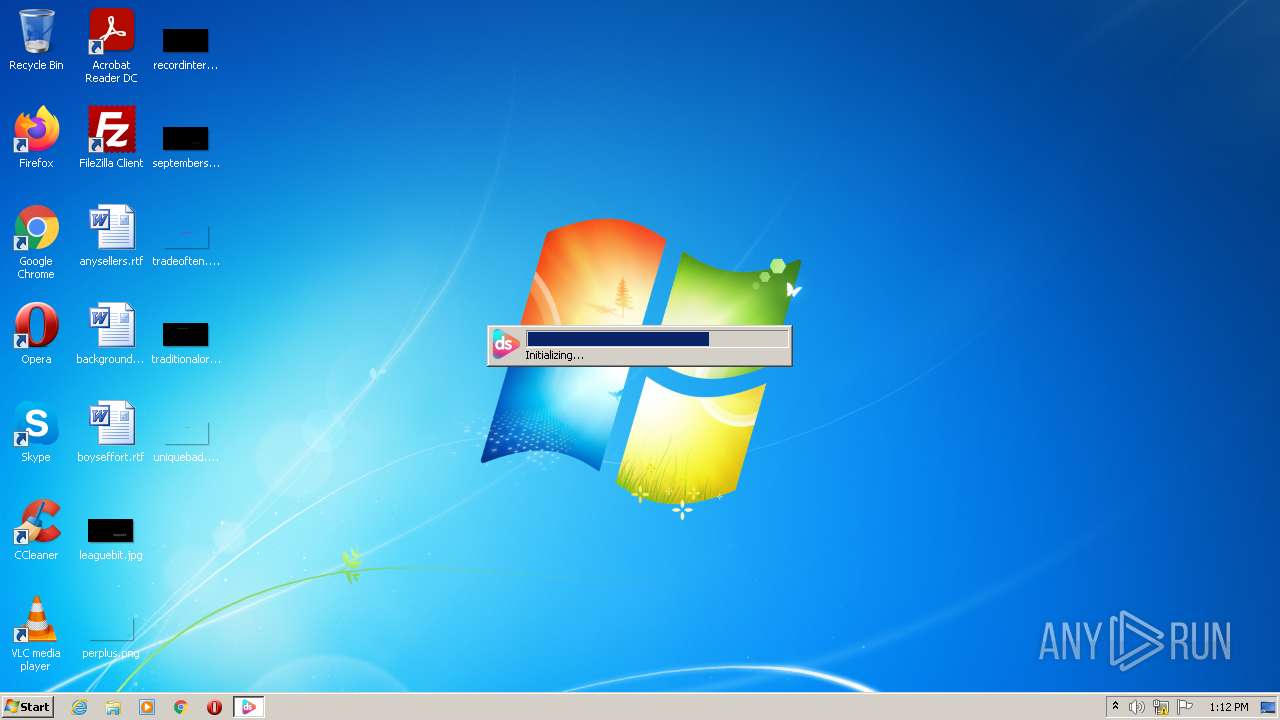
| File name: | Blood Trail[bGIlYJ5rE].exe |
| Full analysis: | https://app.any.run/tasks/aede50c7-8a61-4e95-bd77-58f9fce368b7 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 12:12:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, Nullsoft Installer self-extracting archive |
| MD5: | 887996967CFAAE5C1509CBB48203455D |
| SHA1: | E50547E37DEDC0ADFEDDD193E9C78EF70A79F71A |
| SHA256: | E6A07B661A3180A089126D7357A4AE1DED3FF26E04002C8FE7AD7157E2FB77DD |
| SSDEEP: | 3072:ePLwgcuSh/PdDEbKOJwanLEw3rgL4zgSNkW54aDF:ePNohdmKOLnAwEL4Z3DF |
MALICIOUS
Drops executable file immediately after starts
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Loads dropped or rewritten executable
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
SUSPICIOUS
Reads the computer name
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Checks supported languages
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Executable content was dropped or overwritten
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Drops a file with a compile date too recent
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
INFO
Checks Windows Trust Settings
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Reads settings of System Certificates
- Blood Trail[bGIlYJ5rE].exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| ProductVersion: | 0.0.3.3 |
|---|---|
| ProductName: | Setup Downloader |
| LegalCopyright: | Copyright (C) 2022 DS Project |
| FileVersion: | 0.0.3.3 |
| FileDescription: | Setup Downloader |
| CompanyName: | DS Project |
| CharacterSet: | Unicode |
| LanguageCode: | Unknown (04B0) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 0.0.3.3 |
| FileVersionNumber: | 0.0.3.3 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | 6 |
| OSVersion: | 5.1 |
| EntryPoint: | 0x10a340 |
| UninitializedDataSize: | 1069056 |
| InitializedDataSize: | 122880 |
| CodeSize: | 20480 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:06:22 19:00:02+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jun-2022 17:00:02 |
| Detected languages: |
|
| CompanyName: | DS Project |
| FileDescription: | Setup Downloader |
| FileVersion: | 0.0.3.3 |
| LegalCopyright: | Copyright (C) 2022 DS Project |
| ProductName: | Setup Downloader |
| ProductVersion: | 0.0.3.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Jun-2022 17:00:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00105000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00106000 | 0x00005000 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.843 |
.rsrc | 0x0010B000 | 0x0001E000 | 0x0001DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.06202 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29431 | 1260 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.92982 | 18748 | UNKNOWN | English - United States | RT_ICON |
3 | 4.33435 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.49243 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.80295 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.10184 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 6.77191 | 184 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.79908 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 7.30318 | 316 | UNKNOWN | English - United States | RT_DIALOG |
105 | 7.02323 | 256 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3028 | "C:\Users\admin\AppData\Local\Temp\Blood Trail[bGIlYJ5rE].exe" | C:\Users\admin\AppData\Local\Temp\Blood Trail[bGIlYJ5rE].exe | Explorer.EXE | ||||||||||||
User: admin Company: DS Project Integrity Level: MEDIUM Description: Setup Downloader Exit code: 0 Version: 0.0.3.3 Modules
| |||||||||||||||
Total events
6 267
Read events
6 233
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3028) Blood Trail[bGIlYJ5rE].exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
2
Suspicious files
7
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\Local\Temp\nst9C29.tmp\System.dll | executable | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\Local\Temp\CabF602.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\Local\Temp\nst9C29.tmp\INetC.dll | executable | |
MD5:3BCB32A09D868557568F3E3F2148D371 | SHA256:DAB0CB7767E3B764E1E2A67FD19B57F3C8C79C91F9C0C0B4AF6853E297D41E5E | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:EC8FF3B1DED0246437B1472C69DD1811 | SHA256:E634C2D1ED20E0638C95597ADF4C9D392EBAB932D3353F18AF1E4421F4BB9CAB | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\Local\Temp\TarF603.tmp | cat | |
MD5:— | SHA256:— | |||
| 3028 | Blood Trail[bGIlYJ5rE].exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | Blood Trail[bGIlYJ5rE].exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2d6a0d36f7a146c7 | US | compressed | 60.0 Kb | whitelisted |
3028 | Blood Trail[bGIlYJ5rE].exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?986f66c3135c6af7 | US | compressed | 4.70 Kb | whitelisted |
3028 | Blood Trail[bGIlYJ5rE].exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | Blood Trail[bGIlYJ5rE].exe | 5.135.110.103:443 | dl7.dstudio.app | OVH SAS | FR | unknown |
3028 | Blood Trail[bGIlYJ5rE].exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
3028 | Blood Trail[bGIlYJ5rE].exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl7.dstudio.app |
| unknown |
dns.msftncsi.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |