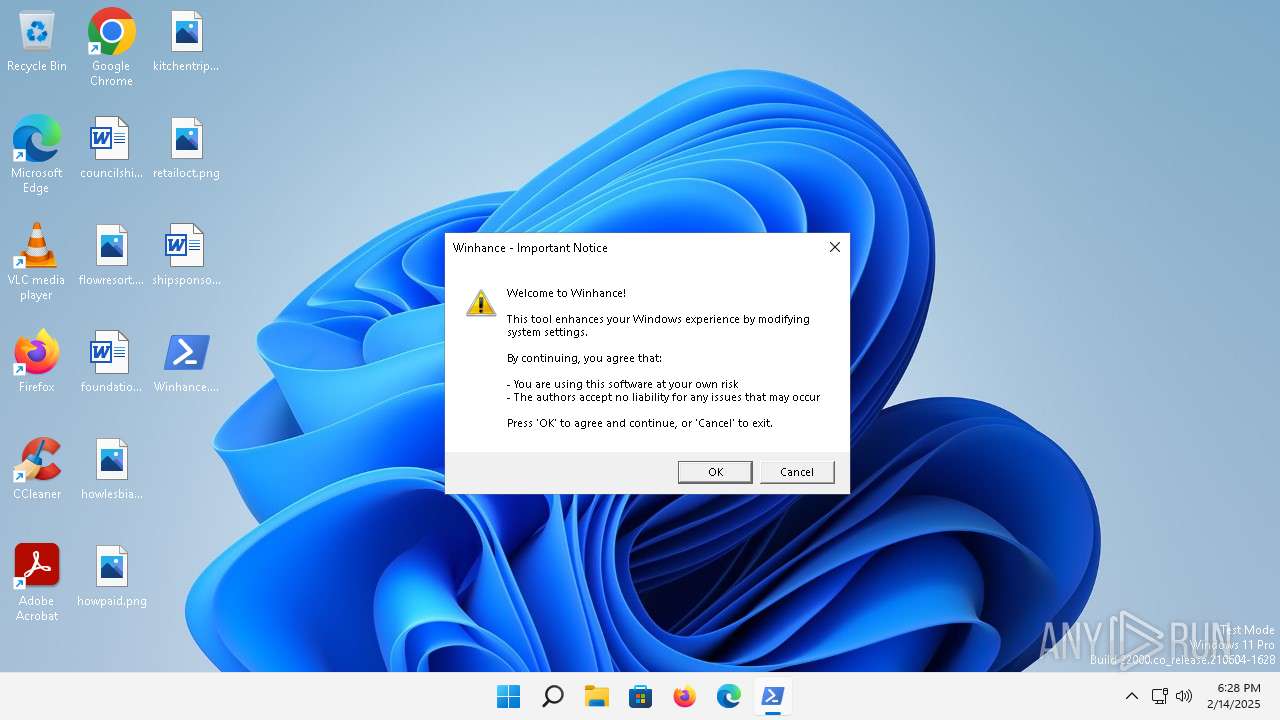
| File name: | Winhance.ps1 |
| Full analysis: | https://app.any.run/tasks/b4cadba3-e670-41ae-b29c-60496cf9815c |
| Verdict: | Malicious activity |
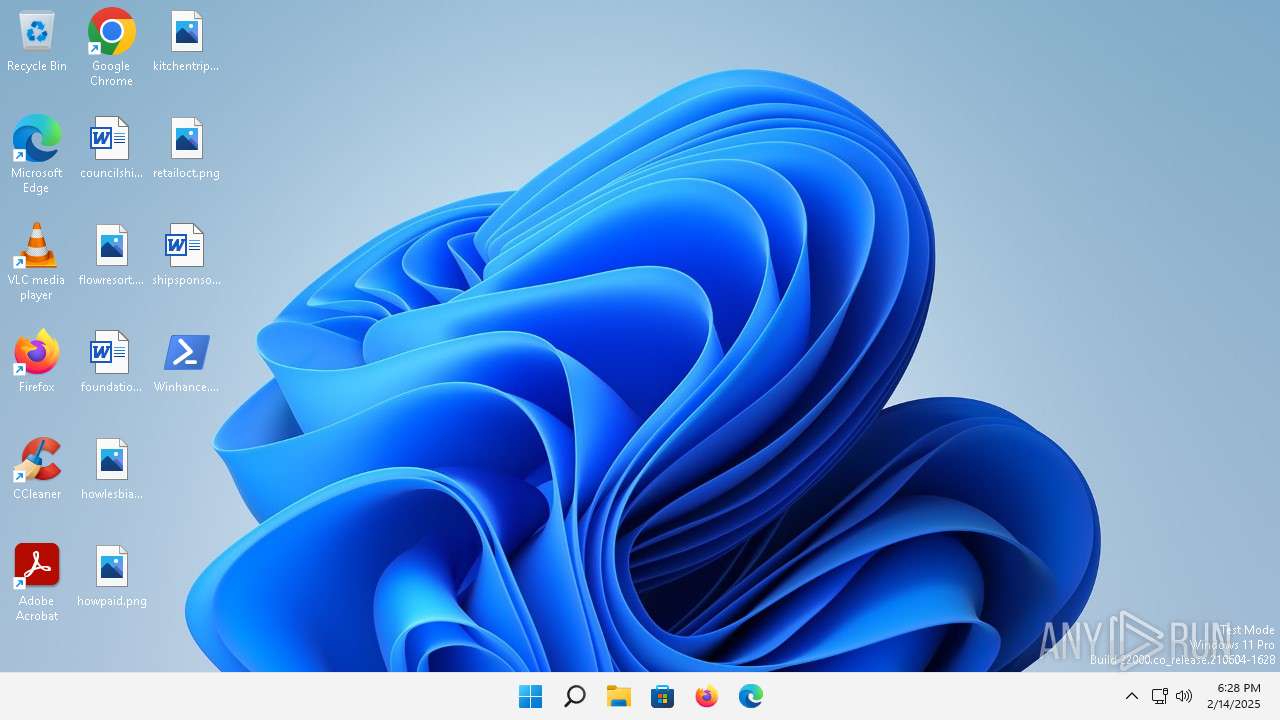
| Analysis date: | February 14, 2025, 18:28:13 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | F96CB921FD8E27EAB044A76D33B5CCD7 |
| SHA1: | 1FD8EAA1626931F15ACB56D9327173B8EAE301D7 |
| SHA256: | E66A699BCC7BB9368C6E9D86DCF0CA7B589D2006AEB5590A8227400C1E2D00F8 |
| SSDEEP: | 6144:+Qy8DgVcvPbksVuEKVfGdnZnVn6aWBul3G:+Qy8f1Gv |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 596)
- powershell.exe (PID: 4176)
Run PowerShell with an invisible window
- powershell.exe (PID: 4176)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 596)
SUSPICIOUS
CSC.EXE is used to compile C# code
- csc.exe (PID: 7128)
- csc.exe (PID: 6380)
- csc.exe (PID: 5752)
- csc.exe (PID: 2700)
Executable content was dropped or overwritten
- csc.exe (PID: 6380)
- csc.exe (PID: 7128)
- csc.exe (PID: 5752)
- csc.exe (PID: 2700)
- powershell.exe (PID: 4176)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 596)
- powershell.exe (PID: 4176)
Reads the Internet Settings
- powershell.exe (PID: 596)
- powershell.exe (PID: 4176)
Application launched itself
- powershell.exe (PID: 596)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 596)
The process executes Powershell scripts
- powershell.exe (PID: 596)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 596)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 5232)
- DismHost.exe (PID: 7108)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4176)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 4176)
Process drops legitimate windows executable
- powershell.exe (PID: 4176)
The process creates files with name similar to system file names
- powershell.exe (PID: 4176)
INFO
Checks supported languages
- cvtres.exe (PID: 4012)
- csc.exe (PID: 7128)
- csc.exe (PID: 6380)
- cvtres.exe (PID: 2032)
- csc.exe (PID: 5752)
- cvtres.exe (PID: 4260)
- csc.exe (PID: 2700)
- cvtres.exe (PID: 3664)
- DismHost.exe (PID: 5232)
- DismHost.exe (PID: 7108)
Reads the machine GUID from the registry
- csc.exe (PID: 7128)
- csc.exe (PID: 6380)
- csc.exe (PID: 5752)
- csc.exe (PID: 2700)
Create files in a temporary directory
- cvtres.exe (PID: 4012)
- cvtres.exe (PID: 2032)
- csc.exe (PID: 7128)
- csc.exe (PID: 6380)
- cvtres.exe (PID: 4260)
- csc.exe (PID: 2700)
- csc.exe (PID: 5752)
- cvtres.exe (PID: 3664)
Creates files in the program directory
- powershell.exe (PID: 4176)
Reads mouse settings
- powershell.exe (PID: 4176)
The sample compiled with english language support
- powershell.exe (PID: 4176)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 5232)
- DismHost.exe (PID: 7108)
Reads Environment values
- DismHost.exe (PID: 7108)
- DismHost.exe (PID: 5232)
Reads the computer name
- DismHost.exe (PID: 5232)
- DismHost.exe (PID: 7108)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xaml | | | Microsoft Extensible Application Markup Language (100) |
|---|
Total processes
124
Monitored processes
15
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\Winhance.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1633.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC4C9D8ABAD53426BA1757B2642355A.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2700 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\uy512rl2\uy512rl2.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3256 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3664 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES22F5.tmp" "c:\Users\admin\AppData\Local\Temp\uy512rl2\CSC1E1866CC36AE4AA7AAB7F66D358CB2B.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4012 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES15A7.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF5F3DAAB1ABB473B9570AEDDCD311559.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 4168 | C:\Windows\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.22000.795_none_047def894cac2b60\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.22000.795 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4176 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -File "C:\Users\admin\Desktop\Winhance.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4260 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES2278.tmp" "c:\Users\admin\AppData\Local\Temp\e3utysyt\CSC8B6E4FFBA5B54B0BACBC63A1B3FA5A.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 5232 | C:\Users\admin\AppData\Local\Temp\BFF8DFCD-61BA-487F-AB1C-2236BB088B70\dismhost.exe {B1FB260C-C1D8-43C8-8AC9-E8D500F59176} | C:\Users\admin\AppData\Local\Temp\BFF8DFCD-61BA-487F-AB1C-2236BB088B70\DismHost.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
89 330
Read events
89 310
Write events
20
Delete events
0
Modification events
| (PID) Process: | (596) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (596) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (596) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (596) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4176) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4176) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4176) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4176) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4168) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31162126 | |||
| (PID) Process: | (4168) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
Executable files
110
Suspicious files
17
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R8Z7S9IGSCQN9JQMWIS1.temp | binary | |
MD5:05B551C61DEC85F741D0EE25C2F1C1E7 | SHA256:877D3F4115D08D1105D0FD3D228C790419D4CA33ADCFFE178EED0E172B33252B | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:05B551C61DEC85F741D0EE25C2F1C1E7 | SHA256:877D3F4115D08D1105D0FD3D228C790419D4CA33ADCFFE178EED0E172B33252B | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\g0gccfer.cmdline | text | |
MD5:E098CA211E1CAE574750F18714AA63C6 | SHA256:111218895DF1BCA95C2CAE5B912763C3532FE64F7118AC284CF39671C8761AAA | |||
| 7128 | csc.exe | C:\Users\admin\AppData\Local\Temp\g0gccfer.out | text | |
MD5:A06614A76F38ED09743BCBEFC6F9DF95 | SHA256:7737E6845483DB128009554B0C1292A9EDDD43C4CB8F805082407E256BAC6407 | |||
| 6380 | csc.exe | C:\Users\admin\AppData\Local\Temp\onmpebyt.out | text | |
MD5:69613645A58CFDDC38AC231F9C7C27CA | SHA256:01CE63E918416FEE6A2DBE7E67B1CC90DC7E93B122572D8B7B971E5F868BA20C | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF25078d.TMP | binary | |
MD5:237E19DC75ACC63ACE8E9AEE22F875F4 | SHA256:D7FDDF203D2B28EC578D77014357A3CE17C5A0277875D74FEE62FF89ABEEC253 | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zrwl3zvk.lgq.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wksnqbfe.ns0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\g0gccfer.0.cs | text | |
MD5:0E2CDC2657BE537834C77429EC55CF02 | SHA256:3817813F399AD49DA2ED1F1FF3B044D8E80934C6E83E9FFFE06E6ECDFE1195AE | |||
| 7128 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCF5F3DAAB1ABB473B9570AEDDCD311559.TMP | binary | |
MD5:0D991CB8DB9416A108A697201BEC773E | SHA256:7155467F31DC3C45038069CB42E25E97121DE0586A1BB297B3E4A0B2B83425CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.124.11.219:80 | http://www.msftconnecttest.com/connecttest.txt | DE | text | 22 b | whitelisted |
2932 | MoUsoCoreWorker.exe | GET | 200 | 217.20.57.19:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ece3e531bf08729f | US | compressed | 4.65 Kb | whitelisted |
— | — | HEAD | 200 | 23.35.236.109:443 | https://fs.microsoft.com/fs/windows/config.json | US | — | — | unknown |
2860 | svchost.exe | GET | 200 | 88.221.110.91:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?d427199d7579a766 | DE | compressed | 7.61 Kb | whitelisted |
2860 | svchost.exe | GET | 200 | 88.221.110.91:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0b3de69d37a33f41 | DE | compressed | 70.2 Kb | whitelisted |
— | — | GET | 200 | 23.35.236.109:443 | https://fs.microsoft.com/fs/windows/config.json | US | binary | 55 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.124.11.219:80 | — | Akamai International B.V. | DE | unknown |
2932 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2932 | MoUsoCoreWorker.exe | 217.20.57.19:80 | ctldl.windowsupdate.com | — | US | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4592 | svchost.exe | 92.123.18.162:443 | fs.microsoft.com | AKAMAI-AS | AT | whitelisted |
2860 | svchost.exe | 88.221.110.91:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
powershell.exe | PID=4176 TID=4152 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 Input parameters: LogLevel: 2, LogFilePath: C:\Windows\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 DismApi.dll: Host machine information: OS Version=10.0.22000, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 DismApi.dll: Parent process command line: "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -File "C:\Users\admin\Desktop\Winhance.ps1" - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 DismApi.dll: API Version 10.0.22000.653 - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 Enter - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 Initialized SessionTable - DismInitializeInternal
|
powershell.exe | PID=4176 TID=4152 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|