| File name: | x86.zip |
| Full analysis: | https://app.any.run/tasks/c44ddc10-9335-44b1-8ba3-8fc25324eeb4 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 17:43:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6FB4676057C0F20BB37346DCFC3B9B25 |
| SHA1: | 0D58B3F6095807AE78888DA8217F79B30B495EA6 |
| SHA256: | E7015F22DAE1F9E9372377AA09C28CCA965D4C93349A0BB9A9E49D936E17DA9D |
| SSDEEP: | 49152:8UTMznChcHAtzhe1NdioDJnFK2STbq3XIH:VT7Bu1nioDLK2EbhH |
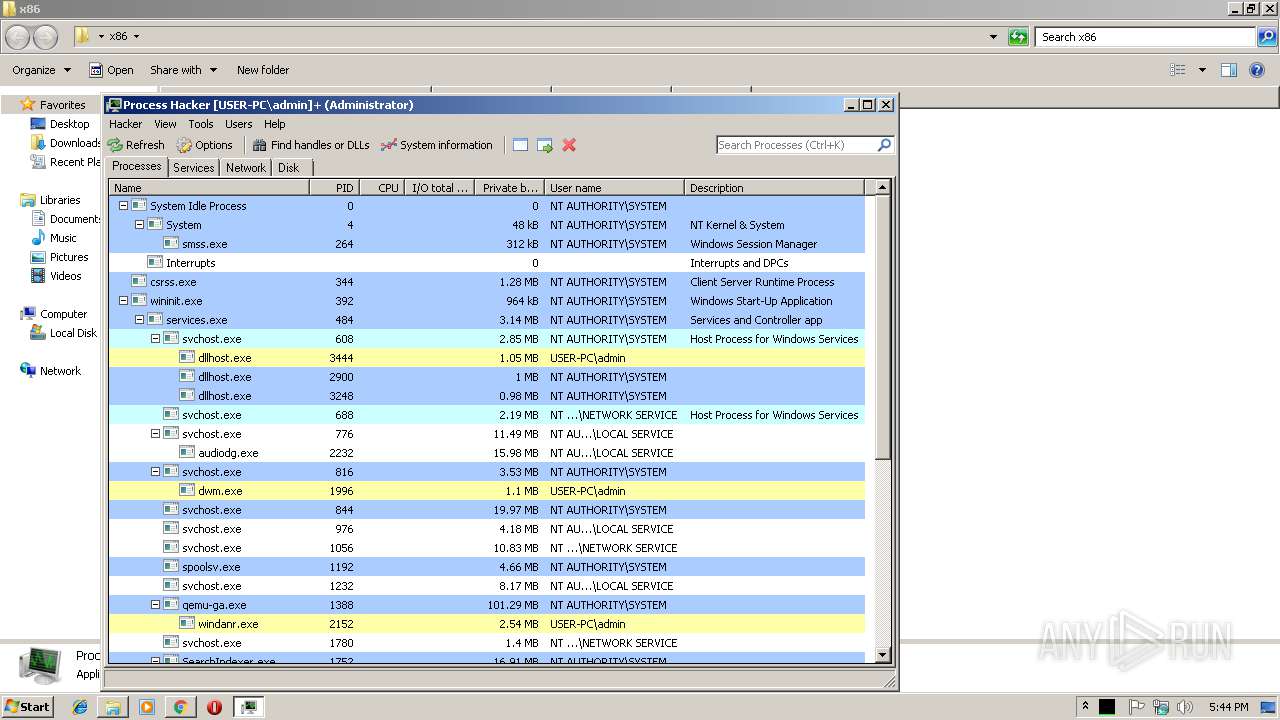
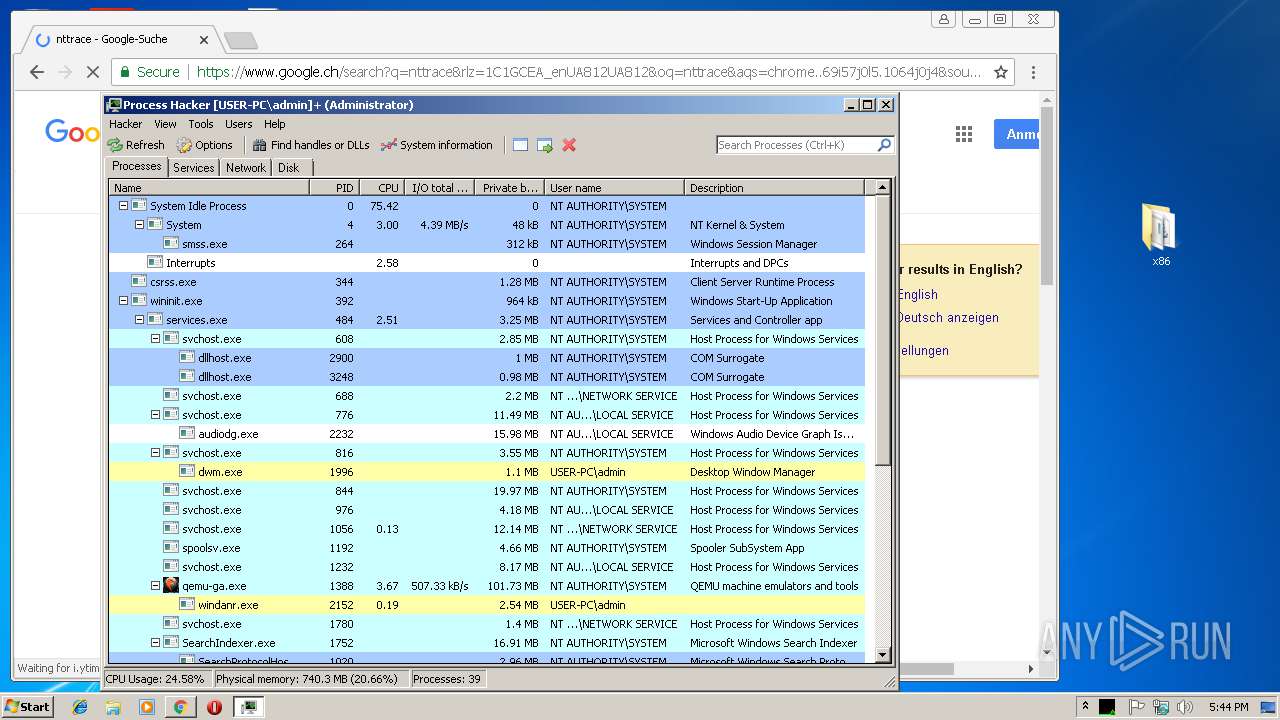
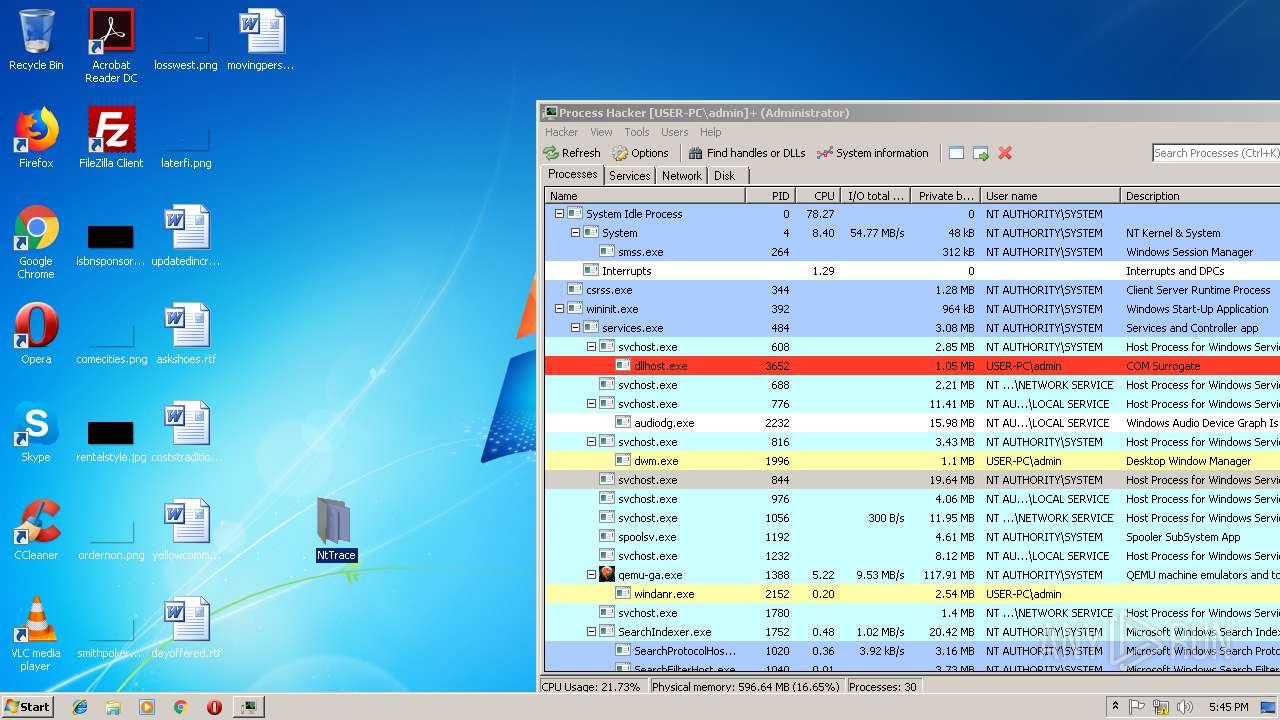
MALICIOUS
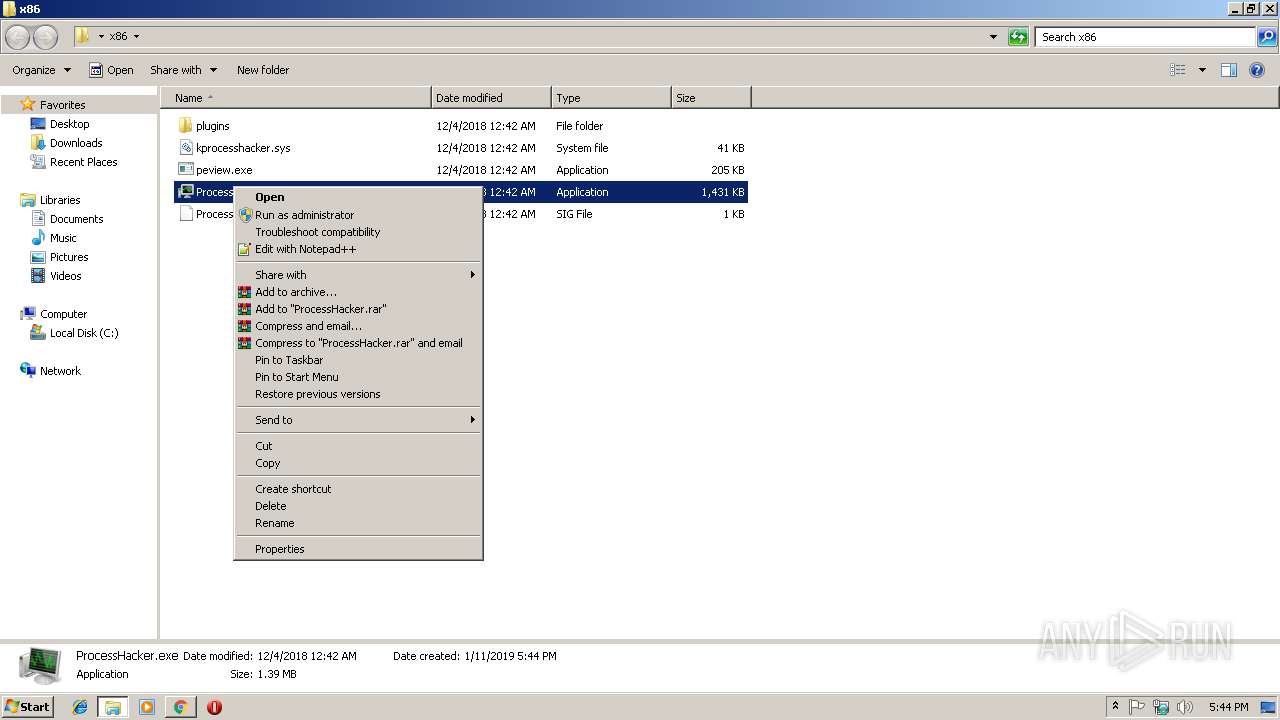
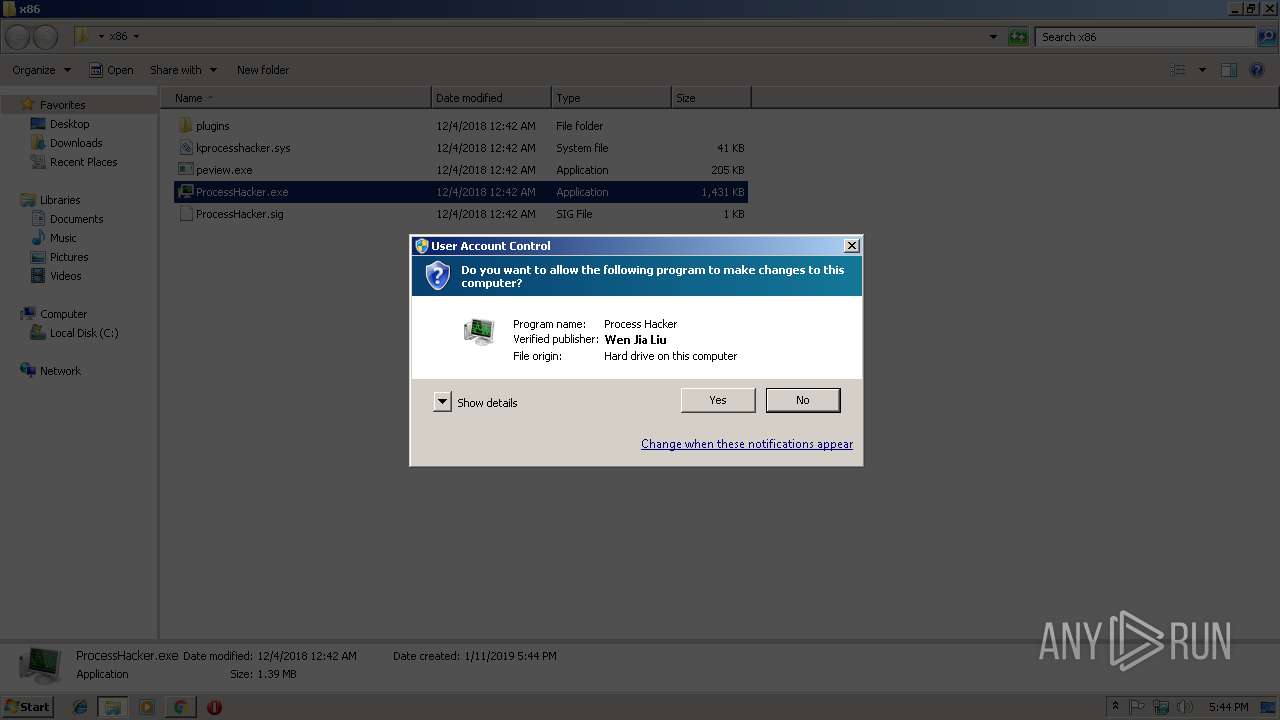
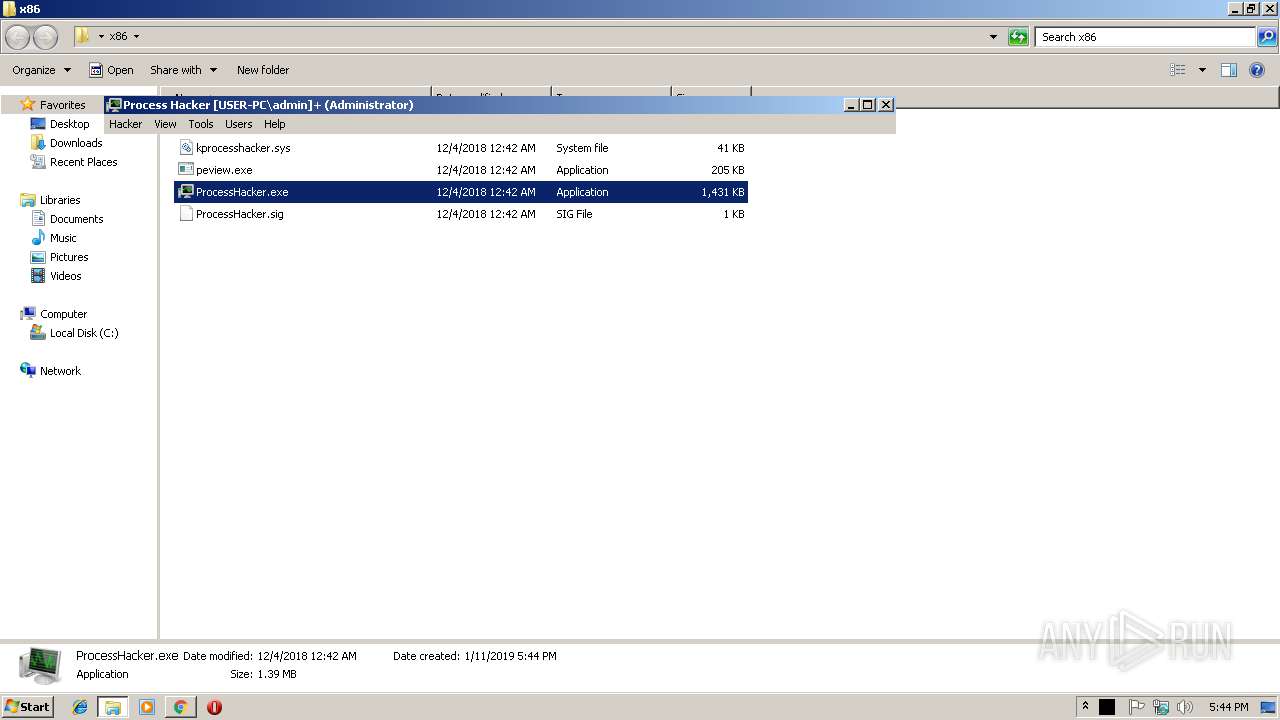
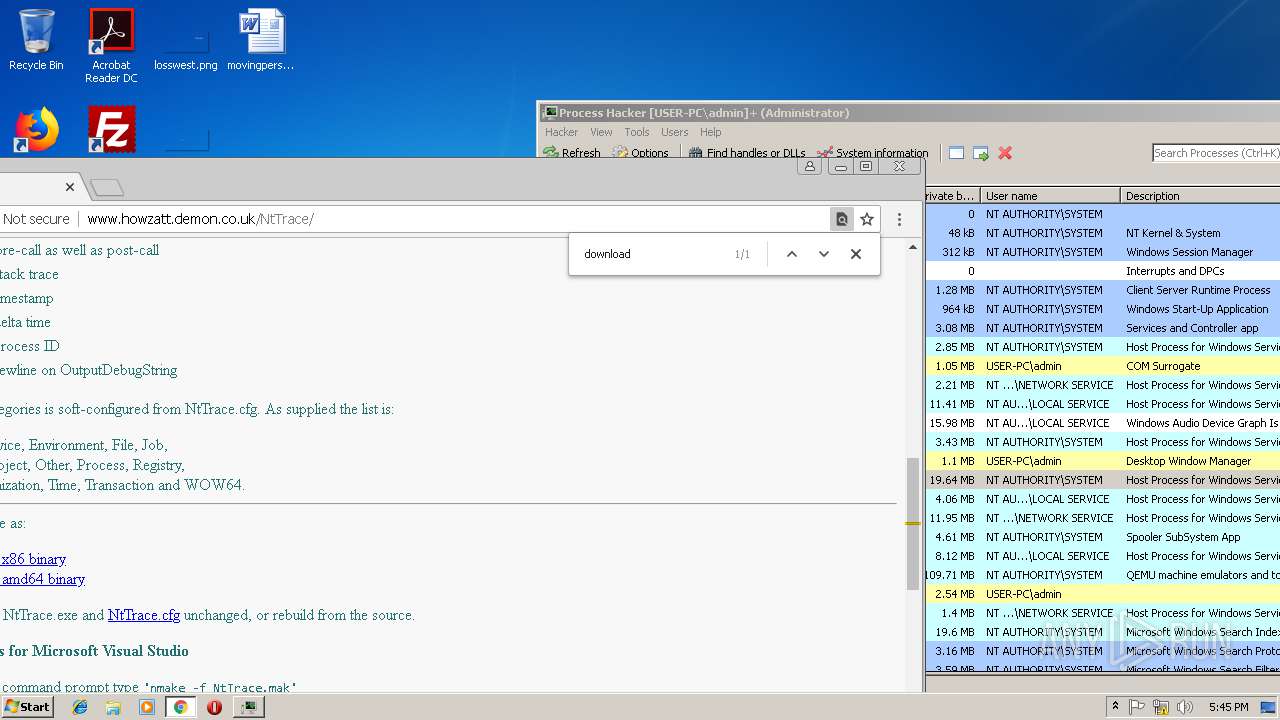
Loads dropped or rewritten executable
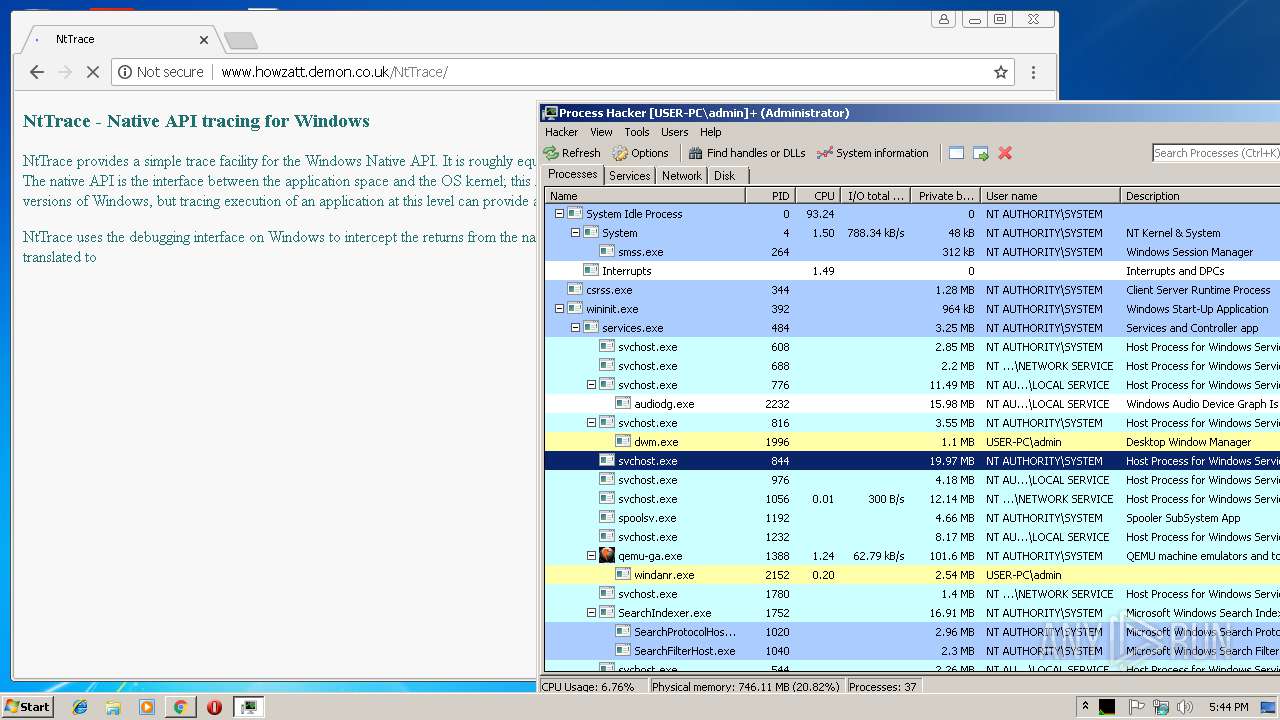
- SearchProtocolHost.exe (PID: 1020)
- ProcessHacker.exe (PID: 2572)
Changes settings of System certificates
- ProcessHacker.exe (PID: 2572)
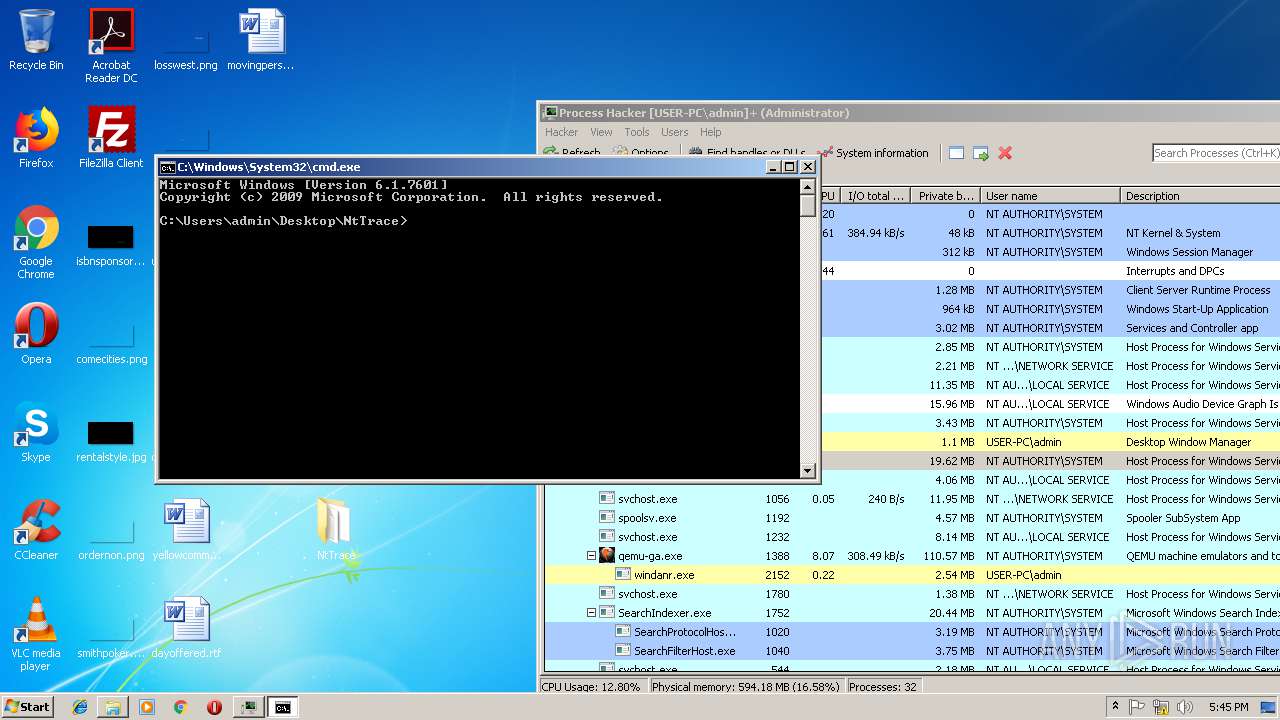
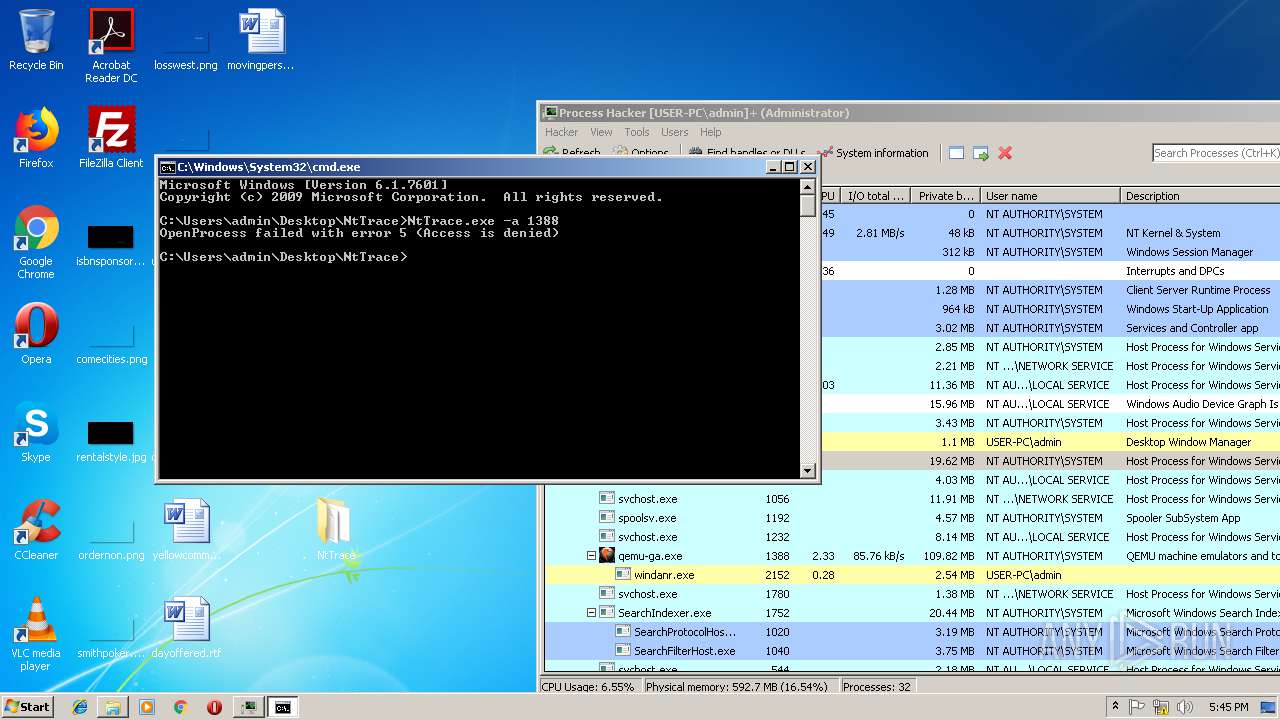
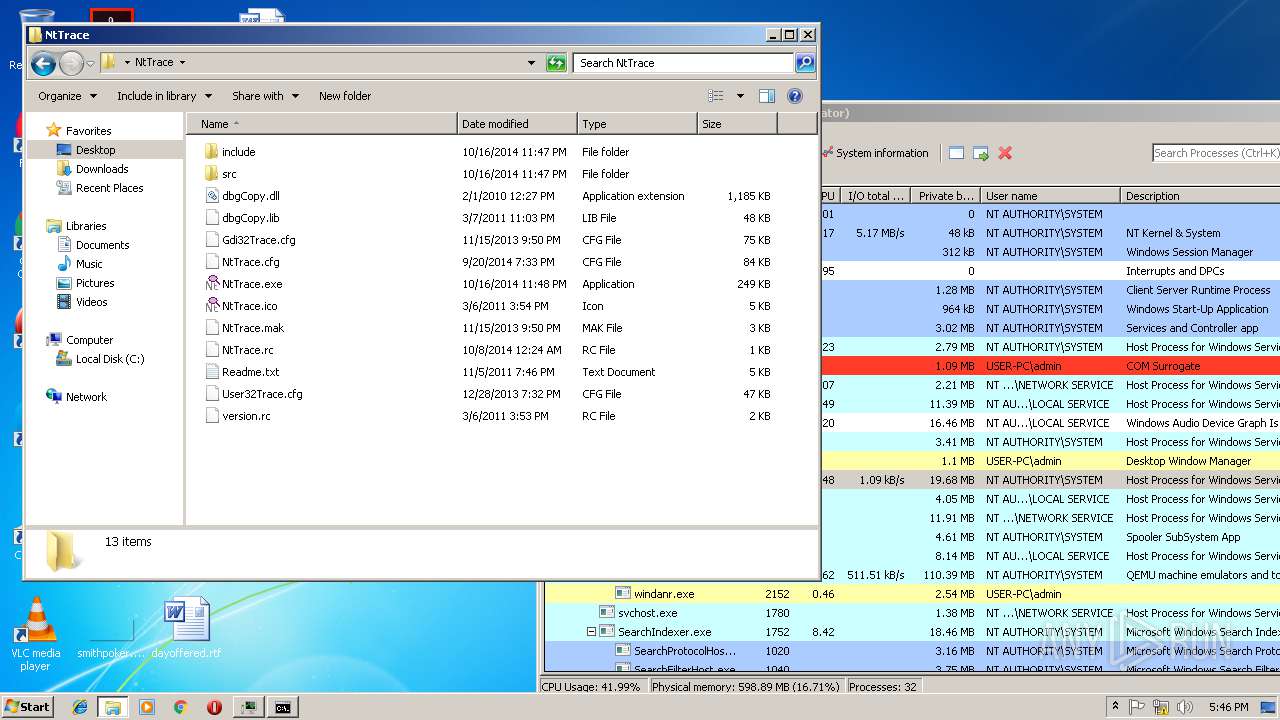
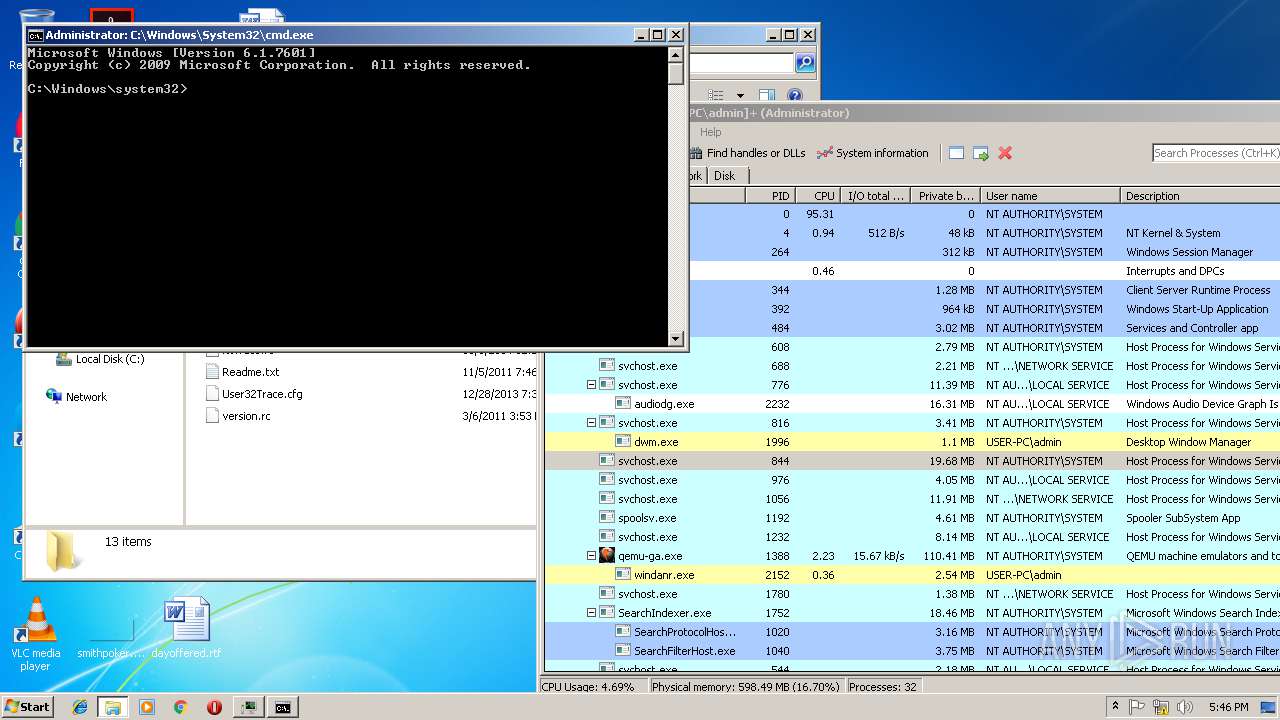
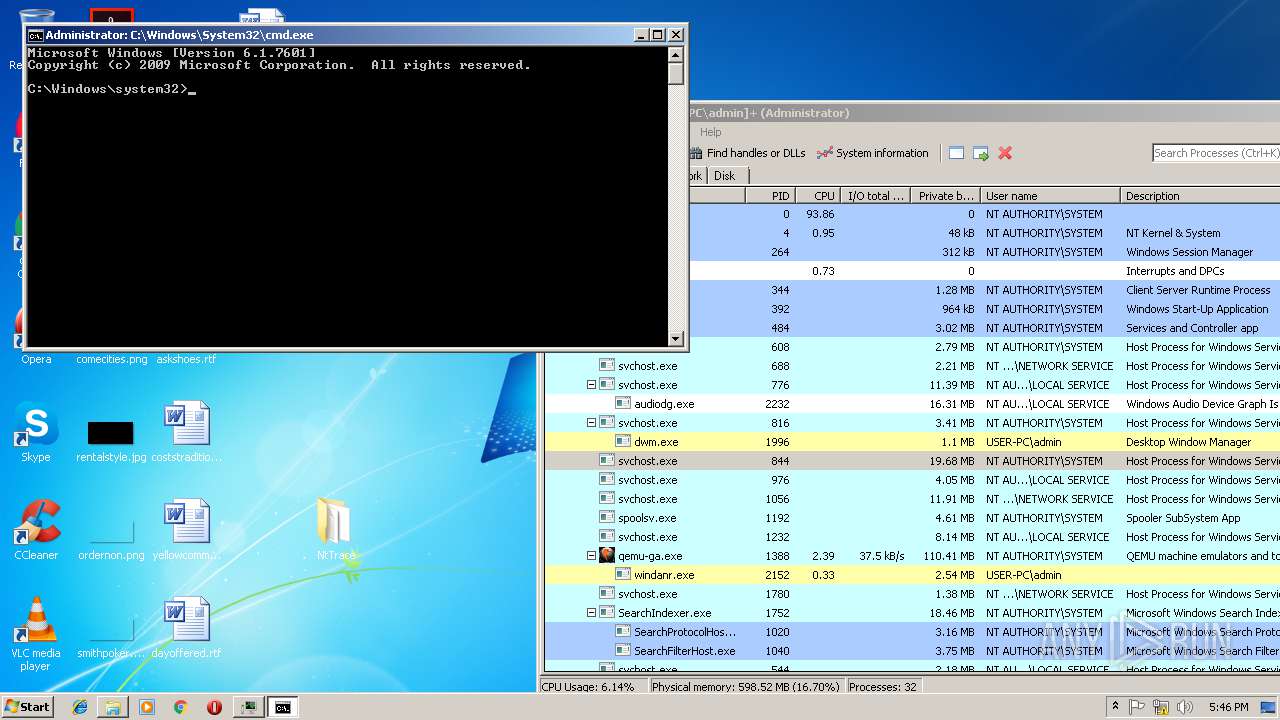
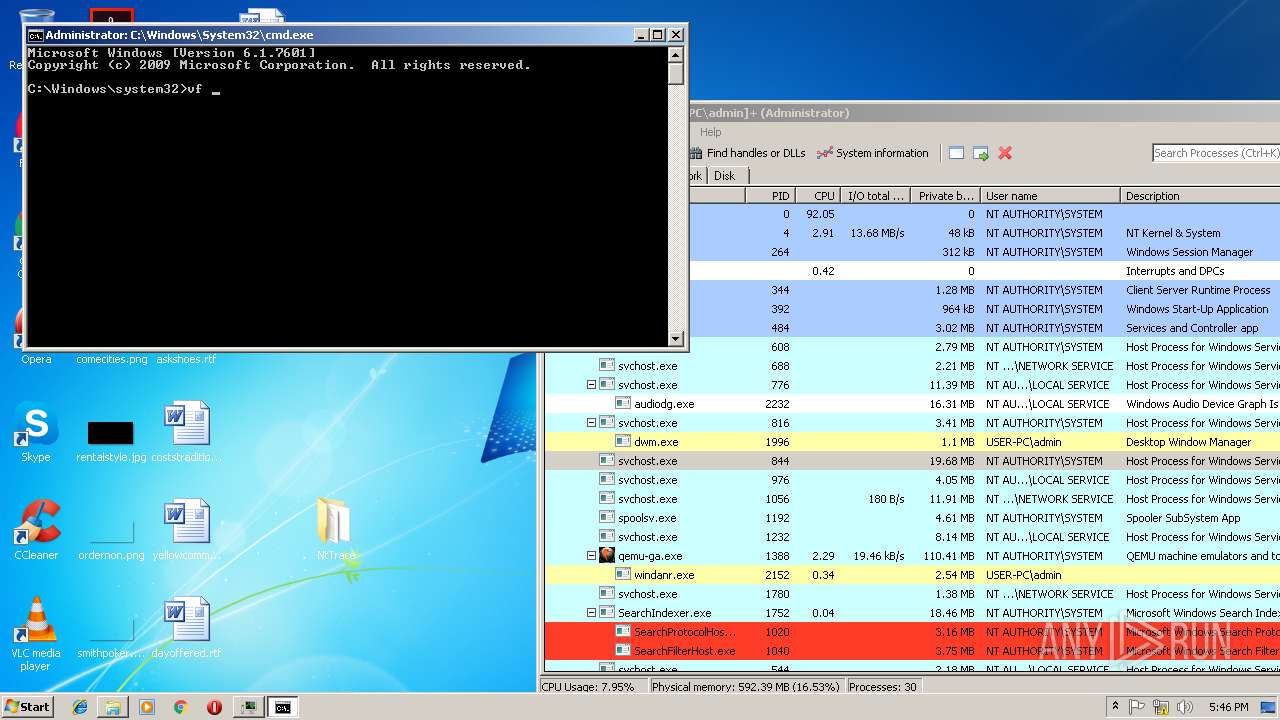
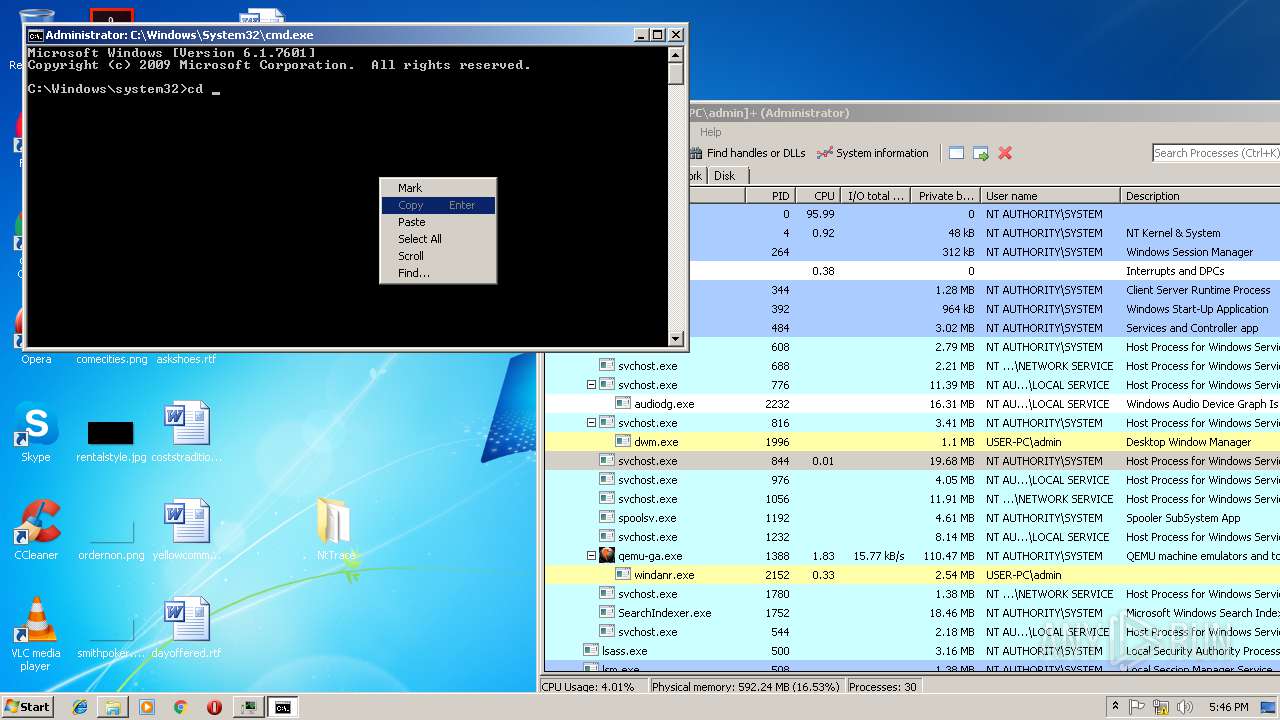
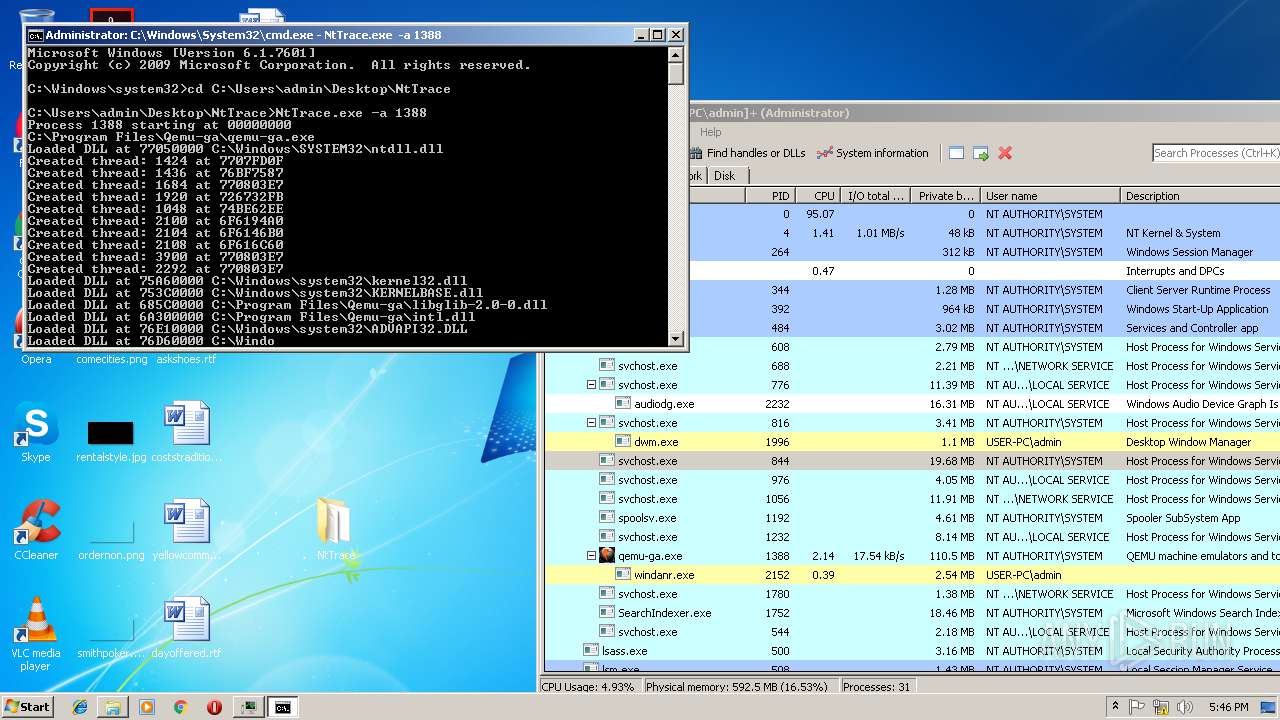
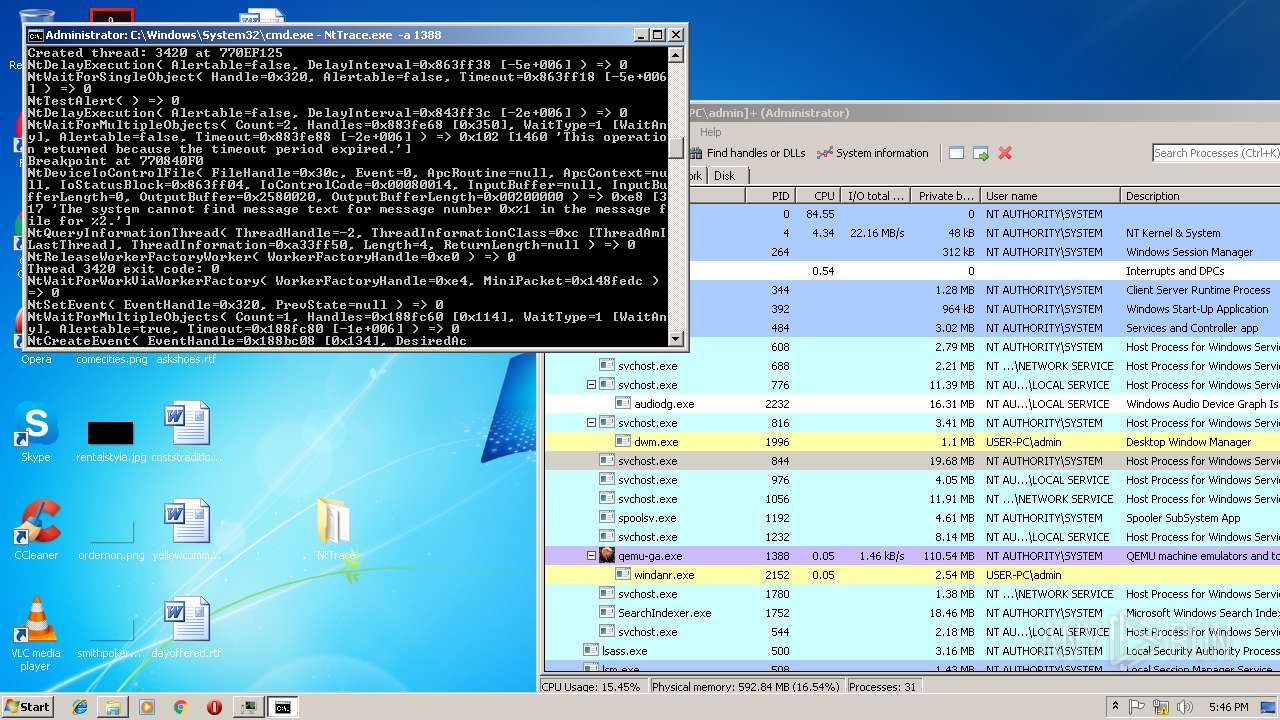
Runs injected code in another process
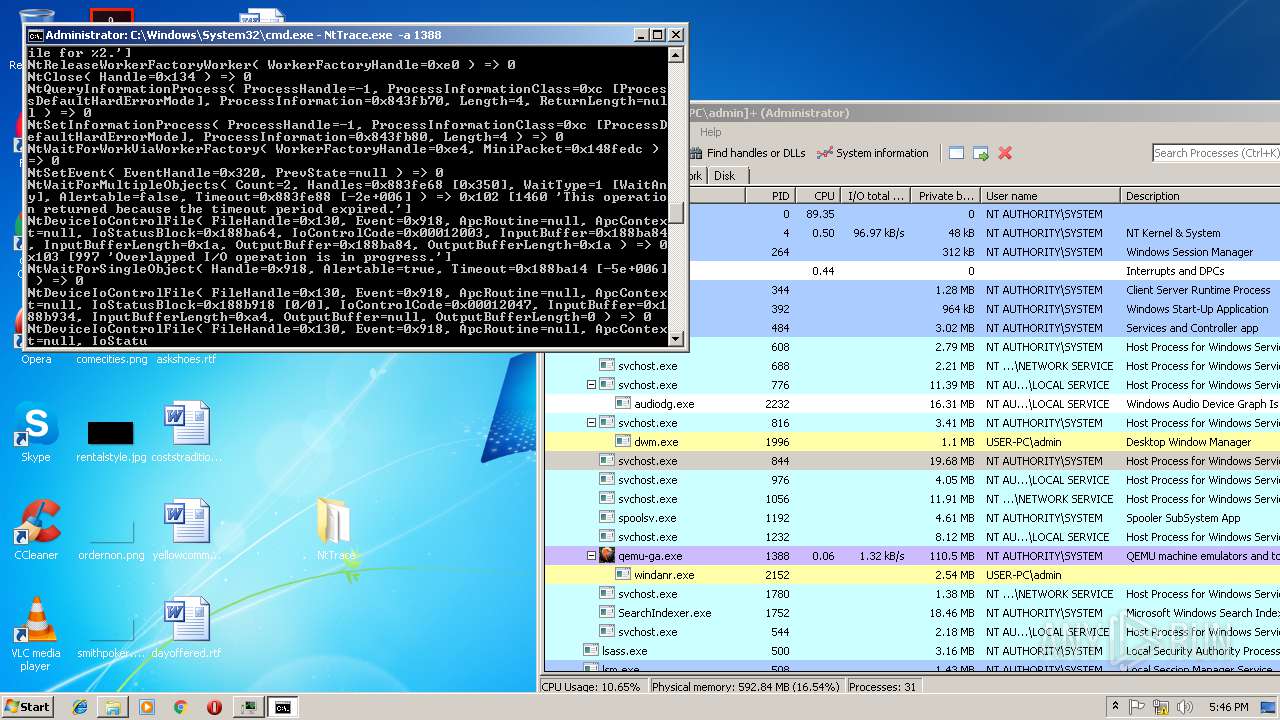
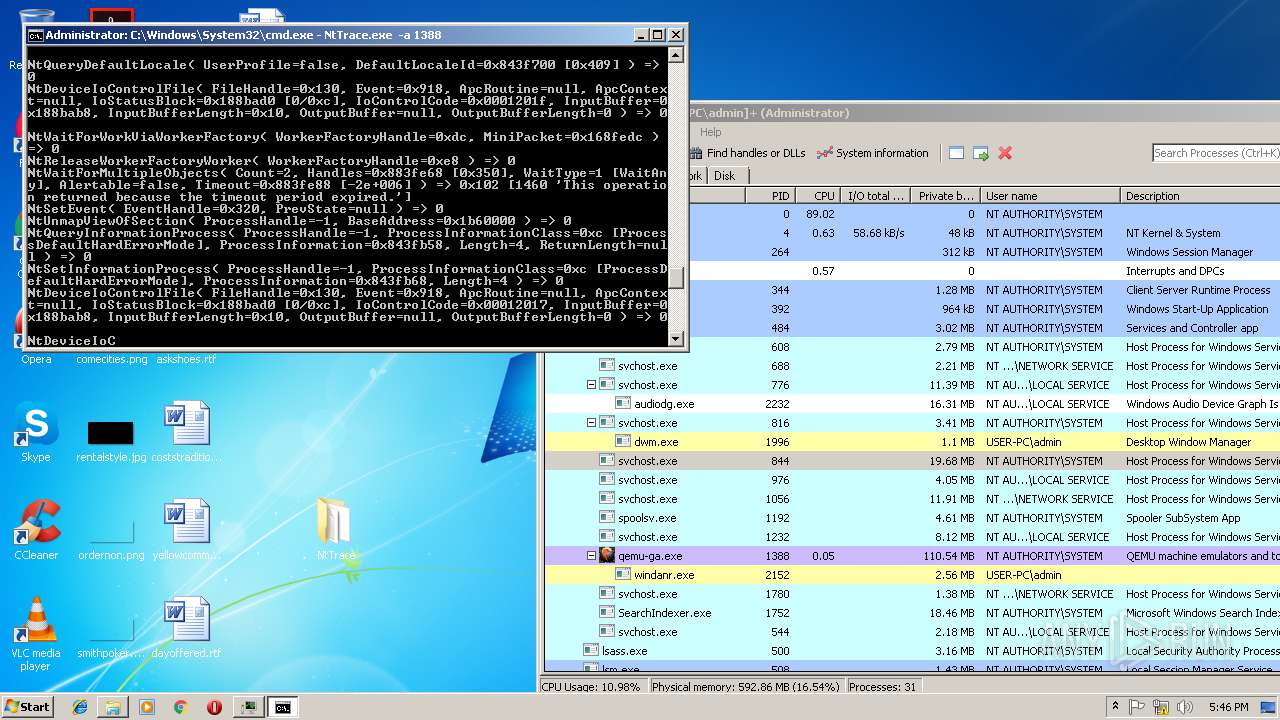
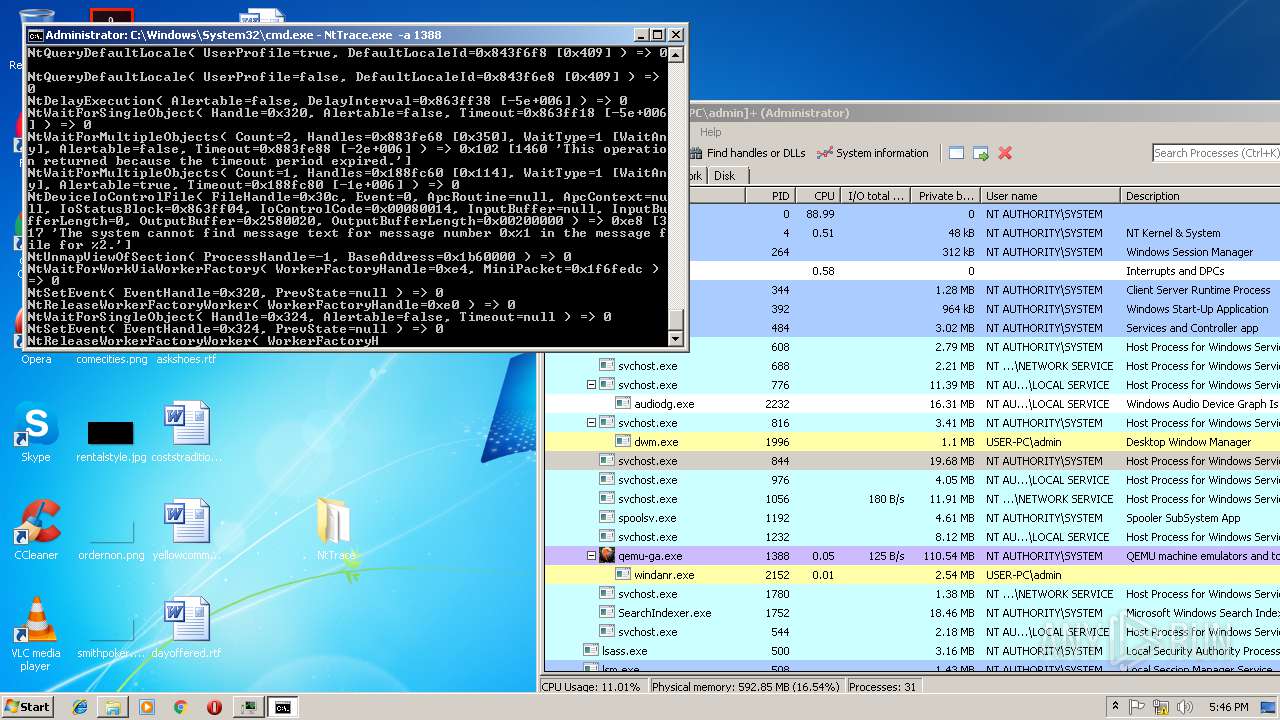
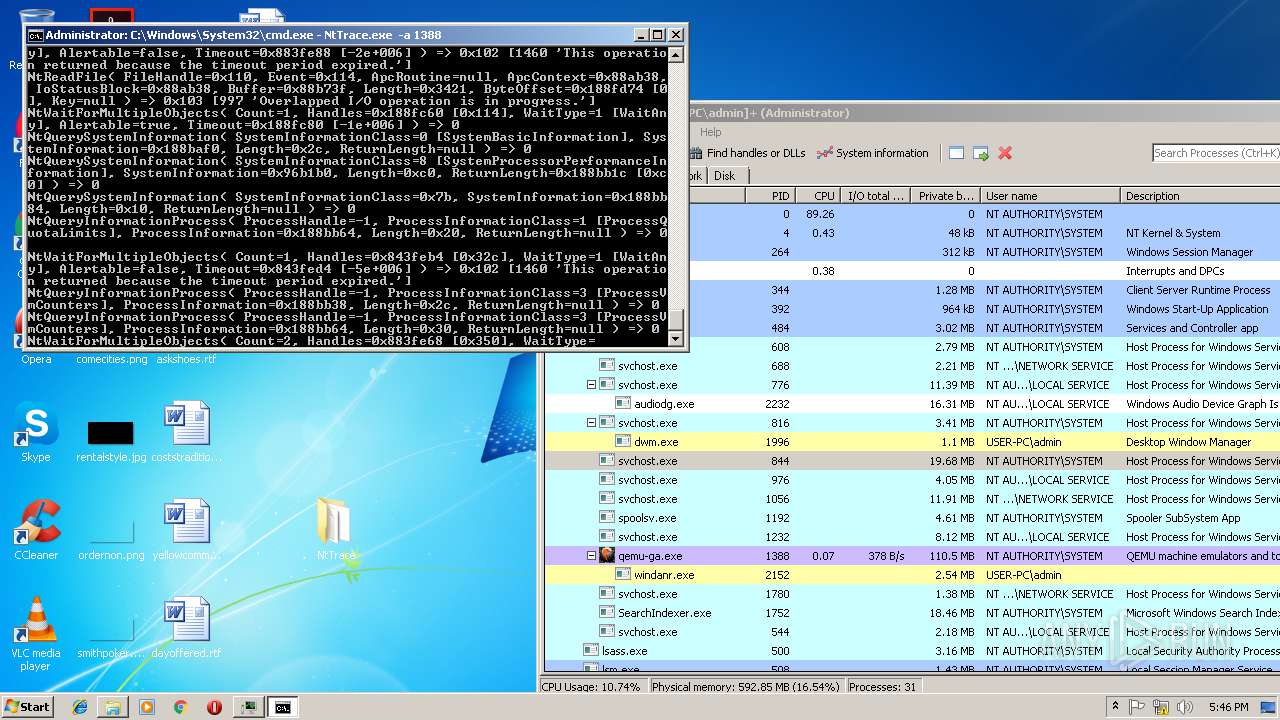
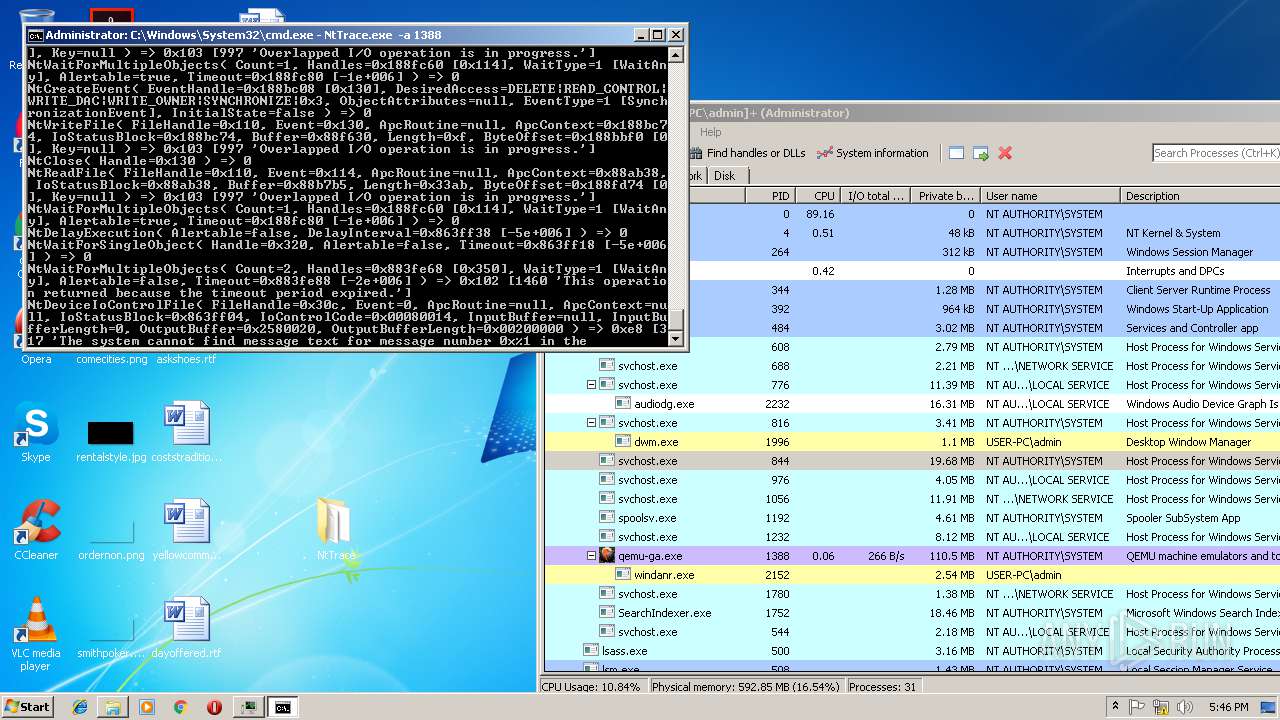
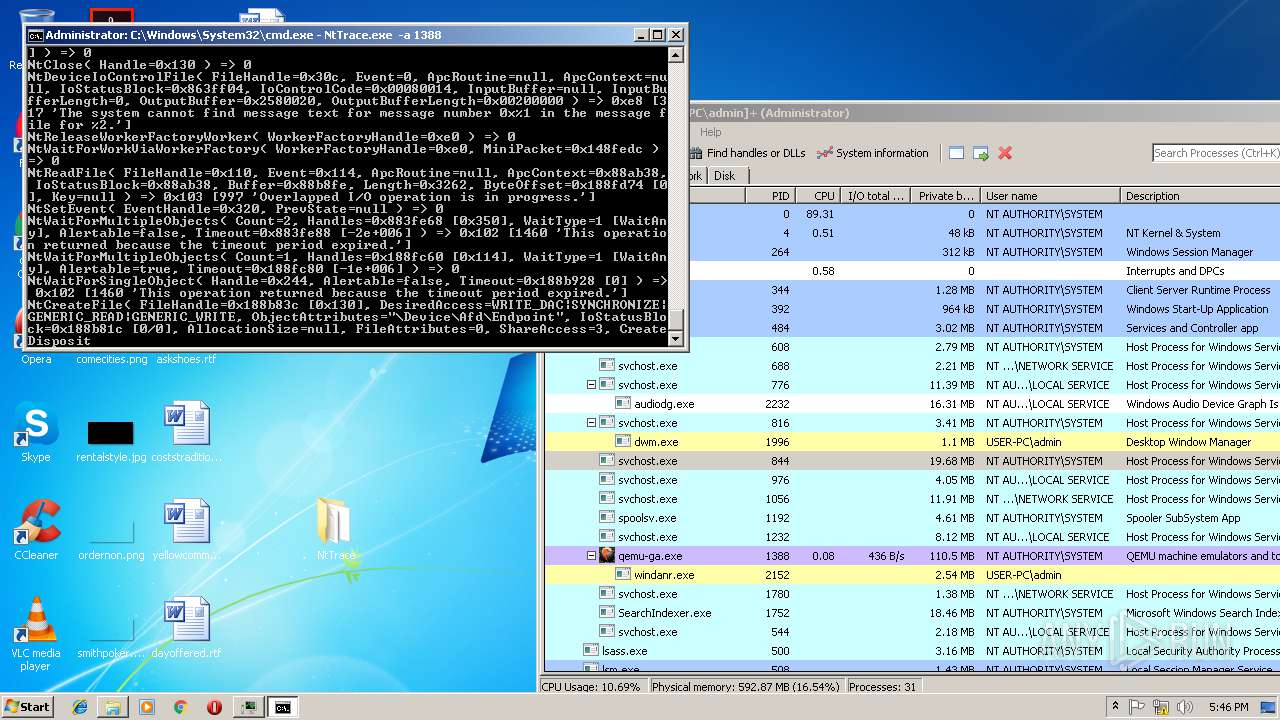
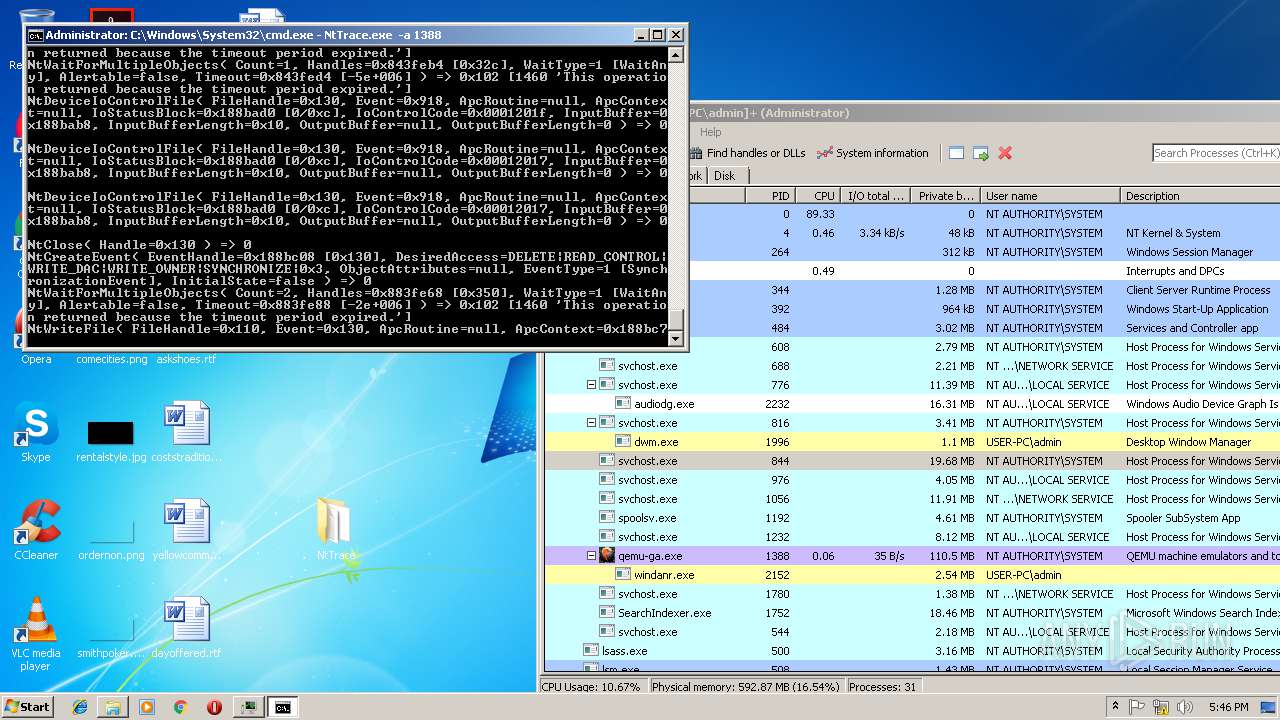
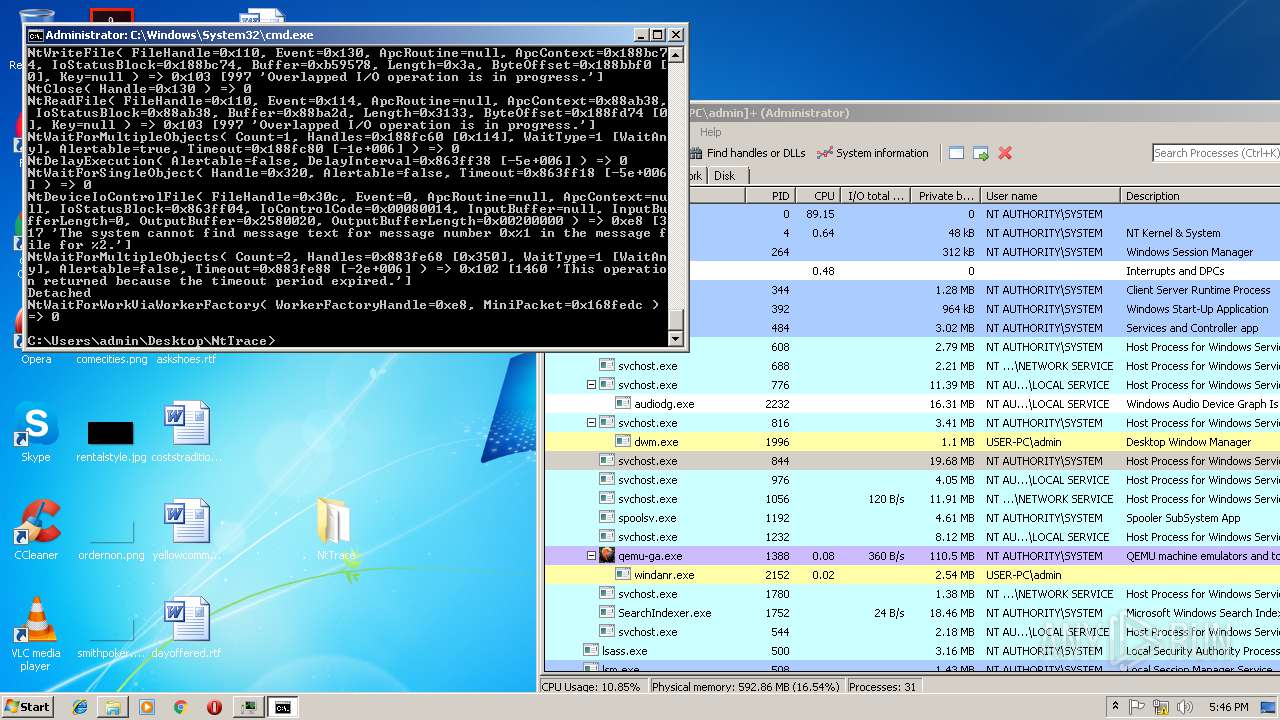
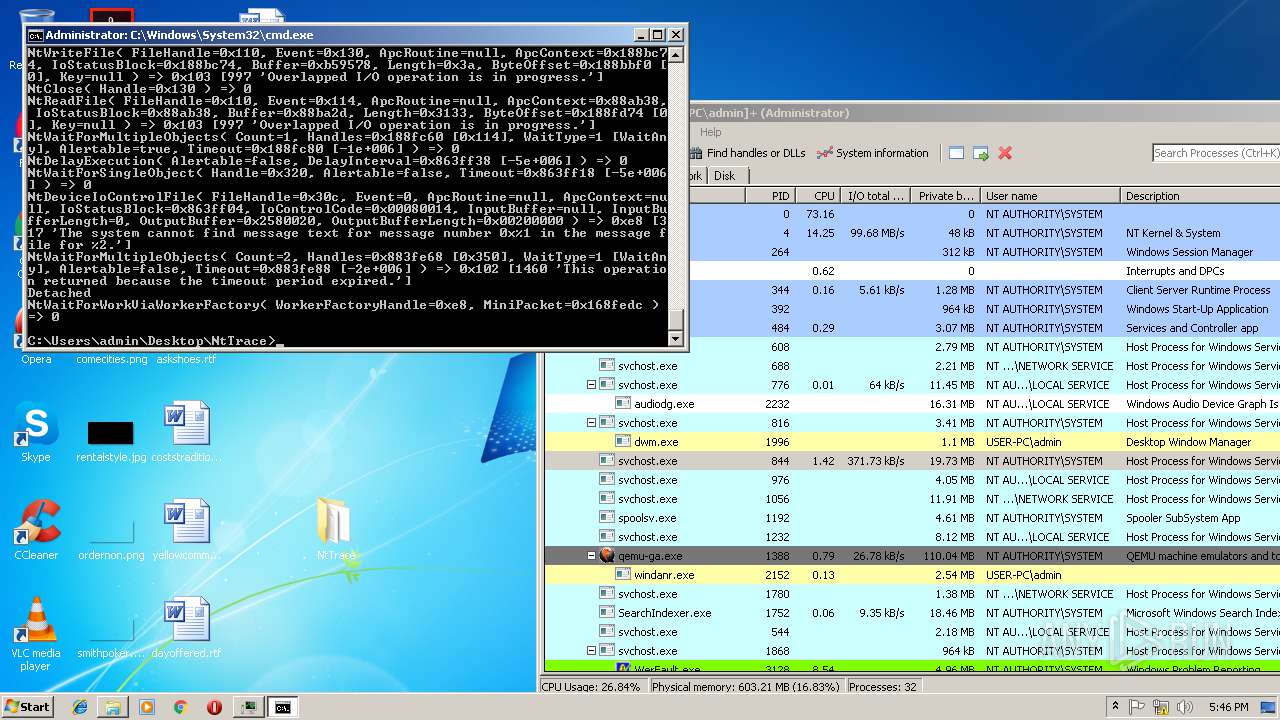
- NtTrace.exe (PID: 3844)
Application was injected by another process
- qemu-ga.exe (PID: 1388)
SUSPICIOUS
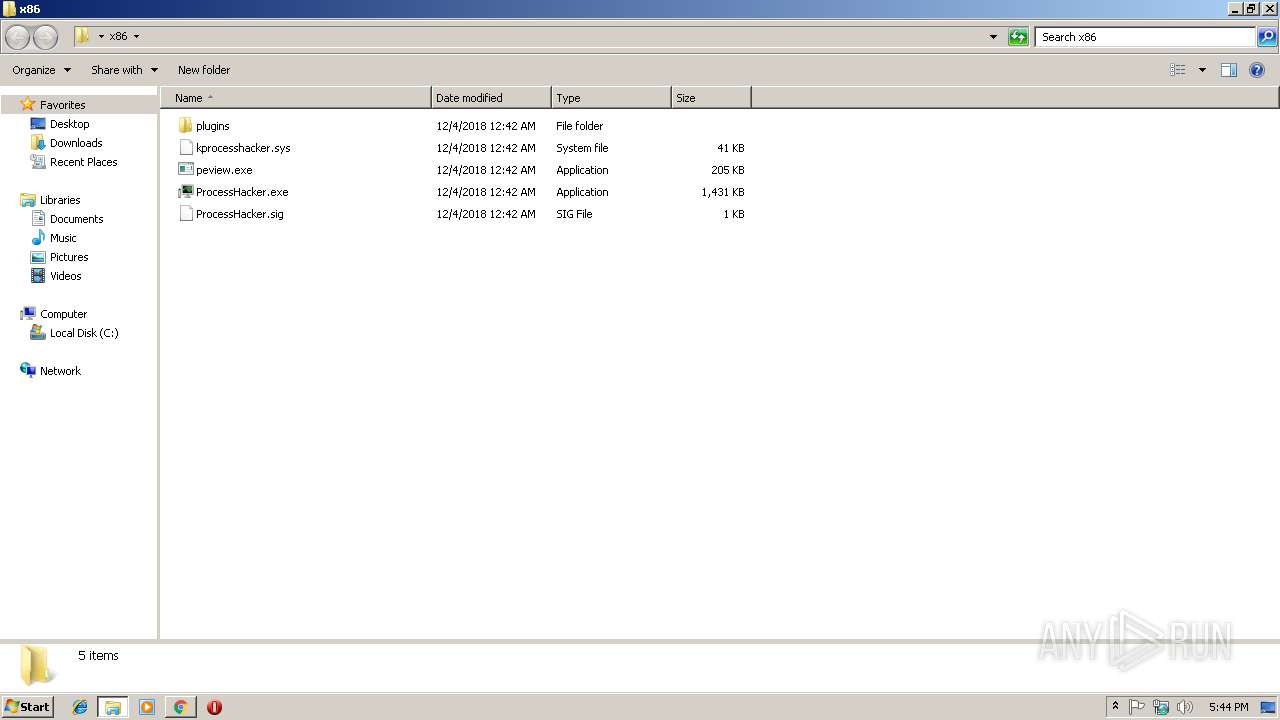
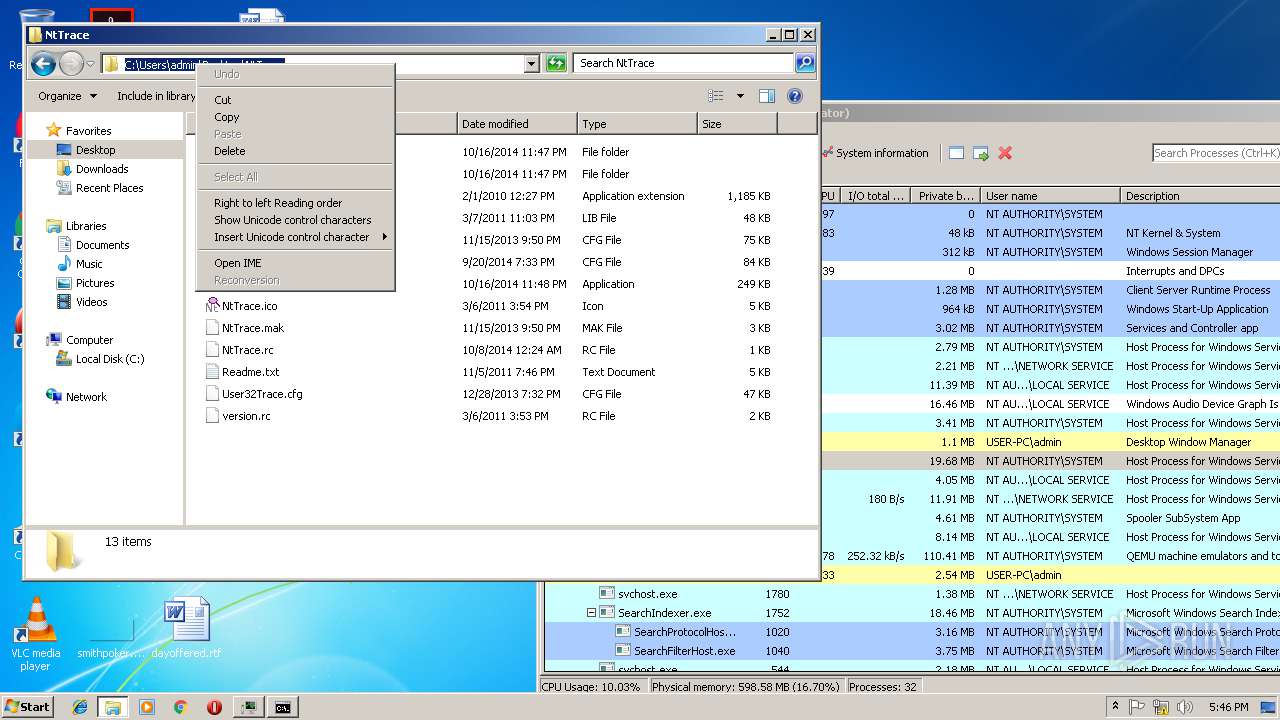
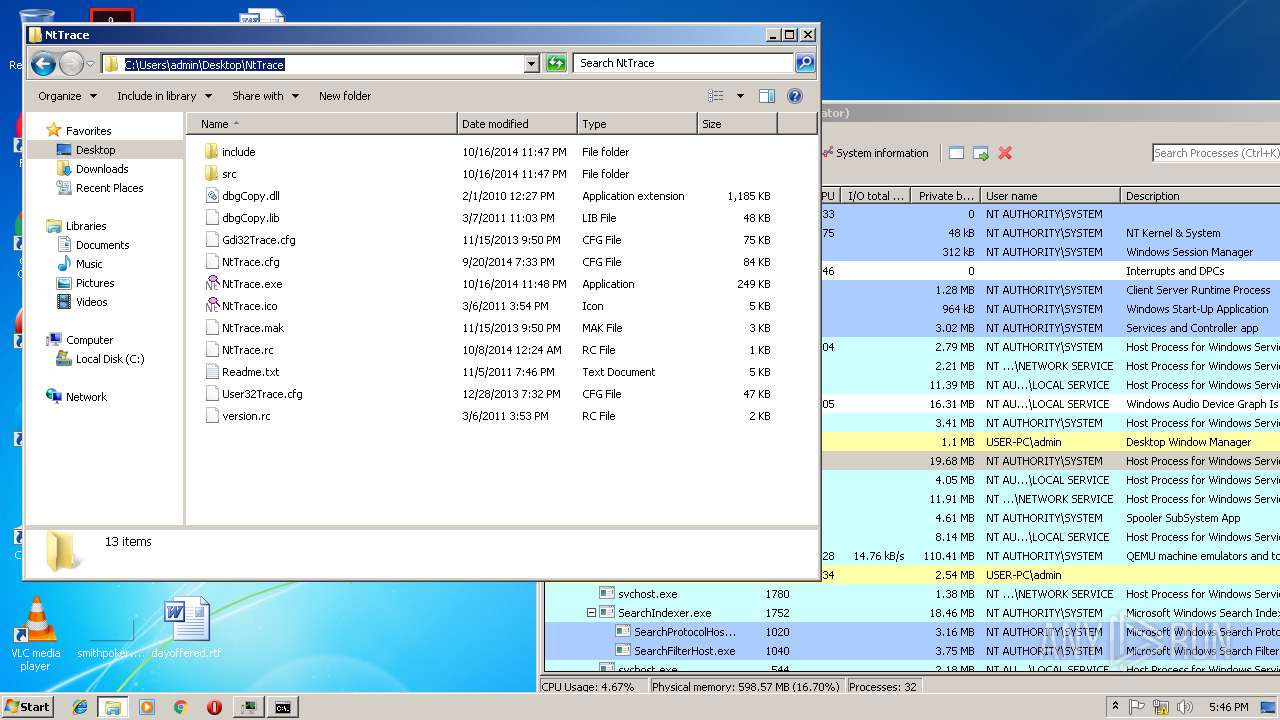
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2816)
Adds / modifies Windows certificates
- ProcessHacker.exe (PID: 2572)
INFO
Application launched itself
- chrome.exe (PID: 2452)
Reads Internet Cache Settings
- chrome.exe (PID: 2452)
Reads settings of System Certificates
- ProcessHacker.exe (PID: 2572)
- chrome.exe (PID: 2452)
Creates files in the user directory
- chrome.exe (PID: 2452)
Application was crashed
- qemu-ga.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
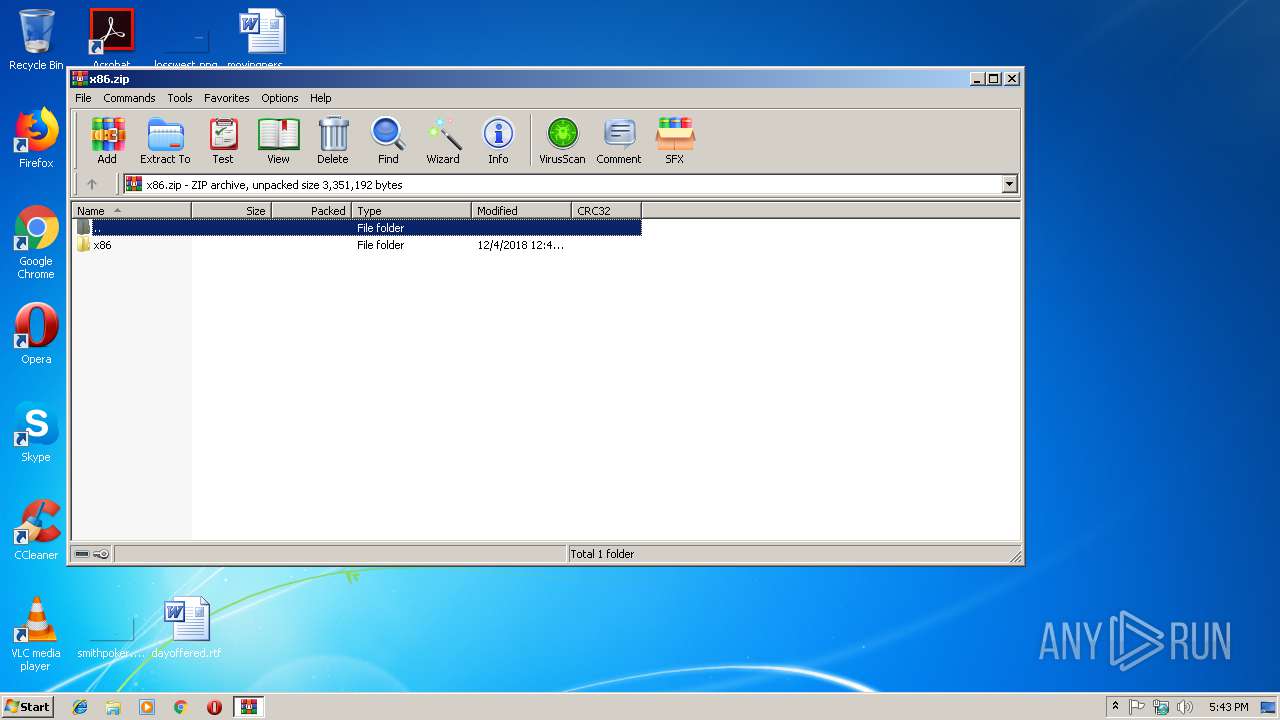
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:12:04 03:42:23 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | x86/ |
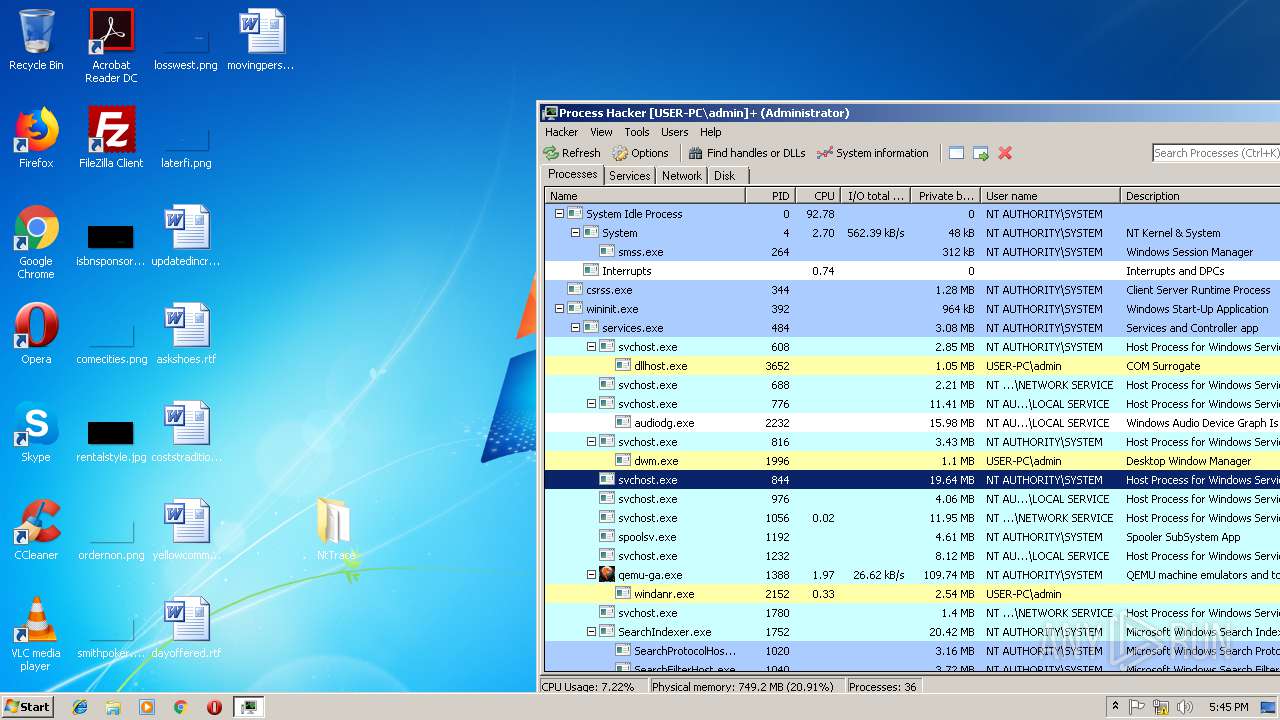
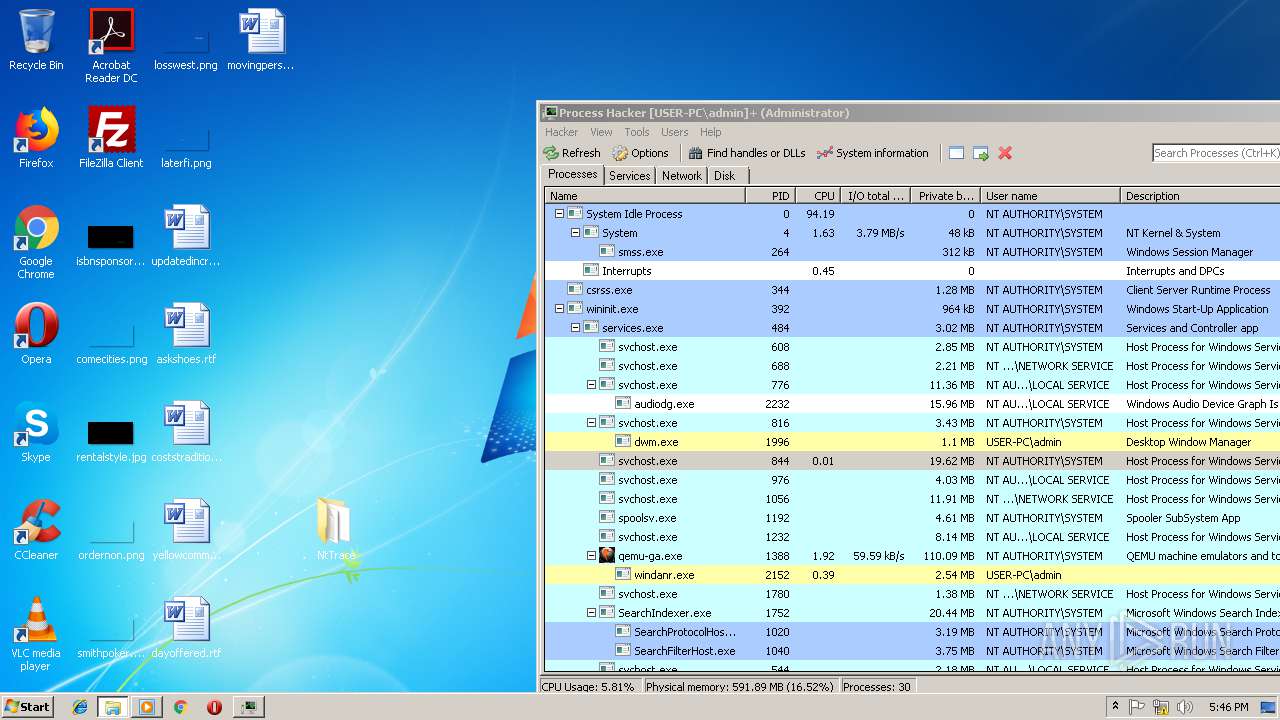
Total processes
66
Monitored processes
25
Malicious processes
2
Suspicious processes
0
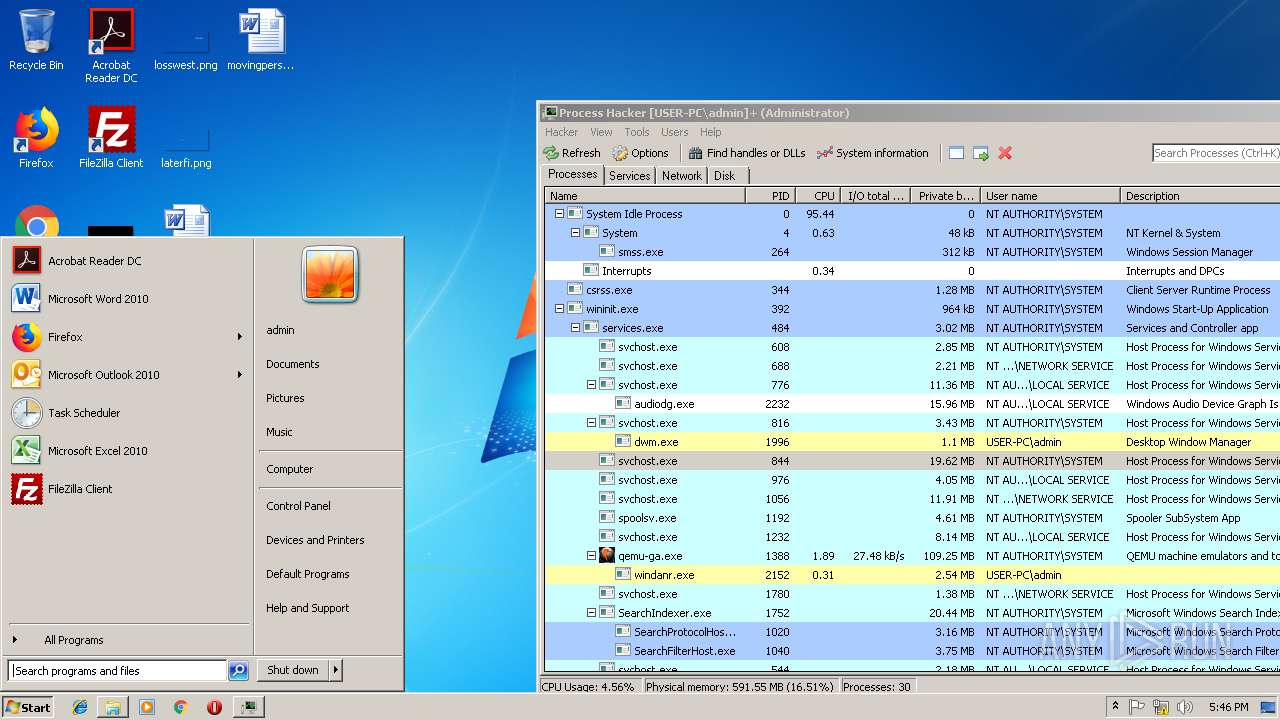
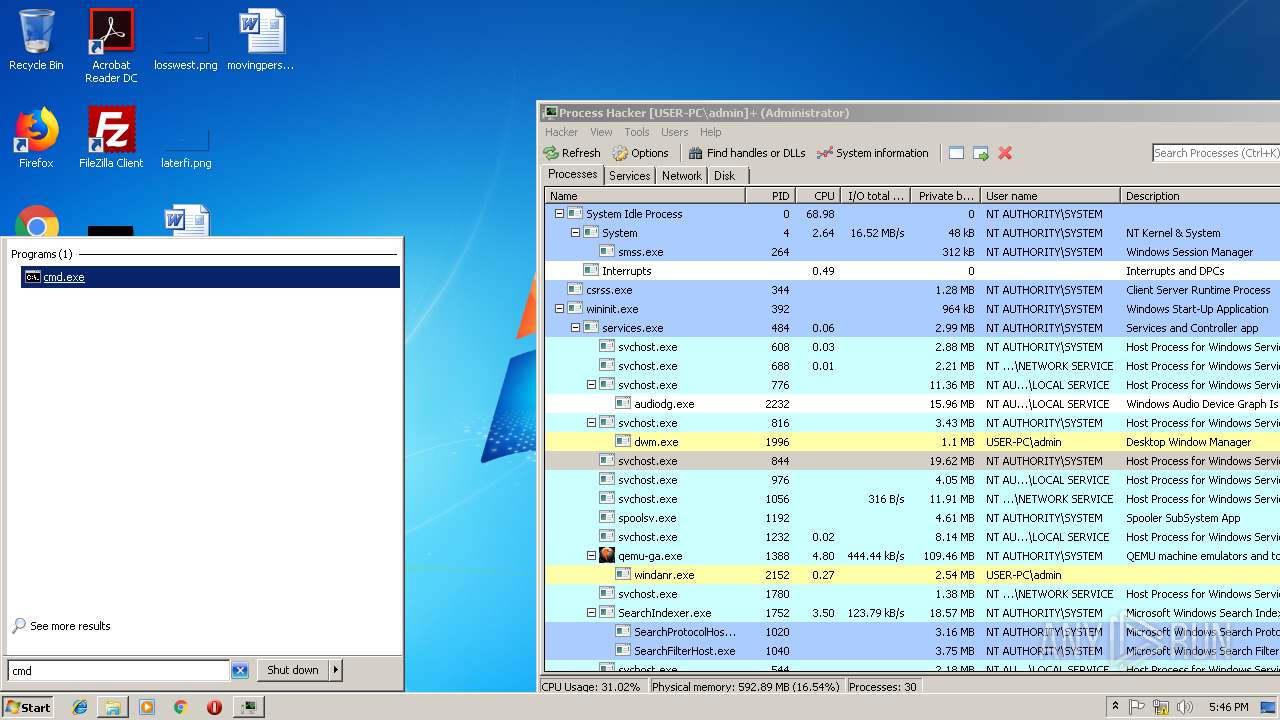
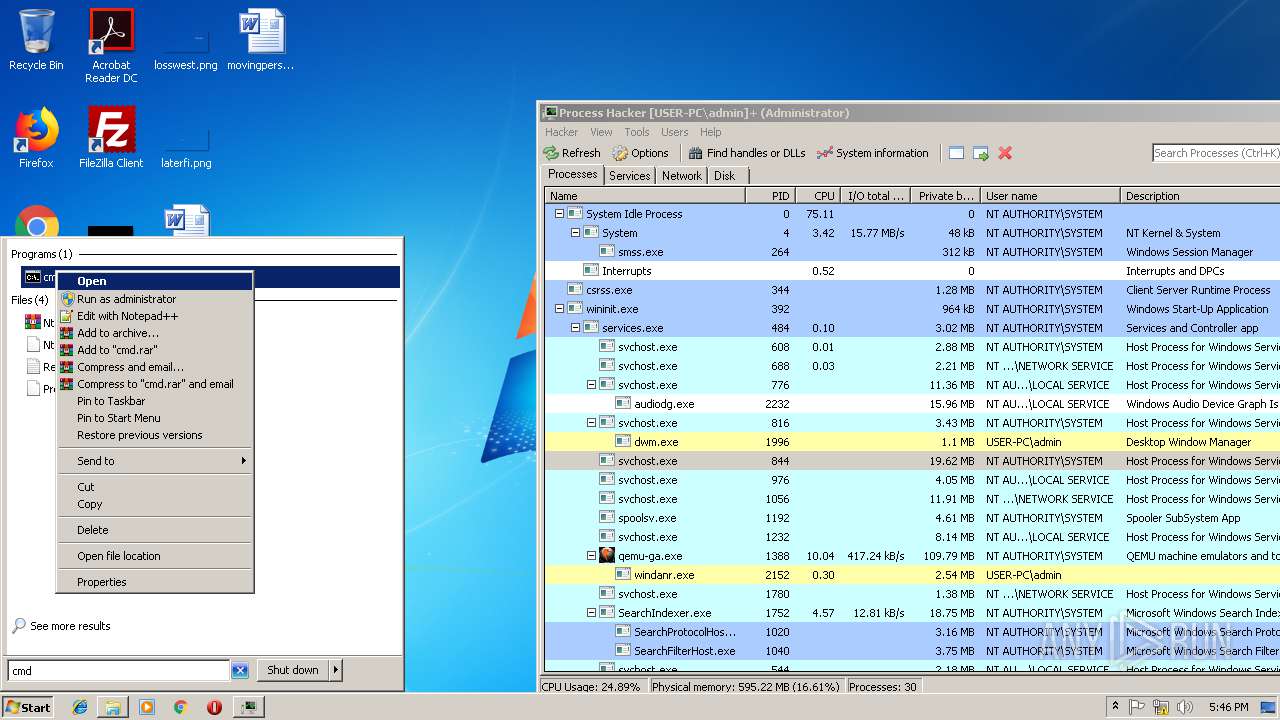
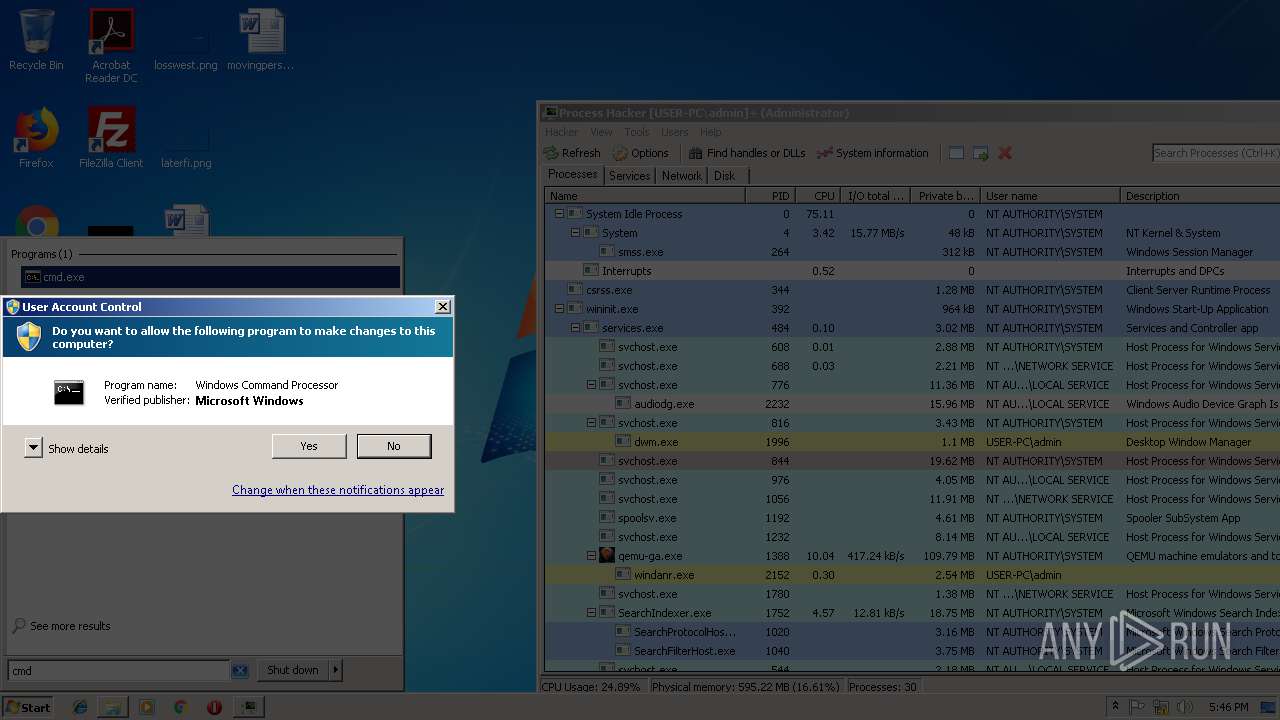
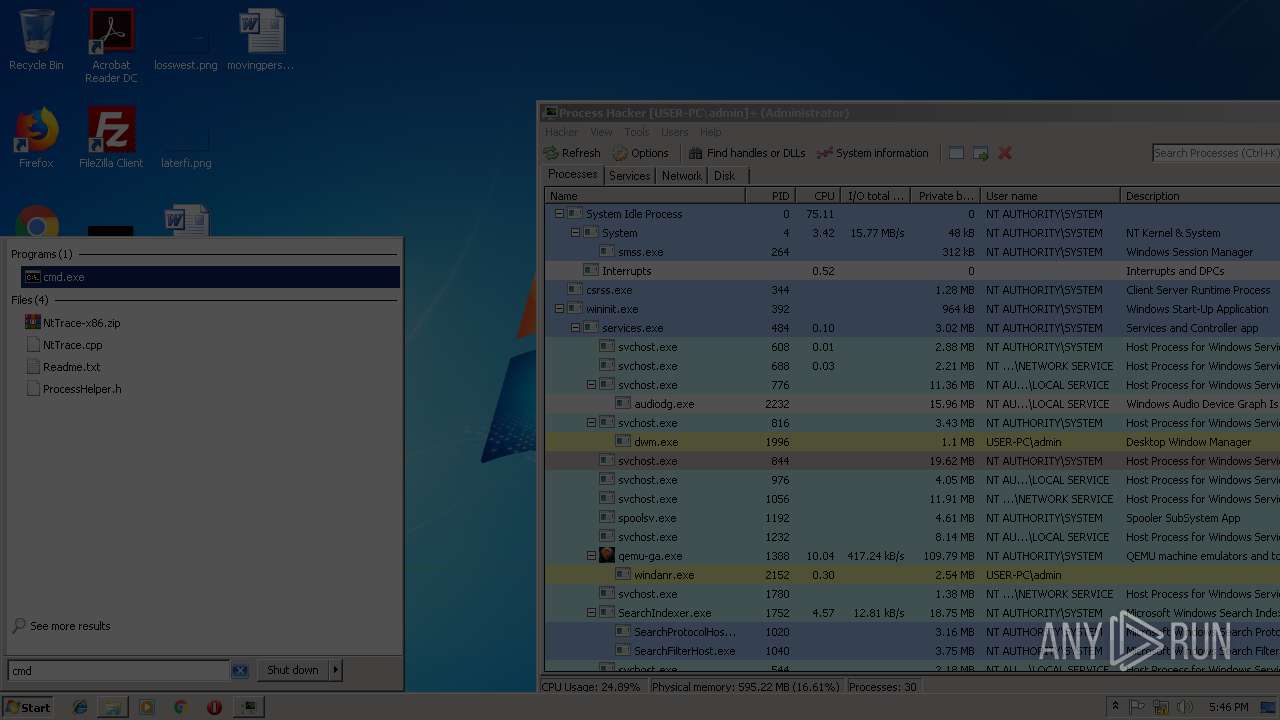
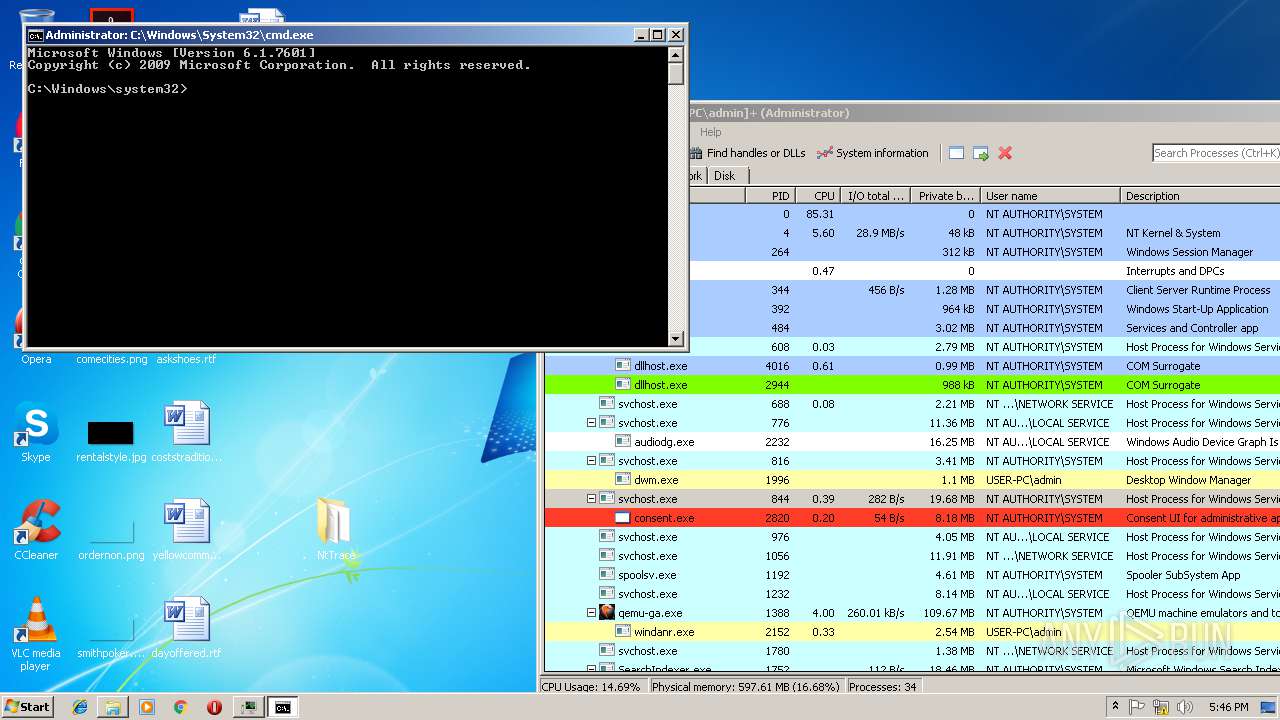
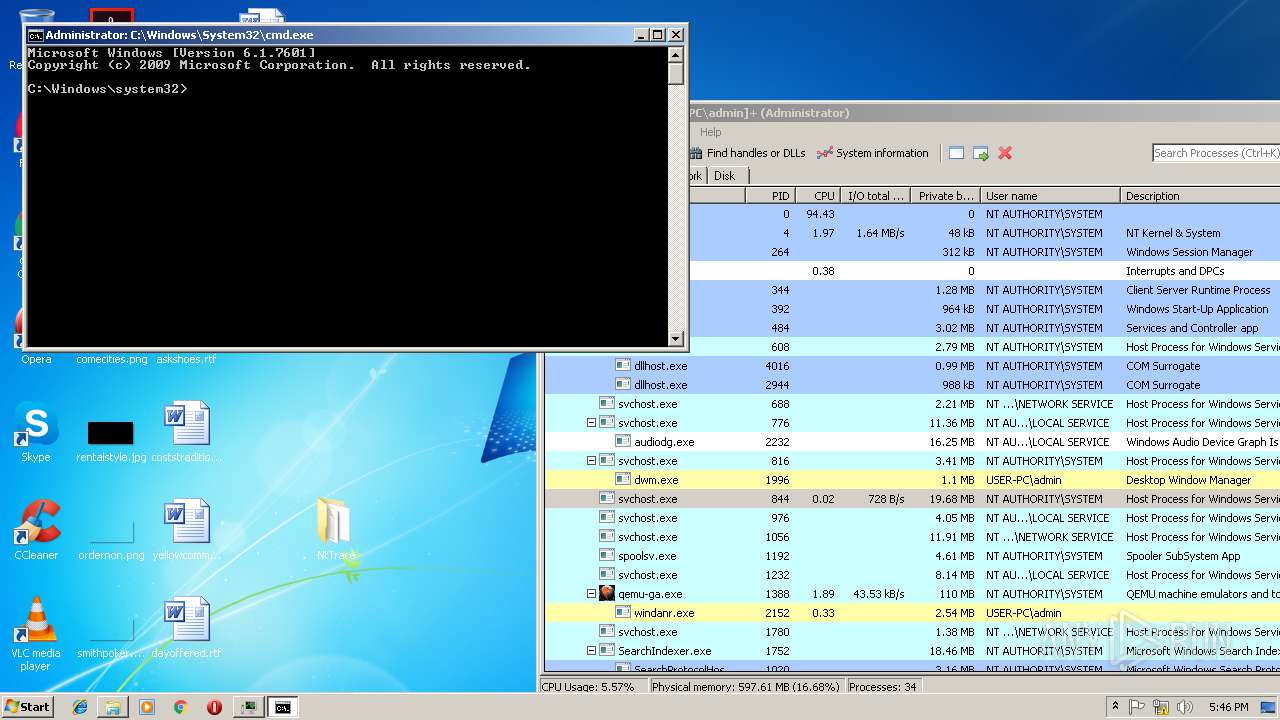
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
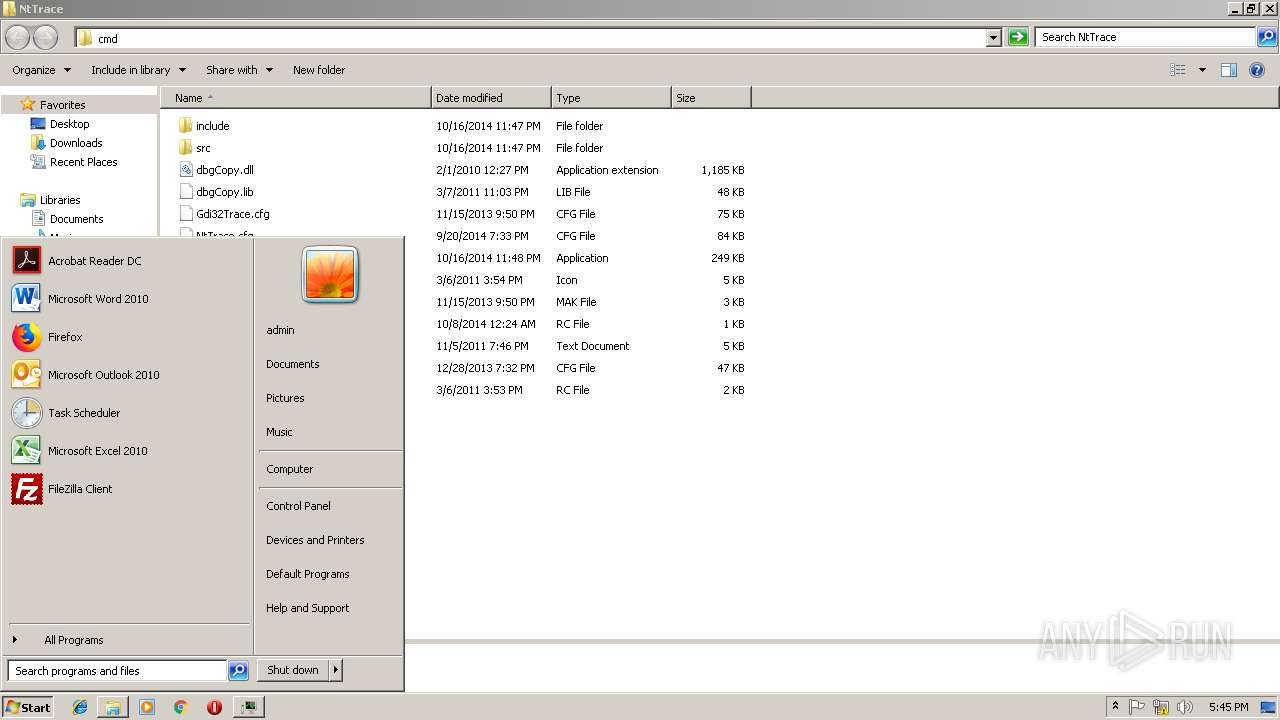
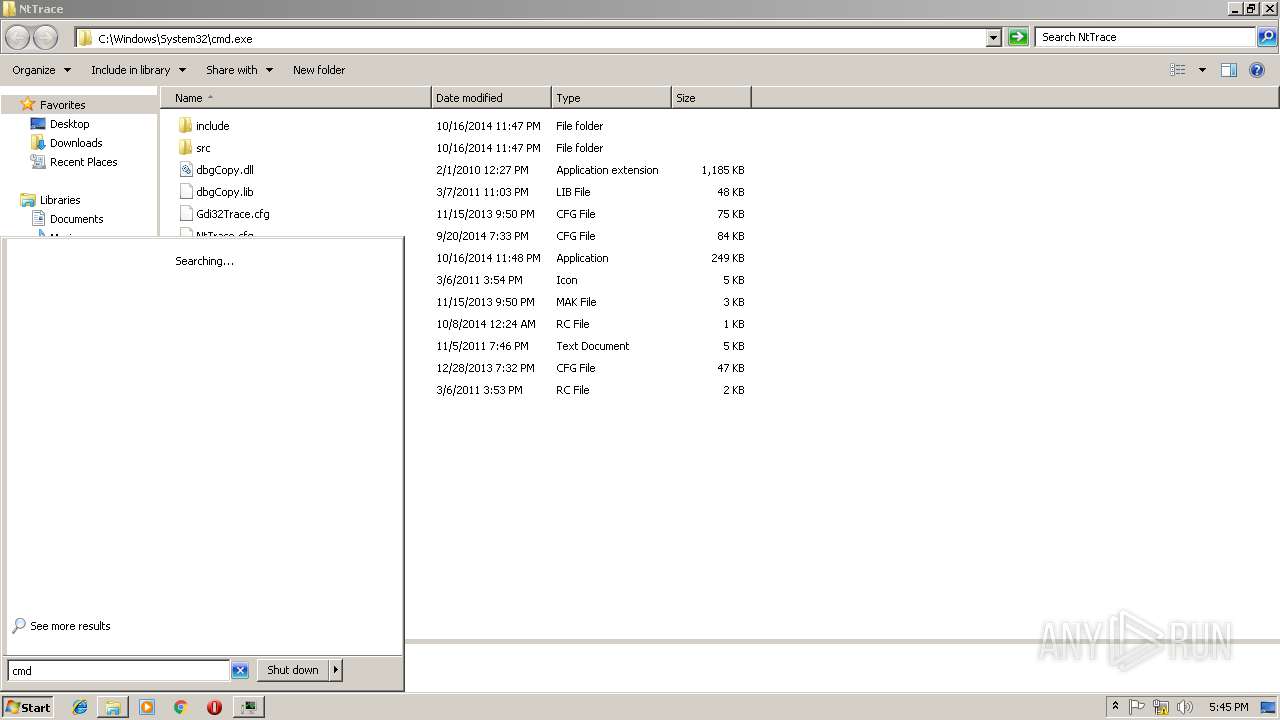
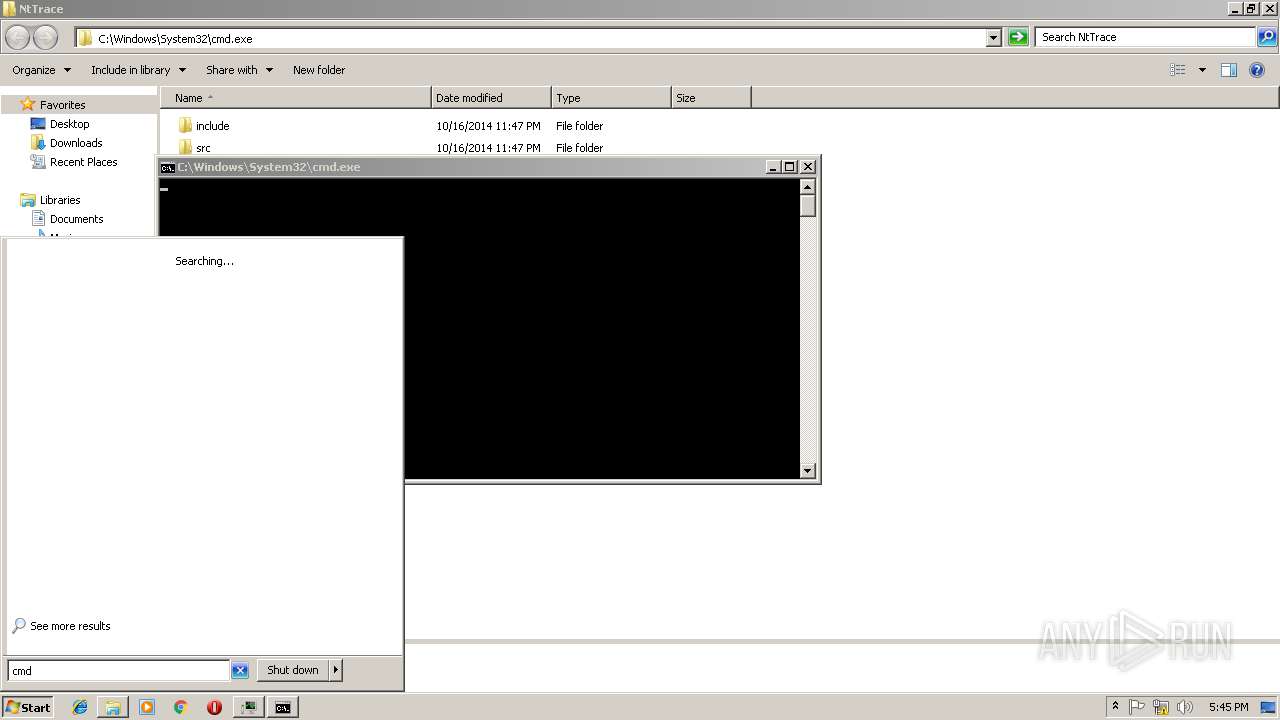
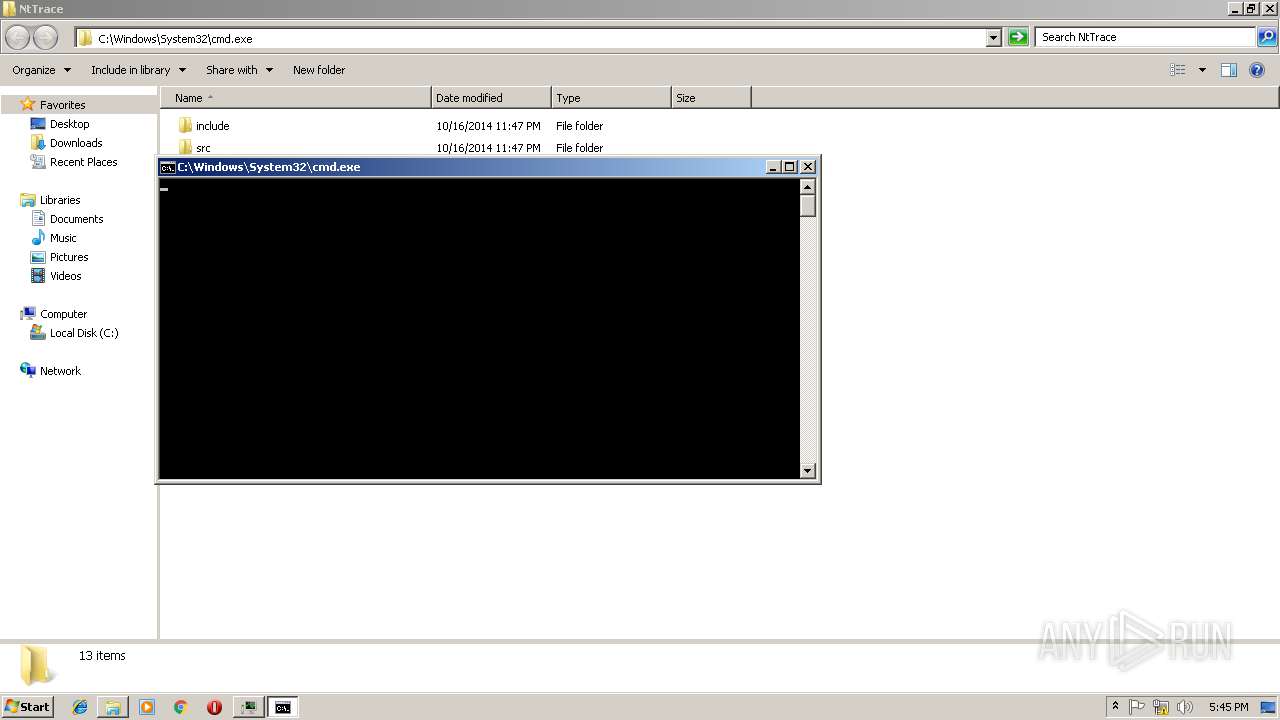
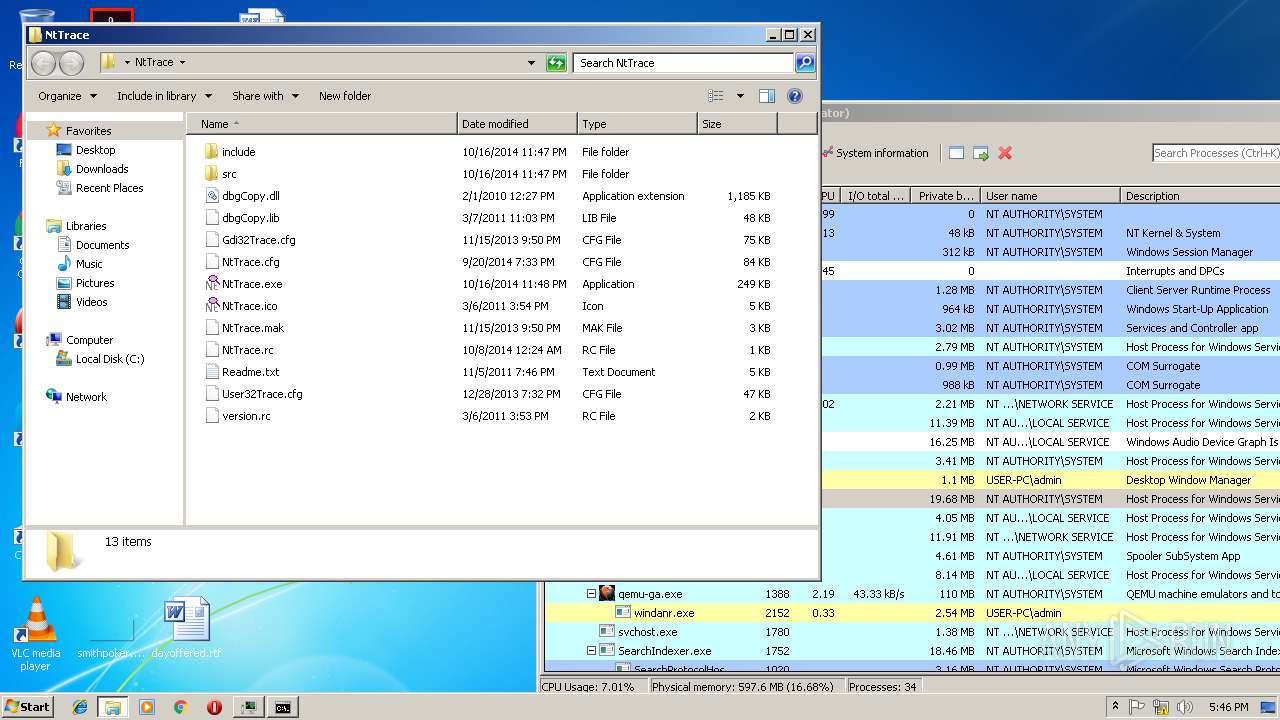
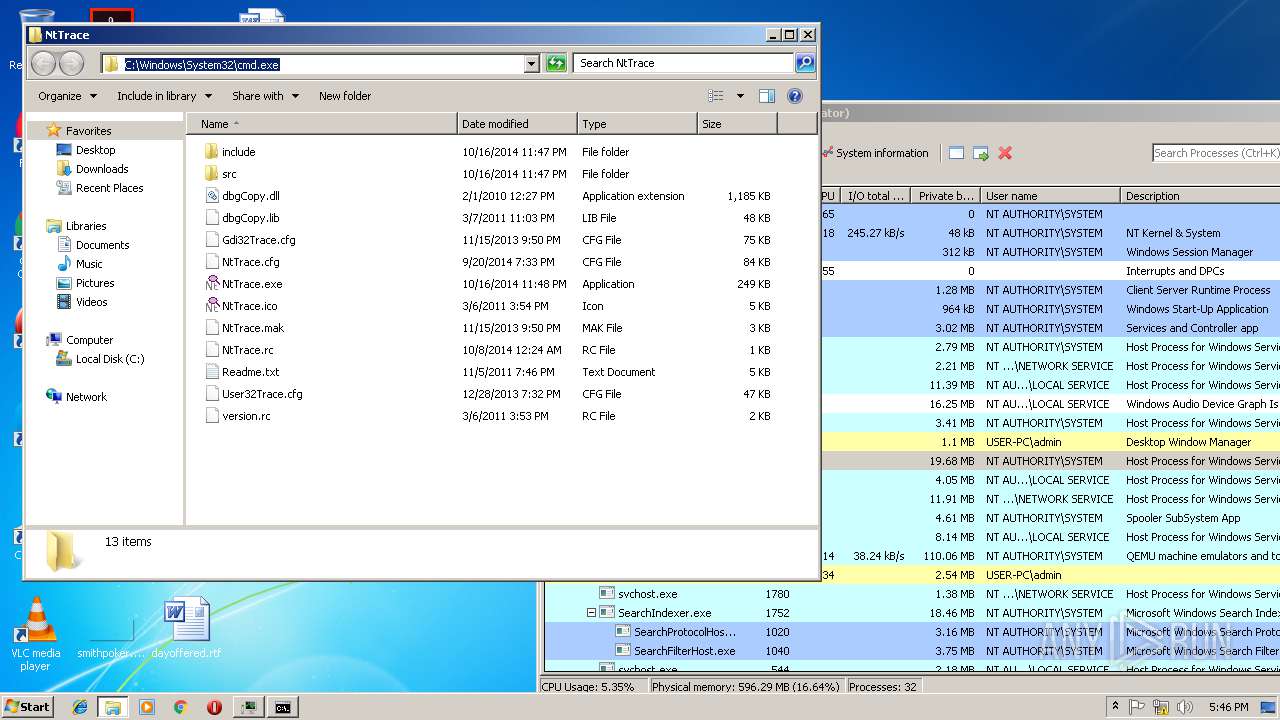
| 256 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6933512963913501986,555698112393458604,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5921CED8E3B1A3315127CF356C182A79 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5921CED8E3B1A3315127CF356C182A79 --renderer-client-id=6 --mojo-platform-channel-handle=3108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1020 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Qemu-ga\qemu-ga.exe" -d | C:\Program Files\Qemu-ga\qemu-ga.exe | services.exe | ||||||||||||
User: SYSTEM Company: http://www.qemu-project.org Integrity Level: SYSTEM Description: QEMU machine emulators and tools Exit code: 0 Version: 2.10.59 Modules
| |||||||||||||||
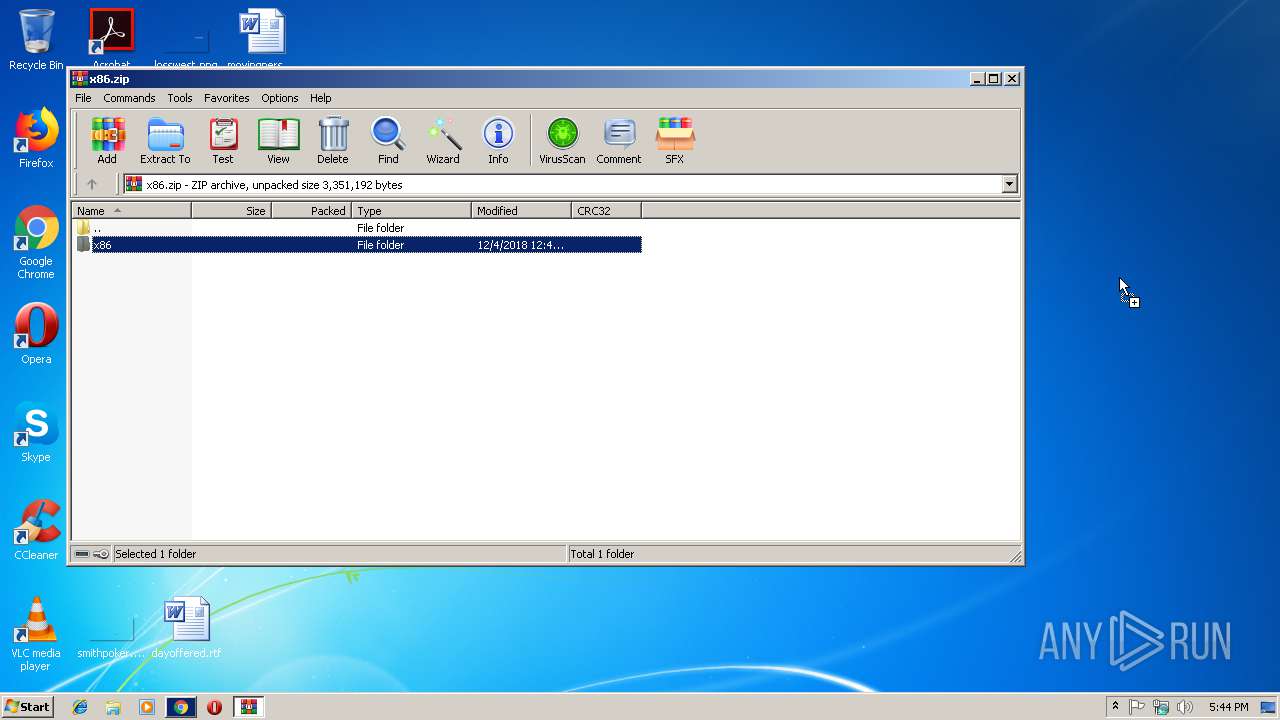
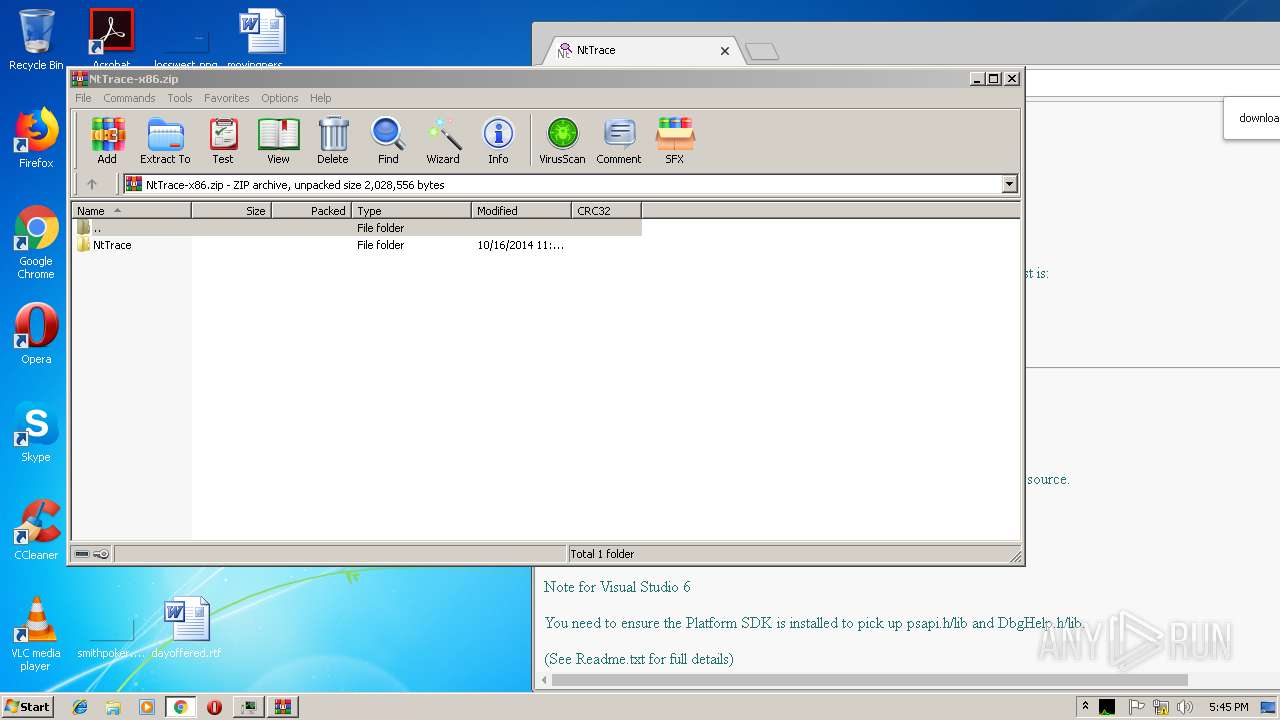
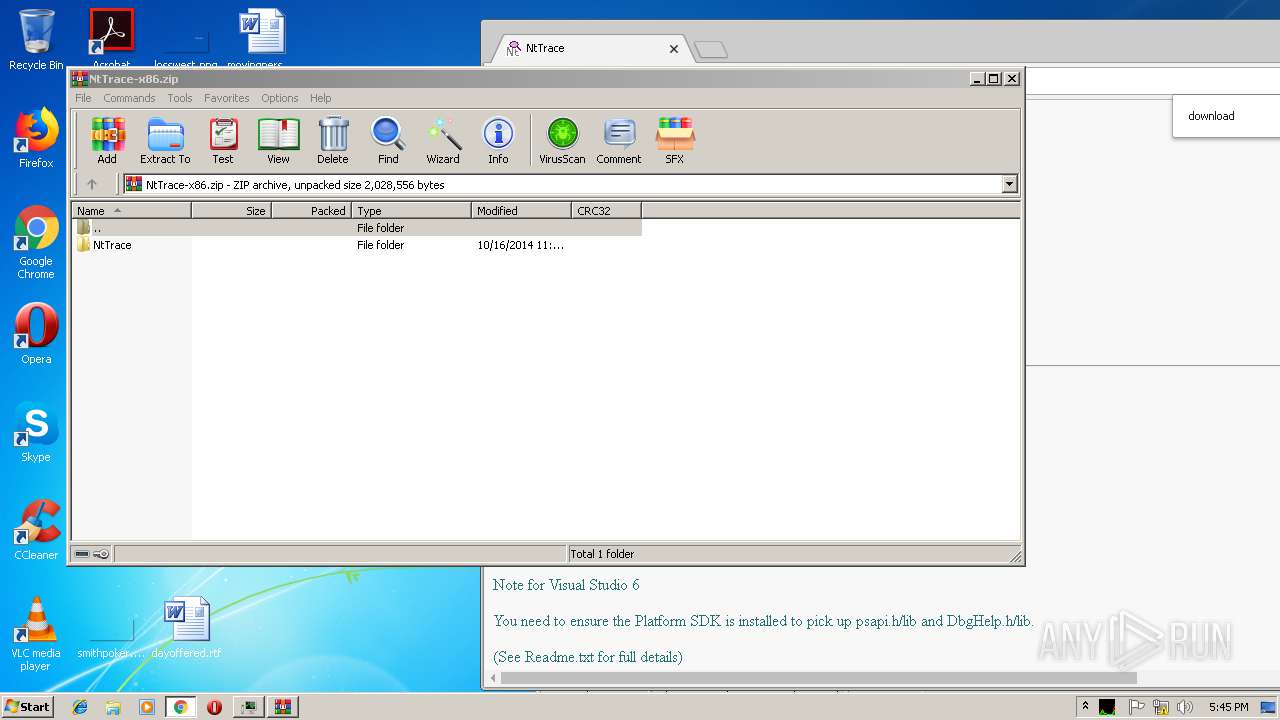
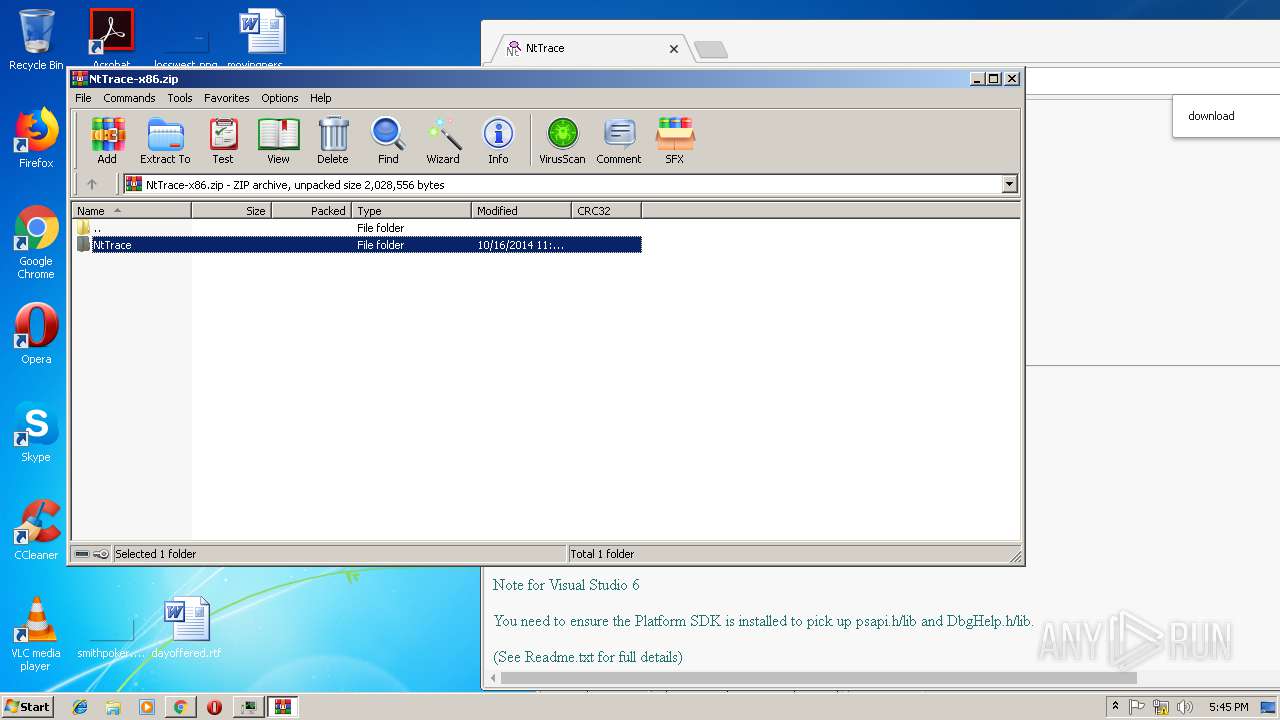
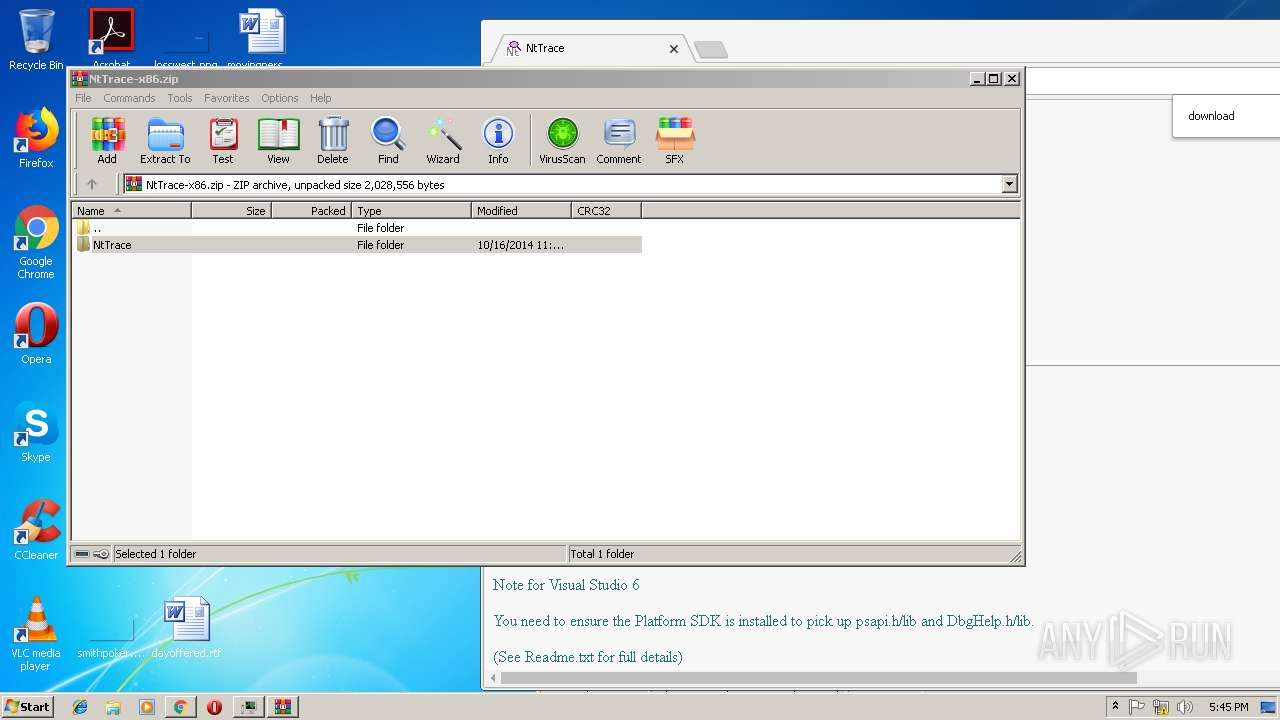
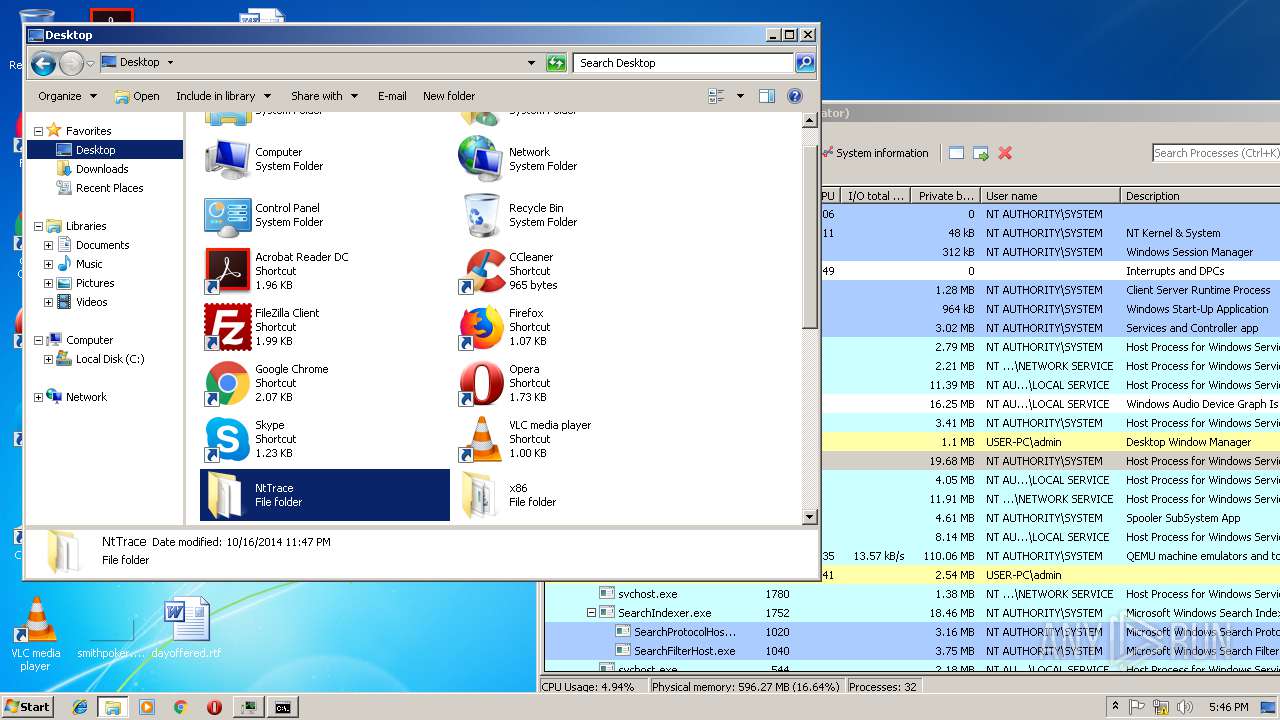
| 2336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\NtTrace-x86.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6933512963913501986,555698112393458604,131072 --enable-features=PasswordImport --service-pipe-token=1154CDBFA95143290D90CE897EE3BC9F --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1154CDBFA95143290D90CE897EE3BC9F --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,6933512963913501986,555698112393458604,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D9C415032CC8B3A1281B8DE4C067CA00 --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2456 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
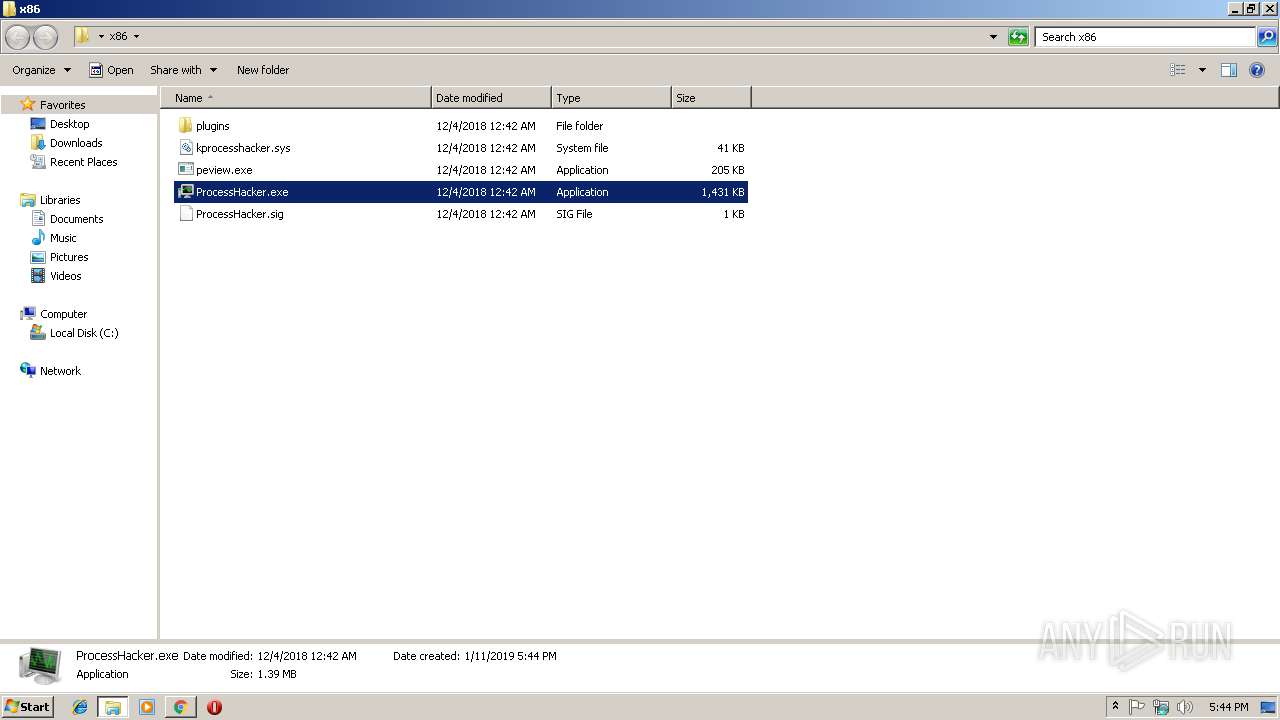
| 2572 | "C:\Users\admin\Desktop\x86\ProcessHacker.exe" | C:\Users\admin\Desktop\x86\ProcessHacker.exe | explorer.exe | ||||||||||||
User: admin Company: wj32 Integrity Level: HIGH Description: Process Hacker Exit code: 0 Version: 2.39.0.124 Modules
| |||||||||||||||
Total events
2 160
Read events
2 048
Write events
109
Delete events
3
Modification events
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\x86.zip | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2816) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
14
Suspicious files
84
Text files
109
Unknown types
11
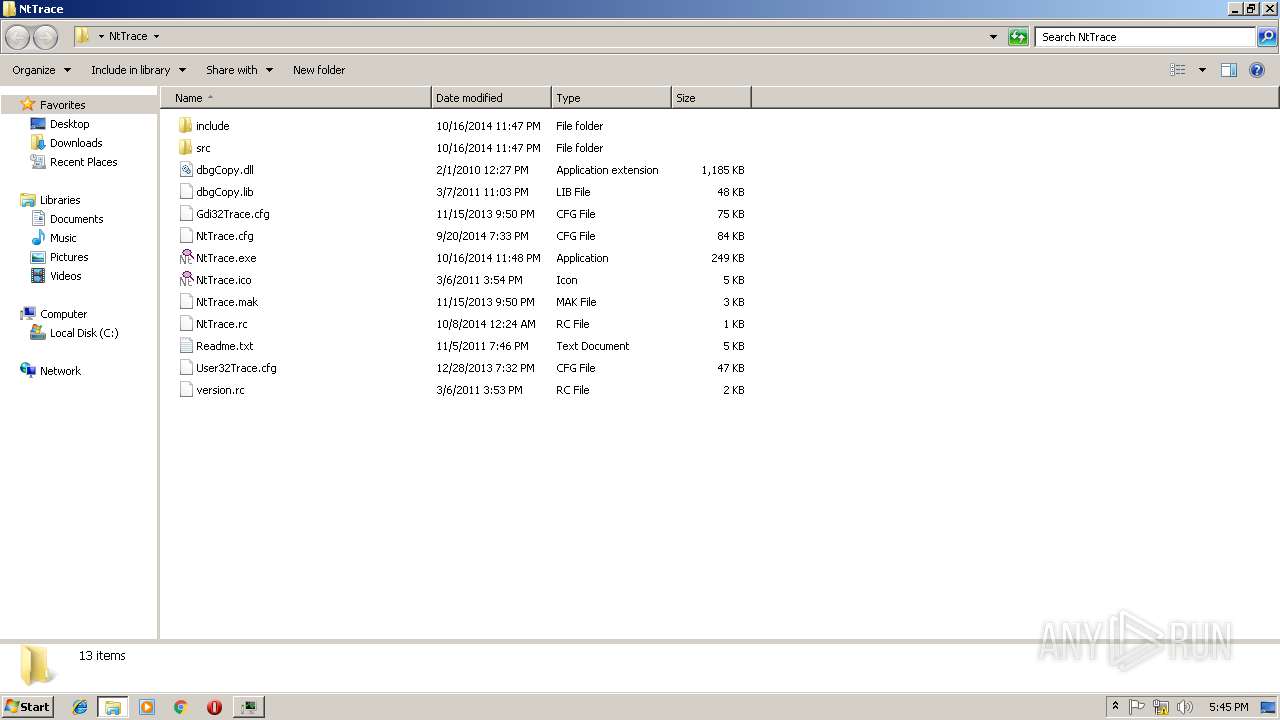
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e3a236a4-e9cd-4f5f-94b7-a196dd8879b8.tmp | — | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF19c50b.TMP | text | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF19c49e.TMP | text | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF19c51b.TMP | text | |
MD5:— | SHA256:— | |||
| 2452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:9543068B6751E1F3E11F91D72EE78D95 | SHA256:D060AD21AE6E04CB58668CAA52ADFCA573E018102CC07554D2ED3EAE11AB7785 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
37
DNS requests
26
Threats
0
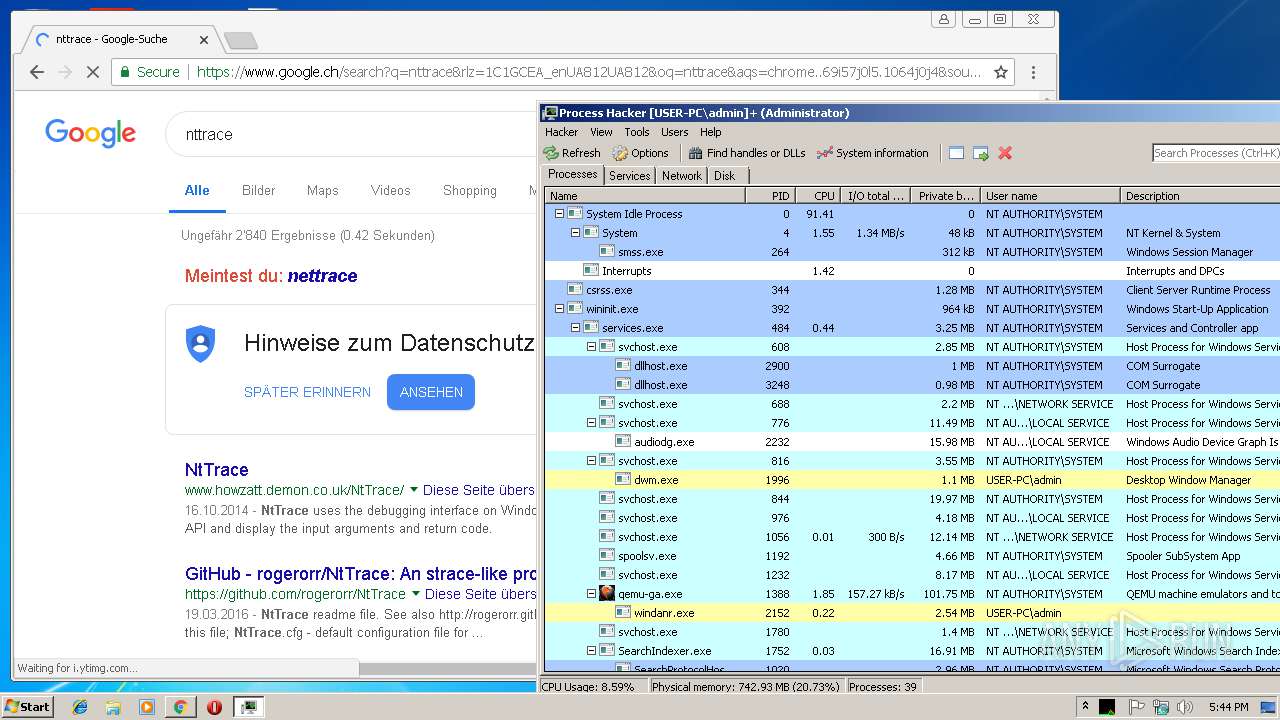
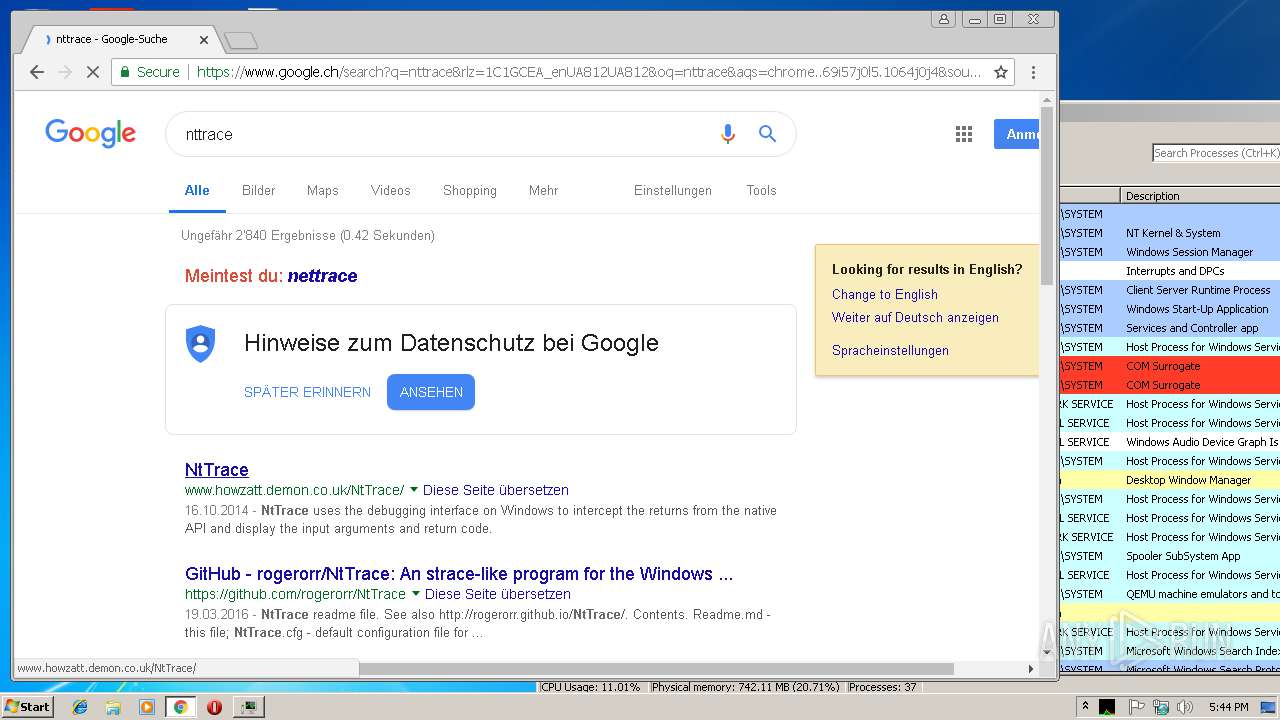
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
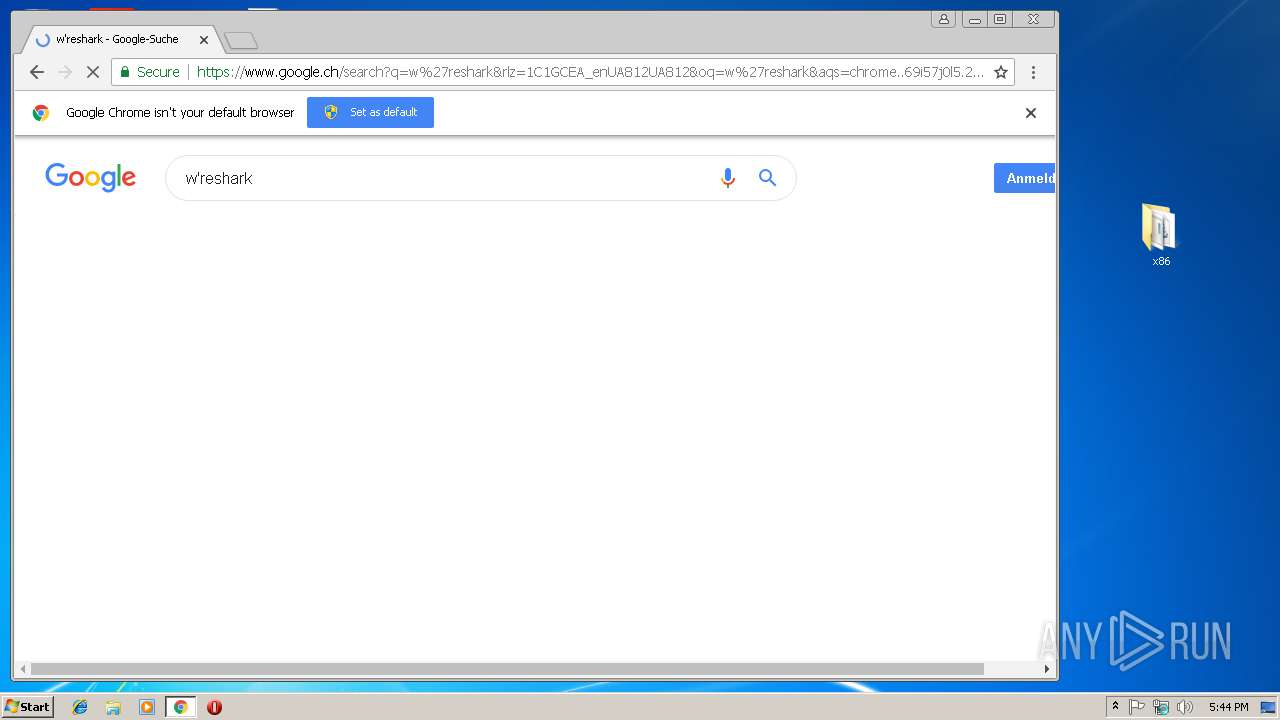
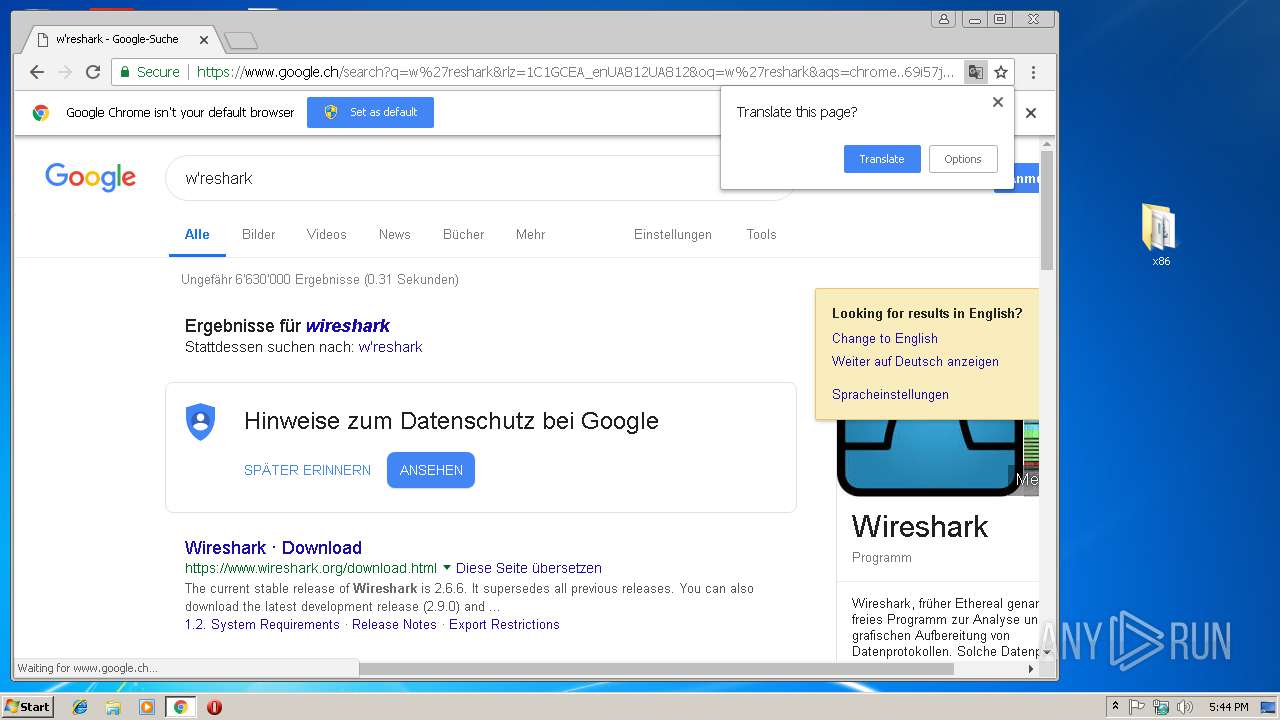
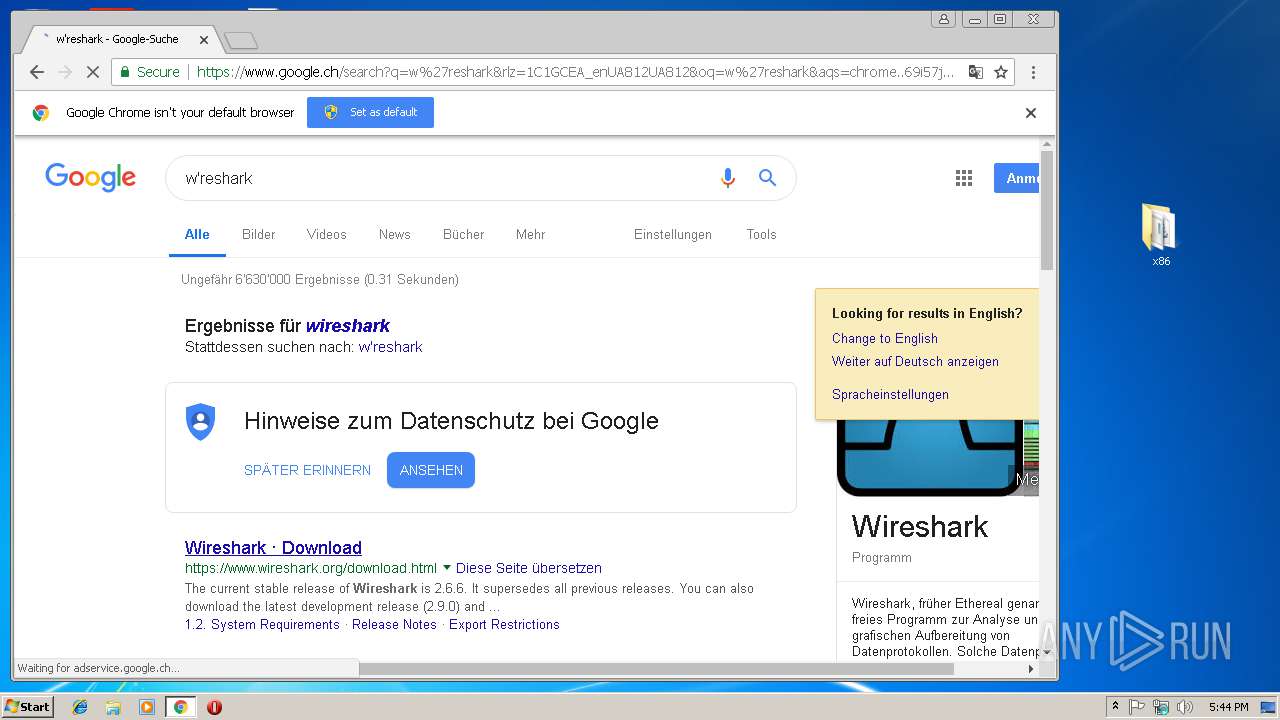
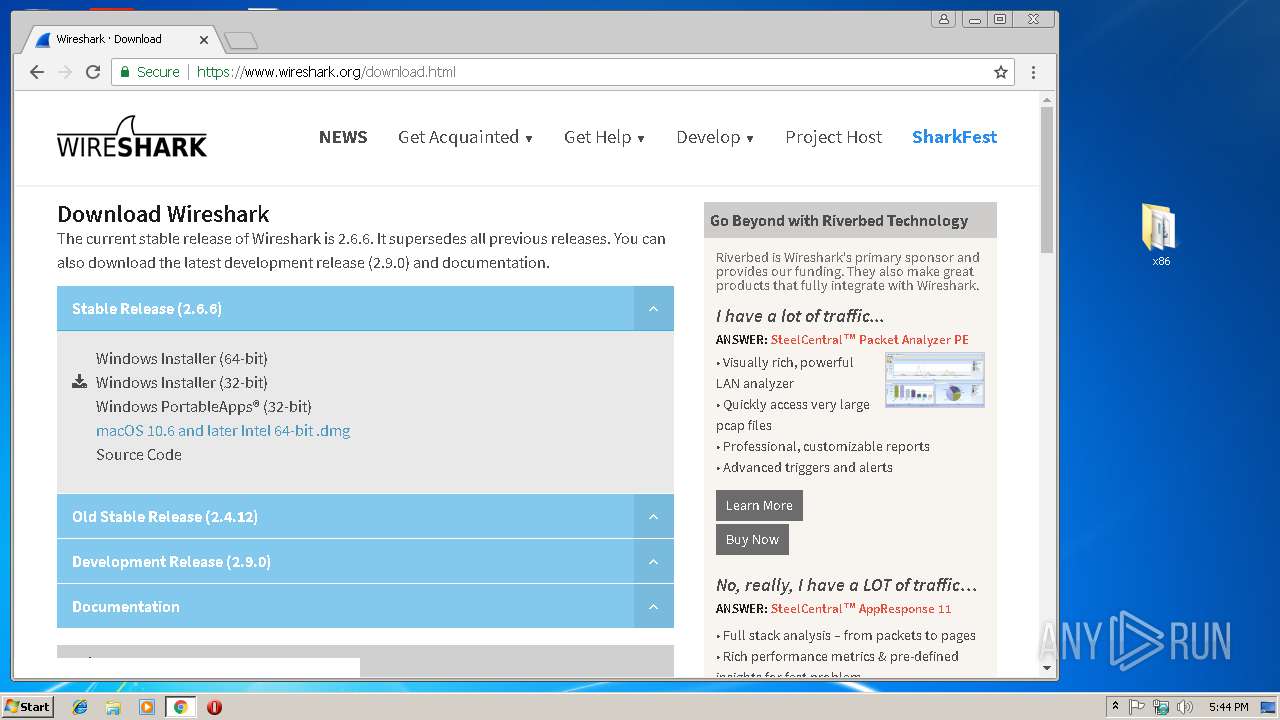
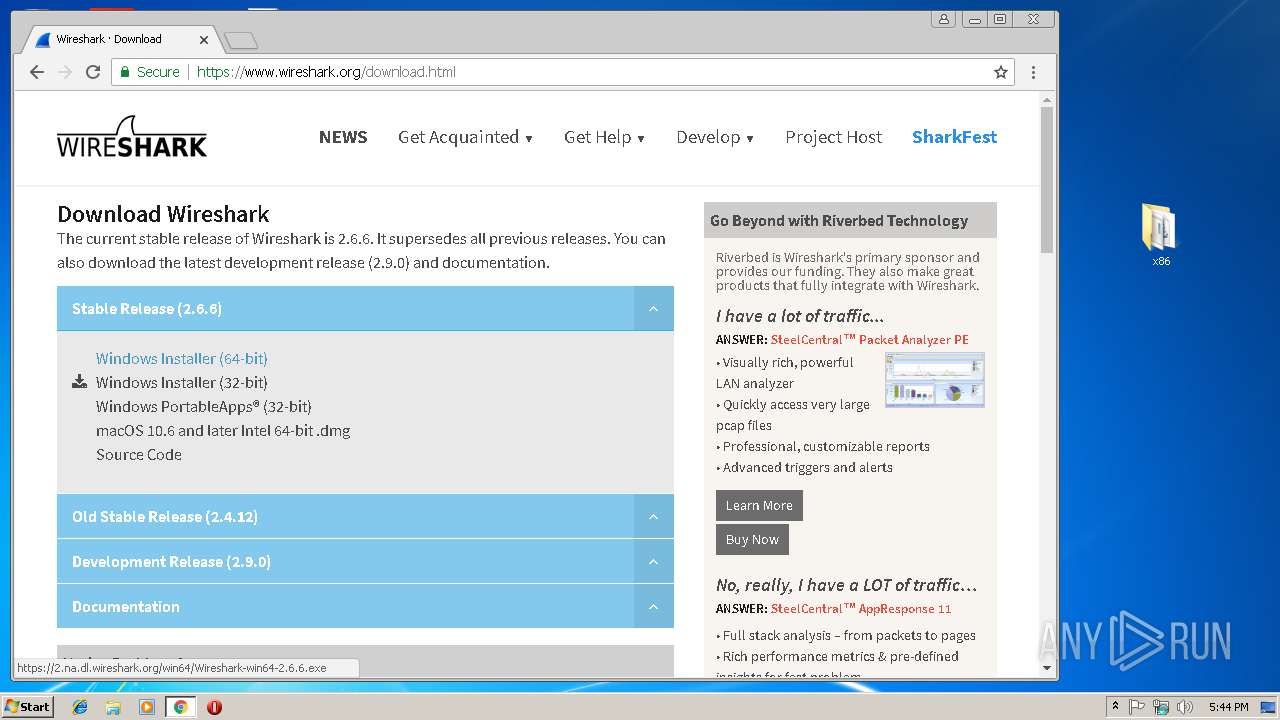
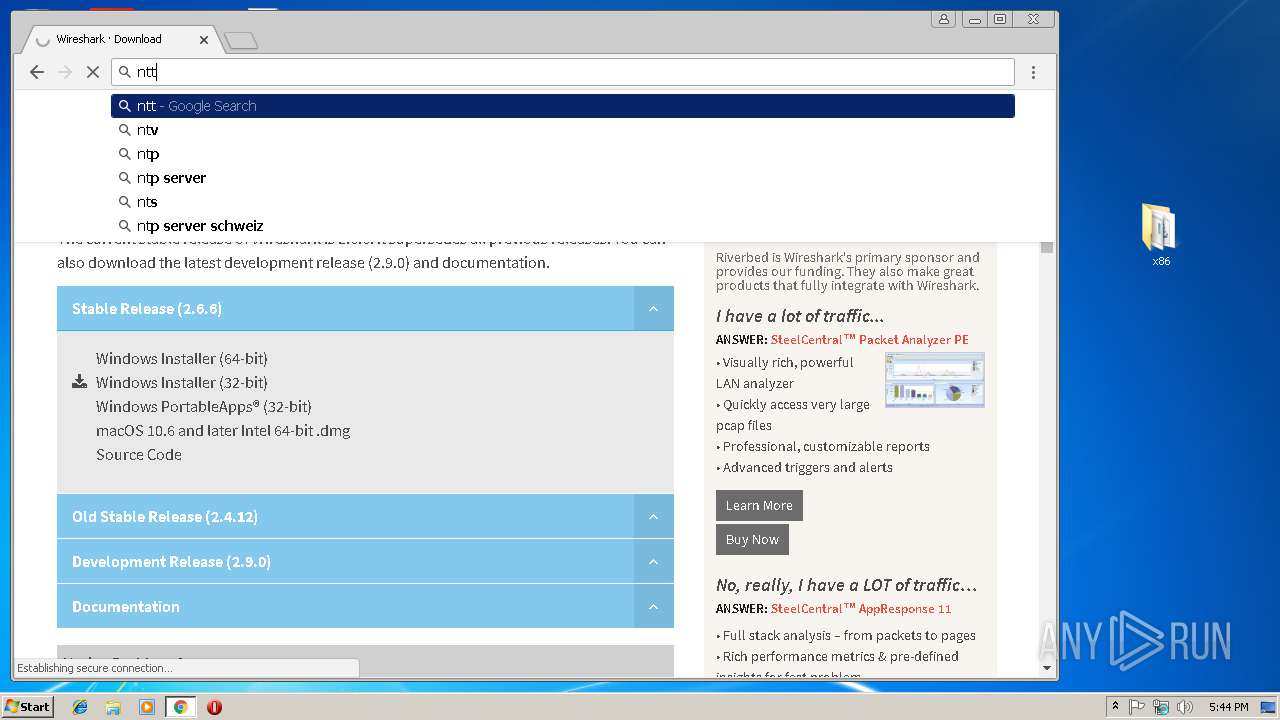
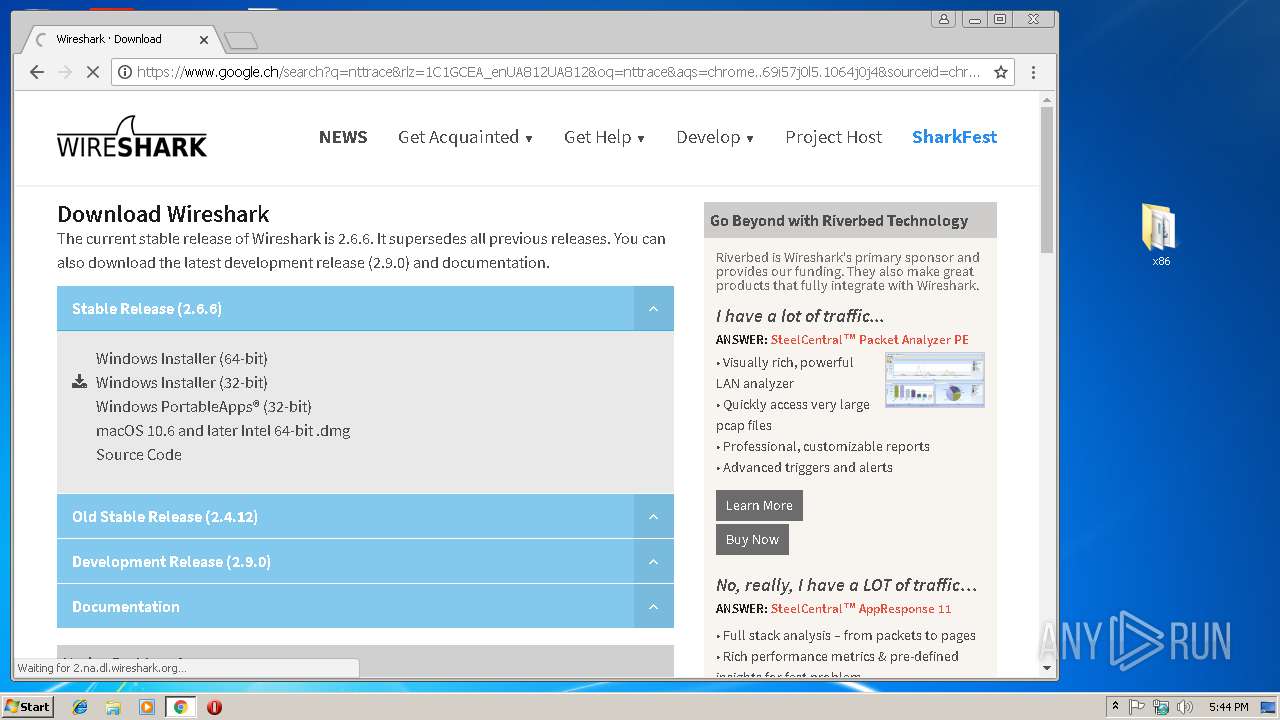
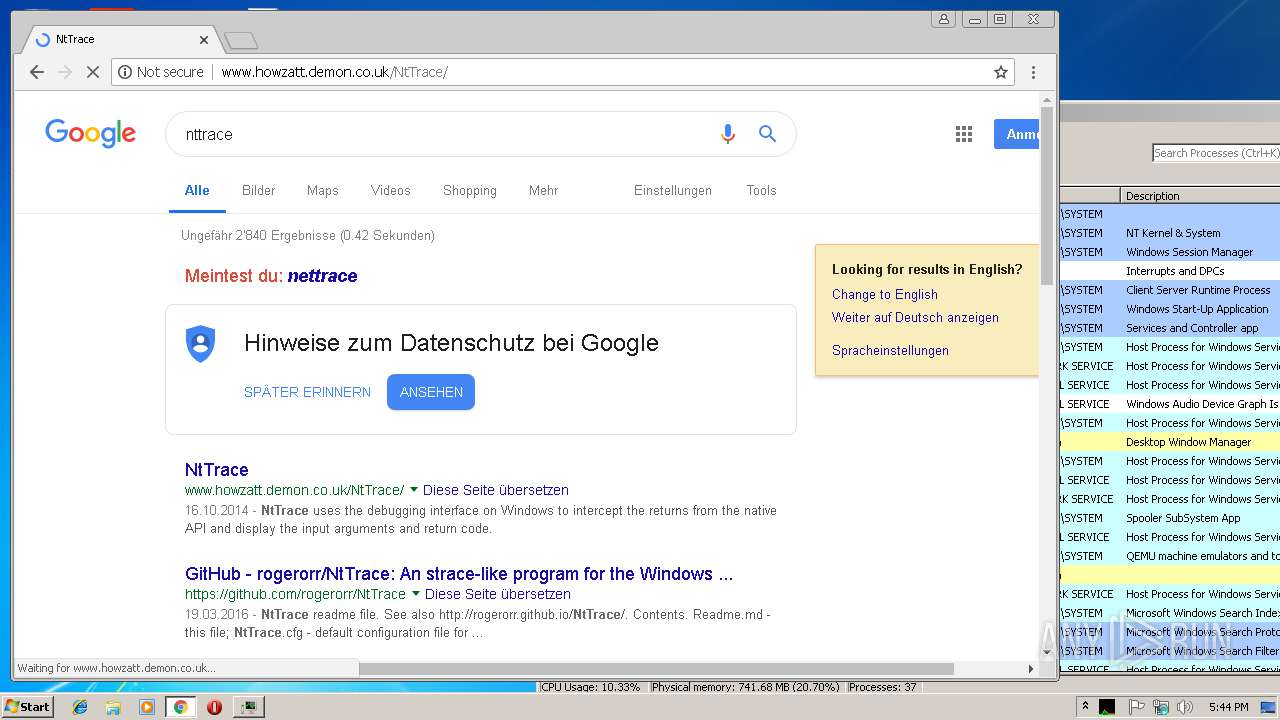
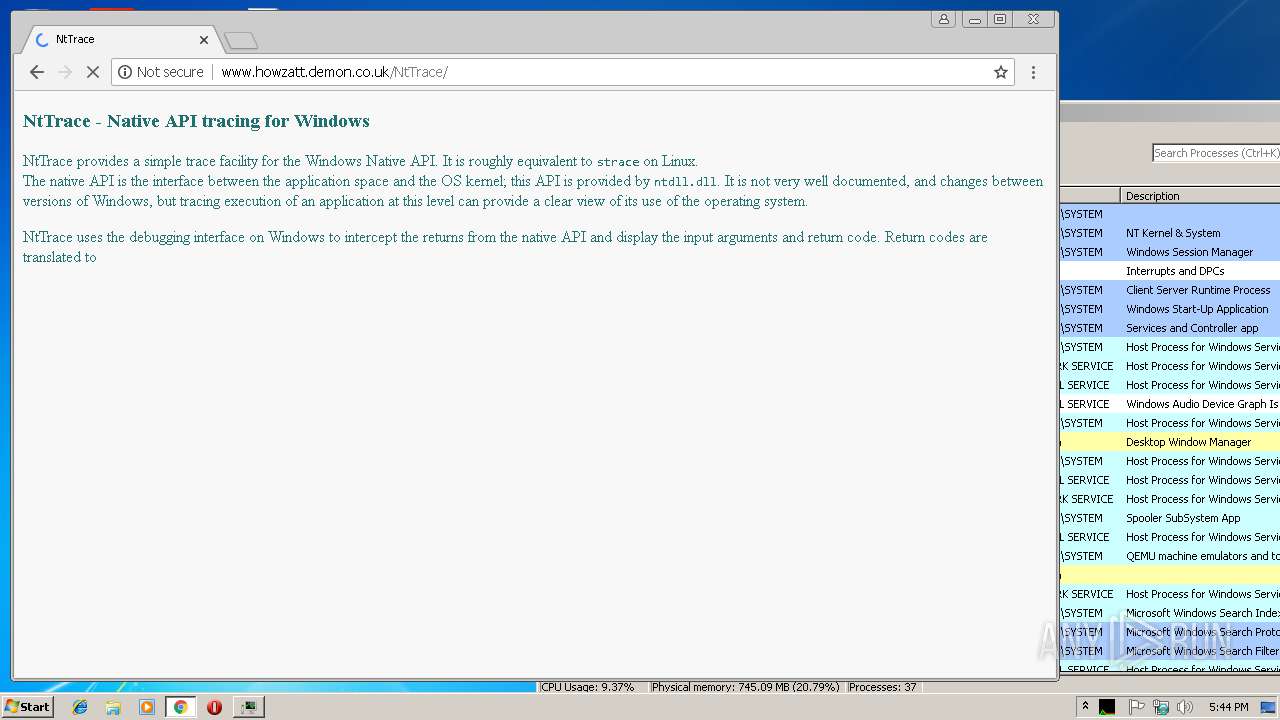
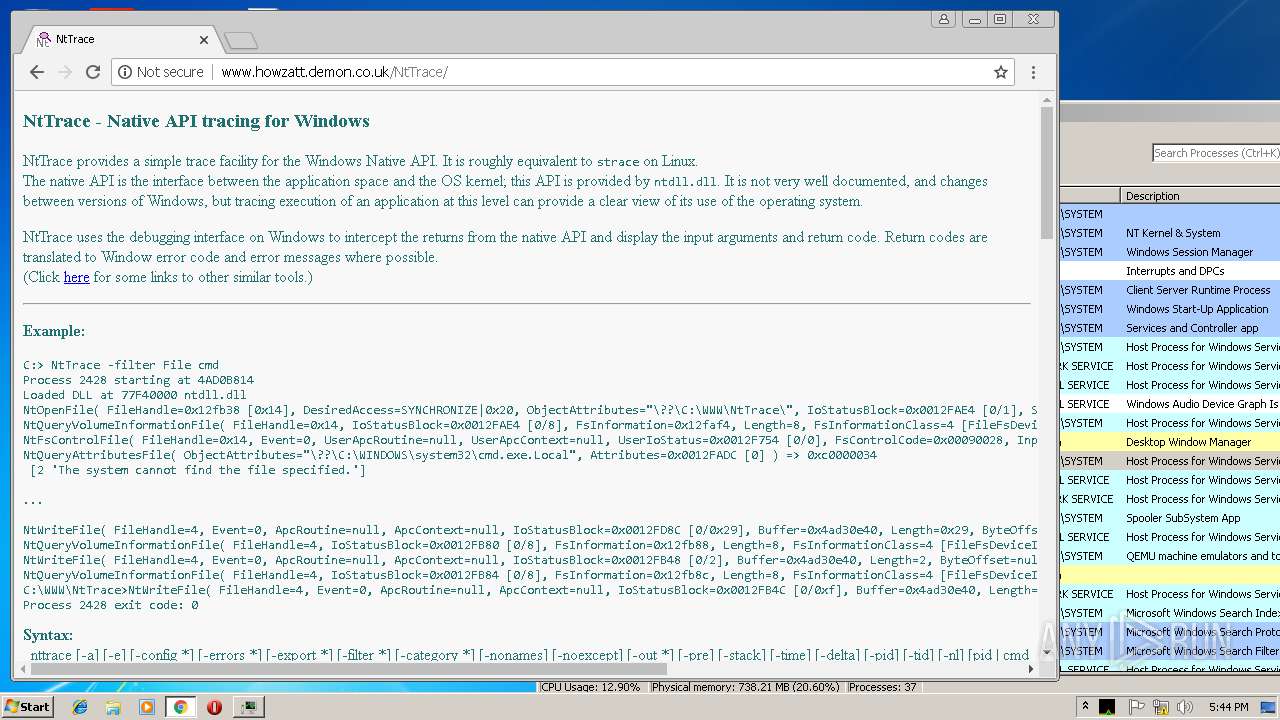
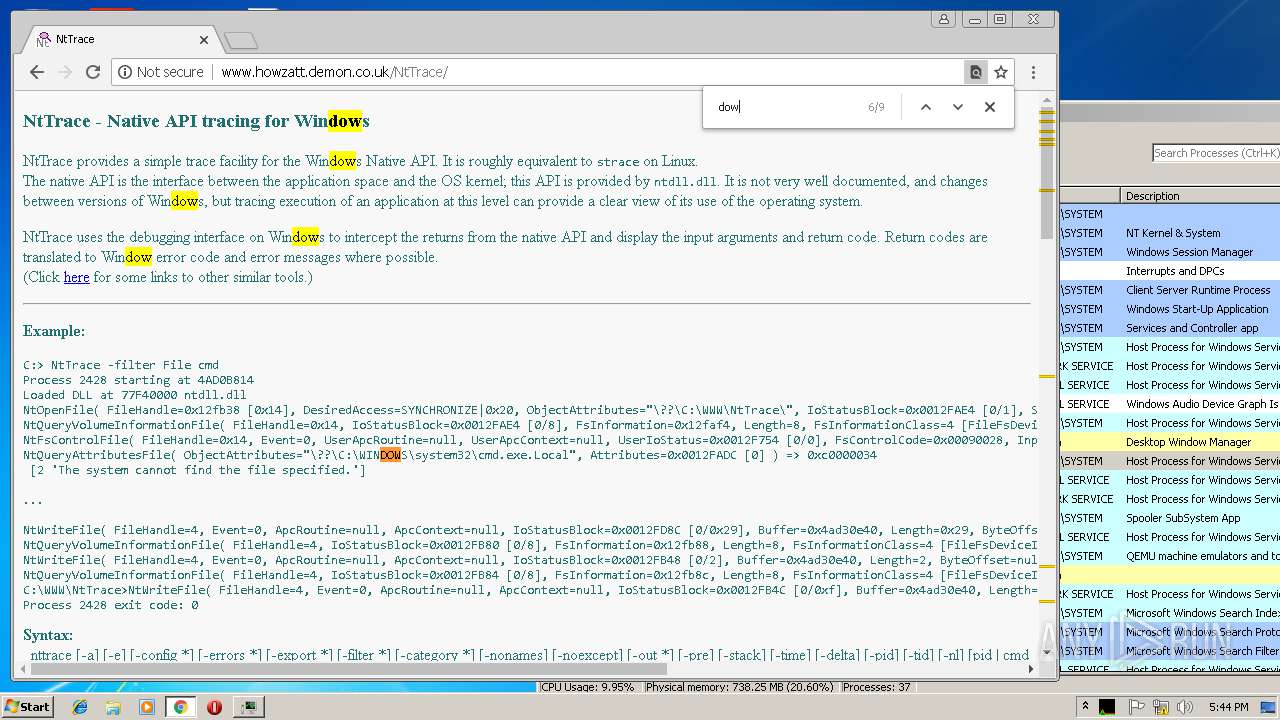
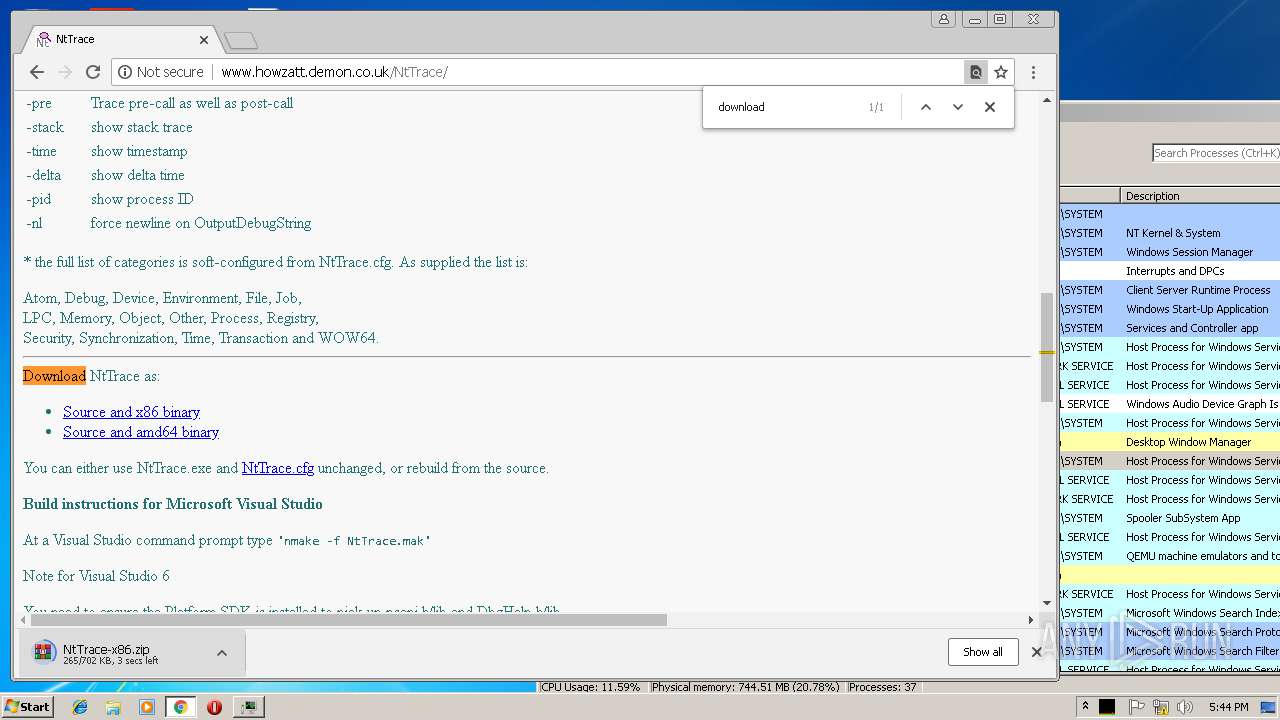
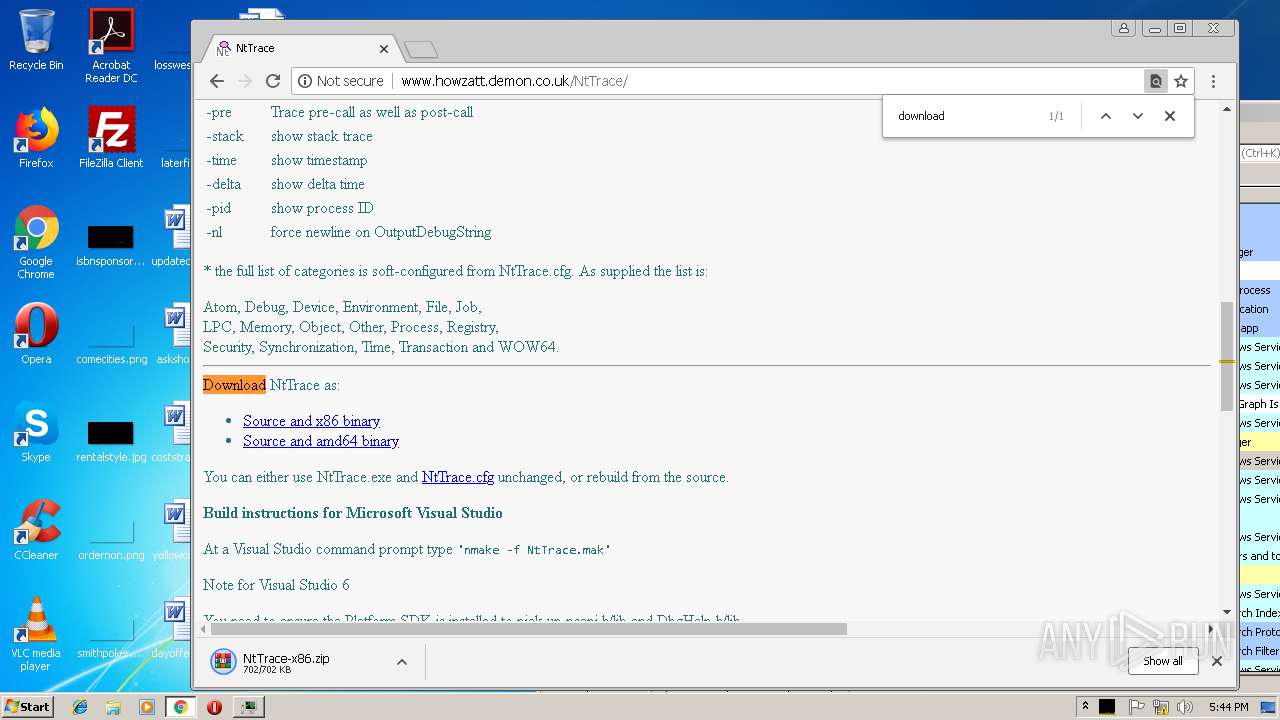
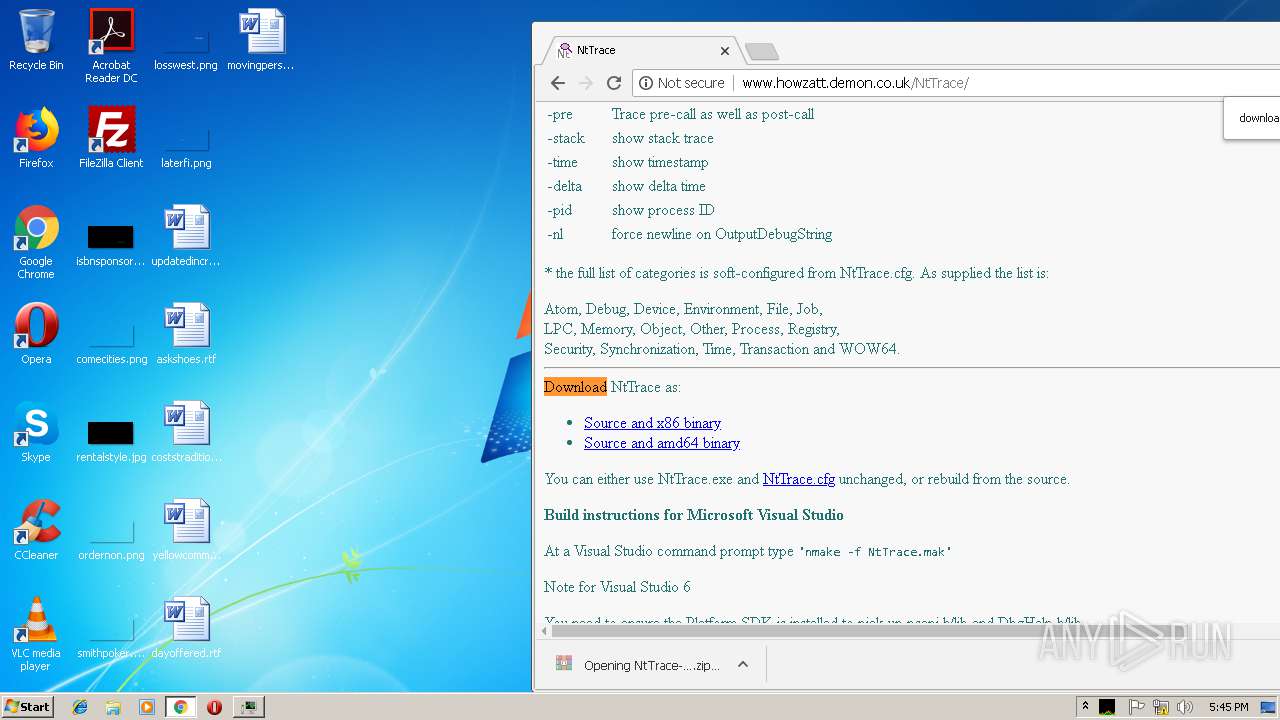
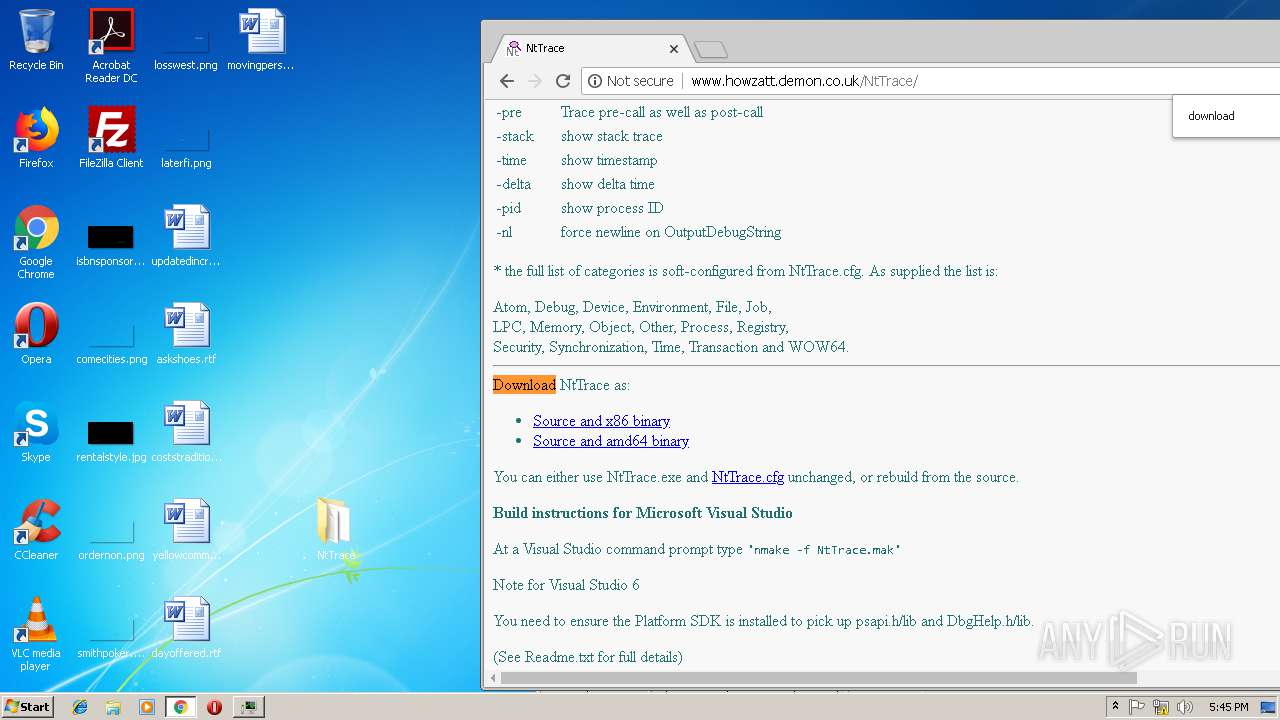
2452 | chrome.exe | GET | 200 | 85.233.160.129:80 | http://www.howzatt.demon.co.uk/NtTrace/ | GB | html | 3.14 Kb | suspicious |
2452 | chrome.exe | GET | 200 | 85.233.160.129:80 | http://www.howzatt.demon.co.uk/NtTrace/NtTrace.ico | GB | image | 4.73 Kb | suspicious |
2452 | chrome.exe | GET | 200 | 85.233.160.129:80 | http://www.howzatt.demon.co.uk/or2.css | GB | text | 95 b | suspicious |
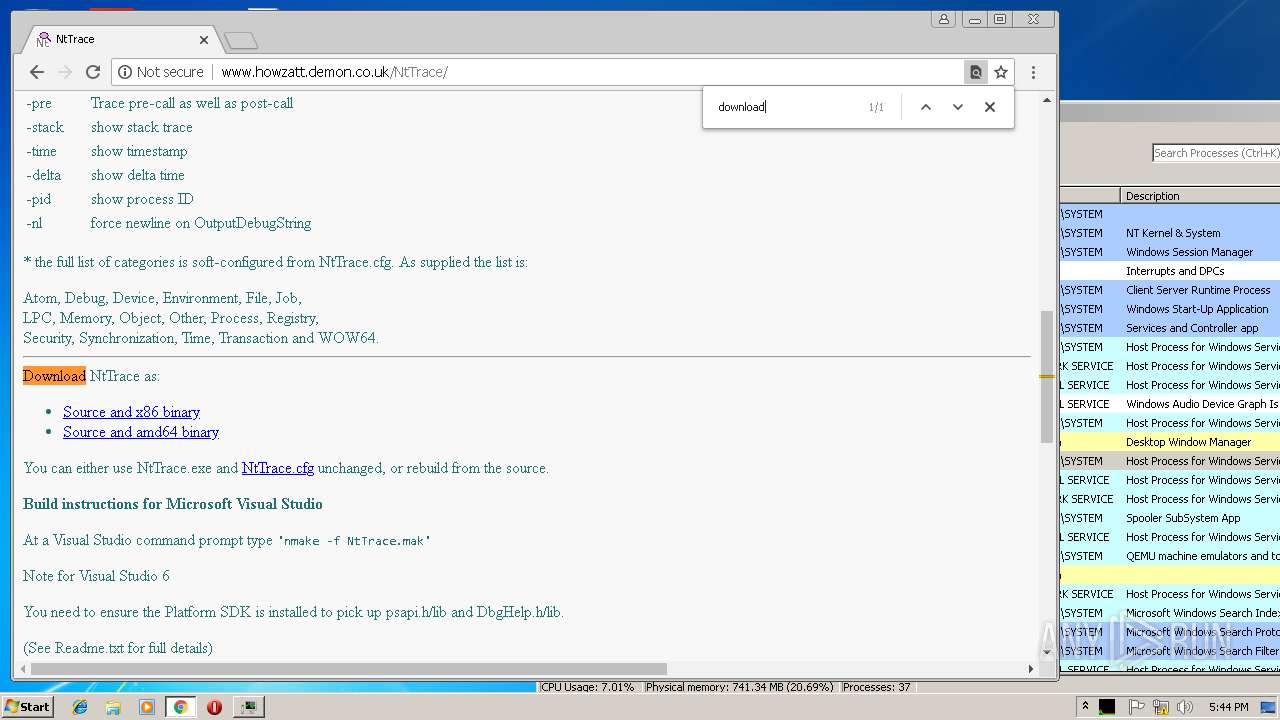
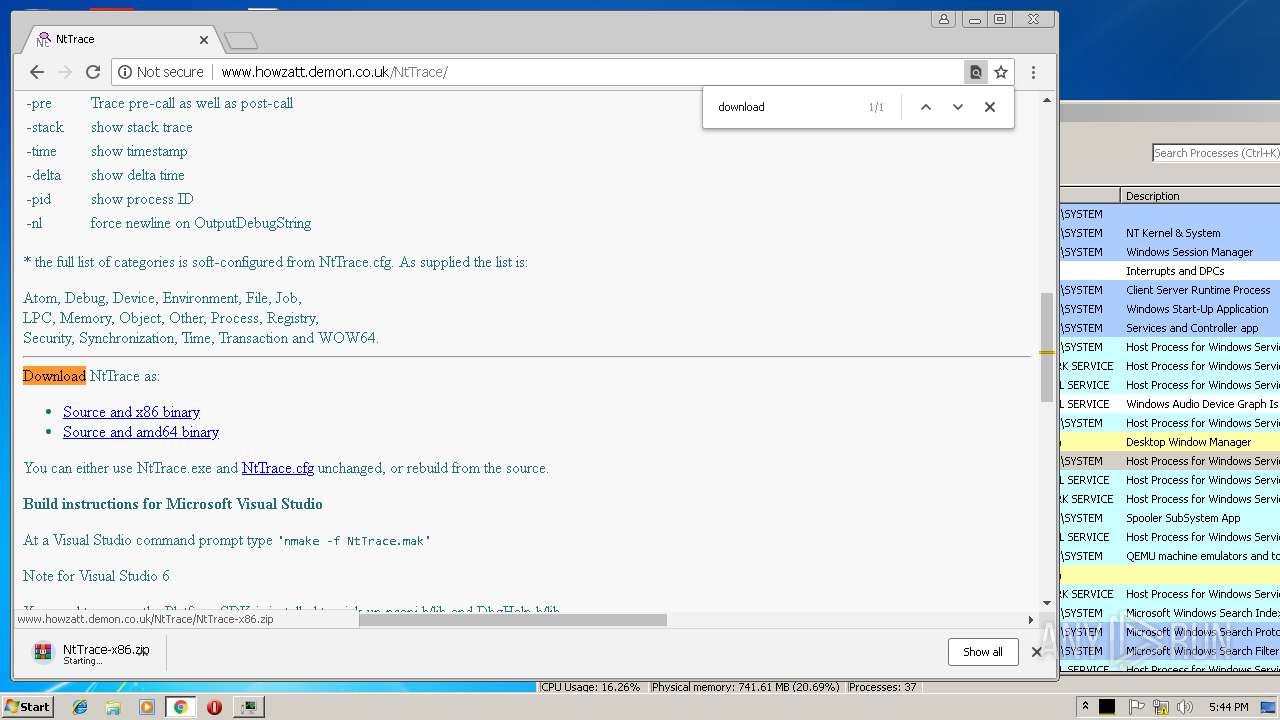
2452 | chrome.exe | GET | 200 | 85.233.160.129:80 | http://www.howzatt.demon.co.uk/NtTrace/NtTrace-x86.zip | GB | compressed | 702 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | chrome.exe | 216.58.208.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.22.3:443 | www.google.de | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 216.58.208.46:443 | consent.google.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.16.194:443 | adservice.google.ch | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |