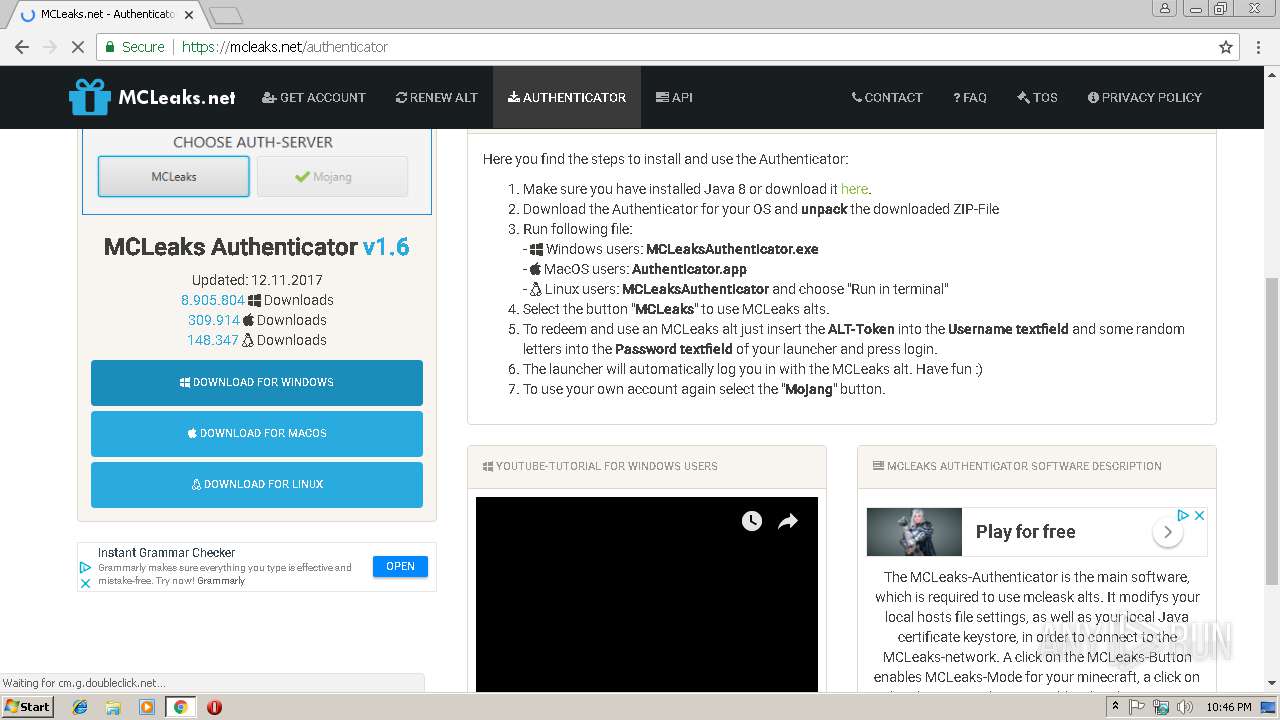
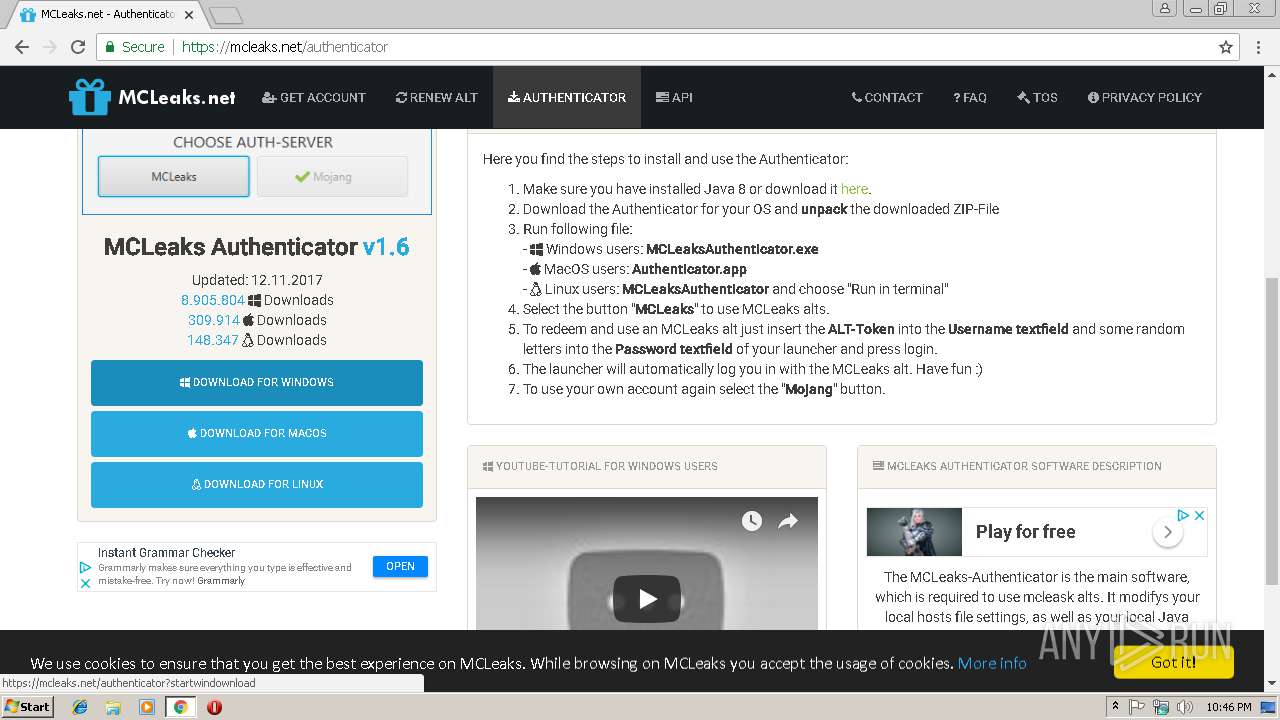
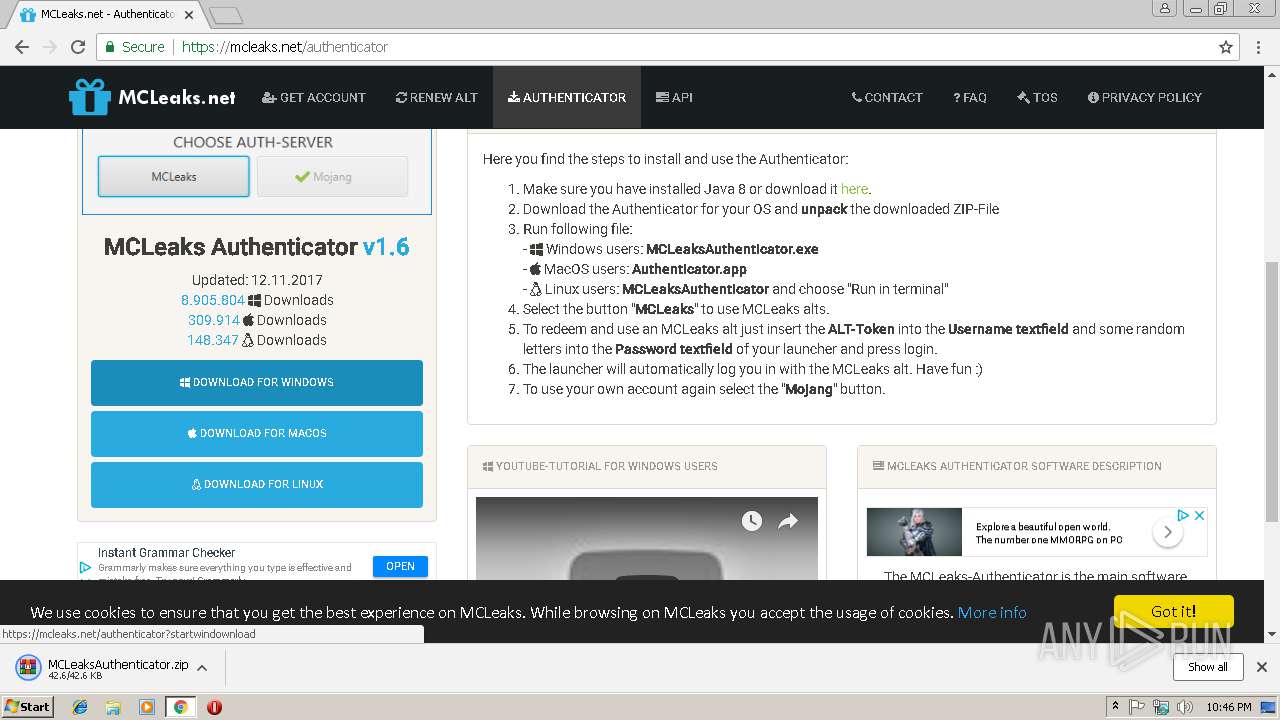
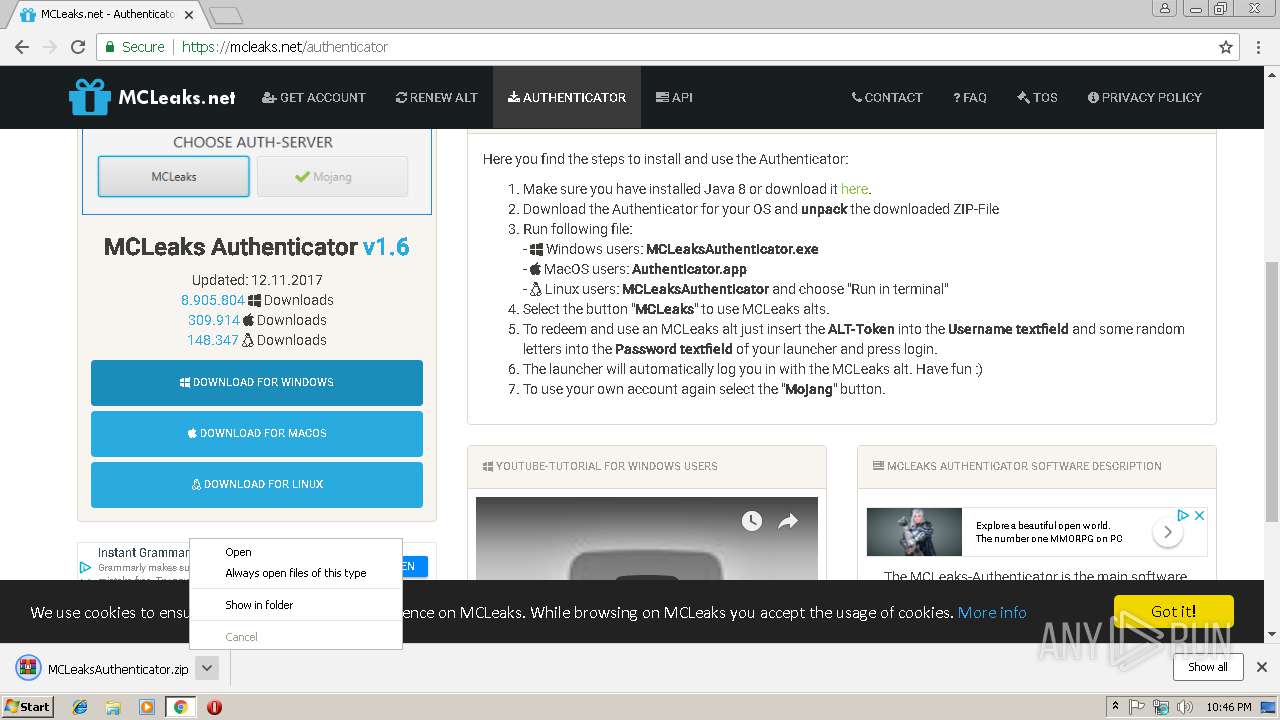
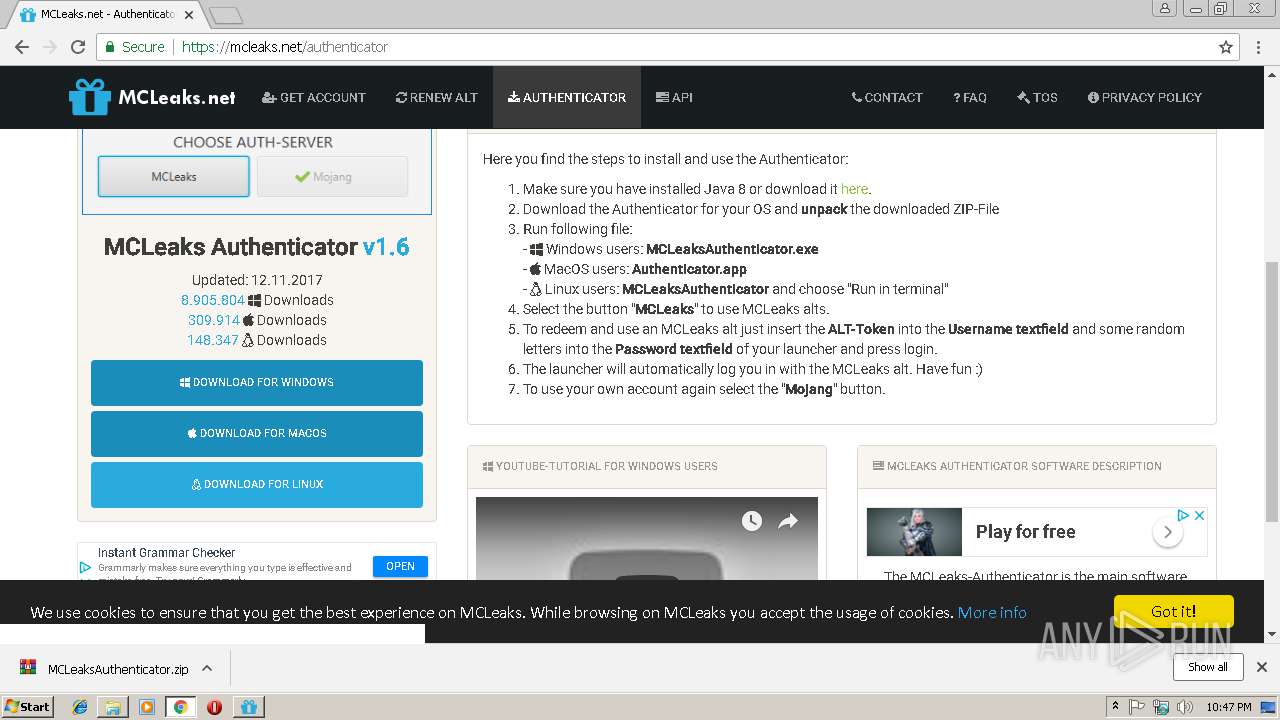
| URL: | https://mcleaks.net |
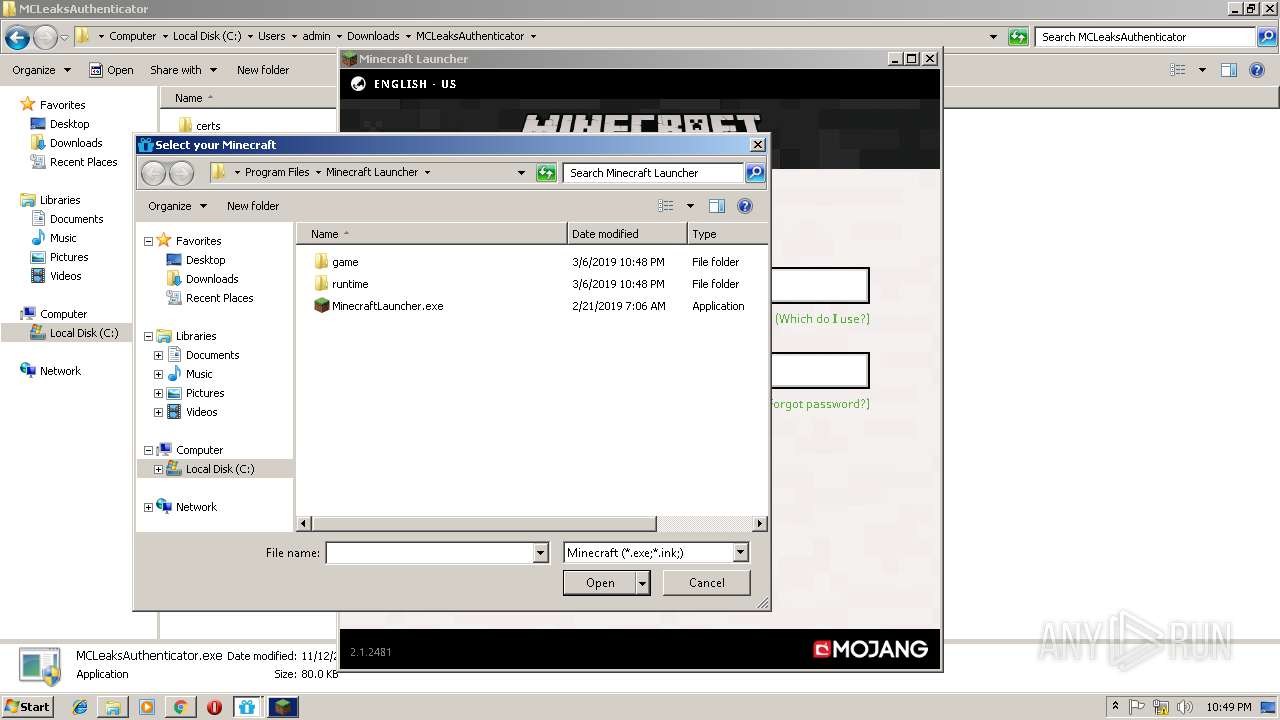
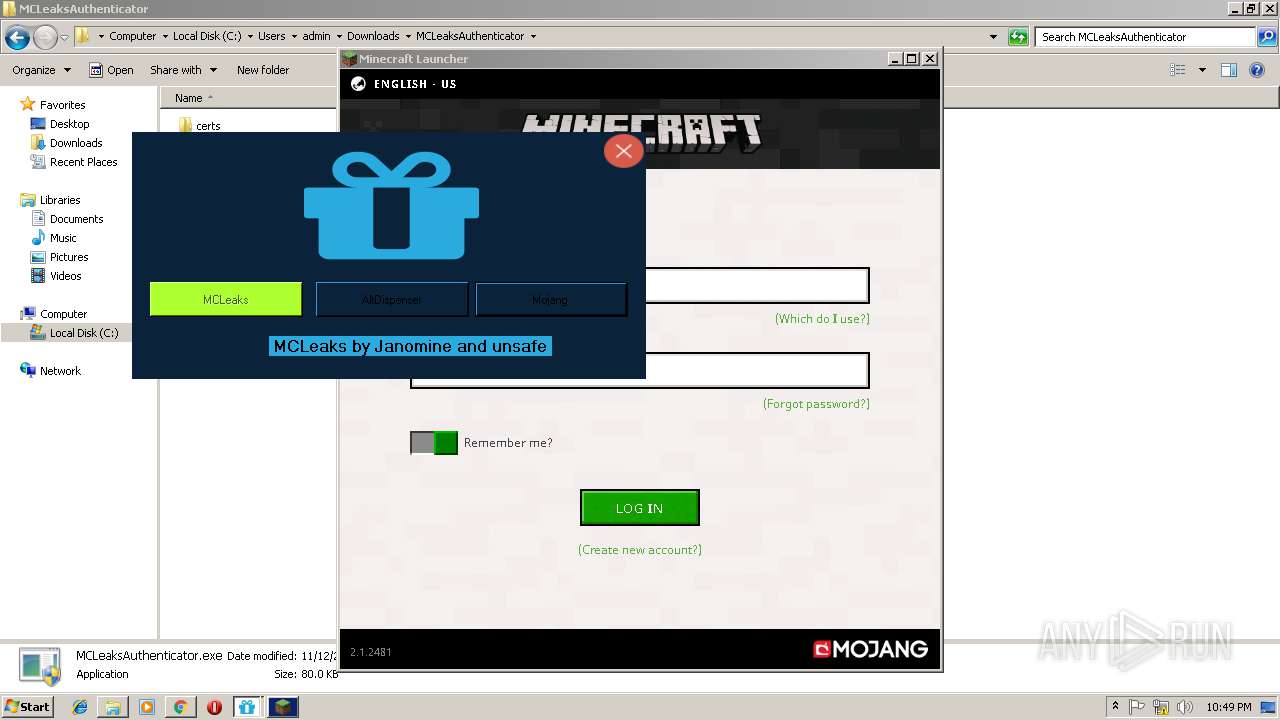
| Full analysis: | https://app.any.run/tasks/c4a3bc43-93b6-48b7-8db5-583e56408e31 |
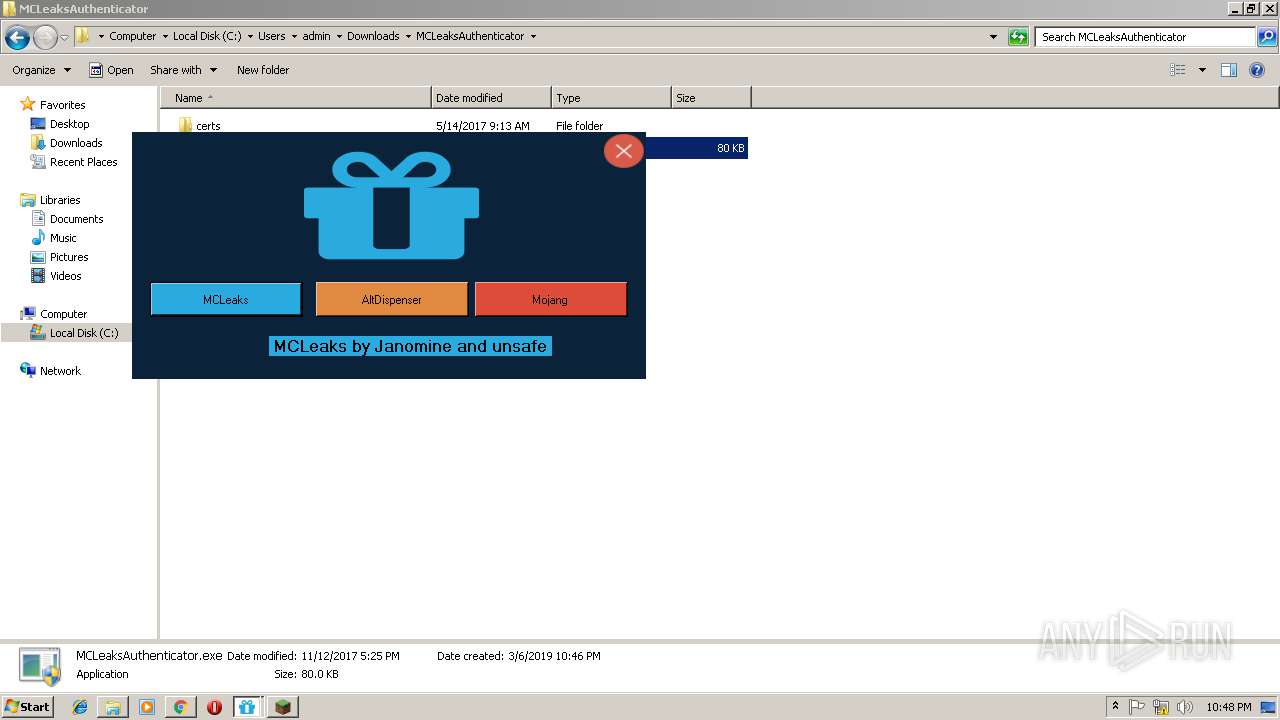
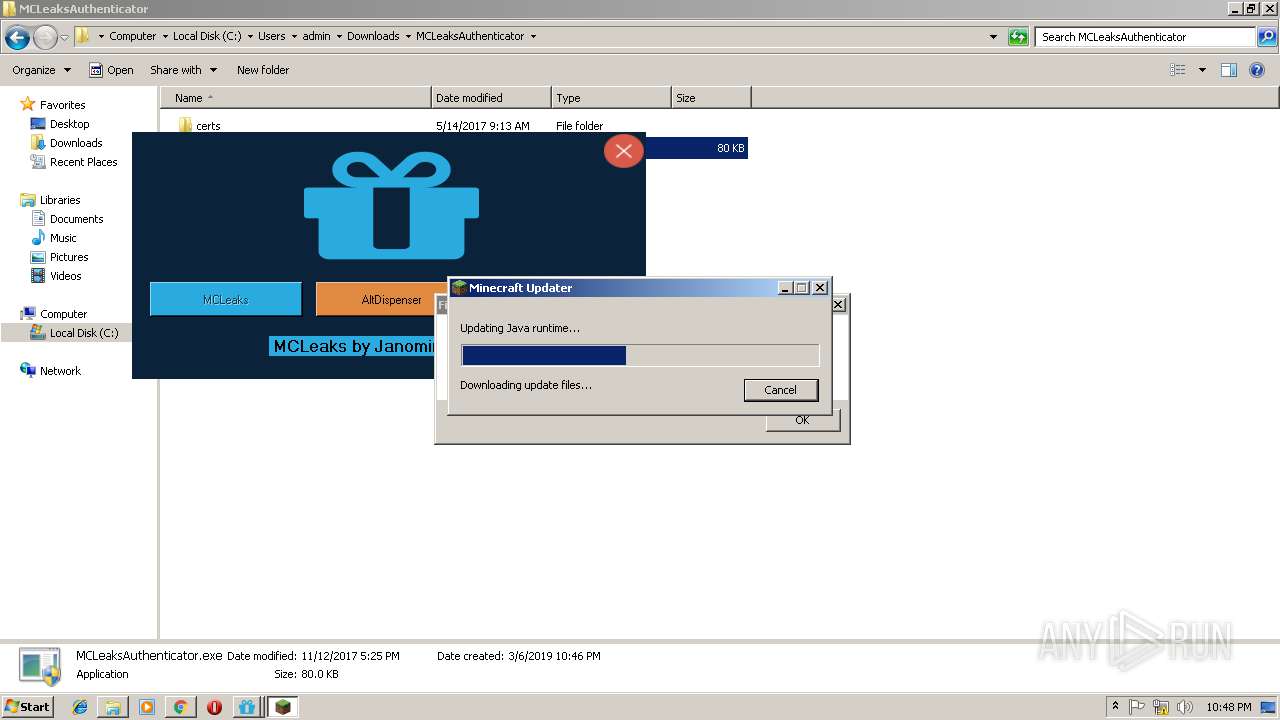
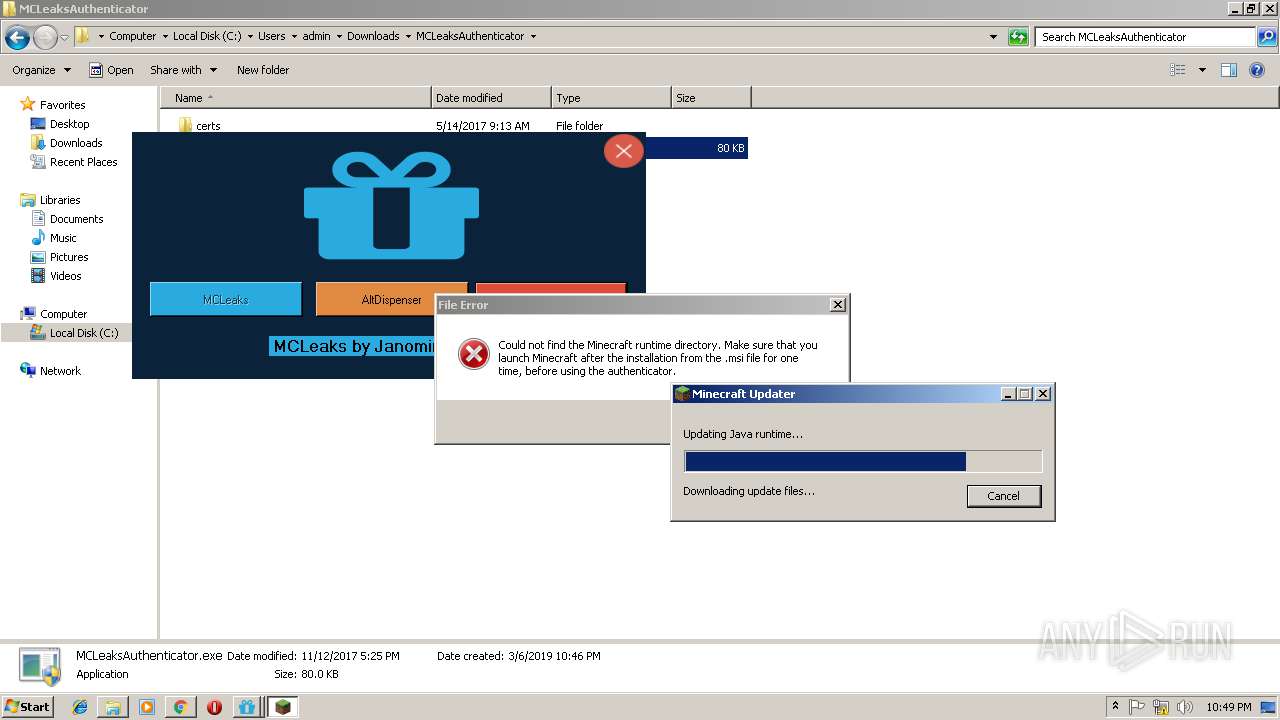
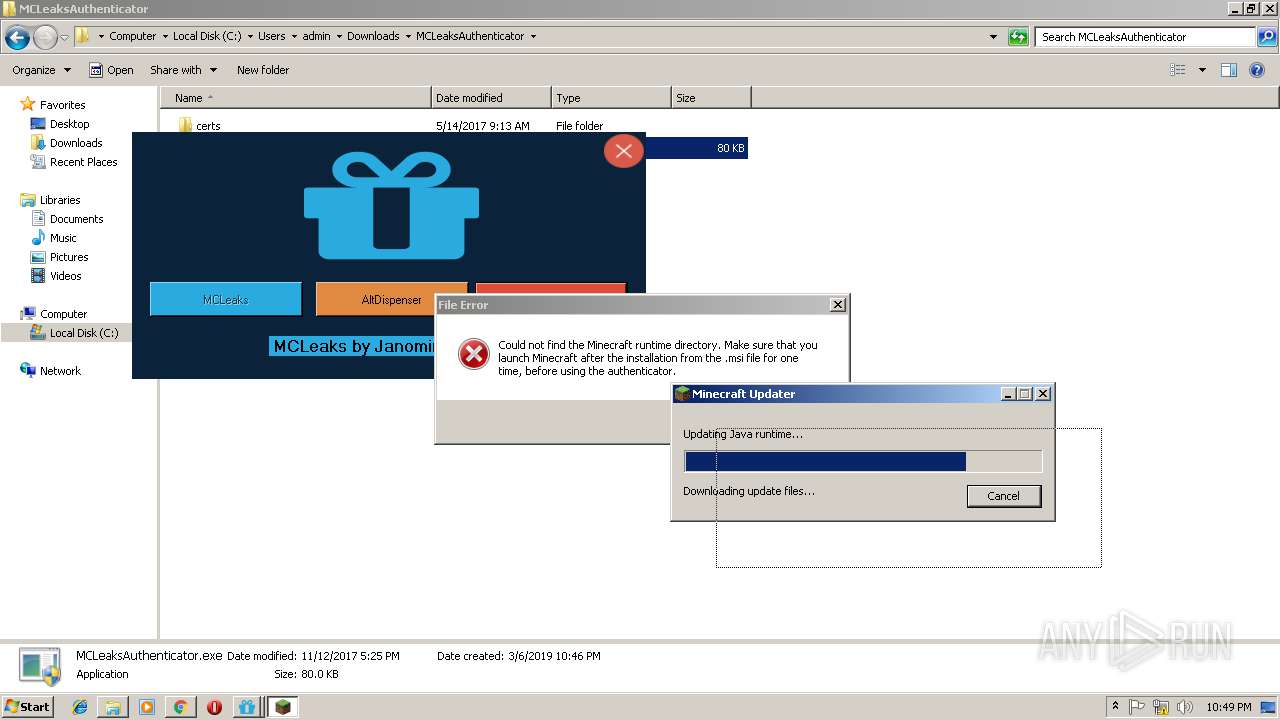
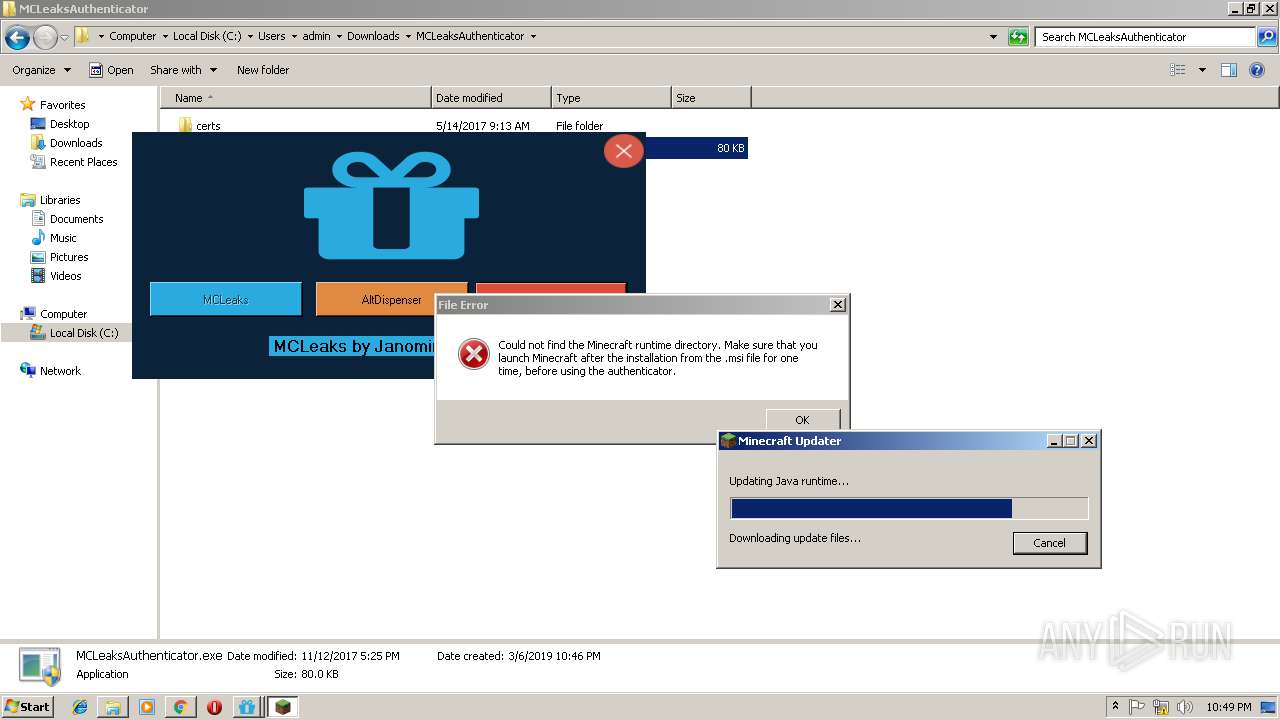
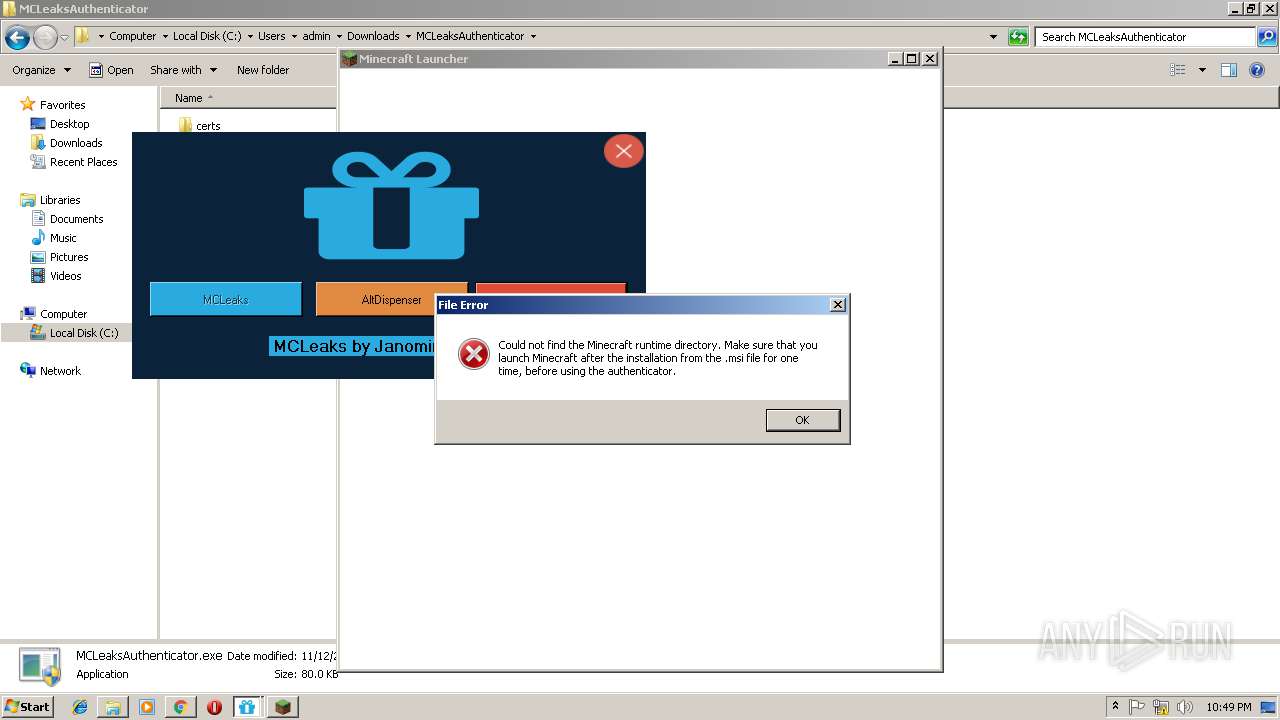
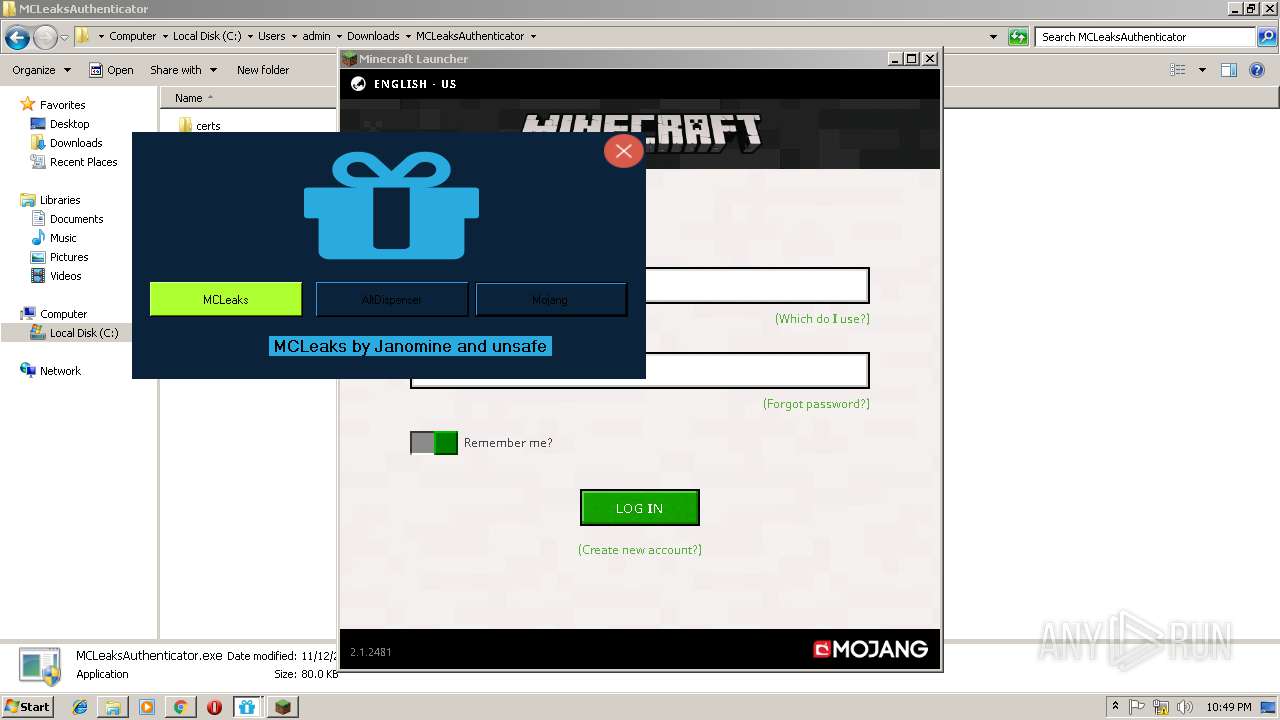
| Verdict: | Malicious activity |
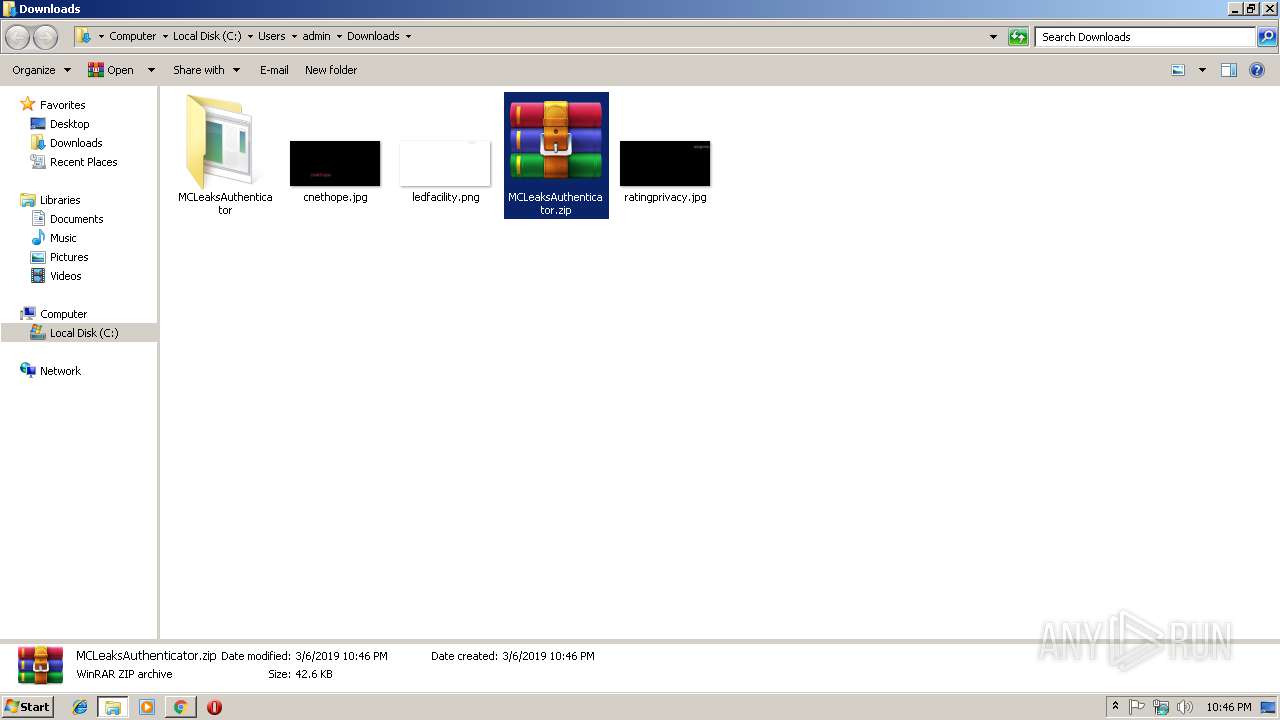
| Analysis date: | March 06, 2019, 22:45:59 |
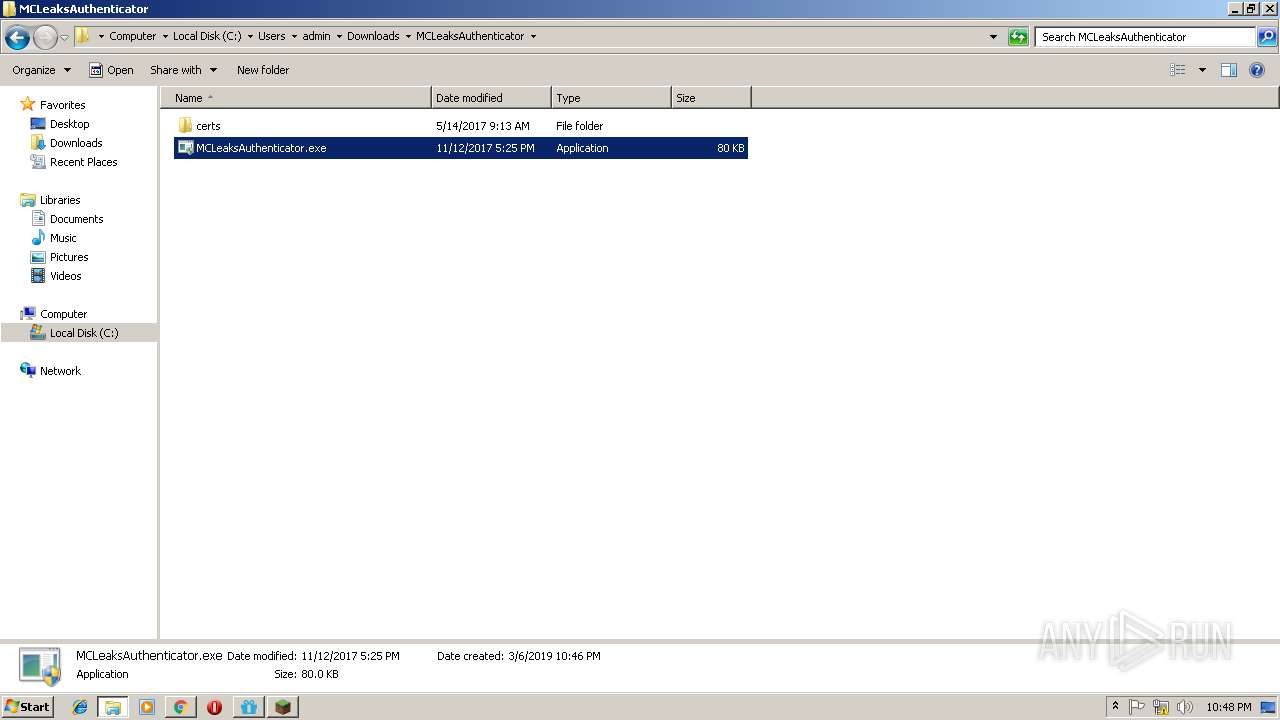
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CF636C727026A850F607365E51BF2D00 |
| SHA1: | 9A6731AD58A7FB0280649FDC8750CE4D385EEC1C |
| SHA256: | E6B085BD77E190B974630464D6D379C5EA6ABEC2251115F3EA672A6092E45E06 |
| SSDEEP: | 3:N8PAEh0:241 |
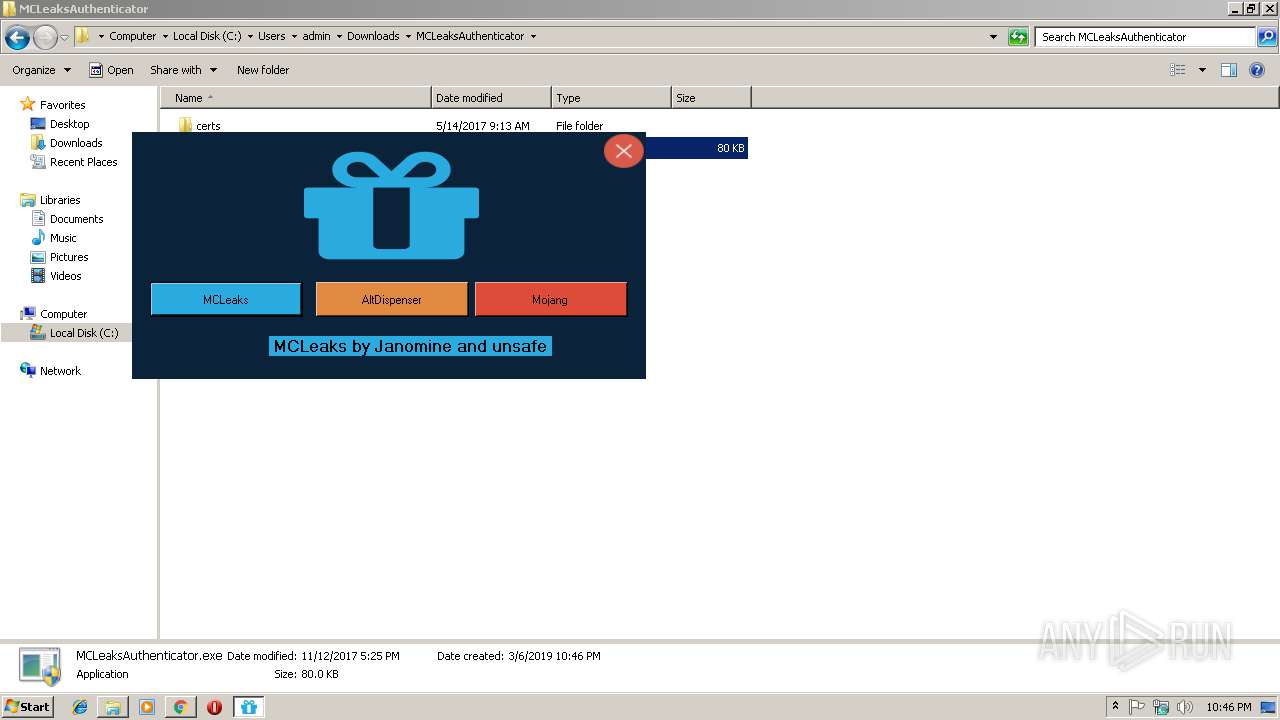
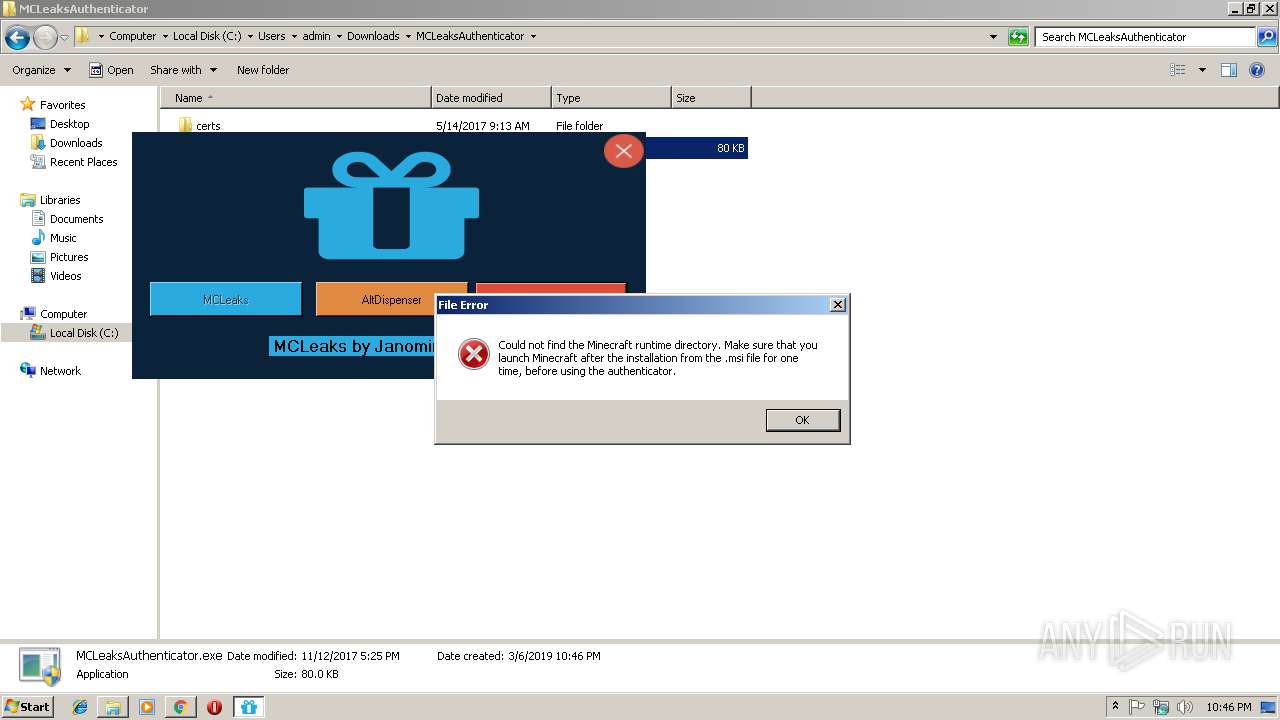
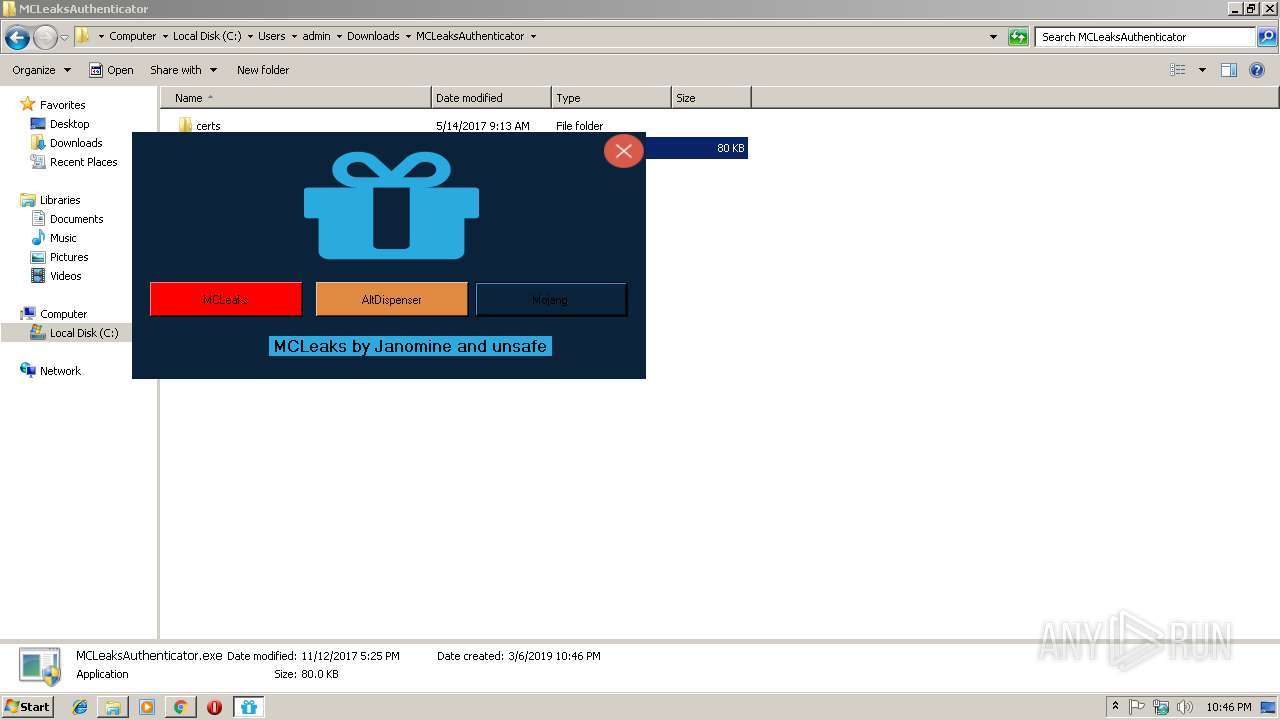
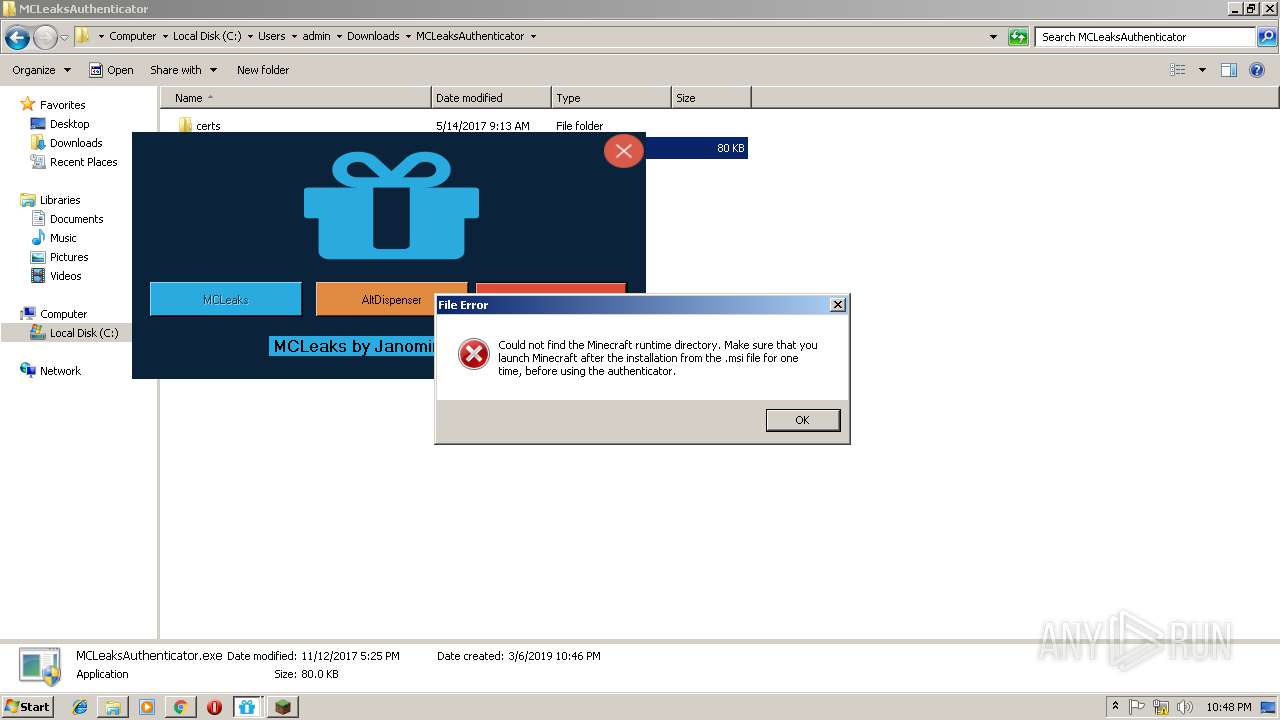
MALICIOUS
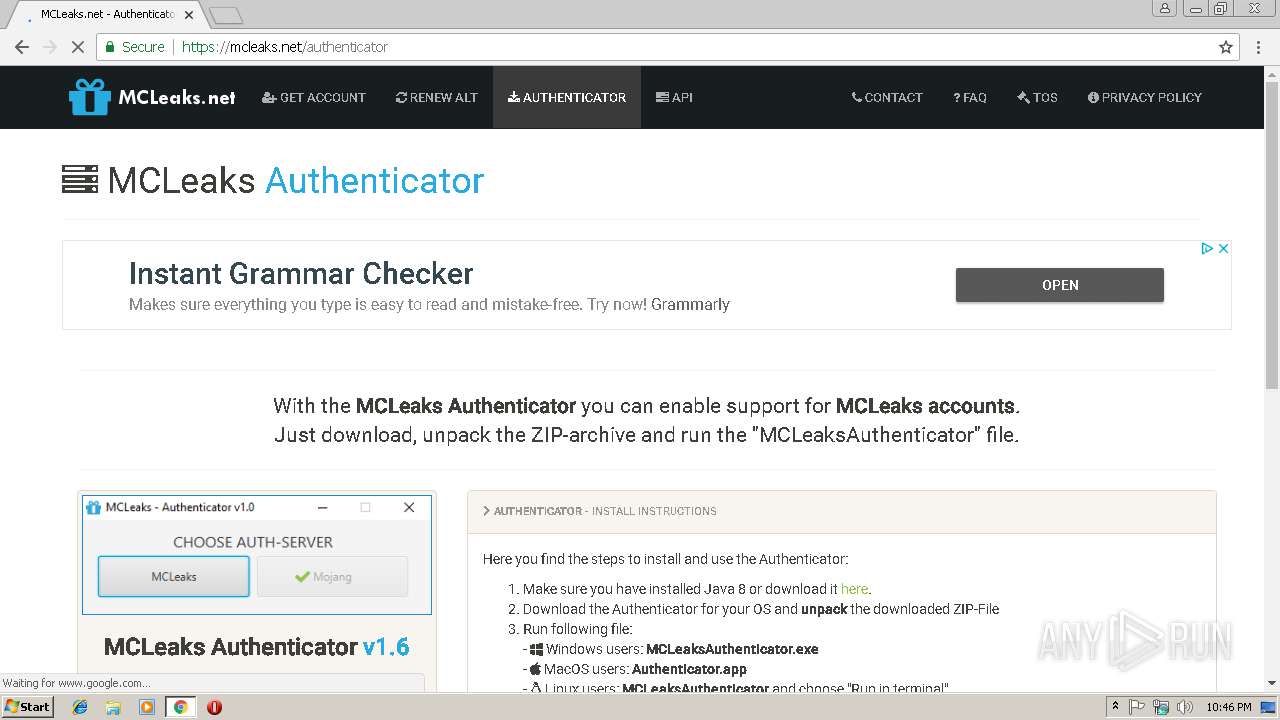
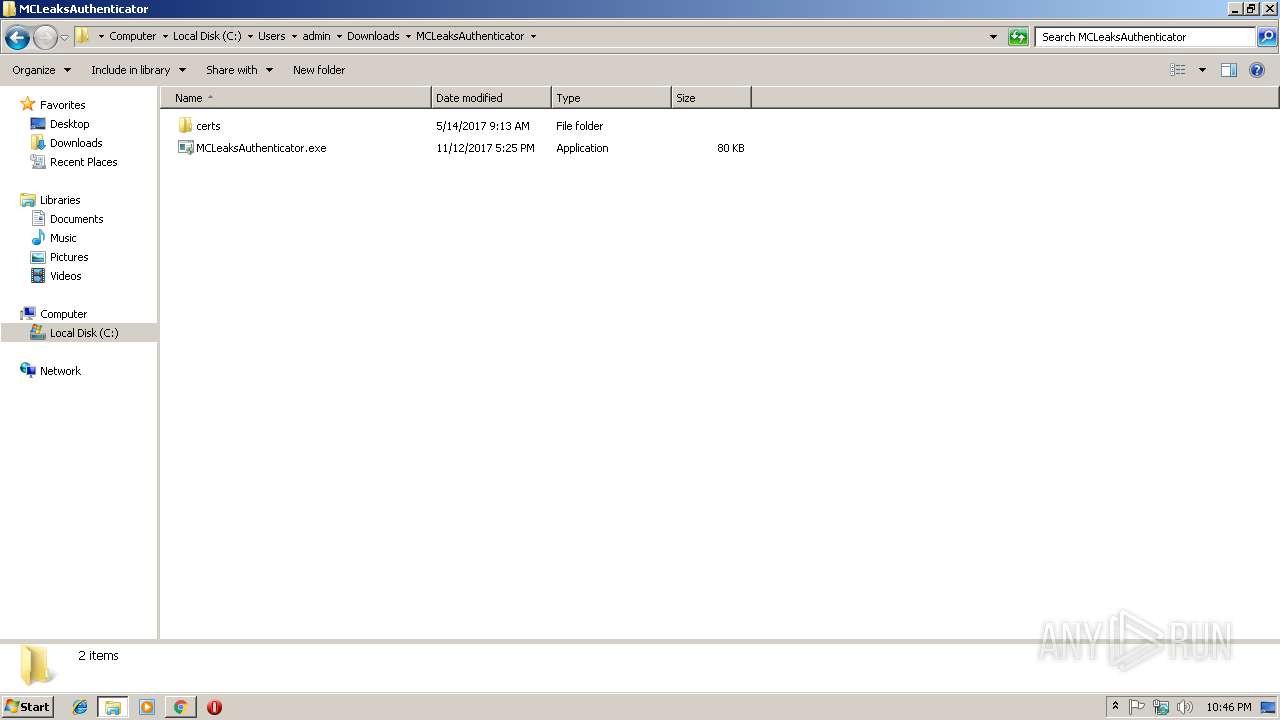
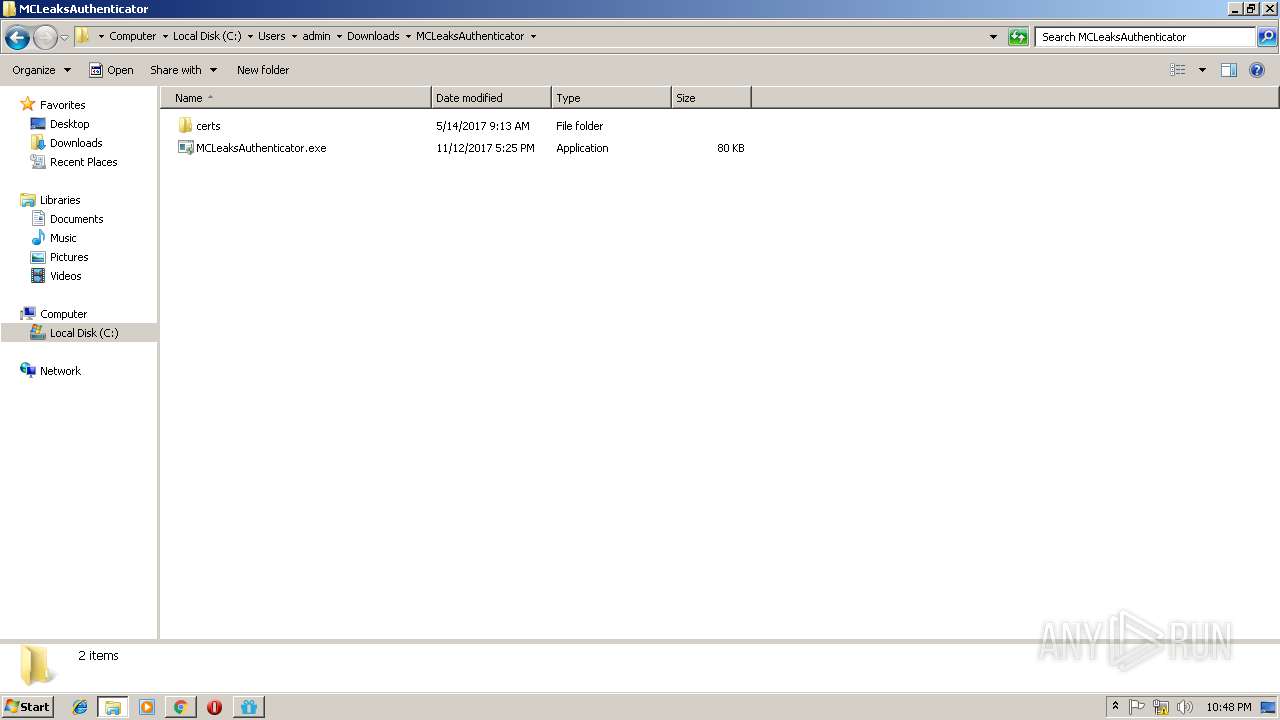
Application was dropped or rewritten from another process
- MCLeaksAuthenticator.exe (PID: 2660)
- MCLeaksAuthenticator.exe (PID: 3520)
- MCLeaksAuthenticator.exe (PID: 3020)
- MinecraftLauncher.exe (PID: 2260)
- MinecraftLauncher.exe (PID: 3816)
- MCLeaksAuthenticator.exe (PID: 2820)
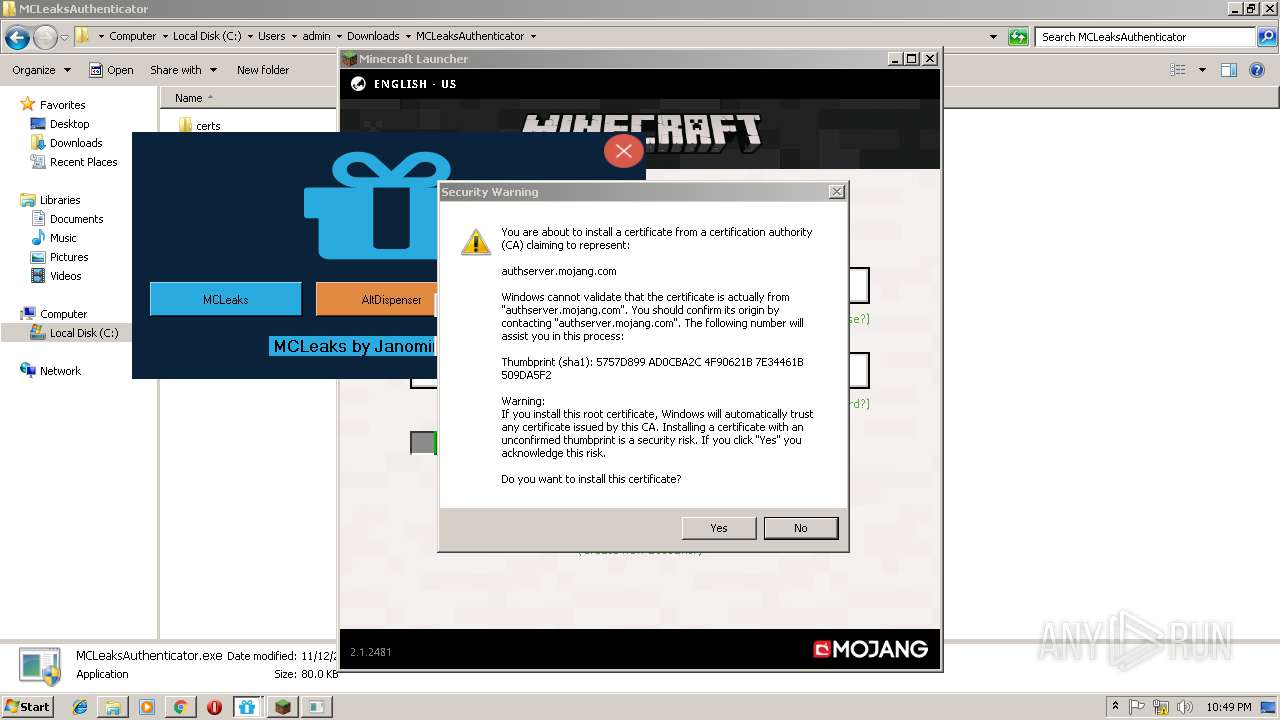
Changes settings of System certificates
- MCLeaksAuthenticator.exe (PID: 2660)
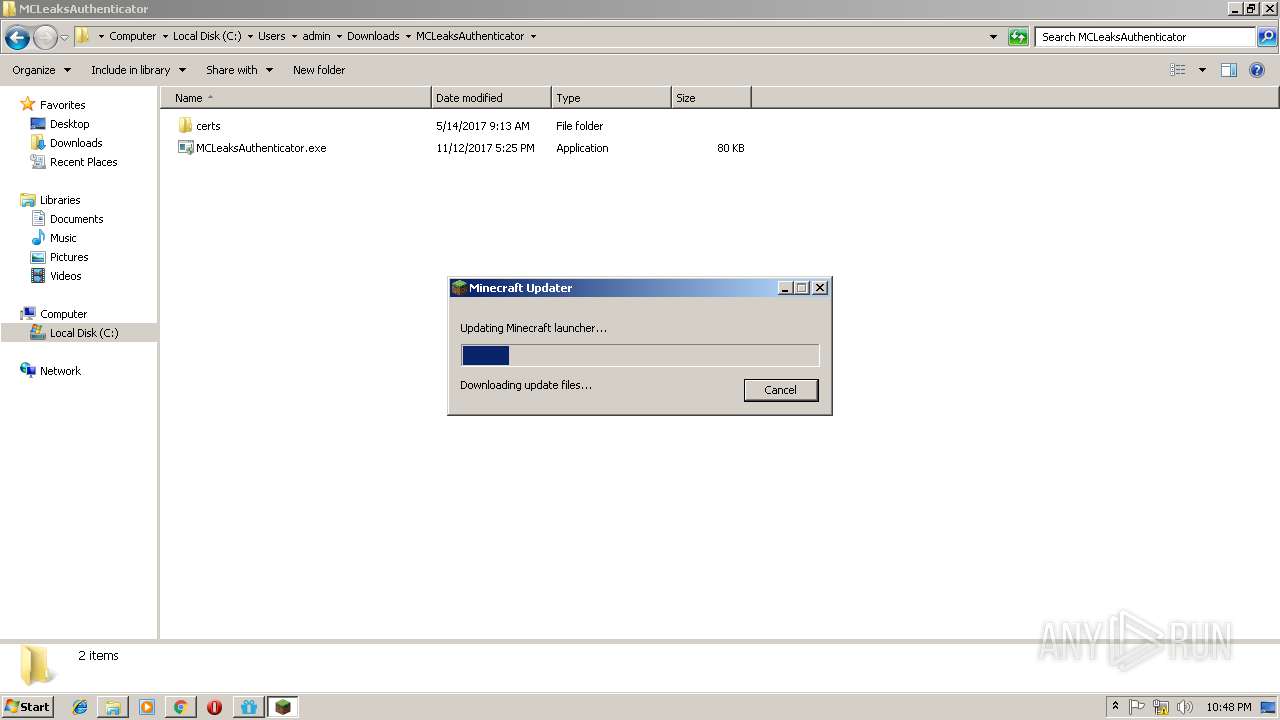
Loads dropped or rewritten executable
- MinecraftLauncher.exe (PID: 3816)
- MinecraftLauncher.exe (PID: 2260)
SUSPICIOUS
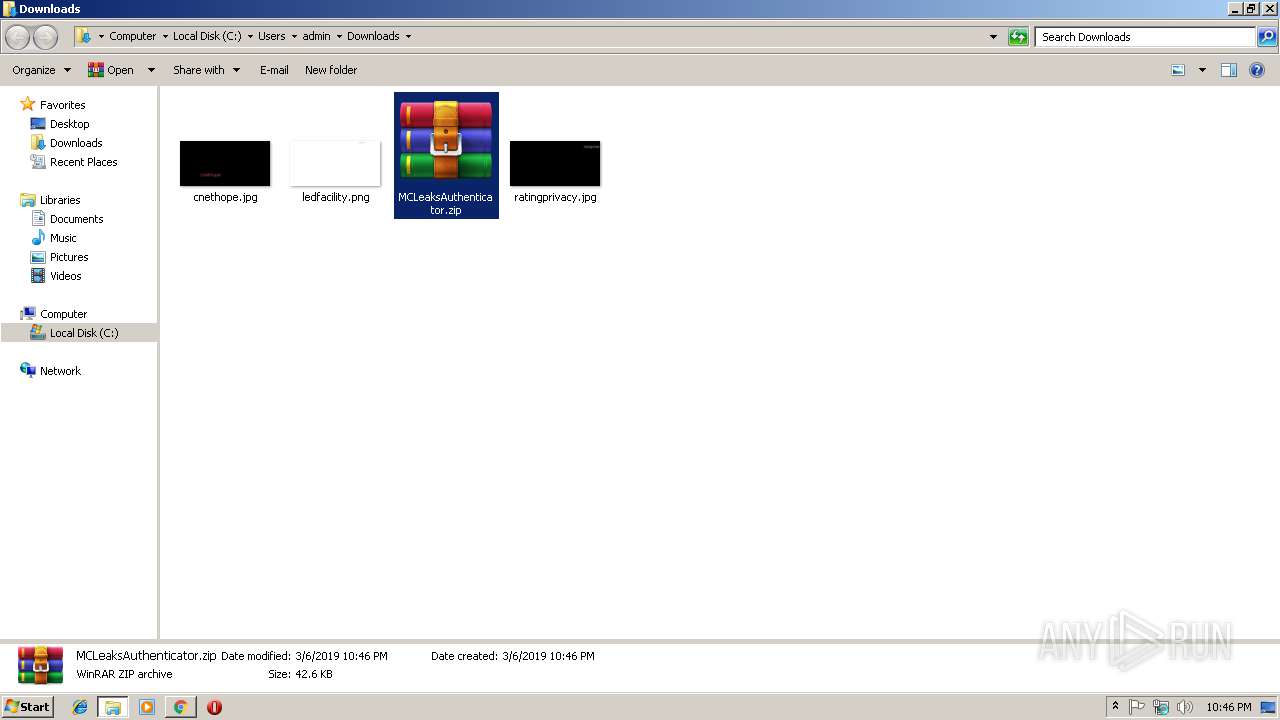
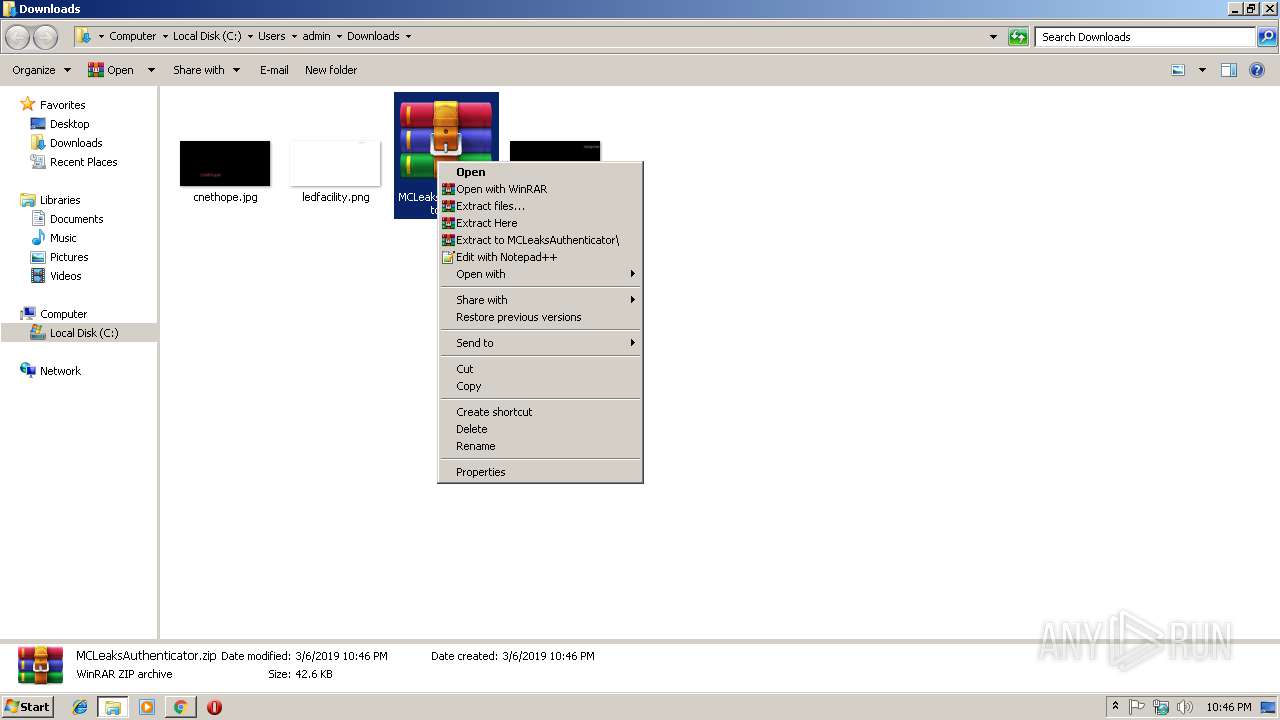
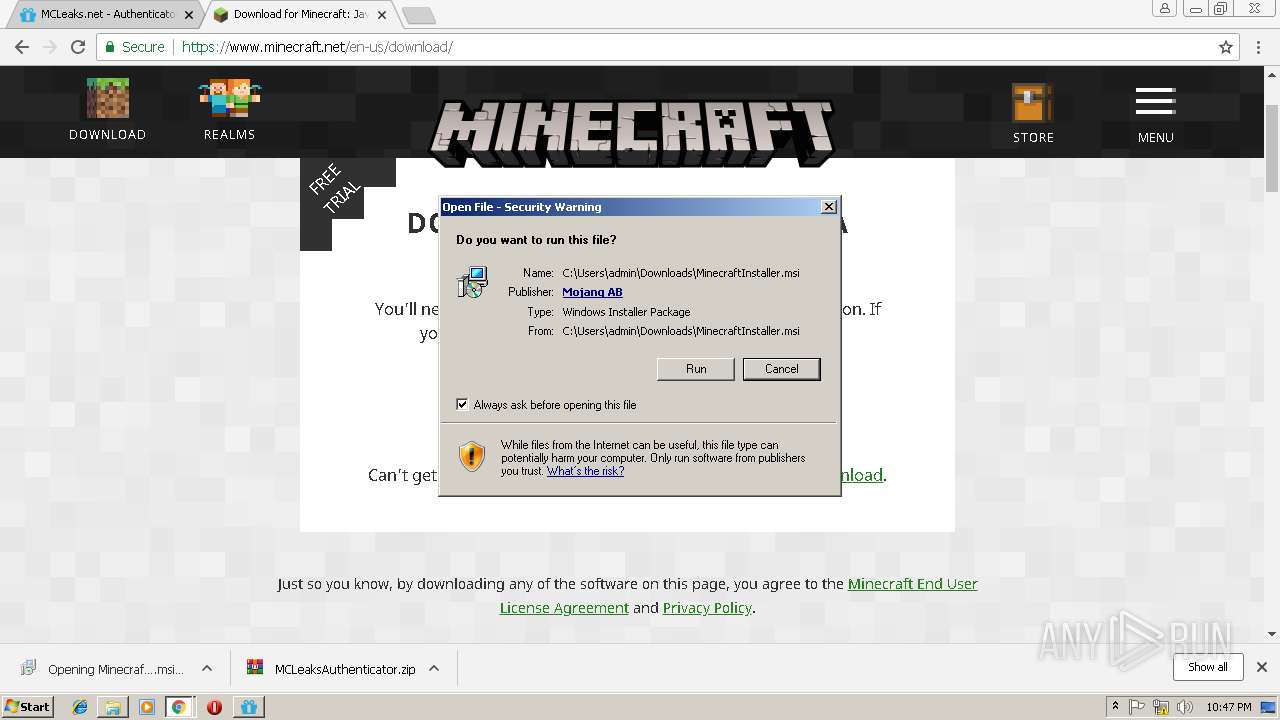
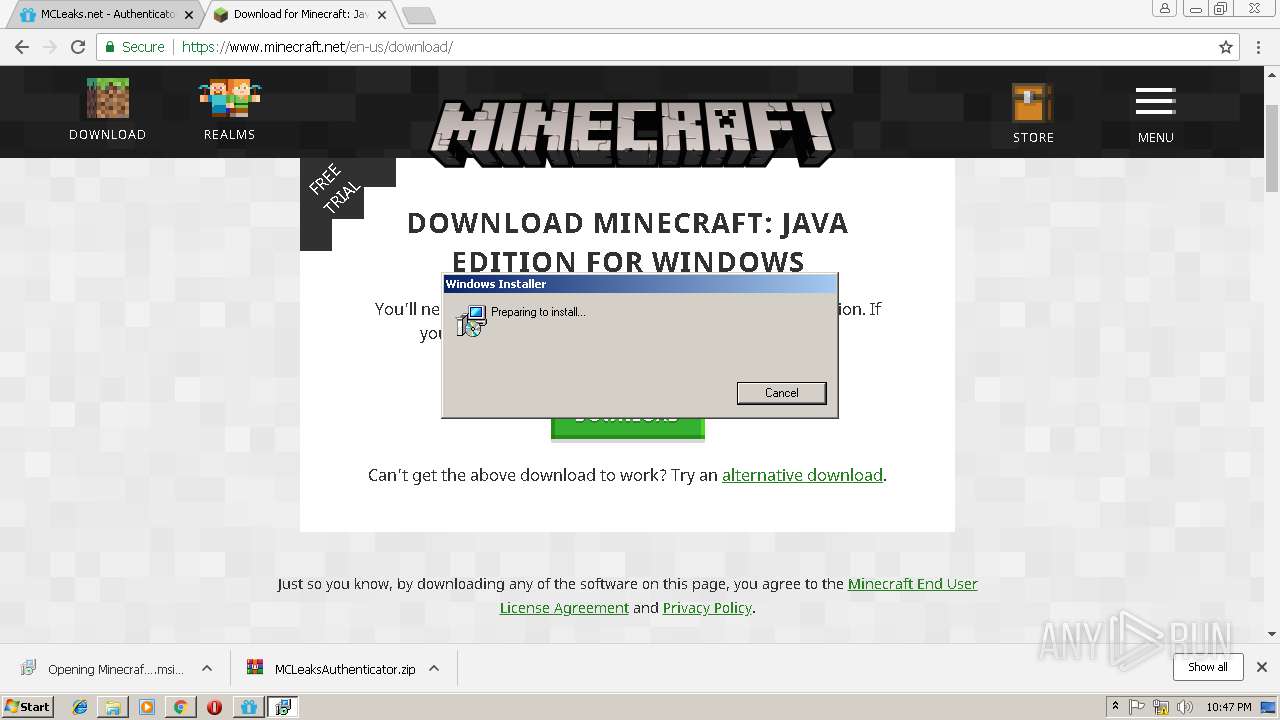
Executable content was dropped or overwritten
- msiexec.exe (PID: 2160)
- WinRAR.exe (PID: 2688)
- chrome.exe (PID: 3424)
- msiexec.exe (PID: 3368)
- MinecraftLauncher.exe (PID: 2260)
Adds / modifies Windows certificates
- MCLeaksAuthenticator.exe (PID: 2660)
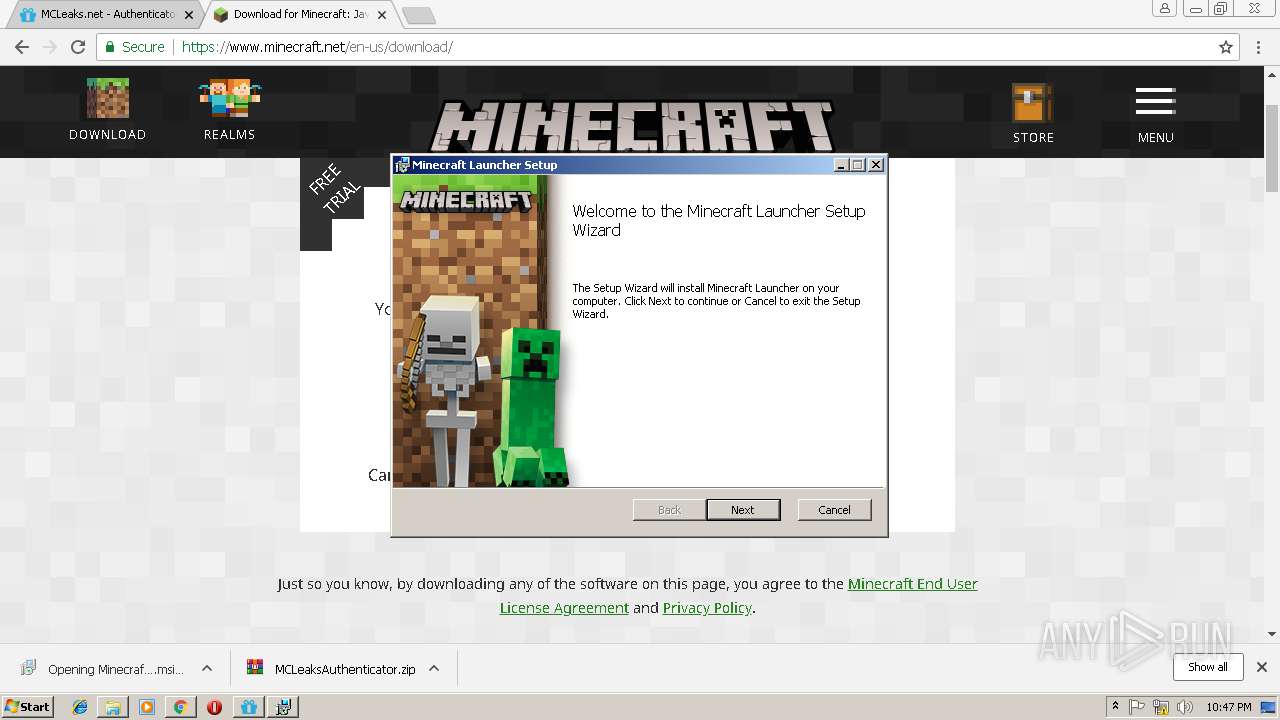
Starts Microsoft Installer
- chrome.exe (PID: 3424)
Creates files in the user directory
- MinecraftLauncher.exe (PID: 2260)
Application launched itself
- MinecraftLauncher.exe (PID: 2260)
Starts CMD.EXE for commands execution
- MCLeaksAuthenticator.exe (PID: 3020)
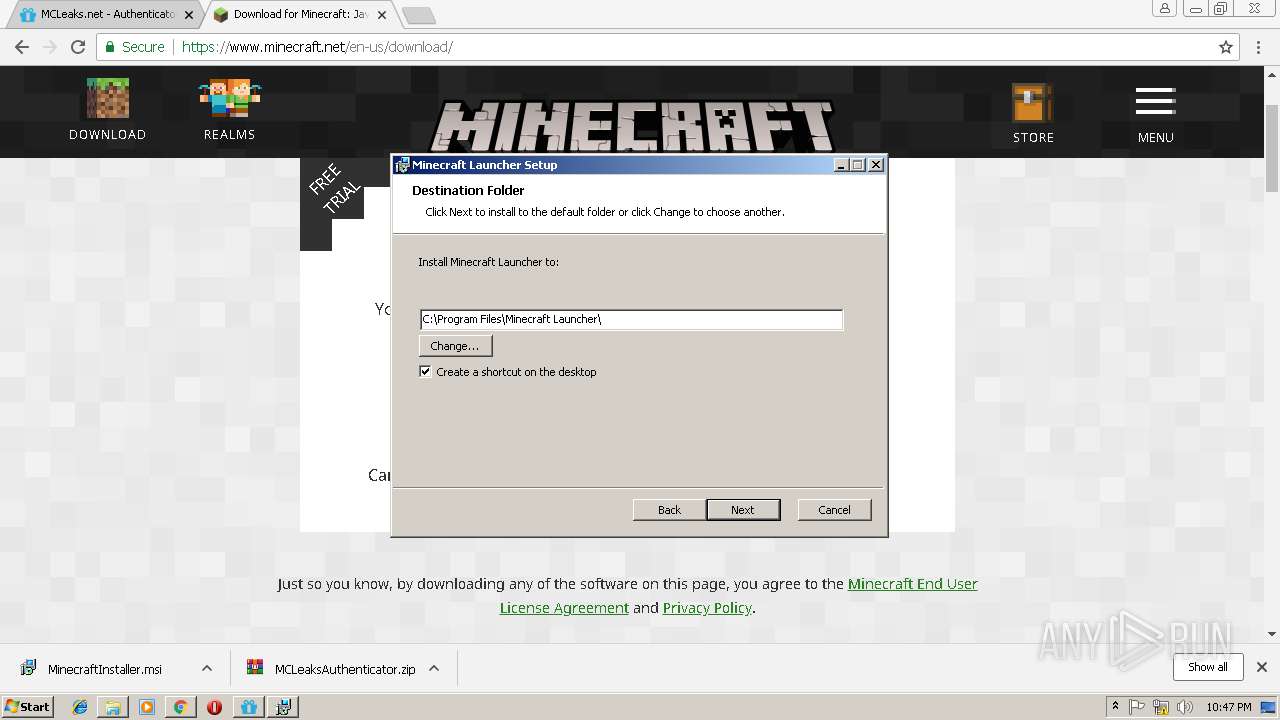
Creates files in the program directory
- MinecraftLauncher.exe (PID: 2260)
INFO
Application launched itself
- chrome.exe (PID: 3424)
- msiexec.exe (PID: 3368)
Reads Internet Cache Settings
- chrome.exe (PID: 3424)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3424)
- MinecraftLauncher.exe (PID: 2260)
Creates files in the program directory
- msiexec.exe (PID: 3368)
Creates a software uninstall entry
- msiexec.exe (PID: 3368)
Reads settings of System Certificates
- chrome.exe (PID: 3424)
- MCLeaksAuthenticator.exe (PID: 3020)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3556)
- MsiExec.exe (PID: 672)
- MsiExec.exe (PID: 1240)
Searches for installed software
- msiexec.exe (PID: 3368)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3152)
Changes settings of System certificates
- DrvInst.exe (PID: 2468)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
32
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
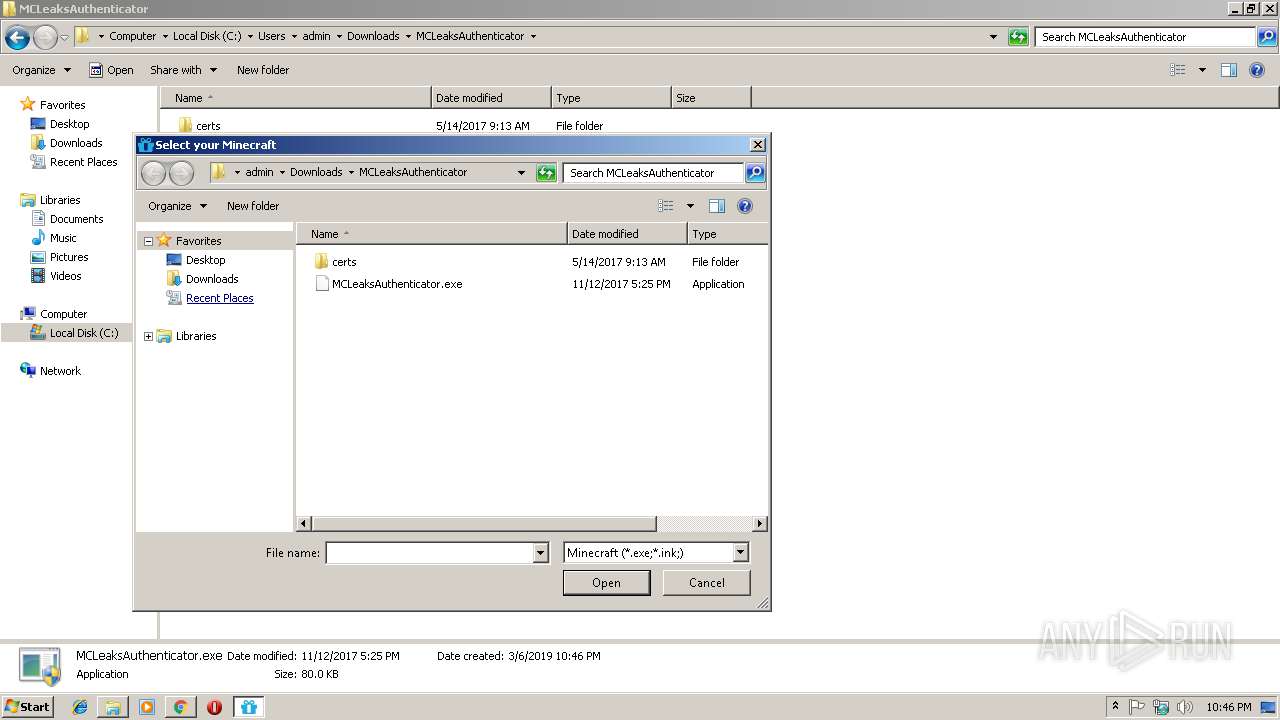
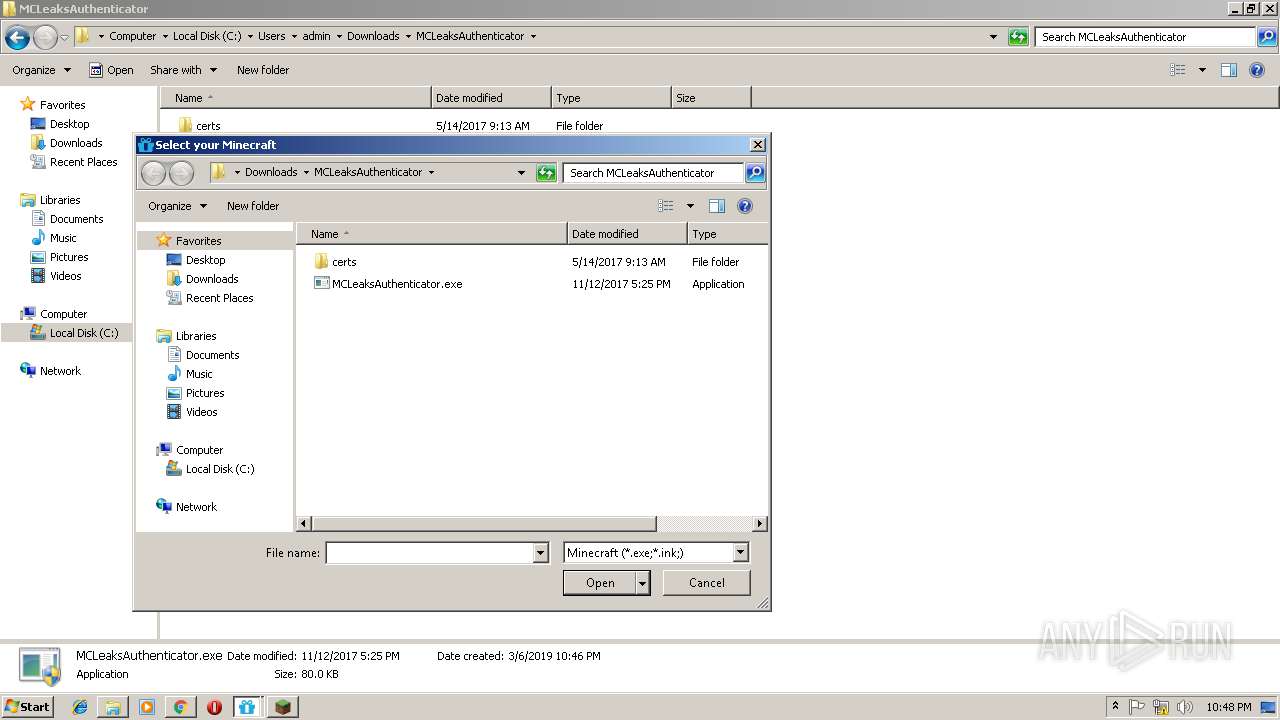
| 184 | "C:\Windows\System32\cmd.exe" /C ""C:\Program Files\Minecraft Launcher\runtime\jre-x86\bin\bin\keytool.exe" -storepass "changeit" -noprompt -import -alias authserver.mojang.com.cert -file "C:\Users\admin\Downloads\MCLeaksAuthenticator\certs\mcleaks.authserver.mojang.com.cert" -keystore "C:\Program Files\Minecraft Launcher\runtime\jre-x86\bin\lib\security\cacerts"" | C:\Windows\System32\cmd.exe | — | MCLeaksAuthenticator.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 672 | C:\Windows\system32\MsiExec.exe -Embedding D97581F64289760327A5816E2A2931CD | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | C:\Windows\system32\MsiExec.exe -Embedding B6DFF4AA961CE1D02EA0E9CFA1535F59 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CFF2B3238AFD0EF2FF99EE6BE556E59F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CFF2B3238AFD0EF2FF99EE6BE556E59F --renderer-client-id=14 --mojo-platform-channel-handle=5036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6feb00b0,0x6feb00c0,0x6feb00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
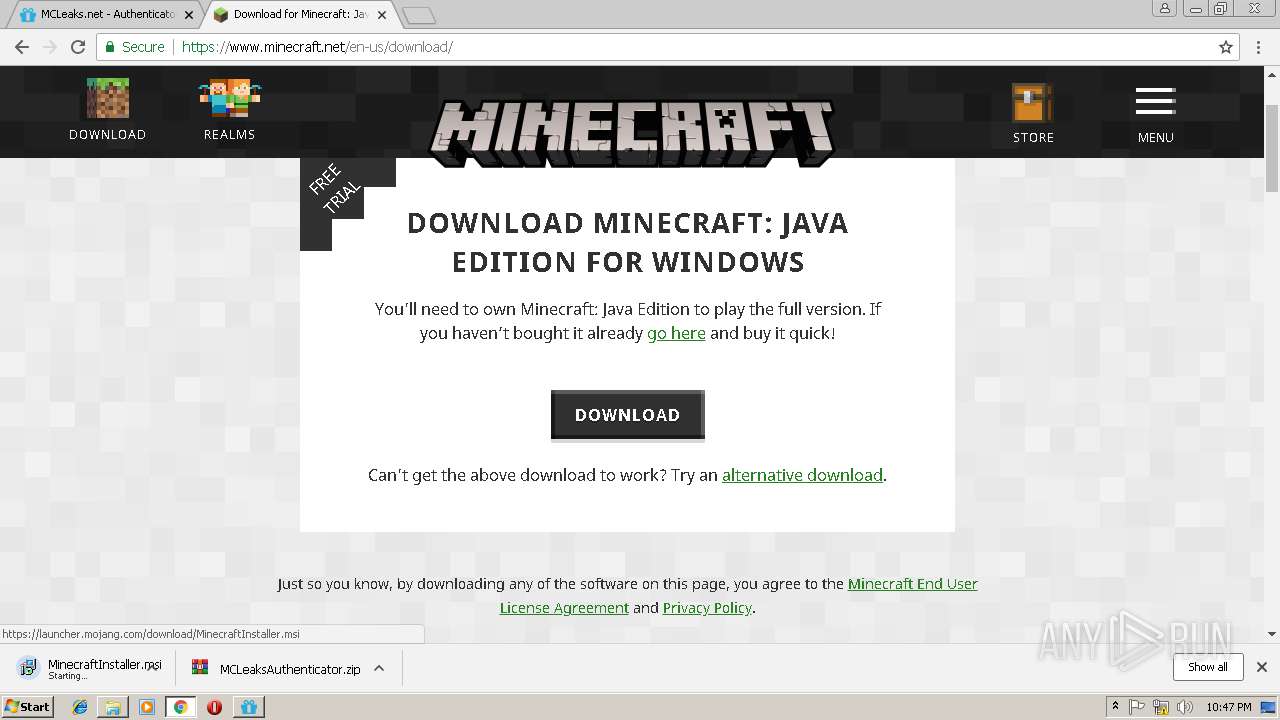
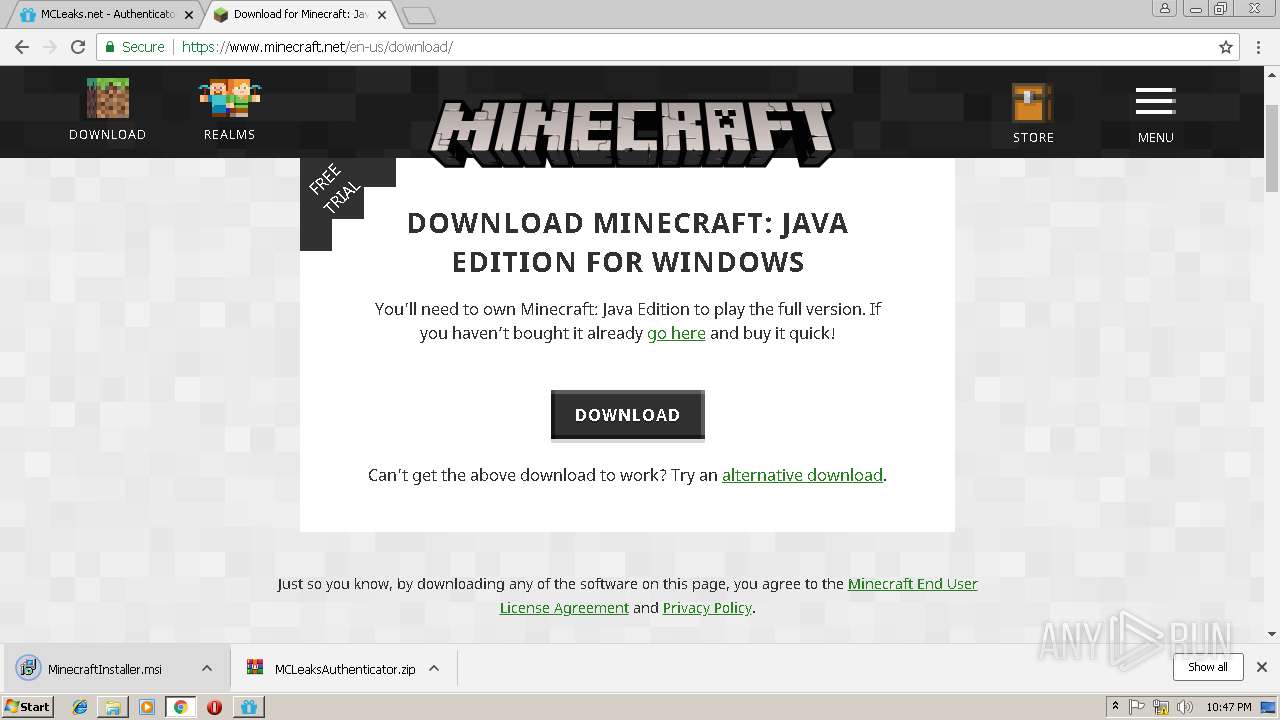
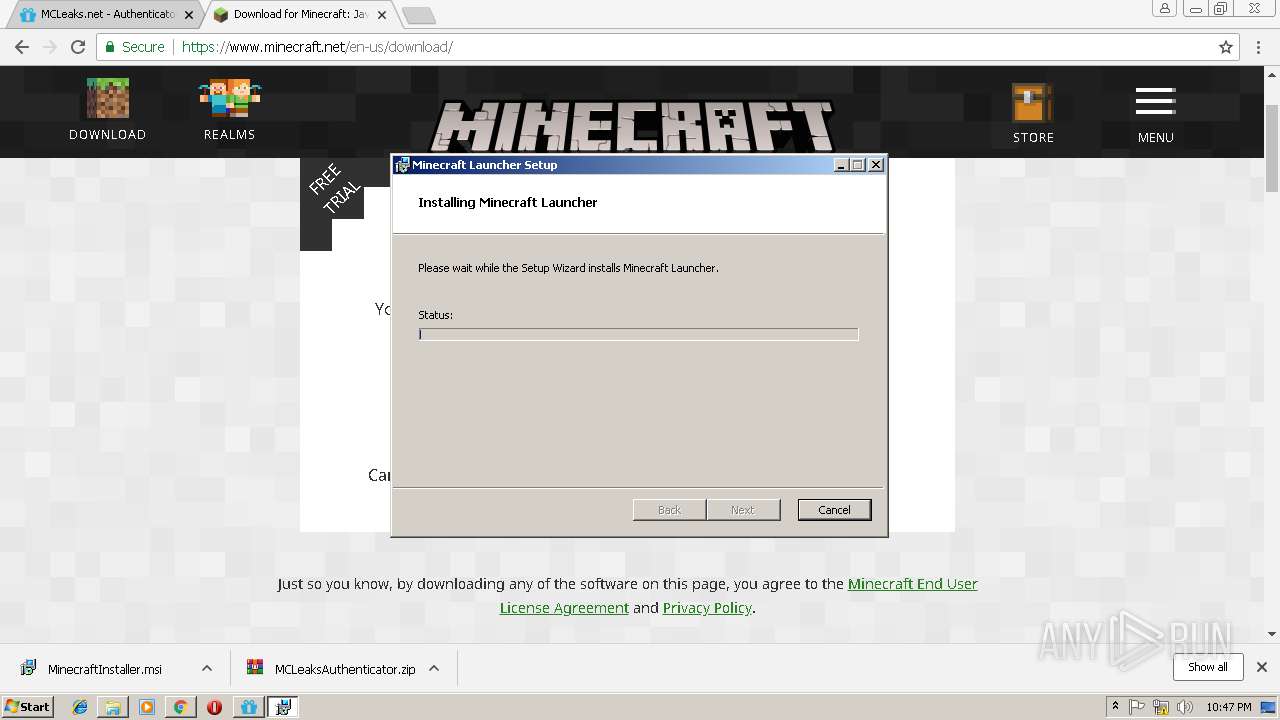
| 2160 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\MinecraftInstaller.msi" | C:\Windows\System32\msiexec.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe" | C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe | MsiExec.exe | ||||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft launcher Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=1DF6CE24415C0D47DBDC682FF8E09CC1 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2468 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005C0" "000005BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,6042726318627865543,4325218840144401037,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E913C10888078AAEBF82013F2495F5E2 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E913C10888078AAEBF82013F2495F5E2 --renderer-client-id=9 --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 609
Read events
2 816
Write events
770
Delete events
23
Modification events
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3424-13196385974795625 |
Value: 259 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3424-13196385974795625 |
Value: 259 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
247
Suspicious files
492
Text files
337
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dcfd86b2-7e45-4f66-a515-ff00ad73e7e1.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f6f779cf-0ef4-4c61-9208-48f9543cb626.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1ae475.TMP | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF1ae475.TMP | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
105
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | chrome.exe | GET | 200 | 92.122.213.217:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
3424 | chrome.exe | GET | 200 | 92.122.213.217:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
3424 | chrome.exe | GET | 200 | 52.85.188.32:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3424 | chrome.exe | GET | 200 | 52.85.188.75:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3424 | chrome.exe | 104.28.10.138:443 | mcleaks.net | Cloudflare Inc | US | shared |
3424 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3424 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
3424 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3424 | chrome.exe | 104.19.198.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
3424 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3424 | chrome.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
3424 | chrome.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3424 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3424 | chrome.exe | 172.217.18.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mcleaks.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
code.jquery.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MinecraftLauncher.exe | [0306/224908:INFO:LauncherAppBrowser.cpp(73)] Work dir is C:\Users\admin\AppData\Roaming\.minecraft
|
MinecraftLauncher.exe | [0306/224908:INFO:ClientHandler.cpp(280)] Creating launcher window.
|
MinecraftLauncher.exe | [0306/224909:INFO:LauncherAppRenderer.cpp(115)] Javascript bridge extended.
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Preferences / startup: Read preferences
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Preferences: Wrote preferences
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] System language is en-us
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Loading fallback language en-us...
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Will not load en-us as a main language...
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Preferences: Wrote preferences
|
MinecraftLauncher.exe | [0306/224909:INFO:ClientHandler.cpp(1049)] Configurations: Loading profiles
|