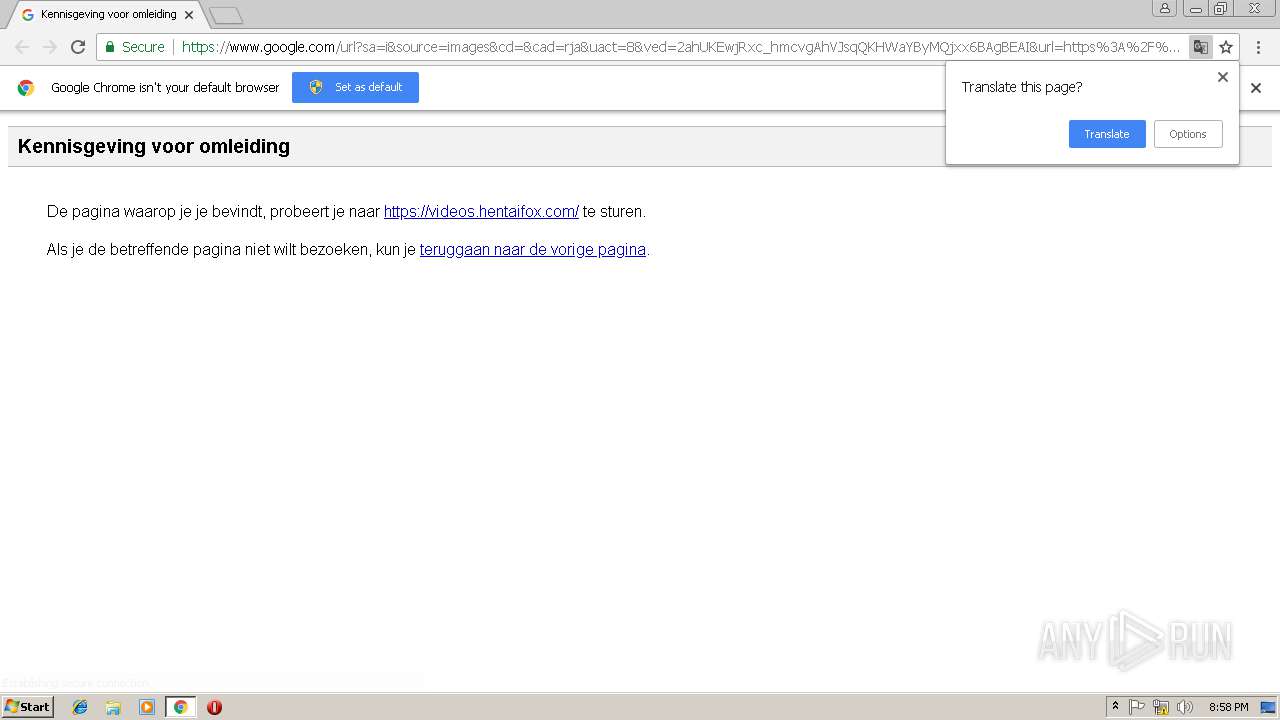
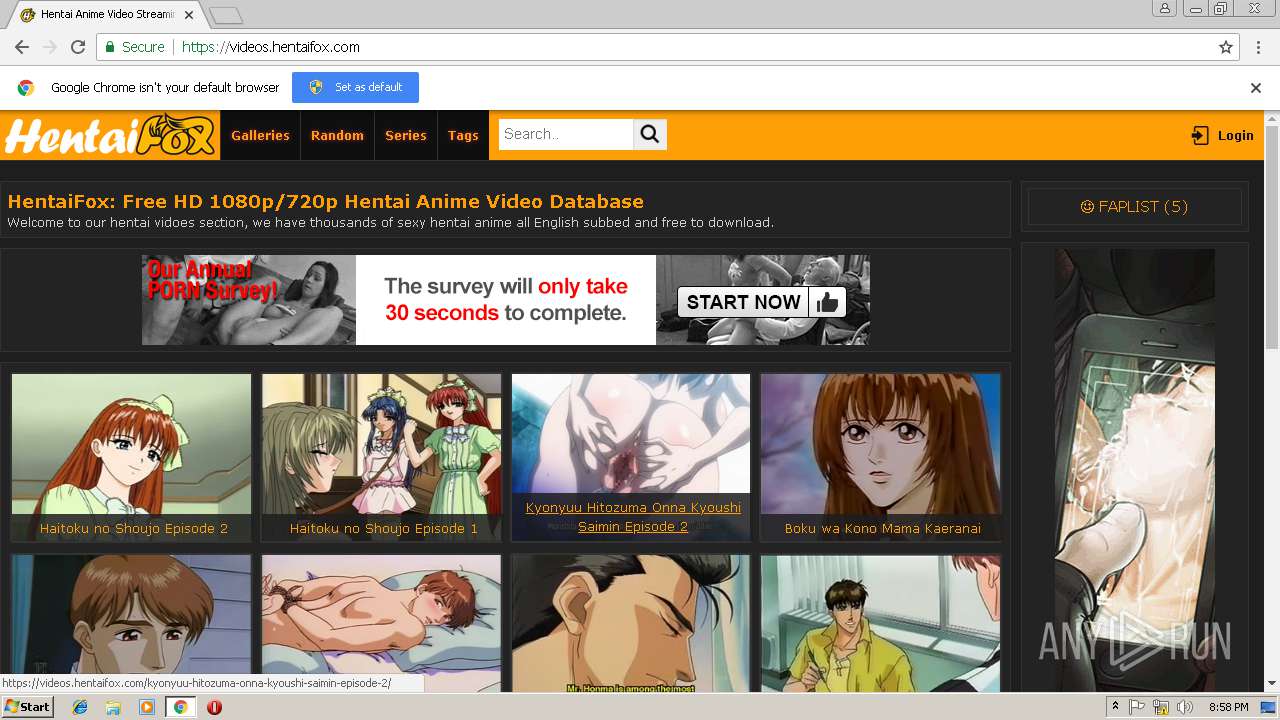
| URL: | https://www.google.com/url?sa=i&source=images&cd=&cad=rja&uact=8&ved=2ahUKEwjRxc_hmcvgAhVJsqQKHWaYByMQjxx6BAgBEAI&url=https%3A%2F%2Fvideos.hentaifox.com%2F&psig=AOvVaw1yruXlSY9EPq5piA0zD54m&ust=1550782511876806 |
| Full analysis: | https://app.any.run/tasks/38df6287-de95-43db-b038-610153066bcb |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2019, 20:57:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FD83D7E7E8B01A3A79C7C8EB0237A107 |
| SHA1: | 3669EA9DF2DF9D5B9D4B8FB31AD4FCA62238373C |
| SHA256: | E656CAF0885D0269DA53F9379D04079B6B9B3A2EA880D8FE0180508158704BF7 |
| SSDEEP: | 6:2OLI2sZCl1w4pNFOk7PYK7KR3zAtBlxSiiEcQA5:2V2OEnNs/ZEvlxBm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AA494380577D90A2CDEFA9D0D1E41C19 --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=7902E1C7612ABD71EF83087B4AAD65DB --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7902E1C7612ABD71EF83087B4AAD65DB --renderer-client-id=4 --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.google.com/url?sa=i&source=images&cd=&cad=rja&uact=8&ved=2ahUKEwjRxc_hmcvgAhVJsqQKHWaYByMQjxx6BAgBEAI&url=https%3A%2F%2Fvideos.hentaifox.com%2F&psig=AOvVaw1yruXlSY9EPq5piA0zD54m&ust=1550782511876806 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2960 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AFB197B401BD848EEE811BD697A8DA36 --mojo-platform-channel-handle=4644 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2936 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8879D6AC121355F6564EFF056EF26AAB --mojo-platform-channel-handle=3712 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x700600b0,0x700600c0,0x700600cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --service-pipe-token=A476A9D1919CDB71C85A5C94B7F0B3CD --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A476A9D1919CDB71C85A5C94B7F0B3CD --renderer-client-id=3 --mojo-platform-channel-handle=2148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,6648249723427096982,15695952238347034389,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5FF39FA20495A7B4DEC667782539EA8F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5FF39FA20495A7B4DEC667782539EA8F --renderer-client-id=6 --mojo-platform-channel-handle=4568 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
560
Read events
512
Write events
45
Delete events
3
Modification events
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2932-13195169887185625 |
Value: 259 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2932-13195169887185625 |
Value: 259 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
72
Text files
80
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a4c806f6-671a-4ad9-9aa7-97d793cbf183.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e02b4169-4add-40d0-a846-85cd23bcc1cb.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20d4d8.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
128
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
2932 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEA96F1Rsa9jjw5yJodY%2Fbhg%3D | US | der | 471 b | whitelisted |
2932 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2932 | chrome.exe | GET | 200 | 52.222.146.104:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2932 | chrome.exe | GET | 200 | 184.30.214.88:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
2932 | chrome.exe | GET | 200 | 172.217.168.227:80 | http://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=68 | US | compressed | 28.1 Kb | whitelisted |
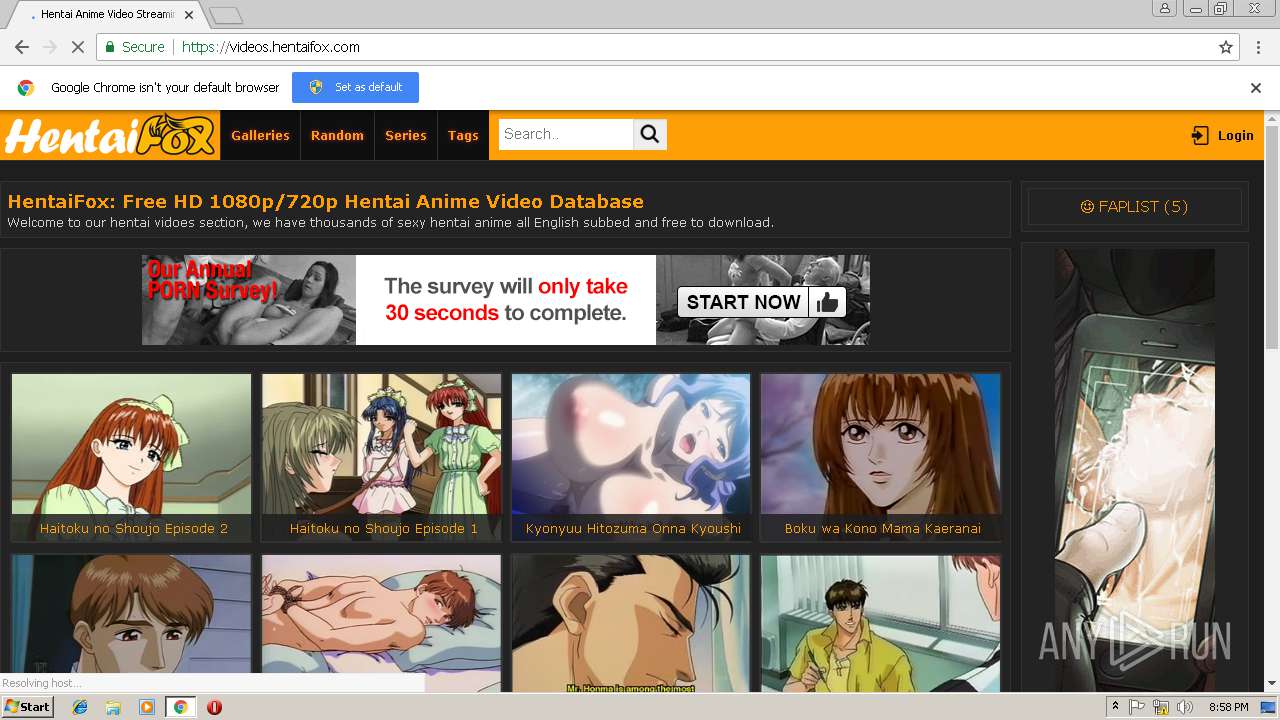
2932 | chrome.exe | GET | 200 | 216.21.13.15:80 | http://qbldzsktv.com/gNZ.htm?e=6033583&c=1033728316&g=1550696306&p=1439378565&s=409&n=%21InAmyfS5bqp%2BrSmAQ%2BVgbEIRVdLxdIRvXTzp9tFmmw0zlzjD8vGap7bTrYQws4oJ5i6seebFHbCm30K2esvqFuA4kHWypj40xoUbyIcyRpkh6dh4Vh7Yj8eba6tZtaoh1fYDztbpOALNCslQygoyQGoRaONZGxFT264BsHfxRe%2F64RSkaF1a5kdPdZ0Kb7wpOIdSnhYbSEkj754C%2FLoXTKq1HdBCi%2F%2BNfYfTcwUcMEQFjk%2Fif4WPfxHGF5nZ28vMIVA21L5Gse8ZL%2Fl%2BX4RQ0iDlmcukaaC%2FMBSynqD0zeyZVv4A%2Bj5L%2BhqnDZ7bp6Fv2MUpxdP2ZLWotamPcCiA3qUt304VoLF5Ah%2FdUmsz3Dhkjnn9zYofHRcTL4H5XGv2sHU3qz038ZQmLp2AZdbG%2FA%3D%3D&r=&p=&g= | US | html | 1.78 Kb | suspicious |
2932 | chrome.exe | GET | 303 | 216.21.13.15:80 | http://qbldzsktv.com/e2cf3.aspx?65374&94640=direct&siteId=3134249&371b4=0.0&c7694=10&ed678=http%3A%2F%2F35.225.234.73%2FMTU1MDczNjM0Ni8xNTUyMzAzMTQ3LzE1NTA3NDQ1MjU%3D&70556&b3905= | US | — | — | suspicious |
2932 | chrome.exe | GET | 302 | 216.21.13.15:80 | http://qbldzsktv.com/hpKqd.html?k=10000000000&v=0&c=&t=2206768486824&g=&a=1033728316&i=1439378565&z=409&w=%21InAmyfS5bqp%2BrSmAQ%2BVgbEIRVdLxdIRvXTzp9tFmmw0zlzjD8vGap7bTrYQws4oJ5i6seebFHbCm30K2esvqFuA4kHWypj40xoUbyIcyRpkh6dh4Vh7Yj8eba6tZtaoh1fYDztbpOALNCslQygoyQGoRaONZGxFT264BsHfxRe%2F64RSkaF1a5kdPdZ0Kb7wpOIdSnhYbSEkj754C%2FLoXTKq1HdBCi%2F%2BNfYfTcwUcMEQFjk%2Fif4WPfxHGF5nZ28vMIVA21L5Gse8ZL%2Fl%2BX4RQ0iDlmcukaaC%2FMBSynqD0zeyZVv4A%2Bj5L%2BhqnDZ7bp6Fv2MUpxdP2ZLWotamPcCiA3qUt304VoLF5Ah%2FdUmsz3Dhkjnn9zYofHRcTL4H5XGv2sHU3qz038ZQmLp2AZdbG%2FA%3D%3D&m=9837646769033365&r=017&s=0&d=1 | US | compressed | 1.78 Kb | suspicious |
2932 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2932 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 104.31.95.127:443 | go.hentaigold.net | Cloudflare Inc | US | shared |
2932 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 95.211.229.246:443 | syndication.exosrv.com | LeaseWeb Netherlands B.V. | NL | suspicious |
2932 | chrome.exe | 68.232.35.133:443 | ads.exosrv.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2932 | chrome.exe | 185.225.208.133:443 | widgets.amung.us | — | — | suspicious |
2932 | chrome.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2932 | chrome.exe | 67.202.94.93:443 | whos.amung.us | Steadfast | US | malicious |
2932 | chrome.exe | 205.185.216.42:443 | ads.exoclick.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
translate.googleapis.com |
| whitelisted |
videos.hentaifox.com |
| suspicious |
safebrowsing.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
hentaifox.com |
| whitelisted |