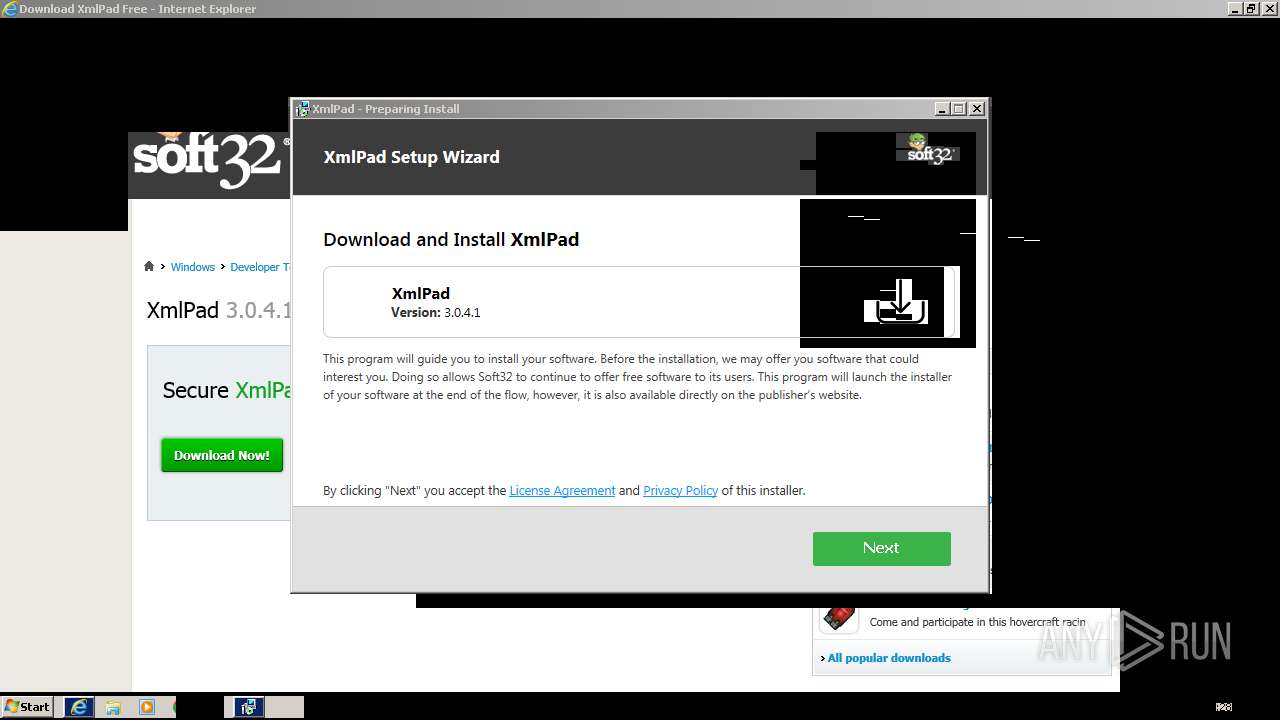
| URL: | https://xmlpad.soft32.com/free-download/?nc |
| Full analysis: | https://app.any.run/tasks/e479e35f-bcd9-4c26-996e-a149ea5ede13 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2023, 15:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FFBACCC66DF20B47AD6952A0B93D326B |
| SHA1: | 646A274EF9A38F0285E200E7679030316D9C4963 |
| SHA256: | E693F22AECA431CB270FFB6B9CA61694DCB06716ECB275FB038D3F18365885D0 |
| SSDEEP: | 3:N8kJfYu3DQRmayn:2kT0byn |
MALICIOUS
Drops the executable file immediately after the start
- XmlPad_3.0.4.1.exe (PID: 2468)
Actions looks like stealing of personal data
- XmlPad_3.0.4.1.exe (PID: 2468)
SUSPICIOUS
The process drops C-runtime libraries
- XmlPad_3.0.4.1.exe (PID: 2468)
Process drops legitimate windows executable
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads the Internet Settings
- XmlPad_3.0.4.1.exe (PID: 2468)
The process creates files with name similar to system file names
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads the Windows owner or organization settings
- XmlPad_3.0.4.1.exe (PID: 2468)
Checks Windows Trust Settings
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads security settings of Internet Explorer
- XmlPad_3.0.4.1.exe (PID: 2468)
Searches for installed software
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads settings of System Certificates
- XmlPad_3.0.4.1.exe (PID: 2468)
Adds/modifies Windows certificates
- XmlPad_3.0.4.1.exe (PID: 2468)
INFO
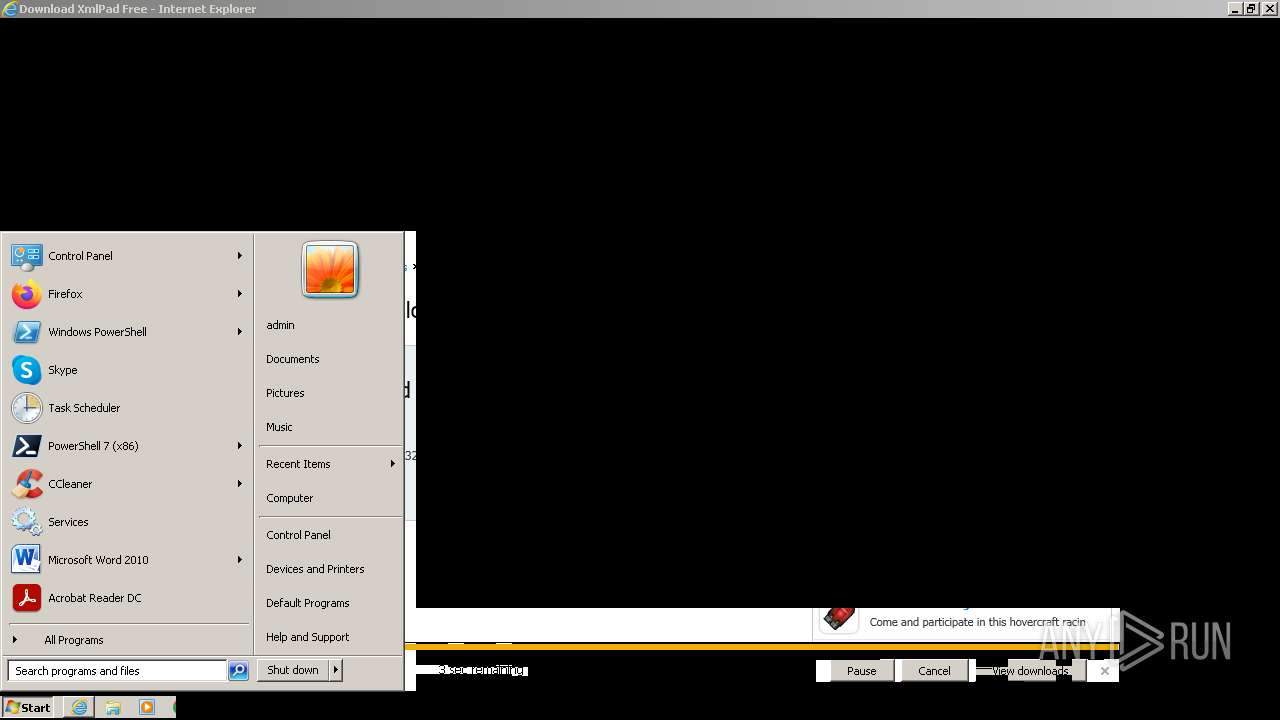
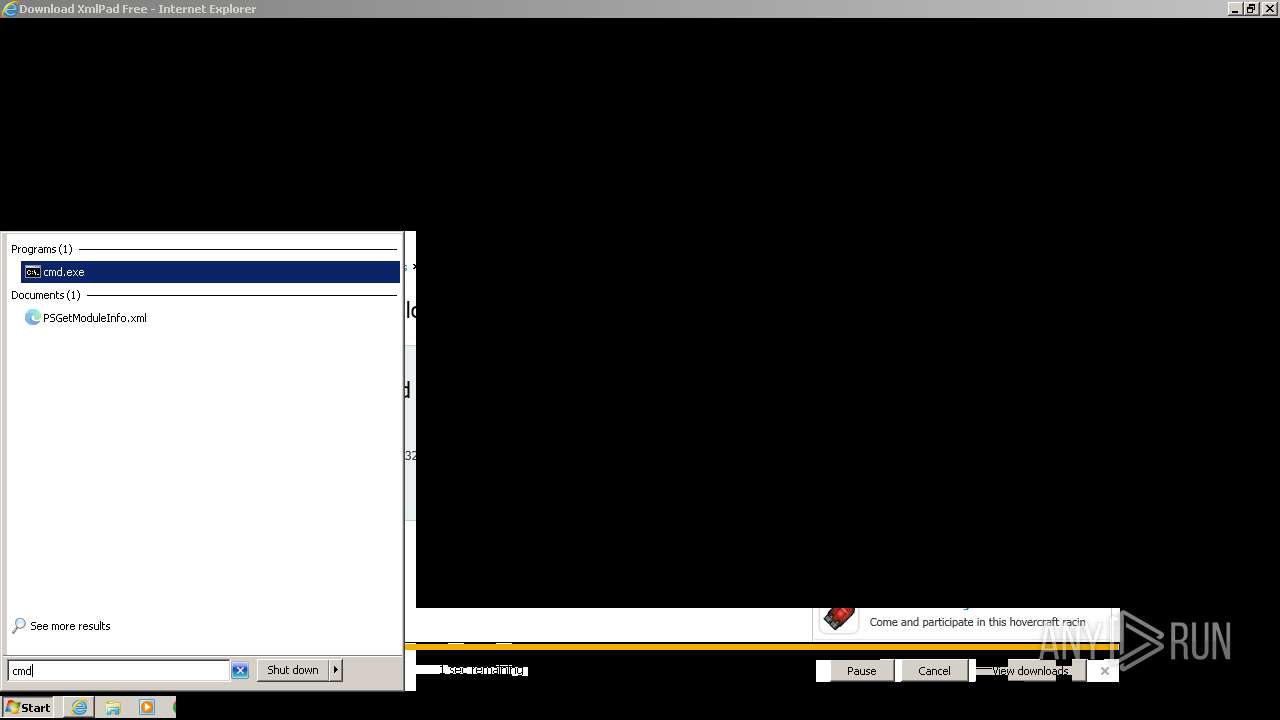
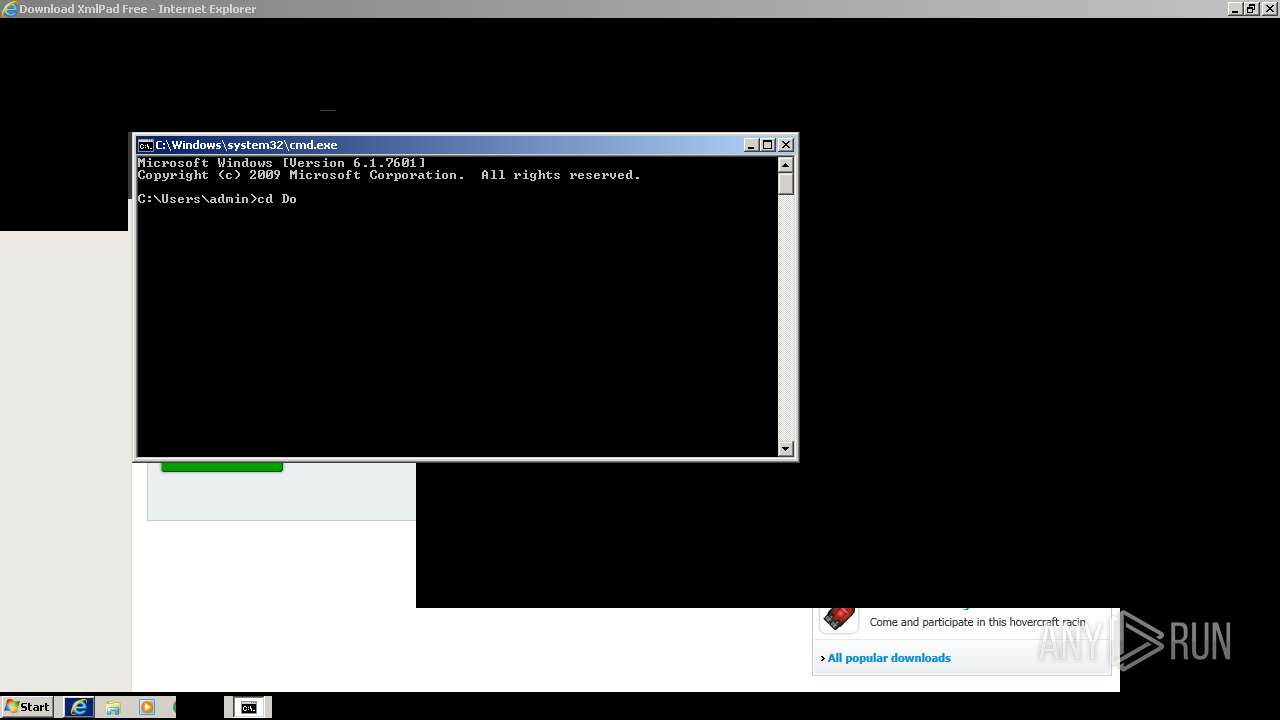
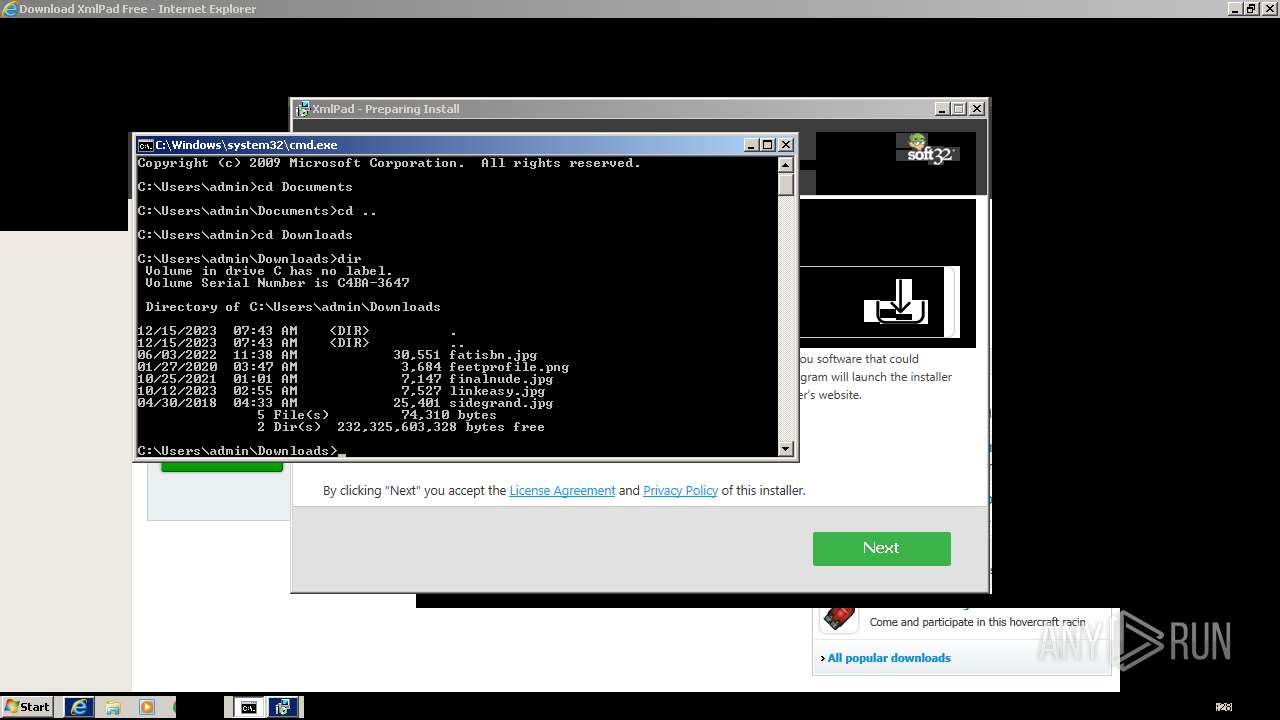
Manual execution by a user
- cmd.exe (PID: 188)
Application launched itself
- iexplore.exe (PID: 1776)
Checks supported languages
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads the computer name
- XmlPad_3.0.4.1.exe (PID: 2468)
Drops the executable file immediately after the start
- iexplore.exe (PID: 1776)
- iexplore.exe (PID: 2072)
The process uses the downloaded file
- iexplore.exe (PID: 1776)
- XmlPad_3.0.4.1.exe (PID: 2468)
Create files in a temporary directory
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads the machine GUID from the registry
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads Environment values
- XmlPad_3.0.4.1.exe (PID: 2468)
Reads product name
- XmlPad_3.0.4.1.exe (PID: 2468)
Creates files or folders in the user directory
- XmlPad_3.0.4.1.exe (PID: 2468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://xmlpad.soft32.com/free-download/?nc" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1776 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2444 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\XmlPad_3.0.4.1.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\XmlPad_3.0.4.1.exe | — | iexplore.exe | |||||||||||
User: admin Company: Xmlpad Integrity Level: MEDIUM Description: Software Installation Exit code: 3221226540 Version: 1.1.2.6582 Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\XmlPad_3.0.4.1.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\XmlPad_3.0.4.1.exe | iexplore.exe | ||||||||||||
User: admin Company: Xmlpad Integrity Level: HIGH Description: Software Installation Exit code: 0 Version: 1.1.2.6582 Modules
| |||||||||||||||
Total events
27 018
Read events
26 848
Write events
166
Delete events
4
Modification events
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1776) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
22
Suspicious files
39
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:D887F877C13538C31B2B03132ECFCA8A | SHA256:F350E36A0257F04E5E02365BD8DD06F1248BF2730795A46D45CC21B72EEEA668 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:A4301BA5CCB778E2C9095CF54FECB680 | SHA256:F4B19544059F43CD1714C77FB0C5EC986B83C7A53D7B7883E53688CFB37AA61D | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:4FD169B9A298E92843810A5DD1BE21E6 | SHA256:BB34FD5CD6C671A835BE00E36F107B982FB9CA9C406633F20DAE9020BC820585 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:B878B42838DA107F8EA104B2E280E765 | SHA256:846EEAFD960DBF13512BCC152B8ABD97179037848B9F0DE4E473A0008E92815A | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:A038F683E6BC47701B47CFD1E04ED300 | SHA256:8B32FD57995D57CE2523D5EDAE0919004054ACA93378845ADE74430A50C0BACA | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:6C987AC175BAB65B628A1E05BFE27713 | SHA256:2AEB989C020DE705A33D1B5803E7D87AF8DBD8492F1EFA3BF6CC8CF9ACEF29DA | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_B5D3A17E5BEDD2EDA793611A0A74E1E8 | binary | |
MD5:1A58C9BAA199C4A119650D818BCDA2D3 | SHA256:D9FFFF006F17B67EEC9A0585F36115C2818905D2D09A4B253AB06AE70576C13B | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\styles[1].css | text | |
MD5:06F12C8544892C82993EEBF15F6E7BD0 | SHA256:BF72BB2923D01765BB227F203FE55A18394CDA7F2382E4D9BF588FD8095D4B3F | |||
| 2072 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\free-download[1].htm | html | |
MD5:A55F1087420DCE947A9E05F67AB735DF | SHA256:421C5F472BAEEBD96C71DB9C55D7BC00A82782EB7D5F94B57A74F7AF324EB585 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
78
DNS requests
41
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2072 | iexplore.exe | GET | 200 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f6bf34dbb61e71d7 | unknown | compressed | 4.66 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 184.24.77.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6243fee378382ed7 | unknown | compressed | 4.66 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 108.138.2.107:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.51 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 18.66.142.79:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.39 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2072 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
2072 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGupzMnM%2BqGaCjIQPyd58u0%3D | unknown | binary | 471 b | unknown |
2072 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCZXmpIP%2Bo%2BHhJmodADfw%2Fc | unknown | binary | 472 b | unknown |
2072 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGpYRvzN3kAuEMlMWsqSFLc%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2072 | iexplore.exe | 52.84.90.18:443 | xmlpad.soft32.com | AMAZON-02 | US | unknown |
2072 | iexplore.exe | 184.24.77.203:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2072 | iexplore.exe | 108.138.2.107:80 | o.ss2.us | AMAZON-02 | US | whitelisted |
2072 | iexplore.exe | 18.66.142.79:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | unknown |
2072 | iexplore.exe | 99.86.1.71:443 | d3gx3uz4yj2hnq.cloudfront.net | AMAZON-02 | US | unknown |
2072 | iexplore.exe | 13.32.23.205:443 | d3fnqfpn2r2a3x.cloudfront.net | AMAZON-02 | US | unknown |
2072 | iexplore.exe | 142.250.184.194:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xmlpad.soft32.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
d3gx3uz4yj2hnq.cloudfront.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
d3fnqfpn2r2a3x.cloudfront.net |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
js.centerbodyapps.com |
| whitelisted |
Threats
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
XmlPad_3.0.4.1.exe | Error: File not found - sciterwrapper:console.tis
|
XmlPad_3.0.4.1.exe | |
XmlPad_3.0.4.1.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|
XmlPad_3.0.4.1.exe | at sciter:init-script.tis
|
XmlPad_3.0.4.1.exe | |
XmlPad_3.0.4.1.exe | Error: File not found - sciterwrapper:console.tis
|
XmlPad_3.0.4.1.exe | at sciter:init-script.tis
|
XmlPad_3.0.4.1.exe | |
XmlPad_3.0.4.1.exe | |
XmlPad_3.0.4.1.exe | file:resources/tis/TranslateOfferTemplate.tis(82) : warning :'async' does not contain any 'await'
|