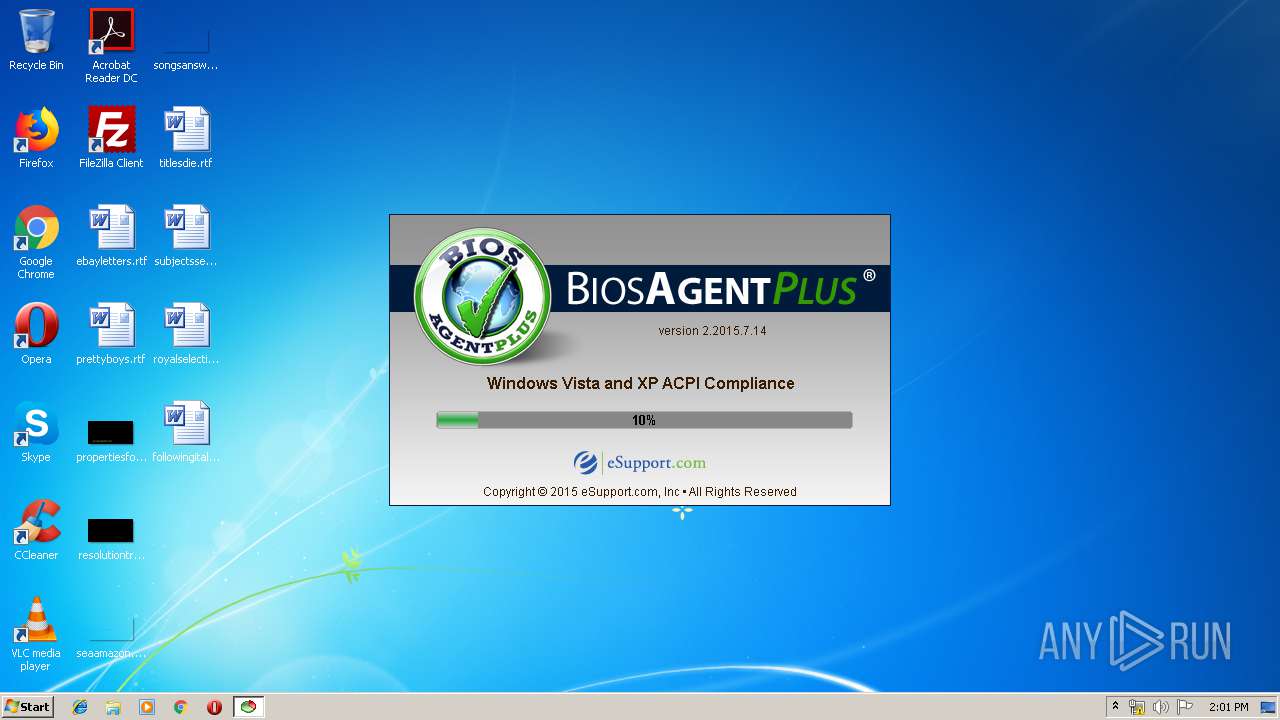
| File name: | biosagentplus_1583.virus |
| Full analysis: | https://app.any.run/tasks/a8b7539c-8a86-4f00-a7b5-e0b8ed00ec77 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2019, 13:01:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 60DC1B29934803C06E79B4097EA55EEB |
| SHA1: | 6A0585371E6C75094D80D5C0AD17597579686343 |
| SHA256: | E6EE1C7FDEC1A48D850EC281636288F059865CC8DFBE2A83B6437FF6206C4D7D |
| SSDEEP: | 12288:hzc3ztP/92xmsQxaKmn3Bj5e/AbKKJA2ta0/+NhAow6D9Xyw:6jtPMxmhxaL3BjgAbKKGz0/+VbDz |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 3324)
- explorer.exe (PID: 116)
SUSPICIOUS
Creates files in the Windows directory
- biosagentplus_1583.virus.exe (PID: 996)
Creates files in the driver directory
- biosagentplus_1583.virus.exe (PID: 996)
Uses RUNDLL32.EXE to load library
- biosagentplus_1583.virus.exe (PID: 996)
Searches for installed software
- biosagentplus_1583.virus.exe (PID: 996)
Low-level read access rights to disk partition
- biosagentplus_1583.virus.exe (PID: 996)
Executable content was dropped or overwritten
- biosagentplus_1583.virus.exe (PID: 996)
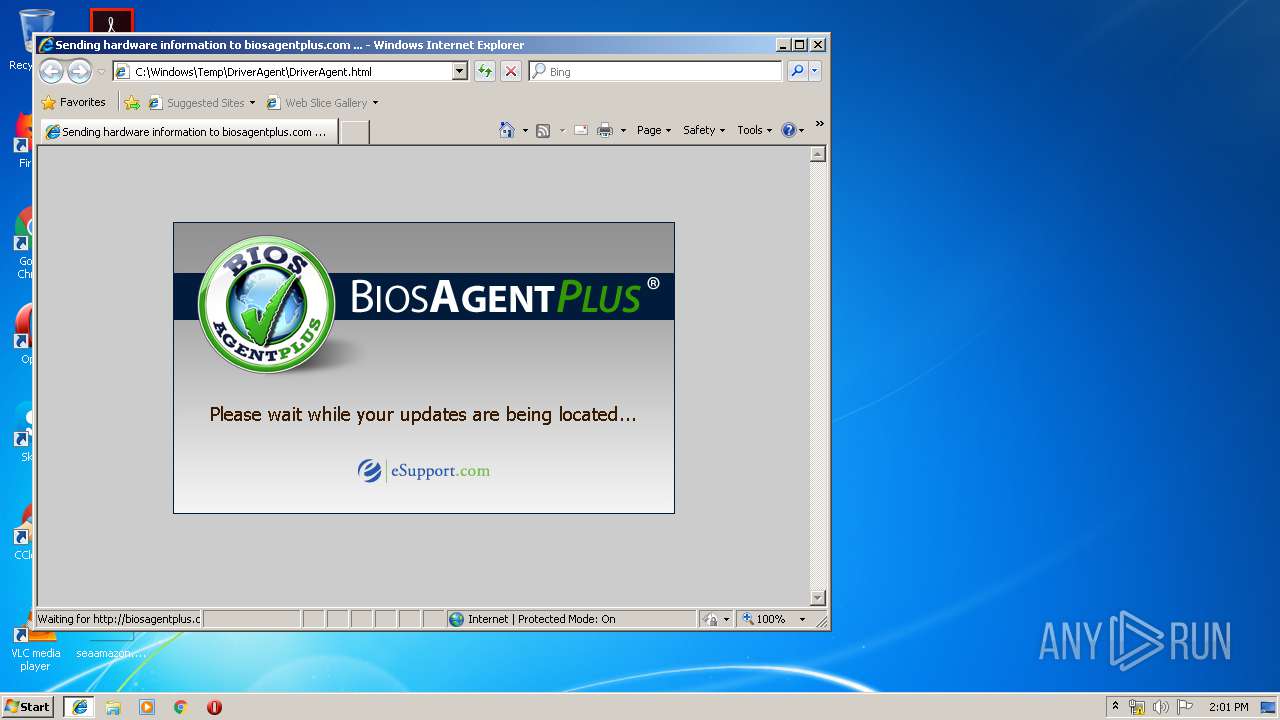
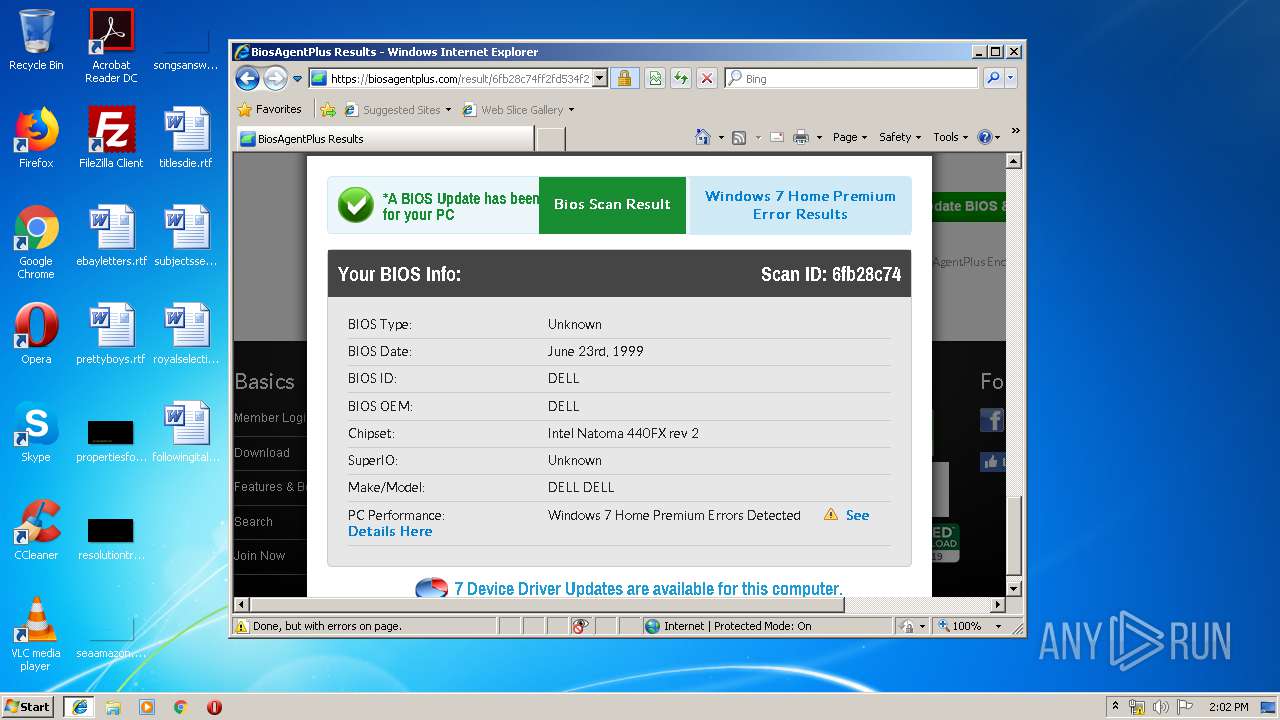
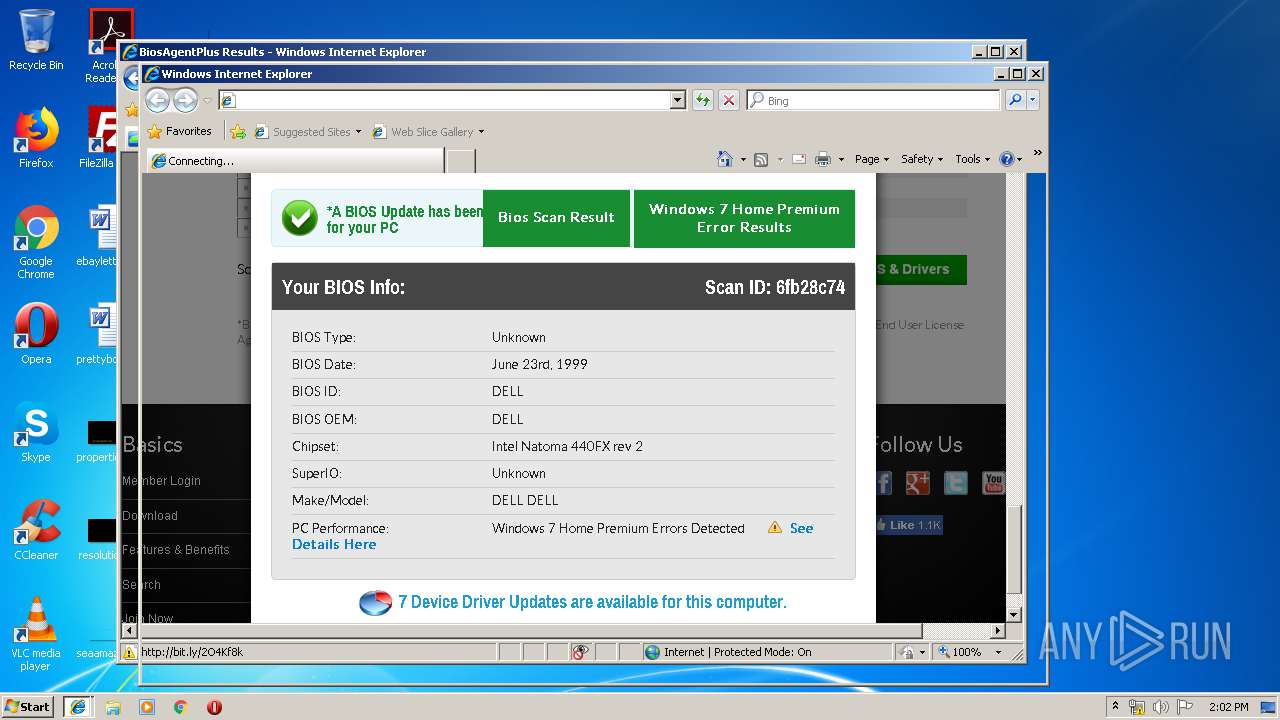
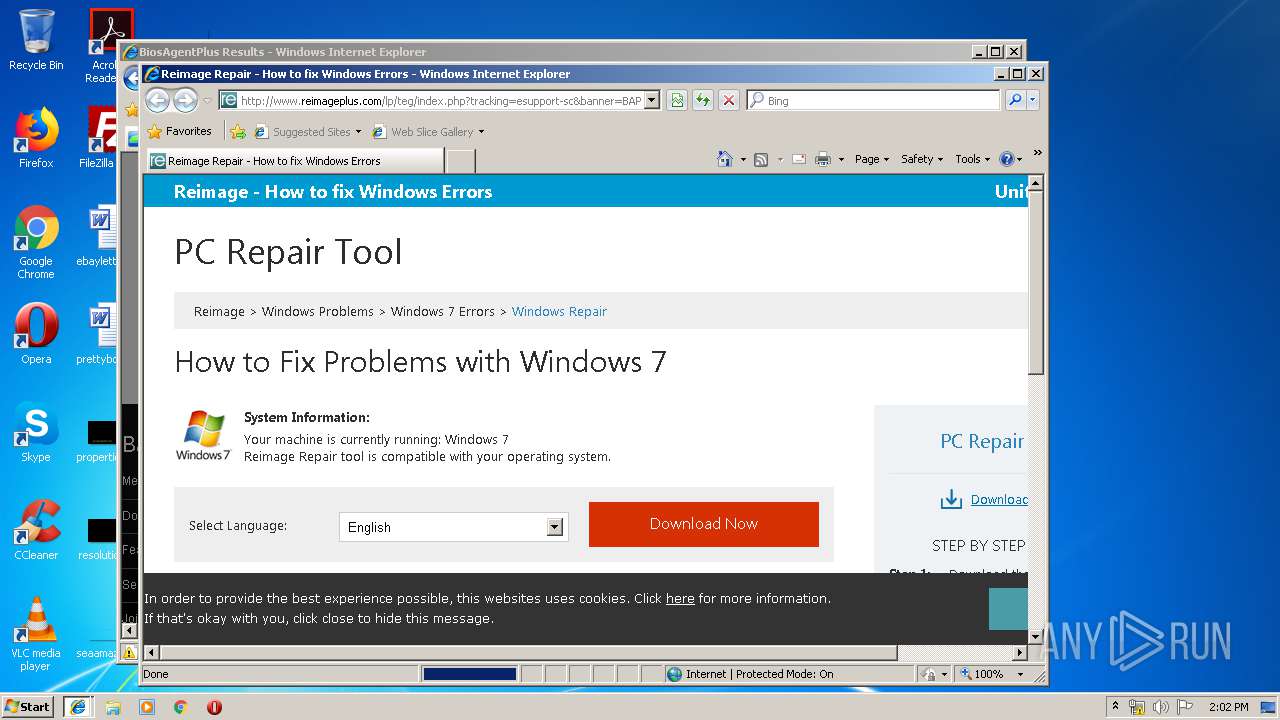
Starts Internet Explorer
- explorer.exe (PID: 116)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2088)
INFO
Manual execution by user
- iexplore.exe (PID: 2600)
Application launched itself
- iexplore.exe (PID: 2600)
Creates files in the user directory
- iexplore.exe (PID: 2600)
- iexplore.exe (PID: 1232)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2088)
- iexplore.exe (PID: 3520)
Changes internet zones settings
- iexplore.exe (PID: 2600)
Reads Internet Cache Settings
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 2600)
- iexplore.exe (PID: 3520)
Reads internet explorer settings
- iexplore.exe (PID: 1232)
- iexplore.exe (PID: 3520)
Reads settings of System Certificates
- iexplore.exe (PID: 2600)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2600)
Changes settings of System certificates
- iexplore.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (38.2) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (37.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.2) |
| .exe | | | Win32 Executable (generic) (6.3) |
| .exe | | | Win16/32 Executable Delphi generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:07:14 07:19:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 606208 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | 827392 |
| EntryPoint: | 0x15e7c0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2015.7.14 |
| ProductVersionNumber: | 2.2015.7.14 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Copyright © 2010 eSupport.com. All Rights Reserved. |
| FileDescription: | - |
| FileVersion: | 2.2015.7.14 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | DriverAgent |
| ProductName: | DriverAgent Application |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jul-2015 05:19:50 |
| Detected languages: |
|
| CompanyName: | Copyright © 2010 eSupport.com. All Rights Reserved. |
| FileDescription: | - |
| FileVersion: | 2.2015.7.14 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | DriverAgent |
| ProductName: | DriverAgent Application |
| ProductVersion: | 1.0.0.0 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Jul-2015 05:19:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x000CA000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x000CB000 | 0x00094000 | 0x00093A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.91261 |
.rsrc | 0x0015F000 | 0x0000D000 | 0x0000C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.3745 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03829 | 1165 | UNKNOWN | Russian - Russia | RT_MANIFEST |
2 | 5.88647 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 6.03757 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 7.95069 | 35924 | Cyrillic | UNKNOWN | RT_ICON |
5 | 7.20506 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 7.36591 | 560 | UNKNOWN | UNKNOWN | RT_STRING |
7 | 7.22515 | 308 | UNKNOWN | English - United States | RT_CURSOR |
100 | 7.84191 | 9352 | UNKNOWN | Russian - Russia | RT_RCDATA |
101 | 7.72411 | 18385 | UNKNOWN | Russian - Russia | RT_RCDATA |
102 | 7.67024 | 12510 | UNKNOWN | Russian - Russia | RT_RCDATA |
Imports
KERNEL32.DLL |
advapi32.dll |
cfgmgr32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
ole32.dll |
oleaut32.dll |
setupapi.dll |
shell32.dll |
Total processes
46
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | "C:\Users\admin\AppData\Local\Temp\biosagentplus_1583.virus.exe" | C:\Users\admin\AppData\Local\Temp\biosagentplus_1583.virus.exe | explorer.exe | ||||||||||||
User: admin Company: Copyright © 2010 eSupport.com. All Rights Reserved. Integrity Level: HIGH Exit code: 0 Version: 2.2015.7.14 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2600 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
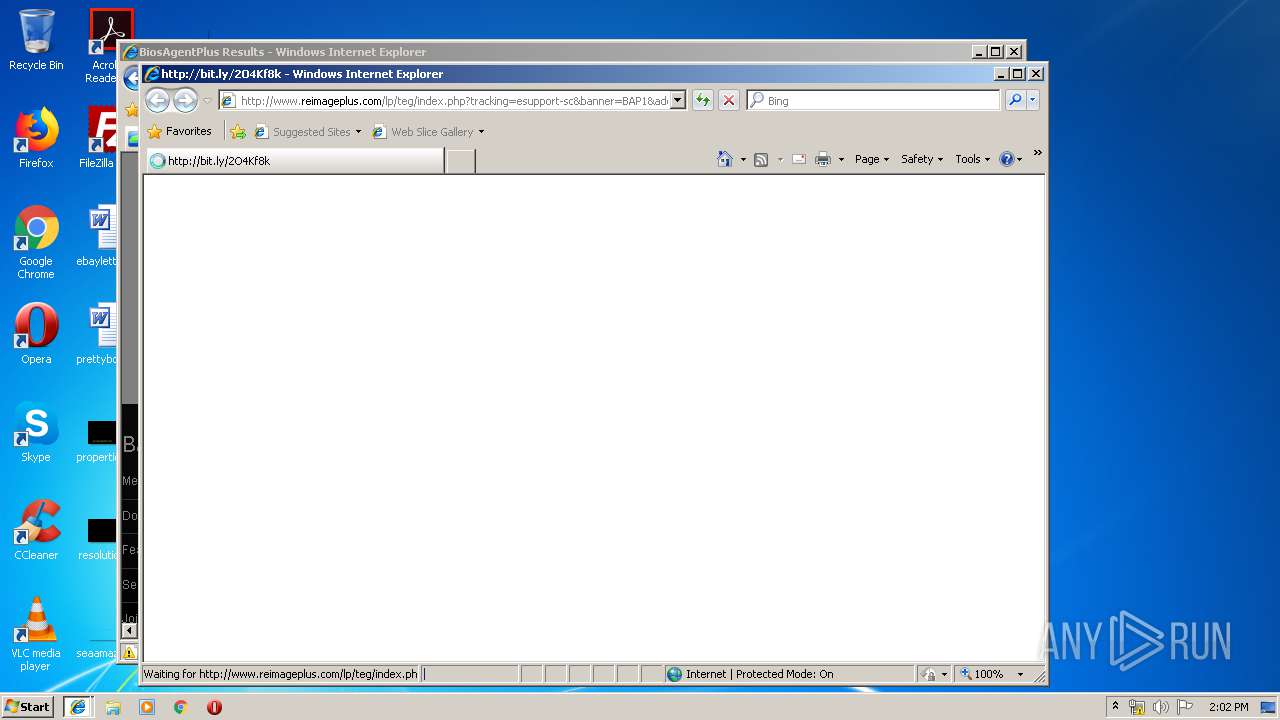
| 2600 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Windows\TEMP\DriverAgent\DriverAgent.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3324 | C:\Windows\system32\rundll32.exe C:\Users\admin\AppData\Local\Temp\launcher32.dll,launch "C:\Program Files\Internet Explorer\iexplore.exe" C:\Windows\TEMP\DriverAgent\DriverAgent.html | C:\Windows\system32\rundll32.exe | — | biosagentplus_1583.virus.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\biosagentplus_1583.virus.exe" | C:\Users\admin\AppData\Local\Temp\biosagentplus_1583.virus.exe | — | explorer.exe | |||||||||||
User: admin Company: Copyright © 2010 eSupport.com. All Rights Reserved. Integrity Level: MEDIUM Exit code: 3221226540 Version: 2.2015.7.14 Modules
| |||||||||||||||
| 3520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2600 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
916
Read events
749
Write events
162
Delete events
5
Modification events
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_CURRENT_USER\Software\eSupport.com\BIOSAgentPlus |
| Operation: | write | Name: | Source |
Value: 1583 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_CURRENT_USER\Software\eSupport.com\BIOSAgentPlus |
| Operation: | write | Name: | Change |
Value: 201906081401 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (996) biosagentplus_1583.virus.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\biosagentplus_1583_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
13
Text files
124
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 996 | biosagentplus_1583.virus.exe | C:\Windows\TEMP\DriverAgent\background.jpg | image | |
MD5:— | SHA256:— | |||
| 1232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\Q56WUWPL\6fb28c74ff2fd534f2c39f14d6a0fd70[1].txt | — | |
MD5:— | SHA256:— | |||
| 996 | biosagentplus_1583.virus.exe | C:\Windows\TEMP\DriverAgent\DriverAgent.html | html | |
MD5:— | SHA256:— | |||
| 1232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1232 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@secure.esupport[1].txt | text | |
MD5:— | SHA256:— | |||
| 2600 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019060820190609\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012019060820190609\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
61
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
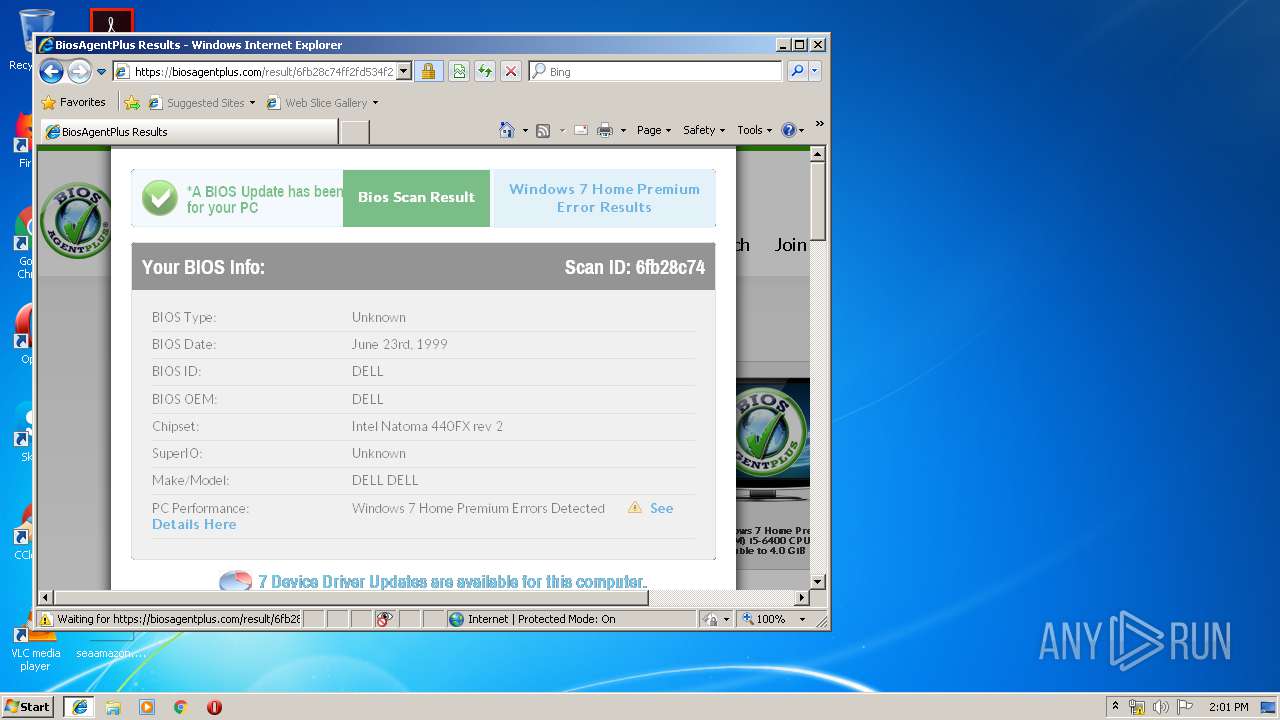
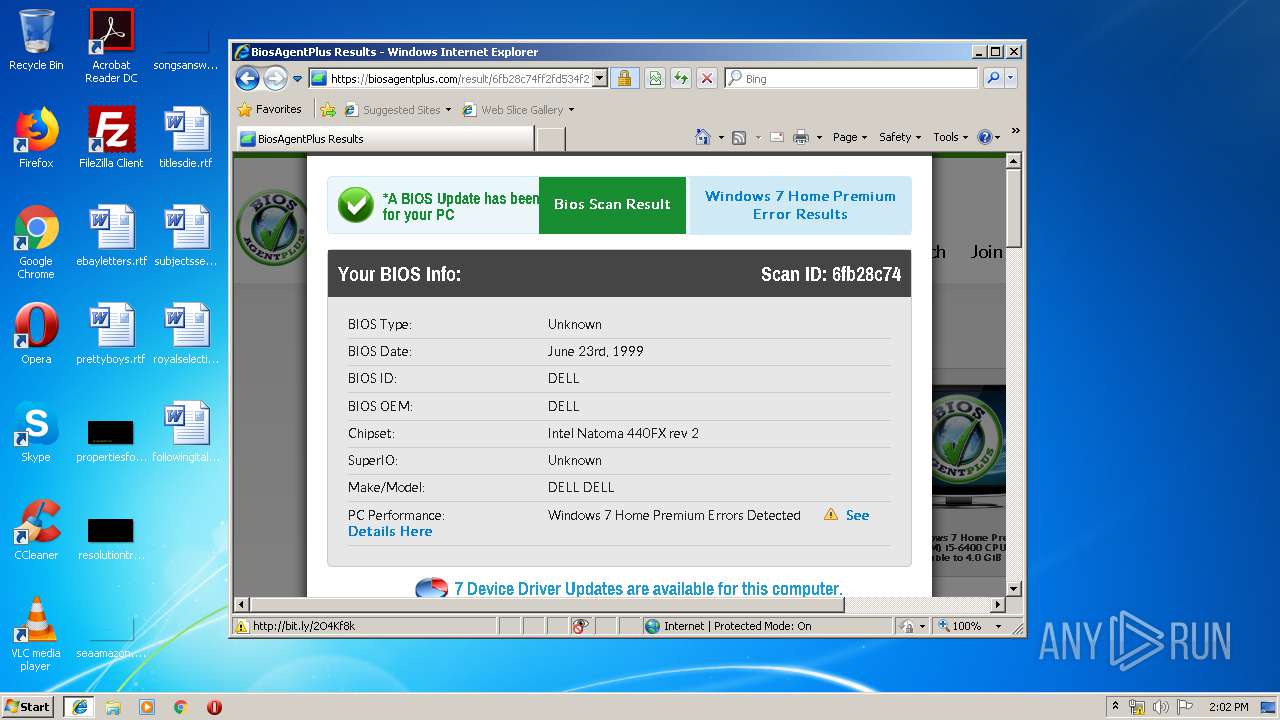
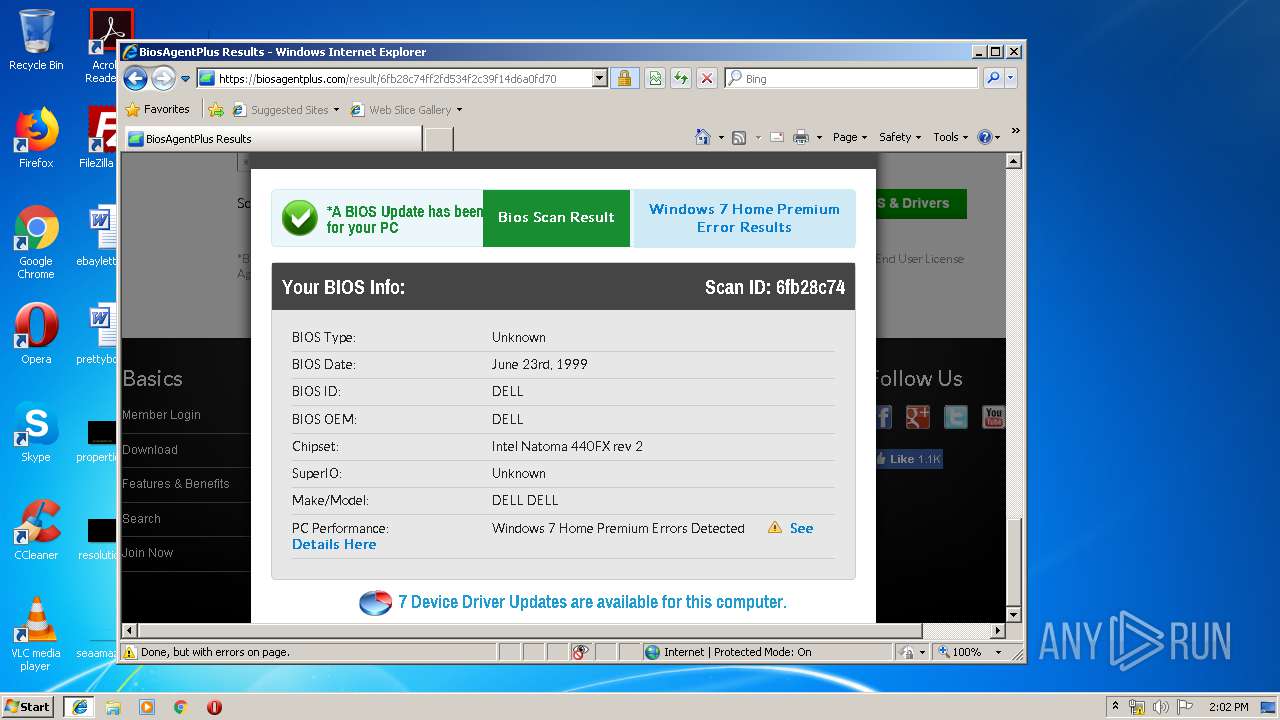
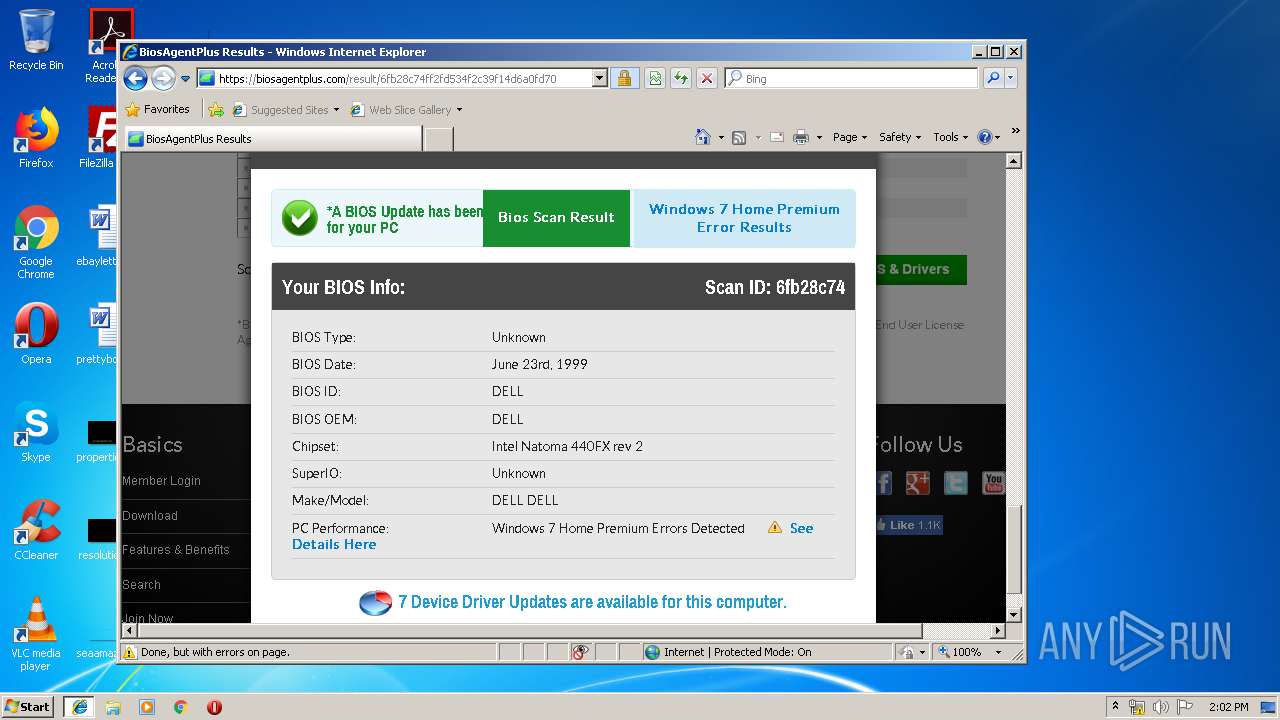
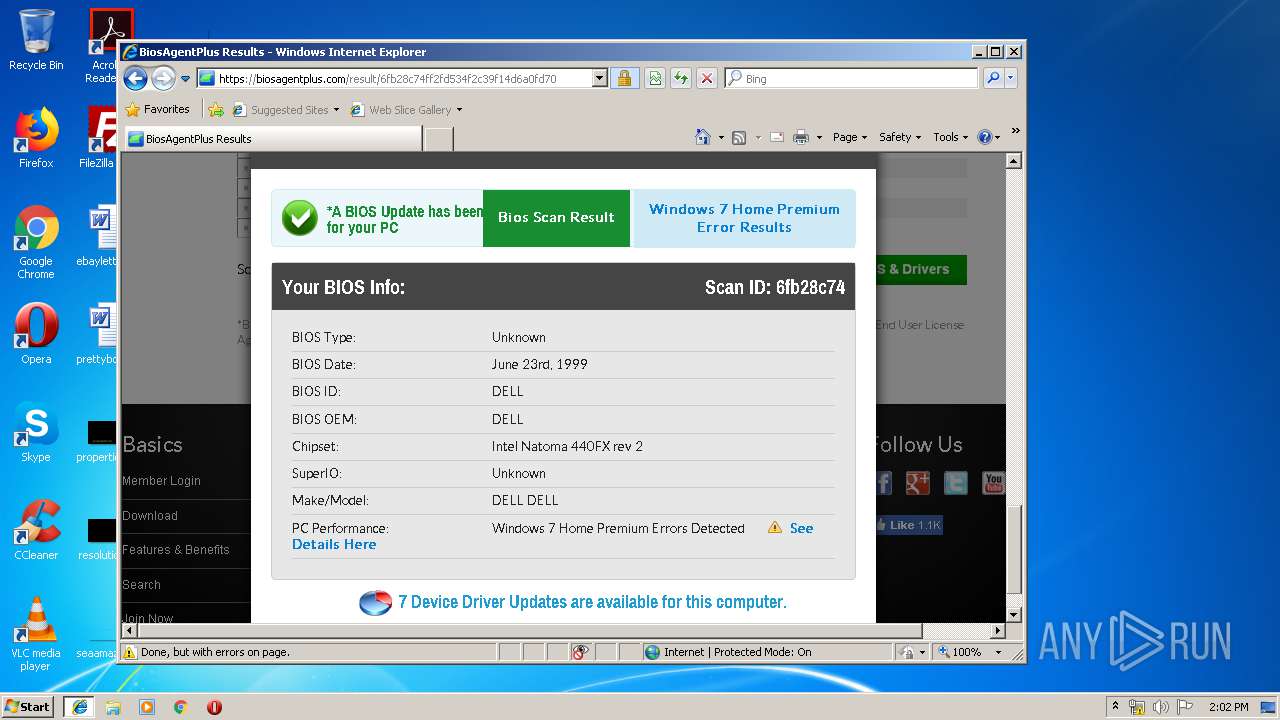
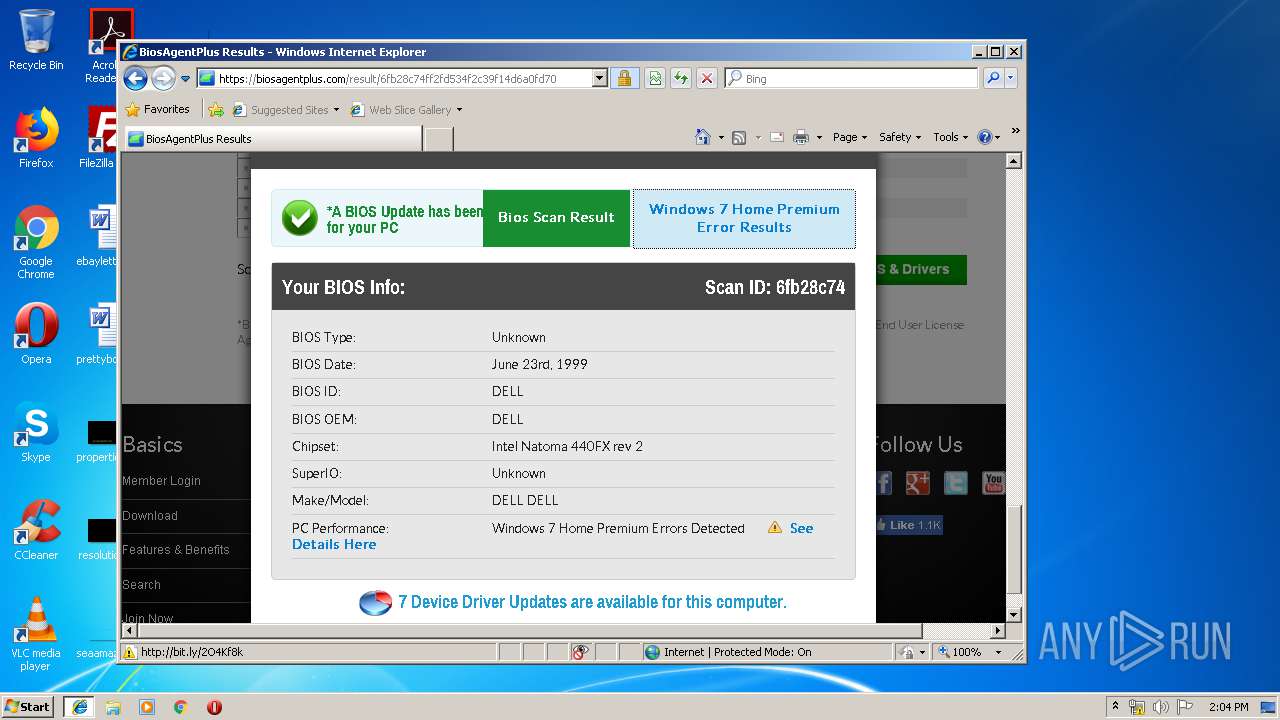
1232 | iexplore.exe | POST | 302 | 18.214.34.242:80 | http://biosagentplus.com/post_results.php | US | — | — | whitelisted |
1232 | iexplore.exe | GET | 301 | 18.214.34.242:80 | http://biosagentplus.com/result/6fb28c74ff2fd534f2c39f14d6a0fd70 | US | html | 356 b | whitelisted |
1232 | iexplore.exe | GET | 301 | 18.214.34.242:80 | http://biosagentplus.com/global/inc/setsid.php?pcid=1d117ef6e1c35d58054c7b98f9a2810e&bounce=http%3A%2F%2Fbiosagentplus.com%2Fresult%2F6fb28c74ff2fd534f2c39f14d6a0fd70&check=41714303&sess=0aj419m6kvjmvu61f93argqsr5 | US | html | 356 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/tree_i.gif | US | image | 99 b | whitelisted |
1232 | iexplore.exe | GET | 301 | 18.214.34.242:80 | http://biosagentplus.com/result/6fb28c74ff2fd534f2c39f14d6a0fd70 | US | html | 356 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/icon_mycomp.gif | US | image | 171 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/tree_l.gif | US | image | 94 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/icon_diskdrives.gif | US | image | 289 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/icon_network.gif | US | image | 217 b | whitelisted |
1232 | iexplore.exe | GET | 200 | 35.168.85.138:80 | http://driveragent.com/img/icon_port.gif | US | image | 148 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1232 | iexplore.exe | 216.58.208.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2600 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1232 | iexplore.exe | 18.214.34.242:80 | biosagentplus.com | — | US | unknown |
1232 | iexplore.exe | 18.214.34.242:443 | biosagentplus.com | — | US | unknown |
1232 | iexplore.exe | 52.205.218.143:443 | biosagentplus.com | Amazon.com, Inc. | US | unknown |
1232 | iexplore.exe | 172.217.18.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1232 | iexplore.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1232 | iexplore.exe | 13.224.63.139:443 | dw26xg4lubooo.cloudfront.net | — | US | unknown |
1232 | iexplore.exe | 52.44.156.154:443 | www.dlshield.com | Amazon.com, Inc. | US | unknown |
1232 | iexplore.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
biosagentplus.com |
| whitelisted |
www.bing.com |
| whitelisted |
secure.esupport.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
driveragent.com |
| whitelisted |