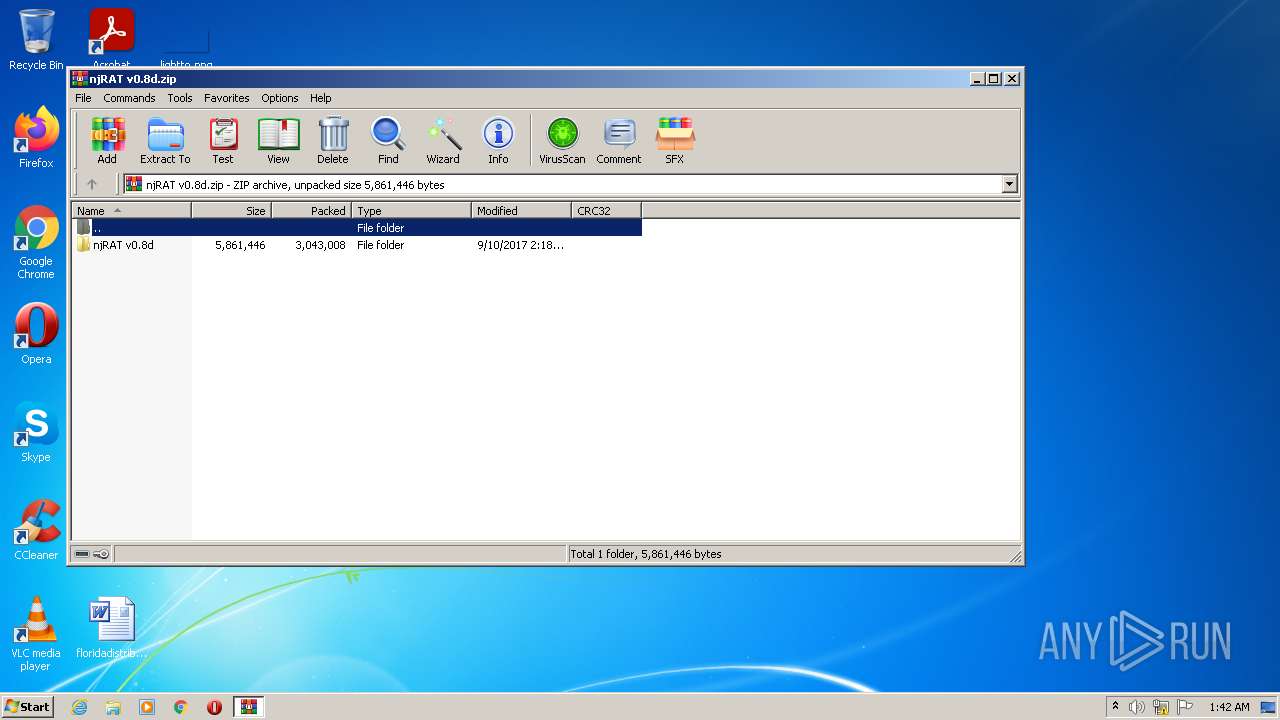
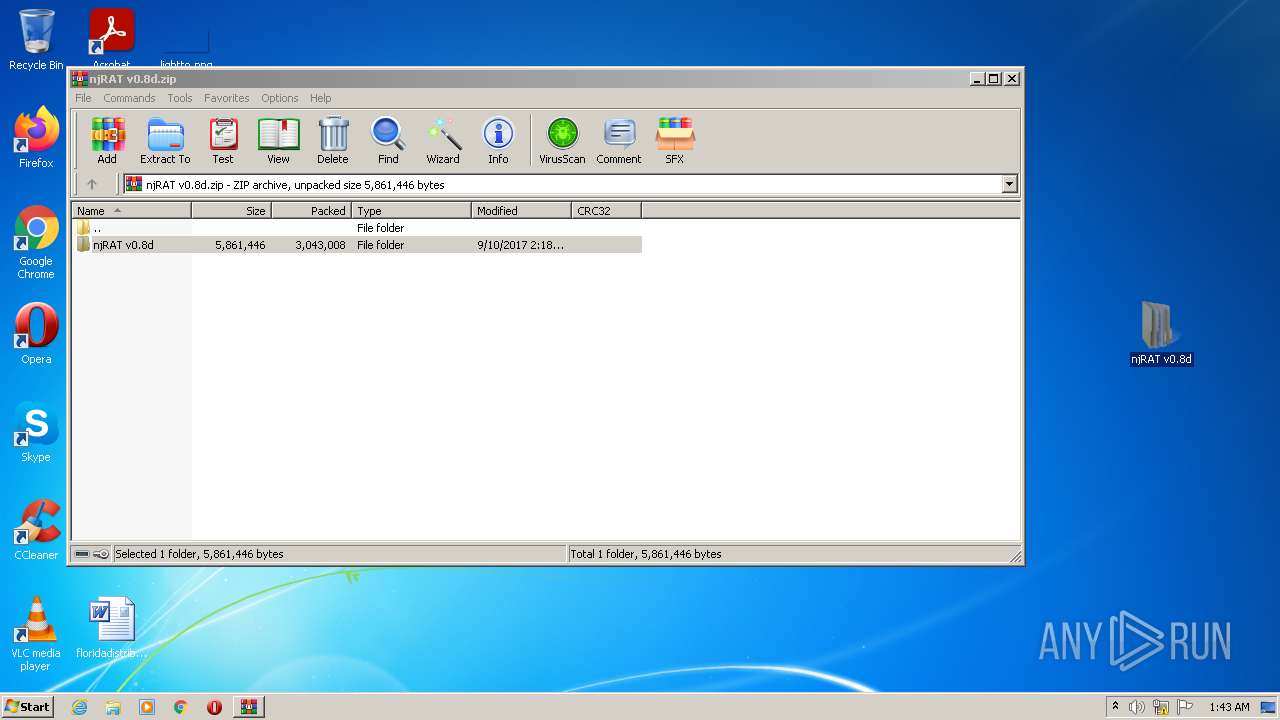
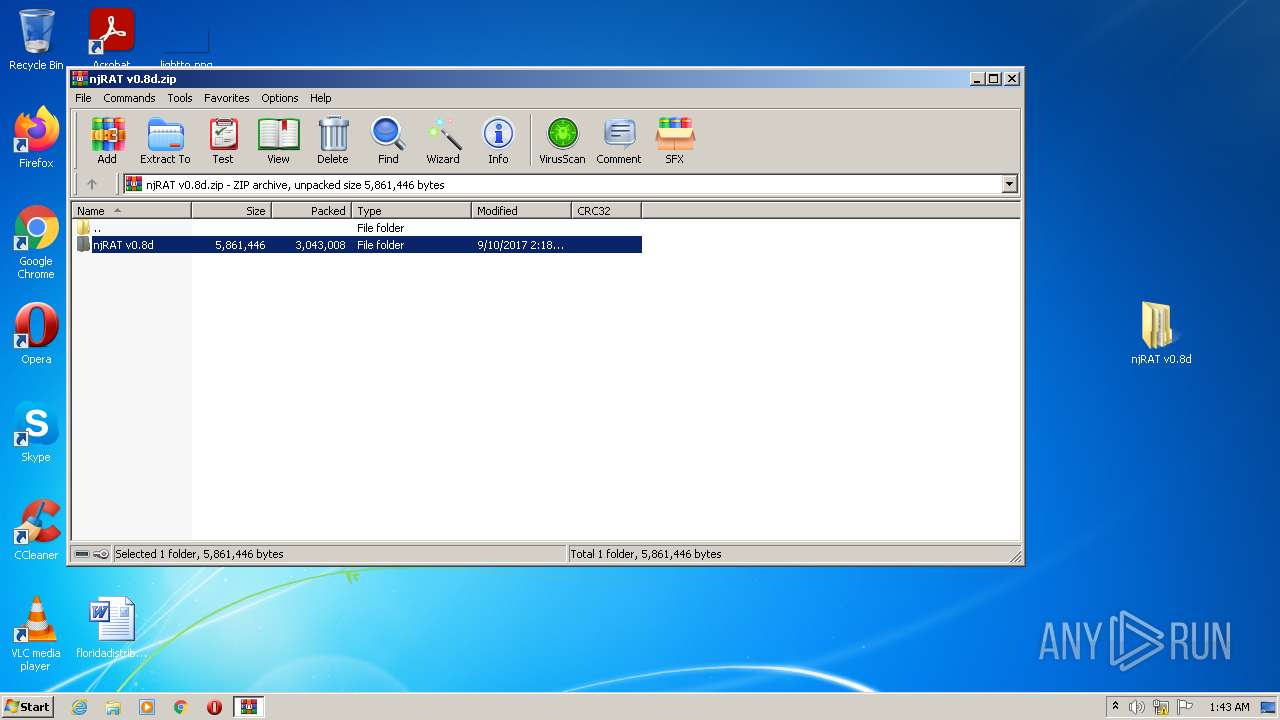
| File name: | njRAT v0.8d.zip |
| Full analysis: | https://app.any.run/tasks/7dd6ec72-9bf3-4d95-abec-be8b4b3961ee |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 01:42:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 921D8AAFB904D76CB6A5A89B3F6207EC |
| SHA1: | 6790CBEE3137DF9043F8E8397312ADB1D0DDD1D8 |
| SHA256: | E6C836818C882ED65E7412C551D4B1A46C490E66A8447CF231B5346FB350EE5D |
| SSDEEP: | 49152:g8B+mV827Kd68B+mV827Kdx8B+mV827KdF8B+mV827Kdl:5d17KRd17Kmd17Kqd17KH |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3448)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2216)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2216)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2216)
Checks supported languages
- WinRAR.exe (PID: 2216)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
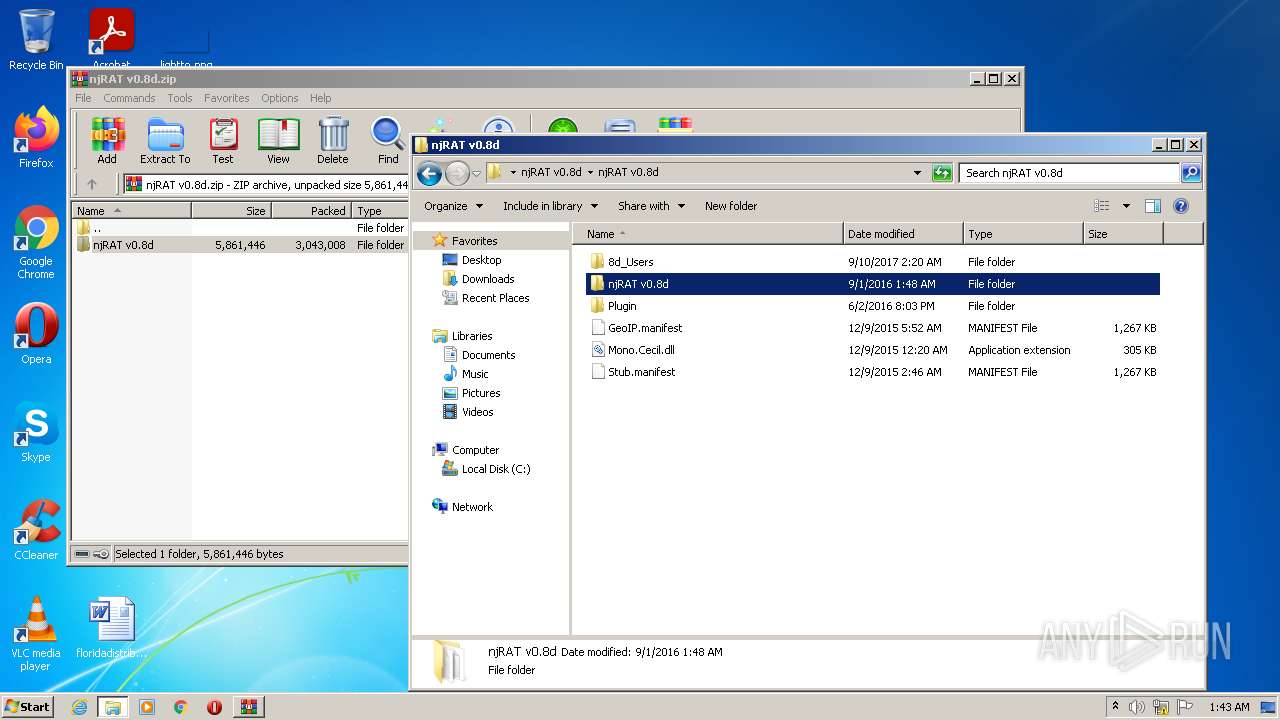
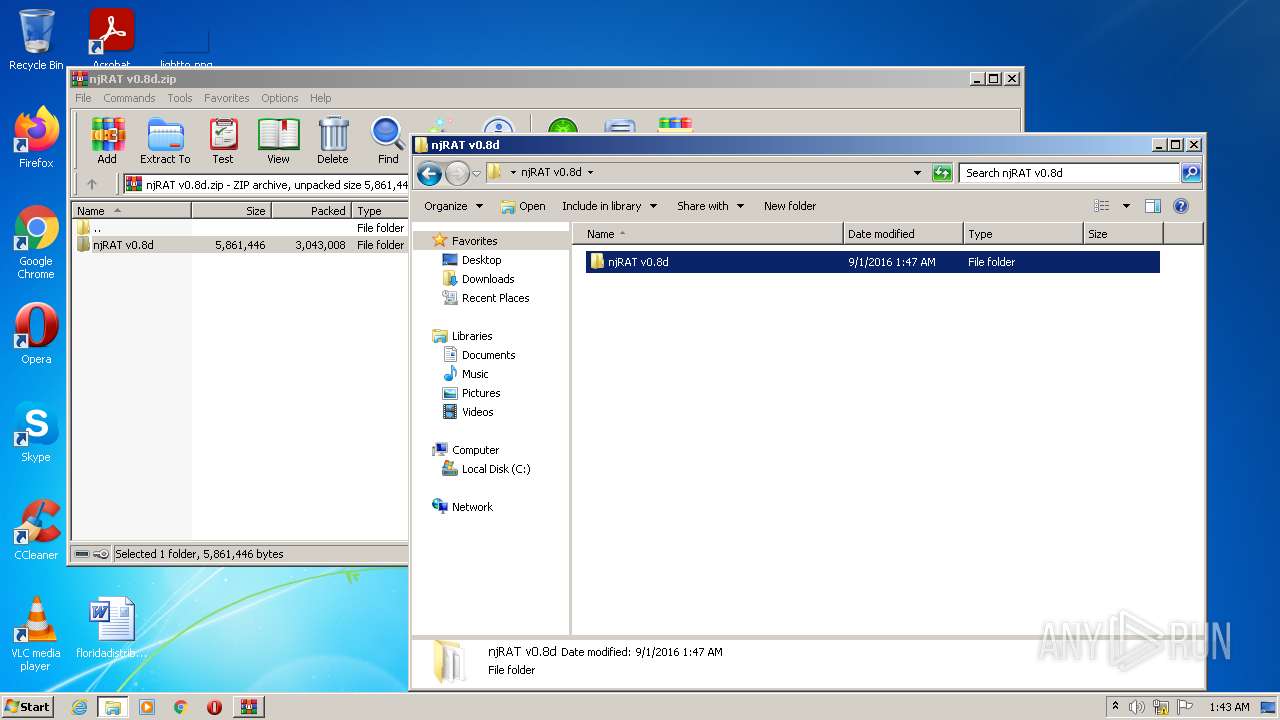
| ZipFileName: | njRAT v0.8d/ |
|---|---|
| ZipUncompressedSize: | - |
| ZipCompressedSize: | - |
| ZipCRC: | 0x00000000 |
| ZipModifyDate: | 2017:09:10 13:18:22 |
| ZipCompression: | None |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2216 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\njRAT v0.8d.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3448 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
1 675
Read events
1 665
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\njRAT v0.8d.zip | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
6
Suspicious files
0
Text files
5
Unknown types
4
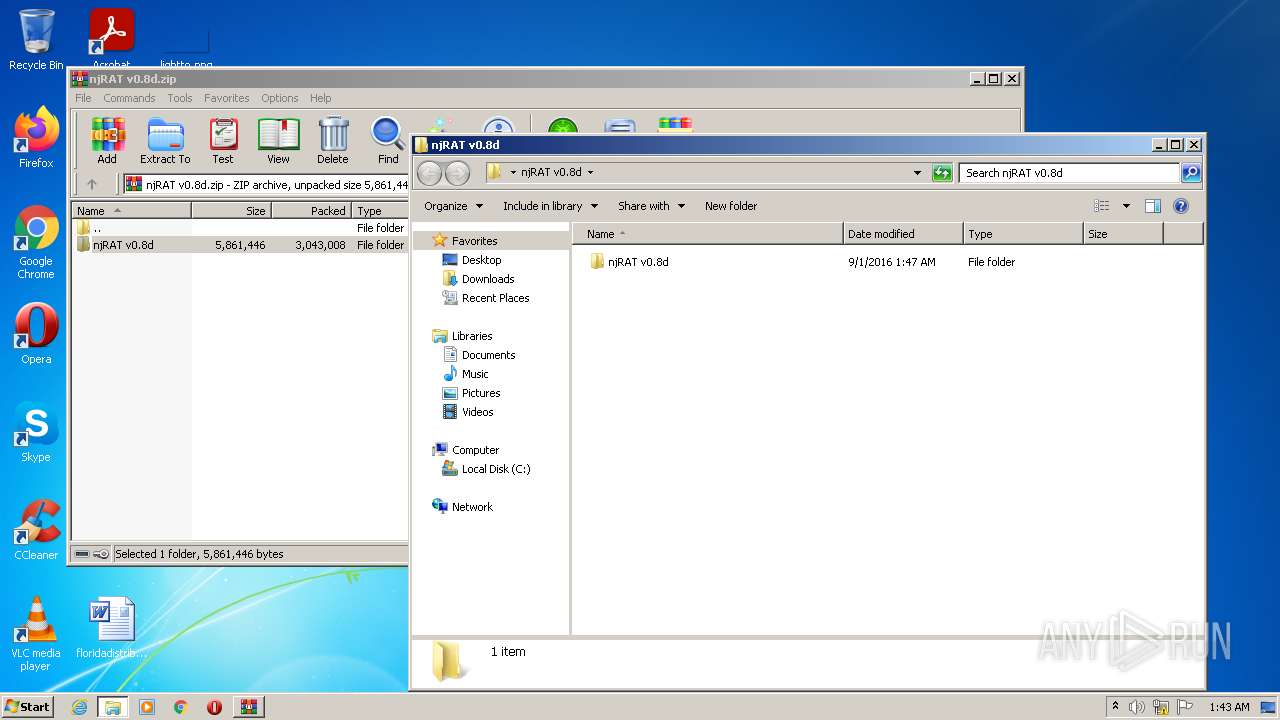
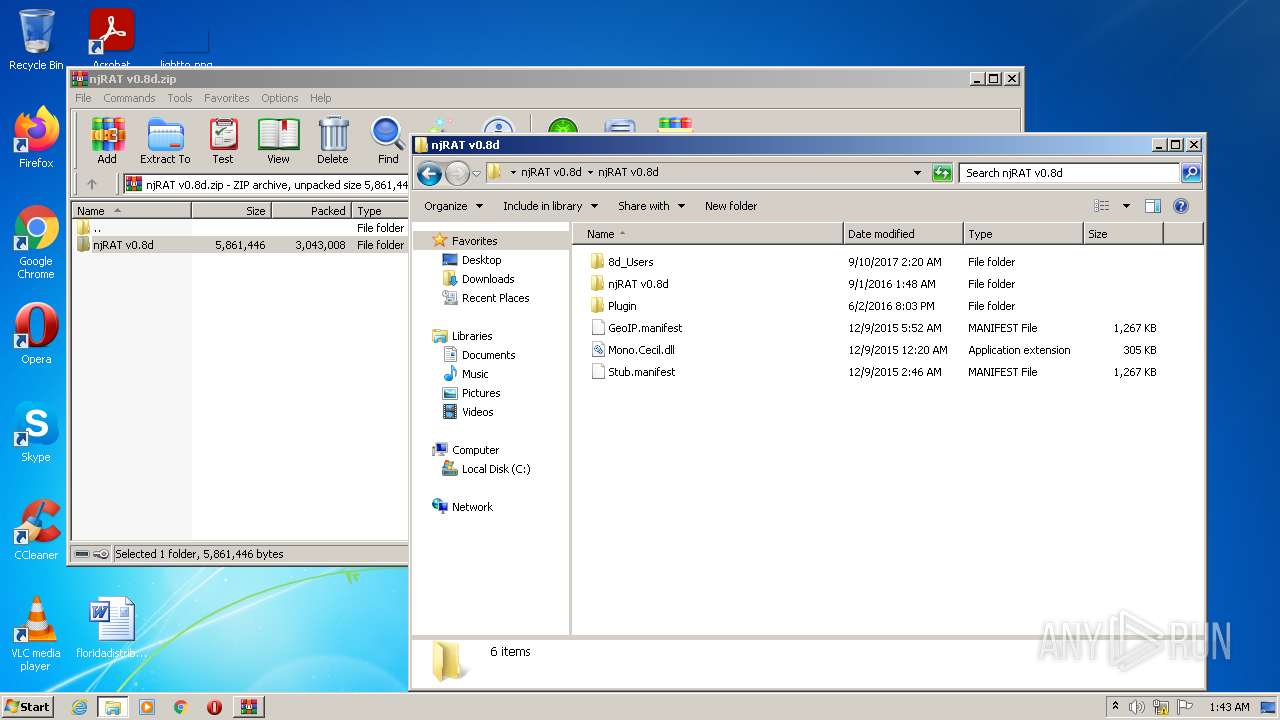
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\8d_Users\MSI-PC_msi_845E28C4\Naseer2012.jpg | image | |
MD5:— | SHA256:— | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\8d_Users\MSI-PC_msi_845E28C4\Keyloger.rtf | text | |
MD5:— | SHA256:— | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\njRAT v0.8d\8d_Users\MSI-PC_msi_845E28C4\Keyloger.rtf | text | |
MD5:— | SHA256:— | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\8d_Users\DOMINIC-PC_Dominic_B82B50AD\Naseer2012.jpg | image | |
MD5:— | SHA256:— | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\njRAT v0.8d\8d_Users\MSI-PC_msi_845E28C4\Naseer2012.jpg | image | |
MD5:— | SHA256:— | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\njRAT v0.8d\GeoIP.manifest | prg | |
MD5:D6A5BA3494C5CFA8ADAABA2D5F138610 | SHA256:5FA0FD7178A5883A5A9C66DE58F01BCD66FB156A515E21E7CAE1E00EC4226360 | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\GeoIP.manifest | prg | |
MD5:D6A5BA3494C5CFA8ADAABA2D5F138610 | SHA256:5FA0FD7178A5883A5A9C66DE58F01BCD66FB156A515E21E7CAE1E00EC4226360 | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\njRAT v0.8d\Mono.Cecil.dll | executable | |
MD5:851EC9D84343FBD089520D420348A902 | SHA256:CDADC26C09F869E21053EE1A0ACF3B2D11DF8EDD599FE9C377BD4D3CE1C9CDA9 | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\Mono.Cecil.dll | executable | |
MD5:851EC9D84343FBD089520D420348A902 | SHA256:CDADC26C09F869E21053EE1A0ACF3B2D11DF8EDD599FE9C377BD4D3CE1C9CDA9 | |||
| 2216 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2216.14430\njRAT v0.8d\njRAT v0.8d\njRAT v0.8d\Stub.manifest | prg | |
MD5:D6A5BA3494C5CFA8ADAABA2D5F138610 | SHA256:5FA0FD7178A5883A5A9C66DE58F01BCD66FB156A515E21E7CAE1E00EC4226360 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report