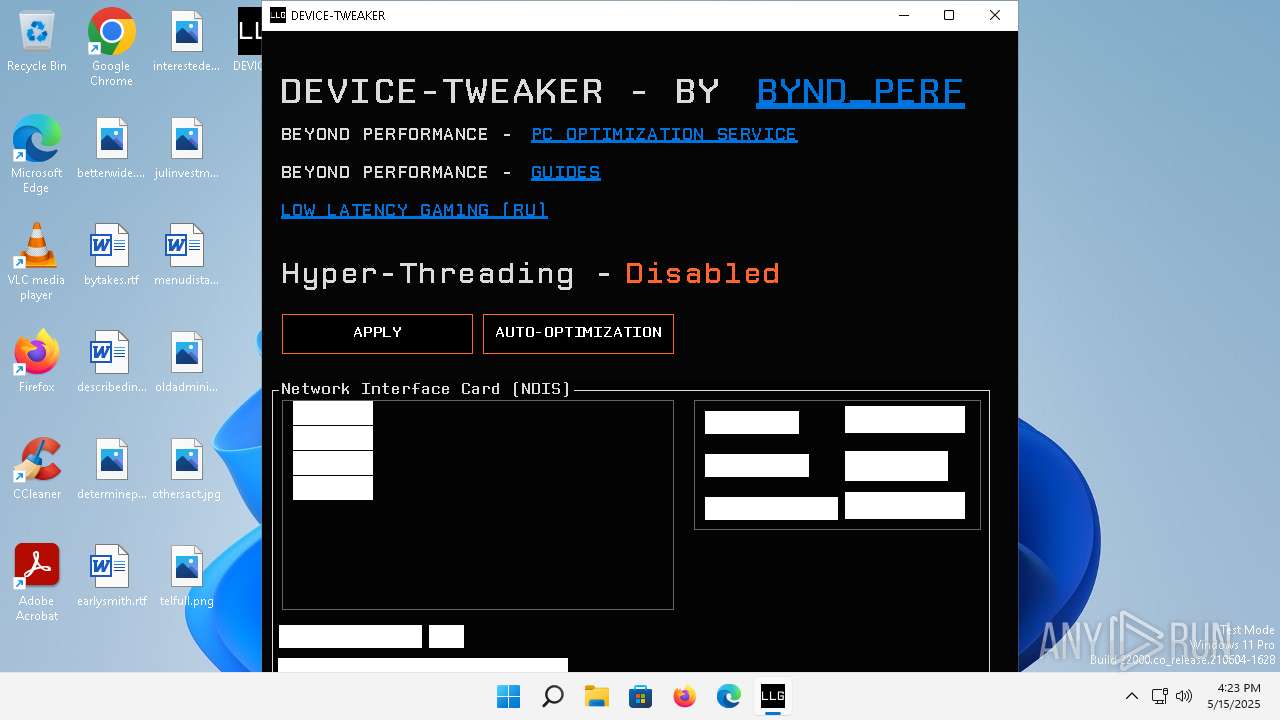
| File name: | DEVICE-TWEAKER.exe |
| Full analysis: | https://app.any.run/tasks/10f92032-b55c-4a77-bcde-99d68961503e |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 16:22:42 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 5E915A7BAE95BEDB3A5C7C5AA1865C0B |
| SHA1: | BE946C7B6CFEF71B8E598D02C8A81B81B39B5435 |
| SHA256: | E652B9B466D84ADBDA644A87AEB36E087D2A1569B35D58DDDAE46C332A3FFF91 |
| SSDEEP: | 98304:SCDr9I6mZMz9hPJYkrcSPiiphGfjJ4Mo2qF5km+UnhWGrU7RuY9bljBWT6ogU0JR:H6GXnisQ9dOWlK/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- DEVICE-TWEAKER.exe (PID: 4712)
Uses base64 encoding (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 4712)
Writes data into a file (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 4712)
Reads security settings of Internet Explorer
- DEVICE-TWEAKER.exe (PID: 4712)
Reads settings of System Certificates
- DEVICE-TWEAKER.exe (PID: 4712)
Reads the Internet Settings
- DEVICE-TWEAKER.exe (PID: 4712)
INFO
Process checks whether UAC notifications are on
- DEVICE-TWEAKER.exe (PID: 4712)
Reads the computer name
- DEVICE-TWEAKER.exe (PID: 4712)
Checks supported languages
- DEVICE-TWEAKER.exe (PID: 4712)
Reads the machine GUID from the registry
- DEVICE-TWEAKER.exe (PID: 4712)
Reads Environment values
- DEVICE-TWEAKER.exe (PID: 4712)
Create files in a temporary directory
- DEVICE-TWEAKER.exe (PID: 4712)
Reads the software policy settings
- DEVICE-TWEAKER.exe (PID: 4712)
Checks if a key exists in the options dictionary (POWERSHELL)
- DEVICE-TWEAKER.exe (PID: 4712)
Themida protector has been detected
- DEVICE-TWEAKER.exe (PID: 4712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:13 11:38:29+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 11 |
| CodeSize: | 139264 |
| InitializedDataSize: | 5632 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb4c058 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.8.8 |
| ProductVersionNumber: | 1.4.8.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | BYND_PERF |
| FileVersion: | 1.4.8.8 |
| InternalName: | DEVICE-TWEAKER.exe |
| LegalCopyright: | BYND_PERF |
| OriginalFileName: | DEVICE-TWEAKER.exe |
| ProductName: | DEVICE-TWEAKER |
| ProductVersion: | 1.4.8.8 |
| AssemblyVersion: | 1.4.8.8 |
Total processes
101
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3420 | "C:\Users\admin\Desktop\DEVICE-TWEAKER.exe" | C:\Users\admin\Desktop\DEVICE-TWEAKER.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BYND_PERF Exit code: 3221226540 Version: 1.4.8.8 Modules
| |||||||||||||||
| 4712 | "C:\Users\admin\Desktop\DEVICE-TWEAKER.exe" | C:\Users\admin\Desktop\DEVICE-TWEAKER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BYND_PERF Version: 1.4.8.8 Modules
| |||||||||||||||
Total events
23 680
Read events
23 672
Write events
8
Delete events
0
Modification events
| (PID) Process: | (4712) DEVICE-TWEAKER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4712) DEVICE-TWEAKER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4712) DEVICE-TWEAKER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4712) DEVICE-TWEAKER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4712 | DEVICE-TWEAKER.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gybob4sv.jrk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4712 | DEVICE-TWEAKER.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bg2thxzf.s4e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4712 | DEVICE-TWEAKER.exe | C:\Users\admin\AppData\Local\Temp\CPMono_v07_Plain.ttf | binary | |
MD5:CEC2670064F93D247C30D60FFD375E30 | SHA256:43EDBE0C38AEB163BD8A581AD21EA071B0C0EB52B0999D760ED373CF0A6A210D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
14
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f4d2af8a3f2bbfd8 | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.4:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?b5c209eb39f9a373 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ae0cec35f73e7201 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?58861b0b6735a5a4 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2efe063e74f19306 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 184.24.77.4:80 | — | Akamai International B.V. | DE | unknown |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3640 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5088 | smartscreen.exe | 48.209.180.244:443 | checkappexec.microsoft.com | — | US | whitelisted |
2592 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | Akamai International B.V. | US | whitelisted |
2768 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2988 | OfficeClickToRun.exe | 20.189.173.18:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |