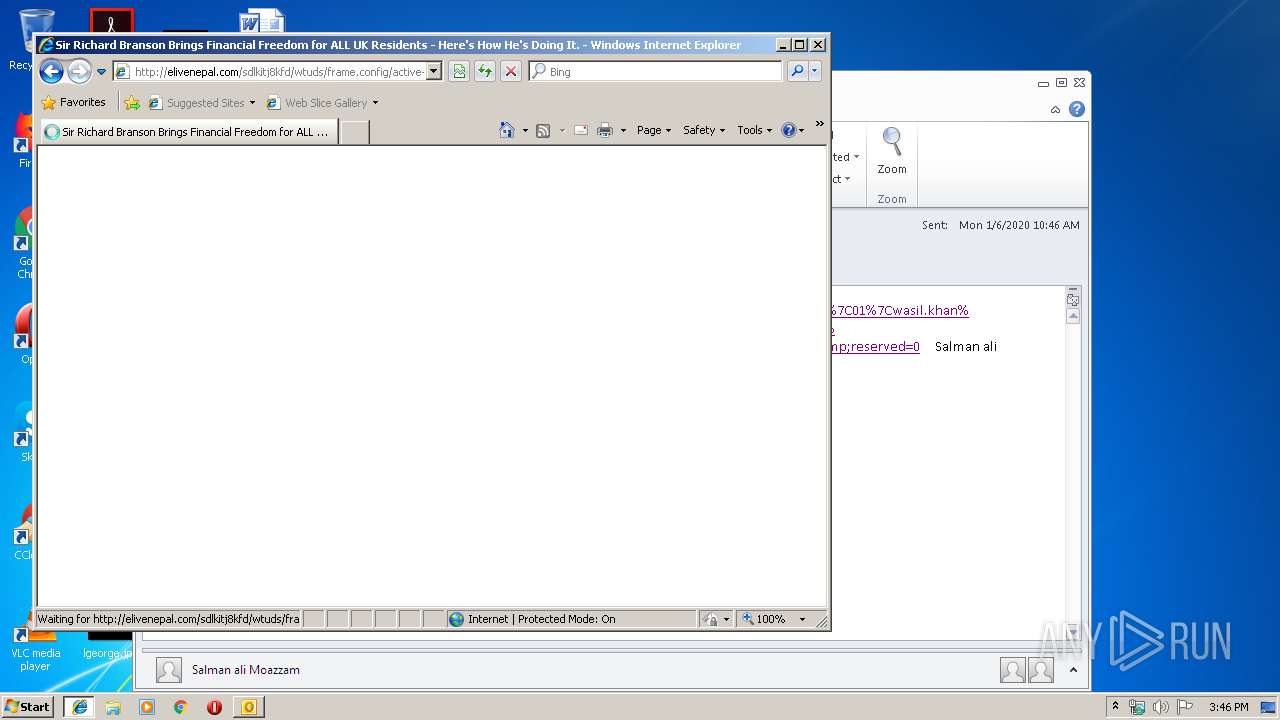
272 | iexplore.exe | GET | — | 160.153.91.165:80 | http://elivenepal.com/favicon.ico | US | — | — | malicious |
1292 | iexplore.exe | GET | 200 | 160.153.91.165:80 | http://elivenepal.com/sdlkitj8kfd/wtuds/frame.config/active-topics/coupons/frfr-myoffice/payment_gateway.php/udvm/ncvn/?practice=h105n5pctu5rkv | US | html | 1.38 Kb | malicious |
272 | iexplore.exe | GET | 500 | 160.153.91.165:80 | http://elivenepal.com/favicon.ico | US | html | 675 b | malicious |
1292 | iexplore.exe | GET | 200 | 160.153.91.165:80 | http://elivenepal.com/sdlkitj8kfd/wtuds/frame.config/active-topics/coupons/frfr-myoffice/payment_gateway.php/cev/tsh/?9m9mk9y9fx0 | US | html | 484 Kb | malicious |
1292 | iexplore.exe | GET | 200 | 172.217.16.170:80 | http://fonts.googleapis.com/css?family=Open+Sans+Condensed:700|Open+Sans:400,600,700&subset=latin-ext | US | text | 236 b | whitelisted |
1292 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://fonts.gstatic.com/s/opensanscondensed/v14/z7NFdQDnbTkabZAIOl9il_O6KJj73e7Ff0GmDuvMQw.eot | US | eot | 24.9 Kb | whitelisted |
1292 | iexplore.exe | GET | 200 | 8.241.123.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
1292 | iexplore.exe | GET | 200 | 8.241.123.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E.crt | US | der | 993 b | whitelisted |
1292 | iexplore.exe | GET | 200 | 104.17.64.4:80 | http://cdnjs.cloudflare.com/ajax/libs/jquery/3.4.1/jquery.min.js | US | text | 30.1 Kb | whitelisted |
2416 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2416 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
272 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1292 | iexplore.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
1292 | iexplore.exe | 160.153.91.165:80 | elivenepal.com | GoDaddy.com, LLC | US | unknown |
1292 | iexplore.exe | 95.100.130.232:443 | img1.wsimg.com | Akamai Technologies, Inc. | — | unknown |
1292 | iexplore.exe | 8.241.123.126:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
272 | iexplore.exe | 160.153.91.165:80 | elivenepal.com | GoDaddy.com, LLC | US | unknown |
1292 | iexplore.exe | 104.17.65.4:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1292 | iexplore.exe | 172.217.16.170:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1292 | iexplore.exe | 104.17.64.4:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
gbr01.safelinks.protection.outlook.com |
| whitelisted |
www.bing.com |
| whitelisted |
bit.ly |
| shared |
elivenepal.com |
| malicious |
img1.wsimg.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |