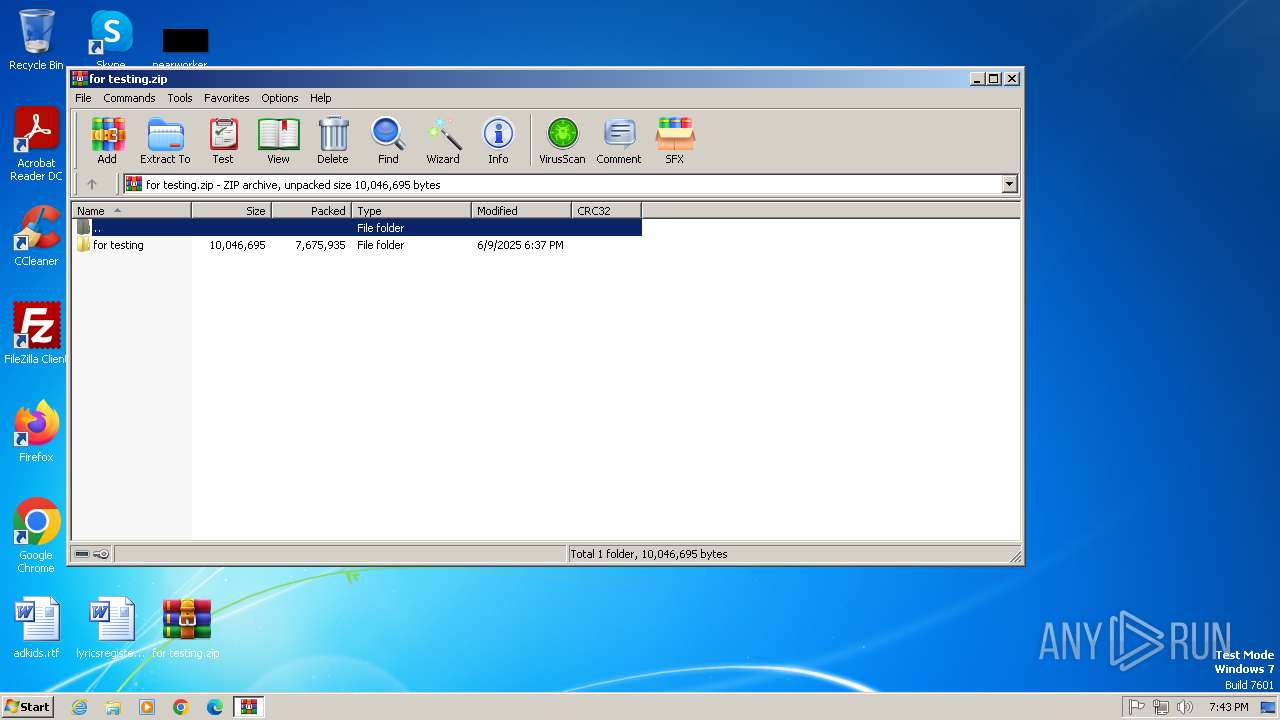
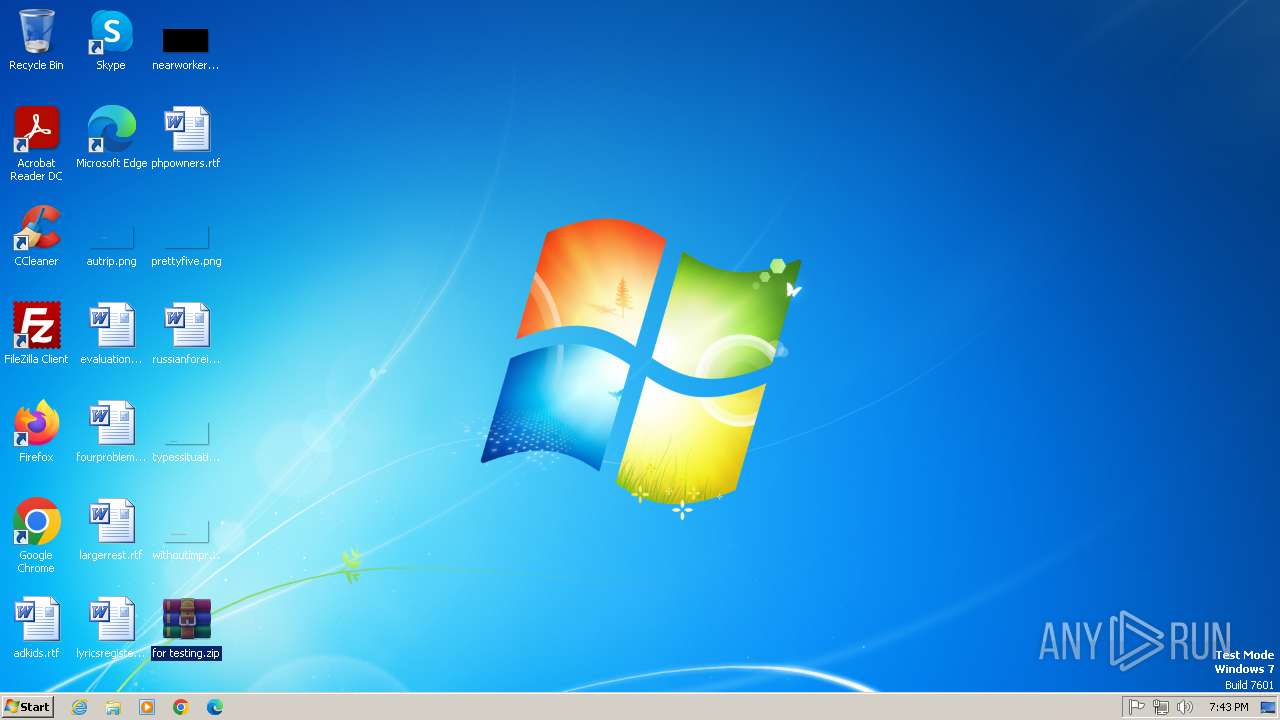
| File name: | for testing.zip |
| Full analysis: | https://app.any.run/tasks/dd340af4-c51f-4ed5-ab62-9d2aa2fc756c |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2025, 18:43:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 03F1AEB7D8CBA4C4BAE49B479F8D1198 |
| SHA1: | 545E6D039E049318A697ACC7B28765CEA526B95E |
| SHA256: | E67E0D5087D317DD85ED348912FC676C85B289E605BD5E101343D45D0ADAA224 |
| SSDEEP: | 98304:WZOQDQogM/xLURvNr5K9Tpy3gp/j0qAYuqTVrhjdDT0BbYdxk8DkebKyCGbpjnhf:qXl9+ucbRURx7V |
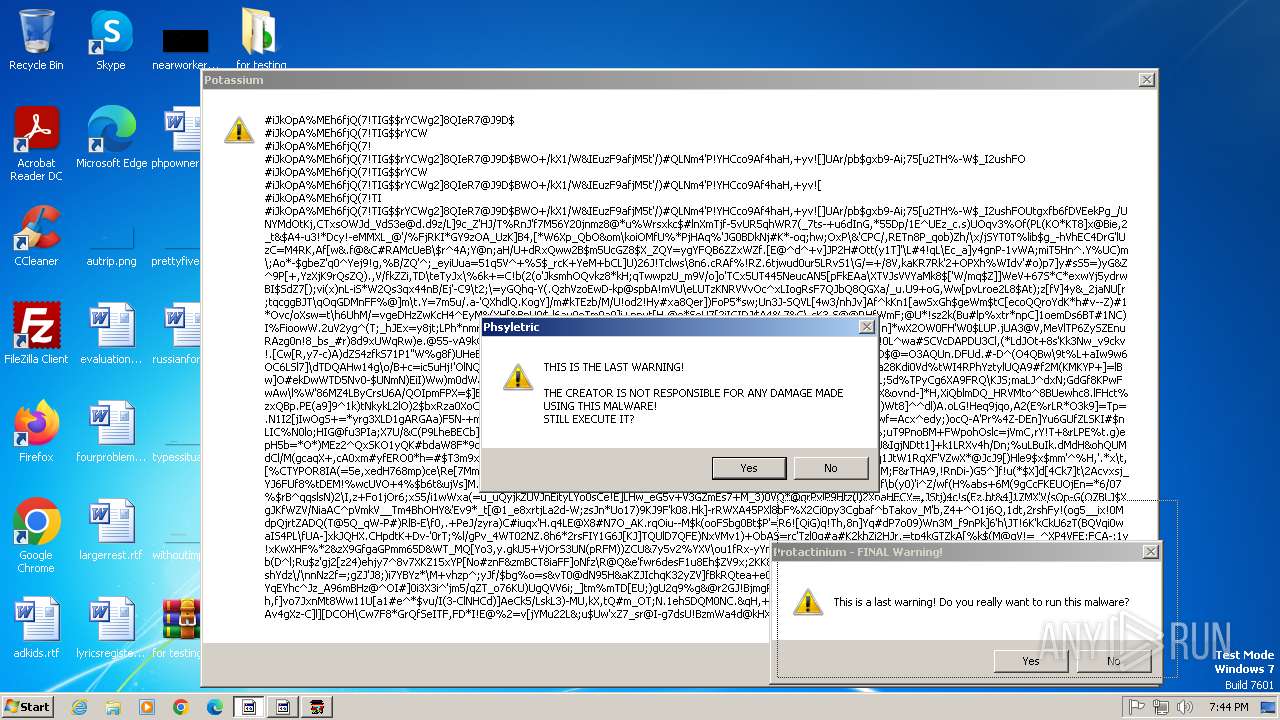
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2152)
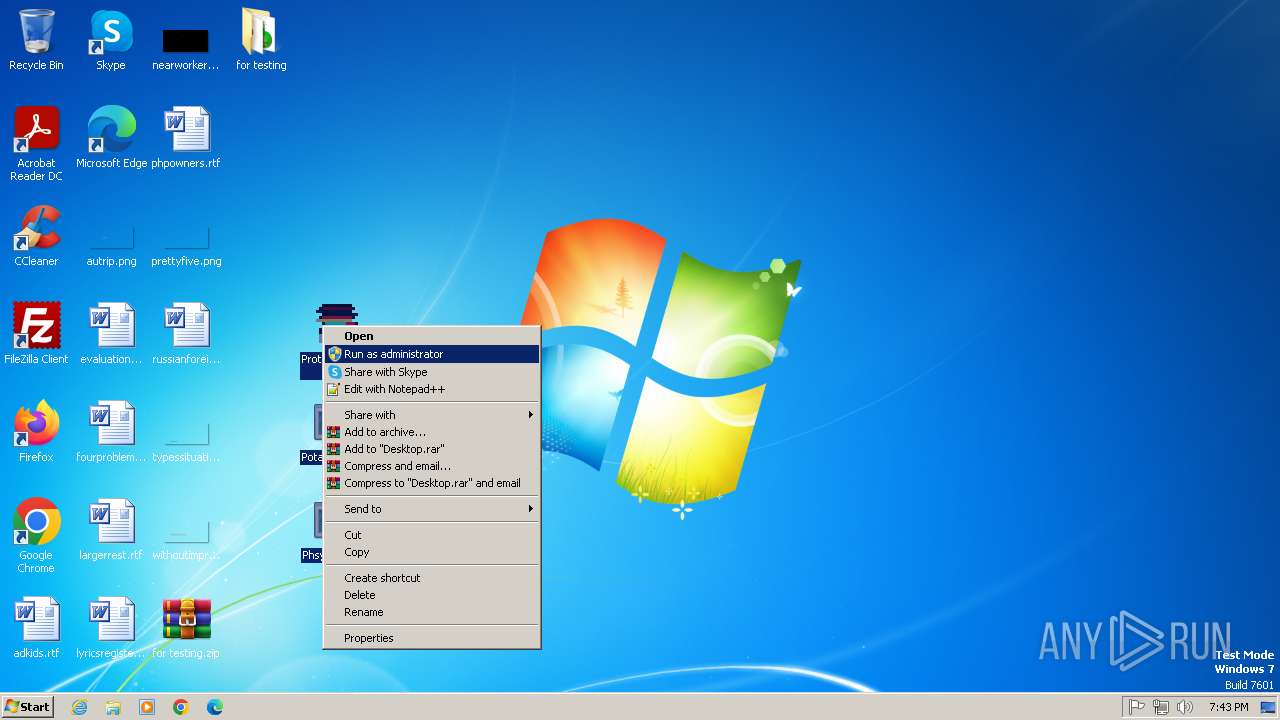
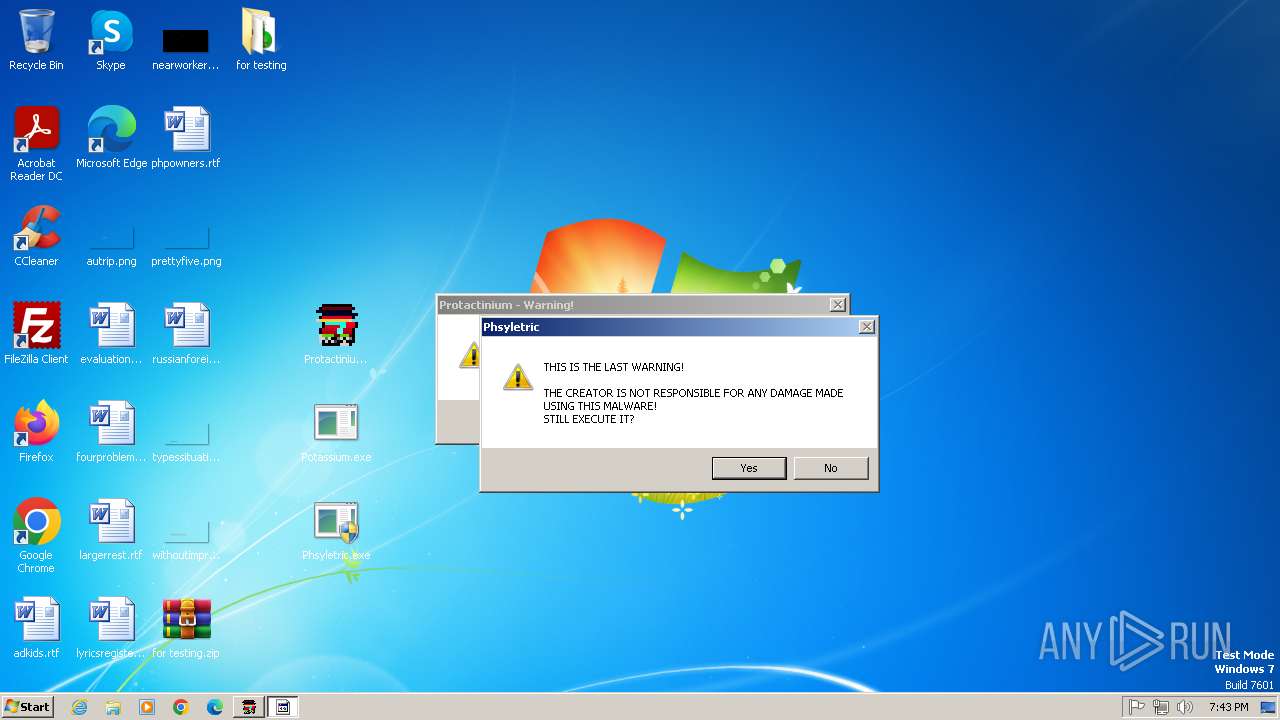
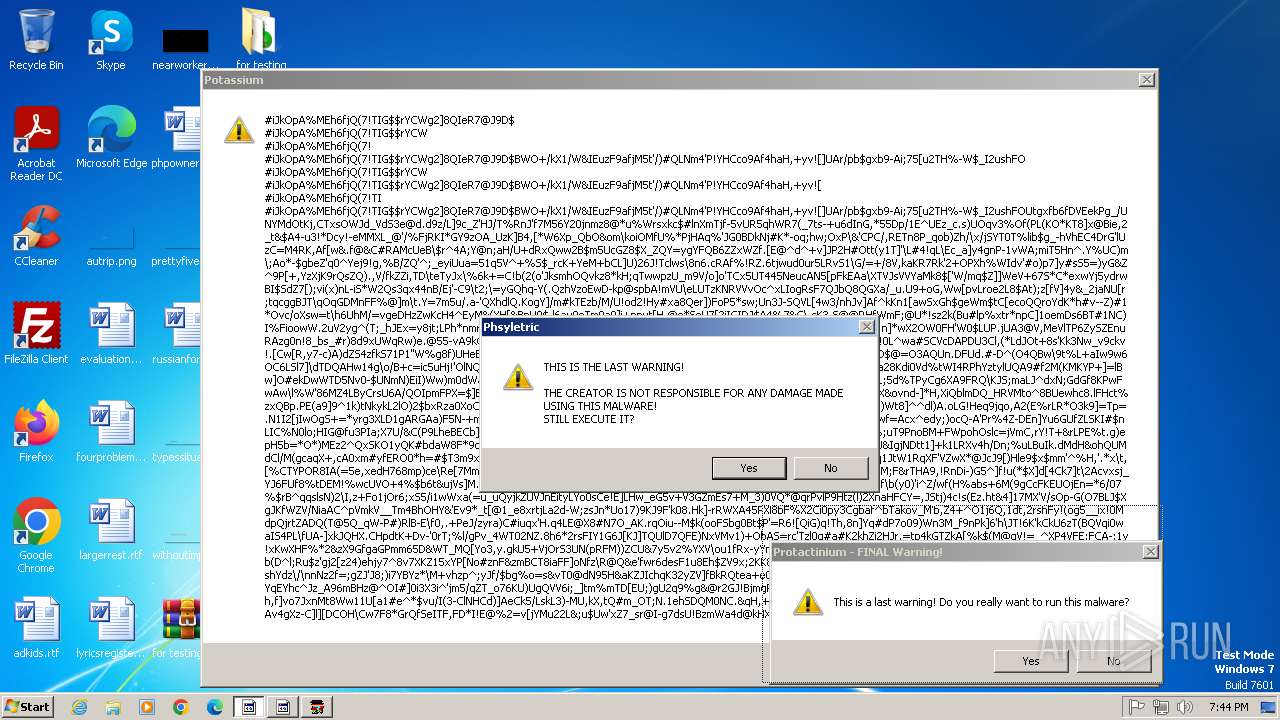
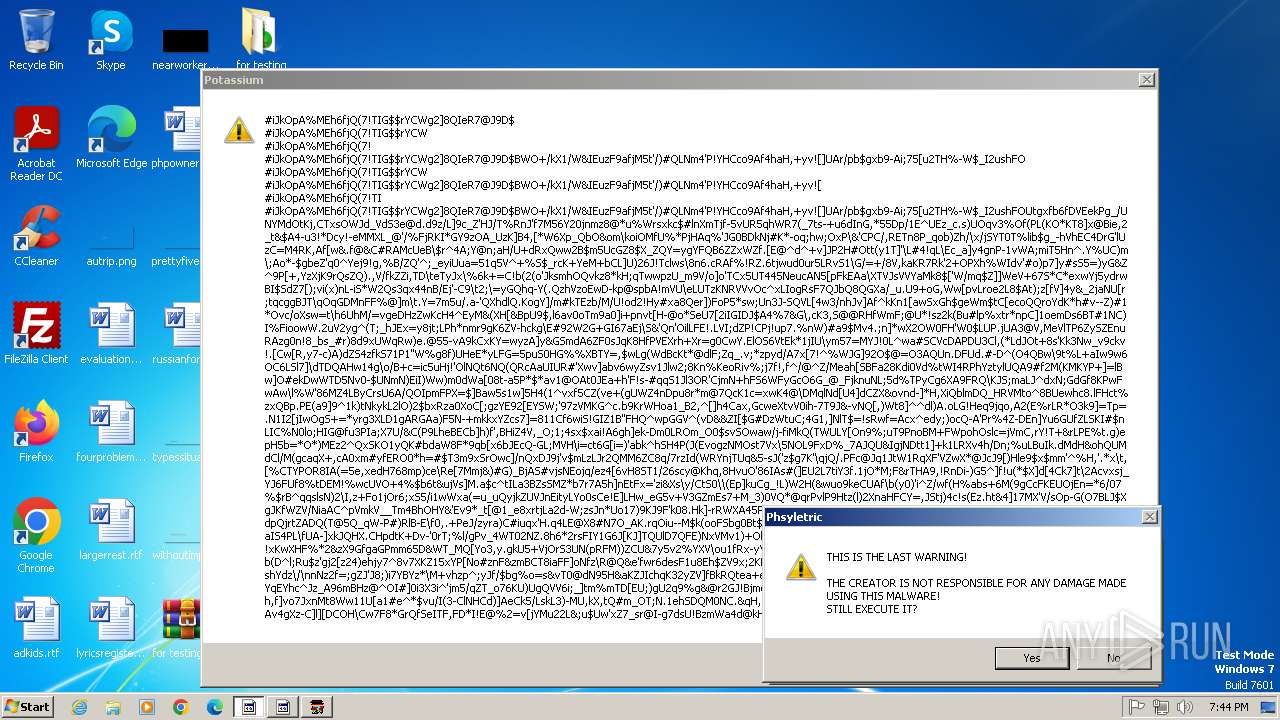
Disables task manager
- reg.exe (PID: 3224)
Disables command prompt
- reg.exe (PID: 3712)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1564)
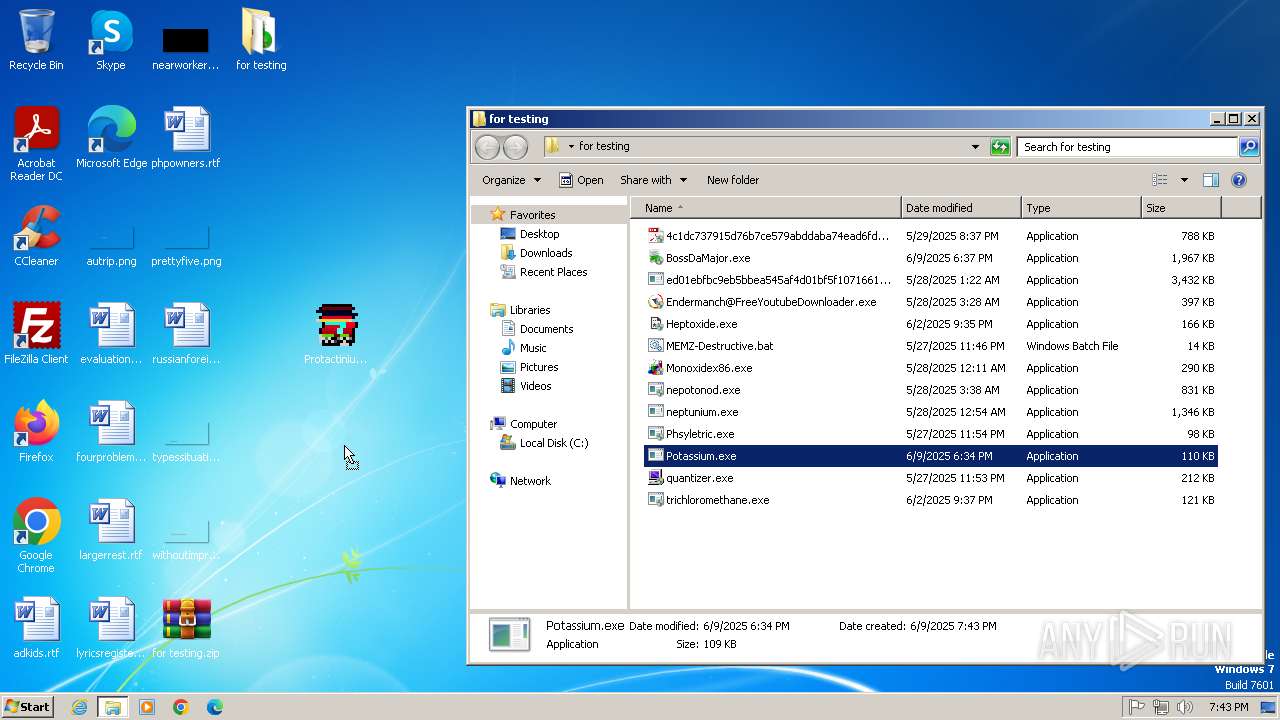
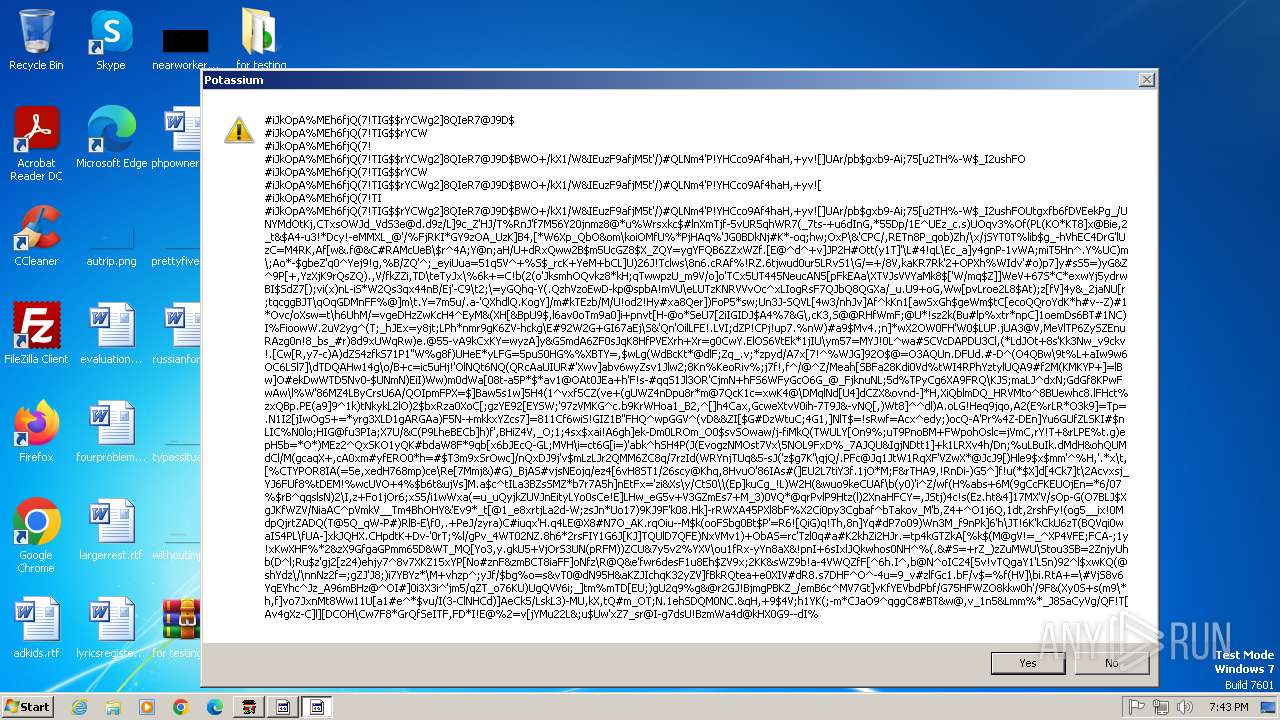
There is functionality for taking screenshot (YARA)
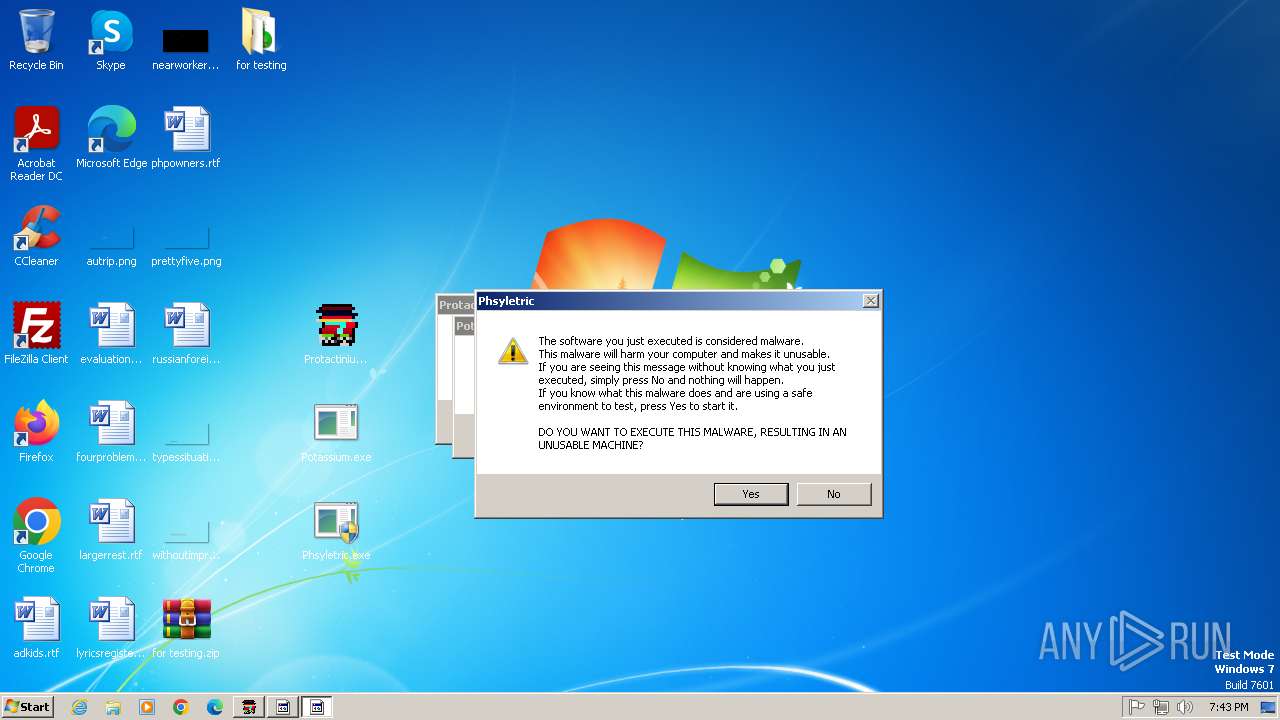
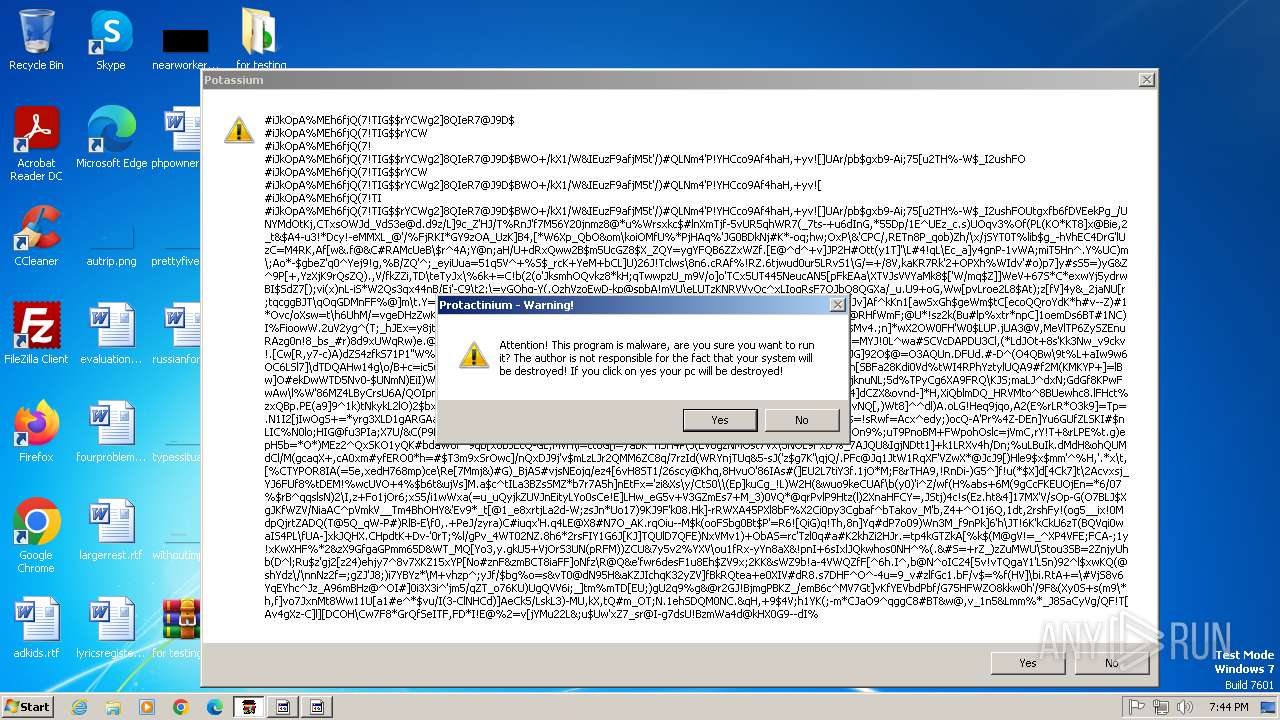
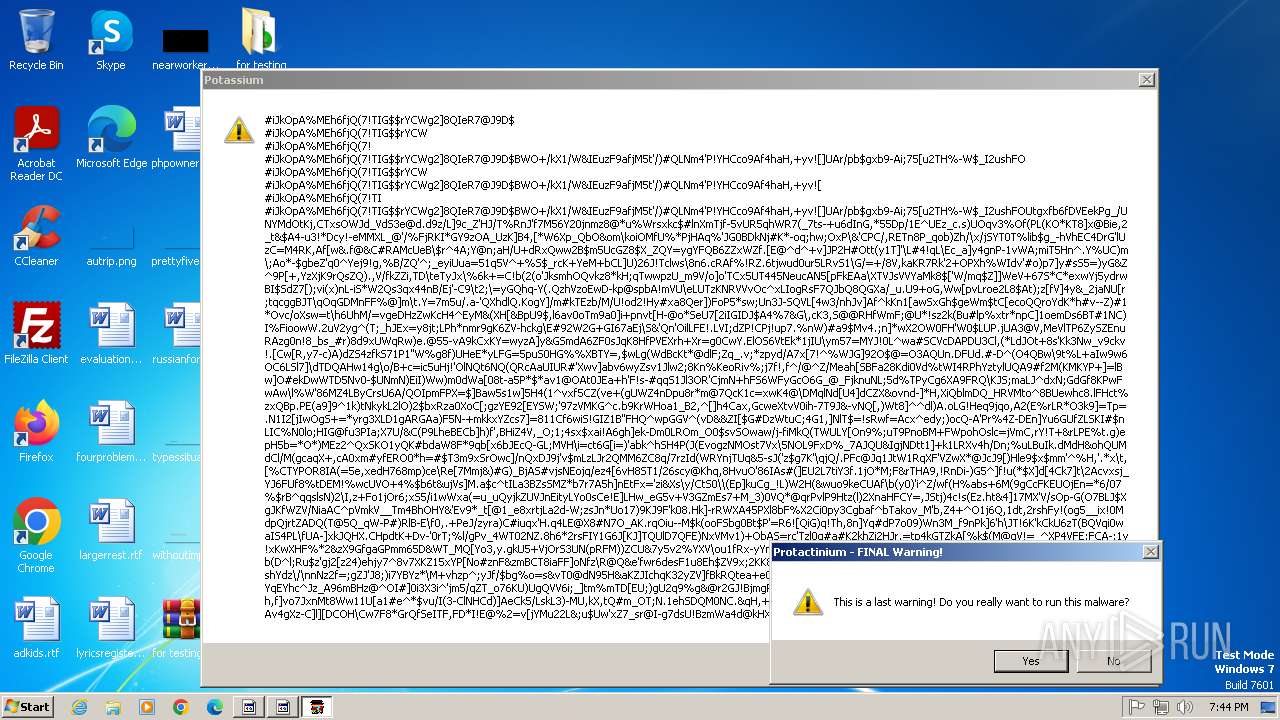
- Potassium.exe (PID: 3216)
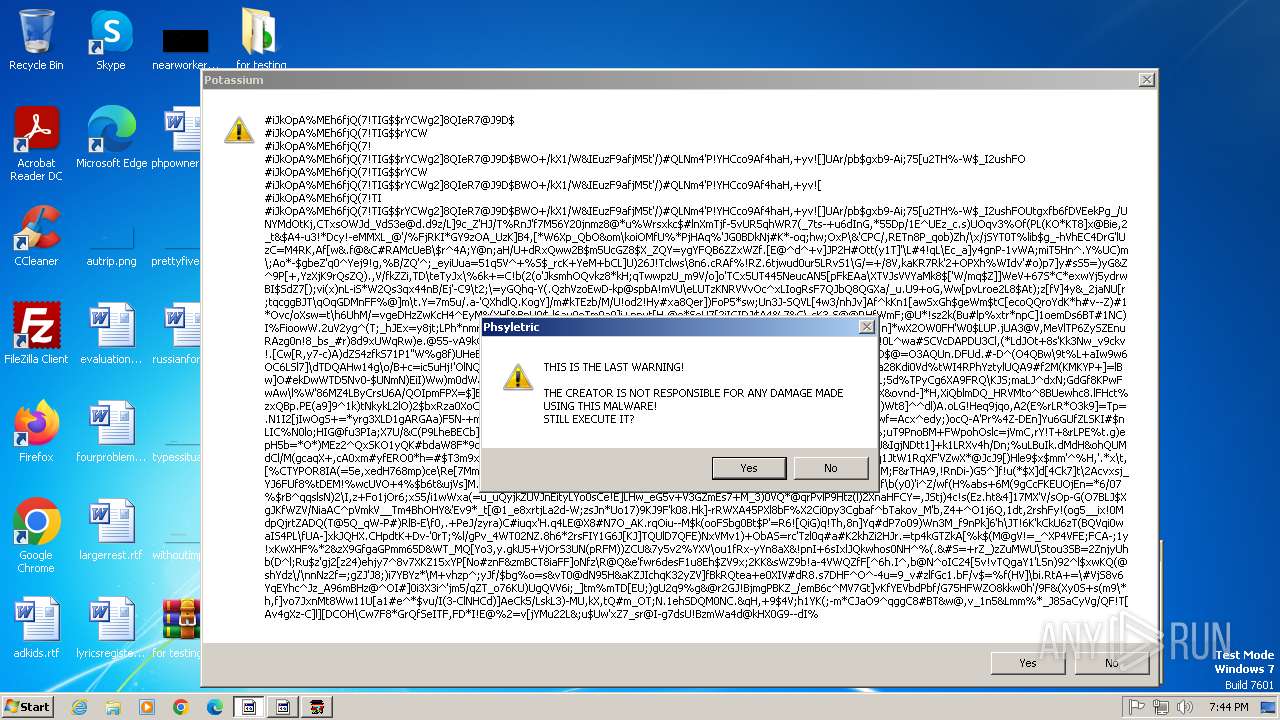
- Phsyletric.exe (PID: 1852)
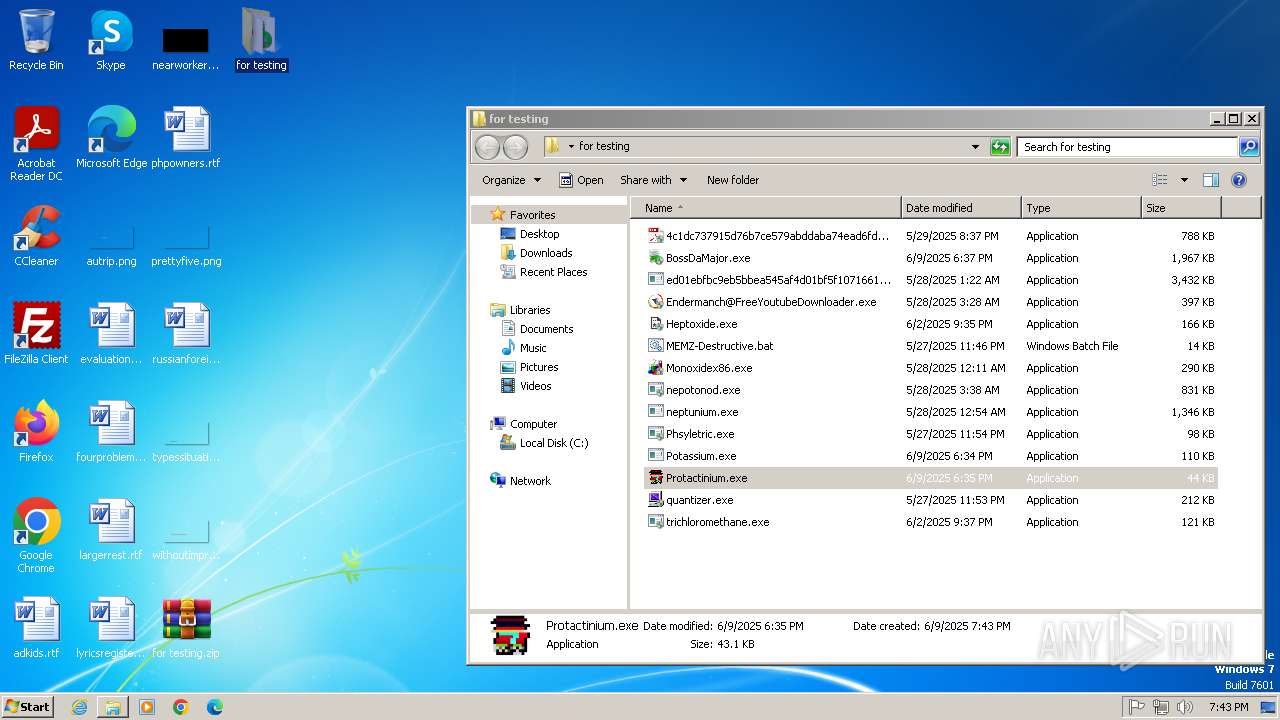
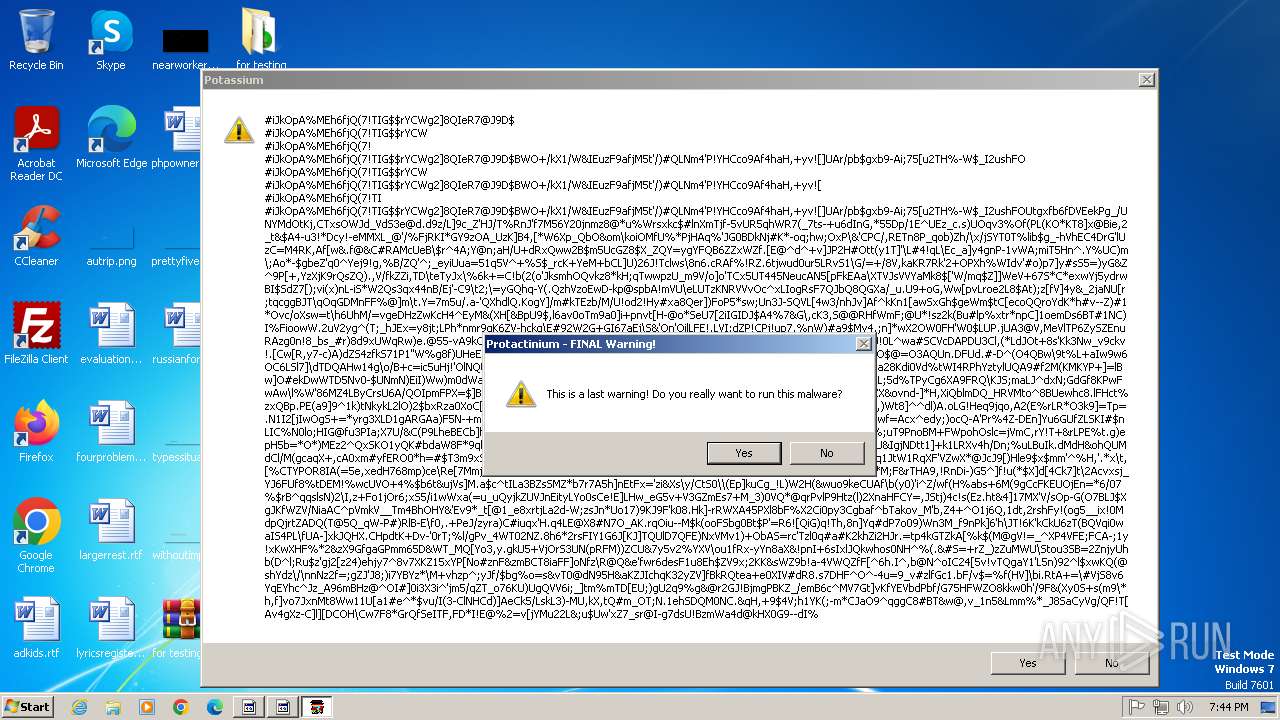
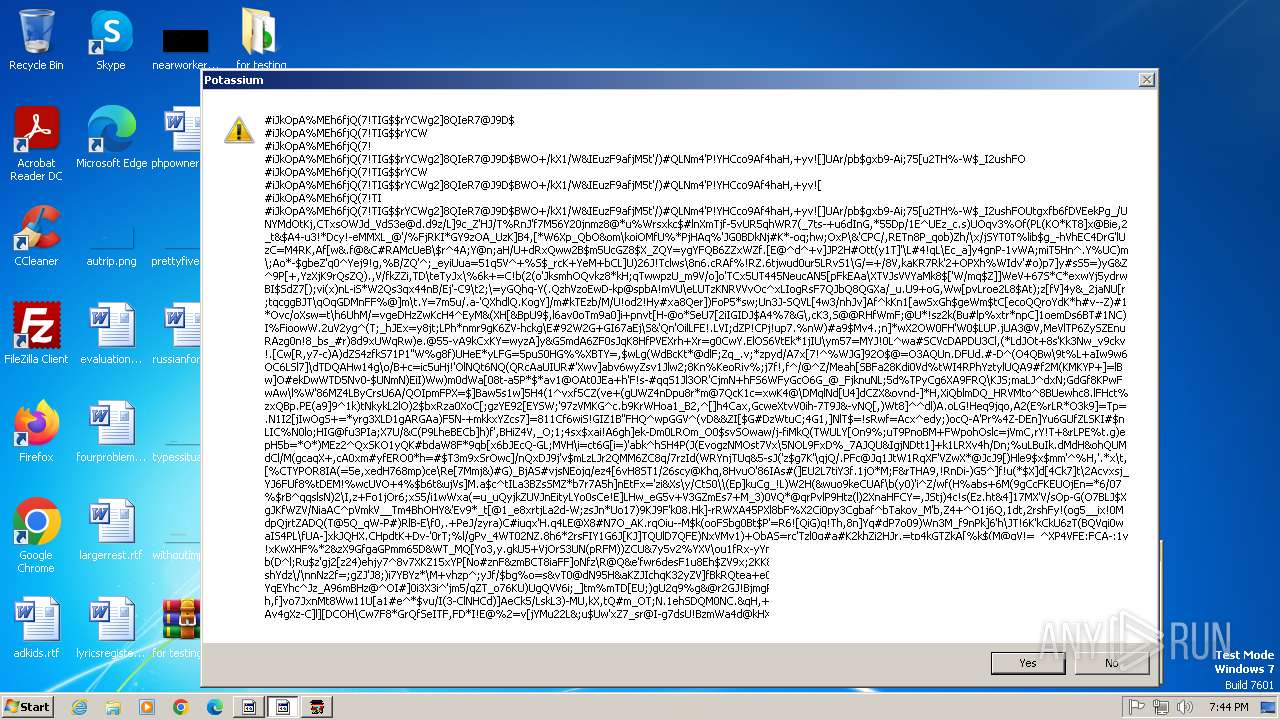
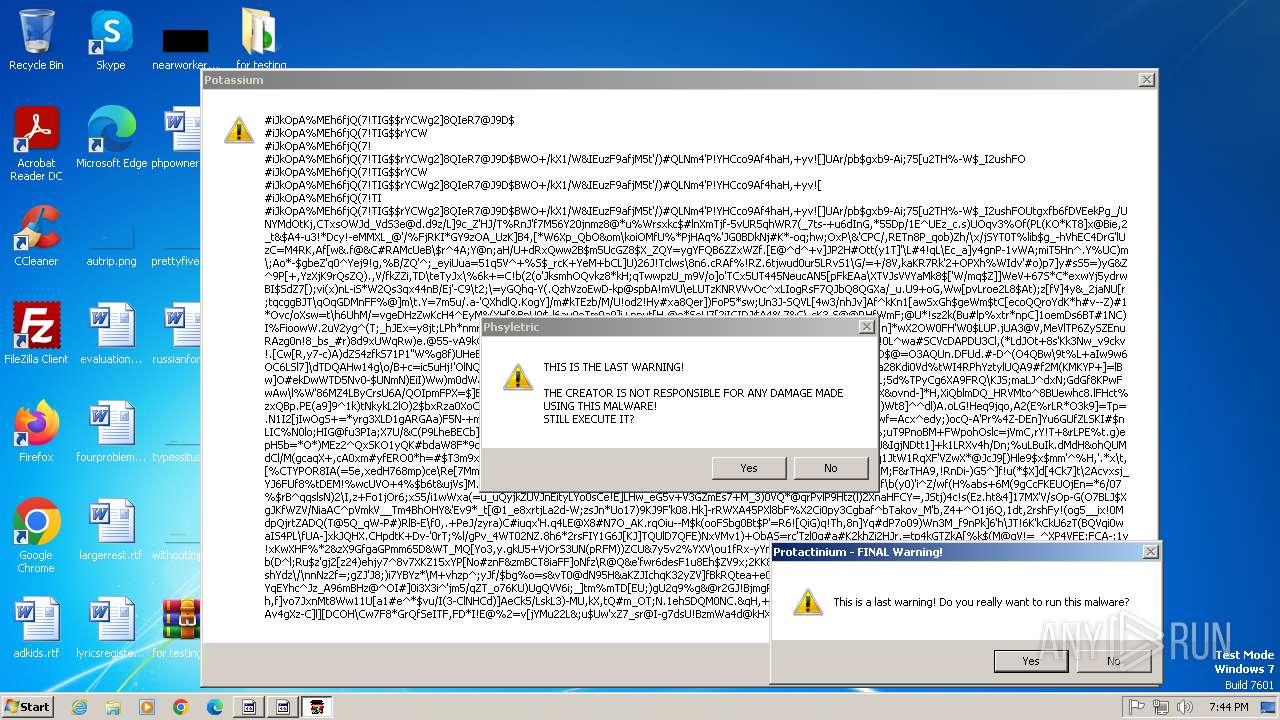
- Protactinium.exe (PID: 3292)
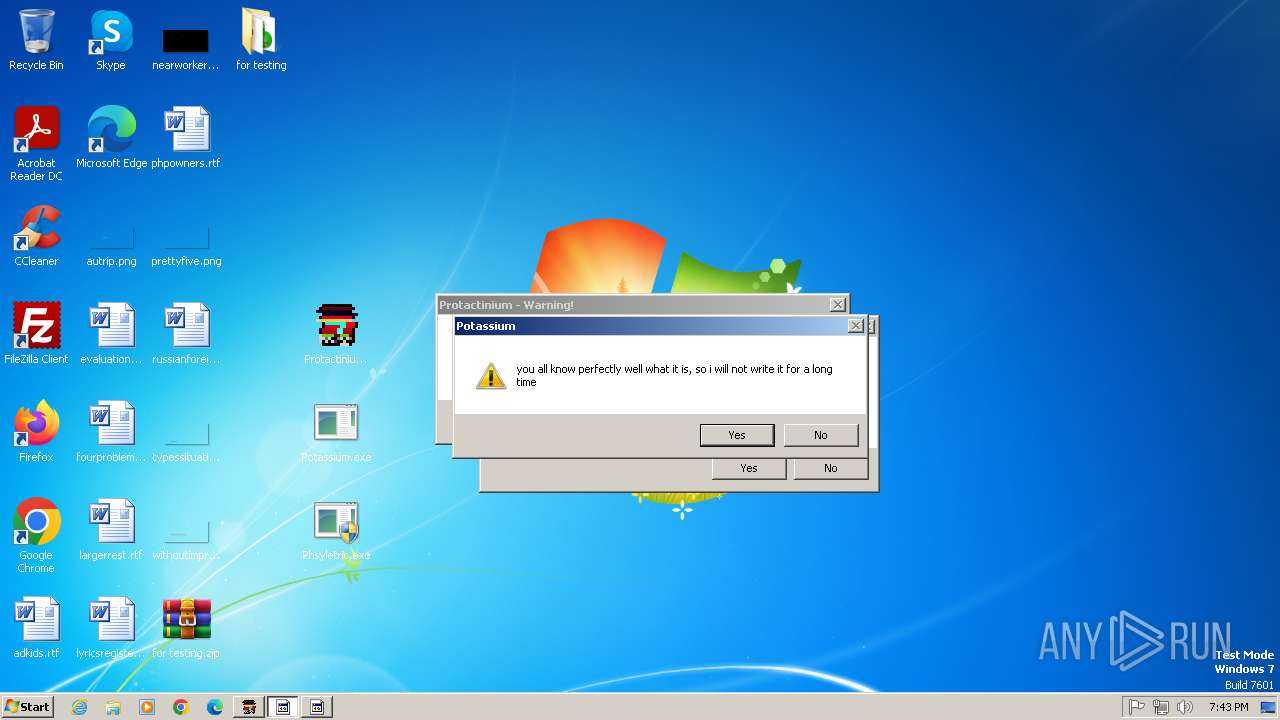
Uses TASKKILL.EXE to kill process
- Protactinium.exe (PID: 3292)
Uses REG/REGEDIT.EXE to modify registry
- Protactinium.exe (PID: 3292)
INFO
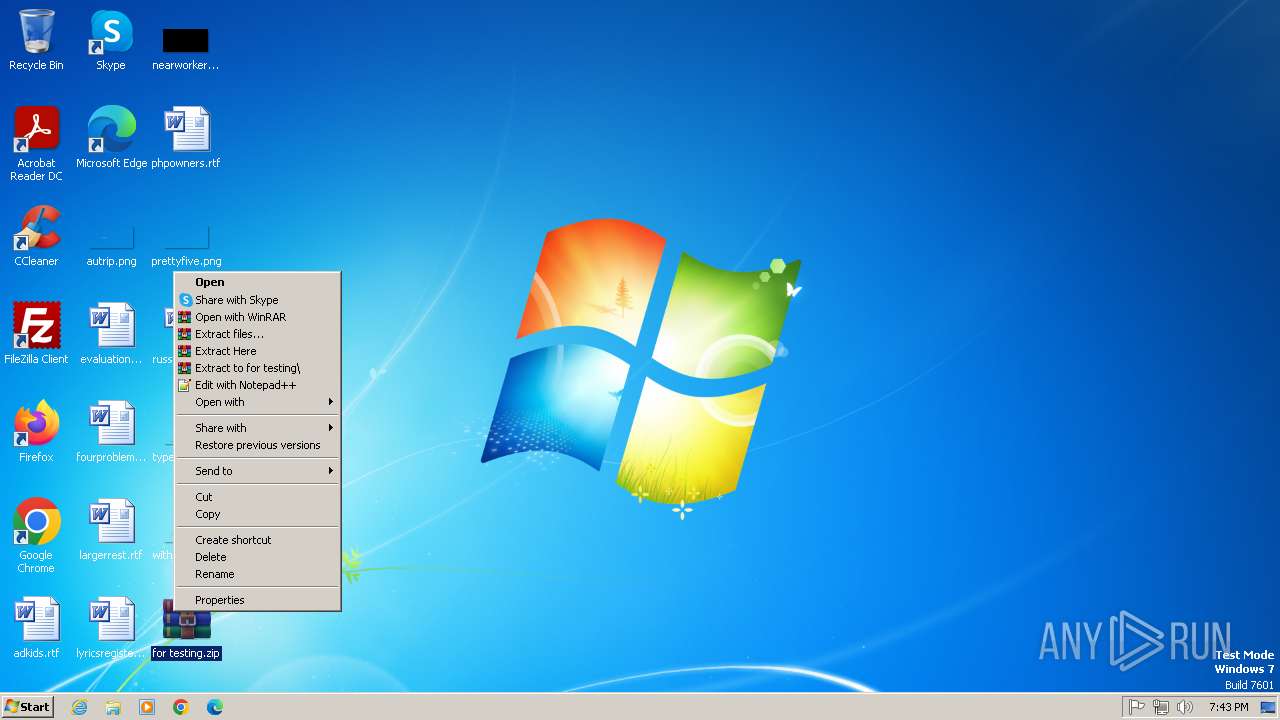
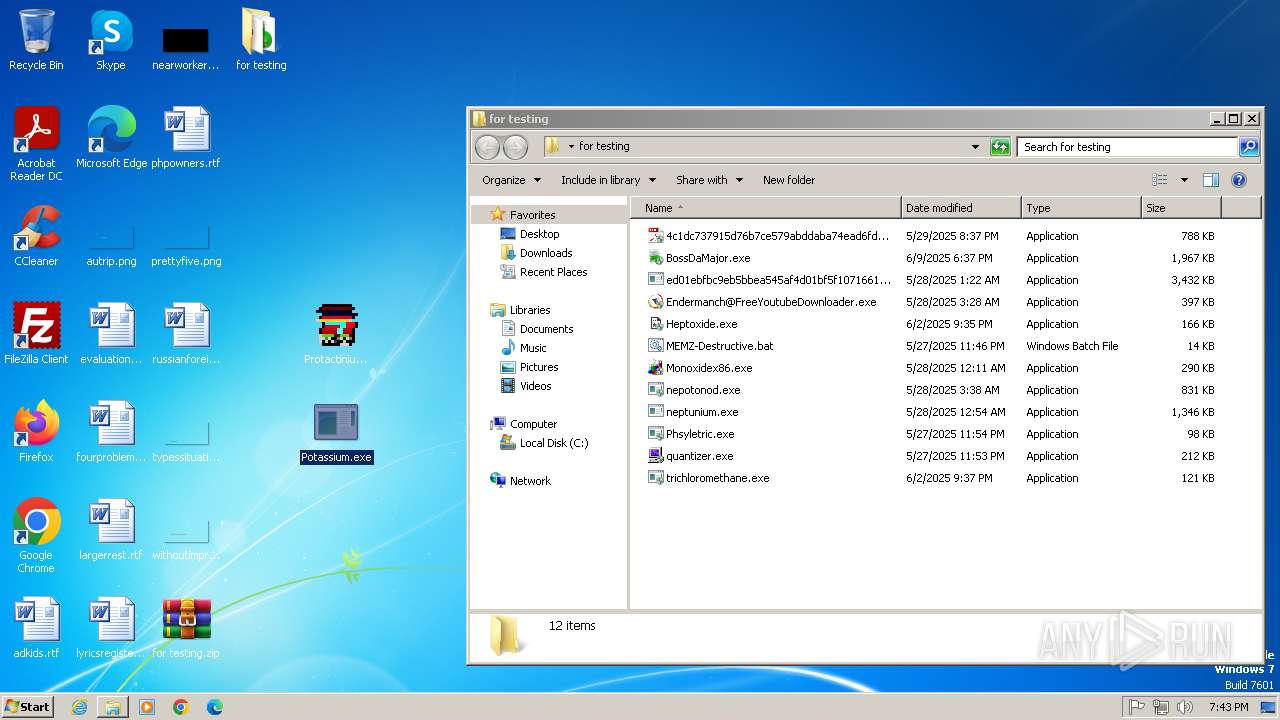
Manual execution by a user
- WinRAR.exe (PID: 1564)
- Protactinium.exe (PID: 3292)
- Potassium.exe (PID: 3216)
- Phsyletric.exe (PID: 1852)
The sample compiled with english language support
- WinRAR.exe (PID: 1564)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1564)
Checks supported languages
- Potassium.exe (PID: 3216)
- Protactinium.exe (PID: 3292)
- Phsyletric.exe (PID: 1852)
Reads the computer name
- Phsyletric.exe (PID: 1852)
- Potassium.exe (PID: 3216)
- Protactinium.exe (PID: 3292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 45 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:06:09 18:37:16 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | for testing/ |
Total processes
57
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1564 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\for testing.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
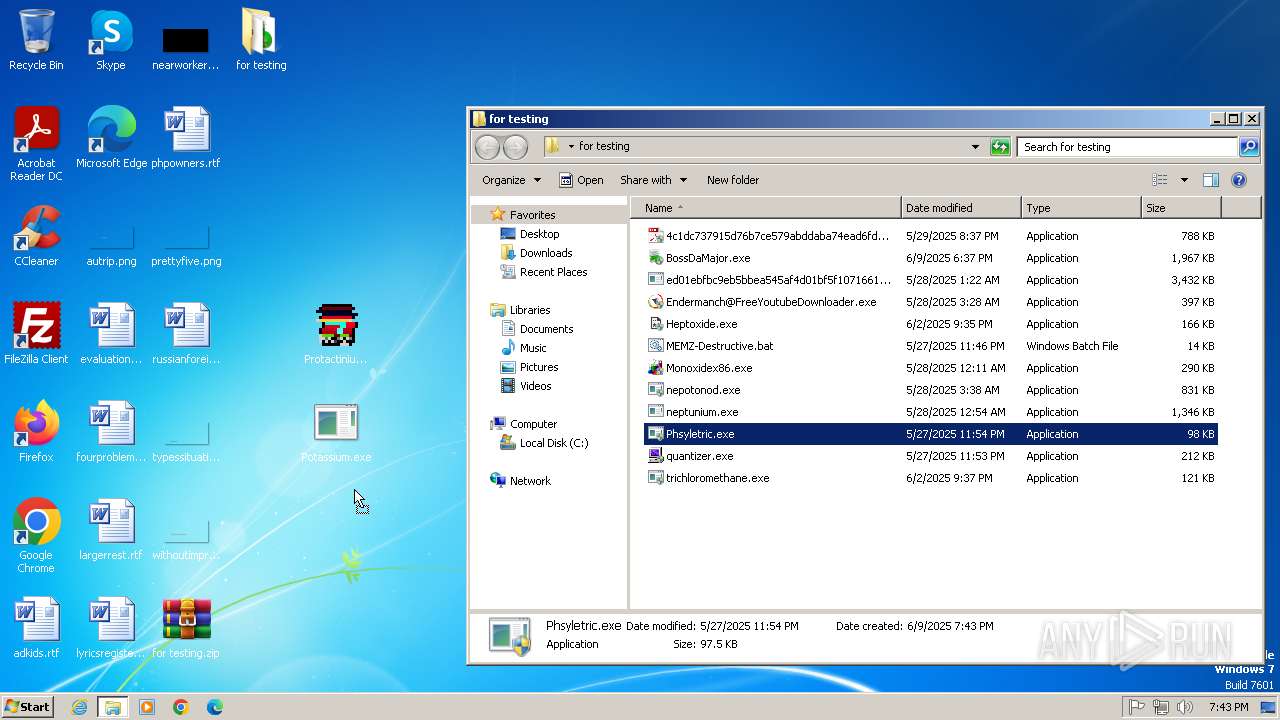
| 1852 | "C:\Users\admin\Desktop\Phsyletric.exe" | C:\Users\admin\Desktop\Phsyletric.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\for testing.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
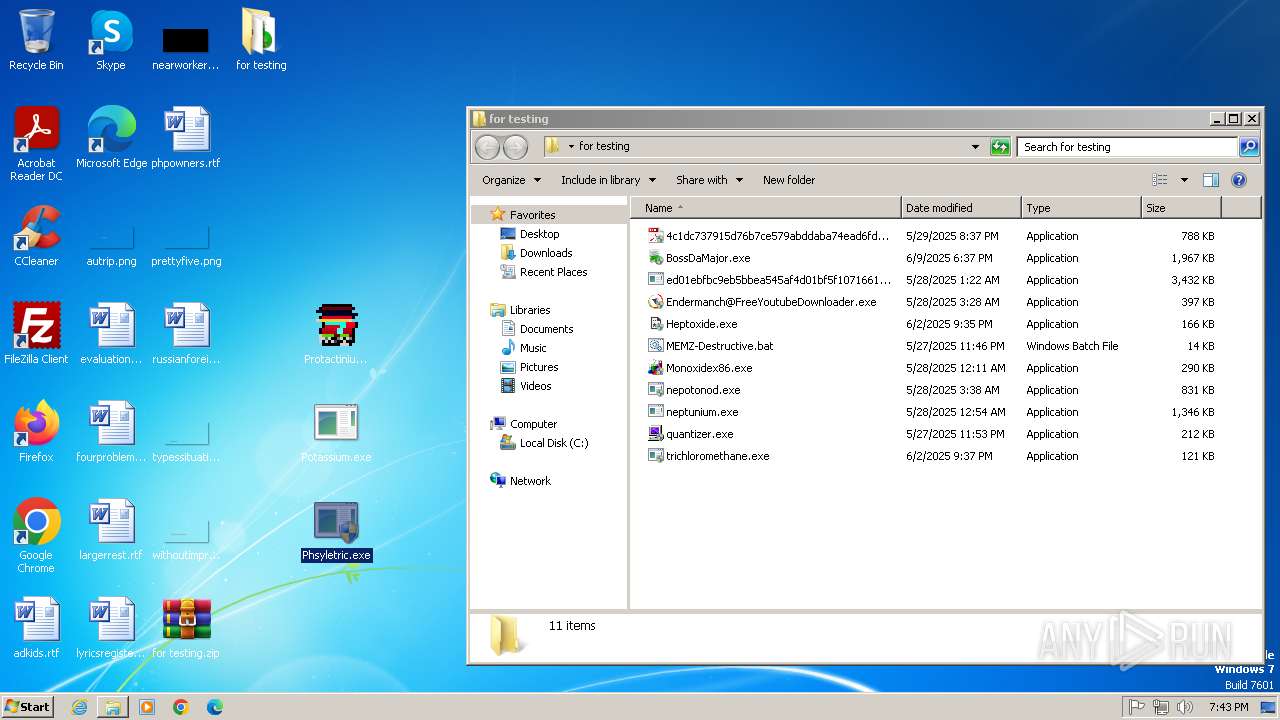
| 3216 | "C:\Users\admin\Desktop\Potassium.exe" | C:\Users\admin\Desktop\Potassium.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3224 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | Protactinium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
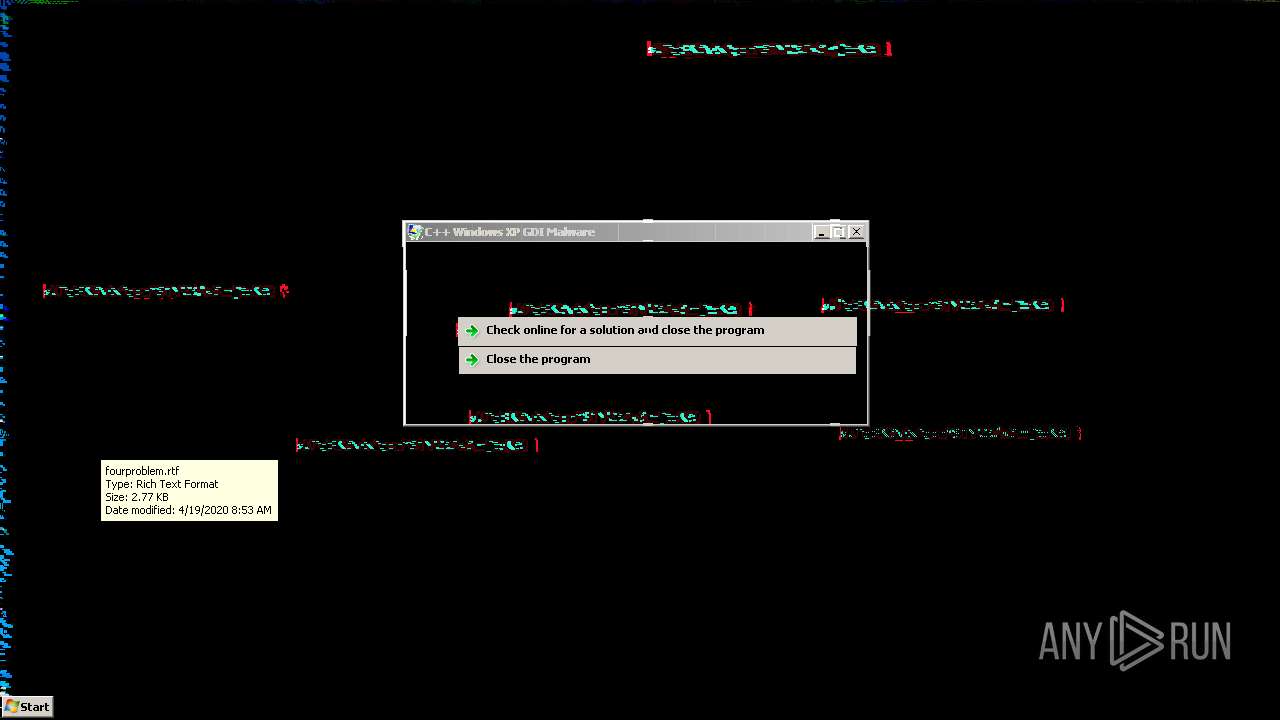
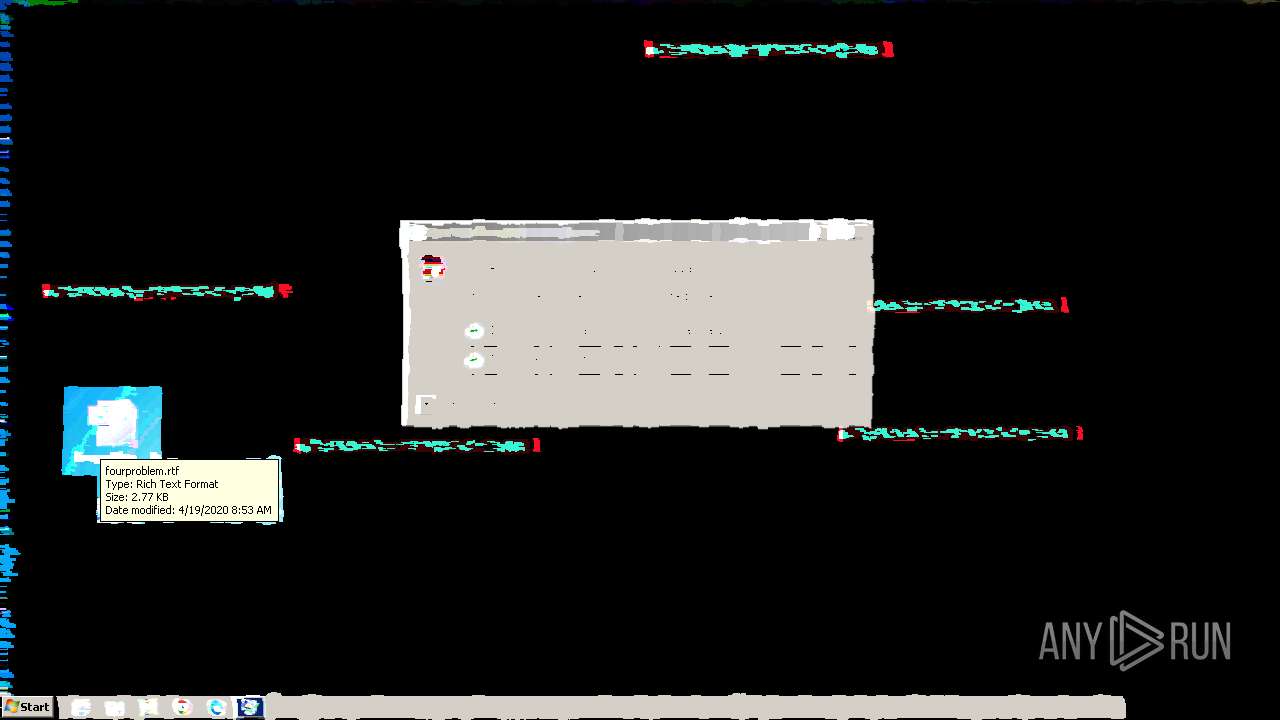
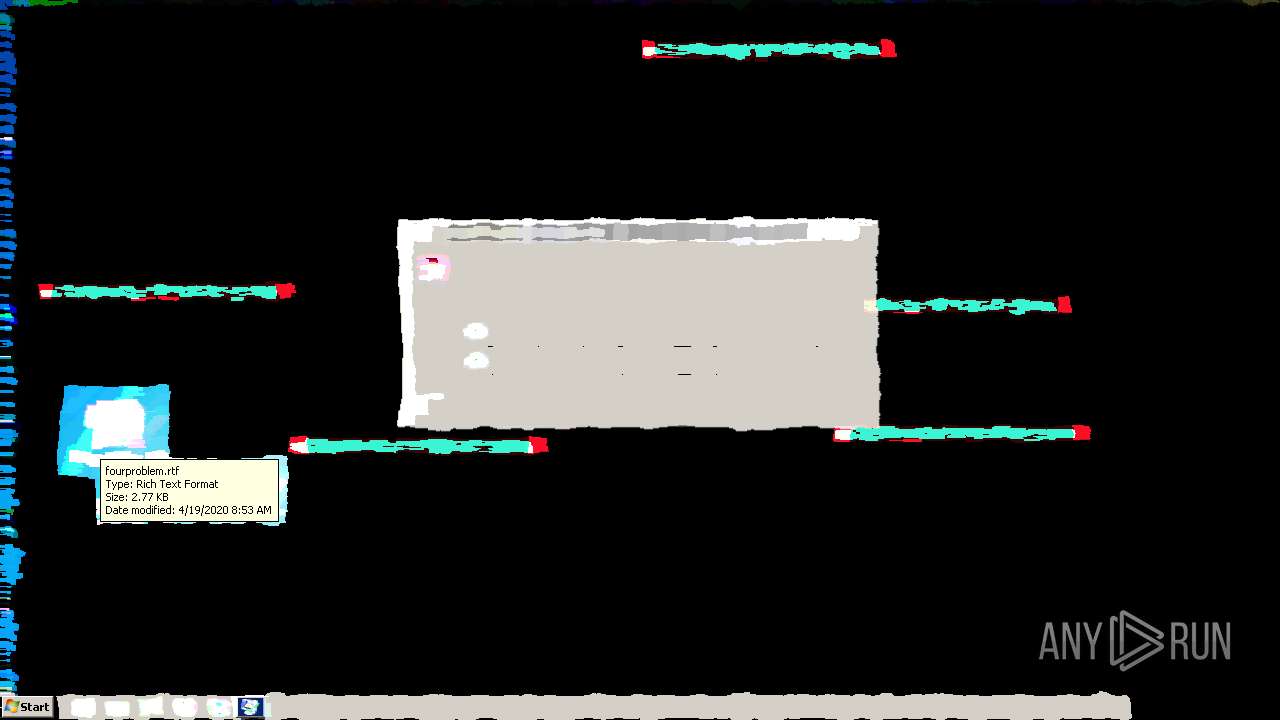
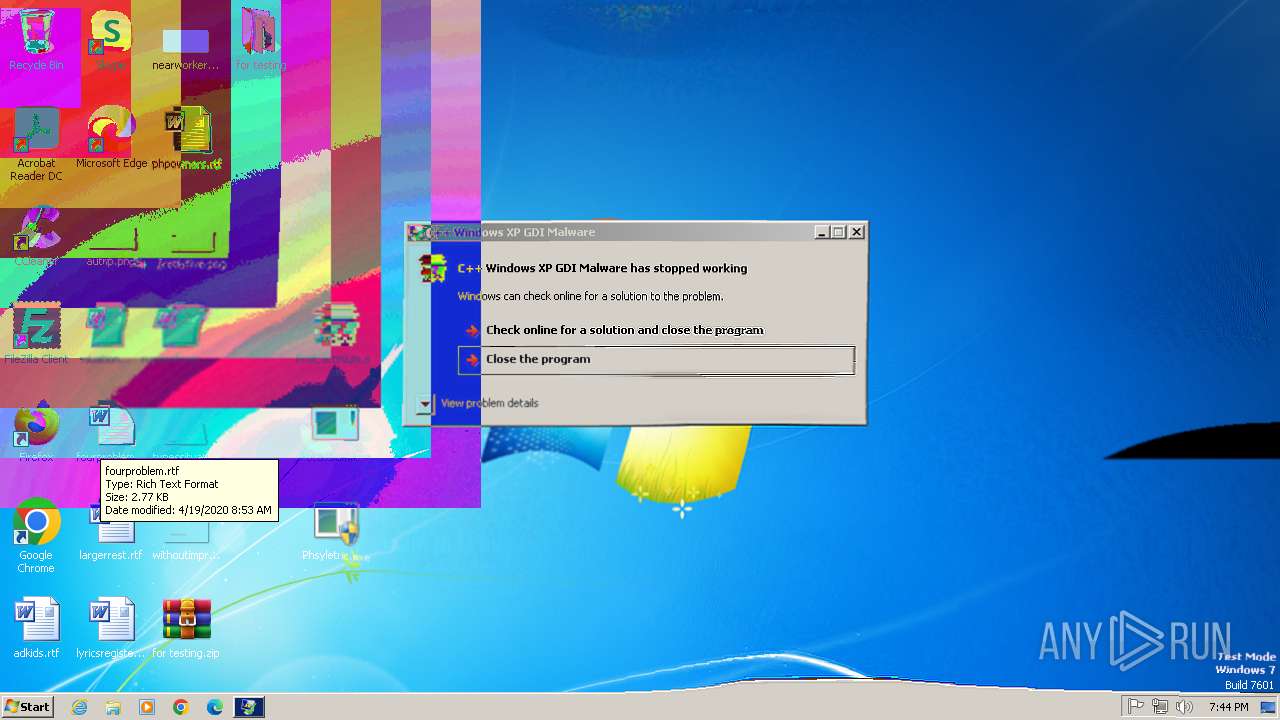
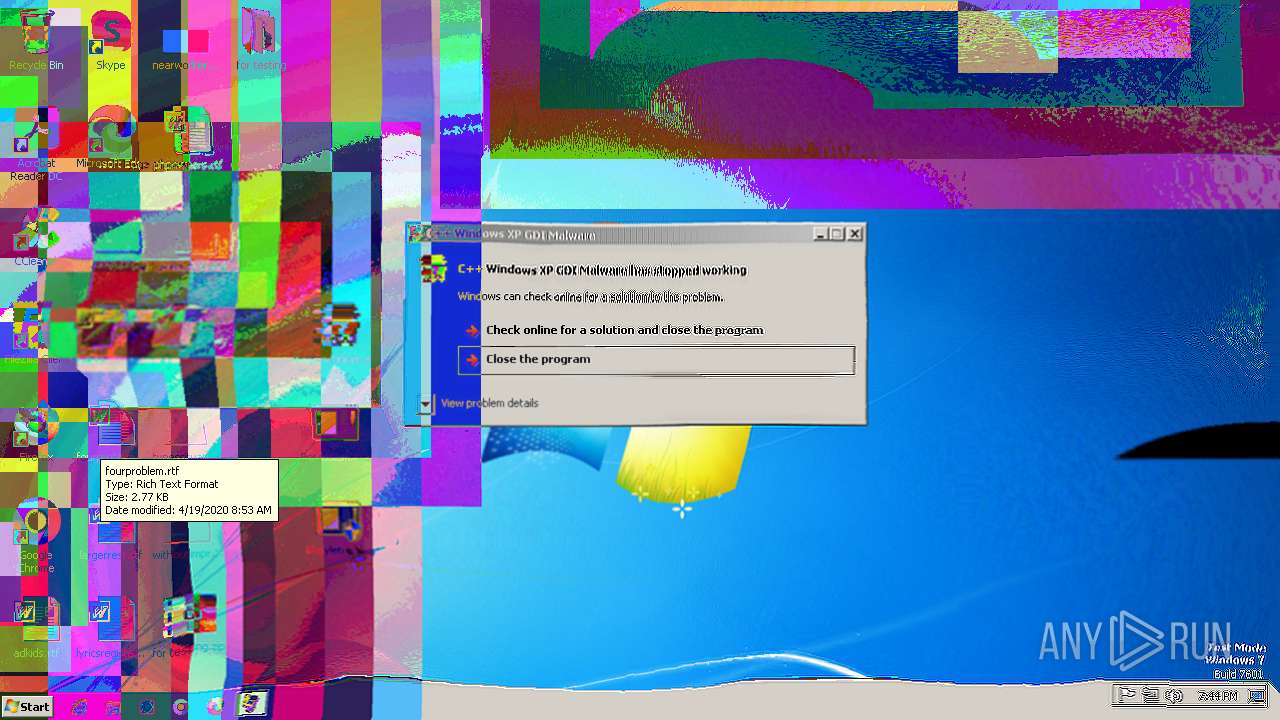
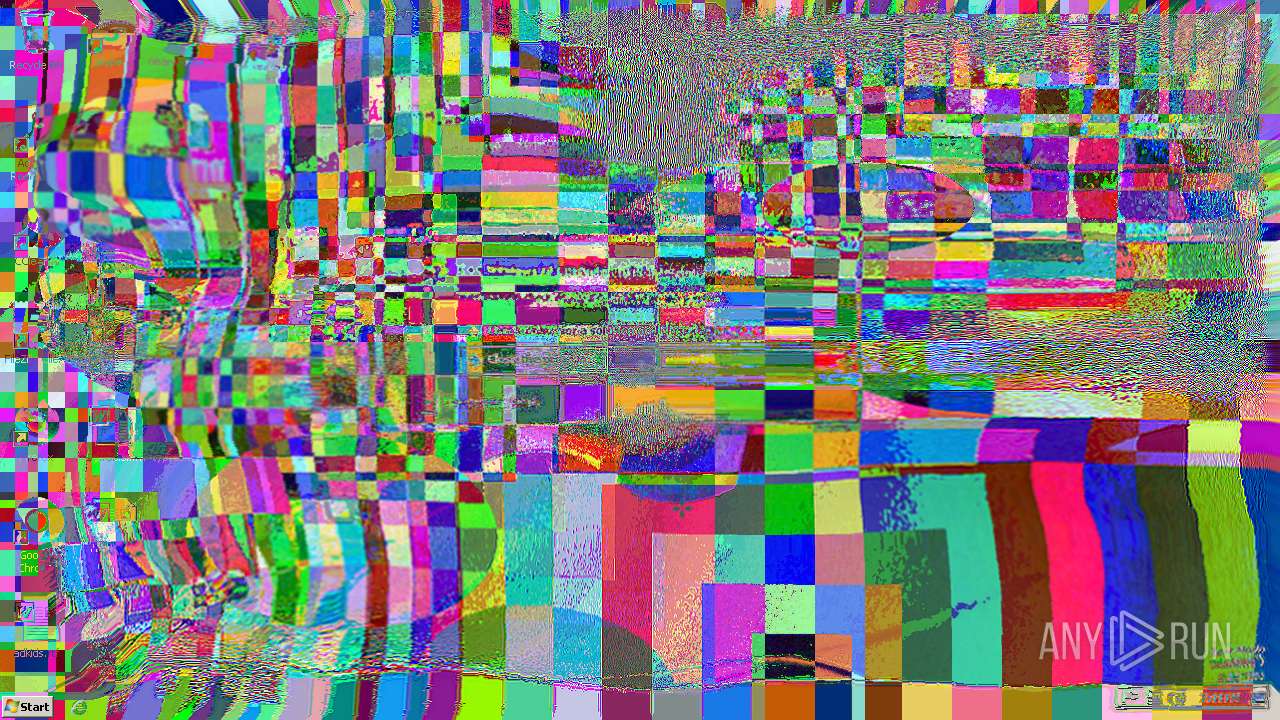
| 3292 | "C:\Users\admin\Desktop\Protactinium.exe" | C:\Users\admin\Desktop\Protactinium.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: C++ Windows XP GDI Malware Modules
| |||||||||||||||
| 3676 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableRegistryTools /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | Protactinium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3712 | REG add HKCU\SOFTWARE\Policies\Microsoft\Windows\System /v DisableCMD /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | Protactinium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3824 | taskkill /f /im taskmgr.exe | C:\Windows\System32\taskkill.exe | — | Protactinium.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 337
Read events
3 306
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\for testing.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
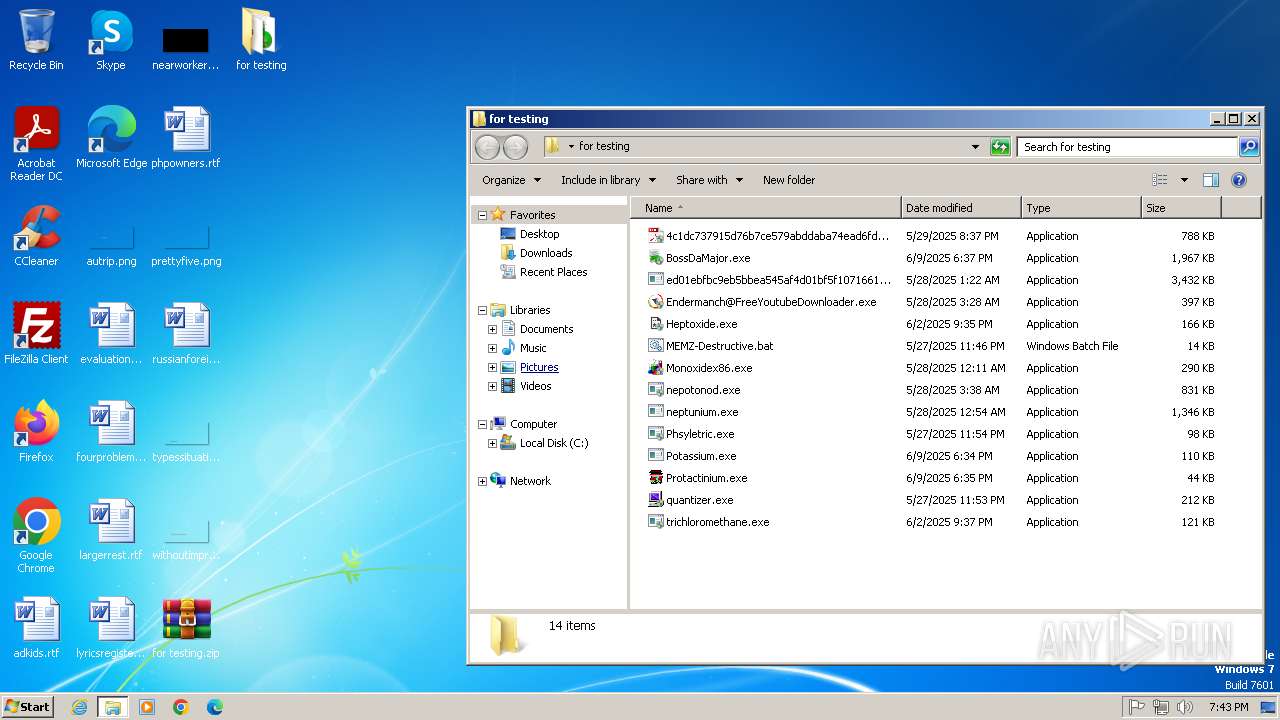
Executable files
13
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | Phsyletric.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 3292 | Protactinium.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\Phsyletric.exe | executable | |
MD5:4DB23CF50F64A83759DB9DF6AD222D65 | SHA256:465F8BF12FE8FC53C9EF45E498B5F9D95B783C61096147BBC09182F6D19DD129 | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\Endermanch@FreeYoutubeDownloader.exe | executable | |
MD5:13F4B868603CF0DD6C32702D1BD858C9 | SHA256:CAE57A60C4D269CD1CA43EF143AEDB8BFC4C09A7E4A689544883D05CE89406E7 | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\nepotonod.exe | executable | |
MD5:5DD681FA32DB64F6119423AFB4DFB6FD | SHA256:E75A807501916DBBFFDBA65E938588DE4E8DC51B8AF90CAB107260C6684873C2 | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\Protactinium.exe | executable | |
MD5:F6AA0DD947FF84DB2C0E991AAB776DCC | SHA256:2AB5F10366EBAD9E4AF9369730495A6BD48AD278E78F880A54D583024491786D | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\quantizer.exe | executable | |
MD5:1458480CF8803569195F934D47AC7481 | SHA256:68D528F9AC891E920449188198A233B71B2860838AF4FB970B9966F941CE82CA | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\ed01ebfbc9eb5bbea545af4d01bf5f1071661840480439c6e5babe8e080e41aa.exe | executable | |
MD5:84C82835A5D21BBCF75A61706D8AB549 | SHA256:ED01EBFBC9EB5BBEA545AF4D01BF5F1071661840480439C6E5BABE8E080E41AA | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\neptunium.exe | executable | |
MD5:94259B5AD79024A5B6F5388F18EC061F | SHA256:100B97224063DBAEA25B4D53672B7E3FC81443AEEF10151C47096FFB3C849334 | |||
| 1564 | WinRAR.exe | C:\Users\admin\Desktop\for testing\Potassium.exe | executable | |
MD5:86D3F3F29362283921A9277BDFB73648 | SHA256:B264D303E833F180F46A5B5F04C8A4EBD41DB3E5AADB2E1E0058F2C2BF7B5A5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |