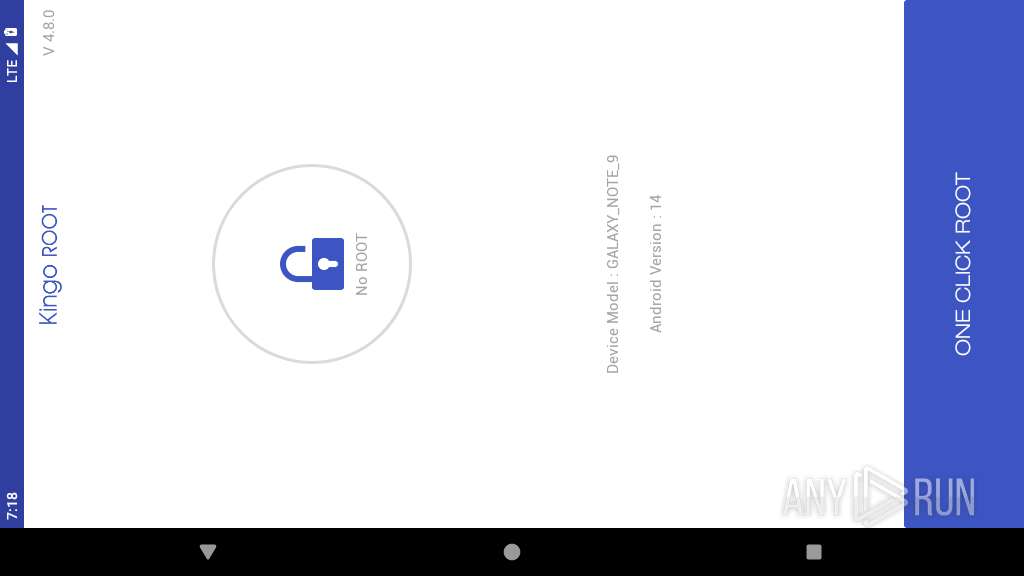
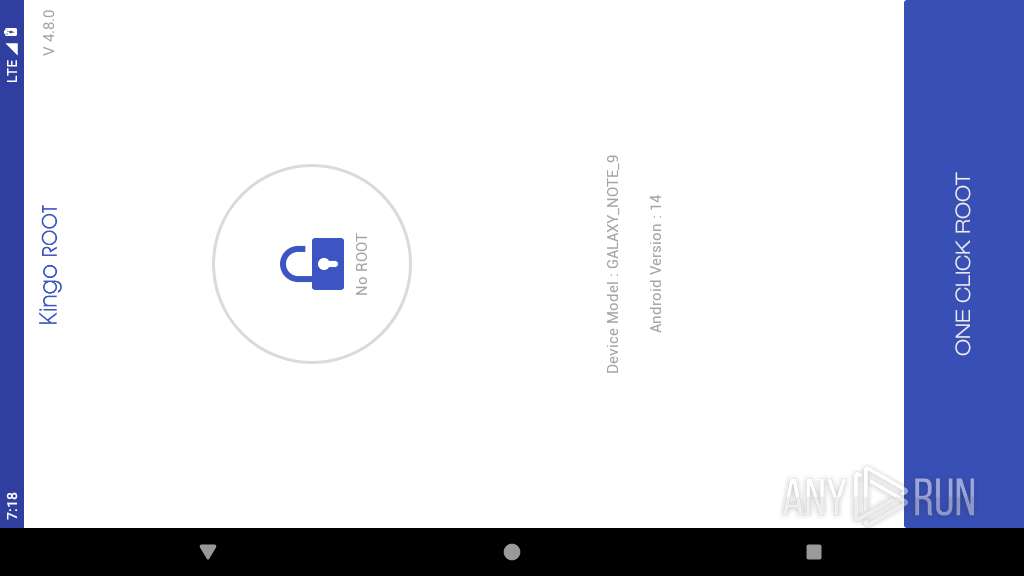
| File name: | KingoRoot (1).apk |
| Full analysis: | https://app.any.run/tasks/ef3d3e45-e7ee-49d7-b843-99259ff52382 |
| Verdict: | Malicious activity |
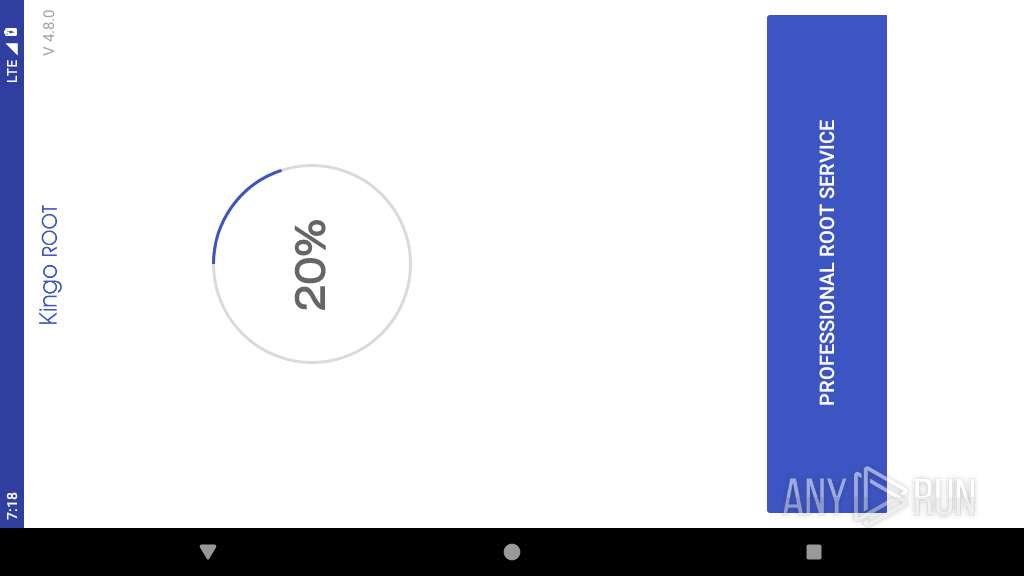
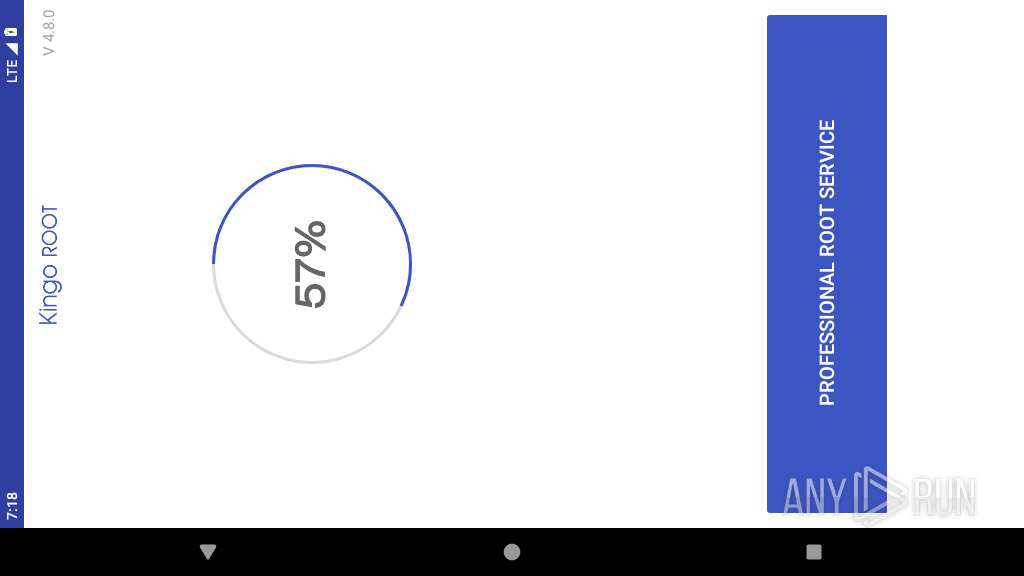
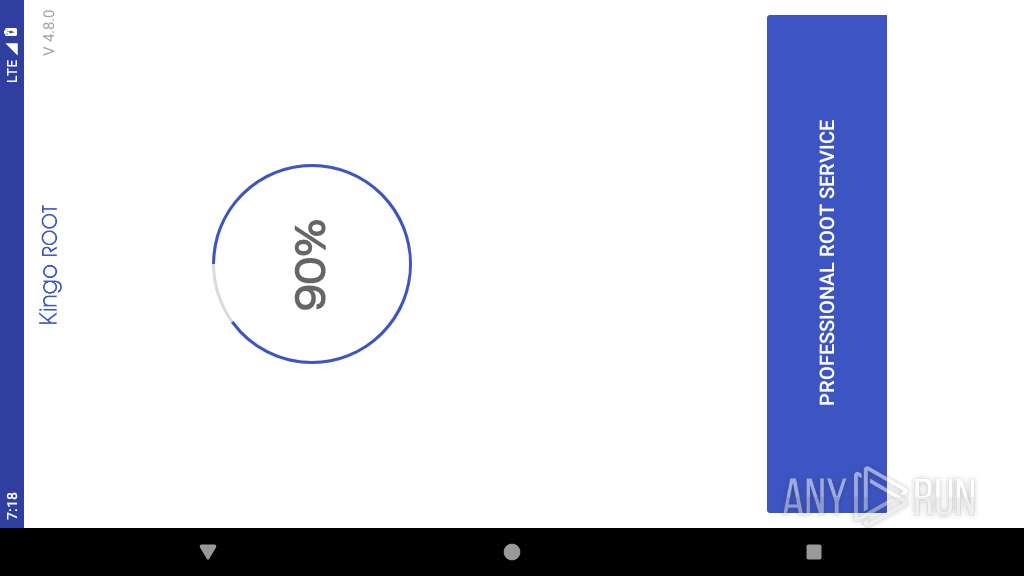
| Analysis date: | May 25, 2025, 19:18:25 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with AndroidManifest.xml, with APK Signing Block |
| MD5: | 984DC0ADB3ABF6F4174DD21E9D946123 |
| SHA1: | E82D633525F54682F2ECFA4EA8C5A5FFB7A991F4 |
| SHA256: | E6B2EC7E8663229A0F8DD903D7704CCFDE81F7AE0B1881407E068E63A7F125B8 |
| SSDEEP: | 98304:LL7c1ghMjxqBMzaGbybIcIi7PakaCFFblLmaG+vahmLPom91wIDgZ94uz9159hO+:ouDlLgnvmWx |
MALICIOUS
Executes system commands or scripts
- app_process64 (PID: 2261)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2261)
Accesses system-level resources
- app_process64 (PID: 2261)
Executes dynamic code using class loader
- app_process64 (PID: 2261)
Potential Corporate Privacy Violation
- app_process64 (PID: 2261)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2261)
Creates a WakeLock to manage power state
- app_process64 (PID: 2261)
Starts a service
- app_process64 (PID: 2261)
INFO
Verifies whether the device is connected to the internet
- app_process64 (PID: 2261)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2261)
Dynamically loads a class in Java
- app_process64 (PID: 2261)
Handles throwable exceptions in the app
- app_process64 (PID: 2261)
Gets file name without full path
- app_process64 (PID: 2261)
Retrieves the value of a secure system setting
- app_process64 (PID: 2261)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2261)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xf84c422c |
| ZipCompressedSize: | 3880 |
| ZipUncompressedSize: | 17120 |
| ZipFileName: | AndroidManifest.xml |
Total processes
188
Monitored processes
63
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2261 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2324 | com.kingoapp.apk | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 32512 | ||||
| 2326 | com.kingoapp.apk | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 32512 | ||||
| 2351 | com.kingoapp.apk | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2353 | com.kingoapp.apk | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2354 | getprop ro.board.platform | /system/bin/toolbox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2356 | cat proc/version | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
| 2358 | com.kingoapp.apk | /system/bin/app_process64 | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2359 | getprop ro.product.cpu.abi | /system/bin/toolbox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2361 | cat proc/version | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 256 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
54
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/com.crashlytics.sdk.android:answers:settings.xml | xml | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/LOG_COONFIG.xml | — | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/com.crashlytics.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/files/ac | binary | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/files/.Fabric/com.crashlytics.sdk.android.crashlytics-core/68336D0E01BB-0001-08D5-5FAFAC25FEE6BeginSession.cls_temp | binary | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/TwitterAdvertisingInfoPreferences.xml | xml | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/files/.Fabric/com.crashlytics.sdk.android:answers/session_analytics.tap.tmp | binary | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/files/.Fabric/com.crashlytics.sdk.android.crashlytics-core/68336D0E01BB-0001-08D5-5FAFAC25FEE6BeginSession.json | binary | |
MD5:— | SHA256:— | |||
| 2261 | app_process64 | /data/data/com.kingoapp.apk/shared_prefs/VM_COONFIG.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
16
DNS requests
12
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 172.217.18.3:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2261 | app_process64 | POST | 200 | 45.33.31.138:80 | http://service.kingoapp.com/api/v3/new-mobile-root?api-key=kingosdk¤t-version=480&sdk-version=10 | unknown | — | — | unknown |
2261 | app_process64 | GET | 200 | 104.26.13.219:80 | http://dl.kingoapp.com/mobile-root/dependent/KingoUser.apk | unknown | — | — | unknown |
2261 | app_process64 | GET | 200 | 104.26.13.219:80 | http://dl.kingoapp.com/mobile-root/dependent/rootkit_io.zip | unknown | — | — | unknown |
2261 | app_process64 | GET | 200 | 104.26.13.219:80 | http://dl.kingoapp.com/mobile-root/dependent/busybox | unknown | — | — | unknown |
2261 | app_process64 | POST | 200 | 45.33.31.138:80 | http://service.kingoapp.com/api/other/sdk/status | unknown | — | — | unknown |
2261 | app_process64 | POST | 200 | 45.33.31.138:80 | http://service.kingoapp.com/api/v3/new-mobile-root?api-key=kingosdk¤t-version=480&sdk-version=10 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 216.239.35.0:123 | time.android.com | — | — | whitelisted |
— | — | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 172.217.18.3:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 64.233.167.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2261 | app_process64 | 50.116.31.237:80 | api.bos.kgmobi.com | Linode, LLC | US | unknown |
2261 | app_process64 | 47.91.65.64:80 | — | Alibaba US Technology Co., Ltd. | DE | unknown |
2261 | app_process64 | 45.33.31.138:80 | service.kingoapp.com | Linode, LLC | US | unknown |
2261 | app_process64 | 104.26.13.219:80 | dl.kingoapp.com | CLOUDFLARENET | US | unknown |
2261 | app_process64 | 142.250.185.238:443 | app-measurement.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
google.com |
| whitelisted |
api.bos.kgmobi.com |
| unknown |
settings.crashlytics.com |
| whitelisted |
javacloud.bmob.cn |
| unknown |
service.kingoapp.com |
| unknown |
dl.kingoapp.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2261 | app_process64 | Potential Corporate Privacy Violation | ET INFO Executable and linking format (ELF) file download Over HTTP |