| File name: | 10%.exe |
| Full analysis: | https://app.any.run/tasks/10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 13:44:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | C76AEE58817B1A80E2D6C84D8519E0C9 |
| SHA1: | 3EAD7A39215F1A47BE6BBDBB1DAB37A56BA0BBBF |
| SHA256: | E6576A7D85D97CBB8090059F1098291C4A300130F4FE809555AF0BDDFEFD7AA1 |
| SSDEEP: | 98304:j1T2Q60oo5+EajRROBd9HPIkdYFuuOMwU8Jdk2n/vqisegFqy+vjRjiC5S3kE6H9:i8pPRBaHfjmxUPbyhGK0Y3aIg65 |
MALICIOUS
Changes the autorun value in the registry
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 1764)
SUSPICIOUS
Process drops legitimate windows executable
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
The process drops C-runtime libraries
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
Executable content was dropped or overwritten
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
Process drops python dynamic module
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
There is functionality for taking screenshot (YARA)
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
Loads Python modules
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 1764)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7396)
Application launched itself
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
INFO
The sample compiled with english language support
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
Checks supported languages
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 1764)
- ShellExperienceHost.exe (PID: 7396)
Reads the computer name
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 1764)
- ShellExperienceHost.exe (PID: 7396)
Create files in a temporary directory
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 1764)
PyInstaller has been detected (YARA)
- 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe (PID: 7444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:22 13:39:55+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 173568 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1764 | "C:\Users\admin\AppData\Local\Temp\10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe" | C:\Users\admin\AppData\Local\Temp\10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7396 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7444 | "C:\Users\admin\AppData\Local\Temp\10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe" | C:\Users\admin\AppData\Local\Temp\10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7488 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7520 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7712 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 618
Read events
1 617
Write events
1
Delete events
0
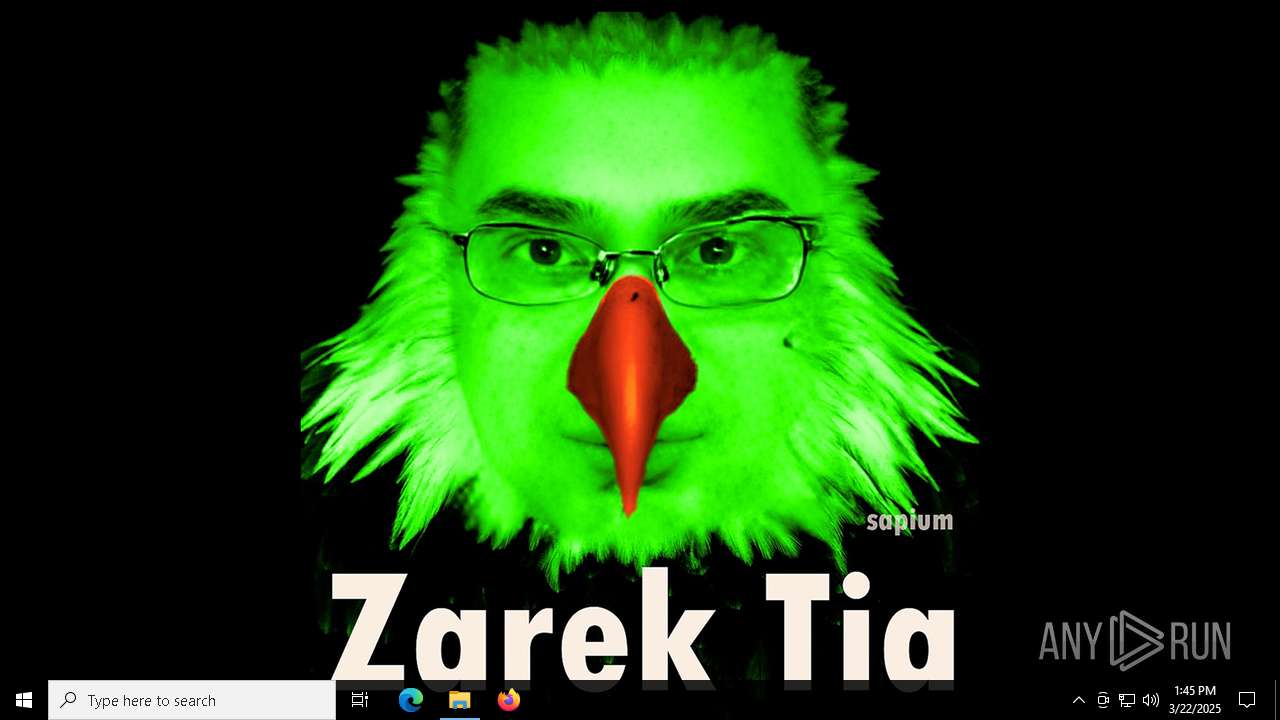
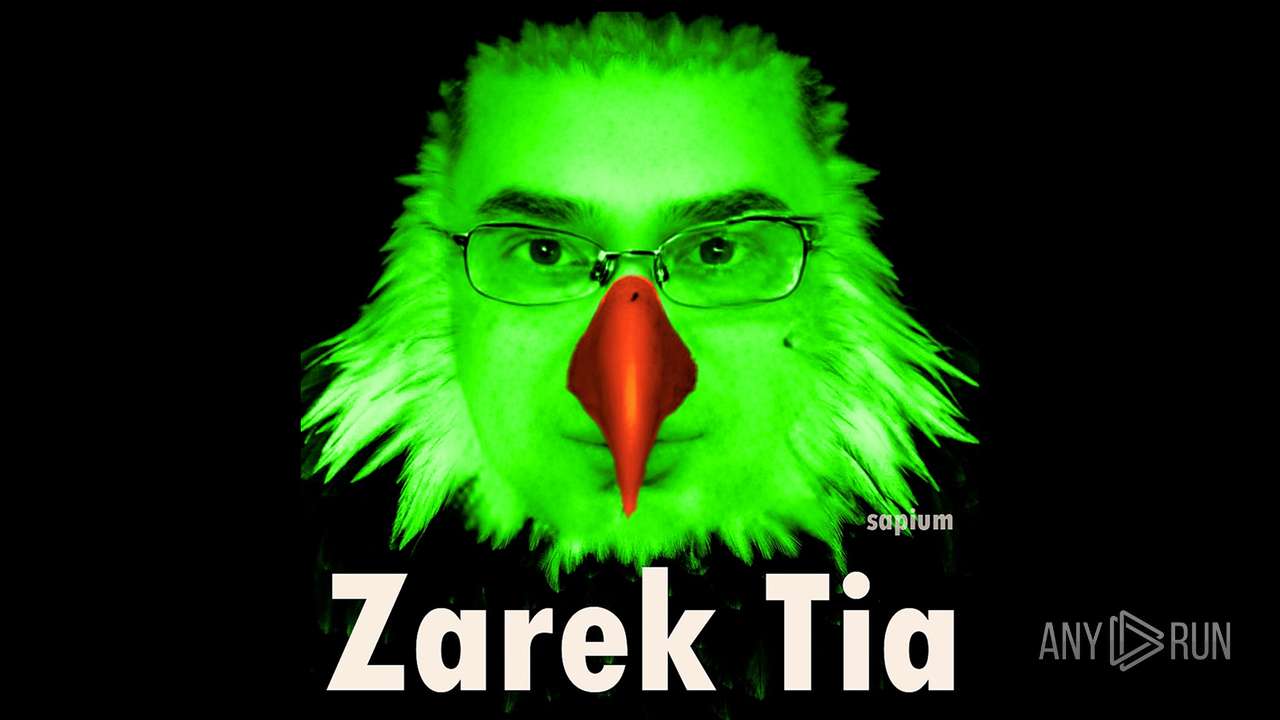
Modification events
| (PID) Process: | (1764) 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | JokeApp |
Value: C:\Users\admin\AppData\Local\Temp\10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | |||
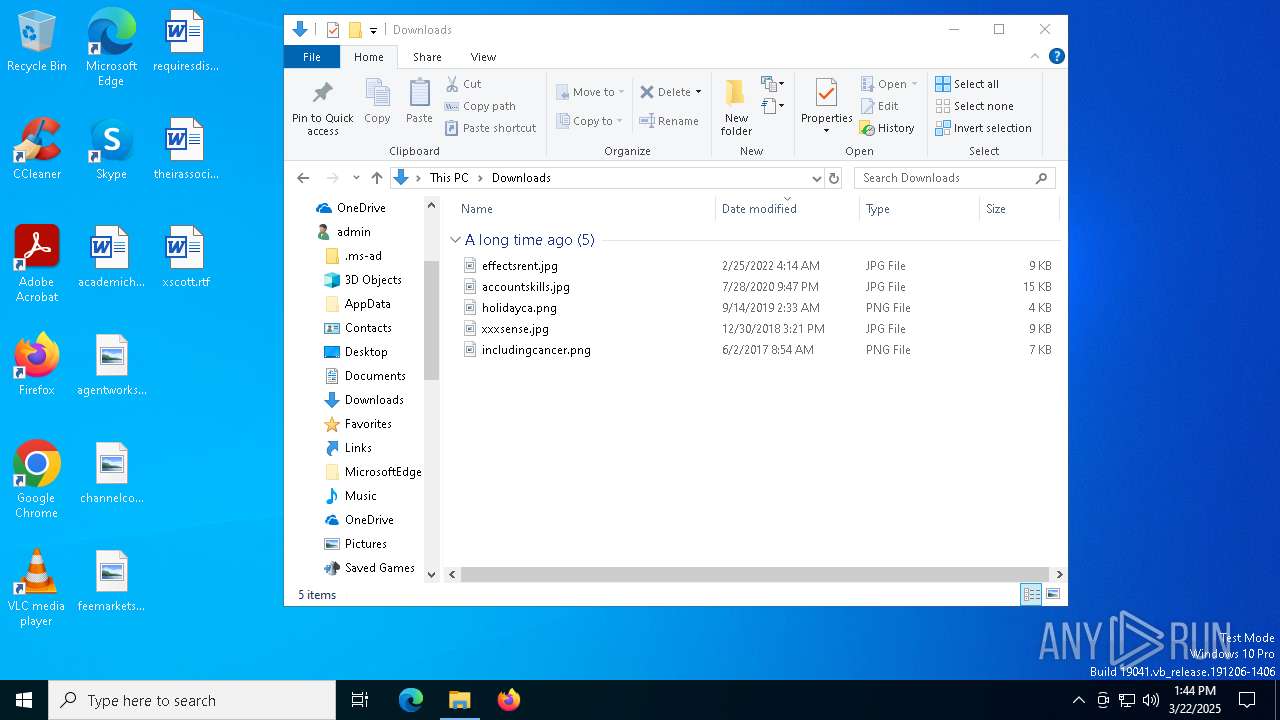
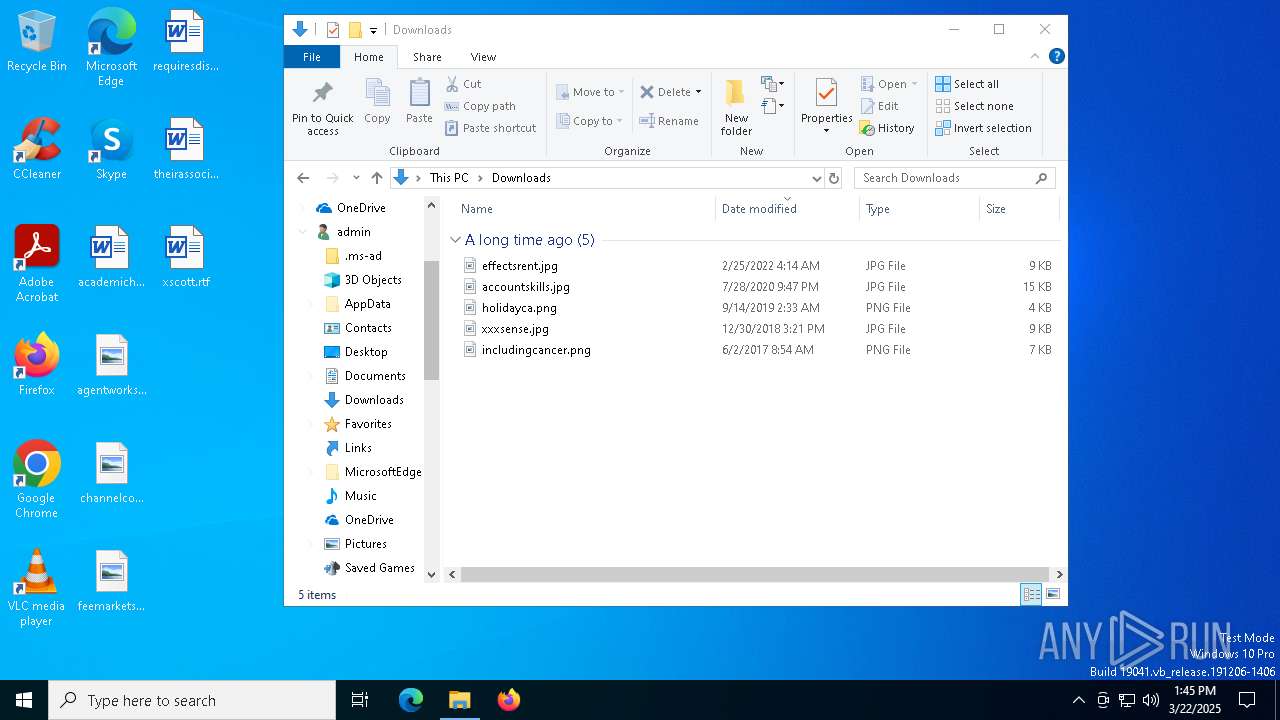
Executable files
27
Suspicious files
5
Text files
921
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\_bz2.pyd | executable | |
MD5:90F58F625A6655F80C35532A087A0319 | SHA256:BD8621FCC901FA1DE3961D93184F61EA71068C436794AF2A4449738CCF949946 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\VCRUNTIME140.dll | executable | |
MD5:BE8DBE2DC77EBE7F88F910C61AEC691A | SHA256:4D292623516F65C80482081E62D5DADB759DC16E851DE5DB24C3CBB57B87DB83 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\_ctypes.pyd | executable | |
MD5:452305C8C5FDA12F082834C3120DB10A | SHA256:543CE9D6DC3693362271A2C6E7D7FC07AD75327E0B0322301DD29886467B0B0E | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\_tcl_data\auto.tcl | text | |
MD5:08EDF746B4A088CB4185C165177BD604 | SHA256:517204EE436D08EFC287ABC97433C3BFFCAF42EC6592A3009B9FD3B985AD772C | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\_hashlib.pyd | executable | |
MD5:8BAEB2BD6E52BA38F445EF71EF43A6B8 | SHA256:6C50C9801A5CAF0BB52B384F9A0D5A4AA182CA835F293A39E8999CF6EDF2F087 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\PIL\_webp.cp312-win_amd64.pyd | executable | |
MD5:A21A05FB1CB9830977DF1ED788B805D6 | SHA256:6C7AF1E7C6D500F39BBF29E5DB9F897F3BCBB830117E6B6AD177FE1965413152 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\PIL\_imagingtk.cp312-win_amd64.pyd | executable | |
MD5:DD231AFD7EF2247CC89B27B8EE5A8F32 | SHA256:3FA78A526C9D24620FD84673BB724C86FB68F8BF290B1AC7D8FD94C895081538 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\PIL\_imaging.cp312-win_amd64.pyd | executable | |
MD5:2B071B2EFF704F30B8A59D5B6D06C845 | SHA256:286CB70BFF80BCFD68E8BCEC15F019A433C213E9AF1998A241177009CB2ACB39 | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\_ssl.pyd | executable | |
MD5:6774D6FB8B9E7025254148DC32C49F47 | SHA256:2B6F1B1AC47CB7878B62E8D6BB587052F86CA8145B05A261E855305B9CA3D36C | |||
| 7444 | 10a4f1f2-90c9-469a-9f5a-40d4a0f37e1c.exe | C:\Users\admin\AppData\Local\Temp\_MEI74442\PIL\_imagingcms.cp312-win_amd64.pyd | executable | |
MD5:F9936AF55479CF0DCB14735628E65DC1 | SHA256:D037B8AF3B59C56E70C38A044EF4532730C77C5602F8EE8B76E2A5FDCFEA21B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6028 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8108 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8108 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6028 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6028 | backgroundTaskHost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |