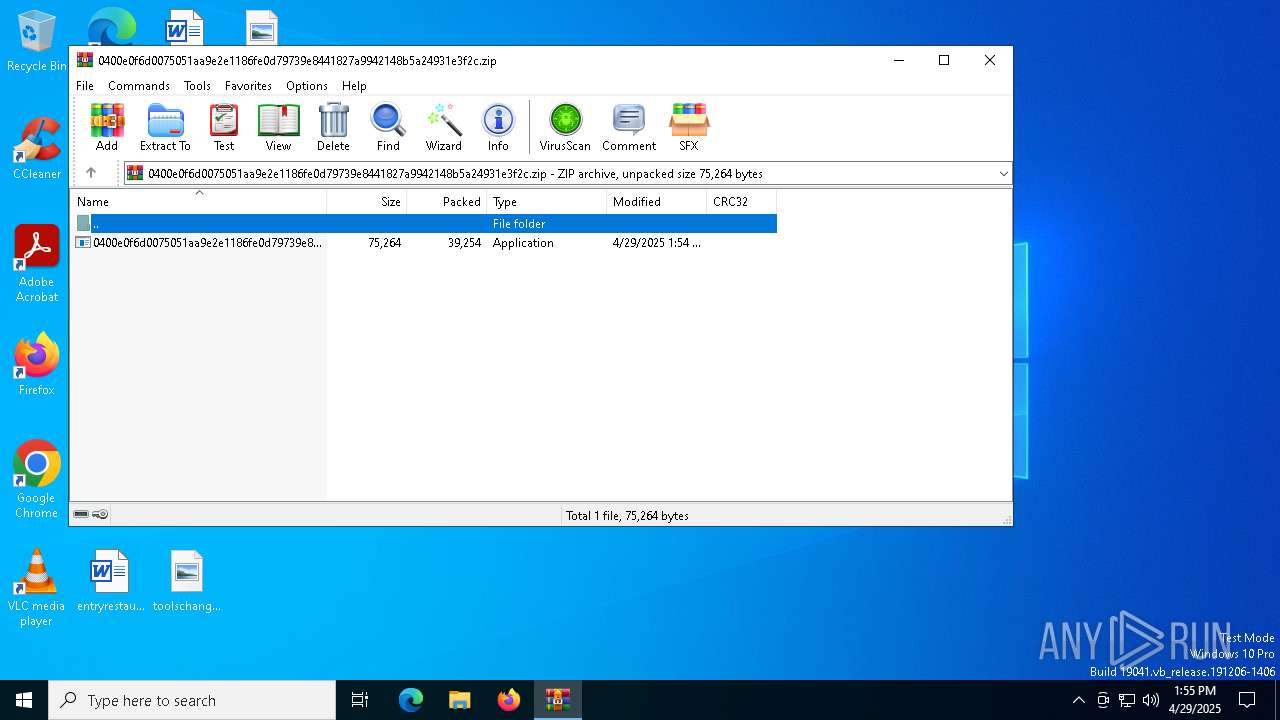
| File name: | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.zip |
| Full analysis: | https://app.any.run/tasks/8b132740-6d12-40e6-8d6f-fbbc755b38da |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | April 29, 2025, 13:54:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
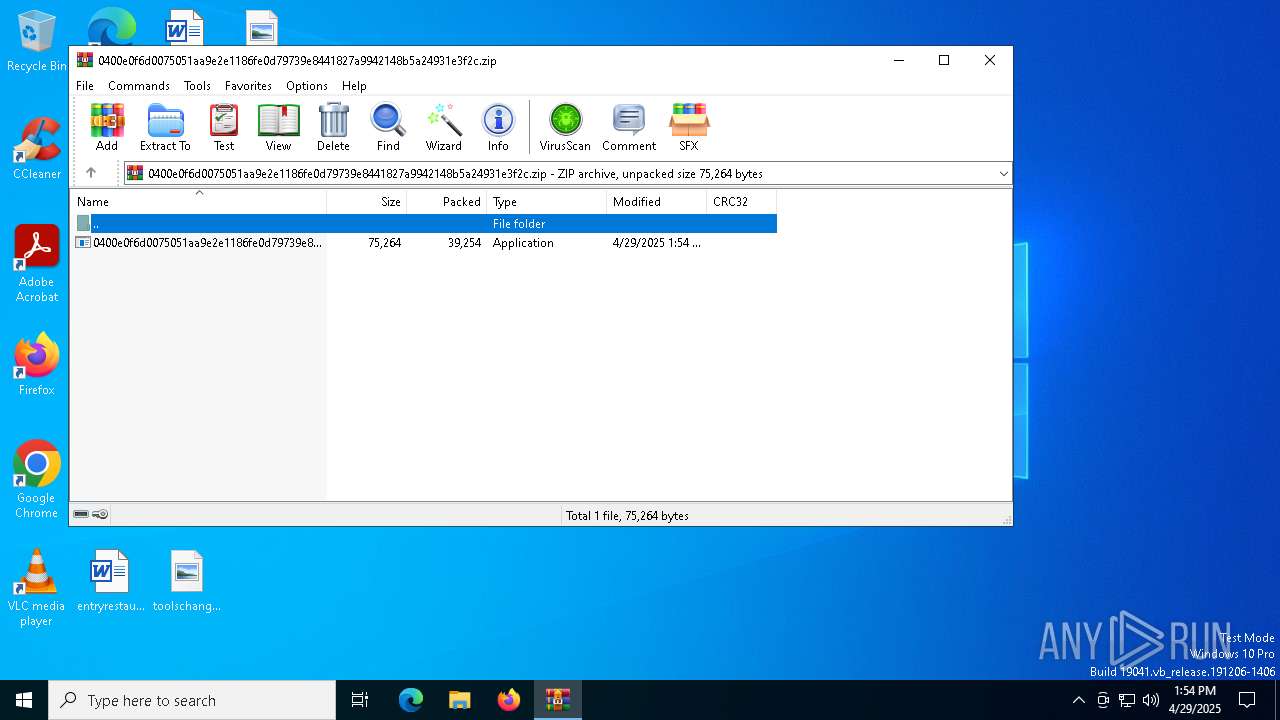
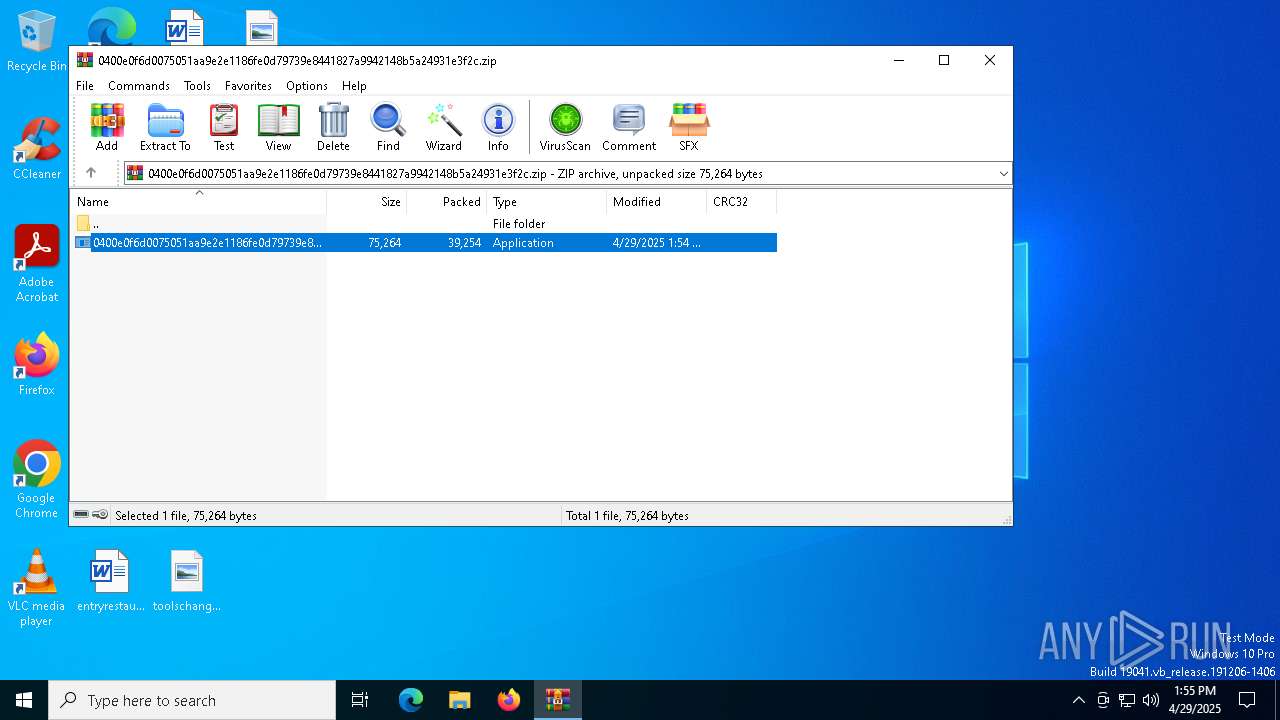
| MIME: | application/zip |
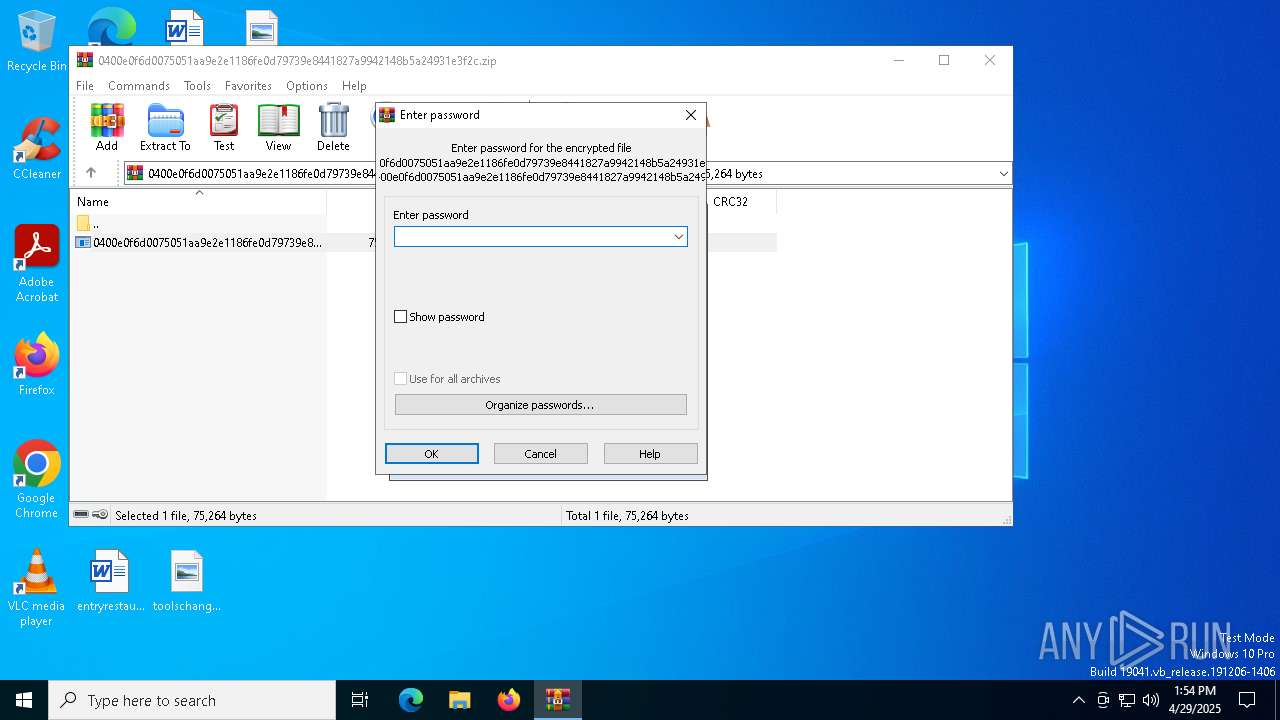
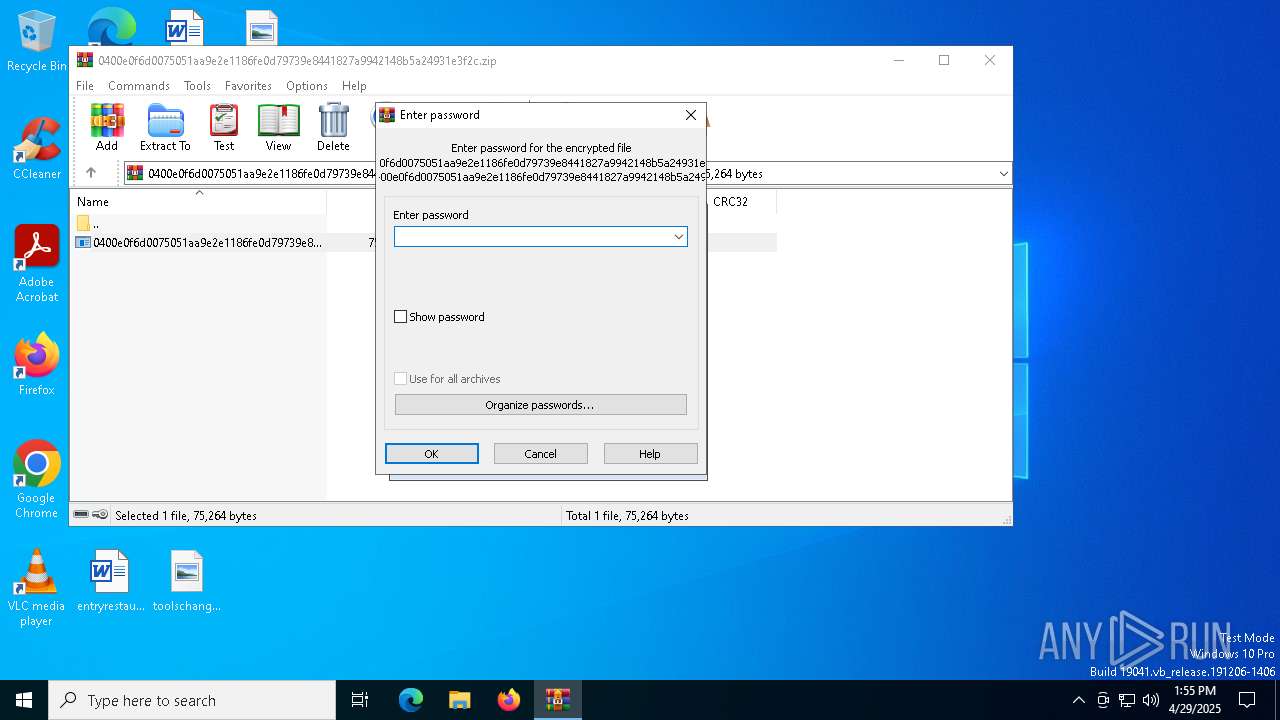
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 53AE9CD2246FF6AE0978A275ACB36EC4 |
| SHA1: | 80C07E7E7472D83A1CA0220C8F278C56704192A6 |
| SHA256: | E6D6D5D8B6A59D39239F947DF387E6887B336EE6FC7A0A098EBC51BF34742DDD |
| SSDEEP: | 768:JR2SGMZqnXMzFs+1j2K4gkGegHQIpYDbFksKMeFkewedDYePoD3ZFM:pqkFs+17syQMMFkqfsPK3ZFM |
MALICIOUS
GANDCRAB mutex has been found
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 6068)
Changes the autorun value in the registry
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
GANDCRAB has been detected (SURICATA)
- nslookup.exe (PID: 5244)
- nslookup.exe (PID: 1240)
- nslookup.exe (PID: 8072)
- nslookup.exe (PID: 7864)
- nslookup.exe (PID: 3896)
- nslookup.exe (PID: 8132)
- nslookup.exe (PID: 7904)
- nslookup.exe (PID: 4844)
- nslookup.exe (PID: 7988)
- nslookup.exe (PID: 5728)
- nslookup.exe (PID: 6372)
- nslookup.exe (PID: 1164)
- nslookup.exe (PID: 7252)
- nslookup.exe (PID: 2644)
- nslookup.exe (PID: 1180)
- nslookup.exe (PID: 7592)
- nslookup.exe (PID: 5384)
- nslookup.exe (PID: 7420)
- nslookup.exe (PID: 7940)
- nslookup.exe (PID: 7832)
- nslookup.exe (PID: 2800)
- nslookup.exe (PID: 7196)
- nslookup.exe (PID: 2564)
- nslookup.exe (PID: 6988)
- nslookup.exe (PID: 1012)
GandCrab is detected
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7312)
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Checks for external IP
- svchost.exe (PID: 2196)
Uses NSLOOKUP.EXE to check DNS info
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
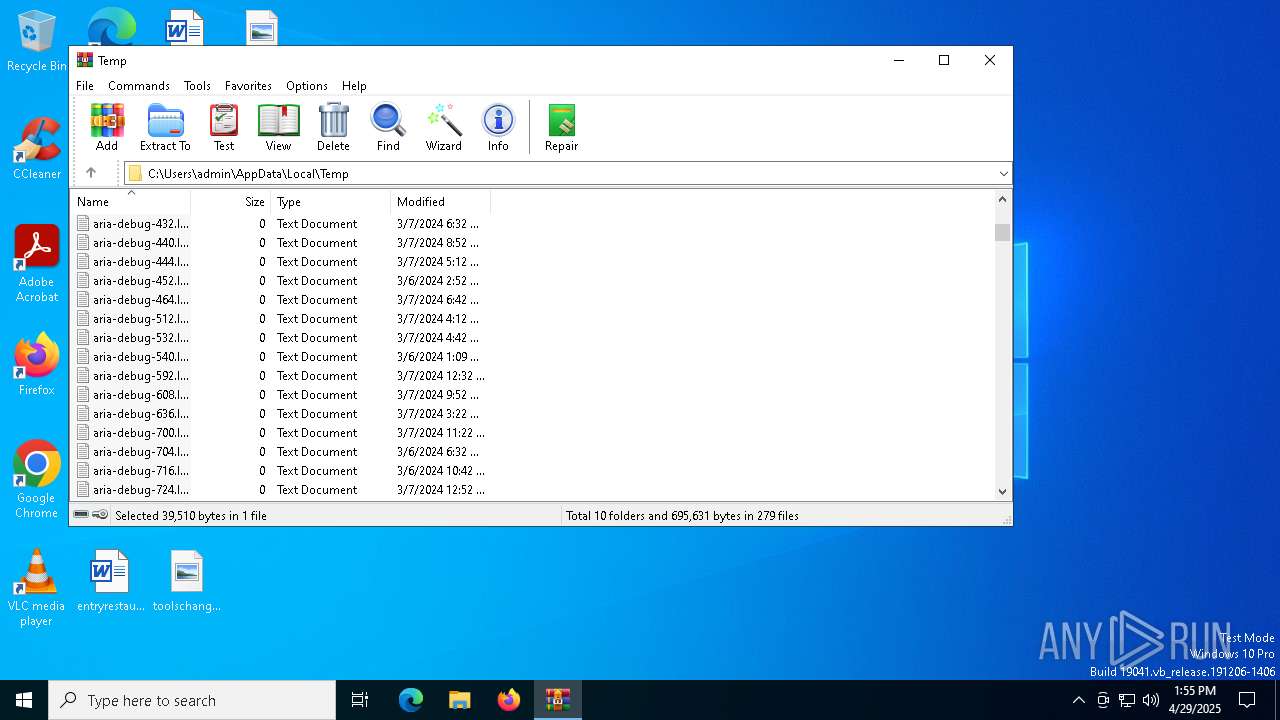
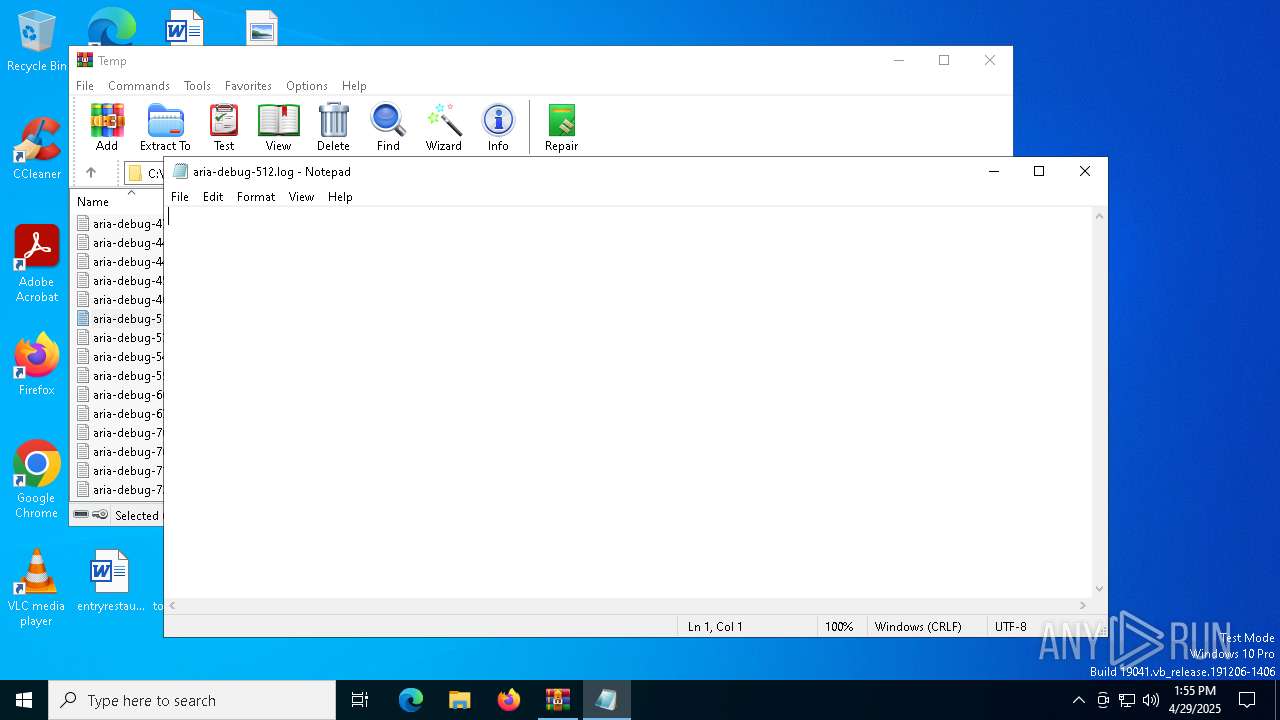
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 7312)
INFO
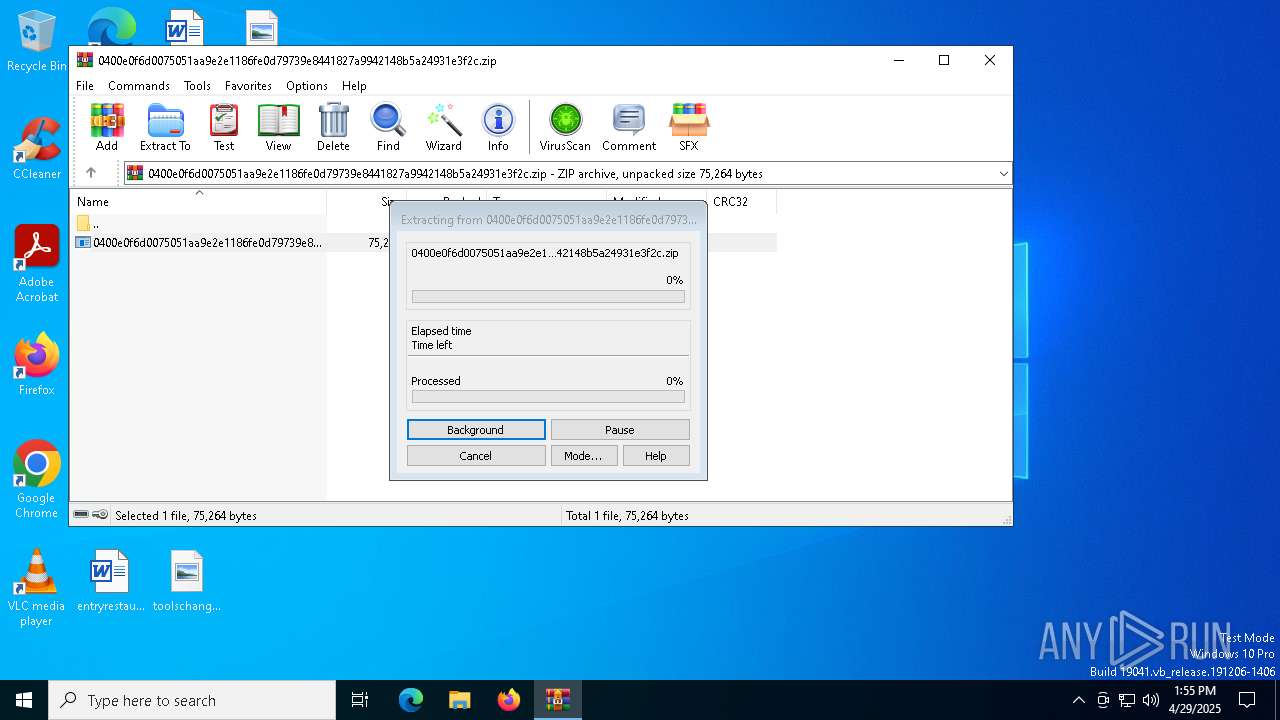
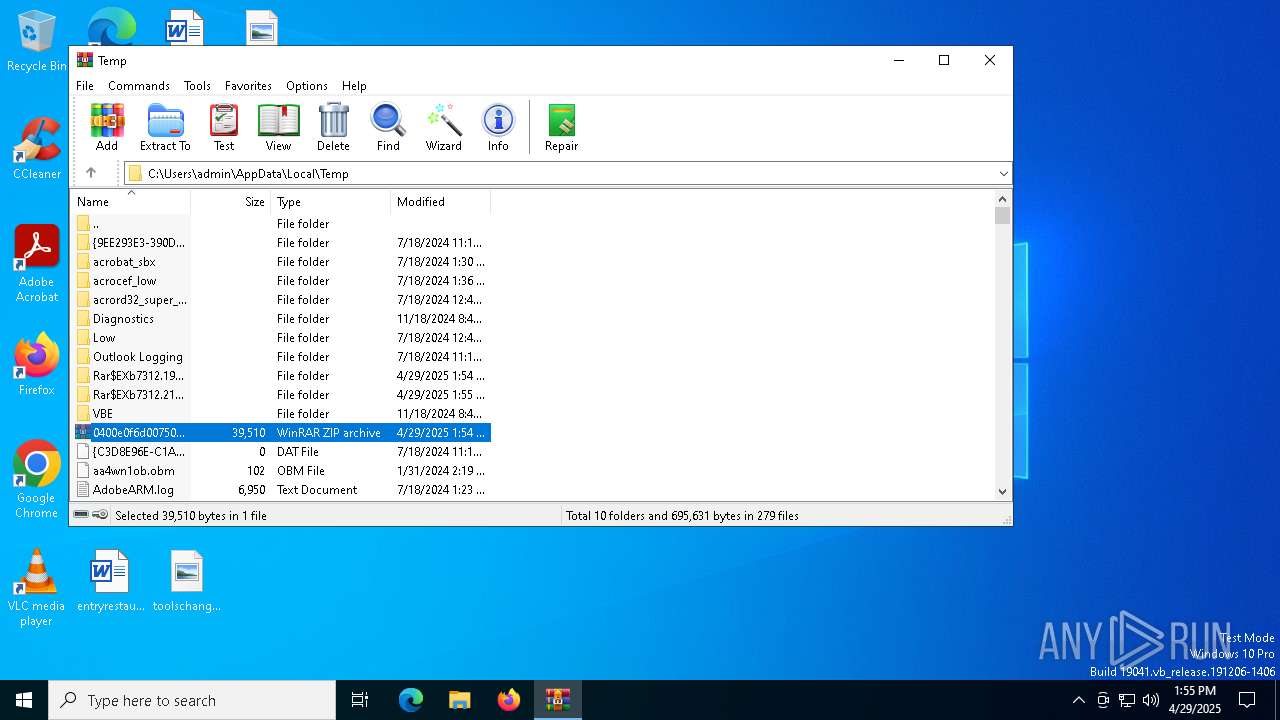
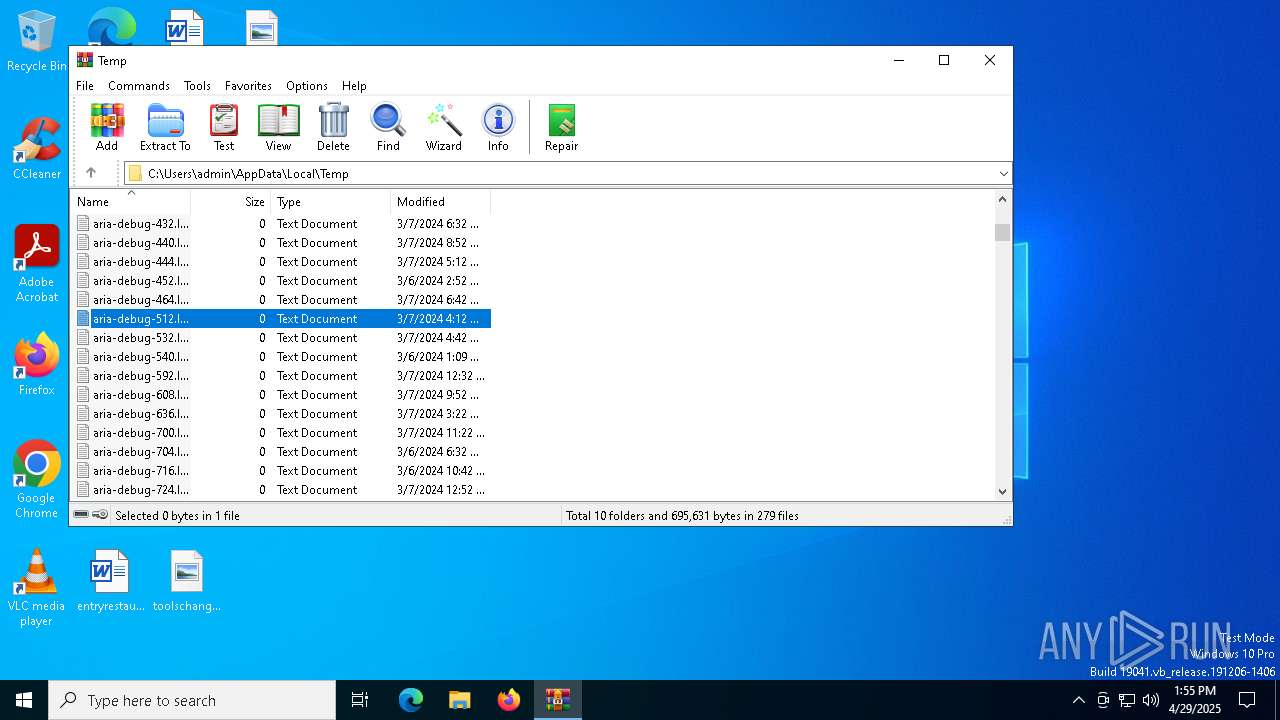
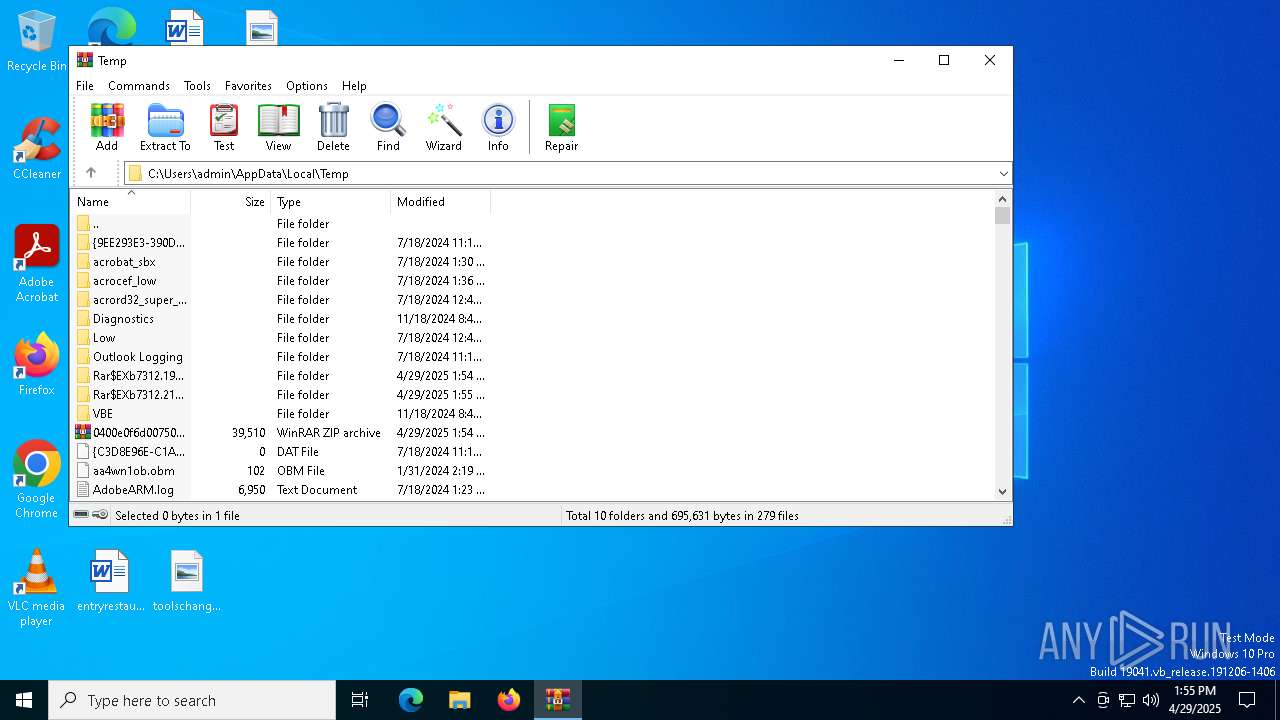
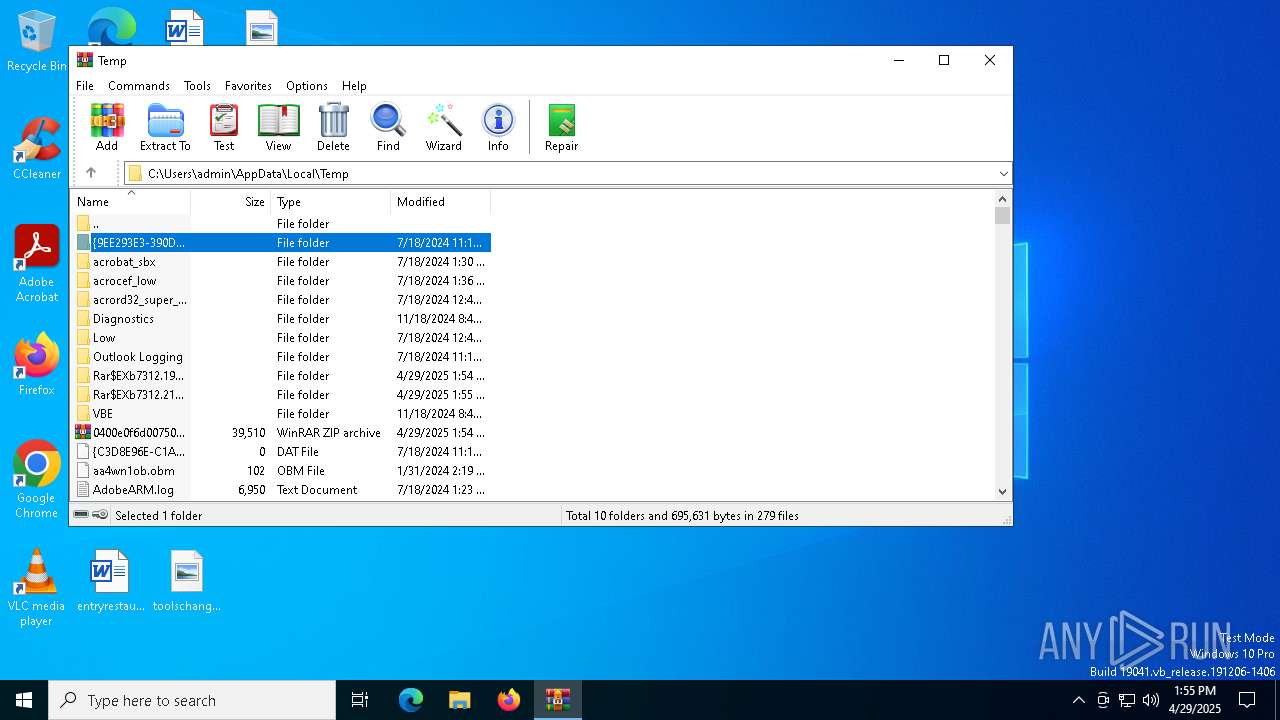
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7312)
Reads CPU info
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Checks supported languages
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Reads the machine GUID from the registry
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Reads the computer name
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Checks proxy server information
- 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe (PID: 7760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:04:29 13:54:18 |
| ZipCRC: | 0x2c0fb5cf |
| ZipCompressedSize: | 39254 |
| ZipUncompressedSize: | 75264 |
| ZipFileName: | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe |
Total processes
209
Monitored processes
83
Malicious processes
28
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nslookup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | nslookup nomoreransom.coin dns1.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | nslookup gandcrab.bit dns2.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | nslookup nomoreransom.coin dns1.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nslookup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | nslookup nomoreransom.bit dns1.soprodns.ru | C:\Windows\SysWOW64\nslookup.exe | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nslookup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nslookup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 013
Read events
24 987
Write events
26
Delete events
0
Modification events
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.zip | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7312) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7760) 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | oviaebeeons |
Value: C:\Users\admin\AppData\Local\Temp\Rar$EXb7312.19608\0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
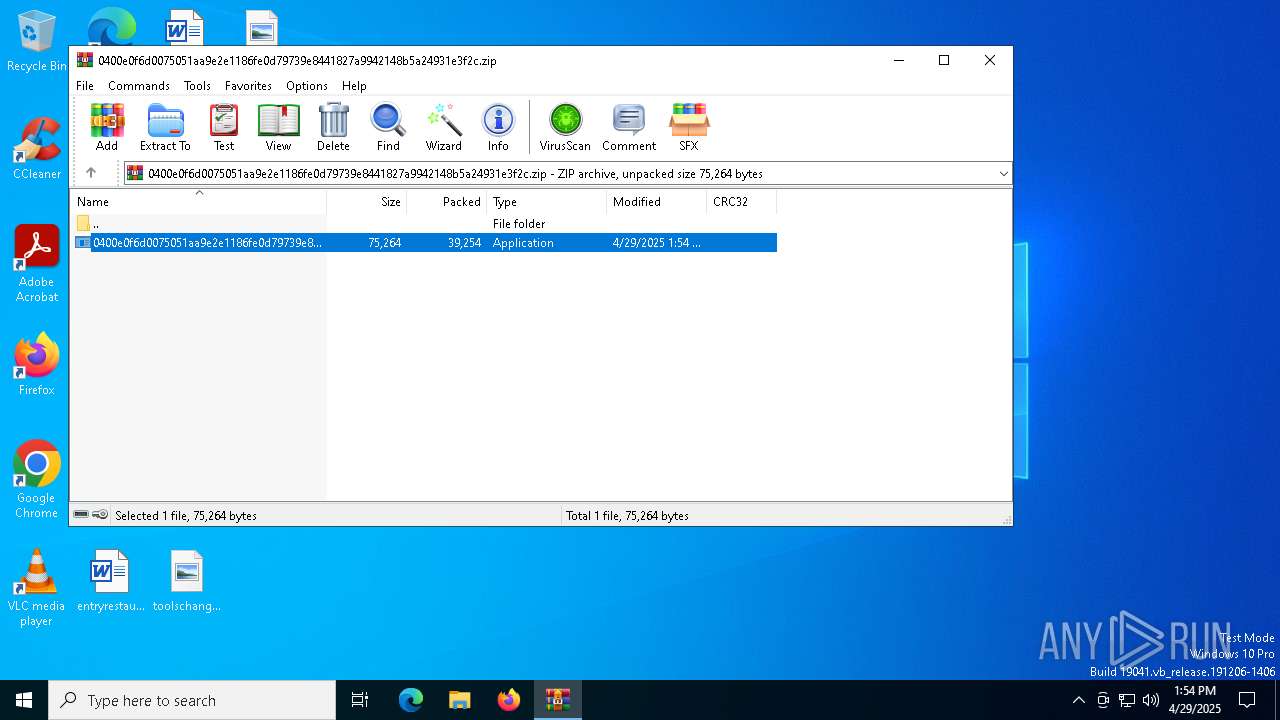
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7312.19608\0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | executable | |
MD5:8EED604DC104D2D82CF1A4F0865CDB20 | SHA256:0400E0F6D0075051AA9E2E1186FE0D79739E8441827A9942148B5A24931E3F2C | |||
| 7312 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb7312.21030\0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | executable | |
MD5:8EED604DC104D2D82CF1A4F0865CDB20 | SHA256:0400E0F6D0075051AA9E2E1186FE0D79739E8441827A9942148B5A24931E3F2C | |||
| 7760 | 0400e0f6d0075051aa9e2e1186fe0d79739e8441827a9942148b5a24931e3f2c.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\0f5007522459c86e95ffcc62f32308f1_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:01BDEA6D519698E43BF0968D0A67080D | SHA256:232C49E8D73DD1D726F96D03601228230D38FA772775AC305562BF7D34EE65AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
207
Threats
253
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7516 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7516 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ipv4bot.whatismyipaddress.com |
| whitelisted |
dns1.soprodns.ru |
| shared |
2.100.168.192.in-addr.arpa |
| whitelisted |
nomoreransom.coin |
| unknown |
nomoreransom.bit |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (whatismyipaddress .com) |
7828 | nslookup.exe | Potentially Bad Traffic | ET HUNTING Observed DNS Query for EmerDNS TLD (.coin) |
7828 | nslookup.exe | Potentially Bad Traffic | ET HUNTING Observed DNS Query for EmerDNS TLD (.coin) |
7828 | nslookup.exe | Potentially Bad Traffic | ET HUNTING Observed DNS Query for EmerDNS TLD (.coin) |
7828 | nslookup.exe | Potentially Bad Traffic | ET HUNTING Observed DNS Query for EmerDNS TLD (.coin) |
7904 | nslookup.exe | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
7904 | nslookup.exe | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
7904 | nslookup.exe | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
7904 | nslookup.exe | A Network Trojan was detected | RANSOMWARE [ANY.RUN] GandCrab Domain has been detected (nomoreransom .bit) |
7904 | nslookup.exe | A Network Trojan was detected | RANSOMWARE [ANY.RUN] GandCrab Domain has been detected (nomoreransom .bit) |