| File name: | HRSword.exe |
| Full analysis: | https://app.any.run/tasks/864406b6-7272-40b5-bfd9-f9aa917382ca |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2021, 16:01:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0F73B467FF03F9224C024F4EB3AECEDB |
| SHA1: | 75EBD5BAB5E2707D4533579A34D983B65AF5EC7F |
| SHA256: | E705F69AFD97F343F3C1F2BC6027D30935A0BFD29FF025C563F6F8C1F9A7478E |
| SSDEEP: | 49152:NjPlJMkPEno1ZBv9UERkKo7xGH4mDmpM296:NDlJPEo19zRRVnDmpMC6 |
MALICIOUS
Drops executable file immediately after starts
- HRSword.exe (PID: 348)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
Loads dropped or rewritten executable
- HRSword.exe (PID: 3740)
Application was dropped or rewritten from another process
- HRSword.exe (PID: 3740)
- usysdiag.exe (PID: 2636)
Loads the Task Scheduler COM API
- HRSword.exe (PID: 3740)
Changes settings of System certificates
- usysdiag.exe (PID: 2636)
SUSPICIOUS
Checks supported languages
- HRSword.exe (PID: 348)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 3436)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 3600)
- usysdiag.exe (PID: 2636)
- cmd.exe (PID: 296)
- HRSword.exe (PID: 3740)
Drops a file that was compiled in debug mode
- HRSword.exe (PID: 348)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
Executable content was dropped or overwritten
- cmd.exe (PID: 3268)
- HRSword.exe (PID: 348)
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
Creates files in the Windows directory
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
Reads the computer name
- HRSword.exe (PID: 348)
- HRSword.exe (PID: 3740)
- usysdiag.exe (PID: 2636)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 296)
- HRSword.exe (PID: 348)
Application launched itself
- cmd.exe (PID: 296)
Creates files in the driver directory
- cmd.exe (PID: 3456)
- cmd.exe (PID: 3520)
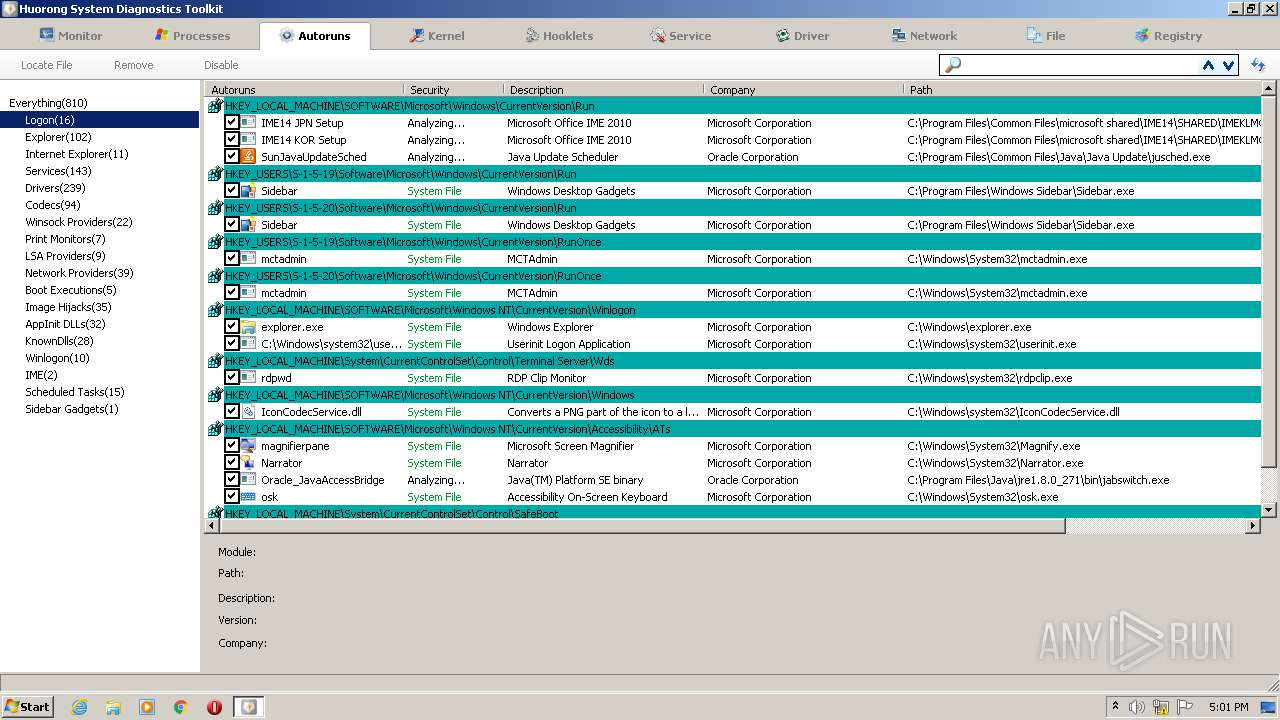
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 296)
Starts SC.EXE for service management
- cmd.exe (PID: 296)
Creates or modifies windows services
- reg.exe (PID: 3972)
- reg.exe (PID: 3580)
- reg.exe (PID: 660)
- reg.exe (PID: 2436)
- reg.exe (PID: 2164)
Adds / modifies Windows certificates
- usysdiag.exe (PID: 2636)
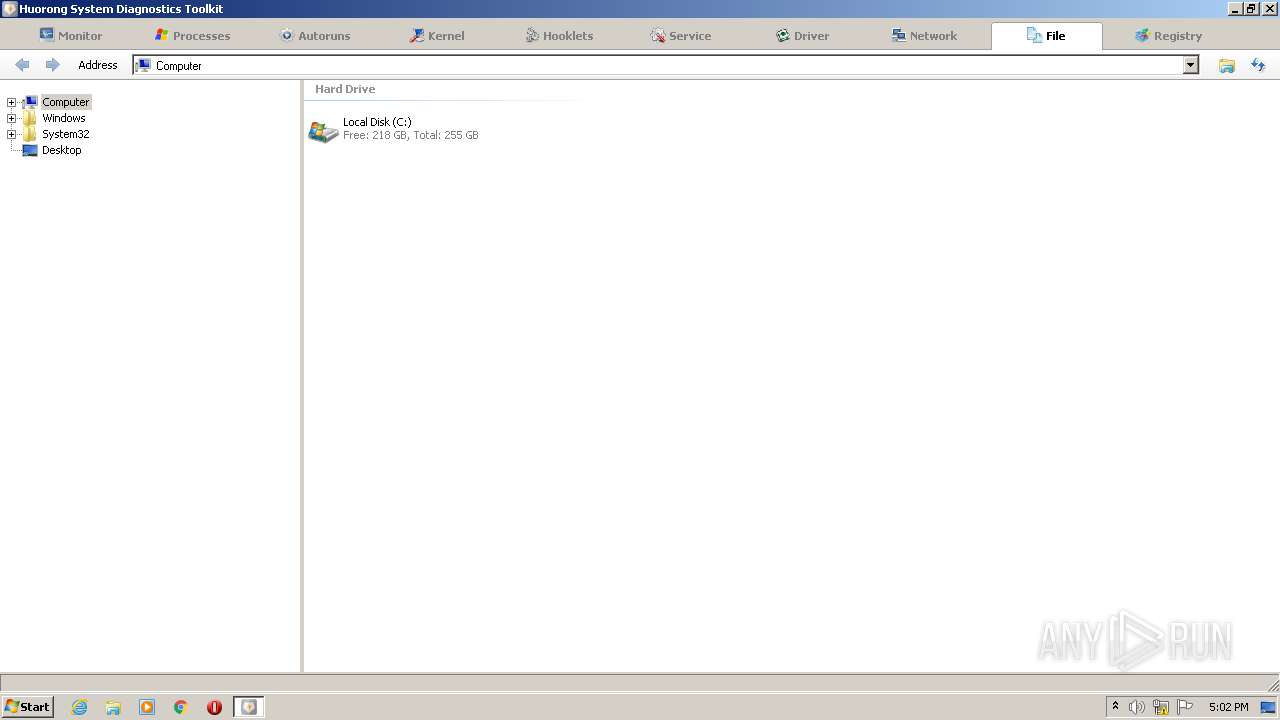
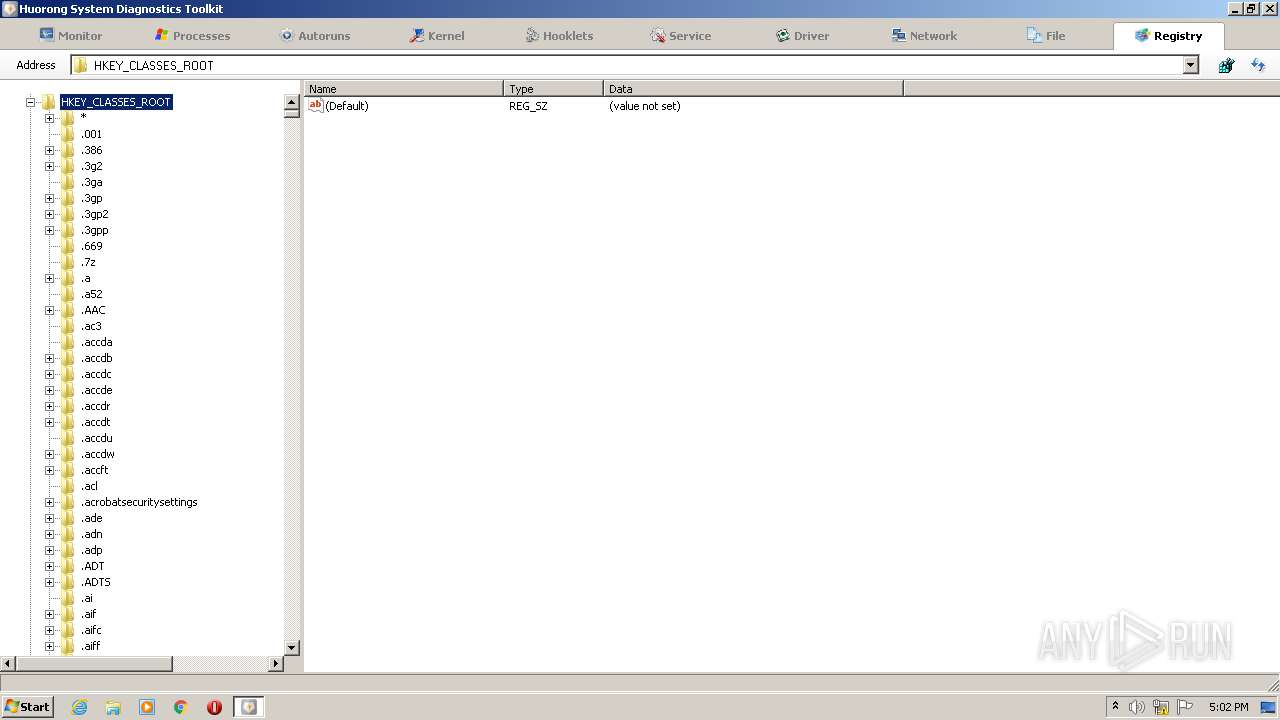
Reads default file associations for system extensions
- HRSword.exe (PID: 3740)
INFO
Checks supported languages
- sc.exe (PID: 3716)
- sc.exe (PID: 3828)
- reg.exe (PID: 3972)
- reg.exe (PID: 2436)
- reg.exe (PID: 660)
- reg.exe (PID: 2308)
- reg.exe (PID: 336)
- reg.exe (PID: 1212)
- reg.exe (PID: 2164)
- sc.exe (PID: 2924)
- sc.exe (PID: 2644)
- reg.exe (PID: 3580)
Reads the computer name
- sc.exe (PID: 3716)
- sc.exe (PID: 3828)
- sc.exe (PID: 2644)
- sc.exe (PID: 2924)
Reads settings of System Certificates
- usysdiag.exe (PID: 2636)
Checks Windows Trust Settings
- usysdiag.exe (PID: 2636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| ProductVersion: | 5.0.0.1 |
|---|---|
| ProductName: | Huorong Internet Security |
| OriginalFileName: | HRSword.exe |
| LegalCopyright: | Beijing Huorong Network Technology Co., Ltd. |
| InternalName: | HRSword |
| FileVersion: | 5.0.1.1 |
| FileDescription: | Huorong Sword GUI Frontend |
| CompanyName: | Beijing Huorong Network Technology Co., Ltd. |
| CharacterSet: | Unicode |
| LanguageCode: | Unknown (0009) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.0.0.1 |
| FileVersionNumber: | 5.0.1.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x28920 |
| UninitializedDataSize: | 98304 |
| InitializedDataSize: | 16384 |
| CodeSize: | 65536 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2012:12:31 01:38:51+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:51 |
| Detected languages: |
|
| CompanyName: | Beijing Huorong Network Technology Co., Ltd. |
| FileDescription: | Huorong Sword GUI Frontend |
| FileVersion: | 5.0.1.1 |
| InternalName: | HRSword |
| LegalCopyright: | Beijing Huorong Network Technology Co., Ltd. |
| OriginalFilename: | HRSword.exe |
| ProductName: | Huorong Internet Security |
| ProductVersion: | 5.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 31-Dec-2012 00:38:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00018000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00019000 | 0x00010000 | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91125 |
.rsrc | 0x00029000 | 0x00004000 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.33064 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.41855 | 1528 | UNKNOWN | Chinese - PRC | RT_MANIFEST |
50 | 6.04792 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
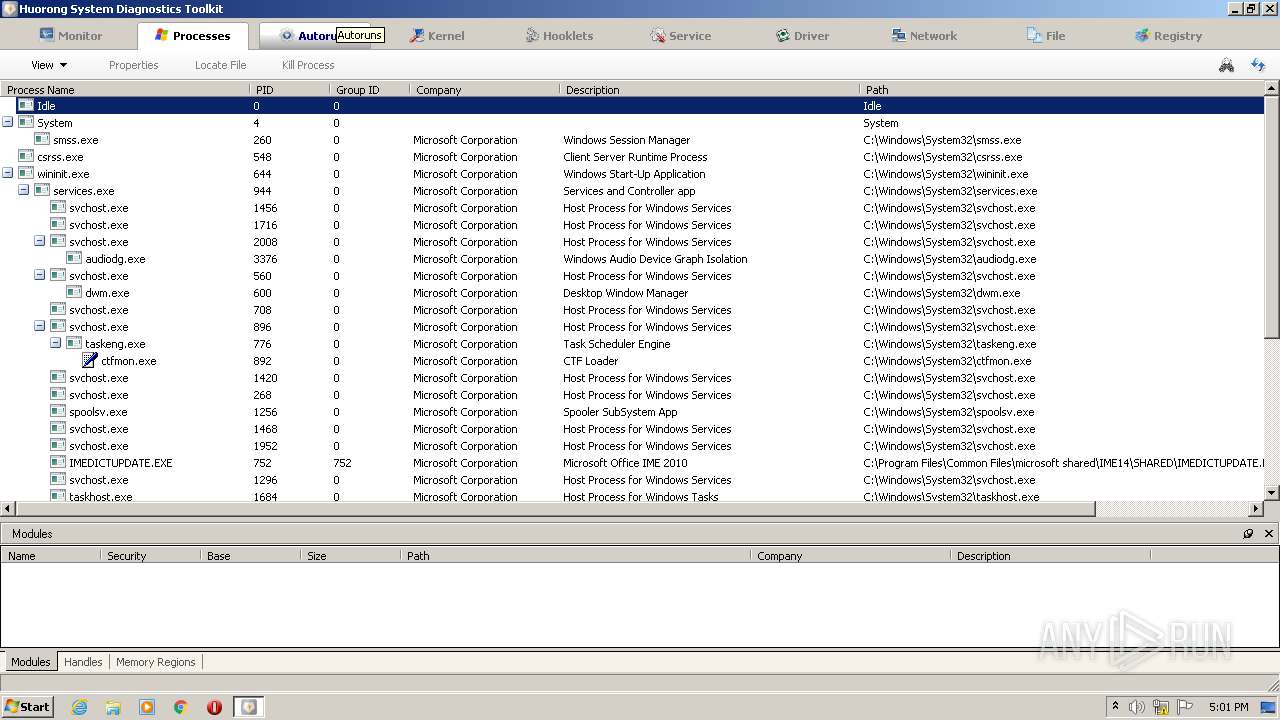
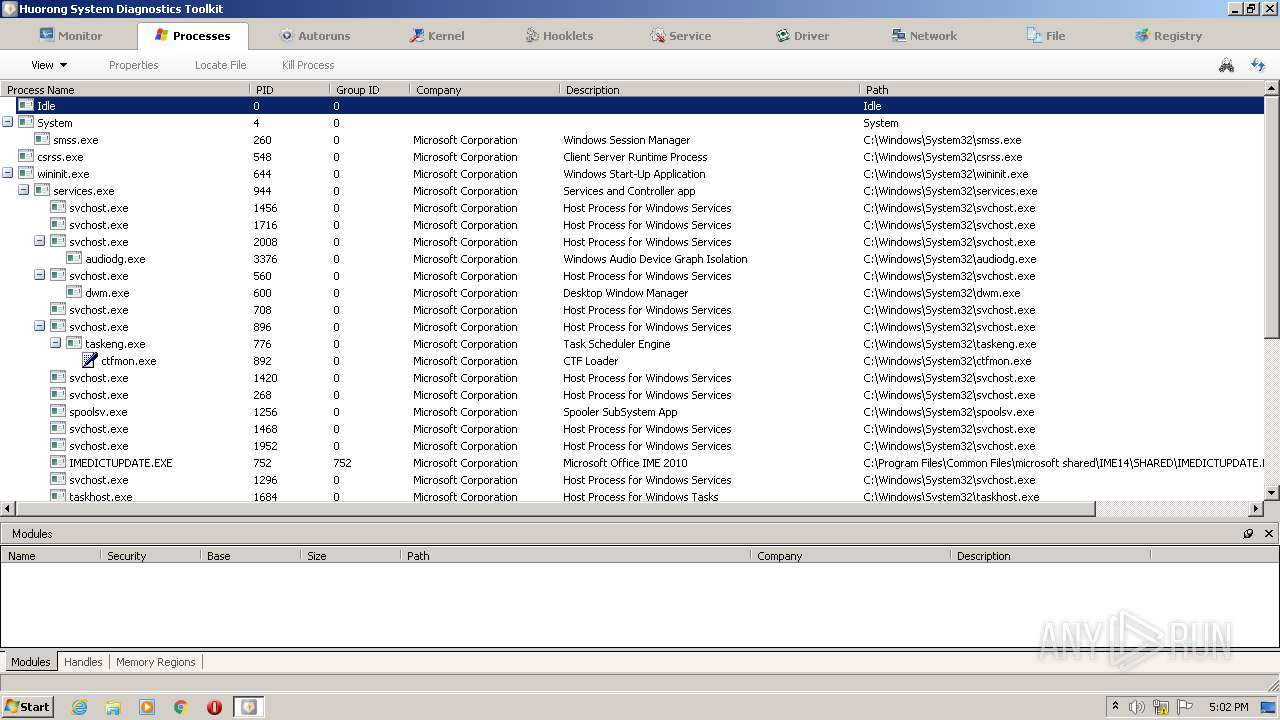
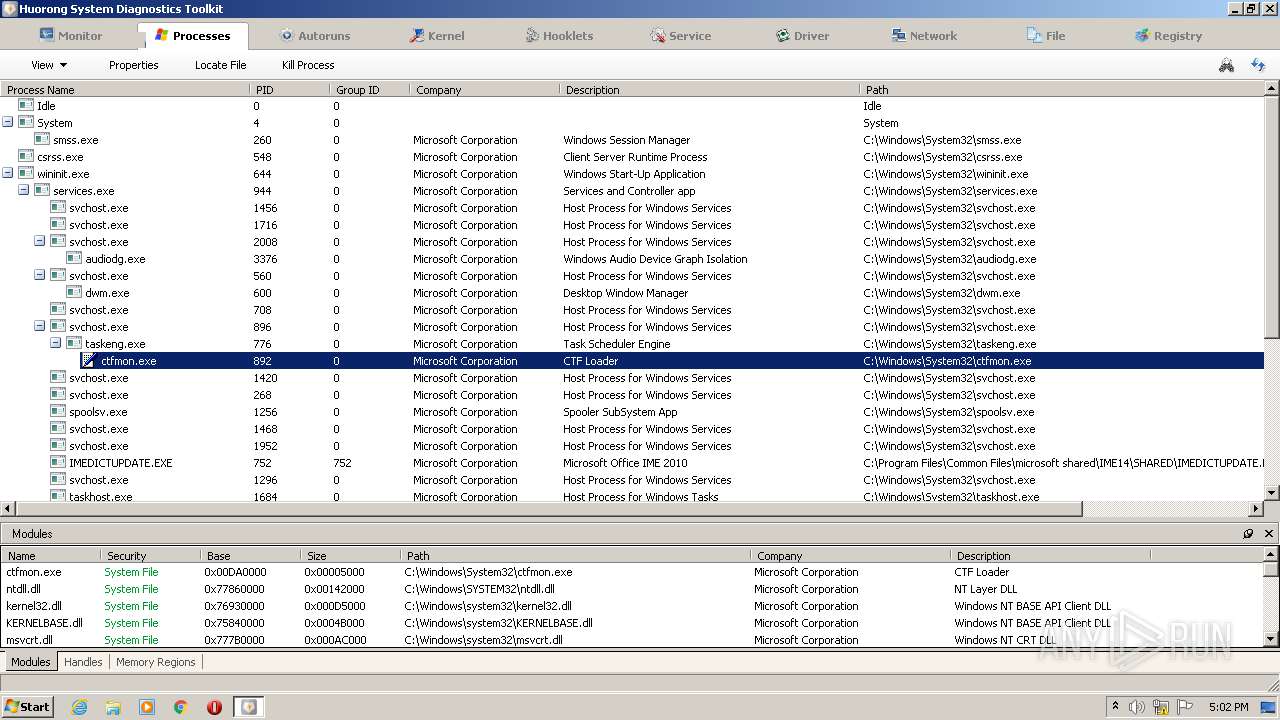
Total processes
59
Monitored processes
23
Malicious processes
6
Suspicious processes
1
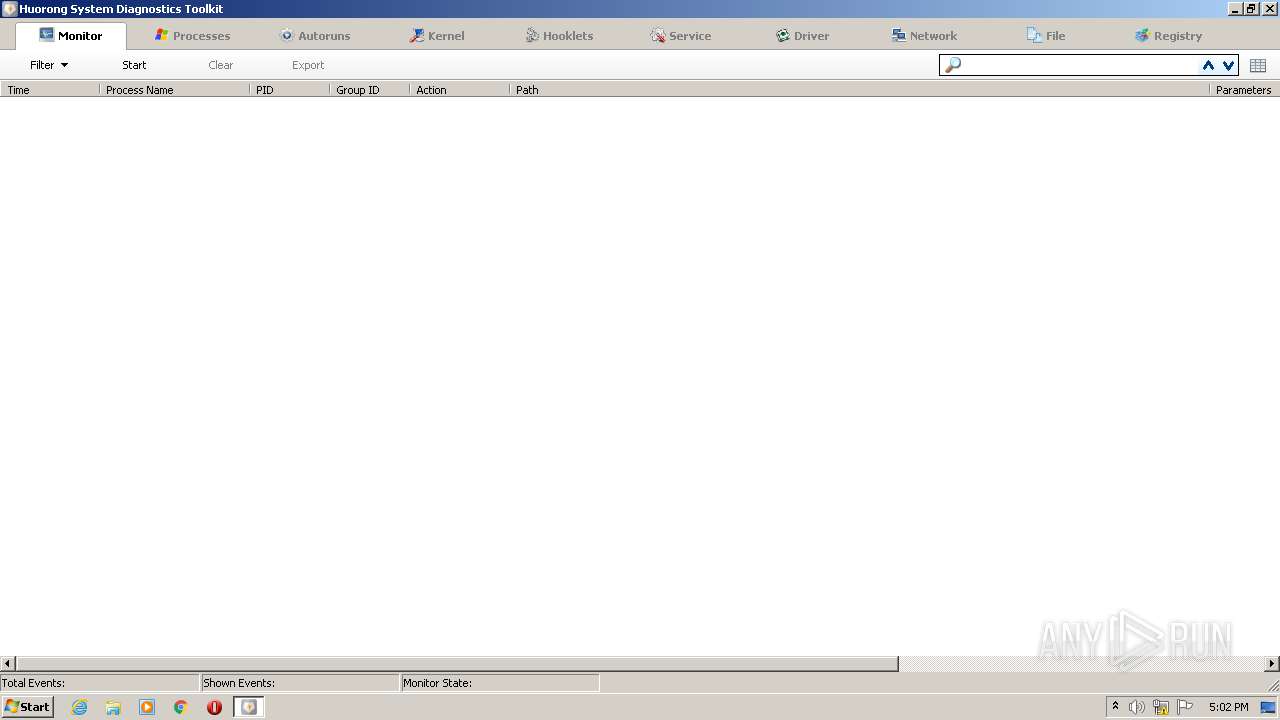
Behavior graph
Click at the process to see the details
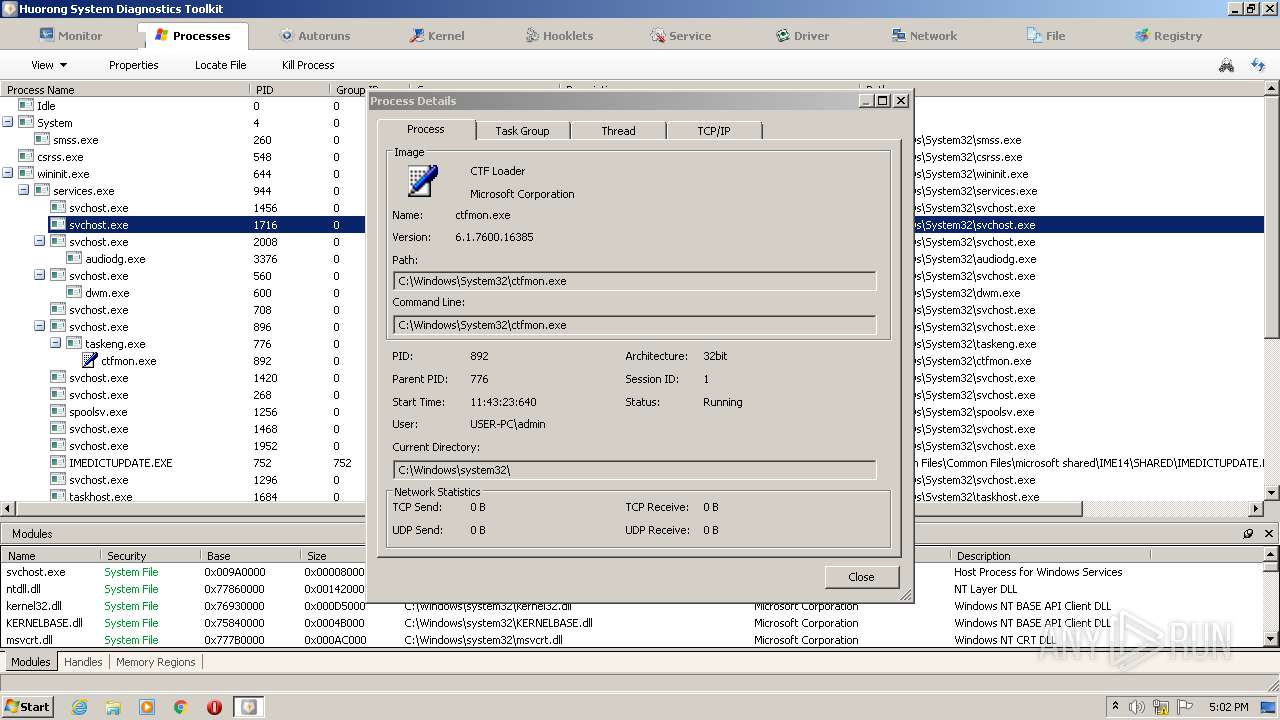
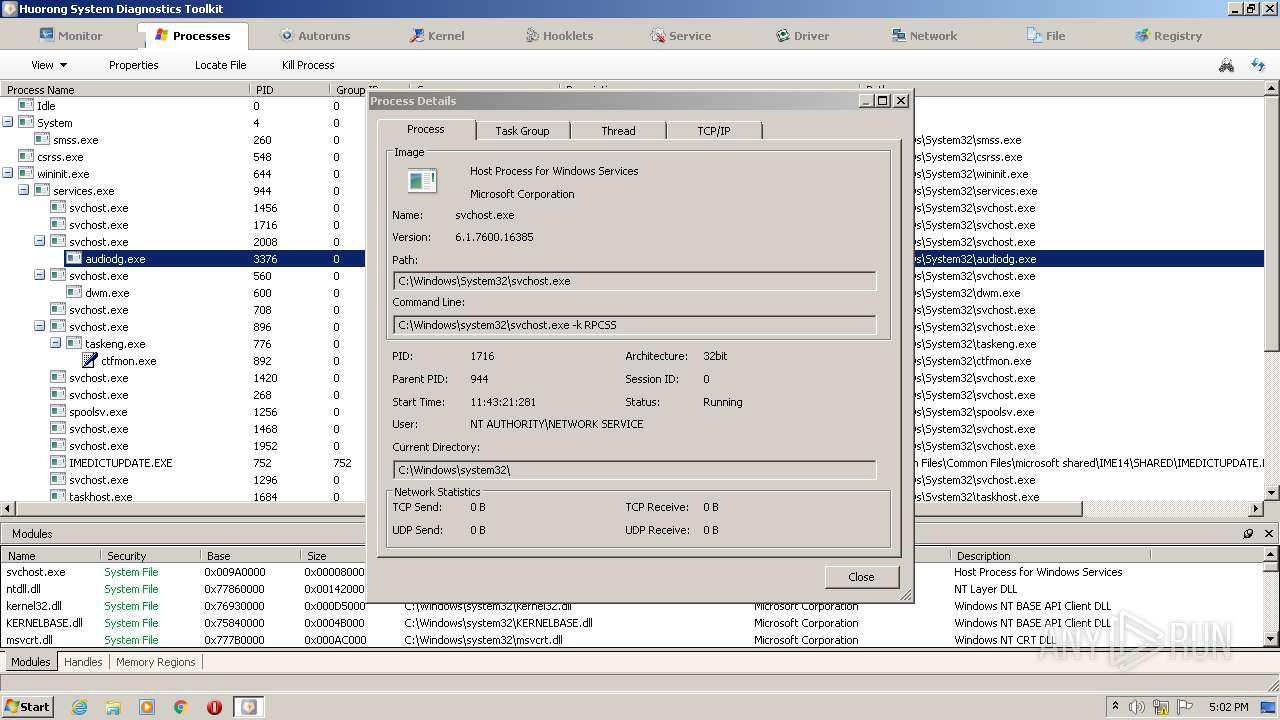
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Windows\System32\cmd.exe" /c @pushd "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000" >nul 2>&1 & CALL "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\HRSword.bat" | C:\Windows\System32\cmd.exe | — | HRSword.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 336 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag\Instances\sysdiag" /f /v "Flags" /t reg_dword /d "0" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | "C:\Users\admin\AppData\Local\Temp\HRSword.exe" | C:\Users\admin\AppData\Local\Temp\HRSword.exe | Explorer.EXE | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sword GUI Frontend Exit code: 0 Version: 5.0.1.1 Modules
| |||||||||||||||
| 660 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\hrwfpdr" /f /v "Start" /t reg_dword /d "1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1212 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag\Instances\sysdiag" /f /v "Altitude" /d "324600" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1780 | C:\Windows\system32\cmd.exe /S /D /c" echo y" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2164 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag" /f /v "Group" /d "PNP_TDI" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2308 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag\Instances" /f /v "DefaultInstance" /d "sysdiag" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | reg add "HKLM\SYSTEM\CurrentControlSet\Services\sysdiag" /f /v "Start" /t reg_dword /d "1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\usysdiag.exe" 276 | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\usysdiag.exe | — | HRSword.exe | |||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong Sysdiag Helper Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
45 590
Read events
45 555
Write events
35
Delete events
0
Modification events
| (PID) Process: | (348) HRSword.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (348) HRSword.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (348) HRSword.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (348) HRSword.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3972) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\sysdiag.sys | |||
| (PID) Process: | (3580) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\hrwfpdr |
| Operation: | write | Name: | ImagePath |
Value: system32\DRIVERS\hrwfpdrv.sys | |||
| (PID) Process: | (2436) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (660) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\hrwfpdr |
| Operation: | write | Name: | Start |
Value: 1 | |||
| (PID) Process: | (2164) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag |
| Operation: | write | Name: | Group |
Value: PNP_TDI | |||
| (PID) Process: | (2308) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\sysdiag\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: sysdiag | |||
Executable files
15
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Drivers\x32\usysdiag.exe | executable | |
MD5:0DAB2B702C7D5EE0B3BFA49D6056EF88 | SHA256:DF33AD03FC7DFB1C3F5FEA50F6C7E7849475B02513FB8B14E64485B341936E08 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Drivers\x64\hrwfpdrv.sys | executable | |
MD5:3D6B41A929F4E43DD314D1FAACFEAA07 | SHA256:01A3DABB4684908082CB2AC710D5D42AFAE2D30F282F023D54D7E945AD3272F5 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\uactmon.dll | executable | |
MD5:B5EFA5D82E2D5E56641DF5F51C2F4FA9 | SHA256:D54E680DE12427DEE9BD3F1681C388B9D68856BF05A04AAF8F3285ACC02E9A62 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\daemon.dll | executable | |
MD5:FF1FEBCBE870732F1D5C05249BF170BD | SHA256:C73619449CEA5194E5D8B43BD45758419853DC6CF67FDC0D6C561011671E1007 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Drivers\x64\usysdiag.exe | executable | |
MD5:033C9F28ACADAAA32D947A4026020BEA | SHA256:90040340EE101CAC7831D7035230AC8AD4224D432E5636F34F13AA1C4A0C2041 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Drivers\x32\sysdiag.sys | executable | |
MD5:98009F56C26AD1965F72C99C97B6E1A0 | SHA256:00E9FFD2D752E93B8965E0F337808D4885FA8DBE2F6EDD5CD3BC06C364D200FB | |||
| 3520 | cmd.exe | C:\Windows\System32\drivers\hrwfpdrv.sys | executable | |
MD5:EB360278D37EE0F622E11EE283089D6D | SHA256:709574B19CA0951264FAF3C8E2C1A5EA85FA38AFB4D7A1B1EF9034FEC0193778 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\libcodecs.dll | executable | |
MD5:6450F7382AB6829AB19E46F05EBE1A35 | SHA256:2A20F321C58F83E0CB79000033ABBD5DCBE94FEB91272A77F959069395289561 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Drivers\x32\hrwfpdrv.sys | executable | |
MD5:EB360278D37EE0F622E11EE283089D6D | SHA256:709574B19CA0951264FAF3C8E2C1A5EA85FA38AFB4D7A1B1EF9034FEC0193778 | |||
| 348 | HRSword.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\libxsse.dll | executable | |
MD5:4DE8057329A2F741E4C67F4CBE962632 | SHA256:B8BD7D55298617AB2620C83789D61A4CC4765E868BE706CE1C361C9C2603E421 | |||
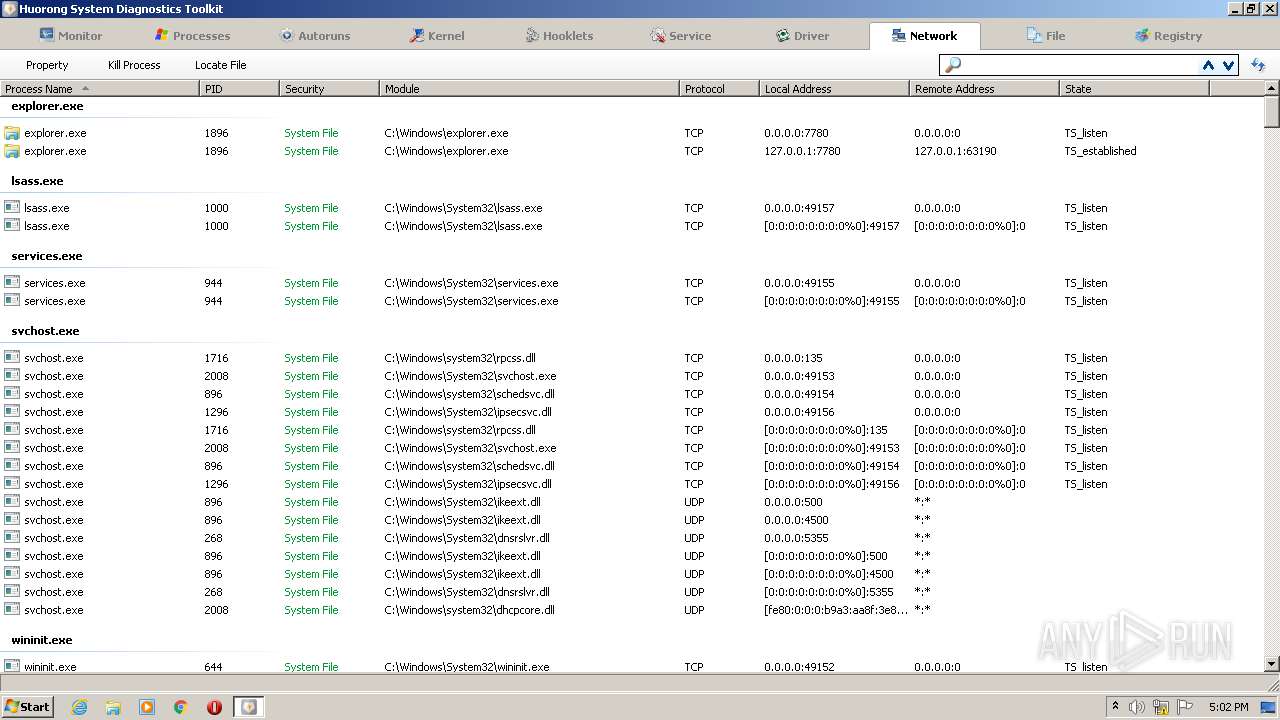
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report