| download: | index.html |
| Full analysis: | https://app.any.run/tasks/7588bddc-e10c-47df-86f3-f0885d0d2bf0 |
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2018, 16:50:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 928BF25B9569C155AE3D6A064ACCE31A |
| SHA1: | 48EA6899C1E020F949C08B94C1A0D794DFFD922B |
| SHA256: | E6647E22E6AA9775C54526AA5F6373C868FD8FB0CC9DAB4EA7DE5EC31F66304D |
| SSDEEP: | 3:nmNjJMzVJu+1zWNVq+Fzcwbyn:GMRJVCNXzzu |
MALICIOUS
Changes internet zones settings
- iexplore.exe (PID: 3088)
SUSPICIOUS
Starts Internet Explorer
- iexplore.exe (PID: 3088)
Application launched itself
- iexplore.exe (PID: 3088)
Reads Internet Cache Settings
- iexplore.exe (PID: 3548)
- iexplore.exe (PID: 3856)
Reads internet explorer settings
- iexplore.exe (PID: 3856)
- iexplore.exe (PID: 3548)
Creates files in the user directory
- iexplore.exe (PID: 3856)
- iexplore.exe (PID: 3548)
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 3396)
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 3088)
INFO
Loads rich edit control libraries
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 3396)
Dropped object may contain URL's
- iexplore.exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
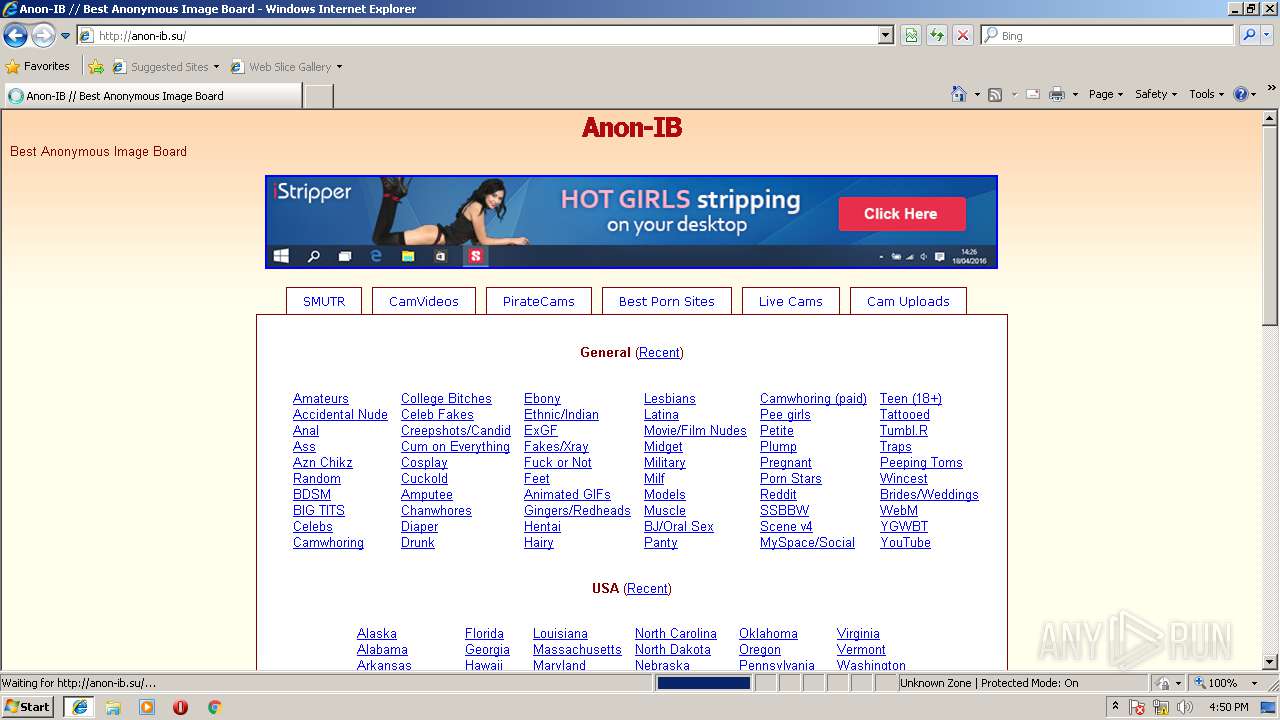
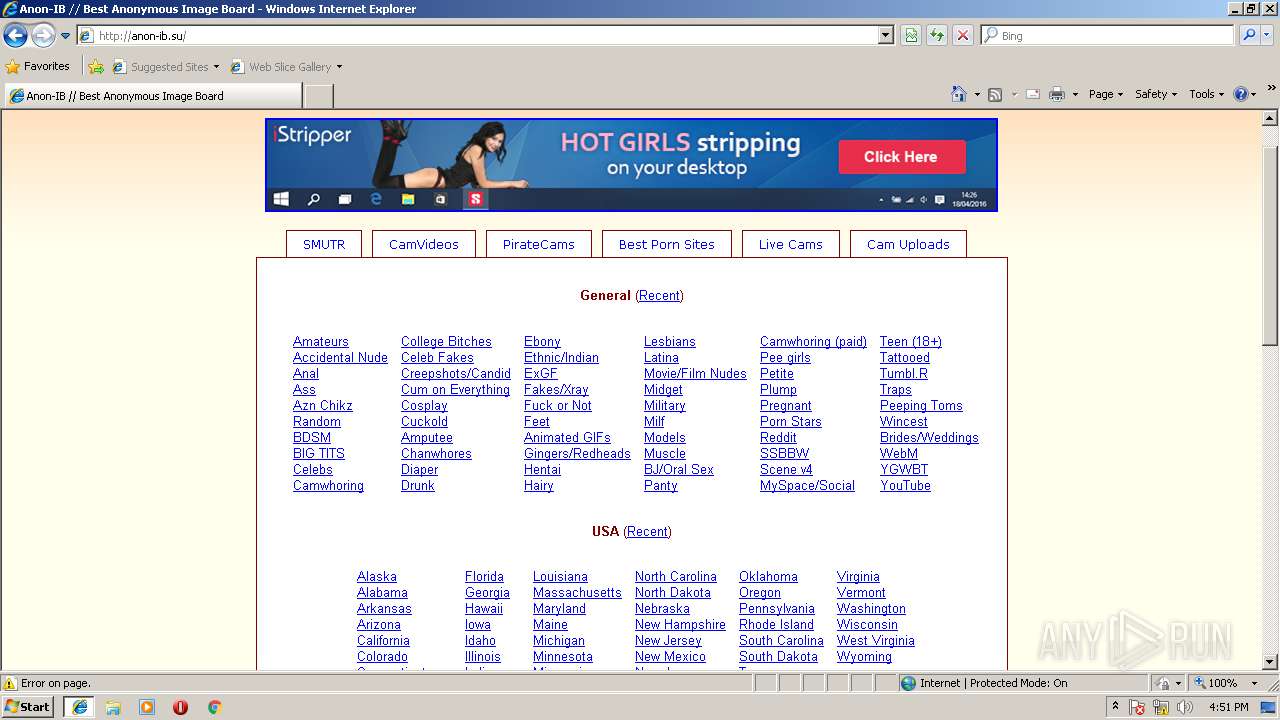
| 3088 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3396 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
| 3548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:137473 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3088 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
587
Read events
471
Write events
116
Delete events
0
Modification events
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005D00000009000000000000000000000000000000040000000000000090CE7F108CAFD301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A864640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {AAF6A557-2B95-11E8-943E-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3088) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207030001001300100032002F006A02 | |||
Executable files
0
Suspicious files
7
Text files
28
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GZH9GIXH\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4429C91BE7875D9F.TMP | — | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018031920180320\index.dat | dat | |
MD5:0C1D954802F0151C2FFC7E04AAD641D1 | SHA256:4249614EDF4922175962DD507F0393F763B9A009AB74B85F58B7C60D59494CFC | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:BE1233A076B3248D7A8CBE79E3B790F2 | SHA256:7D861BD5FA3333BFB2402393AA5647A98FDC14FB41BB3A923C1FF38BEB85C414 | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@anon-ib[2].txt | — | |
MD5:— | SHA256:— | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\X2RB5P9V\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\58BWEPS6\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
14
DNS requests
11
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
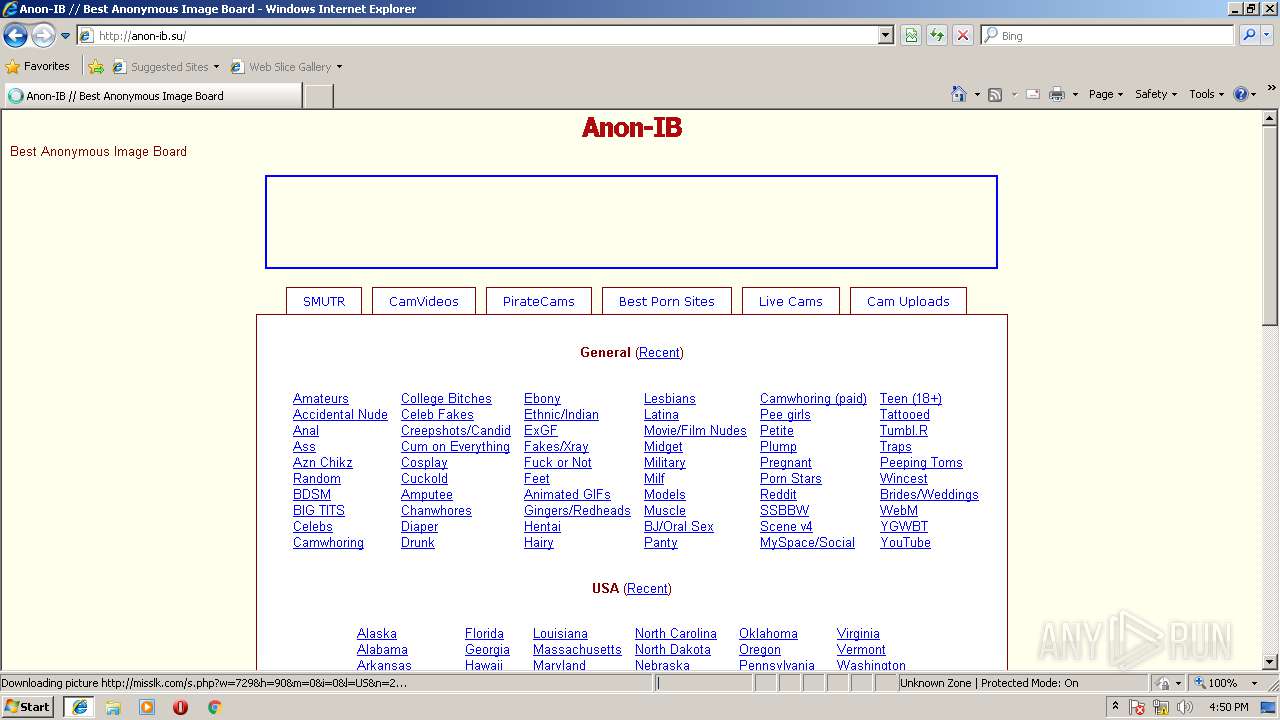
— | — | GET | — | 80.82.77.70:80 | http://anon-ib.su/stylesheets/yotsuba.css | SC | — | — | suspicious |
— | — | GET | — | 80.82.77.70:80 | http://anon-ib.su/stylesheets/style.css | SC | — | — | suspicious |
— | — | GET | 200 | 80.82.77.70:80 | http://anon-ib.su/stylesheets/style.css | SC | text | 3.23 Kb | suspicious |
— | — | GET | 200 | 80.82.77.70:80 | http://anon-ib.su/stylesheets/yotsuba.css | SC | text | 415 b | suspicious |
— | — | GET | 200 | 216.58.213.142:80 | http://www.google-analytics.com/analytics.js | US | text | 14.2 Kb | whitelisted |
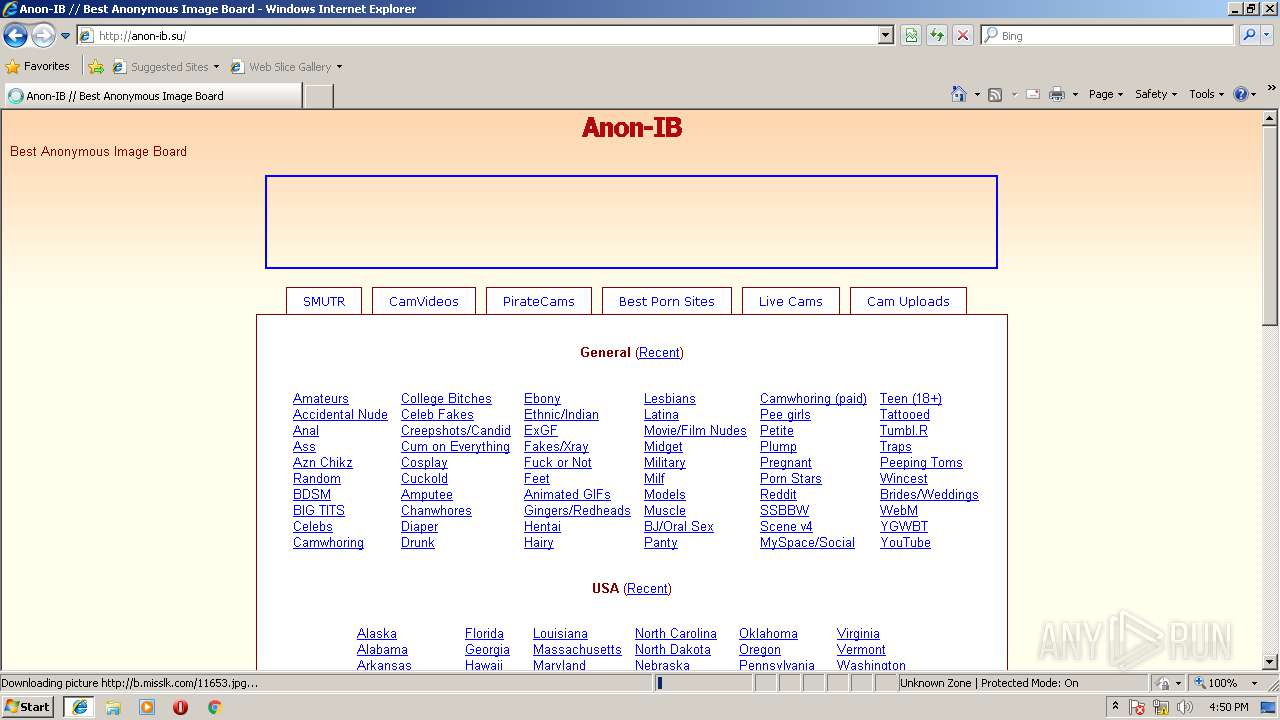
— | — | GET | 302 | 173.192.200.80:80 | http://misslk.com/s.php?w=729&h=90&m=0&i=0&l=US&n=2 | US | — | — | whitelisted |
— | — | GET | 200 | 80.82.77.70:80 | http://anon-ib.su/stylesheets/img/fade-yotsuba.png | SC | image | 149 b | suspicious |
— | — | GET | 302 | 216.58.213.142:80 | http://www.google-analytics.com/r/collect?v=1&_v=j66&a=668374623&t=pageview&_s=1&dl=http%3A%2F%2Fanon-ib.su%2F&ul=en-us&de=utf-8&dt=Anon-IB%20%2F%2F%20Best%20Anonymous%20Image%20Board&sd=32-bit&sr=1280x720&vp=1260x560&je=0&fl=26.0%20r0&_u=IEBAAE~&jid=758410243&gjid=532061290&cid=340311792.1521478257&tid=UA-59560634-1&_gid=1026493879.1521478257&_r=1&z=1265845204 | US | html | 417 b | whitelisted |
— | — | GET | 200 | 50.97.49.90:80 | http://b.misslk.com/11653.jpg | US | image | 74.7 Kb | unknown |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 80.82.77.70:80 | anon-ib.su | Quasi Networks LTD. | SC | suspicious |
— | — | 93.93.53.189:80 | pto.awecr.com | DuoDecad IT Services Luxembourg S.a r.l. | LU | unknown |
— | — | 216.58.213.142:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
— | — | 104.16.146.241:443 | chaturbate.com | Cloudflare Inc | US | shared |
— | — | 173.192.200.80:80 | misslk.com | SoftLayer Technologies Inc. | US | unknown |
— | — | 50.97.49.90:80 | b.misslk.com | SoftLayer Technologies Inc. | US | unknown |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 74.125.133.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 93.93.51.195:80 | static1.awestatic.com | DuoDecad IT Services Luxembourg S.a r.l. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
anon-ib.su |
| suspicious |
pto.awecr.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
misslk.com |
| whitelisted |
chaturbate.com |
| suspicious |
b.misslk.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
— | — | A Network Trojan was detected | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |