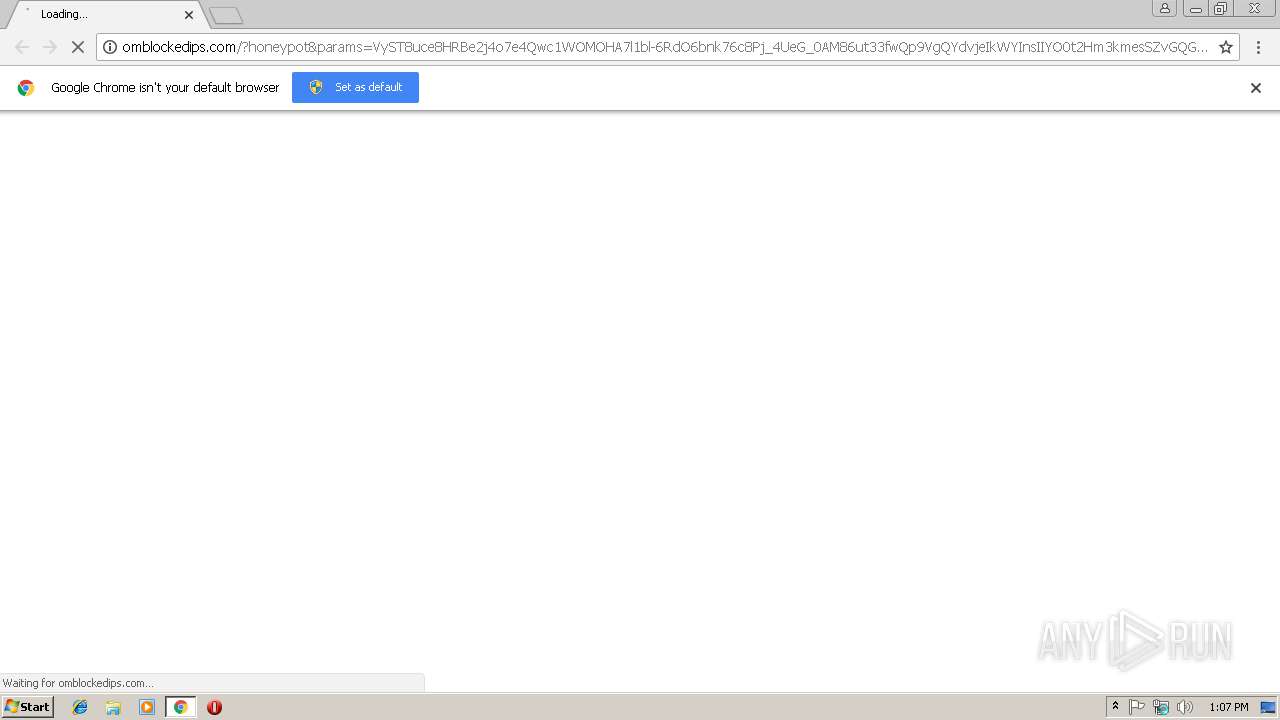
| URL: | http://omblockedips.com/?honeypot¶ms=VyST8uce8HRBe2j4o7e4Qwc1WOMOHA7l1bl-6RdO6bnk76c8Pj_4UeG_0AM86ut33fwQp9VgQYdvjeIkWYInsIIYO0t2Hm3kmesSZvGQGHgze4vRpaFgUZ9oDjoeHi7W81jEGOn9Q606ouJWzHPnTRkMndeld8ypVX7-yf1dWBIOIVE1BpWNSsouTkVXZBuyuE_CfiaddawBJ1bD |
| Full analysis: | https://app.any.run/tasks/8fd8f68e-5074-4714-bc73-a56cde655a8c |
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2019, 13:07:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 95501A3102D0A87285447B5E2D75F183 |
| SHA1: | 4857CAB03B5771C3F5D9155D7348A8537984BC3B |
| SHA256: | E6B9410BC40EE63161CB11B62B58BE62C52359B74F23A6A5F7DEA66FC8B97AB6 |
| SSDEEP: | 6:Cu6VMPuKAv6RMrS6BdpI0iq6ctOhLkHbyWS1sS:h6VIubiMrS6BHJt6rLkHbLS5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3004)
Reads settings of System Certificates
- chrome.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
10
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5F7496F8BC1B6C3DF53F3C0AFCE0D2E8 --mojo-platform-channel-handle=1136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=916 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=FB2E31B2E9FA238B52A4F88B5E9E2823 --mojo-platform-channel-handle=2252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3008 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://omblockedips.com/?honeypot¶ms=VyST8uce8HRBe2j4o7e4Qwc1WOMOHA7l1bl-6RdO6bnk76c8Pj_4UeG_0AM86ut33fwQp9VgQYdvjeIkWYInsIIYO0t2Hm3kmesSZvGQGHgze4vRpaFgUZ9oDjoeHi7W81jEGOn9Q606ouJWzHPnTRkMndeld8ypVX7-yf1dWBIOIVE1BpWNSsouTkVXZBuyuE_CfiaddawBJ1bD | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=06F0A89E26151B7EC37DAD82D462C525 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=06F0A89E26151B7EC37DAD82D462C525 --renderer-client-id=4 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=3BB5C0C8CD8BCCA8D9CCFCD02B4B1ED0 --mojo-platform-channel-handle=3420 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8F3D2EF644B947862CECFC93BBD4C700 --mojo-platform-channel-handle=3800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701600b0,0x701600c0,0x701600cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=A476A9D1919CDB71C85A5C94B7F0B3CD --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A476A9D1919CDB71C85A5C94B7F0B3CD --renderer-client-id=3 --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
525
Read events
460
Write events
61
Delete events
4
Modification events
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3004-13197474464416000 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3004-13197474464416000 |
Value: 259 | |||
| (PID) Process: | (3004) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
69
Text files
118
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c6a484de-d67a-4c9d-b966-e6a0837a8f8f.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fffc9174-b7a3-4ba2-8eaf-08be0edb2a4e.tmp | — | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20e39d.TMP | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF20e3dc.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
108
DNS requests
99
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
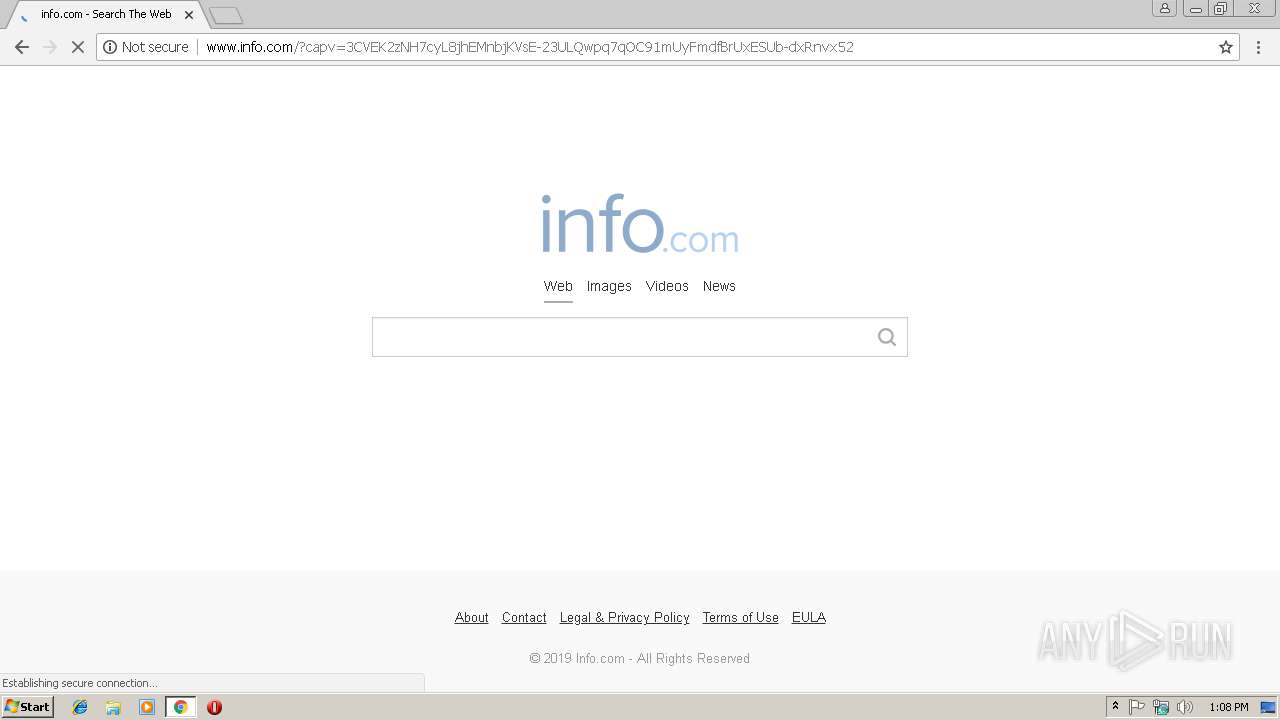
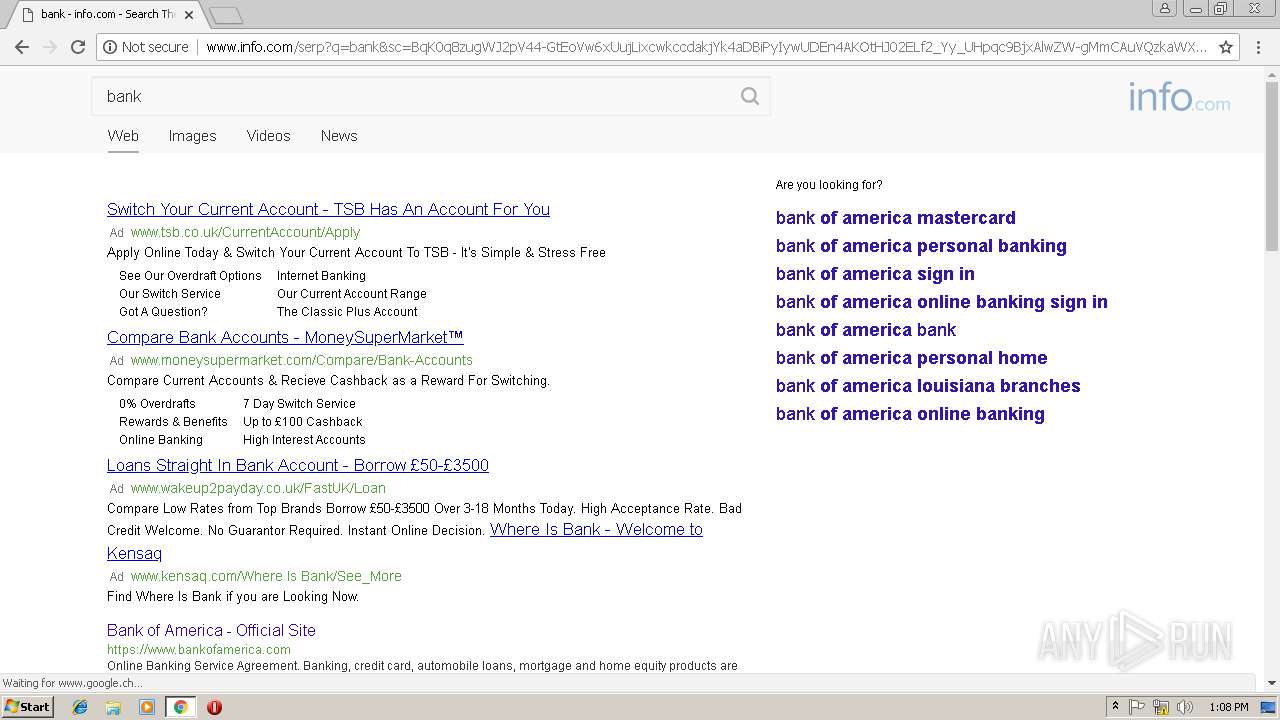
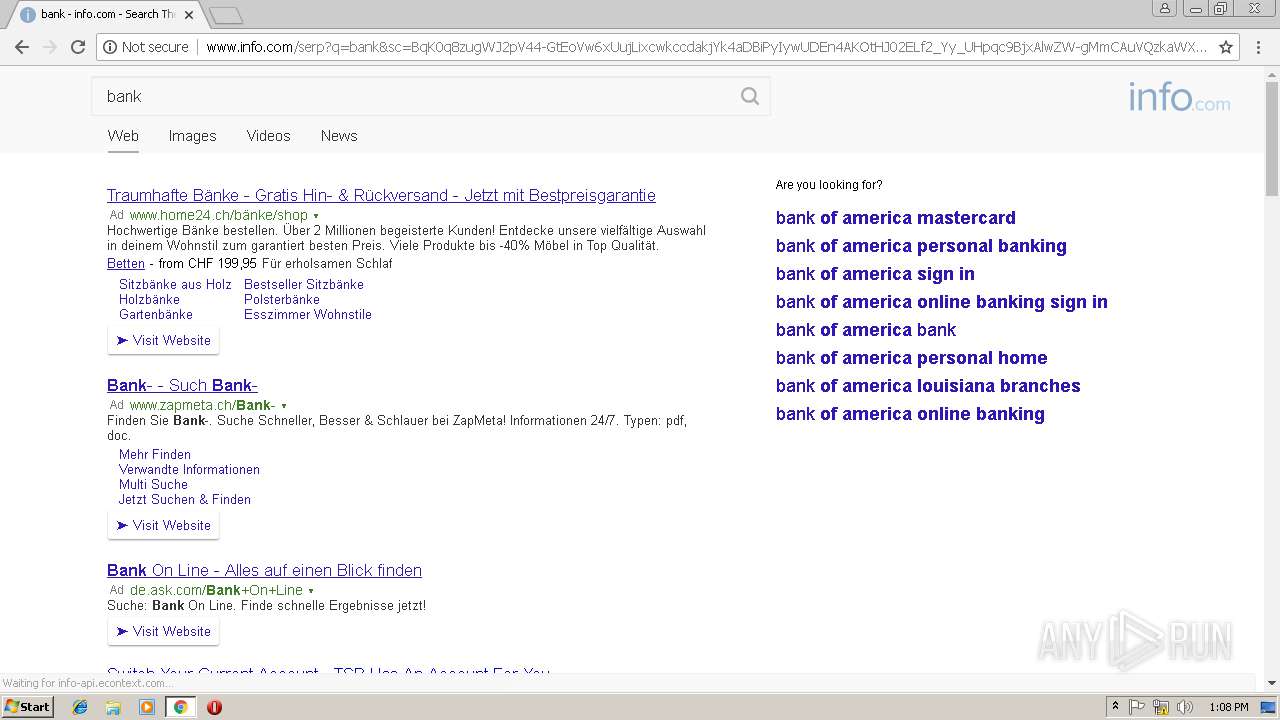
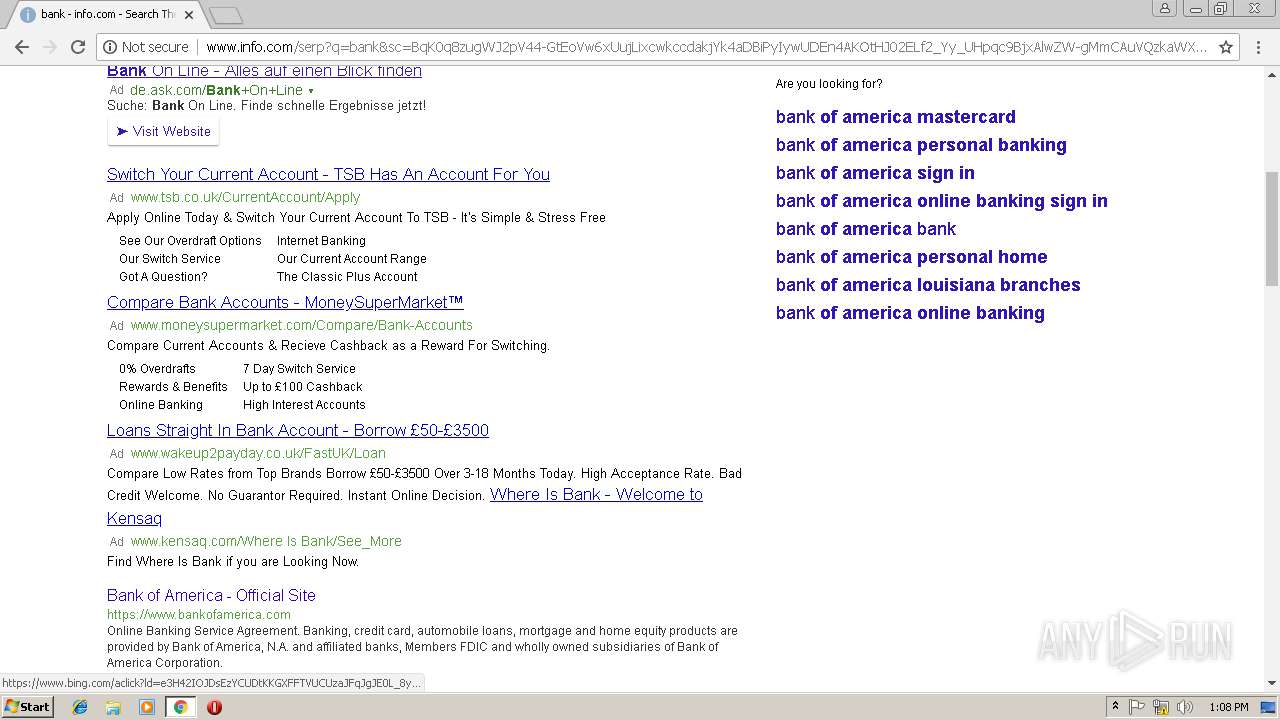
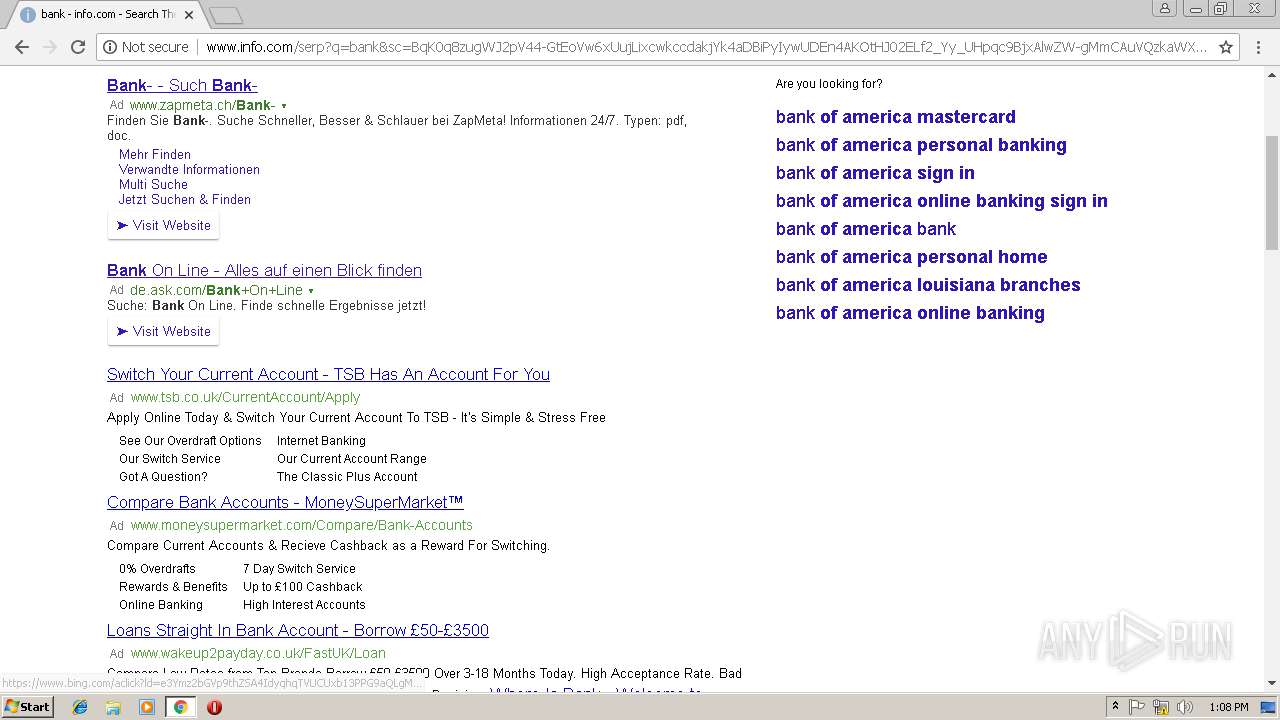
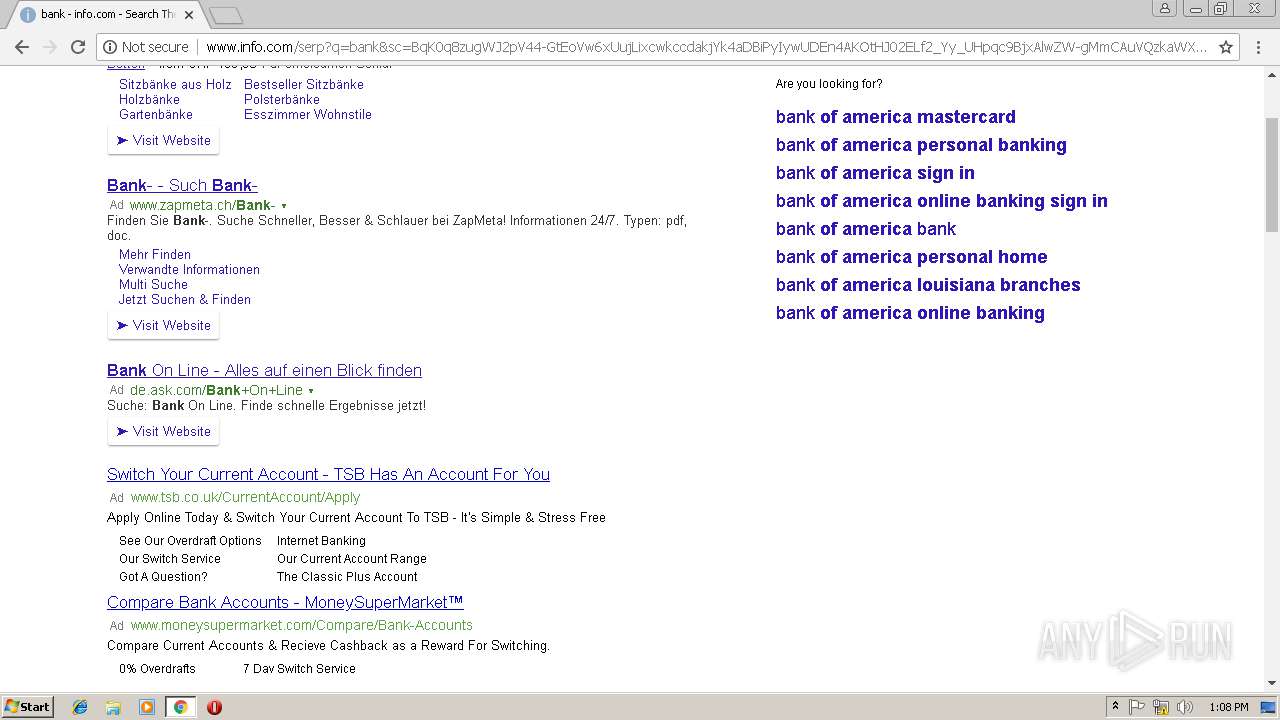
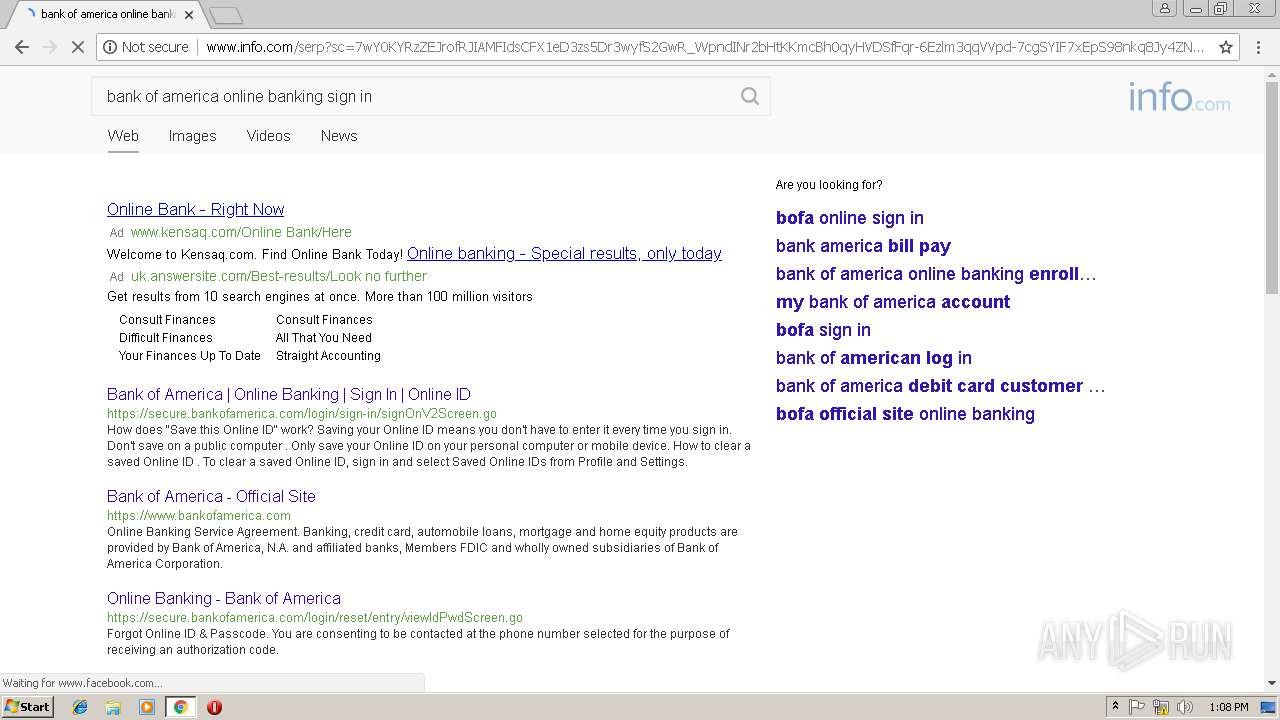
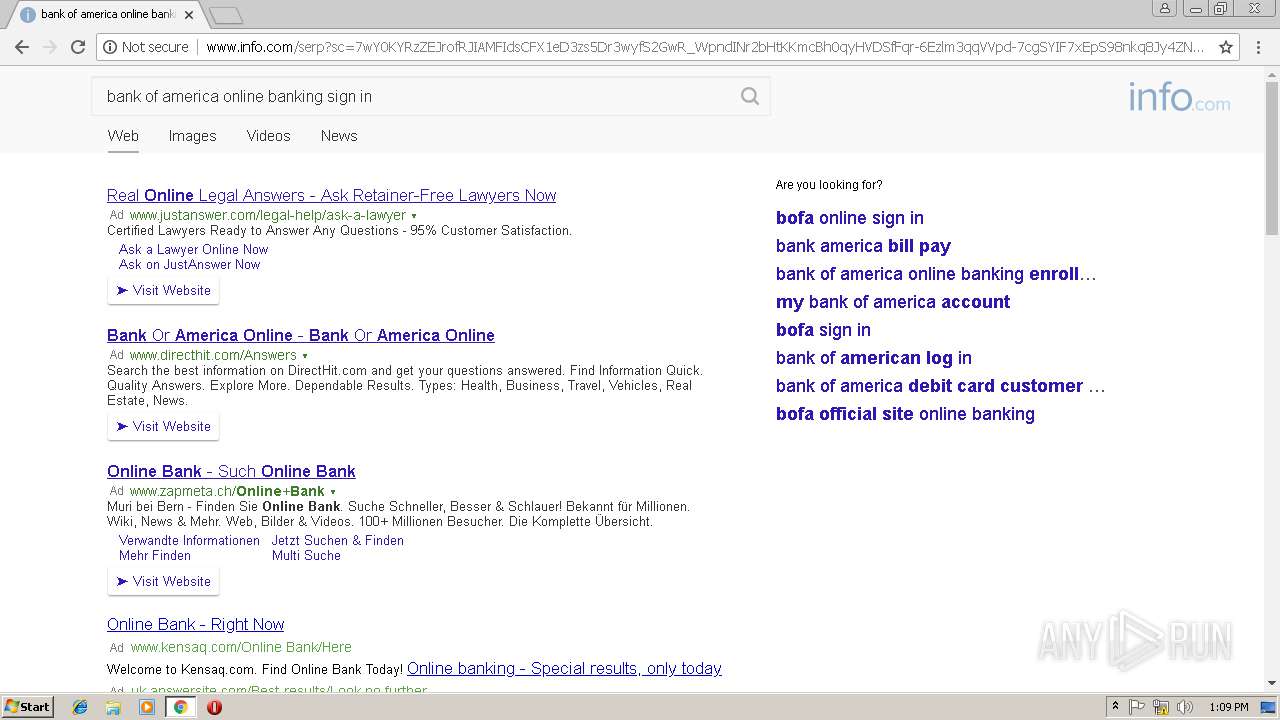
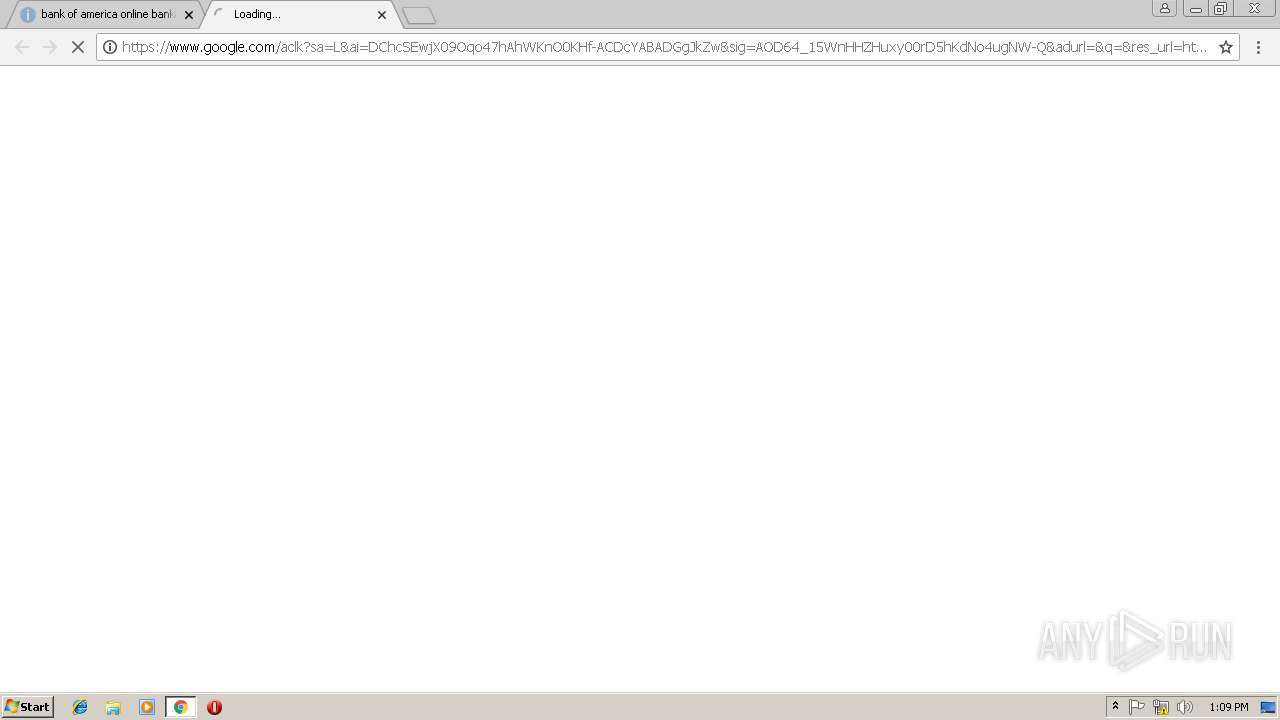
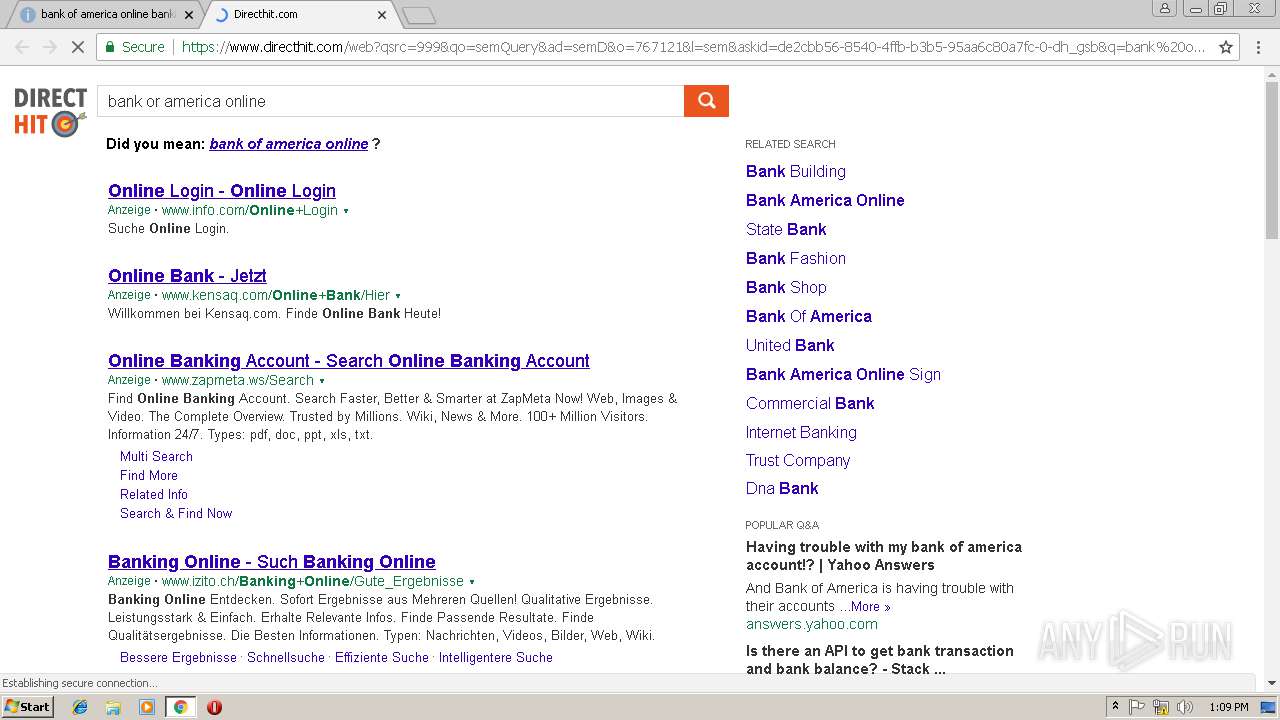
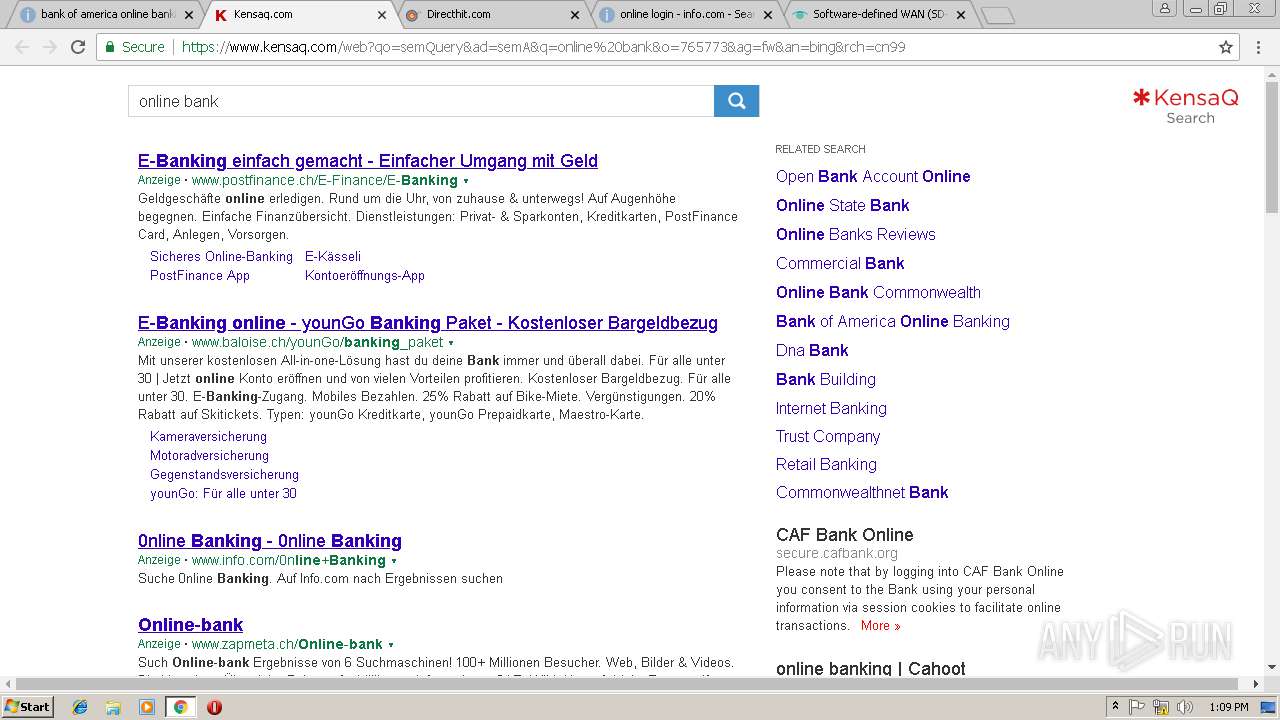
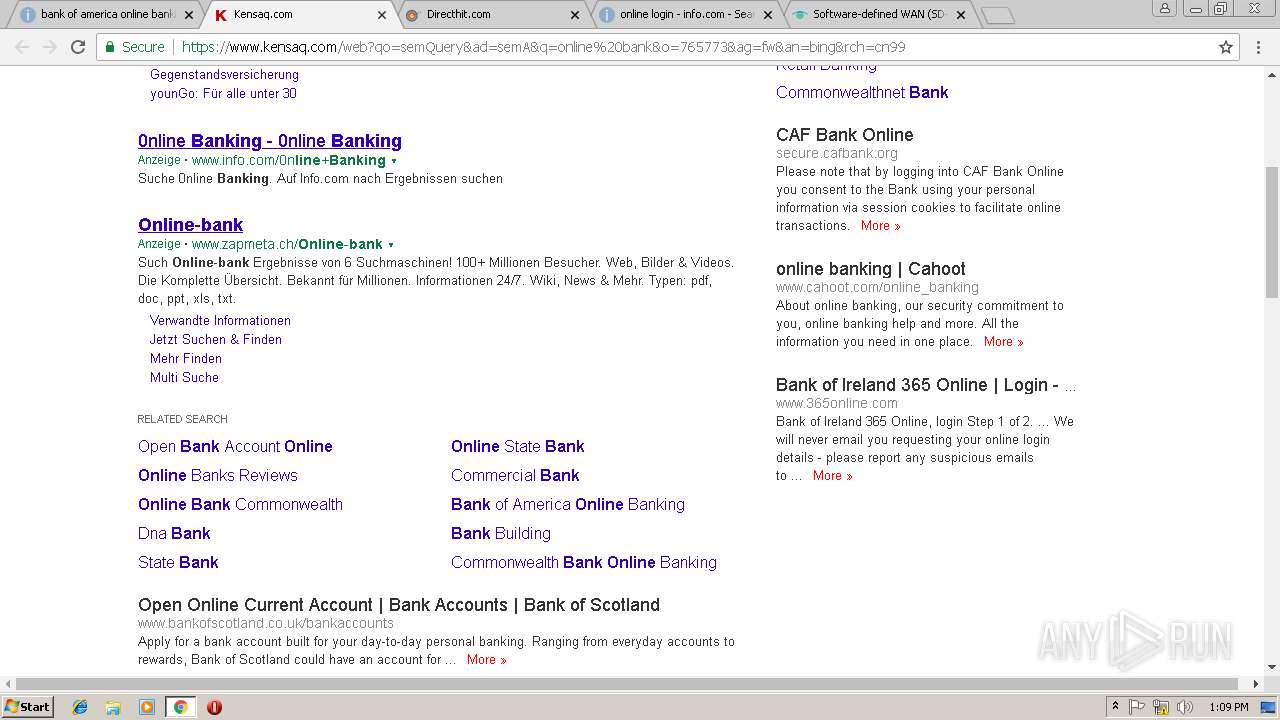
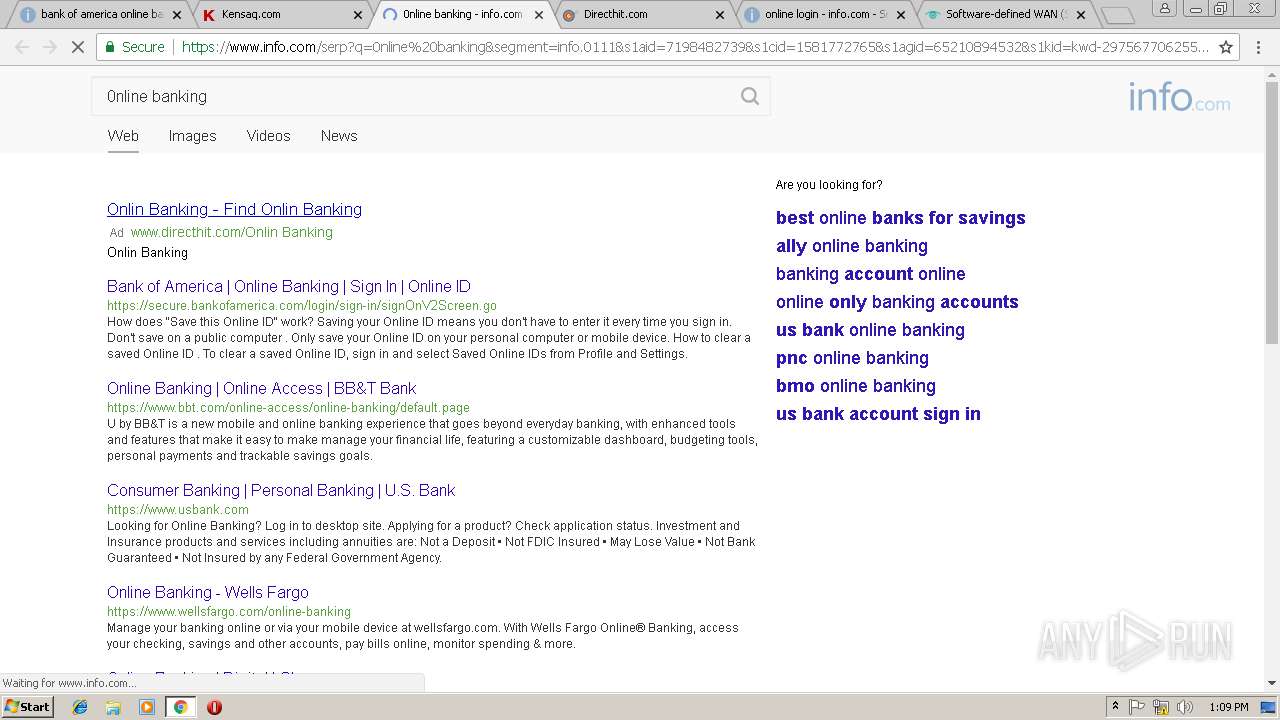
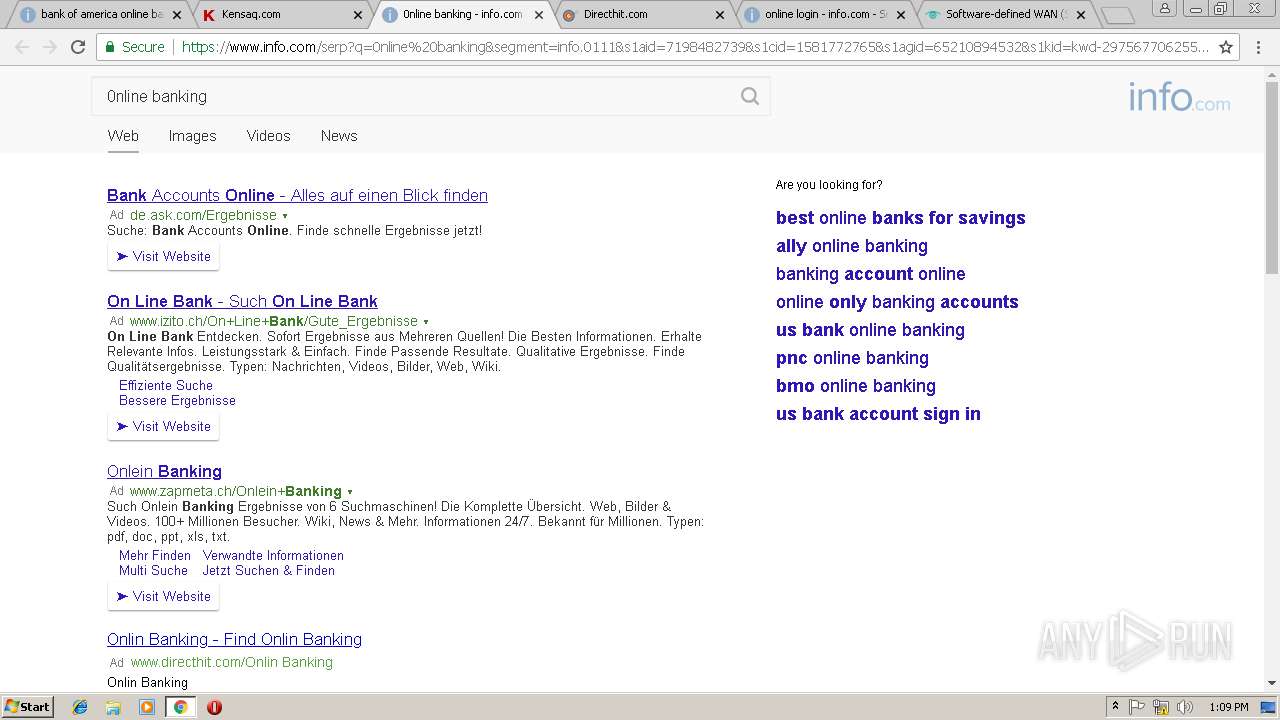
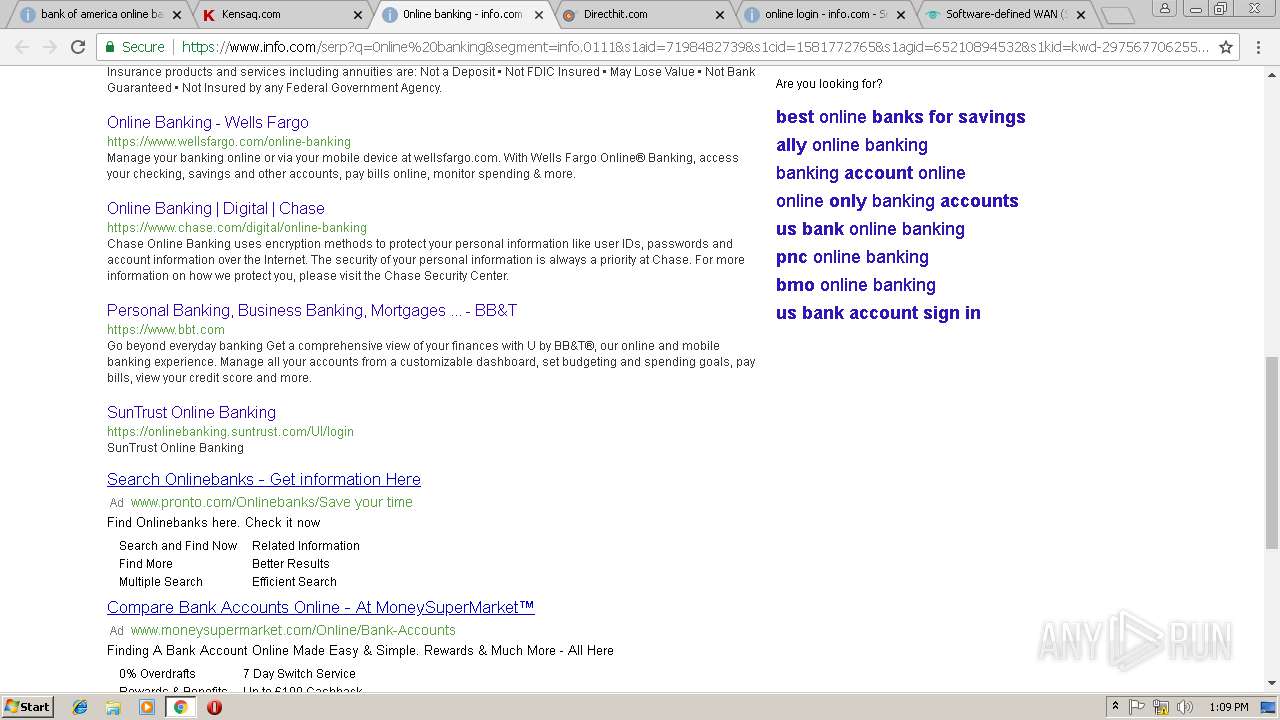
3004 | chrome.exe | POST | 204 | 52.17.173.115:80 | http://www.info.com/pingback?sc=iwkMex3PG-hUFXGkpqDoFDVIZJDcgxvYhZbiAR-6OU9gWbh0mGPupYwBg19x-SVVORr-rrthOHq2w50djg8VZklBThLpZqb03c_ImcpbRaR-Q9lnRDXHeWmjS330qMxmmHfit7jOMyFvQT42xRTcpD3oPZ8GL9Oqpy3BzEi7CtavhtLuvZy_HBjsPct3l8-GttXzfIJhZs-U2ME0JPSx9-0xkW_RfuqXhDA8F7YcuicyJAjIJtFeecTtNvyiMyvEH0BNE1y-hy57PIq_j-wN0jPtfcEB6lWjZqhDBgZg0kJt6dJQHapJIF1Qb-kd_6wX5Plk5ry-RTR8Ed9EIzPEVcxdwwMFugmWb93g0p3bOEsmfUxC48ZLYuyi8apD&pbid=aH7VSMH8ANiaFhbgFJ82&gcsa_links=%5B%22de.ask.com%2FBank%2BOn%2BLine%22%2C%22www.home24.ch%2Fb%C3%A4nke%2Fshop%22%2C%22www.zapmeta.ch%2FBank-%22%5D | IE | — | — | suspicious |
3004 | chrome.exe | POST | 204 | 52.17.173.115:80 | http://www.info.com/pingback?sc=iwkMex3PG-hUFXGkpqDoFDVIZJDcgxvYhZbiAR-6OU9gWbh0mGPupYwBg19x-SVVORr-rrthOHq2w50djg8VZklBThLpZqb03c_ImcpbRaR-Q9lnRDXHeWmjS330qMxmmHfit7jOMyFvQT42xRTcpD3oPZ8GL9Oqpy3BzEi7CtavhtLuvZy_HBjsPct3l8-GttXzfIJhZs-U2ME0JPSx9-0xkW_RfuqXhDA8F7YcuicyJAjIJtFeecTtNvyiMyvEH0BNE1y-hy57PIq_j-wN0jPtfcEB6lWjZqhDBgZg0kJt6dJQHapJIF1Qb-kd_6wX5Plk5ry-RTR8Ed9EIzPEVcxdwwMFugmWb93g0p3bOEsmfUxC48ZLYuyi8apD&pbid=aH7VSMH8ANiaFhbgFJ82&gcsa_loaded=%7B%22gcsa-top%22%3Atrue%7D | IE | — | — | suspicious |
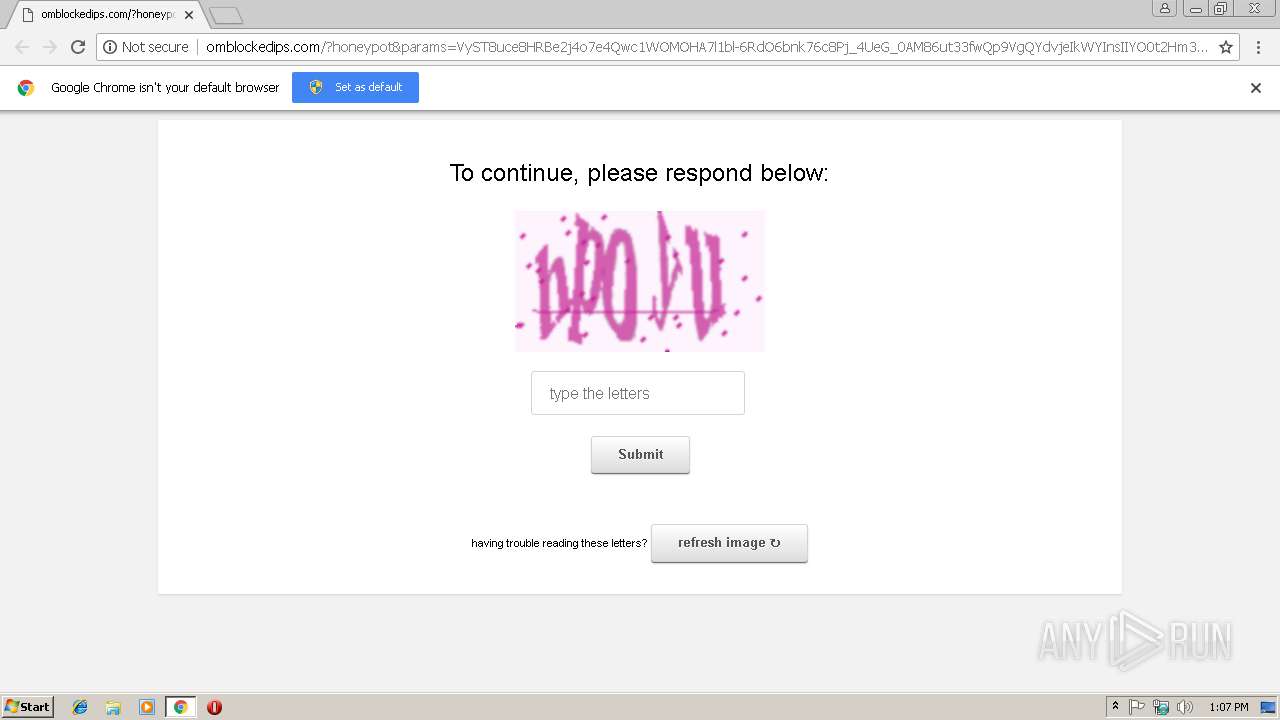
3004 | chrome.exe | GET | 302 | 35.161.37.37:80 | http://omblockedips.com/validate?captcha_response=hpoyu¶ms=UUiktEJFlfRv2UxukLI_jObvDrM8H8G08sWeScv5S-_9Yl47Wg_-fwYHraAc31HXSgyFky1b4b-ra6BYc1Rg6nx1b8FNZB-9de1OE6TXKPI2Tz0TlvZBohpv9t2Vw4z0A3P60wB0xQSzKBsx6bYt1d7sisnuQTleuH5NpRoEqZ6ADWr1_ttGJAi3F9HAxzL7OyTsngcH1uSXmPuSOjYp1sE7C4vVYuN2hho | US | html | 387 b | unknown |
3004 | chrome.exe | GET | 204 | 35.161.37.37:80 | http://omblockedips.com/favicon.ico | US | compressed | 11.7 Kb | unknown |
3004 | chrome.exe | GET | 200 | 35.161.37.37:80 | http://omblockedips.com/?honeypot¶ms=VyST8uce8HRBe2j4o7e4Qwc1WOMOHA7l1bl-6RdO6bnk76c8Pj_4UeG_0AM86ut33fwQp9VgQYdvjeIkWYInsIIYO0t2Hm3kmesSZvGQGHgze4vRpaFgUZ9oDjoeHi7W81jEGOn9Q606ouJWzHPnTRkMndeld8ypVX7-yf1dWBIOIVE1BpWNSsouTkVXZBuyuE_CfiaddawBJ1bD | US | html | 11.7 Kb | unknown |
3004 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
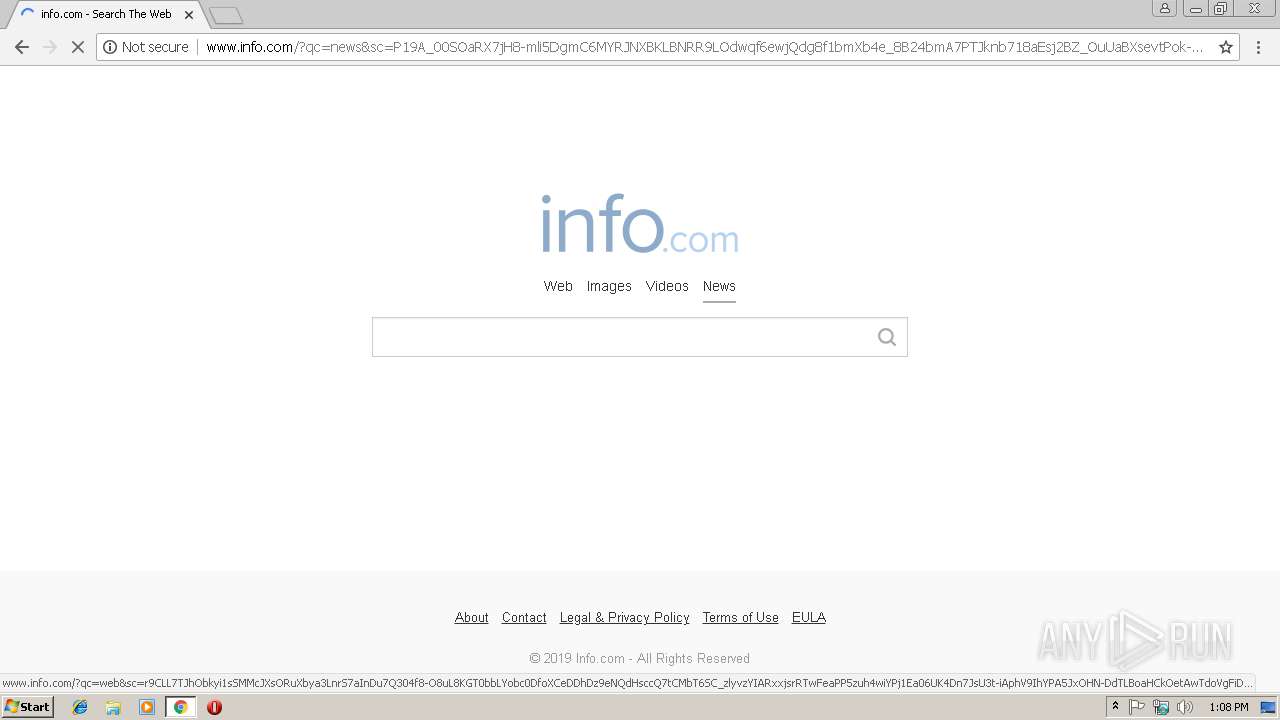
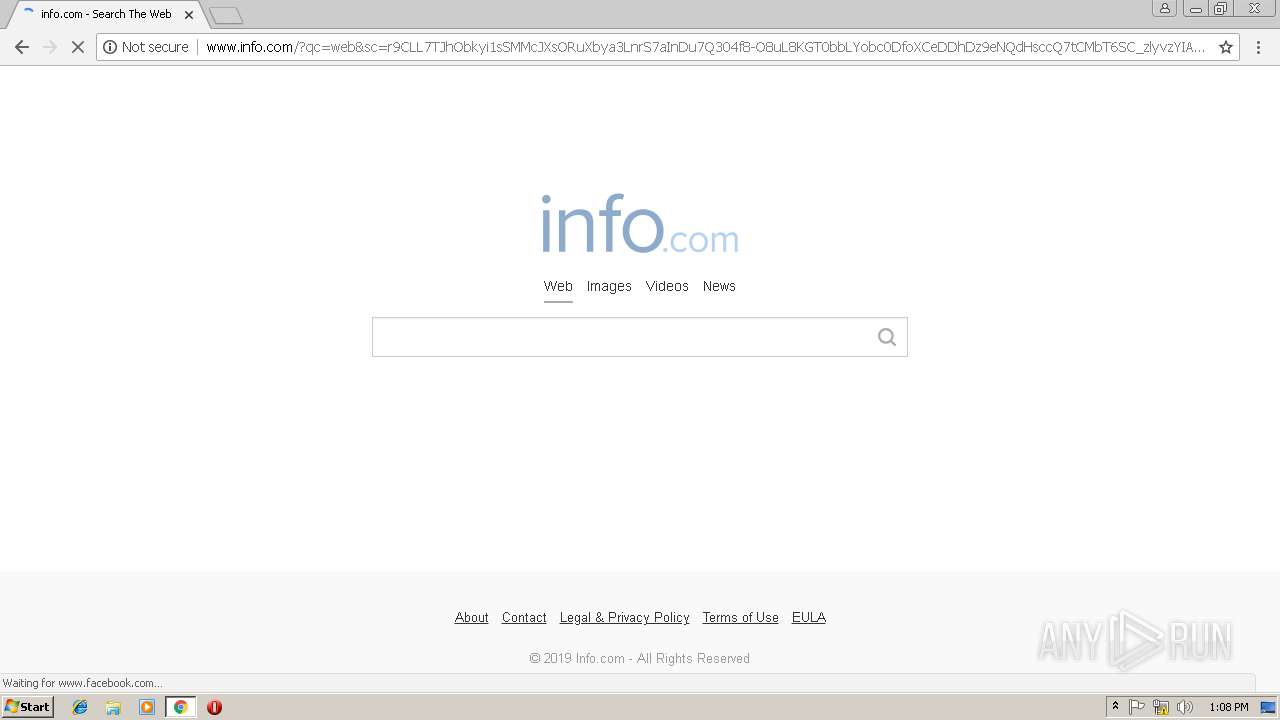
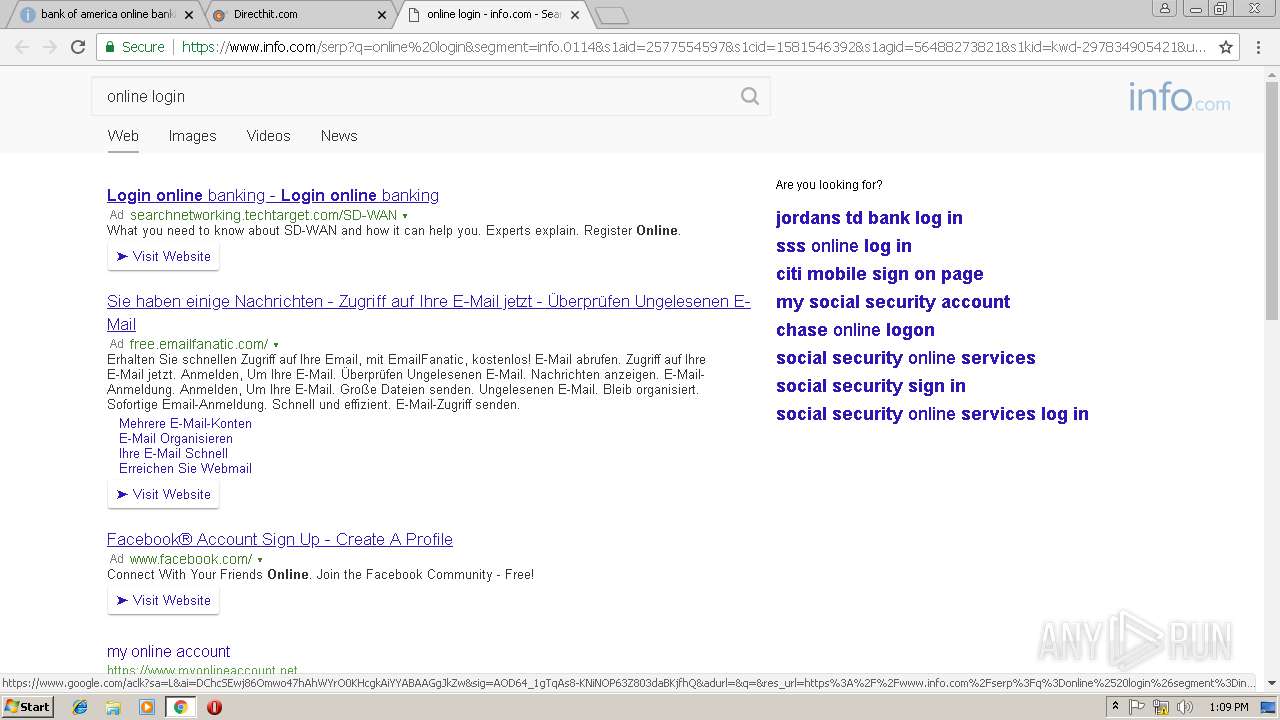
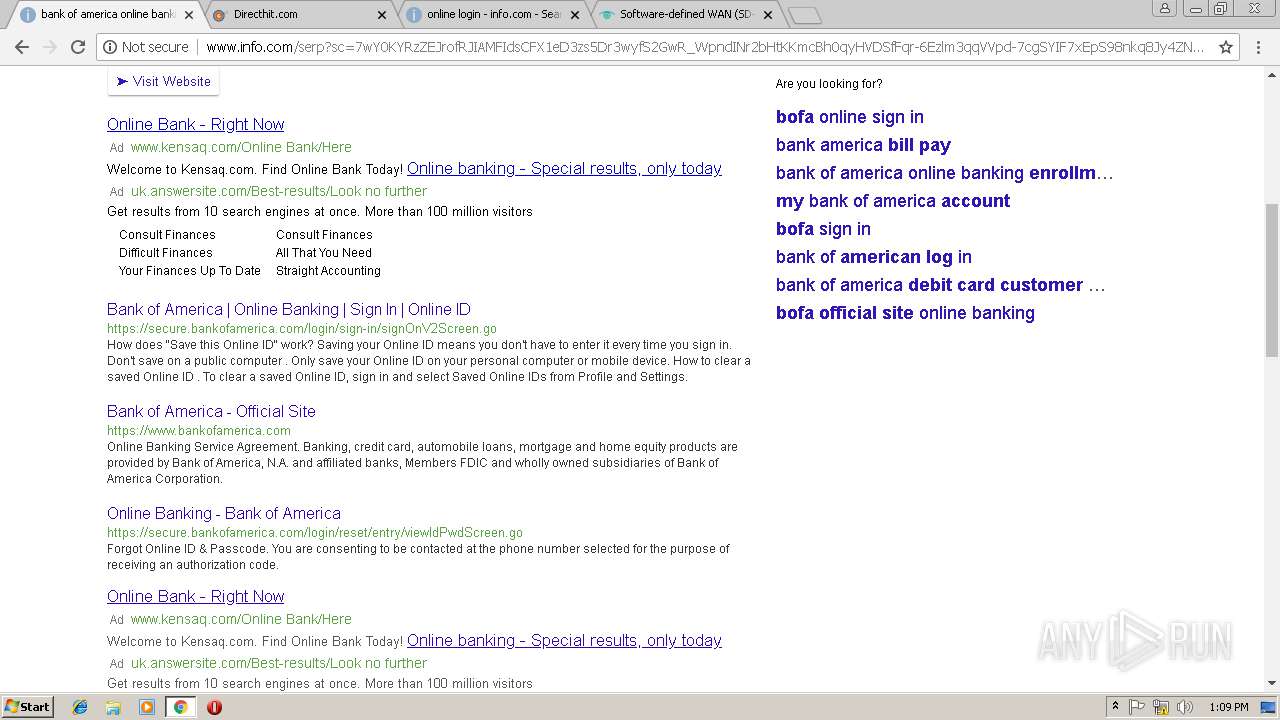
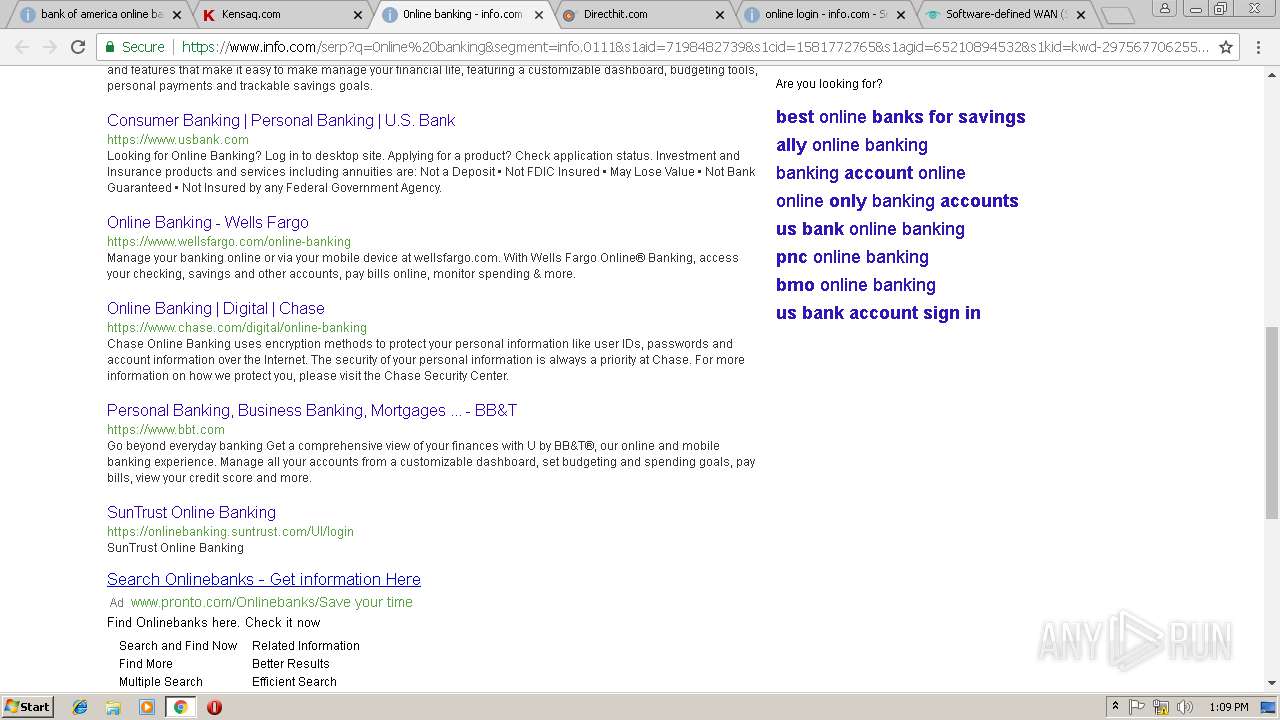
3004 | chrome.exe | GET | 200 | 52.17.173.115:80 | http://www.info.com/?capv=3CVEK2zNH7cyL8jhEMnbjKVsE-23ULQwpq7qOC91mUyFmdfBrUxESUb-dxRnvx52 | IE | html | 11.6 Kb | suspicious |
3004 | chrome.exe | GET | 200 | 52.17.173.115:80 | http://www.info.com/static/www.info.com/favicon-16x16.png | IE | image | 411 b | suspicious |
3004 | chrome.exe | GET | 200 | 52.17.173.115:80 | http://www.info.com/?sc=pskZC2gwg2ZAA7Vyt7pSxBIfT62PAwbHwqbryxi0lk0_4anU8Or-ya5zj_ySUHRCa_Zm1zeh6FGns34QtOd_Zj8AvnBwfUL_zAlIHHnyQqqPOsf5EUdY7d9LxH7spNZtaW-HTZEoqsFhswaj8HbeOkvD_zmnVGmuUctZ7Q8RcdNpw3hiM8ubHXBDoLrkT8WAP3tY1nnCs0ZlhVWYB9mEB5PZBL-T1oZB2L2VGDPICl5LeJQtF2ucureg2hqfNz7UEbC2uC6X72otqCoUi_we5NhO_q8daFiYnhcII3Wz-ZY9mtV9PvD9n5jOADI4V0TGvnaS2wWOVGImcZvEYbeQusHlK8Fza_jUvuf86cyQXTodi3rYUT7-CgRz7hdDOx2x84mQf3CSasqC-wEStLW8YVqROzF034lxAwbdnQOLZH2yBHEW4Ittc-5ZIdnC1JCXOM-7ZdWS4lR0sNkzjCkVwYWup45mJpXj9fCjio2pxf9pOgjs3Q3qJcj8PnKdkku0HOivJ-EGkUfGI-u3ZFpy92tXmPs3kE_rLMh-Va7PeG9FuTKvsJQQn3sZf51bWeEaHCTazicCvwauKc9K6p1pFmyEFhfpFQ7r0_dwHDbguZBfSCEDlTb9Gst3xQ5MIpxMT-xBWPHYzr7d3OKNDVBLslKQhEZ_5Z_3h8-7Yc7KIv4ehCNJ1Au3Am4rM9CE9sMP-9g3l4CNv4v5e5wiEAgWZWNaef_HJjXvqIKsgFJImMk_J5VprfkymKEwb7RQ9V6oFShee-pFkq4p3deOmilChFsxJEfAr13KQ0CHMCUwBCPxfisurS5LMUY9ez4NiLYu9_oW8Zk2WIp0hje-csh5S_jMHrCt8b5wn2KcA5uebKhVGOXIXYSj5v3T9E03NzqXBi6imz8K1QQ5kmYpu4TfvCeqswT0yyoGRFfJ0n6QZ4fIkx-ZMFca9UY8En_2EI4CXkfl1K7gb2DEvJMc-2zUOTuVeKJtl59VKaF4jlLMIPW9SsGX_2E0WhHbdnakrQD2b27t4tWEvds2yfuKKqv6uQrxTasmhrIuQjivMmtJHaqp0hPOrOE_Q4vcKxvo5aSn66CUweG77mdVFLF8qncILr3Zd06O8Ss8AGi3VogiXMorSYXevnxvBwRAXHhYBkCMaNAc2kpRFJ6uxG55F5IPaUE7mLAFO07vHRYvkwm-Xl4AAGliapT4Ny1mRWy1awjX7JzLcWzmJdh2MIHQMhQG0xxLG43fpvVsNhMnDz8TMZtkKOk-I4bI2wiRv9cuX_psBElGKhhe4PZyKgXkXzn6IM-S6Bz0axx1smiOl-VfufofHrhPeL76M13_ua-pdiVnxWKAsfN5oNAWeKGi-vHVNnJHGCgas6MATjckU3IiK1J5vnB_a_XR5iKx5l8wQ4MTUSxjWrcYzKMWt-vnAw_5LUl7G61206nAOEx8fMdB0ZddRCiHR81cOz_4WUAEsjK1r-1ldD4xRz-lgdzC452lhh8ycVfie7TA4bnCV5mCjDLAUr4tccz62vPaQ5vr6Eay6318JcsaGw&qc=video | IE | html | 11.7 Kb | suspicious |
3004 | chrome.exe | GET | 200 | 52.17.173.115:80 | http://www.info.com/static/www.info.com/favicon.ico | IE | image | 5.30 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 35.161.37.37:80 | omblockedips.com | Amazon.com, Inc. | US | unknown |
3004 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3004 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 52.17.173.115:80 | www.info.com | Amazon.com, Inc. | IE | unknown |
3004 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3004 | chrome.exe | 13.32.222.182:80 | x.ss2.us | Amazon.com, Inc. | US | malicious |
3004 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3004 | chrome.exe | 52.210.170.99:443 | soflopxl.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
omblockedips.com |
| unknown |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.info.com |
| suspicious |
soflopxl.com |
| whitelisted |
www.google.com |
| malicious |
www.infospace.com |
| unknown |
x.ss2.us |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3004 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3004 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report