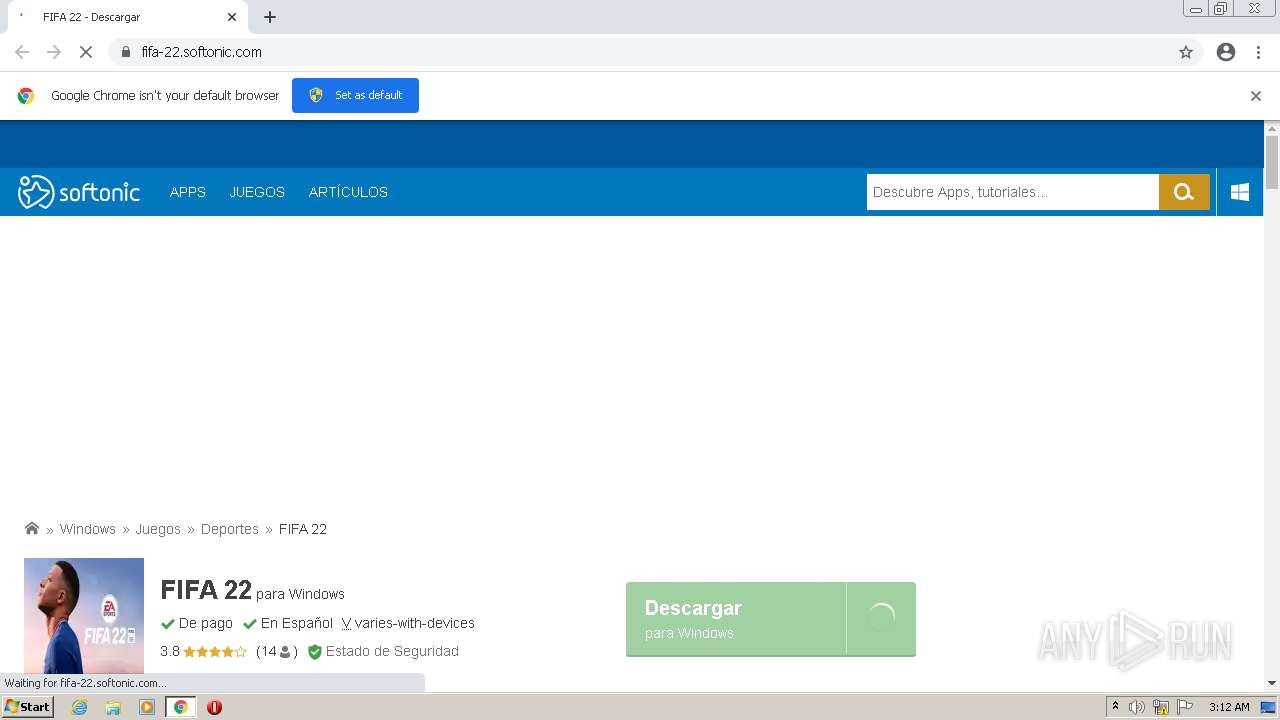
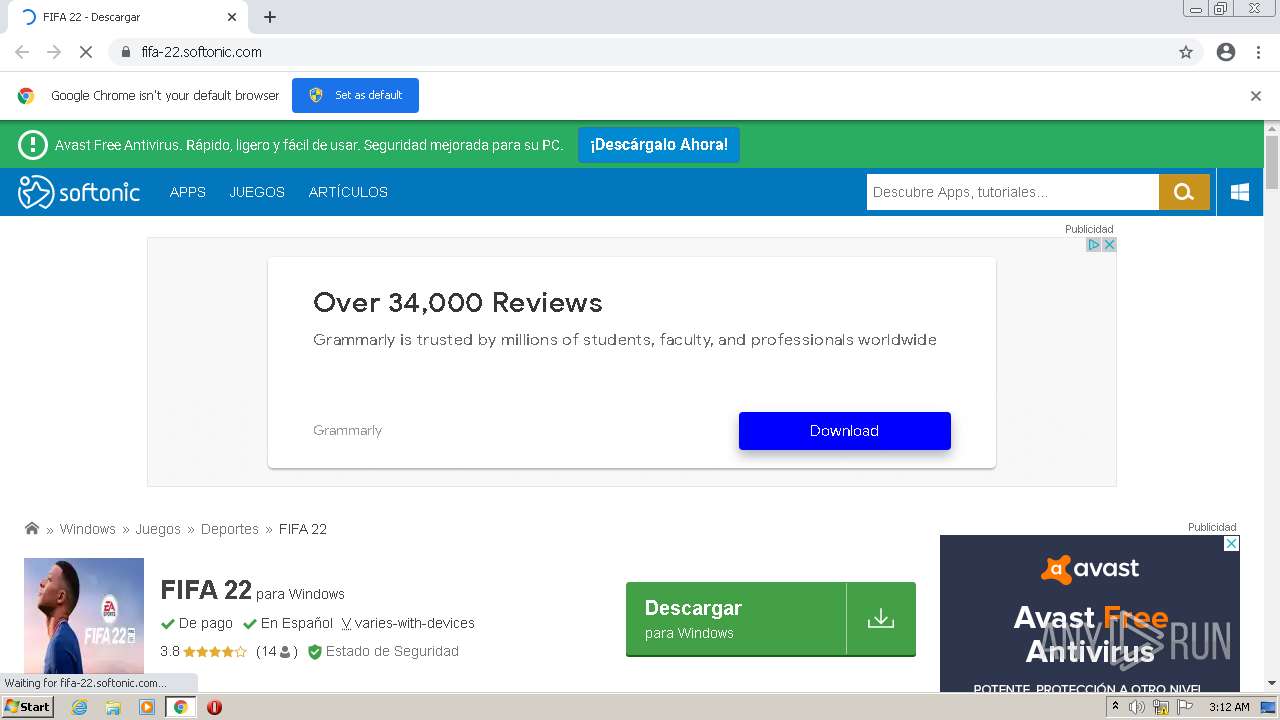
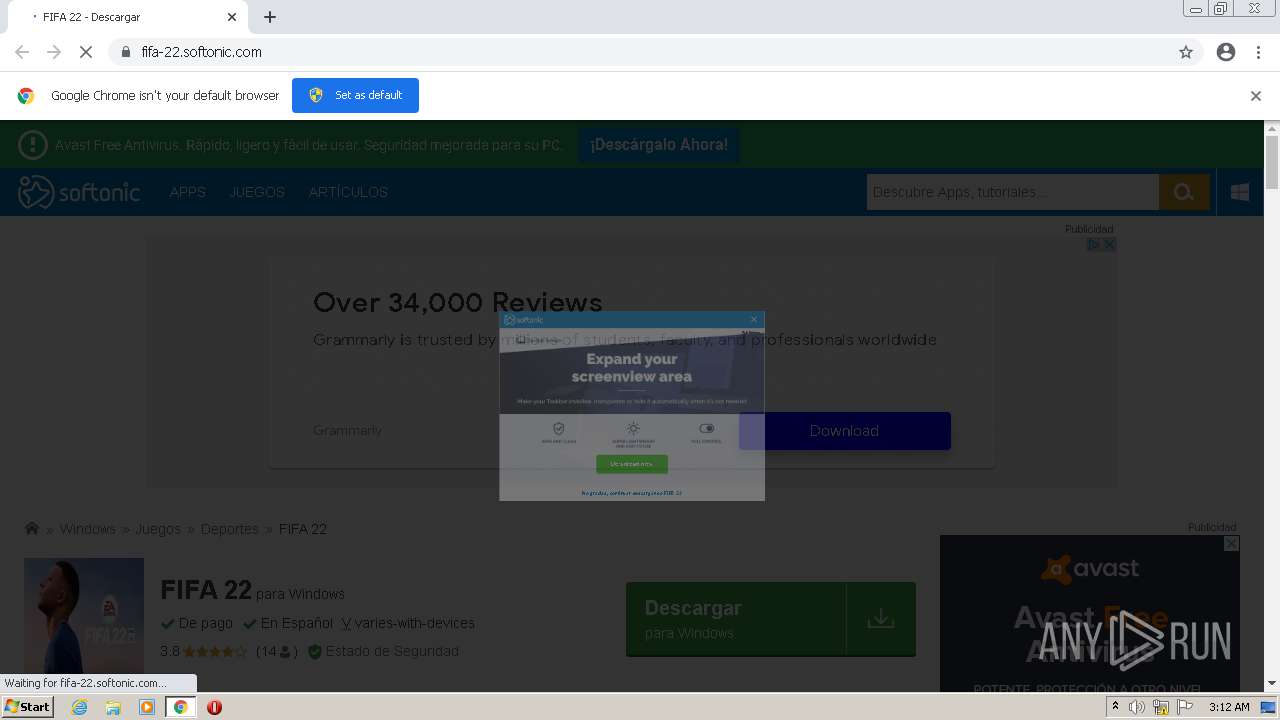
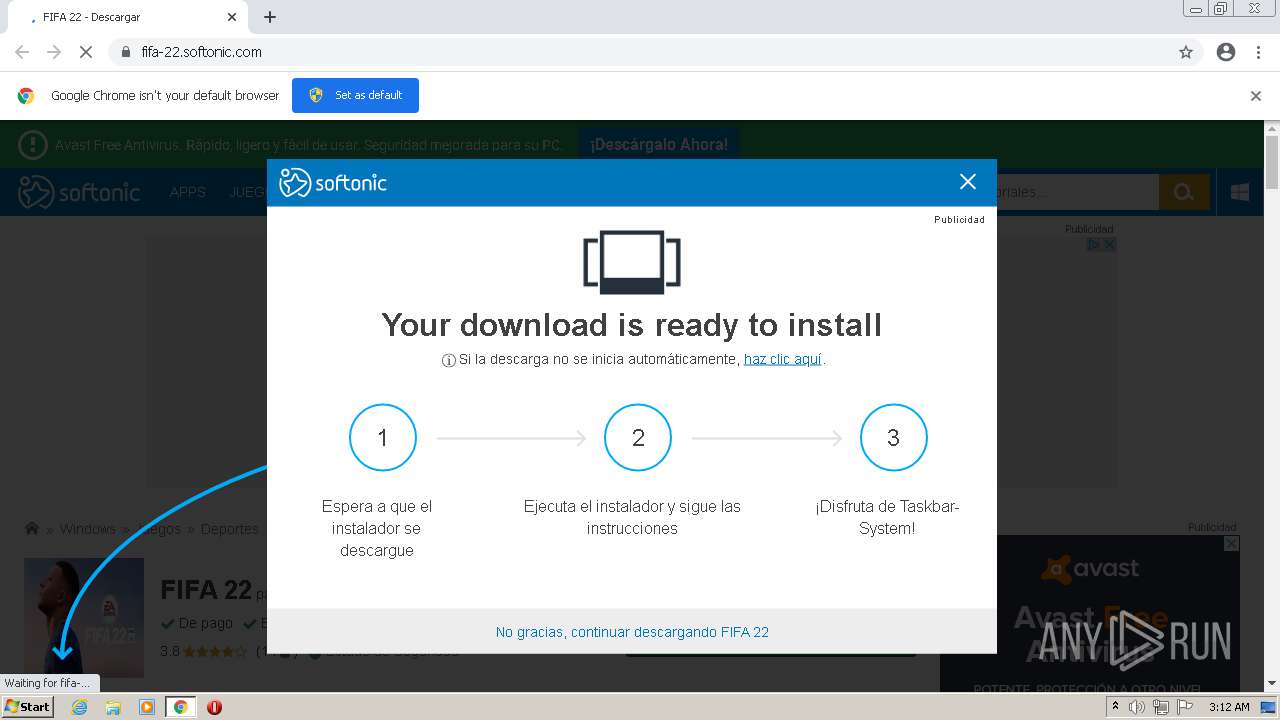
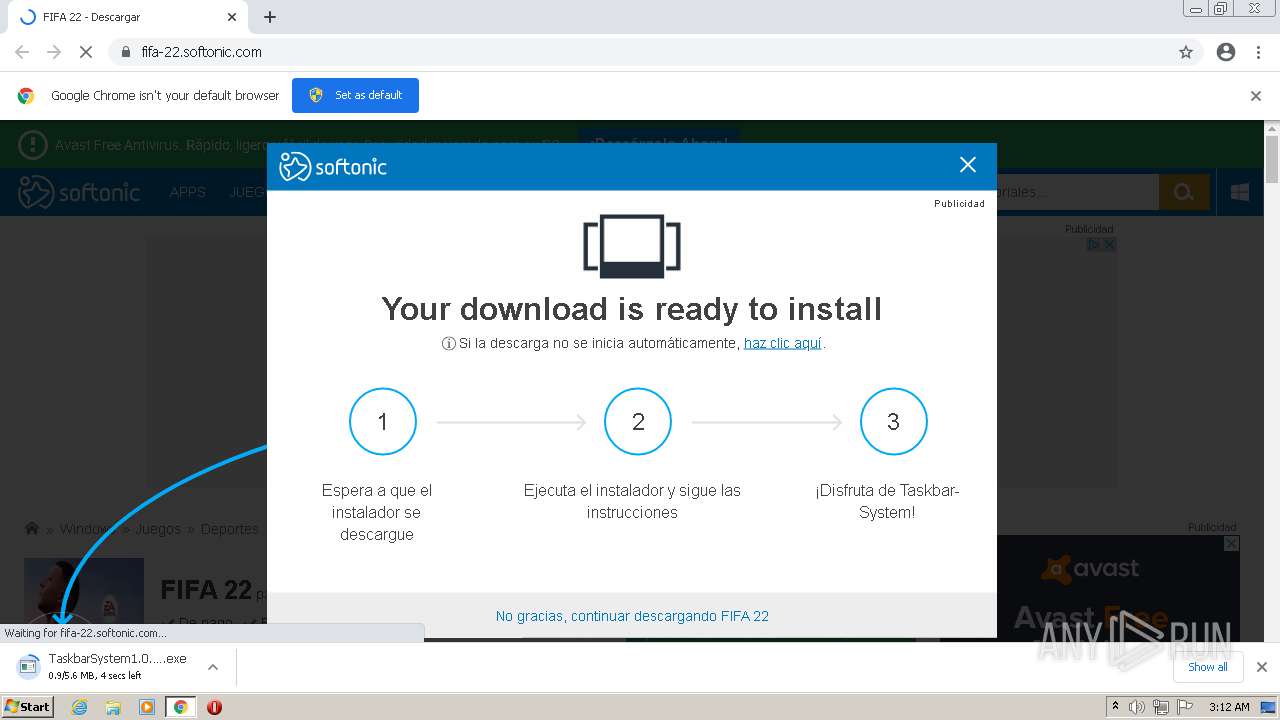
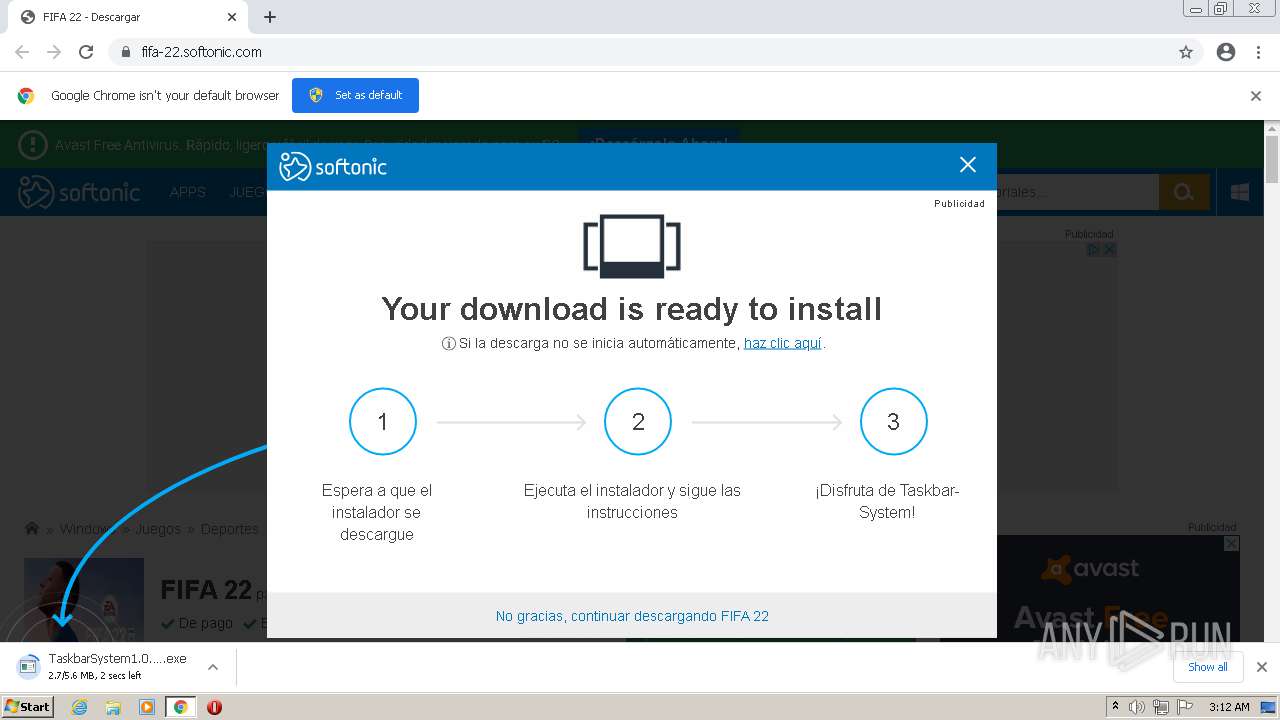
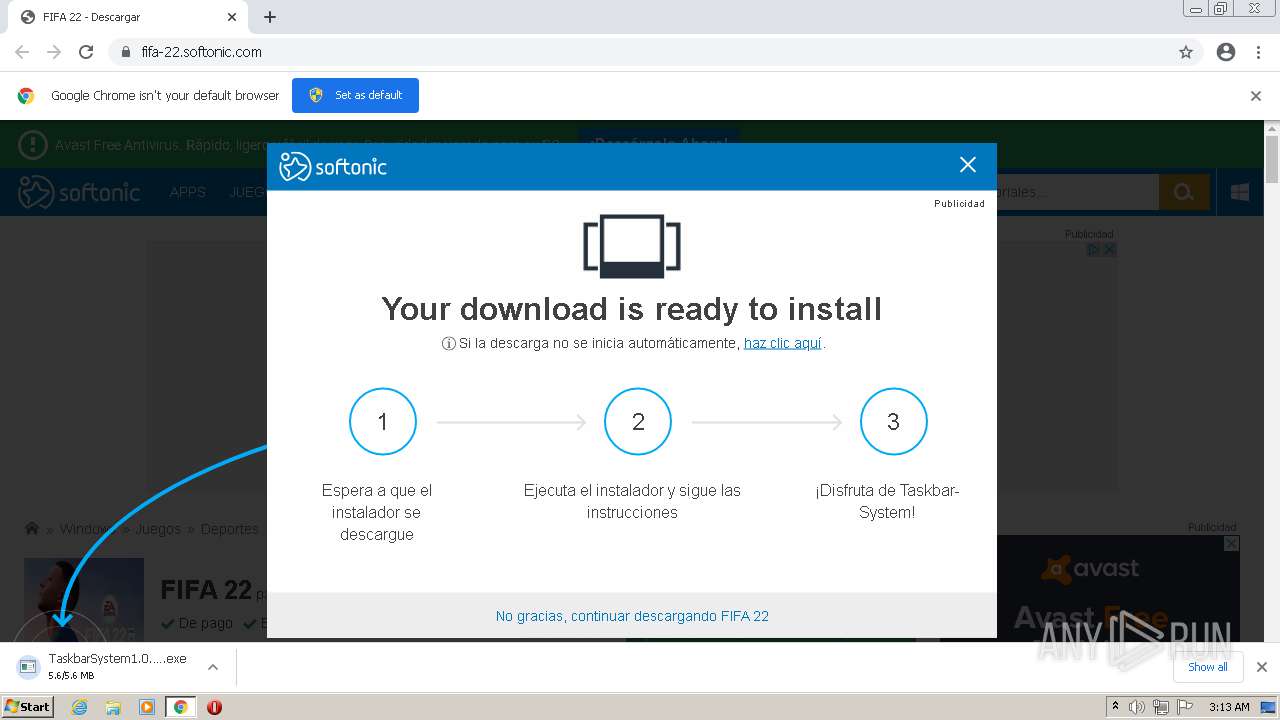
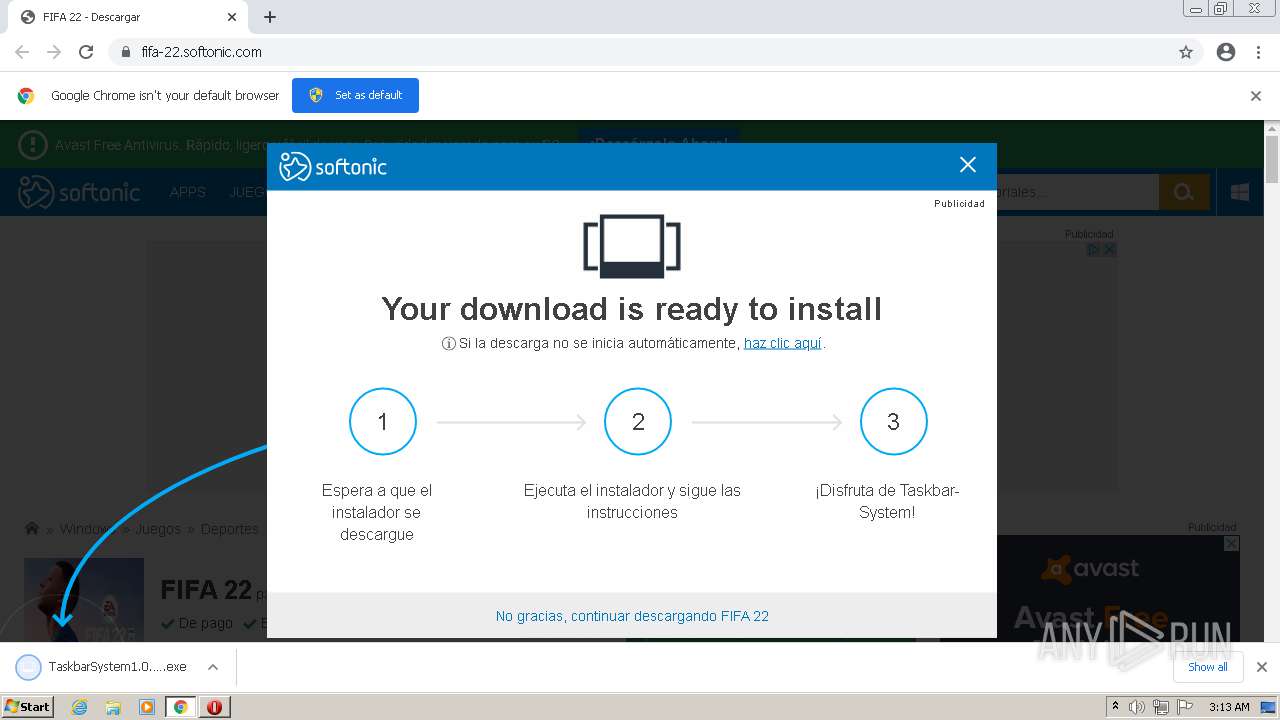
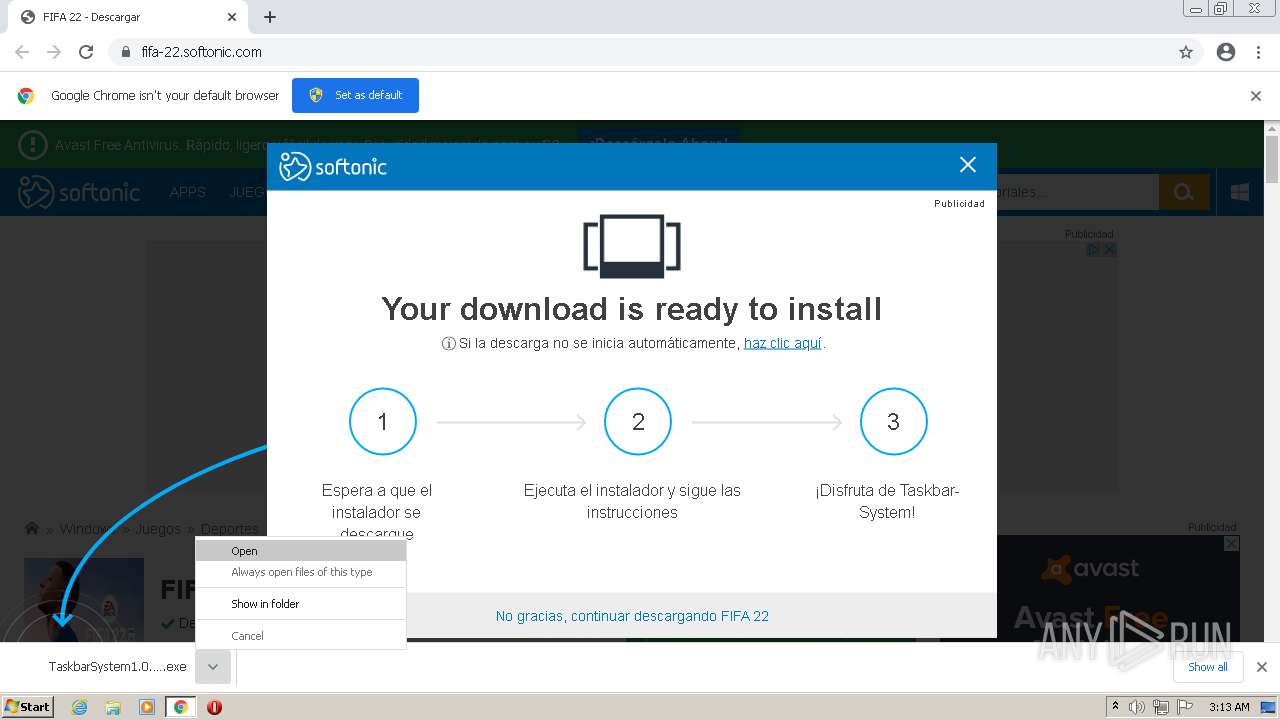
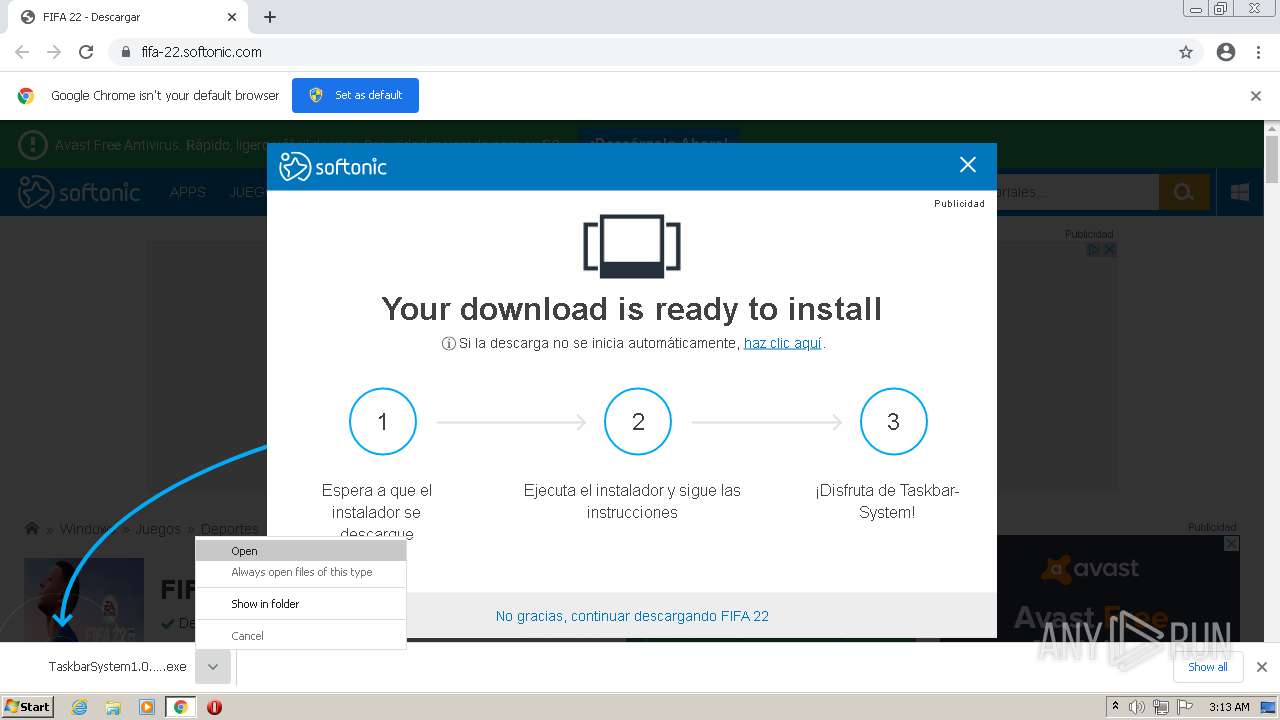
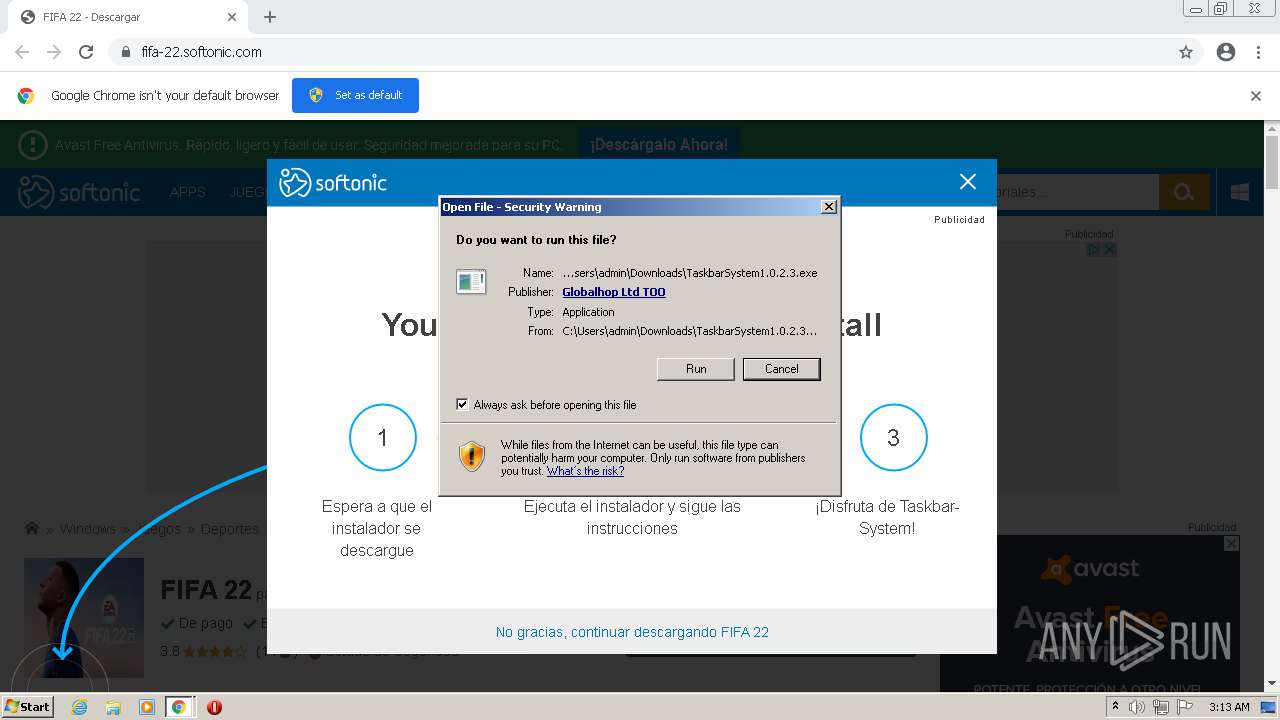
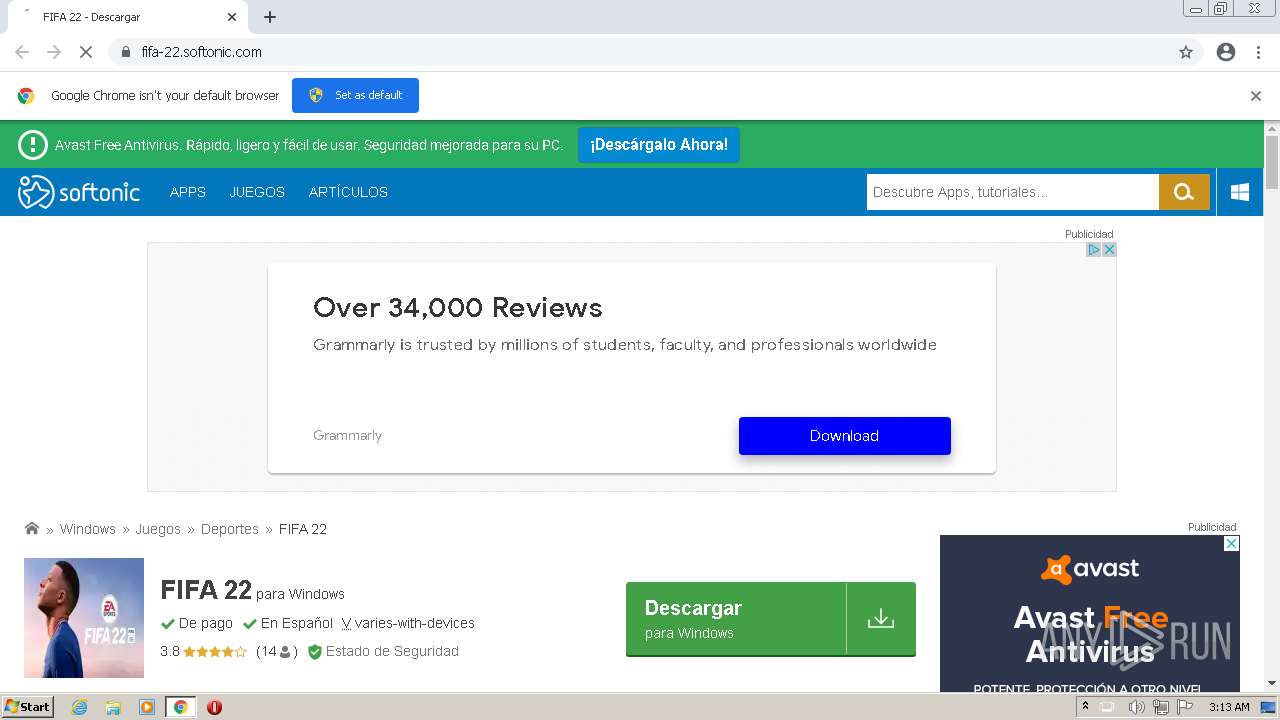
| URL: | https://fifa-22.softonic.com/ |
| Full analysis: | https://app.any.run/tasks/49ff9f7b-13c6-467f-aa56-c34ab382b653 |
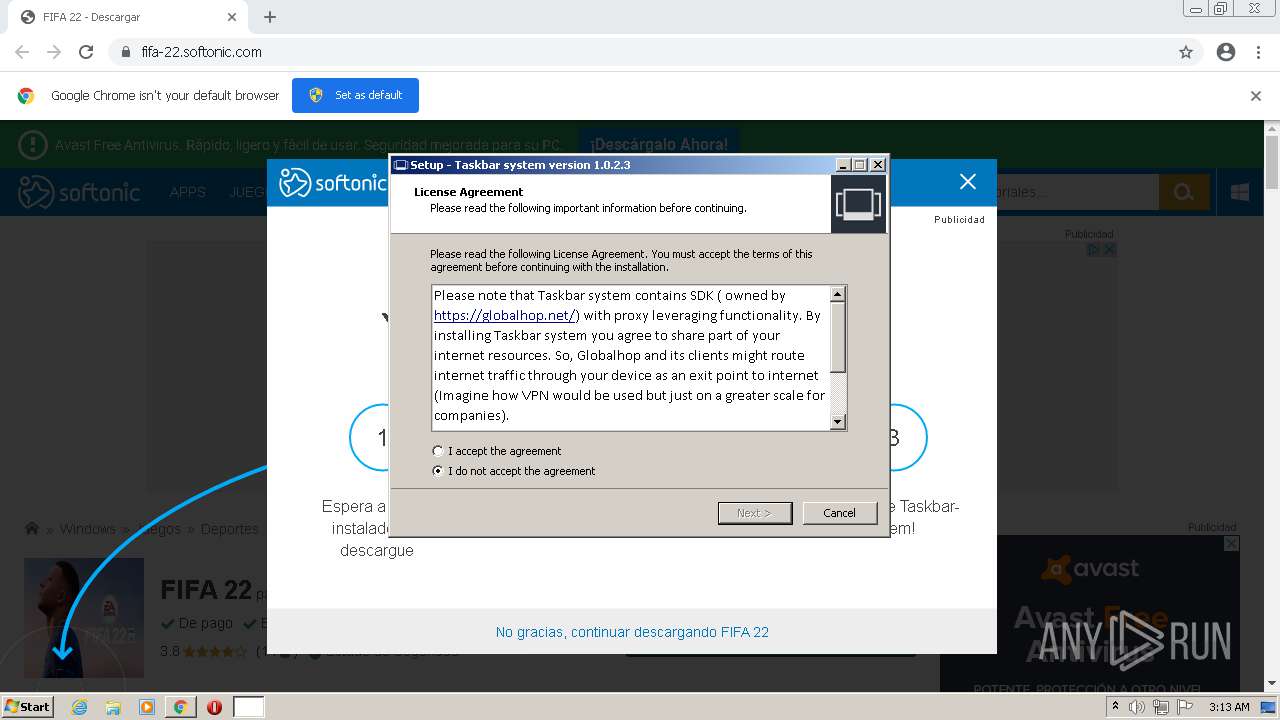
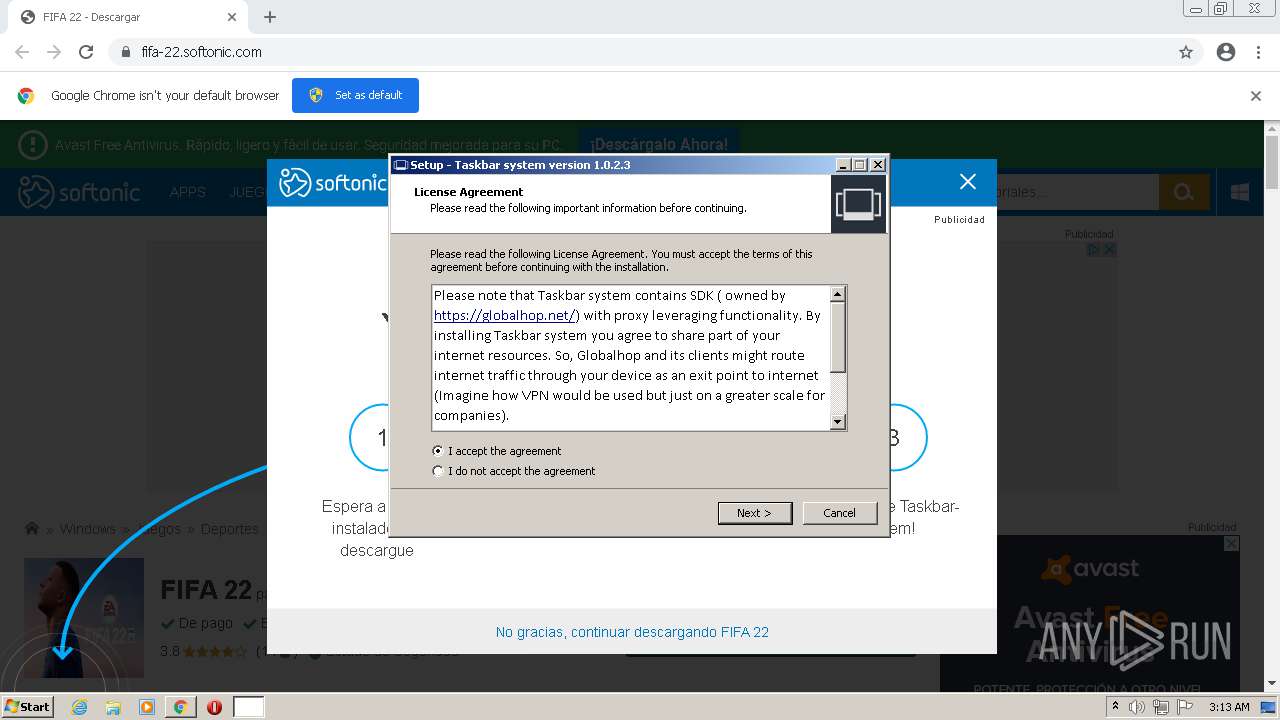
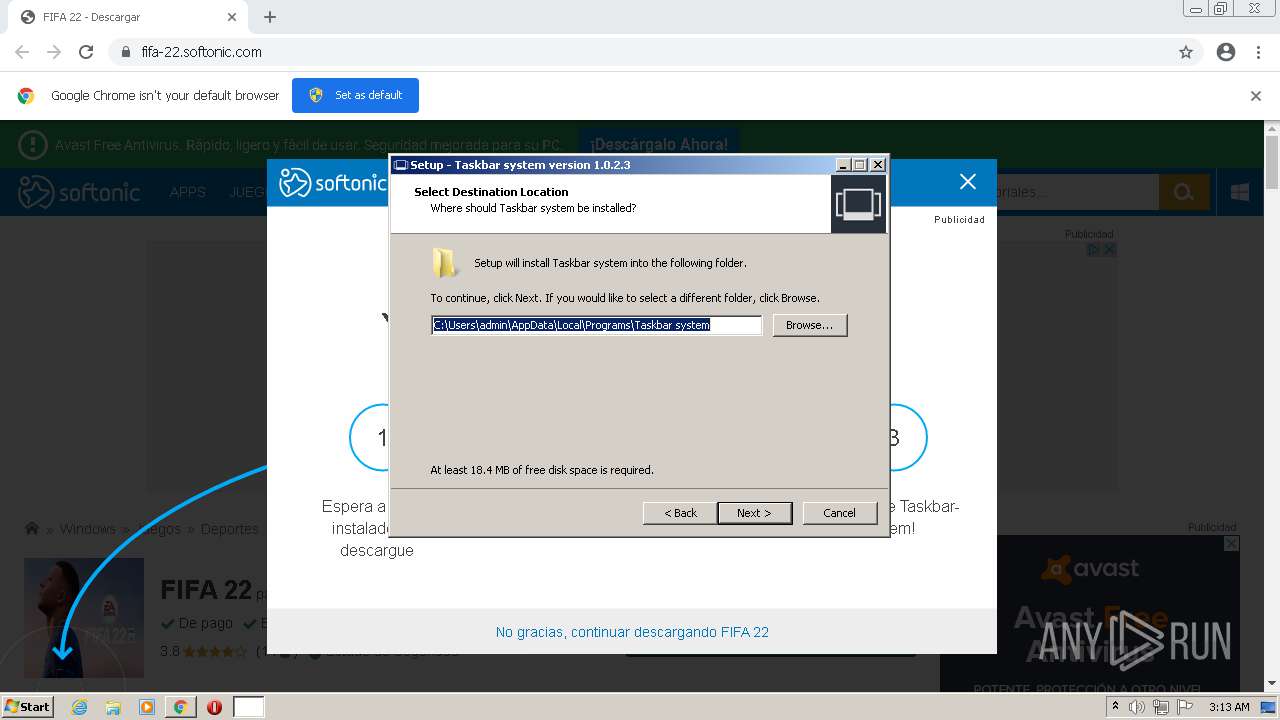
| Verdict: | Malicious activity |
| Analysis date: | July 30, 2021, 02:12:14 |
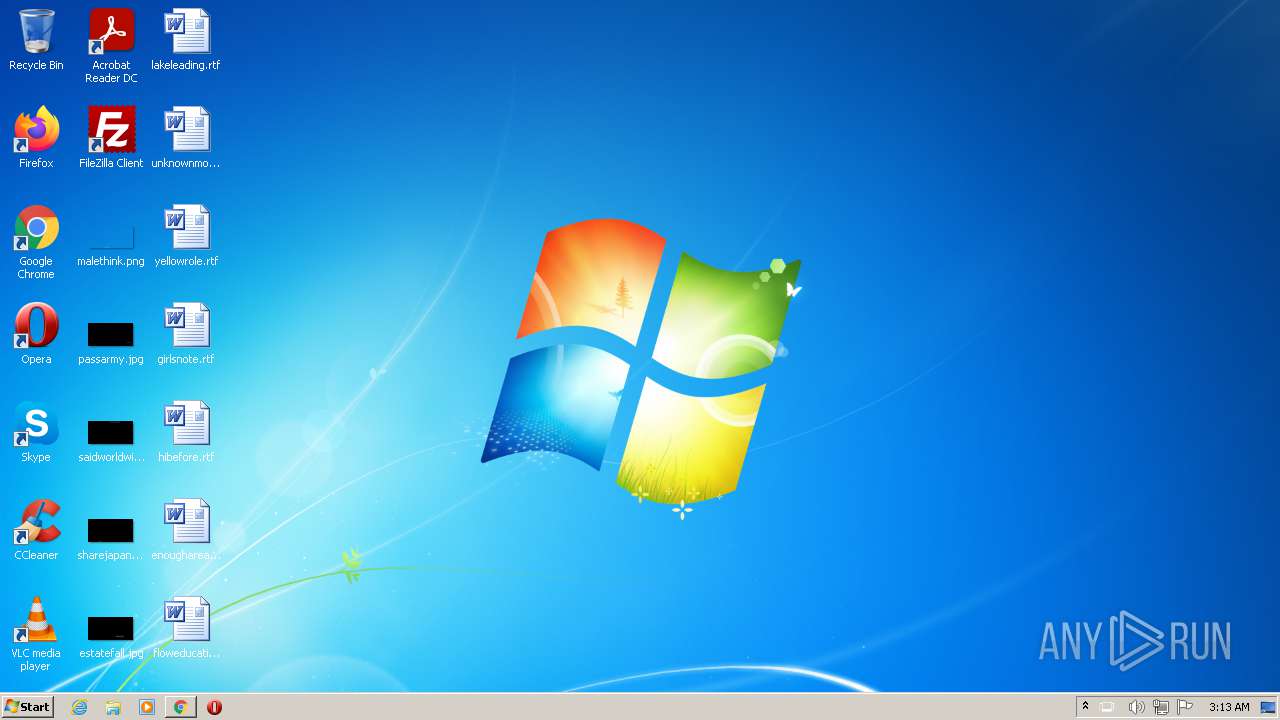
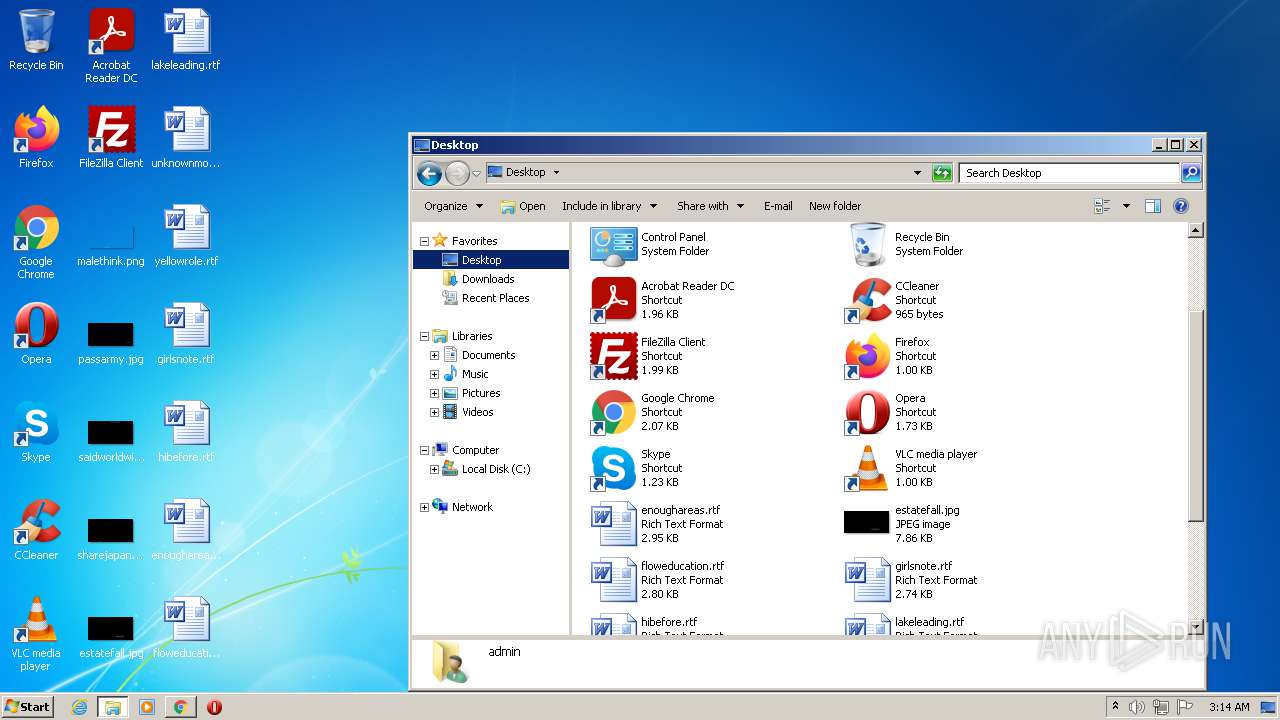
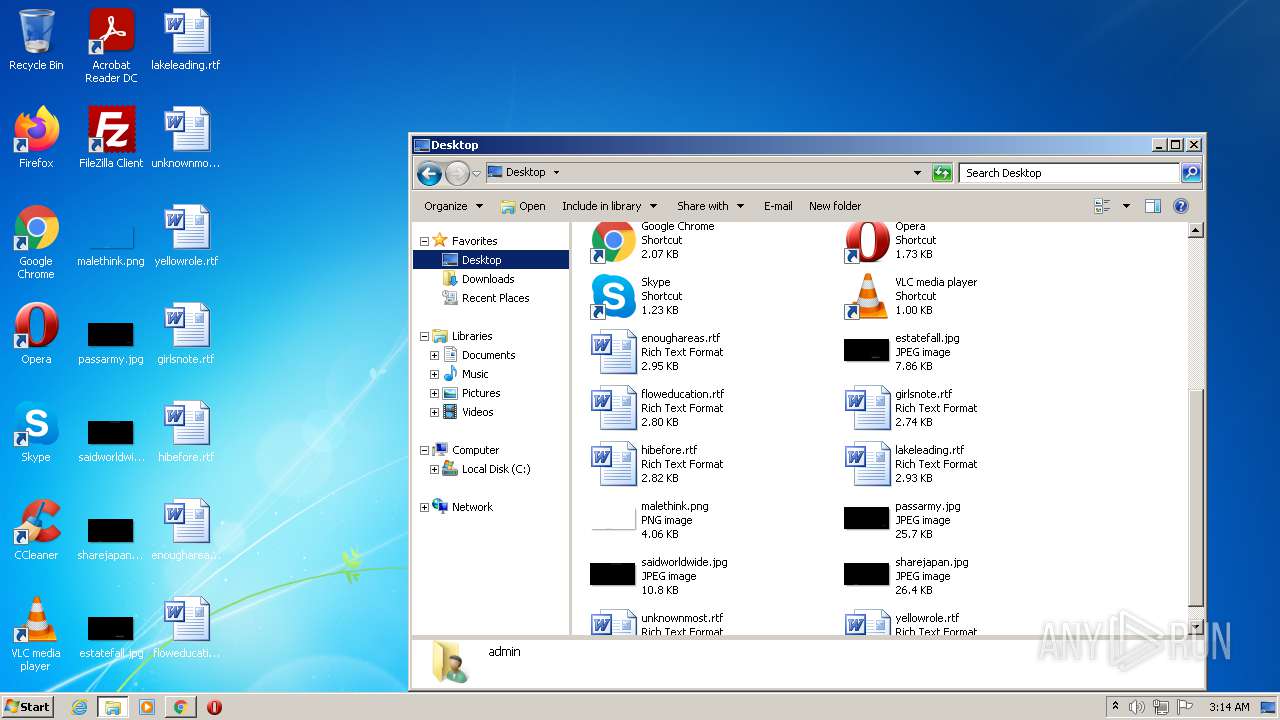
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 29196E28CD35393B87CD043B0AABEDB4 |
| SHA1: | 0D4E9990443B8CA124F9802C8BCA5E62EE38BD46 |
| SHA256: | E666A556A62AAFE9D4353E22E0E68E8BF4999383F1CD679D215CFB3FC83E4994 |
| SSDEEP: | 3:N8VIXyvHLGK3:20ELGK3 |
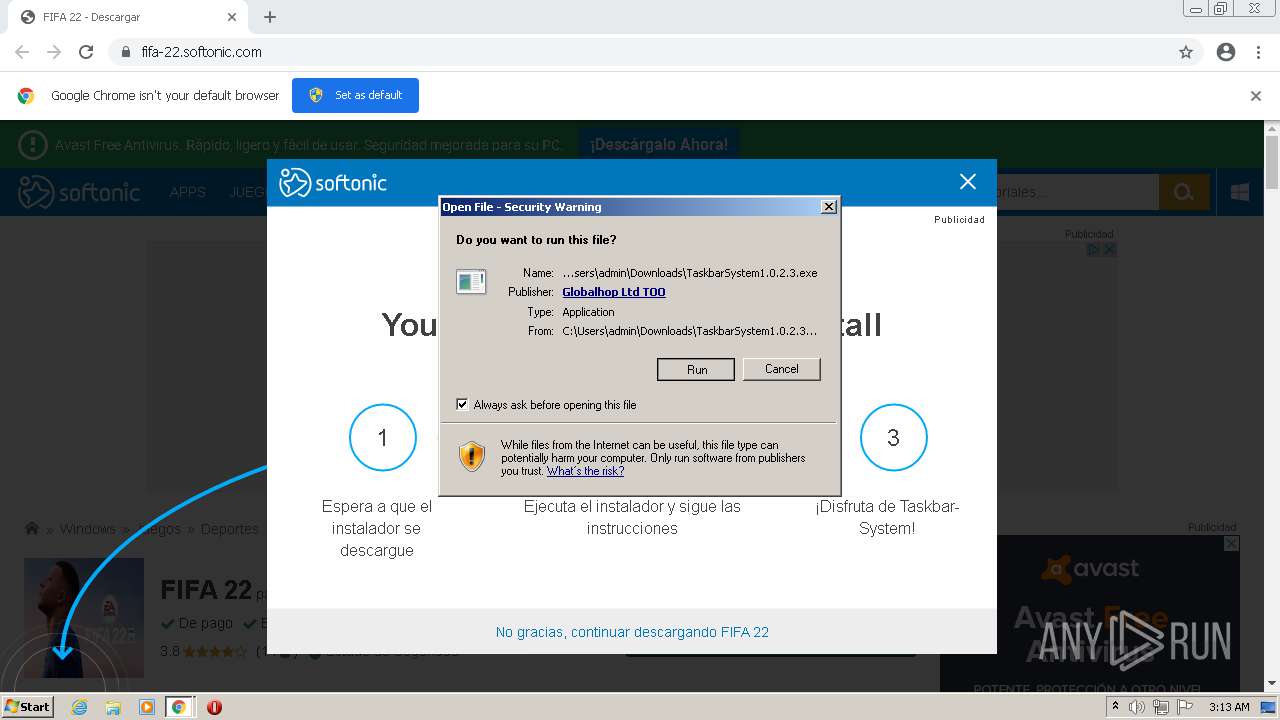
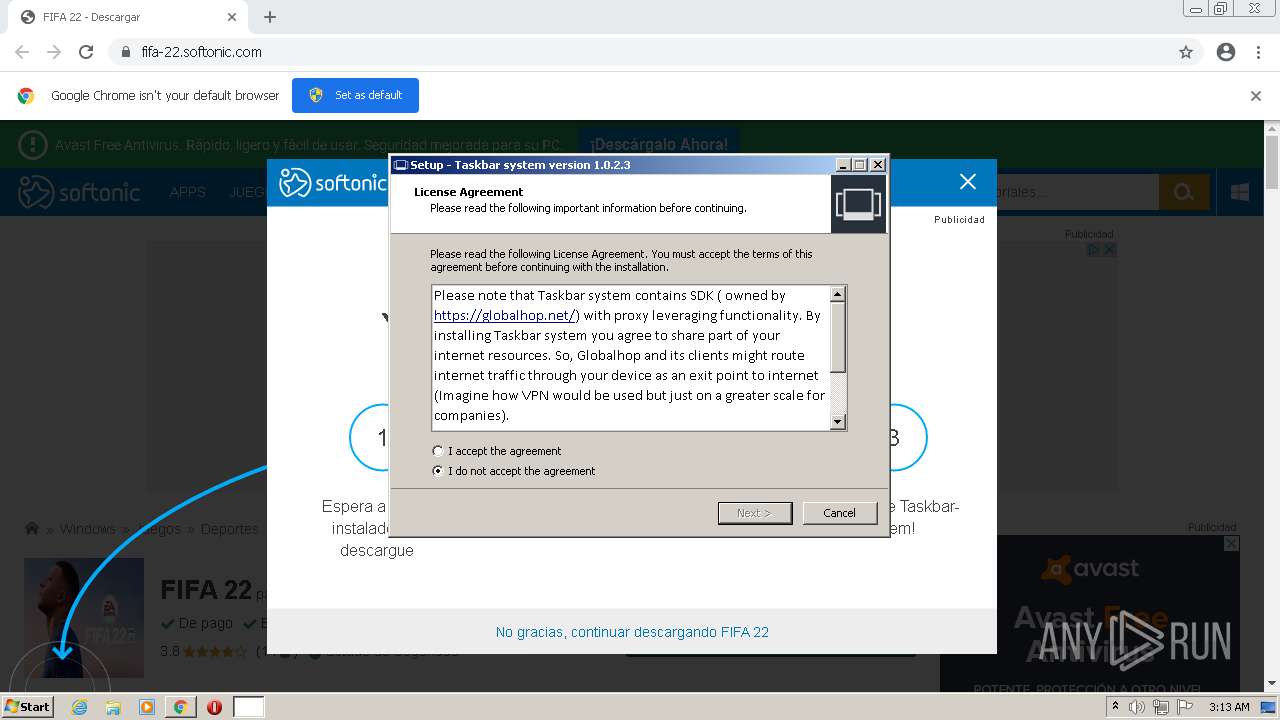
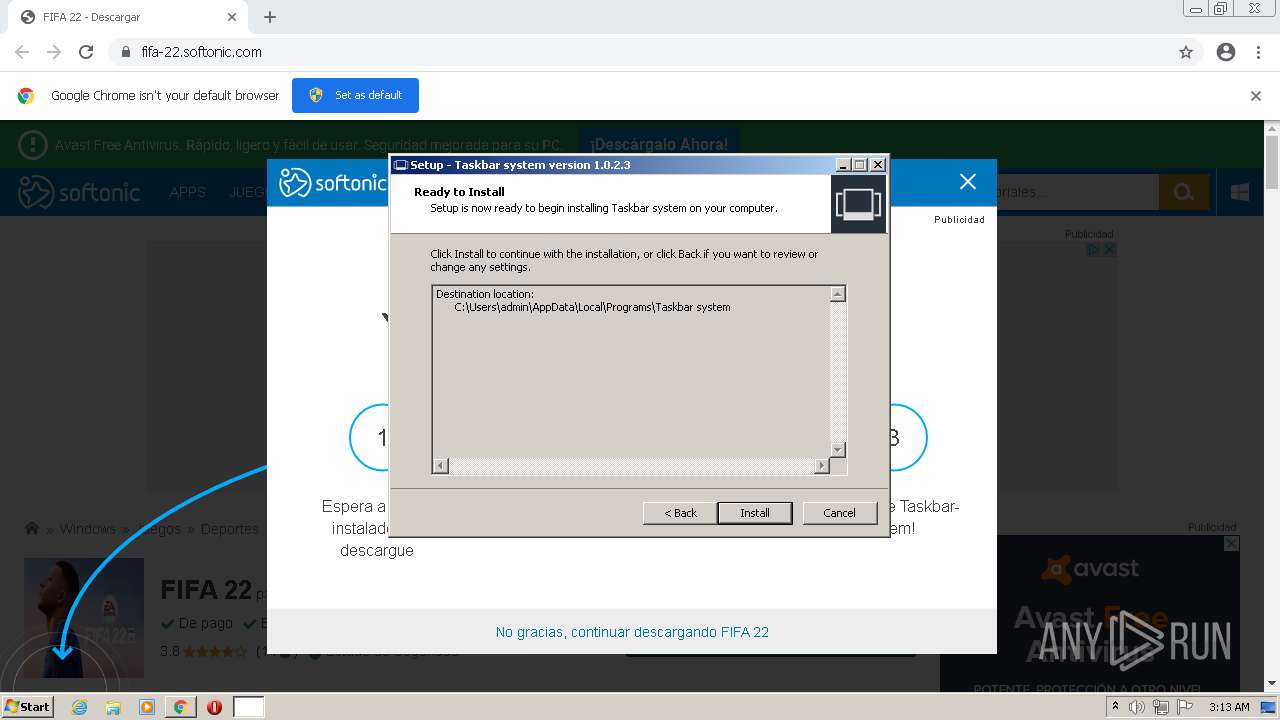
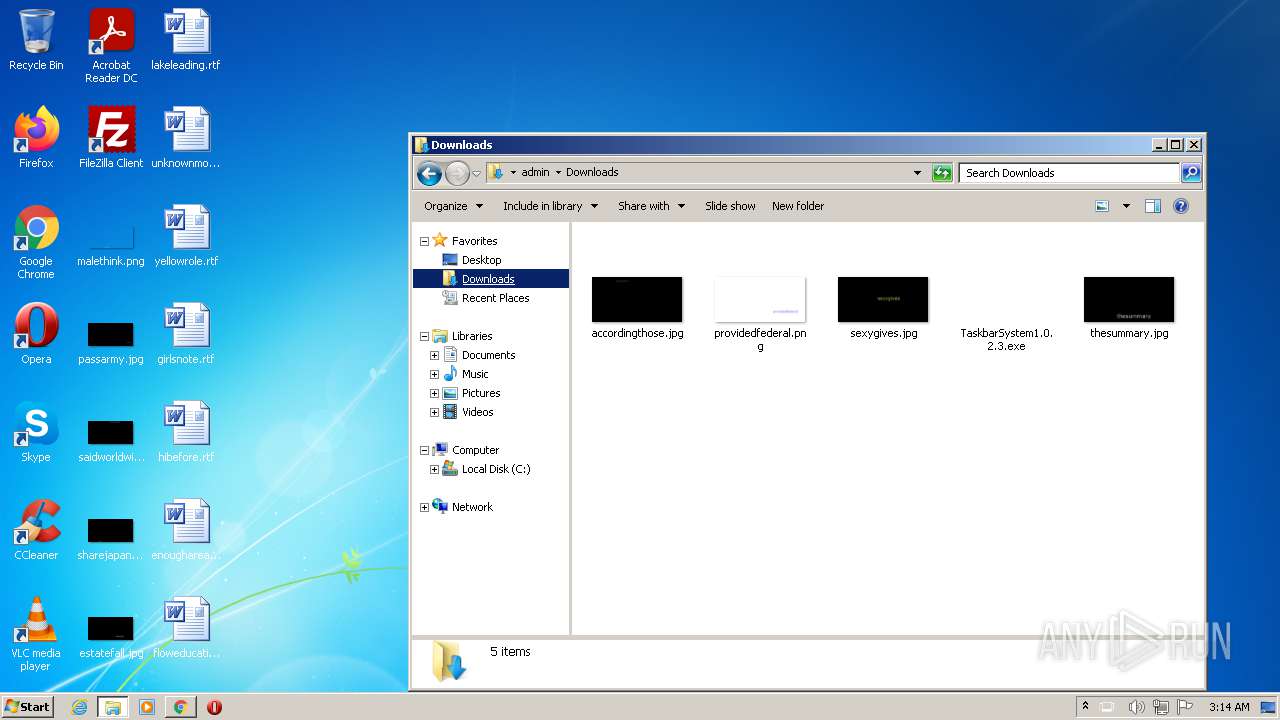
MALICIOUS
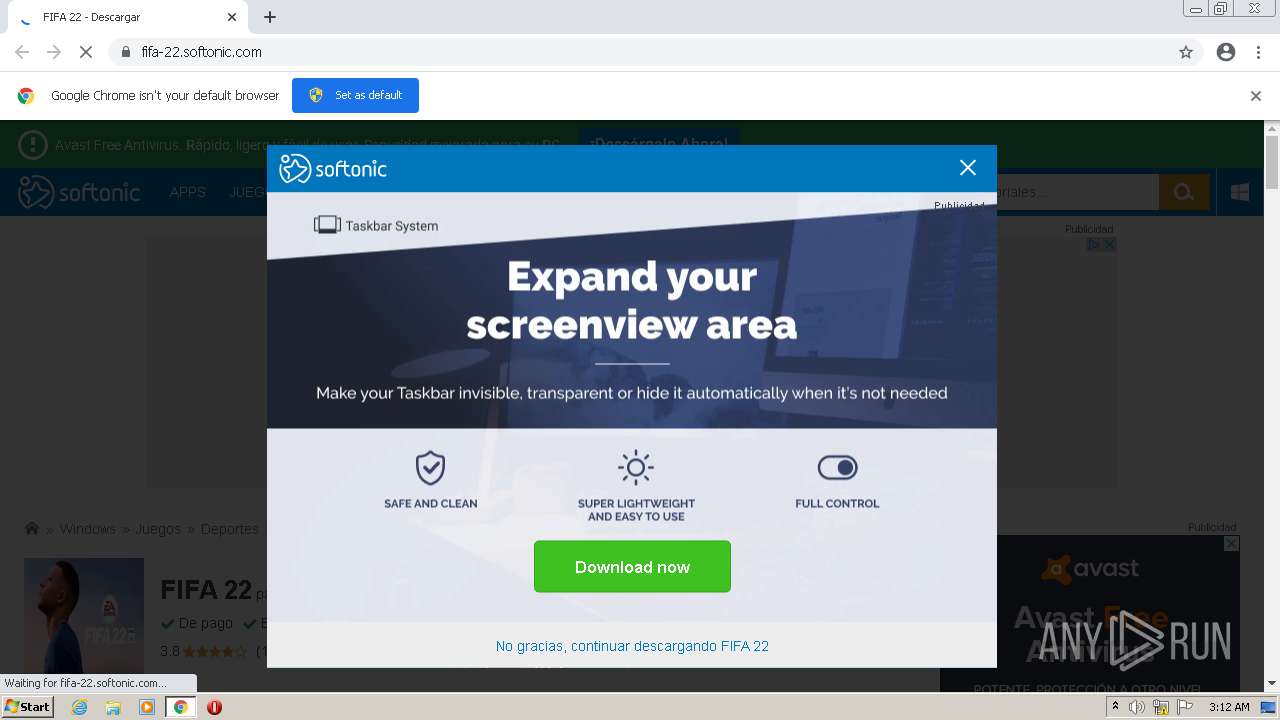
Application was dropped or rewritten from another process
- TaskbarSystem1.0.2.3.exe (PID: 1516)
- TaskbarSystem.exe (PID: 1584)
- TaskbarSystem.exe (PID: 2196)
- TaskbarSystem.exe (PID: 3444)
Drops executable file immediately after starts
- TaskbarSystem1.0.2.3.exe (PID: 1516)
- chrome.exe (PID: 2308)
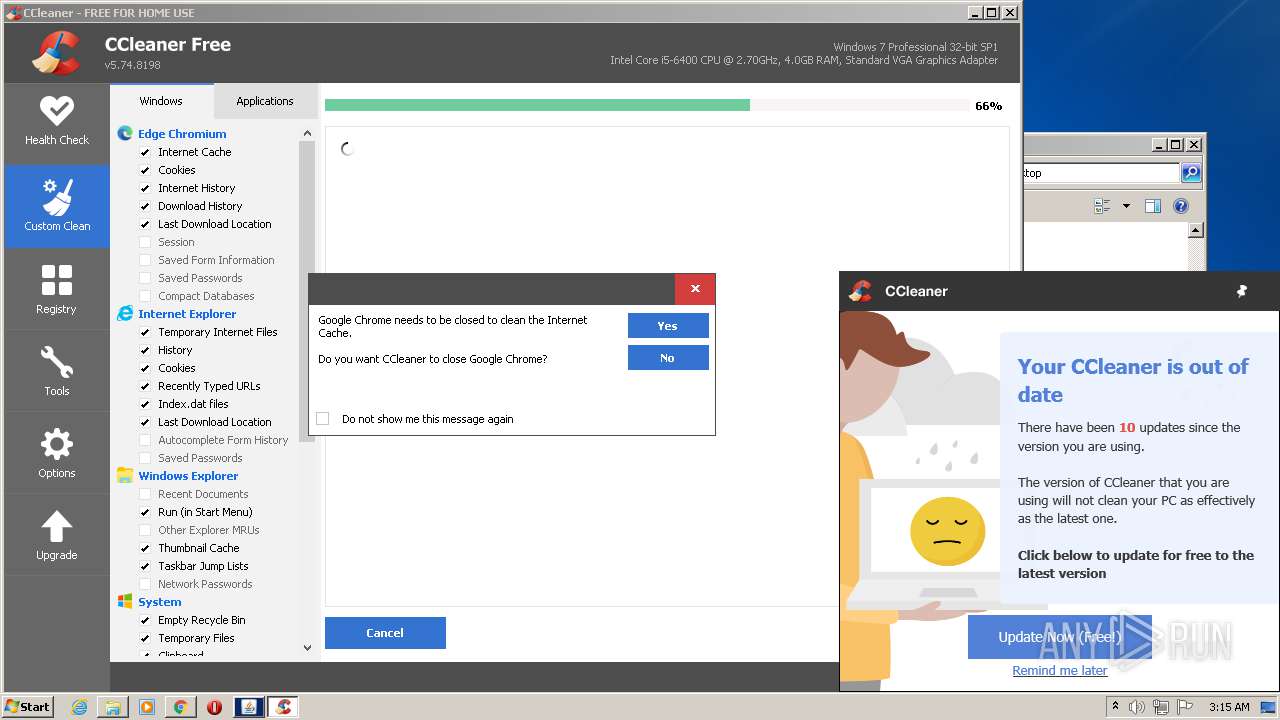
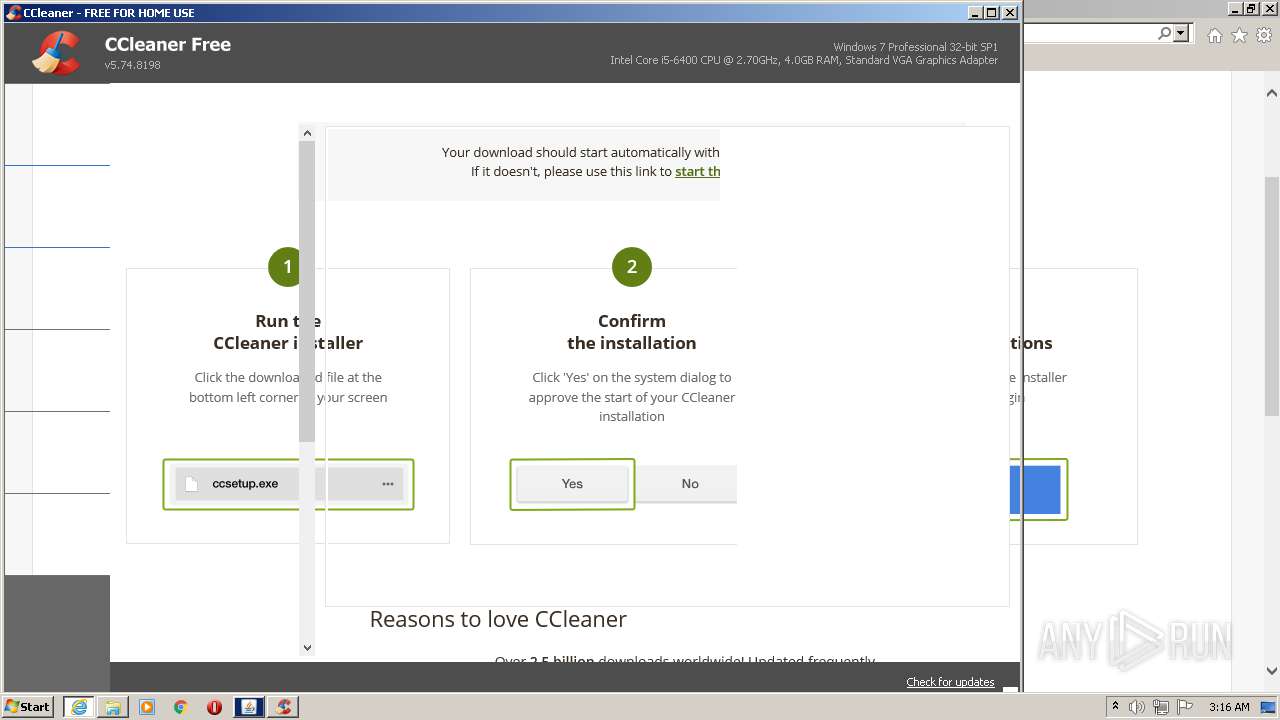
- CCleaner.exe (PID: 3064)
Changes the autorun value in the registry
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
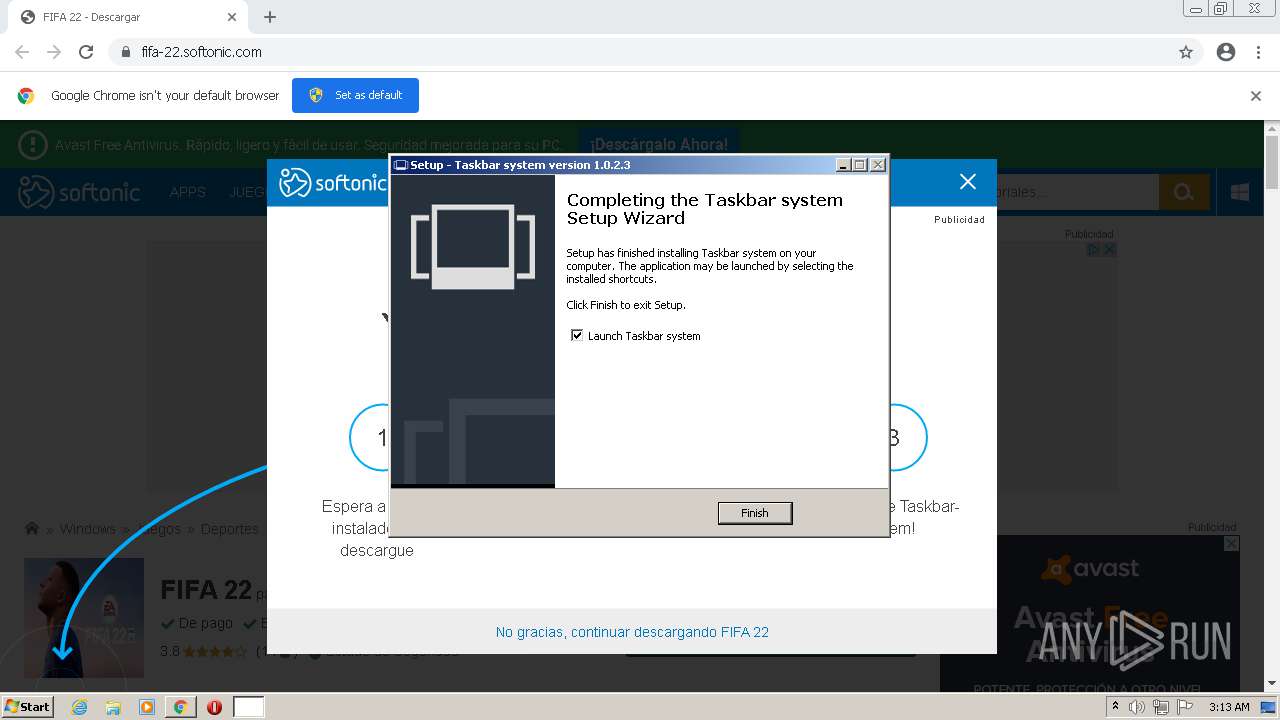
Loads dropped or rewritten executable
- TaskbarSystem.exe (PID: 1584)
- CCleaner.exe (PID: 3064)
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 2180)
- CCleaner.exe (PID: 3064)
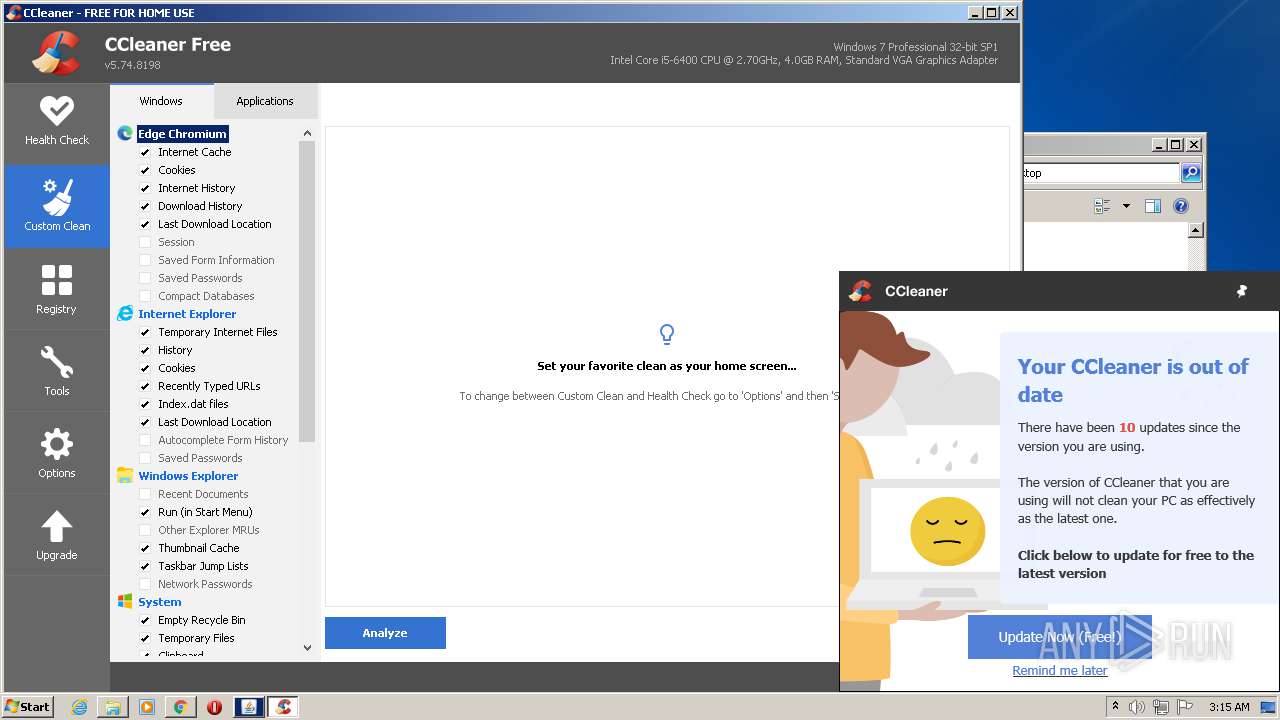
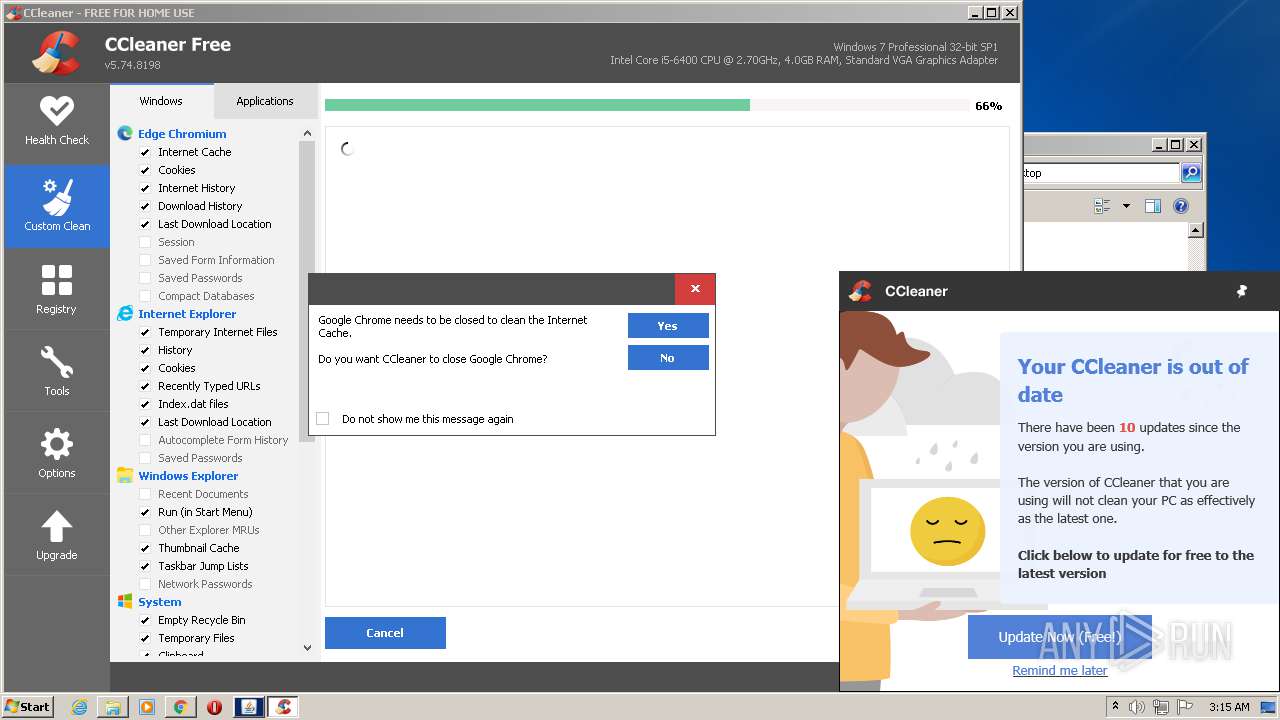
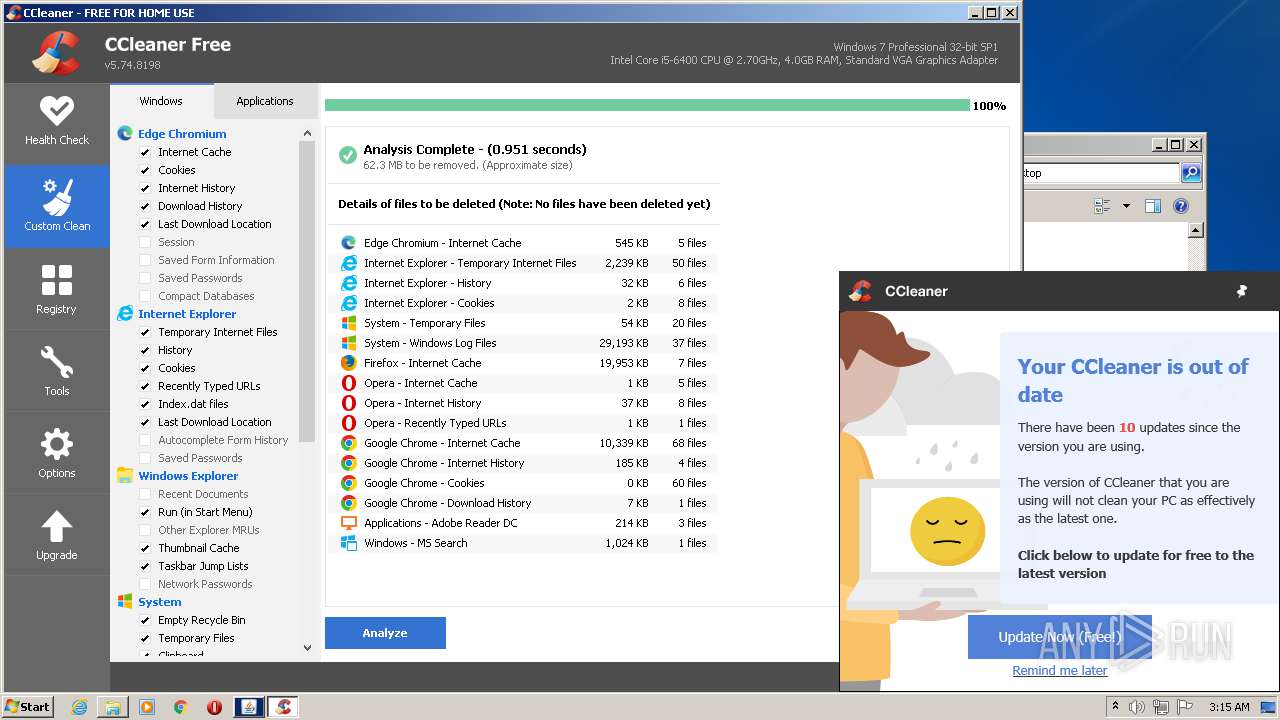
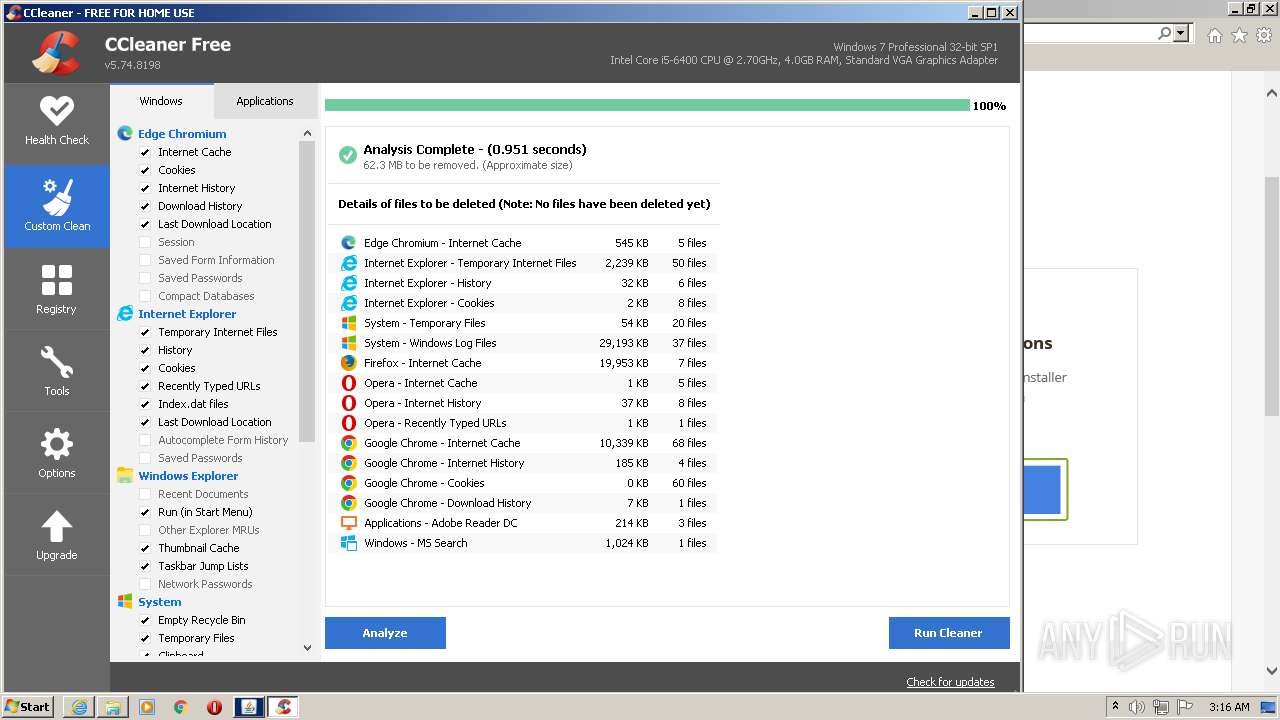
Steals credentials from Web Browsers
- CCleaner.exe (PID: 3064)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 3064)
Changes settings of System certificates
- CCleaner.exe (PID: 3064)
SUSPICIOUS
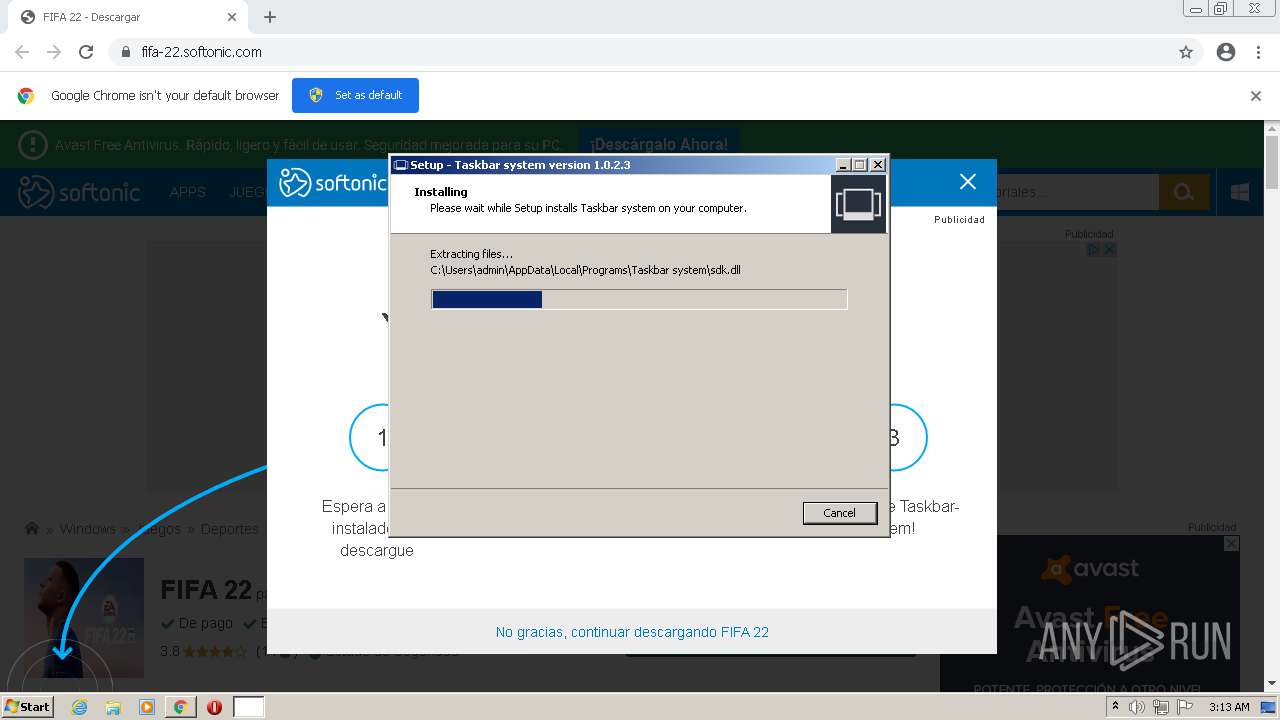
Executable content was dropped or overwritten
- chrome.exe (PID: 1412)
- TaskbarSystem1.0.2.3.exe (PID: 1516)
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- chrome.exe (PID: 2308)
- CCleaner.exe (PID: 3064)
Checks supported languages
- TaskbarSystem1.0.2.3.exe (PID: 1516)
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- TaskbarSystem.exe (PID: 1584)
- TaskbarSystem.exe (PID: 2196)
- javaw.exe (PID: 3896)
- jucheck.exe (PID: 3984)
- javacpl.exe (PID: 3888)
- jucheck.exe (PID: 3832)
- jucheck.exe (PID: 3872)
- javacpl.exe (PID: 2440)
- javaw.exe (PID: 3176)
- TaskbarSystem.exe (PID: 3444)
- CCleaner.exe (PID: 2180)
- jucheck.exe (PID: 948)
- CCleaner.exe (PID: 3064)
- jucheck.exe (PID: 952)
Reads the computer name
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- TaskbarSystem.exe (PID: 1584)
- TaskbarSystem.exe (PID: 2196)
- javaw.exe (PID: 3896)
- jucheck.exe (PID: 3984)
- jucheck.exe (PID: 3832)
- jucheck.exe (PID: 3872)
- TaskbarSystem.exe (PID: 3444)
- javaw.exe (PID: 3176)
- jucheck.exe (PID: 948)
- CCleaner.exe (PID: 2180)
- jucheck.exe (PID: 952)
- CCleaner.exe (PID: 3064)
Reads the Windows organization settings
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
Reads Windows owner or organization settings
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
Drops a file that was compiled in debug mode
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- chrome.exe (PID: 2308)
- CCleaner.exe (PID: 3064)
Drops a file with too old compile date
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
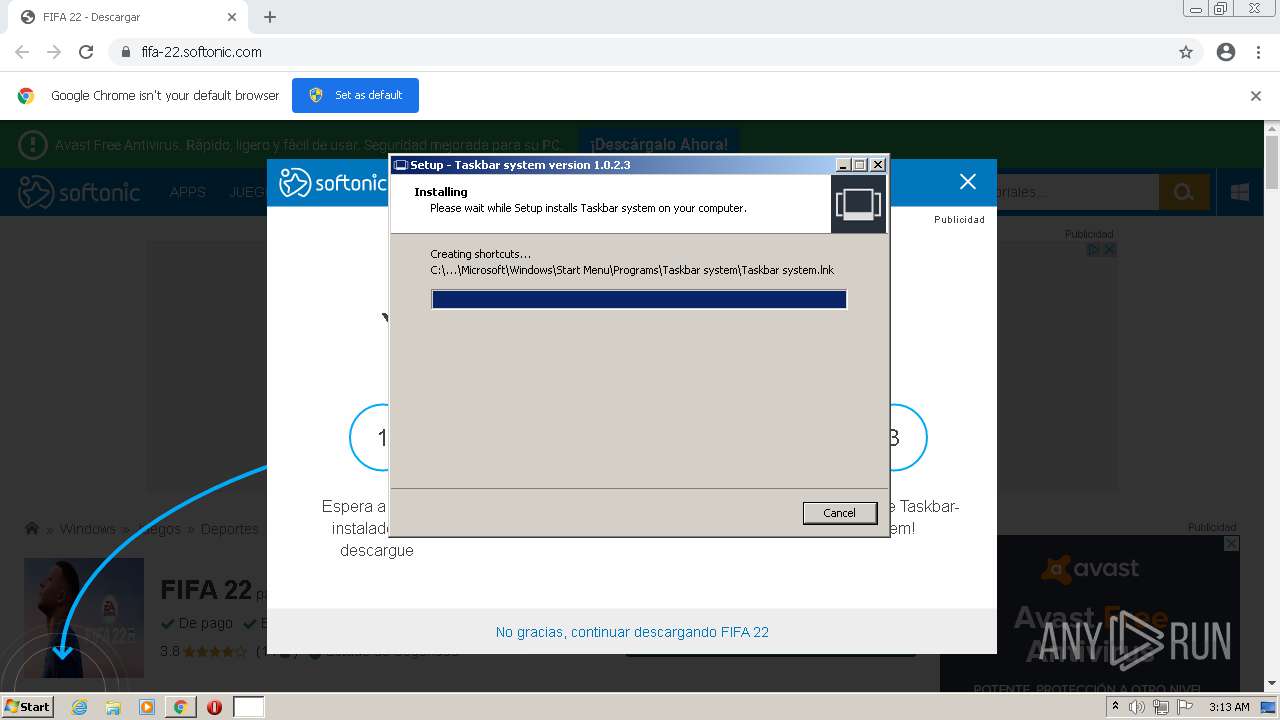
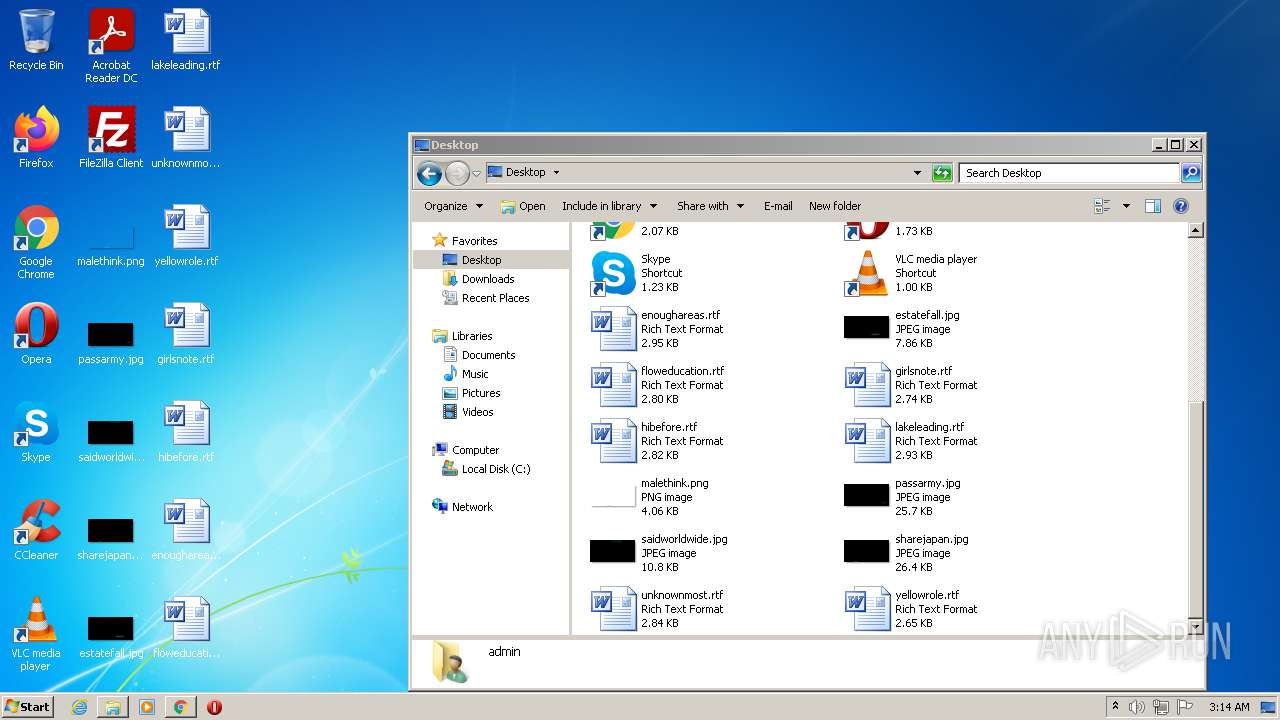
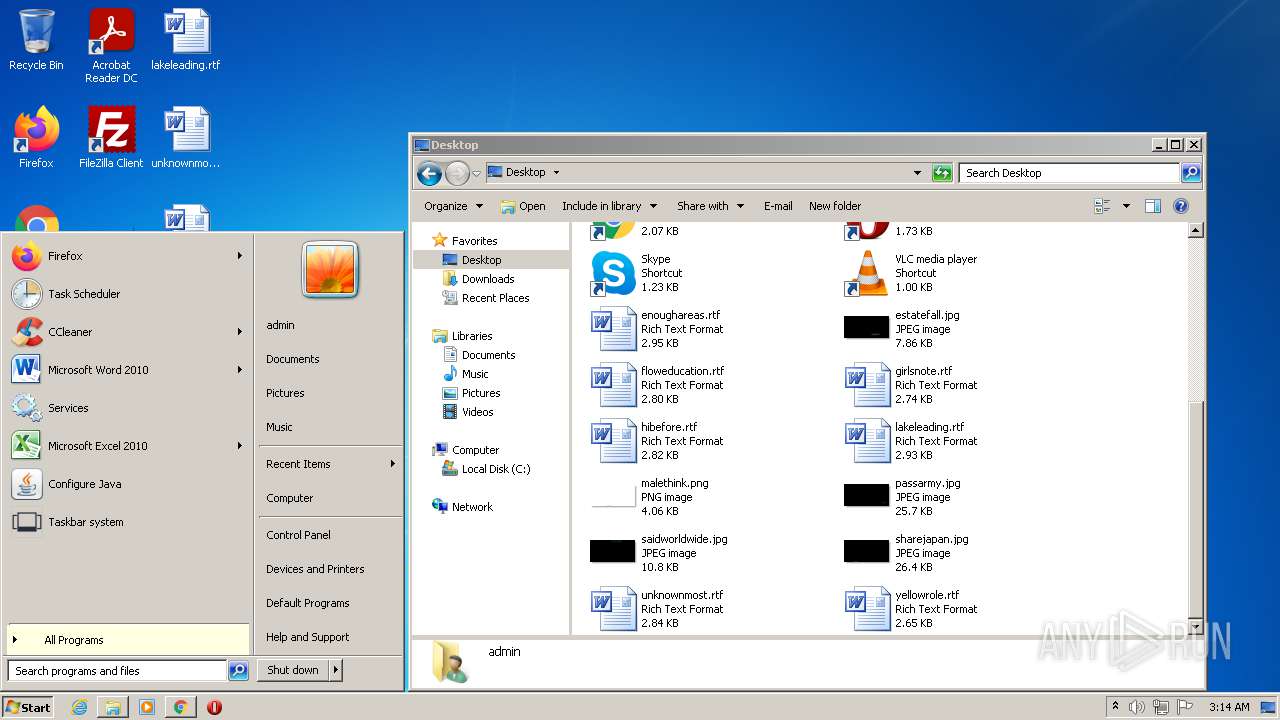
Creates files in the user directory
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- CCleaner.exe (PID: 3064)
Reads Environment values
- TaskbarSystem.exe (PID: 1584)
- CCleaner.exe (PID: 2180)
- CCleaner.exe (PID: 3064)
Reads Microsoft Outlook installation path
- TaskbarSystem.exe (PID: 1584)
- CCleaner.exe (PID: 3064)
- iexplore.exe (PID: 3712)
Reads internet explorer settings
- TaskbarSystem.exe (PID: 1584)
- CCleaner.exe (PID: 3064)
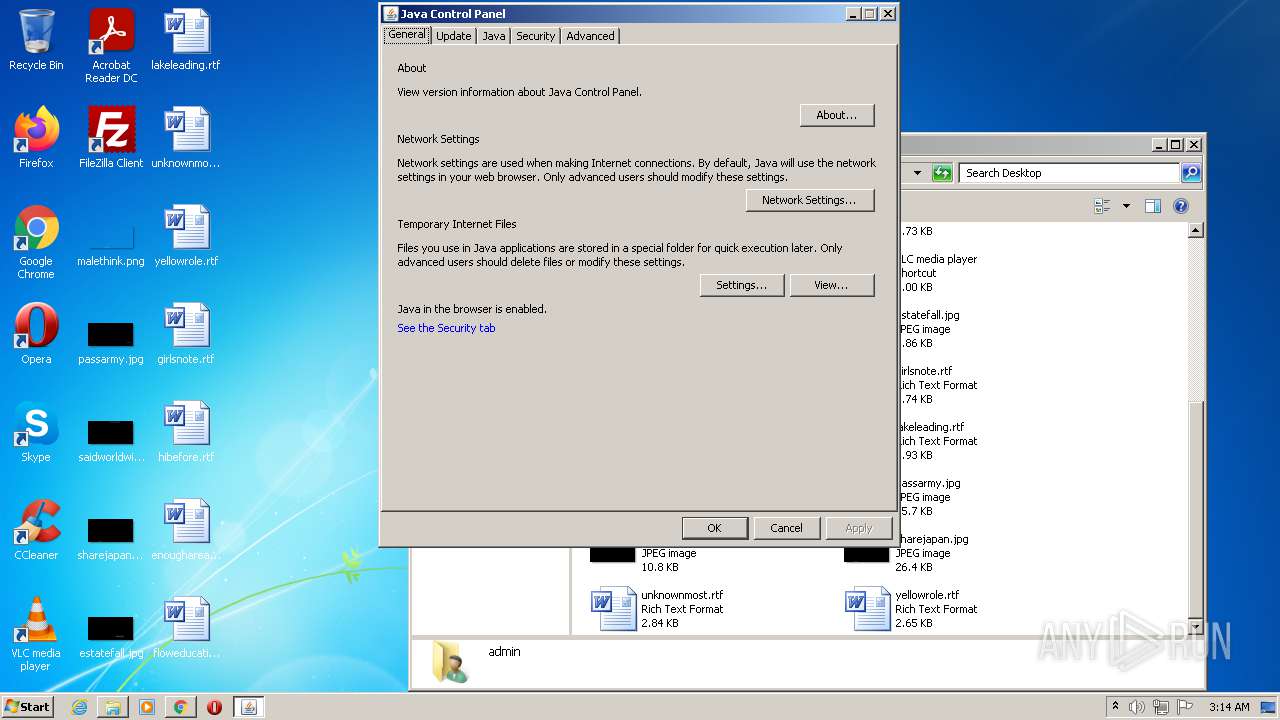
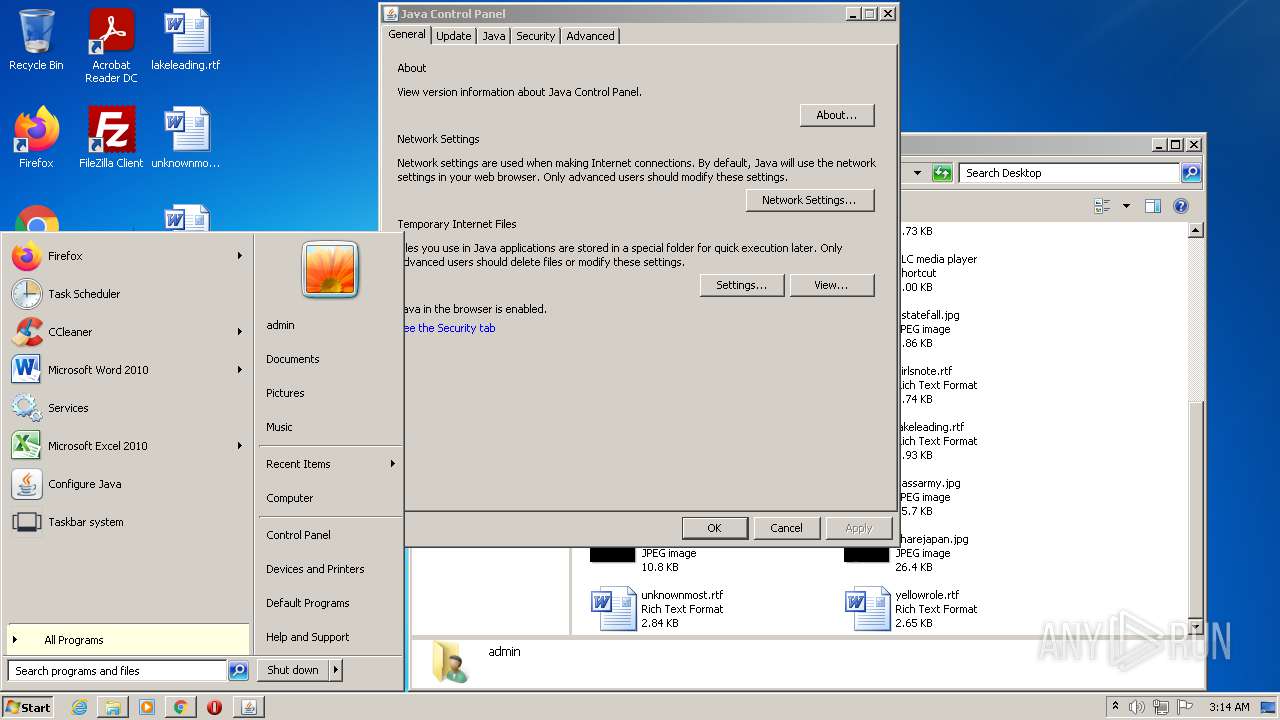
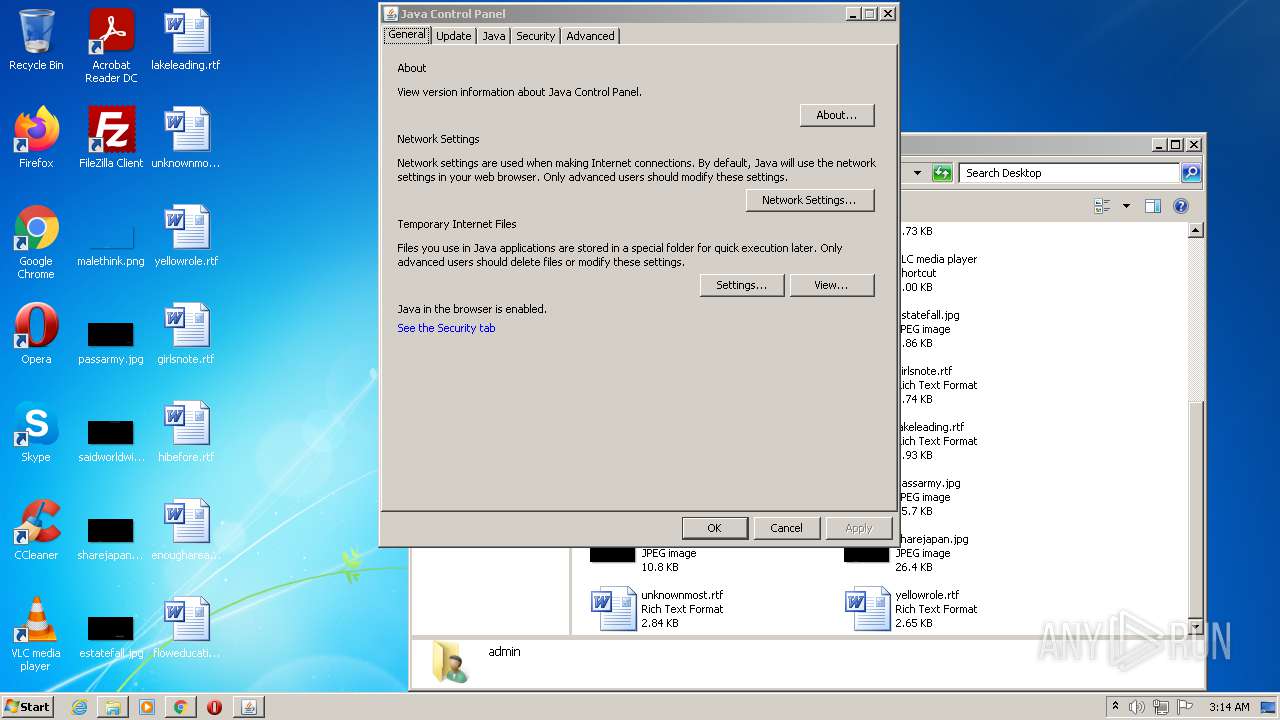
Check for Java to be installed
- javaw.exe (PID: 3896)
- jucheck.exe (PID: 3832)
- jucheck.exe (PID: 3984)
- jucheck.exe (PID: 3872)
- javaw.exe (PID: 3176)
- jucheck.exe (PID: 948)
- jucheck.exe (PID: 952)
Executes JAVA applets
- javacpl.exe (PID: 3888)
- javacpl.exe (PID: 2440)
Executed via COM
- DllHost.exe (PID: 4092)
Executed via Task Scheduler
- CCleaner.exe (PID: 3064)
Creates files in the program directory
- CCleaner.exe (PID: 3064)
Reads CPU info
- CCleaner.exe (PID: 3064)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 3064)
Reads the date of Windows installation
- CCleaner.exe (PID: 3064)
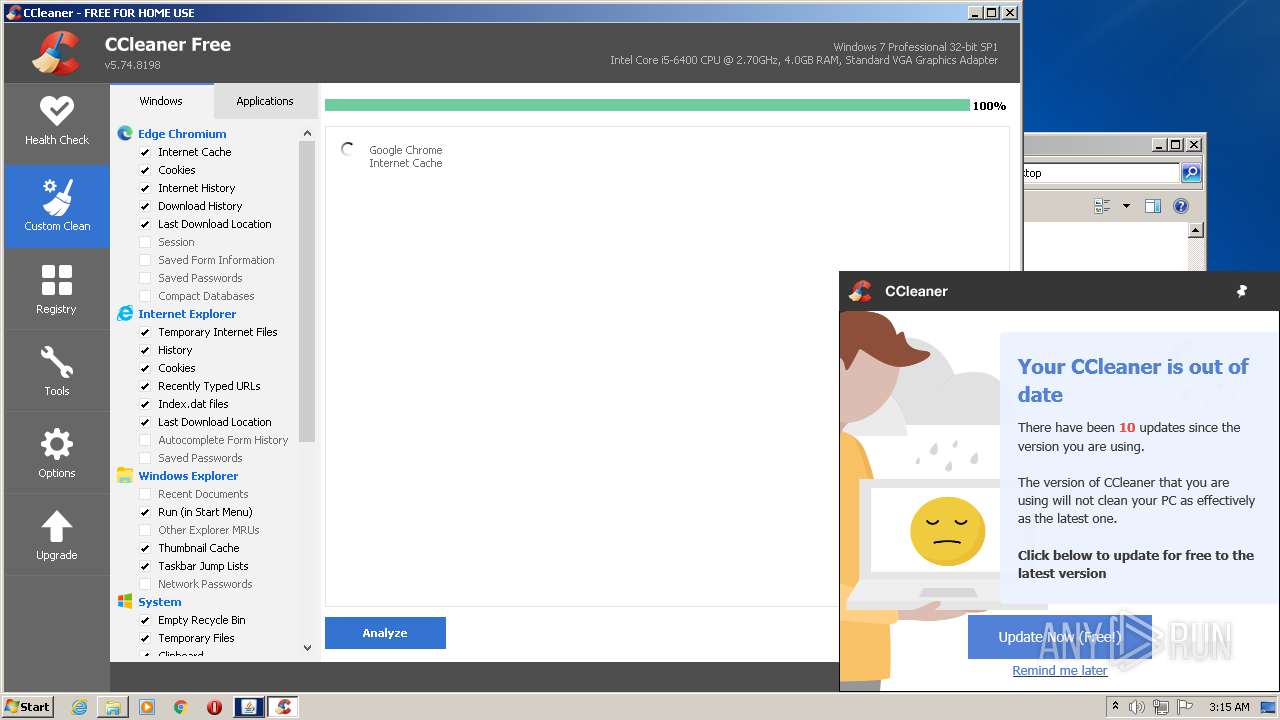
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 3064)
Executed as Windows Service
- taskhost.exe (PID: 2836)
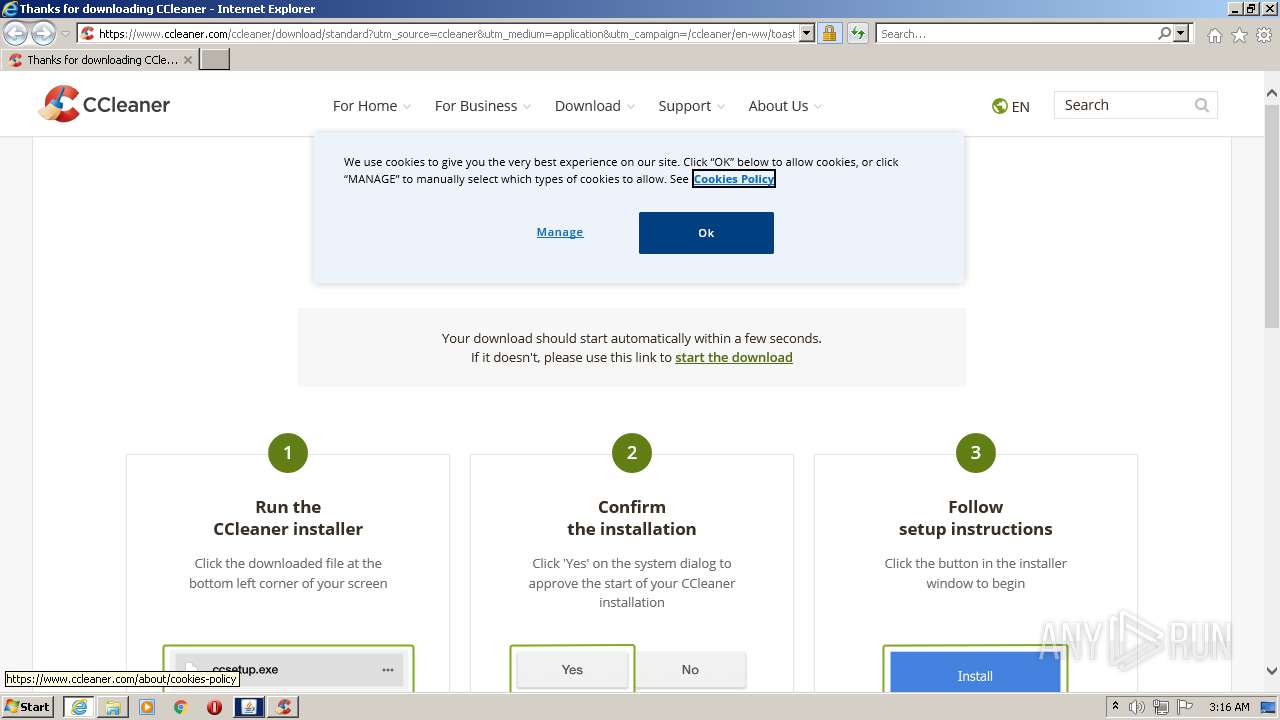
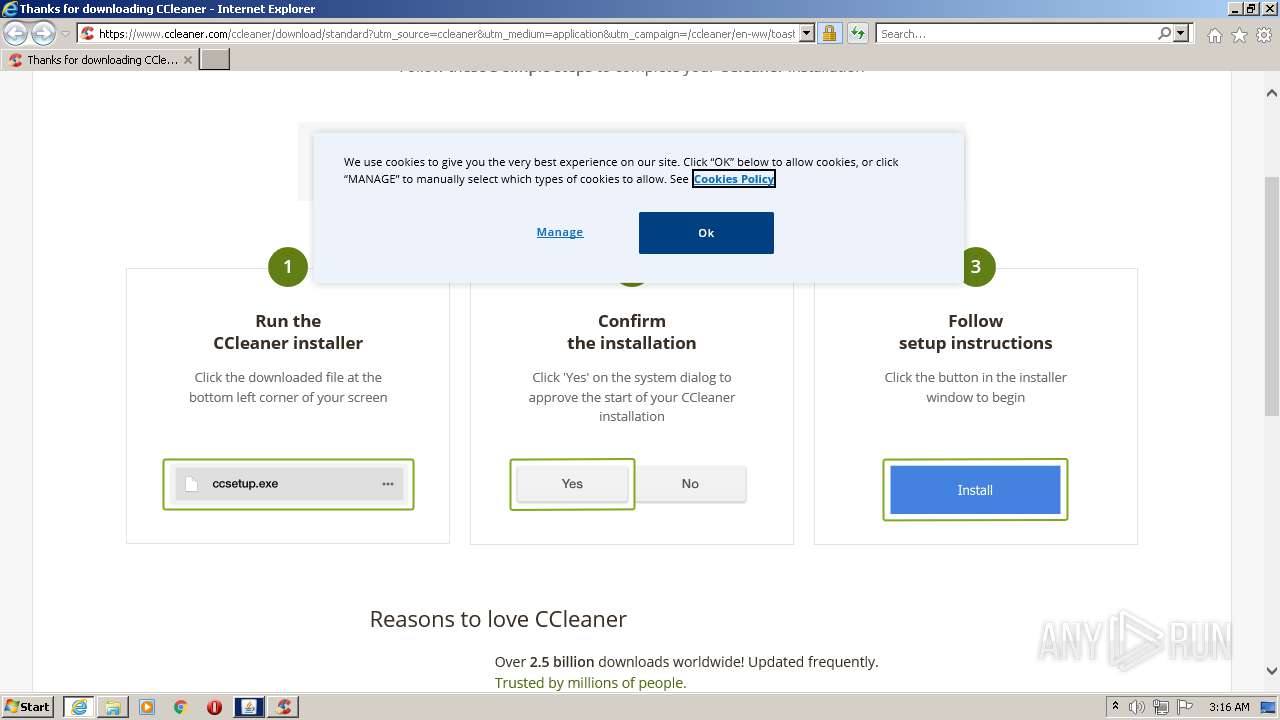
Starts Internet Explorer
- CCleaner.exe (PID: 3064)
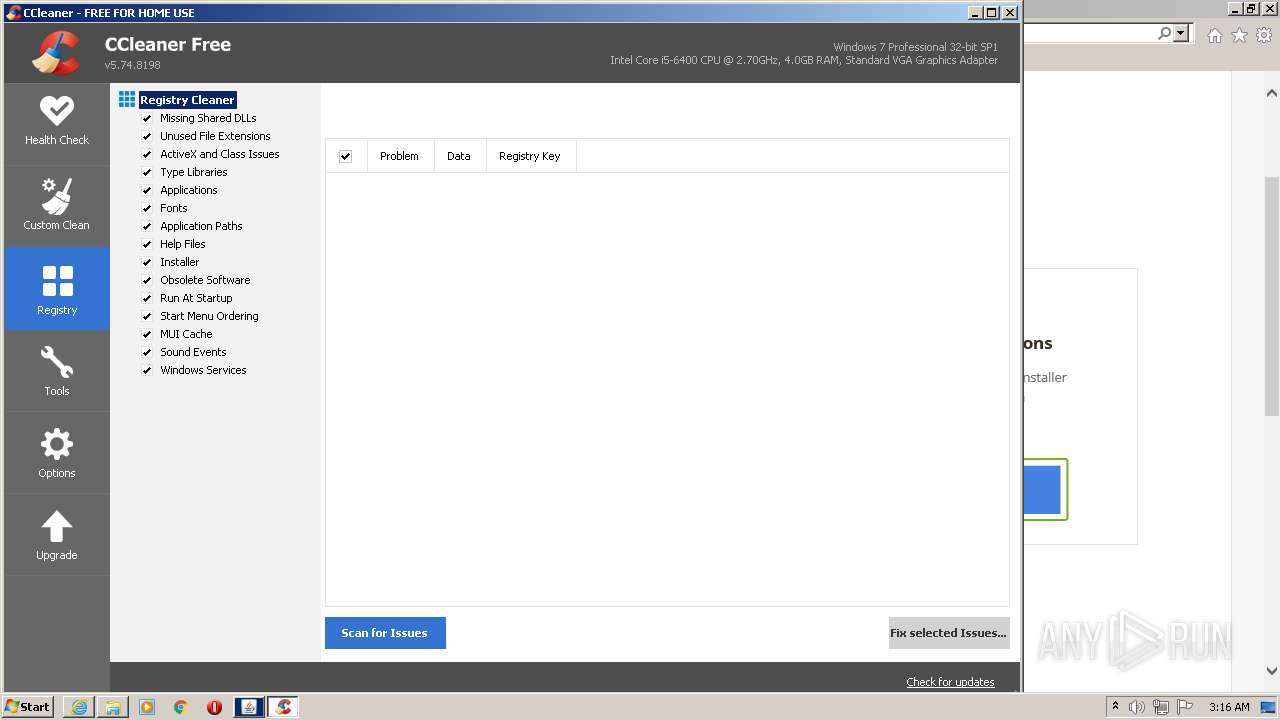
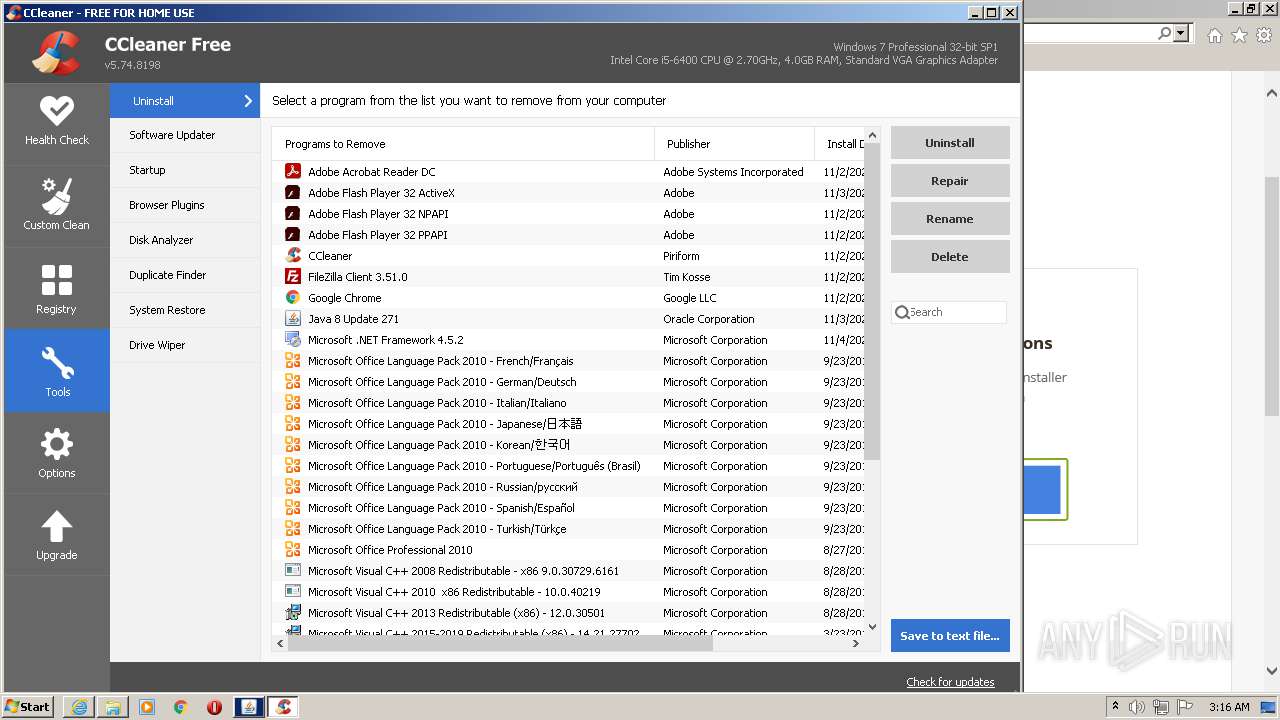
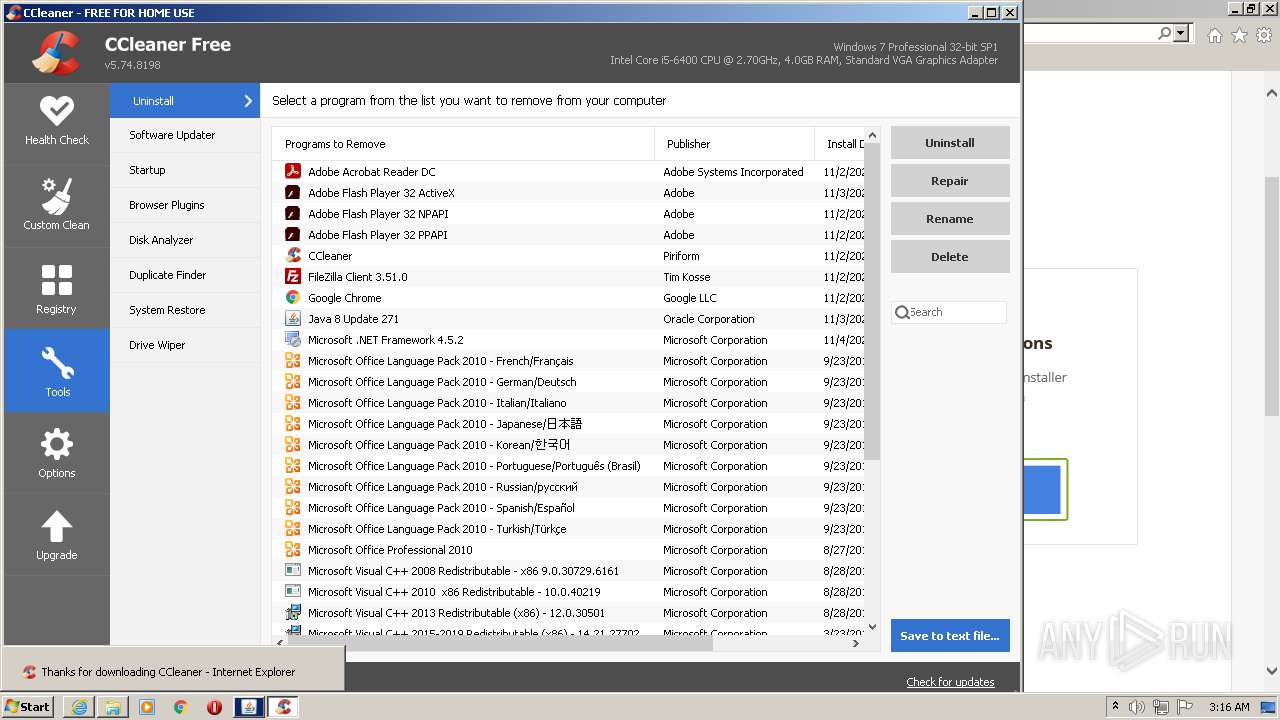
Searches for installed software
- CCleaner.exe (PID: 3064)
INFO
Checks supported languages
- chrome.exe (PID: 1412)
- chrome.exe (PID: 760)
- chrome.exe (PID: 556)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3500)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1428)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 836)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 316)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 376)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 2016)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 3380)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 552)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 2756)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 280)
- chrome.exe (PID: 3344)
- explorer.exe (PID: 2248)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 3368)
- DllHost.exe (PID: 4092)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3772)
- taskhost.exe (PID: 2836)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3168)
- chrome.exe (PID: 3632)
- chrome.exe (PID: 3508)
- iexplore.exe (PID: 2508)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2368)
- iexplore.exe (PID: 3712)
Application launched itself
- chrome.exe (PID: 1412)
- iexplore.exe (PID: 2508)
Reads the hosts file
- chrome.exe (PID: 1412)
- chrome.exe (PID: 760)
- CCleaner.exe (PID: 3064)
Reads the computer name
- chrome.exe (PID: 1412)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 760)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2240)
- explorer.exe (PID: 2248)
- DllHost.exe (PID: 4092)
- taskhost.exe (PID: 2836)
- iexplore.exe (PID: 2508)
- iexplore.exe (PID: 3712)
Reads settings of System Certificates
- chrome.exe (PID: 760)
- chrome.exe (PID: 1412)
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
- TaskbarSystem.exe (PID: 1584)
- TaskbarSystem.exe (PID: 3444)
- TaskbarSystem.exe (PID: 2196)
- CCleaner.exe (PID: 3064)
- javaw.exe (PID: 3176)
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2508)
Checks Windows Trust Settings
- chrome.exe (PID: 1412)
- TaskbarSystem.exe (PID: 2196)
- TaskbarSystem.exe (PID: 1584)
- TaskbarSystem.exe (PID: 3444)
- CCleaner.exe (PID: 3064)
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2508)
Application was dropped or rewritten from another process
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
Creates a software uninstall entry
- TaskbarSystem1.0.2.3.tmp (PID: 2976)
Reads the date of Windows installation
- chrome.exe (PID: 2532)
Changes settings of System certificates
- chrome.exe (PID: 760)
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2508)
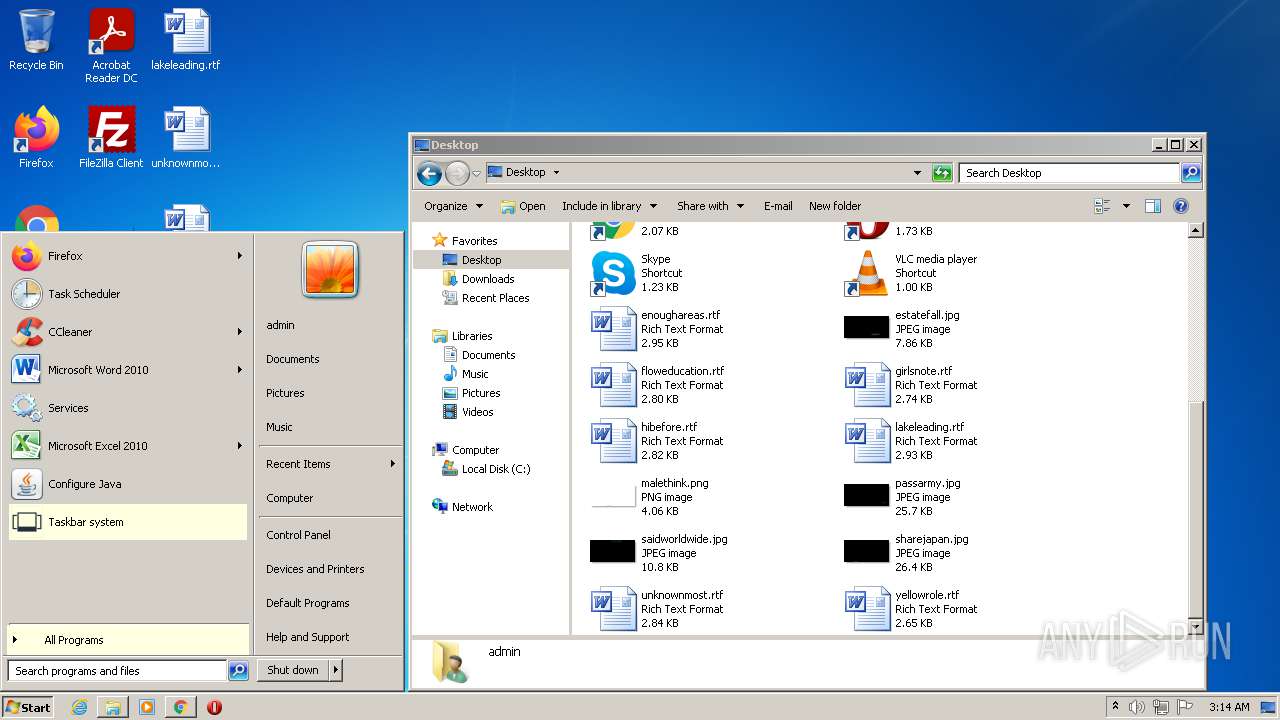
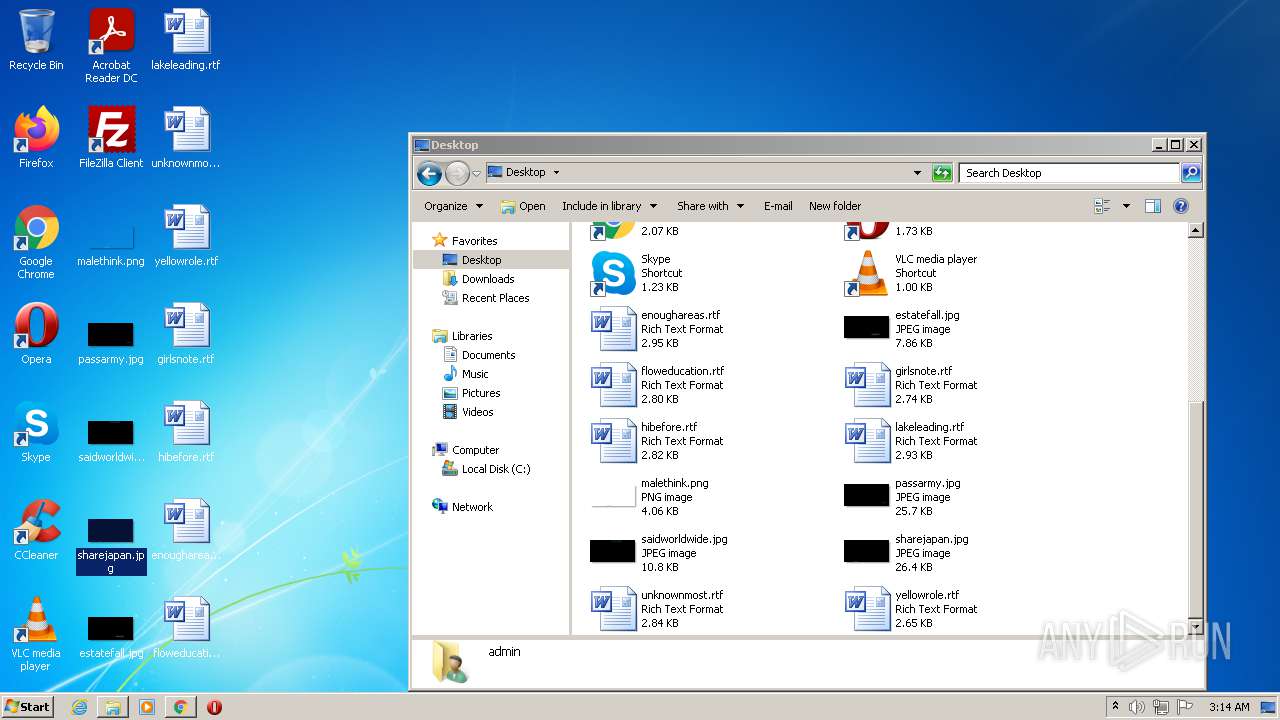
Manual execution by user
- TaskbarSystem.exe (PID: 2196)
- explorer.exe (PID: 2248)
- javacpl.exe (PID: 3888)
- TaskbarSystem.exe (PID: 3444)
- javacpl.exe (PID: 2440)
- CCleaner.exe (PID: 2180)
Changes internet zones settings
- iexplore.exe (PID: 2508)
Reads internet explorer settings
- iexplore.exe (PID: 3712)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2508)
Creates files in the user directory
- iexplore.exe (PID: 3712)
- iexplore.exe (PID: 2508)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
127
Monitored processes
80
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=7716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Common Files\Java\Java Update\jucheck.exe" -getconfig=1 | C:\Program Files\Common Files\Java\Java Update\jucheck.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.271.9 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Common Files\Java\Java Update\jucheck.exe" -setconfig=enabledUser:0;frequency:weekly;day:7;hour:22;notifyType:beforeDownload | C:\Program Files\Common Files\Java\Java Update\jucheck.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java Update Checker Exit code: 0 Version: 2.8.271.9 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,14470173189784511576,10612256954406766559,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=7704 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
90 855
Read events
90 096
Write events
704
Delete events
55
Modification events
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
23
Suspicious files
85
Text files
313
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61036010-584.pma | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a2412670-3ead-4763-910b-be82e9c7303c.tmp | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFac15b.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFac17a.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
379
DNS requests
219
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | — | — | whitelisted |
760 | chrome.exe | GET | 200 | 2.16.186.25:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8574cb02e76fb224 | unknown | compressed | 59.5 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 511 b | whitelisted |
— | — | GET | 206 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.45.13&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1627610657&mv=m&mvi=1&pl=24&rmhost=r4---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 5.76 Kb | whitelisted |
— | — | GET | 206 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.45.13&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1627610657&mv=m&mvi=1&pl=24&rmhost=r4---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 10.0 Kb | whitelisted |
— | — | HEAD | 200 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.45.13&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1627610657&mv=m&mvi=1&pl=24&rmhost=r4---sn-1gi7znes.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
— | — | GET | 206 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.45.13&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1627611137&mv=m&mvi=1&pl=24&rmhost=r4---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 9.92 Kb | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 511 b | whitelisted |
— | — | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | html | 511 b | whitelisted |
— | — | GET | 206 | 173.194.160.70:80 | http://r1---sn-1gi7znes.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw?cms_redirect=yes&mh=-b&mip=85.203.45.13&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1627610657&mv=m&mvi=1&pl=24&rmhost=r4---sn-1gi7znes.gvt1.com&shardbypass=yes | US | binary | 10.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
760 | chrome.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
760 | chrome.exe | 35.227.233.104:443 | fifa-22.softonic.com | — | US | malicious |
760 | chrome.exe | 151.101.2.133:443 | sc.sftcdn.net | Fastly | US | malicious |
760 | chrome.exe | 104.109.90.33:443 | images.sftcdn.net | Akamai International B.V. | NL | unknown |
760 | chrome.exe | 178.250.0.130:443 | static.criteo.net | Criteo SA | FR | unknown |
760 | chrome.exe | 178.250.0.163:443 | sslwidget.criteo.com | Criteo SA | FR | unknown |
760 | chrome.exe | 178.250.2.146:443 | gum.criteo.com | Criteo SA | FR | unknown |
760 | chrome.exe | 142.250.186.130:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 142.250.186.106:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
760 | chrome.exe | 13.32.21.201:443 | c.amazon-adsystem.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
fifa-22.softonic.com |
| malicious |
accounts.google.com |
| shared |
images.sftcdn.net |
| whitelisted |
sc.sftcdn.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
c.amazon-adsystem.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
static.criteo.net |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3712 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3712 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3712 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3712 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
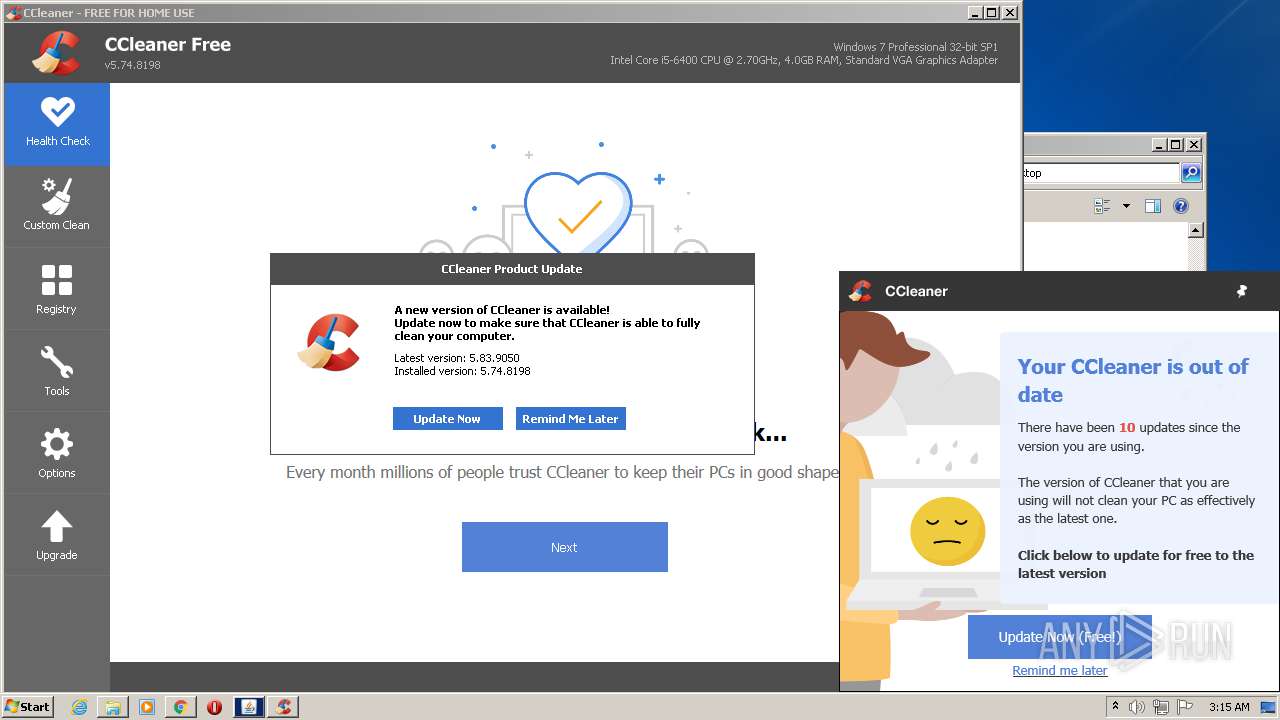
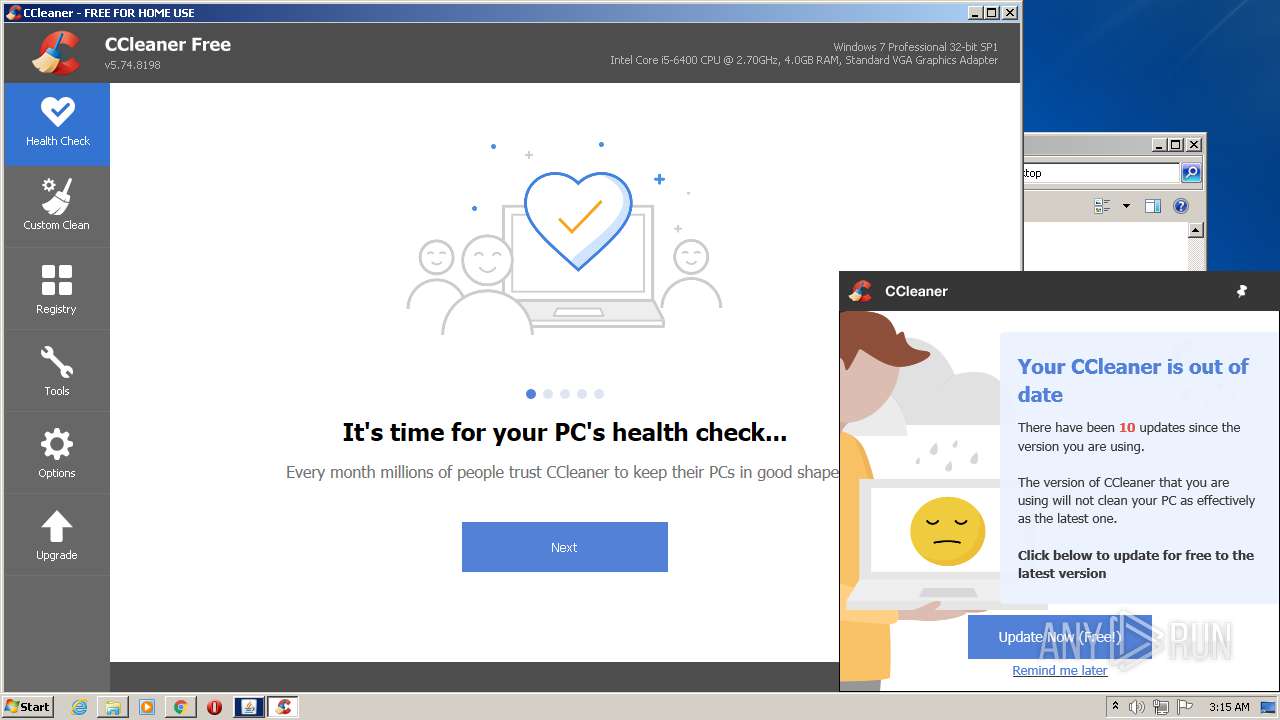
Process | Message |
|---|---|
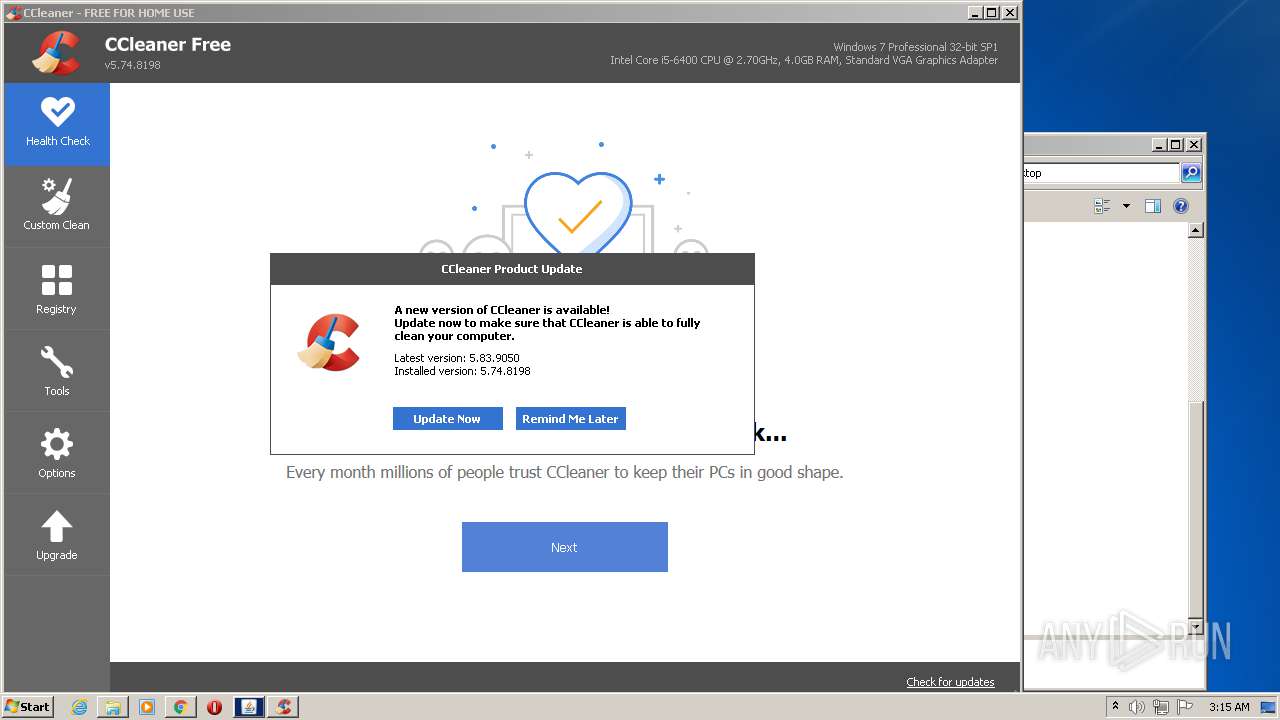
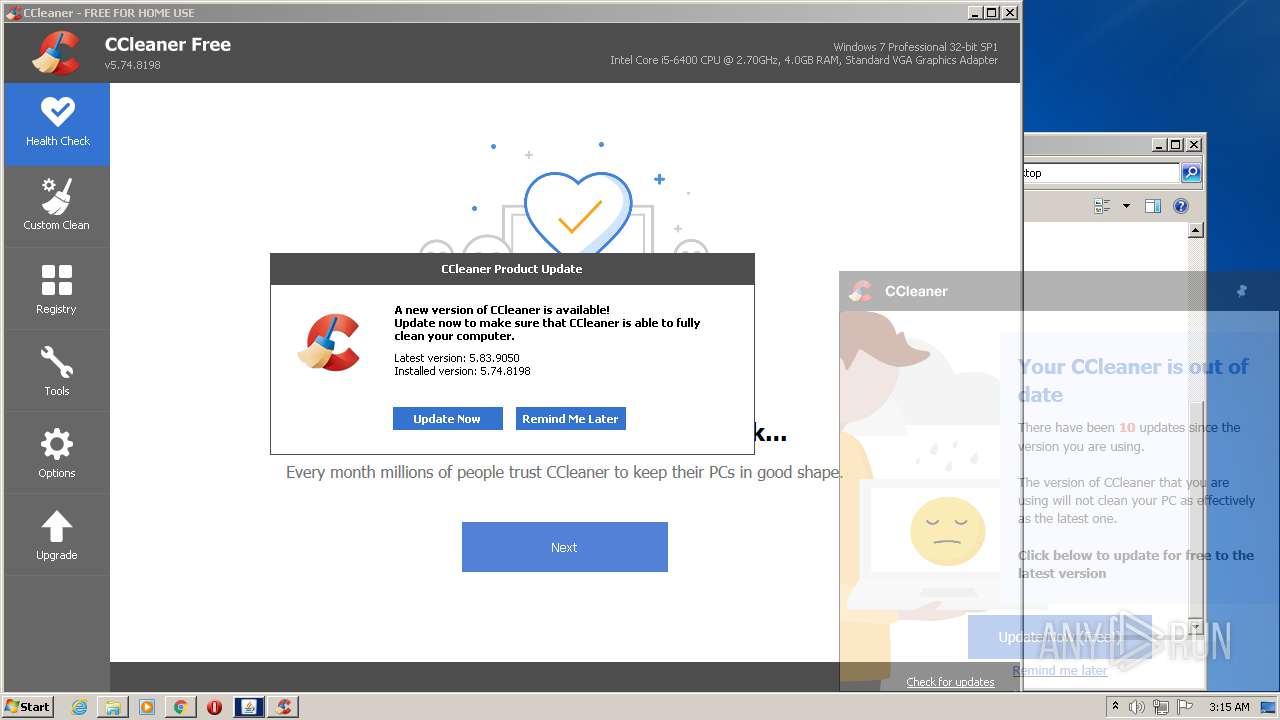
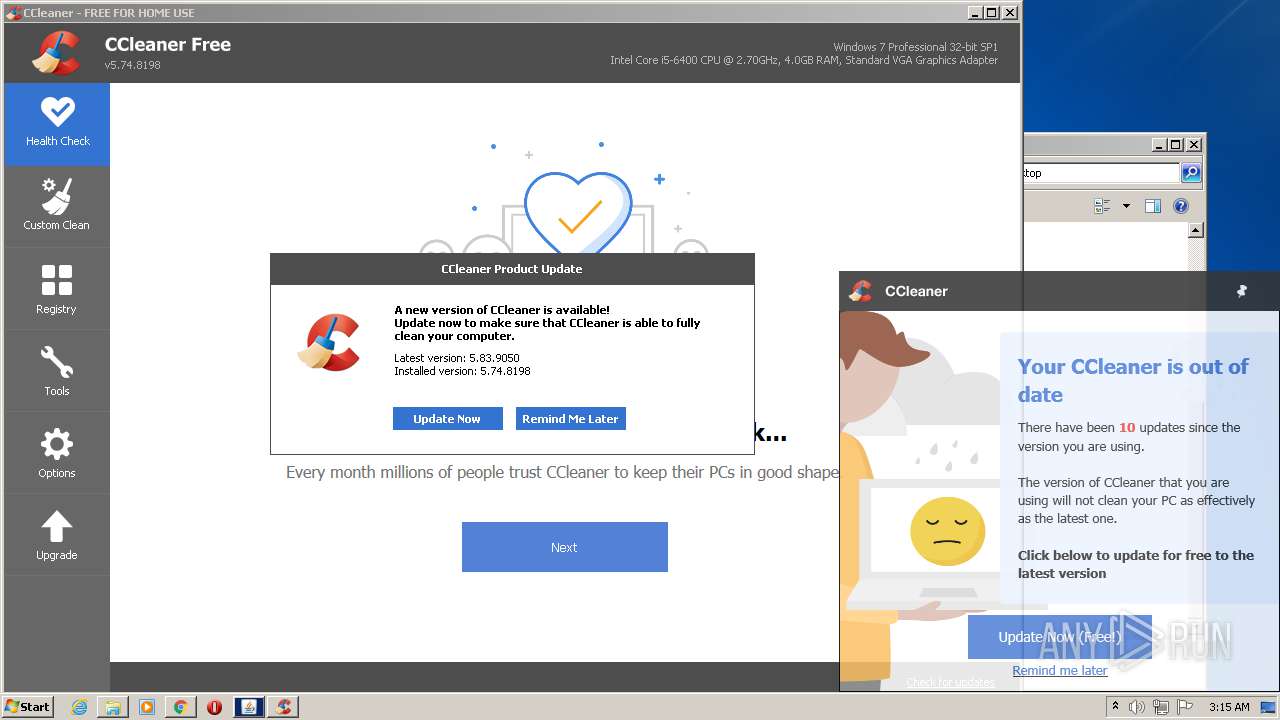
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | Using Sciter version 4.4.4.4-r8057
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | observing CurrentIndex changed - 0
|
CCleaner.exe | observing CurrentIndex changed - Context.FirstTime=true CurrentIndex=0 LastIndex=4
|
CCleaner.exe | observing currentResultDetails changed - None
|
CCleaner.exe | SetStrings - Live Region updated: ,
|
CCleaner.exe | observing currentModeType changed - Preview
|