| download: | mlb.html |
| Full analysis: | https://app.any.run/tasks/5800bb06-e62c-4202-818f-c00959666a73 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2018, 10:54:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 7A5124E84779758A1238602B796B8FAA |
| SHA1: | D9E7F26B9DCACCF32149406734514B79BE92343D |
| SHA256: | E6F30B733374BABF3B563C63024D4860DB5120B774AA8CA6486C722DB547CF2F |
| SSDEEP: | 768:gdf2OceVUDDkGWjT5N5p/3Dljazndf028/9Yi1ktkwJsO/Er3LxOb03LdRTvjPTk:g12OceVUDDkzyW2HkpOkt20hYWK |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
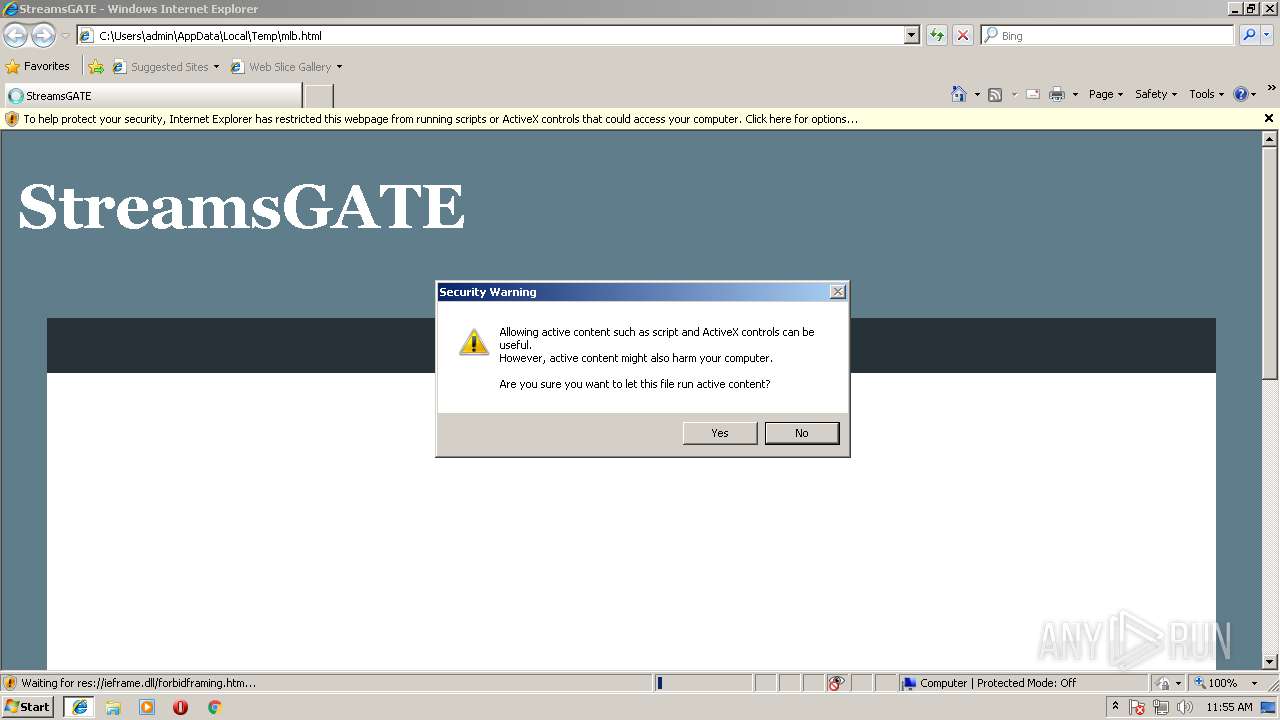
Application launched itself
- iexplore.exe (PID: 372)
Creates files in the user directory
- iexplore.exe (PID: 2580)
Dropped object may contain URL's
- iexplore.exe (PID: 2580)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2580)
Changes internet zones settings
- iexplore.exe (PID: 372)
Changes settings of System certificates
- iexplore.exe (PID: 2580)
Reads internet explorer settings
- iexplore.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml/atom | | | Atom web feed (92.2) |
|---|---|---|
| .html | | | HyperText Markup Language (7.7) |
EXIF
HTML
| viewport: | width=device-width, initial-scale=1 |
|---|---|
| Title: | StreamsGATE |
| exoclickSiteVerification: | 4fef71bb655d59ec58ada611e4b111c0 |
| googleSiteVerification: | V6BFTEJJ5kLVRBHjQXBxDcV_7VuHgmUtXDj9WRB16G4 |
| ContentType: | text/html; charset=UTF-8 |
| themeColor: | #607d8b |
| msapplicationNavbuttonColor: | #607d8b |
| Generator: | blogger |
Total processes
33
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\mlb.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:372 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
365
Read events
290
Write events
71
Delete events
4
Modification events
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070700030019000A0036003900CB01 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000047000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (372) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {2AAC829F-8FF9-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
11
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\XB3OCR2W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 372 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\authorization[1].css | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab821F.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar8220.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab8231.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar8232.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab8290.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar8291.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\NBLQPZGH\authorization[1].css | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
27
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | iexplore.exe | GET | 200 | 52.56.118.143:80 | http://52.56.118.143/mlbgames | GB | html | 114 b | unknown |
2580 | iexplore.exe | GET | 304 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
372 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2580 | iexplore.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | iexplore.exe | 205.185.216.10:443 | ads.exdynsrv.com | Highwinds Network Group, Inc. | US | whitelisted |
2580 | iexplore.exe | 216.58.215.225:443 | lh6.googleusercontent.com | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2580 | iexplore.exe | 52.56.118.143:80 | — | Amazon.com, Inc. | GB | unknown |
4 | System | 94.31.29.128:445 | cdn.popcash.net | netDNA | GB | malicious |
— | — | 94.31.29.128:137 | cdn.popcash.net | netDNA | GB | malicious |
2580 | iexplore.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2580 | iexplore.exe | 95.211.229.247:443 | syndication.exdynsrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
4 | System | 208.93.230.22:445 | st.chatango.com | Chatango LLC | US | suspicious |
4 | System | 208.93.230.24:445 | st.chatango.com | Chatango LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ads.exdynsrv.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.blogger.com |
| shared |
apps.identrust.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
lh6.googleusercontent.com |
| whitelisted |
cdn.popcash.net |
| whitelisted |
syndication.exdynsrv.com |
| suspicious |
st.chatango.com |
| whitelisted |