| File name: | Assign Document.exe |
| Full analysis: | https://app.any.run/tasks/6826528b-af66-4edc-a305-51bbc3110e26 |
| Verdict: | No threats detected |
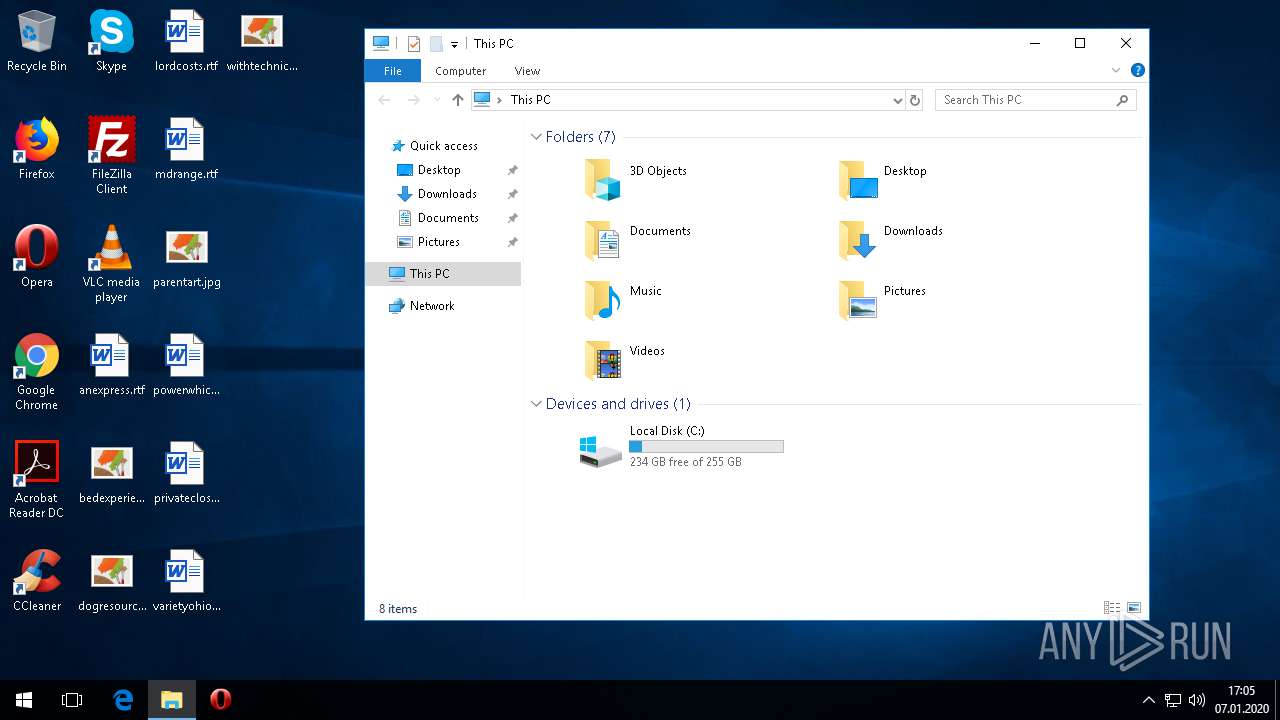
| Analysis date: | January 07, 2020, 16:54:32 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D46A243899465E22B61C95CE73D11508 |
| SHA1: | 3D549AA079ED02FFA6D5B602CCB3B58A48B9F347 |
| SHA256: | E6F2D277D61FD27D2A6452619111C272047FF478247251C9EC5651F5F67E1519 |
| SSDEEP: | 12288:kHq+Solcjjr/g+HfBriIGN0cusKGJ61vzltIM:kK62j//g+/Y70vs/6hJt9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
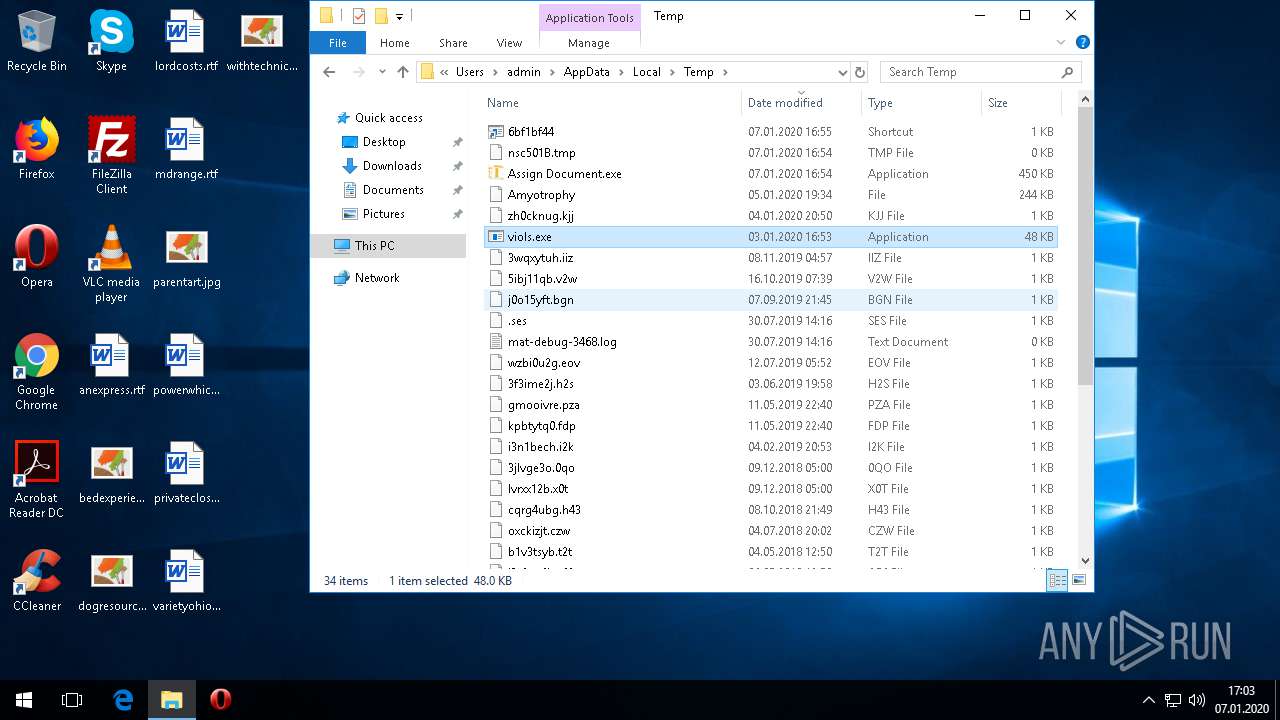
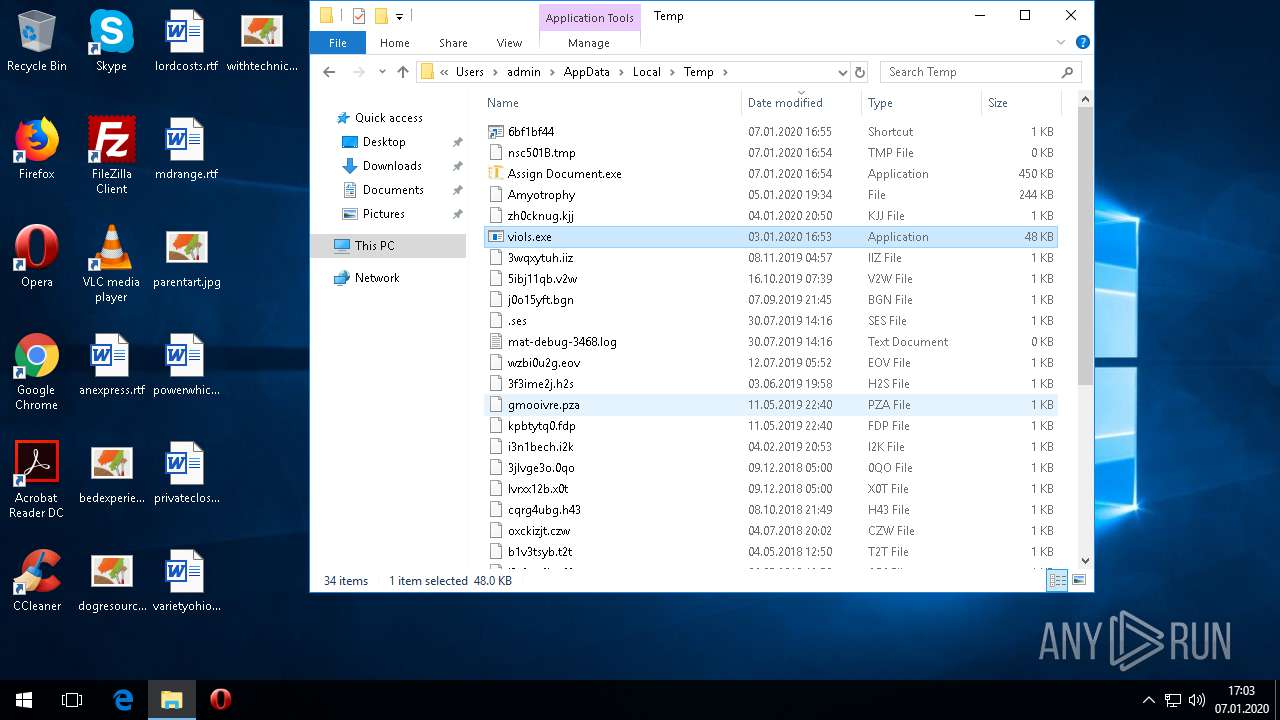
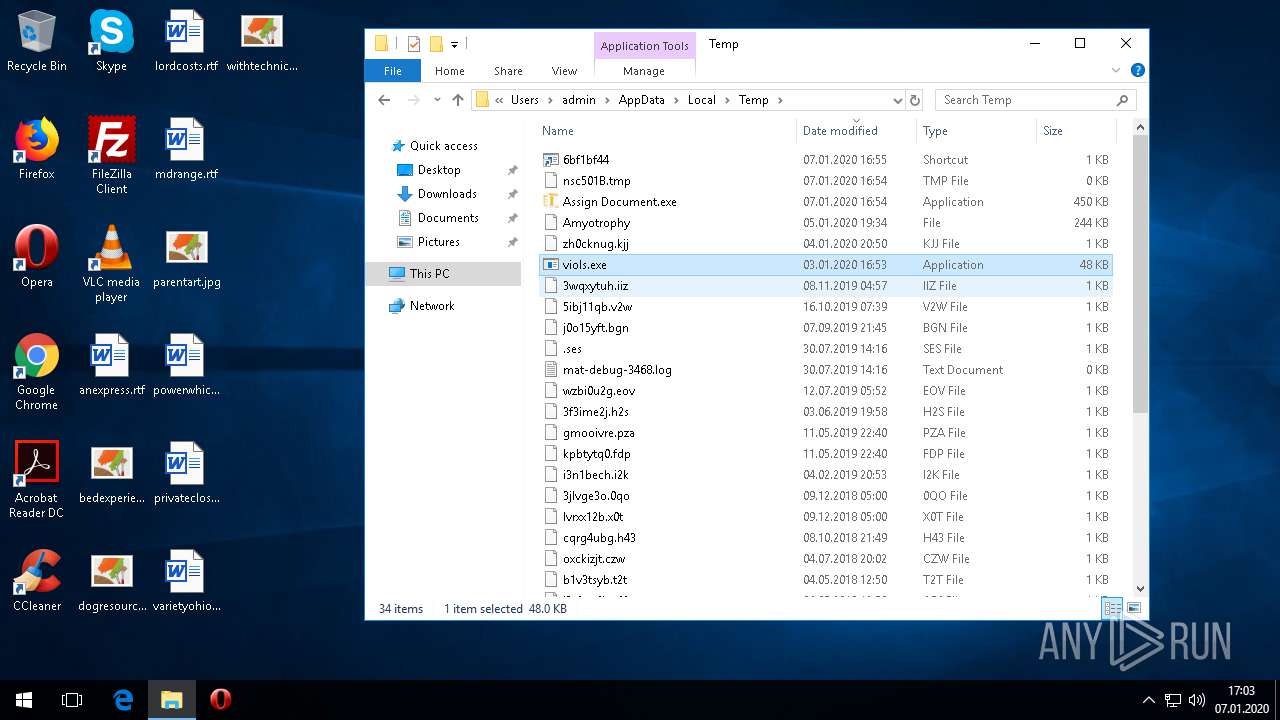
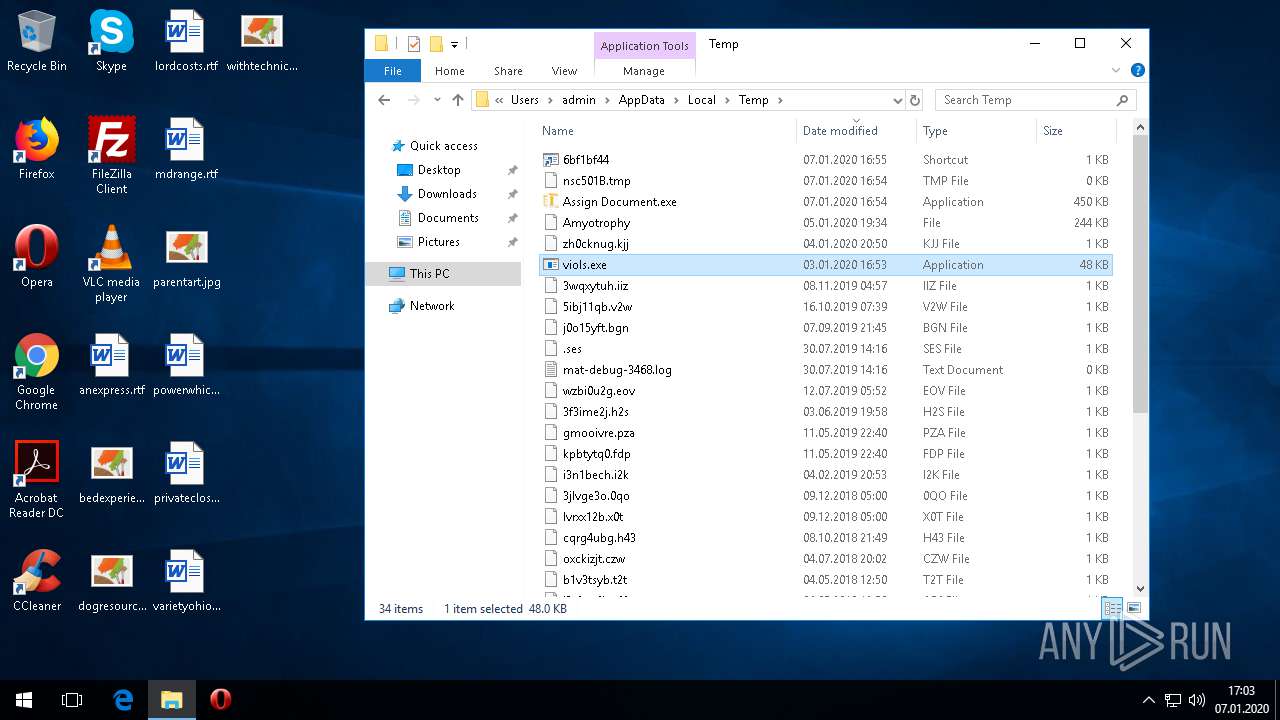
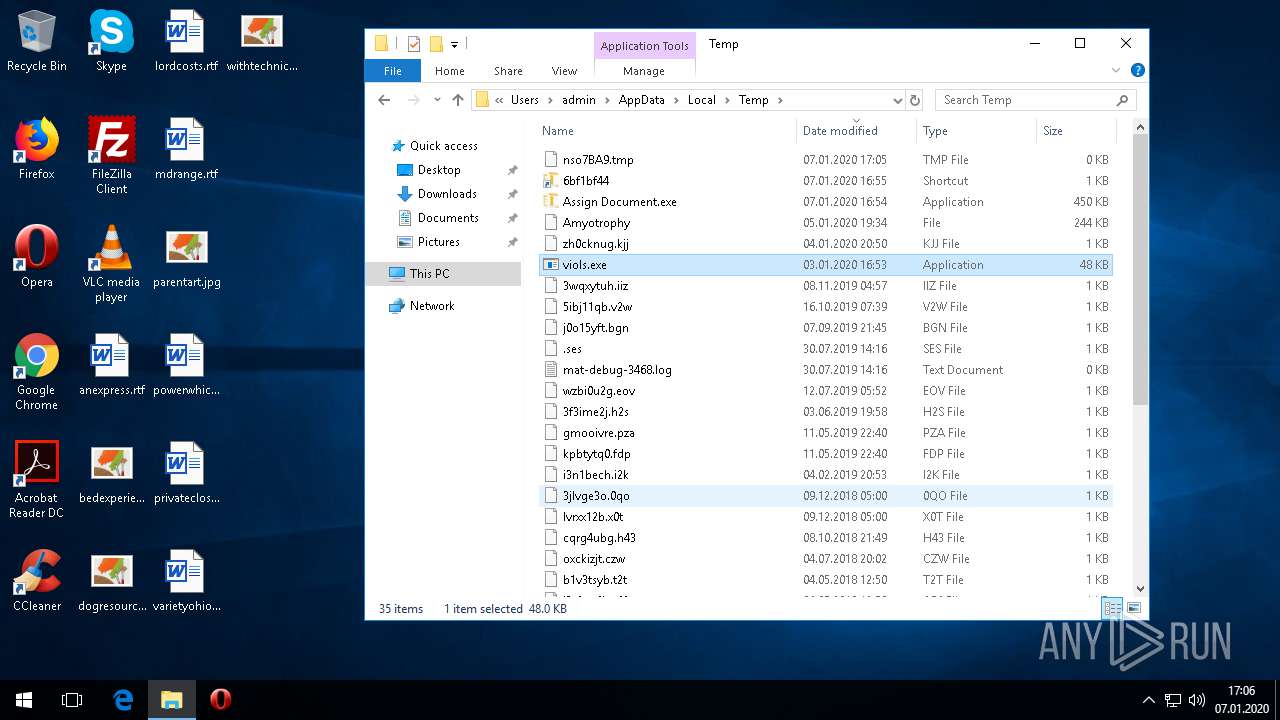
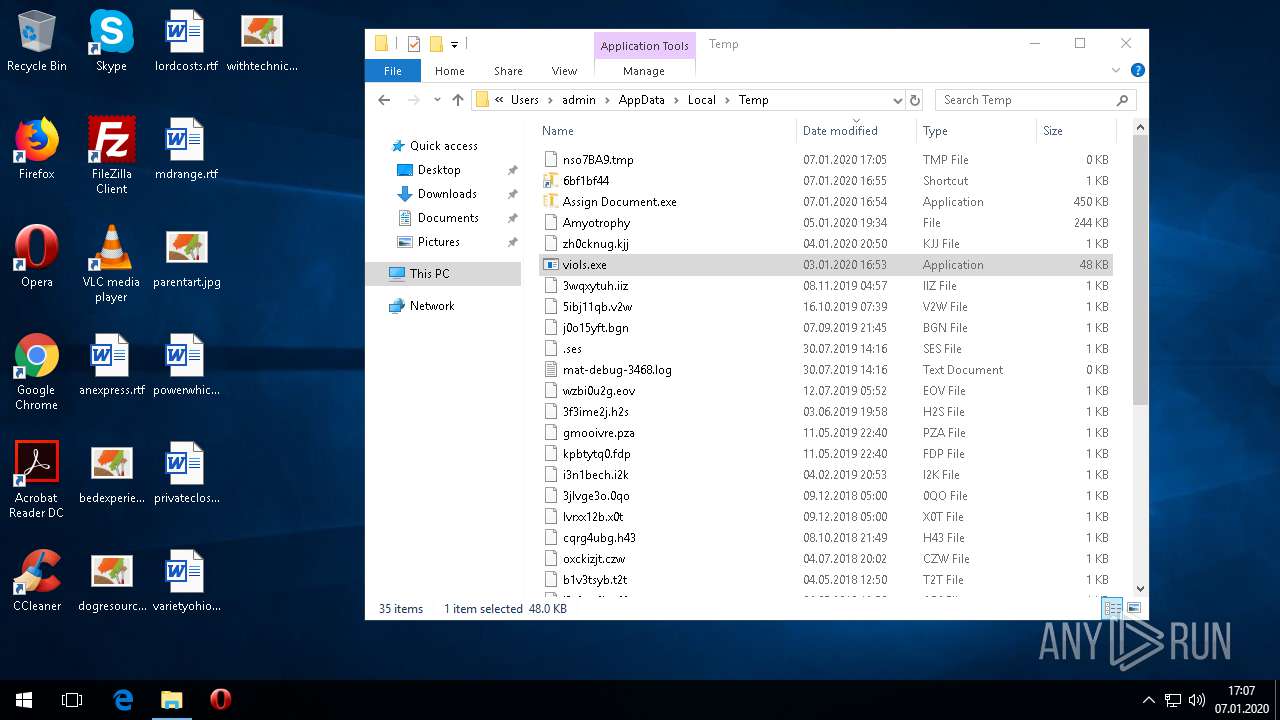
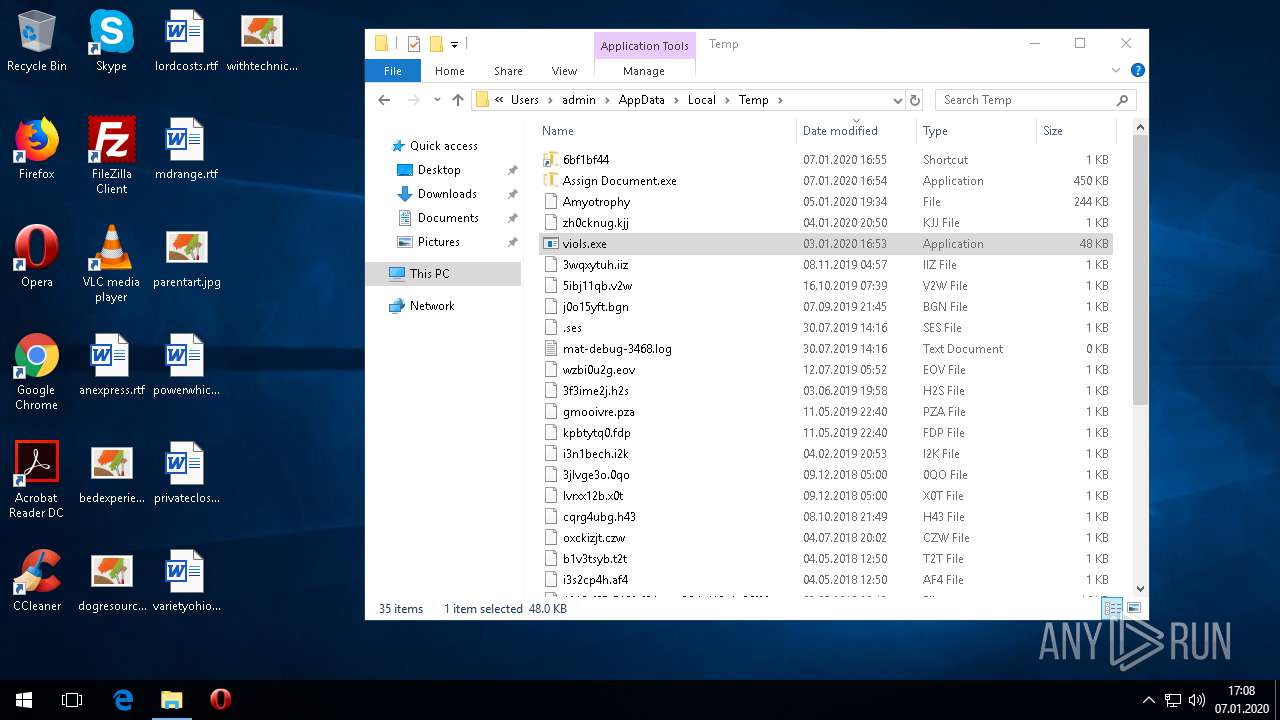
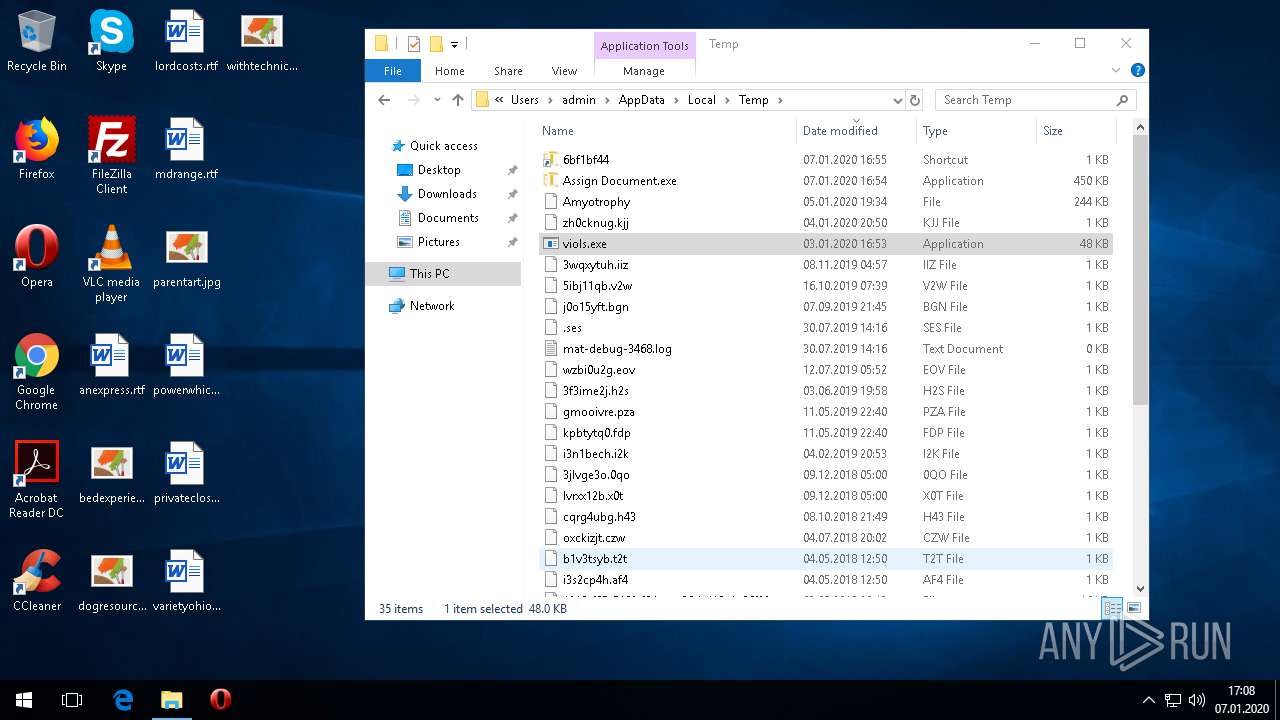
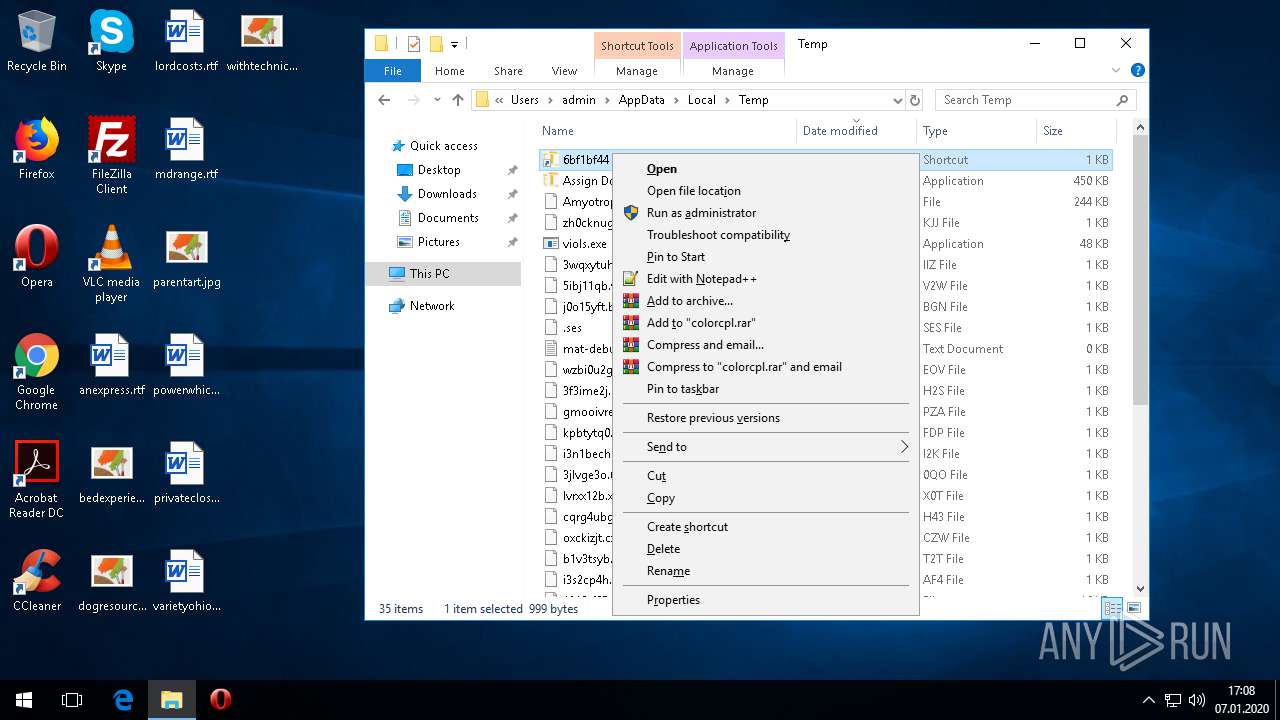
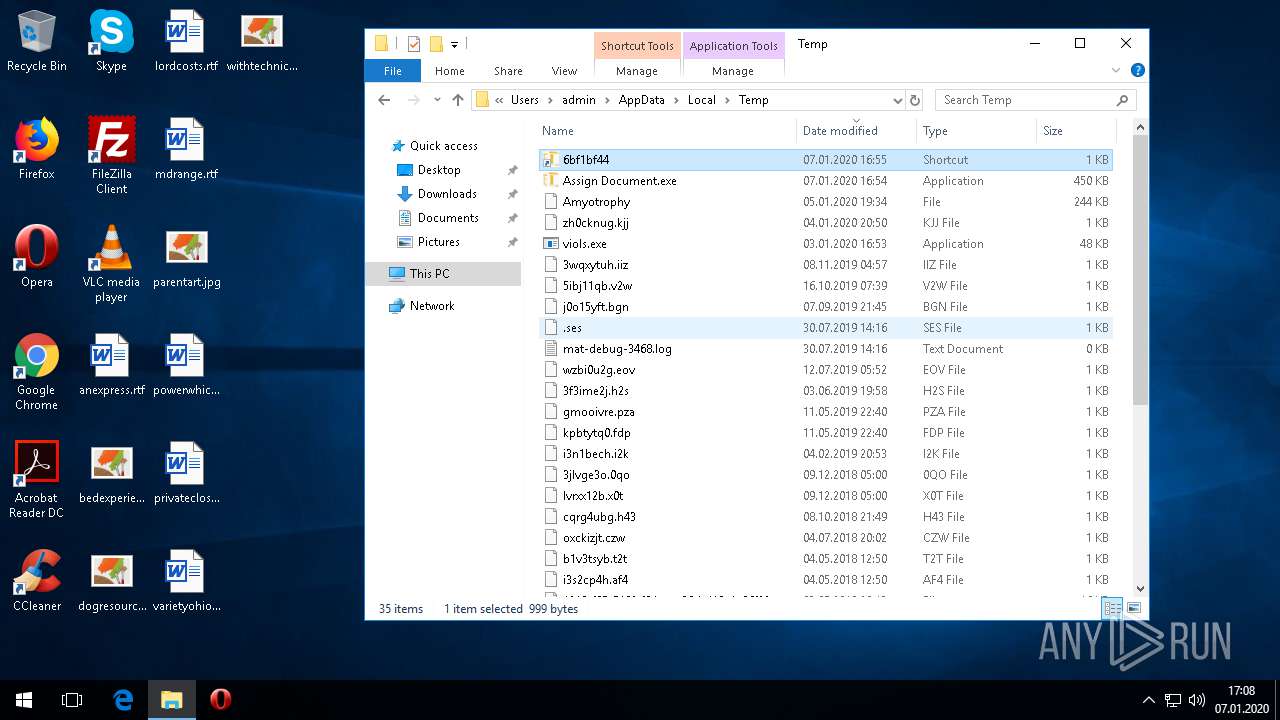
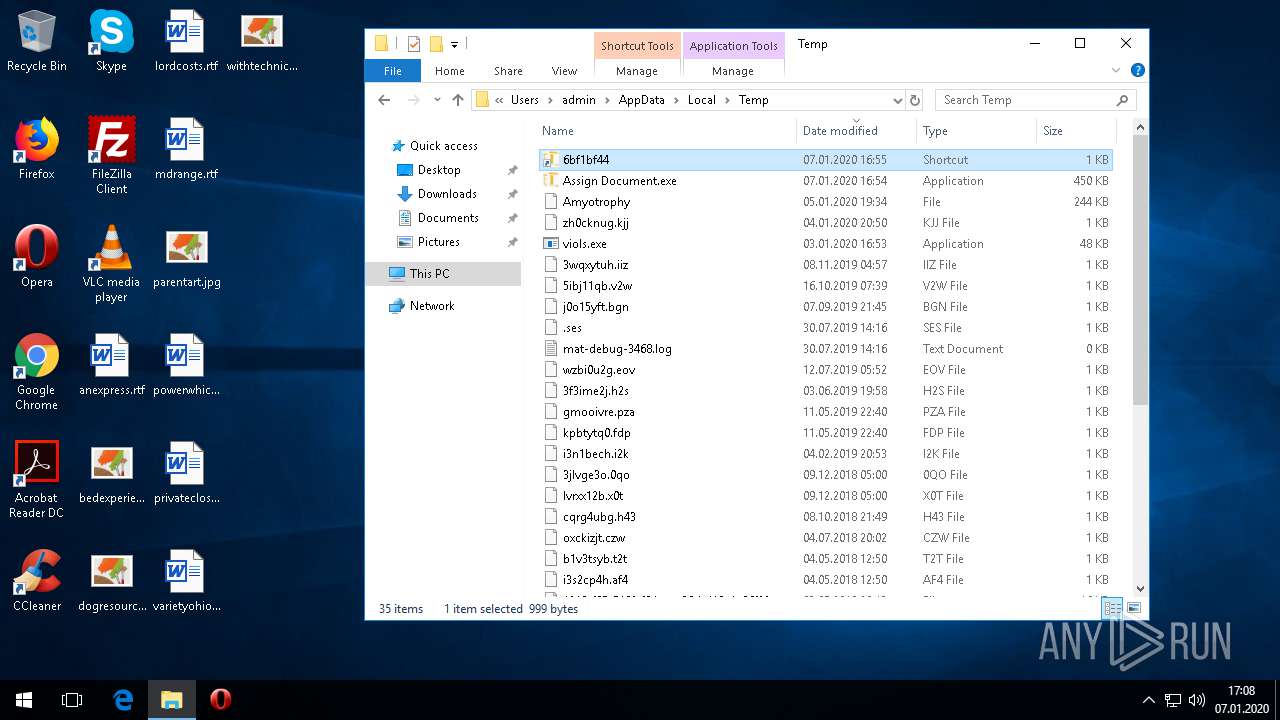
Executable content was dropped or overwritten
- colorcpl.exe (PID: 2072)
- Assign Document.exe (PID: 3032)
INFO
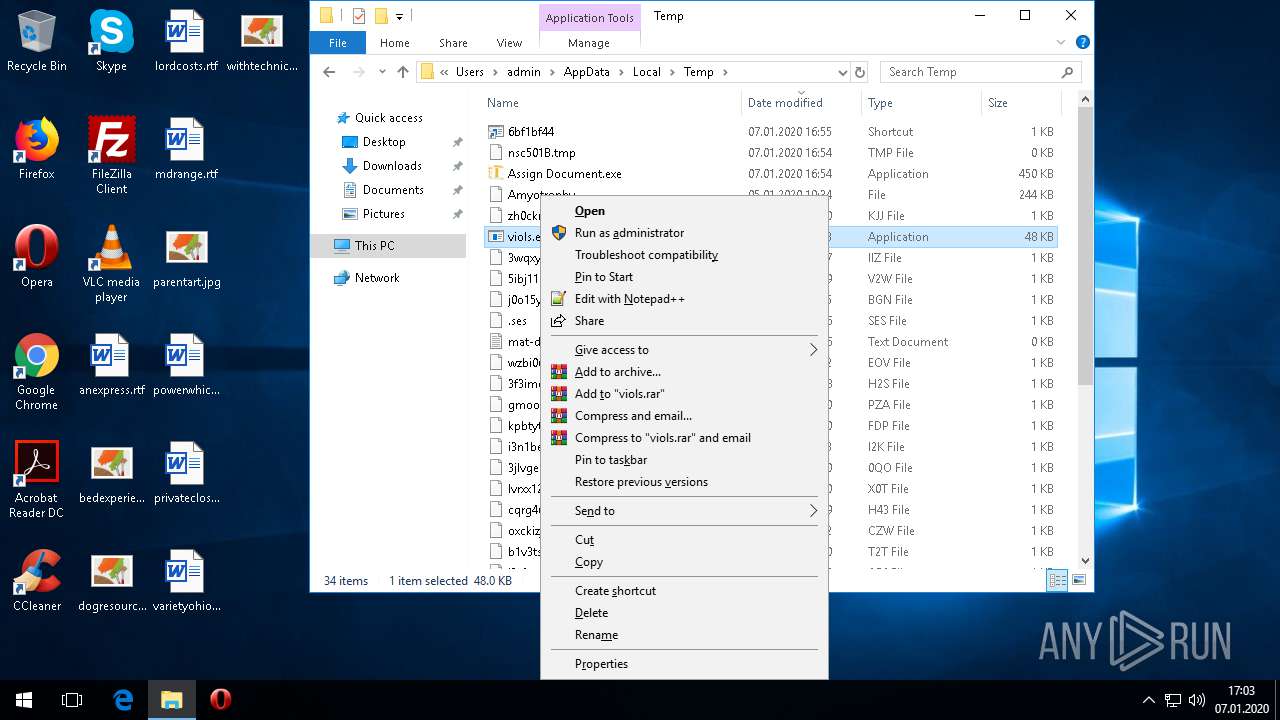
Manual execution by user
- colorcpl.exe (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 01:50:53+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x350d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2019 00:50:53 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2019 00:50:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000647B | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42652 |
.rdata | 0x00008000 | 0x00001384 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13635 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.00585 |
.ndata | 0x0002B000 | 0x00011000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003C000 | 0x00004380 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8878 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29987 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.65331 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.78658 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.74309 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.45849 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
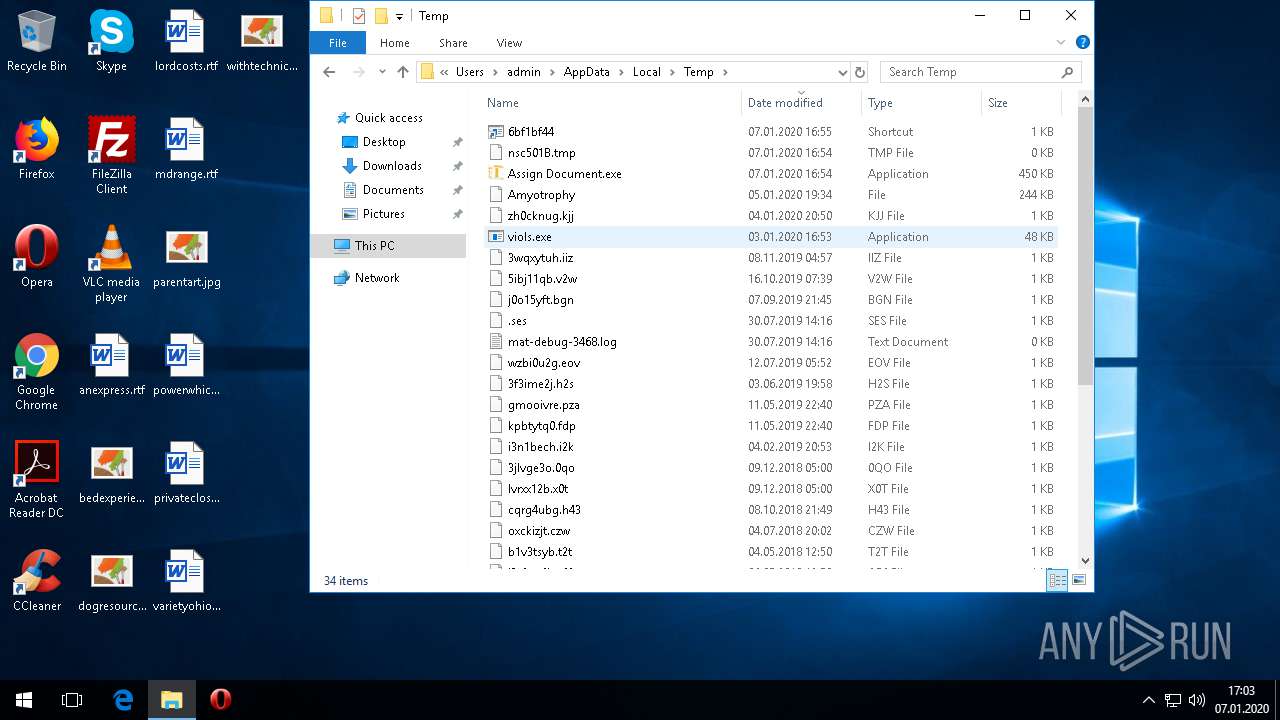
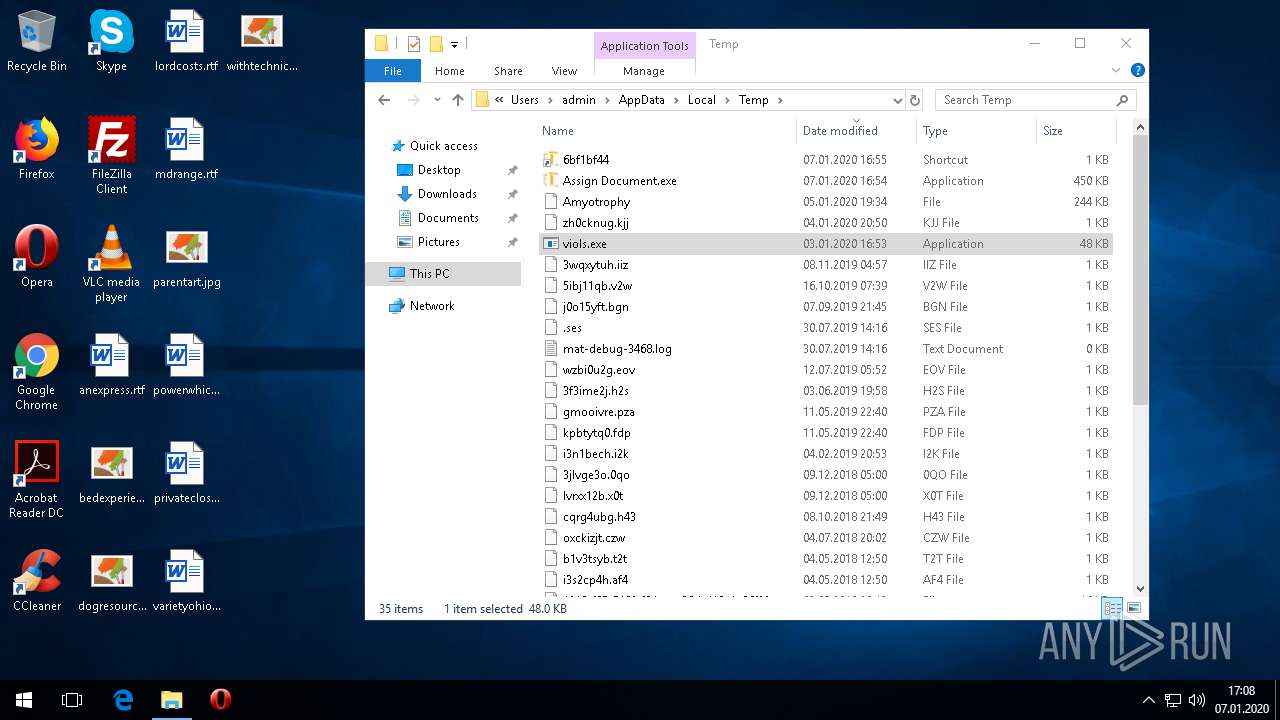
Total processes
100
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
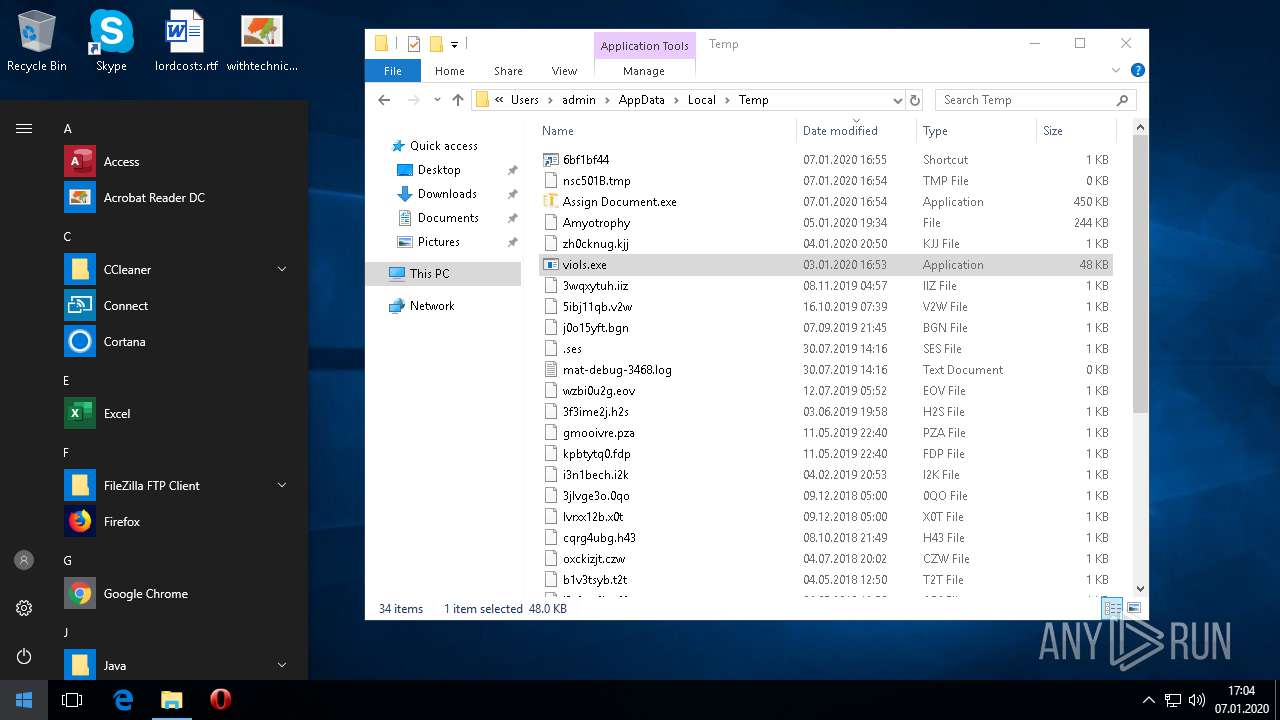
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
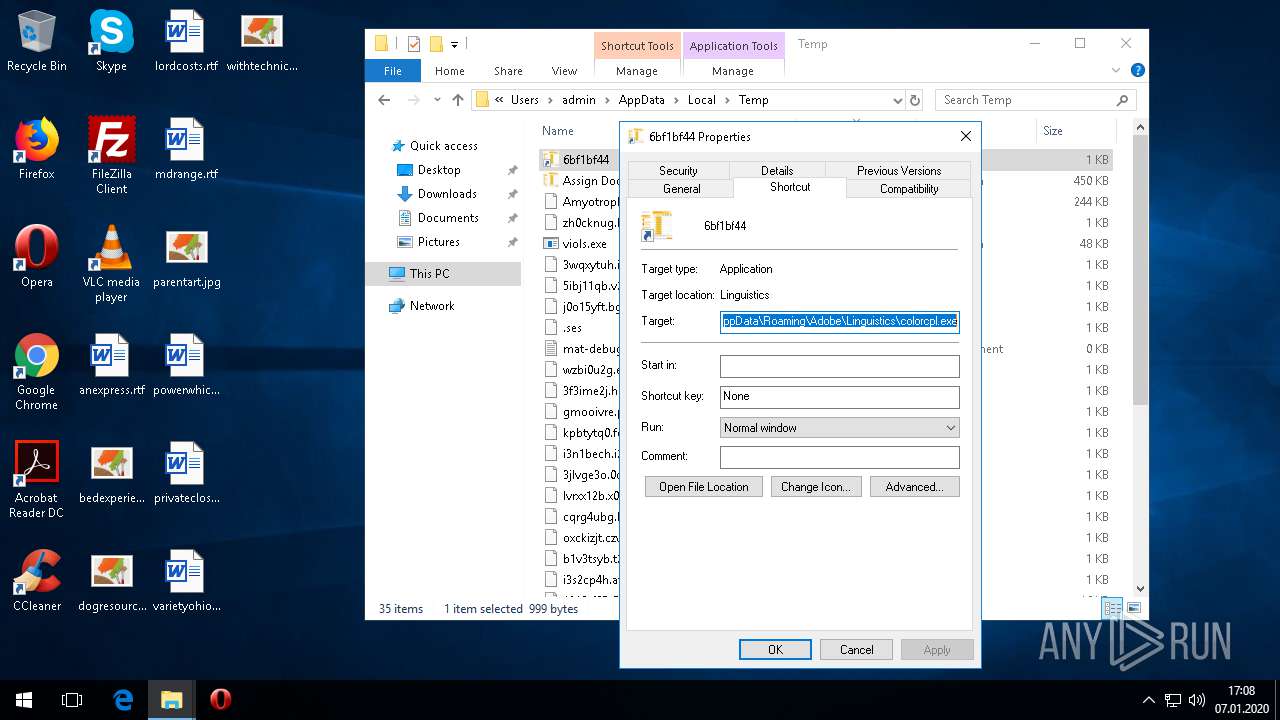
| 2072 | "C:\Users\admin\AppData\Roaming\Adobe\Linguistics\colorcpl.exe" | C:\Users\admin\AppData\Roaming\Adobe\Linguistics\colorcpl.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
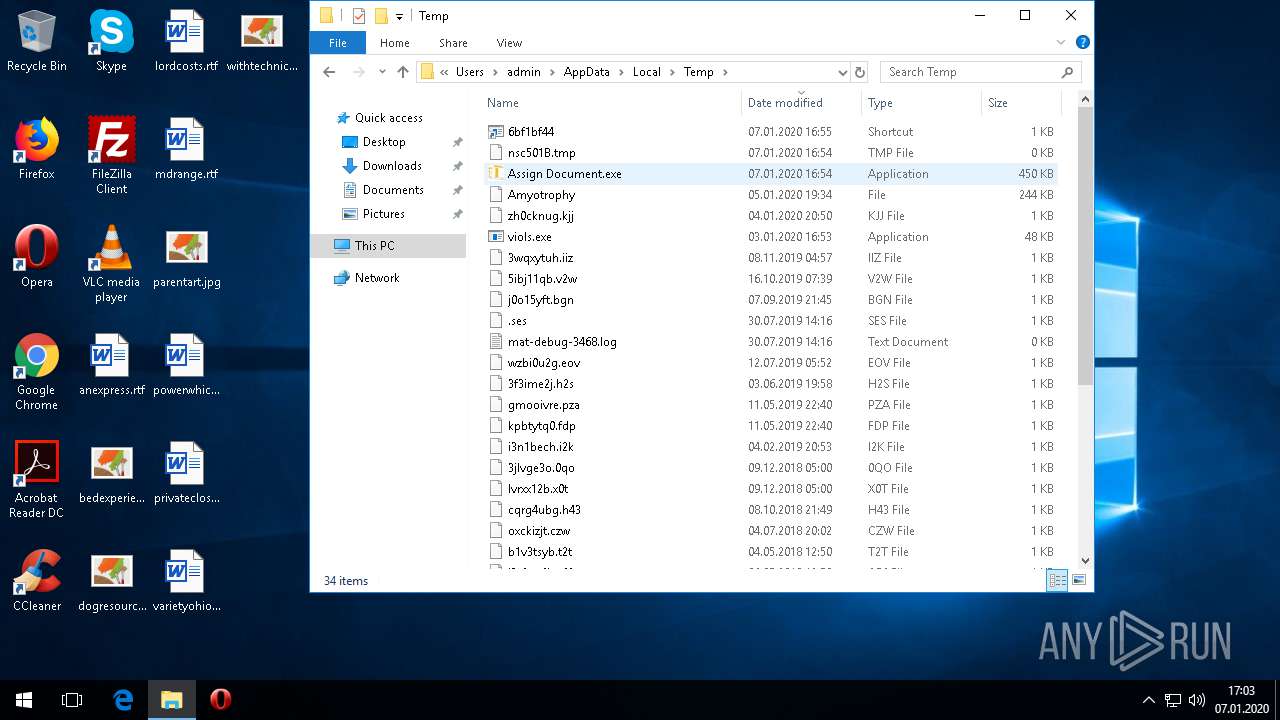
| 3032 | "C:\Users\admin\AppData\Local\Temp\Assign Document.exe" | C:\Users\admin\AppData\Local\Temp\Assign Document.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
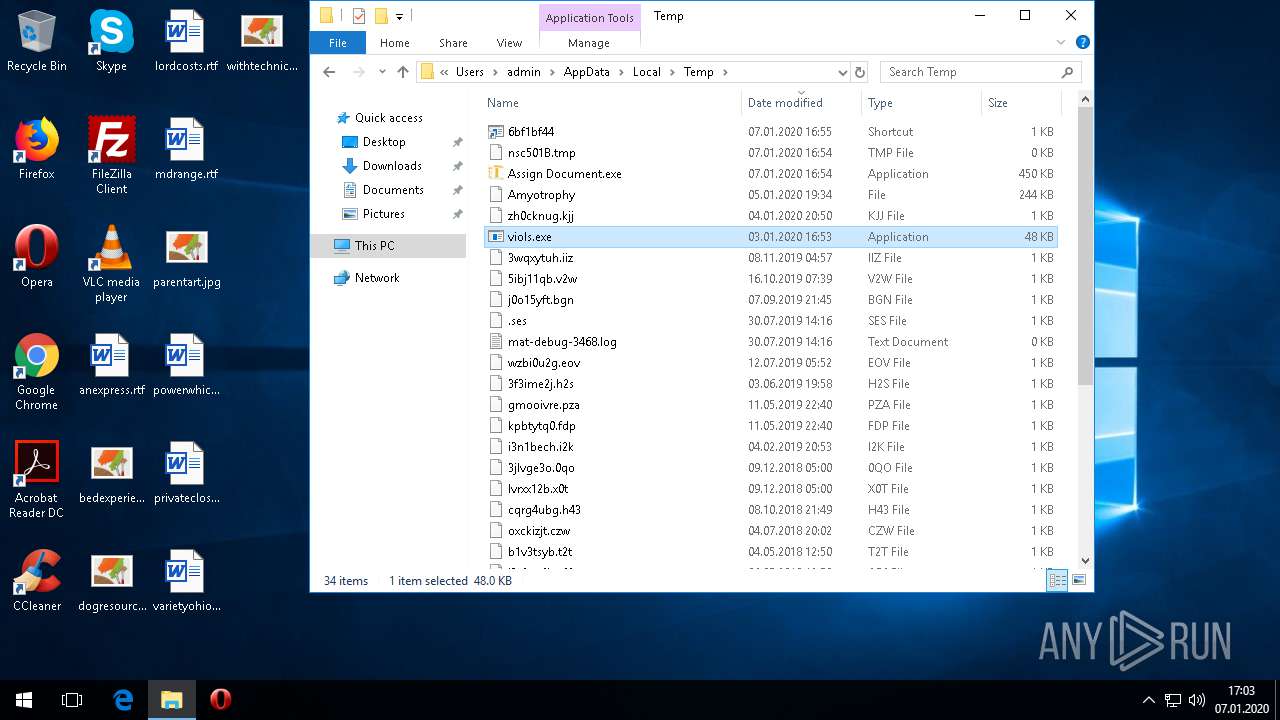
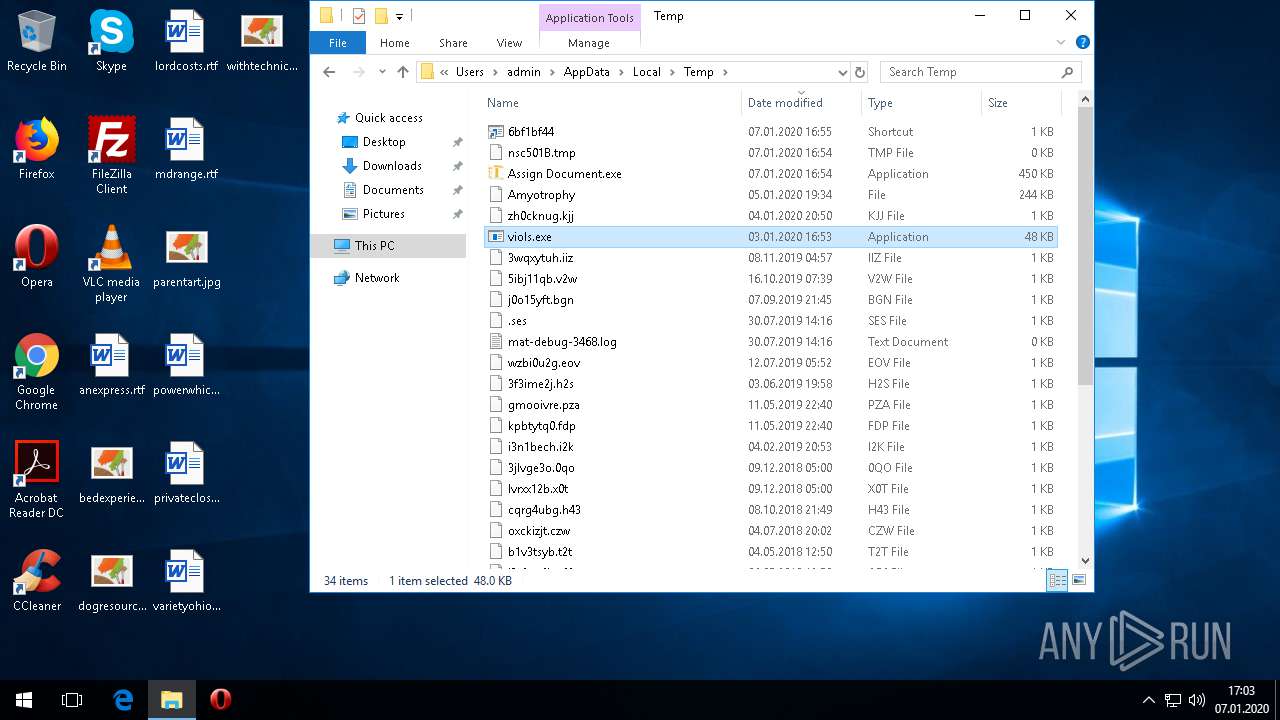
Total events
729
Read events
729
Write events
0
Delete events
0
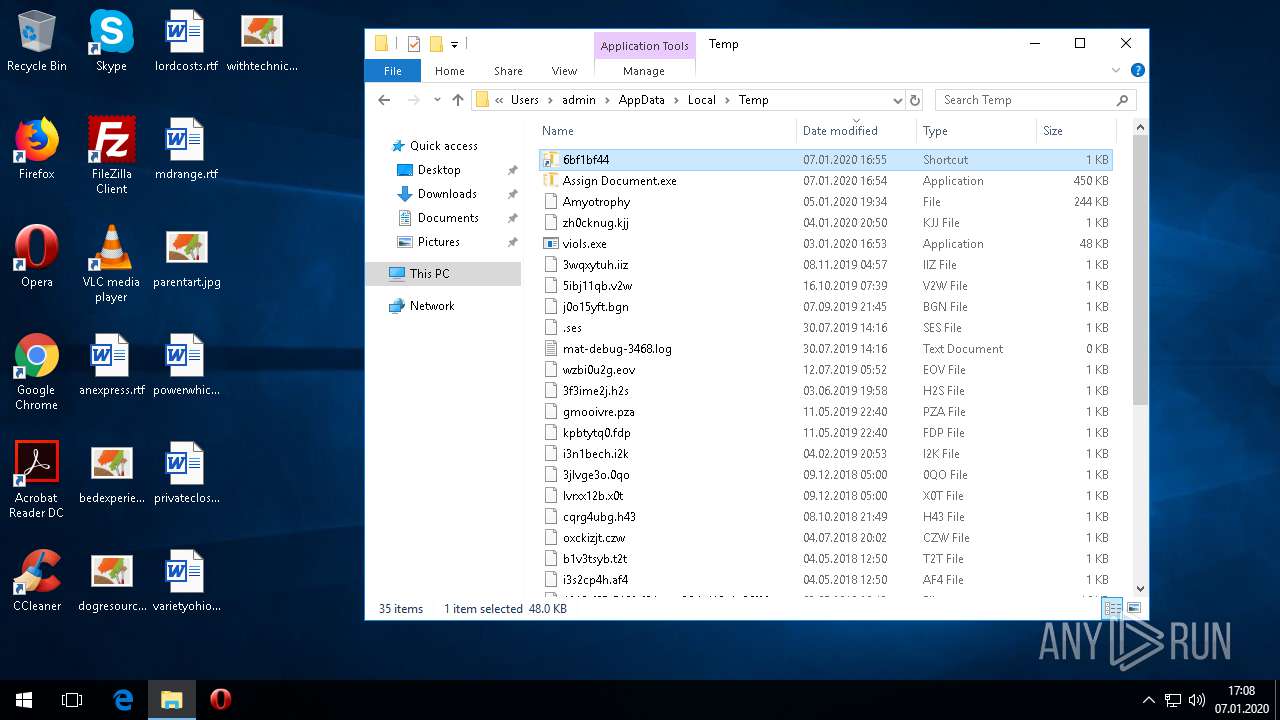
Modification events
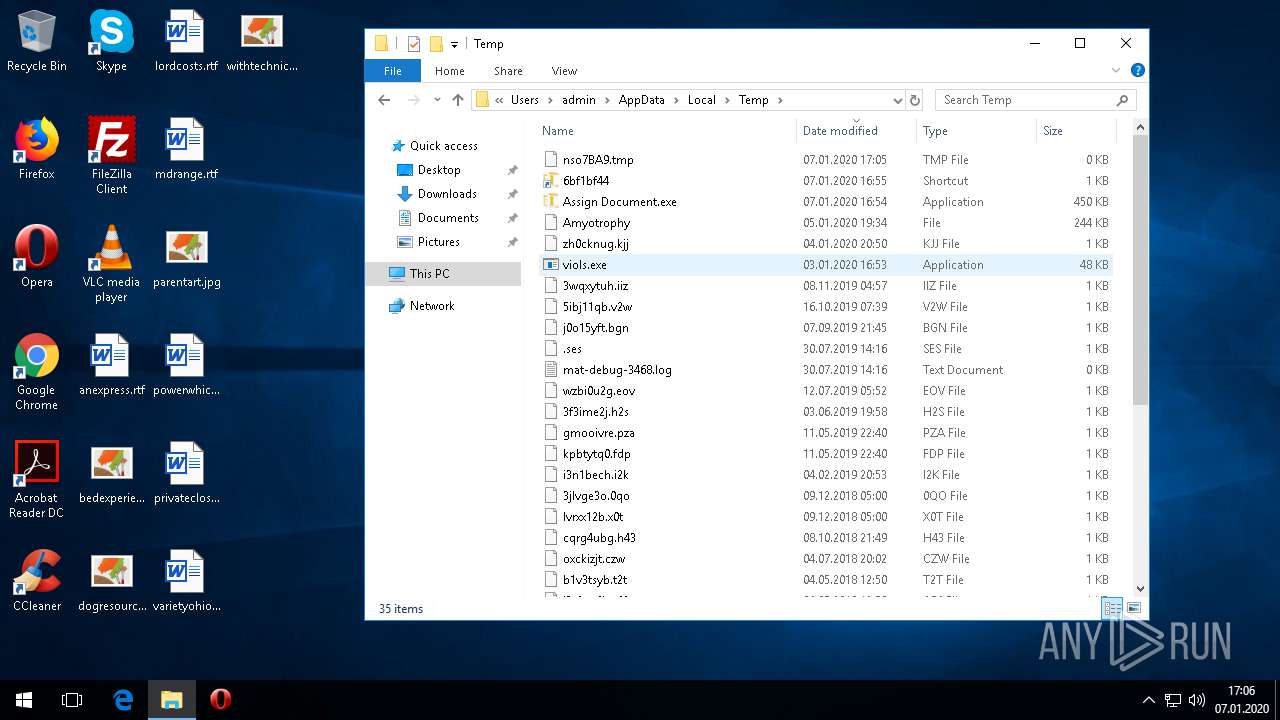
Executable files
10
Suspicious files
4
Text files
38
Unknown types
2
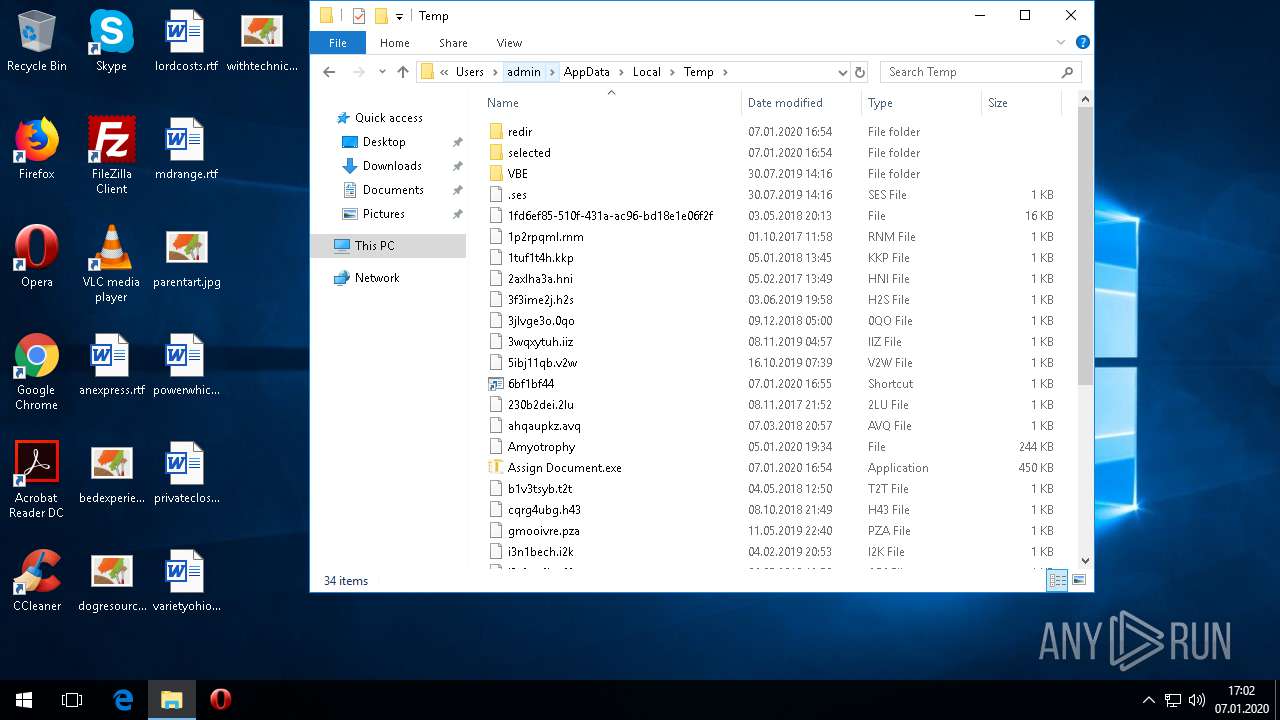
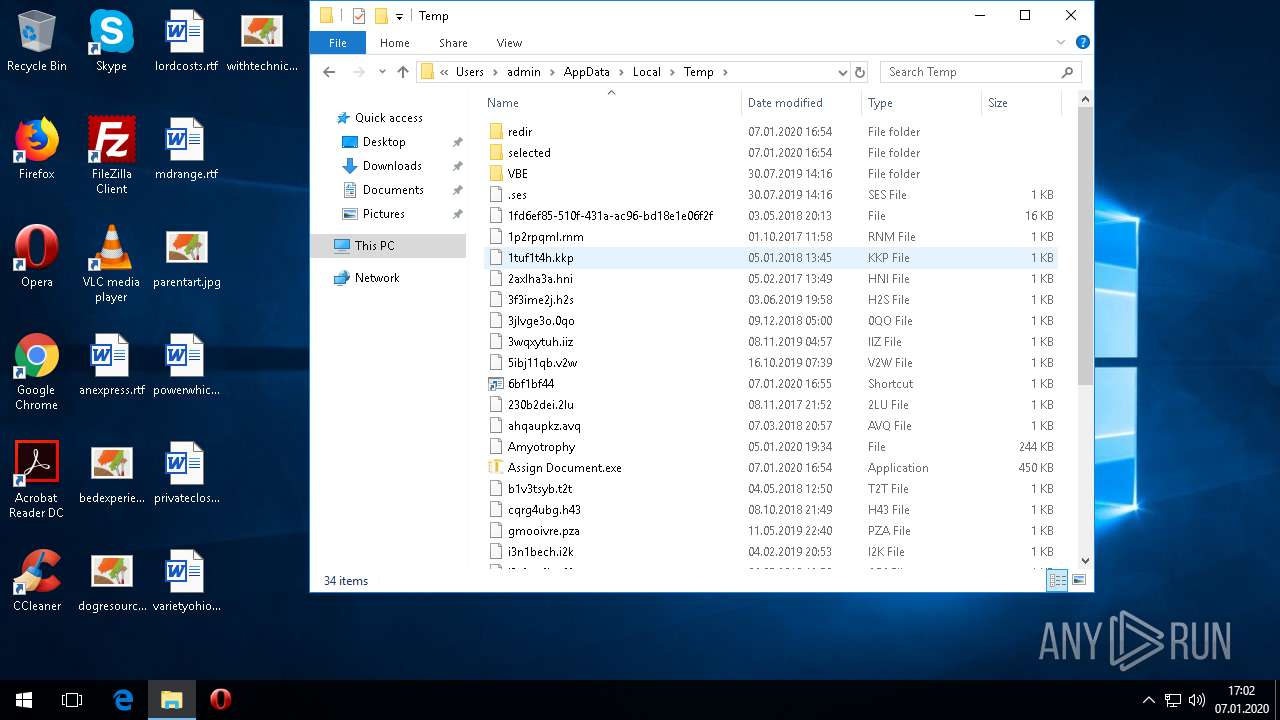
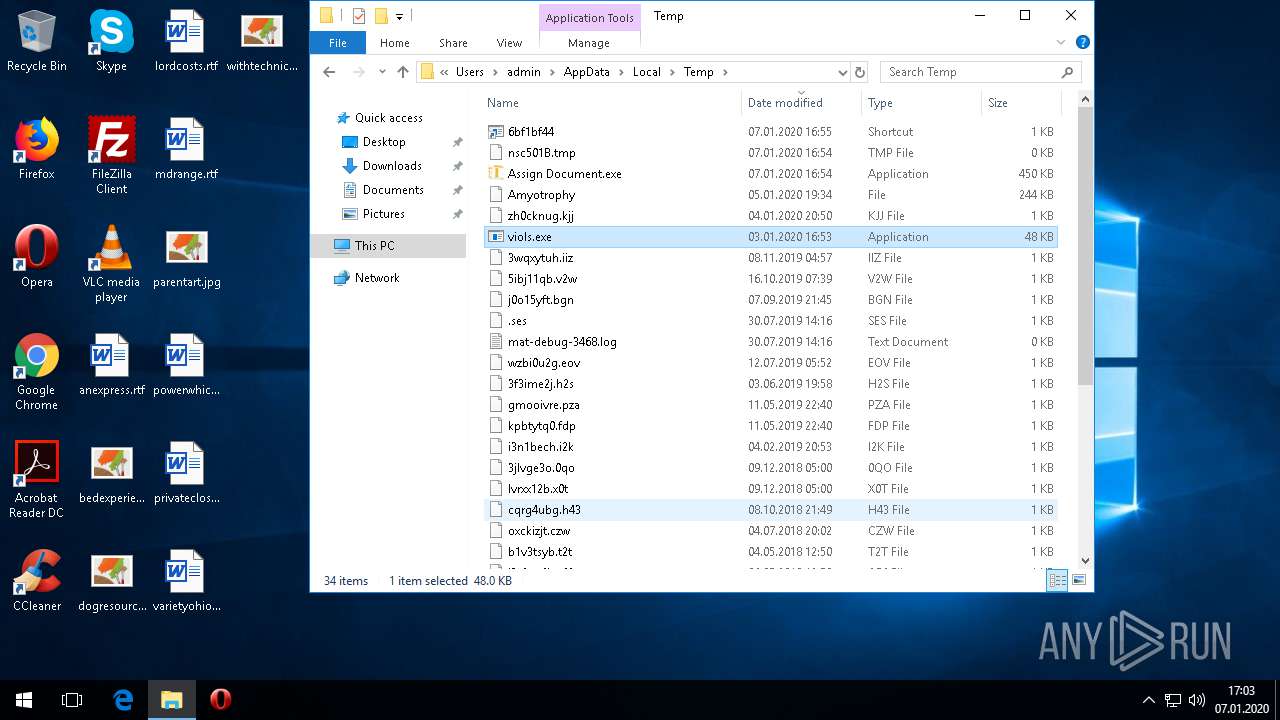
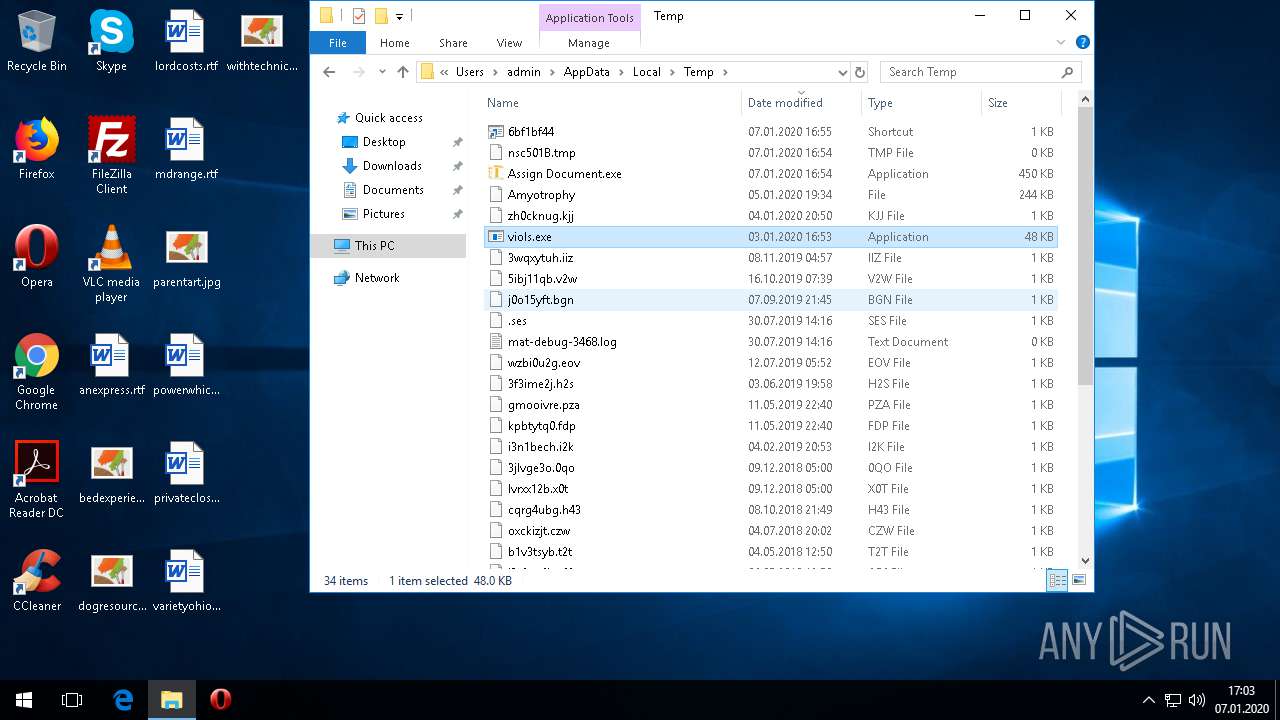
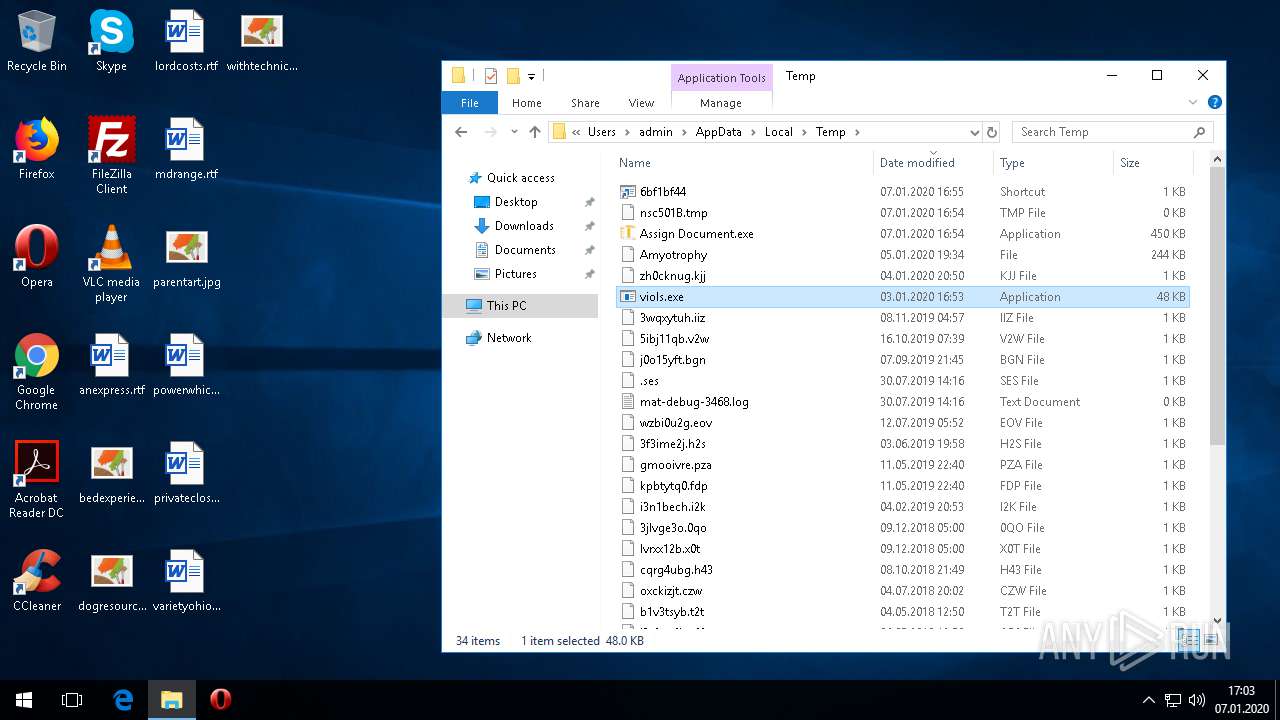
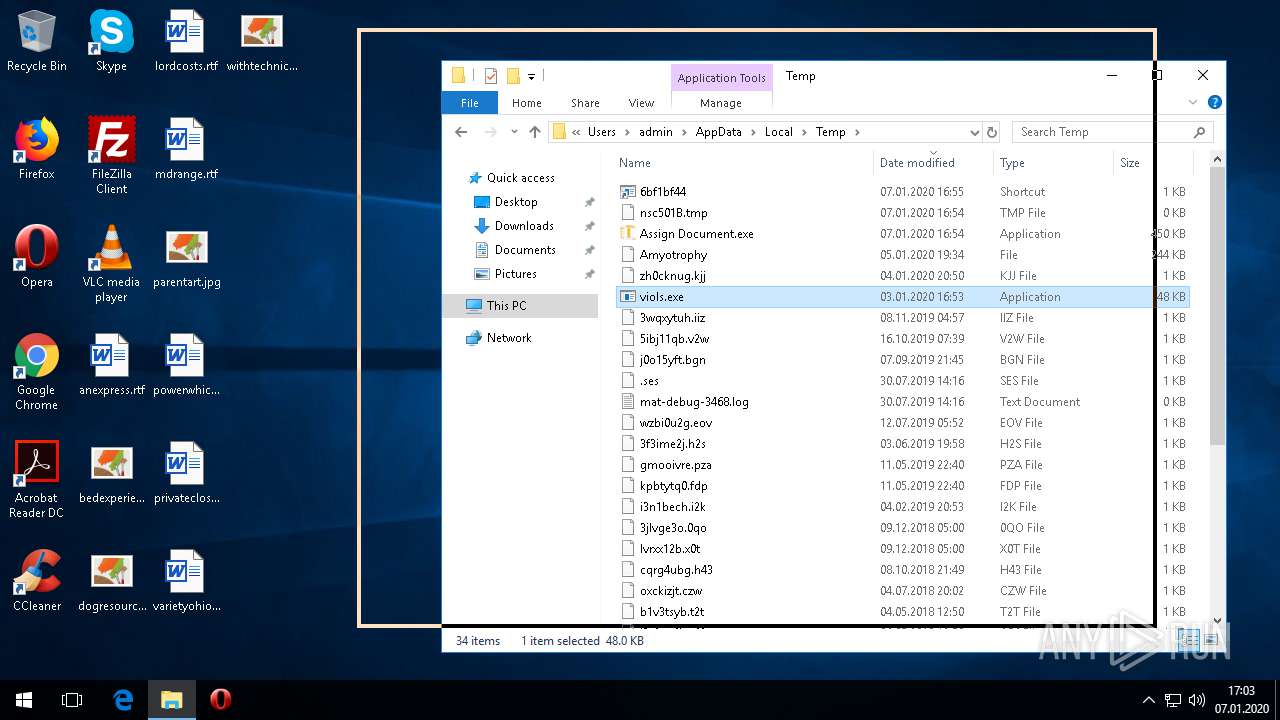
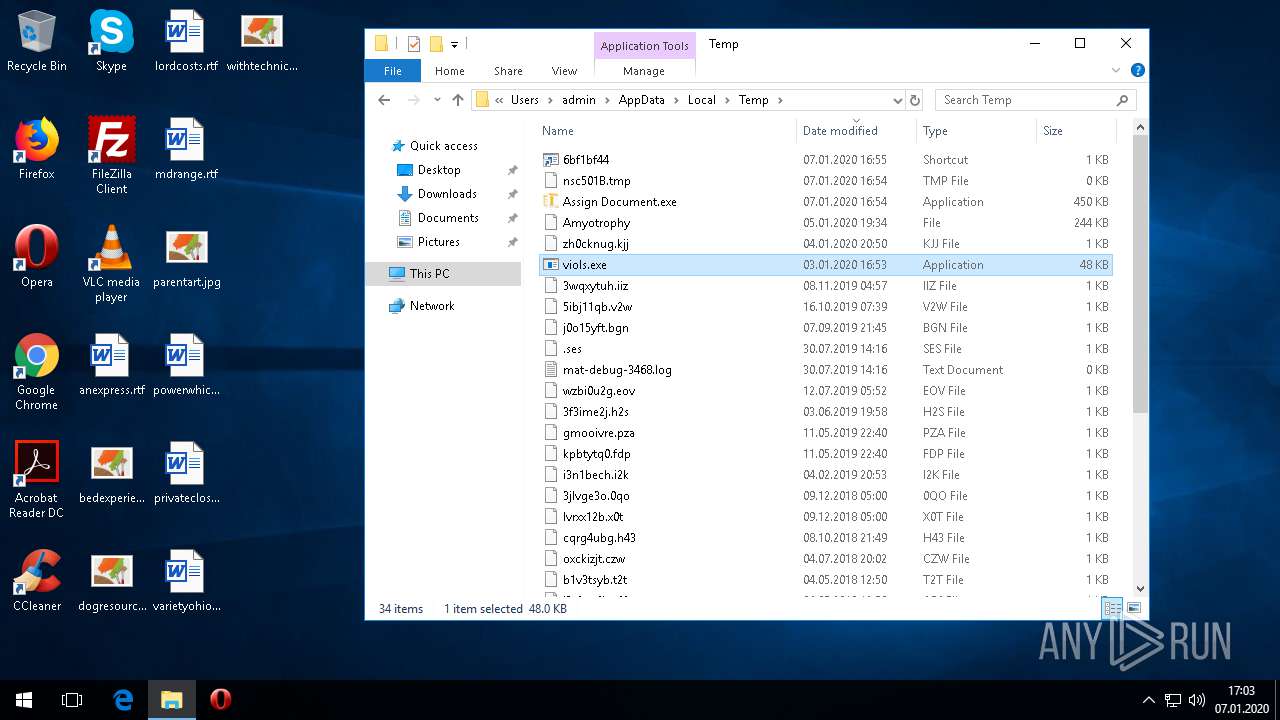
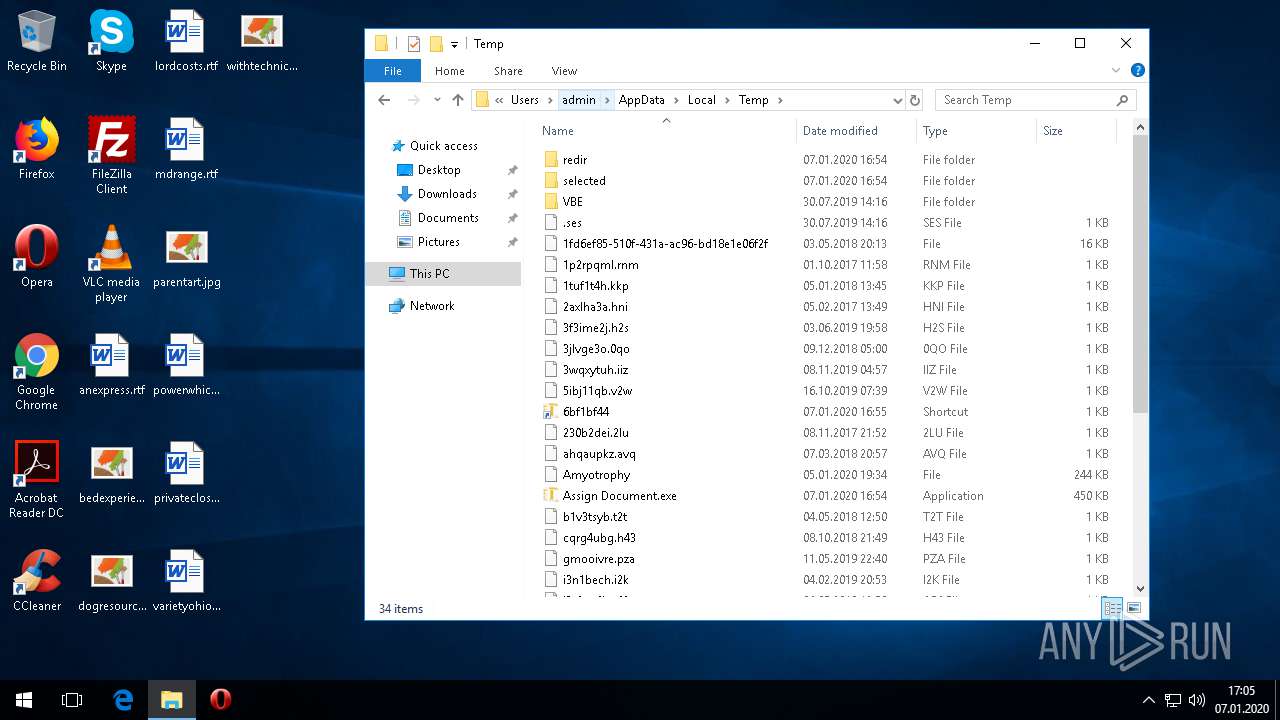
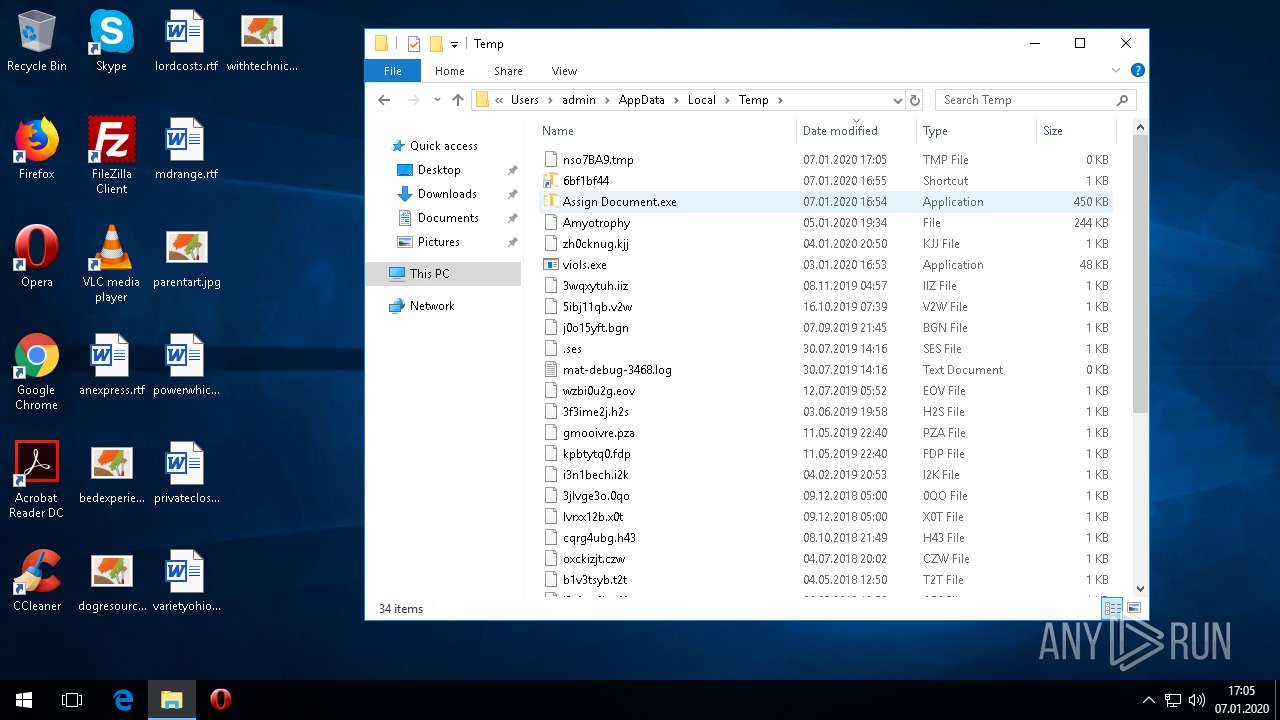
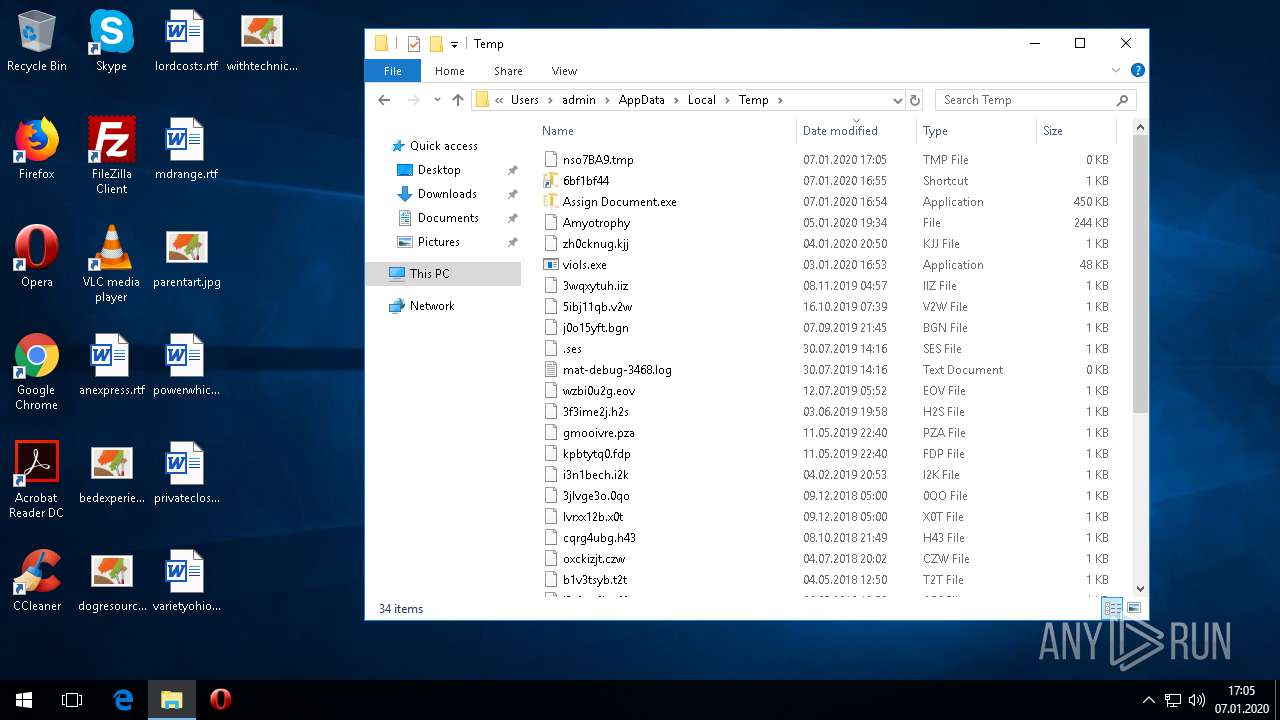
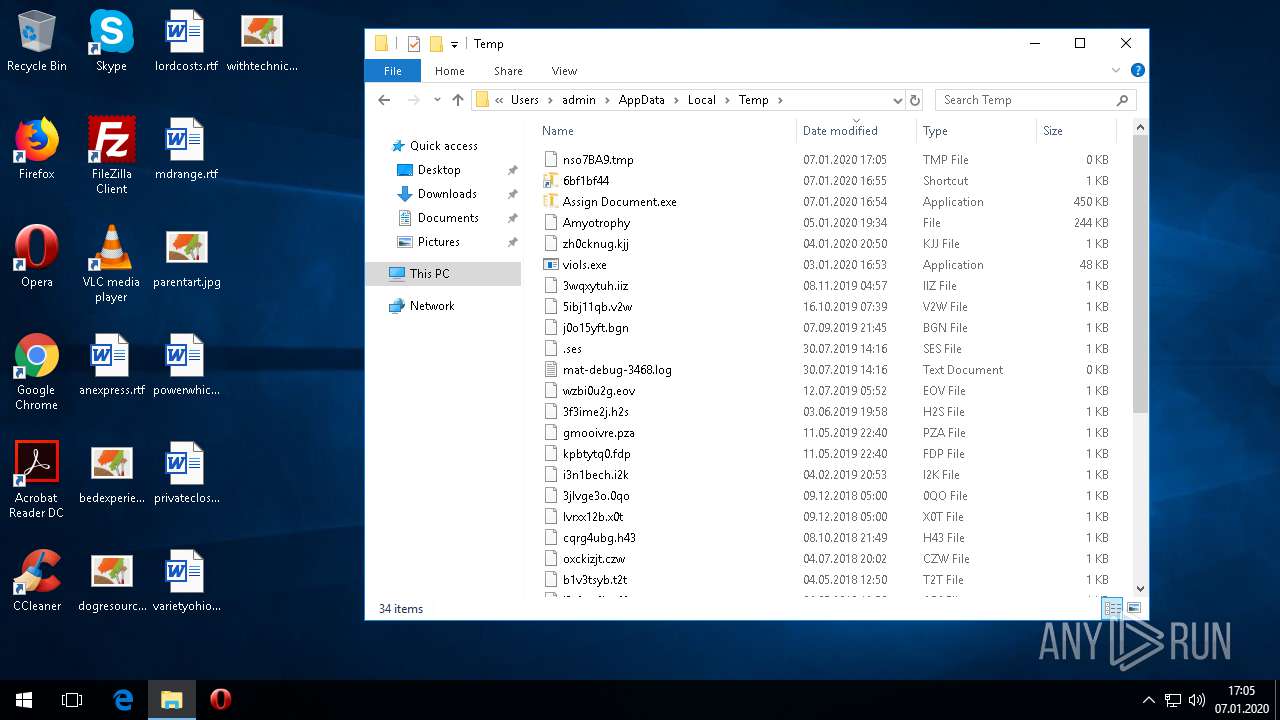
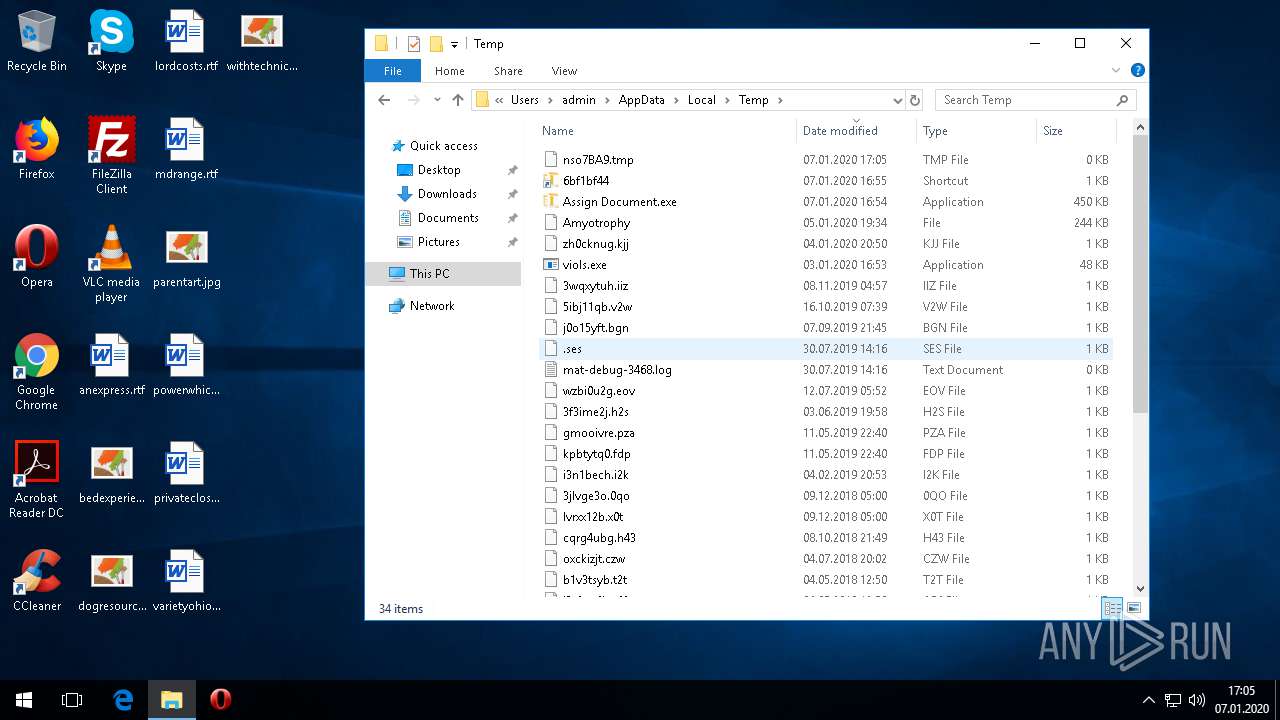
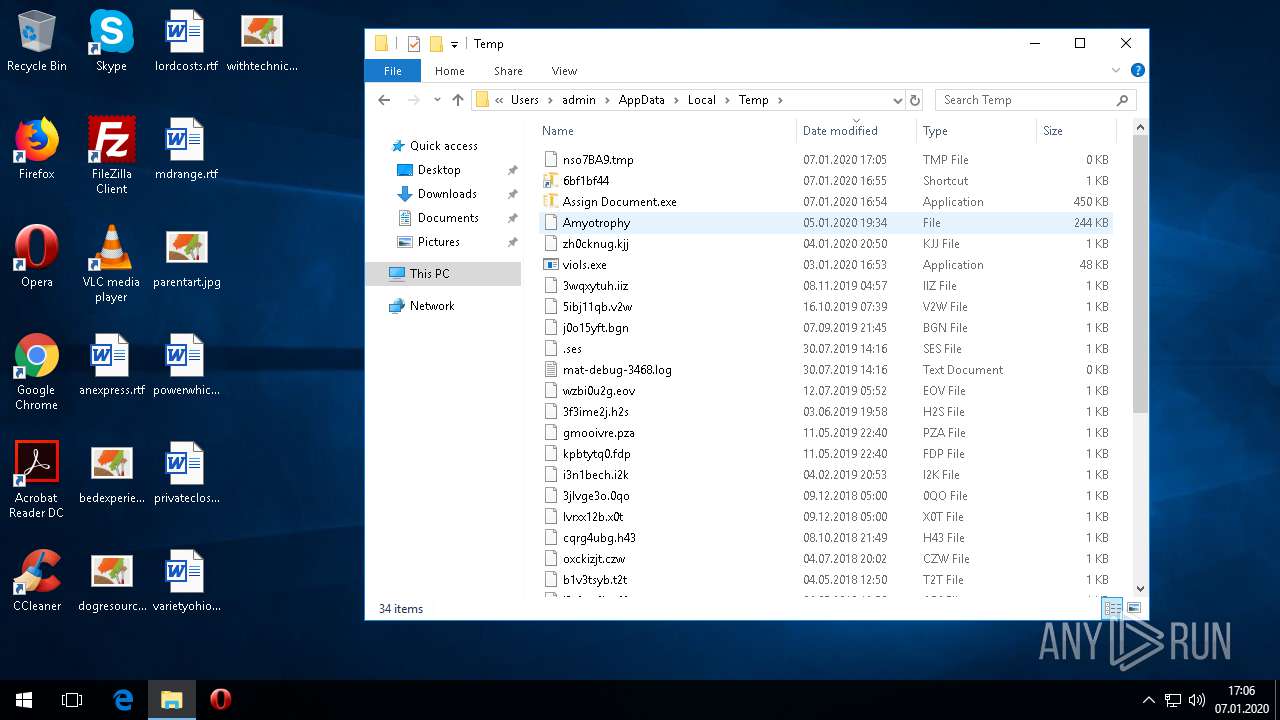
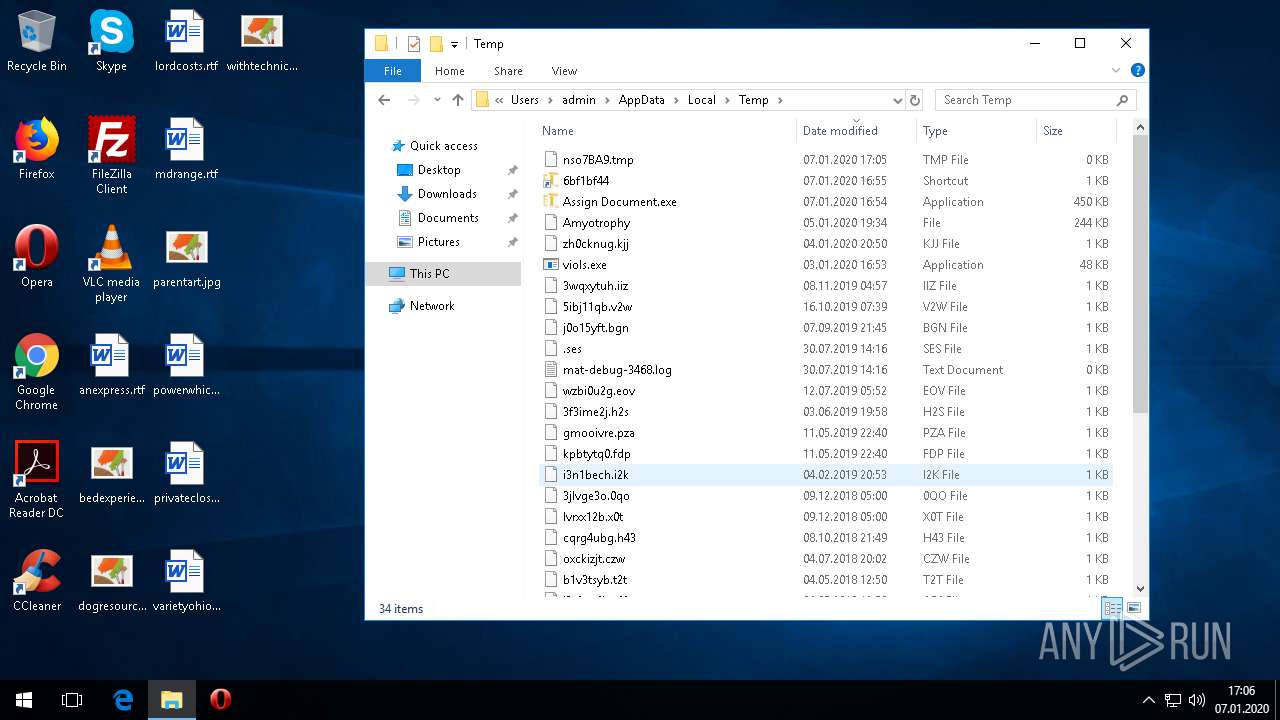
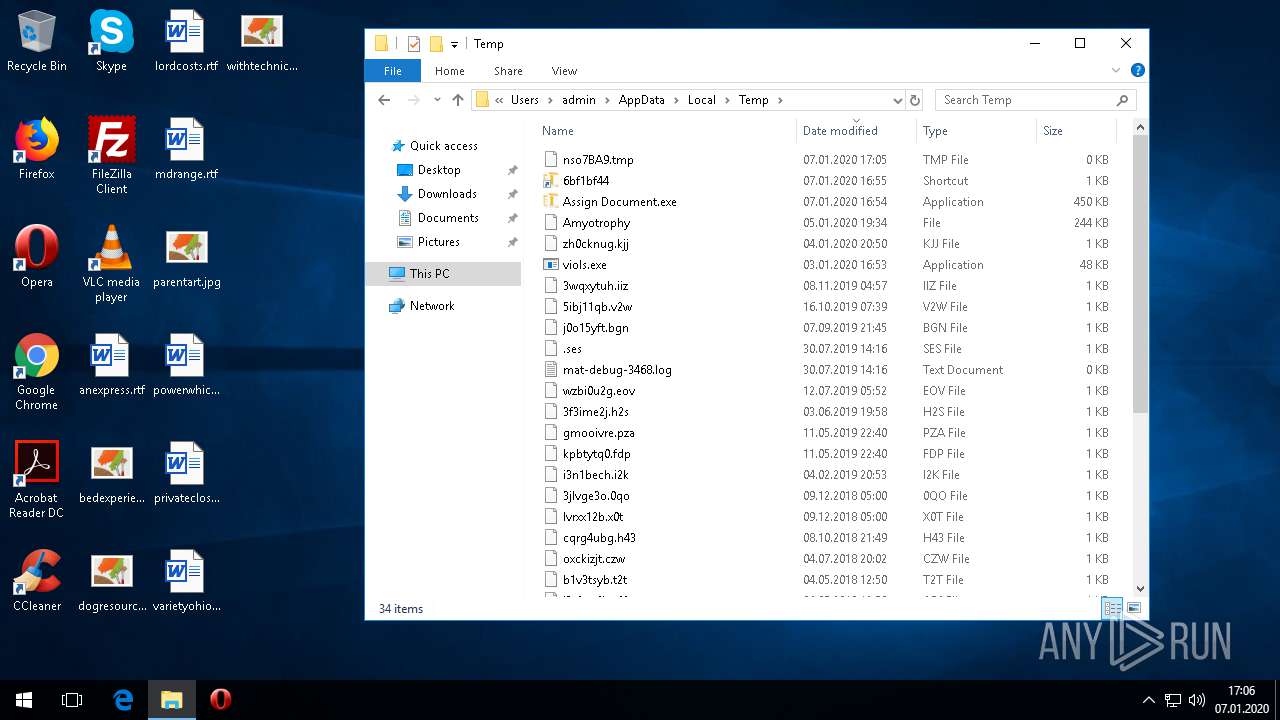
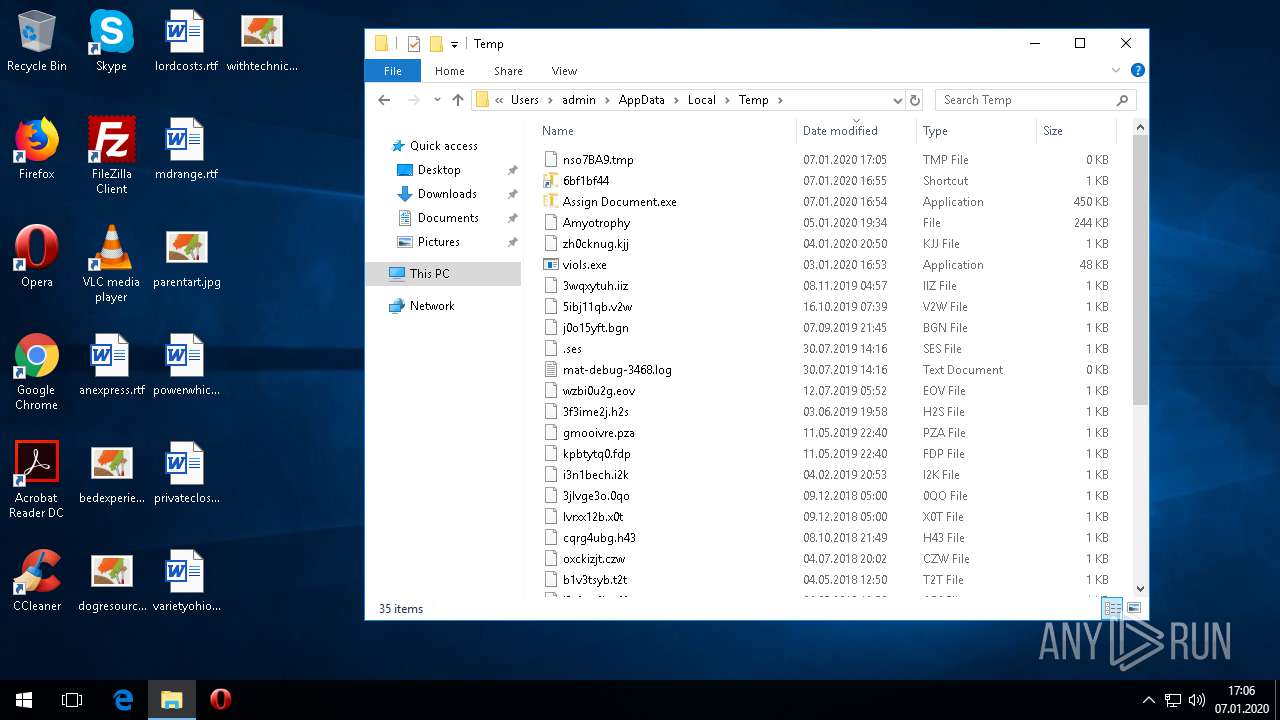
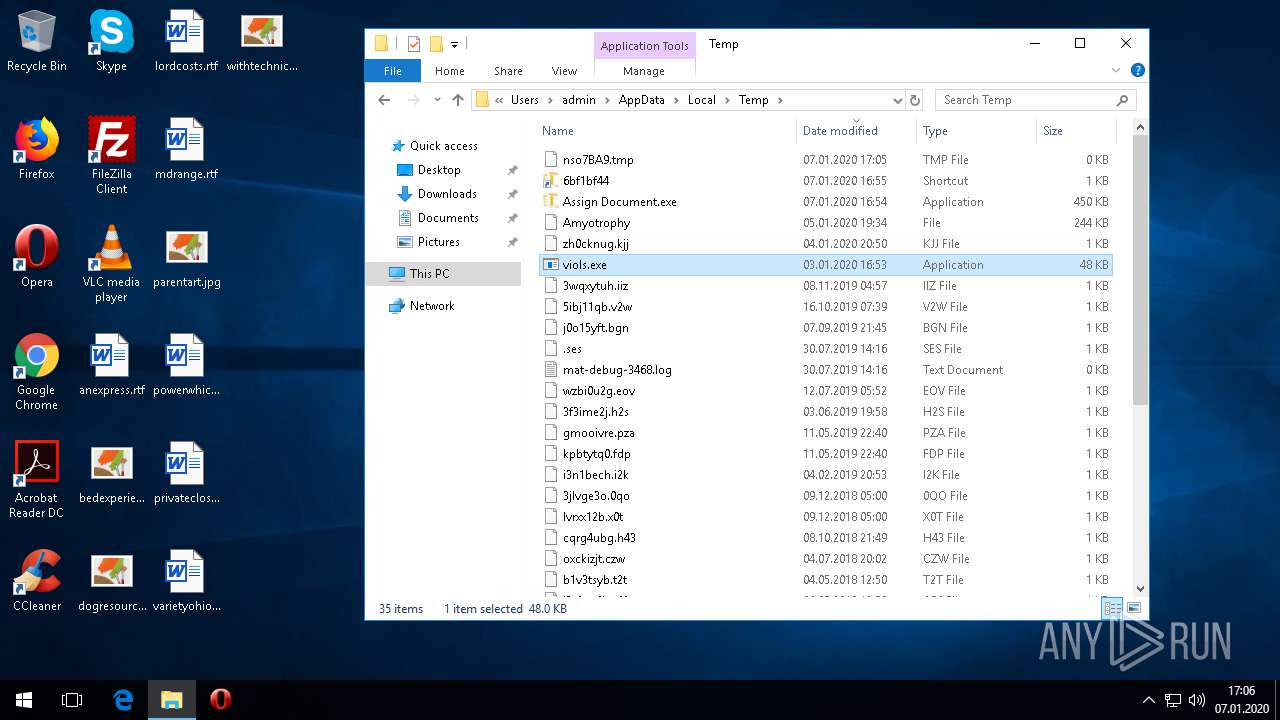
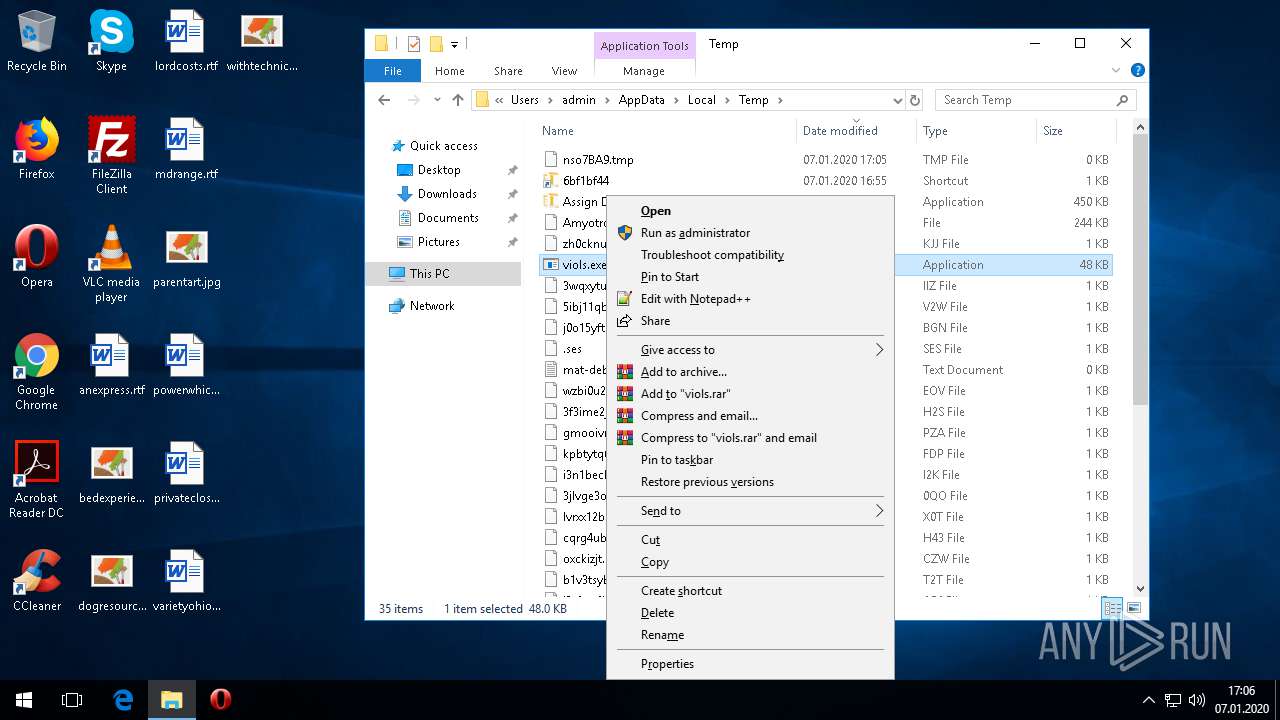
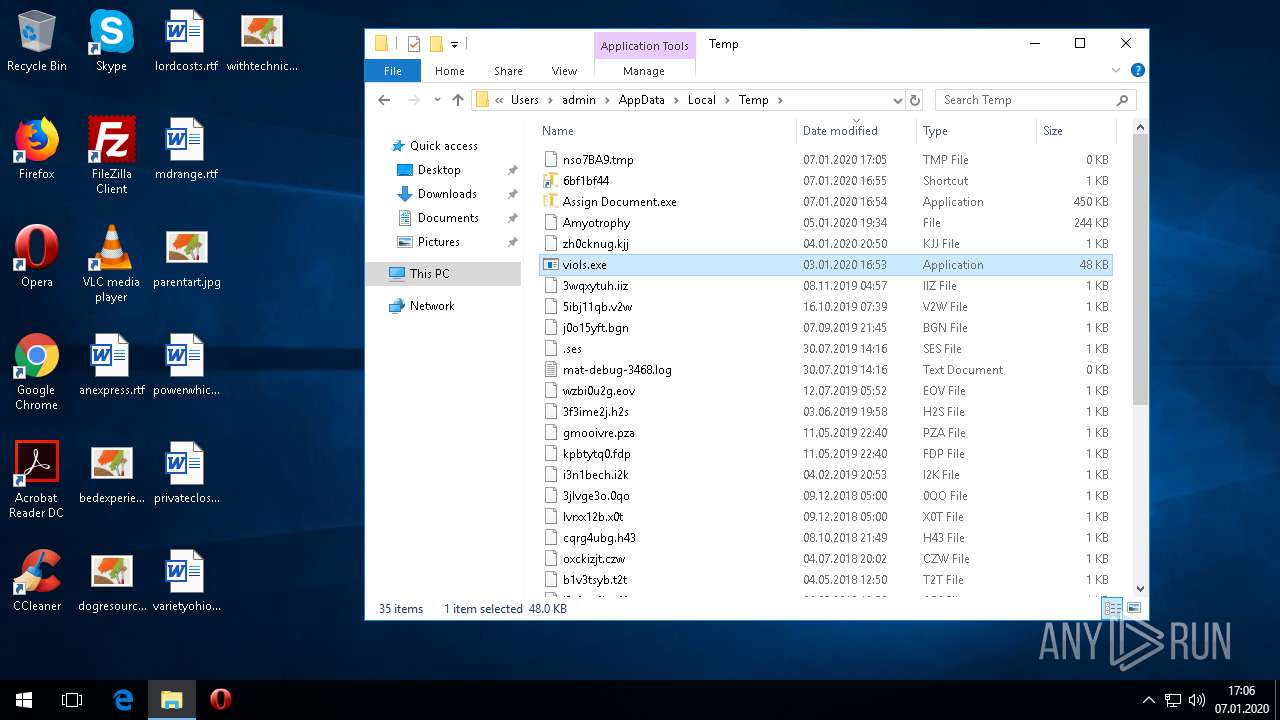
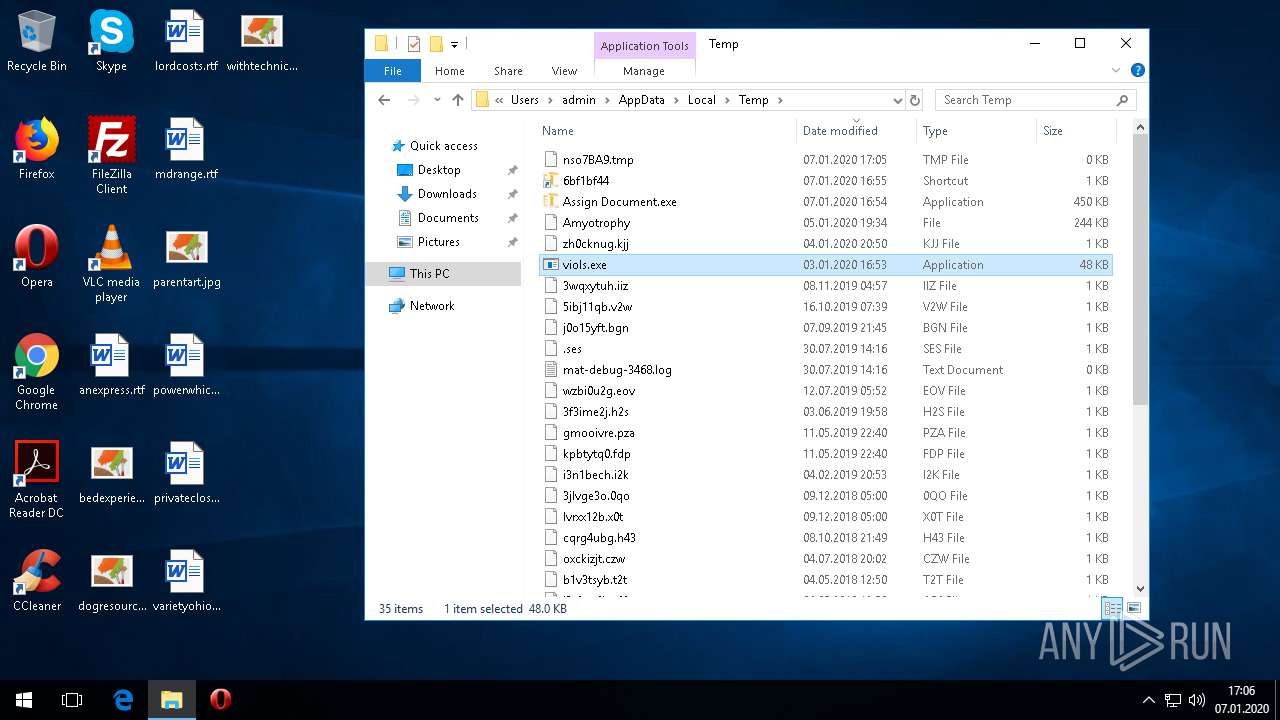
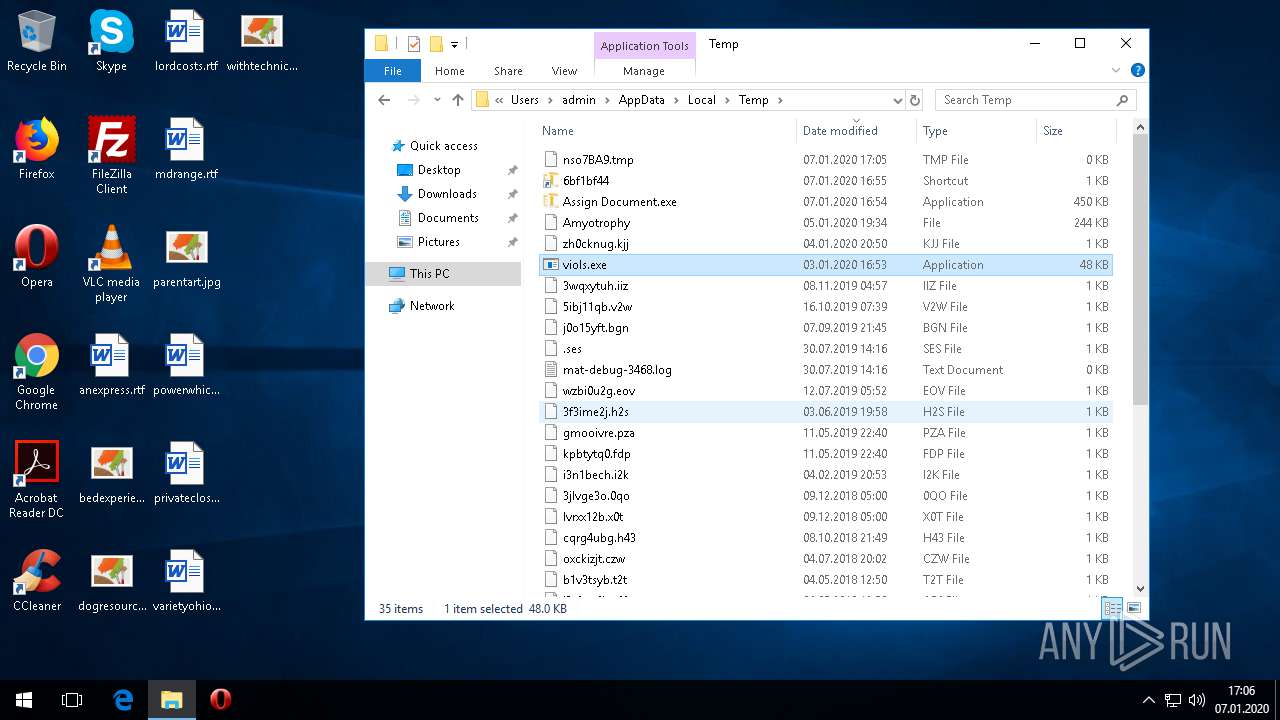
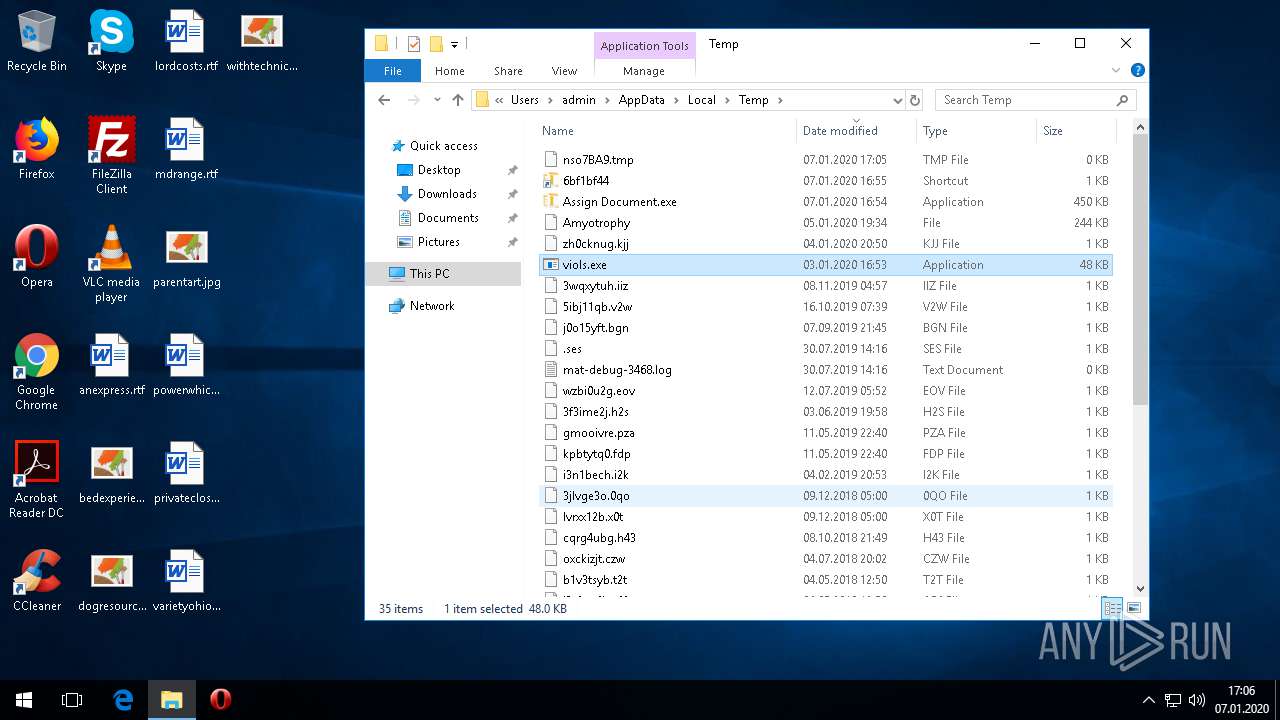
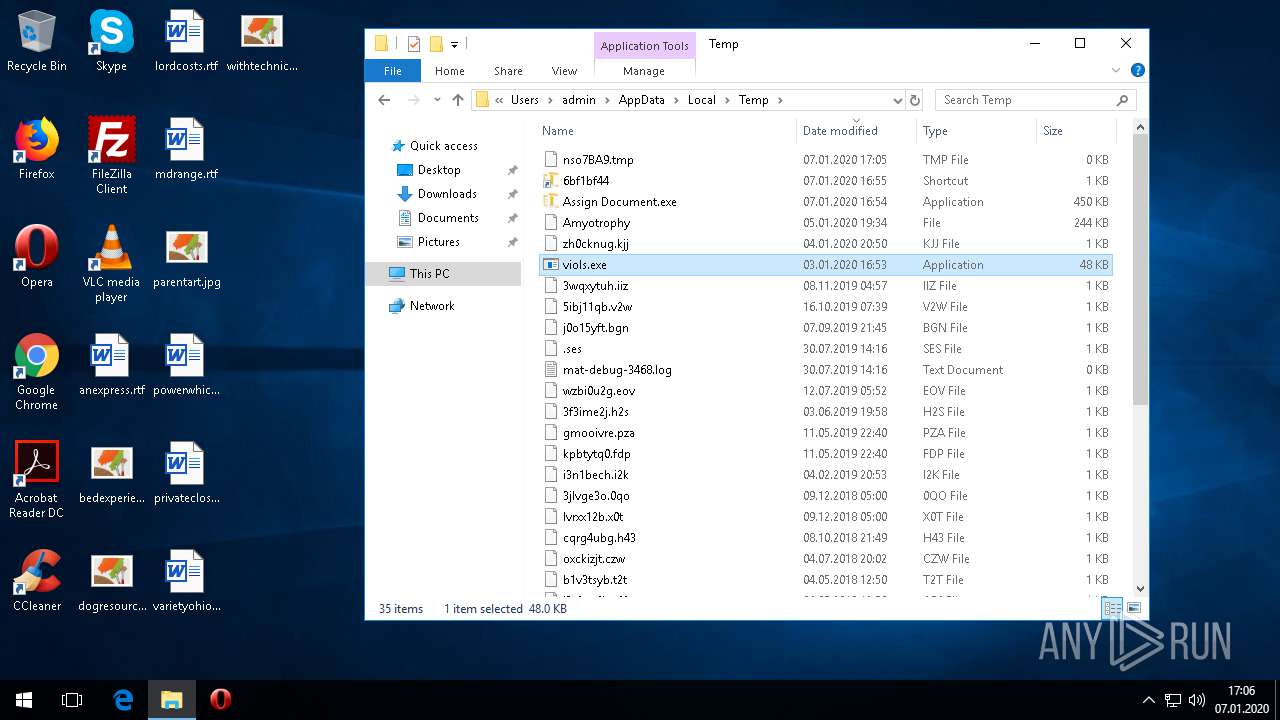
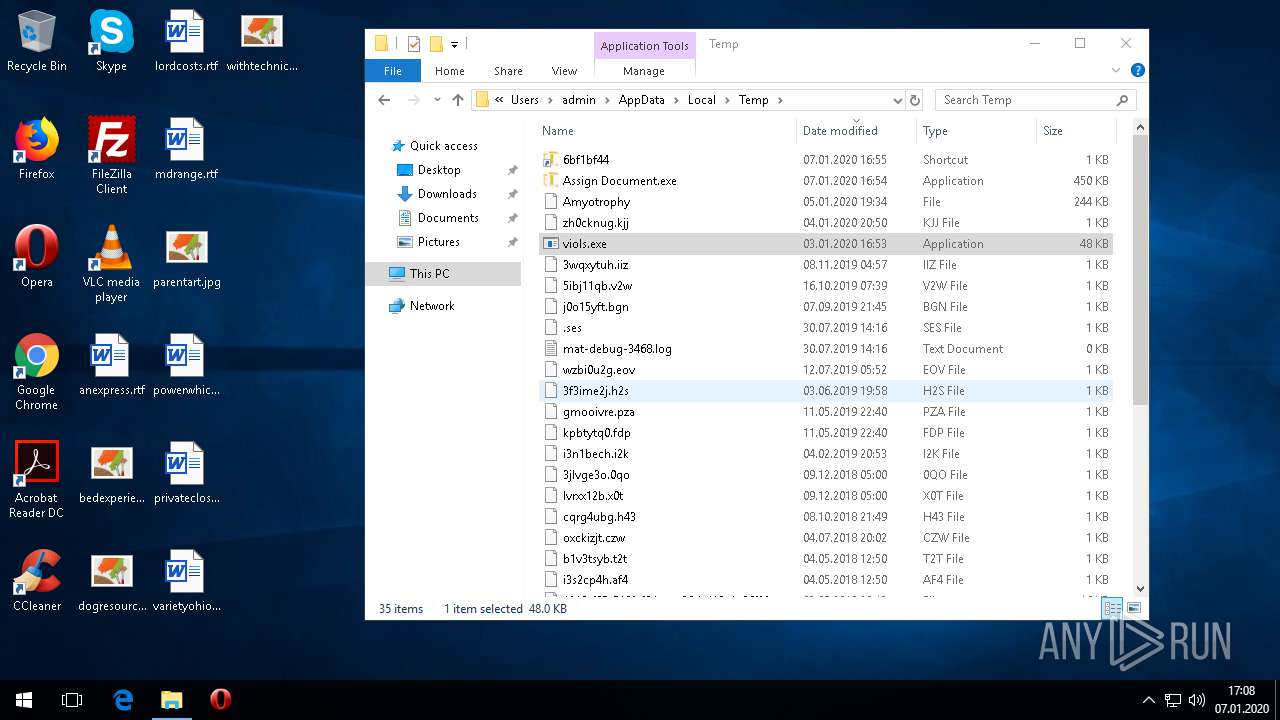
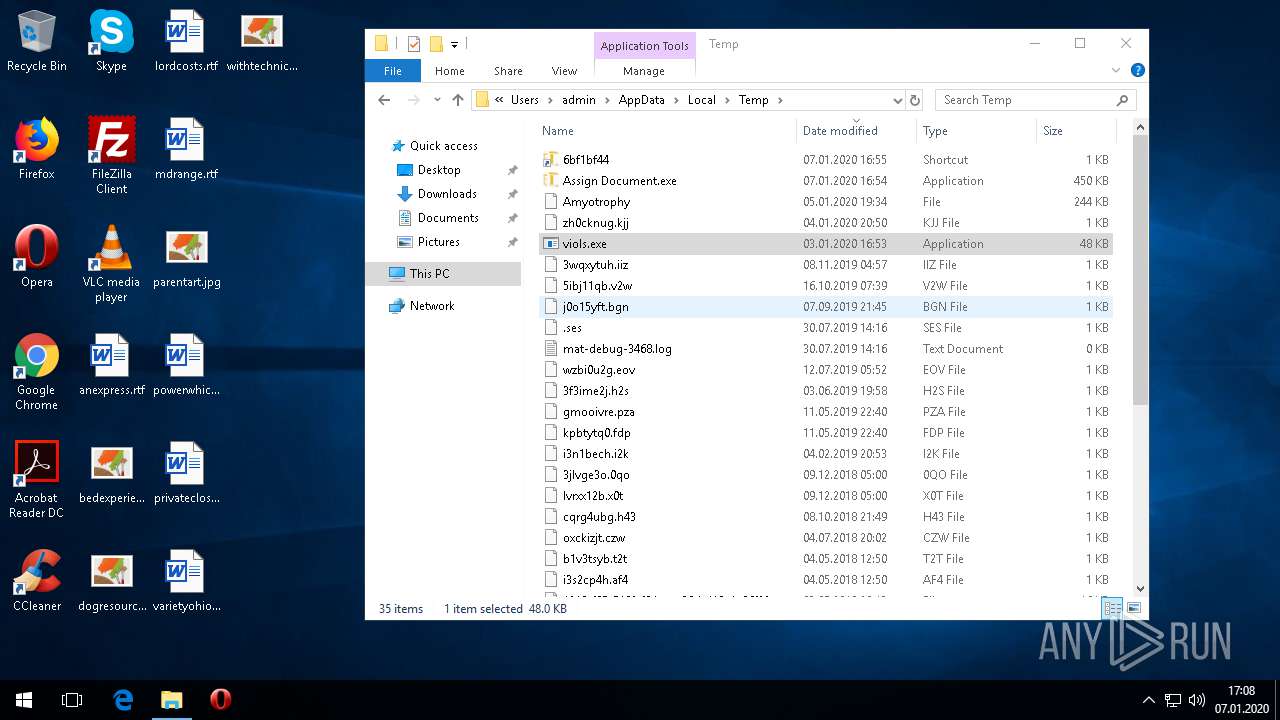
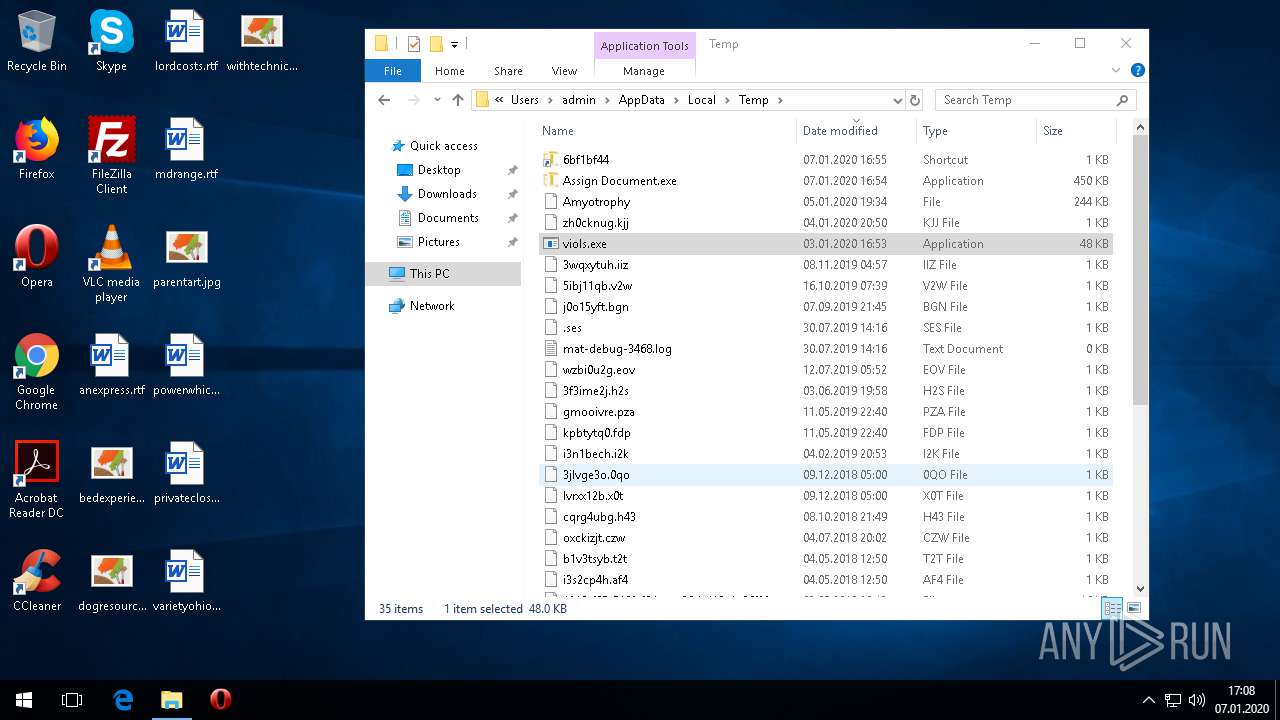
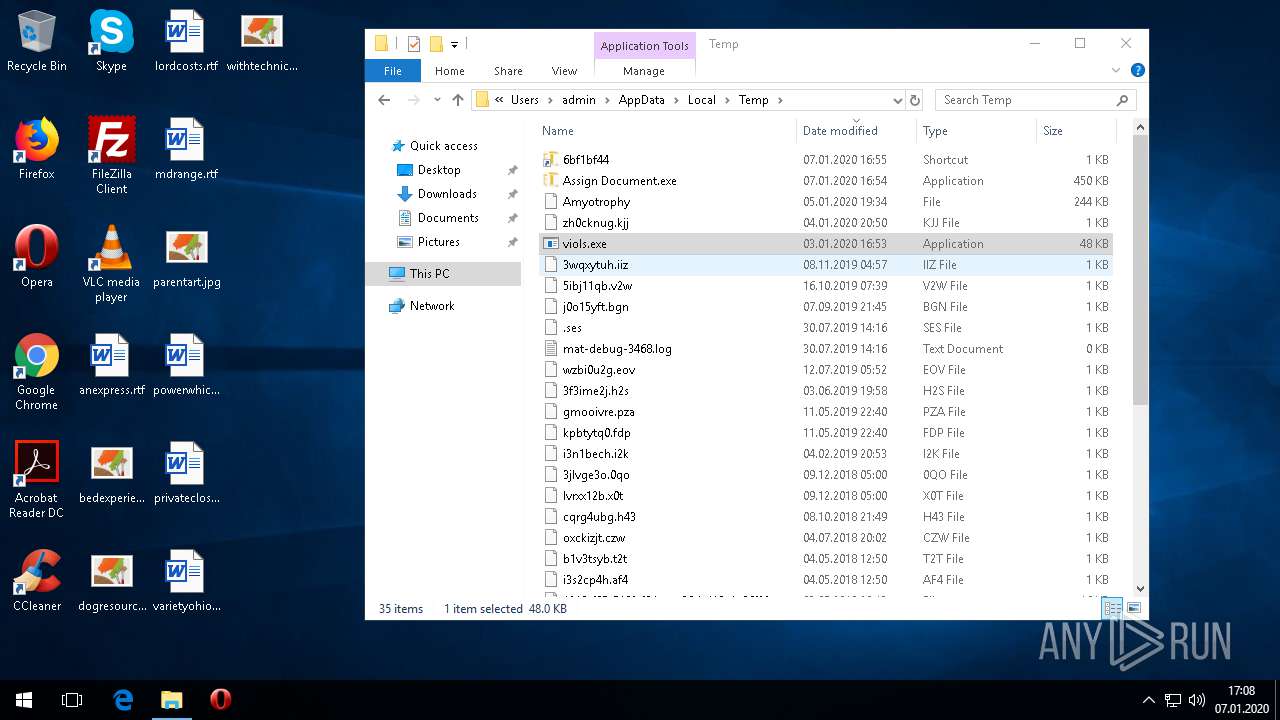
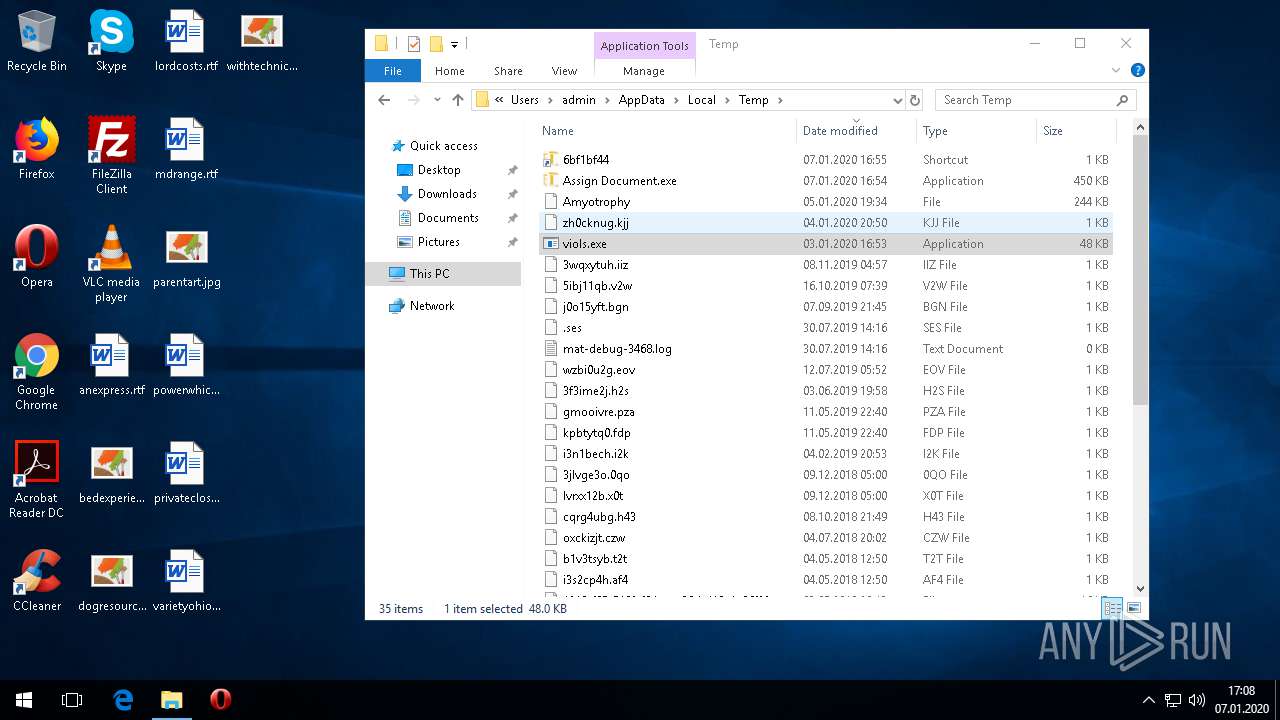
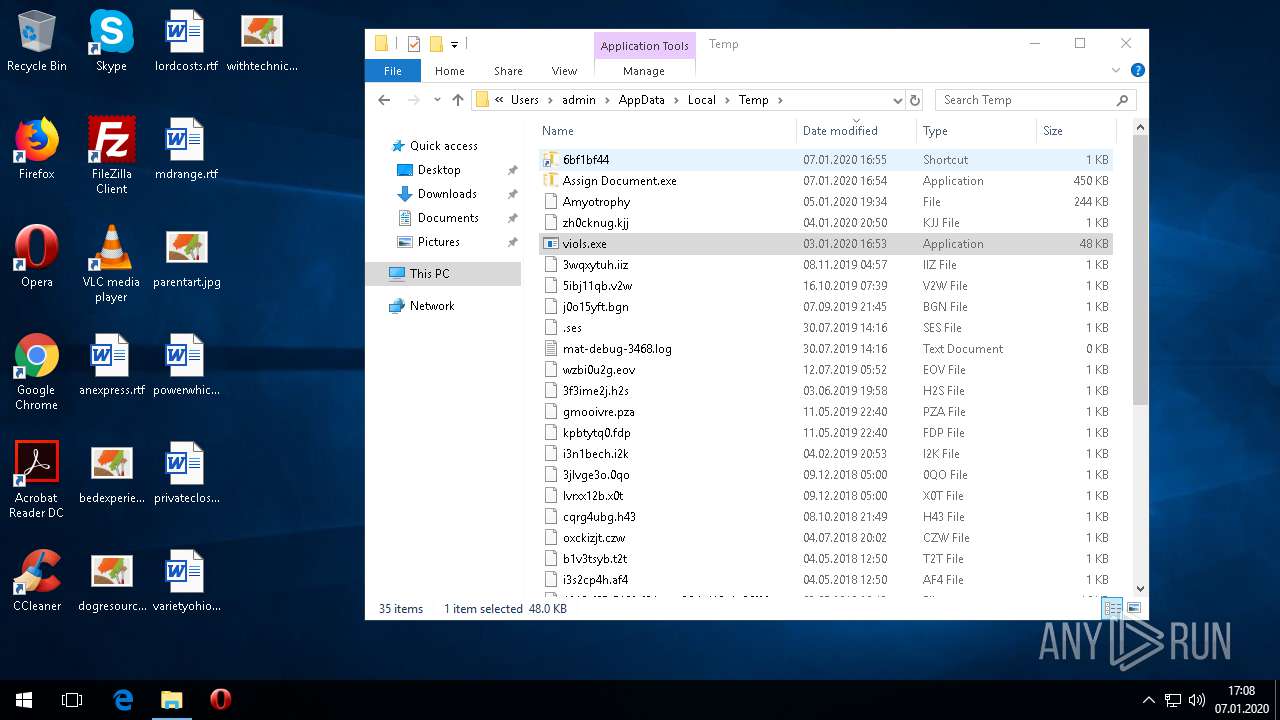
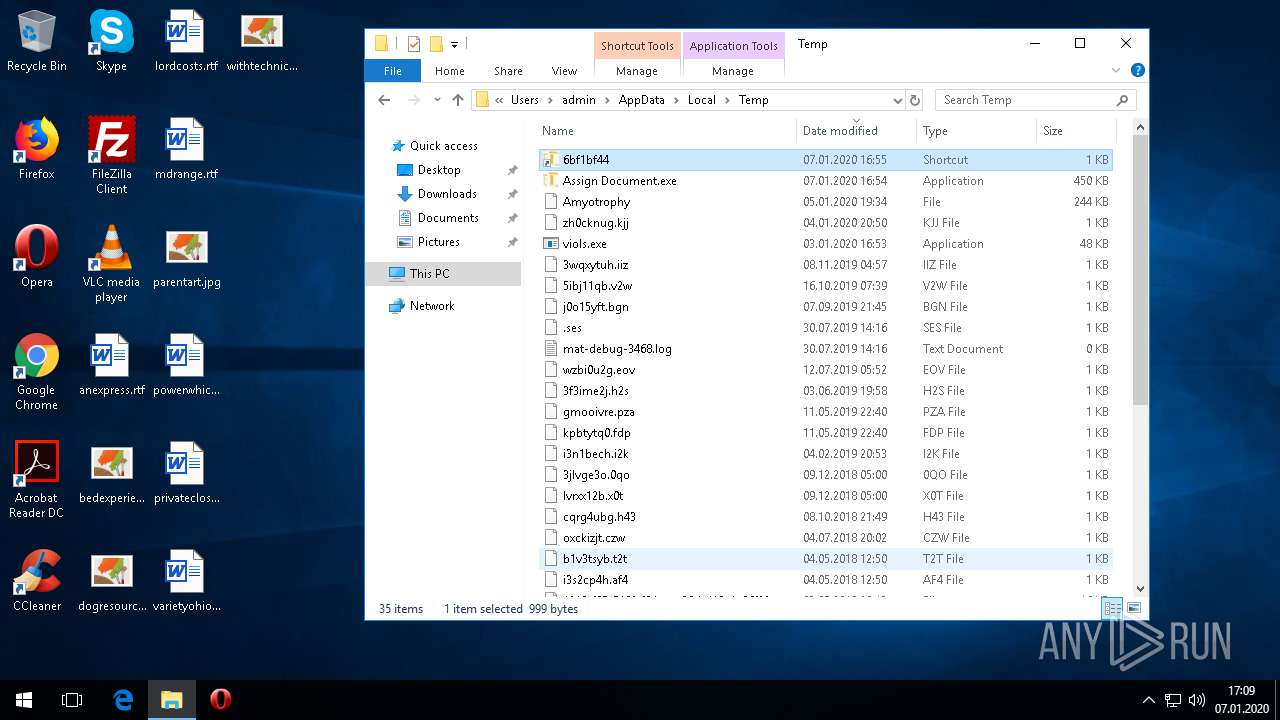
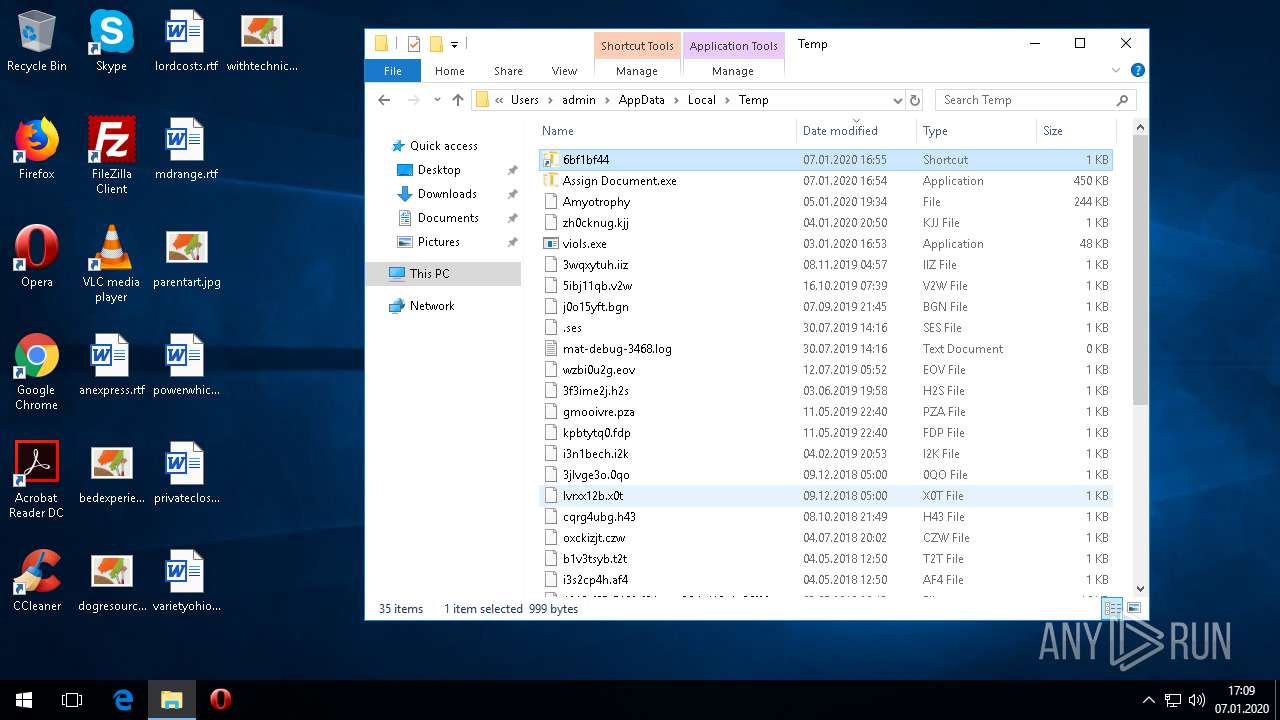
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\JConvert.exe | xml | |
MD5:12C8C3F33E65F2F0BFE9D4CC566DCD52 | SHA256:2676EDF40299F52F249CE15EA1DA621C8019364B85647C54B9FEA2ABDBA85565 | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\examplescript | text | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\odcacolauto03.gif | image | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\f02intpatt11.gif | image | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\redir\09\project\decryption\wbsadmin\list-edit\scsihost.h | text | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\outer.rgs | text | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\indicator-keyboard-Ru-9.svg | image | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\vdtflavuil.dll | executable | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\selected\signaturepics\resources\compressed\scriptlet\secrets\image-svg+xml.png | image | |
MD5:— | SHA256:— | |||
| 3032 | Assign Document.exe | C:\Users\admin\AppData\Local\Temp\redir\09\project\decryption\wbsadmin\list-edit\dtpwdesignerfig06.gif | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
14
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
260 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 162.215.253.15:587 | mail.alhilaly-group.com | PDR | US | malicious |
1852 | svchost.exe | 20.186.48.46:443 | geo-prod.do.dsp.mp.microsoft.com | Microsoft Corporation | US | unknown |
1852 | svchost.exe | 104.96.140.83:443 | kv601.prod.do.dsp.mp.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
260 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
260 | svchost.exe | 40.90.22.191:443 | login.live.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
mail.alhilaly-group.com |
| malicious |
geo-prod.do.dsp.mp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
kv601.prod.do.dsp.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
— | — | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
— | — | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |